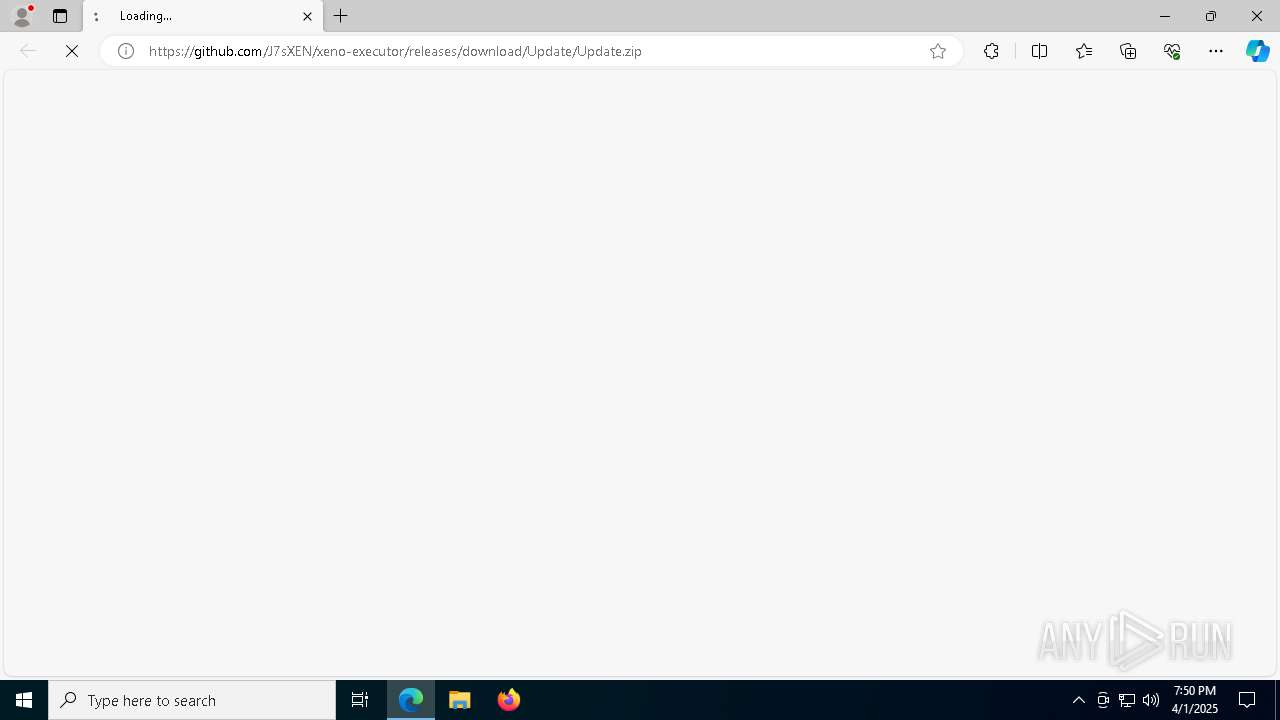
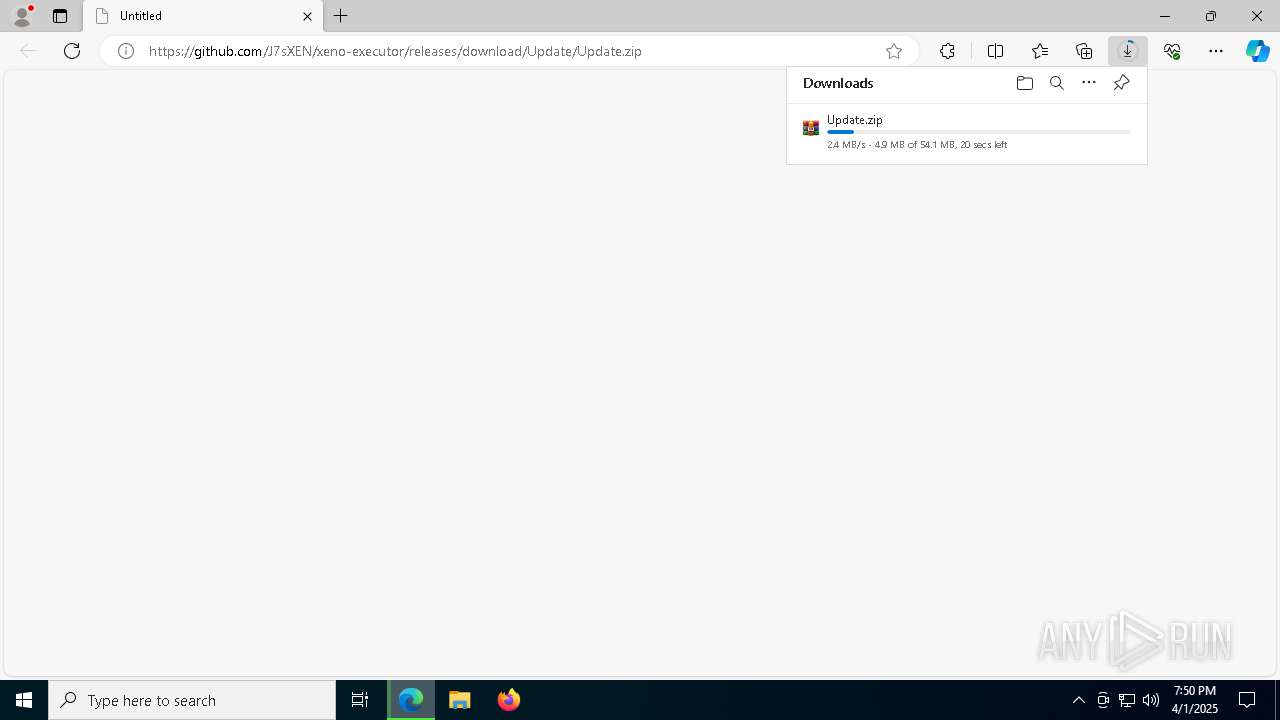
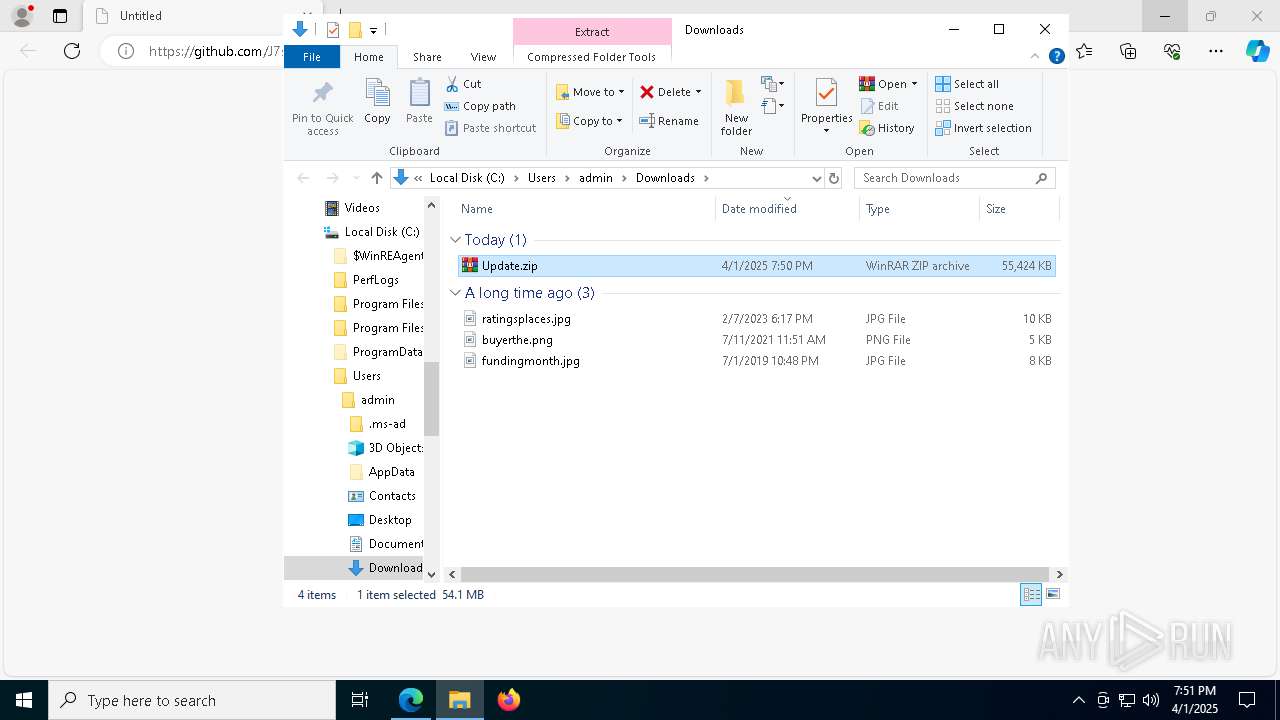
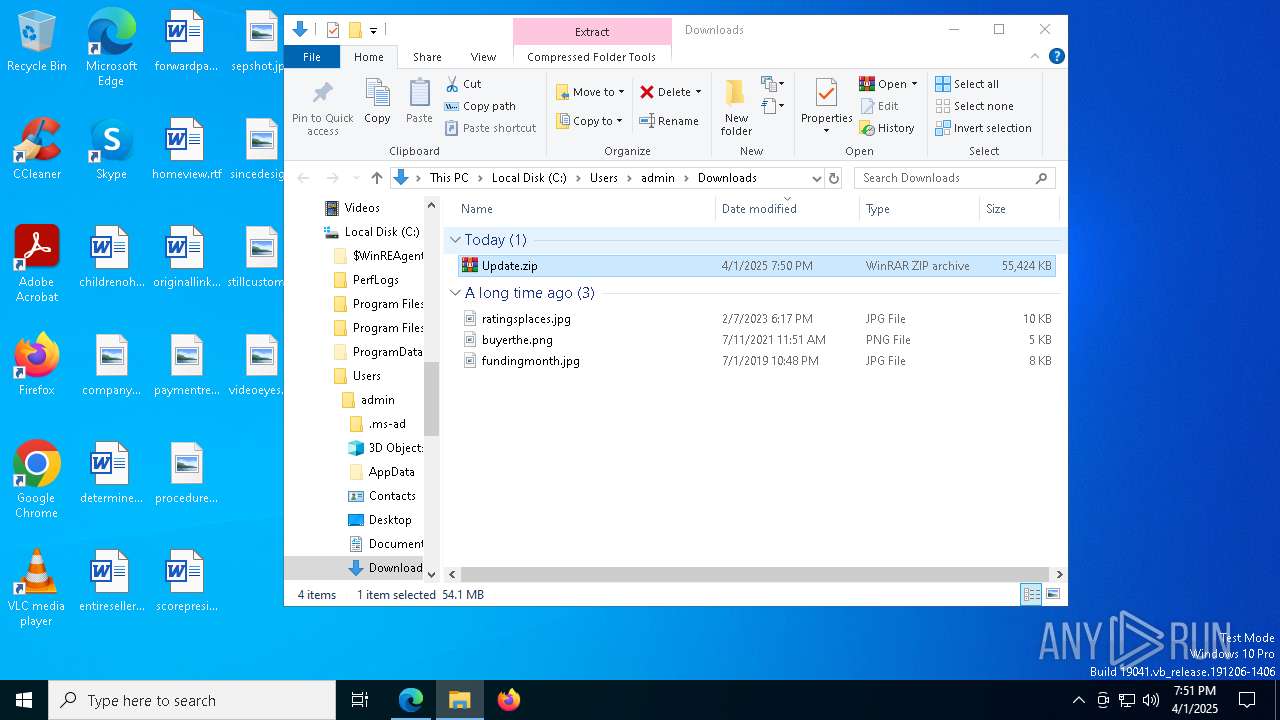
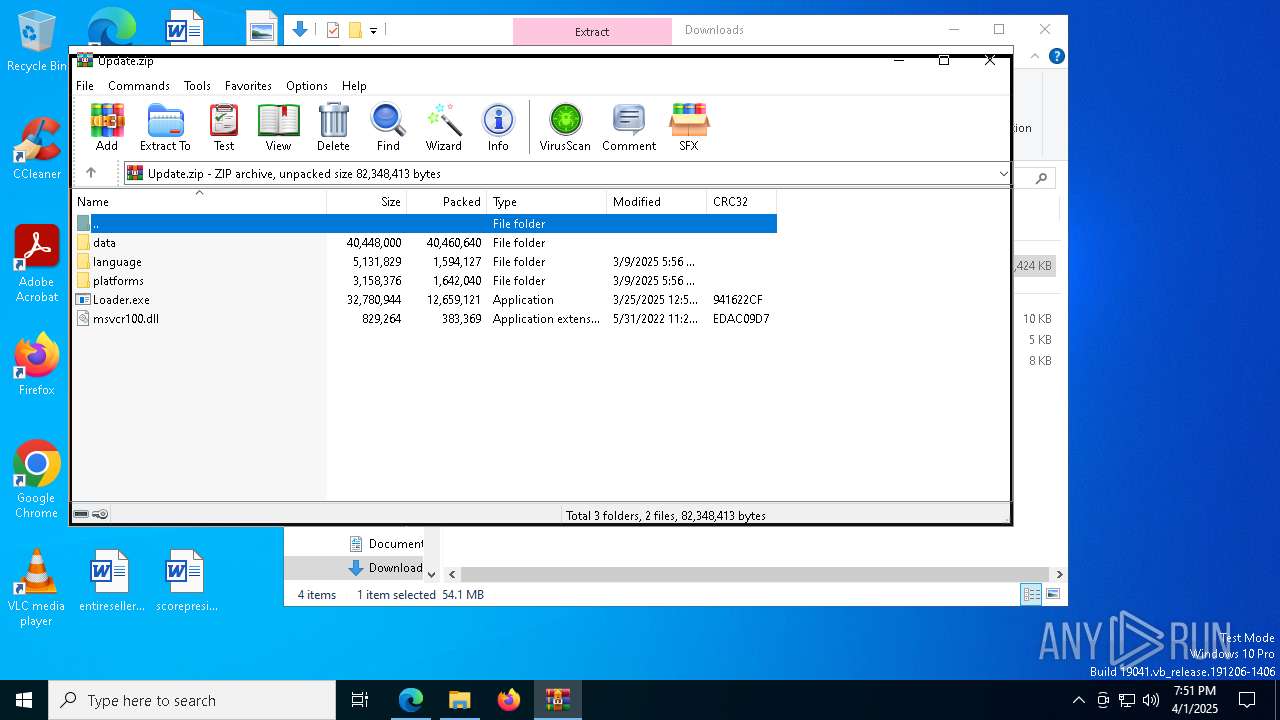
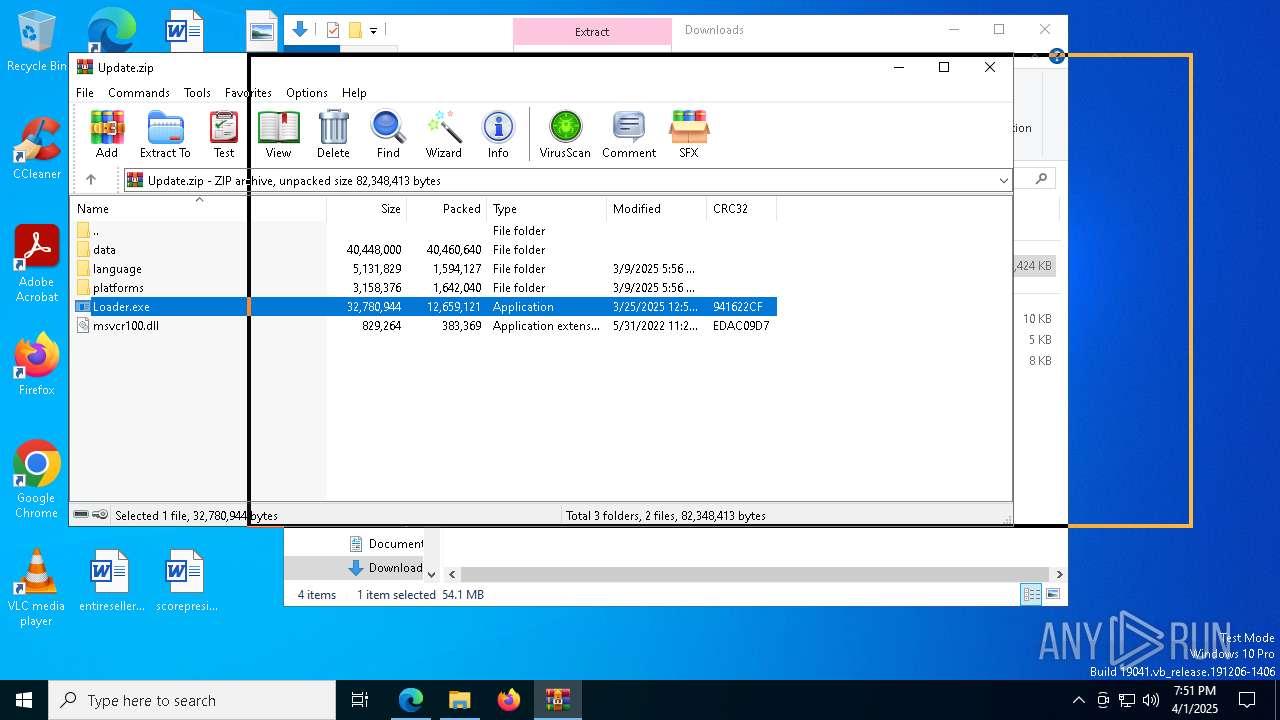
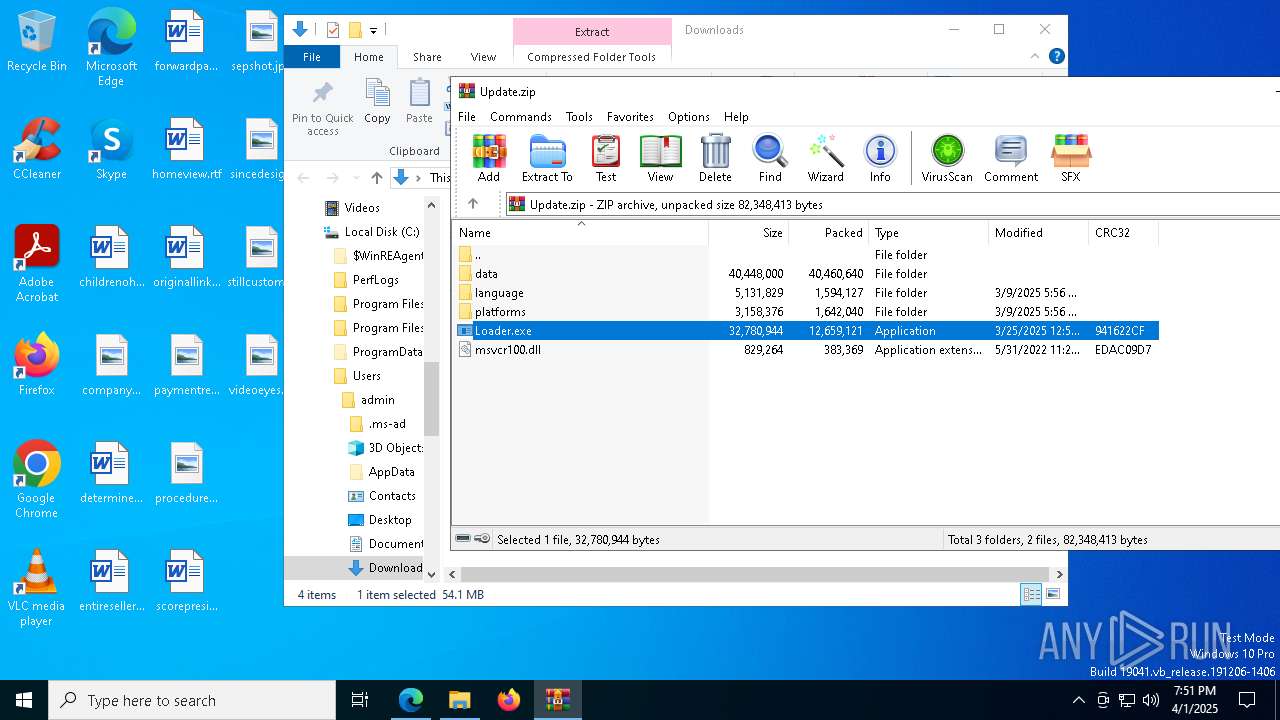
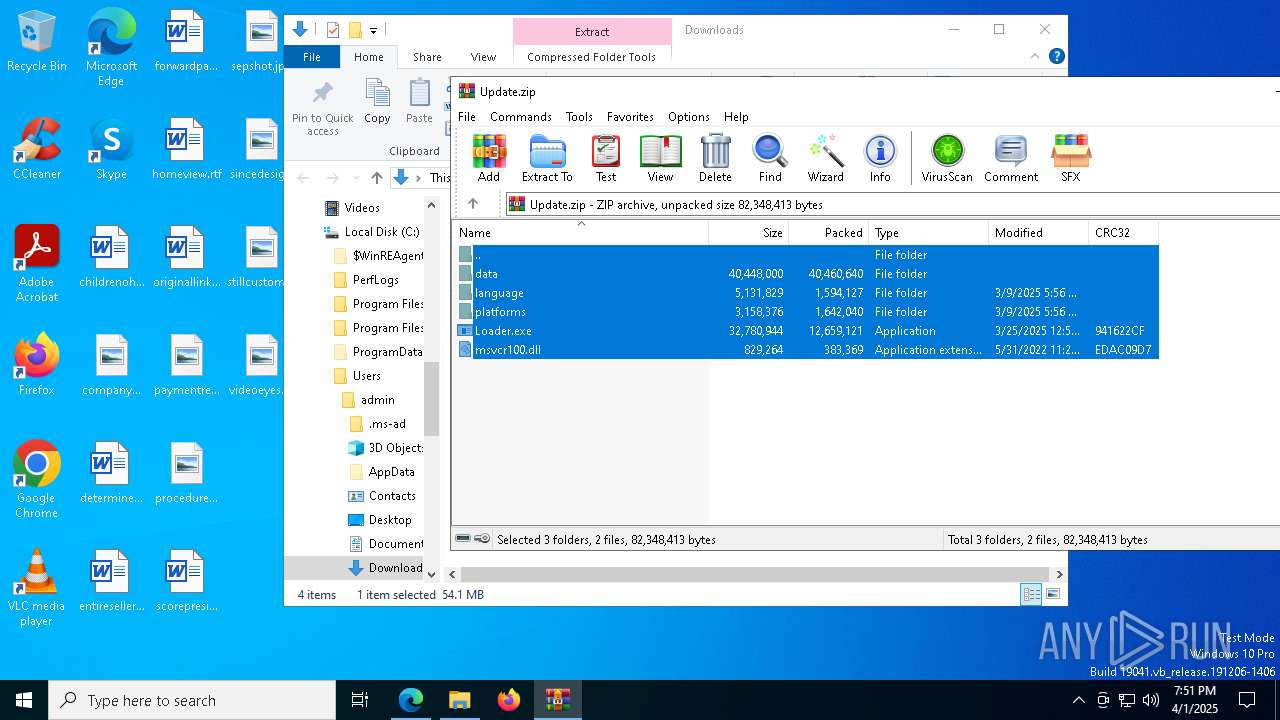
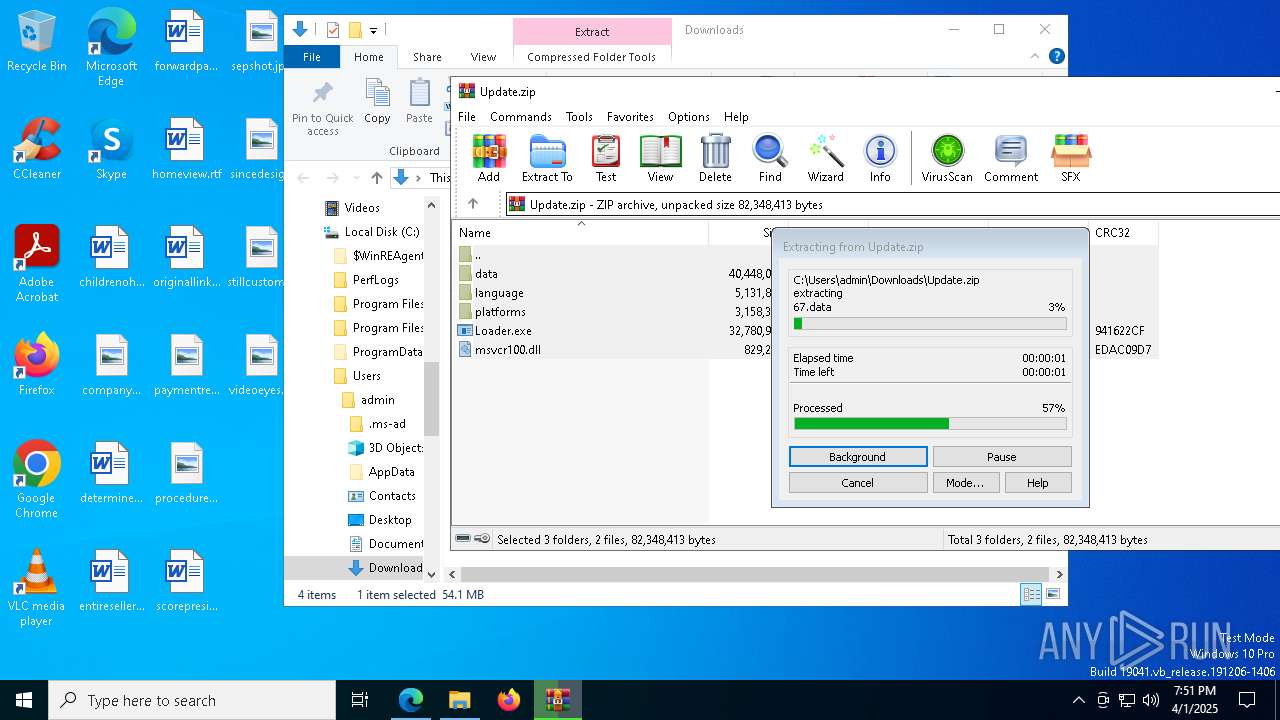
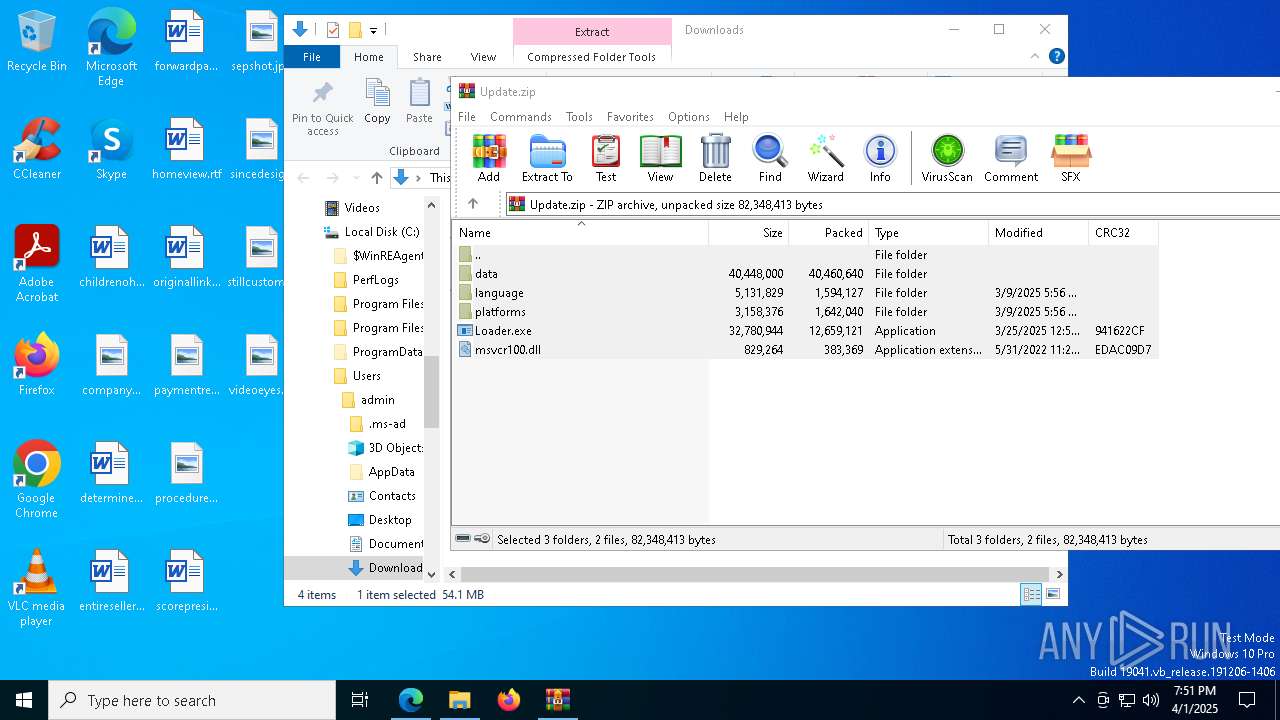
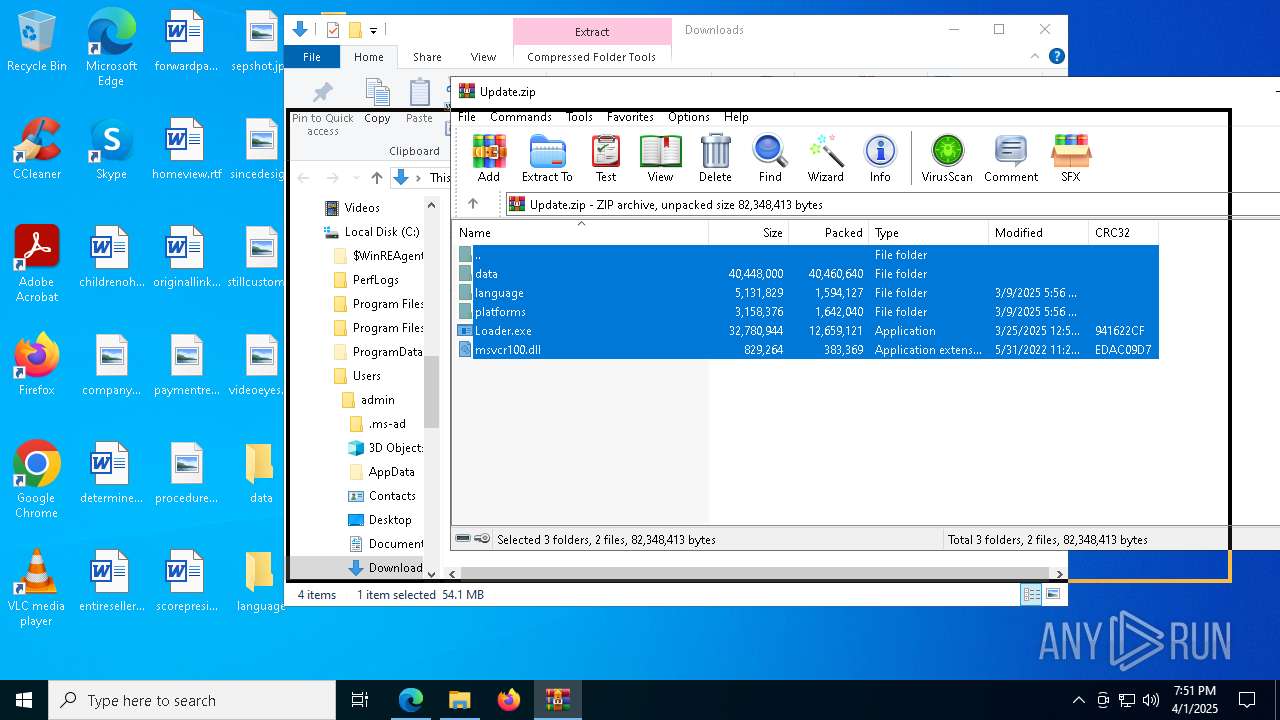
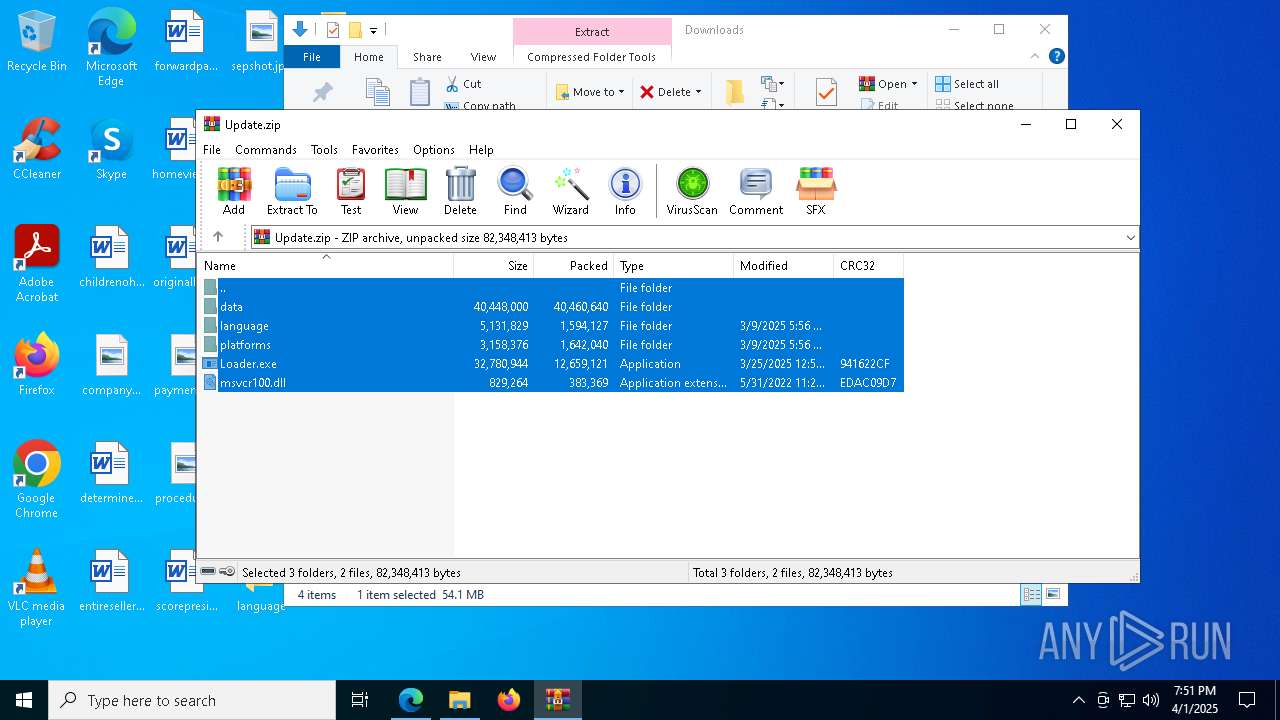
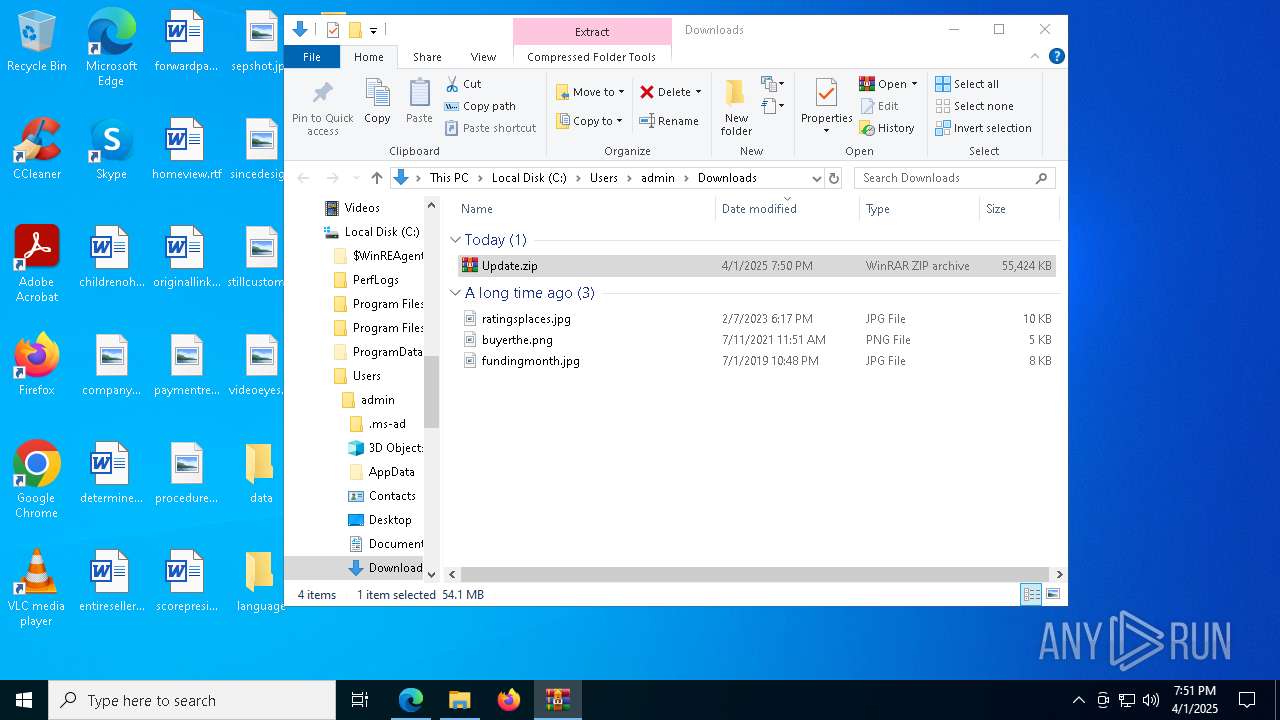
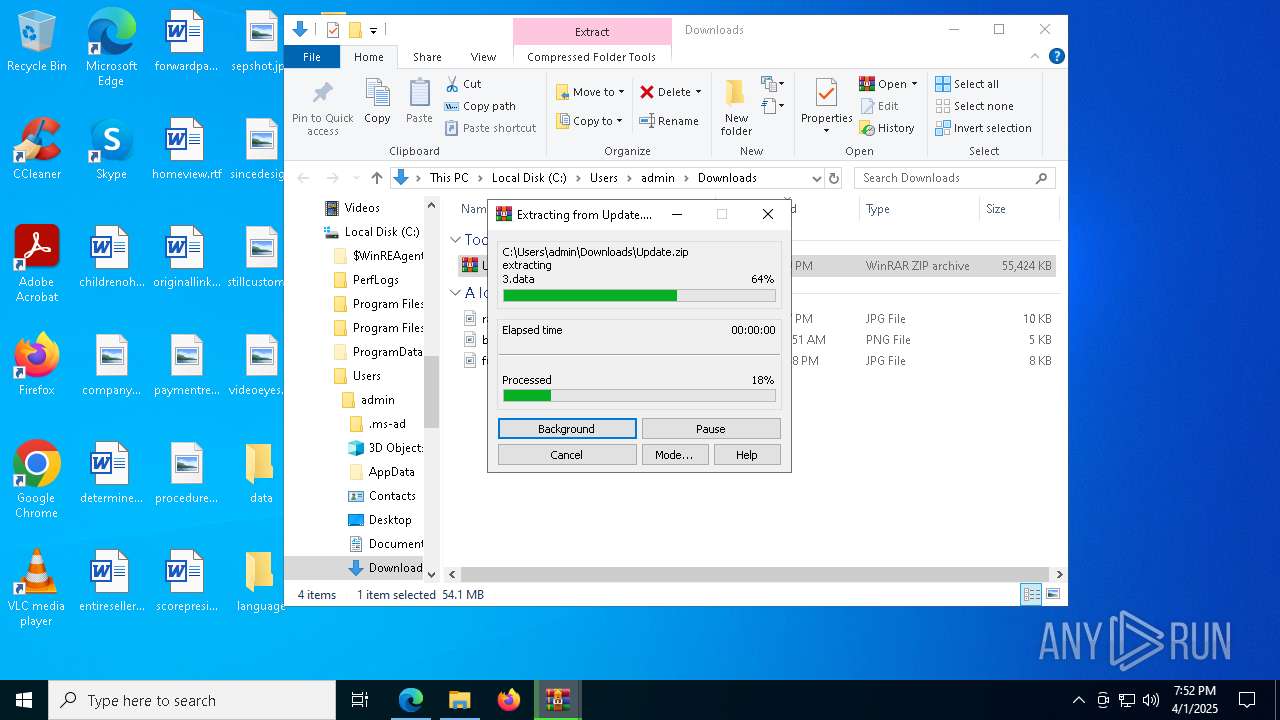
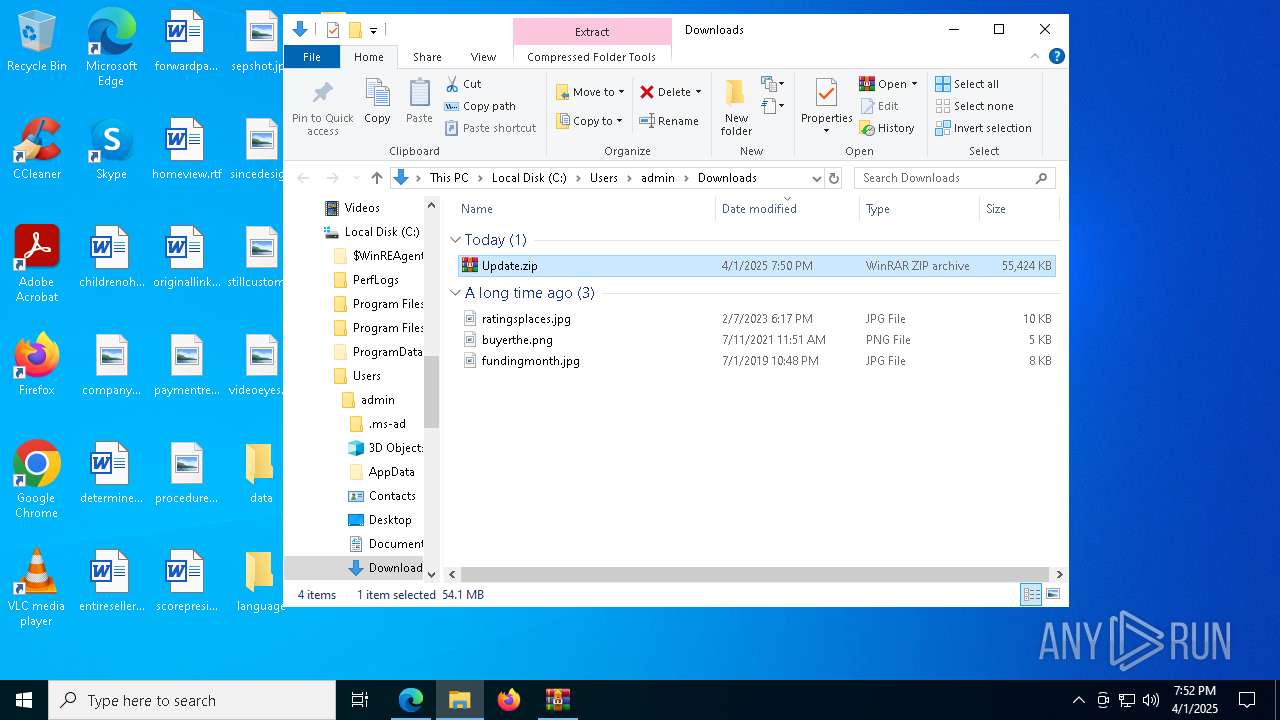
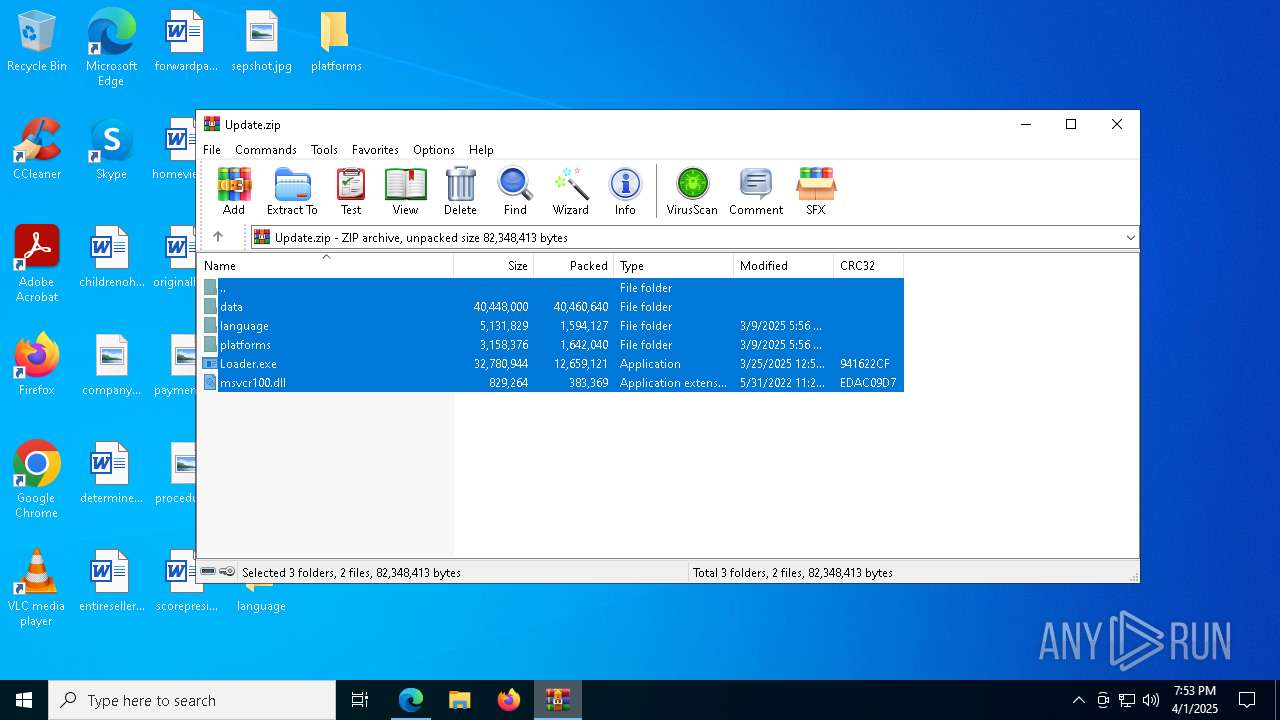
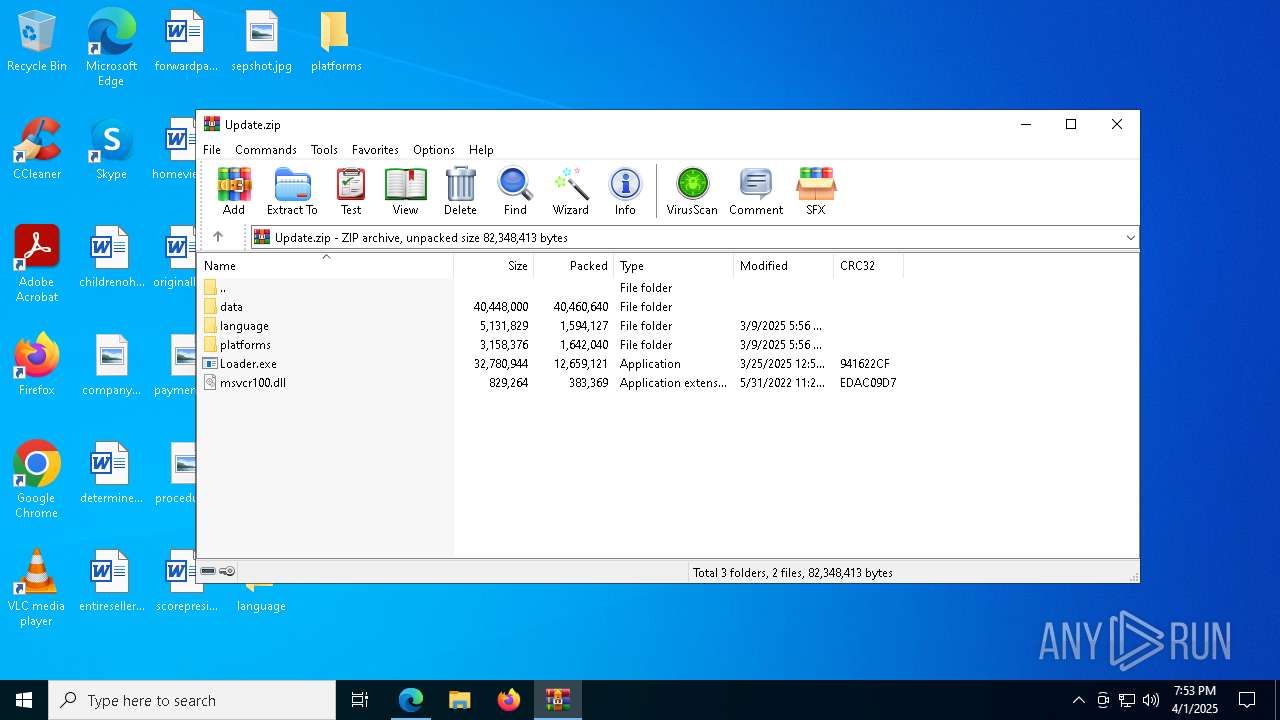
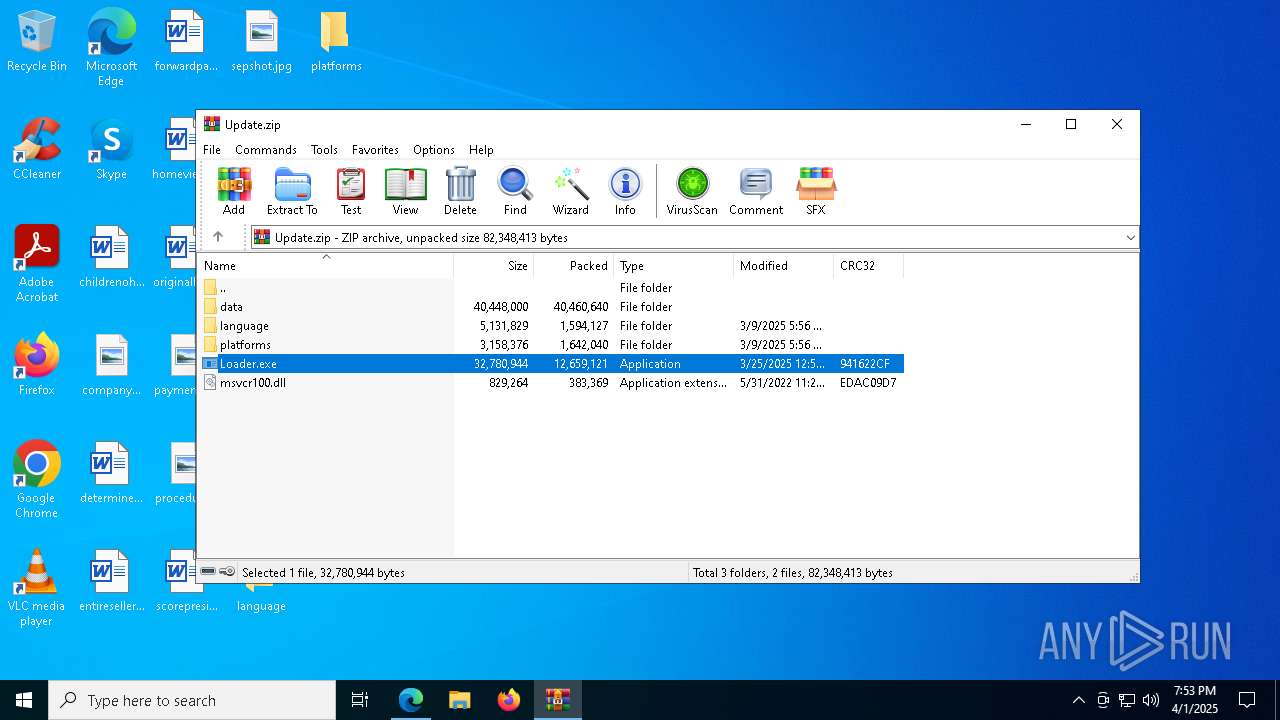
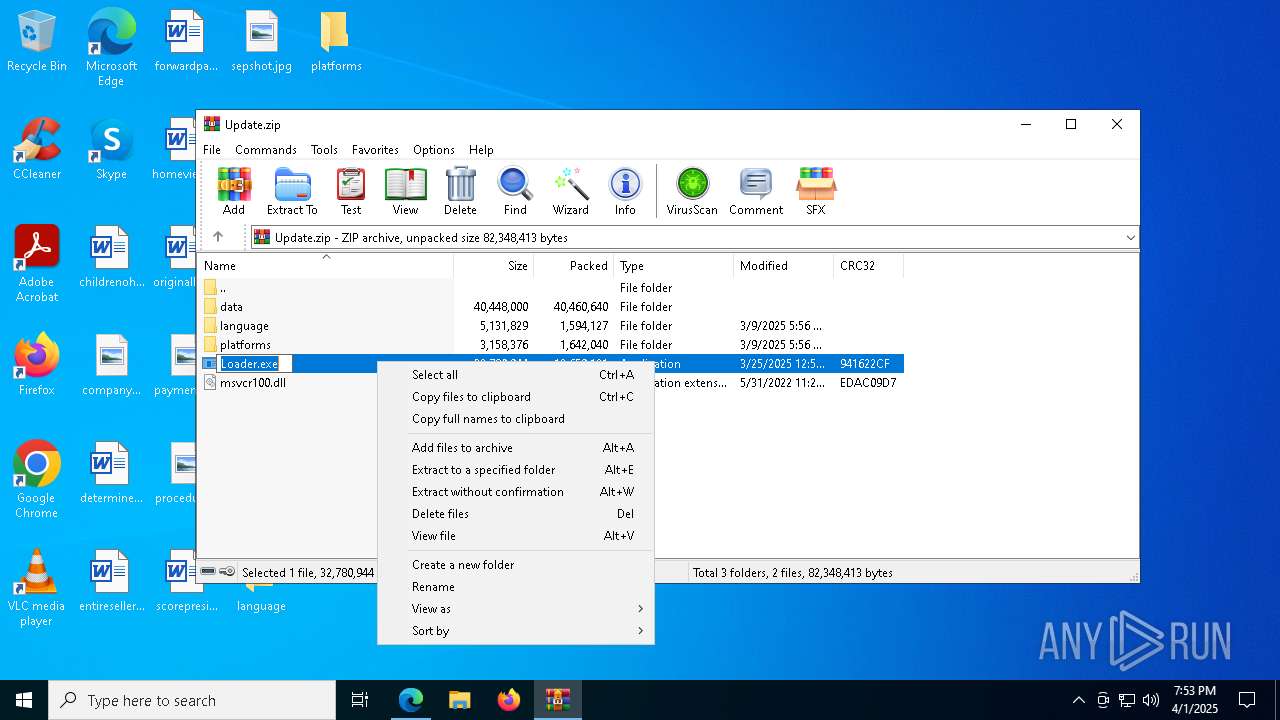
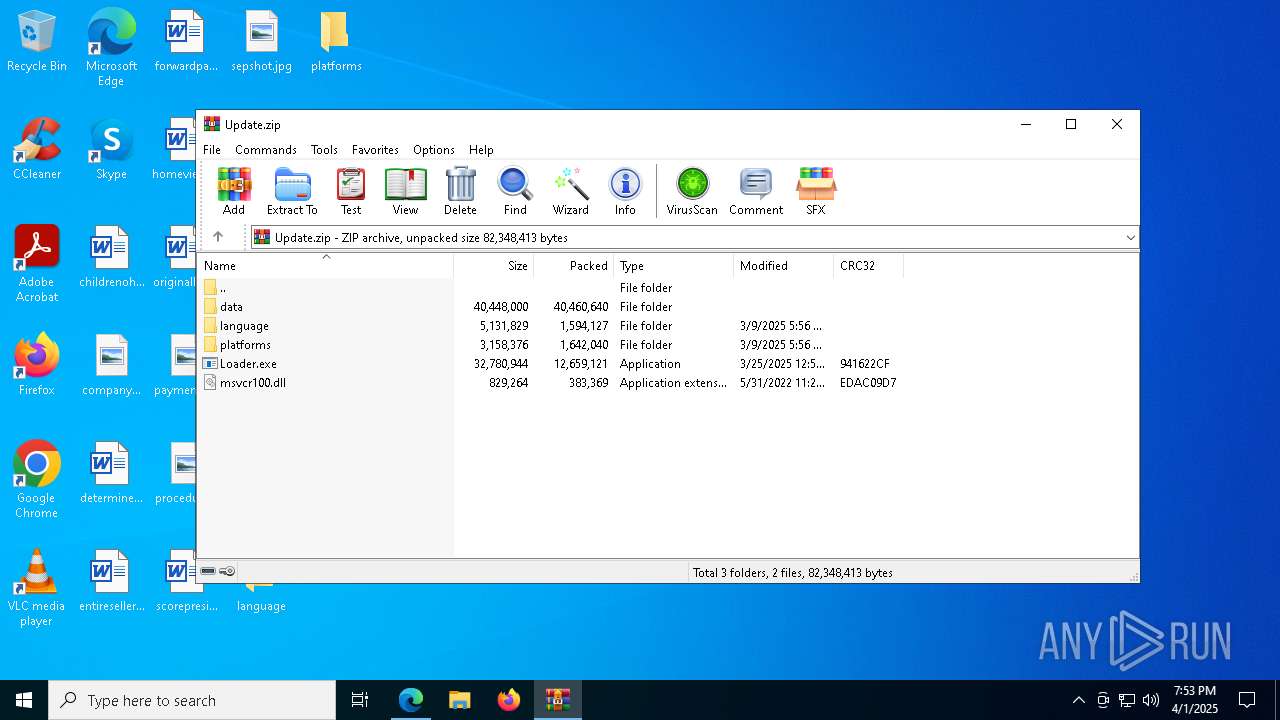
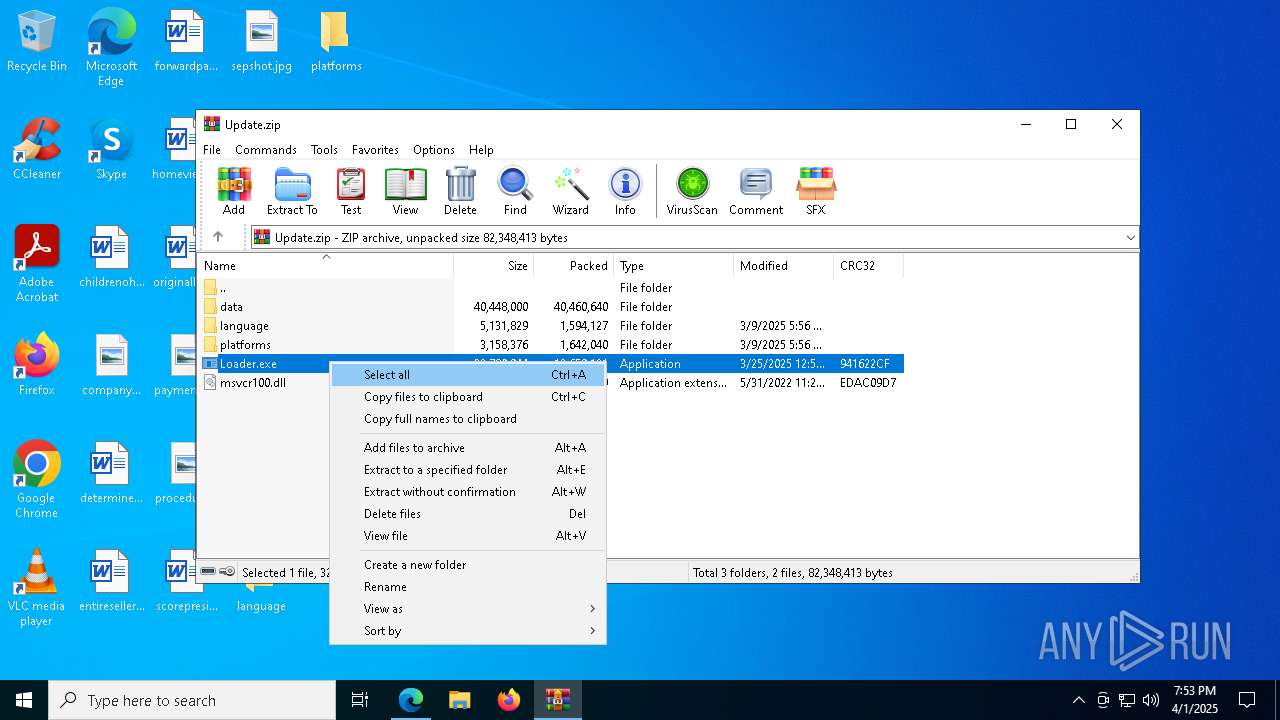
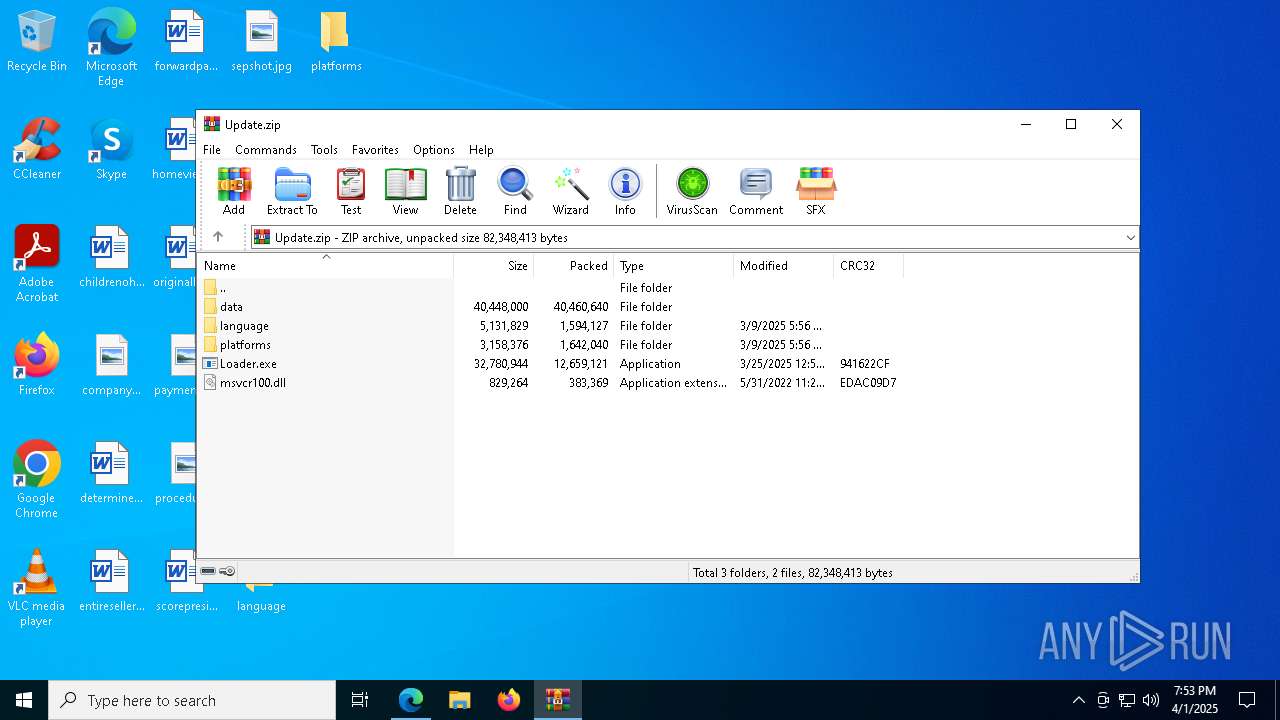
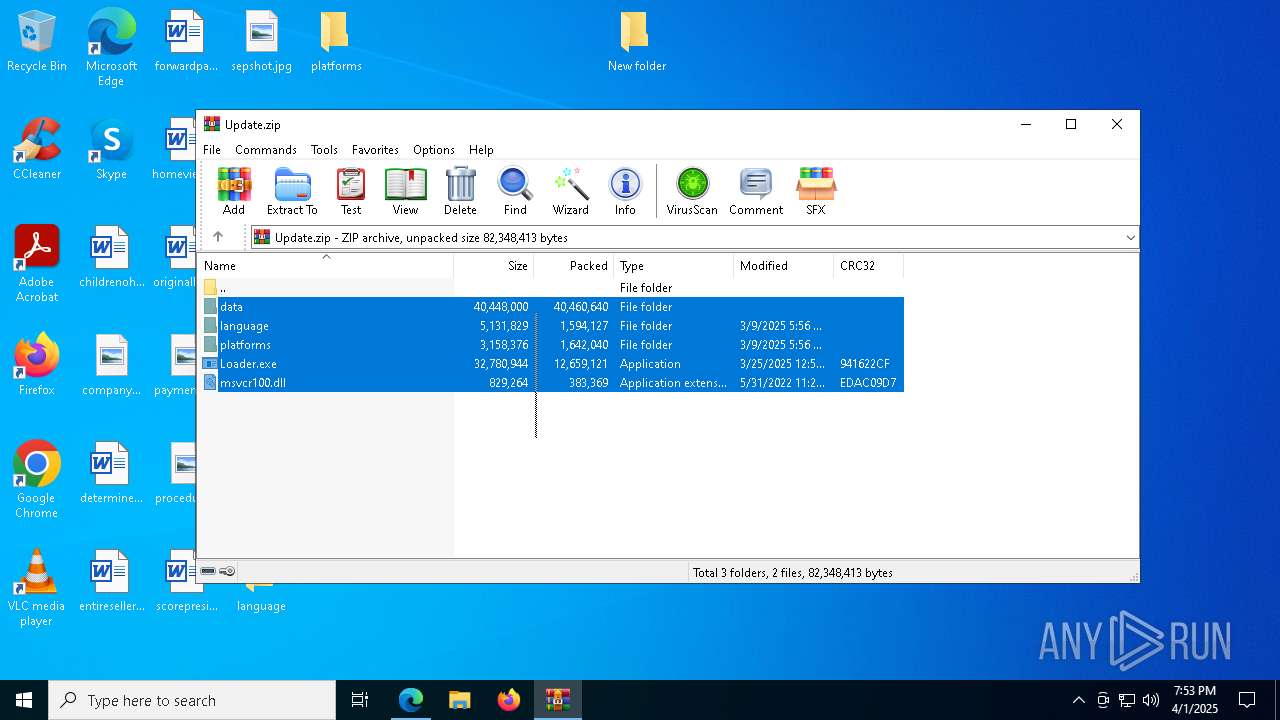
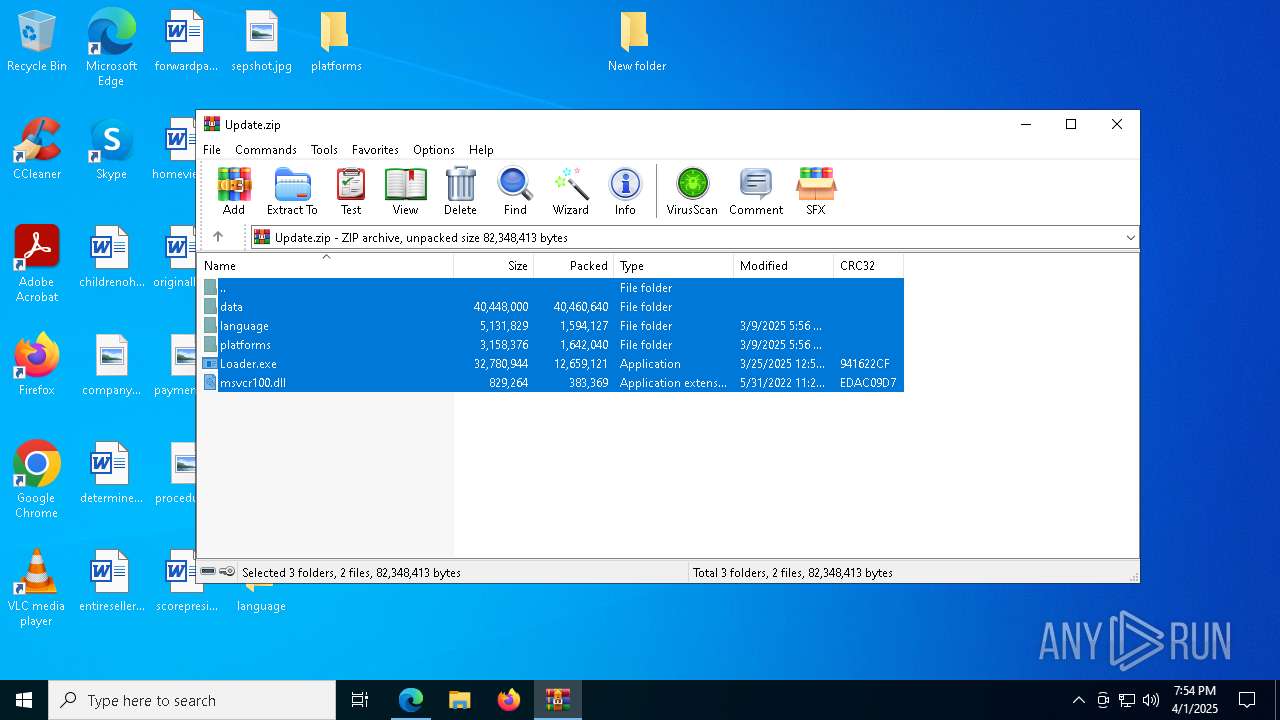
| URL: | https://github.com/J7sXEN/xeno-executor/releases/download/Update/Update.zip |
| Full analysis: | https://app.any.run/tasks/cd53f01f-6b84-45d0-ab33-5730d9278baf |
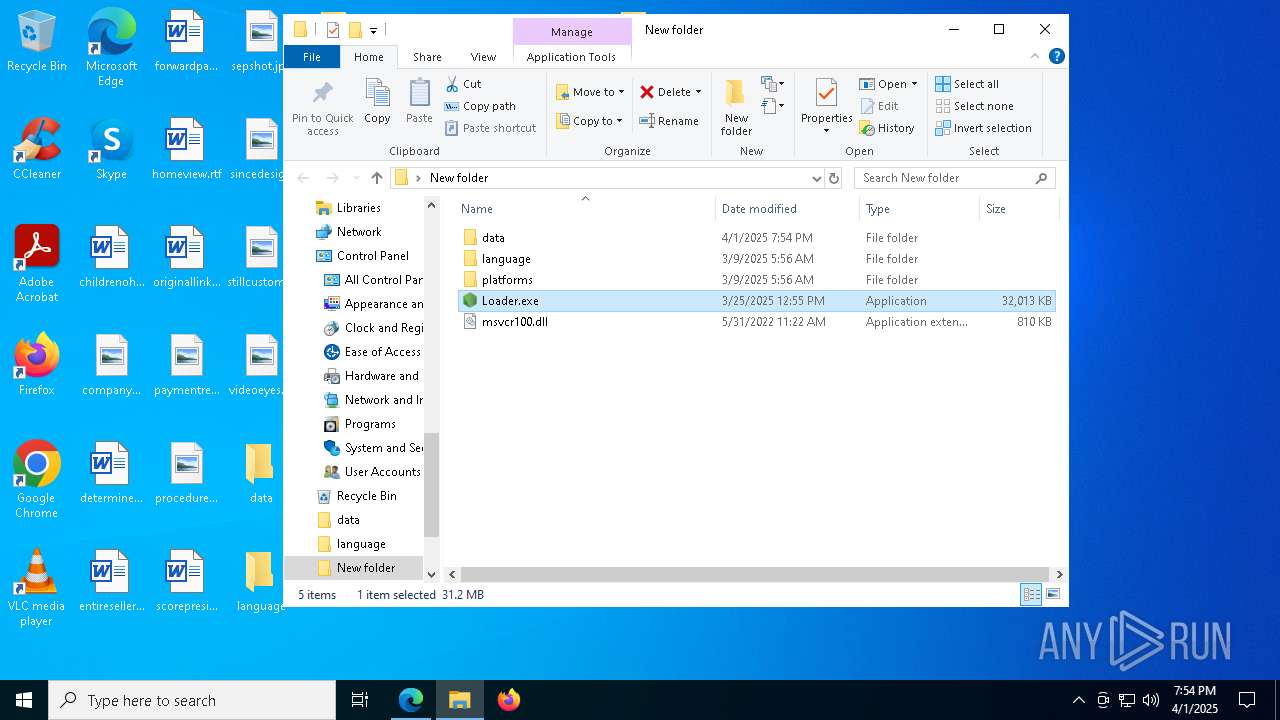
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2025, 19:50:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7619080770DB51788E28301EB436C53A |
| SHA1: | BBE769DC25ECF2BDAD6F257584C0439205A42D2E |
| SHA256: | E24E078227D966B641DFB1EF0E8D6ABAE8613BD466C0487B04986BD2B2270BEC |
| SSDEEP: | 3:N8tEd99gDoAGQRtE2kCE4Iyp:2uCDosRtrOyp |
MALICIOUS
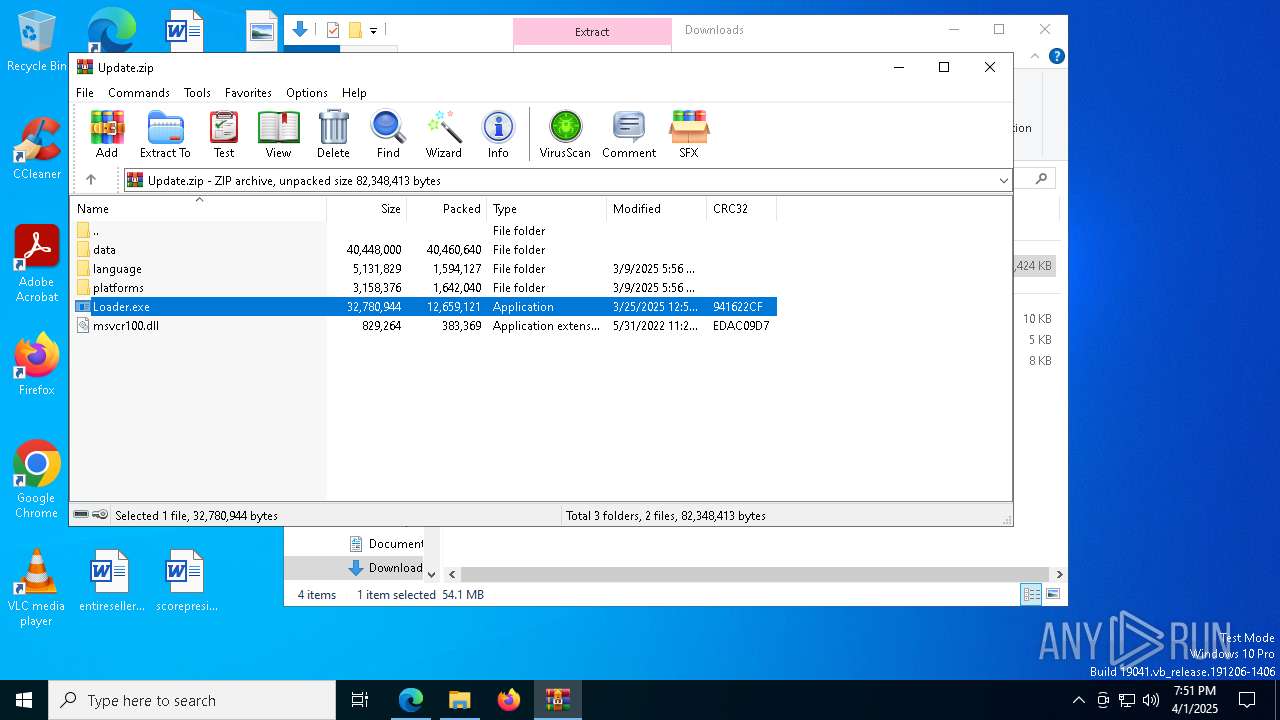
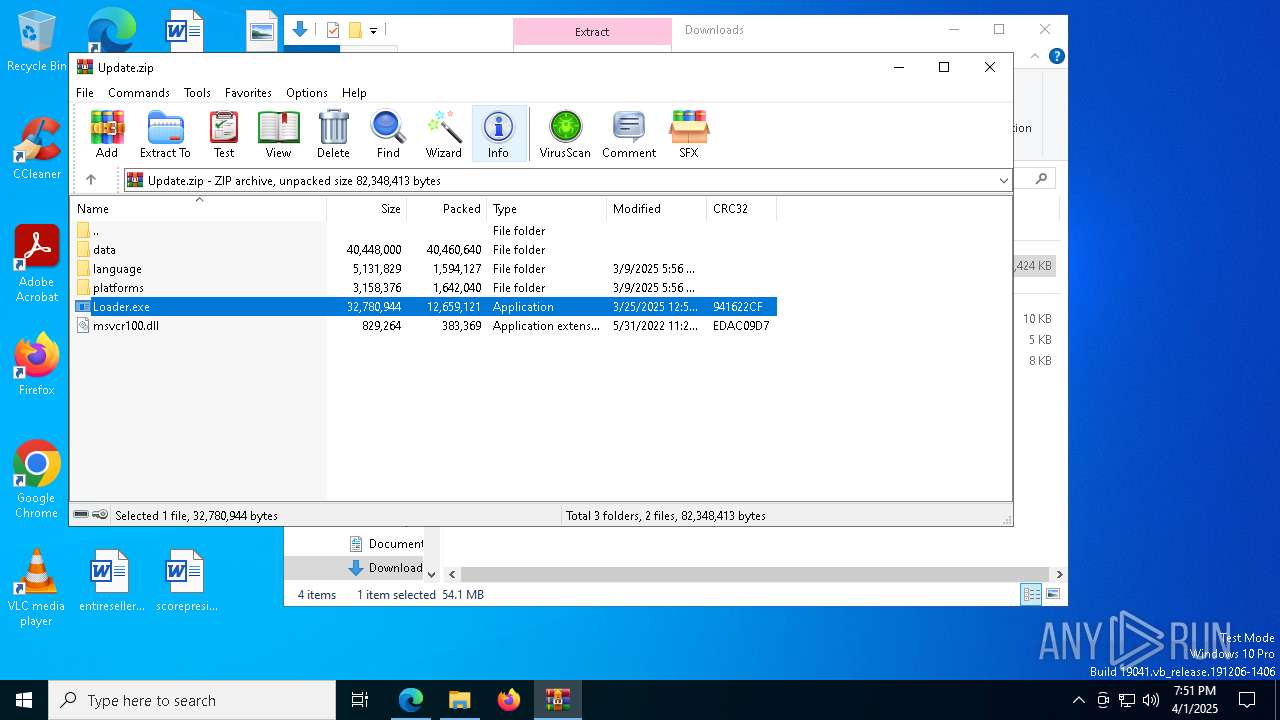
Adds path to the Windows Defender exclusion list
- Loader.exe (PID: 2140)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8112)
- Loader.exe (PID: 2596)
- cmd.exe (PID: 3968)
- Loader.exe (PID: 4452)
- cmd.exe (PID: 7836)
- Loader.exe (PID: 2096)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 5952)
- Loader.exe (PID: 5384)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 664)
- Loader.exe (PID: 2244)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8104)
- Loader.exe (PID: 5680)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 6044)
Changes Windows Defender settings
- cmd.exe (PID: 3268)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 5952)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 664)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 6044)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6272)
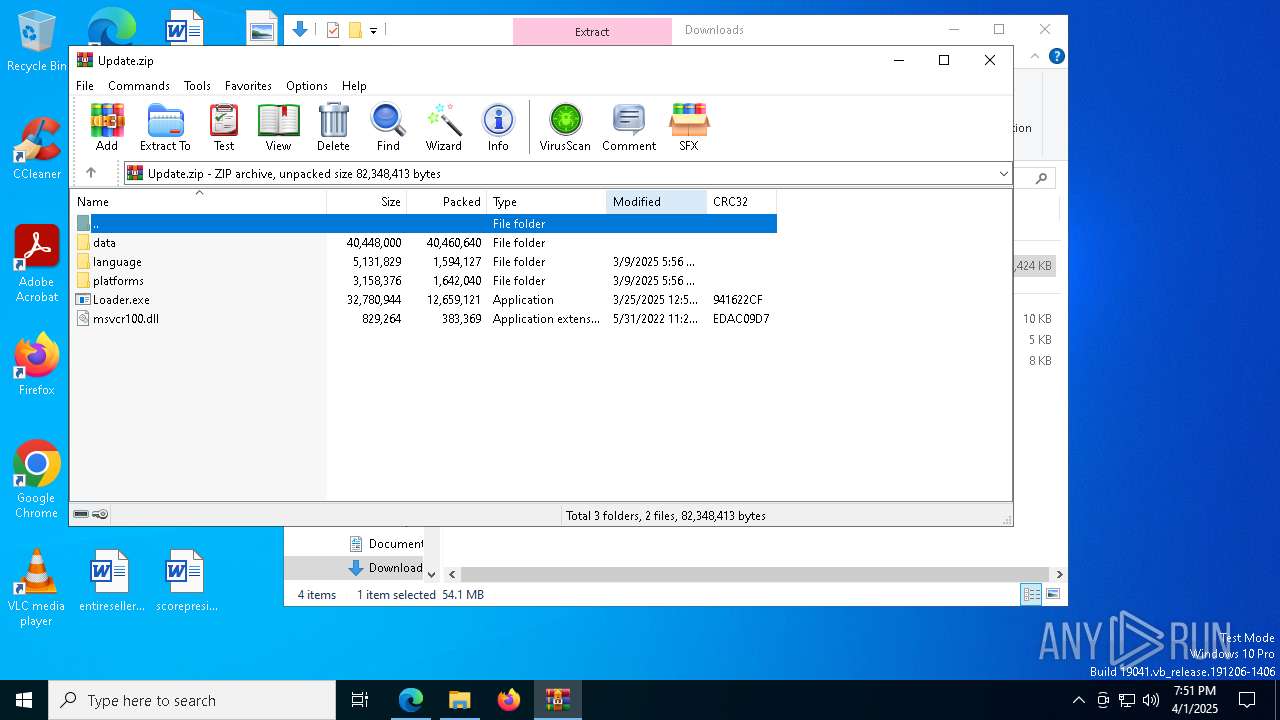
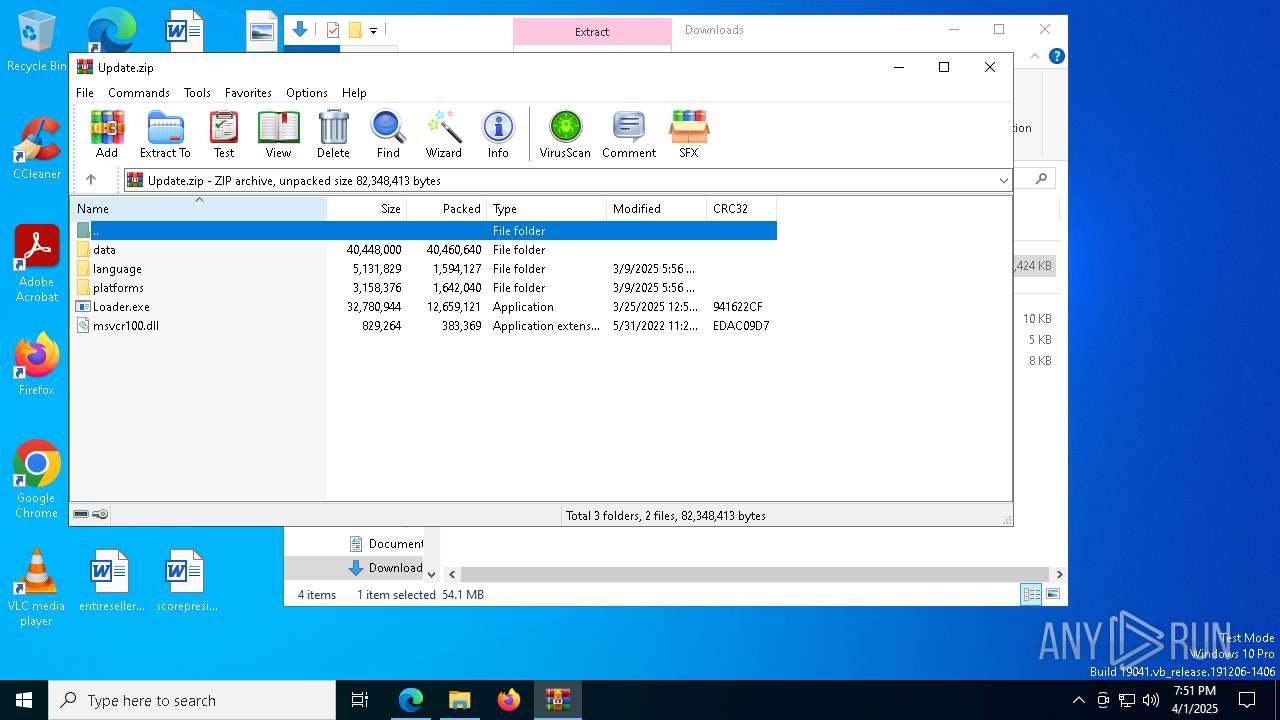
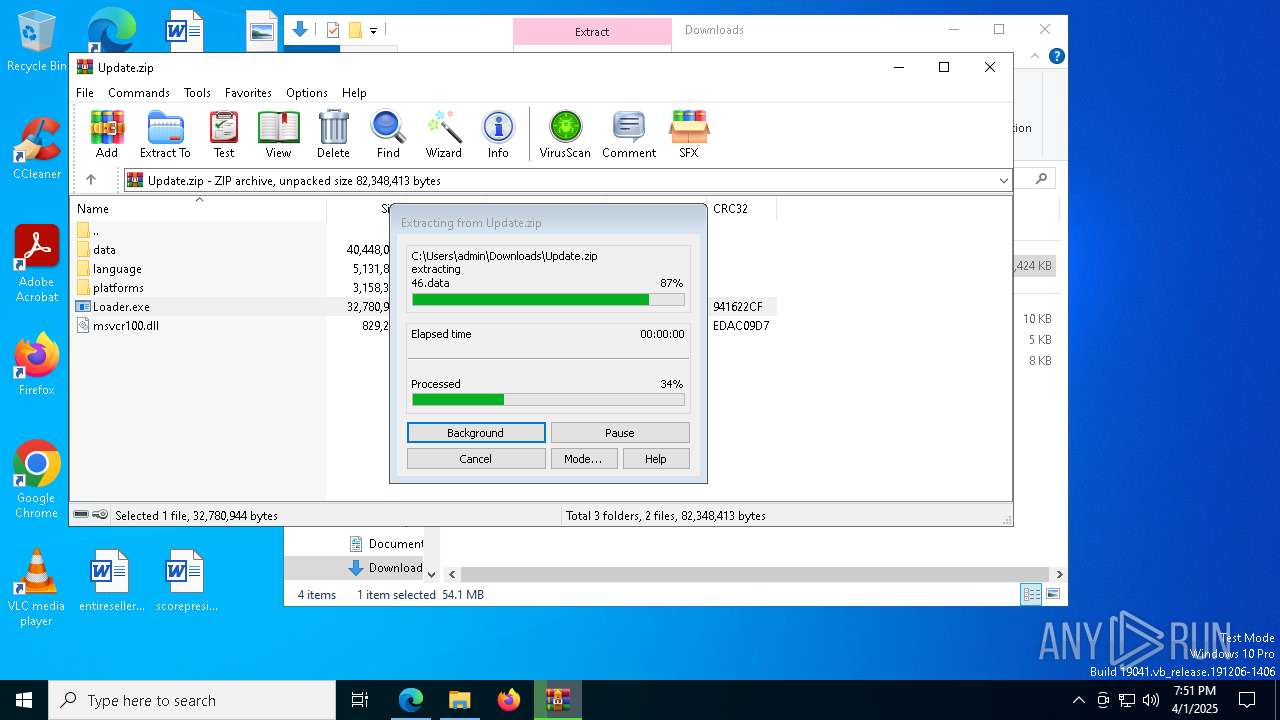
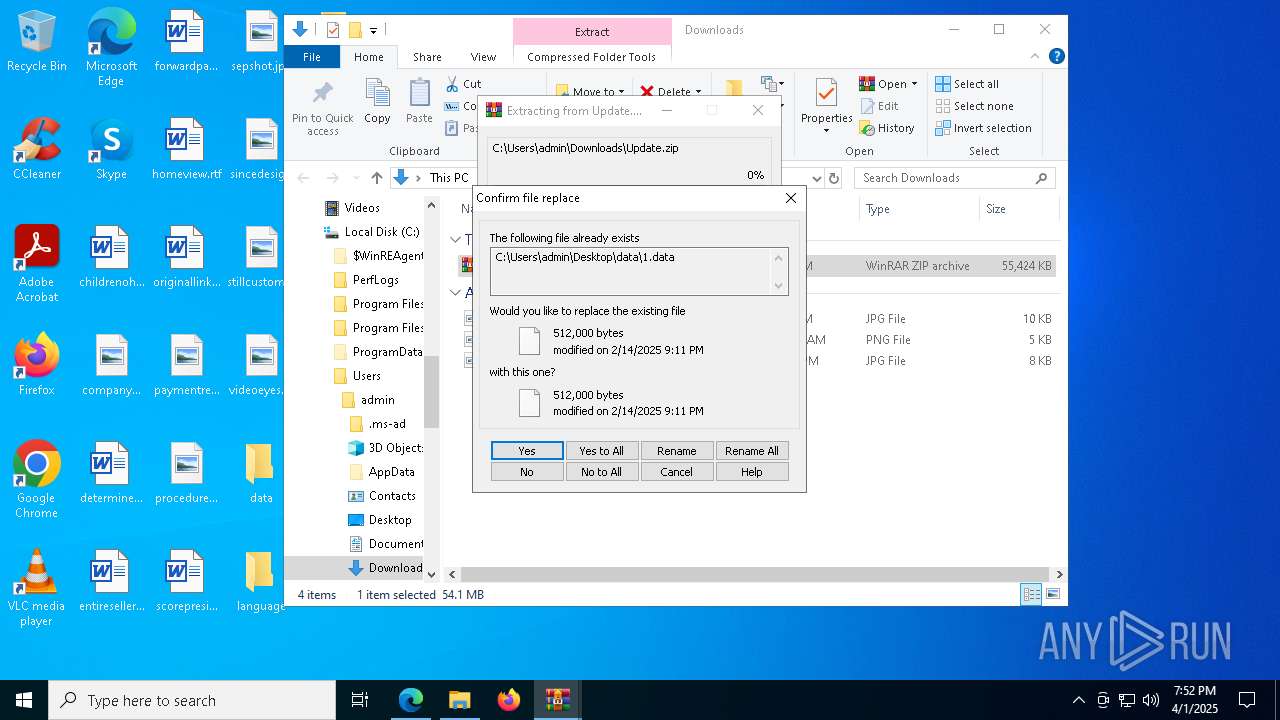
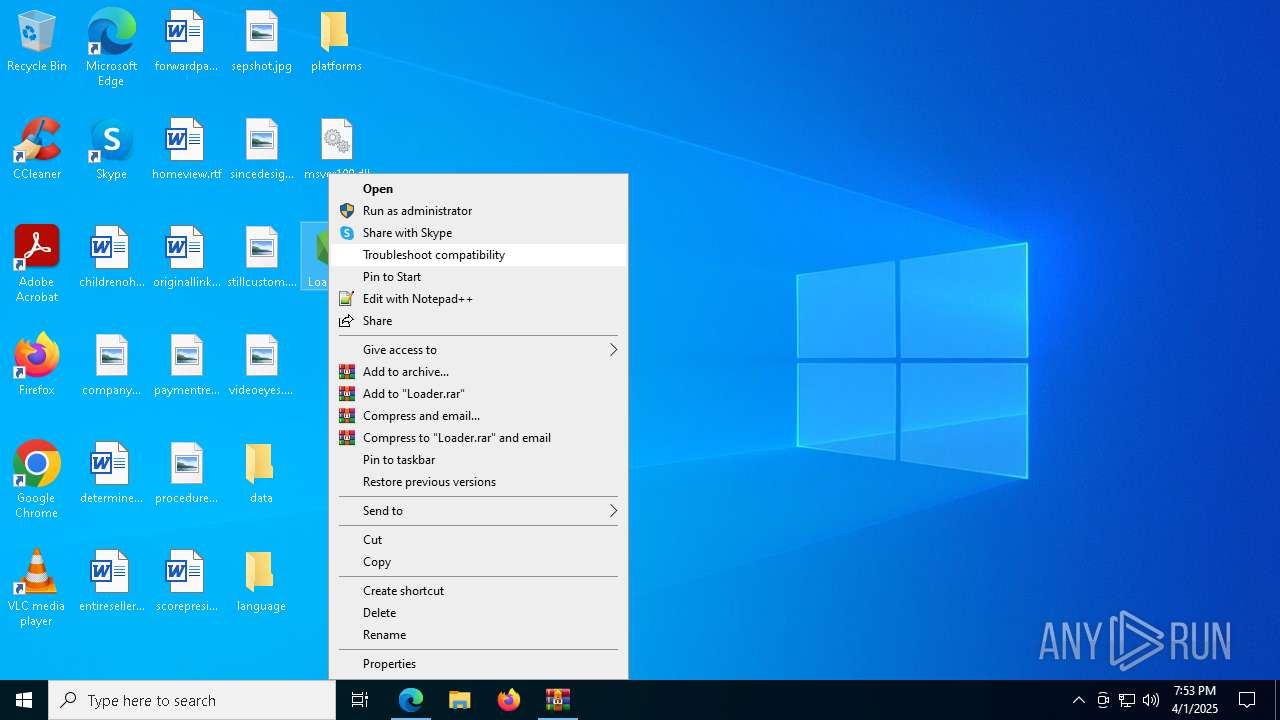
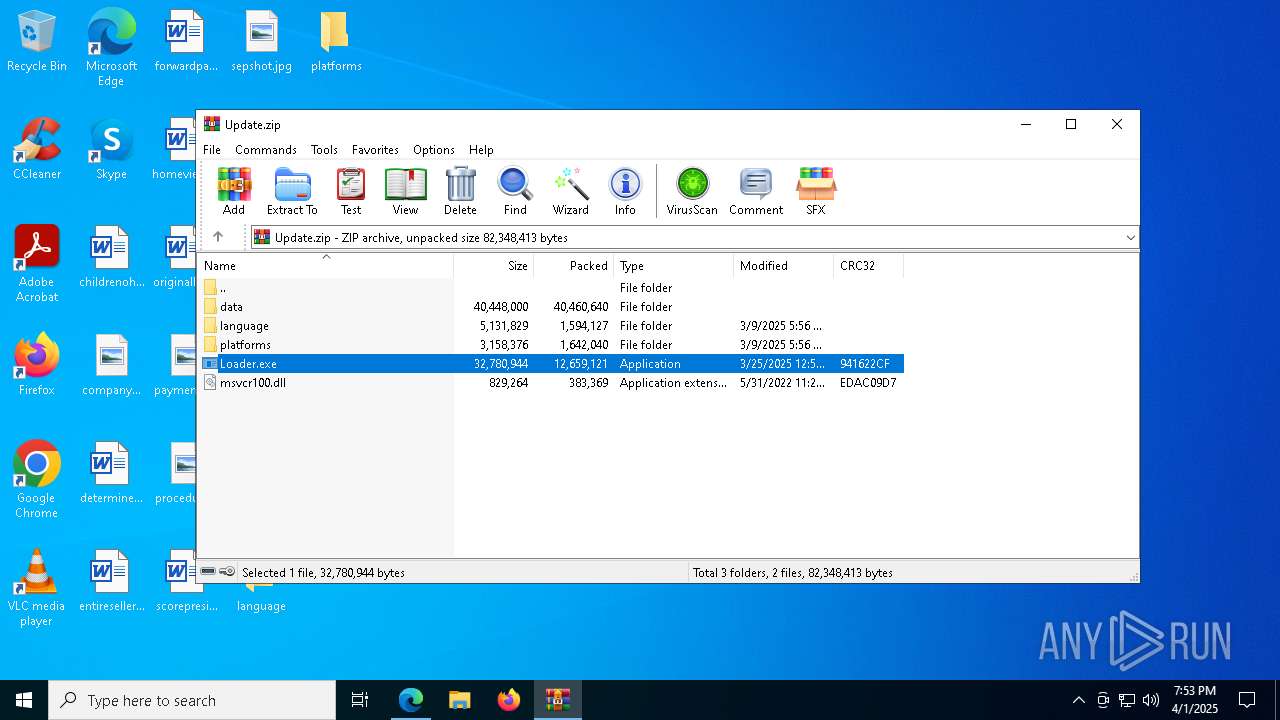
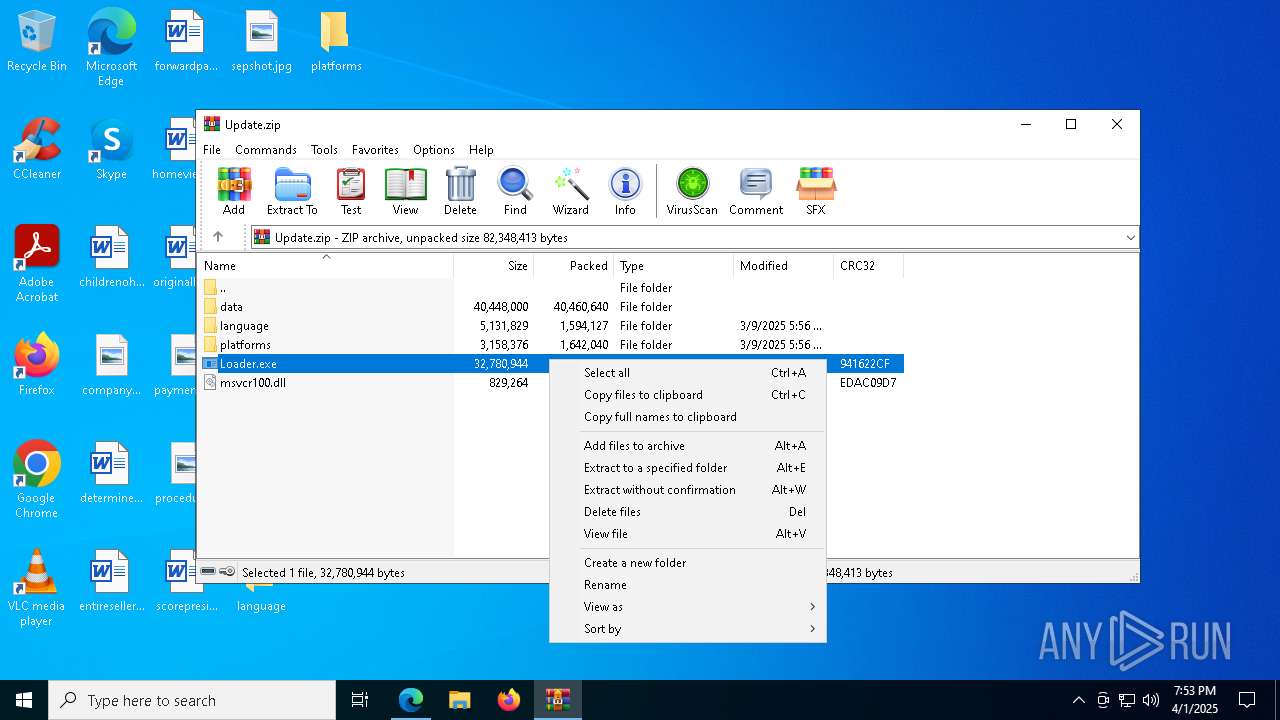
Process drops legitimate windows executable
- WinRAR.exe (PID: 6272)
- WinRAR.exe (PID: 7944)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 1056)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 5188)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 4012)
Node.exe was dropped
- WinRAR.exe (PID: 6272)
- WinRAR.exe (PID: 7944)
Starts CMD.EXE for commands execution
- Loader.exe (PID: 5892)
- Loader.exe (PID: 2140)
- Loader.exe (PID: 6512)
- Loader.exe (PID: 2596)
- Loader.exe (PID: 2040)
- Loader.exe (PID: 4452)
- Loader.exe (PID: 5408)
- Loader.exe (PID: 2096)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 1672)
- Loader.exe (PID: 2244)
- Loader.exe (PID: 5680)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5740)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7680)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 2416)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 236)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 5952)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 6004)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 664)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 4448)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 6044)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 3268)
- net.exe (PID: 864)
- net.exe (PID: 6372)
- cmd.exe (PID: 8028)
- net.exe (PID: 4452)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 864)
- net.exe (PID: 8160)
- cmd.exe (PID: 5548)
- net.exe (PID: 7144)
- net.exe (PID: 3800)
- cmd.exe (PID: 5608)
- cmd.exe (PID: 5556)
- net.exe (PID: 6156)
- cmd.exe (PID: 728)
- net.exe (PID: 904)
- cmd.exe (PID: 6752)
- net.exe (PID: 2136)
- cmd.exe (PID: 5132)
- net.exe (PID: 1020)
- cmd.exe (PID: 4208)
- net.exe (PID: 8156)
- net.exe (PID: 872)
- cmd.exe (PID: 6248)
Starts process via Powershell
- powershell.exe (PID: 3156)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 132)
- powershell.exe (PID: 5624)
Get information on the list of running processes
- Loader.exe (PID: 2140)
- cmd.exe (PID: 2332)
- Loader.exe (PID: 6512)
- cmd.exe (PID: 4528)
- Loader.exe (PID: 5892)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 5756)
- Loader.exe (PID: 2596)
- Loader.exe (PID: 2040)
- cmd.exe (PID: 7104)
- Loader.exe (PID: 4452)
- cmd.exe (PID: 1348)
- Loader.exe (PID: 5408)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 8044)
- Loader.exe (PID: 2096)
- cmd.exe (PID: 4620)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 1672)
- cmd.exe (PID: 7888)
- Loader.exe (PID: 2244)
- cmd.exe (PID: 4188)
- Loader.exe (PID: 5680)
- cmd.exe (PID: 896)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5112)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 1128)
- cmd.exe (PID: 7652)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5324)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 5952)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 664)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 6044)
INFO
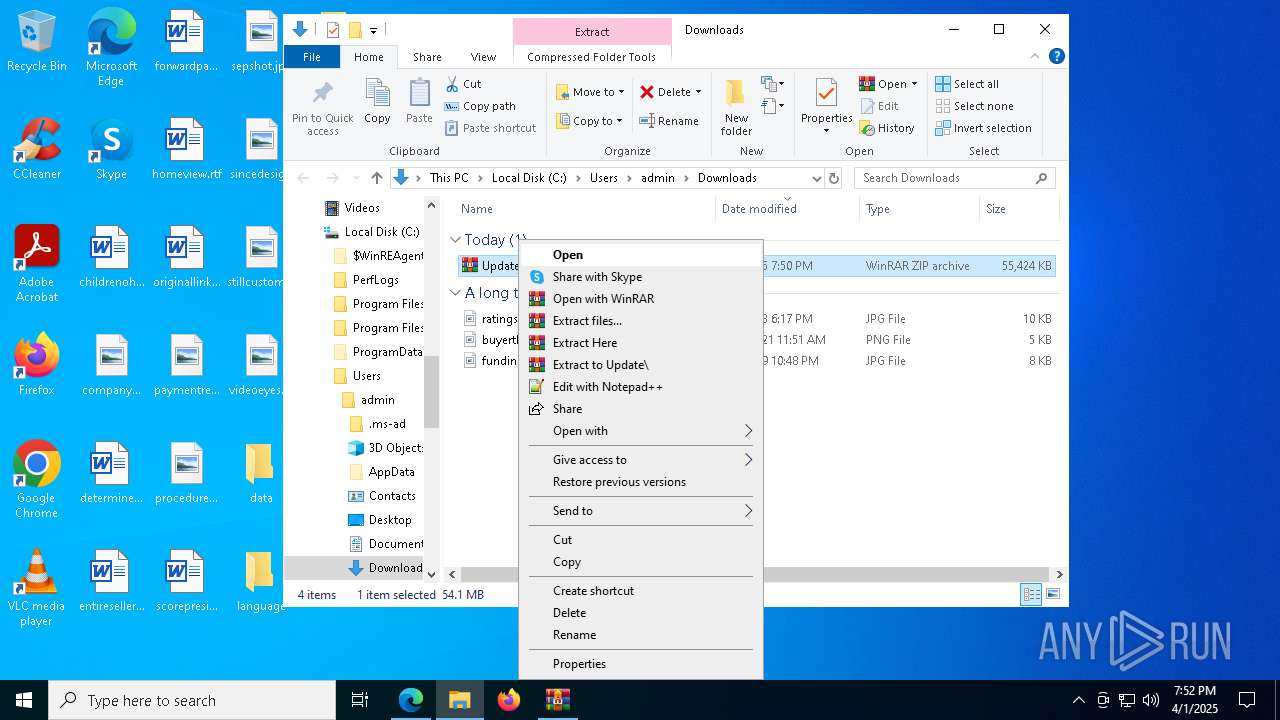
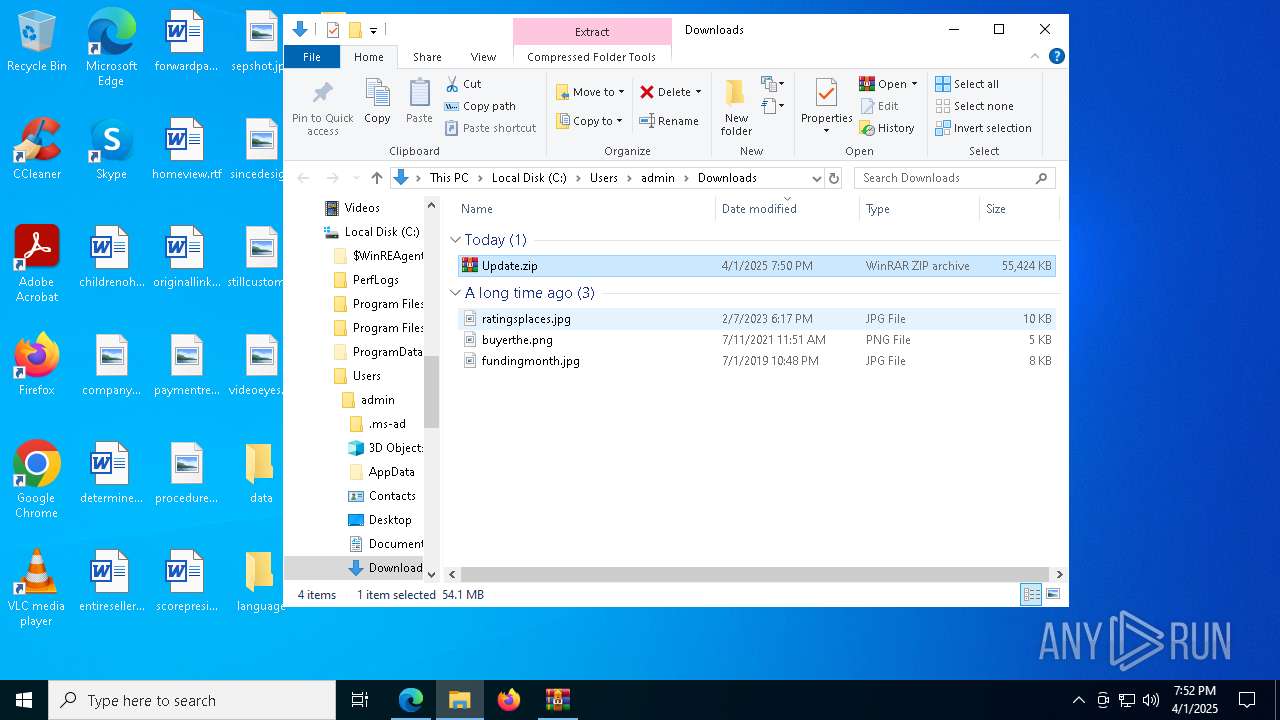
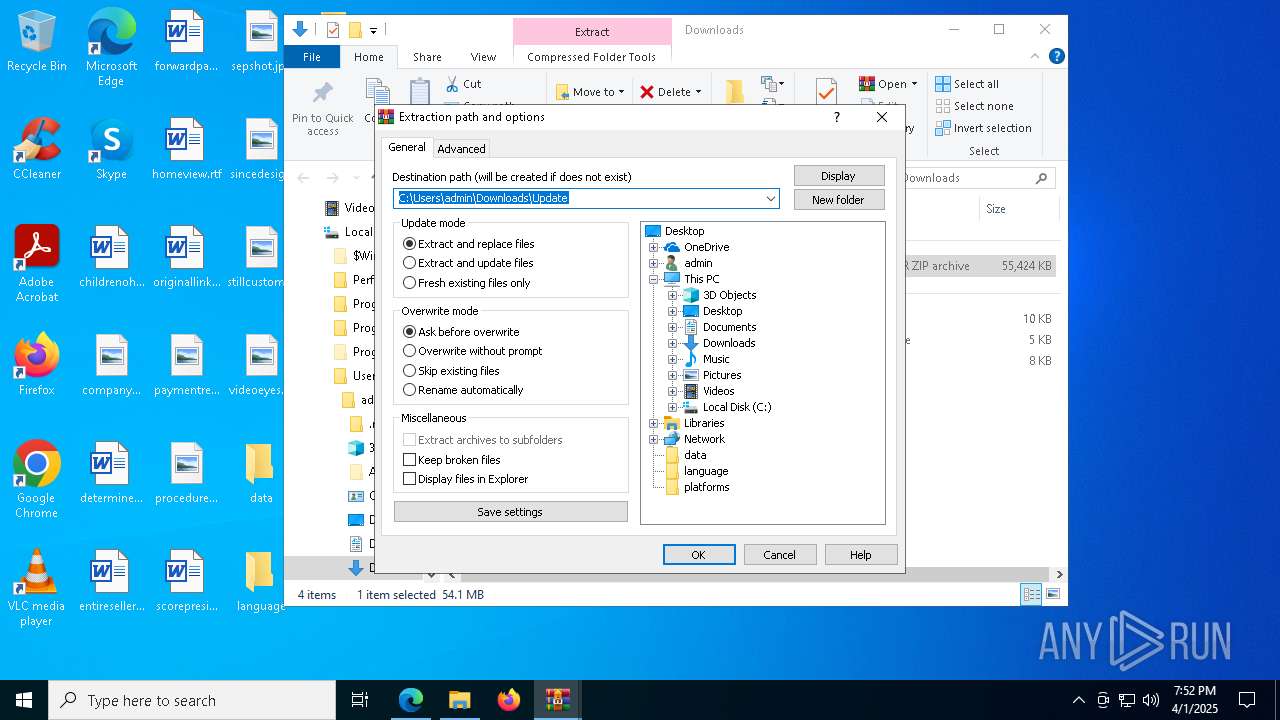
Autorun file from Downloads
- msedge.exe (PID: 7984)
Reads the computer name
- identity_helper.exe (PID: 2096)
- Loader.exe (PID: 2140)
- Loader.exe (PID: 6512)
- Loader.exe (PID: 5892)
- Loader.exe (PID: 2596)
- Loader.exe (PID: 4452)
- Loader.exe (PID: 5408)
- Loader.exe (PID: 2040)
- Loader.exe (PID: 2096)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 1672)
- Loader.exe (PID: 2244)
- Loader.exe (PID: 5680)
Checks supported languages
- identity_helper.exe (PID: 2096)
- Loader.exe (PID: 5892)
- Loader.exe (PID: 2140)
- Loader.exe (PID: 6512)
- Loader.exe (PID: 2596)
- Loader.exe (PID: 2040)
- Loader.exe (PID: 4452)
- Loader.exe (PID: 5408)
- Loader.exe (PID: 2096)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 2244)
- Loader.exe (PID: 1672)
- Loader.exe (PID: 5680)
Reads Environment values
- identity_helper.exe (PID: 2096)
- Loader.exe (PID: 5892)
- Loader.exe (PID: 2140)
- Loader.exe (PID: 6512)
- Loader.exe (PID: 2596)
- Loader.exe (PID: 2040)
- Loader.exe (PID: 4452)
- Loader.exe (PID: 5408)
- Loader.exe (PID: 2096)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 1672)
- Loader.exe (PID: 2244)
- Loader.exe (PID: 5680)
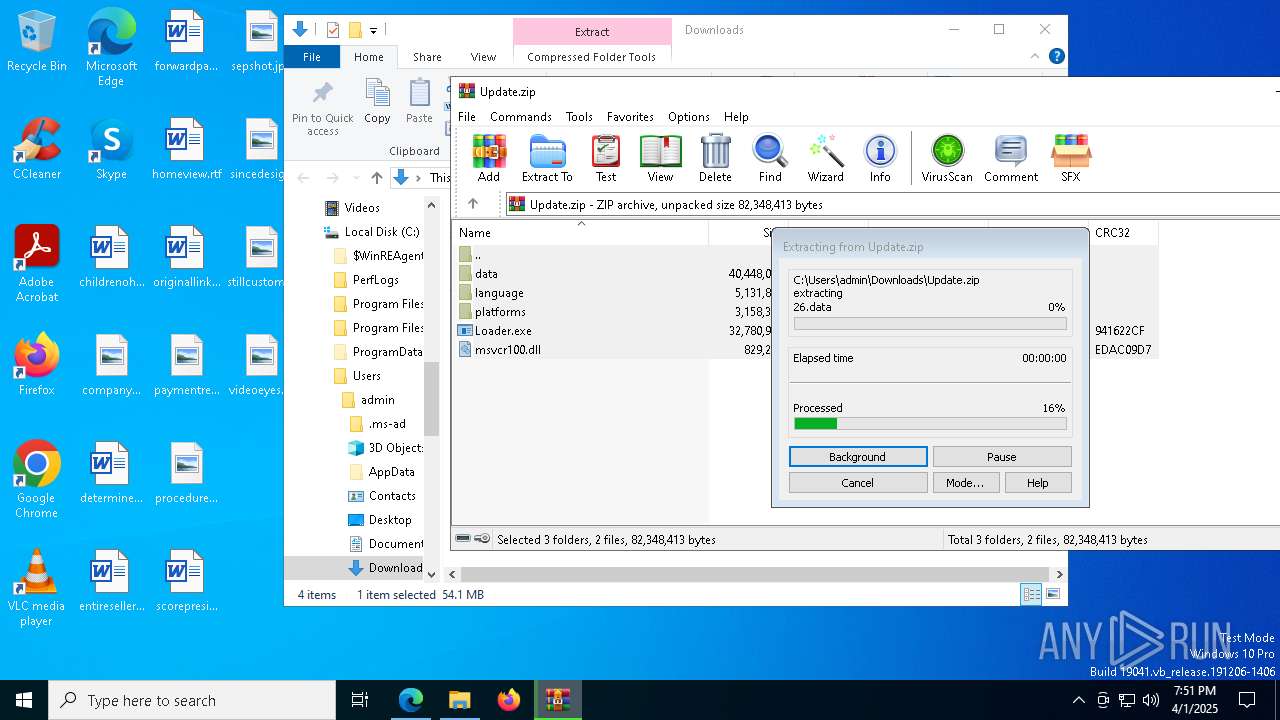
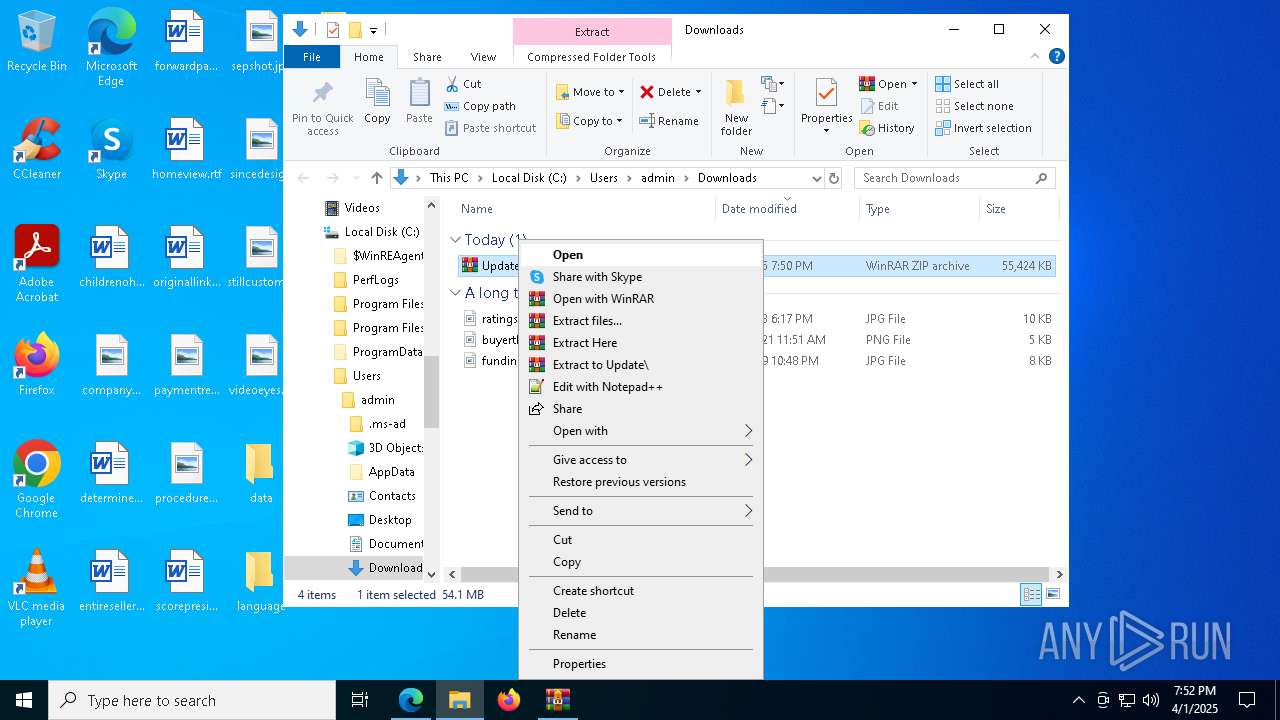
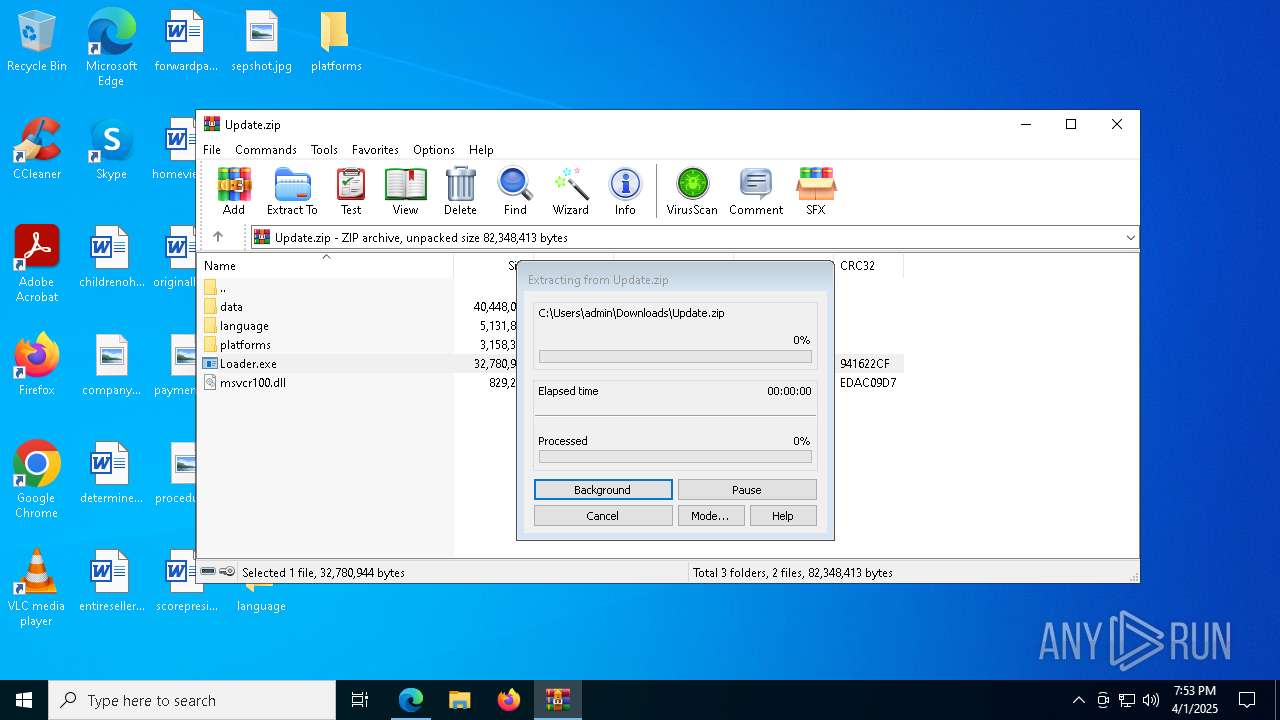
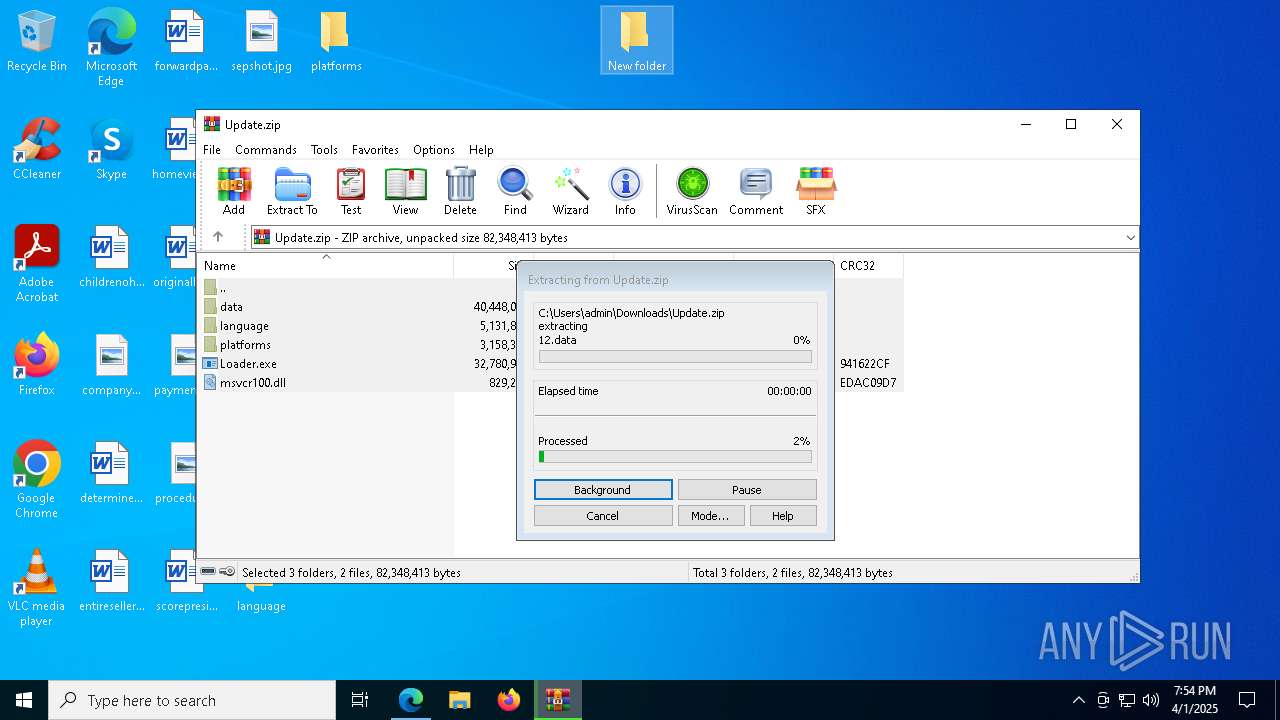
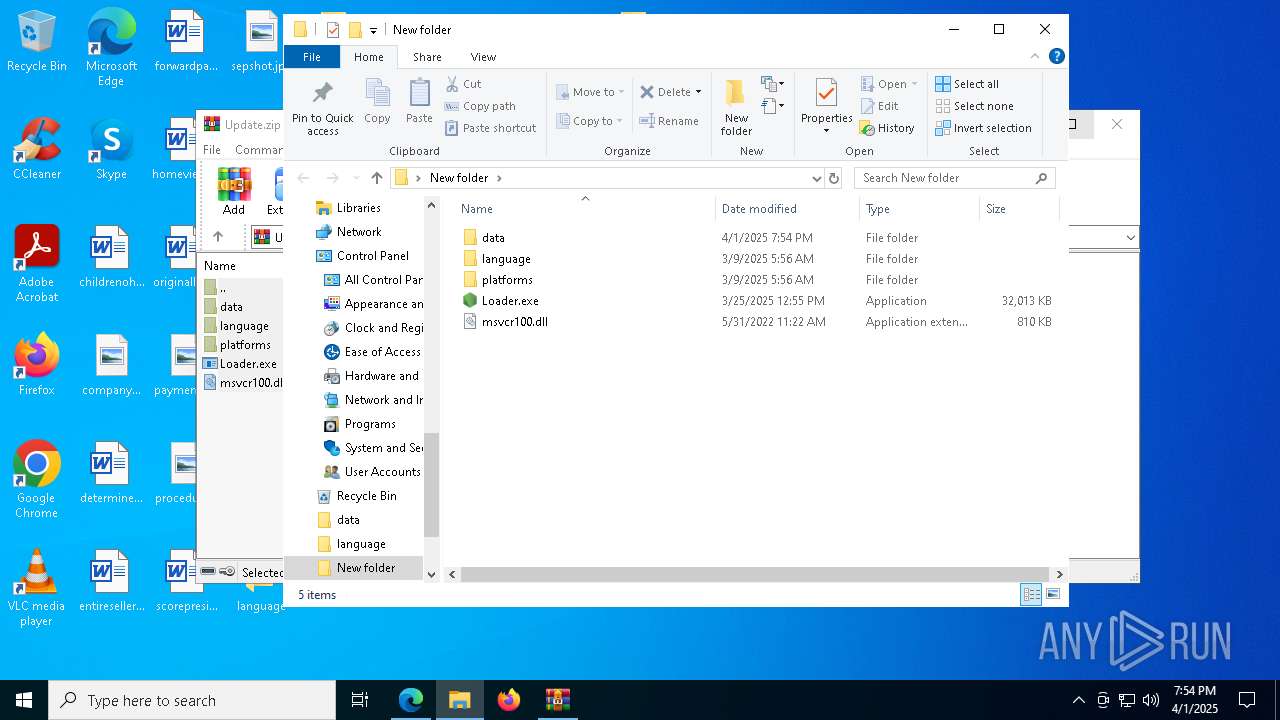
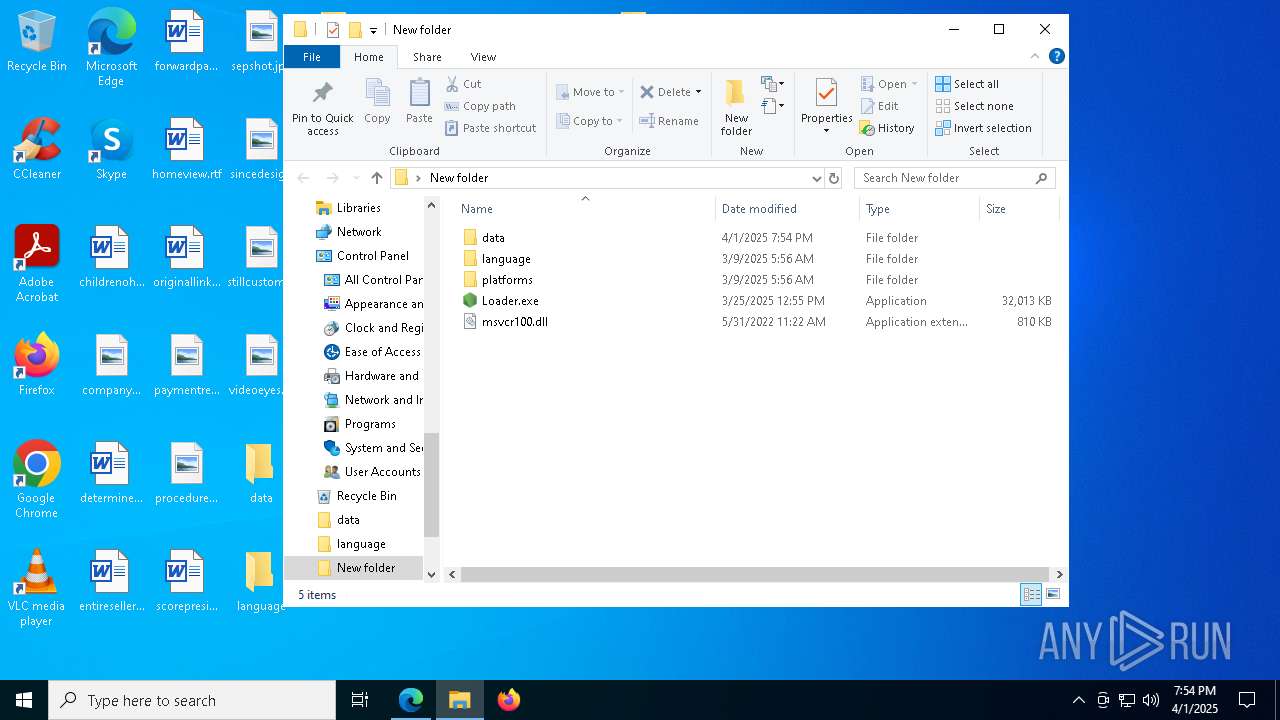
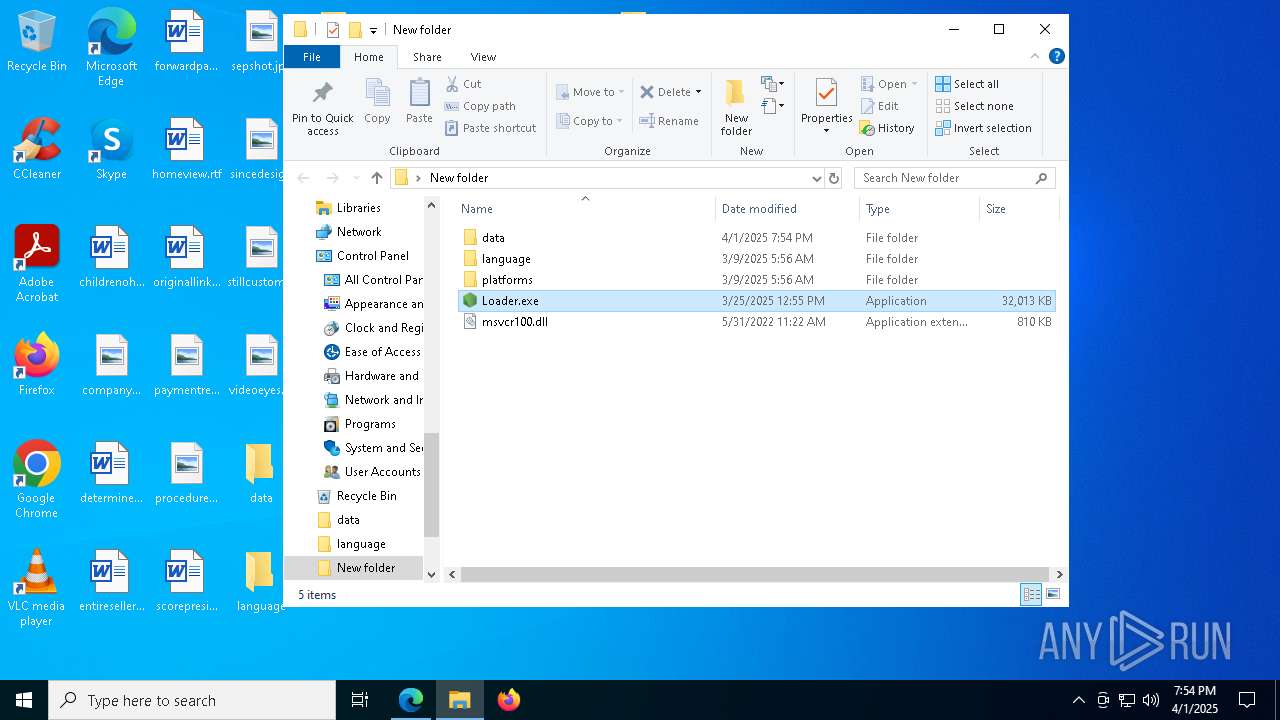
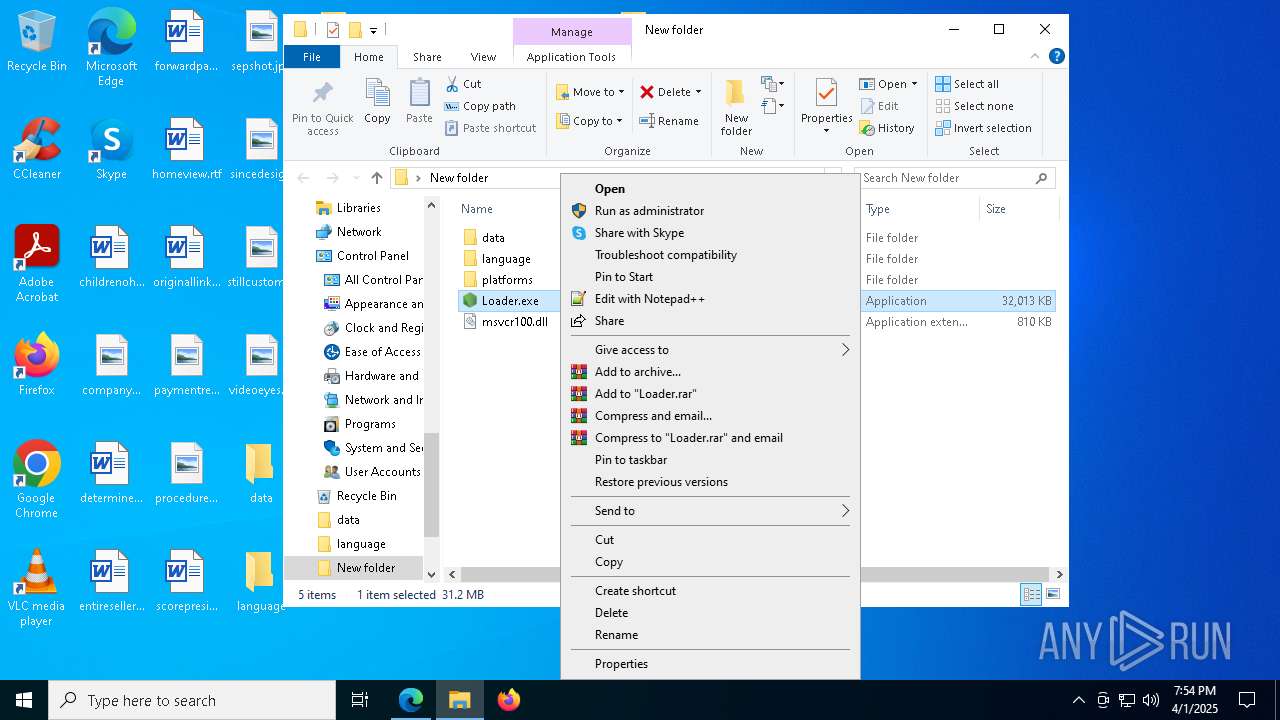
Manual execution by a user
- WinRAR.exe (PID: 6272)
- Loader.exe (PID: 6512)
- Loader.exe (PID: 2040)
- WinRAR.exe (PID: 7944)
- Loader.exe (PID: 5408)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 5680)
The sample compiled with english language support
- WinRAR.exe (PID: 6272)
- WinRAR.exe (PID: 7944)
Reads product name
- Loader.exe (PID: 5892)
- Loader.exe (PID: 2140)
- Loader.exe (PID: 6512)
- Loader.exe (PID: 2596)
- Loader.exe (PID: 2040)
- Loader.exe (PID: 4452)
- Loader.exe (PID: 5408)
- Loader.exe (PID: 2096)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 1672)
- Loader.exe (PID: 2244)
- Loader.exe (PID: 5680)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6272)
- WinRAR.exe (PID: 7944)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1300)
- WMIC.exe (PID: 5576)
- WMIC.exe (PID: 6344)
- WMIC.exe (PID: 5796)
- WMIC.exe (PID: 1240)
- WMIC.exe (PID: 4868)
- WMIC.exe (PID: 1004)
- WMIC.exe (PID: 4056)
- WMIC.exe (PID: 5576)
- WMIC.exe (PID: 7956)
- WMIC.exe (PID: 7844)
- WMIC.exe (PID: 8028)
Application launched itself
- msedge.exe (PID: 4996)
The executable file from the user directory is run by the Powershell process
- Loader.exe (PID: 2140)
- Loader.exe (PID: 2244)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 6384)
- powershell.exe (PID: 1532)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 2776)
- powershell.exe (PID: 5984)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 444)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 6640)
- powershell.exe (PID: 3304)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 6384)
- powershell.exe (PID: 1532)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5984)
- powershell.exe (PID: 2776)
- powershell.exe (PID: 444)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 6640)
- powershell.exe (PID: 3304)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- Loader.exe (PID: 2140)
- Loader.exe (PID: 2596)
- Loader.exe (PID: 4452)
- Loader.exe (PID: 2096)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 2244)
Reads the software policy settings
- slui.exe (PID: 2384)
- slui.exe (PID: 7972)
Found Base64 encoded reference to WMI classes (YARA)
- Loader.exe (PID: 2140)
- Loader.exe (PID: 2596)
- Loader.exe (PID: 4452)
- Loader.exe (PID: 2096)
- Loader.exe (PID: 5384)
- Loader.exe (PID: 2244)
Checks proxy server information
- slui.exe (PID: 7972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
438
Monitored processes
294
Malicious processes
31
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | powershell -Command "Start-Process 'C:\Users\admin\Desktop\Loader.exe' -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell -Command "Start-Process 'C:\Users\admin\Desktop\Loader.exe' -Verb RunAs"" | C:\Windows\System32\cmd.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5792 --field-trial-handle=2344,i,12747629295780216459,5837334666216043318,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData'"" | C:\Windows\System32\cmd.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | C:\WINDOWS\system32\cmd.exe /d /s /c "net session" | C:\Windows\System32\cmd.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6804 --field-trial-handle=2344,i,12747629295780216459,5837334666216043318,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
164 803
Read events
164 751
Write events
39
Delete events
13
Modification events
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4A9E542253902F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CDC3642253902F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5F4120BC-2248-4EDE-A898-10E89E399FF9} | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E7E648D5-8DBE-4668-9D41-D16CCAEA0CDC} | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0F52A02253902F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
34
Suspicious files
911
Text files
117
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bf89.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bf89.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bf99.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bf99.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bf99.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
105
TCP/UDP connections
55
DNS requests
61
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5436 | SIHClient.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.67.160.244:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6592 | svchost.exe | HEAD | 200 | 2.19.252.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/23e5dd61-e224-4d56-858f-6ee086574ada?P1=1744052663&P2=404&P3=2&P4=BoqbxlhLgMmotG5IVTvwIBxH1iiNYW6AchV%2bGsZufmUYgFIVCUVseoUXVW%2f862Hsu3YbOEj8hG2tlrtbzhV5VA%3d%3d | unknown | — | — | whitelisted |
5436 | SIHClient.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 206 | 2.19.252.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/23e5dd61-e224-4d56-858f-6ee086574ada?P1=1744052663&P2=404&P3=2&P4=BoqbxlhLgMmotG5IVTvwIBxH1iiNYW6AchV%2bGsZufmUYgFIVCUVseoUXVW%2f862Hsu3YbOEj8hG2tlrtbzhV5VA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 206 | 2.19.252.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/23e5dd61-e224-4d56-858f-6ee086574ada?P1=1744052663&P2=404&P3=2&P4=BoqbxlhLgMmotG5IVTvwIBxH1iiNYW6AchV%2bGsZufmUYgFIVCUVseoUXVW%2f862Hsu3YbOEj8hG2tlrtbzhV5VA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 206 | 2.19.252.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/23e5dd61-e224-4d56-858f-6ee086574ada?P1=1744052663&P2=404&P3=2&P4=BoqbxlhLgMmotG5IVTvwIBxH1iiNYW6AchV%2bGsZufmUYgFIVCUVseoUXVW%2f862Hsu3YbOEj8hG2tlrtbzhV5VA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 206 | 2.19.252.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/23e5dd61-e224-4d56-858f-6ee086574ada?P1=1744052663&P2=404&P3=2&P4=BoqbxlhLgMmotG5IVTvwIBxH1iiNYW6AchV%2bGsZufmUYgFIVCUVseoUXVW%2f862Hsu3YbOEj8hG2tlrtbzhV5VA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | HEAD | 200 | 2.19.252.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cd4e6fbf-c0e9-4dc2-9e3d-7f538bc7435a?P1=1744052662&P2=404&P3=2&P4=Zii9l7UG2Xg6om1Y2vfxbYPPFKDWD%2fe9%2fGLMOUttAmz5wLg90Z1f0J7d6eYb5j7dYjBrCSsvvXRNHVT0lmPswA%3d%3d | unknown | — | — | whitelisted |
6592 | svchost.exe | GET | 200 | 2.19.252.83:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cd4e6fbf-c0e9-4dc2-9e3d-7f538bc7435a?P1=1744052662&P2=404&P3=2&P4=Zii9l7UG2Xg6om1Y2vfxbYPPFKDWD%2fe9%2fGLMOUttAmz5wLg90Z1f0J7d6eYb5j7dYjBrCSsvvXRNHVT0lmPswA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.83.4.138:80 | crl.microsoft.com | Akamai International B.V. | AT | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4996 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7384 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7384 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |