| File name: | 4kvideodownloader_4.19.4_x64_online.exe |
| Full analysis: | https://app.any.run/tasks/79776aa8-d26d-4da6-ac03-898ab6693abe |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2022, 17:29:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B96C9B28EA2E8488F4984EFAEE45C5DD |
| SHA1: | FD3235CFF92031FA8D701C525094A1F5DA2AE25D |
| SHA256: | E23E3E13CC6F291D29FA188B4B8353469502D714DC14CD52FFE17F5FAC3FF59C |
| SSDEEP: | 24576:2NsfiTdYSuVzZH9tH1v1RobcAC23Qa0aTgp:2T2pZ1GB703 |
MALICIOUS
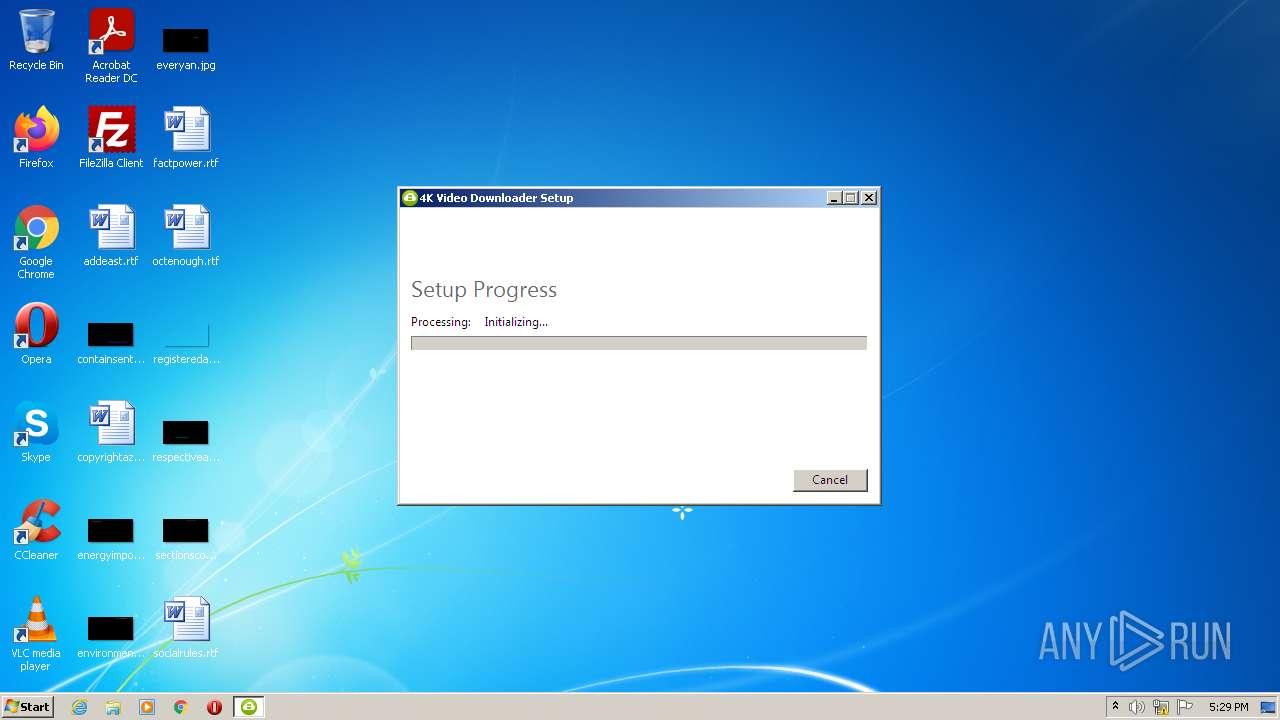
Drops executable file immediately after starts
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 2404)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
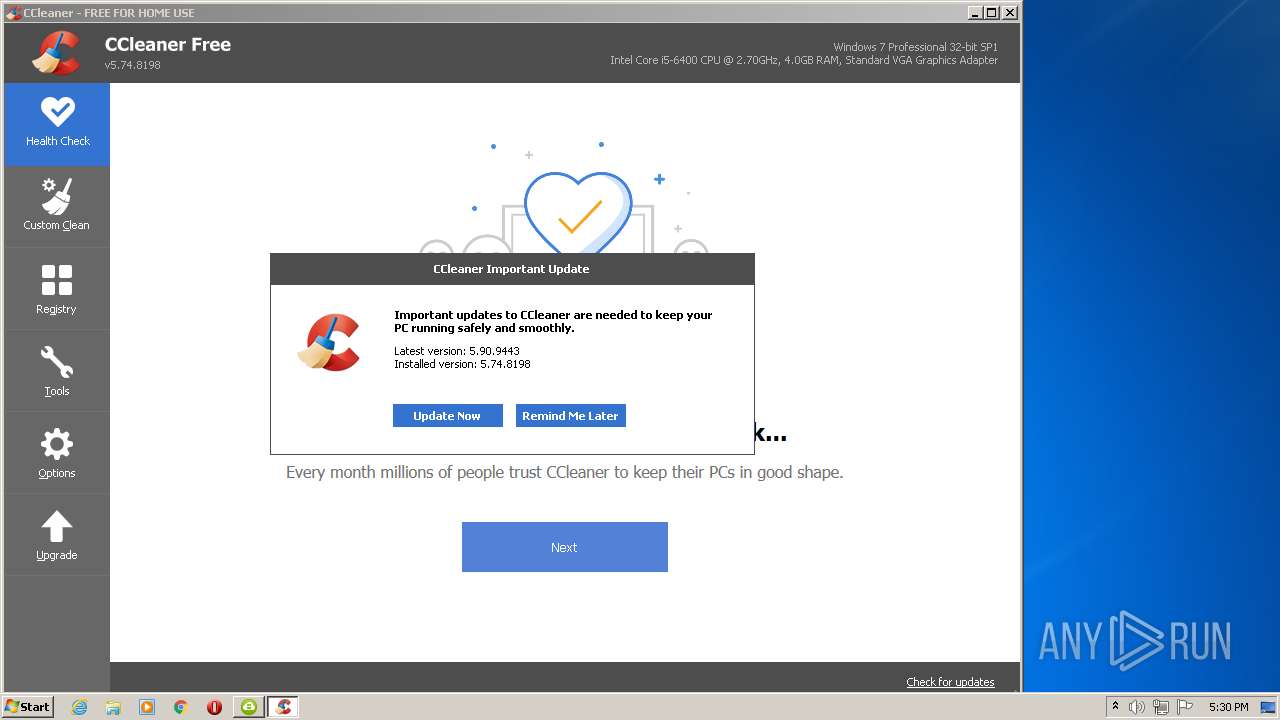
- CCleaner.exe (PID: 576)
Application was dropped or rewritten from another process
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
- msi_analytics.exe (PID: 2736)
Loads dropped or rewritten executable
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- CCleaner.exe (PID: 576)
Changes the autorun value in the registry
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 3748)
- CCleaner.exe (PID: 576)
Changes settings of System certificates
- CCleaner.exe (PID: 576)
Steals credentials from Web Browsers
- CCleaner.exe (PID: 576)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 576)
SUSPICIOUS
Drops a file that was compiled in debug mode
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 2404)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
- CCleaner.exe (PID: 576)
Checks supported languages
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 2404)
- msi_analytics.exe (PID: 2736)
- CCleaner.exe (PID: 3748)
- CCleaner.exe (PID: 576)
Starts itself from another location
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
Executable content was dropped or overwritten
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 2404)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
- CCleaner.exe (PID: 576)
Reads the computer name
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
- msi_analytics.exe (PID: 2736)
- CCleaner.exe (PID: 3748)
- CCleaner.exe (PID: 576)
Searches for installed software
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
- CCleaner.exe (PID: 576)
Executed as Windows Service
- vssvc.exe (PID: 3752)
- taskhost.exe (PID: 1940)
Creates files in the program directory
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
- CCleaner.exe (PID: 576)
Creates a software uninstall entry
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 3272)
Reads Environment values
- vssvc.exe (PID: 3752)
- CCleaner.exe (PID: 3748)
- CCleaner.exe (PID: 576)
Executed via Task Scheduler
- CCleaner.exe (PID: 576)
Reads internet explorer settings
- CCleaner.exe (PID: 576)
Reads the date of Windows installation
- CCleaner.exe (PID: 576)
Reads CPU info
- CCleaner.exe (PID: 576)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 576)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 576)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 576)
Reads Microsoft Outlook installation path
- CCleaner.exe (PID: 576)
Creates files in the user directory
- CCleaner.exe (PID: 576)
INFO
Checks supported languages
- vssvc.exe (PID: 3752)
- taskhost.exe (PID: 1940)
Reads the computer name
- vssvc.exe (PID: 3752)
- taskhost.exe (PID: 1940)
Reads settings of System Certificates
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- CCleaner.exe (PID: 576)
Checks Windows Trust Settings
- 4kvideodownloader_4.19.4_x64_online.exe (PID: 4060)
- CCleaner.exe (PID: 576)
Manual execution by user
- CCleaner.exe (PID: 3748)
Reads the hosts file
- CCleaner.exe (PID: 576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
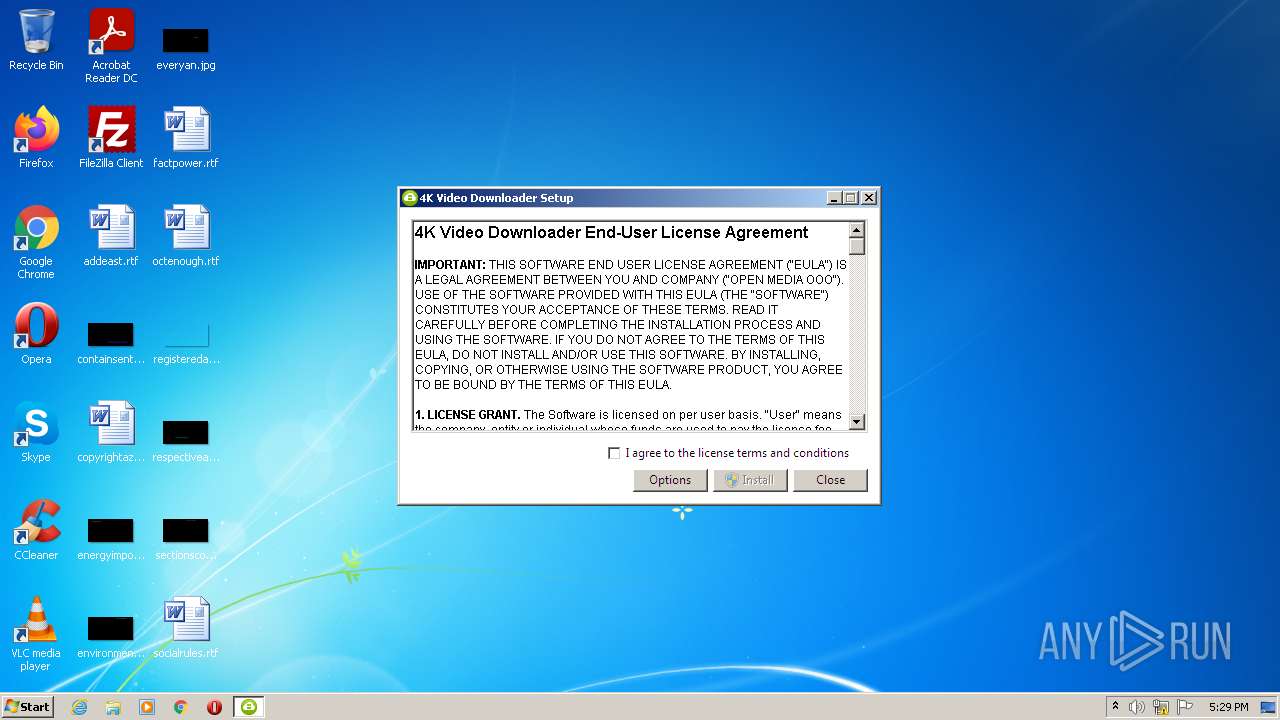
| ProductVersion: | 4.19.4.4720 |
|---|---|
| ProductName: | 4K Video Downloader |
| OriginalFileName: | 4kvideodownloader_4.19.4_x64_online.exe |
| LegalCopyright: | Copyright (c) Open Media LLC. All rights reserved. |
| InternalName: | setup |
| FileVersion: | 4.19.4.4720 |
| FileDescription: | 4K Video Downloader |
| CompanyName: | Open Media LLC |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 4.19.4.4720 |
| FileVersionNumber: | 4.19.4.4720 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x2df71 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 317952 |
| CodeSize: | 299008 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2019:09:17 07:33:38+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Sep-2019 05:33:38 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Open Media LLC |
| FileDescription: | 4K Video Downloader |
| FileVersion: | 4.19.4.4720 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Open Media LLC. All rights reserved. |
| OriginalFilename: | 4kvideodownloader_4.19.4_x64_online.exe |
| ProductName: | 4K Video Downloader |
| ProductVersion: | 4.19.4.4720 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 17-Sep-2019 05:33:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00048FF7 | 0x00049000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57206 |
.rdata | 0x0004A000 | 0x0001F760 | 0x0001F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13752 |
.data | 0x0006A000 | 0x000016FC | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15516 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.737593 |
.rsrc | 0x0006D000 | 0x000296C0 | 0x00029800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.43964 |
.reloc | 0x00097000 | 0x00003DD0 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78827 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.56634 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.62525 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.76242 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.83519 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.3416 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.41991 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.30291 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
50
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 1940 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Users\admin\AppData\Local\Temp\4kvideodownloader_4.19.4_x64_online.exe" | C:\Users\admin\AppData\Local\Temp\4kvideodownloader_4.19.4_x64_online.exe | Explorer.EXE | ||||||||||||
User: admin Company: Open Media LLC Integrity Level: MEDIUM Description: 4K Video Downloader Exit code: 0 Version: 4.19.4.4720 Modules
| |||||||||||||||
| 2736 | "C:\ProgramData\Package Cache\6CDE5BF27C599B4B868205991C5F972E2A7339EB\msi_analytics.exe" --regkey "Software\4kdownload.com\4K Video Downloader\Analytics" --an Wix --av 2 --ec "4K Video Downloader" --ea "before-install" --el "x64" --af "" | C:\ProgramData\Package Cache\6CDE5BF27C599B4B868205991C5F972E2A7339EB\msi_analytics.exe | 4kvideodownloader_4.19.4_x64_online.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3272 | "C:\Users\admin\AppData\Local\Temp\{DC432B00-30ED-4A7F-96FD-9D10EC7DEE8E}\.be\4kvideodownloader_4.19.4_x64_online.exe" -q -burn.elevated BurnPipe.{39752350-0034-4F10-89D2-D13C95EF2ECB} {C528B789-FA7D-4337-9E13-418EA10BD4D8} 4060 | C:\Users\admin\AppData\Local\Temp\{DC432B00-30ED-4A7F-96FD-9D10EC7DEE8E}\.be\4kvideodownloader_4.19.4_x64_online.exe | 4kvideodownloader_4.19.4_x64_online.exe | ||||||||||||
User: admin Company: Open Media LLC Integrity Level: HIGH Description: 4K Video Downloader Exit code: 0 Version: 4.19.4.4720 Modules
| |||||||||||||||
| 3748 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 3752 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\AppData\Local\Temp\{2F794C9F-1C0B-47B4-AE11-4FC762F35BD3}\.cr\4kvideodownloader_4.19.4_x64_online.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\4kvideodownloader_4.19.4_x64_online.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 | C:\Users\admin\AppData\Local\Temp\{2F794C9F-1C0B-47B4-AE11-4FC762F35BD3}\.cr\4kvideodownloader_4.19.4_x64_online.exe | 4kvideodownloader_4.19.4_x64_online.exe | ||||||||||||
User: admin Company: Open Media LLC Integrity Level: MEDIUM Description: 4K Video Downloader Exit code: 0 Version: 4.19.4.4720 Modules
| |||||||||||||||
Total events
26 315
Read events
25 962
Write events
345
Delete events
8
Modification events
| (PID) Process: | (4060) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4060) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4060) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4060) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3272) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000CE355425A429D801C80C0000E4050000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3272) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000CE355425A429D801C80C0000E4050000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3272) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (3272) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000004C959425A429D801C80C0000E4050000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3272) 4kvideodownloader_4.19.4_x64_online.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A6F79625A429D801C80C0000B0070000E8030000010000000000000000000000389DBF39C7706D4FBE32FBD75F09E9810000000000000000 | |||
| (PID) Process: | (3752) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000E81A025A429D801A80E00007C030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
10
Suspicious files
27
Text files
15
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | 4kvideodownloader_4.19.4_x64_online.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2404 | 4kvideodownloader_4.19.4_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{2F794C9F-1C0B-47B4-AE11-4FC762F35BD3}\.cr\4kvideodownloader_4.19.4_x64_online.exe | executable | |
MD5:— | SHA256:— | |||
| 3272 | 4kvideodownloader_4.19.4_x64_online.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{39bf9d38-70c7-4f6d-be32-fbd75f09e981}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 3272 | 4kvideodownloader_4.19.4_x64_online.exe | C:\ProgramData\Package Cache\{1745d00a-e7cd-4baf-84d1-c7447e73b683}\state.rsm | smt | |
MD5:— | SHA256:— | |||
| 3272 | 4kvideodownloader_4.19.4_x64_online.exe | C:\ProgramData\Package Cache\{1745d00a-e7cd-4baf-84d1-c7447e73b683}\4kvideodownloader_4.19.4_x64_online.exe | executable | |
MD5:— | SHA256:— | |||
| 4060 | 4kvideodownloader_4.19.4_x64_online.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4060 | 4kvideodownloader_4.19.4_x64_online.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 4060 | 4kvideodownloader_4.19.4_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{DC432B00-30ED-4A7F-96FD-9D10EC7DEE8E}\.ba\BootstrapperApplicationData.xml | xml | |
MD5:— | SHA256:— | |||
| 4060 | 4kvideodownloader_4.19.4_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{DC432B00-30ED-4A7F-96FD-9D10EC7DEE8E}\.ba\wixstdba.dll | executable | |
MD5:FE7E0BD53F52E6630473C31299A49FDD | SHA256:2BEA14D70943A42D344E09B7C9DE5562FA7E109946E1C615DD584DA30D06CC80 | |||
| 3272 | 4kvideodownloader_4.19.4_x64_online.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
27
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
576 | CCleaner.exe | GET | — | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | — | — | whitelisted |
576 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
576 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
576 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
576 | CCleaner.exe | GET | 200 | 104.18.20.226:80 | http://crl.globalsign.com/root-r3.crl | US | der | 1.77 Kb | whitelisted |
576 | CCleaner.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFJXl5%2FOUoVICgAAAAE3h2s%3D | US | der | 471 b | whitelisted |
2736 | msi_analytics.exe | GET | 200 | 34.213.215.111:8018 | http://sa.openmedia.co:8018/collect?an=Wix&av=2&cid=6fbf1f78-29d3-41e7-8d4e-ab4a5a067a23&ec=4K%20Video%20Downloader&ea=before-install&el=windows%206.1.7601%20|%20x64 | US | image | 35 b | unknown |
576 | CCleaner.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
4060 | 4kvideodownloader_4.19.4_x64_online.exe | GET | 200 | 104.117.200.9:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
576 | CCleaner.exe | GET | 200 | 2.16.107.121:80 | http://ncc.avast.com/ncc.txt | unknown | text | 26 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4060 | 4kvideodownloader_4.19.4_x64_online.exe | 8.248.135.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
576 | CCleaner.exe | 5.62.42.30:443 | ipm-provider.ff.avast.com | AVAST Software s.r.o. | GB | suspicious |
576 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
576 | CCleaner.exe | 5.62.40.208:443 | shepherd.ff.avast.com | AVAST Software s.r.o. | DE | suspicious |
576 | CCleaner.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
576 | CCleaner.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
576 | CCleaner.exe | 151.101.2.202:80 | www.ccleaner.com | Fastly | US | suspicious |
4060 | 4kvideodownloader_4.19.4_x64_online.exe | 2.16.186.9:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
576 | CCleaner.exe | 40.71.11.133:443 | healthcheck.ccleaner.com | Microsoft Corporation | US | suspicious |
576 | CCleaner.exe | 52.209.154.96:443 | softwareupdatechecker.live-everest-media.net | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.4kdownload.com |
| whitelisted |
sa.openmedia.co |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
ncc.avast.com |
| whitelisted |
analytics.ff.avast.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ipm-provider.ff.avast.com |
| whitelisted |
shepherd.ff.avast.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
576 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | Using Sciter version 4.4.4.4-r8057
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | observing CurrentIndex changed - 0
|
CCleaner.exe | observing CurrentIndex changed - Context.FirstTime=true CurrentIndex=0 LastIndex=4
|
CCleaner.exe | observing currentResultDetails changed - None
|
CCleaner.exe | SetStrings - Live Region updated: ,
|
CCleaner.exe | observing currentModeType changed - Preview
|