| File name: | pokemon-sword-and-shield-aa_kFDy-N1.exe |
| Full analysis: | https://app.any.run/tasks/23f4b7cf-1824-4a1f-8c69-f63f893b73f5 |
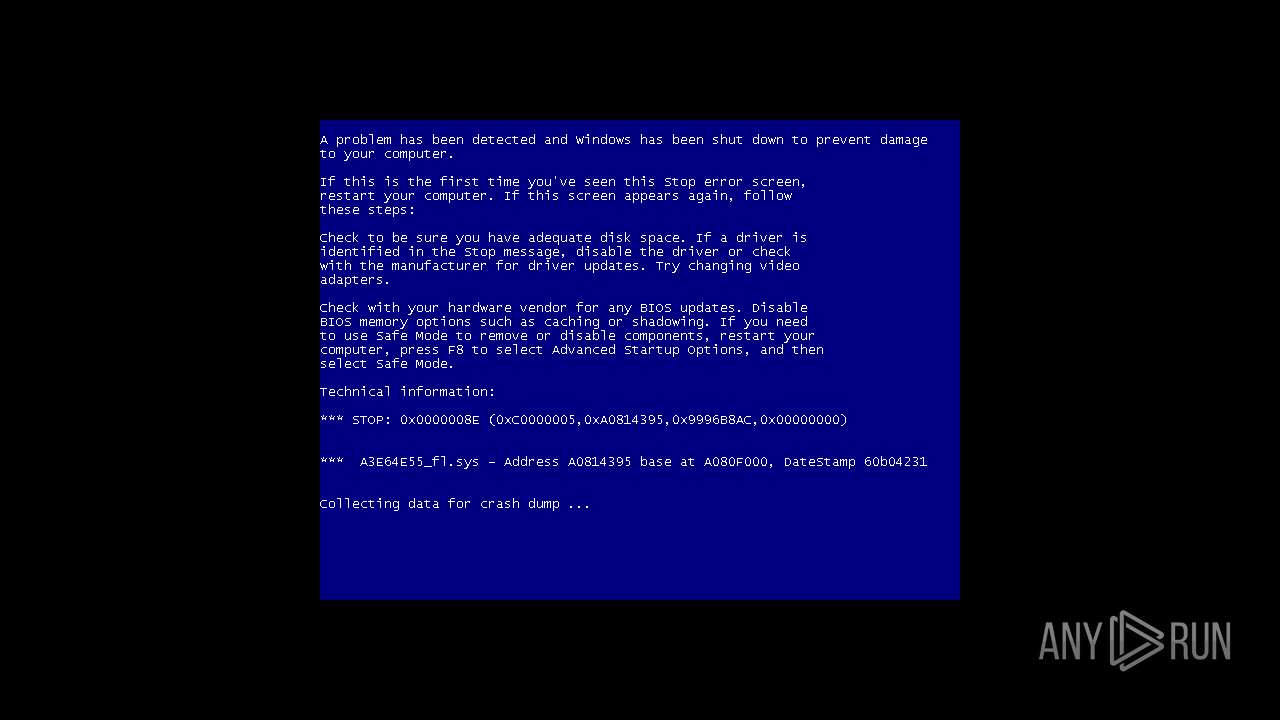
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2021, 08:52:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9801DC06B2D8F59E2B904B0ED388F054 |
| SHA1: | 576CBFFDD81B51A3A4BE2629D2F205D954E349F6 |
| SHA256: | E20681EEC18D8B9F70A1CC153B4D53114320EF93C2A9092999F504F4B14B28F0 |
| SSDEEP: | 49152:Fqe3f6TP6QkO6U6HP6RbtyXXlAr2YvdcxhcjPor:USiTP6Qk/U6iRbtyXXlAyidc7AM |
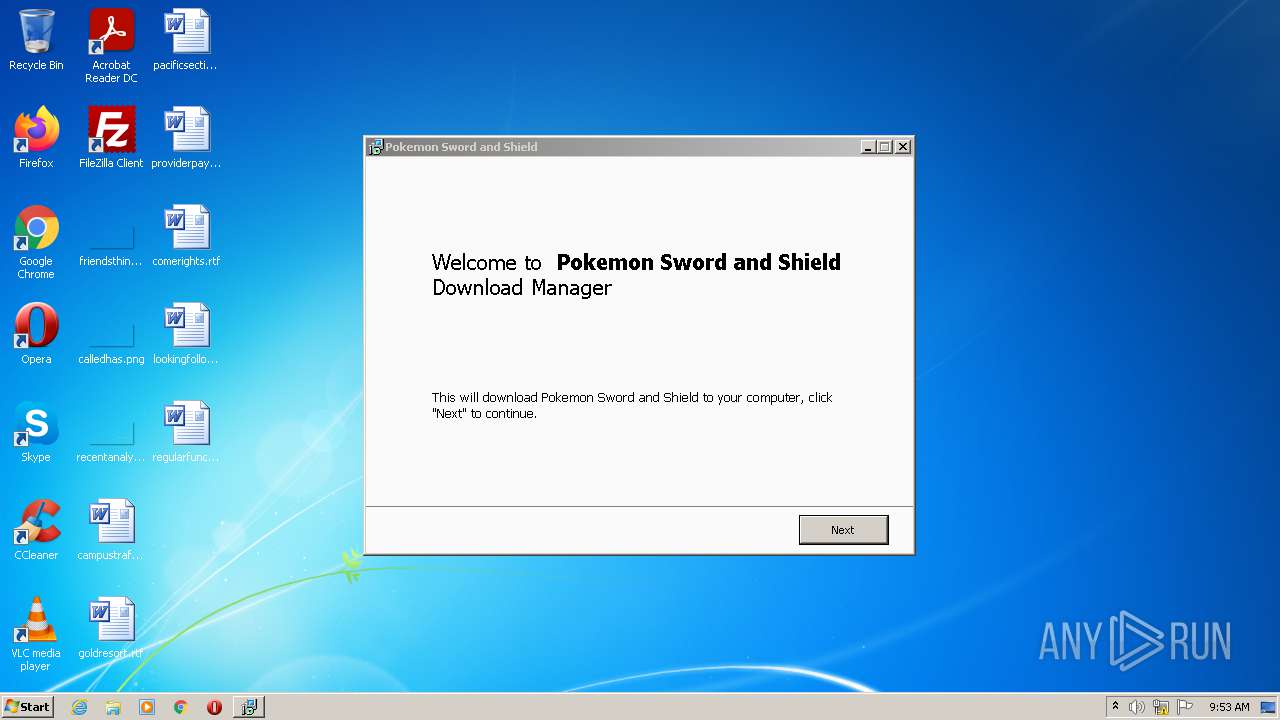
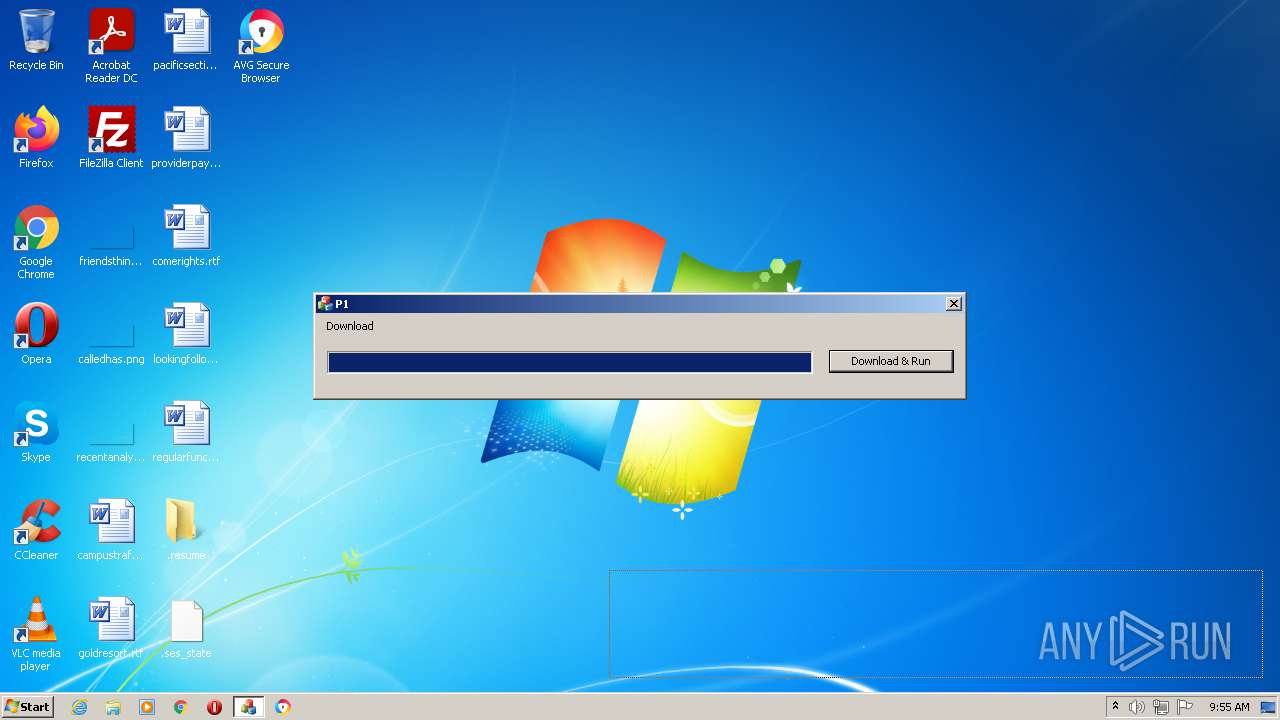
MALICIOUS
Drops executable file immediately after starts
- pokemon-sword-and-shield-aa_kFDy-N1.exe (PID: 3500)
- pokemon-sword-and-shield-aa_kFDy-N1.exe (PID: 2760)
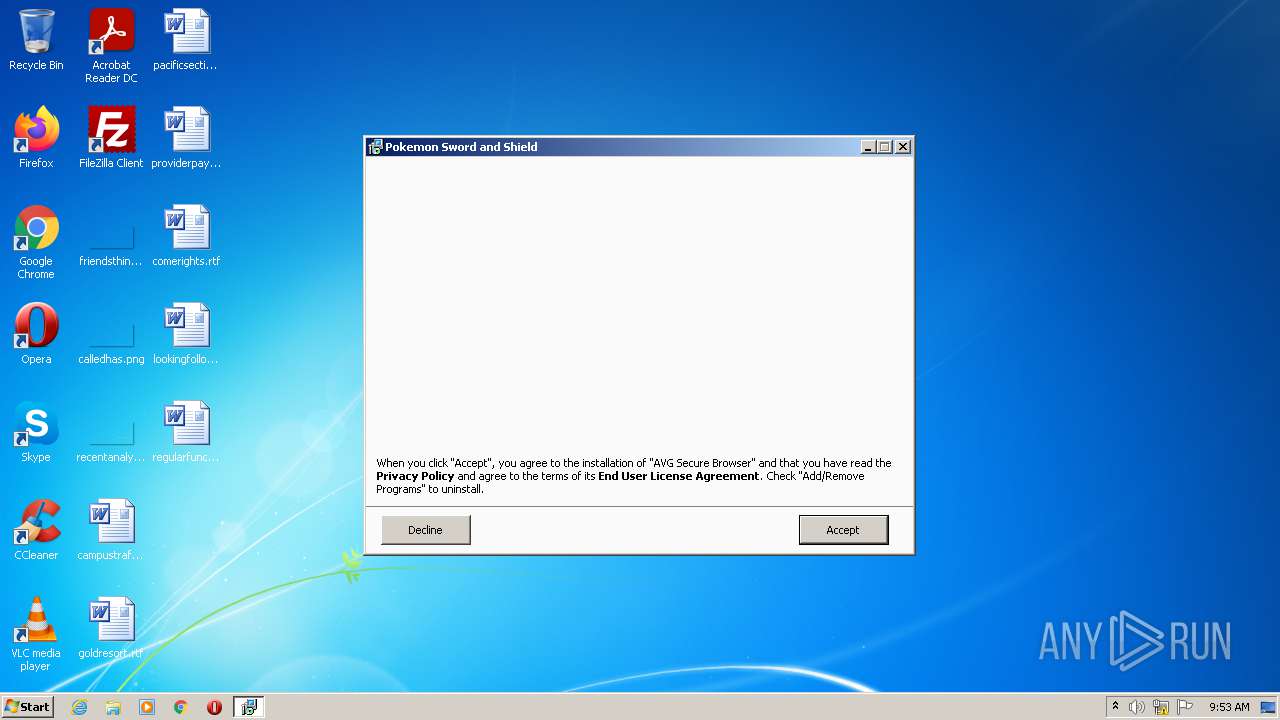
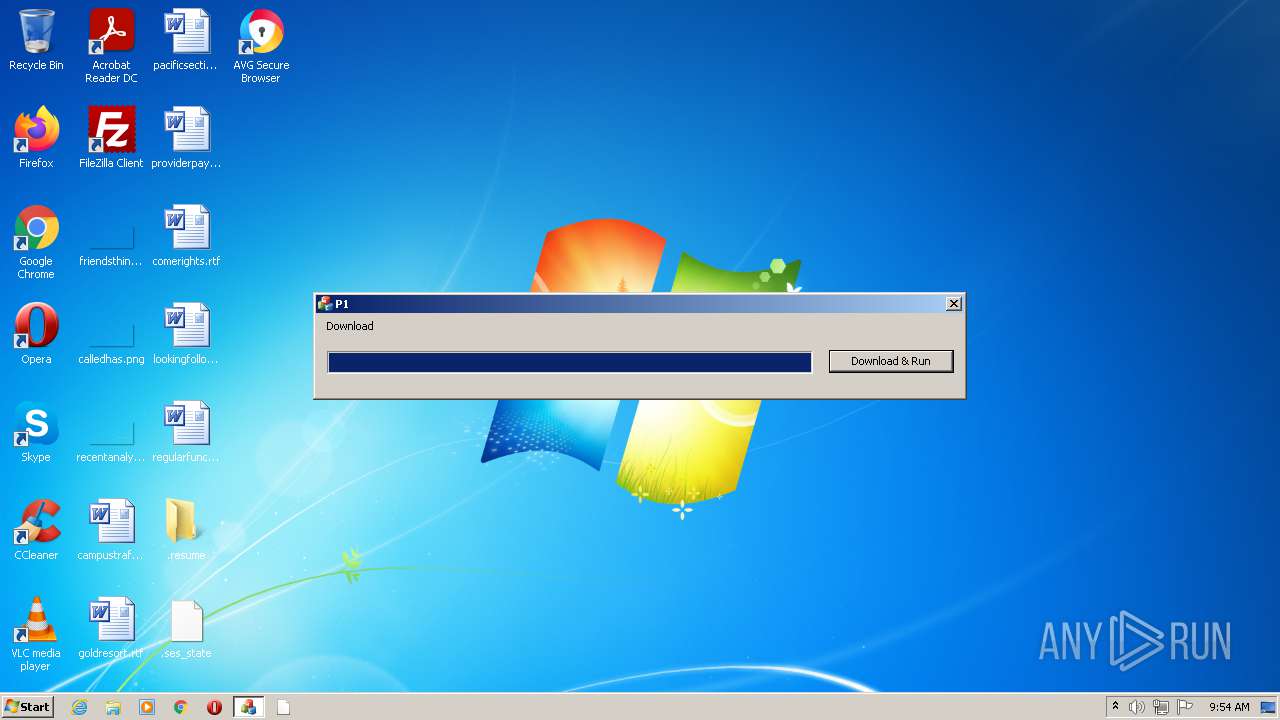
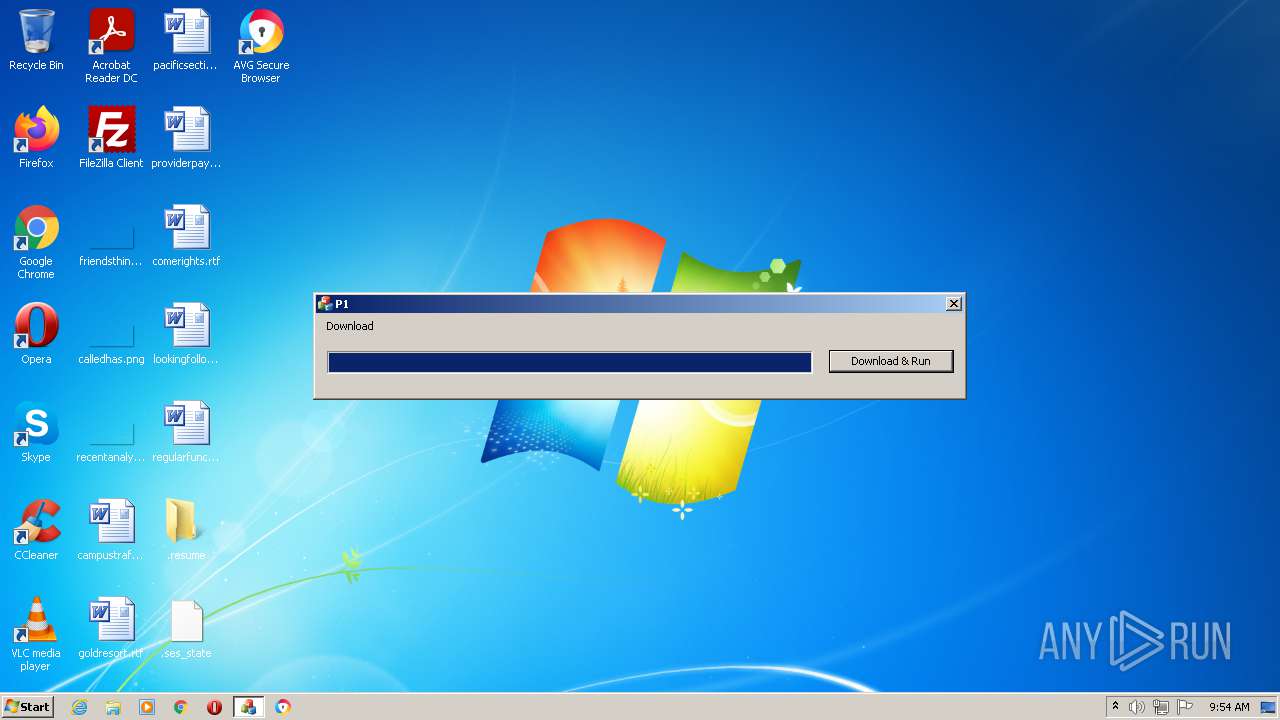
- avg_secure_browser_setup.exe (PID: 2464)
- AVGBrowserUpdateSetup.exe (PID: 2400)
- AVGBrowserUpdate.exe (PID: 2284)
- instup.exe (PID: 2320)
- AVGBrowserInstaller.exe (PID: 2404)
- DrvInst.exe (PID: 3132)
Changes settings of System certificates
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
- AVGBrowserUpdate.exe (PID: 3840)
- AVGBrowser.exe (PID: 1644)
- SetupInf.exe (PID: 3732)
Application was dropped or rewritten from another process
- cookie_mmm_irs_ppi_005_888_a.exe (PID: 2792)
- avg_secure_browser_setup.exe (PID: 2464)
- AVGBrowserUpdateSetup.exe (PID: 2400)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- AVGBrowserUpdate.exe (PID: 2284)
- AVGBrowserUpdate.exe (PID: 3404)
- AVGBrowserUpdate.exe (PID: 3128)
- AVGBrowserUpdate.exe (PID: 3492)
- AVGBrowserUpdate.exe (PID: 764)
- AVGBrowserUpdate.exe (PID: 3840)
- instup.exe (PID: 2340)
- instup.exe (PID: 2320)
- pokemon-sword-and-shield-aa.exe (PID: 3612)
- sbr.exe (PID: 2568)
- setup.exe (PID: 3132)
- setup.exe (PID: 3312)
- AVGBrowserCrashHandler.exe (PID: 708)
- AVGBrowser.exe (PID: 3968)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3744)
- AVGBrowser.exe (PID: 3252)
- AVGBrowser.exe (PID: 2820)
- AVGBrowser.exe (PID: 2104)
- AVGBrowser.exe (PID: 1184)
- AVGBrowser.exe (PID: 668)
- AVGBrowser.exe (PID: 3560)
- AVGBrowser.exe (PID: 3988)
- AVGBrowser.exe (PID: 1380)
- AVGBrowser.exe (PID: 2360)
- AVGBrowser.exe (PID: 1588)
- AVGBrowser.exe (PID: 1152)
- AVGBrowser.exe (PID: 3768)
- AVGBrowser.exe (PID: 2212)
- AVGBrowser.exe (PID: 860)
- AVGBrowser.exe (PID: 1860)
- AVGBrowser.exe (PID: 2332)
- AVGBrowser.exe (PID: 1892)
- AVGBrowser.exe (PID: 4084)
- AVGBrowser.exe (PID: 4024)
- AVGBrowser.exe (PID: 3604)
- AVGBrowser.exe (PID: 2588)
- AVGBrowser.exe (PID: 3140)
- AVGBrowser.exe (PID: 3312)
- AVGBrowser.exe (PID: 3144)
- AVGBrowser.exe (PID: 2040)
- AVGBrowser.exe (PID: 4076)
- AVGBrowser.exe (PID: 340)
- AVGBrowser.exe (PID: 2908)
- AVGBrowser.exe (PID: 3376)
- AVGBrowser.exe (PID: 2564)
- AVGBrowser.exe (PID: 3416)
- AVGBrowser.exe (PID: 2588)
- AVGBrowser.exe (PID: 296)
- AVGBrowser.exe (PID: 3960)
- AVGBrowser.exe (PID: 3092)
- AVGBrowser.exe (PID: 3748)
- AVGBrowser.exe (PID: 3892)
- AVGBrowser.exe (PID: 2440)
- AVGBrowser.exe (PID: 2556)
- AVGBrowser.exe (PID: 3964)
- AVGBrowser.exe (PID: 648)
- AVGBrowser.exe (PID: 1232)
- AVGBrowser.exe (PID: 3232)
- AVGBrowser.exe (PID: 3868)
- AVGBrowser.exe (PID: 3472)
- AVGBrowser.exe (PID: 1136)
- AVGBrowser.exe (PID: 3068)
- AVGBrowser.exe (PID: 3748)
- AVGBrowser.exe (PID: 3724)
- AVGBrowser.exe (PID: 3604)
- AVGBrowser.exe (PID: 3980)
- AVGBrowser.exe (PID: 876)
- AVGBrowser.exe (PID: 280)
- AVGBrowser.exe (PID: 2088)
- AVGBrowser.exe (PID: 2356)
- AVGBrowser.exe (PID: 3548)
- AVGBrowser.exe (PID: 3472)
- AVGBrowser.exe (PID: 4092)
- AVGBrowser.exe (PID: 3532)
- AVGBrowser.exe (PID: 1576)
- AVGBrowser.exe (PID: 4068)
- AVGBrowser.exe (PID: 3384)
- AVGBrowser.exe (PID: 3908)
- AVGBrowser.exe (PID: 3860)
- SetupInf.exe (PID: 2348)
- SetupInf.exe (PID: 3204)
- AVGBrowser.exe (PID: 328)
- AVGBrowser.exe (PID: 3164)
- SetupInf.exe (PID: 3532)
- AvEmUpdate.exe (PID: 3348)
- SetupInf.exe (PID: 3112)
- AvEmUpdate.exe (PID: 3488)
- AvEmUpdate.exe (PID: 3452)
- avBugReport.exe (PID: 3588)
- avBugReport.exe (PID: 3972)
- AvEmUpdate.exe (PID: 2404)
- SetupInf.exe (PID: 3468)
- SetupInf.exe (PID: 3732)
- RegSvr.exe (PID: 3900)
- RegSvr.exe (PID: 116)
Steals credentials from Web Browsers
- avg_secure_browser_setup.exe (PID: 2464)
- AVGBrowser.exe (PID: 1644)
- engsup.exe (PID: 2044)
Loads dropped or rewritten executable
- avg_secure_browser_setup.exe (PID: 2464)
- AVGBrowserUpdate.exe (PID: 2284)
- AVGBrowserUpdate.exe (PID: 3128)
- AVGBrowserUpdate.exe (PID: 3492)
- AVGBrowserUpdate.exe (PID: 764)
- instup.exe (PID: 2340)
- AVGBrowserUpdate.exe (PID: 3404)
- instup.exe (PID: 2320)
- AVGBrowserCrashHandler.exe (PID: 708)
- AVGBrowserUpdate.exe (PID: 3840)
- AvEmUpdate.exe (PID: 3488)
- AvEmUpdate.exe (PID: 2404)
- avBugReport.exe (PID: 3588)
- avBugReport.exe (PID: 3972)
Actions looks like stealing of personal data
- avg_secure_browser_setup.exe (PID: 2464)
- AVGBrowserInstaller.exe (PID: 2404)
- setup.exe (PID: 3312)
- AVGBrowser.exe (PID: 1644)
- engsup.exe (PID: 2044)
Loads the Task Scheduler COM API
- AVGBrowserUpdate.exe (PID: 2284)
- setup.exe (PID: 3312)
- AvEmUpdate.exe (PID: 3348)
- AvEmUpdate.exe (PID: 3452)
- overseer.exe (PID: 2584)
Changes the autorun value in the registry
- instup.exe (PID: 2320)
- setup.exe (PID: 3312)
SUSPICIOUS
Checks supported languages
- pokemon-sword-and-shield-aa_kFDy-N1.exe (PID: 3500)
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 3900)
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
- pokemon-sword-and-shield-aa_kFDy-N1.exe (PID: 2760)
- cookie_mmm_irs_ppi_005_888_a.exe (PID: 2792)
- avg_secure_browser_setup.exe (PID: 2464)
- AVGBrowserUpdateSetup.exe (PID: 2400)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- AVGBrowserUpdate.exe (PID: 2284)
- instup.exe (PID: 2340)
- AVGBrowserUpdate.exe (PID: 3128)
- AVGBrowserUpdate.exe (PID: 3492)
- AVGBrowserUpdate.exe (PID: 3404)
- AVGBrowserUpdate.exe (PID: 764)
- AVGBrowserUpdate.exe (PID: 3840)
- instup.exe (PID: 2320)
- sbr.exe (PID: 2568)
- pokemon-sword-and-shield-aa.exe (PID: 3612)
- AVGBrowserInstaller.exe (PID: 2404)
- setup.exe (PID: 3312)
- setup.exe (PID: 3132)
- AVGBrowserCrashHandler.exe (PID: 708)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3968)
- AVGBrowser.exe (PID: 3252)
- AVGBrowser.exe (PID: 3744)
- elevation_service.exe (PID: 2780)
- AVGBrowser.exe (PID: 2104)
- AVGBrowser.exe (PID: 3560)
- AVGBrowser.exe (PID: 3988)
- AVGBrowser.exe (PID: 668)
- AVGBrowser.exe (PID: 2820)
- AVGBrowser.exe (PID: 1380)
- AVGBrowser.exe (PID: 2360)
- AVGBrowser.exe (PID: 1184)
- AVGBrowser.exe (PID: 2212)
- elevation_service.exe (PID: 3960)
- AVGBrowser.exe (PID: 3768)
- AVGBrowser.exe (PID: 1152)
- AVGBrowser.exe (PID: 1588)
- AVGBrowser.exe (PID: 2332)
- AVGBrowser.exe (PID: 1892)
- elevation_service.exe (PID: 2416)
- AVGBrowser.exe (PID: 860)
- AVGBrowser.exe (PID: 3604)
- cmd.exe (PID: 3668)
- elevation_service.exe (PID: 3580)
- nsF855.tmp (PID: 2816)
- cmd.exe (PID: 4064)
- AVGBrowser.exe (PID: 1860)
- AVGBrowser.exe (PID: 4024)
- AVGBrowser.exe (PID: 2040)
- AVGBrowser.exe (PID: 2588)
- AVGBrowser.exe (PID: 4076)
- AVGBrowser.exe (PID: 3140)
- AVGBrowser.exe (PID: 3312)
- AVGBrowser.exe (PID: 3144)
- AVGBrowser.exe (PID: 4084)
- AVGBrowser.exe (PID: 3892)
- AVGBrowser.exe (PID: 340)
- AVGBrowser.exe (PID: 3376)
- AVGBrowser.exe (PID: 2564)
- AVGBrowser.exe (PID: 3416)
- AVGBrowser.exe (PID: 2588)
- AVGBrowser.exe (PID: 3092)
- AVGBrowser.exe (PID: 3748)
- AVGBrowser.exe (PID: 2908)
- AVGBrowser.exe (PID: 3960)
- AVGBrowser.exe (PID: 2440)
- AVGBrowser.exe (PID: 2556)
- AVGBrowser.exe (PID: 3964)
- AVGBrowser.exe (PID: 648)
- AVGBrowser.exe (PID: 1232)
- AVGBrowser.exe (PID: 3232)
- AVGBrowser.exe (PID: 3868)
- AVGBrowser.exe (PID: 296)
- AVGBrowser.exe (PID: 1136)
- AVGBrowser.exe (PID: 280)
- AVGBrowser.exe (PID: 3068)
- AVGBrowser.exe (PID: 3724)
- AVGBrowser.exe (PID: 3748)
- AVGBrowser.exe (PID: 3604)
- AVGBrowser.exe (PID: 3472)
- AVGBrowser.exe (PID: 876)
- AVGBrowser.exe (PID: 3384)
- AVGBrowser.exe (PID: 3548)
- AVGBrowser.exe (PID: 2088)
- AVGBrowser.exe (PID: 2356)
- AVGBrowser.exe (PID: 4092)
- AVGBrowser.exe (PID: 3472)
- AVGBrowser.exe (PID: 3532)
- AVGBrowser.exe (PID: 1576)
- AVGBrowser.exe (PID: 3980)
- AVGBrowser.exe (PID: 3164)
- AVGBrowser.exe (PID: 3908)
- AVGBrowser.exe (PID: 3860)
- SetupInf.exe (PID: 2348)
- AVGBrowser.exe (PID: 4068)
- AVGBrowser.exe (PID: 328)
- SetupInf.exe (PID: 3532)
- AvEmUpdate.exe (PID: 3348)
- SetupInf.exe (PID: 3204)
- SetupInf.exe (PID: 3112)
- AvEmUpdate.exe (PID: 3488)
- AvEmUpdate.exe (PID: 3452)
- avBugReport.exe (PID: 3972)
- avBugReport.exe (PID: 3588)
- AvEmUpdate.exe (PID: 2404)
- SetupInf.exe (PID: 3468)
- DrvInst.exe (PID: 3132)
- SetupInf.exe (PID: 3732)
- RegSvr.exe (PID: 3900)
- AvastNM.exe (PID: 3356)
- overseer.exe (PID: 2584)
- engsup.exe (PID: 2472)
- wsc_proxy.exe (PID: 1232)
- RegSvr.exe (PID: 116)
- wsc_proxy.exe (PID: 2564)
- AvastSvc.exe (PID: 3176)
- aswToolsSvc.exe (PID: 3252)
- aswEngSrv.exe (PID: 2168)
- engsup.exe (PID: 2044)
Reads the computer name
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 3900)
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
- avg_secure_browser_setup.exe (PID: 2464)
- cookie_mmm_irs_ppi_005_888_a.exe (PID: 2792)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- AVGBrowserUpdate.exe (PID: 2284)
- instup.exe (PID: 2340)
- AVGBrowserUpdate.exe (PID: 3128)
- AVGBrowserUpdate.exe (PID: 764)
- AVGBrowserUpdate.exe (PID: 3840)
- AVGBrowserUpdate.exe (PID: 3404)
- pokemon-sword-and-shield-aa.exe (PID: 3612)
- instup.exe (PID: 2320)
- AVGBrowserInstaller.exe (PID: 2404)
- setup.exe (PID: 3312)
- AVGBrowserCrashHandler.exe (PID: 708)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3744)
- AVGBrowser.exe (PID: 3252)
- elevation_service.exe (PID: 2780)
- AVGBrowser.exe (PID: 1380)
- elevation_service.exe (PID: 3960)
- AVGBrowser.exe (PID: 3768)
- elevation_service.exe (PID: 2416)
- AVGBrowser.exe (PID: 2332)
- AVGBrowser.exe (PID: 1892)
- AVGBrowser.exe (PID: 4024)
- elevation_service.exe (PID: 3580)
- AVGBrowser.exe (PID: 2040)
- SetupInf.exe (PID: 2348)
- SetupInf.exe (PID: 3204)
- SetupInf.exe (PID: 3532)
- AvEmUpdate.exe (PID: 3348)
- SetupInf.exe (PID: 3112)
- AvEmUpdate.exe (PID: 3452)
- AvEmUpdate.exe (PID: 3488)
- avBugReport.exe (PID: 3972)
- avBugReport.exe (PID: 3588)
- AvEmUpdate.exe (PID: 2404)
- SetupInf.exe (PID: 3468)
- SetupInf.exe (PID: 3732)
- DrvInst.exe (PID: 3132)
- RegSvr.exe (PID: 3900)
- overseer.exe (PID: 2584)
- wsc_proxy.exe (PID: 1232)
- RegSvr.exe (PID: 116)
- wsc_proxy.exe (PID: 2564)
- AvastSvc.exe (PID: 3176)
- aswToolsSvc.exe (PID: 3252)
- engsup.exe (PID: 2044)
Executable content was dropped or overwritten
- pokemon-sword-and-shield-aa_kFDy-N1.exe (PID: 2760)
- pokemon-sword-and-shield-aa_kFDy-N1.exe (PID: 3500)
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
- avg_secure_browser_setup.exe (PID: 2464)
- cookie_mmm_irs_ppi_005_888_a.exe (PID: 2792)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- AVGBrowserUpdateSetup.exe (PID: 2400)
- AVGBrowserUpdate.exe (PID: 2284)
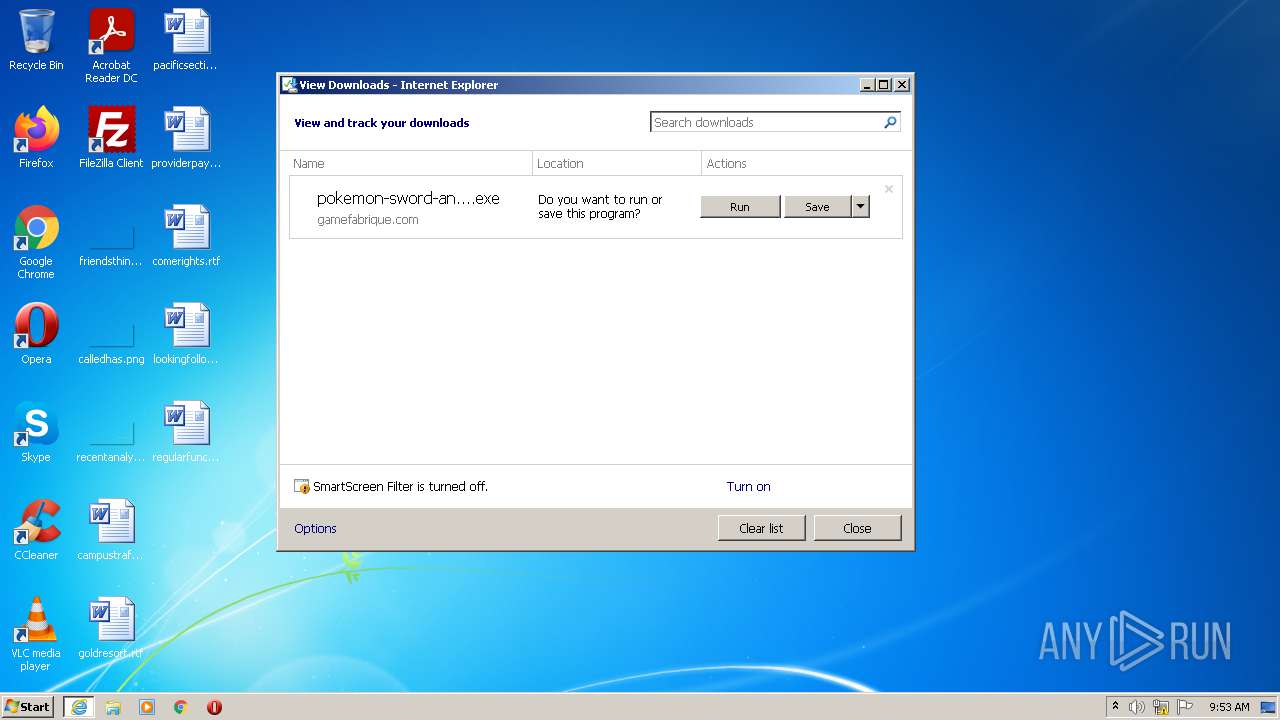
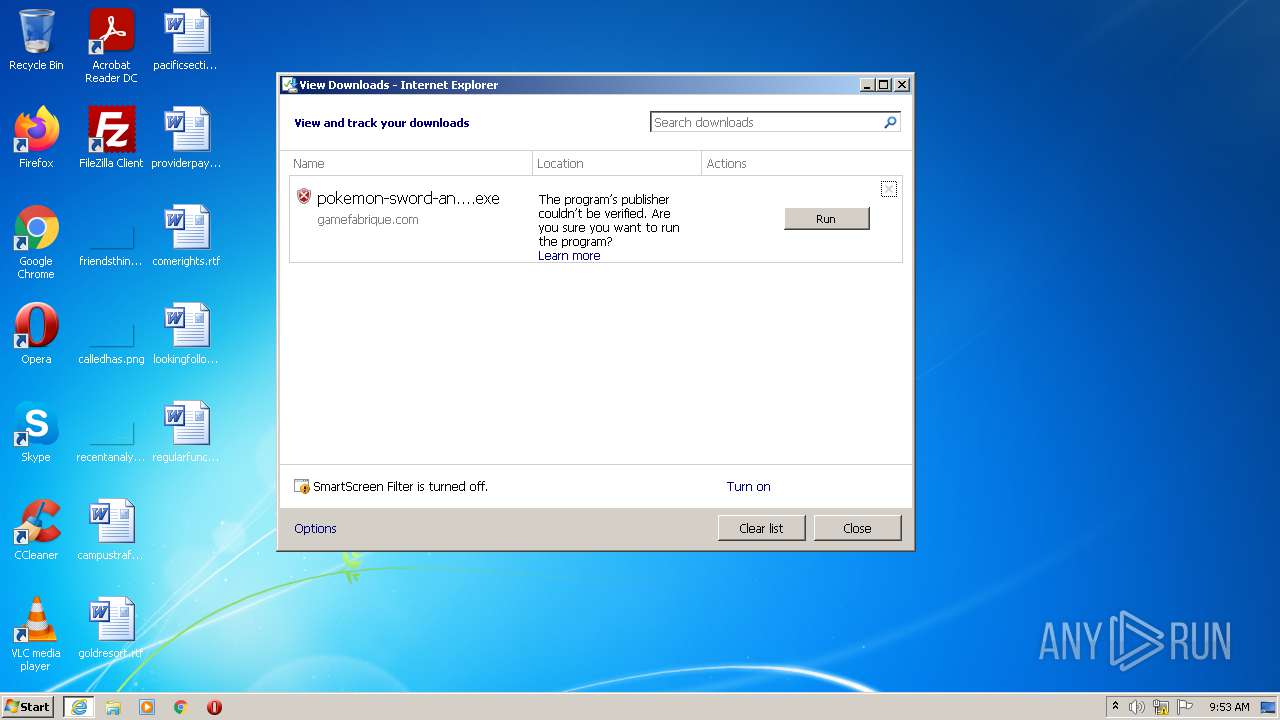
- iexplore.exe (PID: 784)
- instup.exe (PID: 2340)
- iexplore.exe (PID: 2052)
- AVGBrowserInstaller.exe (PID: 2404)
- setup.exe (PID: 3312)
- instup.exe (PID: 2320)
- AvEmUpdate.exe (PID: 3452)
- SetupInf.exe (PID: 3732)
- DrvInst.exe (PID: 3132)
Reads the Windows organization settings
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
Reads Windows owner or organization settings
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
Drops a file that was compiled in debug mode
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
- avg_secure_browser_setup.exe (PID: 2464)
- cookie_mmm_irs_ppi_005_888_a.exe (PID: 2792)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- AVGBrowserUpdateSetup.exe (PID: 2400)
- AVGBrowserUpdate.exe (PID: 2284)
- instup.exe (PID: 2340)
- iexplore.exe (PID: 784)
- iexplore.exe (PID: 2052)
- instup.exe (PID: 2320)
- AVGBrowserInstaller.exe (PID: 2404)
- setup.exe (PID: 3312)
- AvEmUpdate.exe (PID: 3452)
- DrvInst.exe (PID: 3132)
- SetupInf.exe (PID: 3732)
Drops a file with too old compile date
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
- instup.exe (PID: 2320)
Creates files in the Windows directory
- cookie_mmm_irs_ppi_005_888_a.exe (PID: 2792)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- instup.exe (PID: 2340)
- instup.exe (PID: 2320)
- setup.exe (PID: 3132)
- DrvInst.exe (PID: 3132)
- SetupInf.exe (PID: 3732)
- AvastSvc.exe (PID: 3176)
Adds / modifies Windows certificates
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
- AVGBrowserUpdate.exe (PID: 3840)
- AVGBrowser.exe (PID: 1644)
Searches for installed software
- avg_secure_browser_setup.exe (PID: 2464)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3768)
- overseer.exe (PID: 2584)
Reads Environment values
- avg_secure_browser_setup.exe (PID: 2464)
- instup.exe (PID: 2340)
- instup.exe (PID: 2320)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3768)
- AvEmUpdate.exe (PID: 3348)
- AvEmUpdate.exe (PID: 3488)
- AvEmUpdate.exe (PID: 3452)
- AvEmUpdate.exe (PID: 2404)
- AvastSvc.exe (PID: 3176)
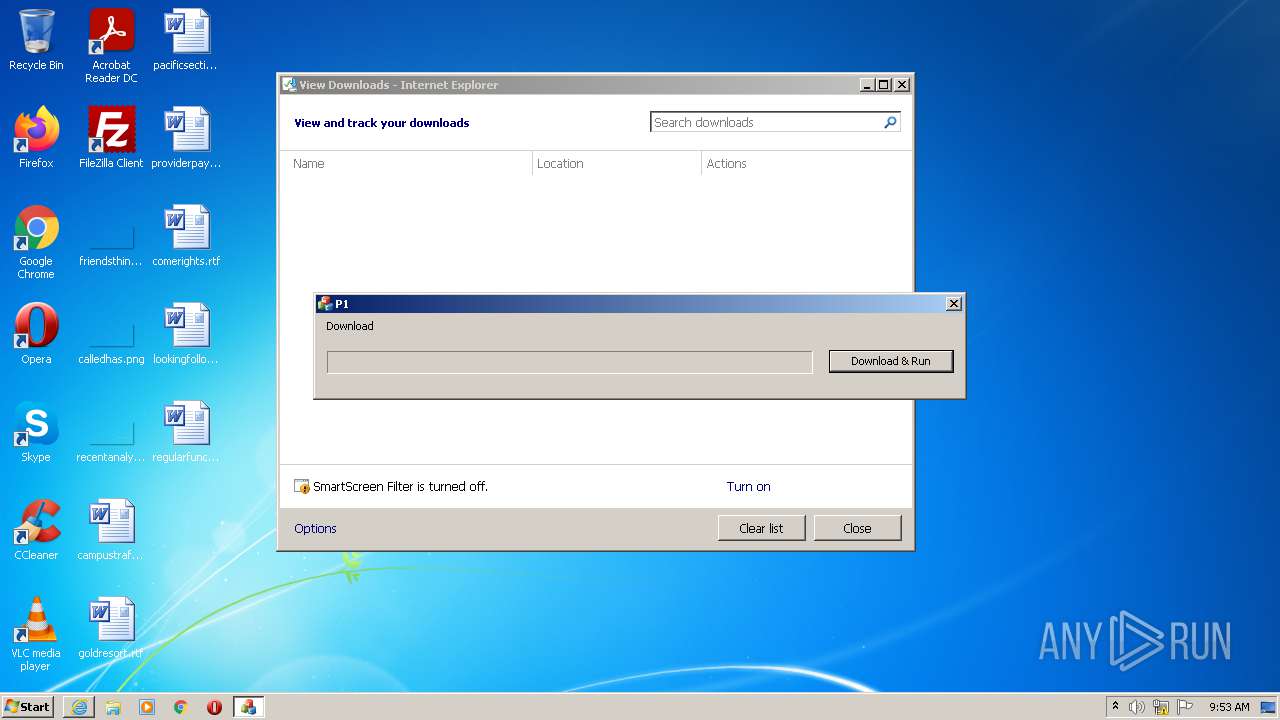
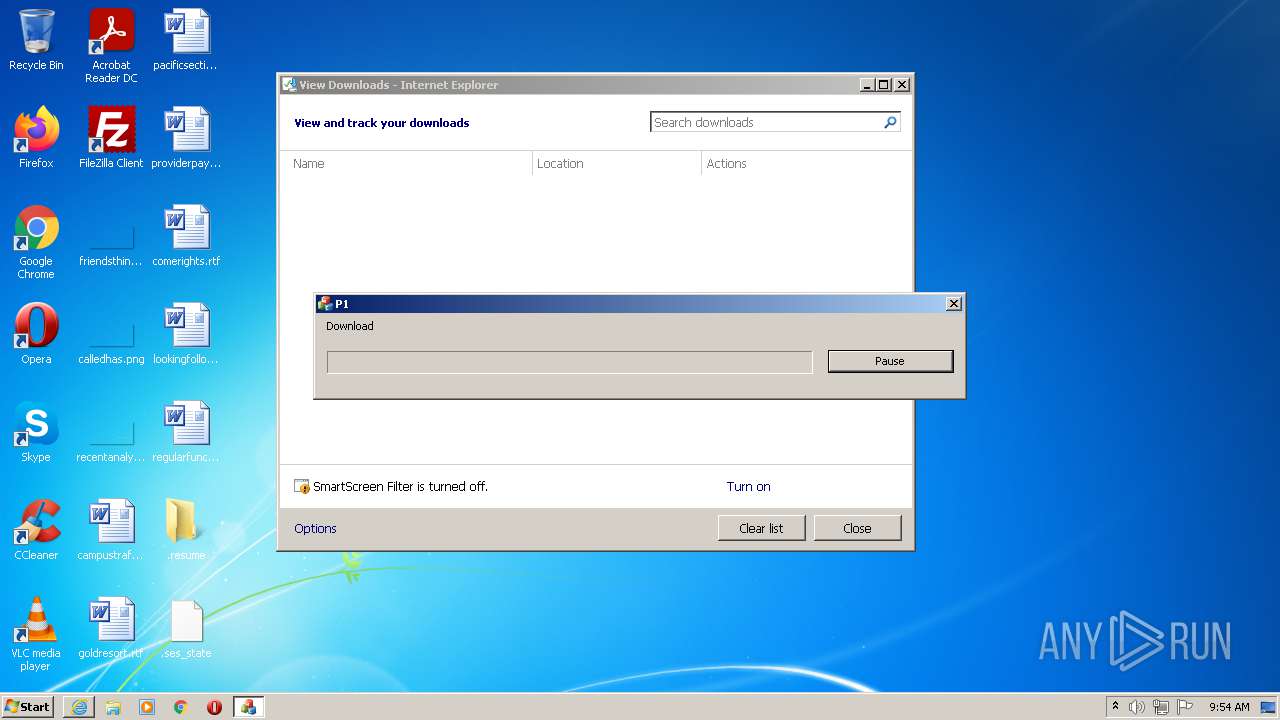
Starts Internet Explorer
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
Creates a directory in Program Files
- AVGBrowserUpdateSetup.exe (PID: 2400)
- AVGBrowserUpdate.exe (PID: 2284)
- AVGBrowserUpdate.exe (PID: 3840)
- instup.exe (PID: 2320)
- AVGBrowserInstaller.exe (PID: 2404)
- setup.exe (PID: 3312)
- AVGBrowser.exe (PID: 1644)
- AvEmUpdate.exe (PID: 3452)
- engsup.exe (PID: 2472)
- AvastSvc.exe (PID: 3176)
Creates files in the program directory
- AVGBrowserUpdateSetup.exe (PID: 2400)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- AVGBrowserUpdate.exe (PID: 2284)
- instup.exe (PID: 2340)
- AVGBrowserInstaller.exe (PID: 2404)
- AVGBrowserUpdate.exe (PID: 3840)
- avg_secure_browser_setup.exe (PID: 2464)
- instup.exe (PID: 2320)
- setup.exe (PID: 3312)
- AVGBrowser.exe (PID: 1644)
- AvEmUpdate.exe (PID: 3348)
- AvEmUpdate.exe (PID: 3452)
- avBugReport.exe (PID: 3972)
- avBugReport.exe (PID: 3588)
- engsup.exe (PID: 2472)
- wsc_proxy.exe (PID: 1232)
- AvastNM.exe (PID: 3356)
- AvastSvc.exe (PID: 3176)
- aswToolsSvc.exe (PID: 3252)
- engsup.exe (PID: 2044)
Drops a file with a compile date too recent
- cookie_mmm_irs_ppi_005_888_a.exe (PID: 2792)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- instup.exe (PID: 2340)
- instup.exe (PID: 2320)
- AVGBrowserInstaller.exe (PID: 2404)
- setup.exe (PID: 3312)
- AvEmUpdate.exe (PID: 3452)
Creates or modifies windows services
- instup.exe (PID: 2340)
- instup.exe (PID: 2320)
Reads CPU info
- instup.exe (PID: 2340)
- instup.exe (PID: 2320)
- SetupInf.exe (PID: 2348)
- SetupInf.exe (PID: 3204)
- SetupInf.exe (PID: 3112)
- SetupInf.exe (PID: 3532)
- AvEmUpdate.exe (PID: 3348)
- AvEmUpdate.exe (PID: 3452)
- AvEmUpdate.exe (PID: 3488)
- AvEmUpdate.exe (PID: 2404)
- avBugReport.exe (PID: 3972)
- avBugReport.exe (PID: 3588)
- SetupInf.exe (PID: 3468)
- SetupInf.exe (PID: 3732)
- RegSvr.exe (PID: 3900)
- RegSvr.exe (PID: 116)
- wsc_proxy.exe (PID: 2564)
- AvastSvc.exe (PID: 3176)
- wsc_proxy.exe (PID: 1232)
- aswToolsSvc.exe (PID: 3252)
Starts itself from another location
- AVGBrowserUpdate.exe (PID: 2284)
- instup.exe (PID: 2340)
Disables SEHOP
- AVGBrowserUpdate.exe (PID: 2284)
Creates/Modifies COM task schedule object
- AVGBrowserUpdate.exe (PID: 3492)
- AVGBrowserUpdate.exe (PID: 2284)
- instup.exe (PID: 2320)
- RegSvr.exe (PID: 3900)
- RegSvr.exe (PID: 116)
Executed as Windows Service
- AVGBrowserUpdate.exe (PID: 3840)
- elevation_service.exe (PID: 2780)
- elevation_service.exe (PID: 3960)
- elevation_service.exe (PID: 2416)
- elevation_service.exe (PID: 3580)
- AvastSvc.exe (PID: 3176)
- aswToolsSvc.exe (PID: 3252)
- wsc_proxy.exe (PID: 2564)
Removes files from Windows directory
- instup.exe (PID: 2340)
- instup.exe (PID: 2320)
- SetupInf.exe (PID: 3732)
- DrvInst.exe (PID: 3132)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 784)
Application launched itself
- setup.exe (PID: 3312)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3768)
- cmd.exe (PID: 3668)
- AvEmUpdate.exe (PID: 3452)
Creates a software uninstall entry
- setup.exe (PID: 3312)
- avg_secure_browser_setup.exe (PID: 2464)
- elevation_service.exe (PID: 2780)
- elevation_service.exe (PID: 2416)
- instup.exe (PID: 2320)
Creates files in the user directory
- setup.exe (PID: 3312)
Reads the date of Windows installation
- setup.exe (PID: 3312)
Changes default file association
- setup.exe (PID: 3312)
- instup.exe (PID: 2320)
Starts application with an unusual extension
- avg_secure_browser_setup.exe (PID: 2464)
Starts CMD.EXE for commands execution
- nsF855.tmp (PID: 2816)
- cmd.exe (PID: 3668)
Creates files in the driver directory
- instup.exe (PID: 2320)
- DrvInst.exe (PID: 3132)
- SetupInf.exe (PID: 3732)
Executed via COM
- DrvInst.exe (PID: 3132)
Reads the cookies of Google Chrome
- engsup.exe (PID: 2044)
Reads the cookies of Mozilla Firefox
- engsup.exe (PID: 2044)
INFO
Application was dropped or rewritten from another process
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 3900)
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
Reads settings of System Certificates
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
- avg_secure_browser_setup.exe (PID: 2464)
- avast_free_antivirus_setup_online.exe (PID: 1956)
- iexplore.exe (PID: 784)
- instup.exe (PID: 2340)
- AVGBrowserUpdate.exe (PID: 764)
- AVGBrowserUpdate.exe (PID: 3840)
- instup.exe (PID: 2320)
- iexplore.exe (PID: 2052)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3768)
- AvEmUpdate.exe (PID: 3452)
- AvEmUpdate.exe (PID: 3488)
- AvEmUpdate.exe (PID: 2404)
- avBugReport.exe (PID: 3972)
- avBugReport.exe (PID: 3588)
- DrvInst.exe (PID: 3132)
Loads dropped or rewritten executable
- pokemon-sword-and-shield-aa_kFDy-N1.tmp (PID: 2408)
Reads the computer name
- iexplore.exe (PID: 2052)
- iexplore.exe (PID: 784)
- PING.EXE (PID: 2084)
Checks Windows Trust Settings
- avg_secure_browser_setup.exe (PID: 2464)
- iexplore.exe (PID: 784)
- iexplore.exe (PID: 2052)
- DrvInst.exe (PID: 3132)
Checks supported languages
- iexplore.exe (PID: 2052)
- iexplore.exe (PID: 784)
- PING.EXE (PID: 2084)
Changes internet zones settings
- iexplore.exe (PID: 2052)
Application launched itself
- iexplore.exe (PID: 2052)
Reads the date of Windows installation
- iexplore.exe (PID: 2052)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2052)
Reads the hosts file
- instup.exe (PID: 2340)
- instup.exe (PID: 2320)
- AVGBrowser.exe (PID: 3252)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3768)
- AVGBrowser.exe (PID: 1892)
- overseer.exe (PID: 2584)
- AvastSvc.exe (PID: 3176)
Dropped object may contain Bitcoin addresses
- instup.exe (PID: 2320)
- AVGBrowser.exe (PID: 1644)
- AVGBrowser.exe (PID: 3724)
- AVGBrowser.exe (PID: 2356)
- AvEmUpdate.exe (PID: 3452)
Creates files in the user directory
- iexplore.exe (PID: 2052)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2052)
Changes settings of System certificates
- iexplore.exe (PID: 2052)
Manual execution by user
- AVGBrowser.exe (PID: 3768)
Dropped object may contain TOR URL's
- AVGBrowser.exe (PID: 3724)
- AVGBrowser.exe (PID: 2356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| ProductVersion: | 1.0.0 |
|---|---|
| ProductName: | Zayats |
| OriginalFileName: | |
| LegalCopyright: | |
| FileVersion: | 1.0.0 |
| FileDescription: | Zayats Download Manager |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 38400 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 09:48:30 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Zayats Download Manager |
| FileVersion: | 1.0.0 |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | Zayats |
| ProductVersion: | 1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 15-Nov-2020 09:48:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x0000463C | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.57956 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.91708 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.91366 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
174
Monitored processes
126
Malicious processes
51
Suspicious processes
41
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Avast Software\Avast\RegSvr.exe" "C:\Program Files\Avast Software\Avast\asOutExt.dll" | C:\Program Files\Avast Software\Avast\RegSvr.exe | — | instup.exe | |||||||||||
User: admin Company: AVAST Software Integrity Level: HIGH Description: Avast Antivirus Installer Exit code: 0 Version: 21.5.6354.0 | |||||||||||||||
| 280 | "C:\Program Files\AVG\Browser\Application\AVGBrowser.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1092,9245044608349970723,324896254169287298,131072 --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4232 /prefetch:8 | C:\Program Files\AVG\Browser\Application\AVGBrowser.exe | — | AVGBrowser.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: LOW Description: AVG Secure Browser Exit code: 0 Version: 91.0.10362.116 Modules
| |||||||||||||||
| 296 | "C:\Program Files\AVG\Browser\Application\AVGBrowser.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1092,9245044608349970723,324896254169287298,131072 --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3560 /prefetch:8 | C:\Program Files\AVG\Browser\Application\AVGBrowser.exe | — | AVGBrowser.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: LOW Description: AVG Secure Browser Exit code: 0 Version: 91.0.10362.116 Modules
| |||||||||||||||
| 328 | "C:\Program Files\AVG\Browser\Application\AVGBrowser.exe" --type=renderer --field-trial-handle=1092,9245044608349970723,324896254169287298,131072 --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=55 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4536 /prefetch:1 | C:\Program Files\AVG\Browser\Application\AVGBrowser.exe | — | AVGBrowser.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: LOW Description: AVG Secure Browser Exit code: 0 Version: 91.0.10362.116 Modules
| |||||||||||||||
| 340 | "C:\Program Files\AVG\Browser\Application\AVGBrowser.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1092,9245044608349970723,324896254169287298,131072 --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2256 /prefetch:8 | C:\Program Files\AVG\Browser\Application\AVGBrowser.exe | — | AVGBrowser.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: LOW Description: AVG Secure Browser Exit code: 0 Version: 91.0.10362.116 Modules
| |||||||||||||||
| 648 | "C:\Program Files\AVG\Browser\Application\AVGBrowser.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1092,9245044608349970723,324896254169287298,131072 --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3636 /prefetch:8 | C:\Program Files\AVG\Browser\Application\AVGBrowser.exe | — | AVGBrowser.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: LOW Description: AVG Secure Browser Exit code: 0 Version: 91.0.10362.116 Modules
| |||||||||||||||
| 668 | "C:\Program Files\AVG\Browser\Application\AVGBrowser.exe" --type=renderer --field-trial-handle=1092,16383265024819019776,10184180296733368842,131072 --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2404 /prefetch:1 | C:\Program Files\AVG\Browser\Application\AVGBrowser.exe | — | AVGBrowser.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: LOW Description: AVG Secure Browser Exit code: 0 Version: 91.0.10362.116 Modules
| |||||||||||||||
| 708 | "C:\Program Files\AVG\Browser\Update\1.8.1066.0\AVGBrowserCrashHandler.exe" | C:\Program Files\AVG\Browser\Update\1.8.1066.0\AVGBrowserCrashHandler.exe | — | AVGBrowserUpdate.exe | |||||||||||
User: SYSTEM Company: AVG Technologies Integrity Level: SYSTEM Description: AVG Browser Crash Handler Exit code: 0 Version: 1.8.1066.0 Modules
| |||||||||||||||
| 764 | "C:\Program Files\AVG\Browser\Update\AVGBrowserUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgb21haGFpZD0iezFDODlFRjJGLUE4OEUtNERFMC05N0ZFLUNCNDBDOEU0RkVFQX0iIHVwZGF0ZXJ2ZXJzaW9uPSIxLjguMTA2Ni4wIiBzaGVsbF92ZXJzaW9uPSIxLjguMTA2Ni4wIiBpc21hY2hpbmU9IjEiIGlzX29tYWhhNjRiaXQ9IjAiIGlzX29zNjRiaXQ9IjAiIHNlc3Npb25pZD0iezAxQzRCMTI0LUYyQjgtNDE1Mi1CQzQzLTk3Q0ZDNkQ1QjRDN30iIGNlcnRfZXhwX2RhdGU9IjIwMjIxMDIwIiB1c2VyaWQ9IntFNDg5RDFGMy01RjFDLTRGMDktQUFDOS1GMzUyQjgwODUwMjR9IiB1c2VyaWRfZGF0ZT0iMjAyMTA3MDMiIG1hY2hpbmVpZD0iezc2MjlGMkIyLTJGN0QtM0UyMi0yMTQyLUIzMEQ0RTk5NjVENH0iIG1hY2hpbmVpZF9kYXRlPSIyMDIxMDcwMyIgaW5zdGFsbHNvdXJjZT0ib3RoZXJpbnN0YWxsY21kIiB0ZXN0c291cmNlPSJhdXRvIiByZXF1ZXN0aWQ9IntDNDdBMDZGRi05MzYzLTRFREQtQUQ5NS1FRTFGMTAwOTk3QjN9IiBkZWR1cD0iY3IiIGRvbWFpbmpvaW5lZD0iMCI-PGh3IHBoeXNtZW1vcnk9IjMiIHNzZT0iMSIgc3NlMj0iMSIgc3NlMz0iMSIgc3NzZTM9IjEiIHNzZTQxPSIxIiBzc2U0Mj0iMSIgYXZ4PSIxIi8-PG9zIHBsYXRmb3JtPSJ3aW4iIHZlcnNpb249IjYuMS43NjAxLjI0NTQ2IiBzcD0iU2VydmljZSBQYWNrIDEiIGFyY2g9Ing4NiIvPjxhcHAgYXBwaWQ9InsxQzg5RUYyRi1BODhFLTRERTAtOTdGRS1DQjQwQzhFNEZFRUF9IiB2ZXJzaW9uPSIiIG5leHR2ZXJzaW9uPSIxLjguMTA2Ni4wIiBsYW5nPSJlbi1VUyIgYnJhbmQ9IjkxNDUiIGNsaWVudD0iIj48ZXZlbnQgZXZlbnR0eXBlPSIyIiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIwIiBpbnN0YWxsX3RpbWVfbXM9IjE1MTYiLz48L2FwcD48L3JlcXVlc3Q- | C:\Program Files\AVG\Browser\Update\AVGBrowserUpdate.exe | AVGBrowserUpdate.exe | ||||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG Browser Exit code: 0 Version: 1.8.1066.0 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2052 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
106 742
Read events
97 026
Write events
9 662
Delete events
54
Modification events
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 6809000041C071CFE86FD701 | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: E300480DF586F0E9DFA2FA50AC63921DFE340F21BBA81C89561681FC1CA91A20 | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\2B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000001BFE69D191B71933A372A80FE155E5B5090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F000000010000003000000066B764A96581128168CF208E374DDA479D54E311F32457F4AEE0DBD2A6C8D171D531289E1CD22BFDBBD4CFD9796254830300000001000000140000002B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E0B00000001000000100000005300650063007400690067006F0000001D0000000100000010000000885010358D29A38F059B028559C95F901400000001000000140000005379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB620000000100000020000000E793C9B02FD8AA13E21C31228ACCB08119643B749C898964B1746D46C3D4CBD2190000000100000010000000EA6089055218053DD01E37E1D806EEDF53000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C02000000001000000E2050000308205DE308203C6A003020102021001FD6D30FCA3CA51A81BBC640E35032D300D06092A864886F70D01010C0500308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F72697479301E170D3130303230313030303030305A170D3338303131383233353935395A308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010080126517360EC3DB08B3D0AC570D76EDCD27D34CAD508361E2AA204D092D6409DCCE899FCC3DA9ECF6CFC1DCF1D3B1D67B3728112B47DA39C6BC3A19B45FA6BD7D9DA36342B676F2A93B2B91F8E26FD0EC162090093EE2E874C918B491D46264DB7FA306F188186A90223CBCFE13F087147BF6E41F8ED4E451C61167460851CB8614543FBC33FE7E6C9CFF169D18BD518E35A6A766C87267DB2166B1D49B7803C0503AE8CCF0DCBC9E4CFEAF0596351F575AB7FFCEF93DB72CB6F654DDC8E7123A4DAE4C8AB75C9AB4B7203DCA7F2234AE7E3B68660144E7014E46539B3360F794BE5337907343F332C353EFDBAAFE744E69C76B8C6093DEC4C70CDFE132AECC933B517895678BEE3D56FE0CD0690F1B0FF325266B336DF76E47FA7343E57E0EA566B1297C3284635589C40DC19354301913ACD37D37A7EB5D3A6C355CDB41D712DAA9490BDFD8808A0993628EB566CF2588CD84B8B13FA4390FD9029EEB124C957CF36B05A95E1683CCB867E2E8139DCC5B82D34CB3ED5BFFDEE573AC233B2D00BF3555740949D849581A7F9236E651920EF3267D1C4D17BCC9EC4326D0BF415F40A94444F499E757879E501F5754A83EFD74632FB1506509E658422E431A4CB4F0254759FA041E93D426464A5081B2DEBE78B7FC6715E1C957841E0F63D6E962BAD65F552EEA5CC62808042539B80E2BA9F24C971C073F0D52F5EDEF2F820F0203010001A3423040301D0603551D0E041604145379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF300D06092A864886F70D01010C050003820201005CD47C0DCFF7017D4199650C73C5529FCBF8CF99067F1BDA43159F9E0255579614F1523C27879428ED1F3A0137A276FC5350C0849BC66B4EBA8C214FA28E556291F36915D8BC88E3C4AA0BFDEFA8E94B552A06206D55782919EE5F305C4B241155FF249A6E5E2A2BEE0B4D9F7FF70138941495430709FB60A9EE1CAB128CA09A5EA7986A596D8B3F08FBC8D145AF18156490120F73282EC5E2244EFC58ECF0F445FE22B3EB2F8ED2D9456105C1976FA876728F8B8C36AFBF0D05CE718DE6A66F1F6CA67162C5D8D083720CF16711890C9C134C7234DFBCD571DFAA71DDE1B96C8C3C125D65DABD5712B6436BFFE5DE4D661151CF99AEEC17B6E871918CDE49FEDD3571A21527941CCF61E326BB6FA36725215DE6DD1D0B2E681B3B82AFEC836785D4985174B1B9998089FF7F78195C794A602E9240AE4C372A2CC9C762C80E5DF7365BCAE0252501B4DD1A079C77003FD0DCD5EC3DD4FABB3FCC85D66F7FA92DDFB902F7F5979AB535DAC367B0874AA9289E238EFF5C276BE1B04FF307EE002ED45987CB524195EAF447D7EE6441557C8D590295DD629DC2B9EE5A287484A59BB790C70C07DFF589367432D628C1B0B00BE09C4CC31CD6FCE369B54746812FA282ABD3634470C48DFF2D33BAAD8F7BB57088AE3E19CF4028D8FCC890BB5D9922F552E658C51F883143EE881DD7C68E3C436A1DA718DE7D3D16F162F9CA90A8FD | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\2B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E |
| Operation: | write | Name: | Blob |
Value: 5C00000001000000040000000010000053000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0190000000100000010000000EA6089055218053DD01E37E1D806EEDF620000000100000020000000E793C9B02FD8AA13E21C31228ACCB08119643B749C898964B1746D46C3D4CBD21400000001000000140000005379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB1D0000000100000010000000885010358D29A38F059B028559C95F900B00000001000000100000005300650063007400690067006F0000000300000001000000140000002B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E0F000000010000003000000066B764A96581128168CF208E374DDA479D54E311F32457F4AEE0DBD2A6C8D171D531289E1CD22BFDBBD4CFD979625483090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080400000001000000100000001BFE69D191B71933A372A80FE155E5B52000000001000000E2050000308205DE308203C6A003020102021001FD6D30FCA3CA51A81BBC640E35032D300D06092A864886F70D01010C0500308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F72697479301E170D3130303230313030303030305A170D3338303131383233353935395A308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010080126517360EC3DB08B3D0AC570D76EDCD27D34CAD508361E2AA204D092D6409DCCE899FCC3DA9ECF6CFC1DCF1D3B1D67B3728112B47DA39C6BC3A19B45FA6BD7D9DA36342B676F2A93B2B91F8E26FD0EC162090093EE2E874C918B491D46264DB7FA306F188186A90223CBCFE13F087147BF6E41F8ED4E451C61167460851CB8614543FBC33FE7E6C9CFF169D18BD518E35A6A766C87267DB2166B1D49B7803C0503AE8CCF0DCBC9E4CFEAF0596351F575AB7FFCEF93DB72CB6F654DDC8E7123A4DAE4C8AB75C9AB4B7203DCA7F2234AE7E3B68660144E7014E46539B3360F794BE5337907343F332C353EFDBAAFE744E69C76B8C6093DEC4C70CDFE132AECC933B517895678BEE3D56FE0CD0690F1B0FF325266B336DF76E47FA7343E57E0EA566B1297C3284635589C40DC19354301913ACD37D37A7EB5D3A6C355CDB41D712DAA9490BDFD8808A0993628EB566CF2588CD84B8B13FA4390FD9029EEB124C957CF36B05A95E1683CCB867E2E8139DCC5B82D34CB3ED5BFFDEE573AC233B2D00BF3555740949D849581A7F9236E651920EF3267D1C4D17BCC9EC4326D0BF415F40A94444F499E757879E501F5754A83EFD74632FB1506509E658422E431A4CB4F0254759FA041E93D426464A5081B2DEBE78B7FC6715E1C957841E0F63D6E962BAD65F552EEA5CC62808042539B80E2BA9F24C971C073F0D52F5EDEF2F820F0203010001A3423040301D0603551D0E041604145379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF300D06092A864886F70D01010C050003820201005CD47C0DCFF7017D4199650C73C5529FCBF8CF99067F1BDA43159F9E0255579614F1523C27879428ED1F3A0137A276FC5350C0849BC66B4EBA8C214FA28E556291F36915D8BC88E3C4AA0BFDEFA8E94B552A06206D55782919EE5F305C4B241155FF249A6E5E2A2BEE0B4D9F7FF70138941495430709FB60A9EE1CAB128CA09A5EA7986A596D8B3F08FBC8D145AF18156490120F73282EC5E2244EFC58ECF0F445FE22B3EB2F8ED2D9456105C1976FA876728F8B8C36AFBF0D05CE718DE6A66F1F6CA67162C5D8D083720CF16711890C9C134C7234DFBCD571DFAA71DDE1B96C8C3C125D65DABD5712B6436BFFE5DE4D661151CF99AEEC17B6E871918CDE49FEDD3571A21527941CCF61E326BB6FA36725215DE6DD1D0B2E681B3B82AFEC836785D4985174B1B9998089FF7F78195C794A602E9240AE4C372A2CC9C762C80E5DF7365BCAE0252501B4DD1A079C77003FD0DCD5EC3DD4FABB3FCC85D66F7FA92DDFB902F7F5979AB535DAC367B0874AA9289E238EFF5C276BE1B04FF307EE002ED45987CB524195EAF447D7EE6441557C8D590295DD629DC2B9EE5A287484A59BB790C70C07DFF589367432D628C1B0B00BE09C4CC31CD6FCE369B54746812FA282ABD3634470C48DFF2D33BAAD8F7BB57088AE3E19CF4028D8FCC890BB5D9922F552E658C51F883143EE881DD7C68E3C436A1DA718DE7D3D16F162F9CA90A8FD | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D1EB23A46D17D68FD92564C2F1F1601764D8E349 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000497904B0EB8719AC47B0BC11519B74D0090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F00000001000000140000003E8E6487F8FD27D322A269A71EDAAC5D57811286030000000100000014000000D1EB23A46D17D68FD92564C2F1F1601764D8E3491D00000001000000100000002E0D6875874A44C820912E85E964CFDB140000000100000014000000A0110A233E96F107ECE2AF29EF82A57FD030A4B40B000000010000001C0000005300650063007400690067006F002000280041004100410029000000620000000100000020000000D7A7A0FB5D7E2731D771E9484EBCDEF71D5F0C3E0A2948782BC83EE0EA699EF41900000001000000100000002AA1C05E2AE606F198C2C5E937C97AA253000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0200000000100000036040000308204323082031AA003020102020101300D06092A864886F70D0101050500307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C18414141204365727469666963617465205365727669636573301E170D3034303130313030303030305A170D3238313233313233353935395A307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C1841414120436572746966696361746520536572766963657330820122300D06092A864886F70D01010105000382010F003082010A0282010100BE409DF46EE1EA76871C4D45448EBE46C883069DC12AFE181F8EE402FAF3AB5D508A16310B9A06D0C57022CD492D5463CCB66E68460B53EACB4C24C0BC724EEAF115AEF4549A120AC37AB23360E2DA8955F32258F3DEDCCFEF8386A28C944F9F68F29890468427C776BFE3CC352C8B5E07646582C048B0A891F9619F762050A891C766B5EB78620356F08A1A13EA31A31EA099FD38F6F62732586F07F56BB8FB142BAFB7AACCD6635F738CDA0599A838A8CB17783651ACE99EF4783A8DCF0FD942E2980CAB2F9F0E01DEEF9F9949F12DDFAC744D1B98B547C5E529D1F99018C7629CBE83C7267B3E8A25C7C0DD9DE6356810209D8FD8DED2C3849C0D5EE82FC90203010001A381C03081BD301D0603551D0E04160414A0110A233E96F107ECE2AF29EF82A57FD030A4B4300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF307B0603551D1F047430723038A036A0348632687474703A2F2F63726C2E636F6D6F646F63612E636F6D2F414141436572746966696361746553657276696365732E63726C3036A034A0328630687474703A2F2F63726C2E636F6D6F646F2E6E65742F414141436572746966696361746553657276696365732E63726C300D06092A864886F70D010105050003820101000856FC02F09BE8FFA4FAD67BC64480CE4FC4C5F60058CCA6B6BC1449680476E8E6EE5DEC020F60D68D50184F264E01E3E6B0A5EEBFBC745441BFFDFC12B8C74F5AF48960057F60B7054AF3F6F1C2BFC4B97486B62D7D6BCCD2F346DD2FC6E06AC3C334032C7D96DD5AC20EA70A99C1058BAB0C2FF35C3ACF6C37550987DE53406C58EFFCB6AB656E04F61BDC3CE05A15C69ED9F15948302165036CECE92173EC9B03A1E037ADA015188FFABA02CEA72CA910132CD4E50826AB229760F8905E74D4A29A53BDF2A968E0A26EC2D76CB1A30F9EBFEB68E756F2AEF2E32B383A0981B56B85D7BE2DED3F1AB7B263E2F5622C82D46A004150F139839F95E93696986E | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D1EB23A46D17D68FD92564C2F1F1601764D8E349 |
| Operation: | write | Name: | Blob |
Value: 5C00000001000000040000000008000053000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C01900000001000000100000002AA1C05E2AE606F198C2C5E937C97AA2620000000100000020000000D7A7A0FB5D7E2731D771E9484EBCDEF71D5F0C3E0A2948782BC83EE0EA699EF40B000000010000001C0000005300650063007400690067006F002000280041004100410029000000140000000100000014000000A0110A233E96F107ECE2AF29EF82A57FD030A4B41D00000001000000100000002E0D6875874A44C820912E85E964CFDB030000000100000014000000D1EB23A46D17D68FD92564C2F1F1601764D8E3490F00000001000000140000003E8E6487F8FD27D322A269A71EDAAC5D57811286090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B06010505070308040000000100000010000000497904B0EB8719AC47B0BC11519B74D0200000000100000036040000308204323082031AA003020102020101300D06092A864886F70D0101050500307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C18414141204365727469666963617465205365727669636573301E170D3034303130313030303030305A170D3238313233313233353935395A307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C1841414120436572746966696361746520536572766963657330820122300D06092A864886F70D01010105000382010F003082010A0282010100BE409DF46EE1EA76871C4D45448EBE46C883069DC12AFE181F8EE402FAF3AB5D508A16310B9A06D0C57022CD492D5463CCB66E68460B53EACB4C24C0BC724EEAF115AEF4549A120AC37AB23360E2DA8955F32258F3DEDCCFEF8386A28C944F9F68F29890468427C776BFE3CC352C8B5E07646582C048B0A891F9619F762050A891C766B5EB78620356F08A1A13EA31A31EA099FD38F6F62732586F07F56BB8FB142BAFB7AACCD6635F738CDA0599A838A8CB17783651ACE99EF4783A8DCF0FD942E2980CAB2F9F0E01DEEF9F9949F12DDFAC744D1B98B547C5E529D1F99018C7629CBE83C7267B3E8A25C7C0DD9DE6356810209D8FD8DED2C3849C0D5EE82FC90203010001A381C03081BD301D0603551D0E04160414A0110A233E96F107ECE2AF29EF82A57FD030A4B4300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF307B0603551D1F047430723038A036A0348632687474703A2F2F63726C2E636F6D6F646F63612E636F6D2F414141436572746966696361746553657276696365732E63726C3036A034A0328630687474703A2F2F63726C2E636F6D6F646F2E6E65742F414141436572746966696361746553657276696365732E63726C300D06092A864886F70D010105050003820101000856FC02F09BE8FFA4FAD67BC64480CE4FC4C5F60058CCA6B6BC1449680476E8E6EE5DEC020F60D68D50184F264E01E3E6B0A5EEBFBC745441BFFDFC12B8C74F5AF48960057F60B7054AF3F6F1C2BFC4B97486B62D7D6BCCD2F346DD2FC6E06AC3C334032C7D96DD5AC20EA70A99C1058BAB0C2FF35C3ACF6C37550987DE53406C58EFFCB6AB656E04F61BDC3CE05A15C69ED9F15948302165036CECE92173EC9B03A1E037ADA015188FFABA02CEA72CA910132CD4E50826AB229760F8905E74D4A29A53BDF2A968E0A26EC2D76CB1A30F9EBFEB68E756F2AEF2E32B383A0981B56B85D7BE2DED3F1AB7B263E2F5622C82D46A004150F139839F95E93696986E | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2408) pokemon-sword-and-shield-aa_kFDy-N1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
662
Suspicious files
356
Text files
1 575
Unknown types
197
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\is-20DR6.tmp | image | |
MD5:— | SHA256:— | |||
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\AVG_BRW.png | image | |
MD5:— | SHA256:— | |||
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\AVAST.png | image | |
MD5:— | SHA256:— | |||
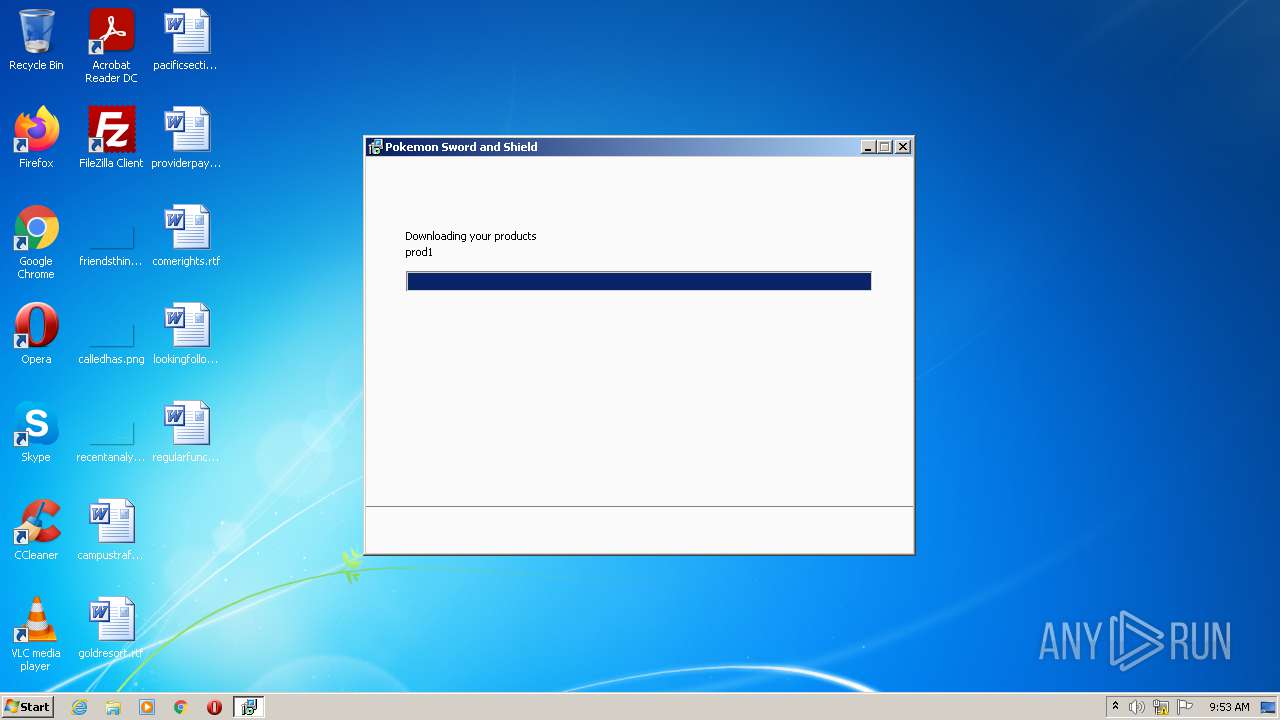
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\prod1.zip | compressed | |
MD5:— | SHA256:— | |||
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\is-12LUM.tmp | image | |
MD5:— | SHA256:— | |||
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\is-C7HJV.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\is-CUTJE.tmp | executable | |
MD5:— | SHA256:— | |||
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\prod1 | compressed | |
MD5:— | SHA256:— | |||
| 2760 | pokemon-sword-and-shield-aa_kFDy-N1.exe | C:\Users\admin\AppData\Local\Temp\is-JJL92.tmp\pokemon-sword-and-shield-aa_kFDy-N1.tmp | executable | |
MD5:311B22DC1AB475024F633C620183F4B9 | SHA256:8B2ABF30C0BF06696702F6D1112155929EBB4D9CEA26B24B21517E7837C9E7B1 | |||
| 2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | C:\Users\admin\AppData\Local\Temp\is-73465.tmp\prod0.zip | compressed | |
MD5:C0526C31262A1C5BCC1F0DE4838A65E8 | SHA256:4248B397B4ADEE48F749F004B8233FD41ECCEF3A0417CB7655070A875EA0CF74 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
44
DNS requests
68
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | avg_secure_browser_setup.exe | GET | — | 2.16.186.25:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1965e42a068b9dfb | unknown | — | — | whitelisted |
2464 | avg_secure_browser_setup.exe | GET | — | 143.204.101.177:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | — | — | whitelisted |
2464 | avg_secure_browser_setup.exe | GET | — | 143.204.101.42:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | — | — | whitelisted |
2340 | instup.exe | GET | — | 2.22.146.73:80 | http://n4291289.iavs9x.u.avast.com/iavs9x/servers.def.vpx | GB | — | — | whitelisted |
2340 | instup.exe | GET | — | 2.22.146.35:80 | http://h4444966.iavs9x.u.avast.com/iavs9x/offertool_ais-9a6.vpx | GB | — | — | whitelisted |
2792 | cookie_mmm_irs_ppi_005_888_a.exe | GET | 200 | 2.16.107.98:80 | http://iavs9x.u.avast.com/iavs9x/avast_free_antivirus_setup_online.exe | unknown | — | 7.83 Mb | whitelisted |
2464 | avg_secure_browser_setup.exe | GET | — | 143.204.101.42:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | — | — | shared |
2464 | avg_secure_browser_setup.exe | GET | — | 143.204.101.188:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAwCnukieaCcF5csPv6uzhA%3D | US | — | — | whitelisted |
2340 | instup.exe | GET | — | 2.22.146.35:80 | http://h4444966.iavs9x.u.avast.com/iavs9x/avbugreport_ais-9a6.vpx | GB | — | — | whitelisted |
2792 | cookie_mmm_irs_ppi_005_888_a.exe | POST | 204 | 5.62.40.212:80 | http://v7event.stats.avast.com/cgi-bin/iavsevents.cgi | DE | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1360 | svchost.exe | 20.73.194.208:443 | — | — | US | whitelisted |
2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | 143.204.101.231:443 | d2yt3cv5wvb9w9.cloudfront.net | — | US | suspicious |
2792 | cookie_mmm_irs_ppi_005_888_a.exe | 142.250.74.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2792 | cookie_mmm_irs_ppi_005_888_a.exe | 5.62.40.212:80 | v7event.stats.avast.com | AVAST Software s.r.o. | DE | unknown |
2464 | avg_secure_browser_setup.exe | 143.204.101.188:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
2408 | pokemon-sword-and-shield-aa_kFDy-N1.tmp | 89.248.171.137:443 | gamefabrique.com | Quasi Networks LTD. | SC | suspicious |
2464 | avg_secure_browser_setup.exe | 54.83.80.136:443 | stats.avgbrowser.com | Amazon.com, Inc. | US | unknown |
2464 | avg_secure_browser_setup.exe | 143.204.101.177:80 | o.ss2.us | — | US | suspicious |
2792 | cookie_mmm_irs_ppi_005_888_a.exe | 2.16.107.98:80 | iavs9x.u.avast.com | Akamai International B.V. | — | suspicious |
2340 | instup.exe | 2.22.146.35:80 | g1928587.iavs9x.u.avast.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d2yt3cv5wvb9w9.cloudfront.net |
| whitelisted |
gamefabrique.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
v7event.stats.avast.com |
| whitelisted |
iavs9x.u.avast.com |
| whitelisted |
stats.avgbrowser.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2792 | cookie_mmm_irs_ppi_005_888_a.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3612 | pokemon-sword-and-shield-aa.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
3452 | AvEmUpdate.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
overseer.exe | Unable to perform cURL request!
Couldn't resolve host name (Could not resolve: yesno.ff.avast.com (DNS server returned answer with no data)) (0x00000006) |
AvastSvc.exe | [2021-07-03 08:56:13.364] [error ] [tasks ] [ 3176: 3316] task asw::settings::SettingsModule::OnPropertyChanged: failed without a caller check.
Exception: asw::event_routing::rpc::GenericEventSender: rpcEndpoint is NULL.
|
AvastSvc.exe | [2021-07-03 08:56:13.989] [error ] [ring_client] [ 3176: 2028] asw::ring_client::NetworkStatus::isInternetAvailable::<lambda_2>::operator () call anen failed
|
AvastSvc.exe | [2021-07-03 08:56:13.989] [error ] [ring_client] [ 3176: 2028] asw::ring_client::call_anen_exception failed reason: Request app.anen.global.get_connectivity was not processed. Routing parameters:
|
AvastSvc.exe | [2021-07-03 08:56:14.458] [error ] [SecureDNS ] [ 3176: 2808] Initialization has failed (1) times
|