| File name: | e2ae3093df1bc88be2cc11f4ce2ad8017a14edf46cbaf0bd1141afc976af5715.apk |
| Full analysis: | https://app.any.run/tasks/c66741dd-1666-496f-afce-4393e9d22e73 |
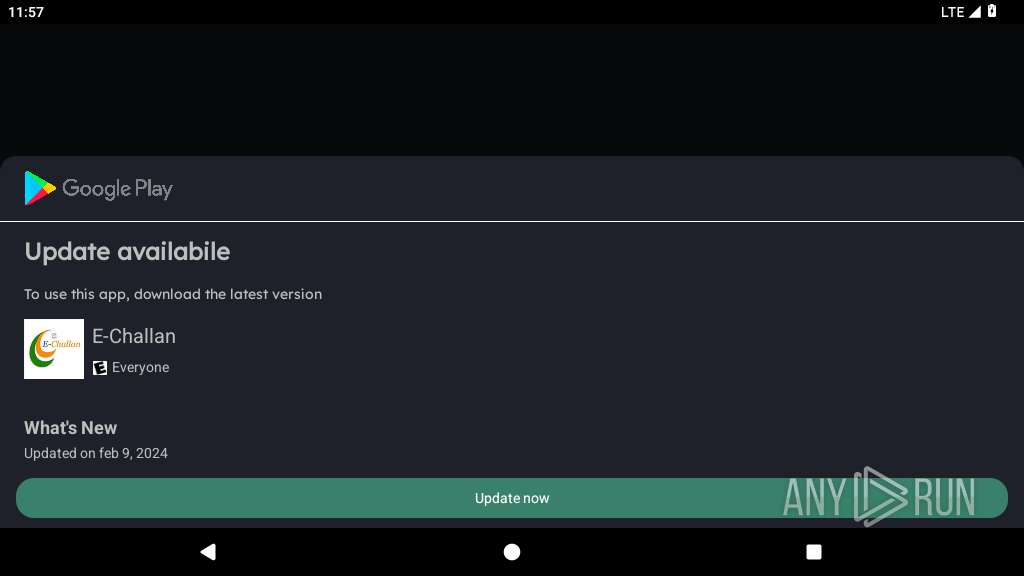
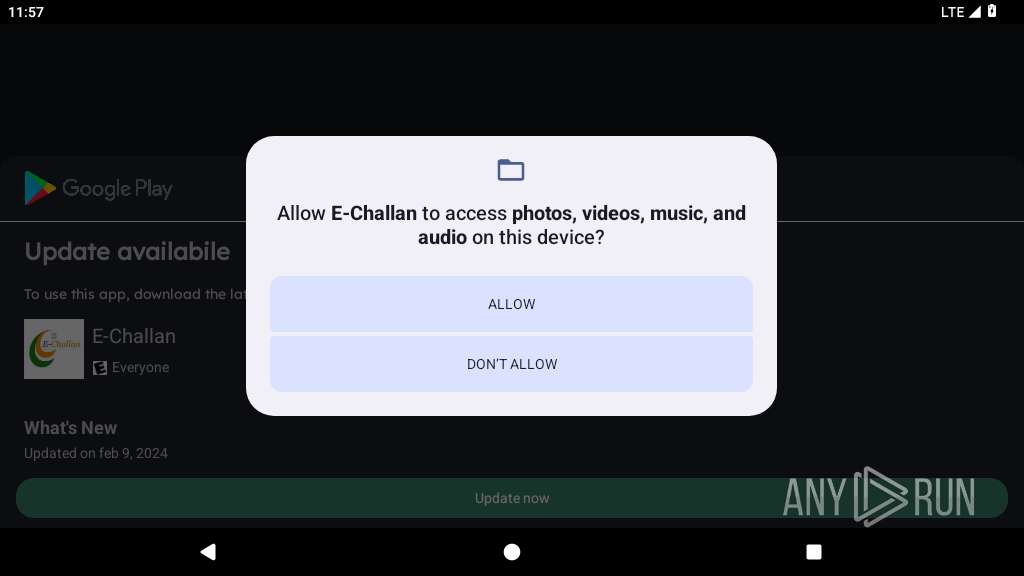
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2025, 23:57:11 |
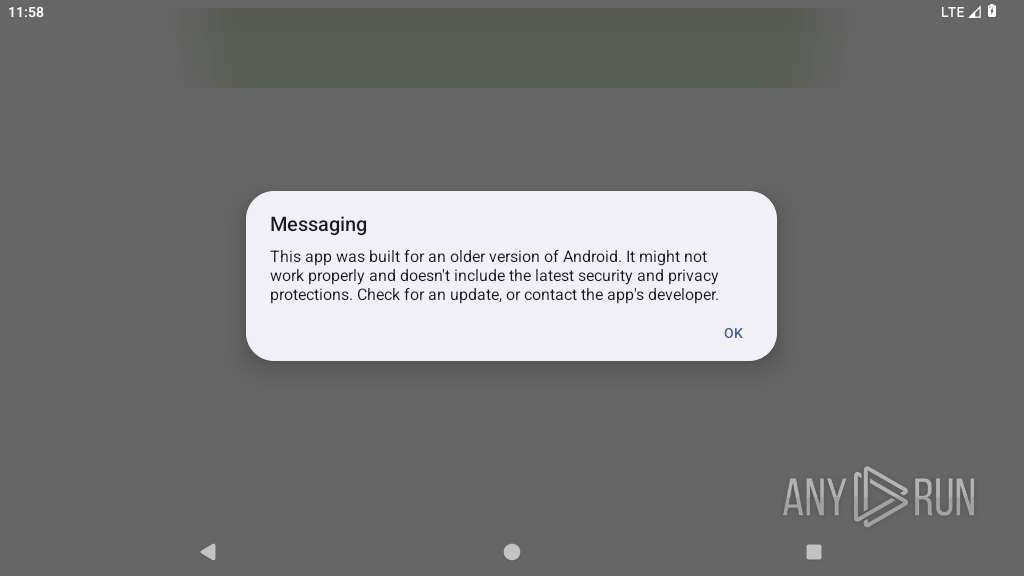
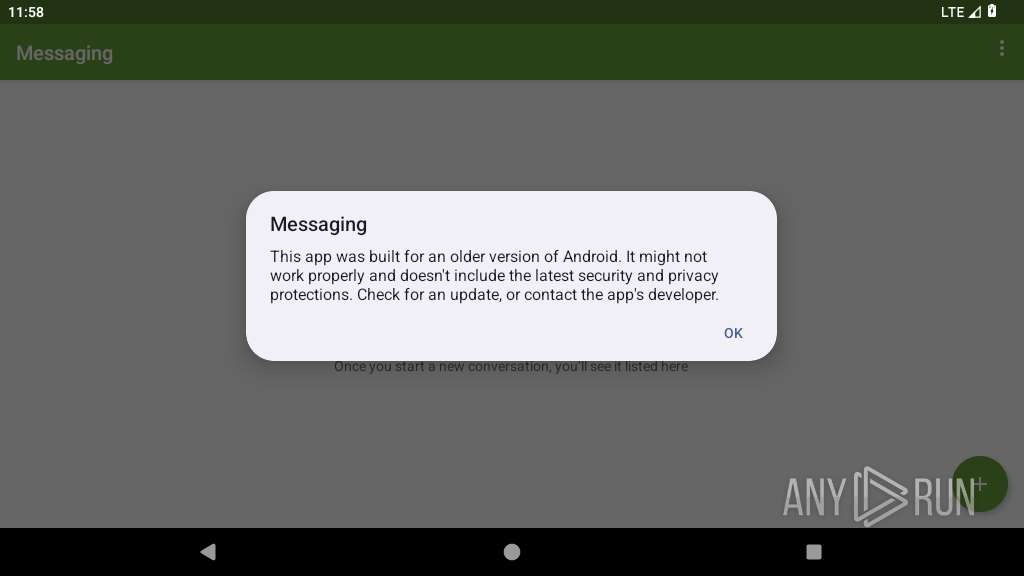
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with AndroidManifest.xml, with APK Signing Block |
| MD5: | 911B816269D6FE93BBCE7EA74B7B801B |
| SHA1: | A497676AF43702E825D240435A20F3DA0B37C1F1 |
| SHA256: | E2AE3093DF1BC88BE2CC11F4CE2AD8017A14EDF46CBAF0BD1141AFC976AF5715 |
| SSDEEP: | 98304:gnQQVxJ626bObN/YSr3s52irhzIb0tRdf8XKJDQ/I2wmdJj3hFuMaY8J1QwjhBZd:553vNQS |
MALICIOUS
Initiates background APK installation
- app_process64 (PID: 2273)
SUSPICIOUS
No suspicious indicators.INFO
Dynamically registers broadcast event listeners
- app_process64 (PID: 2273)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Unknown (7989) |
| ZipModifyDate: | 2025:01:04 02:13:00 |
| ZipCRC: | 0x68f975a5 |
| ZipCompressedSize: | 6490 |
| ZipUncompressedSize: | 18544 |
| ZipFileName: | AndroidManifest.xml |
Total processes
134
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2273 | com.appd.instll.load | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 6 | ||||
| 2354 | crash_dump64 2273 2353 4 | /apex/com.android.runtime/bin/crash_dump64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2355 | crash_dump64 2273 2353 4 | /apex/com.android.runtime/bin/crash_dump64 | — | crash_dump64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2356 | com.appd.instll.load | /system/bin/app_process64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2357 | com.appd.instll.load | /system/bin/app_process64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2371 | org.chromium.webview_shell | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2398 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2414 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2453 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2273 | app_process64 | /data/user/0/com.appd.instll.load/cache/oat_primary/arm64/base.2273.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 172.217.16.131:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
445 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.0:123 | time.android.com | — | — | whitelisted |
— | — | 172.217.16.131:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.184.196:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.110.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2398 | app_process32 | 142.250.184.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2453 | app_process32 | 142.250.181.227:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2453 | app_process32 | 142.250.186.110:443 | dl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
dl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |