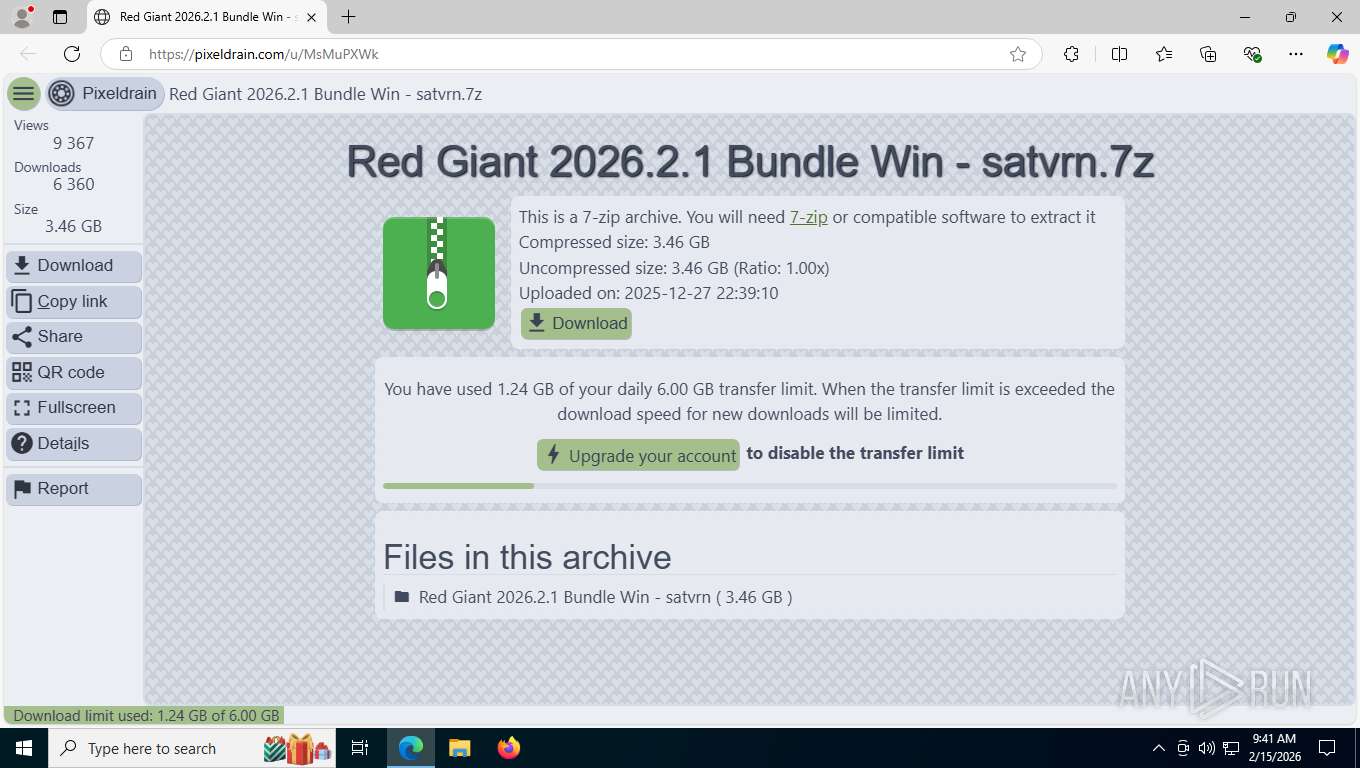
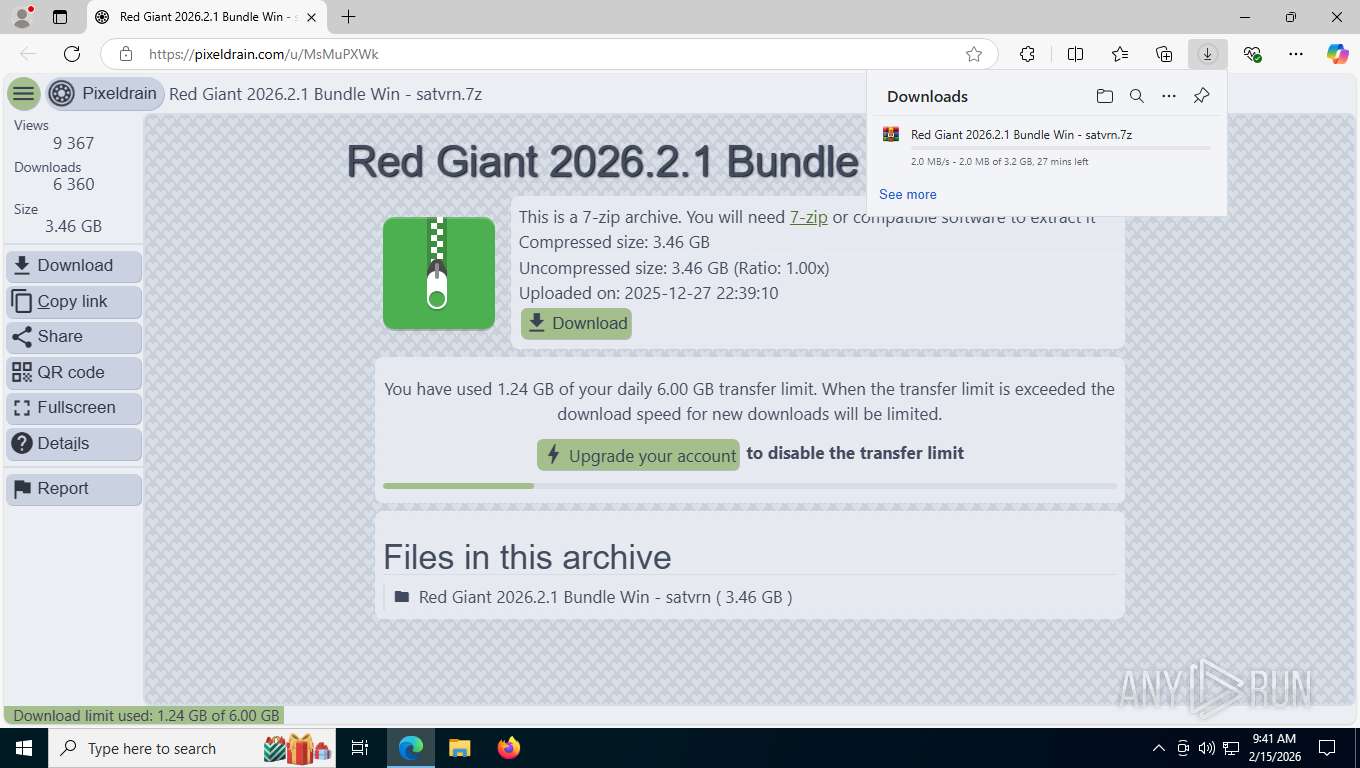
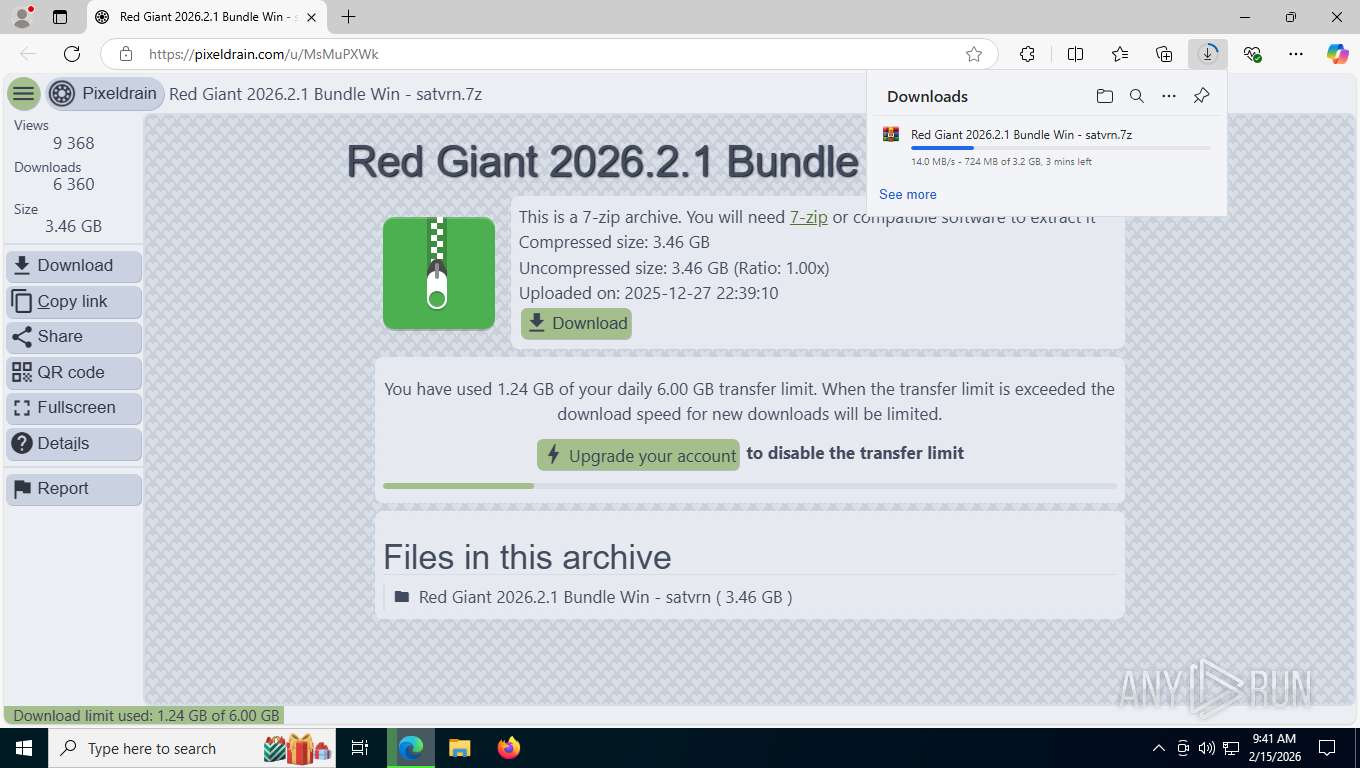
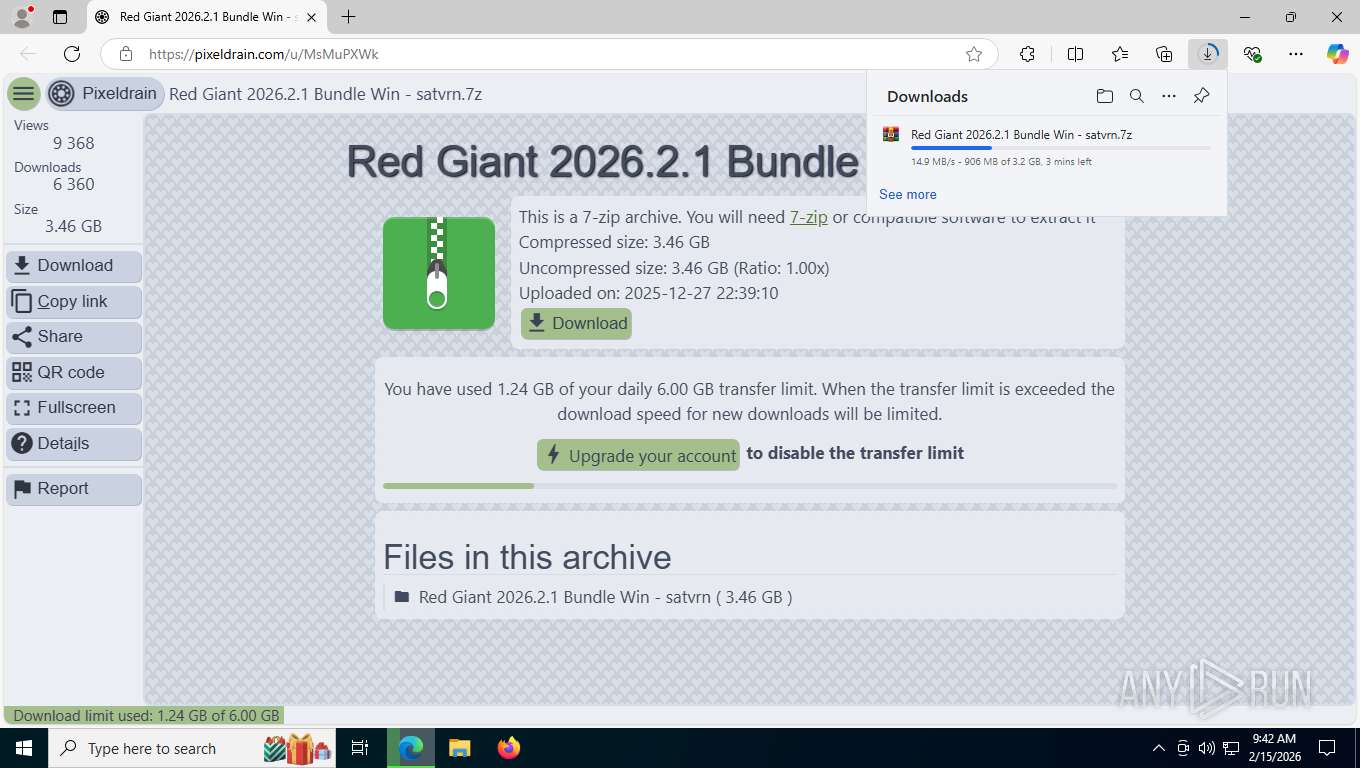
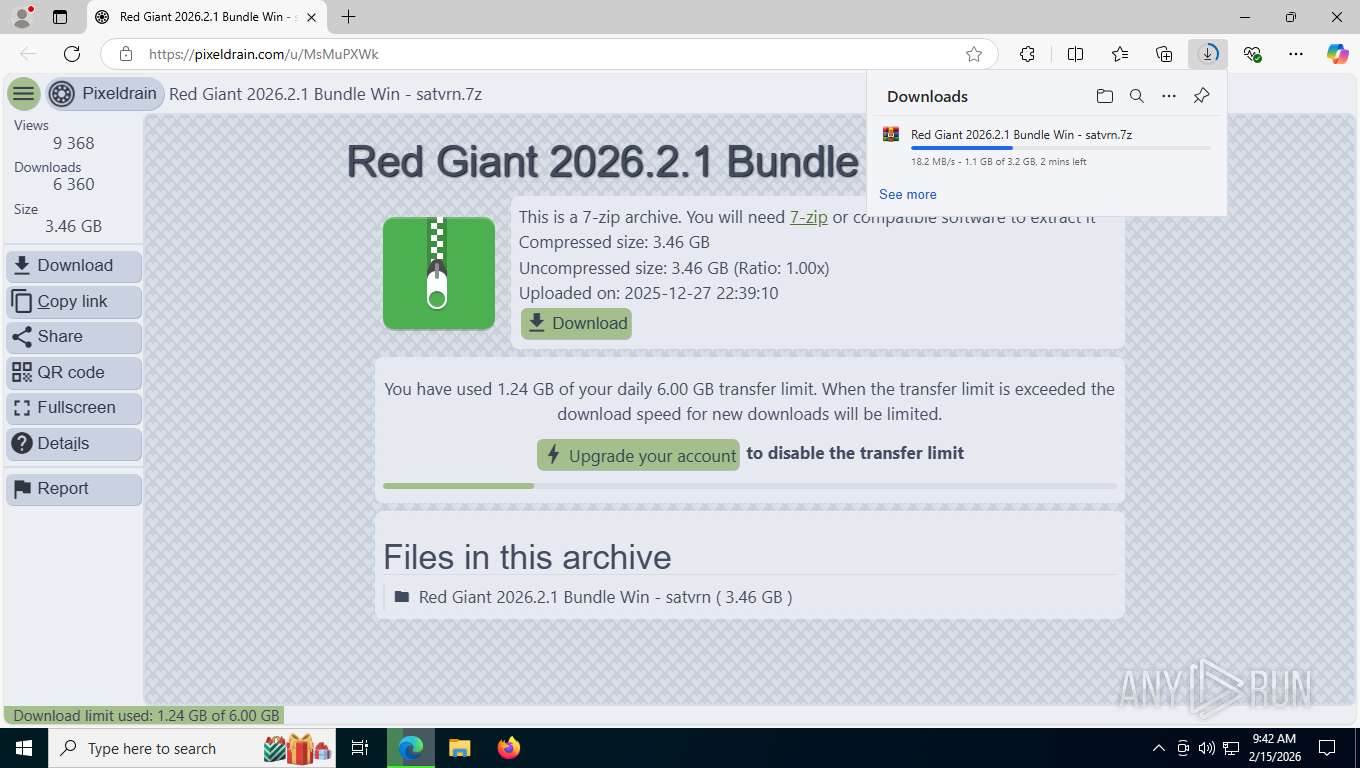
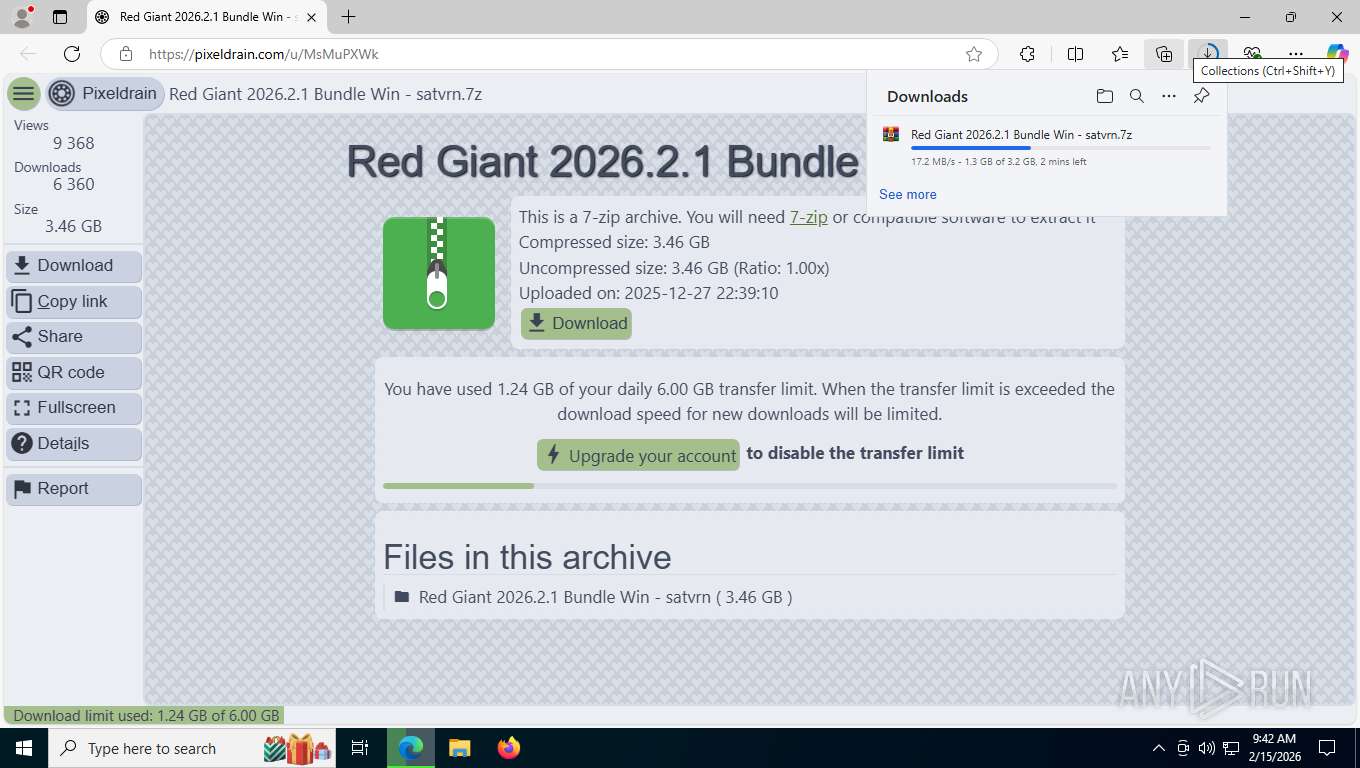
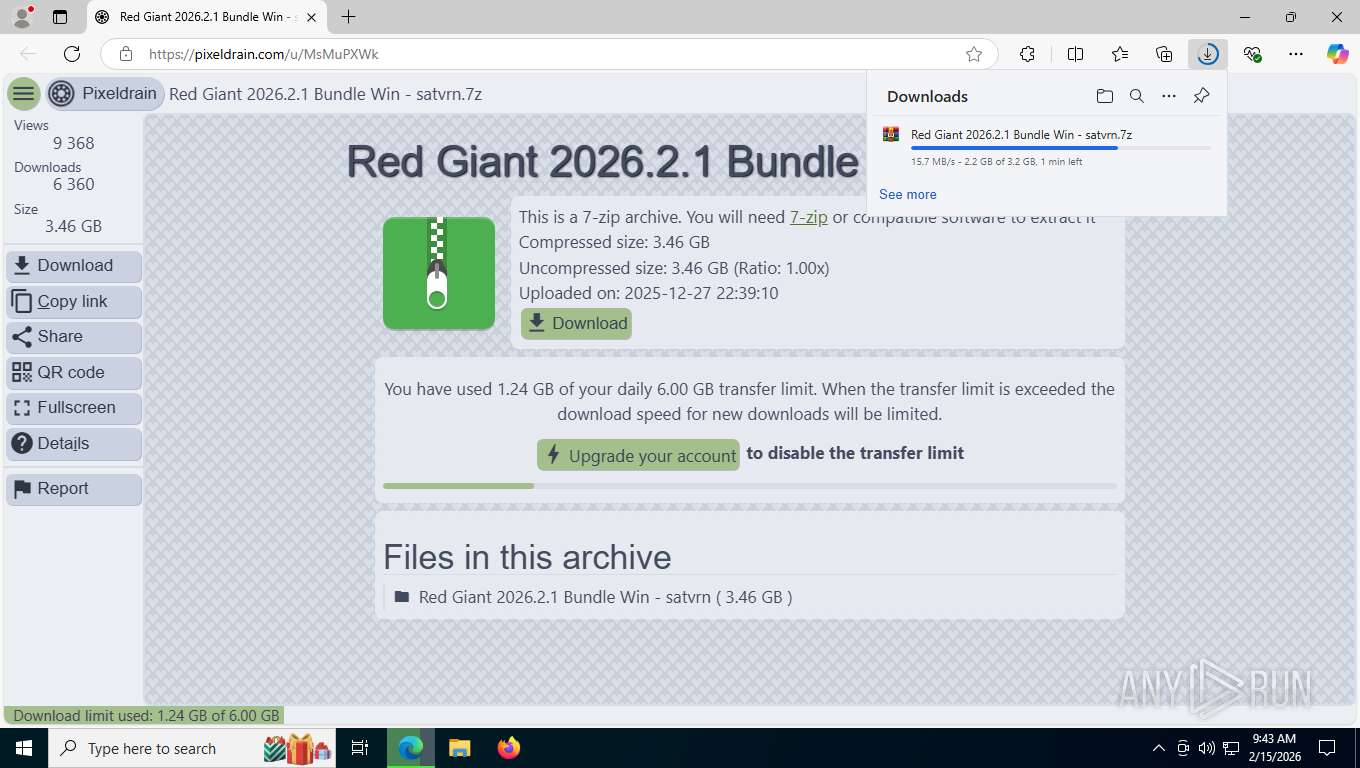
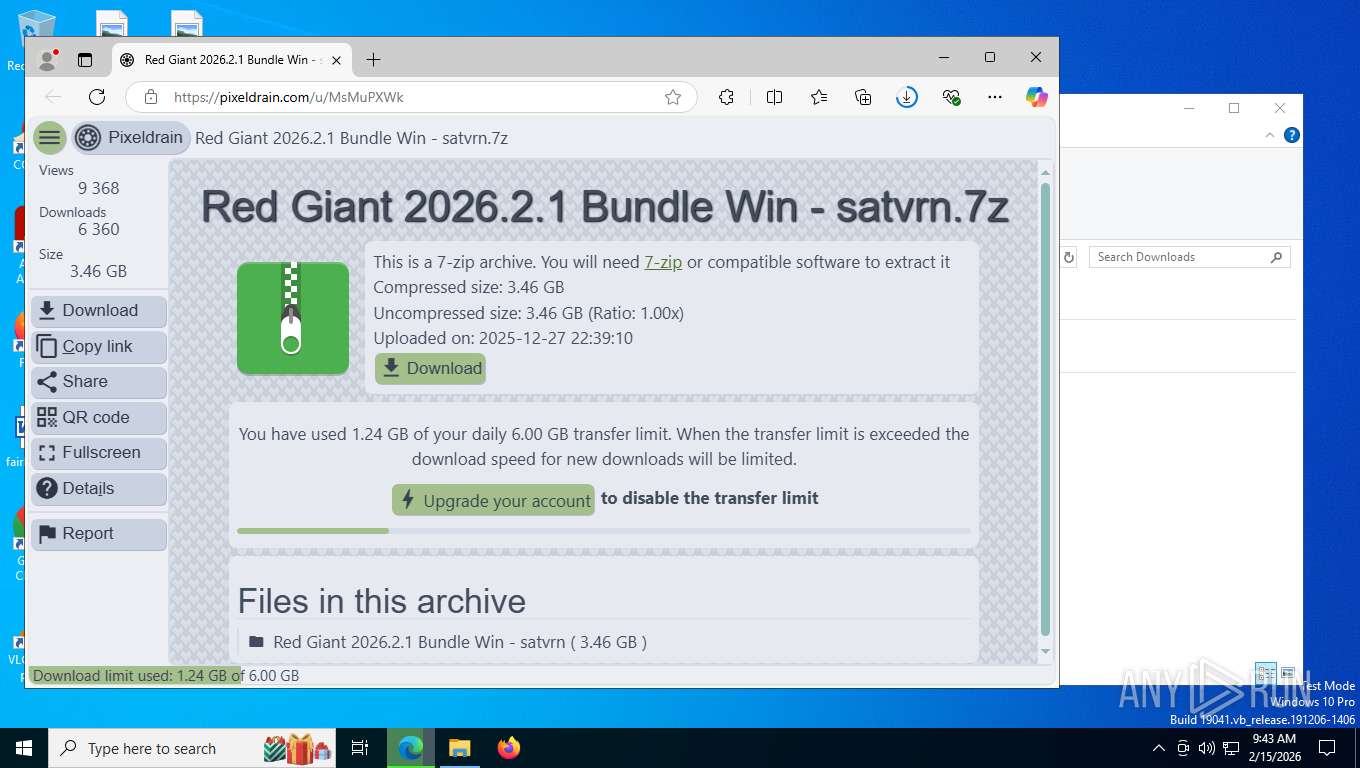
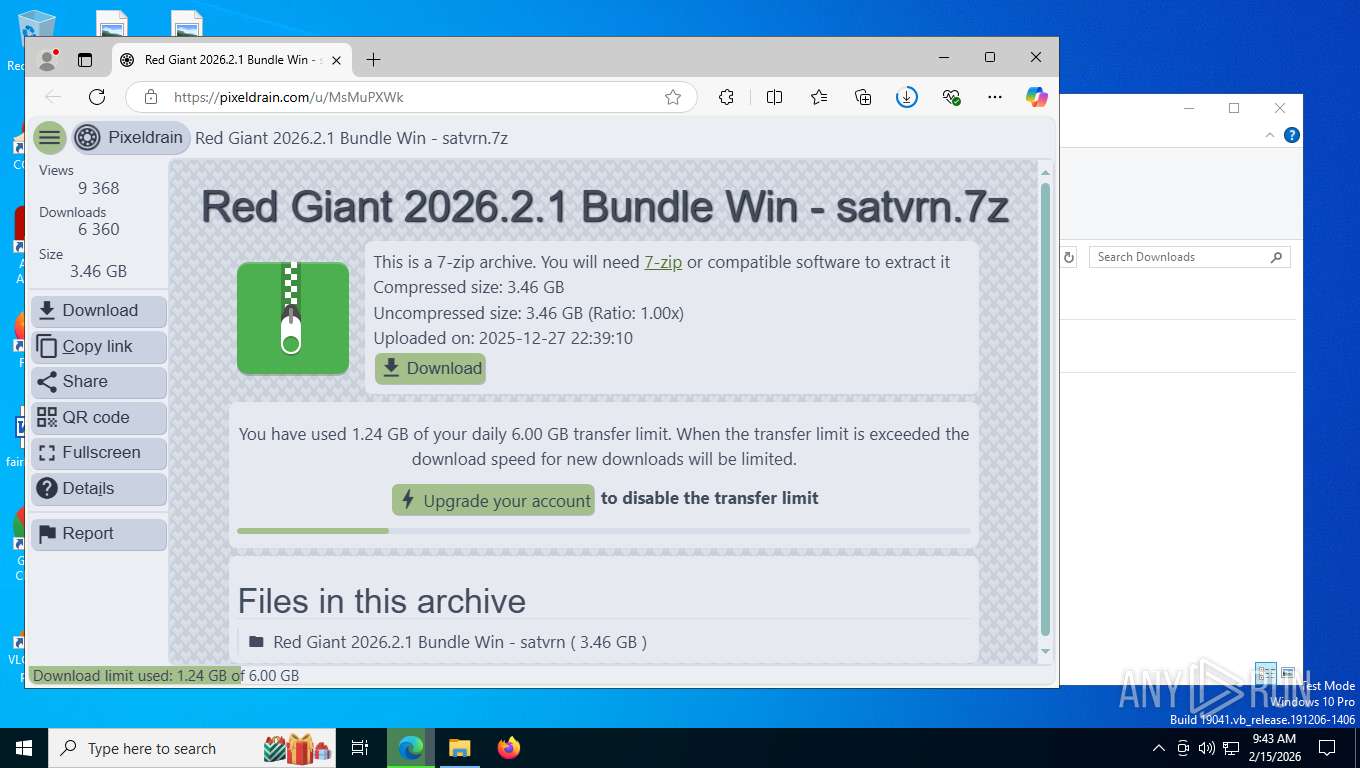
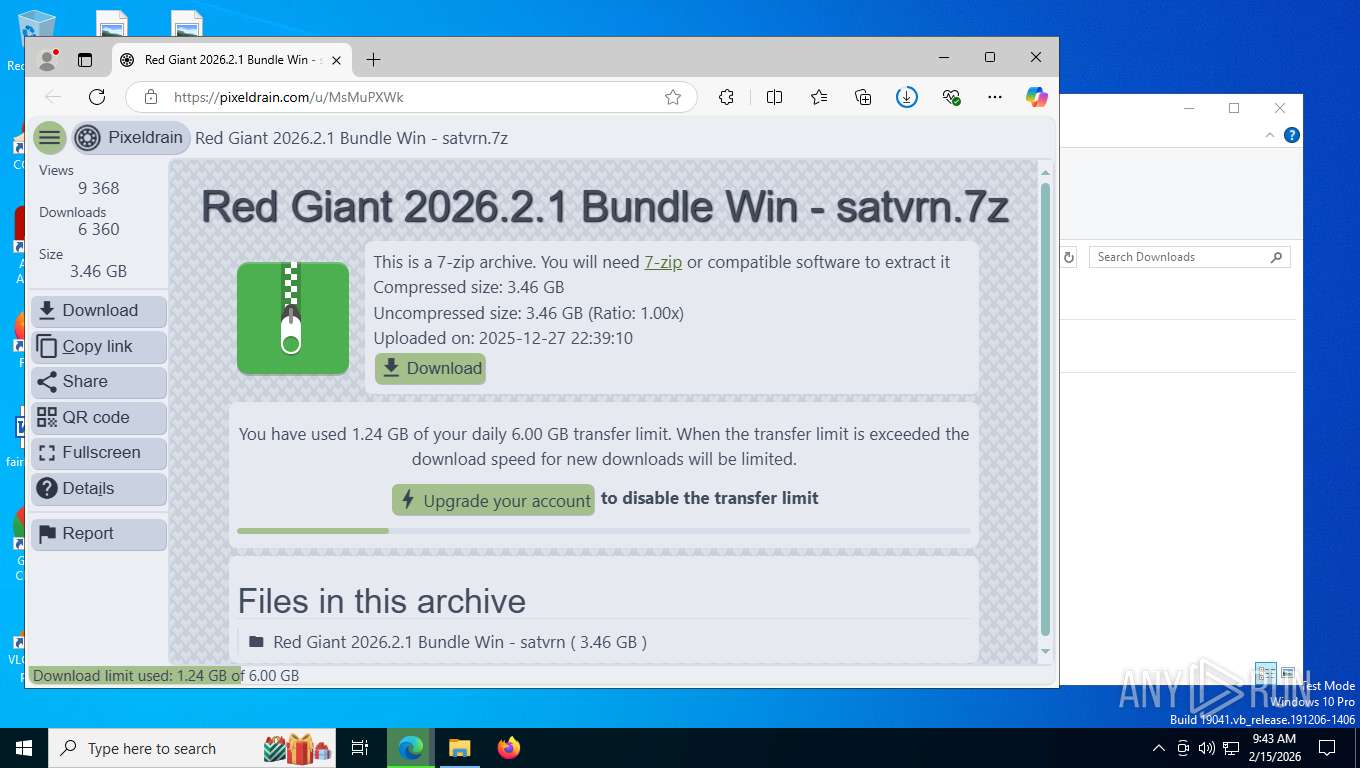
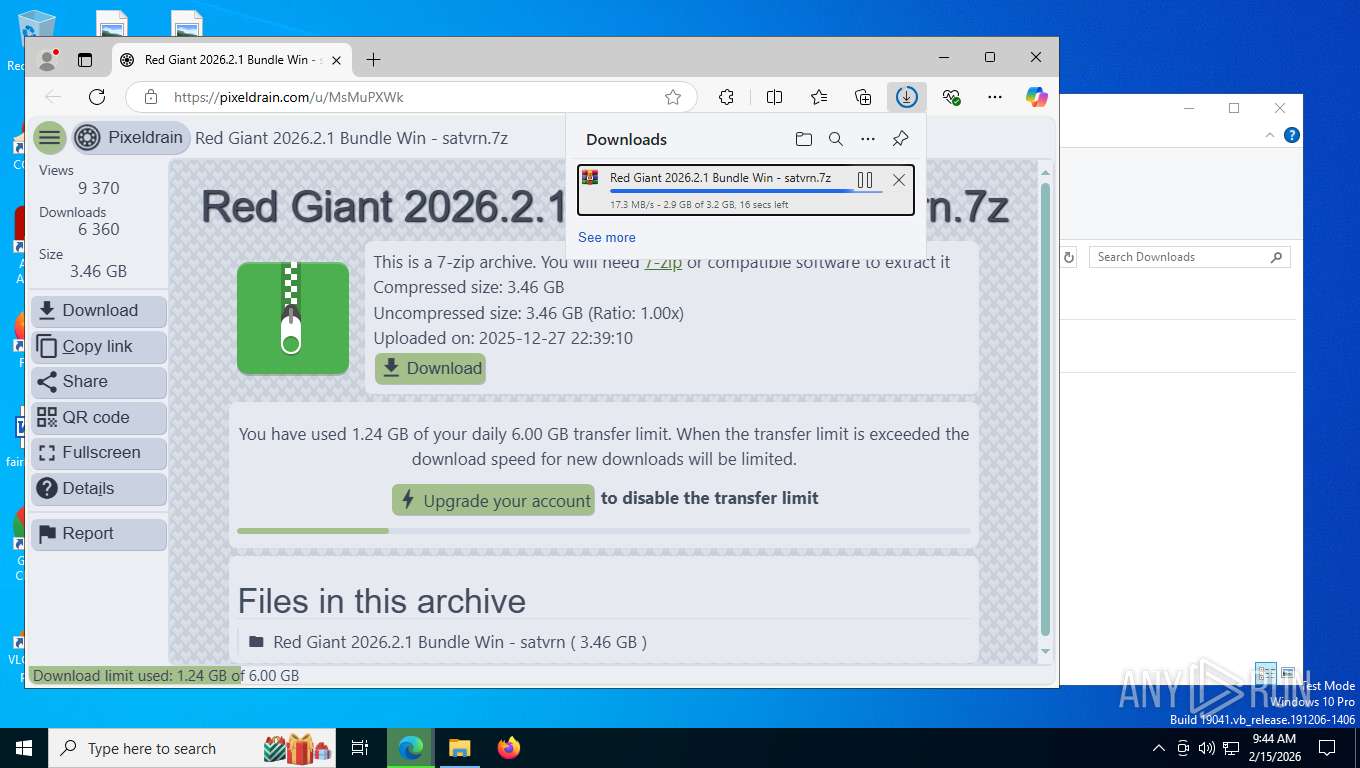
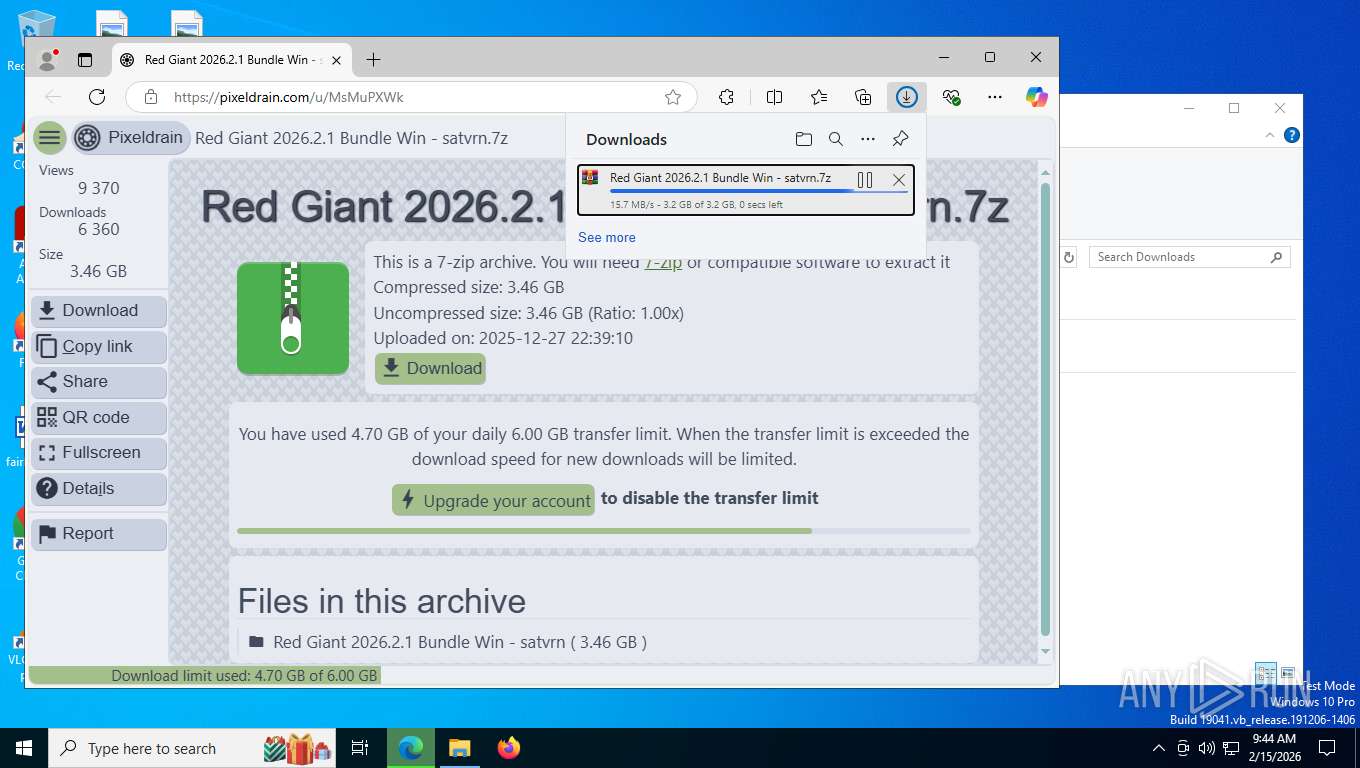
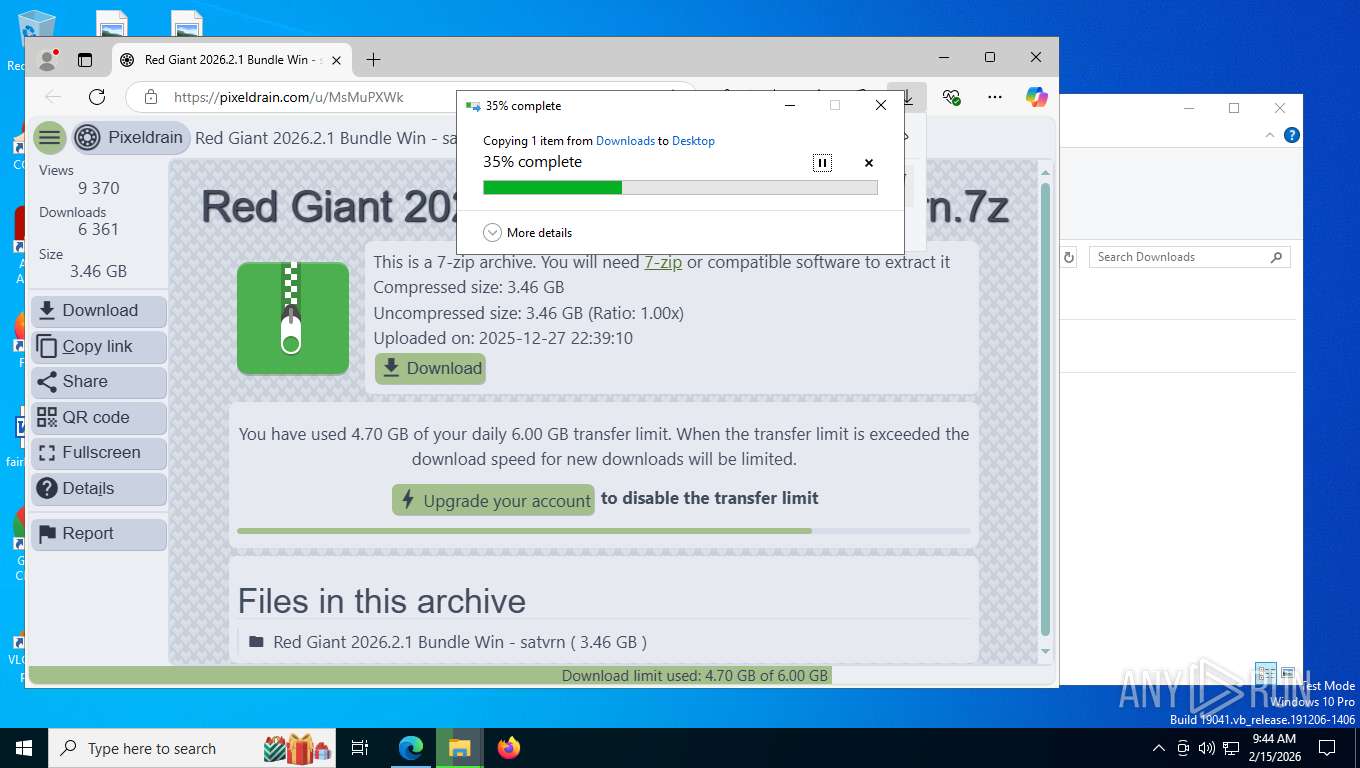
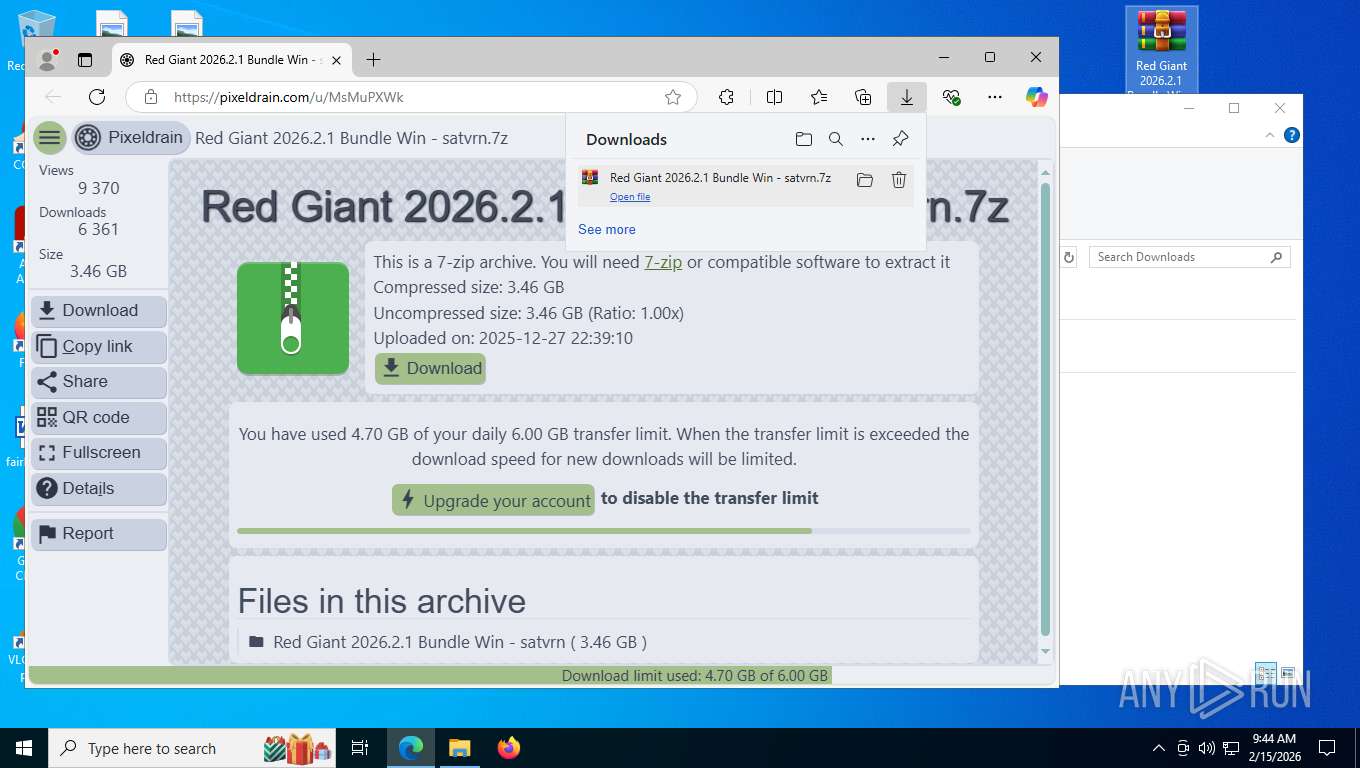
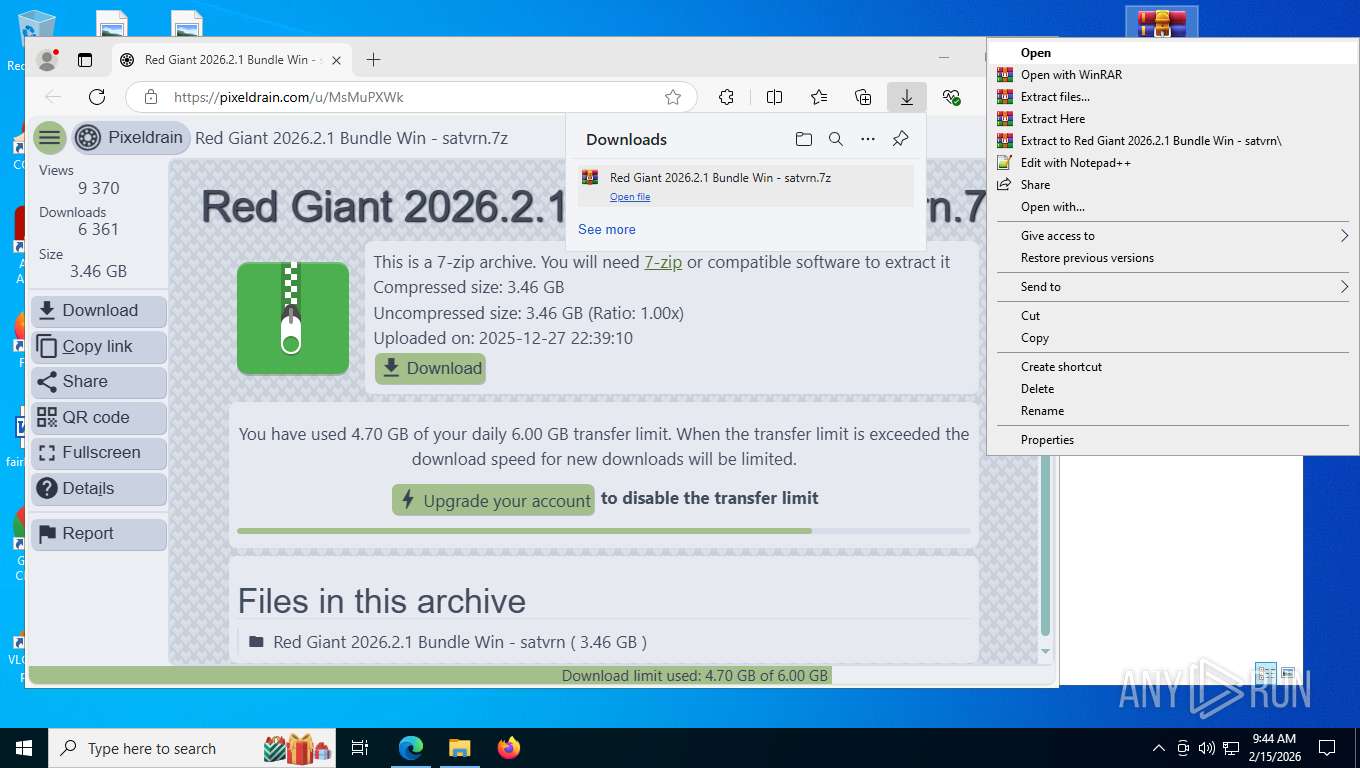
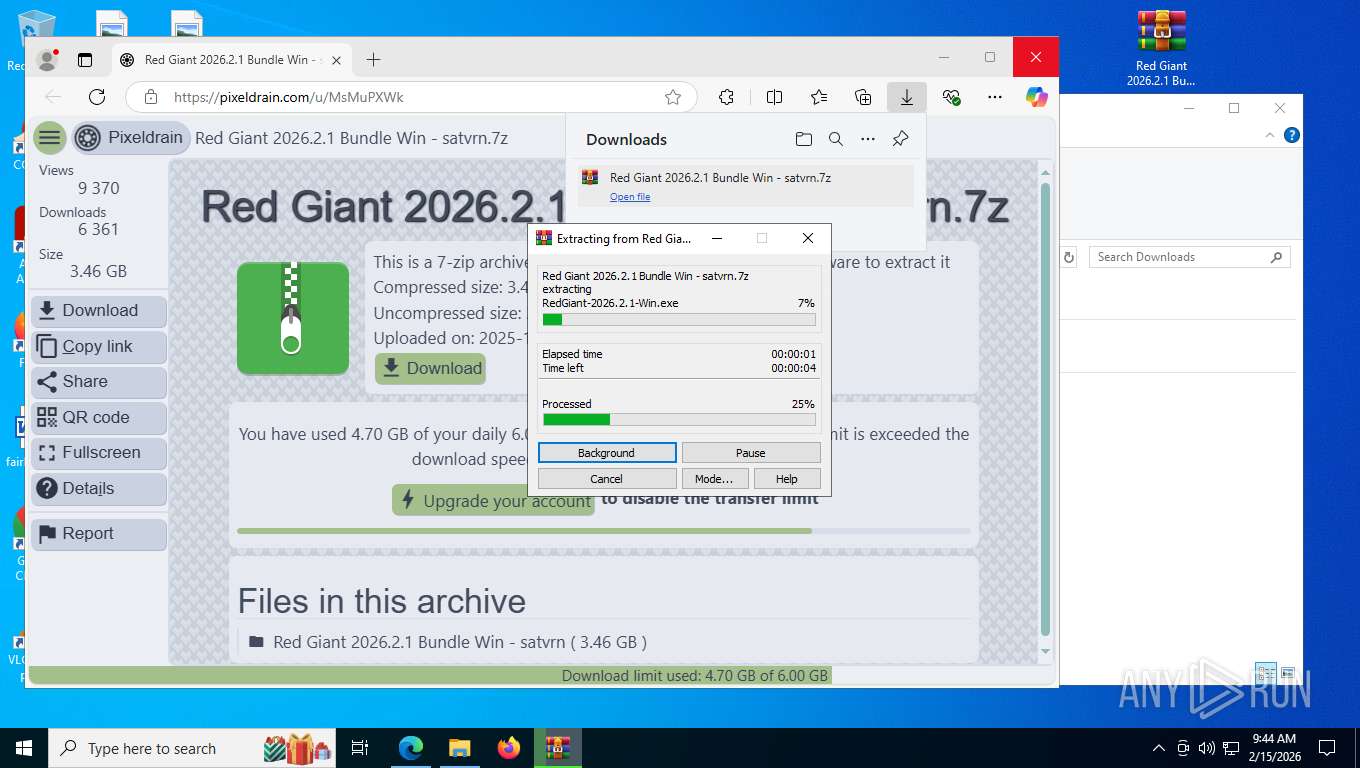
| URL: | https://pixeldrain.com/u/MsMuPXWk |
| Full analysis: | https://app.any.run/tasks/4544a773-2830-4d48-ac60-6131c26298e8 |
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2026, 14:40:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 02BE2F90135BD6FA02DA69B481402CC3 |
| SHA1: | ED97406A526989030BB38EAC54AFDAFC7AD35362 |
| SHA256: | E26BD2E45BCEB1DB6EB39361B08458DA71F37F26EB05FD8E027A2B886AAFD9CE |
| SSDEEP: | 3:N8Icl/GKg09d:2IG/dg0b |
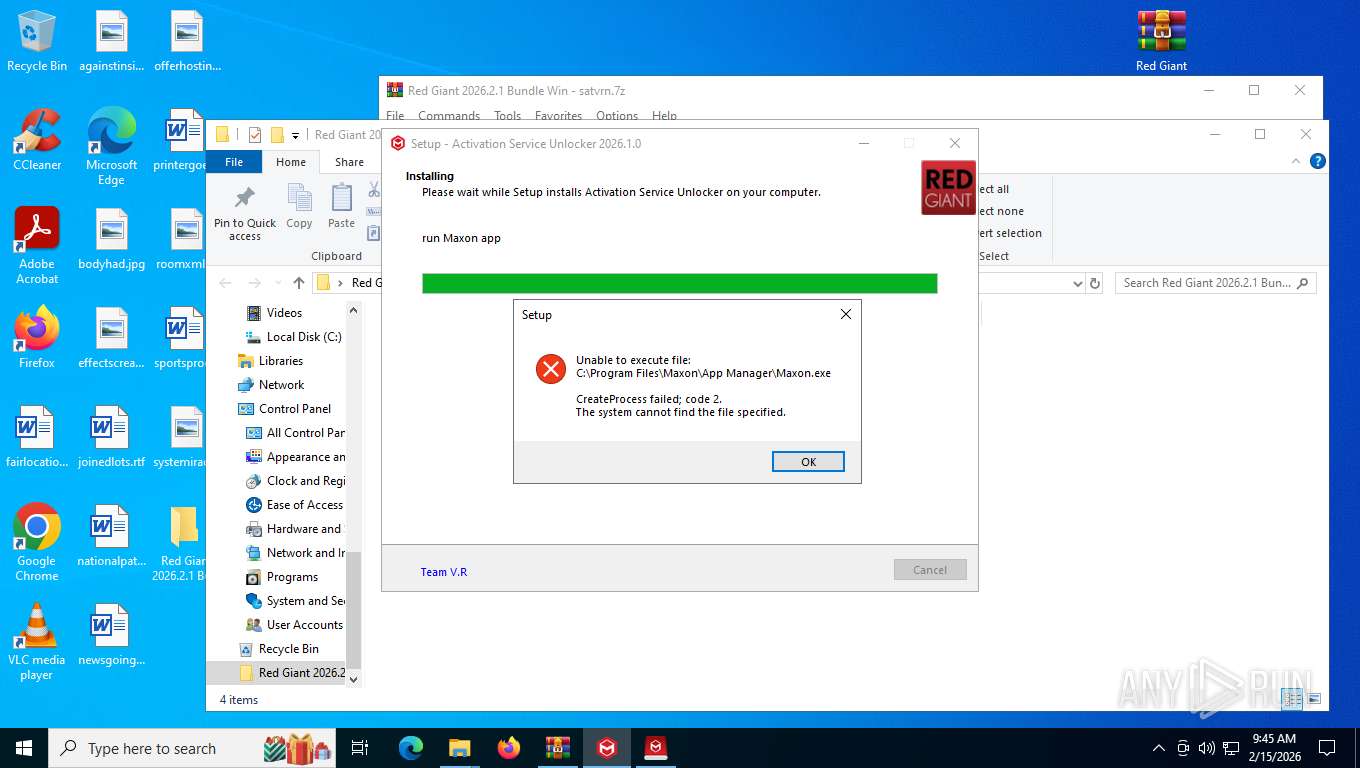
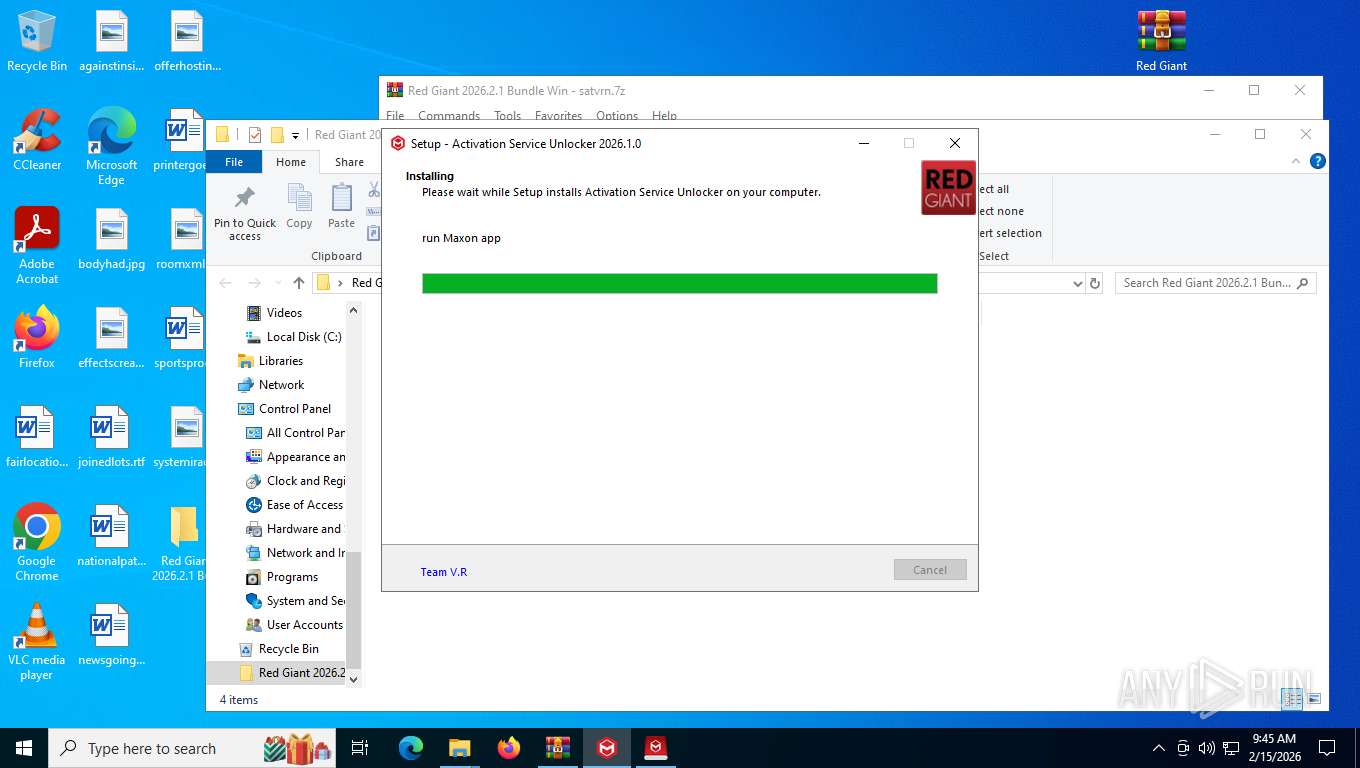
MALICIOUS
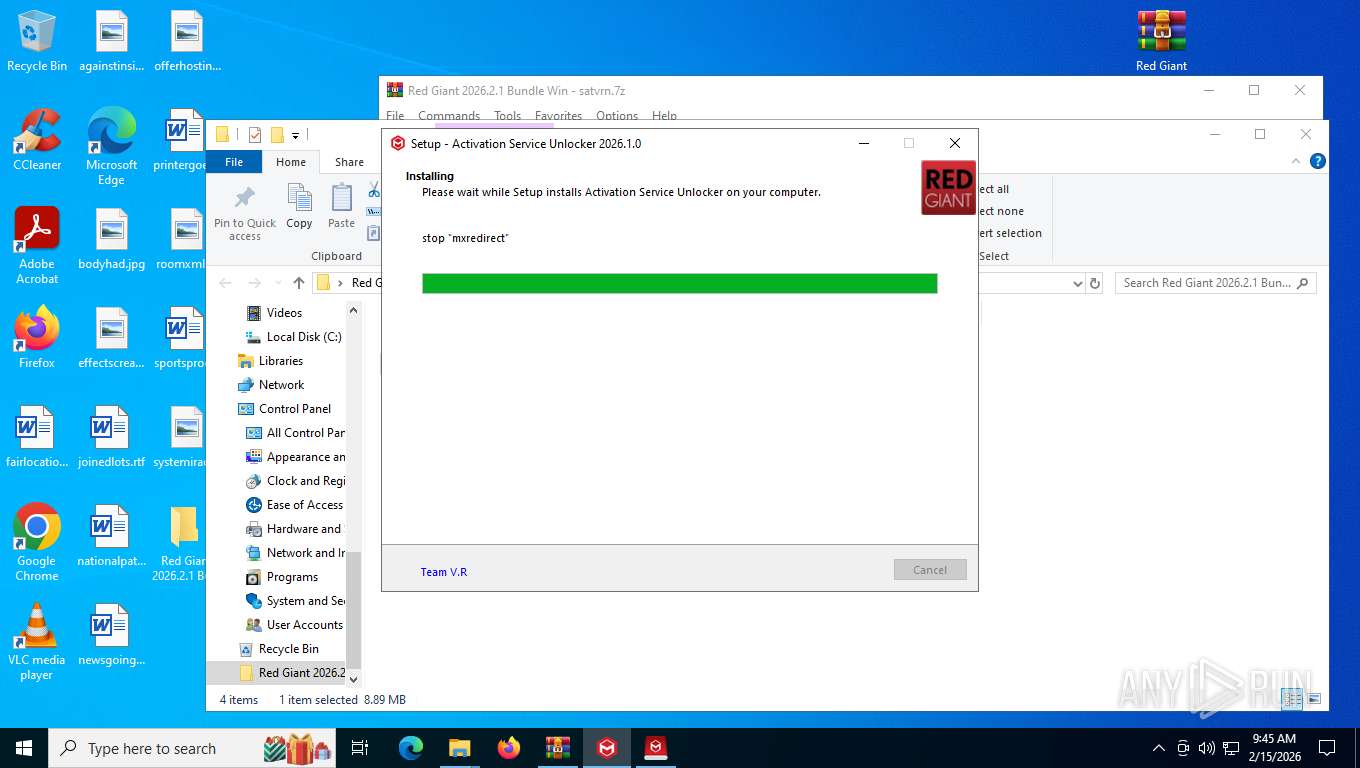
Starts NET.EXE for service management
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- net.exe (PID: 4924)
- net.exe (PID: 6232)
- net.exe (PID: 4828)
- net.exe (PID: 4296)
- net.exe (PID: 6344)
Changes the autorun value in the registry
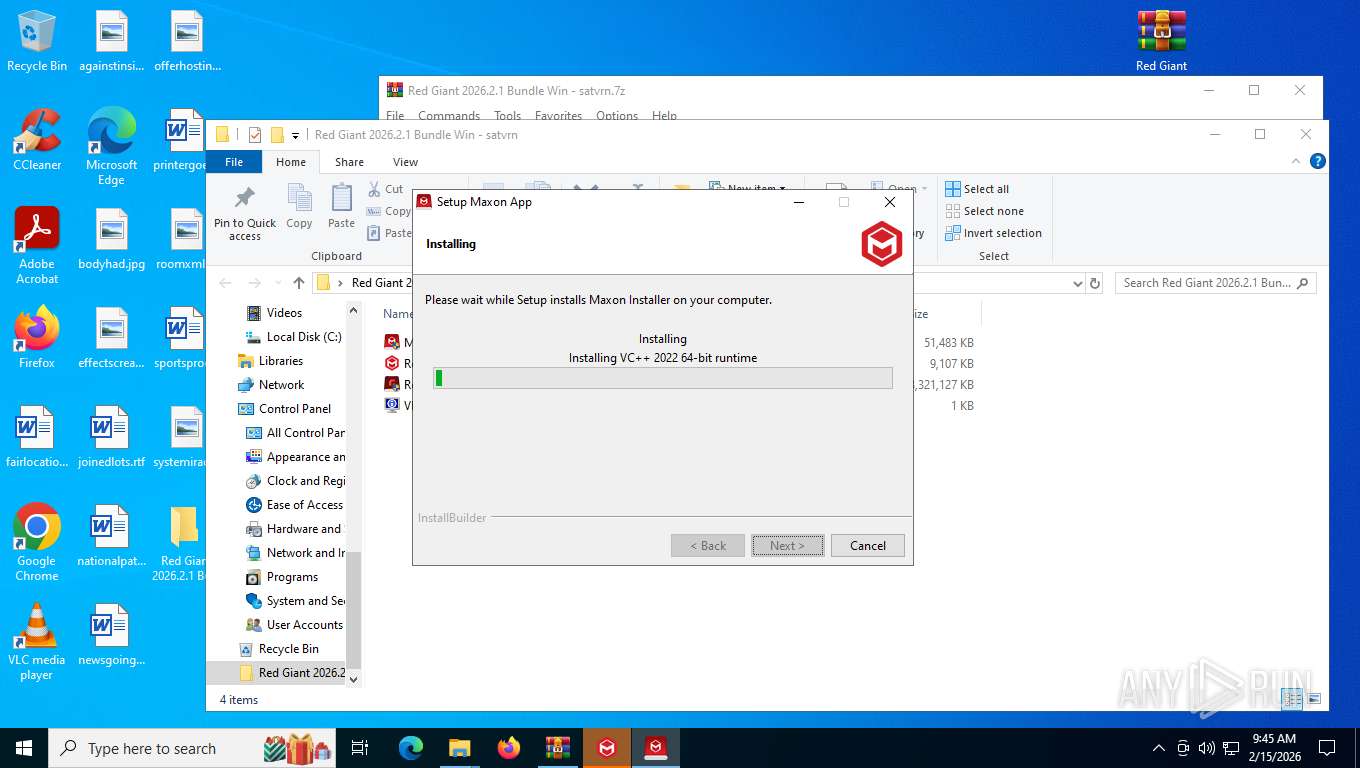
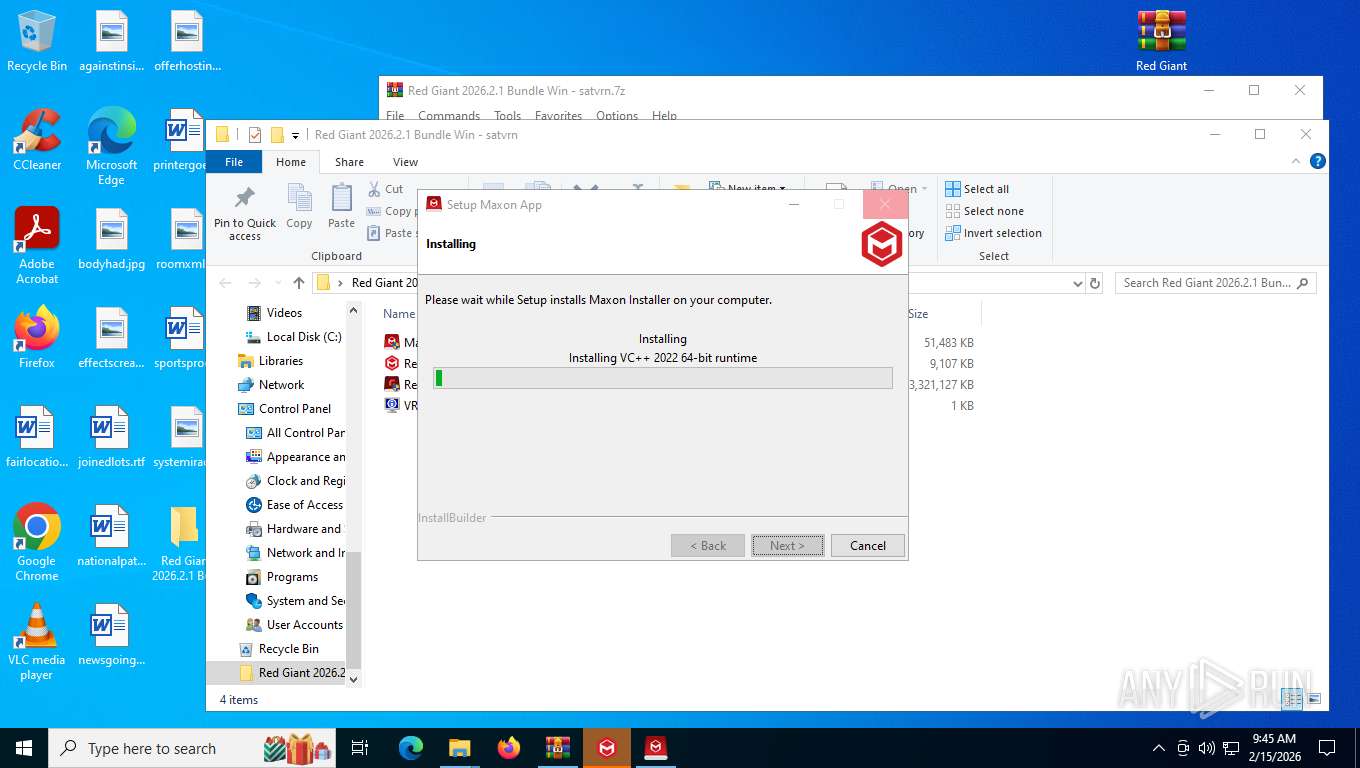
- VC_redist.x64.exe (PID: 8160)
Proxy execution via Explorer
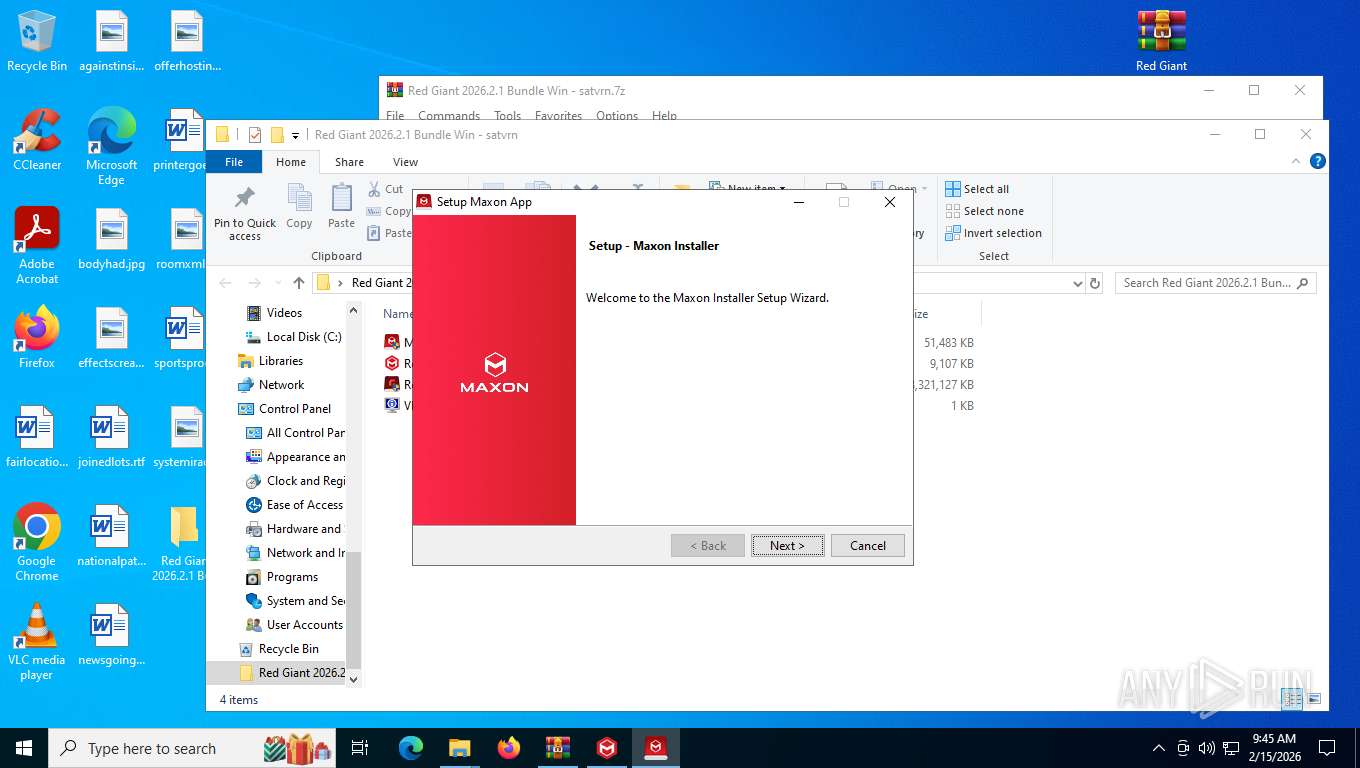
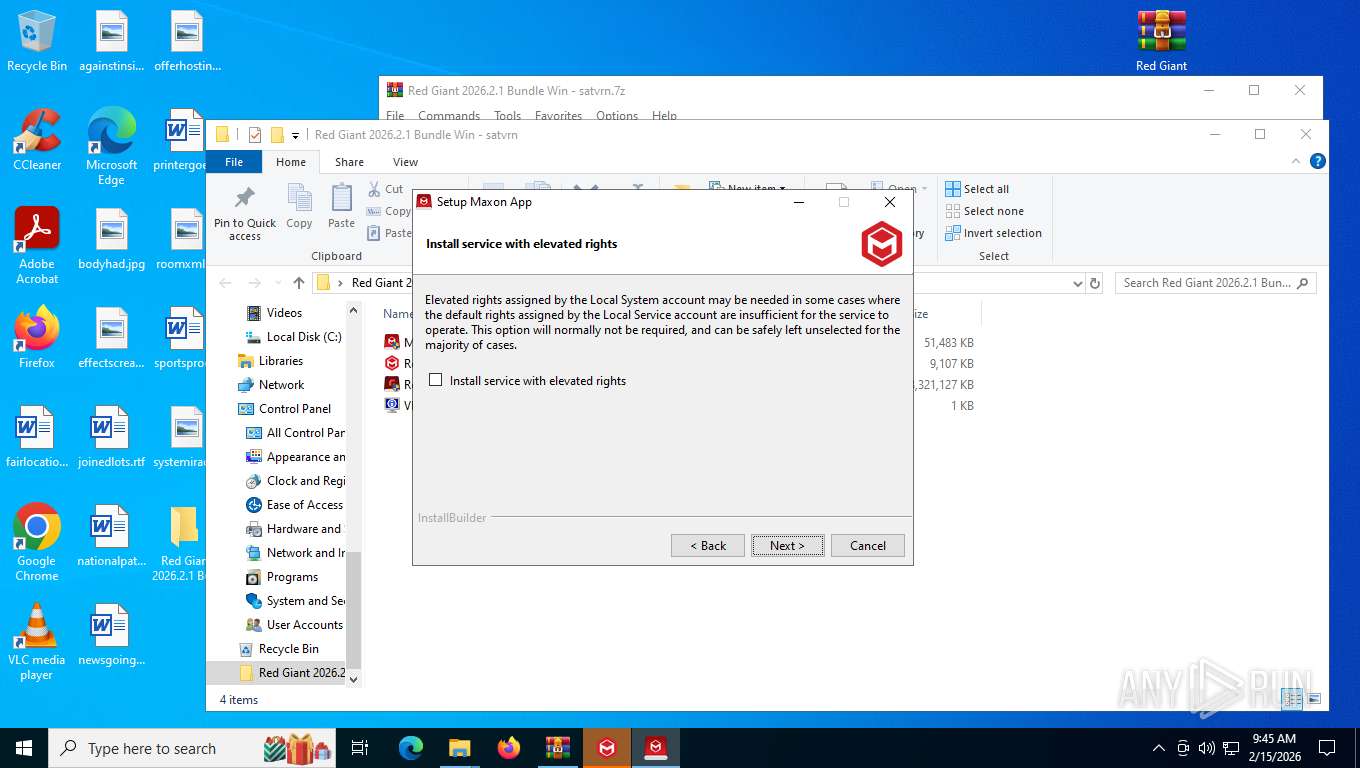
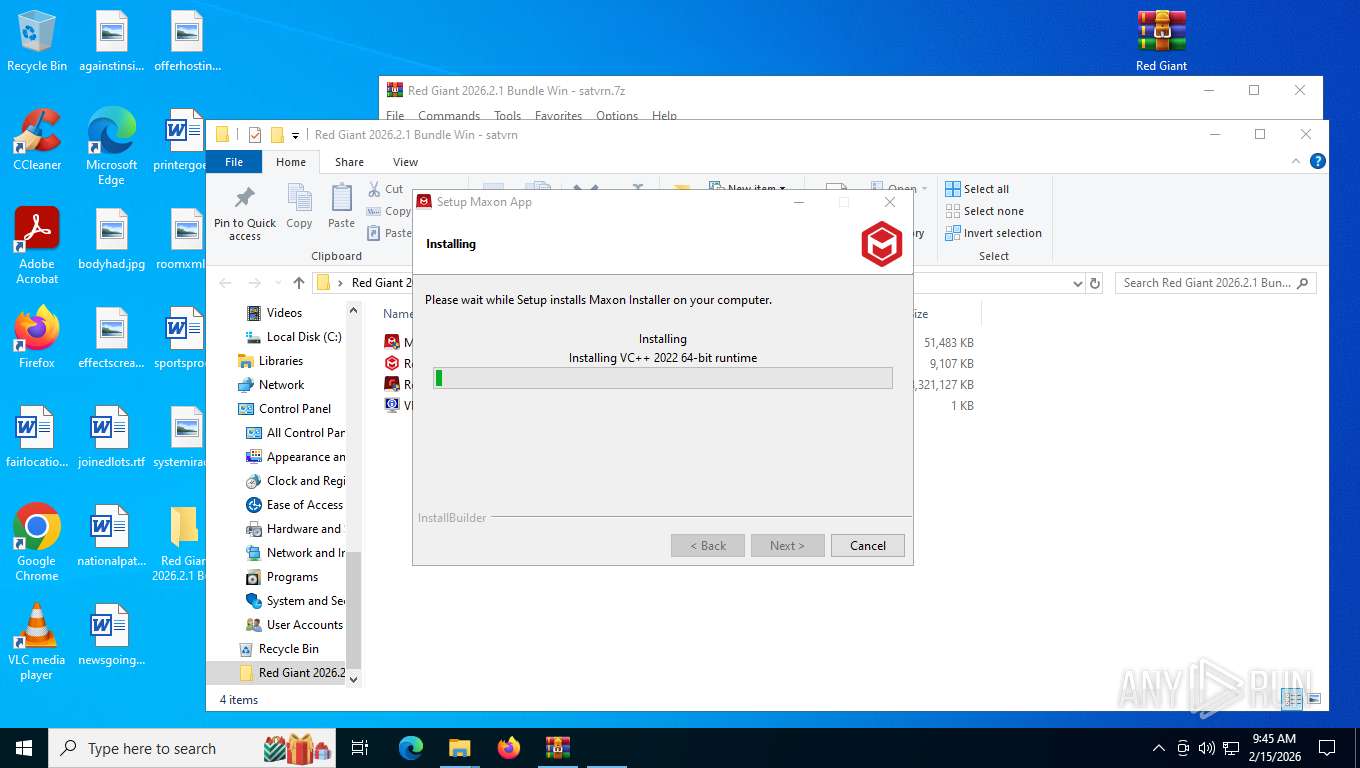
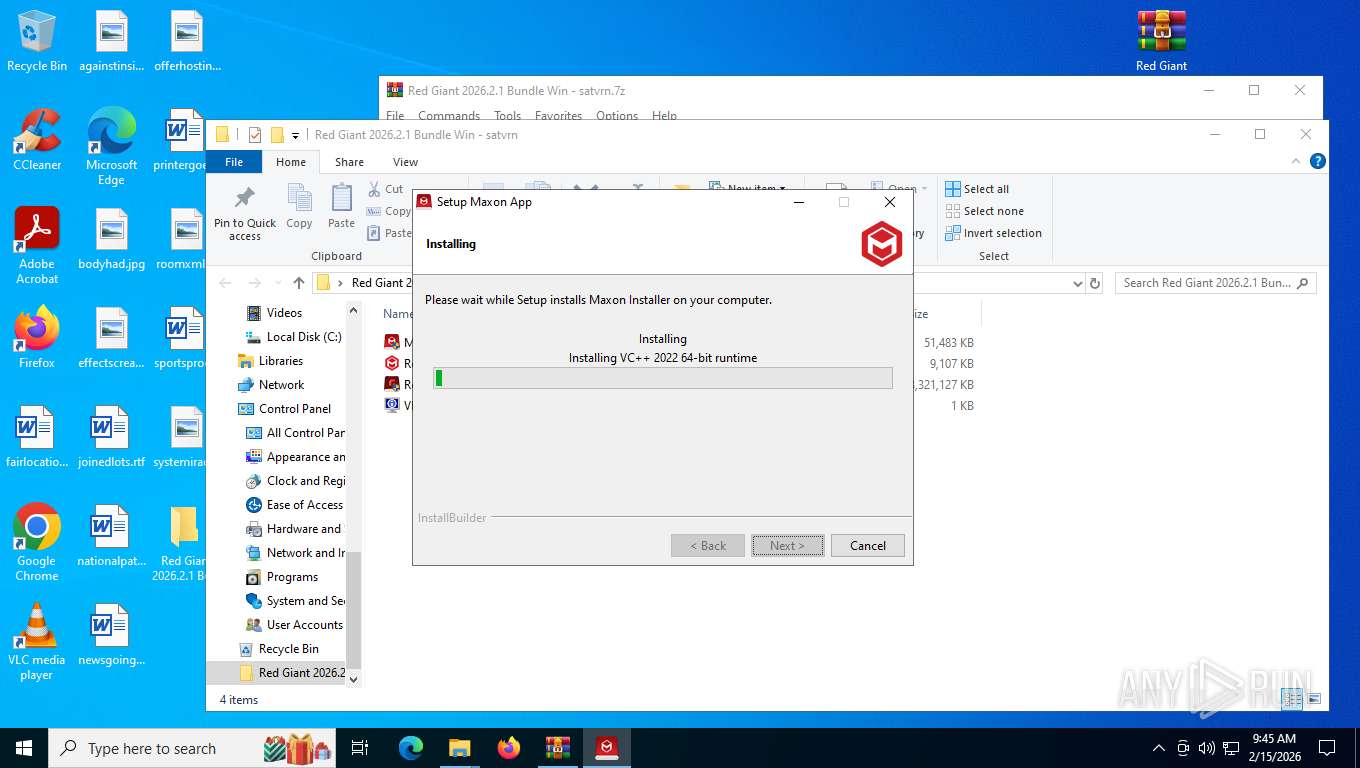
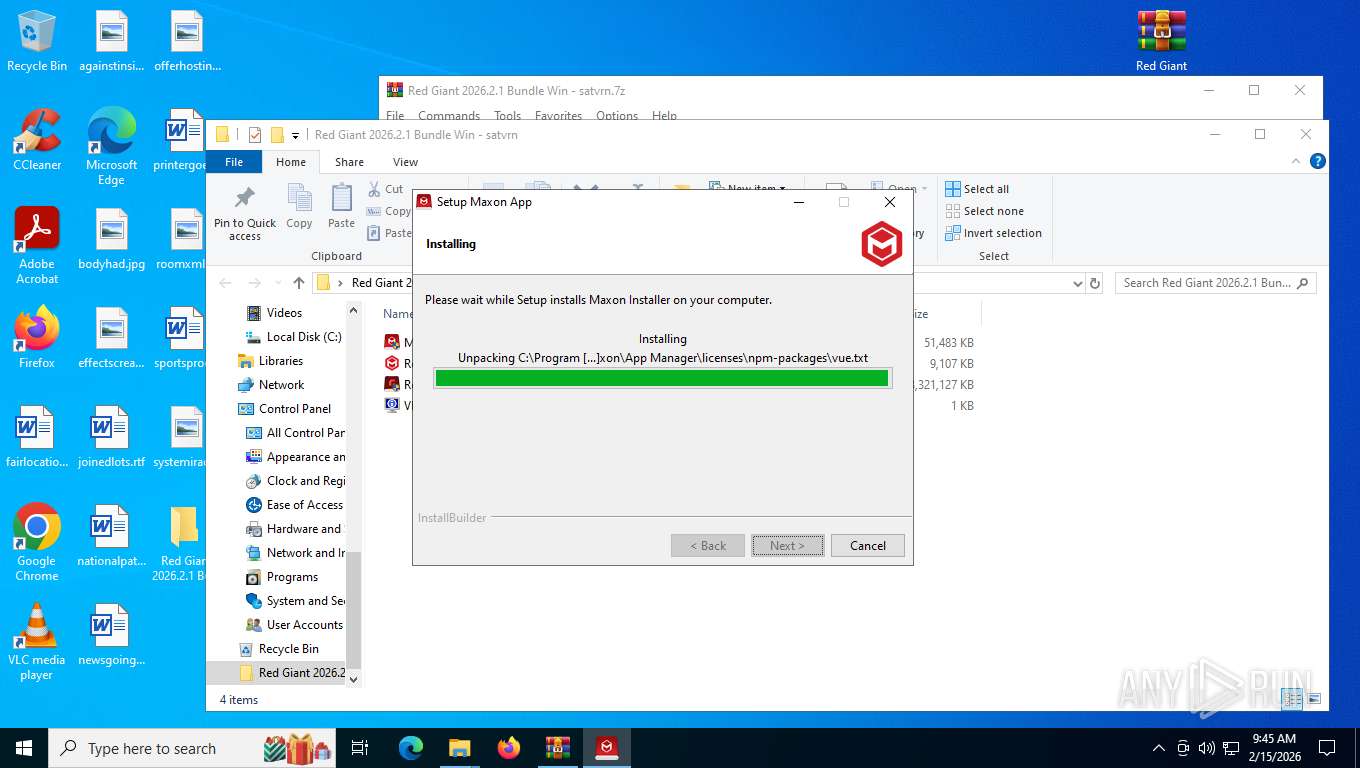
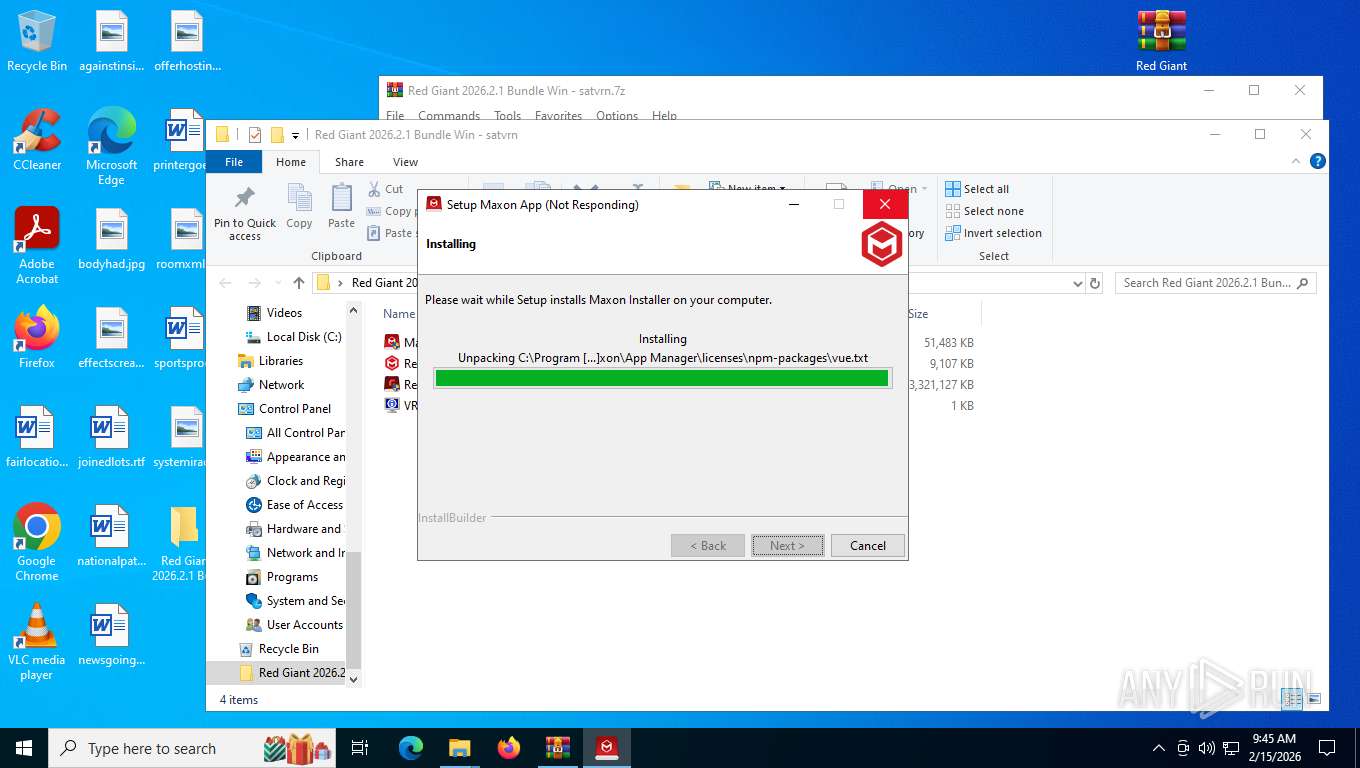
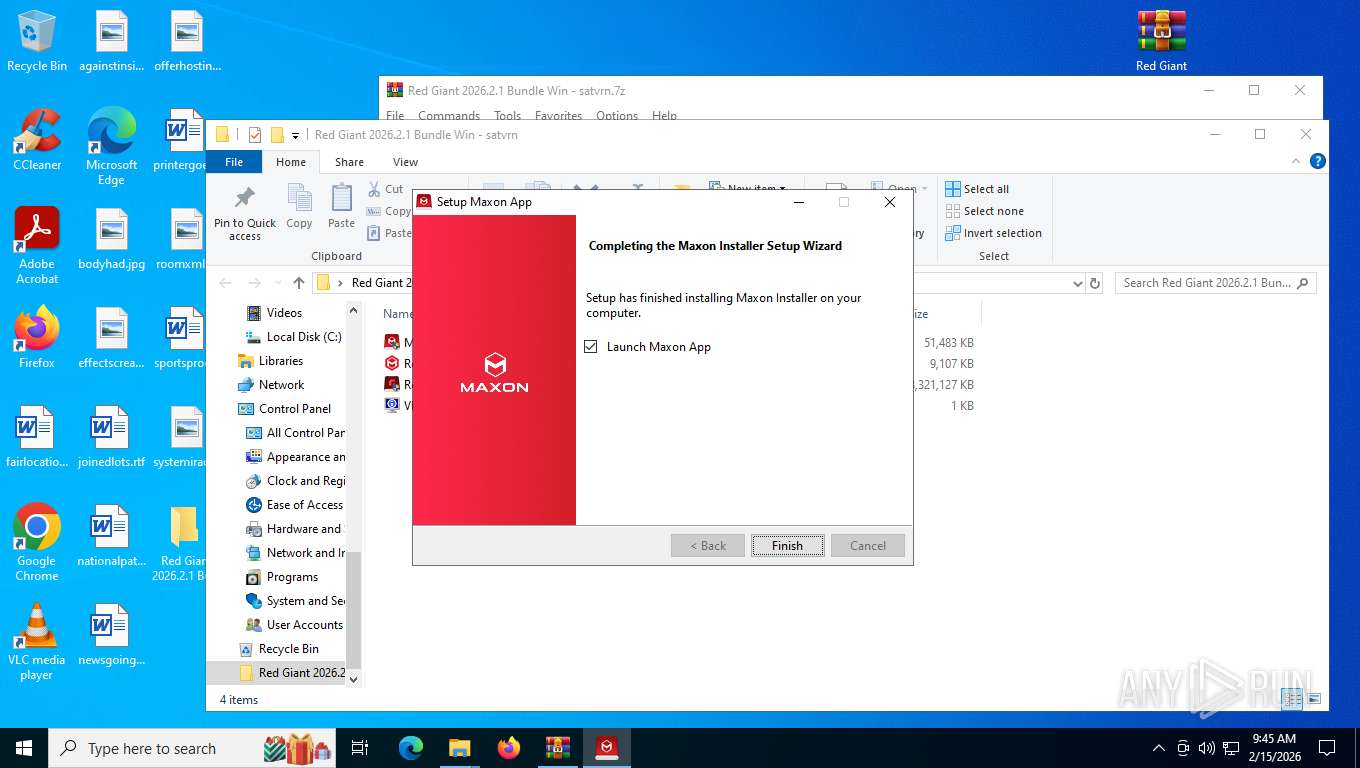
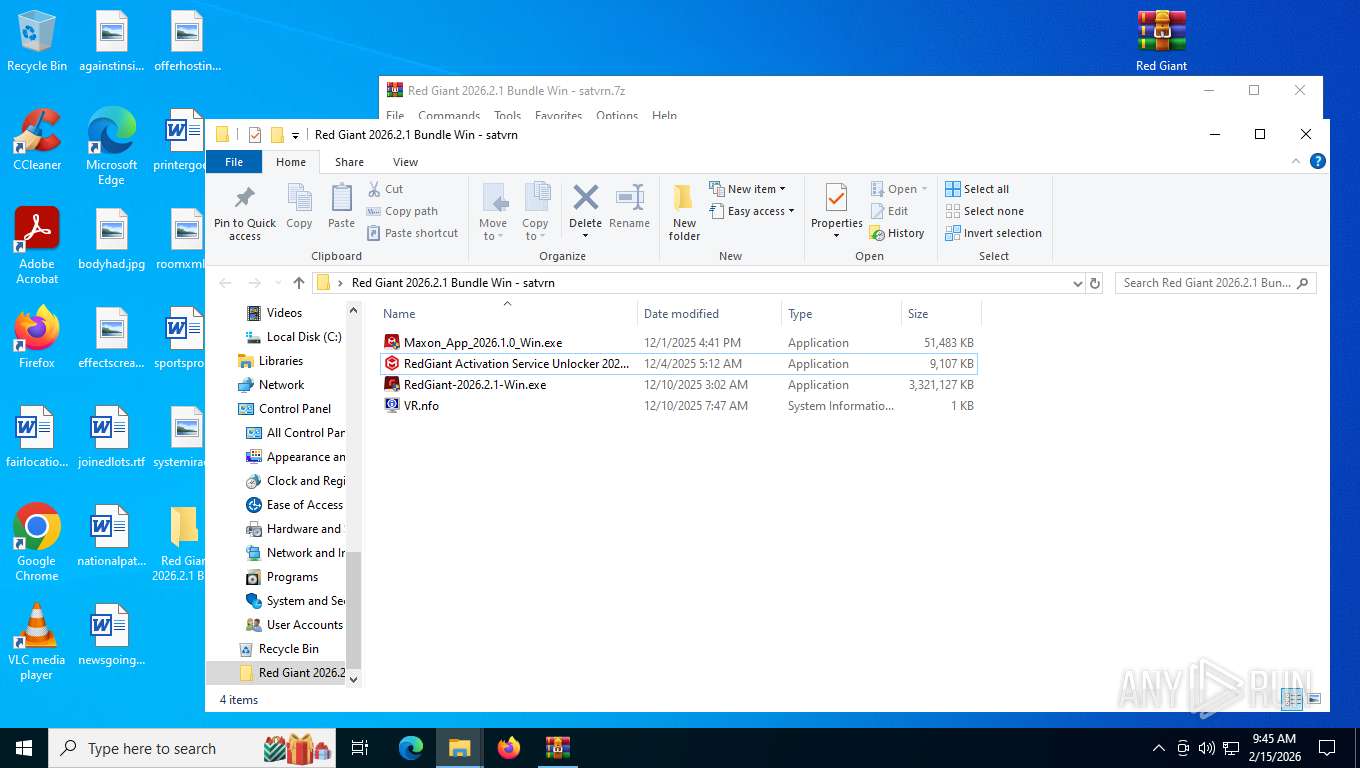
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
SUSPICIOUS
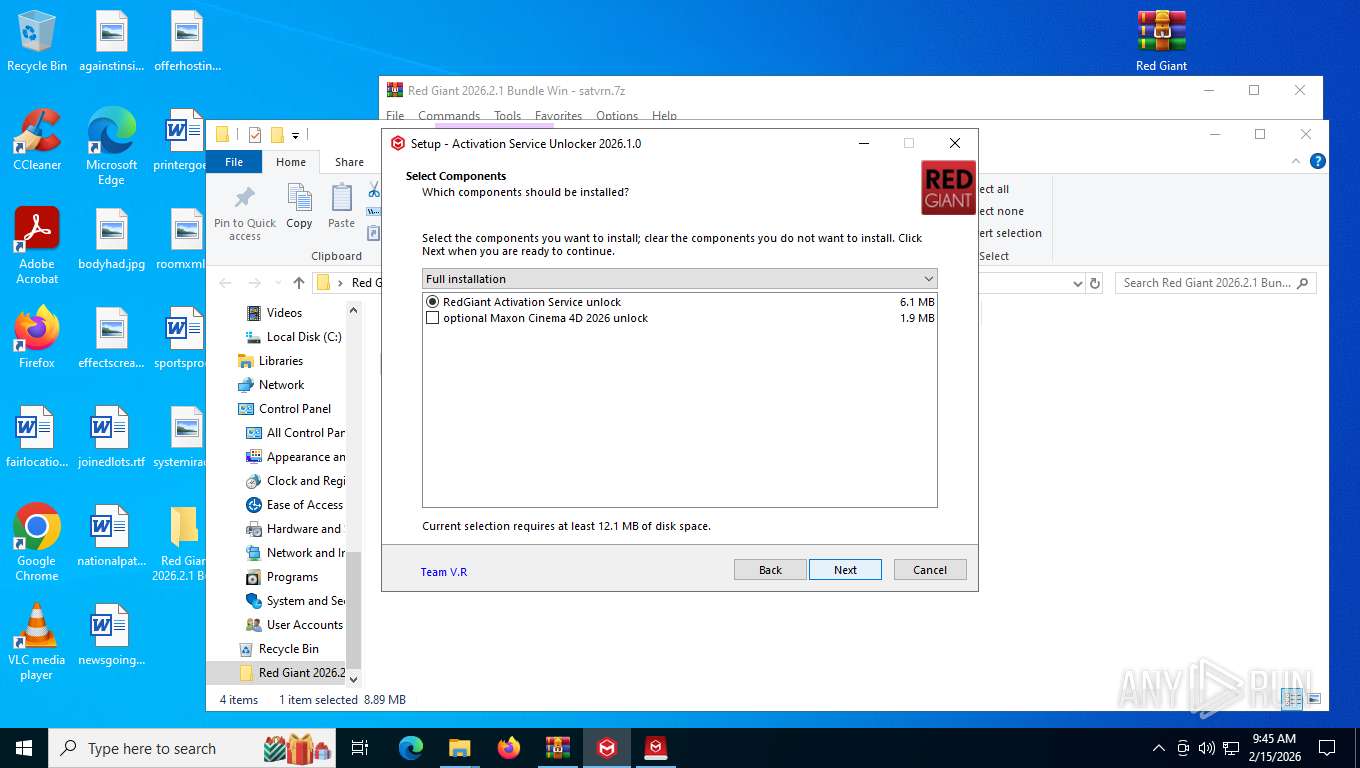
Executable content was dropped or overwritten
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 3208)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 6068)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- deep.exe (PID: 6340)
- deep.tmp (PID: 2456)
- VC_redist.x64.22.exe (PID: 8292)
- VC_RED~1.EXE (PID: 9112)
- VC_redist.x64.exe (PID: 8160)
- VC_redist.x64.exe (PID: 7040)
- VC_redist.x64.exe (PID: 9076)
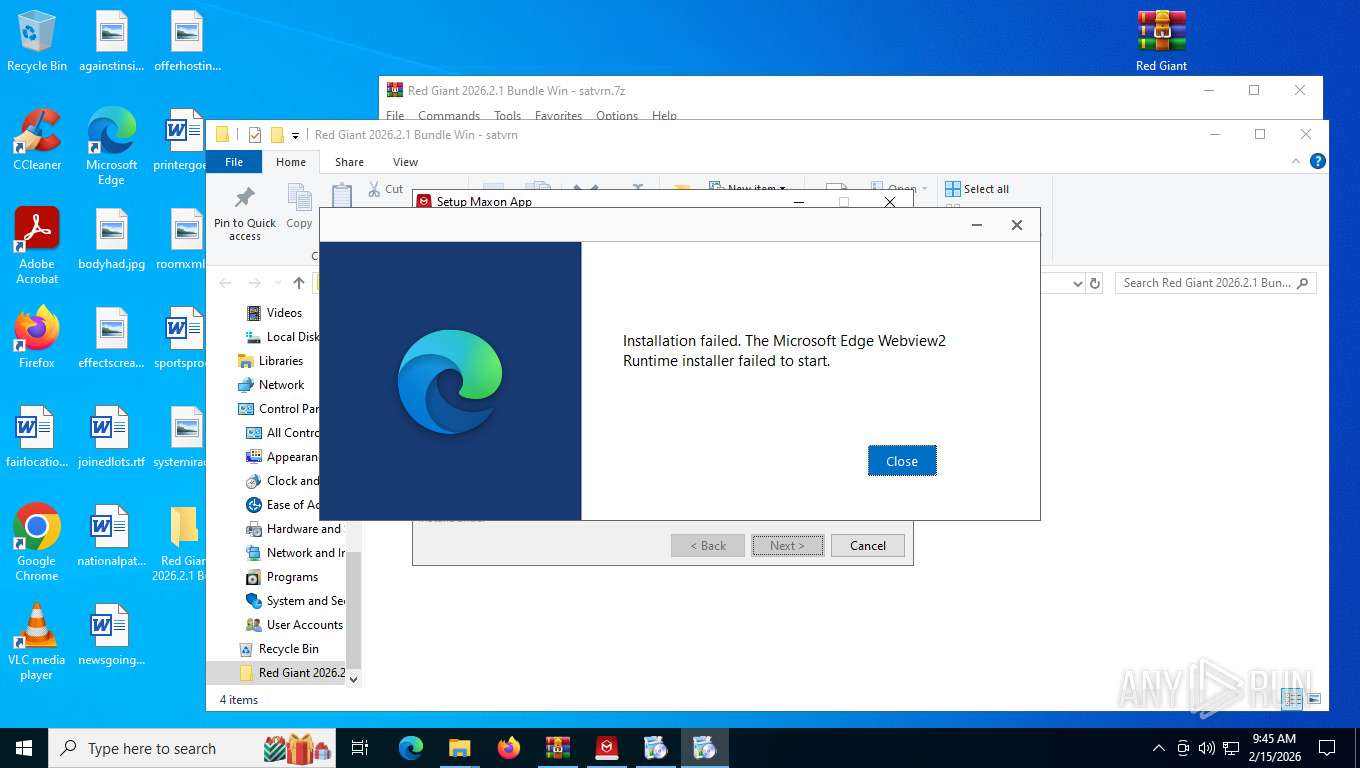
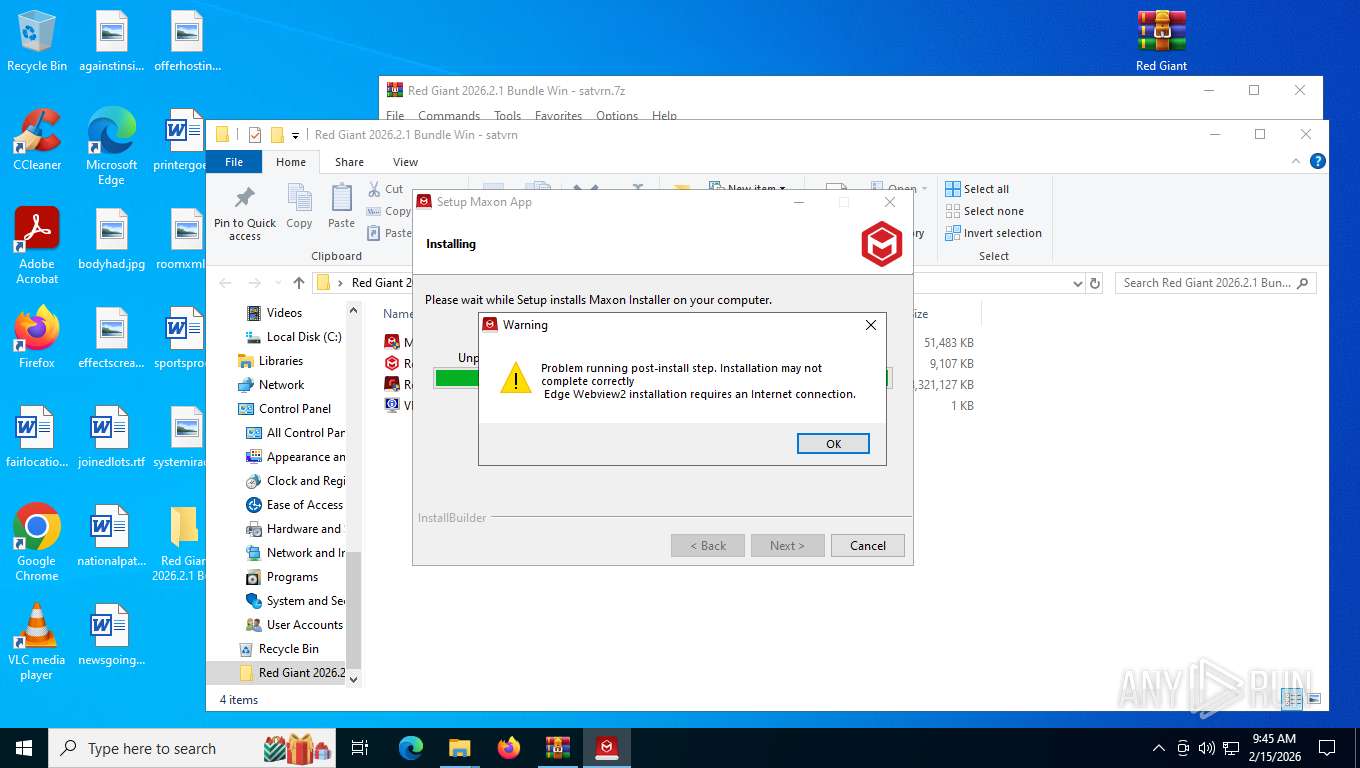
- MicrosoftEdgeWebview2Setup.exe (PID: 4296)
Reads the Windows owner or organization settings
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- deep.tmp (PID: 2456)
- msiexec.exe (PID: 4708)
Starts CMD.EXE for commands execution
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- deep.tmp (PID: 2456)
Using short paths in the command line
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- VC_redist.x64.22.exe (PID: 8292)
Executing commands from a ".bat" file
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
Using the short paths format
- cmd.exe (PID: 8660)
- cmd.exe (PID: 7620)
- VC_redist.x64.22.exe (PID: 8292)
- VC_RED~1.EXE (PID: 9112)
- MicrosoftEdgeWebview2Setup.exe (PID: 4296)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8660)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7620)
Mutex name with non-standard characters
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
Creates or modifies Windows services
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- deep.tmp (PID: 2456)
Uses TIMEOUT.EXE to delay execution
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
Uses TASKKILL.EXE to kill process
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- deep.tmp (PID: 2456)
Executing commands from ".cmd" file
- deep.tmp (PID: 2456)
The executable file from the user directory is run by the CMD process
- perl.exe (PID: 6240)
- perl.exe (PID: 6552)
- perl.exe (PID: 5500)
- perl.exe (PID: 8956)
- perl.exe (PID: 2448)
- perl.exe (PID: 8828)
- perl.exe (PID: 3636)
- perl.exe (PID: 7312)
- perl.exe (PID: 8140)
- perl.exe (PID: 8456)
- perl.exe (PID: 5708)
- perl.exe (PID: 6036)
- perl.exe (PID: 8584)
- perl.exe (PID: 2124)
- perl.exe (PID: 4256)
- perl.exe (PID: 7244)
- perl.exe (PID: 8652)
- perl.exe (PID: 5768)
- perl.exe (PID: 3032)
- perl.exe (PID: 8080)
- perl.exe (PID: 9160)
- perl.exe (PID: 7780)
Process drops legitimate windows executable
- VC_redist.x64.22.exe (PID: 8292)
- VC_RED~1.EXE (PID: 9112)
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- msiexec.exe (PID: 4708)
- VC_redist.x64.exe (PID: 8160)
- VC_redist.x64.exe (PID: 9076)
- MicrosoftEdgeWebview2Setup.exe (PID: 4296)
- MicrosoftEdgeUpdate.exe (PID: 4288)
Starts a Microsoft application from unusual location
- VC_RED~1.EXE (PID: 9112)
- VC_redist.x64.exe (PID: 8160)
- MicrosoftEdgeUpdate.exe (PID: 4288)
Searches for installed software
- VC_RED~1.EXE (PID: 9112)
- dllhost.exe (PID: 4312)
- VC_redist.x64.exe (PID: 7040)
- VC_redist.x64.exe (PID: 9076)
Starts itself from another location
- VC_RED~1.EXE (PID: 9112)
Executes as Windows Service
- VSSVC.exe (PID: 4800)
The process drops C-runtime libraries
- msiexec.exe (PID: 4708)
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
Application launched itself
- VC_redist.x64.exe (PID: 6848)
- VC_redist.x64.exe (PID: 7040)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 4288)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 2376)
INFO
Drops script file
- msedge.exe (PID: 5080)
- msedge.exe (PID: 2232)
- cmd.exe (PID: 8660)
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- cmd.exe (PID: 7620)
- deep.tmp (PID: 2456)
- cmd.exe (PID: 3368)
Reads Environment values
- identity_helper.exe (PID: 9088)
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- MicrosoftEdgeUpdate.exe (PID: 4288)
Checks supported languages
- identity_helper.exe (PID: 9088)
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 3208)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7824)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 6068)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- deep.exe (PID: 6340)
- deep.tmp (PID: 2456)
- perl.exe (PID: 6552)
- perl.exe (PID: 5500)
- perl.exe (PID: 2448)
- perl.exe (PID: 8956)
- perl.exe (PID: 7312)
- perl.exe (PID: 6240)
- perl.exe (PID: 8828)
- perl.exe (PID: 3636)
- perl.exe (PID: 8456)
- perl.exe (PID: 5708)
- perl.exe (PID: 6036)
- perl.exe (PID: 8140)
- perl.exe (PID: 2124)
- perl.exe (PID: 8584)
- perl.exe (PID: 4256)
- perl.exe (PID: 7244)
- perl.exe (PID: 8652)
- perl.exe (PID: 5768)
- perl.exe (PID: 3032)
- perl.exe (PID: 8080)
- perl.exe (PID: 9160)
- perl.exe (PID: 7780)
- VC_redist.x64.22.exe (PID: 8292)
- VC_RED~1.EXE (PID: 9112)
- VC_redist.x64.exe (PID: 8160)
- msiexec.exe (PID: 4708)
- VC_redist.x64.exe (PID: 6848)
- VC_redist.x64.exe (PID: 7040)
- VC_redist.x64.exe (PID: 9076)
- MicrosoftEdgeWebview2Setup.exe (PID: 4296)
- MicrosoftEdgeUpdate.exe (PID: 4288)
- Maxon.exe (PID: 5536)
Reads the computer name
- identity_helper.exe (PID: 9088)
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 6068)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7824)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- deep.exe (PID: 6340)
- deep.tmp (PID: 2456)
- VC_redist.x64.22.exe (PID: 8292)
- VC_RED~1.EXE (PID: 9112)
- VC_redist.x64.exe (PID: 8160)
- msiexec.exe (PID: 4708)
- VC_redist.x64.exe (PID: 7040)
- VC_redist.x64.exe (PID: 9076)
- MicrosoftEdgeUpdate.exe (PID: 4288)
- Maxon.exe (PID: 5536)
Application launched itself
- msedge.exe (PID: 5080)
Checks proxy server information
- slui.exe (PID: 7288)
- wermgr.exe (PID: 7828)
- MicrosoftEdgeUpdate.exe (PID: 4288)
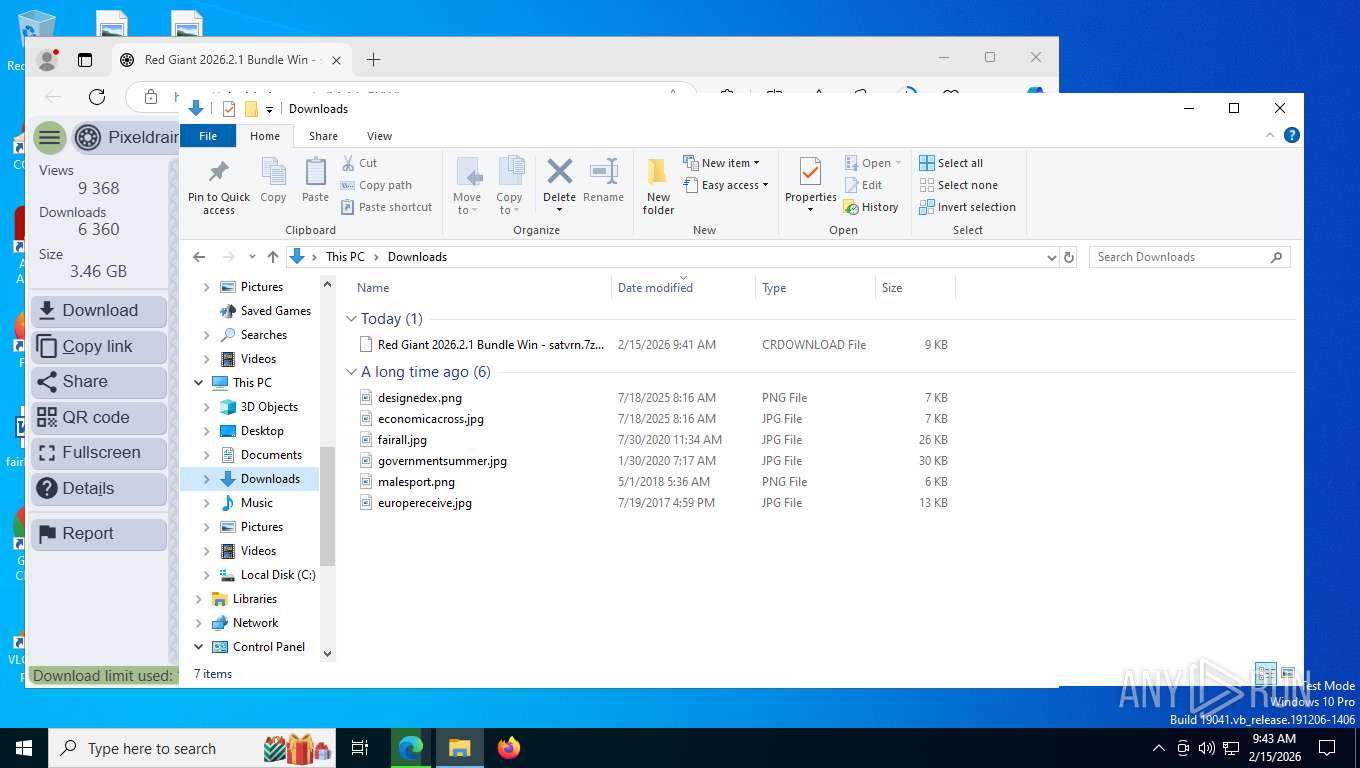
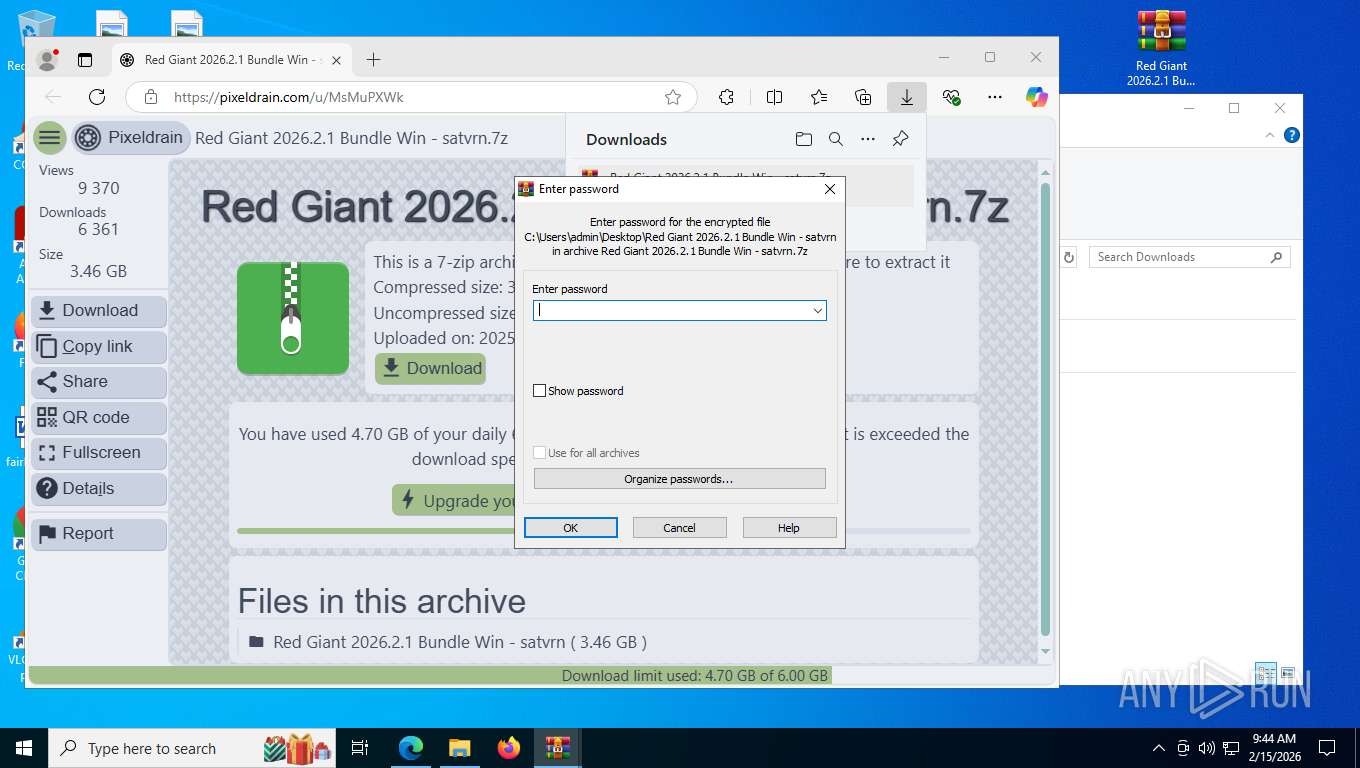
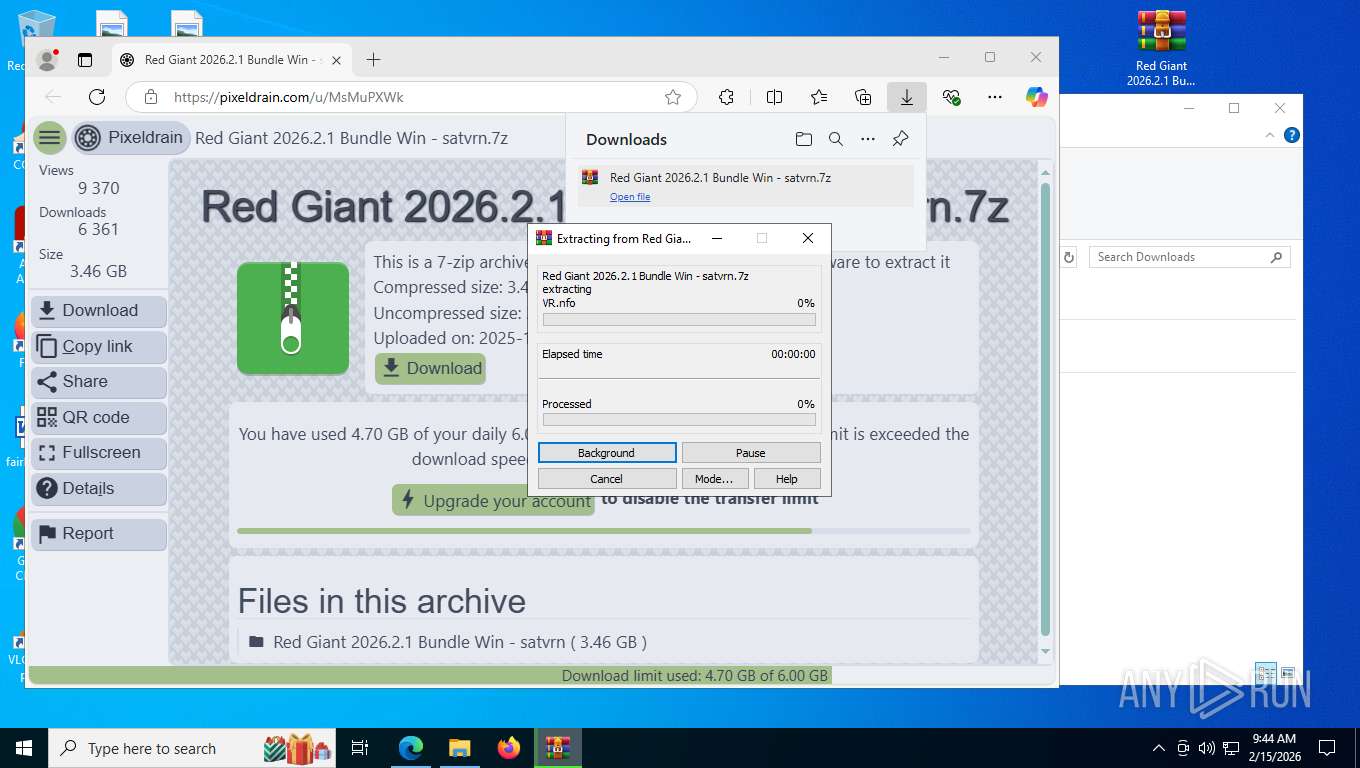
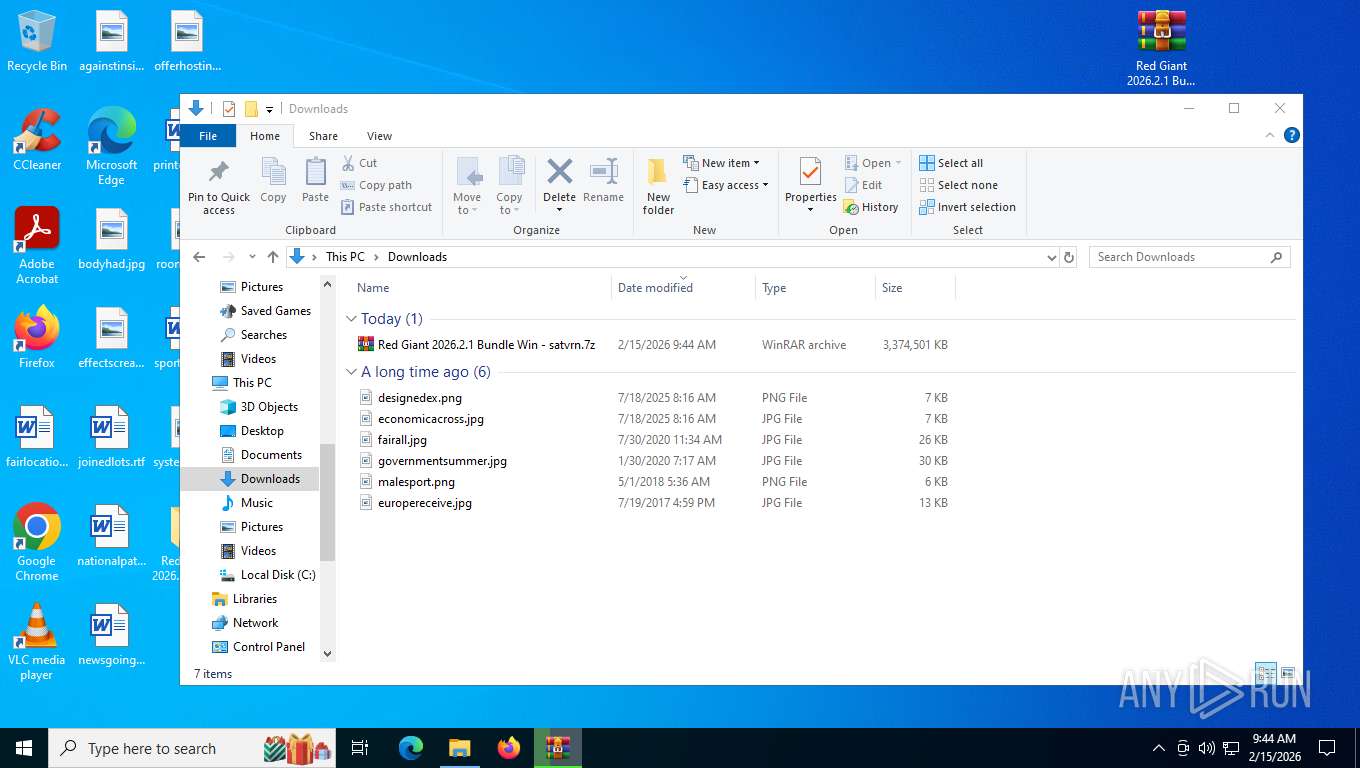
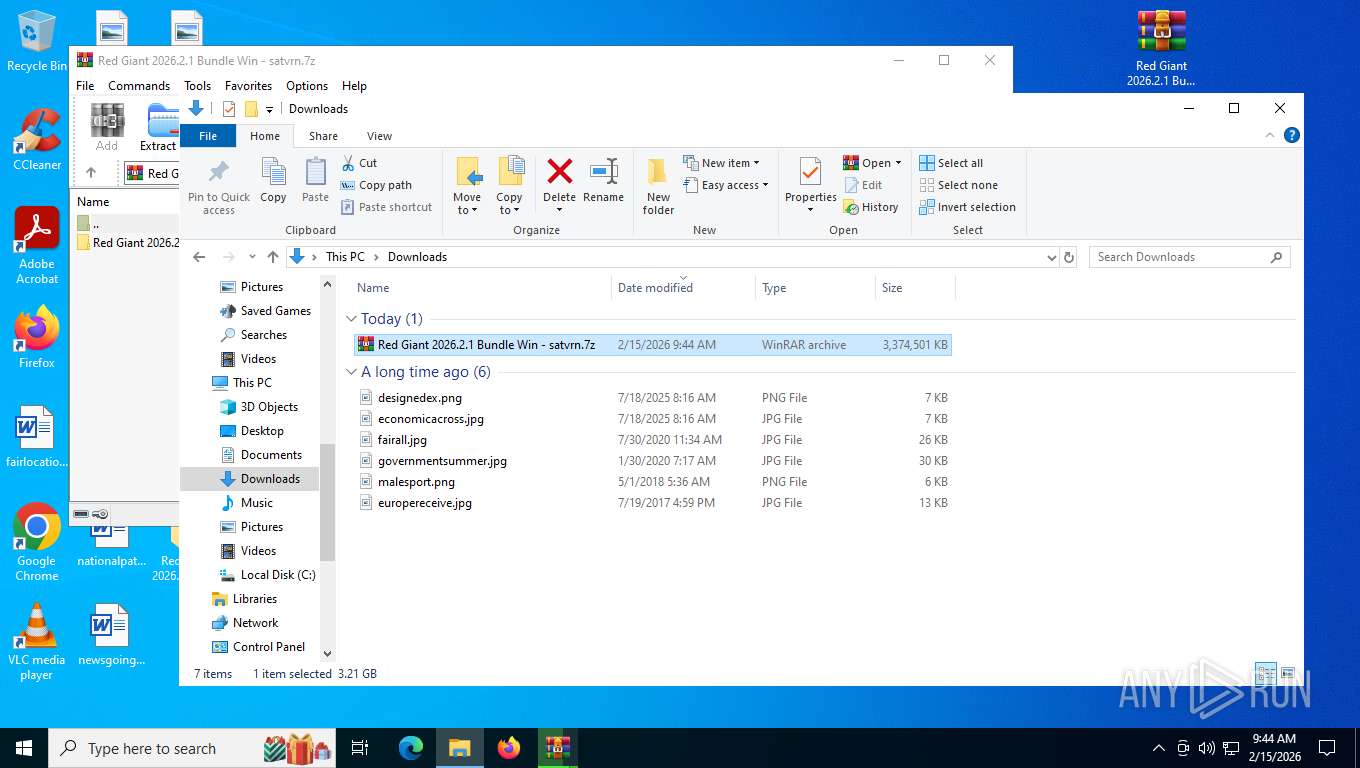
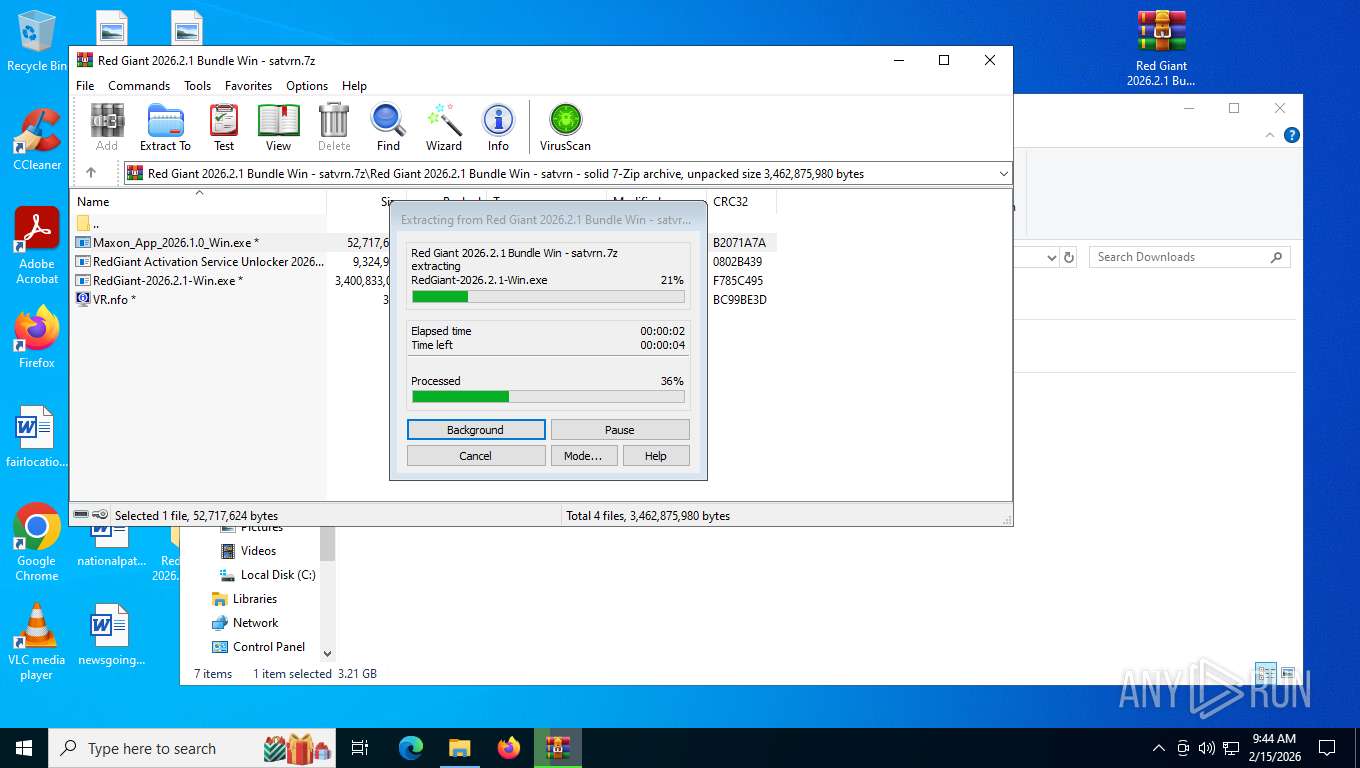
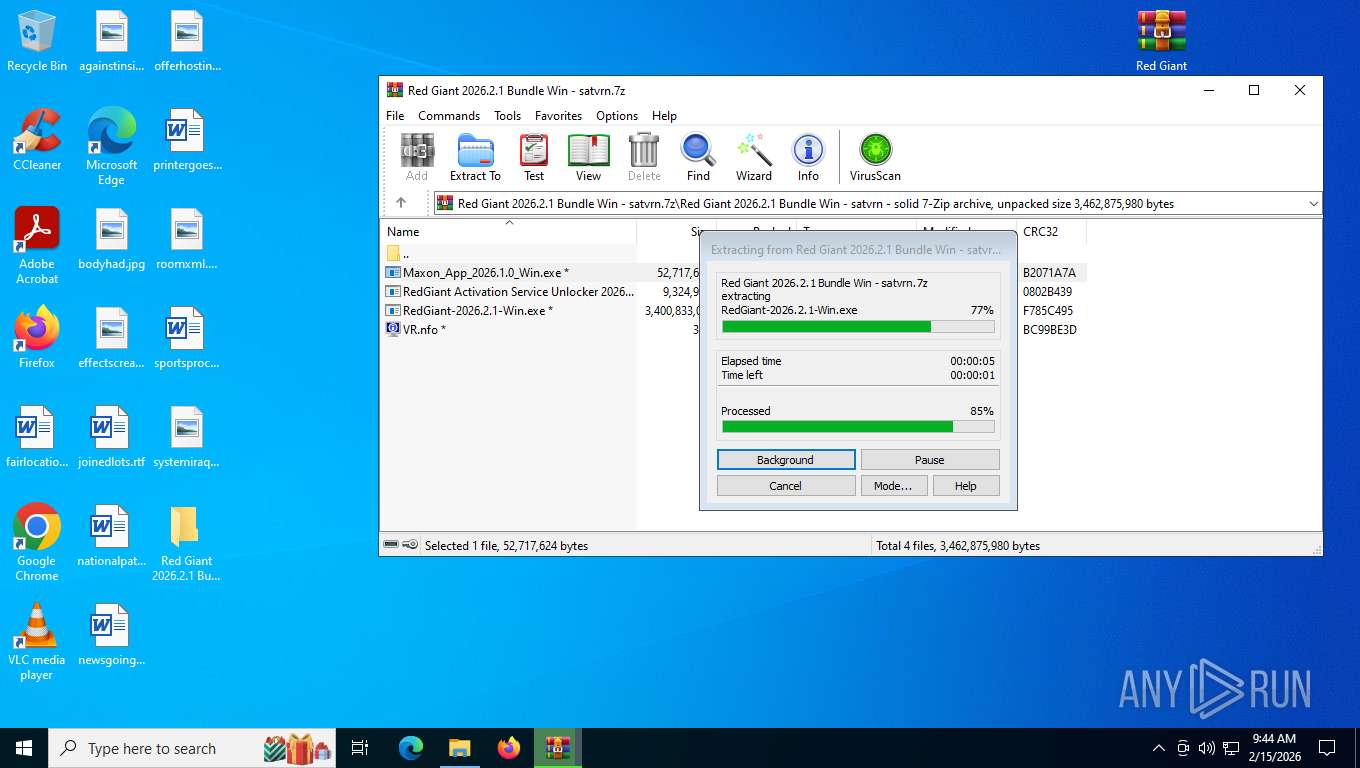
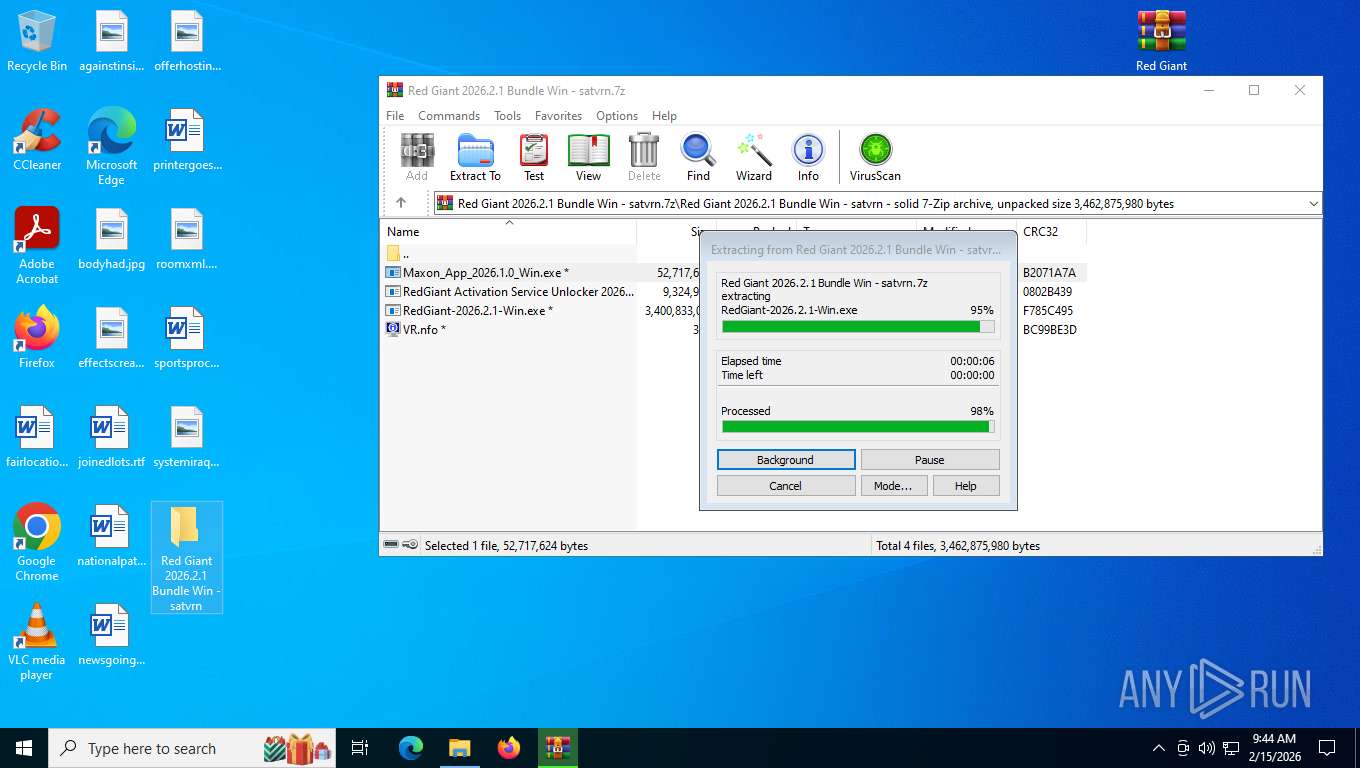
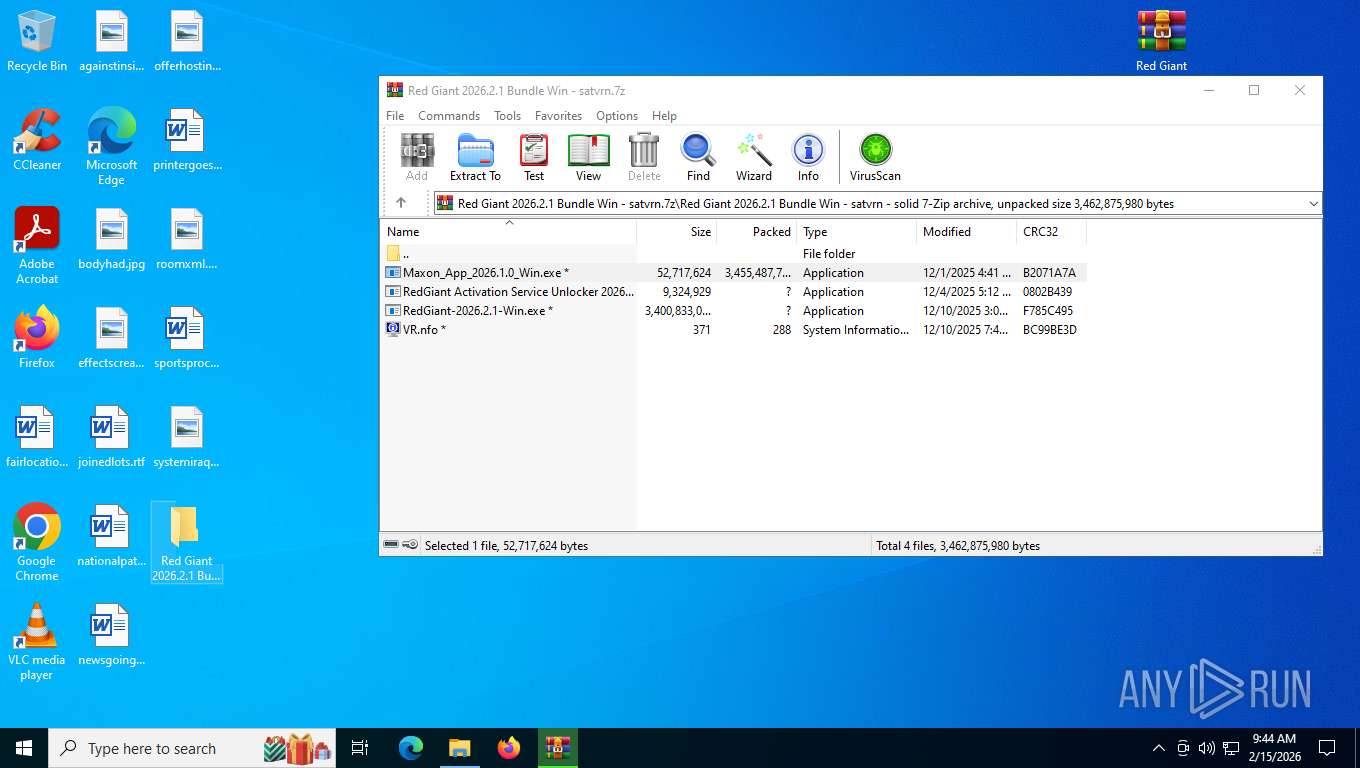
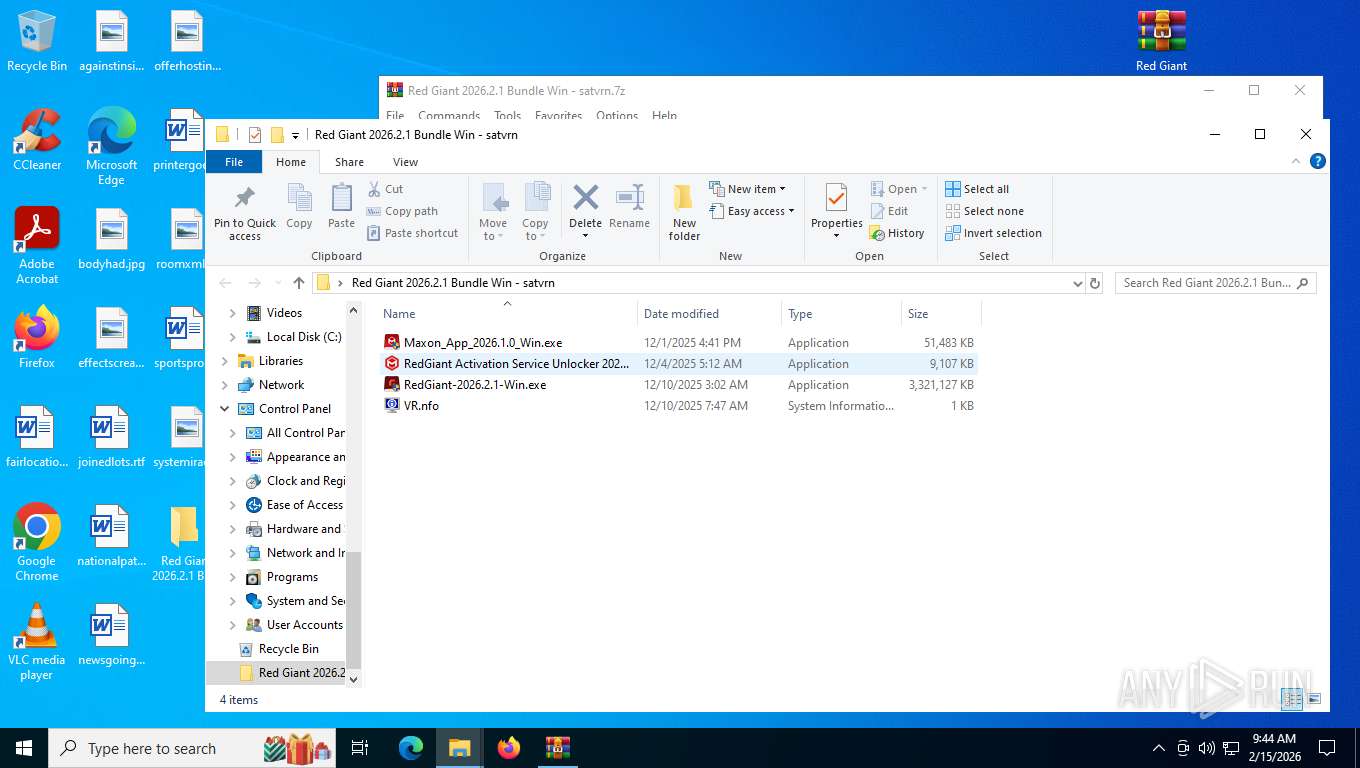
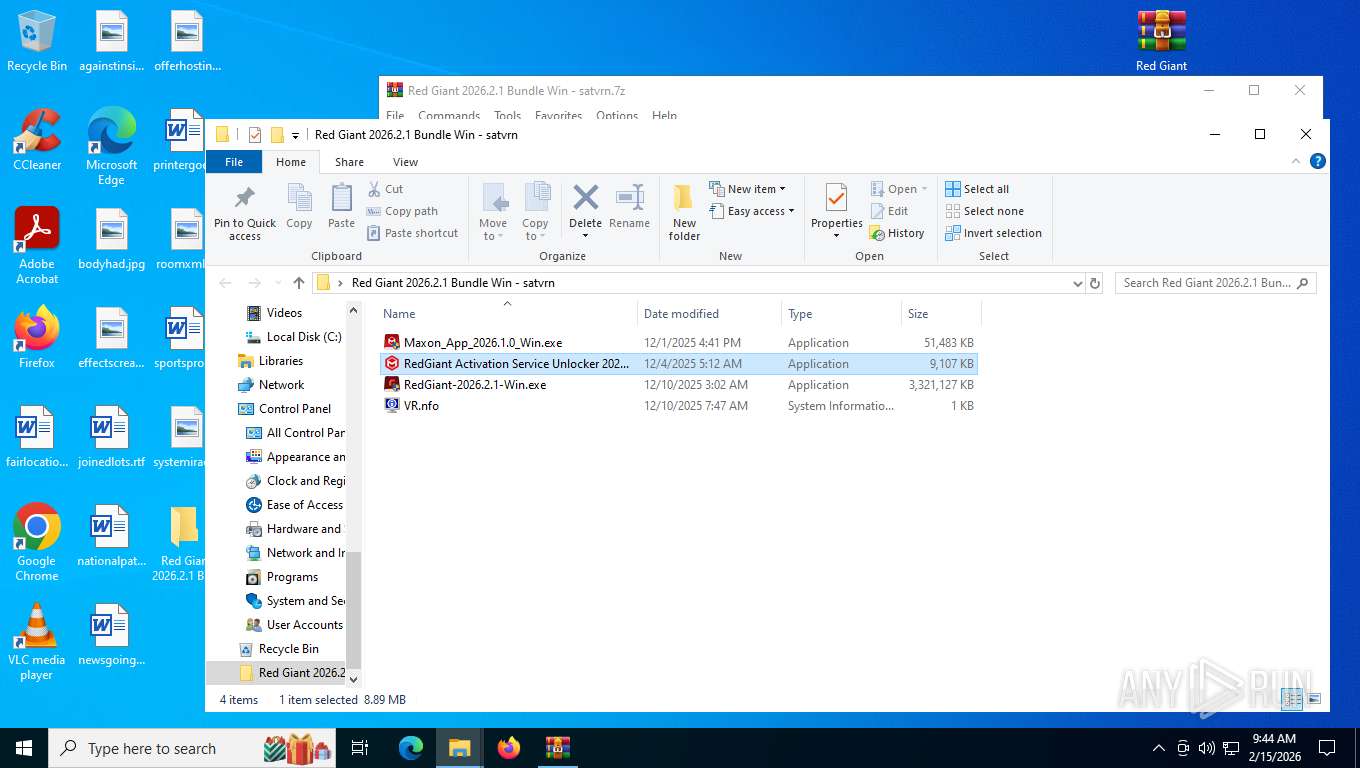
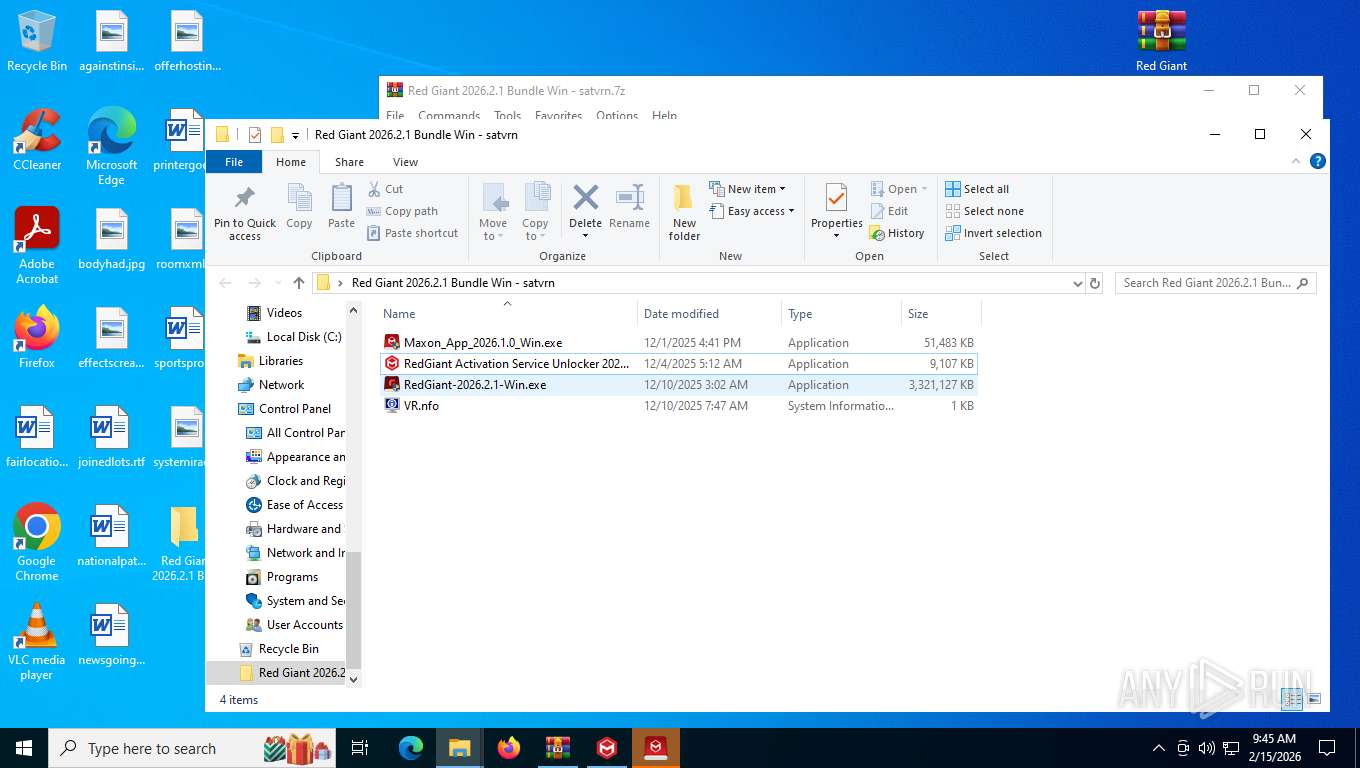
Manual execution by a user
- WinRAR.exe (PID: 8940)
- WinRAR.exe (PID: 7484)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 3208)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7484)
- WinRAR.exe (PID: 8940)
- msiexec.exe (PID: 4708)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8940)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7824)
- VC_RED~1.EXE (PID: 9112)
- VC_redist.x64.exe (PID: 7040)
- MicrosoftEdgeUpdate.exe (PID: 4288)
- explorer.exe (PID: 7680)
Create files in a temporary directory
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 3208)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 6068)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- deep.exe (PID: 6340)
- deep.tmp (PID: 2456)
- VC_RED~1.EXE (PID: 9112)
- VC_redist.x64.exe (PID: 8160)
- VC_redist.x64.exe (PID: 7040)
- MicrosoftEdgeUpdate.exe (PID: 4288)
The sample compiled with english language support
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- VC_redist.x64.22.exe (PID: 8292)
- VC_RED~1.EXE (PID: 9112)
- msiexec.exe (PID: 4708)
- VC_redist.x64.exe (PID: 8160)
- VC_redist.x64.exe (PID: 7040)
- VC_redist.x64.exe (PID: 9076)
- MicrosoftEdgeWebview2Setup.exe (PID: 4296)
- MicrosoftEdgeUpdate.exe (PID: 4288)
Process checks whether UAC notifications are on
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
Reads CPU info
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
Process checks computer location settings
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7824)
- VC_RED~1.EXE (PID: 9112)
- VC_redist.x64.exe (PID: 7040)
- MicrosoftEdgeUpdate.exe (PID: 4288)
Reads the time zone
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
Creates files in the program directory
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7076)
- deep.tmp (PID: 2456)
- VC_redist.x64.exe (PID: 8160)
- MicrosoftEdgeWebview2Setup.exe (PID: 4296)
There is functionality for taking screenshot (YARA)
- Maxon_App_2026.1.0_Win.exe (PID: 3916)
Manages system restore points
- SrTasks.exe (PID: 5612)
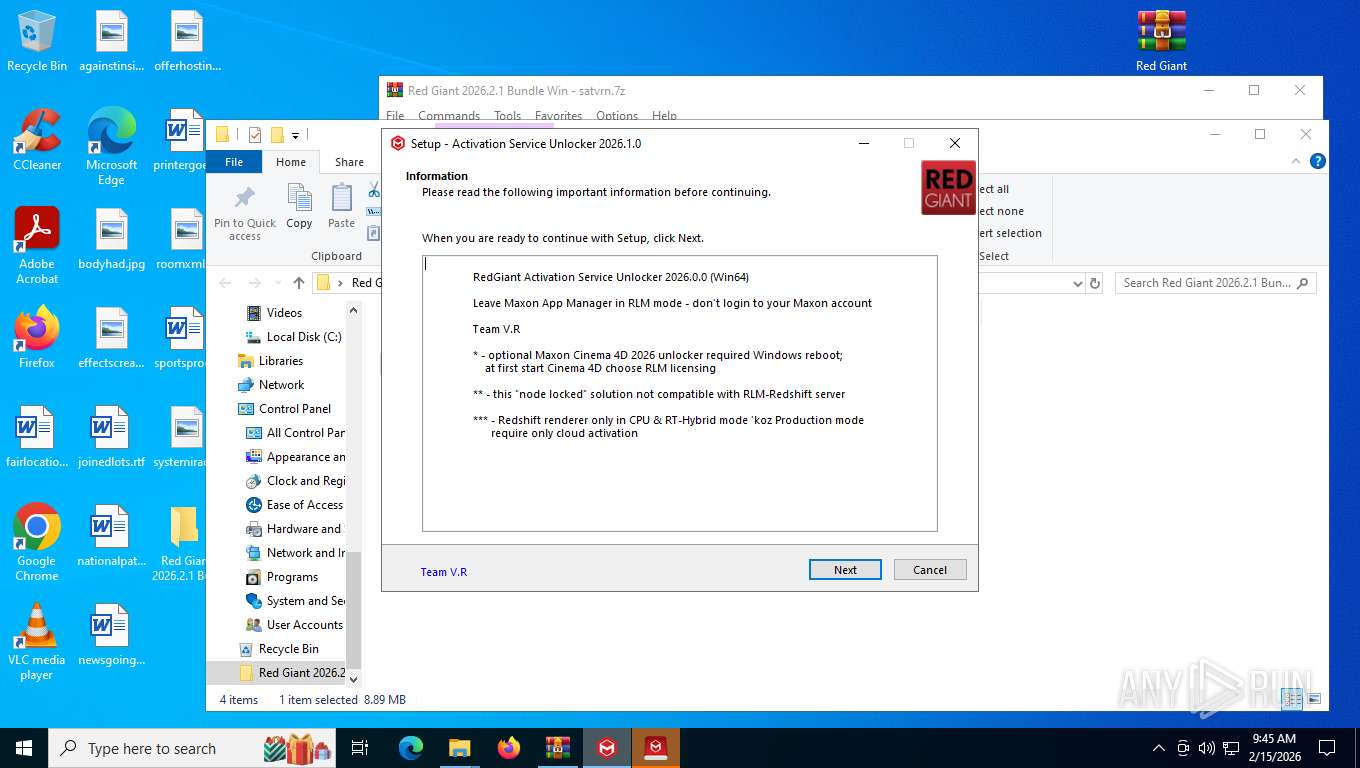
Detects InnoSetup installer (YARA)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 3208)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7824)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 6068)
Compiled with Borland Delphi (YARA)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 3208)
- RedGiant Activation Service Unlocker 2026.1.0.tmp (PID: 7824)
- RedGiant Activation Service Unlocker 2026.1.0.exe (PID: 6068)
Creates a software uninstall entry
- VC_redist.x64.exe (PID: 8160)
- msiexec.exe (PID: 4708)
Reads the machine GUID from the registry
- VC_redist.x64.exe (PID: 8160)
- msiexec.exe (PID: 4708)
Creates files or folders in the user directory
- msiexec.exe (PID: 4708)
- wermgr.exe (PID: 7828)
- Maxon.exe (PID: 5536)
Launching a file from a Registry key
- VC_redist.x64.exe (PID: 8160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
327
Monitored processes
167
Malicious processes
5
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Maxon App v2024.1.1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3200,i,3281868285273423480,16360370403135118959,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7996 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 936 | reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Maxon App v2023.1.1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Maxon App v2023.1.2" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6976,i,3281868285273423480,16360370403135118959,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7240 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6852,i,3281868285273423480,16360370403135118959,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7292 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1424 | reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Maxon App v2023.0.1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Maxon App v1.0.1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | timeout.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 671
Read events
27 613
Write events
671
Delete events
387
Modification events
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
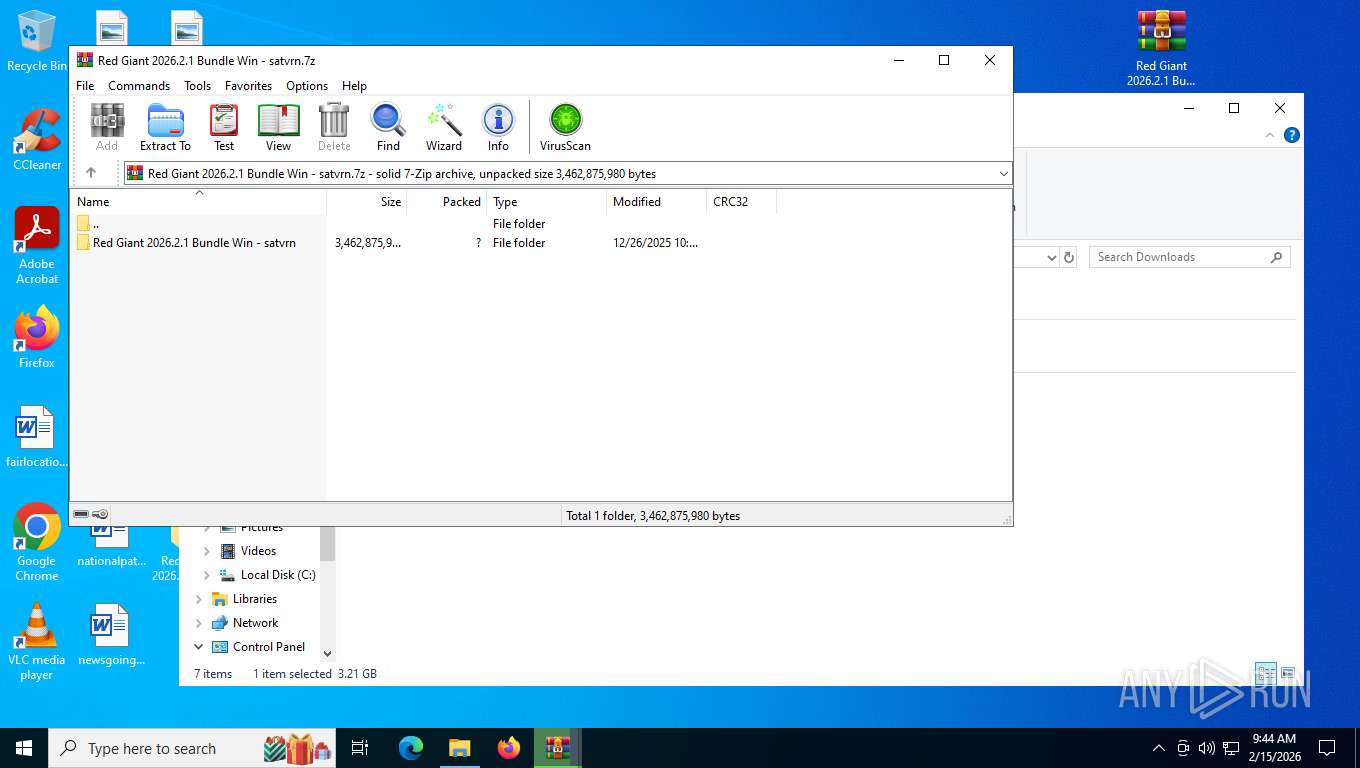
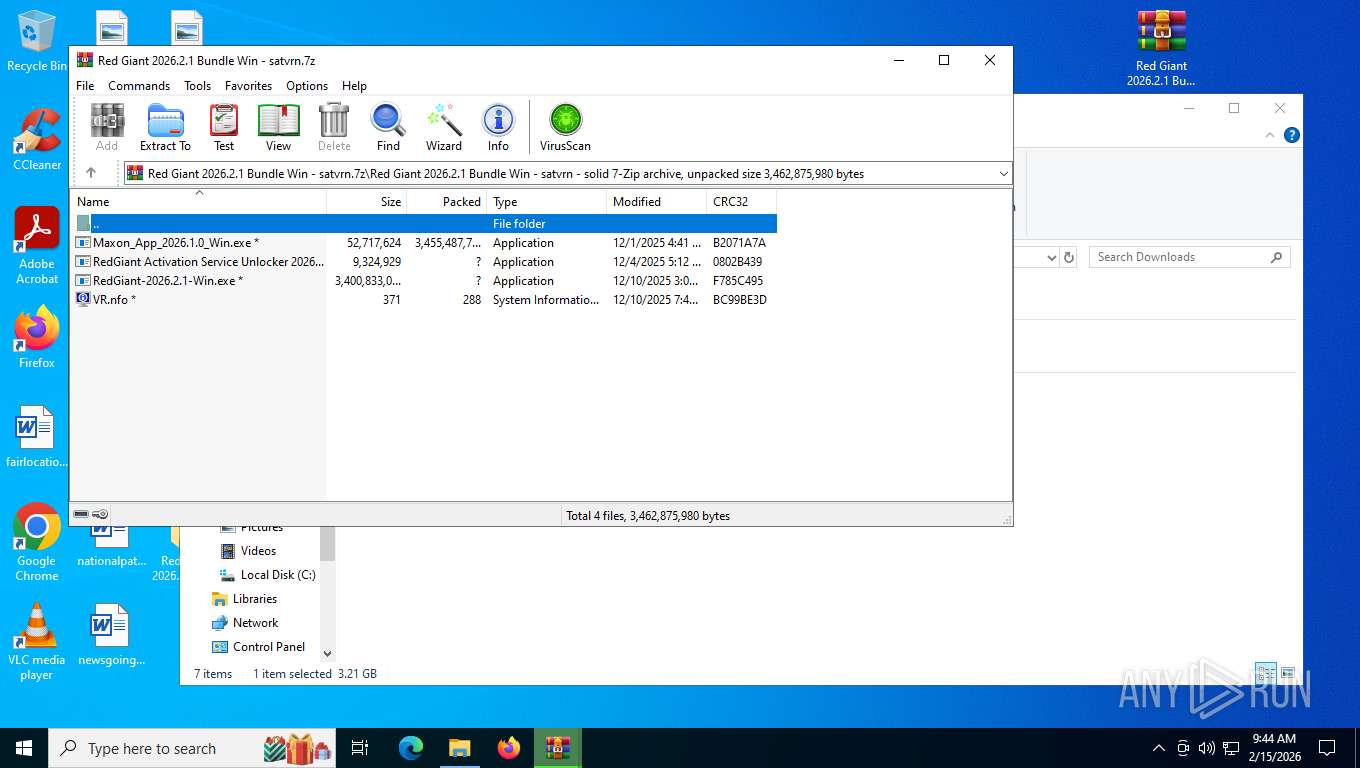
Value: C:\Users\admin\Downloads\Red Giant 2026.2.1 Bundle Win - satvrn.7z | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
314
Suspicious files
128
Text files
550
Unknown types
229
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e4ed9.TMP | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e4ee9.TMP | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e4ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e4ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e4ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
102
DNS requests
81
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
7088 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:A1Wq8y2qeCxhEGWbu9LVbEiPI0ZUVaCyjZGaNOX4kJM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7088 | msedge.exe | GET | 101 | 203.23.179.10:443 | https://pixeldrain.com/api/file_stats | unknown | — | — | unknown |
7088 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1771166463&lafgdate=0 | unknown | text | 4.30 Kb | whitelisted |
7088 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | binary | 295 b | whitelisted |
7088 | msedge.exe | GET | 200 | 203.23.179.10:443 | https://pixeldrain.com/theme.css | unknown | text | 2.25 Kb | unknown |
7088 | msedge.exe | GET | — | 203.23.179.10:443 | https://pixeldrain.com/api/file/MsMuPXWk?download | unknown | — | — | unknown |
7088 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | binary | 25 b | whitelisted |
7088 | msedge.exe | GET | 200 | 203.23.179.10:443 | https://pixeldrain.com/u/MsMuPXWk | unknown | html | 4.08 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3344 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2600 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.207:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.16.241.205:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.205:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
7088 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pixeldrain.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
7088 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|
Maxon.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Maxon.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|