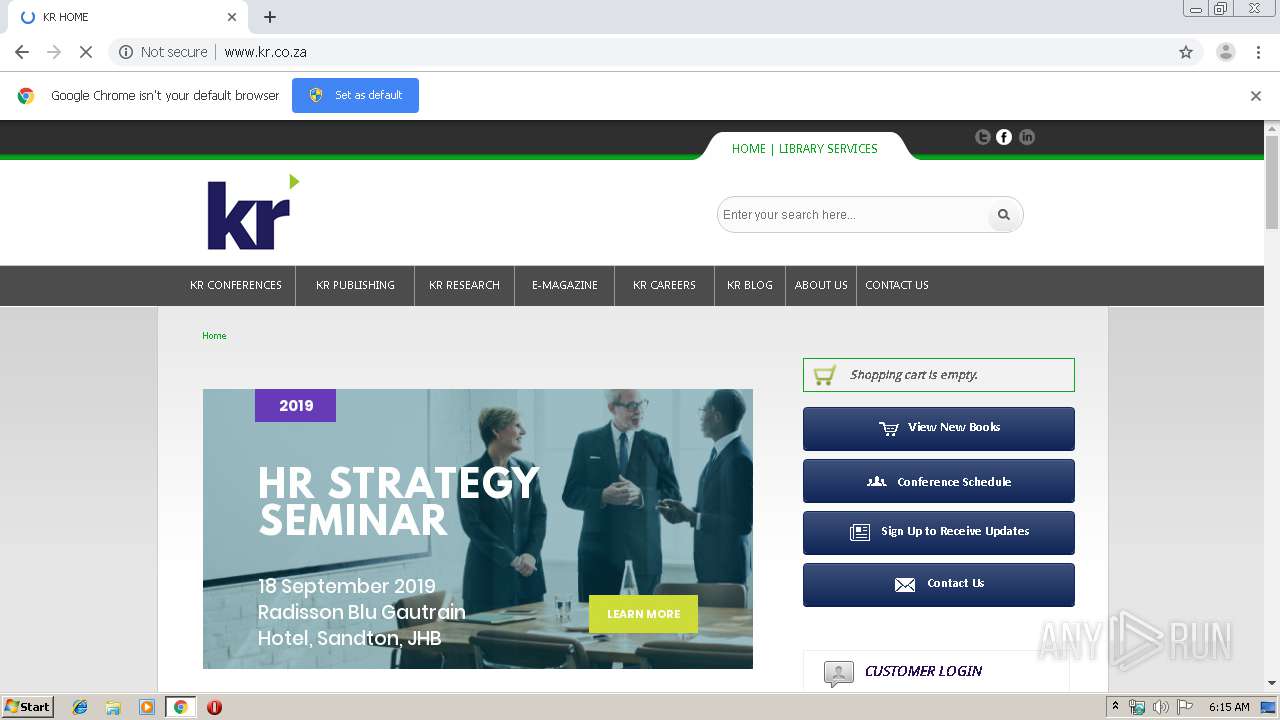
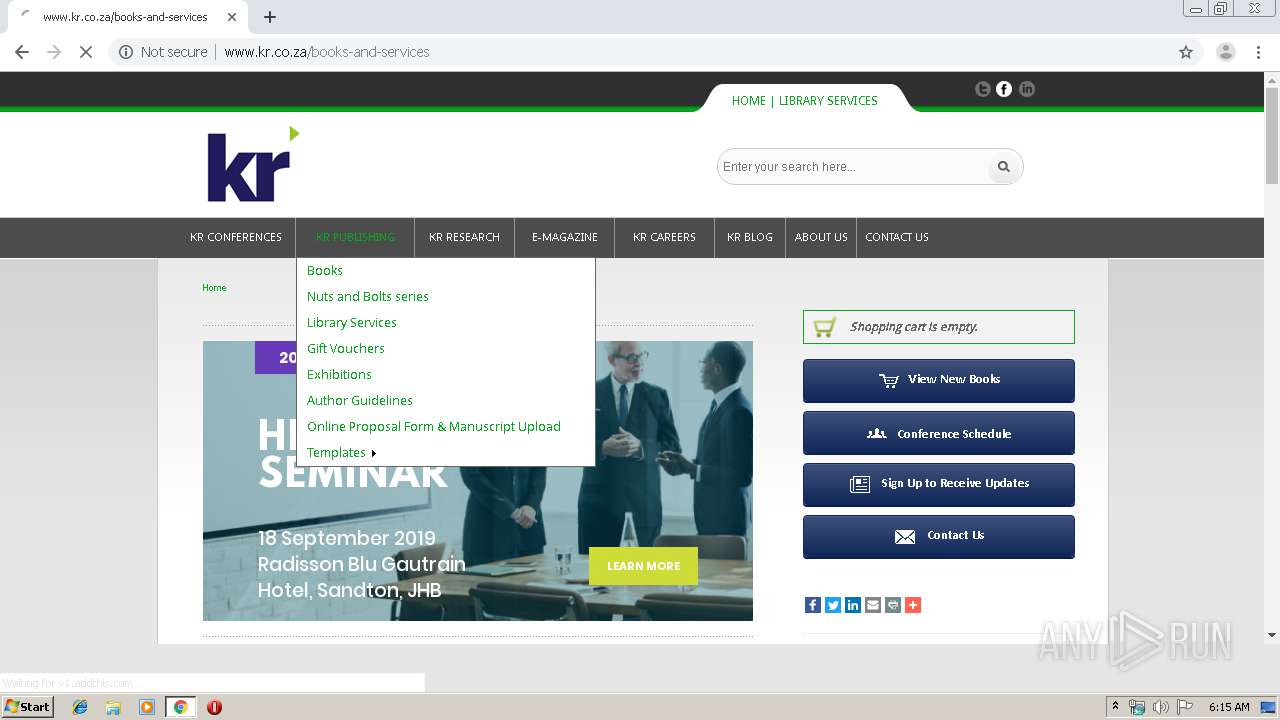
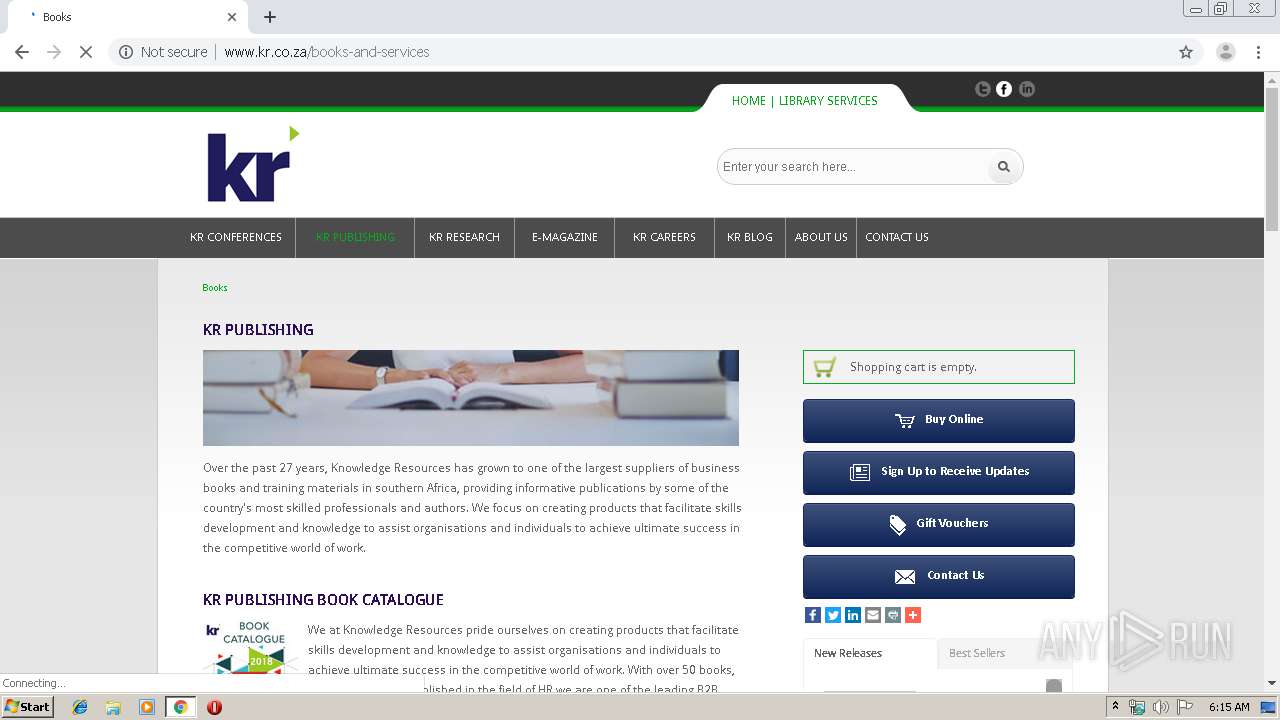
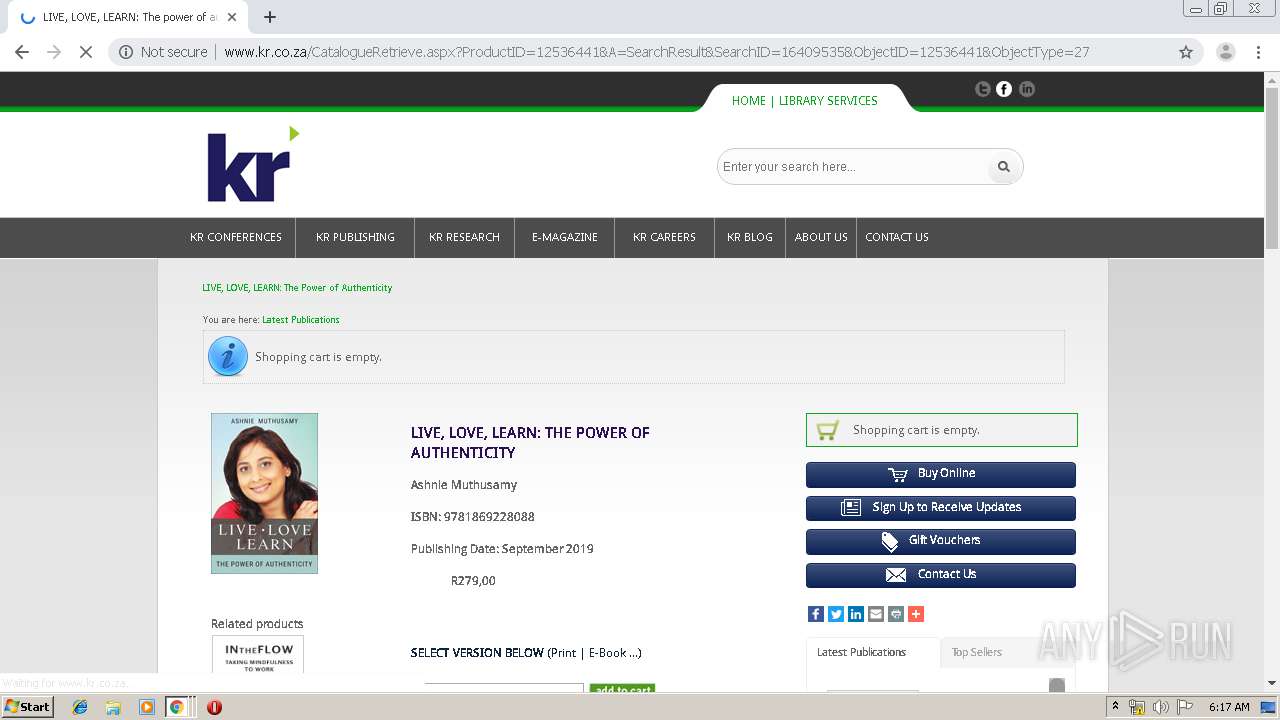
| URL: | http://www.kr.co.za/knowres-publishing-1/gender-equality-at-work-some-are-more-equal-than-others |
| Full analysis: | https://app.any.run/tasks/c254a8ab-fe69-4d67-bd6b-9f212f707f2c |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 05:15:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2F7DB3AAB25901205A6BF9DC44EC69C1 |
| SHA1: | 11D5B2027FFA8BAEB61F3F55F2F2A1B68DD3BB64 |
| SHA256: | E201A7C58D448D717471C3C767F31AEA2F8375014EBB7176465ED745936FF6C8 |
| SSDEEP: | 3:N1KJS4GGQsVatQpdKCpZP54qnN9O1MxJIe3RNAXW:Cc4GGtat63hji16Ie3Rf |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3548)
INFO
Reads the hosts file
- chrome.exe (PID: 3548)
- chrome.exe (PID: 2932)
Reads settings of System Certificates
- chrome.exe (PID: 2932)
Application launched itself
- chrome.exe (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
82
Monitored processes
48
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2584492879919455662 --mojo-platform-channel-handle=4208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14604508412119830211 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10248061882076438953 --mojo-platform-channel-handle=4172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3890174100046625016 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5234939113925608380 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14932323934161375570 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7211506290705814837 --mojo-platform-channel-handle=3188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fd9a9d0,0x6fd9a9e0,0x6fd9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6334610883819278980 --mojo-platform-channel-handle=3936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13887598398254650432 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
659
Read events
548
Write events
106
Delete events
5
Modification events
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3548-13212652519478875 |
Value: 259 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
195
Text files
236
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\43d40fb1-823f-4618-8e8c-b555e66b0d1b.tmp | — | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169ba8.TMP | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169b99.TMP | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169be7.TMP | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
105
TCP/UDP connections
90
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | chrome.exe | GET | 404 | 54.236.190.114:80 | http://www.kr.co.za/StyleSheets/ModuleStyleSheets.css | US | text | 33 b | suspicious |
2932 | chrome.exe | GET | 200 | 54.236.190.114:80 | http://www.kr.co.za/css/styles.css?version=0.2 | US | text | 8.07 Kb | suspicious |
2932 | chrome.exe | GET | 404 | 54.236.190.114:80 | http://www.kr.co.za/knowres-publishing-1/images/scroll/jquery.jscrollpane.lozenge.css | US | text | 33 b | suspicious |
2932 | chrome.exe | GET | 200 | 54.236.190.114:80 | http://www.kr.co.za/css/basic-jquery-slider.css | US | text | 730 b | suspicious |
2932 | chrome.exe | GET | 200 | 54.236.190.114:80 | http://www.kr.co.za/css/pictos.css | US | text | 594 b | suspicious |
2932 | chrome.exe | GET | 200 | 54.236.190.114:80 | http://www.kr.co.za/CatalystStyles/Box.css?vs=b345.r524716-phase1 | US | text | 276 b | suspicious |
2932 | chrome.exe | GET | 200 | 54.236.190.114:80 | http://www.kr.co.za/javascripts/scrollpane/jquery.jscrollpane.js | US | text | 13.3 Kb | suspicious |
2932 | chrome.exe | GET | 200 | 54.236.190.114:80 | http://www.kr.co.za/javascripts/basic-jquery-slider.js | US | html | 3.67 Kb | suspicious |
2932 | chrome.exe | GET | 200 | 54.236.190.114:80 | http://www.kr.co.za/javascripts/simpletabs/simpletabs_1.3.packed.js | US | text | 1.74 Kb | suspicious |
2932 | chrome.exe | GET | 200 | 54.236.190.114:80 | http://www.kr.co.za/css/jquery.jscrollpane.css | US | text | 748 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 54.236.190.114:80 | www.kr.co.za | Amazon.com, Inc. | US | suspicious |
2932 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.16.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 23.210.248.44:80 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2932 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2932 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 216.58.207.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kr.co.za |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.facebook.com |
| whitelisted |
twitter.com |
| whitelisted |
www.linkedin.com |
| whitelisted |