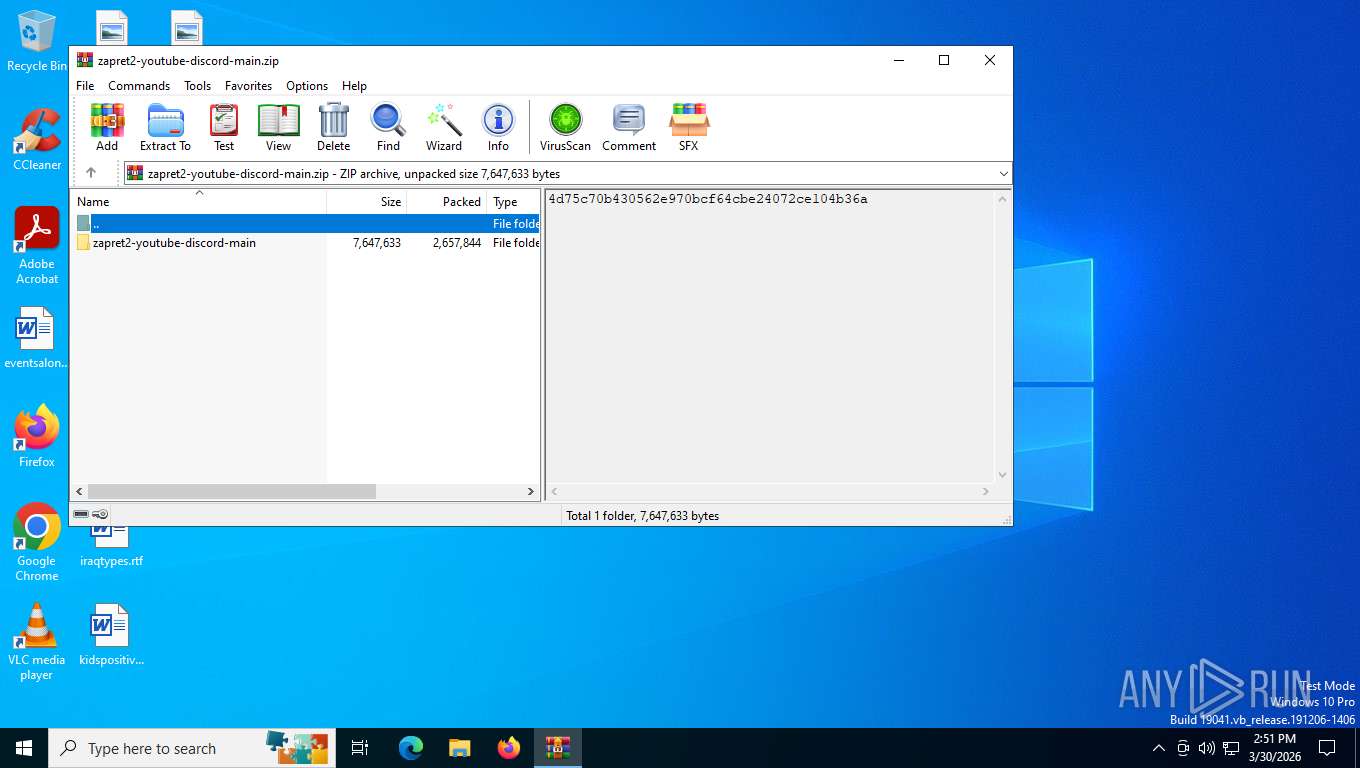
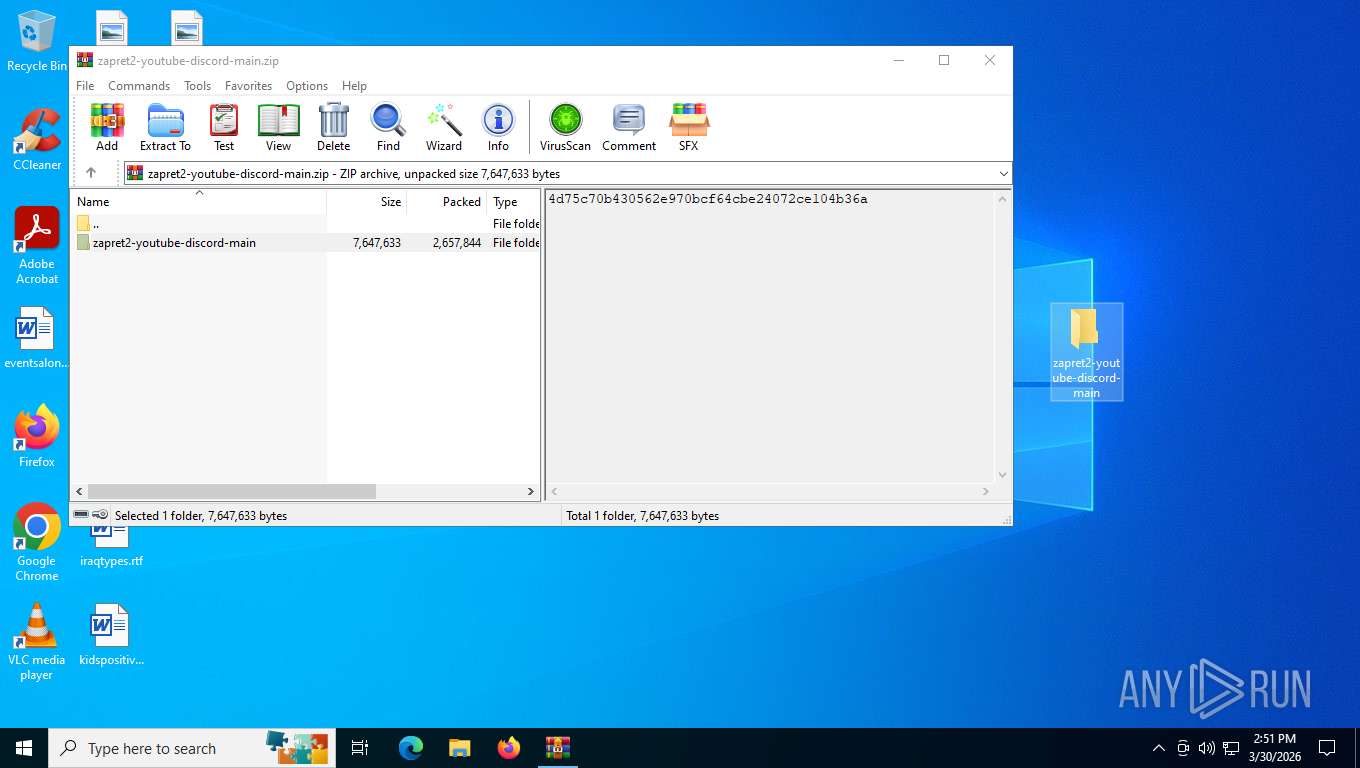
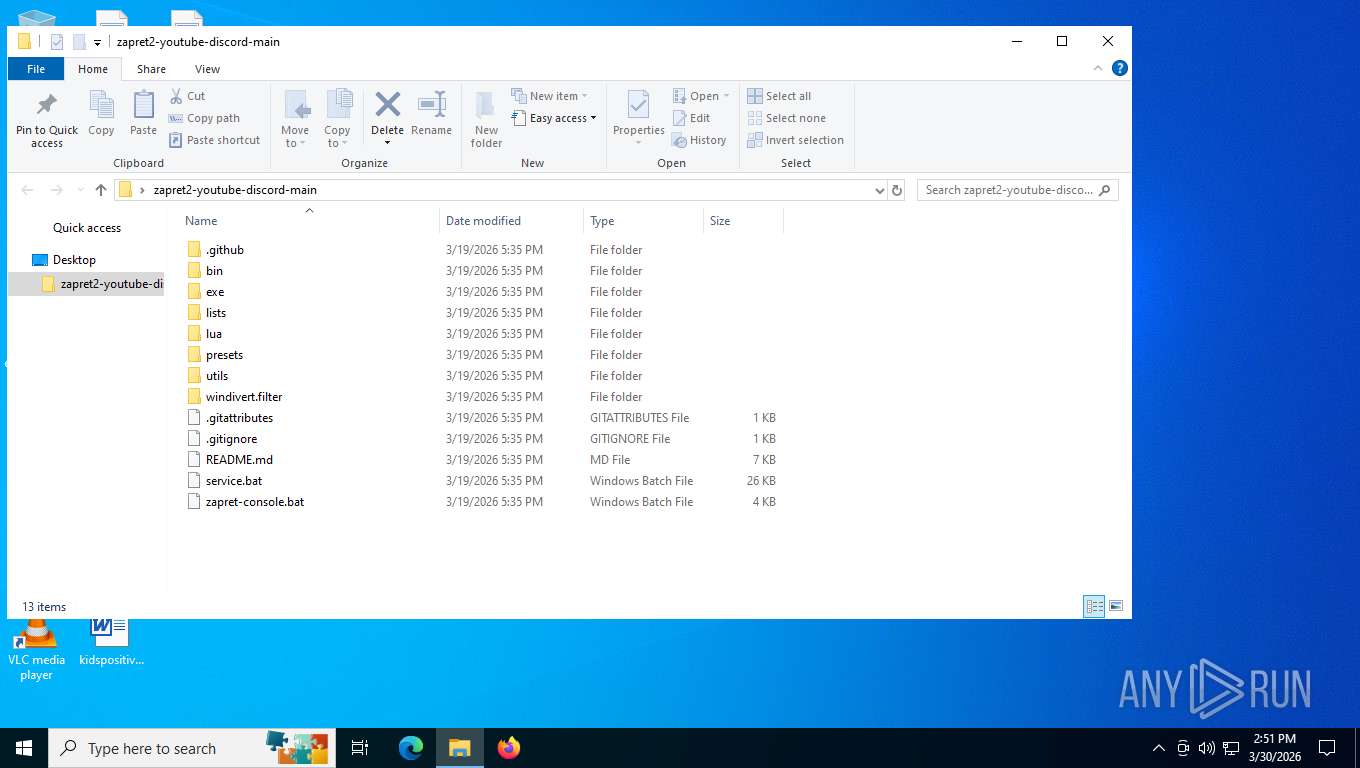
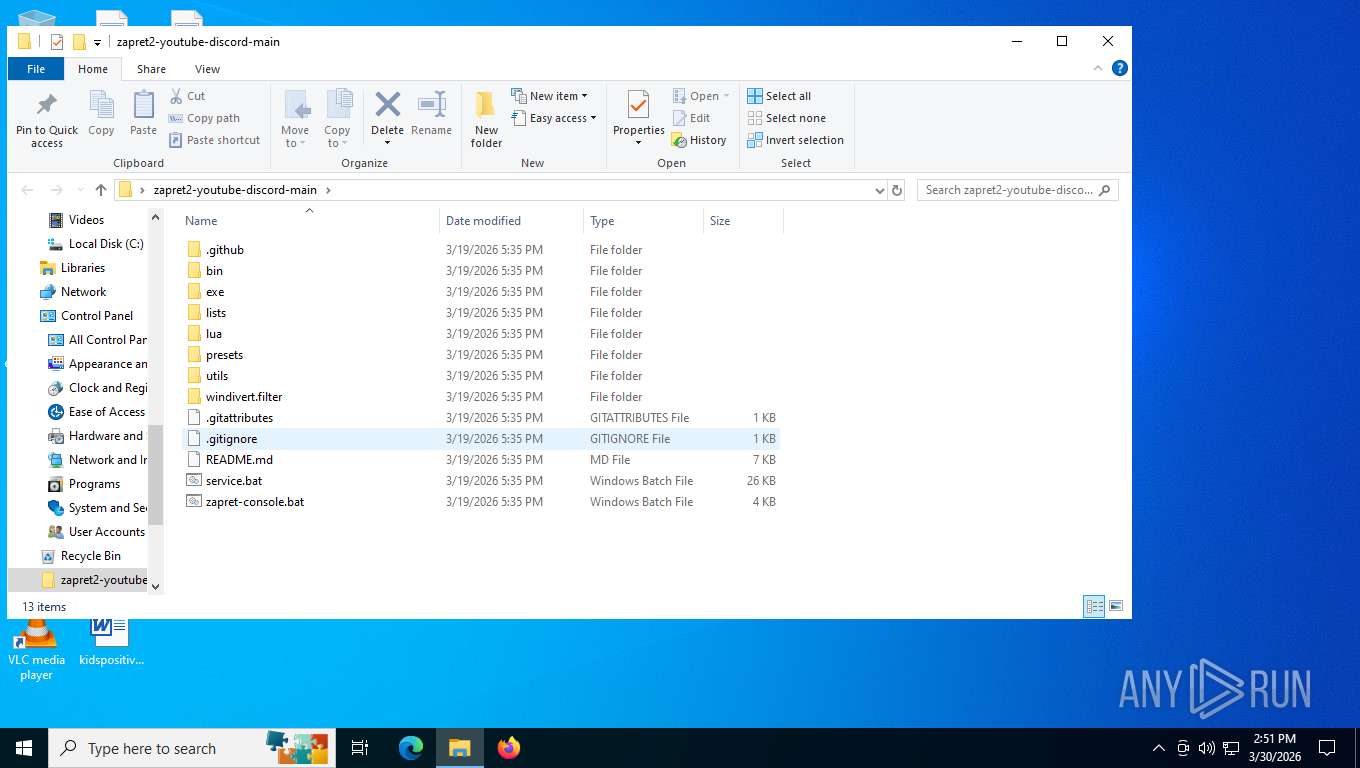
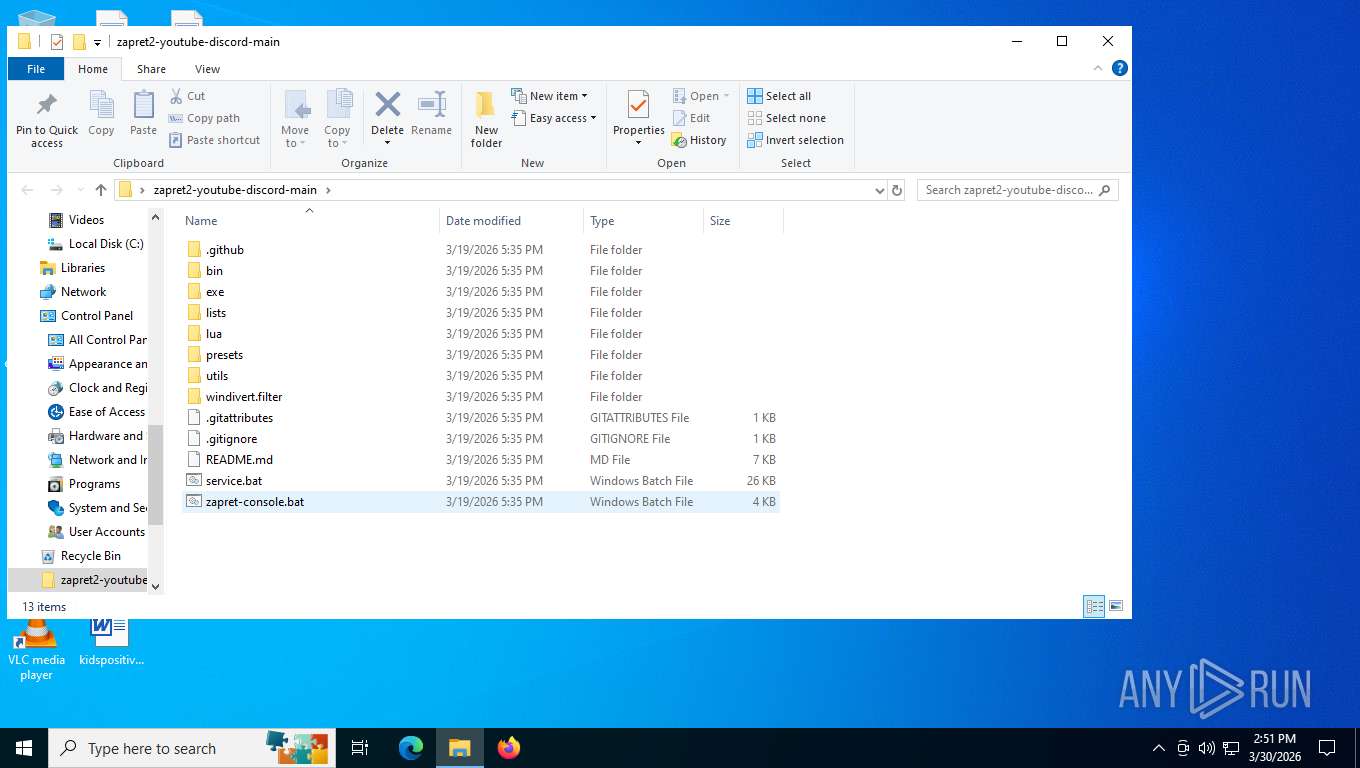
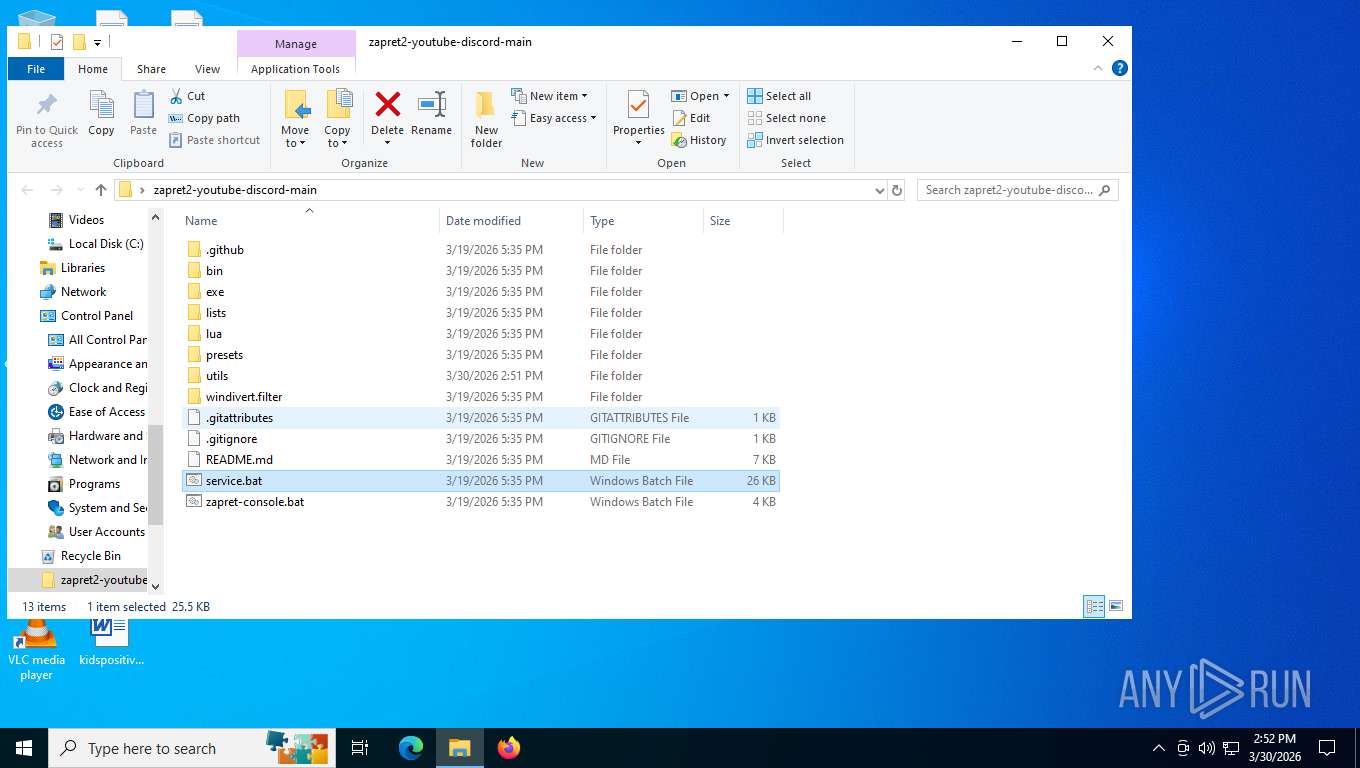
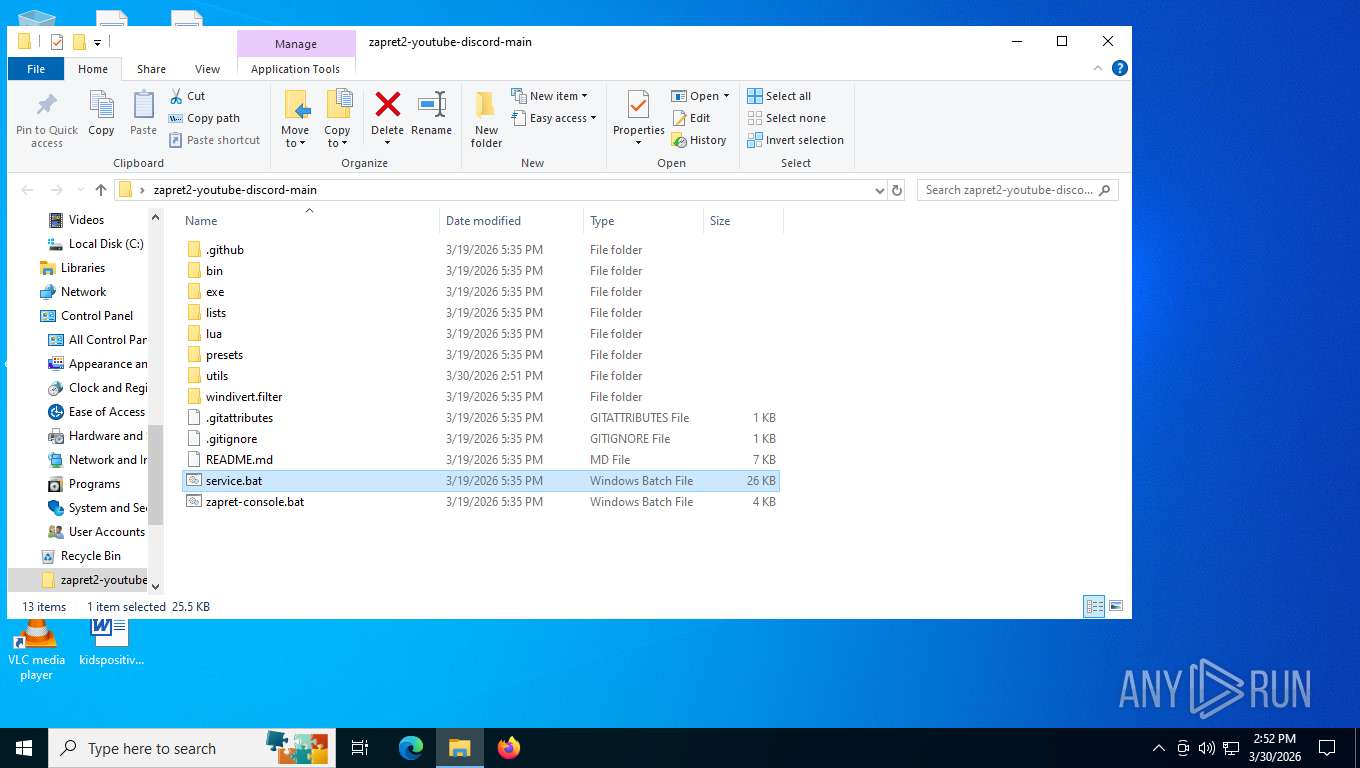
| File name: | zapret2-youtube-discord-main.zip |
| Full analysis: | https://app.any.run/tasks/e6614bd2-f2a5-4601-a653-38c51d50d83d |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2026, 18:51:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 0613A78FF21D98EB6197D4CD7BC5075C |
| SHA1: | 0374DB214CEDA8A4C09EB86CA382386DF37E0752 |
| SHA256: | E26A14C908428D704CBDBE54D855152BEB6F1DFB2C45523075EBEFF3663D49E6 |
| SSDEEP: | 98304:J65mQgQH8+23tP3agiK6TCalIwpz5IZV4/Ns996TnyeYf03DECwlwHhKsDKN+n/R:Pe/r |
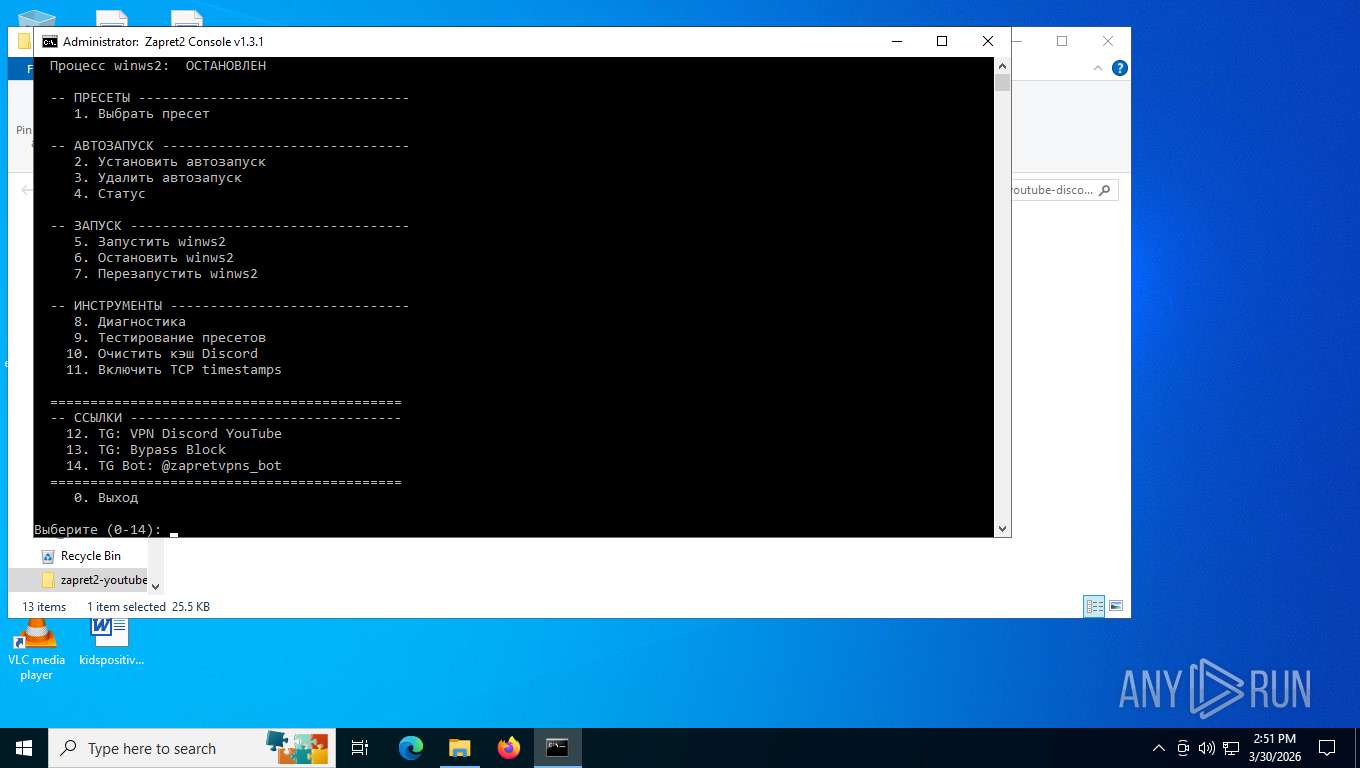
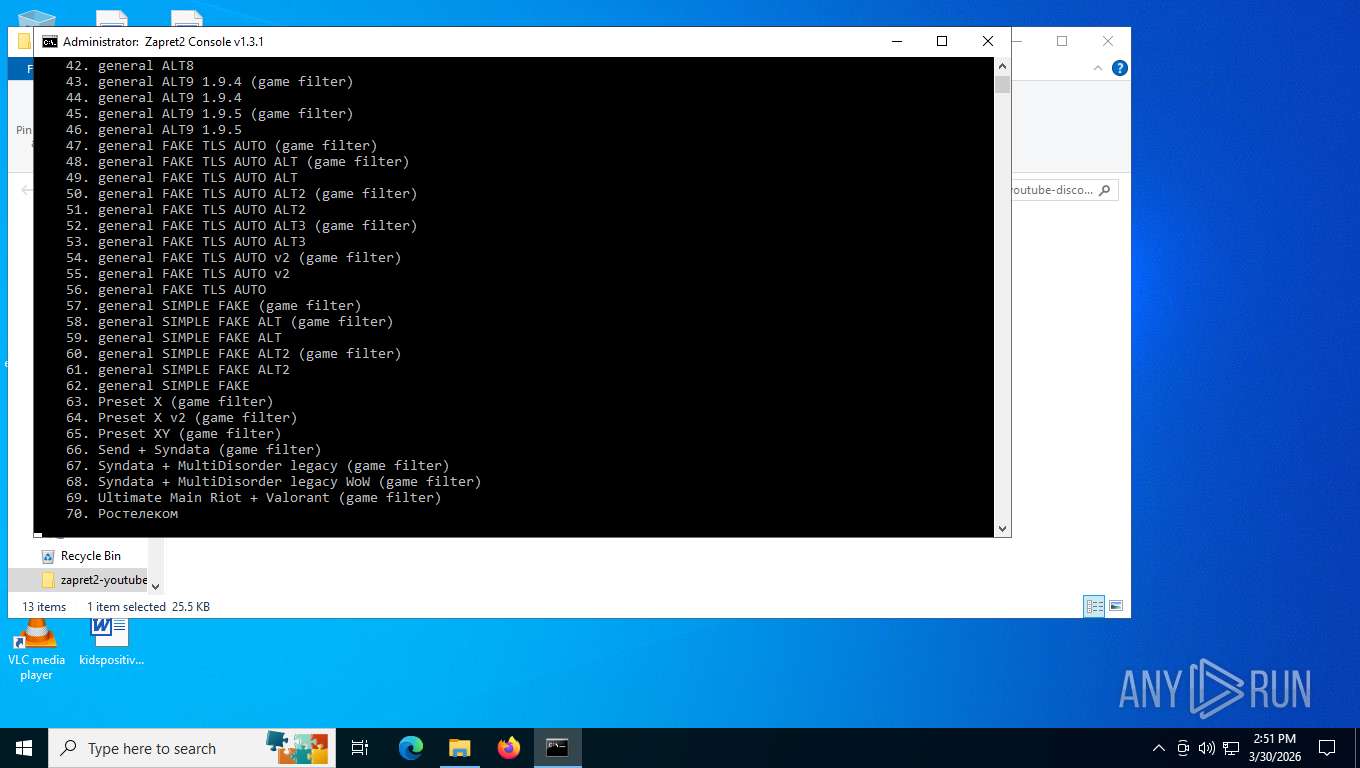
MALICIOUS
Detects Cygwin installation
- WinRAR.exe (PID: 2676)
Malicious driver has been detected
- WinRAR.exe (PID: 2676)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 2676)
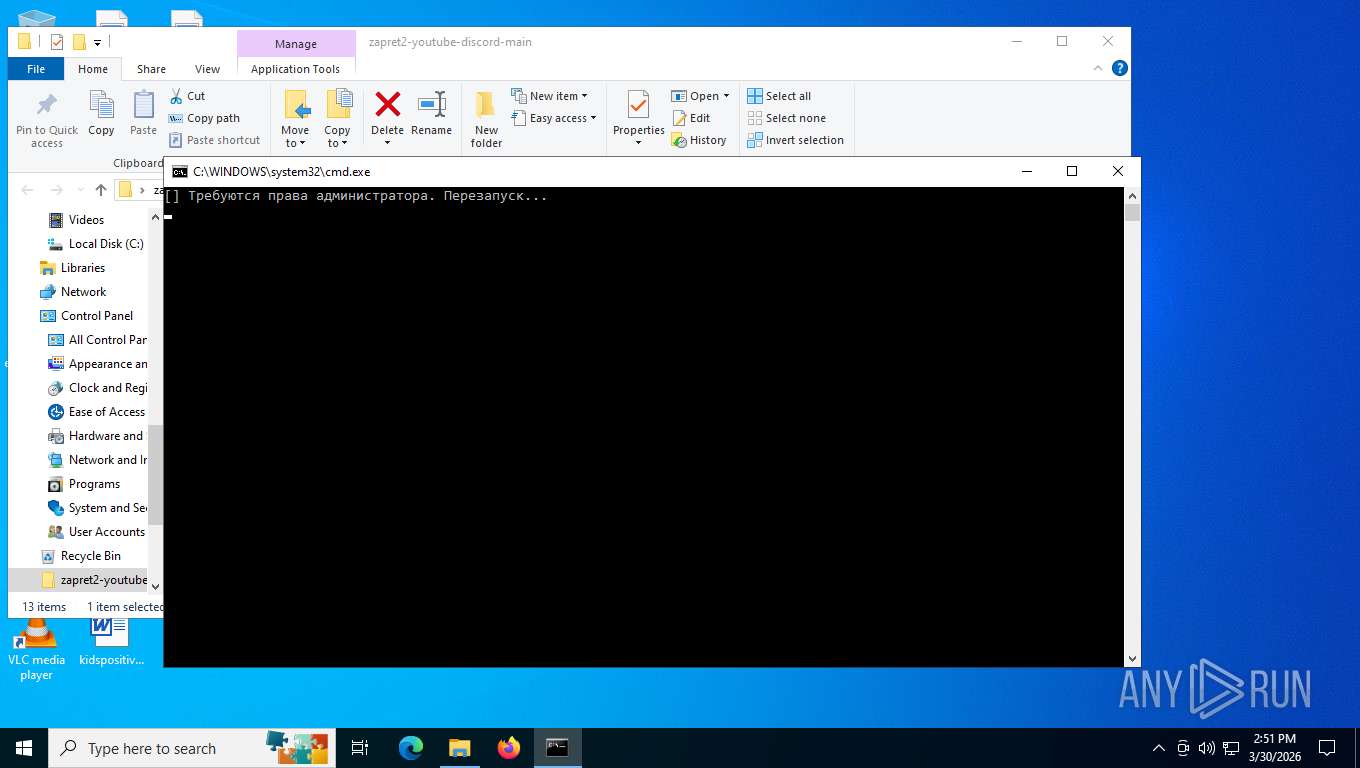
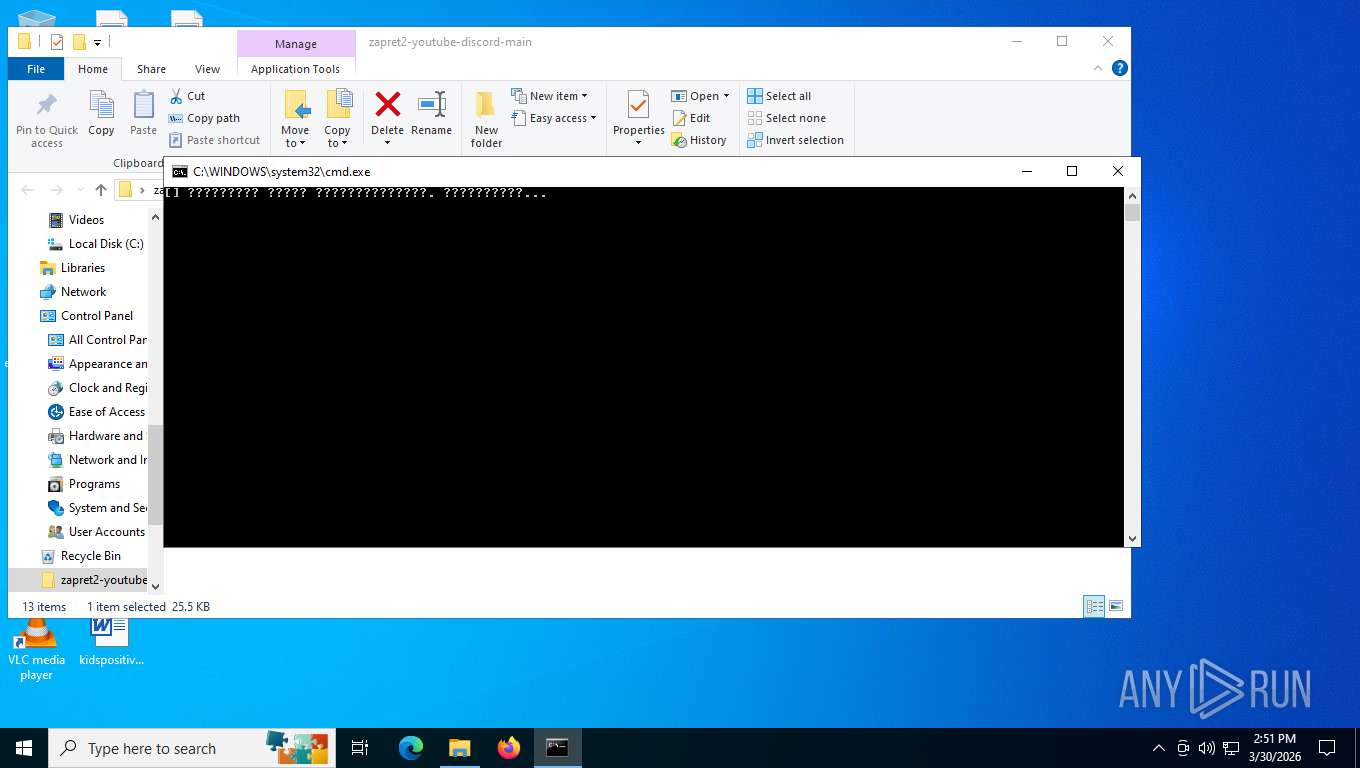
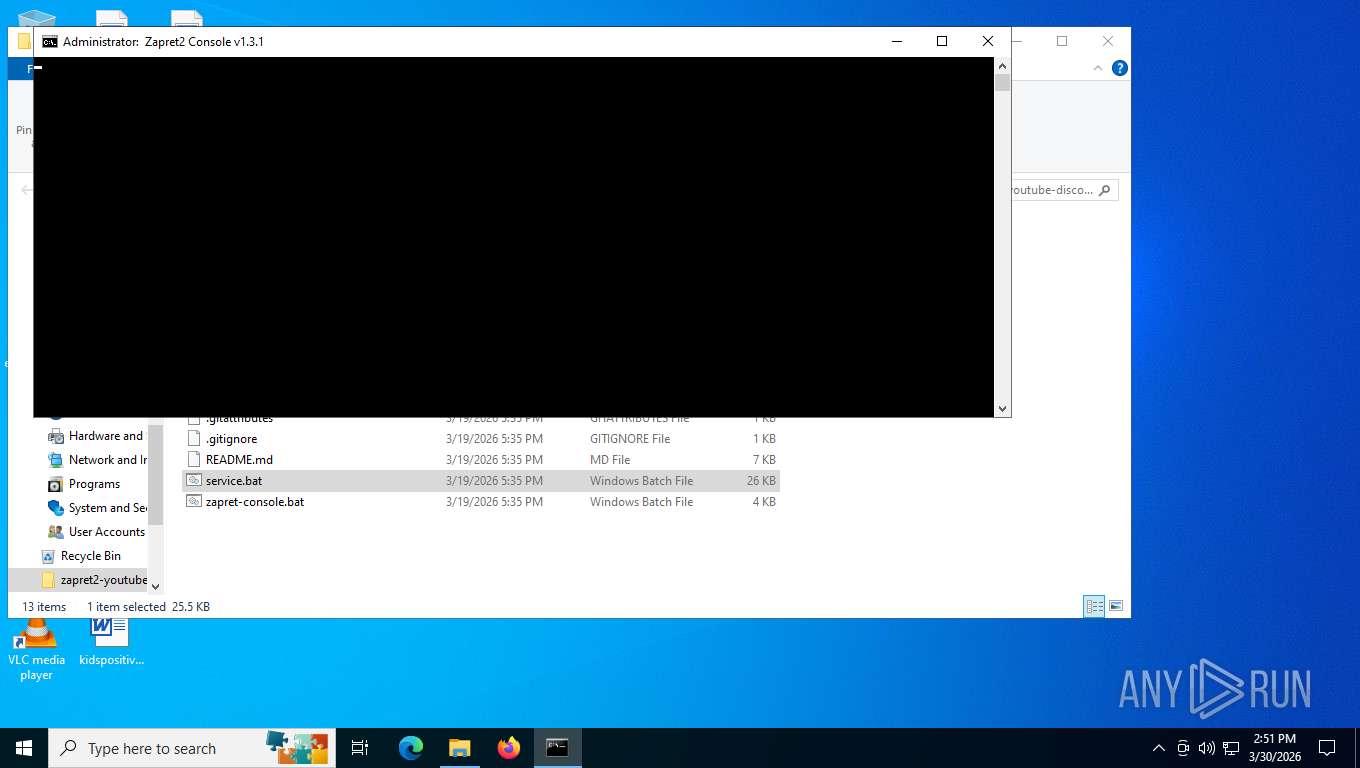
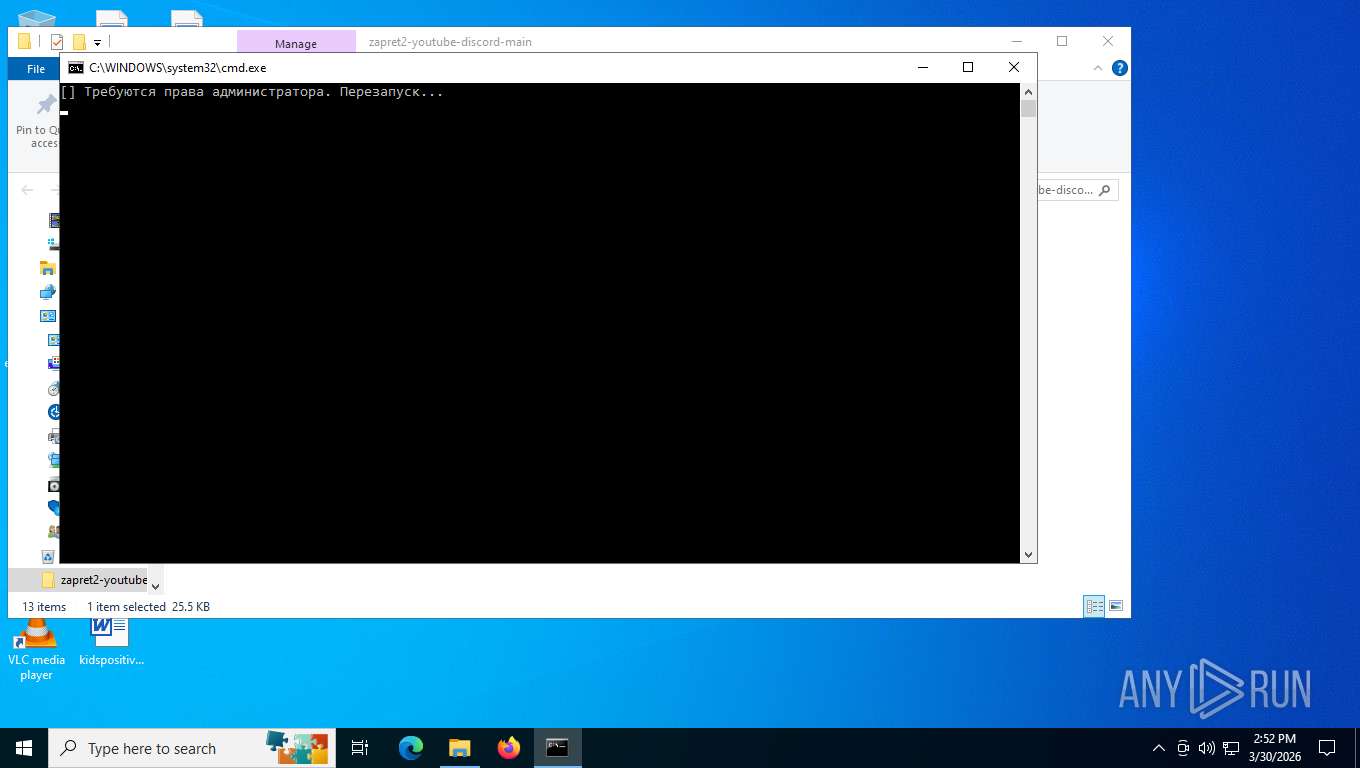
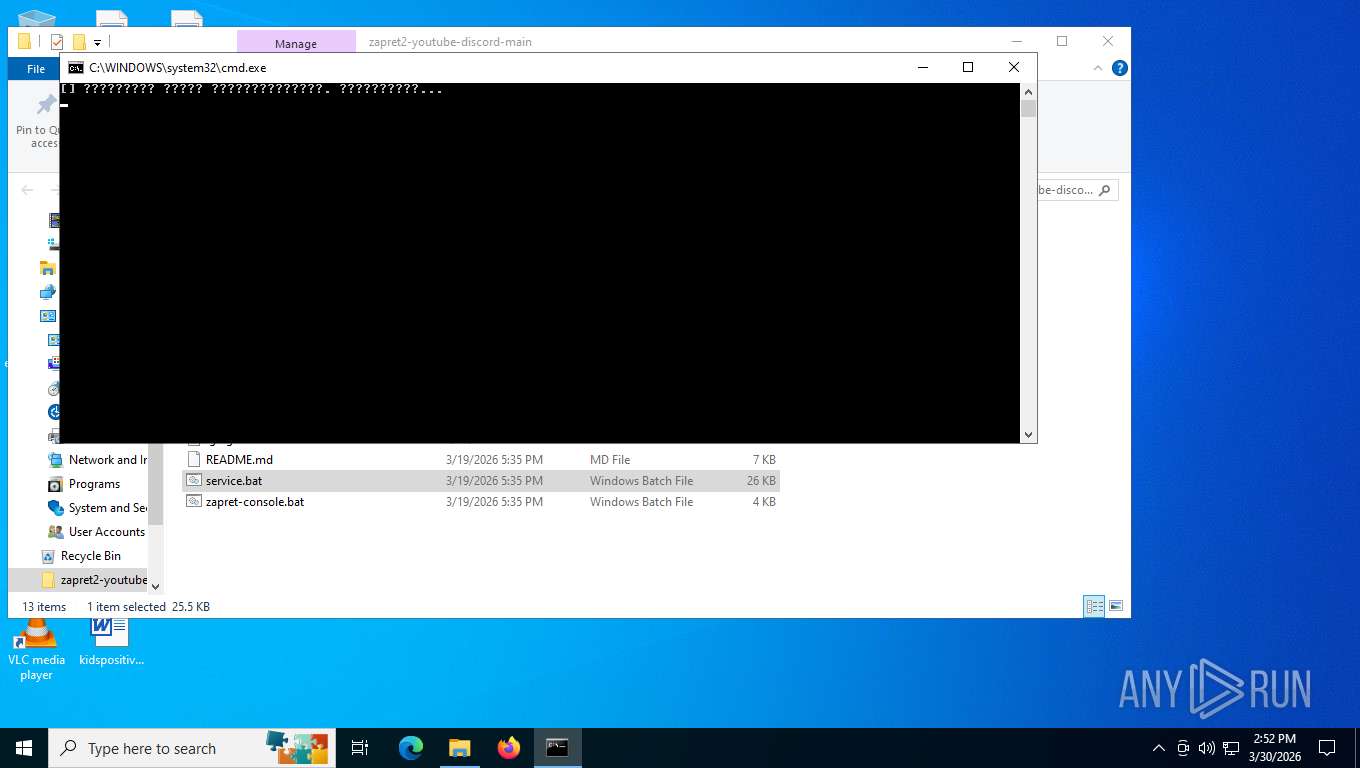
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6844)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 5800)
Starts application with an unusual extension
- cmd.exe (PID: 6844)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 5800)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 5408)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 4944)
- net.exe (PID: 2940)
- net.exe (PID: 2016)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 5800)
- net.exe (PID: 4336)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6844)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 5800)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6844)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 5800)
Executing commands from a ".bat" file
- powershell.exe (PID: 7936)
- powershell.exe (PID: 144)
Starts process via Powershell
- powershell.exe (PID: 7936)
- powershell.exe (PID: 144)
Lists all scheduled tasks
- schtasks.exe (PID: 7664)
- schtasks.exe (PID: 7624)
- schtasks.exe (PID: 4488)
Get information on the list of running processes
- cmd.exe (PID: 4944)
- cmd.exe (PID: 5800)
Windows service management via SC.EXE
- sc.exe (PID: 8044)
- sc.exe (PID: 7260)
- sc.exe (PID: 6272)
- sc.exe (PID: 8076)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 5800)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5800)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 2676)
Manual execution by a user
- cmd.exe (PID: 6844)
- cmd.exe (PID: 4624)
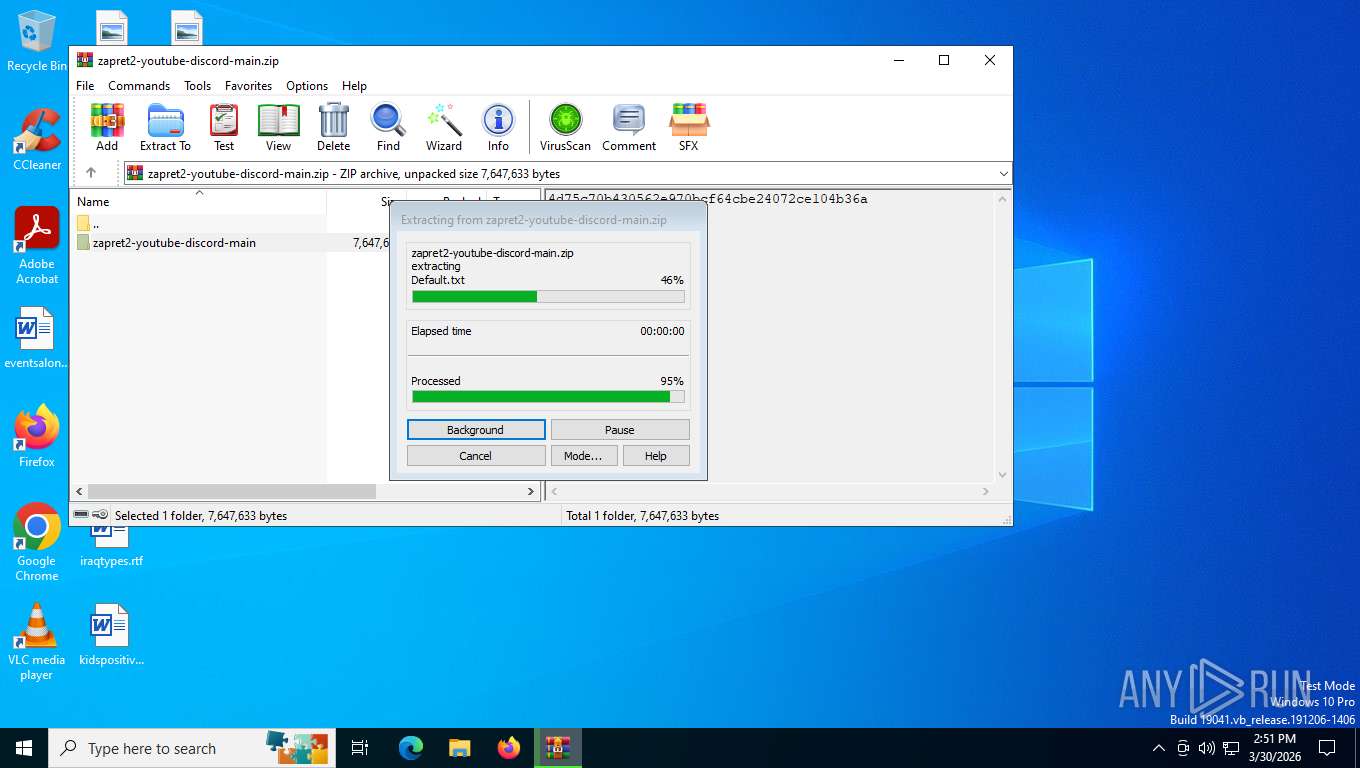
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2676)
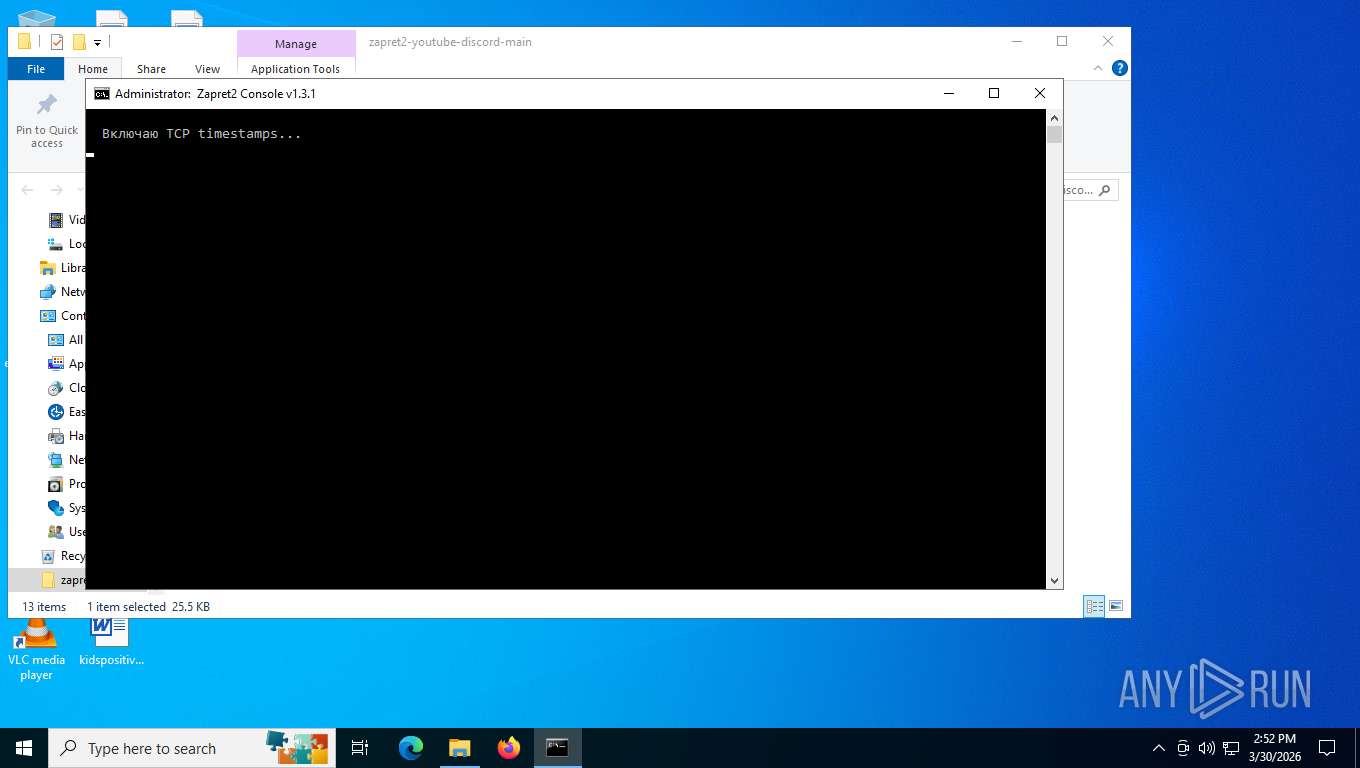
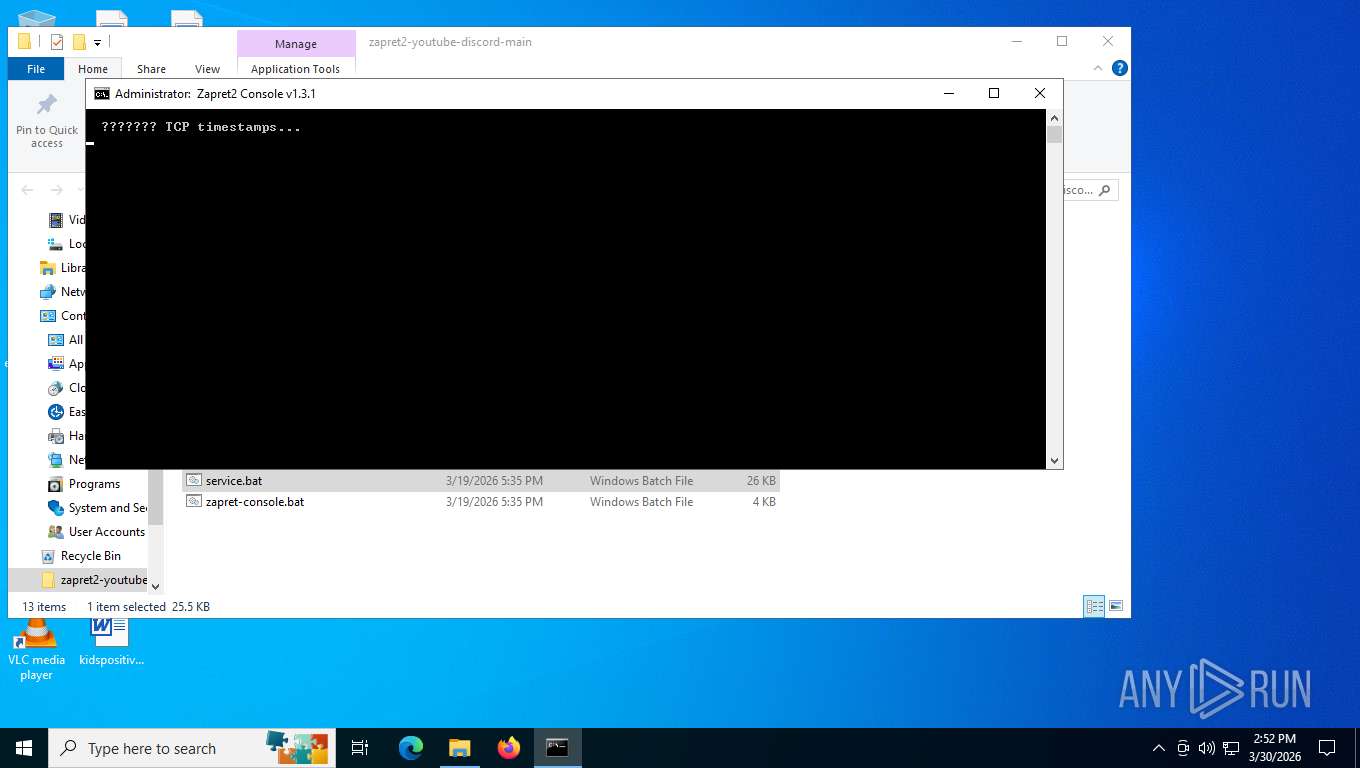
Checks supported languages
- chcp.com (PID: 7588)
- chcp.com (PID: 7456)
- chcp.com (PID: 4308)
- chcp.com (PID: 7840)
- winws2.exe (PID: 2828)
Changes the display of characters in the console
- cmd.exe (PID: 6844)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 5800)
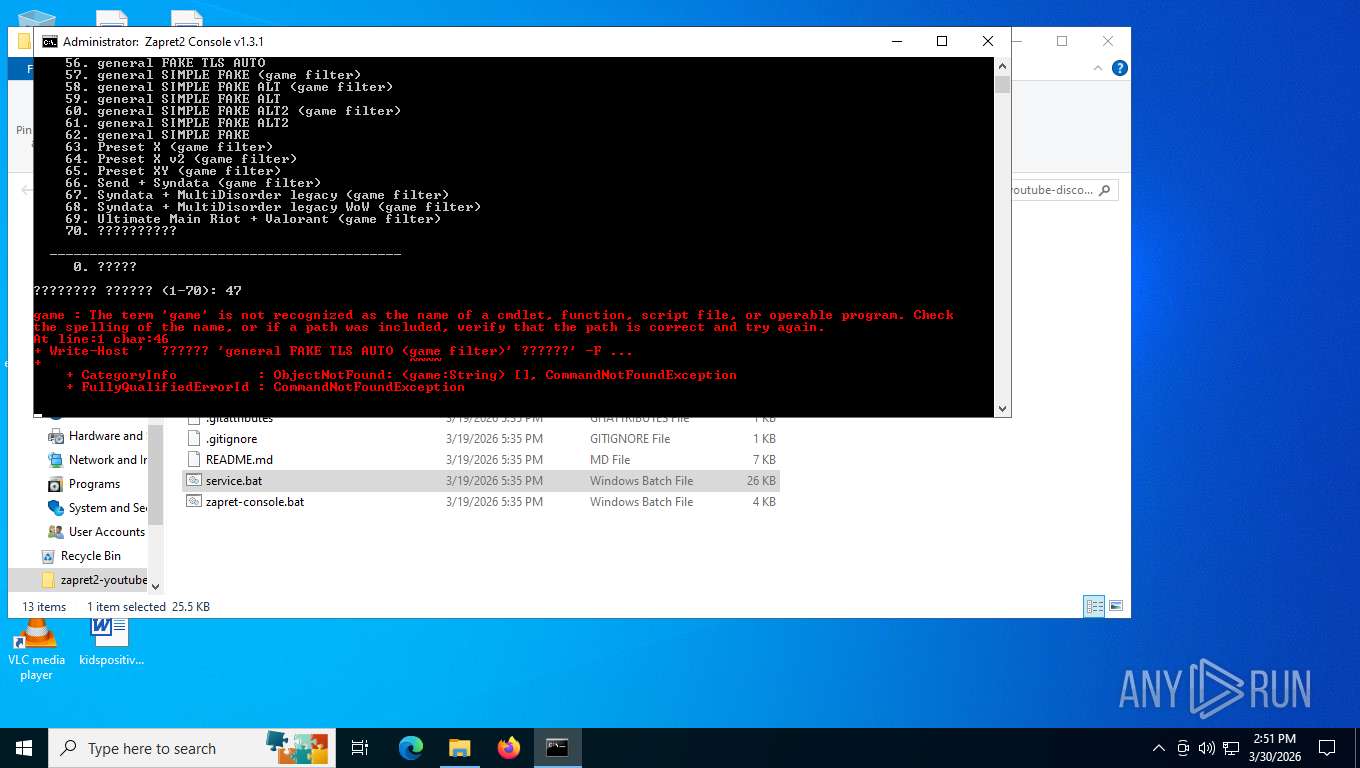
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7960)
Disables trace logs
- netsh.exe (PID: 5748)
- netsh.exe (PID: 3448)
Reads the computer name
- winws2.exe (PID: 2828)
The sample was built using Cygwin
- winws2.exe (PID: 2828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2026:03:19 14:35:52 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | zapret2-youtube-discord-main/ |
Total processes
179
Monitored processes
50
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -Command "Start-Process 'C:\Users\admin\Desktop\zapret2-youtube-discord-main\service.bat' -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1724 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2016 | C:\WINDOWS\System32\net.exe session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | C:\WINDOWS\System32\find.exe /I "winws2.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | C:\WINDOWS\System32\timeout.exe /t 2 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2676 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\zapret2-youtube-discord-main.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
28 067
Read events
28 041
Write events
26
Delete events
0
Modification events
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret2-youtube-discord-main.zip | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
5
Suspicious files
77
Text files
205
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\.github\workflows\release.yml | binary | |
MD5:3249B5A4A563D36F9C8F7A5C7DA98224 | SHA256:5C7DD9FCBF7802C603E54E7BB7CB80DBA9F9A20BAC19F3F33D31870E50DDB2A0 | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\.gitattributes | binary | |
MD5:0AAD7D592B298D3580CAD853FC6EC703 | SHA256:162FC80B99B322E48E581CCA8938810A3FCD35EDFAF619B2C8A51E8BE912ABA7 | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\bin\dtls_clienthello_w3_org.bin | binary | |
MD5:E091D8E448CB76D8842CA22643E12B82 | SHA256:5BACD8CB6BD451F2374E55BC066B632E3C88FB852E3A44F19E6246C04D127BE5 | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\bin\fake_http_postimg.bin | text | |
MD5:A81DCD91626FE25E2909FC126A22F1A6 | SHA256:82799540AE6A10B7ACB2E8321B409BFA06A38EBB7B72CF7B9BA092D759FB1666 | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\README.md | text | |
MD5:4E7B04E9F5309D8C33A140ACA772FB28 | SHA256:88B6BF7818C6E6A942C78AFCA6E7AA6D8B0A9307CA06CCE23BA2F2C6BF31F4B3 | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\.gitignore | text | |
MD5:F96A89DCC468B9DEA0F31A484E97590F | SHA256:99A1DD4BBEA578611E3202274BD59432FAD38DF5BE6E1138200C5712223628FF | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\bin\1.bin | binary | |
MD5:9FACE1ABDAF5B0FCA2C7B49068C9C6F0 | SHA256:E4D572E6BF6DE04C648744CB7271644CB40FD6C79D718E911716D734CBB53841 | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\bin\2.bin | binary | |
MD5:79BE17B482D8EE1E96EEC9E16E7A506D | SHA256:F86D488593A65132C10E7E5B5E02F32FF8E0862988B30BEBC6A671C5380F3976 | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\bin\3.bin | binary | |
MD5:5299F24CF3EF34818300E204CF40C203 | SHA256:D6D63C53BC0E1D97E913A43FC4DB34F6558BB807228BF6100E3B6863F0720404 | |||
| 2676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2676.31762\zapret2-youtube-discord-main\bin\dht_get_peers.bin | binary | |
MD5:D755F09EA9D03F842E1AD2693EBC4BBE | SHA256:B57F6584EB58689CCF81702B44103FA53EA31A5DBA00BE9C95B4059BAD602E77 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
25
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6076 | svchost.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
7488 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
7488 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
7488 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
7488 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 313 b | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.160.22:443 | https://login.live.com/RST2.srf | US | binary | 1.24 Kb | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.22:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | — | 203 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.22:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | — | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6076 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.48.23.173:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.140:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6076 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |