| URL: | https://addons-pa.clients6.google.com |
| Full analysis: | https://app.any.run/tasks/1c94e4cd-7dda-4a38-a576-d963d4507a15 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2022, 00:58:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8CEE4B196B3E6F913D69ACA9E12AEB10 |
| SHA1: | AED0675AD331E7054E140E9B2CC20568707FA012 |
| SHA256: | E20BD85AC83C07EF8ED41FB8B776760639049EDFDEB93AD6E0F17709C797FB23 |
| SSDEEP: | 3:N8qQPVlW4CkK:2qUVbCkK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4044)
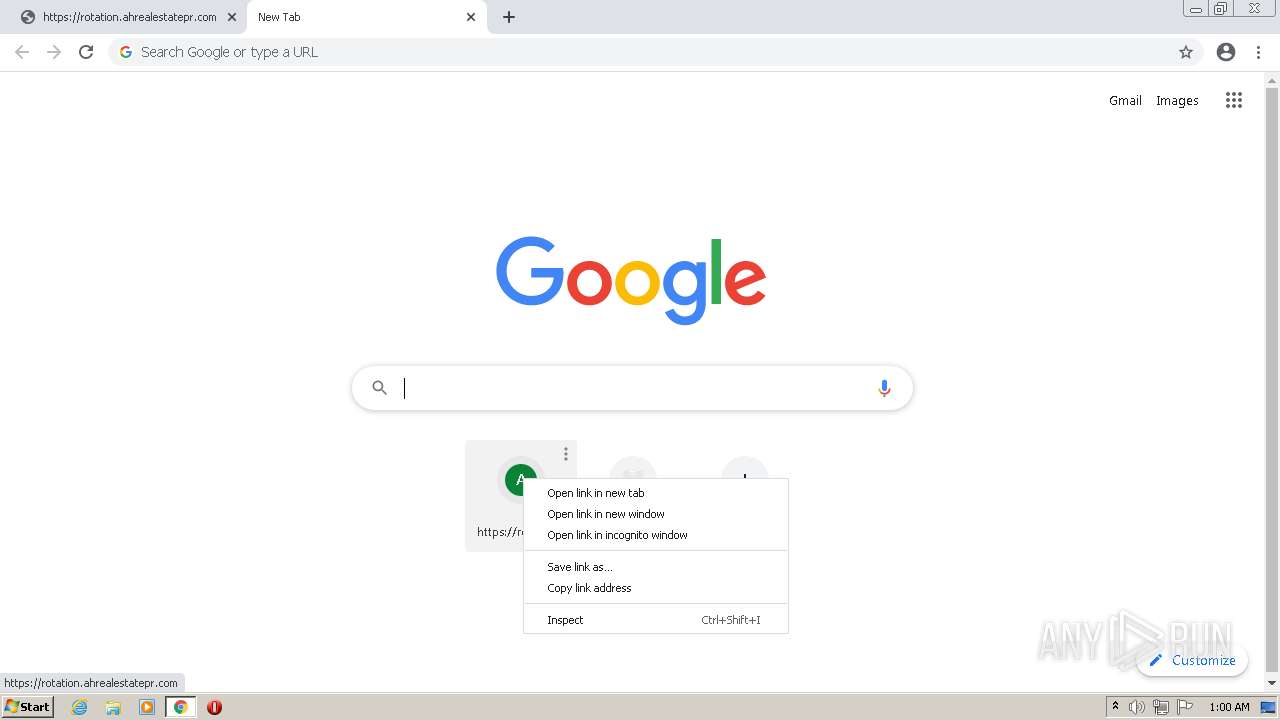
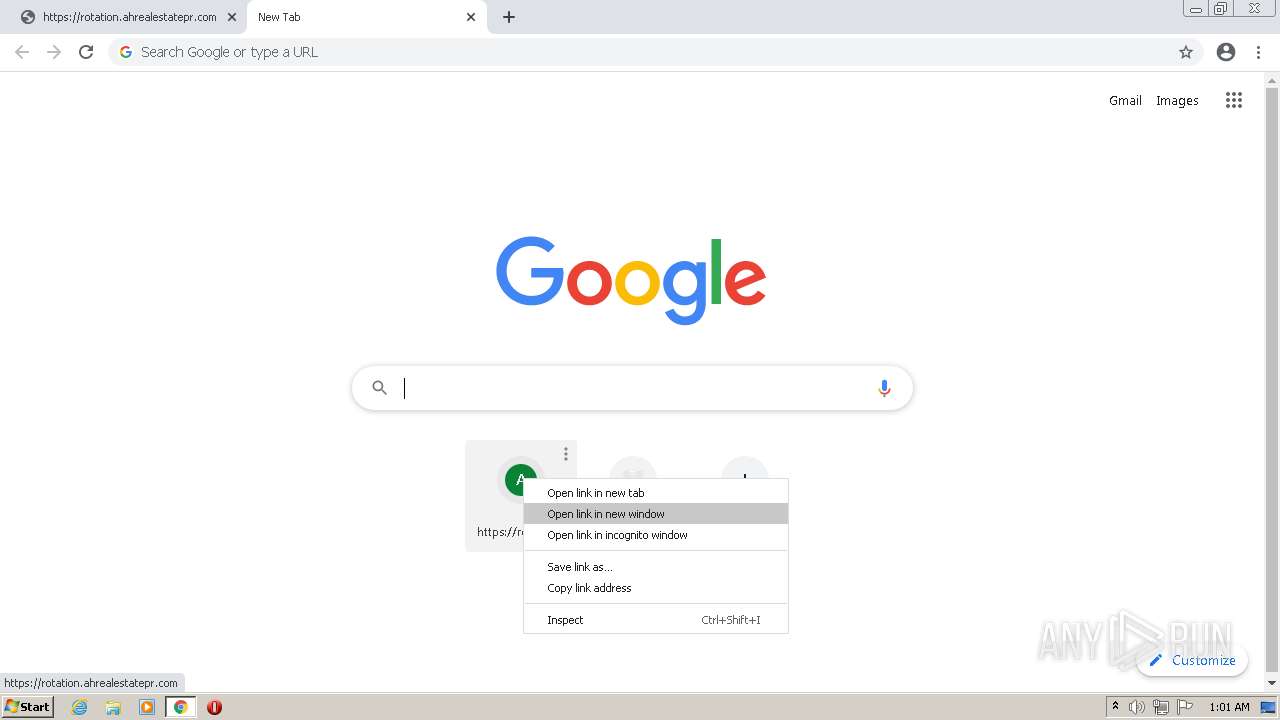
Modifies files in Chrome extension folder
- chrome.exe (PID: 3492)
INFO
Checks supported languages
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 4044)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 1696)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 348)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 1252)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2424)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 1240)
- chrome.exe (PID: 4084)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 1172)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3044)
Changes internet zones settings
- iexplore.exe (PID: 1816)
Application launched itself
- iexplore.exe (PID: 1816)
- chrome.exe (PID: 3492)
Reads the computer name
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 4044)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 1696)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 3044)
Reads internet explorer settings
- iexplore.exe (PID: 4044)
Checks Windows Trust Settings
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 4044)
Reads settings of System Certificates
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1816)
- chrome.exe (PID: 1696)
Creates files in the user directory
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1816)
Manual execution by user
- chrome.exe (PID: 3492)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1816)
Changes settings of System certificates
- iexplore.exe (PID: 1816)
Reads the hosts file
- chrome.exe (PID: 3492)
- chrome.exe (PID: 1696)
Reads the date of Windows installation
- iexplore.exe (PID: 1816)
- chrome.exe (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2836 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1816 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://addons-pa.clients6.google.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1024 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,1170488734507177590,4041218765268633131,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
227
Text files
175
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:44BDBCC88AF117AF07CBBEEDCBE12412 | SHA256:59E89432E5EBF80150EE1CEBD35C355E5E61287A3E6480BD2A6D37631EAAB86D | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:01F7109B83C250719A075BA784F69479 | SHA256:1FD5C1735F89DF2BF327B94EC5ED5BFA8E869F7678E3D8C7F9BAAE1649CE9CDE | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:4B815A0B1674EAE3EB030A83FD045129 | SHA256:50D1422F7D355D986DAC0F5E98C8CE0C8F8A8B0635E747E54D858A34886F334E | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_9FEB5FCAA9F6B83600034A61AFEC7140 | der | |
MD5:24D4A84C1FB77771A5F829F183254391 | SHA256:224F77B86F4894779CC6EB54B5EFDEEC8E32EA3EC02C4F41D5833CE4859F8FF4 | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_518E2370BC94F8A344628AB210B70292 | der | |
MD5:FB1163CE4882FD0469EE37D14222DE79 | SHA256:398AE6CD482D189F80B3229E320B8568CB718E1E717AEB255BDD72AADAAA67FF | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_518E2370BC94F8A344628AB210B70292 | binary | |
MD5:15085997AFA78D566FF0E443D3EA475A | SHA256:EADDDA4ABE2210155FC023B6879425F986B15D15028E3CCBB673B6A84EA5248E | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:64E9B8BB98E2303717538CE259BEC57D | SHA256:76BD459EC8E467EFC3E3FB94CB21B9C77A2AA73C9D4C0F3FAF823677BE756331 | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_9FEB5FCAA9F6B83600034A61AFEC7140 | binary | |
MD5:A6C5E0267AAC8FCDB0368FB6D5AF7F93 | SHA256:8D30F3248CA389A17E776D076E923BCB1B893846759F18A35318BE6275218E97 | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\LE1NAPEU.txt | text | |
MD5:02DC7BC81A342D4C994D9725F4E25810 | SHA256:2B4050C2414997E94CBE8A42568CA56FED9240A459E05A6471ACCF983306CBCF | |||
| 1816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:19536B7351E649CE4C4F57662642D275 | SHA256:D5A8C34A64CB73C36DF07ABB72D54B4617AAD9D9F33B6922D8D64685A89EC7C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
103
DNS requests
81
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 20.9 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC13GRQS4GqKwoAAAABL5H9 | US | der | 472 b | whitelisted |
1816 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 92.123.194.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6870b50d7d20fc33 | unknown | compressed | 4.70 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
4044 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC9xJ9s74KAqgoAAAABL5UT | US | der | 472 b | whitelisted |
4044 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1816 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.64 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4044 | iexplore.exe | 92.123.194.121:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | malicious |
4044 | iexplore.exe | 216.58.212.164:443 | www.google.com | Google Inc. | US | whitelisted |
1816 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1816 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1816 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1816 | iexplore.exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
1816 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
1816 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
4044 | iexplore.exe | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
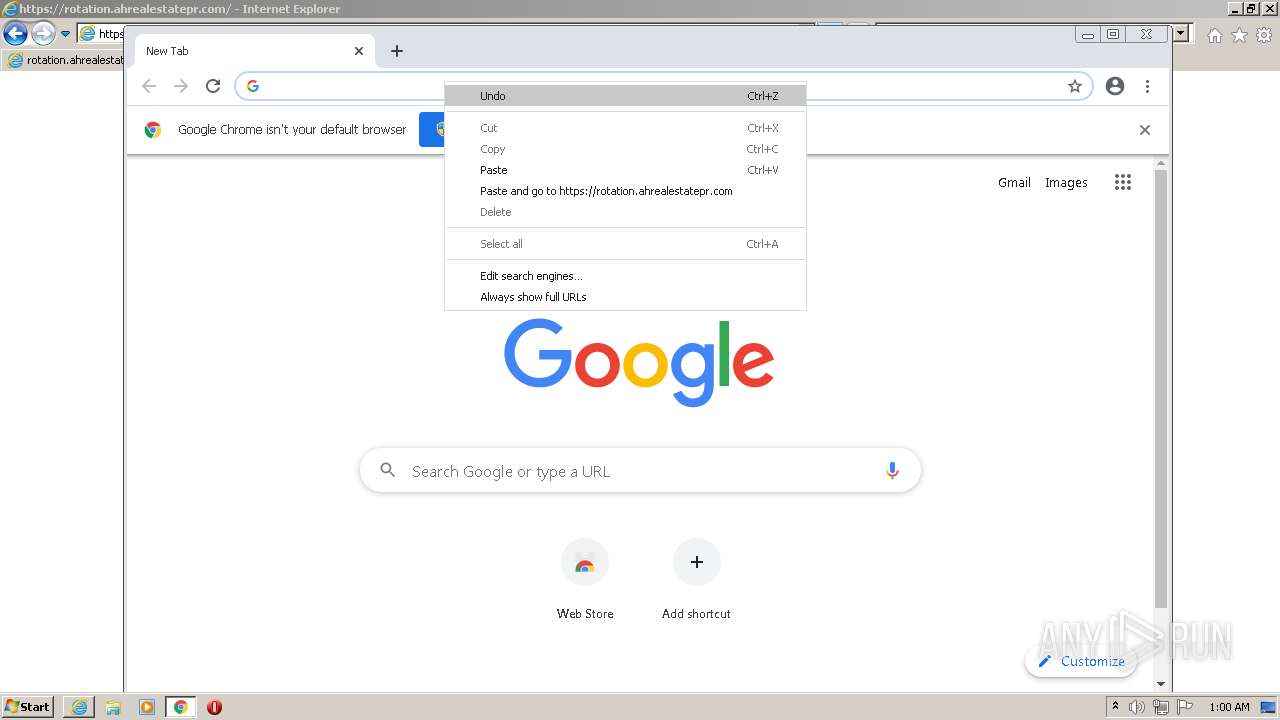
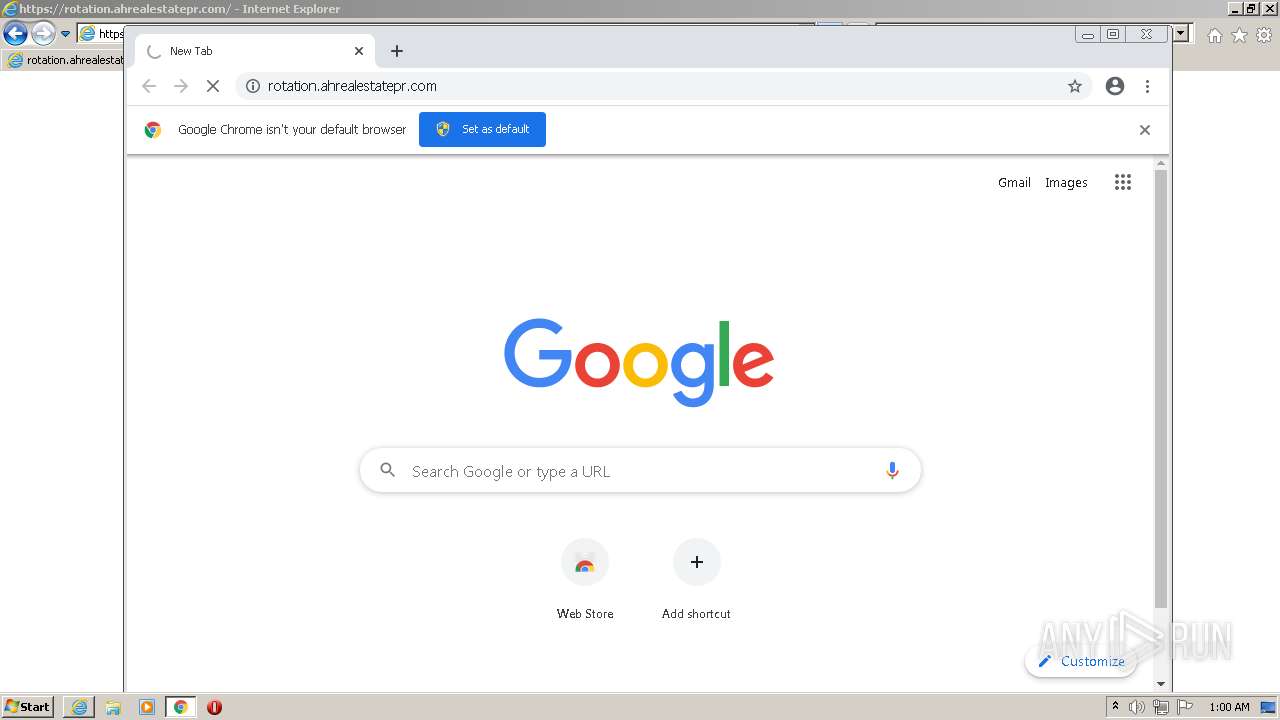
4044 | iexplore.exe | 79.142.69.149:80 | rotation.ahrealestatepr.com | AltusHost B.V. | DK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
addons-pa.clients6.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4044 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1816 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1816 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1696 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1696 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |