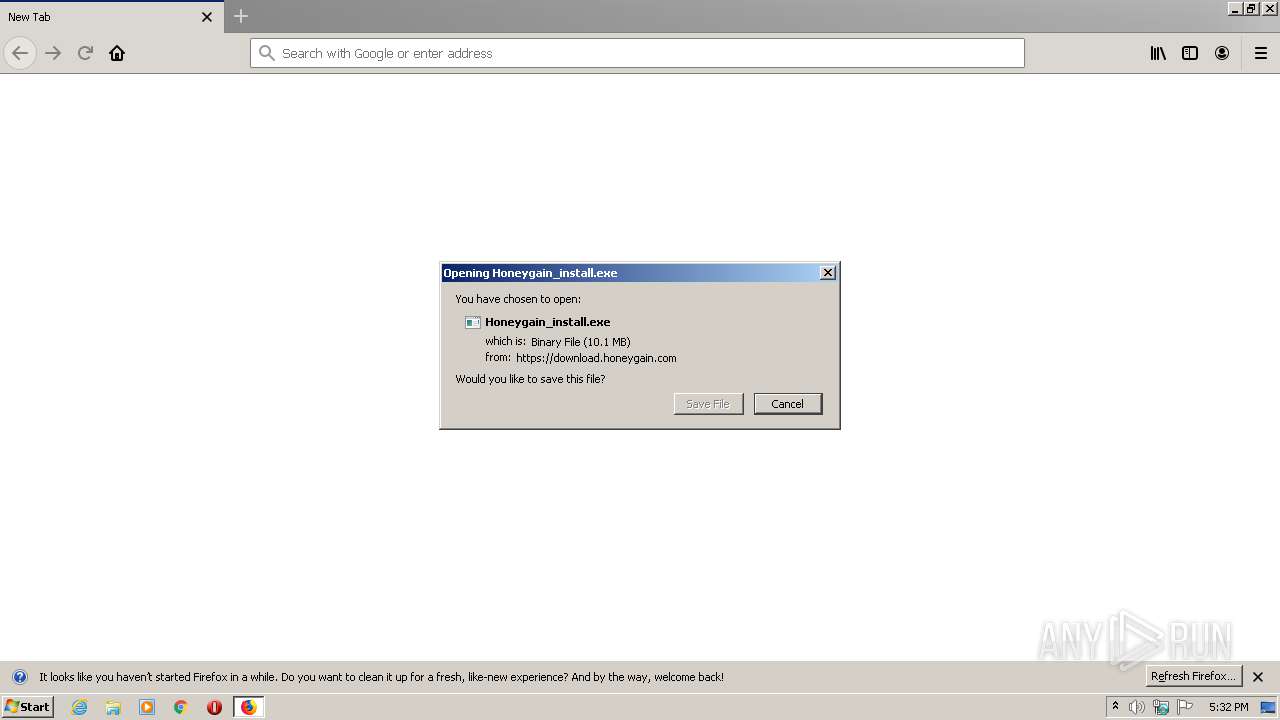
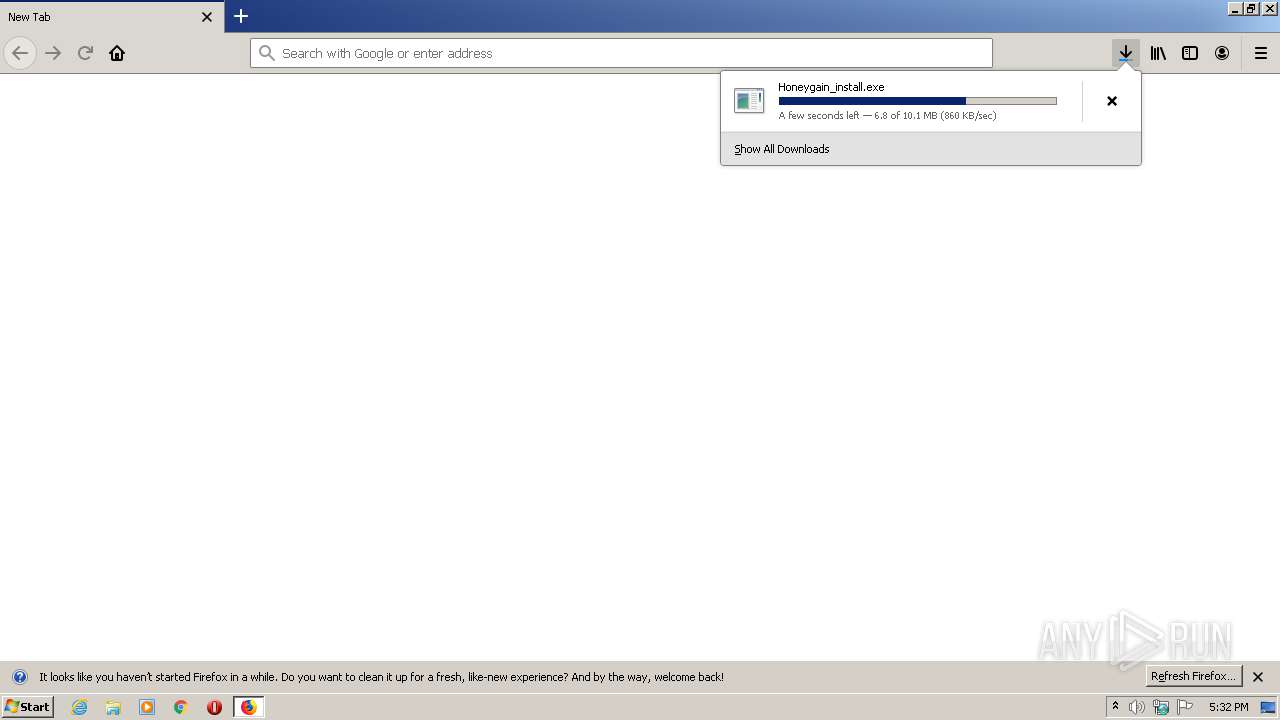
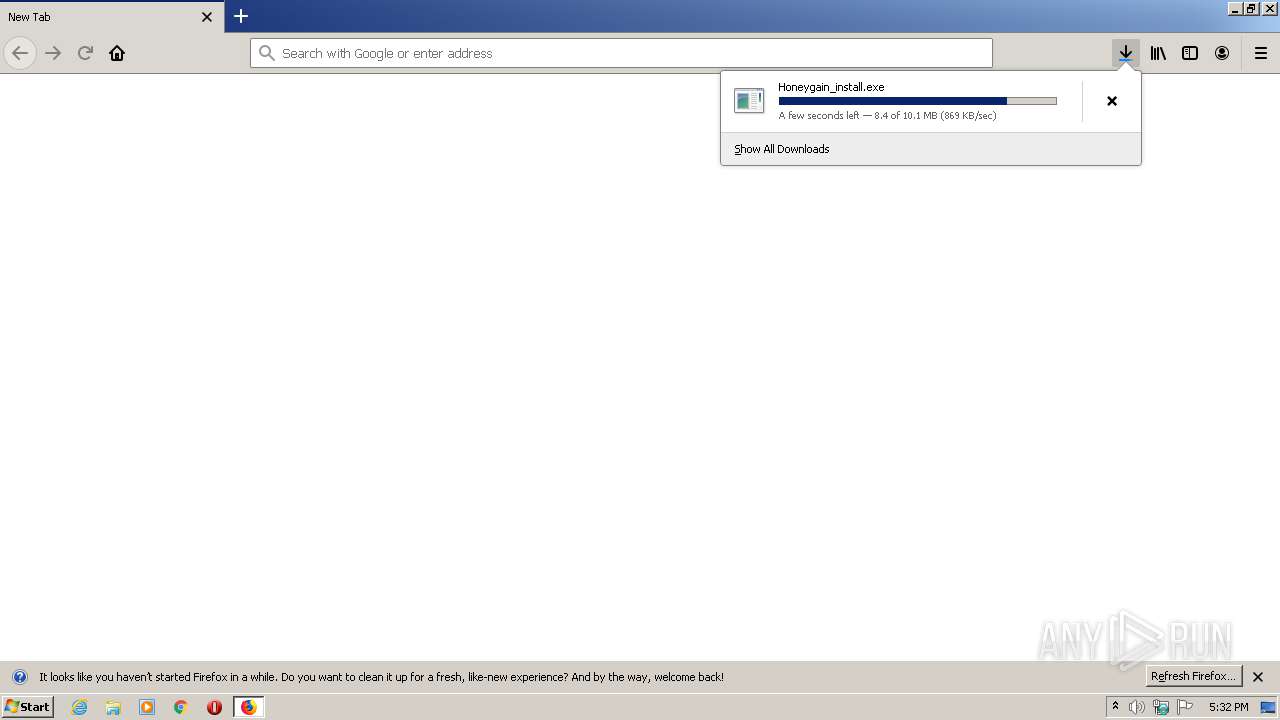
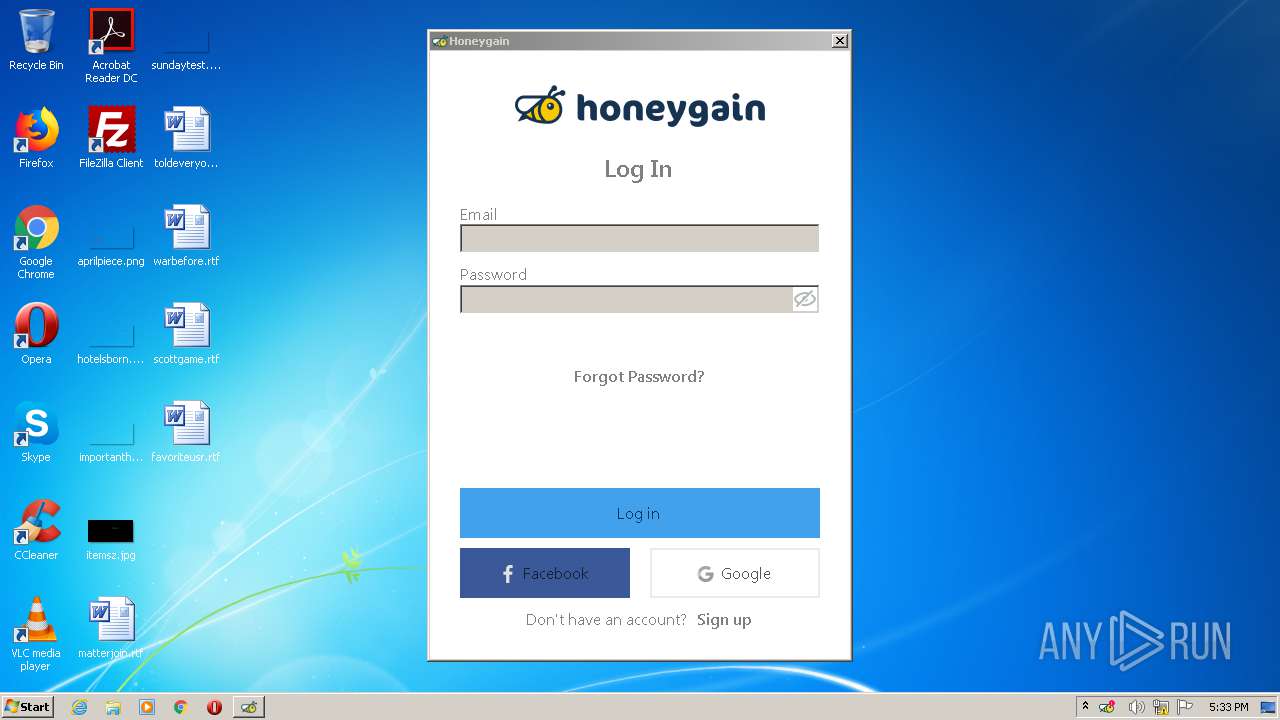
| URL: | https://download.honeygain.com/windows-app/Honeygain_install.exe |
| Full analysis: | https://app.any.run/tasks/73005f67-97ad-4118-a7e3-86816642aa93 |
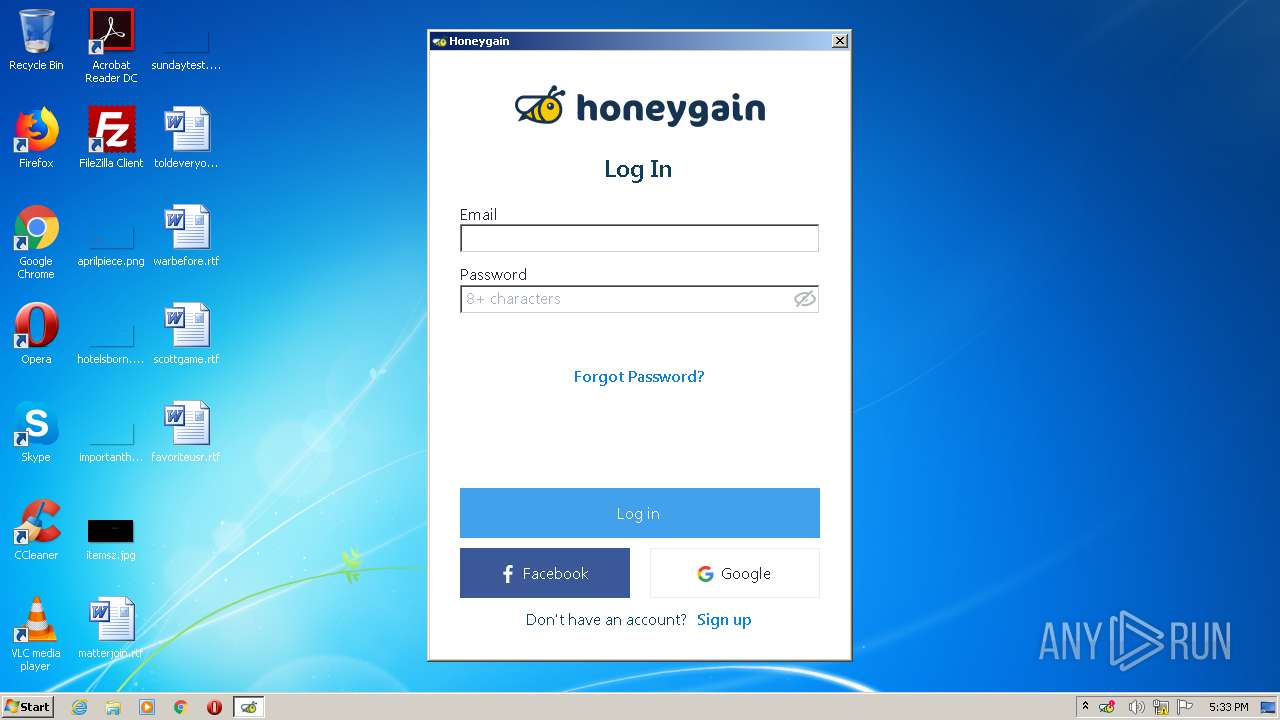
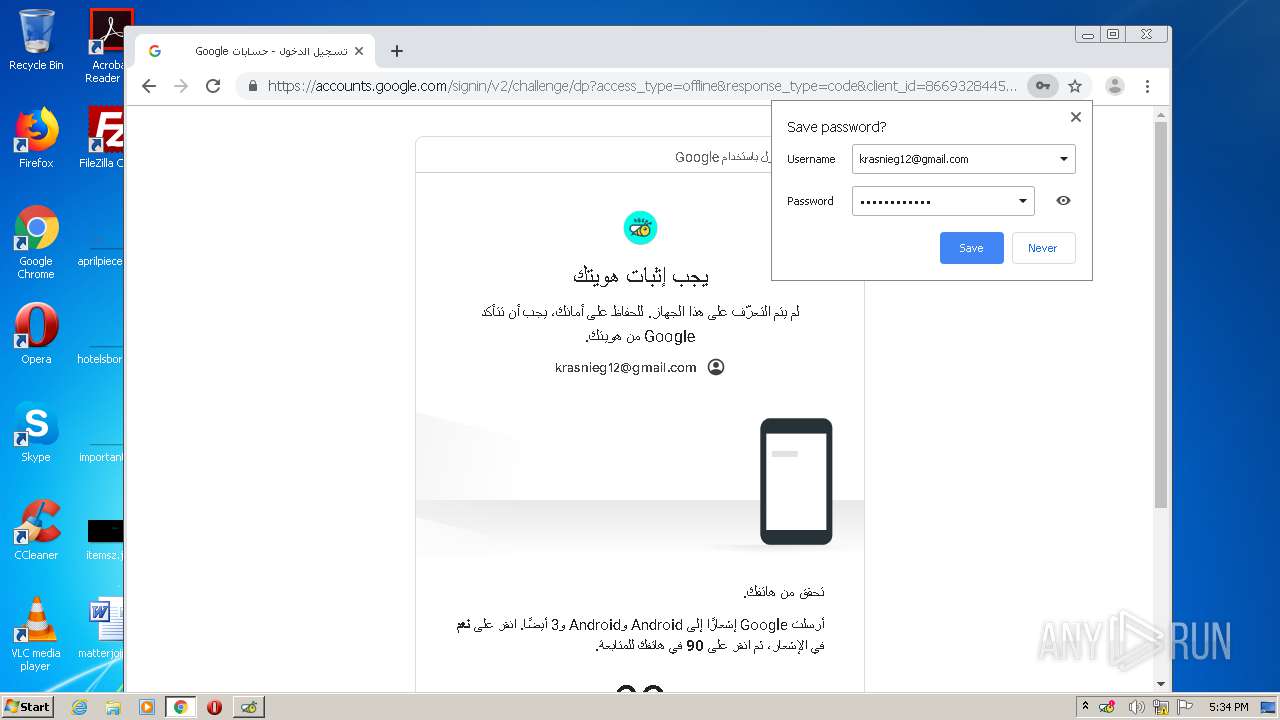
| Verdict: | Malicious activity |
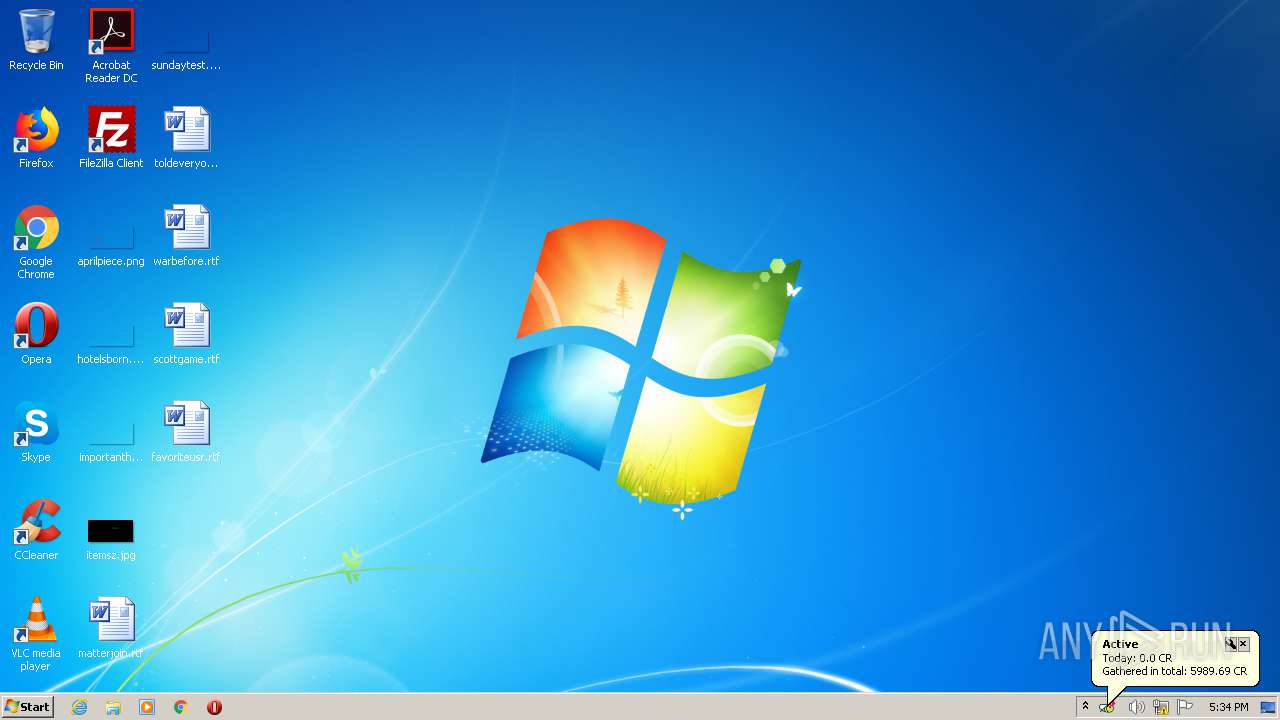
| Analysis date: | March 06, 2021, 17:31:41 |
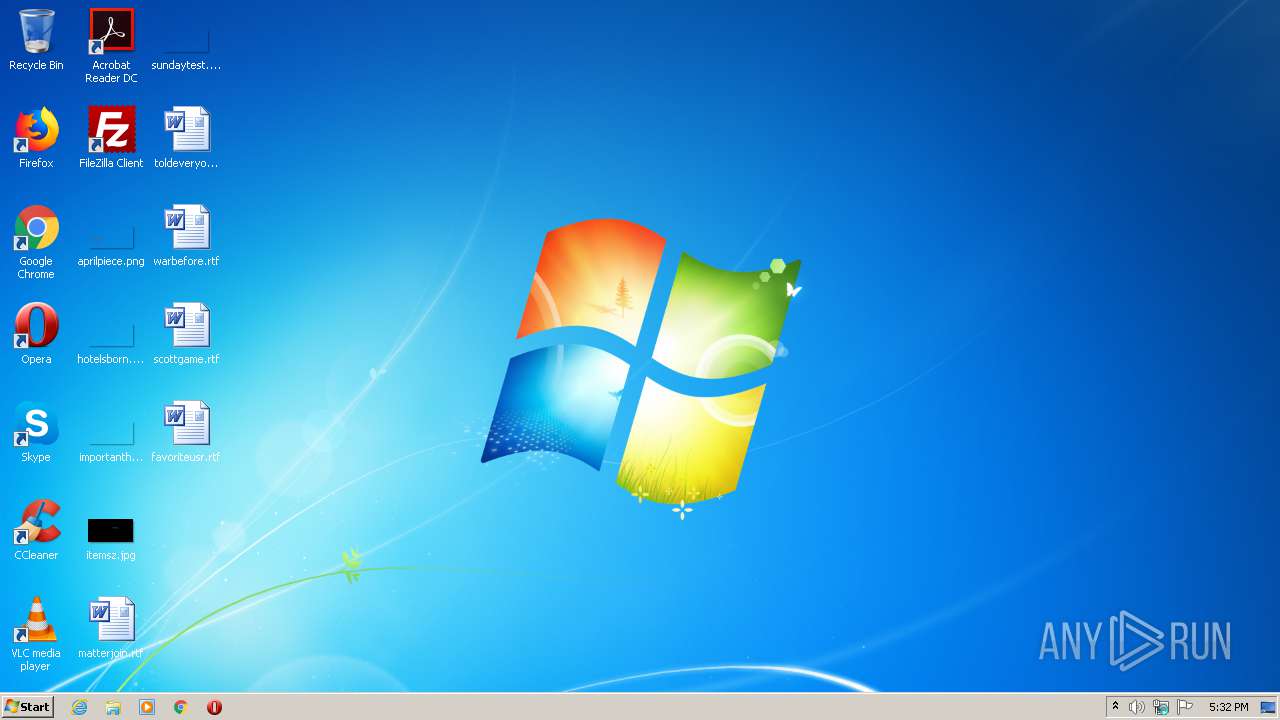
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
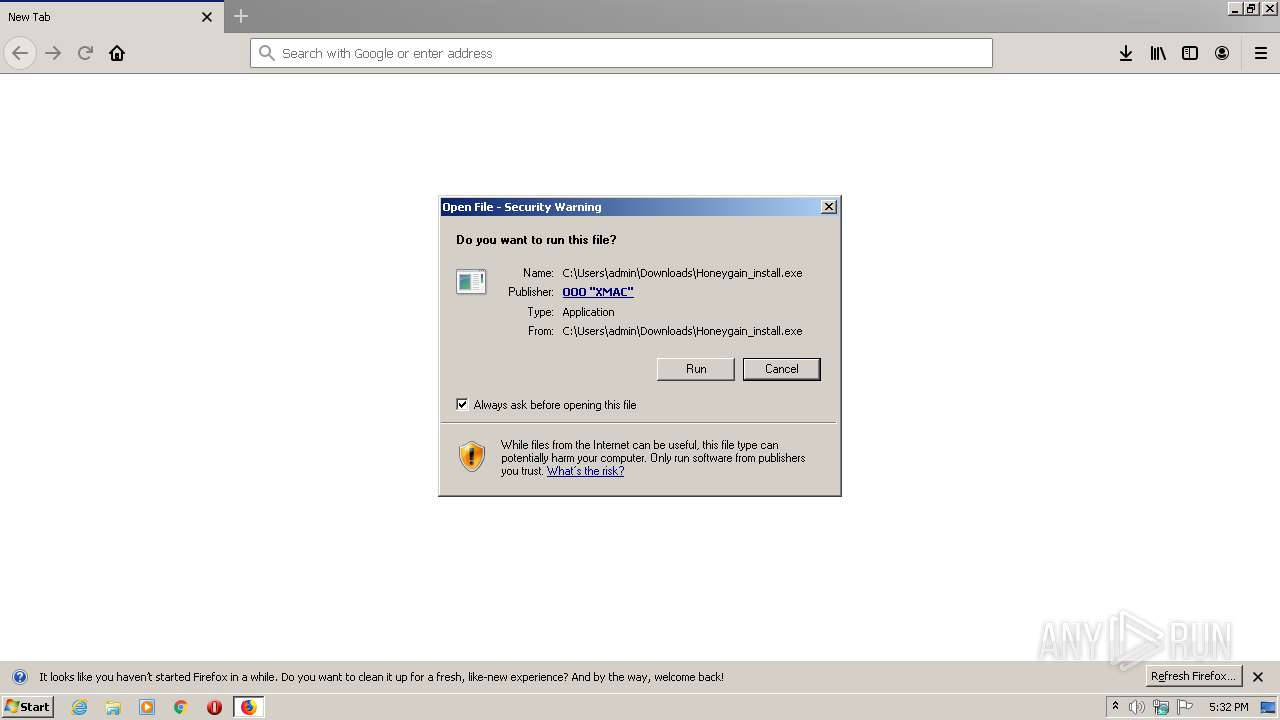
| MD5: | 6ED974C409AF6CA73BD58837DB68B5FD |
| SHA1: | 529B2BE5DC24D14BBB613F1D7D11122AB33A8376 |
| SHA256: | E290459B4F7D7D477B6E47C5A3399E5A284DA1329EC6AEB7F91561C4DEE66B42 |
| SSDEEP: | 3:N8SEloFMM2QAzcKWEJFN:2SKoFQIkn |
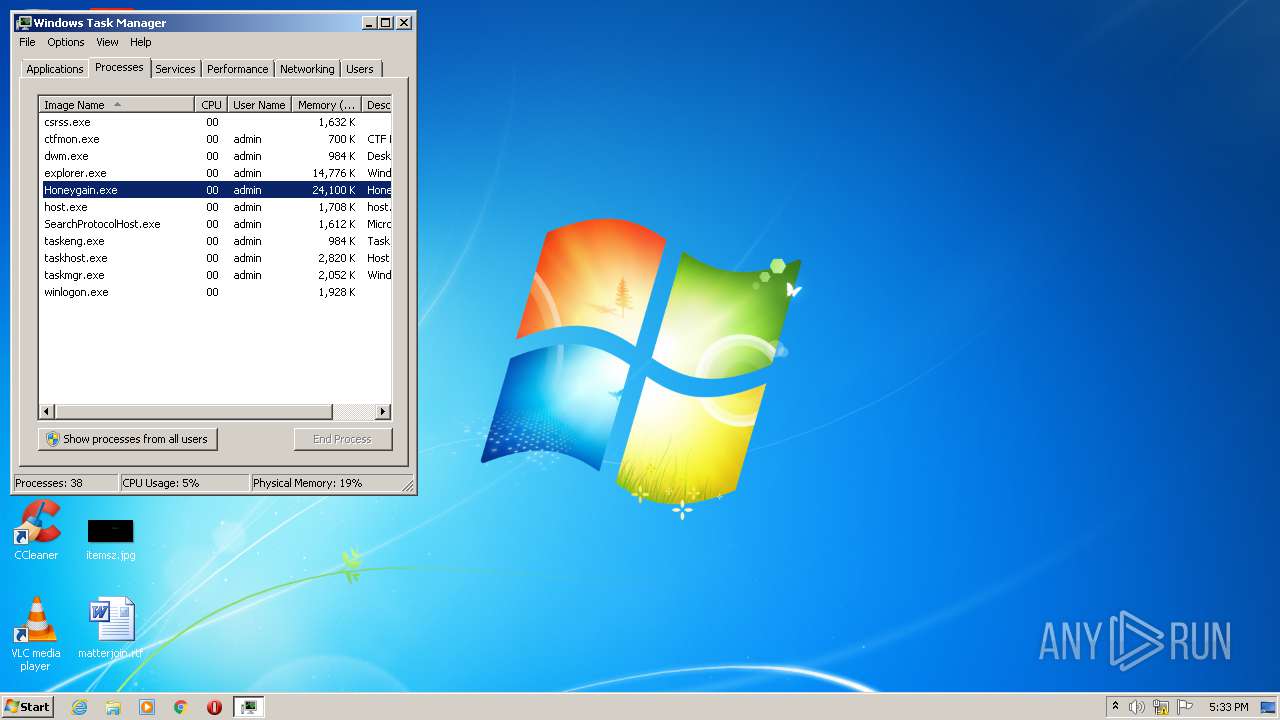
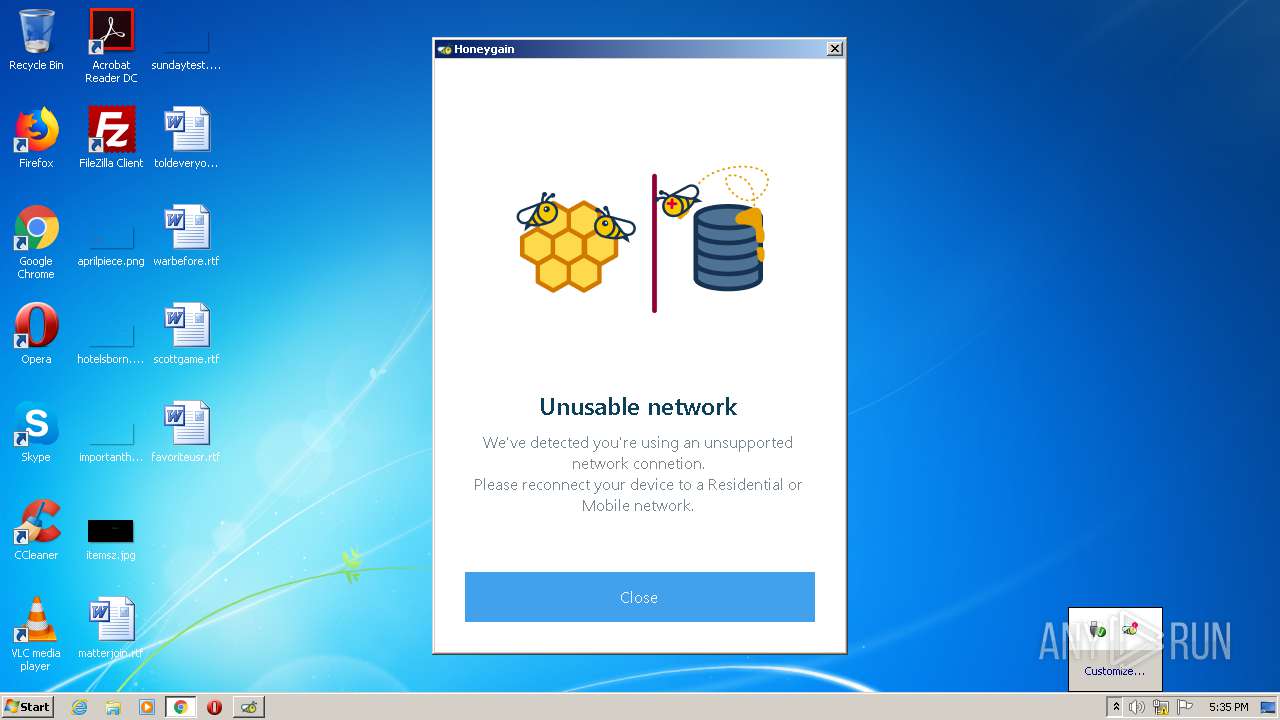
MALICIOUS
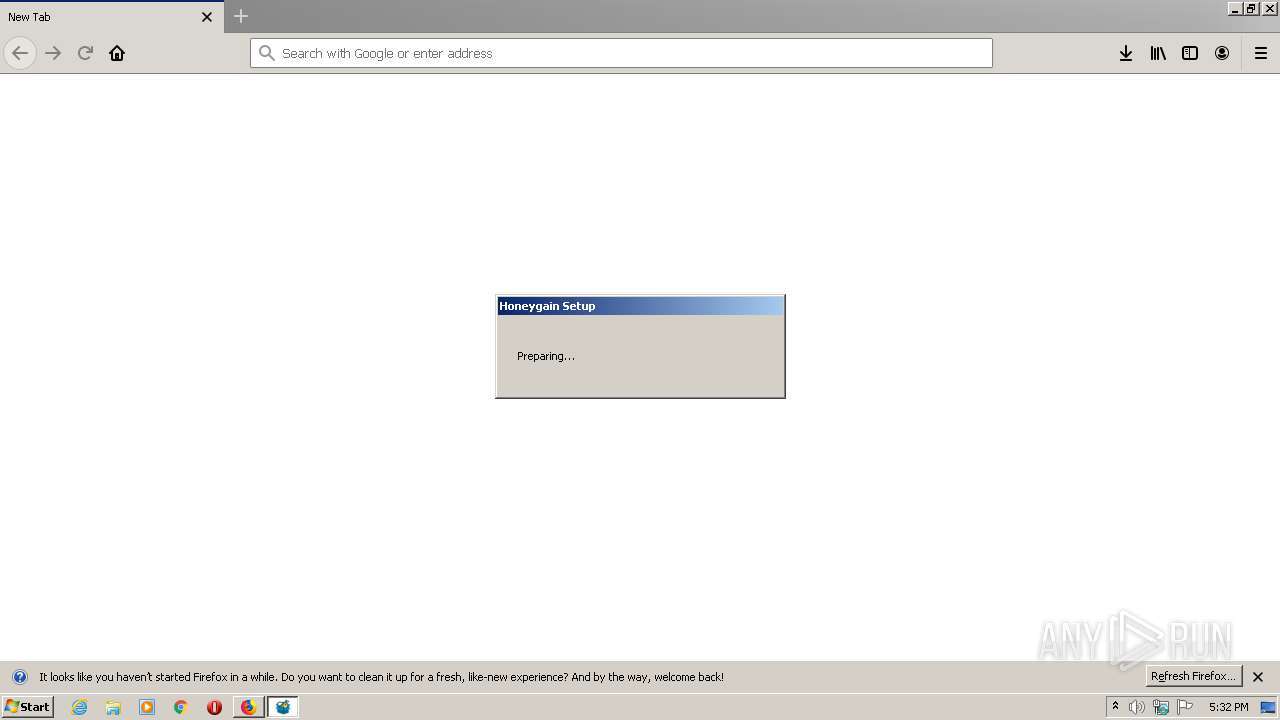
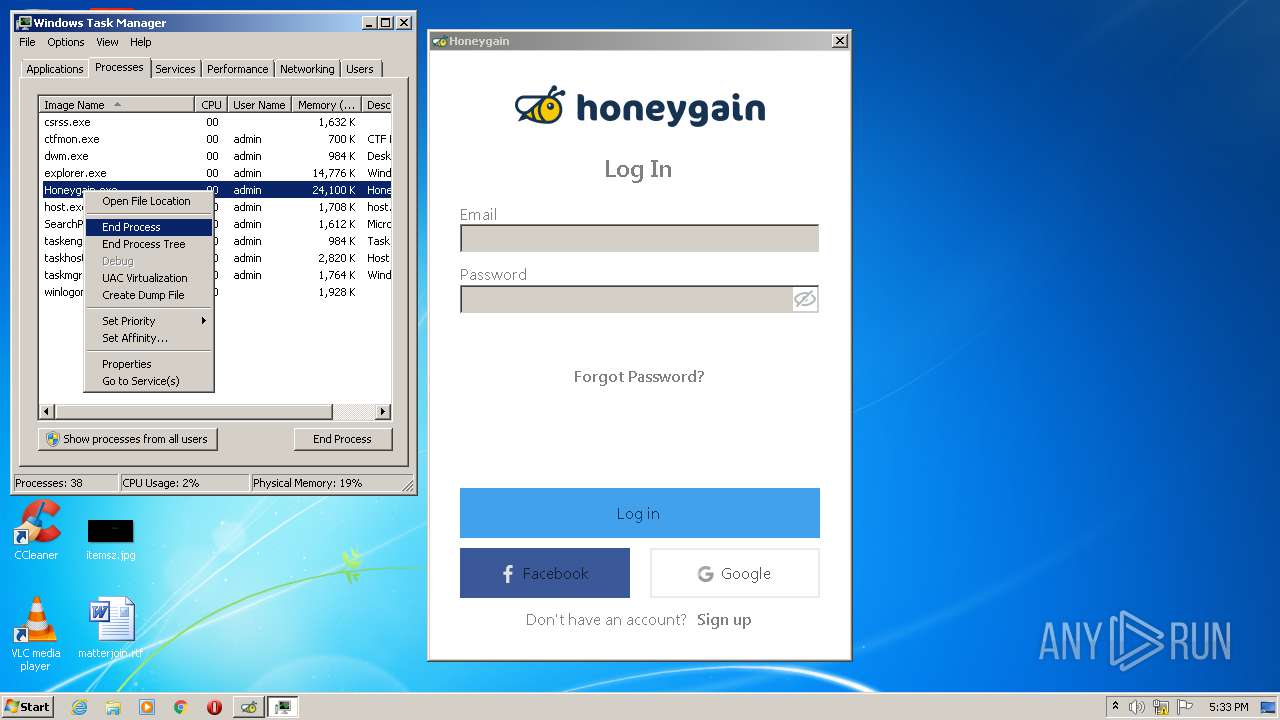
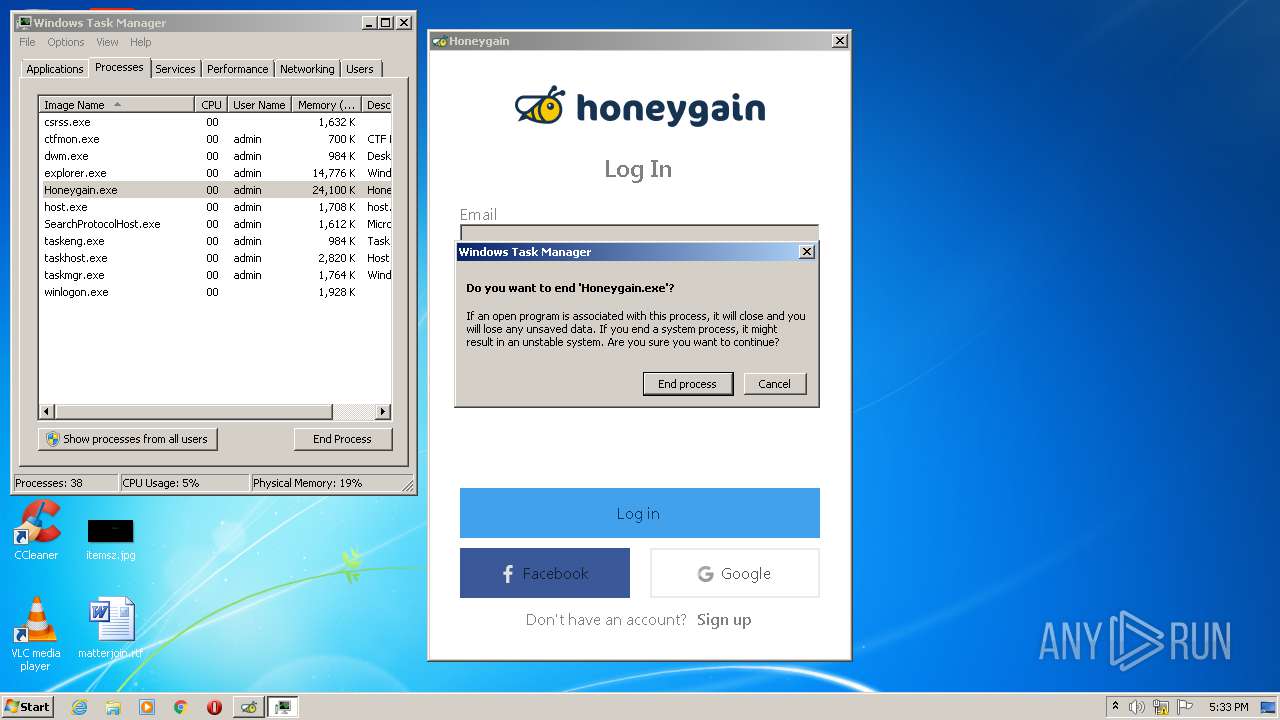
Application was dropped or rewritten from another process
- Honeygain_install.exe (PID: 3720)
- Honeygain_install.exe (PID: 3608)
- Honeygain.exe (PID: 2996)
- Honeygain.exe (PID: 1704)
Loads dropped or rewritten executable
- Honeygain_install.exe (PID: 3720)
- Honeygain.exe (PID: 2996)
- Honeygain.exe (PID: 1704)
Loads the Task Scheduler DLL interface
- Honeygain_install.exe (PID: 3720)
SUSPICIOUS
Executable content was dropped or overwritten
- firefox.exe (PID: 1708)
- Honeygain_install.exe (PID: 3720)
Drops a file that was compiled in debug mode
- Honeygain_install.exe (PID: 3720)
- firefox.exe (PID: 1708)
Reads Environment values
- MsiExec.exe (PID: 2916)
- Honeygain_install.exe (PID: 3720)
- Honeygain.exe (PID: 2996)
- MsiExec.exe (PID: 1756)
- Honeygain.exe (PID: 1704)
Creates files in the user directory
- Honeygain_install.exe (PID: 3720)
Application launched itself
- Honeygain_install.exe (PID: 3720)
Creates files in the program directory
- Honeygain.exe (PID: 2996)
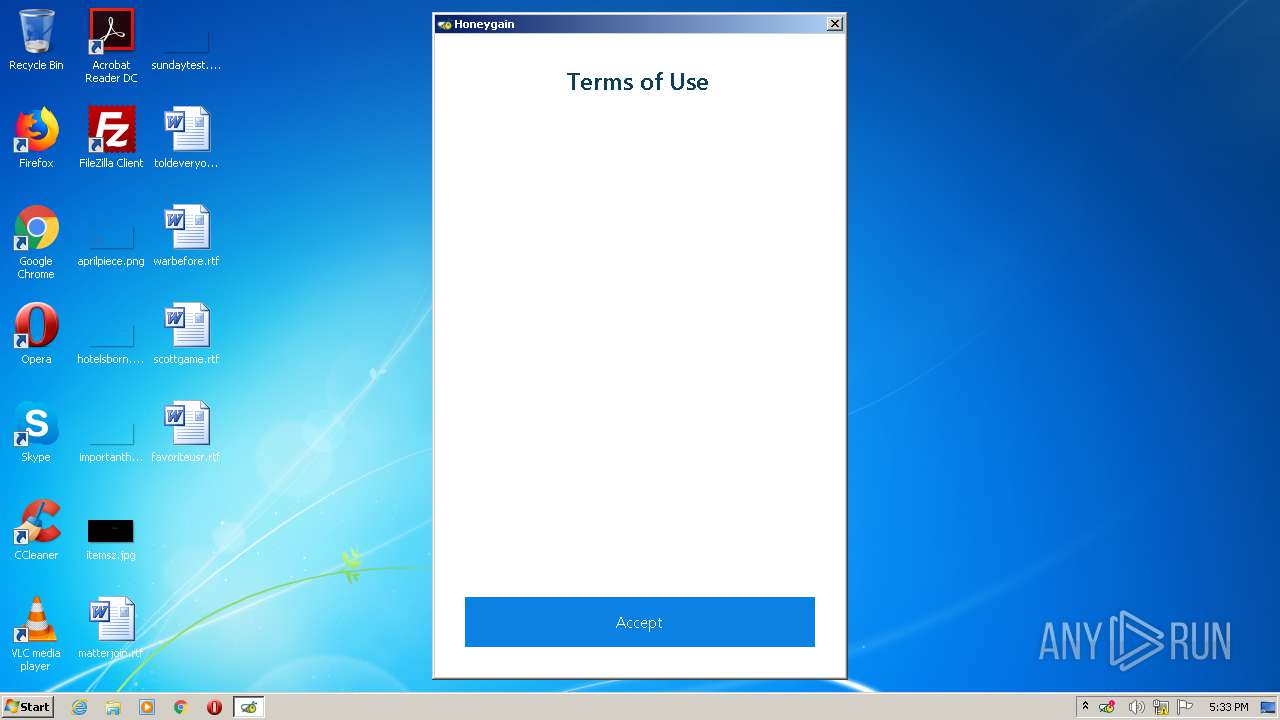
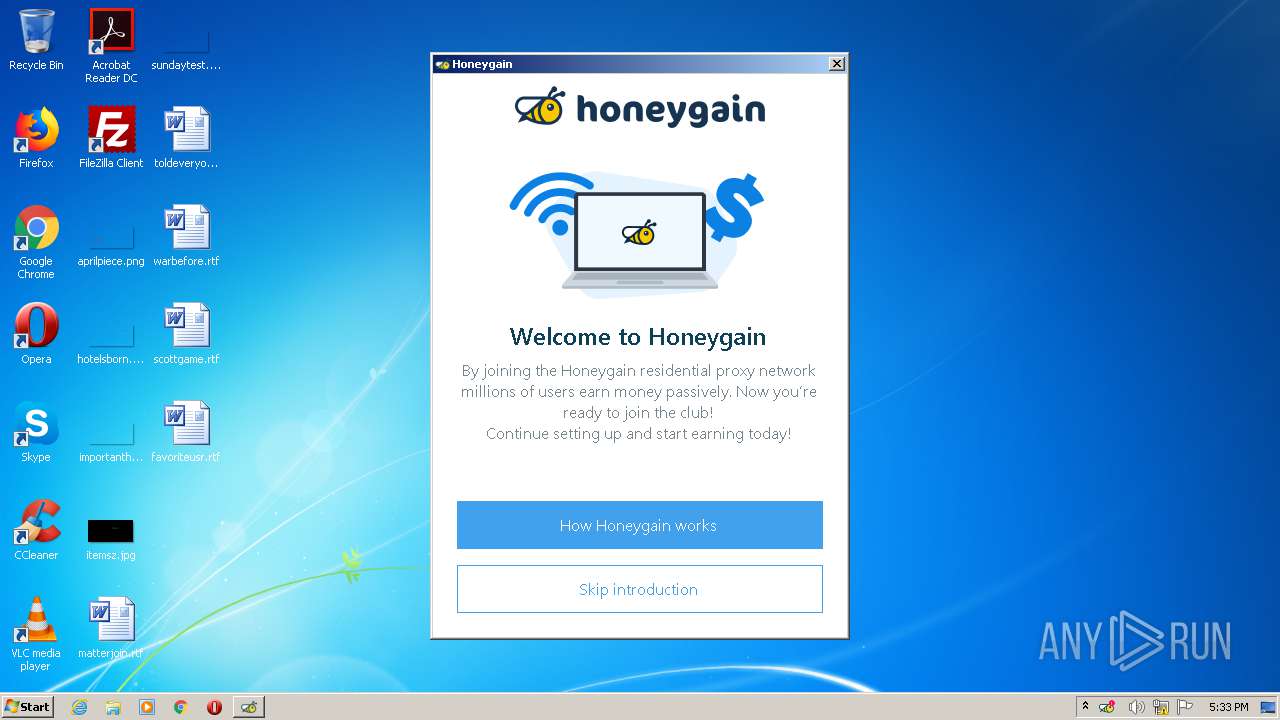
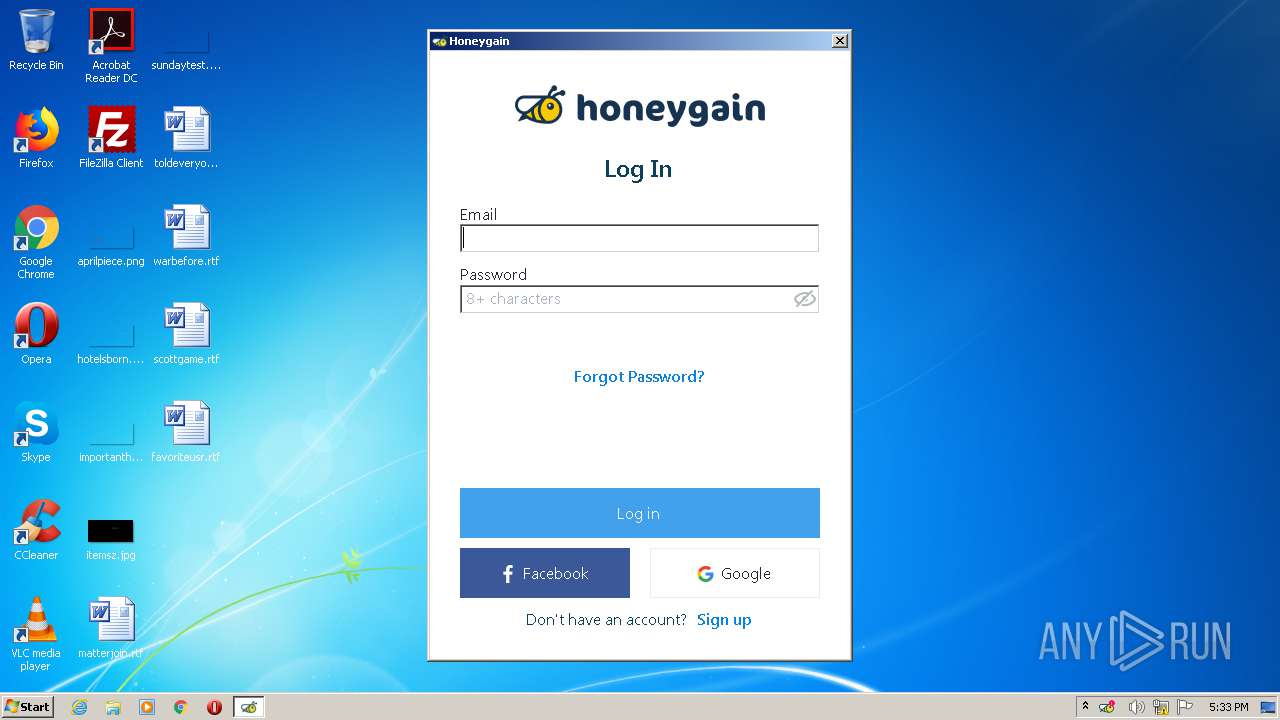
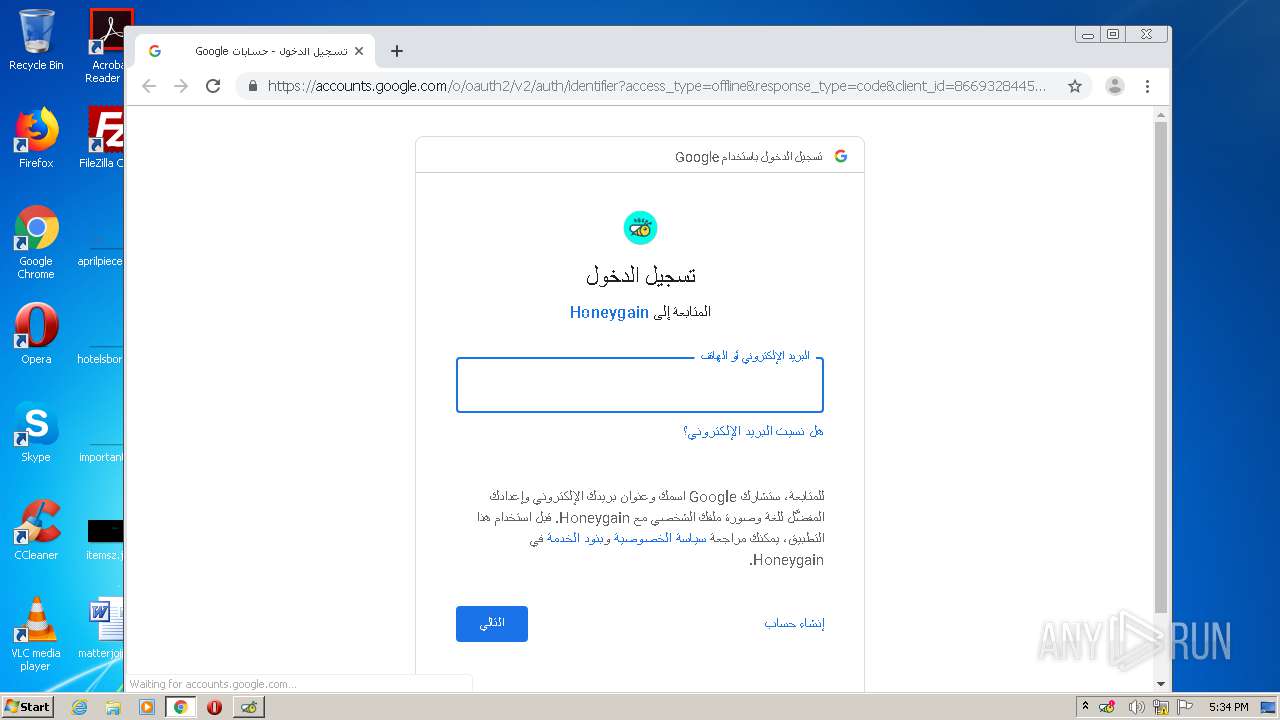
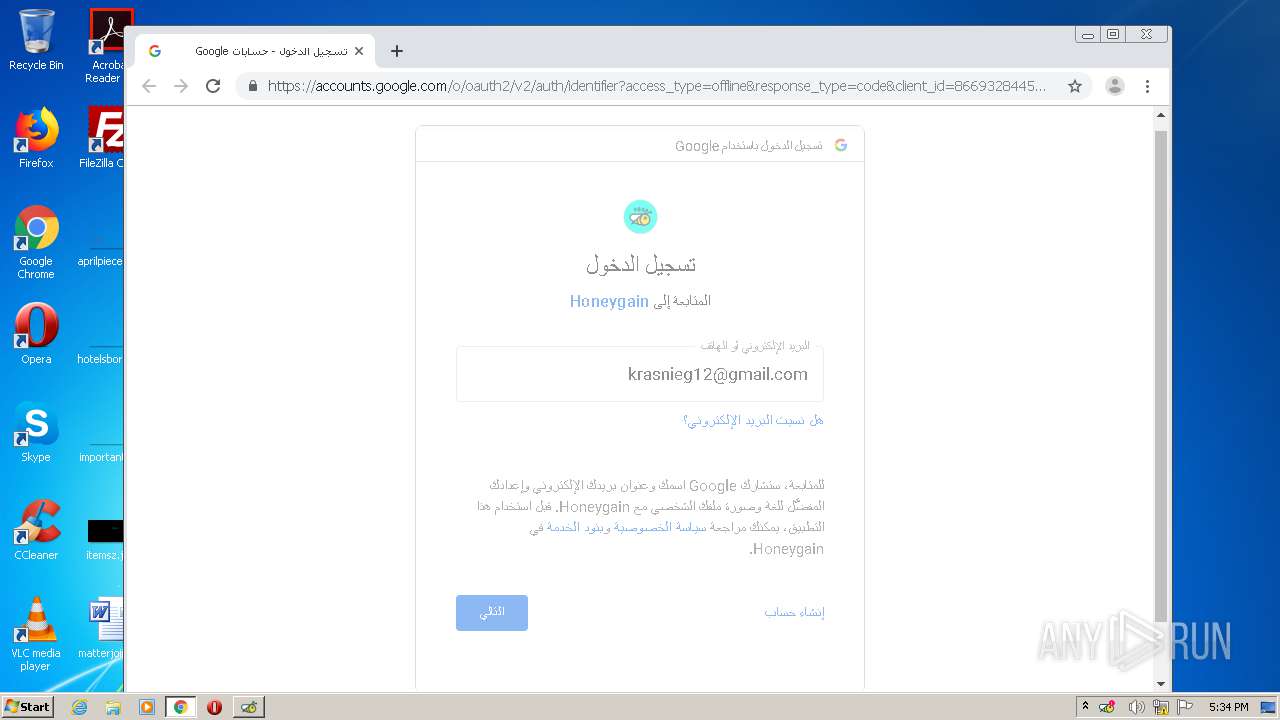
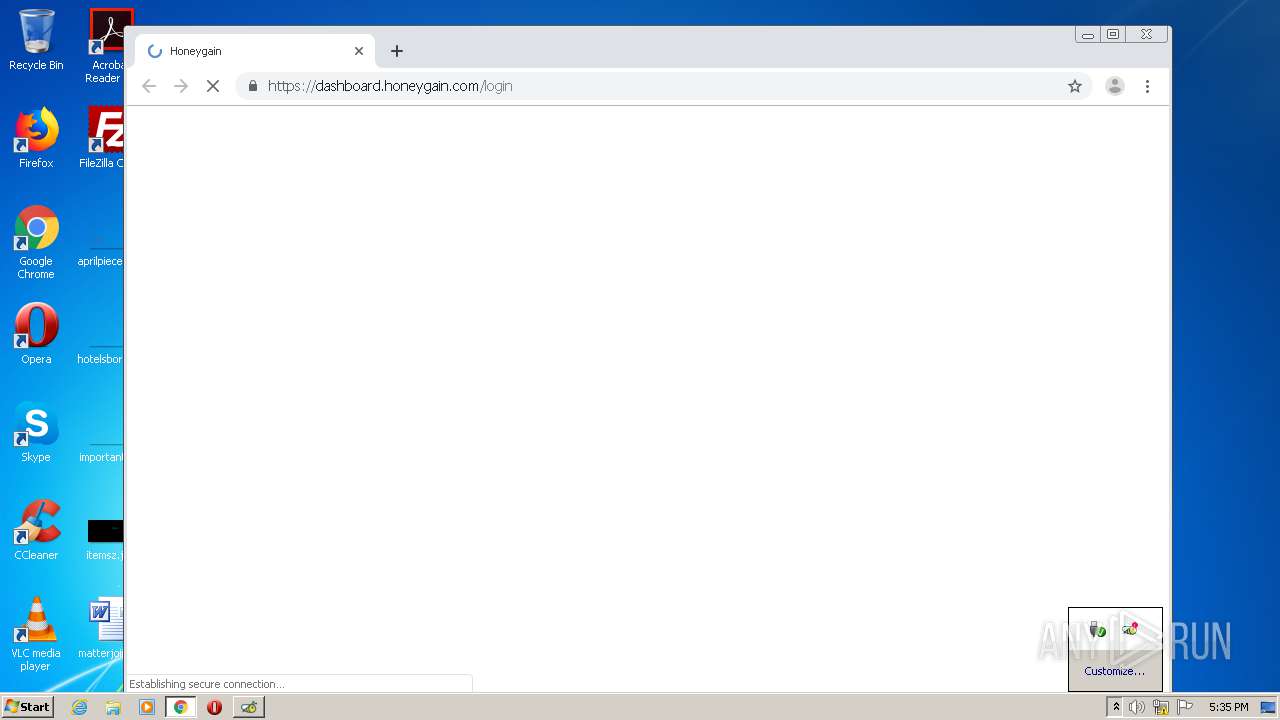
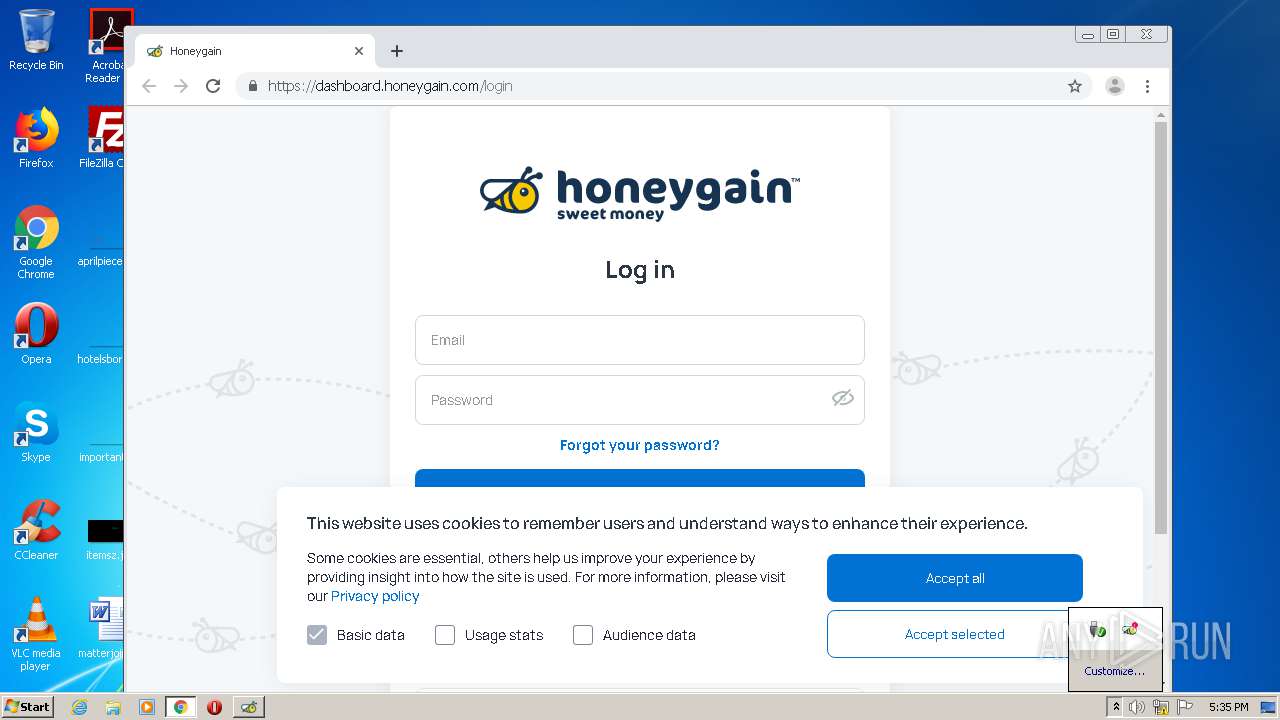
Starts Internet Explorer
- Honeygain.exe (PID: 2996)
Reads internet explorer settings
- Honeygain.exe (PID: 2996)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3812)
INFO
Application launched itself
- firefox.exe (PID: 932)
- firefox.exe (PID: 1708)
- iexplore.exe (PID: 2432)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 272)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2916)
- MsiExec.exe (PID: 1756)
Adds / modifies Windows certificates
- pingsender.exe (PID: 2504)
- pingsender.exe (PID: 2952)
- pingsender.exe (PID: 976)
- iexplore.exe (PID: 2432)
Creates files in the program directory
- firefox.exe (PID: 1708)
Changes settings of System certificates
- pingsender.exe (PID: 976)
- pingsender.exe (PID: 2952)
- pingsender.exe (PID: 2504)
- iexplore.exe (PID: 2432)
Creates files in the user directory
- firefox.exe (PID: 1708)
- iexplore.exe (PID: 2600)
Reads CPU info
- firefox.exe (PID: 1708)
Changes internet zones settings
- iexplore.exe (PID: 2432)
Reads settings of System Certificates
- iexplore.exe (PID: 2600)
- iexplore.exe (PID: 2432)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 1548)
Reads internet explorer settings
- iexplore.exe (PID: 2600)
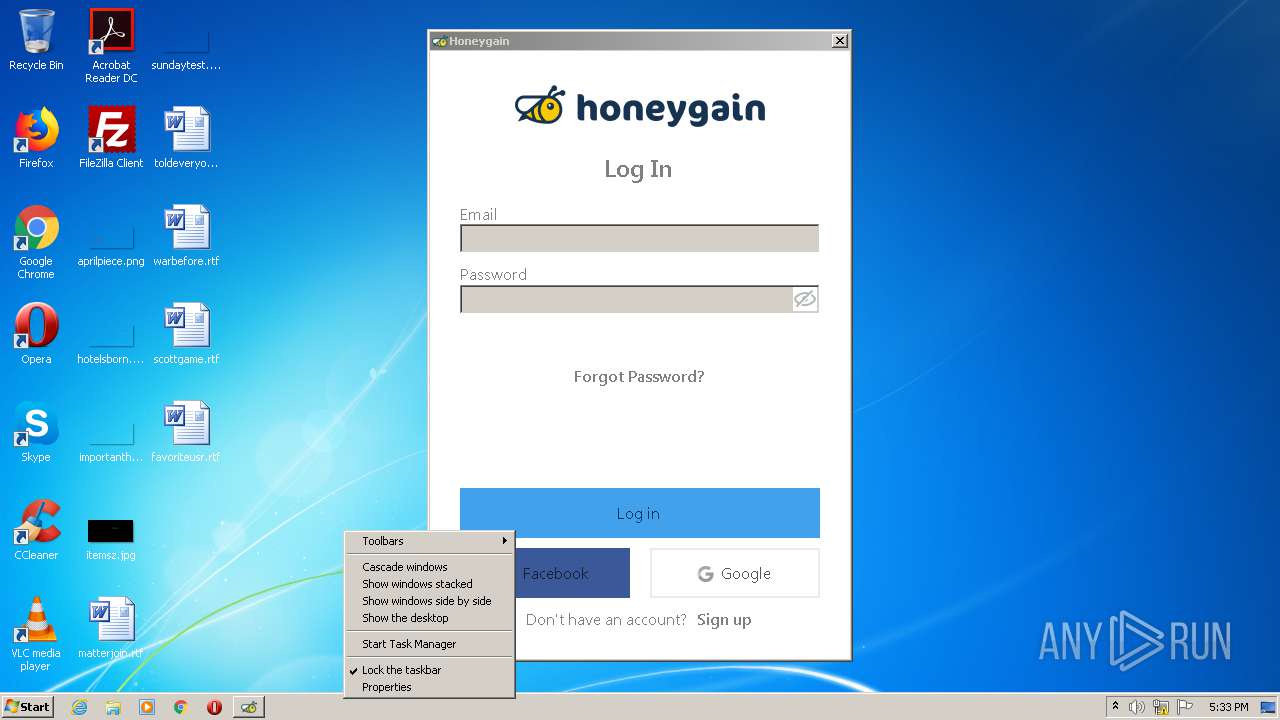
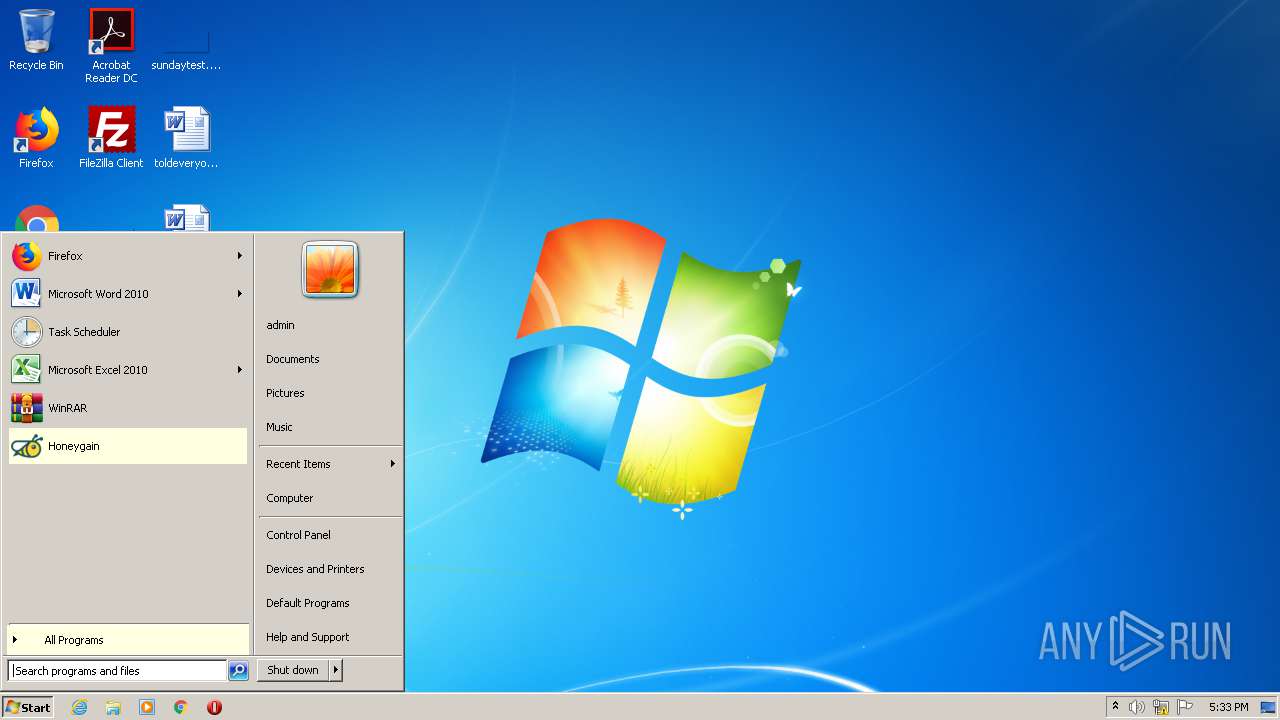
Manual execution by user
- chrome.exe (PID: 2080)
- Honeygain.exe (PID: 1704)
- taskmgr.exe (PID: 444)
Reads the hosts file
- chrome.exe (PID: 2080)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 1548)
- chrome.exe (PID: 272)
Changes default file association
- chrome.exe (PID: 2080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
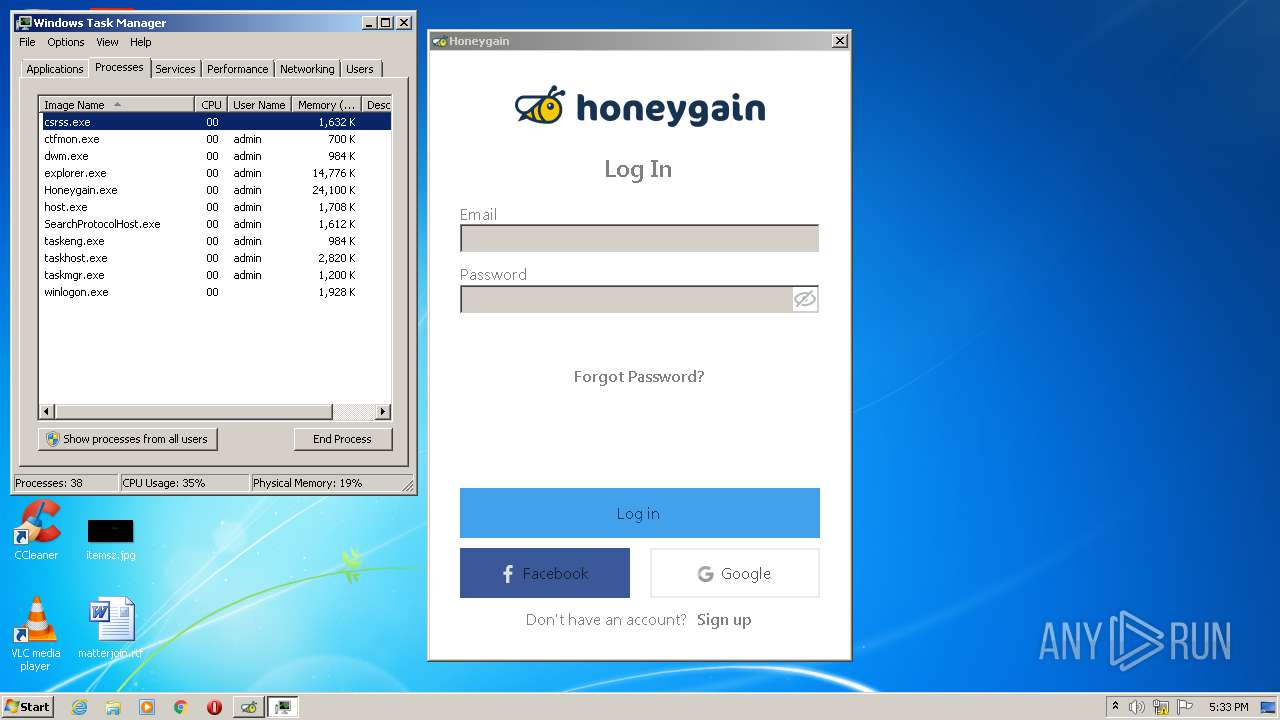
Total processes
118
Monitored processes
77
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
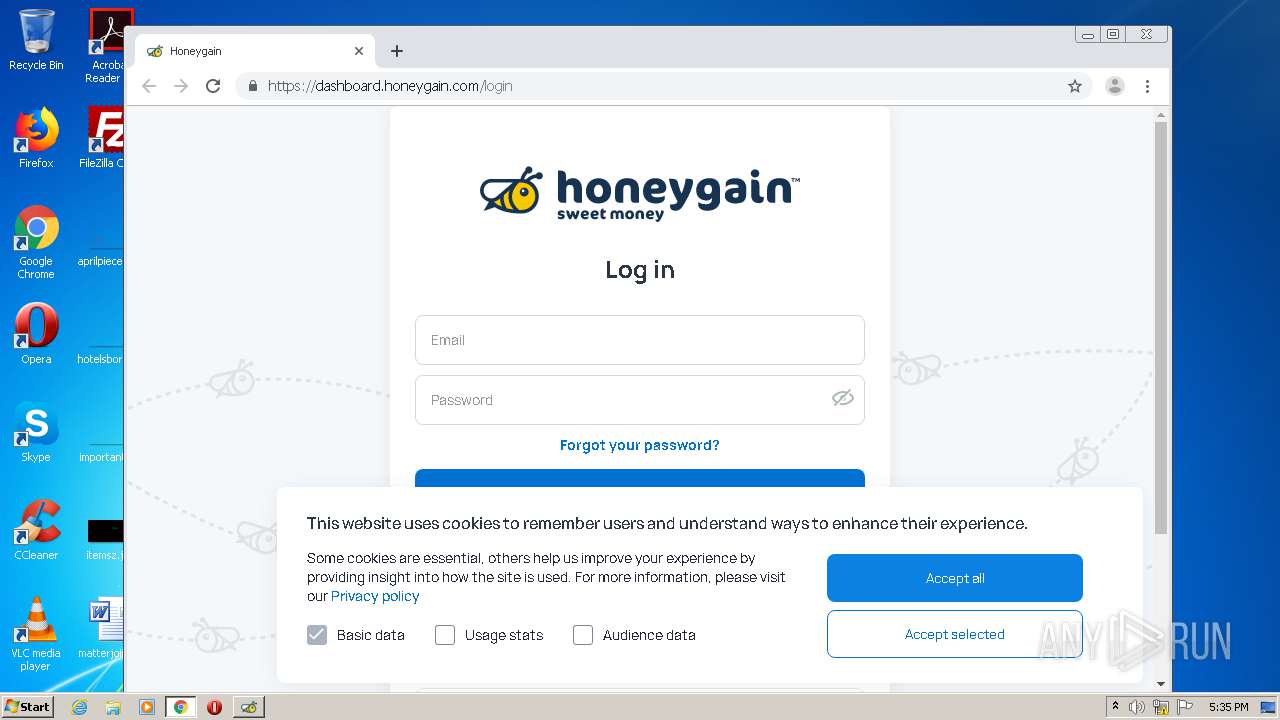
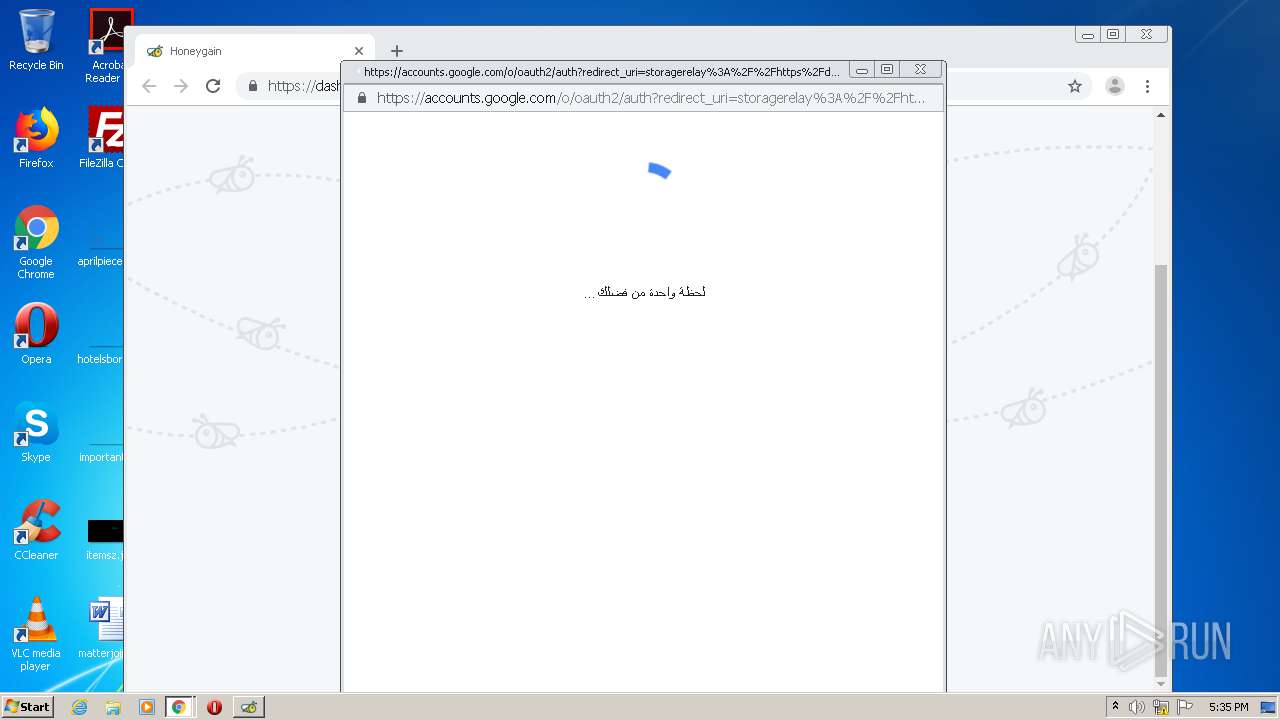
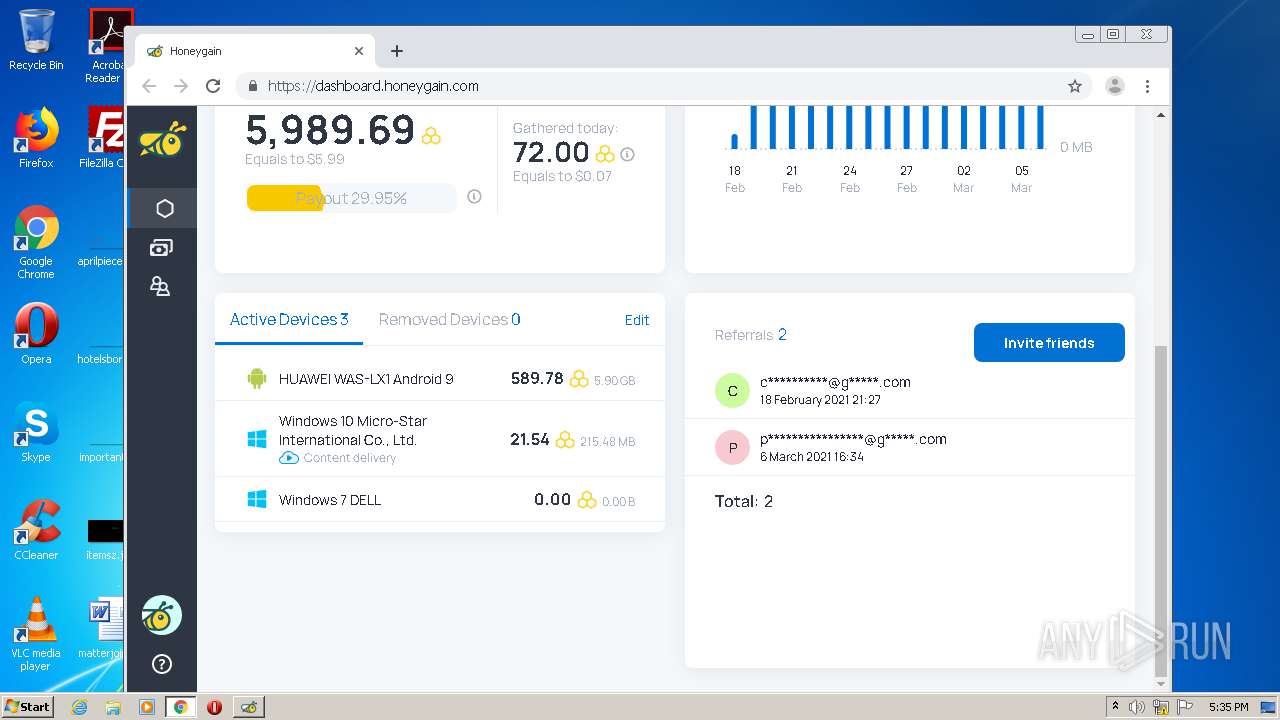
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" -- "https://dashboard.honeygain.com/login" | C:\Program Files\Google\Chrome\Application\chrome.exe | Honeygain.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 444 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,9720649178960938144,7101101446629624477,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14433938758996146020 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9720649178960938144,7101101446629624477,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10379565604225772104 --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,9720649178960938144,7101101446629624477,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=946466745552214328 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://download.honeygain.com/windows-app/Honeygain_install.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9720649178960938144,7101101446629624477,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15878990055800577296 --mojo-platform-channel-handle=3732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/dc920d34-cc3d-435b-9e5e-d8b8cc59b097/main/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\dc920d34-cc3d-435b-9e5e-d8b8cc59b097 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1708.13.1063785458\591755274" -childID 2 -isForBrowser -prefsHandle 2660 -prefMapHandle 2920 -prefsLen 5997 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1708 "\\.\pipe\gecko-crash-server-pipe.1708" 2932 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9720649178960938144,7101101446629624477,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15041945439712800728 --mojo-platform-channel-handle=1644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 053
Read events
3 599
Write events
431
Delete events
23
Modification events
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 6266640600000000 | |||
| (PID) Process: | (932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 6166640600000000 | |||
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (1708) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
Executable files
13
Suspicious files
257
Text files
463
Unknown types
118
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1708 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1708 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\46ADCCEF91A14AD1BAB6DF288FEFC77009EE0815 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
137
DNS requests
76
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3720 | Honeygain_install.exe | GET | 200 | 13.32.23.204:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
— | — | POST | — | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | — | — | whitelisted |
3720 | Honeygain_install.exe | GET | 200 | 13.32.23.215:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1708 | firefox.exe | POST | — | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | — | — | whitelisted |
3720 | Honeygain_install.exe | GET | 200 | 13.32.23.69:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
— | — | POST | — | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core | US | — | — | whitelisted |
1708 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 279 b | whitelisted |
2600 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCED6e95d8DfIfBQAAAACHecw%3D | US | der | 471 b | whitelisted |
2600 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCED6e95d8DfIfBQAAAACHecw%3D | US | der | 471 b | whitelisted |
2600 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEERNBC36FPTKBQAAAACHefI%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1708 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
1708 | firefox.exe | 104.26.12.56:443 | download.honeygain.com | Cloudflare Inc | US | shared |
1708 | firefox.exe | 34.215.65.187:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1708 | firefox.exe | 93.184.220.29:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3720 | Honeygain_install.exe | 54.81.164.221:443 | collect.installeranalytics.com | Amazon.com, Inc. | US | malicious |
3720 | Honeygain_install.exe | 13.32.23.69:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3720 | Honeygain_install.exe | 13.32.23.204:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
2996 | Honeygain.exe | 104.26.12.56:443 | download.honeygain.com | Cloudflare Inc | US | shared |
2600 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2600 | iexplore.exe | 142.250.185.225:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
download.honeygain.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
collect.installeranalytics.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1 ETPRO signatures available at the full report