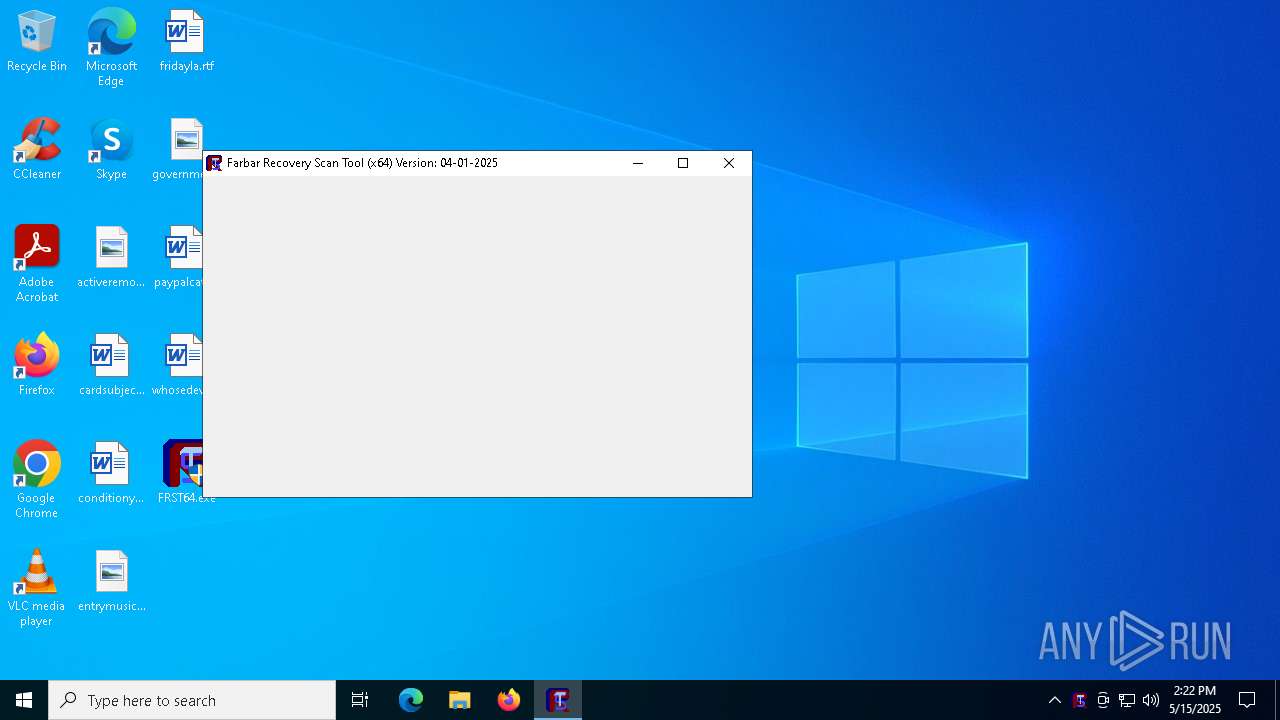
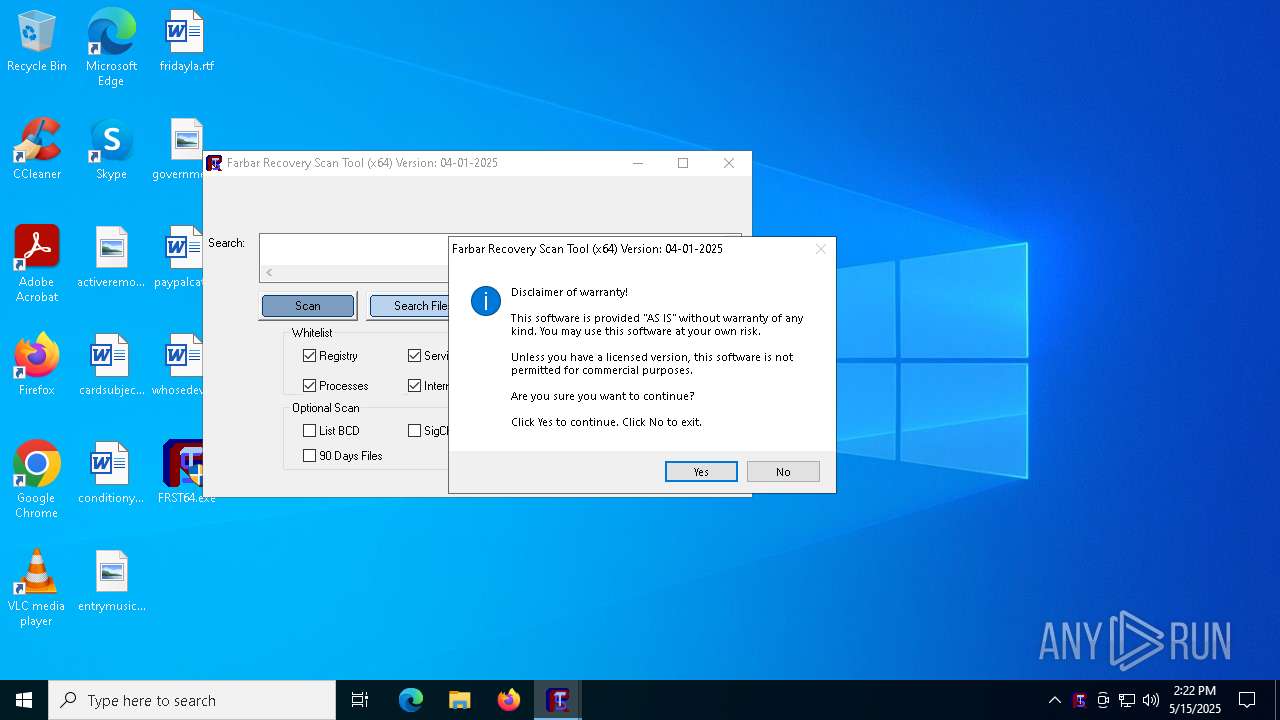
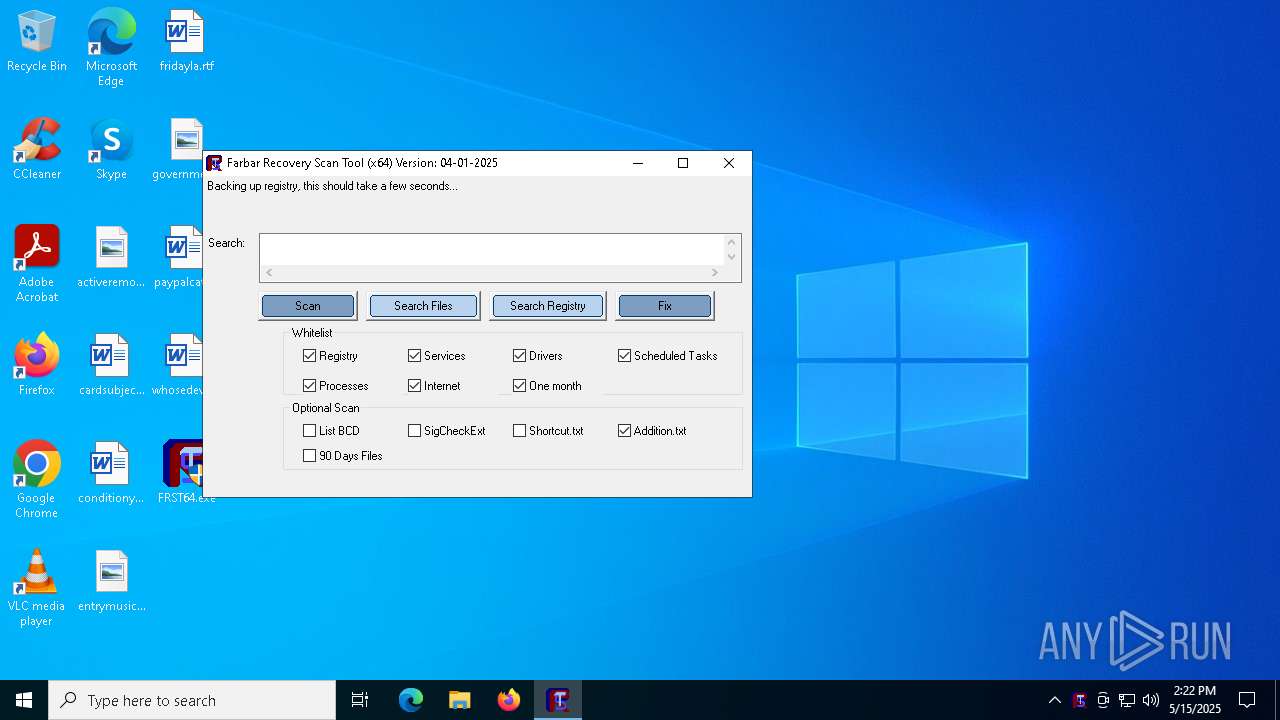
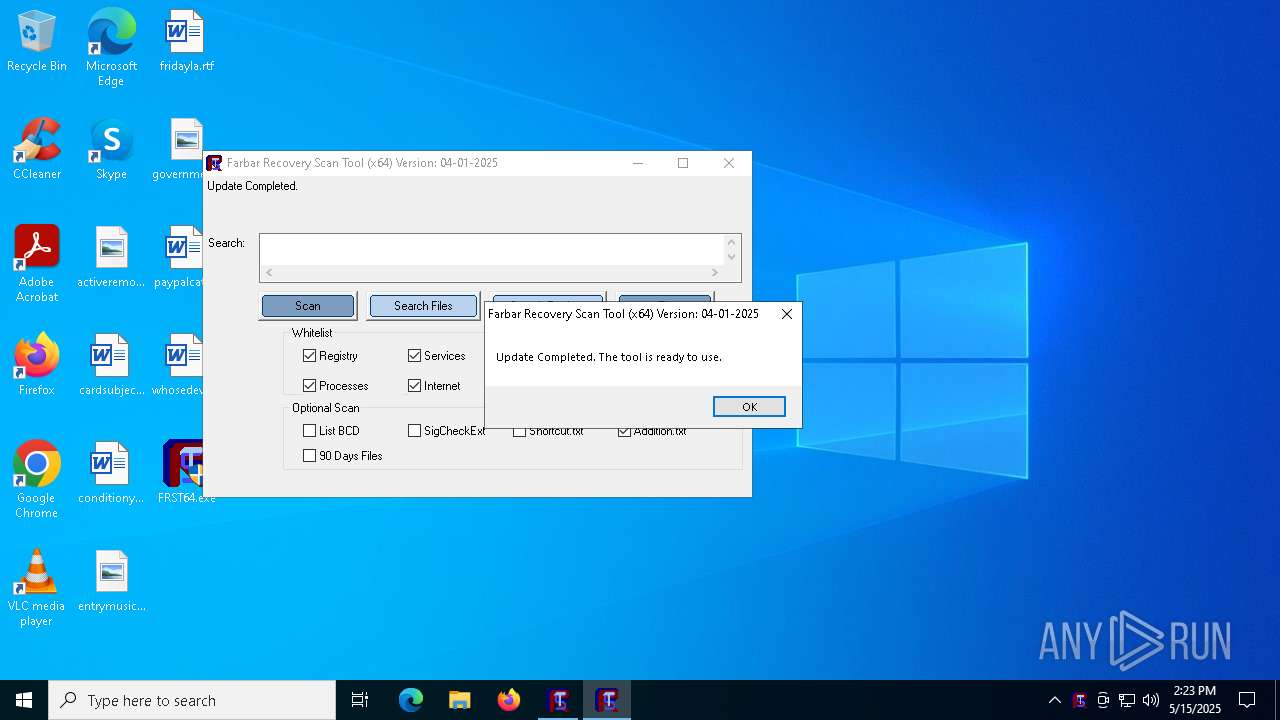
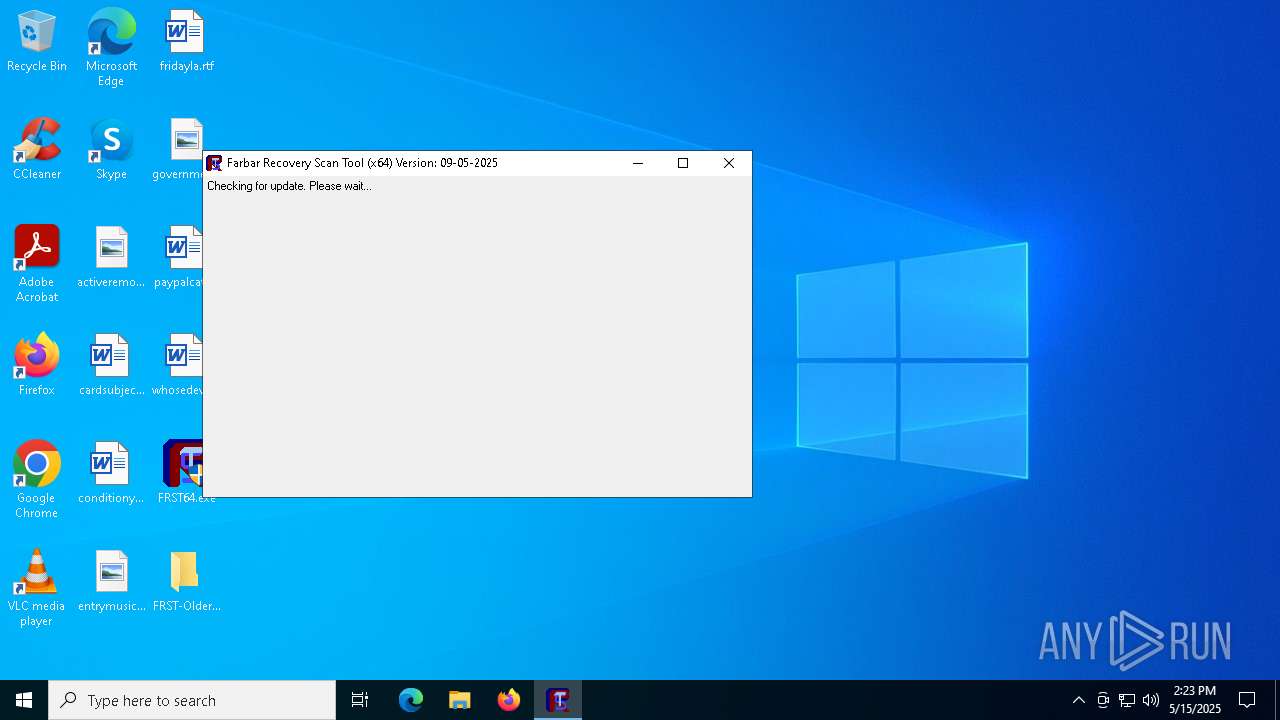
| File name: | FRST64.exe |
| Full analysis: | https://app.any.run/tasks/12cb2bf9-c380-4611-9a26-c0df6c205e50 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 14:22:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | C66C707BBAB21C37C2451BA9C09B2AD1 |
| SHA1: | D59FDC9E5210635EDCF104D289001141403B857D |
| SHA256: | E1FADBAA09B138C4AB897FDDD8436CB52530AA6170682F41C3C78E97FA4BCDF8 |
| SSDEEP: | 98304:+9rem5OidMiu5pkJPj+i8H/Bfyun9xN8tVWU9RsY+RaRvuKHYT2471ZbX2FGJiY:Qv |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- FRST64.exe (PID: 1132)
Detected use of alternative data streams (AltDS)
- FRST64.exe (PID: 1132)
- FRST64.exe (PID: 3008)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1040)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6632)
There is functionality for taking screenshot (YARA)
- FRST64.exe (PID: 1132)
Executes as Windows Service
- VSSVC.exe (PID: 4696)
Starts CMD.EXE for commands execution
- FRST64.exe (PID: 1132)
Reads security settings of Internet Explorer
- FRST64.exe (PID: 1132)
- FRST64.exe (PID: 3008)
Reads the date of Windows installation
- FRST64.exe (PID: 1132)
Potential Corporate Privacy Violation
- FRST64.exe (PID: 1132)
- FRST64.exe (PID: 3008)
Application launched itself
- FRST64.exe (PID: 1132)
INFO
Reads the computer name
- FRST64.exe (PID: 1132)
- FRST64.exe (PID: 3008)
Reads mouse settings
- FRST64.exe (PID: 1132)
Checks supported languages
- FRST64.exe (PID: 1132)
- FRST64.exe (PID: 3008)
The sample compiled with english language support
- FRST64.exe (PID: 1132)
Create files in a temporary directory
- FRST64.exe (PID: 1132)
The process uses AutoIt
- FRST64.exe (PID: 1132)
Checks proxy server information
- FRST64.exe (PID: 1132)
- FRST64.exe (PID: 3008)
Creates files or folders in the user directory
- FRST64.exe (PID: 1132)
- FRST64.exe (PID: 3008)
Reads the machine GUID from the registry
- FRST64.exe (PID: 1132)
Reads the software policy settings
- FRST64.exe (PID: 1132)
Process checks computer location settings
- FRST64.exe (PID: 1132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:01:04 12:04:53+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 1668608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.2025.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 4.1.2025.0 |
| Comments: | http://www.autoitscript.com/autoit3/ |
| FileDescription: | Farbar Recovery Scan Tool |
| ProductName: | FRST64 |
| ProductVersion: | 04-01-2025 |
| CompanyName: | Farbar |
| LegalCopyright: | ©Farbar |
| OriginalFileName: | FRST64.exe |
| InternalName: | FRST64 |
Total processes
164
Monitored processes
35
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | reg load hklm\z8Ks4Of8Uj5 C:\FRST\k0Ub0Hm7Is\SOFTWARE | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | C:\WINDOWS\system32\cmd.exe /c reg load hklm\z8Ks4Of8Uj5 C:\FRST\k0Ub0Hm7Is\SOFTWARE | C:\Windows\System32\cmd.exe | — | FRST64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | reg load hklm\z8Ks4Of8Uj5 C:\FRST\k0Ub0Hm7Is\NTUSER.DAT | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\Desktop\FRST64.exe" | C:\Users\admin\Desktop\FRST64.exe | explorer.exe | ||||||||||||
User: admin Company: Farbar Integrity Level: HIGH Description: Farbar Recovery Scan Tool Exit code: 0 Version: 4.1.2025.0 Modules
| |||||||||||||||
| 1188 | C:\WINDOWS\system32\bcdedit /export C:\FRST\Hives\BCD | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | reg load hklm\z8Ks4Of8Uj5 C:\FRST\k0Ub0Hm7Is\SECURITY | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\bcdedit /export C:\FRST\Hives\BCD | C:\Windows\System32\cmd.exe | — | FRST64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 351
Read events
4 110
Write events
230
Delete events
11
Modification events
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000001\Description |
| Operation: | write | Name: | KeyName |
Value: BCD00000001 | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\BootConfigurationData\NewStoreRoot |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\BootConfigurationData |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000001\Objects\{0ce4991b-e6b3-4b16-b23c-5e0d9250e5d9}\Description |
| Operation: | write | Name: | Type |
Value: 537919488 | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000001\Objects\{0ce4991b-e6b3-4b16-b23c-5e0d9250e5d9}\Elements\16000020 |
| Operation: | write | Name: | Element |
Value: 00 | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000001\Objects\{1afa9c49-16ab-4a5c-901b-212802da9460}\Description |
| Operation: | write | Name: | Type |
Value: 538968068 | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000001\Objects\{1afa9c49-16ab-4a5c-901b-212802da9460}\Elements\14000006 |
| Operation: | write | Name: | Element |
Value: {7ea2e1ac-2e61-4728-aaa3-896d9d0a9f0e} | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000001\Objects\{7ea2e1ac-2e61-4728-aaa3-896d9d0a9f0e}\Description |
| Operation: | write | Name: | Type |
Value: 537919488 | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000001\Objects\{7ea2e1ac-2e61-4728-aaa3-896d9d0a9f0e}\Elements\14000006 |
| Operation: | write | Name: | Element |
Value: {4636856e-540f-4170-a130-a84776f4c654} | |||
| (PID) Process: | (1188) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000001\Objects\{4636856e-540f-4170-a130-a84776f4c654}\Description |
| Operation: | write | Name: | Type |
Value: 537919488 | |||
Executable files
5
Suspicious files
38
Text files
10
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1132 | FRST64.exe | C:\FRST\k0Ub0Hm7Is\SOFTWARE | — | |
MD5:— | SHA256:— | |||
| 1132 | FRST64.exe | C:\FRST\k0Ub0Hm7Is\SOFTWARE.LOG1 | — | |
MD5:— | SHA256:— | |||
| 1132 | FRST64.exe | C:\FRST\k0Ub0Hm7Is\SOFTWARE.LOG2 | — | |
MD5:— | SHA256:— | |||
| 1132 | FRST64.exe | C:\FRST\Hives\SOFTWARE | — | |
MD5:— | SHA256:— | |||
| 1132 | FRST64.exe | C:\FRST\k0Ub0Hm7Is\SYSTEM | — | |
MD5:— | SHA256:— | |||
| 1132 | FRST64.exe | C:\FRST\Hives\SYSTEM | — | |
MD5:— | SHA256:— | |||
| 1188 | bcdedit.exe | C:\FRST\Hives\BCD | hiv | |
MD5:EA6A14838D44F24342A9766D0031CFB4 | SHA256:A23B02DCFFC749059554A6DECC17B1EFC7B52B6CCBC2E359EECC0C652C7A5BBD | |||
| 1132 | FRST64.exe | C:\FRST\k0Ub0Hm7Is\COMPONENTS | — | |
MD5:— | SHA256:— | |||
| 1132 | FRST64.exe | C:\FRST\k0Ub0Hm7Is\COMPONENTS.LOG1 | — | |
MD5:— | SHA256:— | |||
| 1132 | FRST64.exe | C:\FRST\k0Ub0Hm7Is\COMPONENTS.LOG2 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
35
DNS requests
17
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1040 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1040 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1132 | FRST64.exe | GET | 301 | 104.20.184.56:80 | http://download.bleepingcomputer.com/farbar/up64 | unknown | — | — | whitelisted |
1132 | FRST64.exe | GET | 200 | 142.250.186.131:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1132 | FRST64.exe | GET | 200 | 142.250.186.131:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
1132 | FRST64.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
— | — | 92.123.22.101:80 | www.microsoft.com | AKAMAI-AS | AT | whitelisted |
5496 | MoUsoCoreWorker.exe | 92.123.22.101:80 | www.microsoft.com | AKAMAI-AS | AT | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1132 | FRST64.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
1132 | FRST64.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
3008 | FRST64.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |