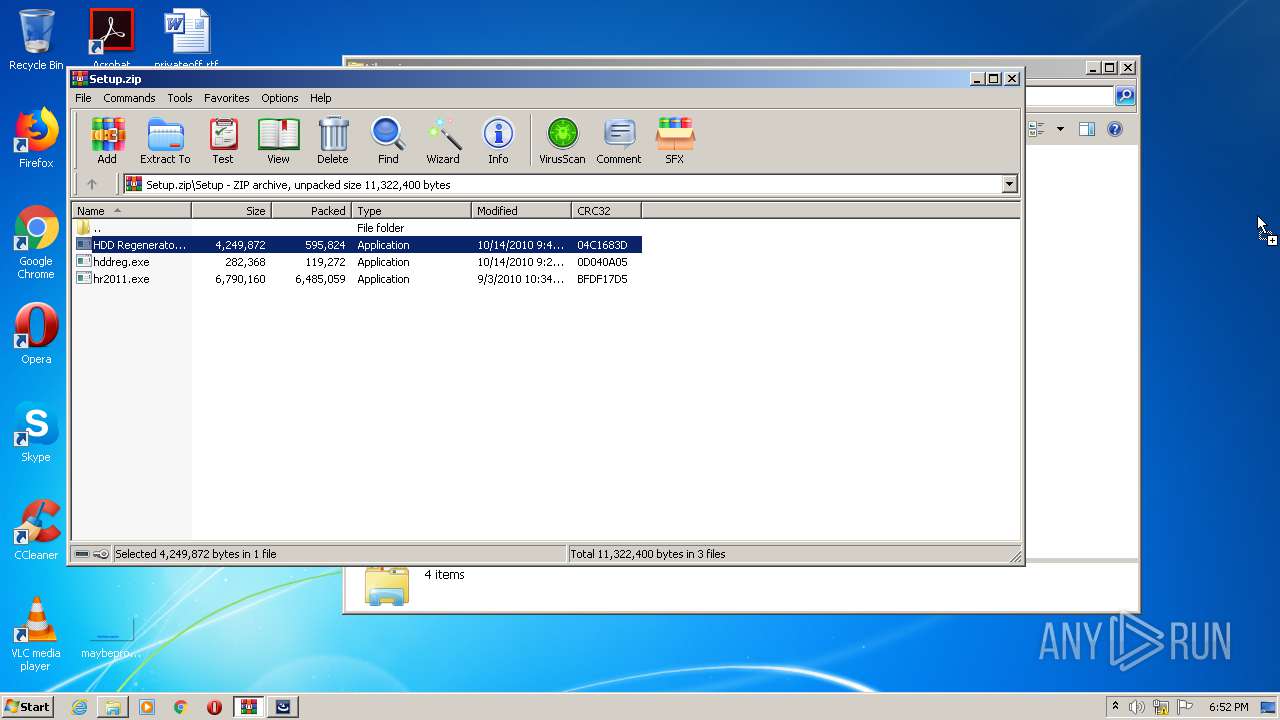
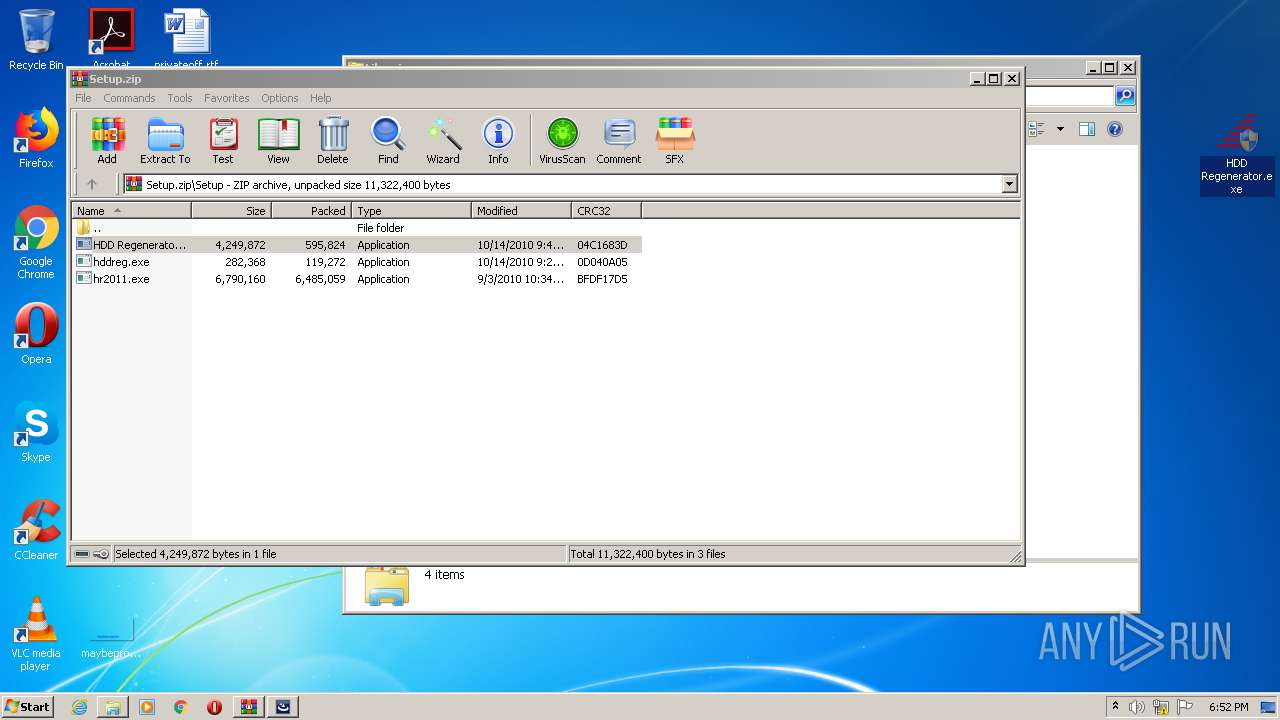
| File name: | Setup.zip |
| Full analysis: | https://app.any.run/tasks/2449d9a3-22e5-4d31-a40d-d6fc7ae651f3 |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2020, 17:52:07 |
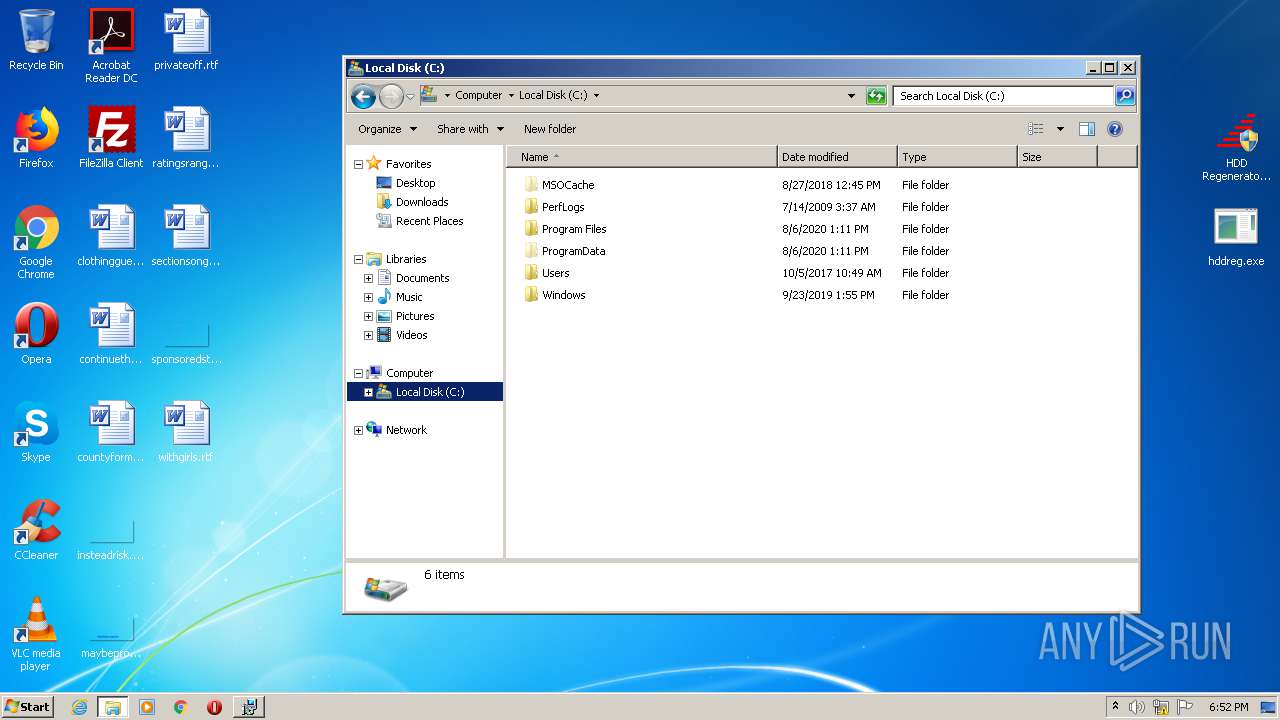
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E85B97123837FADF38638ADF5C6454CB |
| SHA1: | C3C9AA72B625925AB230F376ABB75470FAE1AD40 |
| SHA256: | E24104F514871ED2D352BE6C59D37EA11D655188E60BCEEB1A36EBCBA35A0BEE |
| SSDEEP: | 196608:XD9cbtZ+cGfmx719qk1DWWTarxoD2x3qBdi:zSZsI719RjTarx13qBs |
MALICIOUS
Application was dropped or rewritten from another process
- hr2011.exe (PID: 4044)
- hr2011.exe (PID: 2668)
- Shell.exe (PID: 2720)
- HDD Regenerator.exe (PID: 1020)
- HDD Regenerator.exe (PID: 836)
- HDD Regenerator.exe (PID: 960)
- Shell.exe (PID: 3984)
- Shell.exe (PID: 2992)
Changes settings of System certificates
- MSIEXEC.EXE (PID: 2916)
Loads dropped or rewritten executable
- Shell.exe (PID: 2720)
- HDD Regenerator.exe (PID: 960)
- Shell.exe (PID: 3984)
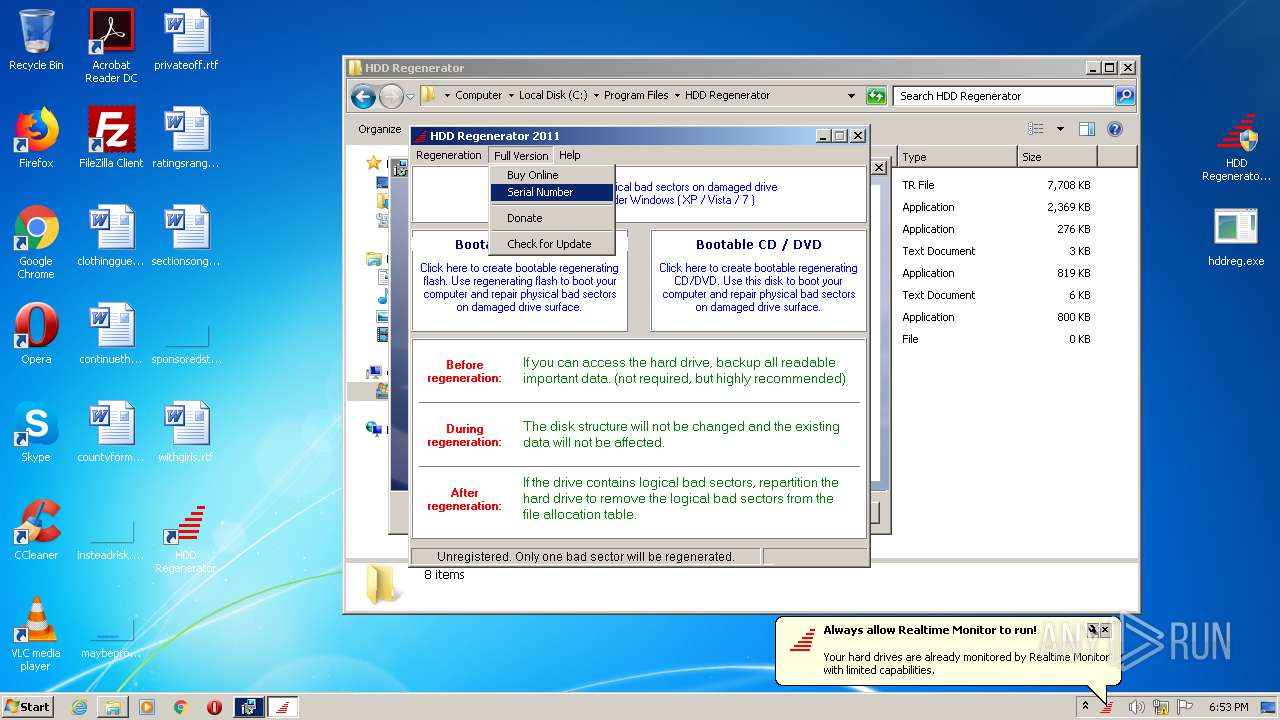
Changes the autorun value in the registry
- HDD Regenerator.exe (PID: 960)
SUSPICIOUS
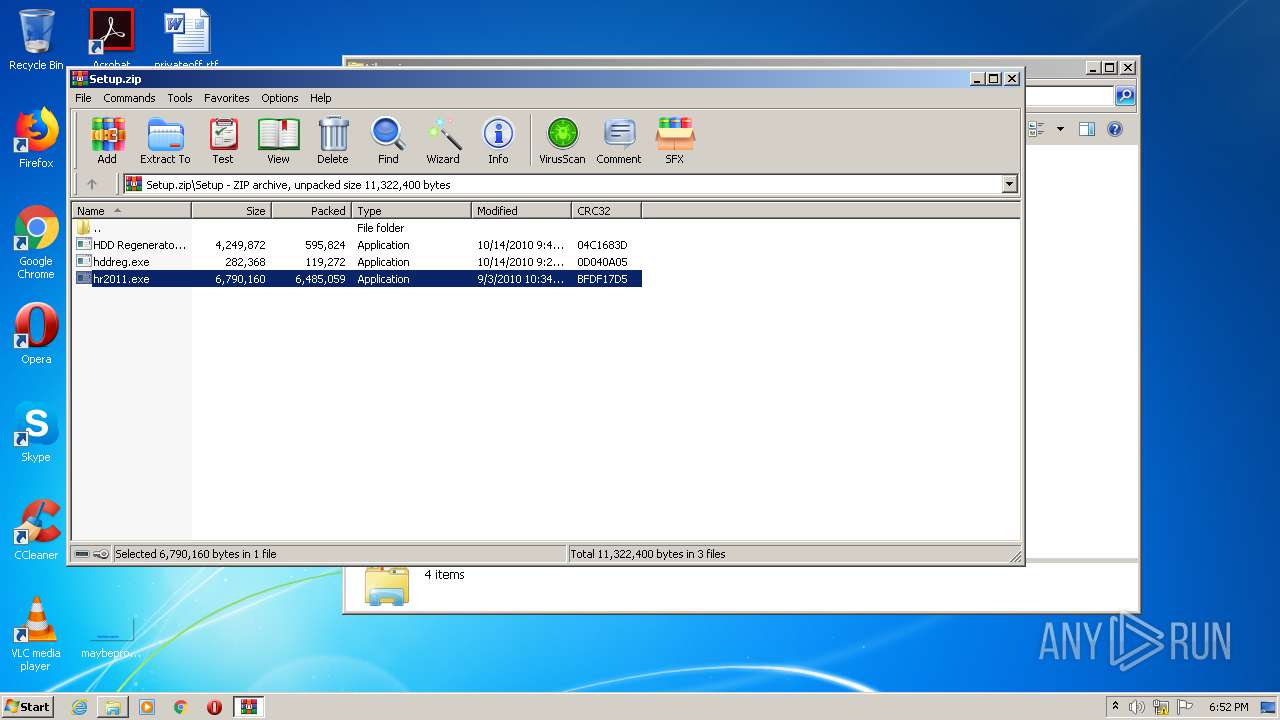
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3068)
- DllHost.exe (PID: 3612)
Adds / modifies Windows certificates
- MSIEXEC.EXE (PID: 2916)
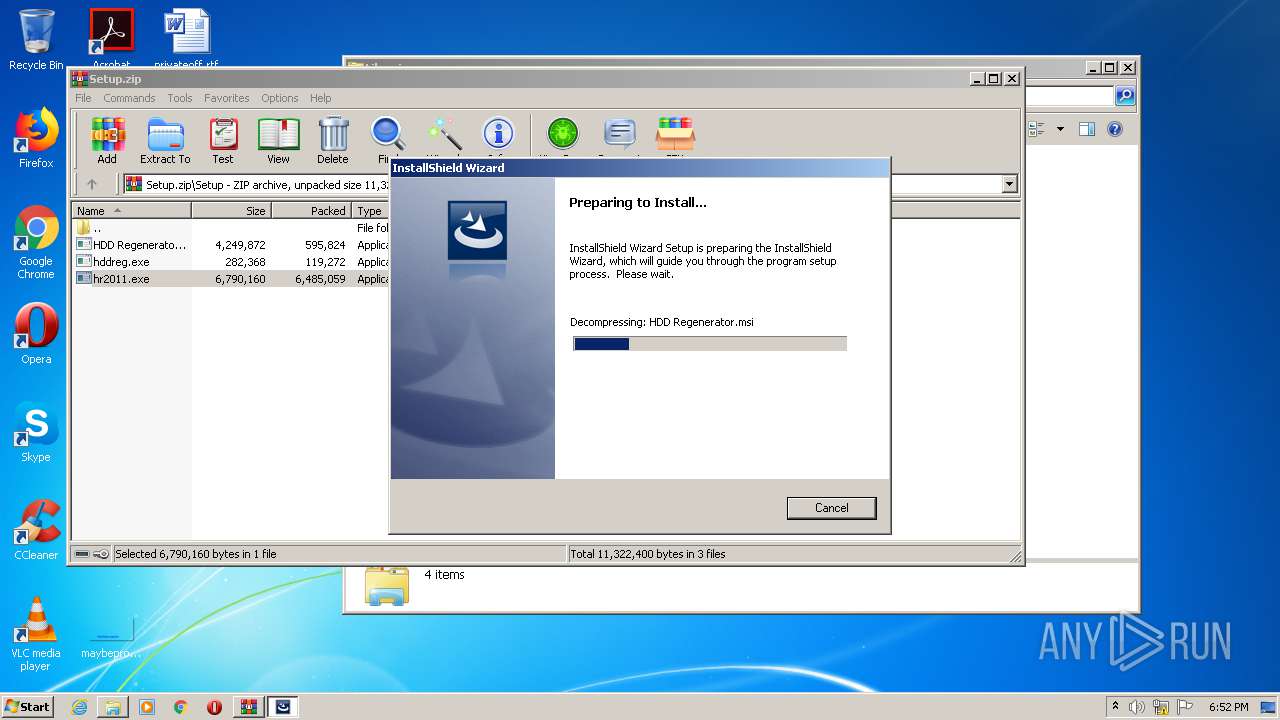
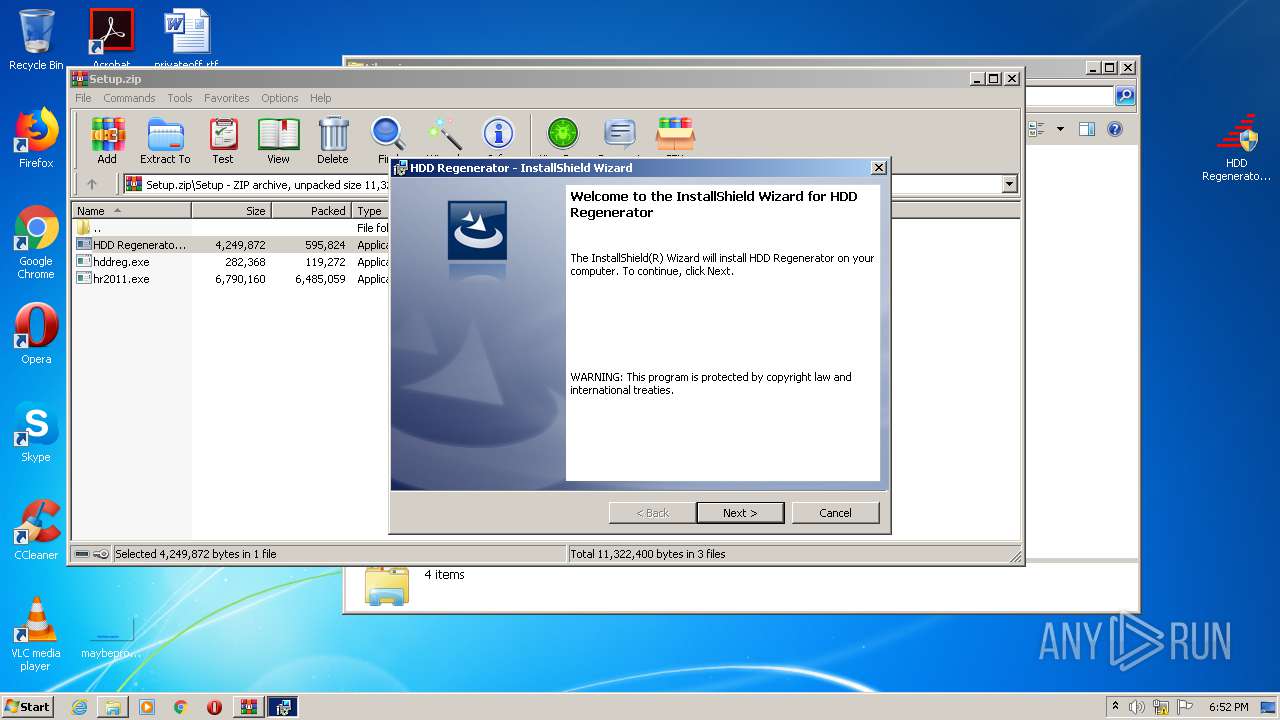
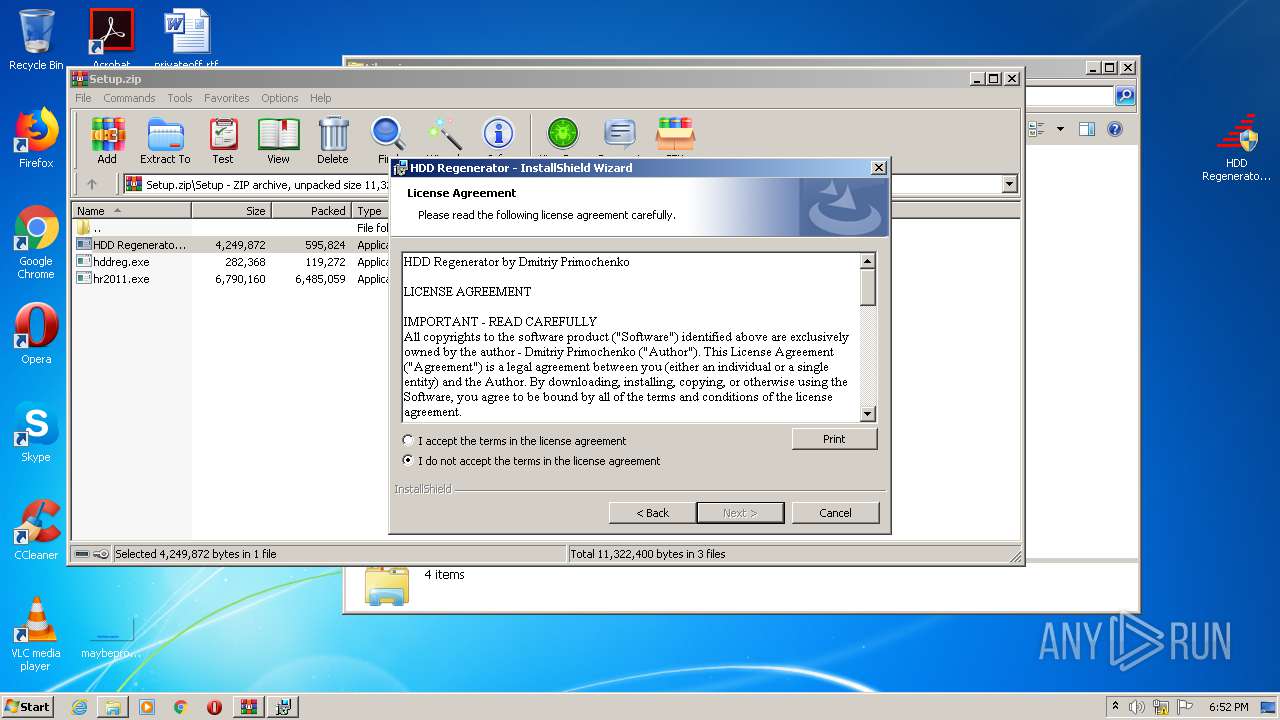
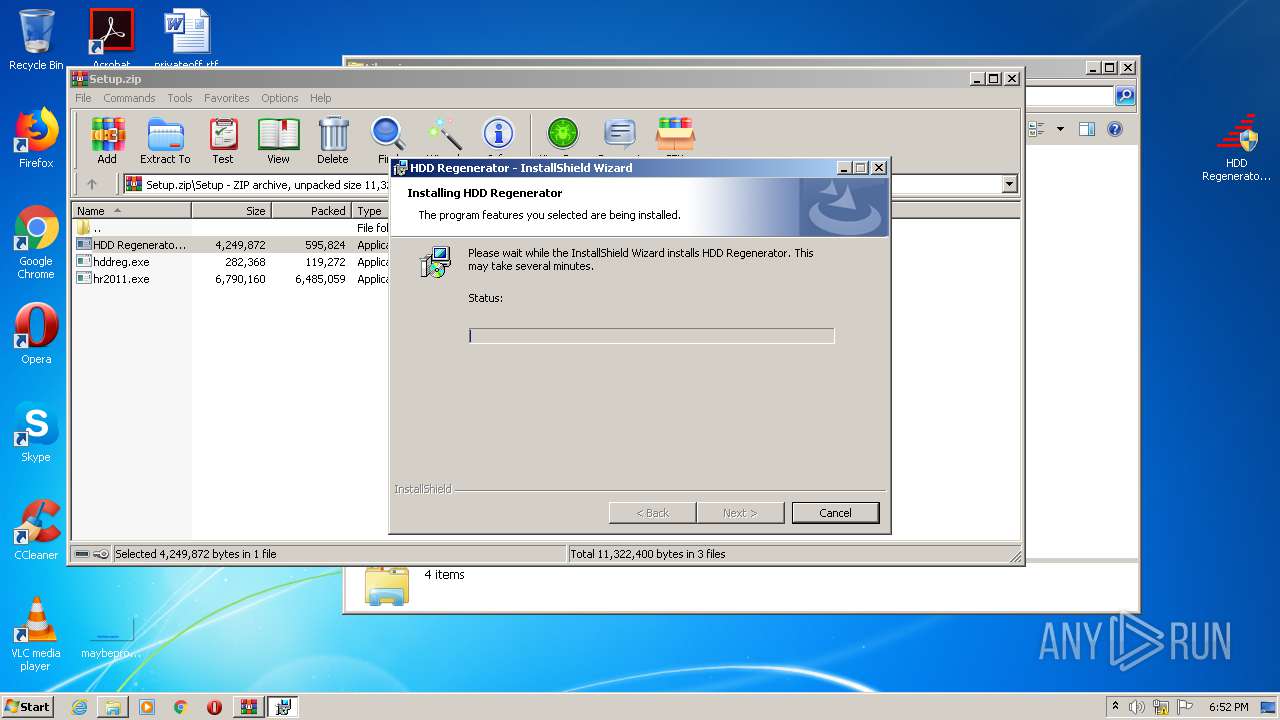
Starts Microsoft Installer
- hr2011.exe (PID: 4044)
Application launched itself
- HDD Regenerator.exe (PID: 836)
- Shell.exe (PID: 2720)
Creates COM task schedule object
- HDD Regenerator.exe (PID: 960)
Low-level read access rights to disk partition
- HDD Regenerator.exe (PID: 960)
Reads Internet Cache Settings
- HDD Regenerator.exe (PID: 960)
Executed via COM
- DllHost.exe (PID: 3612)
INFO
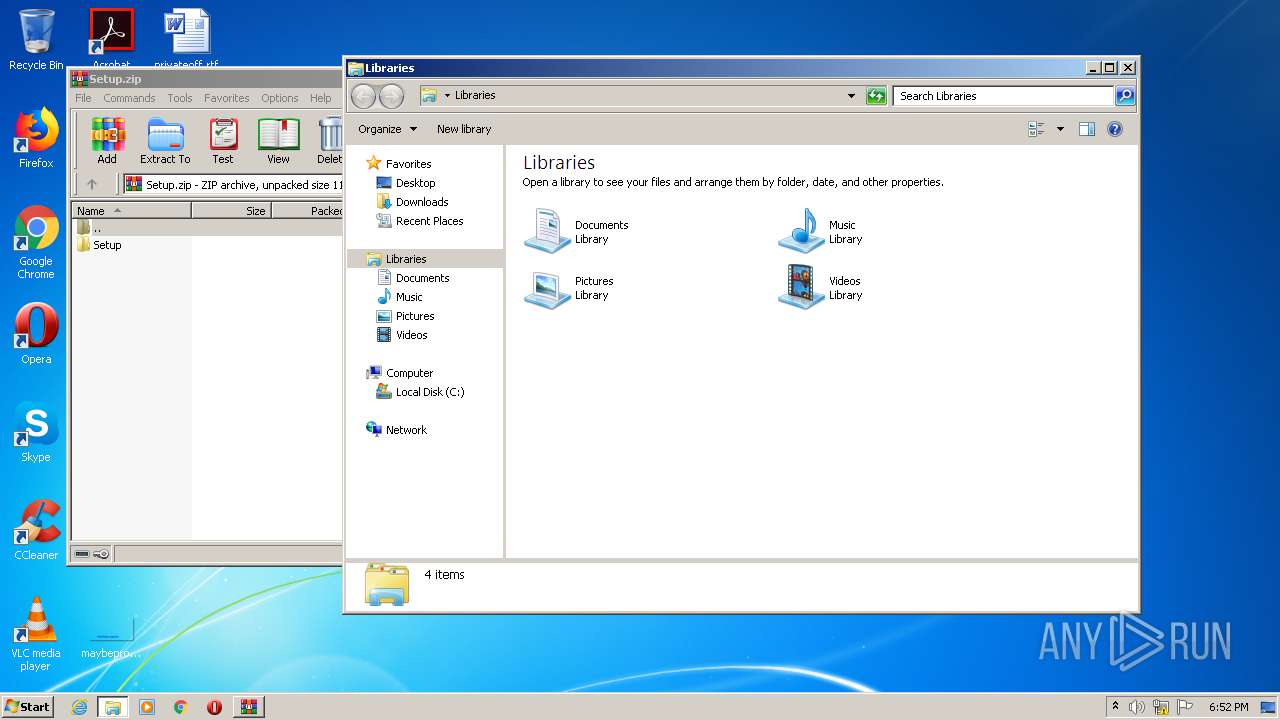
Manual execution by user
- explorer.exe (PID: 2672)
- Shell.exe (PID: 2720)
- Shell.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:09:07 19:47:21 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Setup/ |
Total processes
60
Monitored processes
12
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
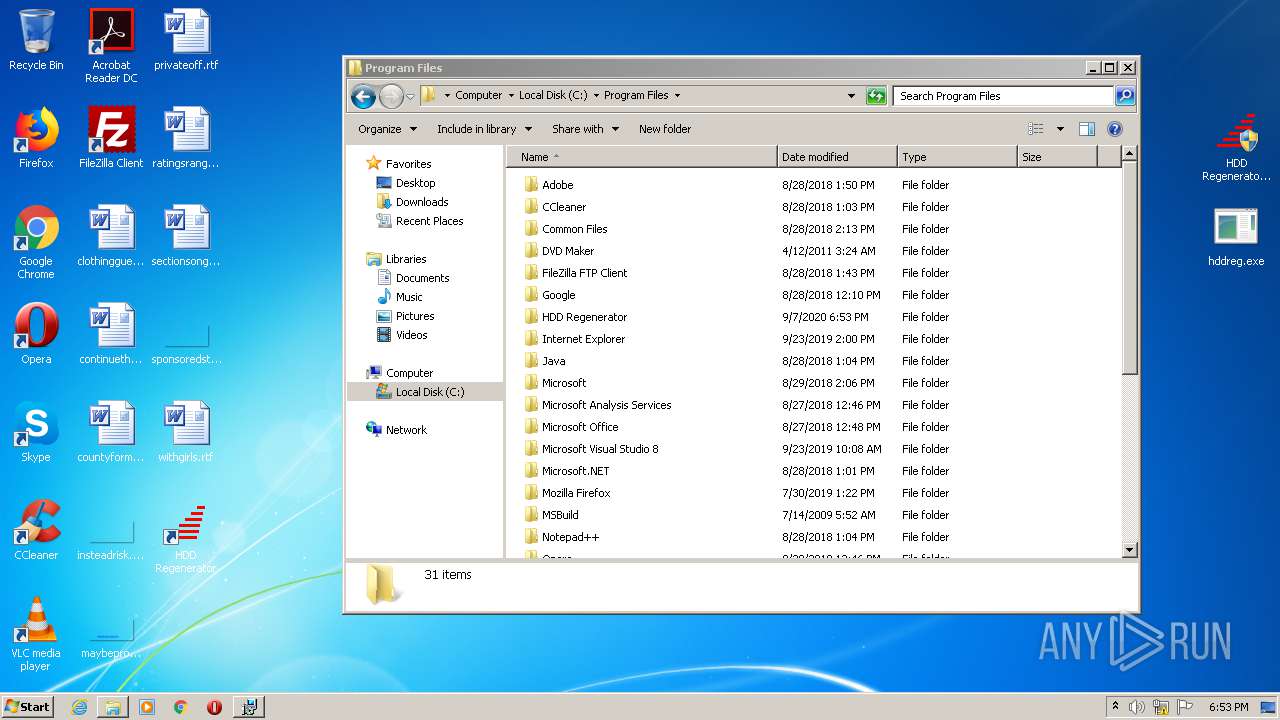
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
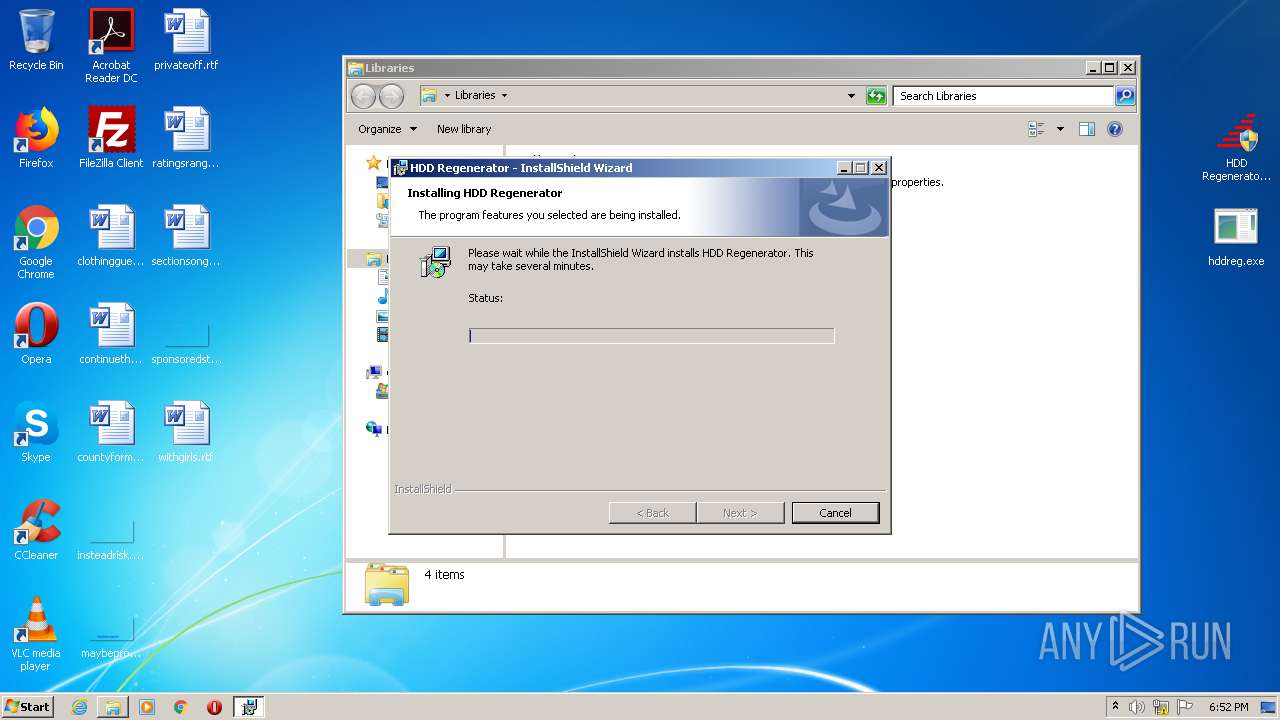
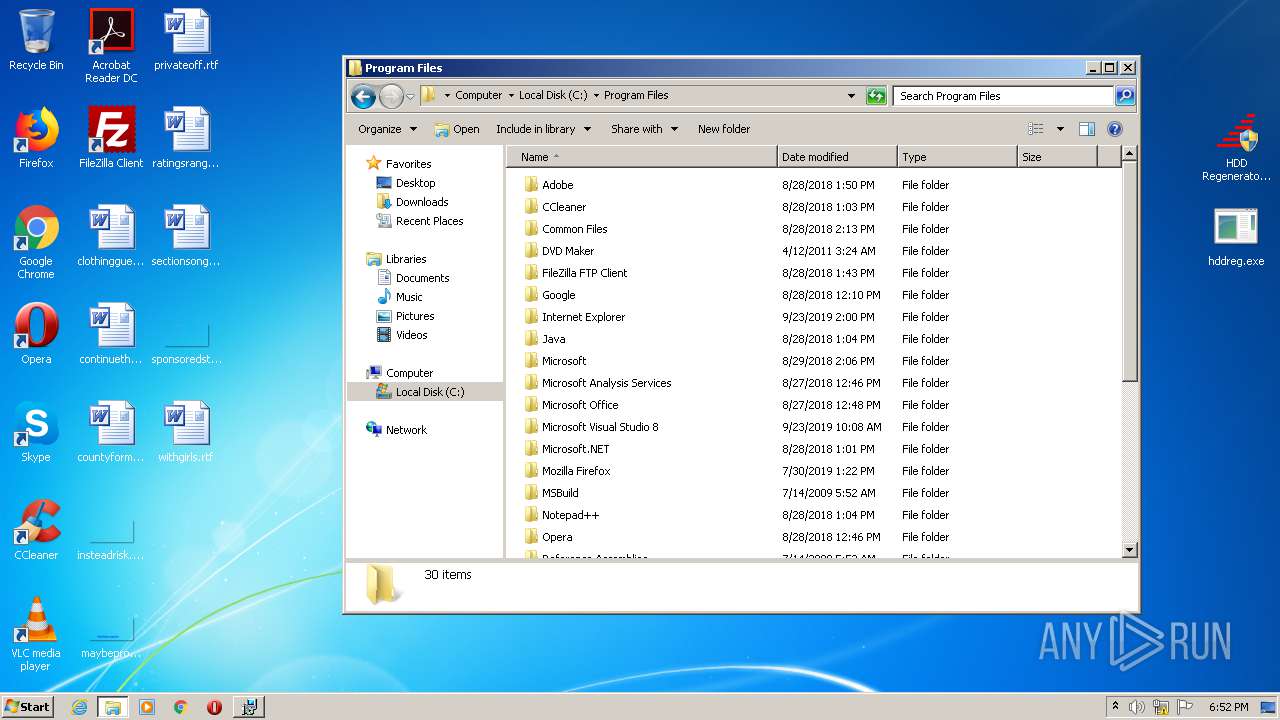
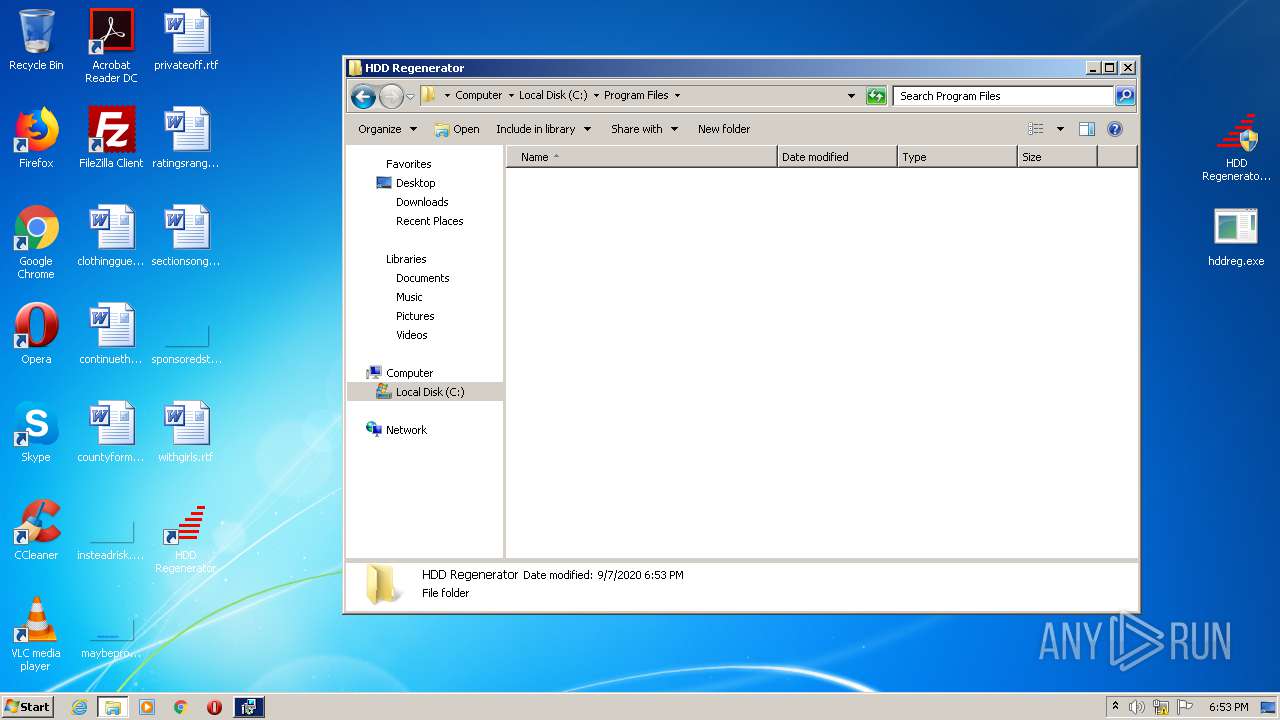
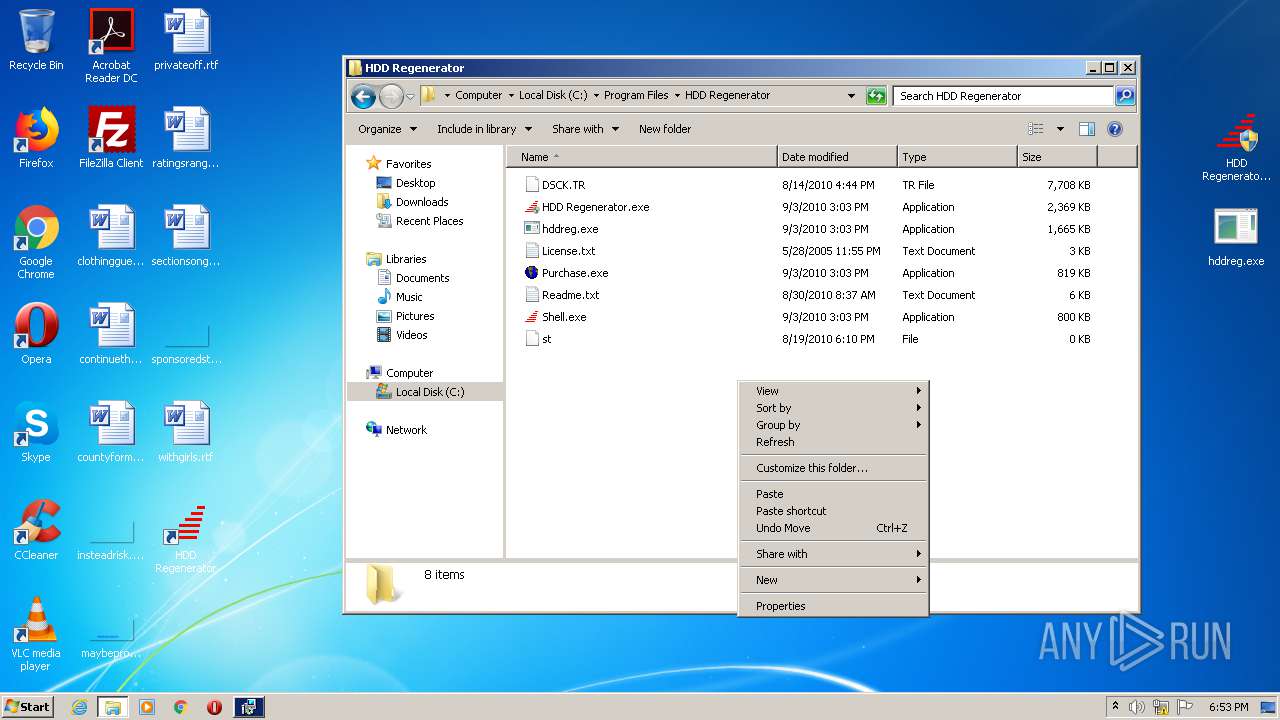
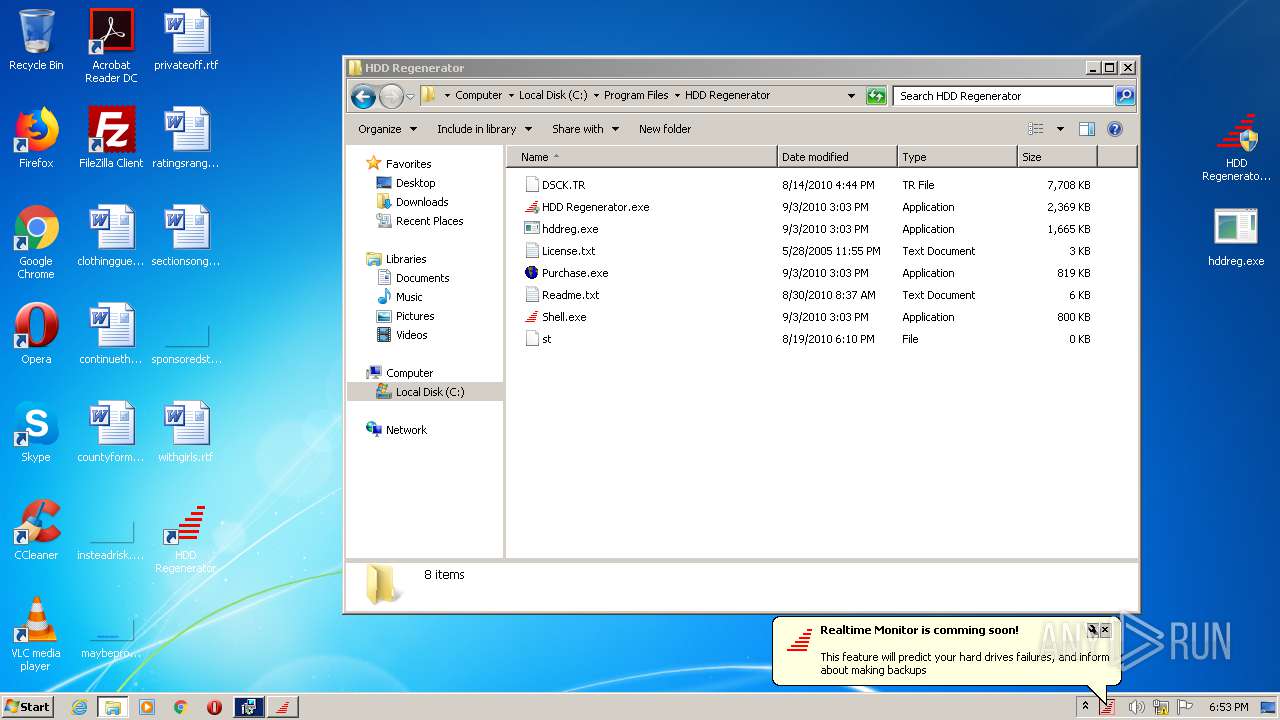
| 836 | "C:\Program Files\HDD Regenerator\HDD Regenerator.exe" | C:\Program Files\HDD Regenerator\HDD Regenerator.exe | Shell.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
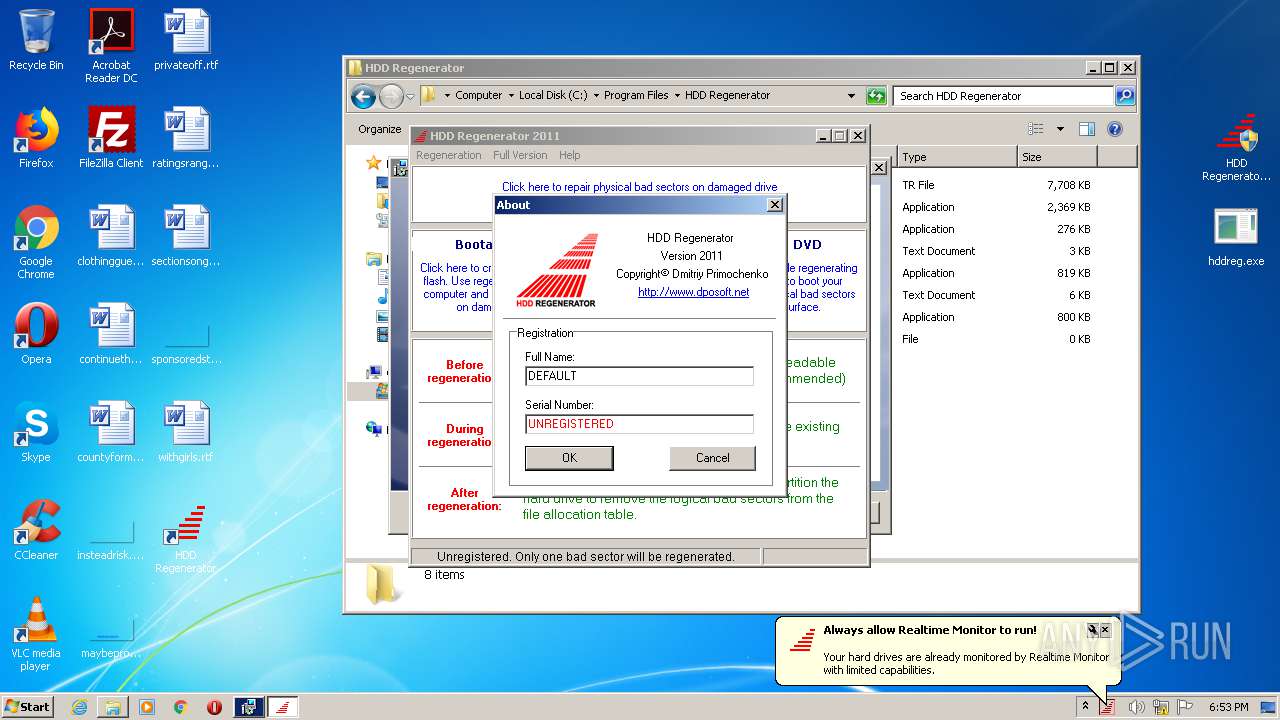
| 960 | "C:\Program Files\HDD Regenerator\HDD Regenerator.exe" | C:\Program Files\HDD Regenerator\HDD Regenerator.exe | HDD Regenerator.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\HDD Regenerator\HDD Regenerator.exe" | C:\Program Files\HDD Regenerator\HDD Regenerator.exe | — | Shell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.48252\Setup\hr2011.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.48252\Setup\hr2011.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Abstradrome Integrity Level: MEDIUM Description: Setup Launcher Unicode Exit code: 3221226540 Version: 20.11.0011 Modules
| |||||||||||||||
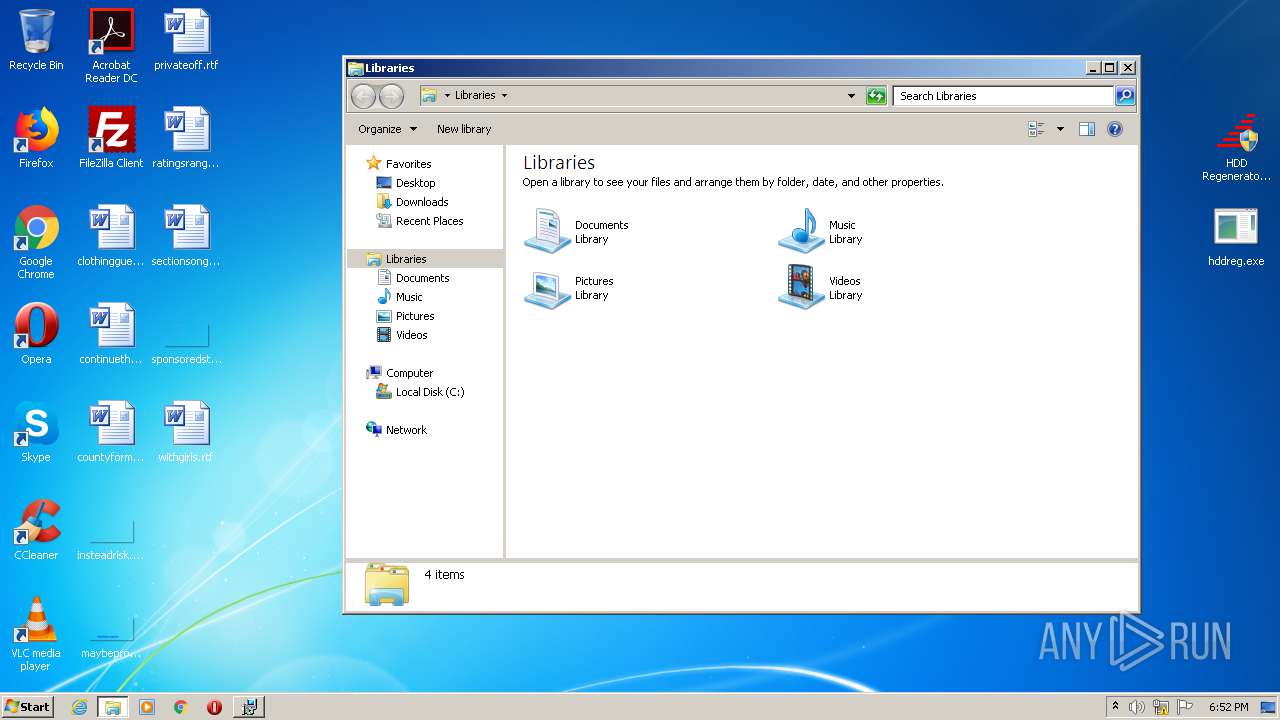
| 2672 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | "C:\Program Files\HDD Regenerator\Shell.exe" | C:\Program Files\HDD Regenerator\Shell.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2916 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Downloaded Installations\{5153A73C-CEE4-41F1-A222-8C9F3736F38D}\HDD Regenerator.msi" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.48252\Setup" SETUPEXENAME="hr2011.exe" | C:\Windows\system32\MSIEXEC.EXE | — | hr2011.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | "C:\Program Files\HDD Regenerator\Shell.exe" | C:\Program Files\HDD Regenerator\Shell.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
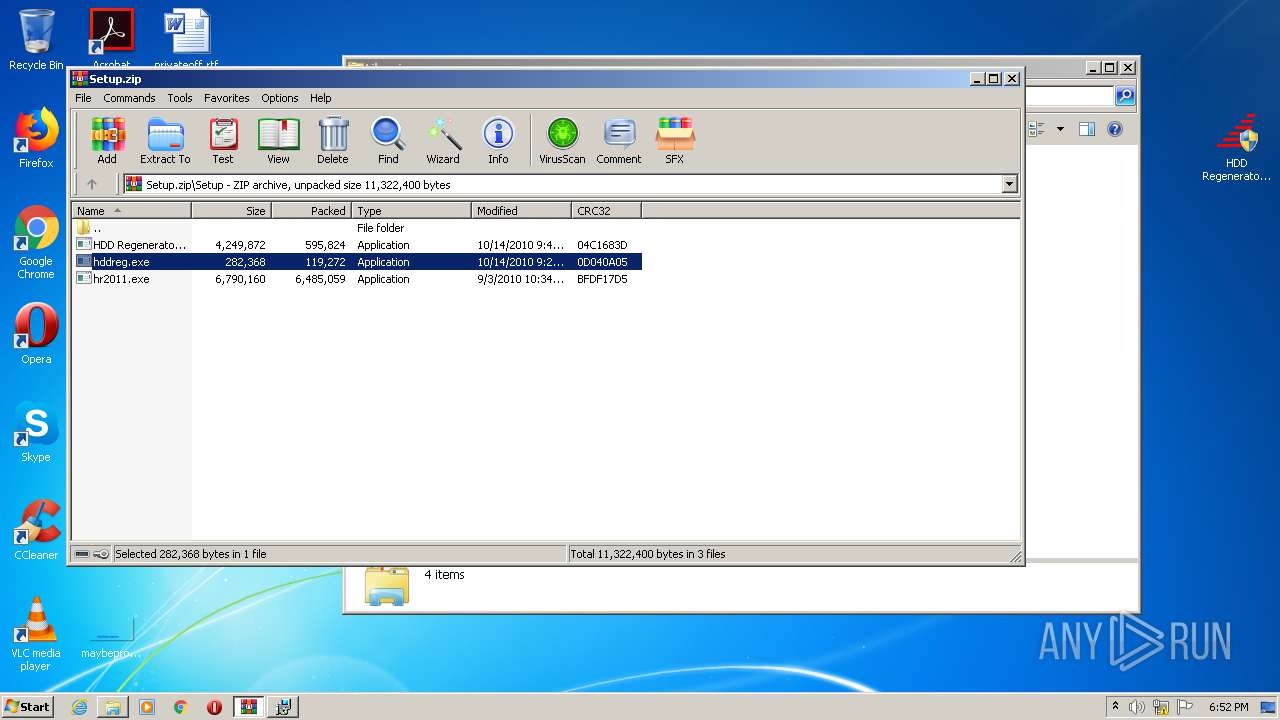
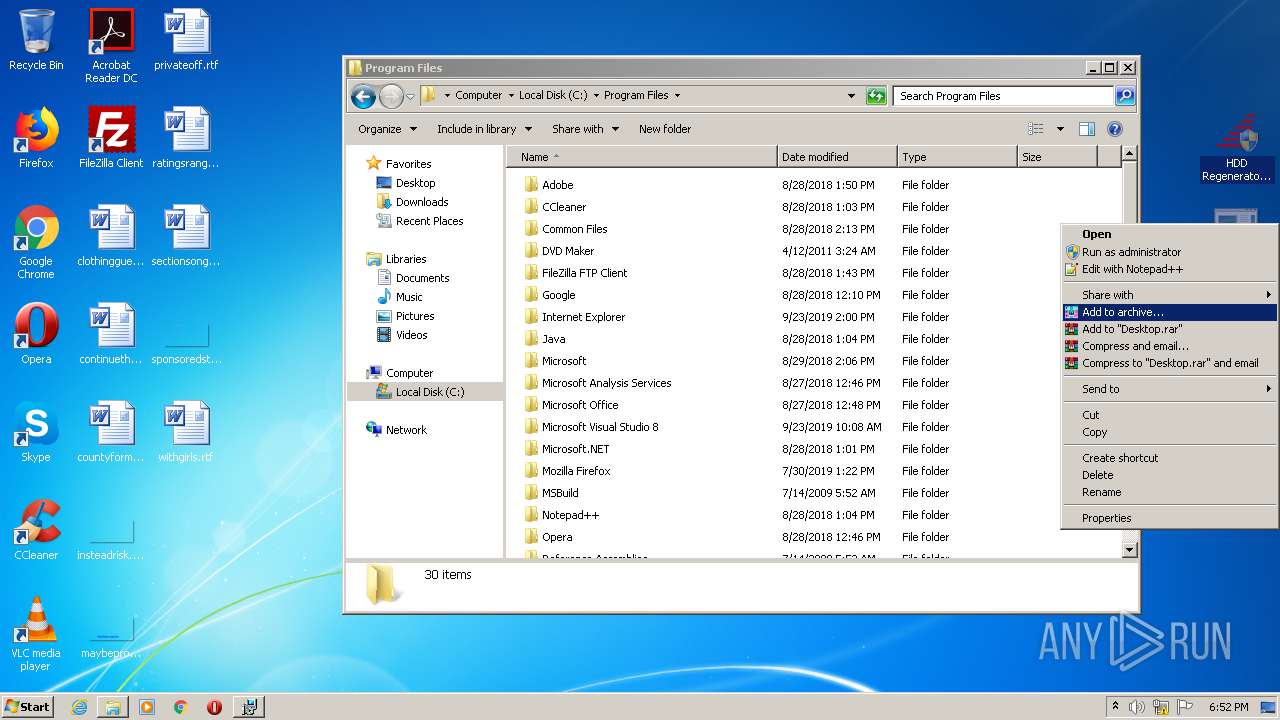
| 3068 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Setup.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3612 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
819
Read events
745
Write events
68
Delete events
6
Modification events
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Setup.zip | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Temp\_is35FE.tmp | — | |
MD5:— | SHA256:— | |||
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Temp\_is35FF.tmp | — | |
MD5:— | SHA256:— | |||
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Temp\_is3601.tmp | — | |
MD5:— | SHA256:— | |||
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Temp\~3600.tmp | — | |
MD5:— | SHA256:— | |||
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Temp\_is3621.tmp | — | |
MD5:— | SHA256:— | |||
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Temp\{C7015B6D-95BE-414E-9577-CFC8AAB4FF27}\HDD Regenerator.msi | — | |
MD5:— | SHA256:— | |||
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Downloaded Installations\{5153A73C-CEE4-41F1-A222-8C9F3736F38D}\HDD Regenerator.msi | — | |
MD5:— | SHA256:— | |||
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Temp\_is372D.tmp | — | |
MD5:— | SHA256:— | |||
| 4044 | hr2011.exe | C:\Users\admin\AppData\Local\Temp\~372C.tmp | — | |
MD5:— | SHA256:— | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3068.48766\Setup\HDD Regenerator.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
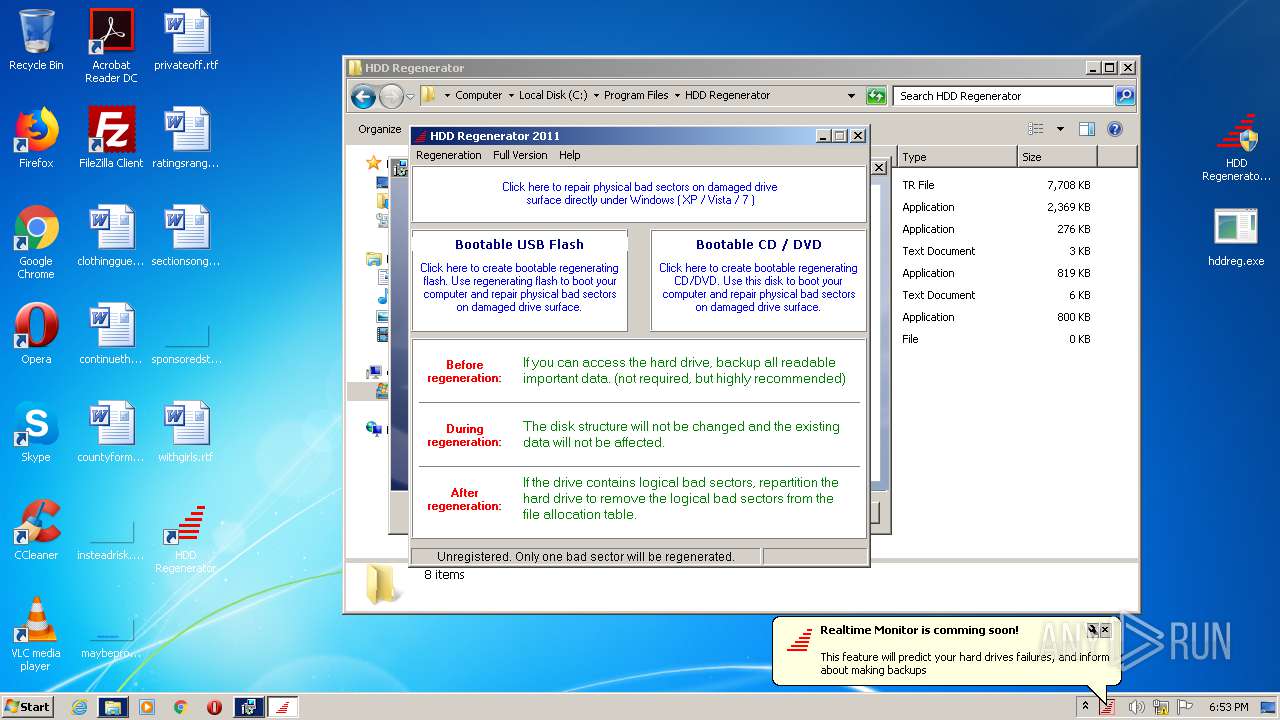
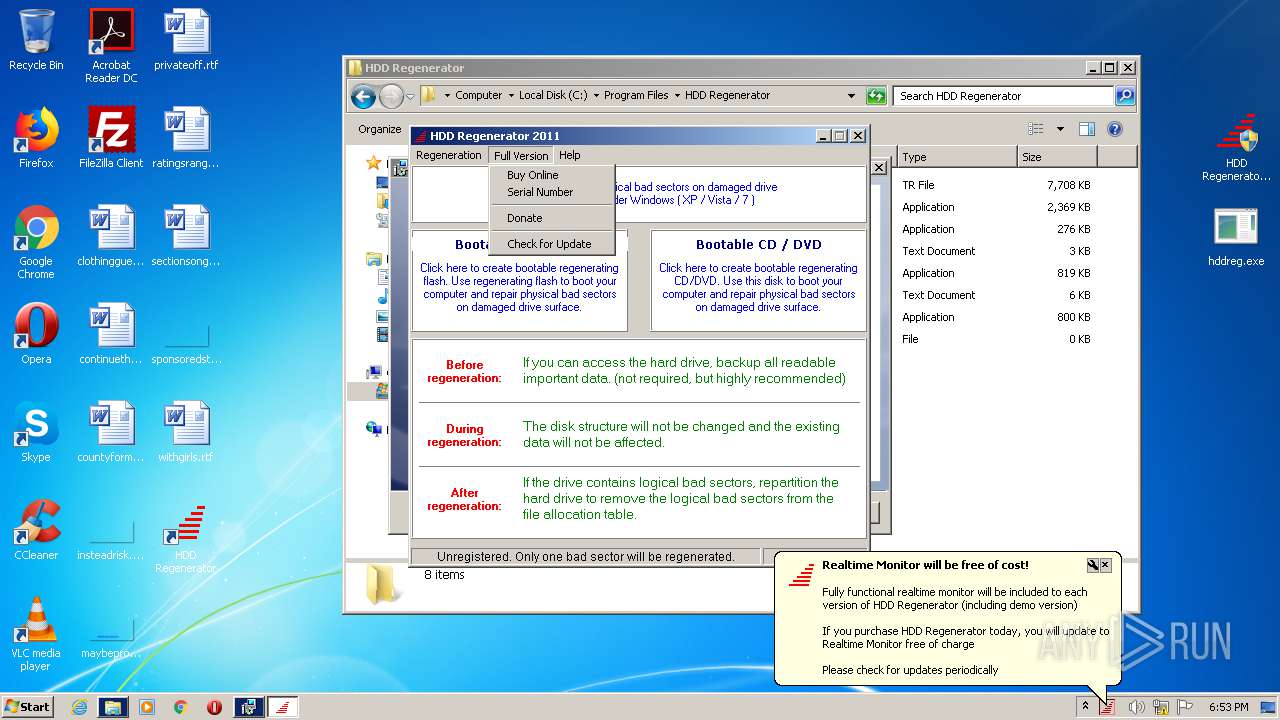
960 | HDD Regenerator.exe | GET | 200 | 217.112.43.73:80 | http://www.dposoft.net/vers/hr2011/kshv2w110 | GB | html | 173 b | suspicious |
960 | HDD Regenerator.exe | GET | 200 | 217.112.43.73:80 | http://www.dposoft.net/vers/hr2011/kshv2w110?40343735332D42313244 | GB | html | 173 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 217.112.43.73:80 | www.dposoft.net | Utransit International Carrier Limited | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dposoft.net |
| suspicious |
Threats
Process | Message |
|---|---|
HDD Regenerator.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
HDD Regenerator.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
HDD Regenerator.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |