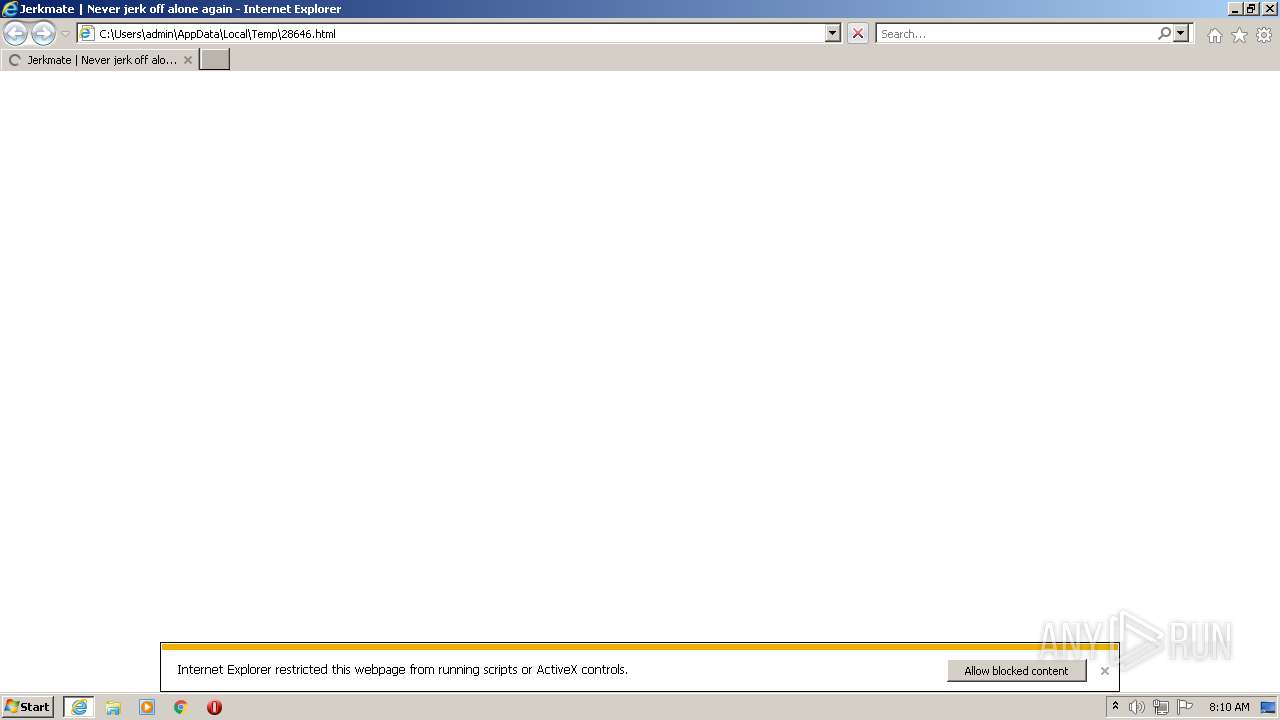
| File name: | 28646 |
| Full analysis: | https://app.any.run/tasks/cc7b0680-13a1-4969-a2f1-2fdb7f9d60d0 |
| Verdict: | Malicious activity |
| Analysis date: | May 01, 2021, 07:09:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | FE2BB6FBEFC2BF83ECCF771A2E925361 |
| SHA1: | 29DD02833B32CA56688C50AD15103F389AACD6D1 |
| SHA256: | E23DEF41DF6AE4E804123C7E741B05ED3EA4799A0D059C48BBF7C192713B8355 |
| SSDEEP: | 1536:4hltYqJLj0+LLZie857CsM7+ihLGZx+c/0fC+xg/QZNb4:mq0e7NM7Ra+xoQZNk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 3604)
- iexplore.exe (PID: 2256)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3140)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3140)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3140)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3140)
INFO
Checks supported languages
- iexplore.exe (PID: 2256)
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 3604)
Reads the computer name
- iexplore.exe (PID: 2256)
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 3604)
Changes internet zones settings
- iexplore.exe (PID: 2256)
Application launched itself
- iexplore.exe (PID: 2256)
Reads internet explorer settings
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 3604)
Reads settings of System Certificates
- iexplore.exe (PID: 3604)
- iexplore.exe (PID: 2256)
- iexplore.exe (PID: 2292)
Checks Windows Trust Settings
- iexplore.exe (PID: 2256)
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 3604)
Changes settings of System certificates
- iexplore.exe (PID: 2256)
Creates files in the user directory
- iexplore.exe (PID: 3604)
- iexplore.exe (PID: 2256)
Reads CPU info
- iexplore.exe (PID: 3604)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| viewport: | initial-scale = 1.0, width = device-width, user-scalable = no |
|---|---|
| themeColor: | #00c4ff |
| verifyV1: | eHWYqz07hRwCLzF/zA+S/SjvZxrJYkUDUYeEhYiOn94= |
| Copyright: | landing.jerkmate.com |
| Author: | - |
| RevisitAfter: | 1 days |
| Robots: | noindex, nofollow |
| CacheControl: | no-cache |
| Pragma: | no-cache |
| Expires: | Fri, Jan 01 1900 00:00:00 GMT |
| HTTPEquivXUACompatible: | IE=Edge |
| Keywords: | - |
| Description: | - |
| Title: | Jerkmate | Never jerk off alone again |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2256 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\28646.html | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2256 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3140 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3604 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2256 CREDAT:398593 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
33 095
Read events
32 684
Write events
408
Delete events
3
Modification events
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 85419568 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30883417 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 385583318 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30883417 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
41
Text files
613
Unknown types
78
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3604 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:93D54EECF23AD177C7EED4B9E59F7FA9 | SHA256:23274BC2ABF2AFC28B964D9F7AE5C8960E04141F3E12167B6D39598FF45D2836 | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:1AF27B22E1352E45E2645FB7C55297AE | SHA256:177835FCD7C3ACF20981D97C28D99482C63DDD4901CDF21860BB00DBB40564EE | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XJ5MVZMN.txt | text | |
MD5:65B4EB36C117994CBA5AC5DD96D8EFBA | SHA256:7461A5D0F6F779D4C827CB1A5C4472BAB35E37311EC4018AB3F7C4C29A163881 | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\CQ4JV7E4.txt | text | |
MD5:9BC2C3F9ECE6F27C24D3BD6C4B97F246 | SHA256:2EF6AA4CED520D7A4575C249E0E9B9843D72175646FEC5DA588C6E9AA71F8F06 | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:28BB8D7B9D2D6E3FF1F4F074FCD2CB2D | SHA256:C8EDEB9486DC752E0B4AAC9F866363D58795F72CDB61C10CAD725ADADF21C6F9 | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YWPQDRZ7.txt | text | |
MD5:51477B9A5767CB9DEB5A3E3F8574D005 | SHA256:679E17B7B6BCA4A7F0B6B2D94819BA8159D2EA5E134E5A33054E16D065051A46 | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\UA1XH9J1.txt | text | |
MD5:6408BA39BF8B92F704317199E9957A1D | SHA256:AC3D7E817D8BEB1655B78929CD7B4B84C3BEEFF6DB1A1D46B780C0BC2429F95D | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].xml | xml | |
MD5:3044BE88FFF56DE8FA0038D7ADFF4090 | SHA256:362F37AD7EBA750C76FD4DDEA95AB5B2F1DAB224254967D7C39C7F667FBAC3DA | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | xml | |
MD5:2E1A5E9D91A037E97F218374741AD1AE | SHA256:4E0B305698F5E300EF51395875B0D9329B7FAAE5581B3A52D9C58FEA1A94A285 | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\11SGJSL1.txt | text | |
MD5:C4A06F9C6D9F738745885E3A7AEC8663 | SHA256:86922E4C69D3C3ECF6808A94C1073E24C94D041F5748F1969B6EF5E0609CB3FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
204
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3604 | iexplore.exe | GET | 200 | 67.27.157.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d5851eaa55348787 | US | compressed | 4.70 Kb | whitelisted |
3604 | iexplore.exe | GET | 200 | 67.27.157.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ea50e1c5b3a6df52 | US | compressed | 4.70 Kb | whitelisted |
3604 | iexplore.exe | GET | 200 | 2.16.186.25:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5e1a9d194f0ea350 | unknown | compressed | 4.70 Kb | whitelisted |
3604 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAd3SBjpSMd4ojHOUsfJYh8%3D | US | der | 313 b | whitelisted |
3604 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3604 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAwbRijP%2Fi%2FbU8PLz0ngZ50%3D | US | der | 471 b | whitelisted |
3604 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
3604 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3604 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.49 Kb | whitelisted |
3604 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 205.185.216.10:445 | static.jerkmate.com | Highwinds Network Group, Inc. | US | whitelisted |
3604 | iexplore.exe | 67.27.157.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3604 | iexplore.exe | 2.16.186.25:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
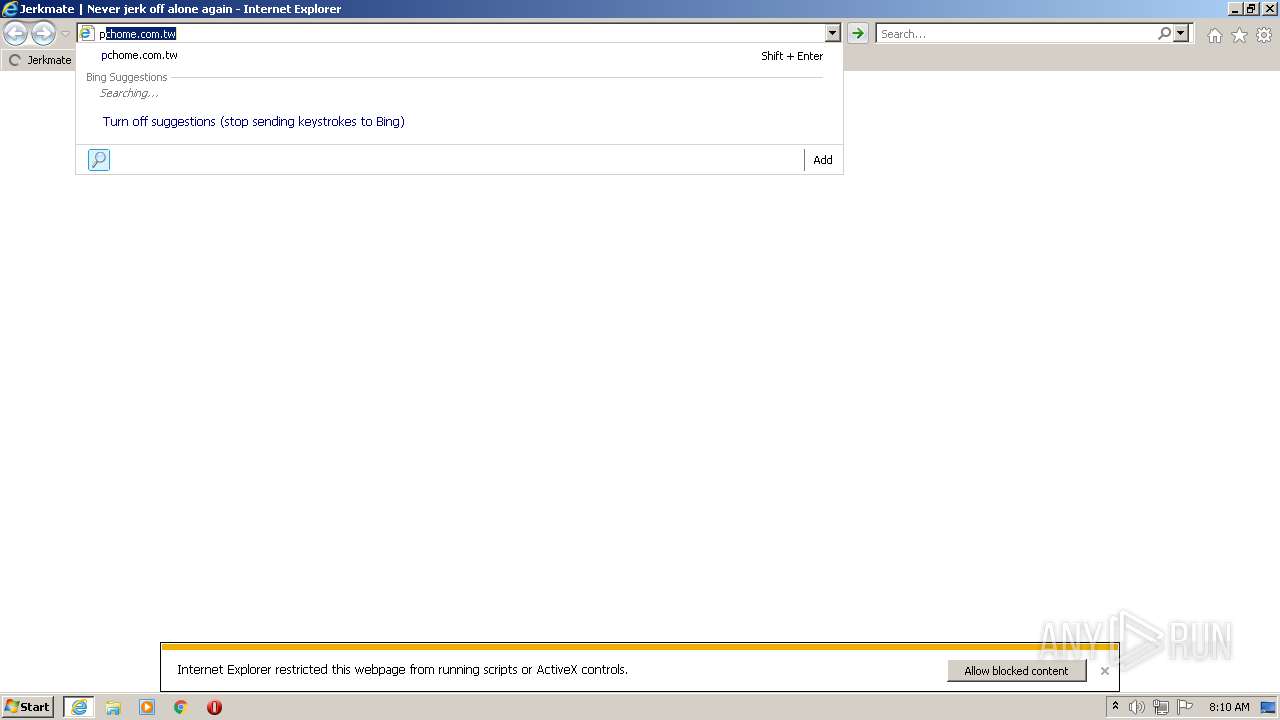
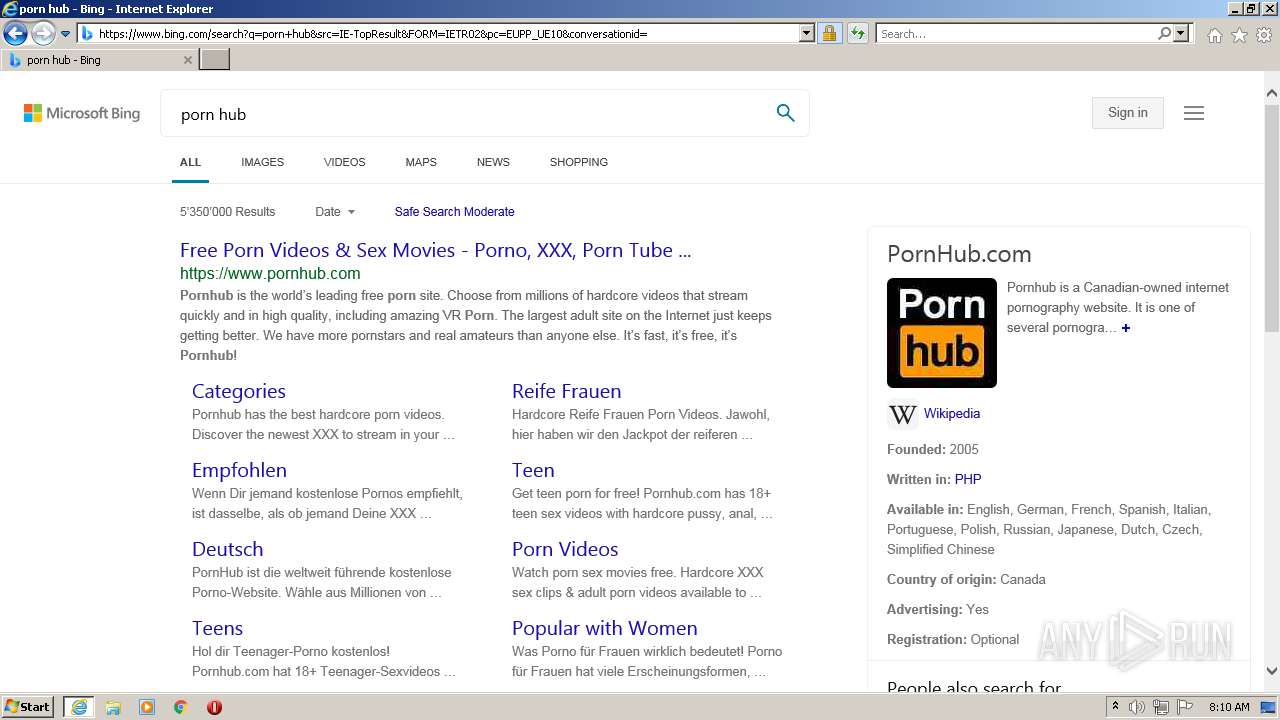
2256 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3604 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
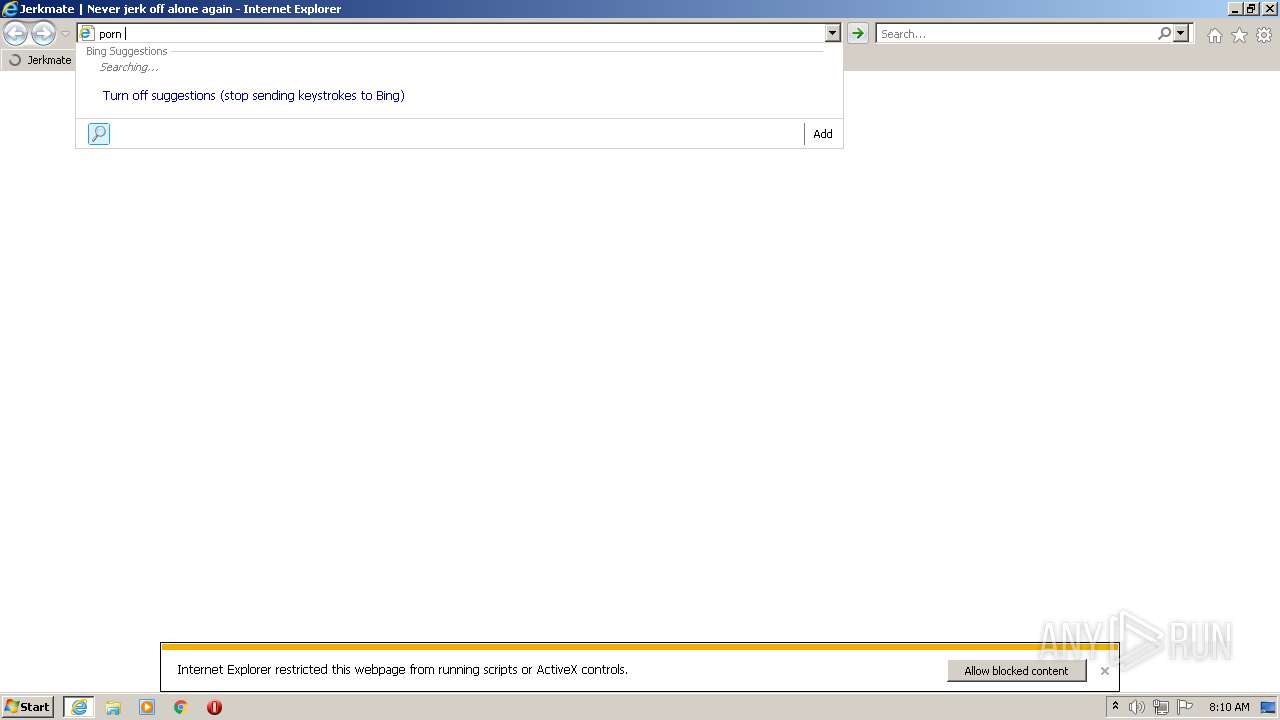
3604 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3604 | iexplore.exe | 40.126.31.1:443 | login.microsoftonline.com | Microsoft Corporation | US | whitelisted |
3604 | iexplore.exe | 40.126.31.141:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
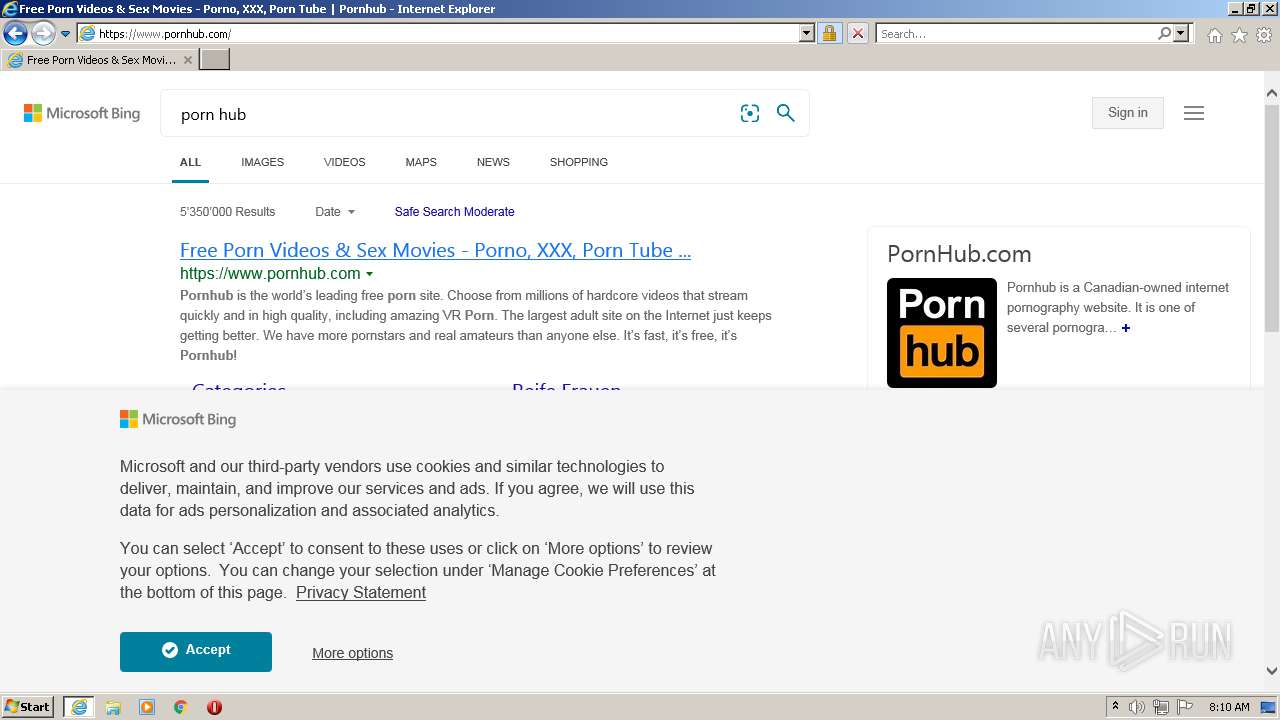
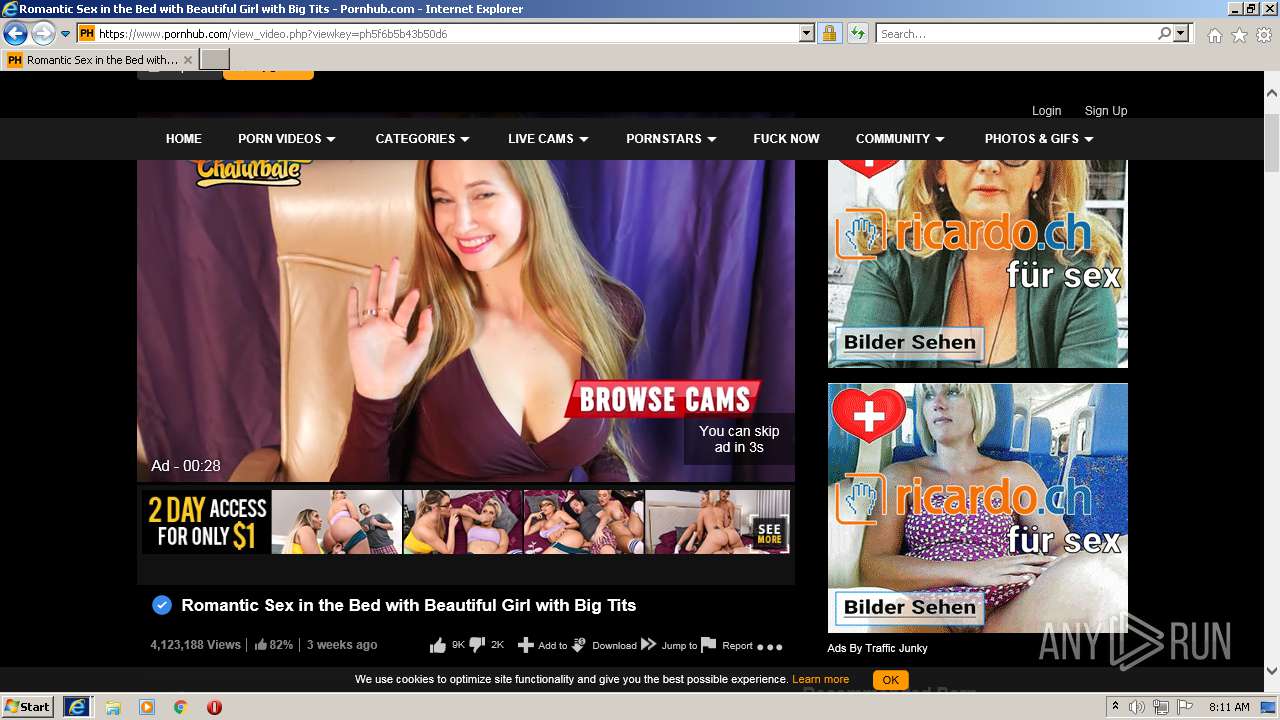
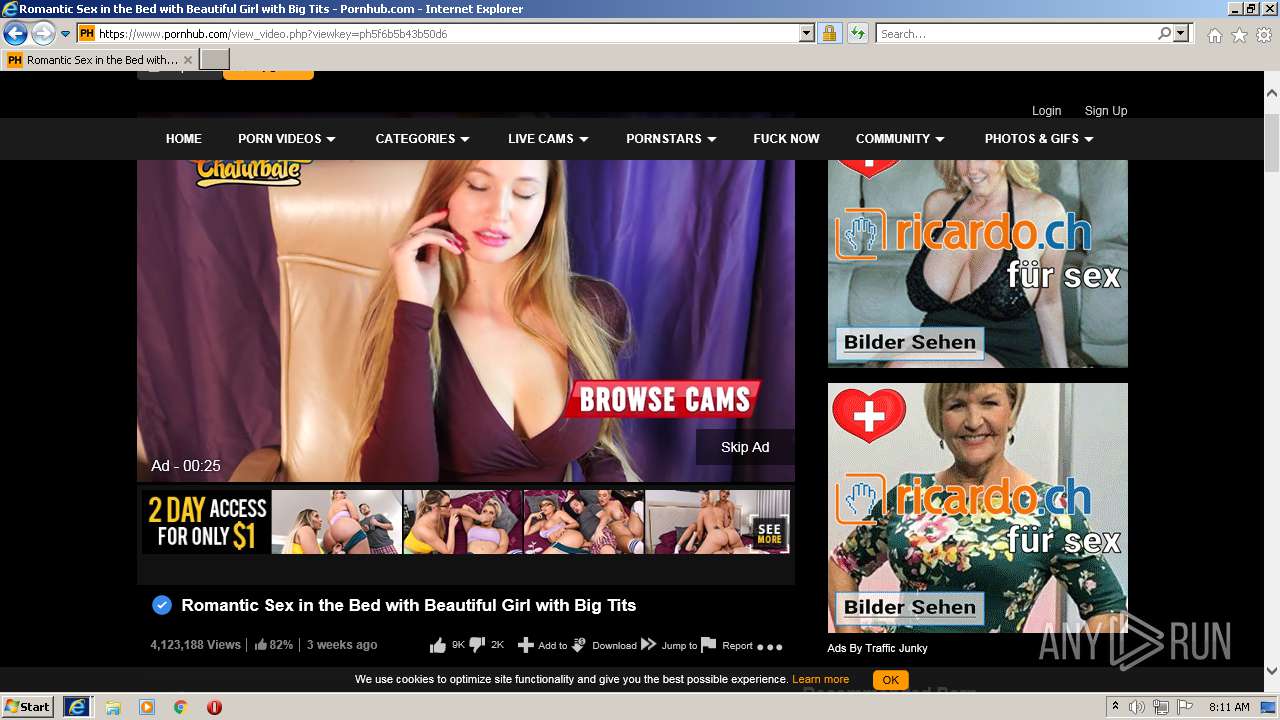
3604 | iexplore.exe | 66.254.114.41:443 | www.pornhub.com | Reflected Networks, Inc. | US | malicious |
3604 | iexplore.exe | 205.185.208.79:443 | static.trafficjunky.com | Highwinds Network Group, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
static.jerkmate.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
www.pornhub.com |
| whitelisted |
ei.phncdn.com |
| whitelisted |
static.trafficjunky.com |
| whitelisted |