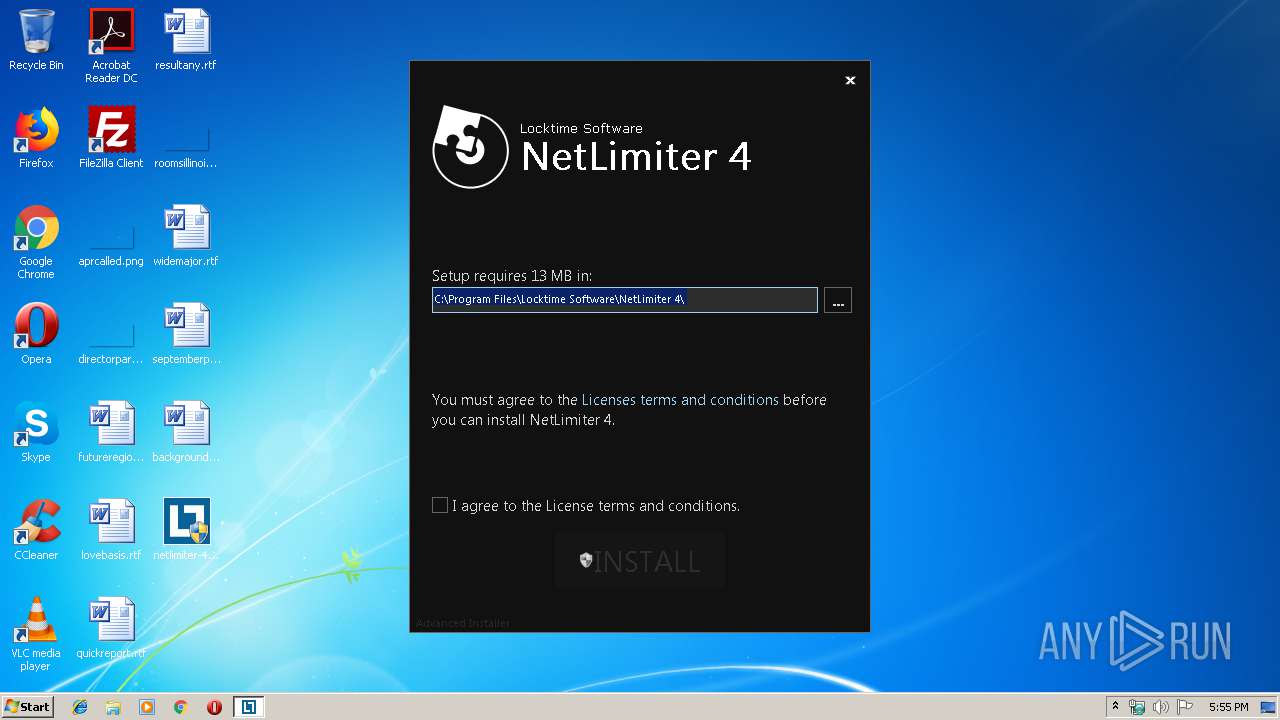
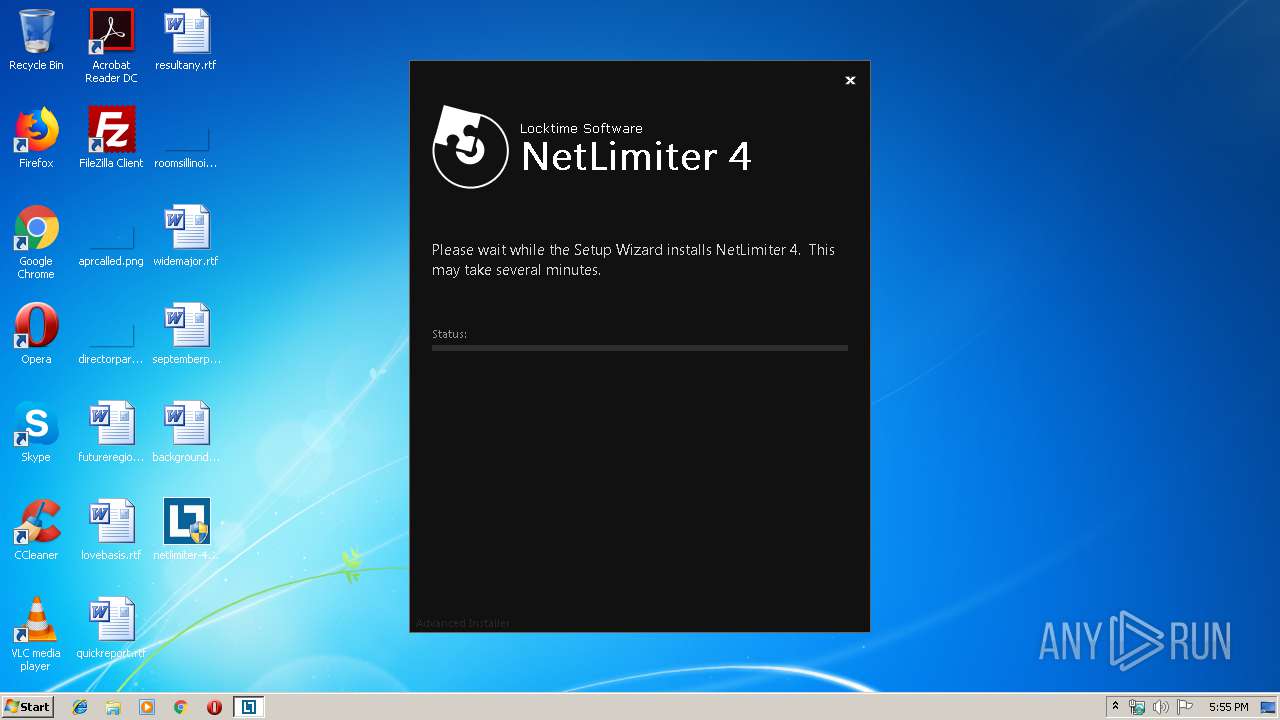
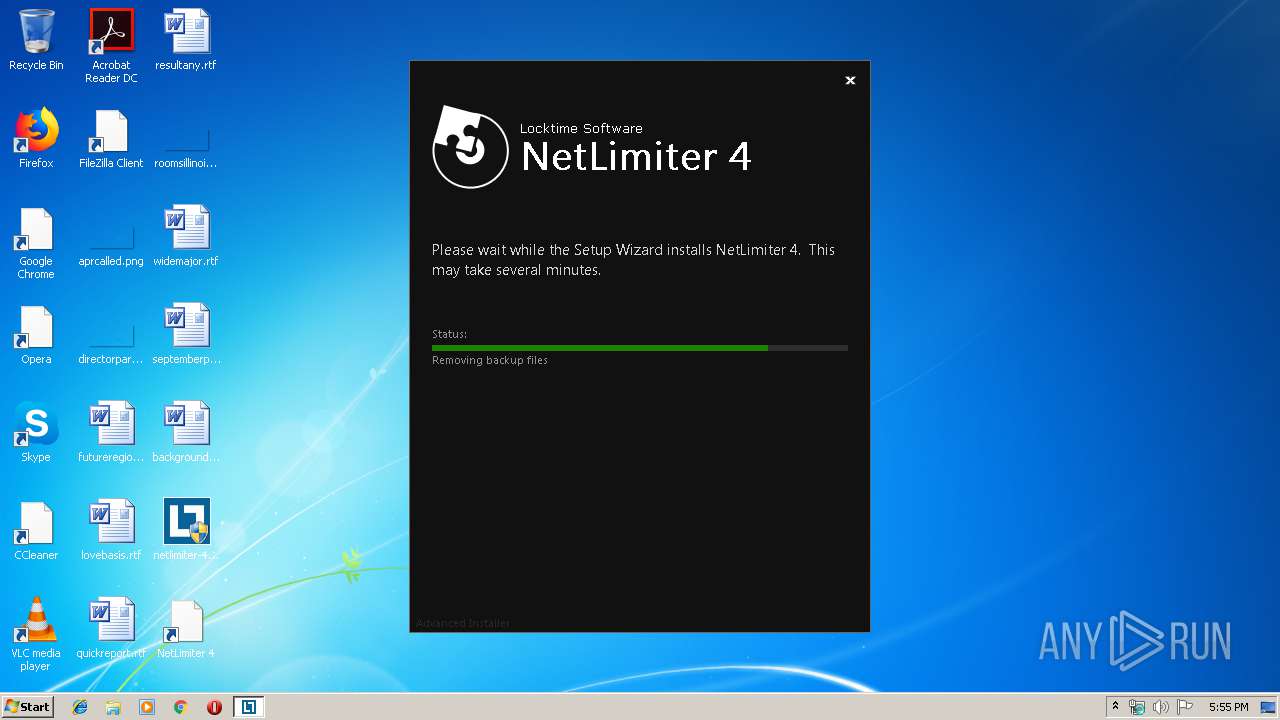
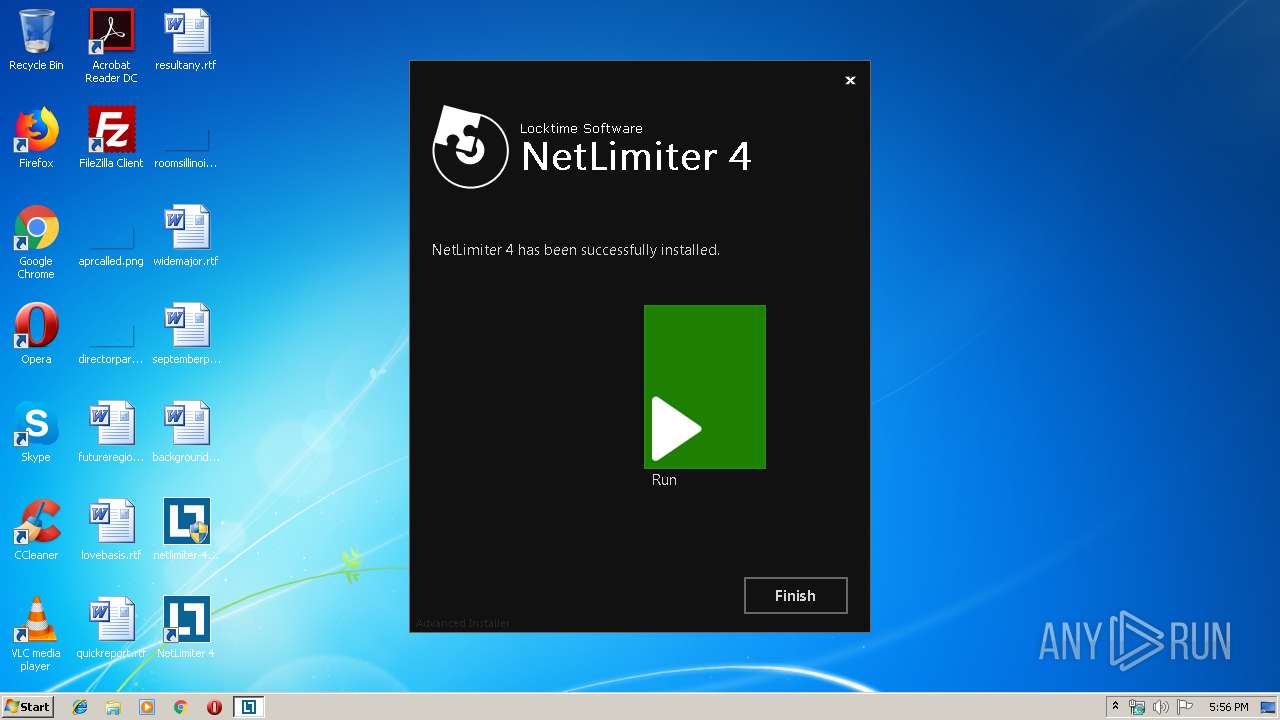
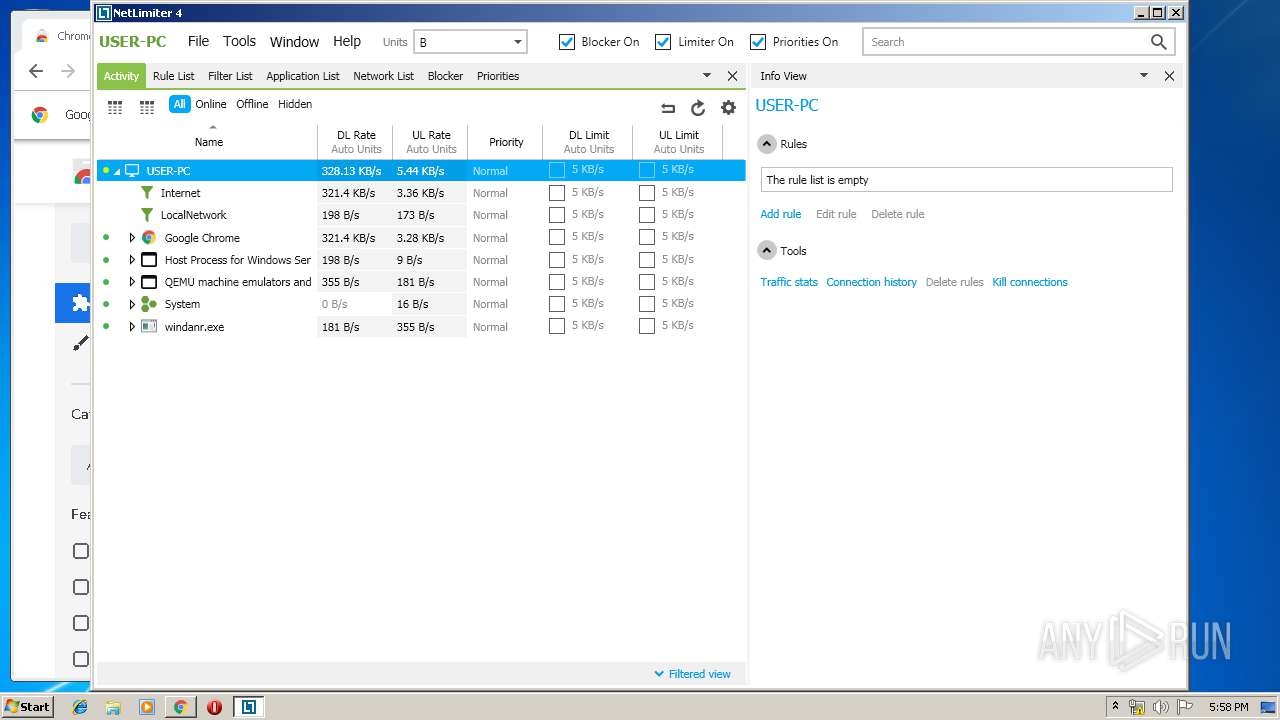
| download: | netlimiter-4.0.53.0.exe |
| Full analysis: | https://app.any.run/tasks/734e2edf-b7a9-4e4e-b825-dd9615123661 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2019, 16:54:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 08B5F934093C4796A49C19247C152DC5 |
| SHA1: | BFE844E30F495145DDDF876D3DFB480756B9C179 |
| SHA256: | E1FA8884BF3D35A03E3B8AAEC009B498E4AF229054E1E4B949F8C516A39FE1B9 |
| SSDEEP: | 196608:MEOtA7F5QUuEA3LkVjupHOyXrn+xwo6D9CuzAScXV1ec:MEOtAIUK3L/9OyXTYwo6D9VASwL |
MALICIOUS
Changes settings of System certificates
- netlimiter-4.0.53.0.exe (PID: 2596)
Loads dropped or rewritten executable
- netlimiter-4.0.53.0.exe (PID: 2596)
- NLSvc.exe (PID: 324)
- mscorsvw.exe (PID: 2900)
- NLSvc.exe (PID: 3304)
- mscorsvw.exe (PID: 1440)
- mscorsvw.exe (PID: 2432)
- mscorsvw.exe (PID: 1428)
- mscorsvw.exe (PID: 712)
- mscorsvw.exe (PID: 1408)
- mscorsvw.exe (PID: 2816)
- mscorsvw.exe (PID: 3084)
- mscorsvw.exe (PID: 2968)
- mscorsvw.exe (PID: 2976)
- NLClientApp.exe (PID: 2376)
- NLClientApp.exe (PID: 3612)
- NLClientApp.exe (PID: 2308)
- NLClientApp.exe (PID: 2744)
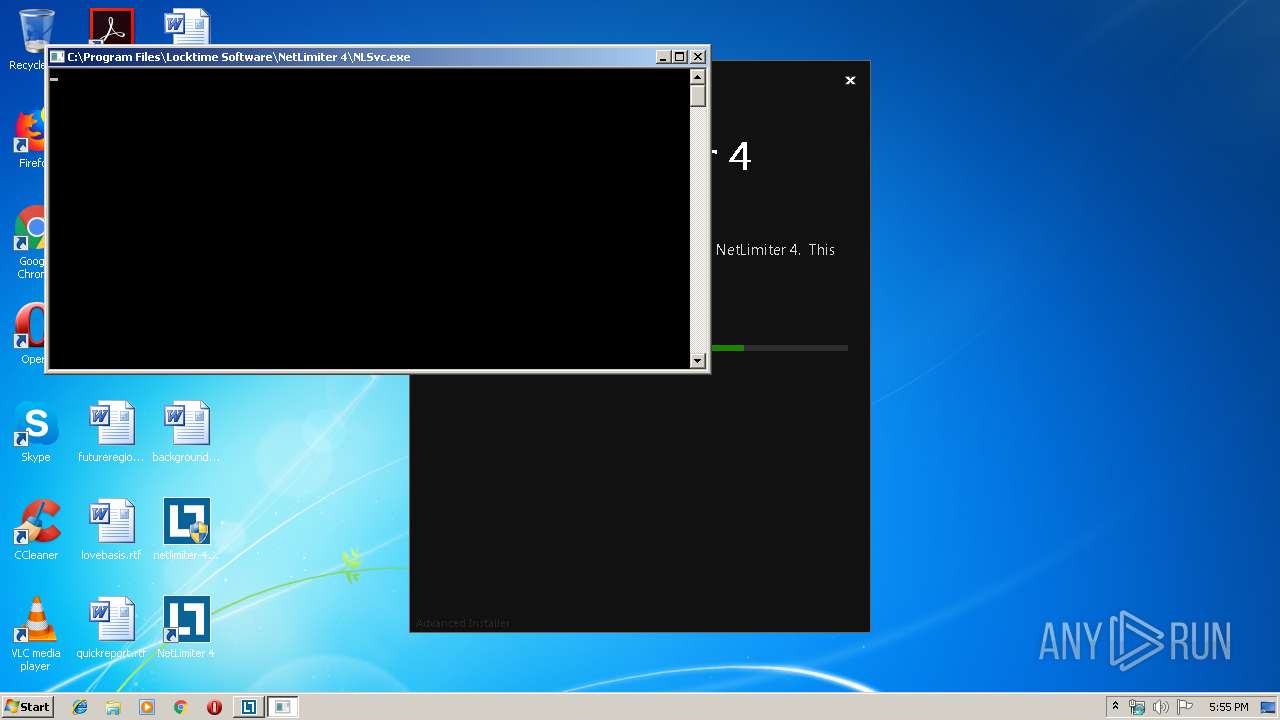
Application was dropped or rewritten from another process
- NLSvc.exe (PID: 324)
- NLSvc.exe (PID: 3304)
- NLClientApp.exe (PID: 3612)
- NLClientApp.exe (PID: 2376)
- NLClientApp.exe (PID: 2308)
- NLClientApp.exe (PID: 2744)
Loads the Task Scheduler DLL interface
- netlimiter-4.0.53.0.exe (PID: 2596)
SUSPICIOUS
Creates files in the user directory
- netlimiter-4.0.53.0.exe (PID: 2596)
- NLClientApp.exe (PID: 3612)
- NLClientApp.exe (PID: 2308)
- NLClientApp.exe (PID: 2744)
Adds / modifies Windows certificates
- netlimiter-4.0.53.0.exe (PID: 2596)
Application launched itself
- netlimiter-4.0.53.0.exe (PID: 2596)
- cmd.exe (PID: 348)
- cmd.exe (PID: 2100)
Executed via COM
- DrvInst.exe (PID: 2932)
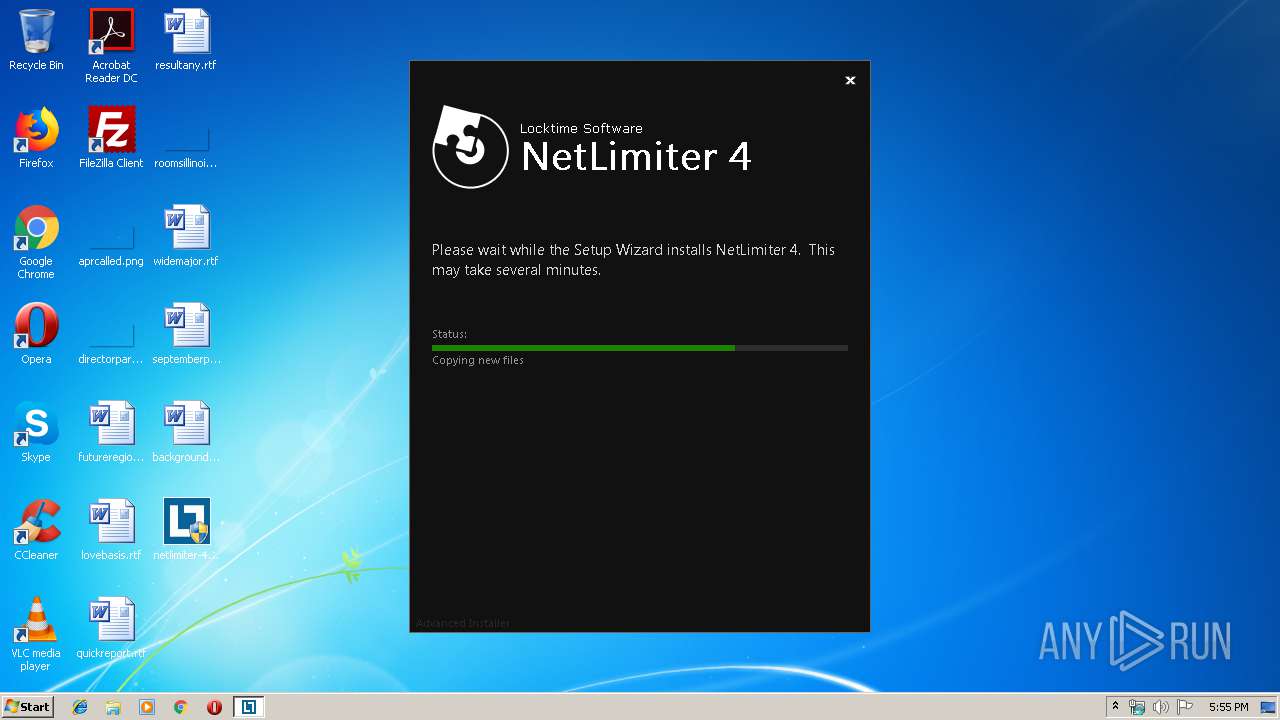
Executable content was dropped or overwritten
- netlimiter-4.0.53.0.exe (PID: 2596)
- msiexec.exe (PID: 3488)
- mscorsvw.exe (PID: 1440)
- mscorsvw.exe (PID: 712)
- mscorsvw.exe (PID: 2432)
- mscorsvw.exe (PID: 1428)
- mscorsvw.exe (PID: 2976)
- mscorsvw.exe (PID: 1408)
- mscorsvw.exe (PID: 2816)
- mscorsvw.exe (PID: 3084)
- mscorsvw.exe (PID: 2968)
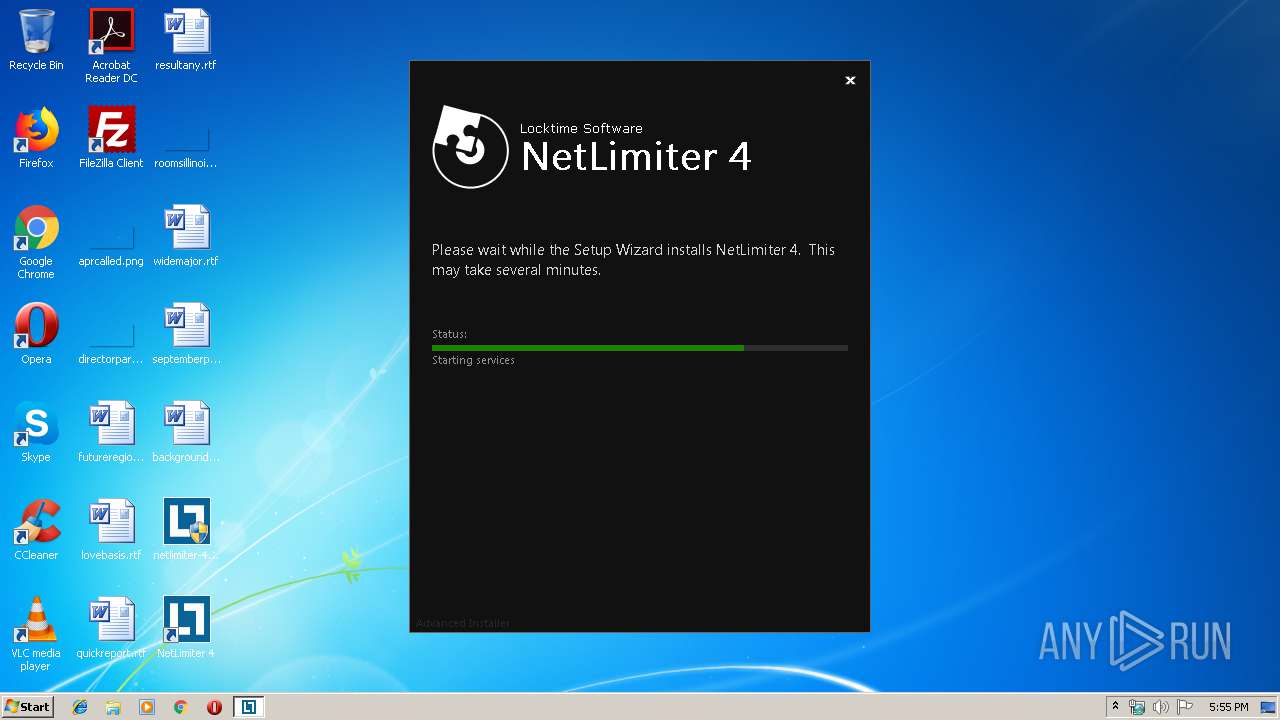
Executed as Windows Service
- vssvc.exe (PID: 3396)
- NLSvc.exe (PID: 324)
Creates files in the driver directory
- msiexec.exe (PID: 3488)
Creates files in the Windows directory
- msiexec.exe (PID: 3488)
- ngen.exe (PID: 3320)
- mscorsvw.exe (PID: 1440)
- mscorsvw.exe (PID: 712)
- mscorsvw.exe (PID: 2432)
- mscorsvw.exe (PID: 1428)
- mscorsvw.exe (PID: 1408)
- mscorsvw.exe (PID: 2976)
- mscorsvw.exe (PID: 2816)
- mscorsvw.exe (PID: 3084)
- mscorsvw.exe (PID: 2968)
Starts CMD.EXE for commands execution
- MsiExec.exe (PID: 3440)
- netlimiter-4.0.53.0.exe (PID: 2596)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 348)
Changes the autorun value in the registry
- msiexec.exe (PID: 3488)
Creates files in the program directory
- NLSvc.exe (PID: 324)
Removes files from Windows directory
- mscorsvw.exe (PID: 1440)
- mscorsvw.exe (PID: 712)
- mscorsvw.exe (PID: 2432)
- mscorsvw.exe (PID: 1428)
- mscorsvw.exe (PID: 2976)
- mscorsvw.exe (PID: 1408)
- mscorsvw.exe (PID: 2816)
- mscorsvw.exe (PID: 3084)
- mscorsvw.exe (PID: 2968)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2100)
- cmd.exe (PID: 348)
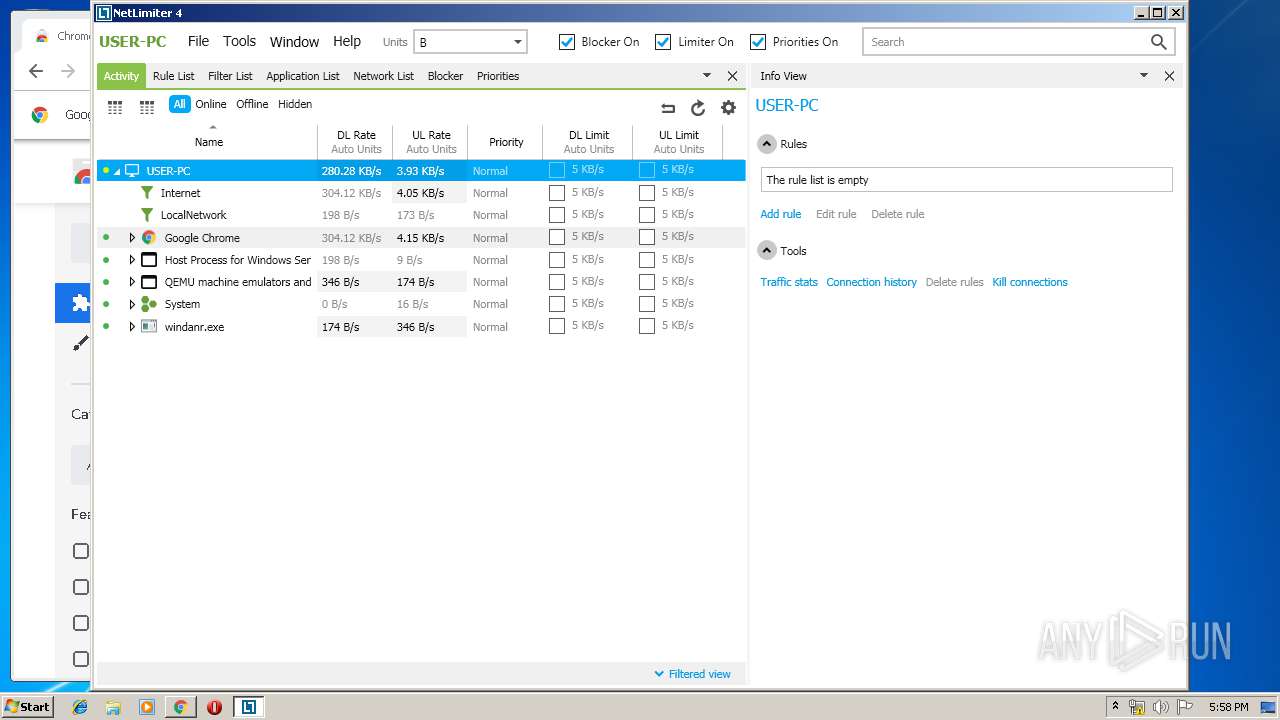
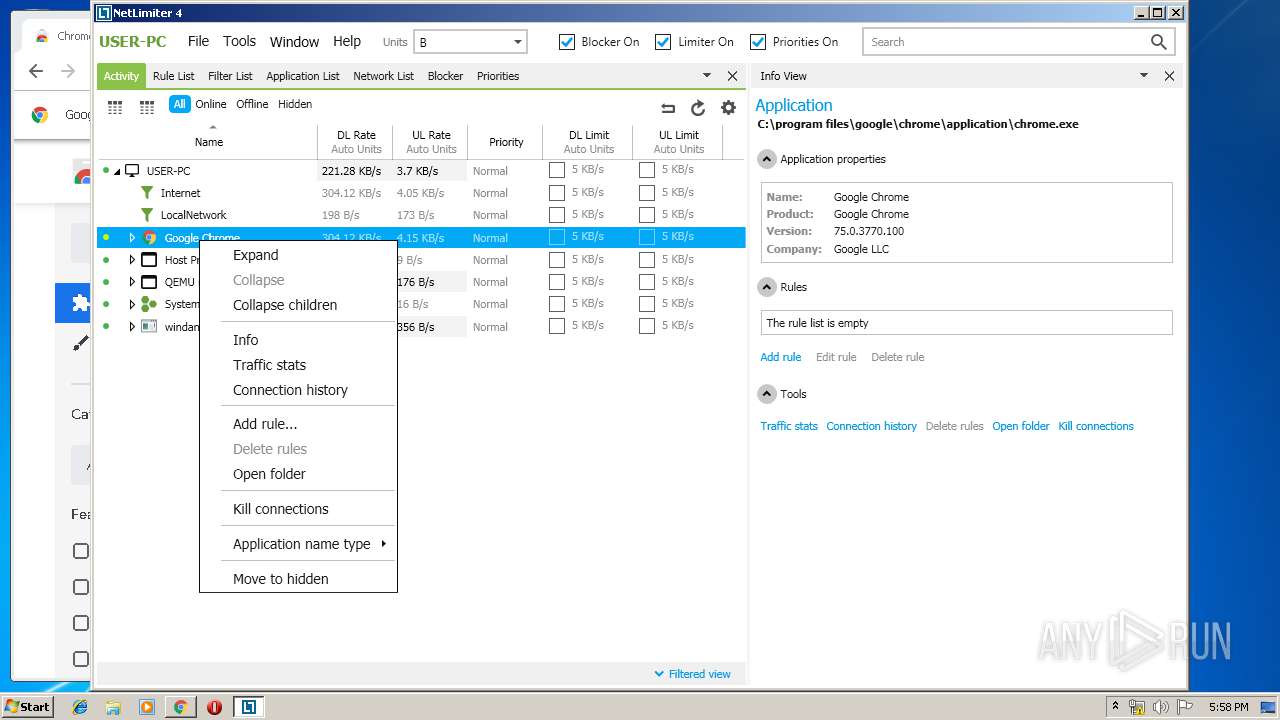
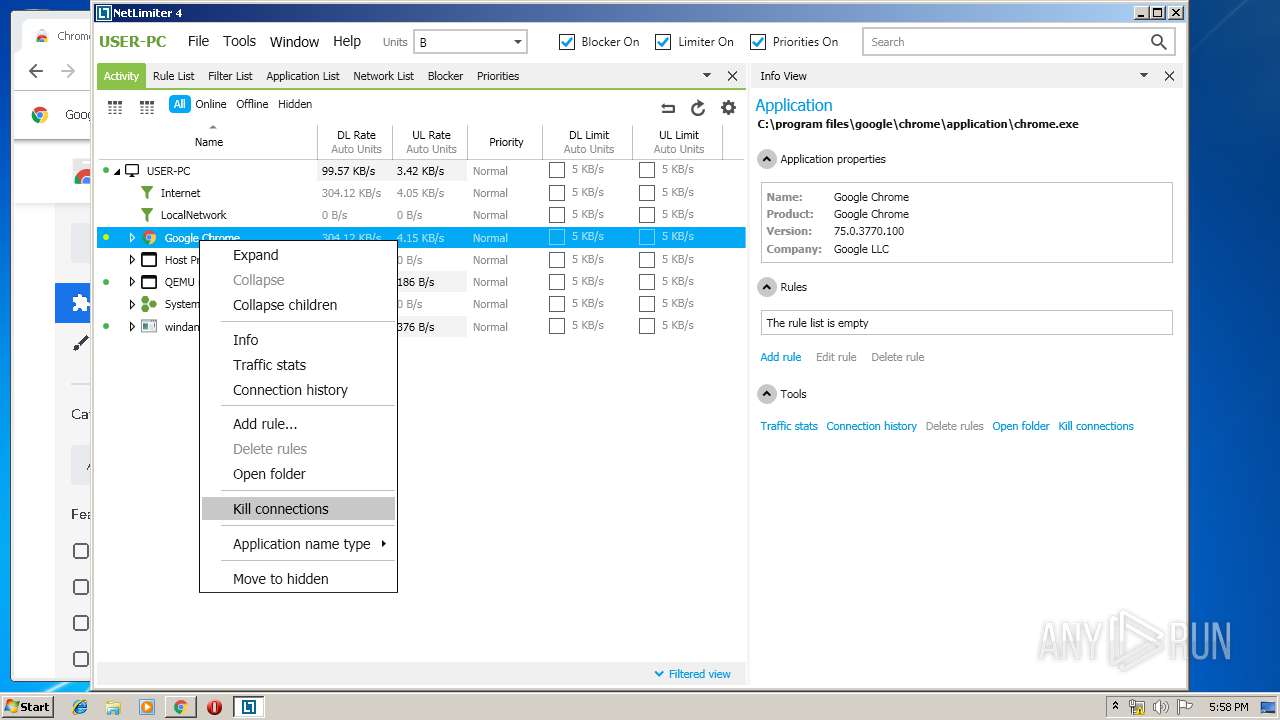
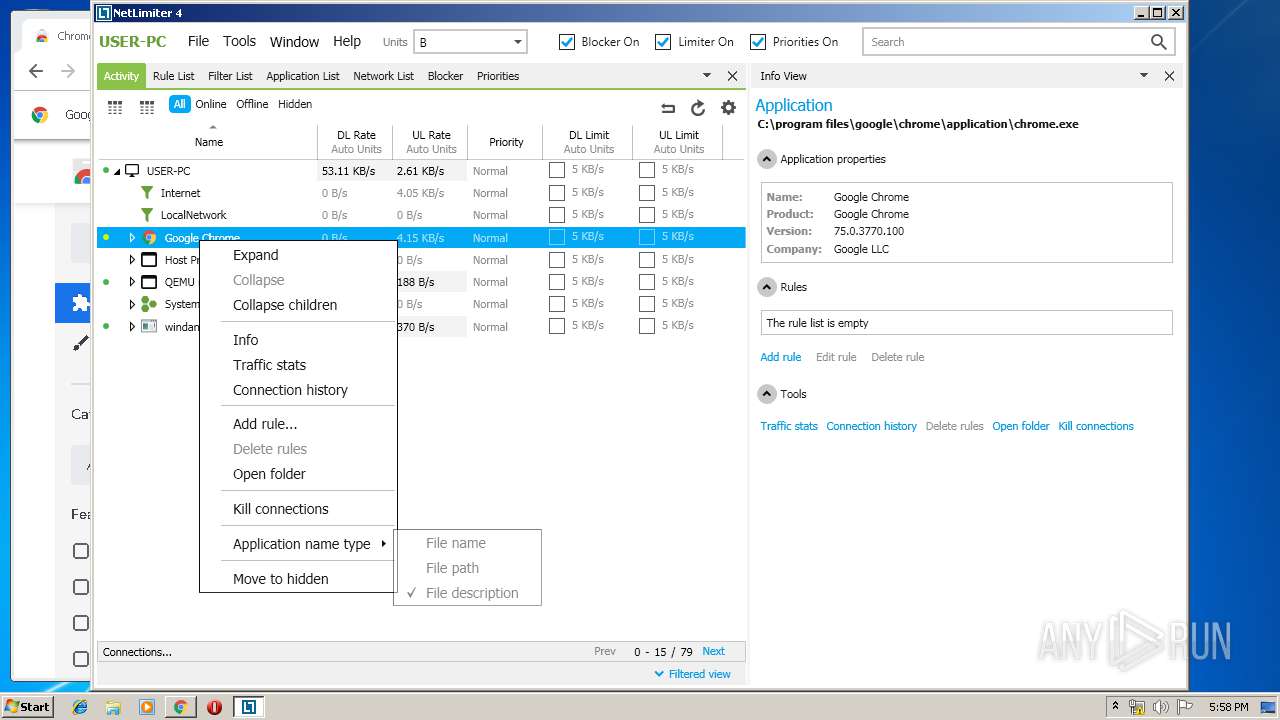
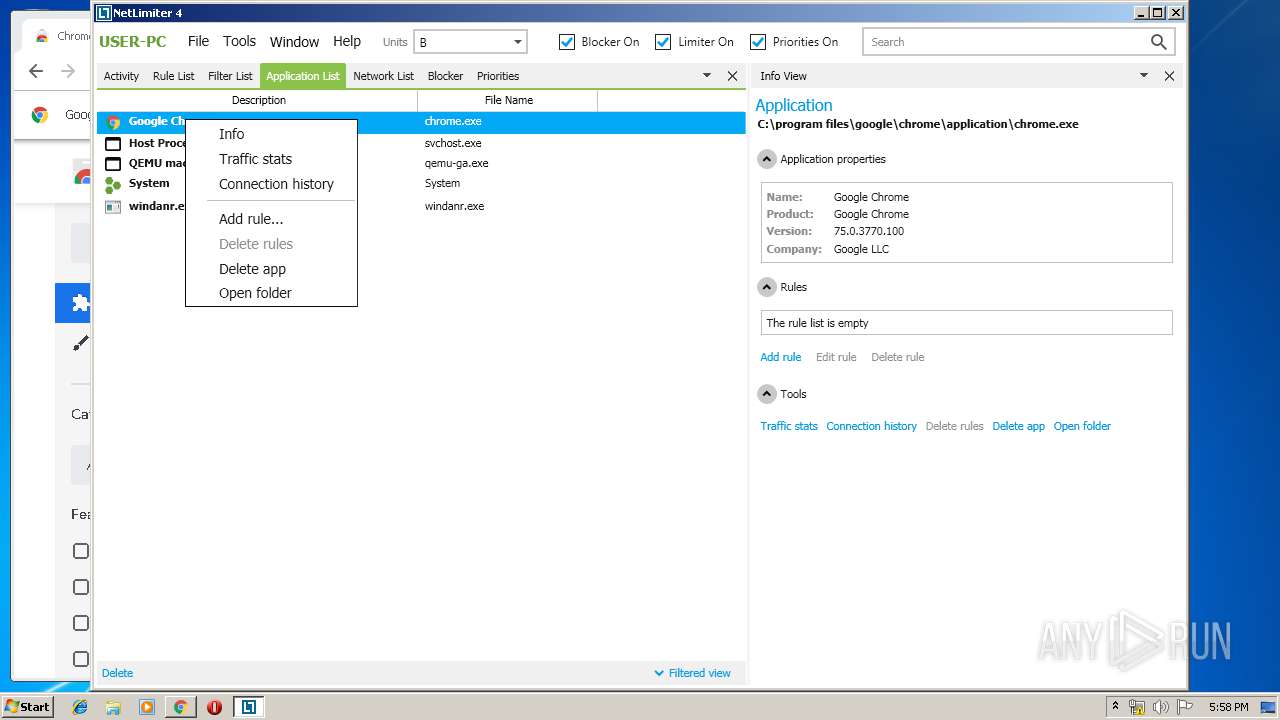
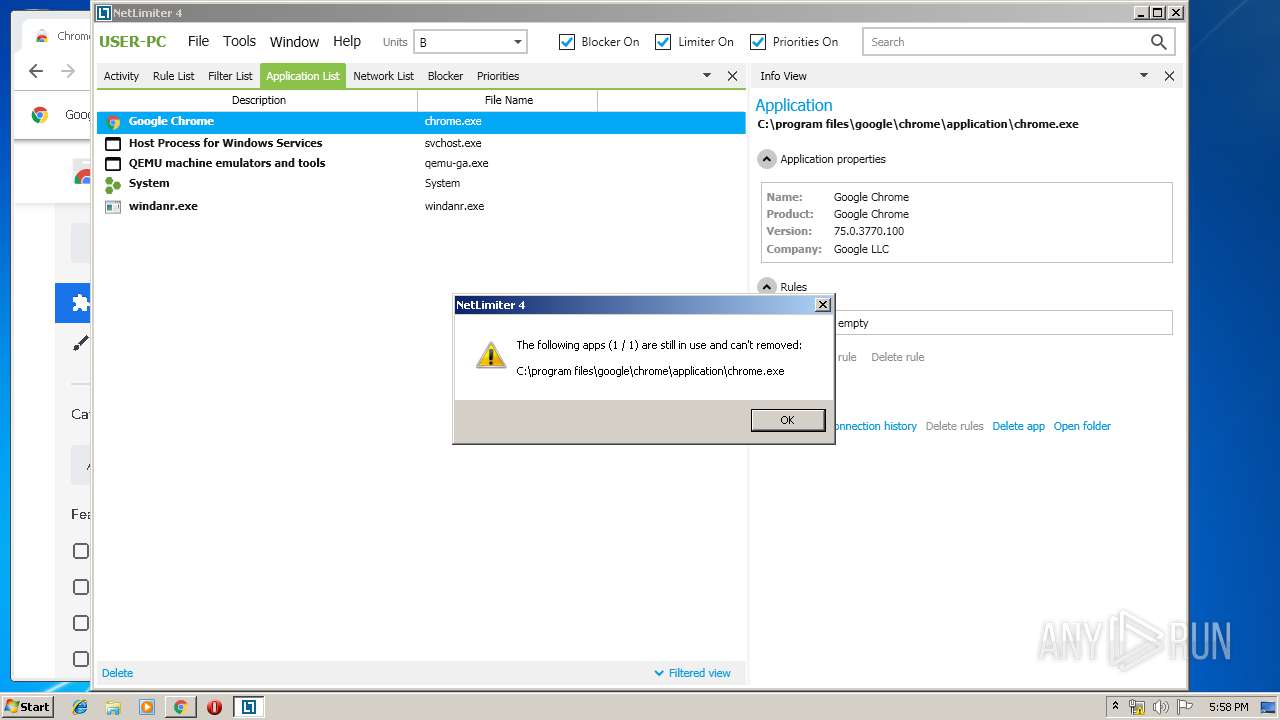
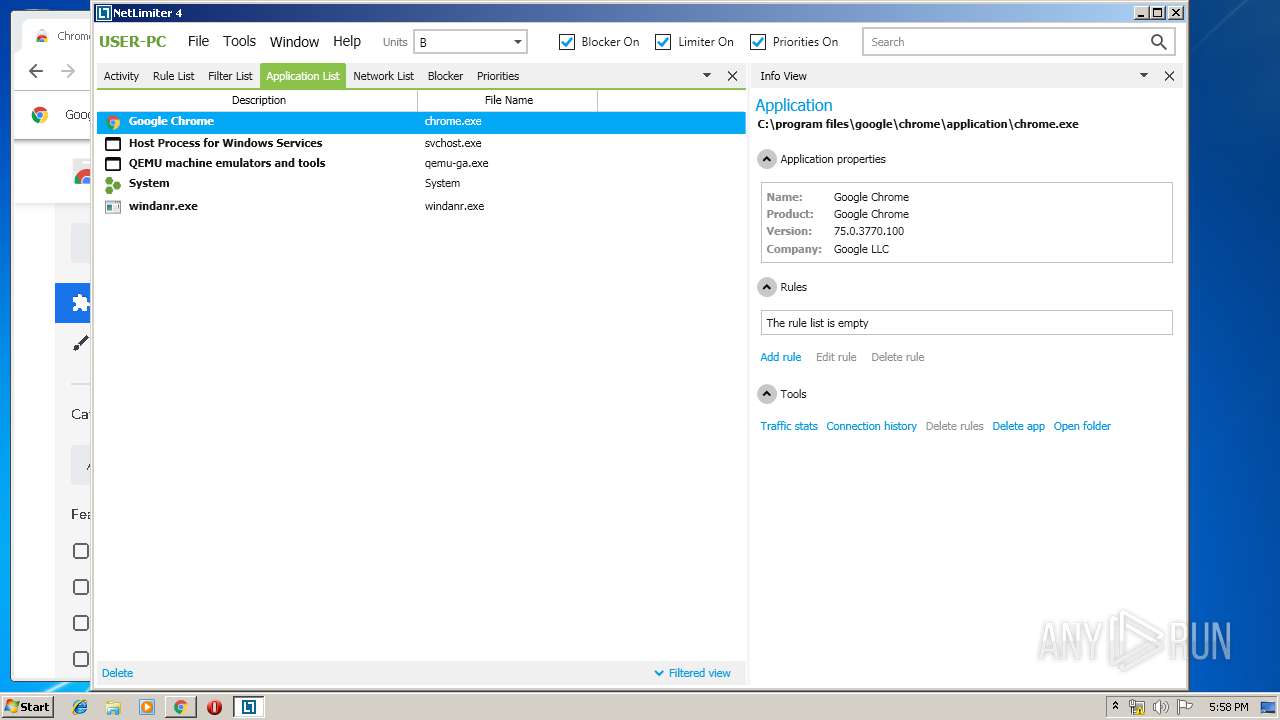
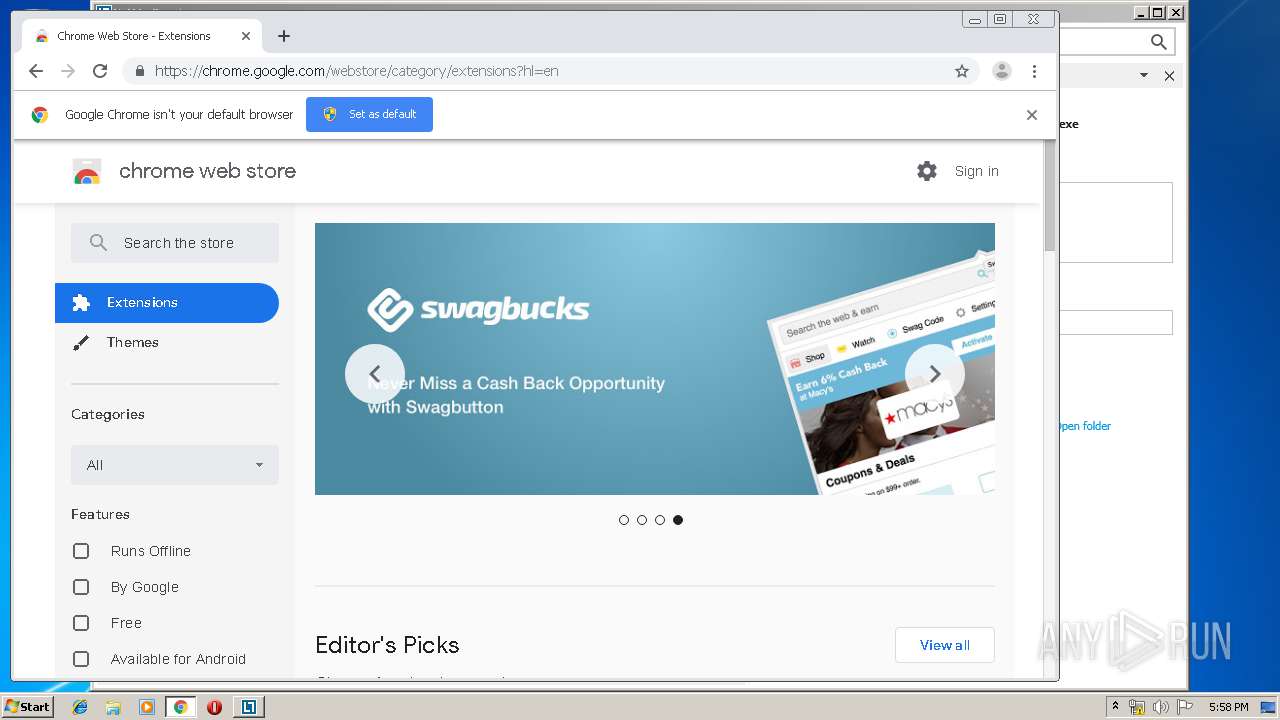
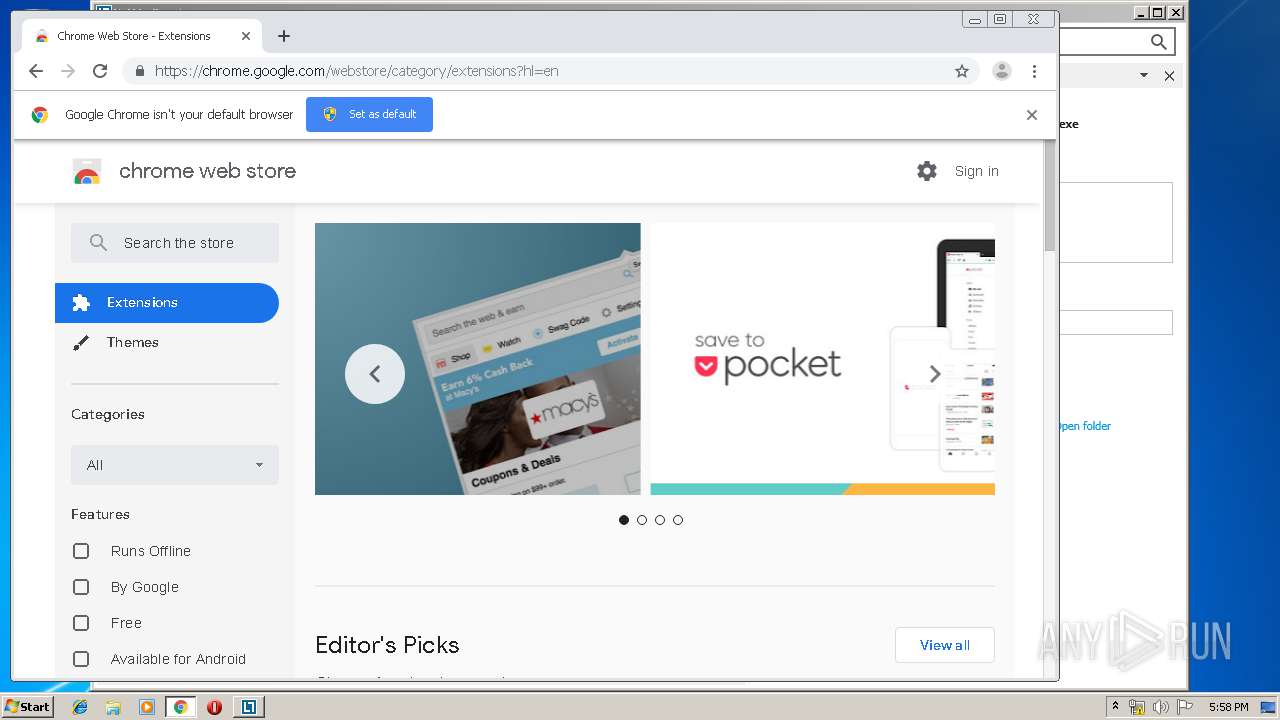
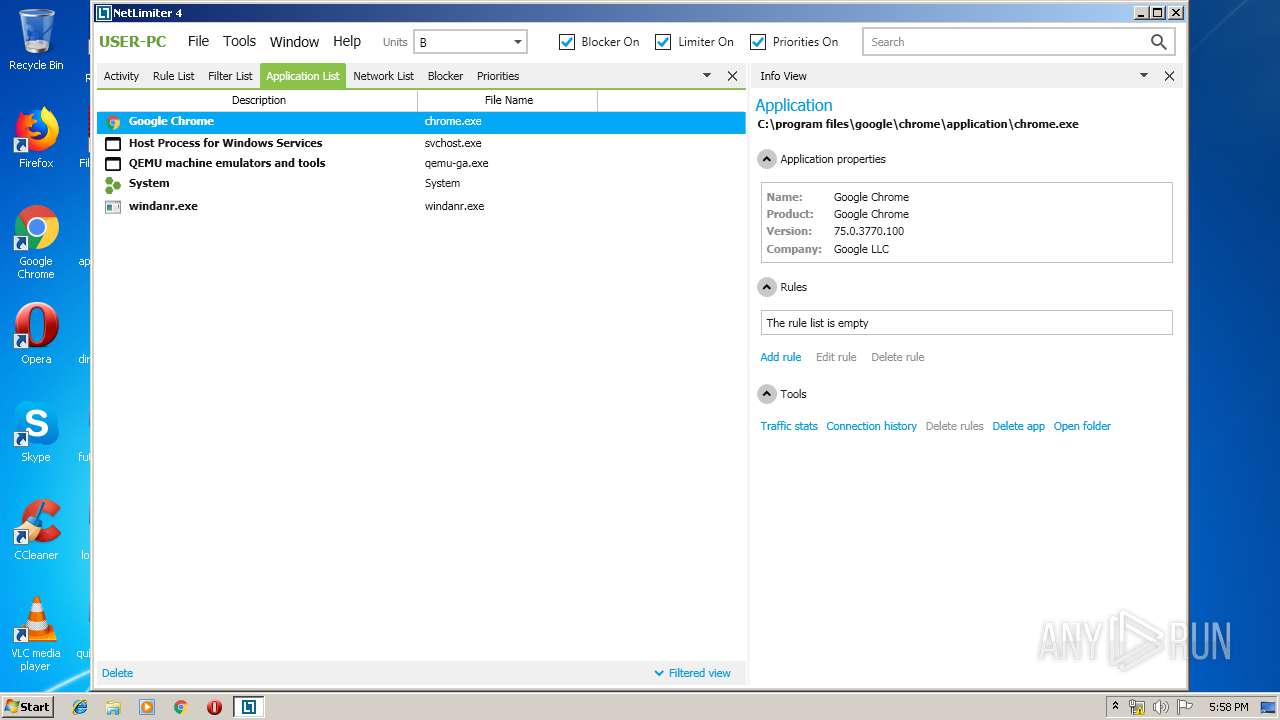
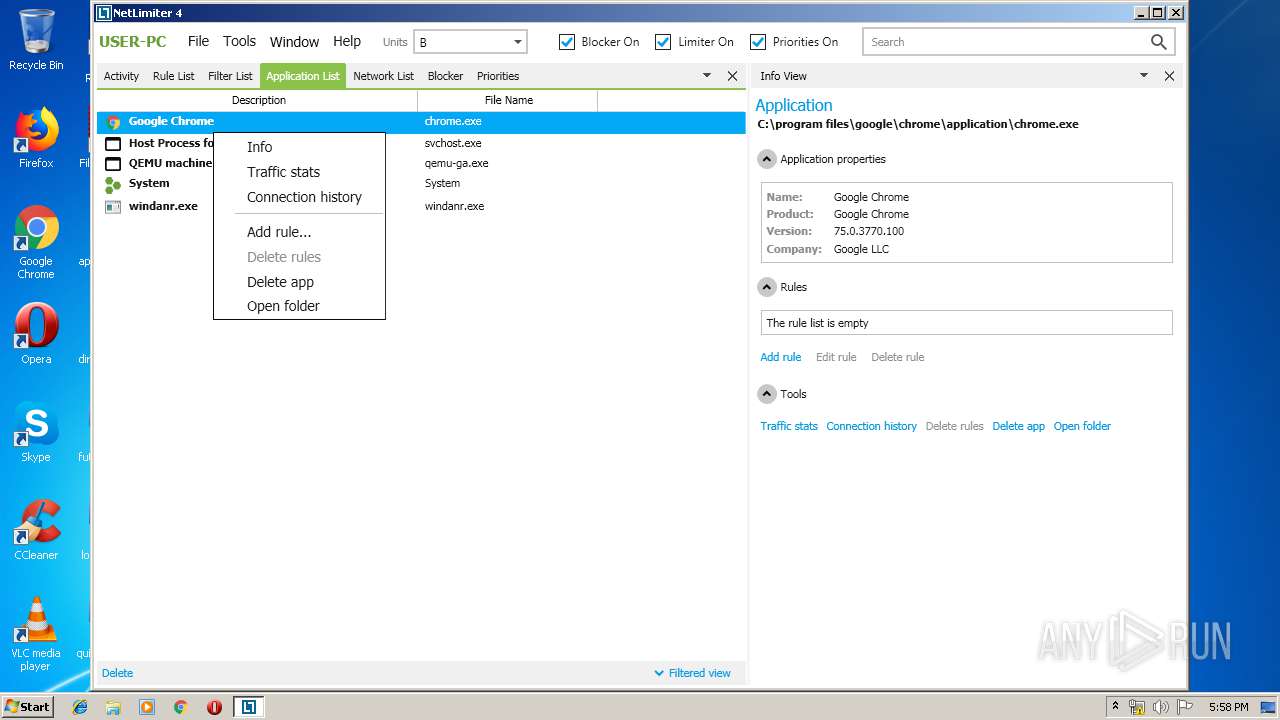
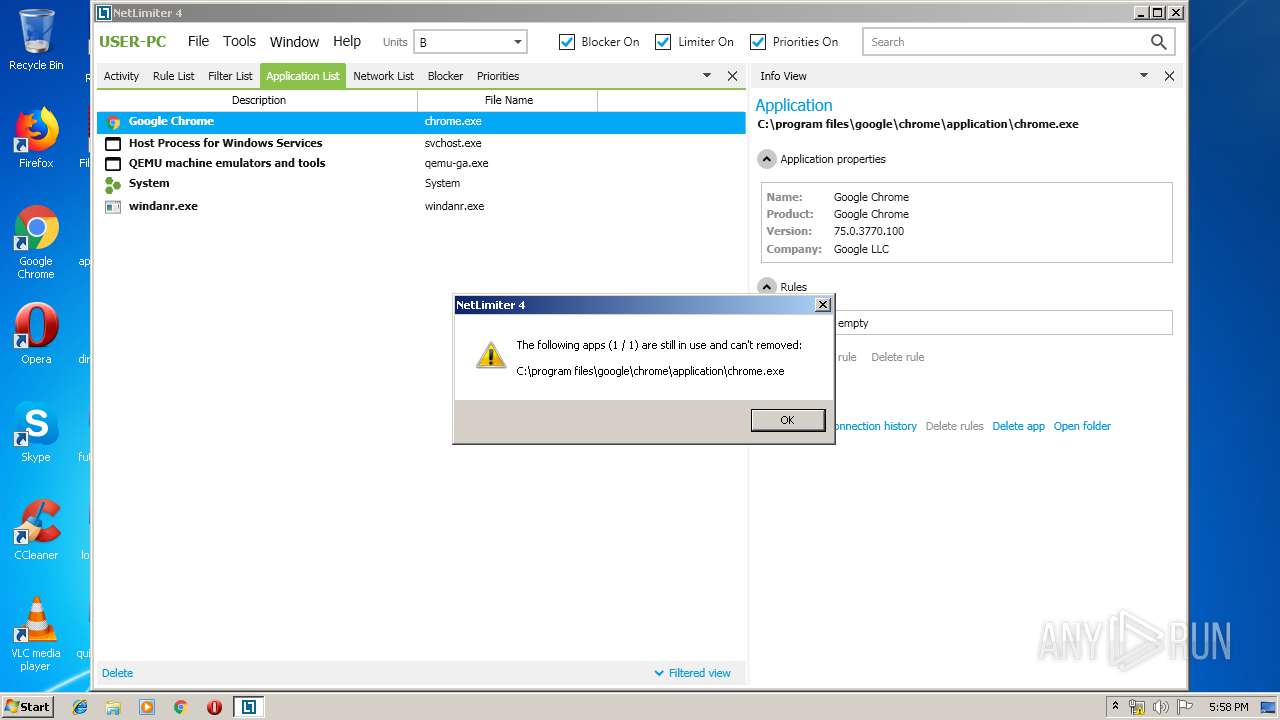
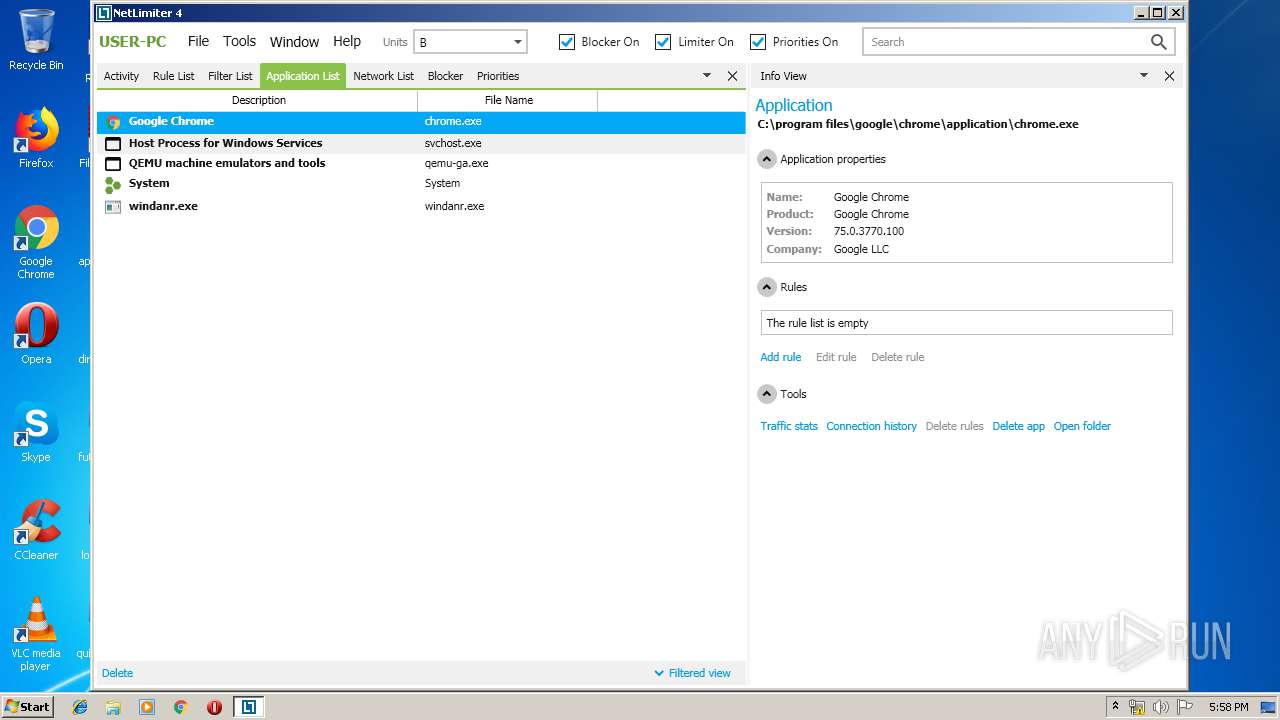
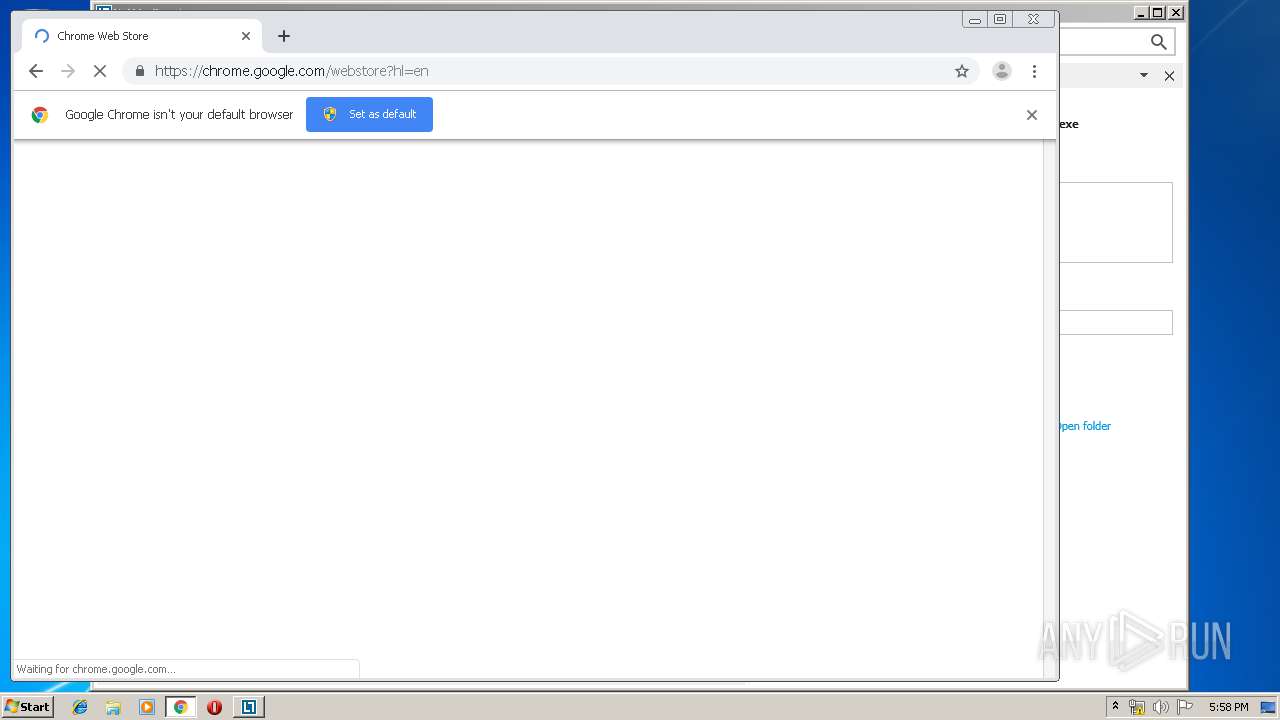
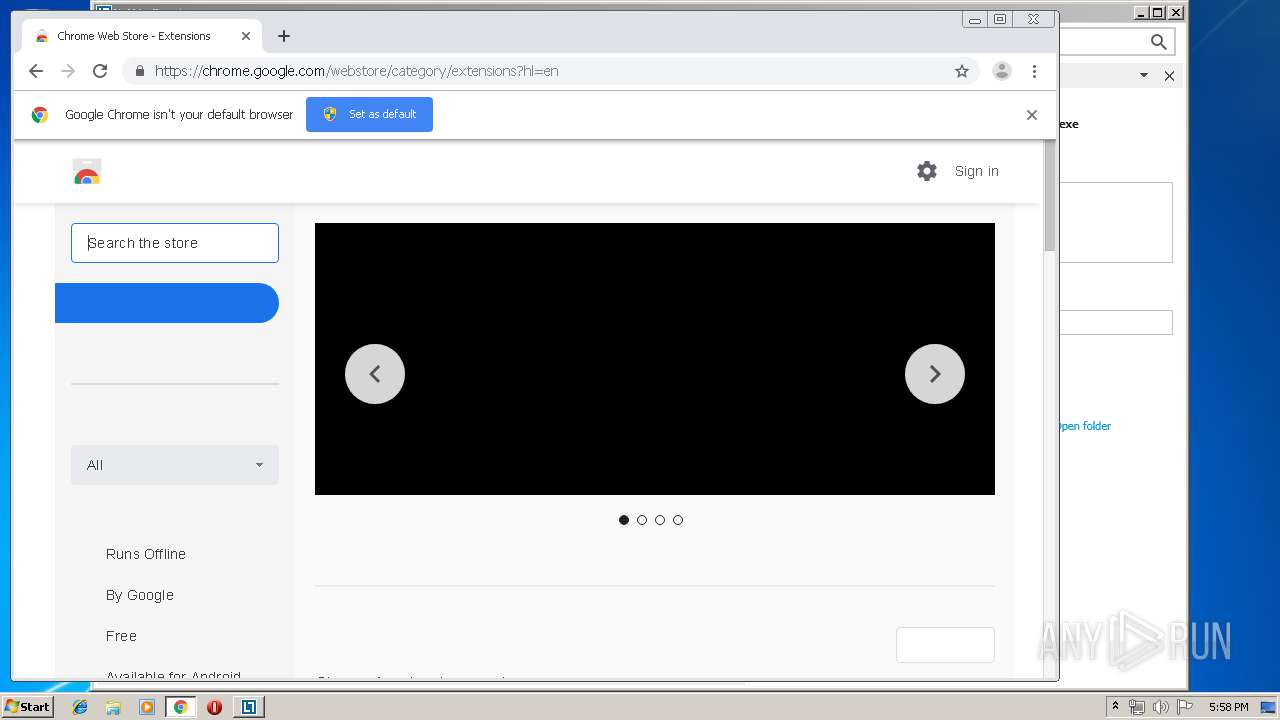
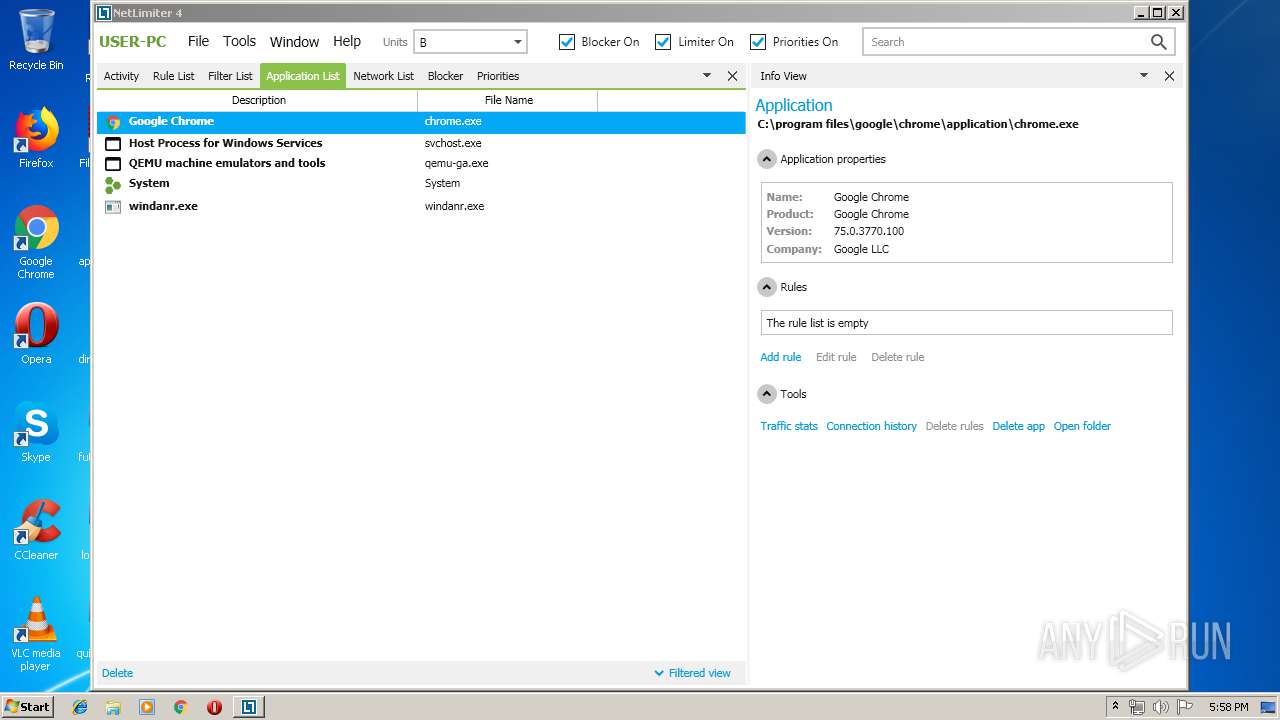
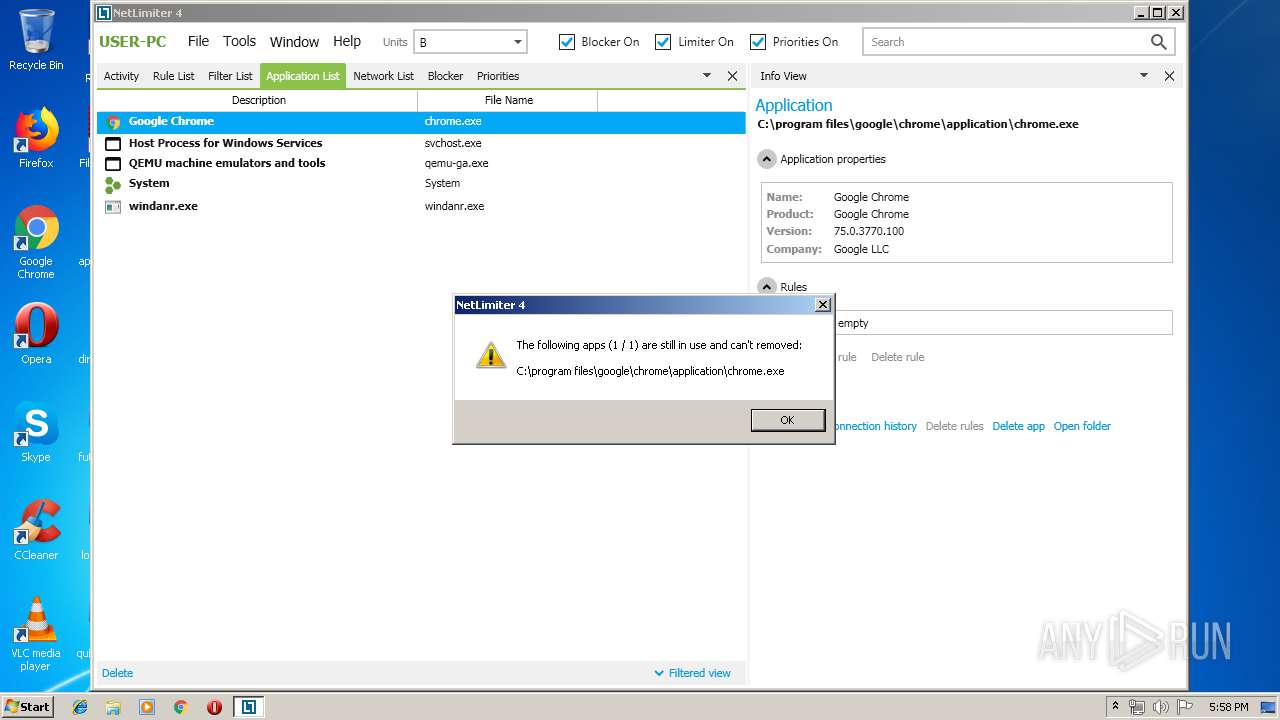
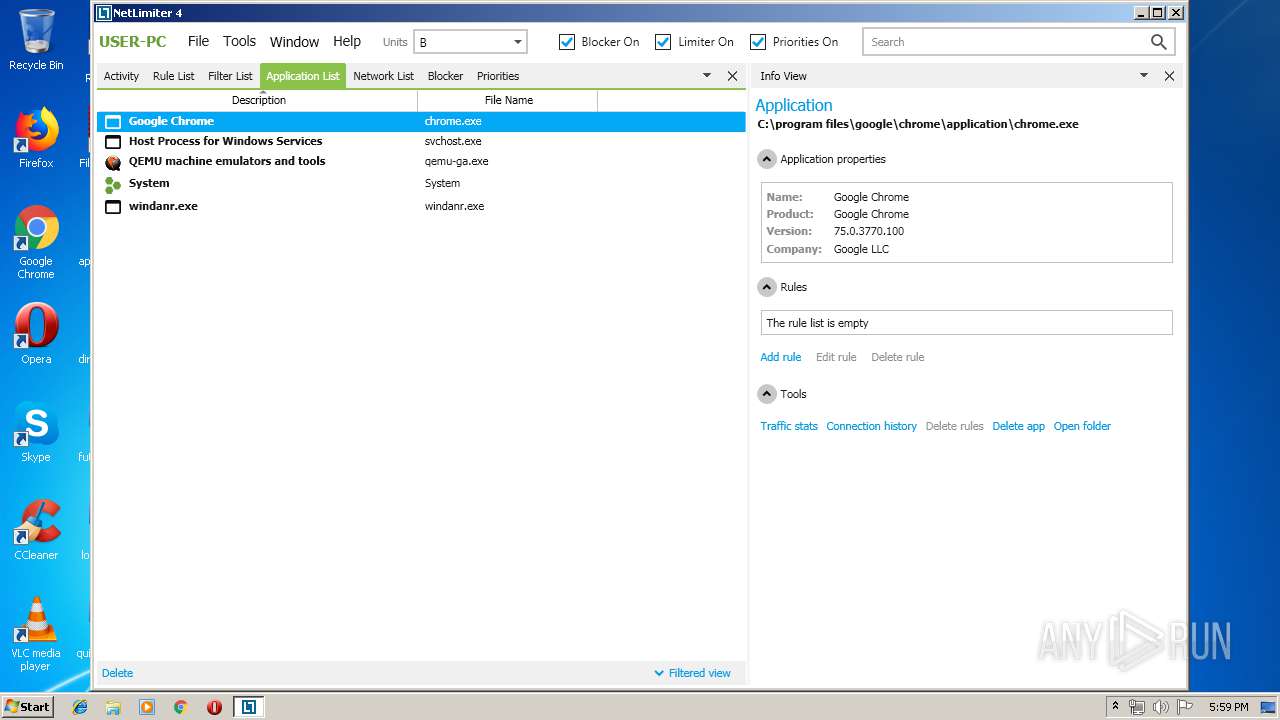
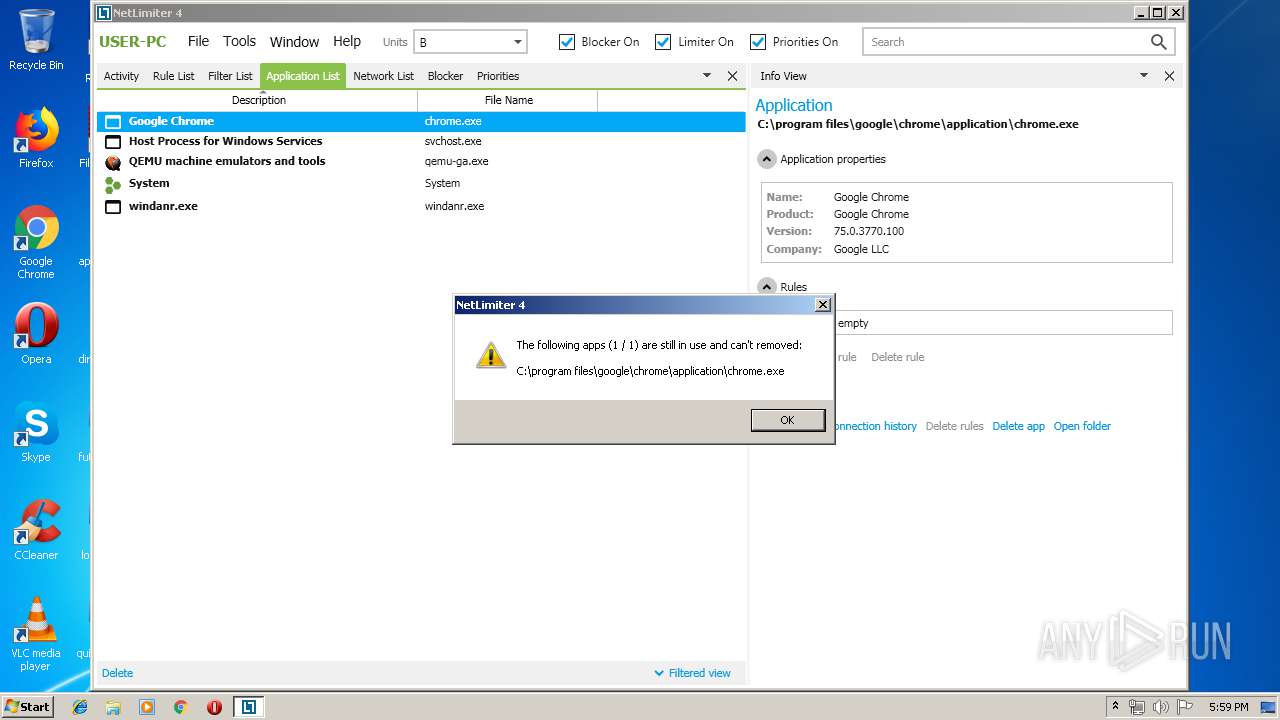
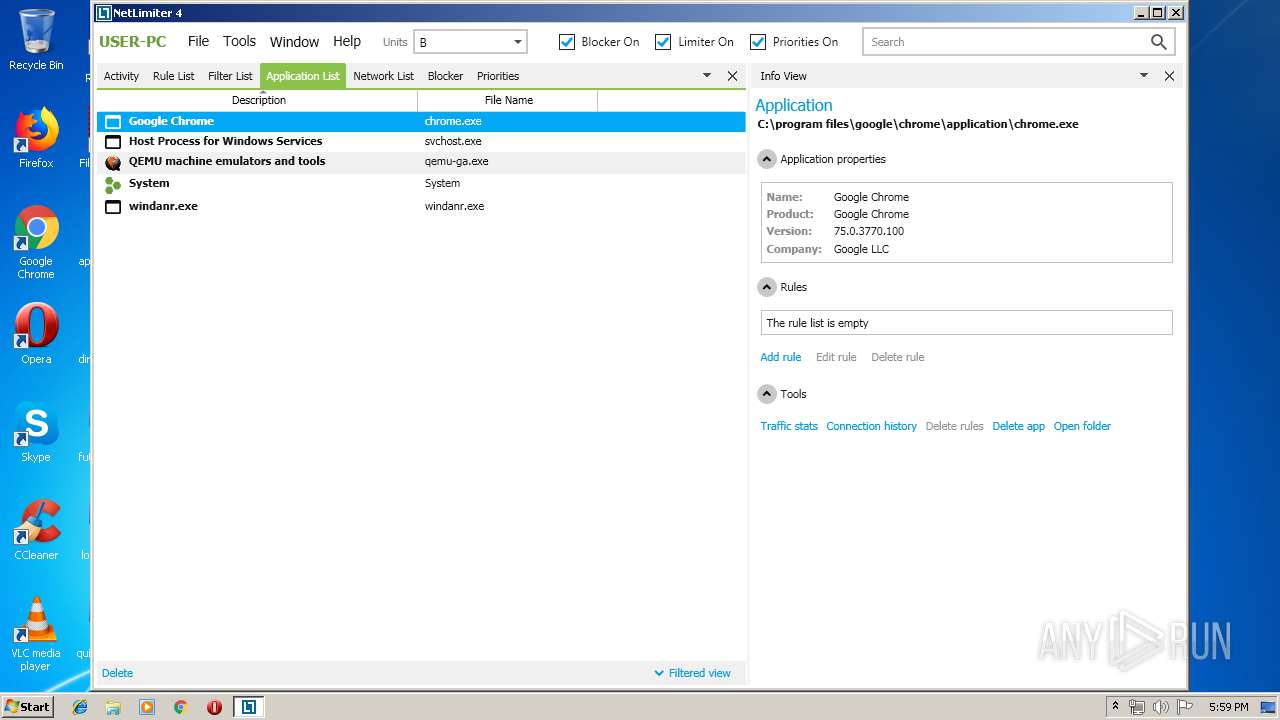
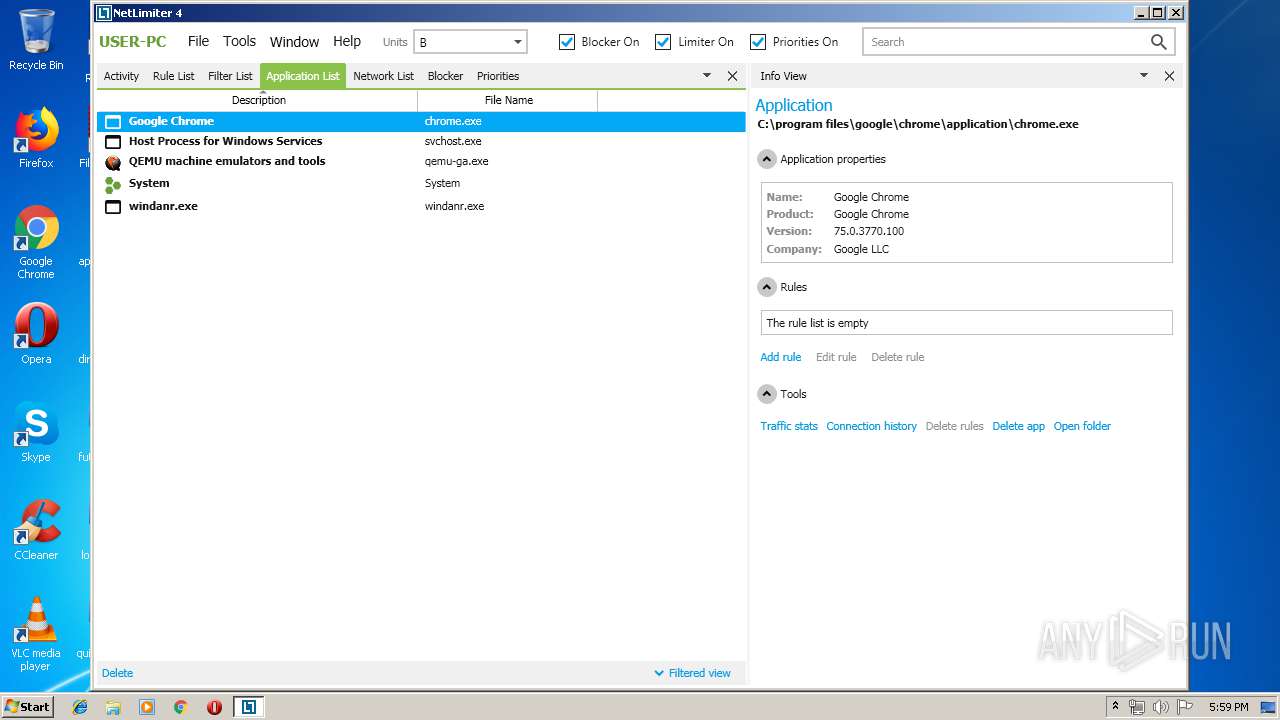
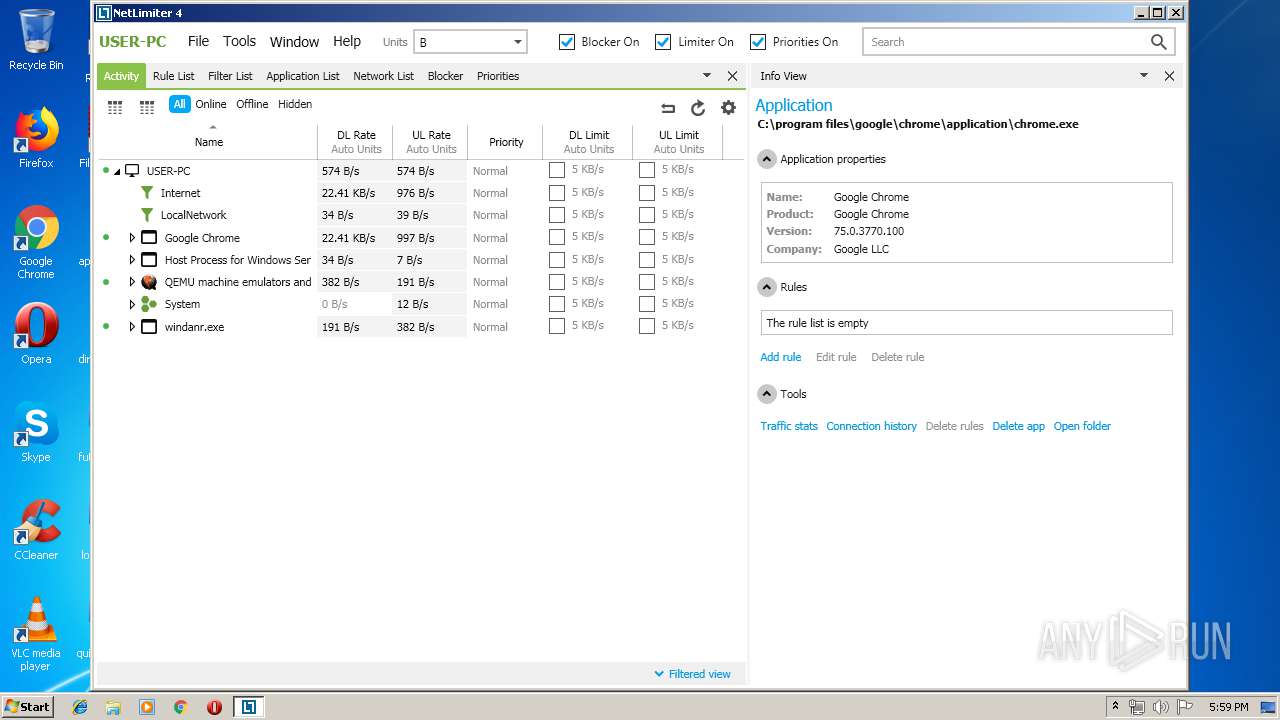
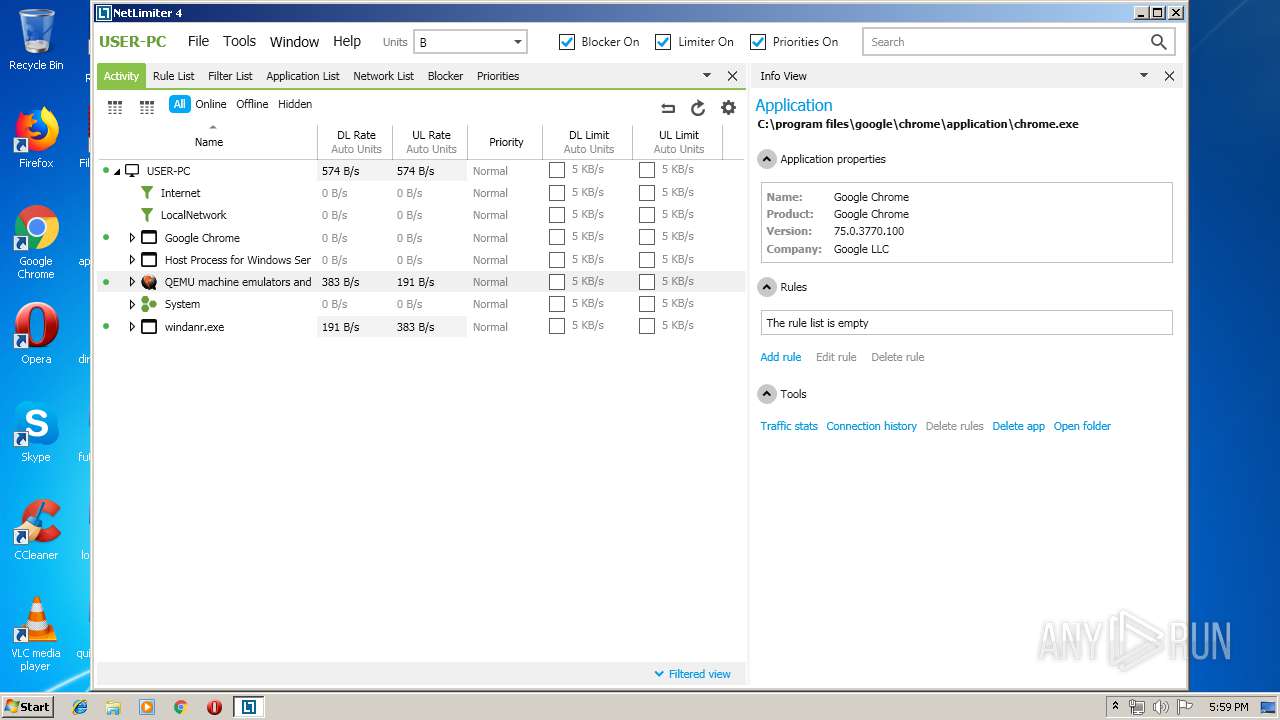
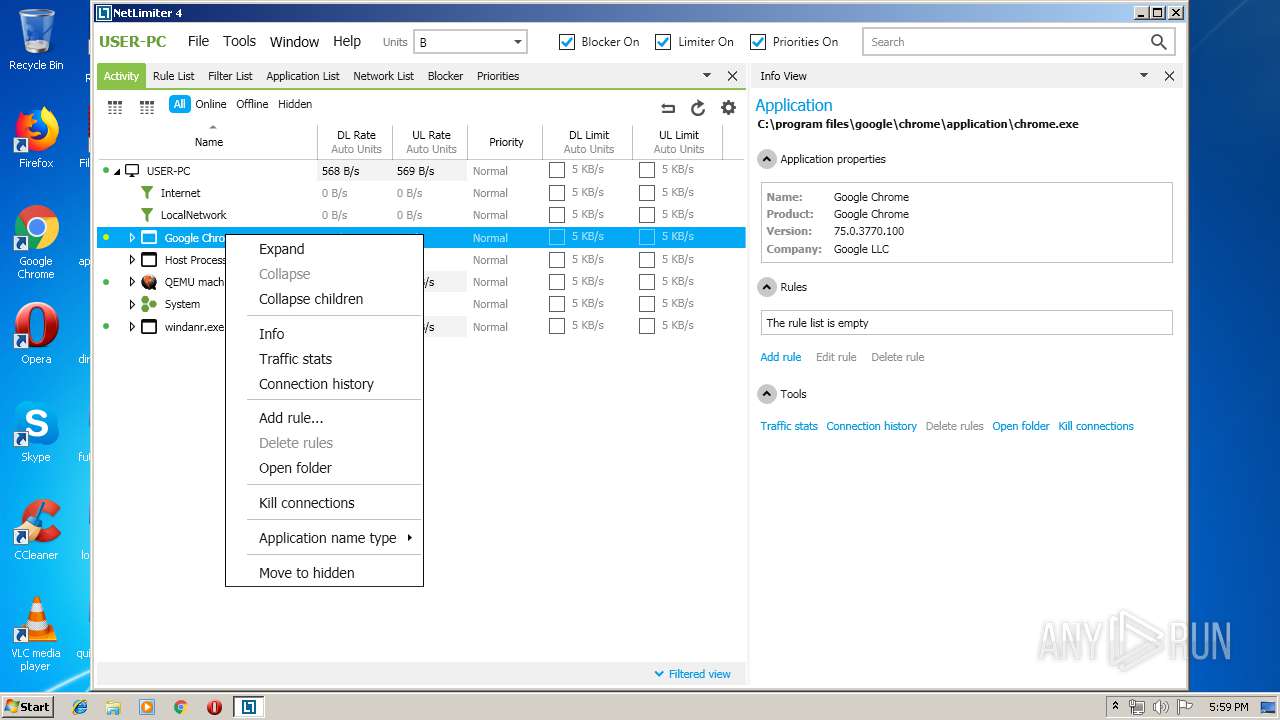
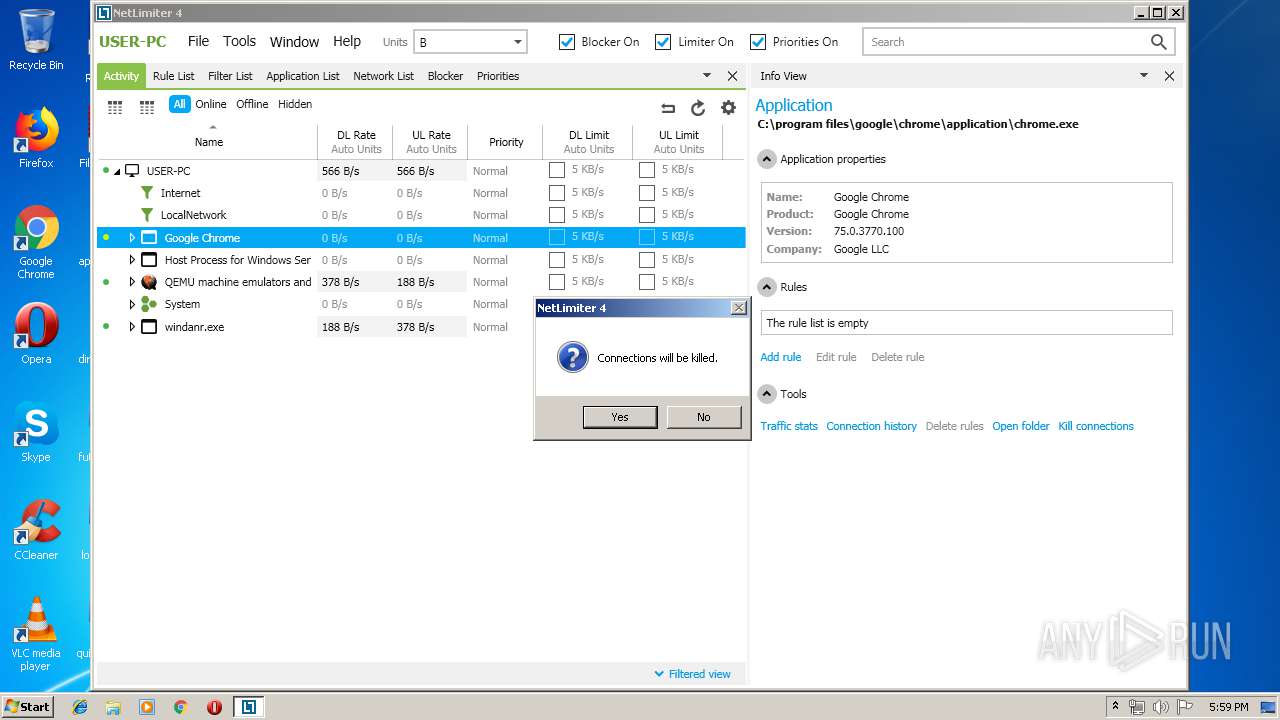
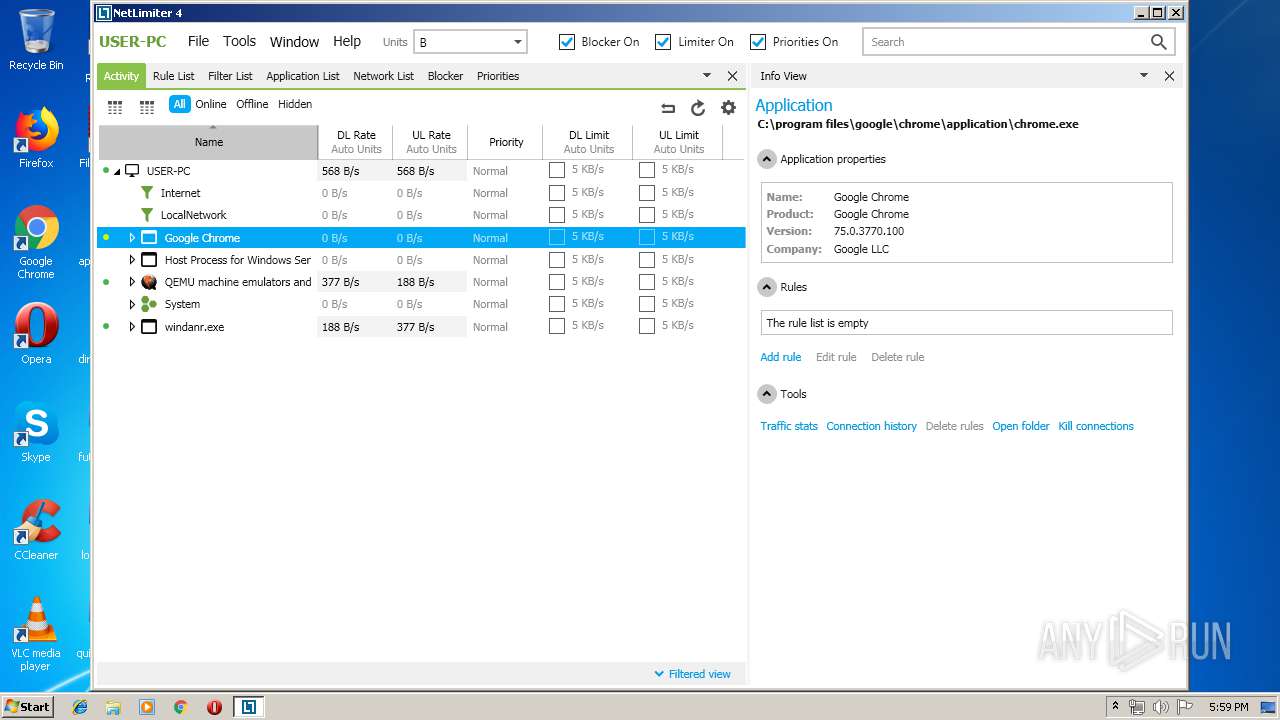
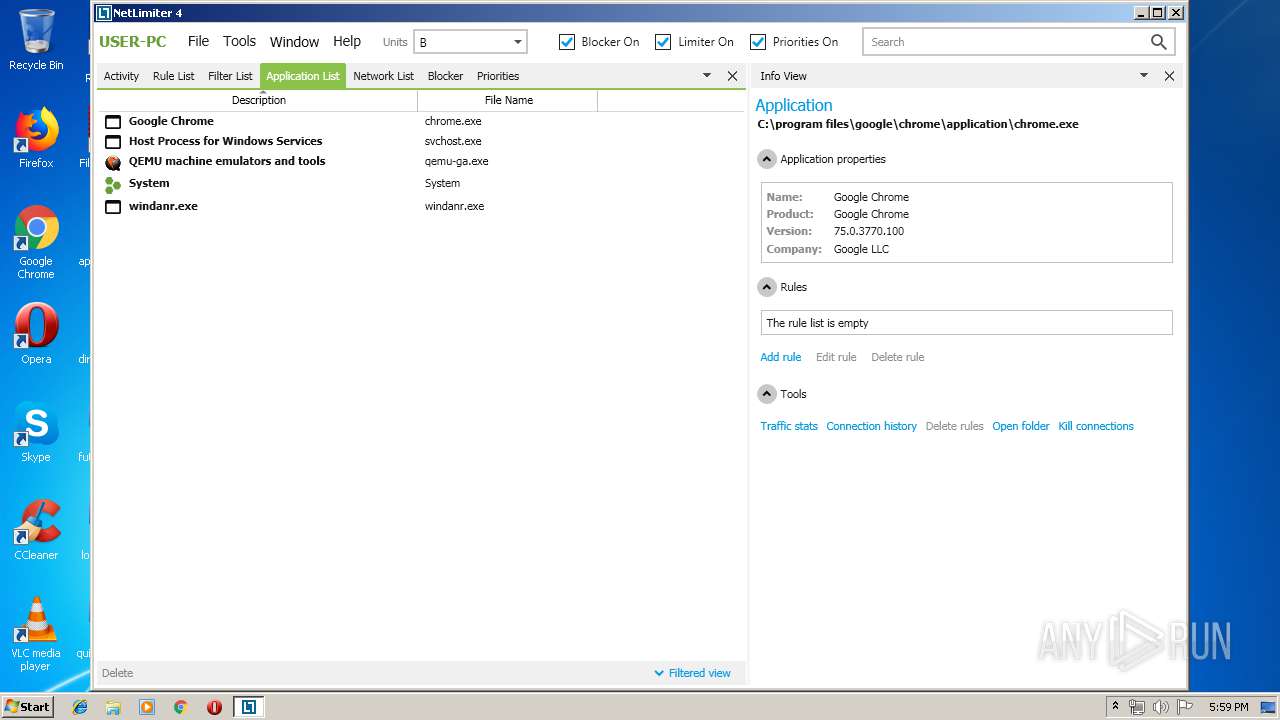
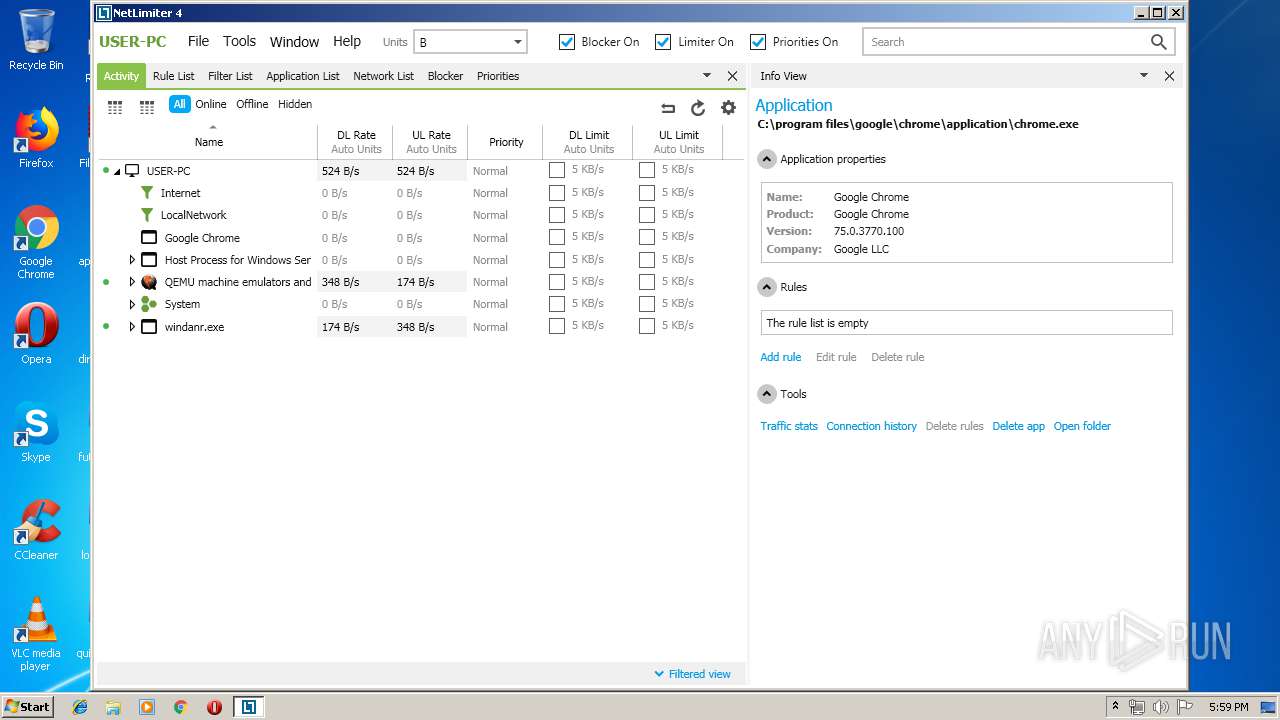
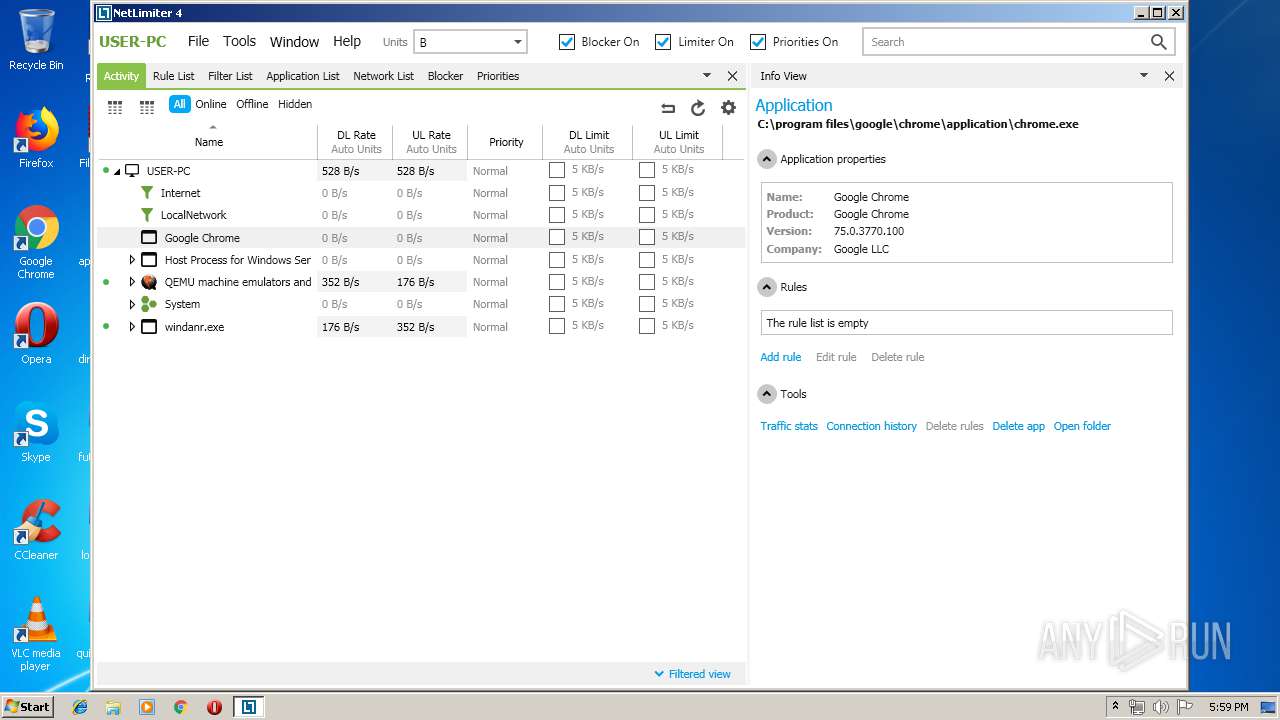
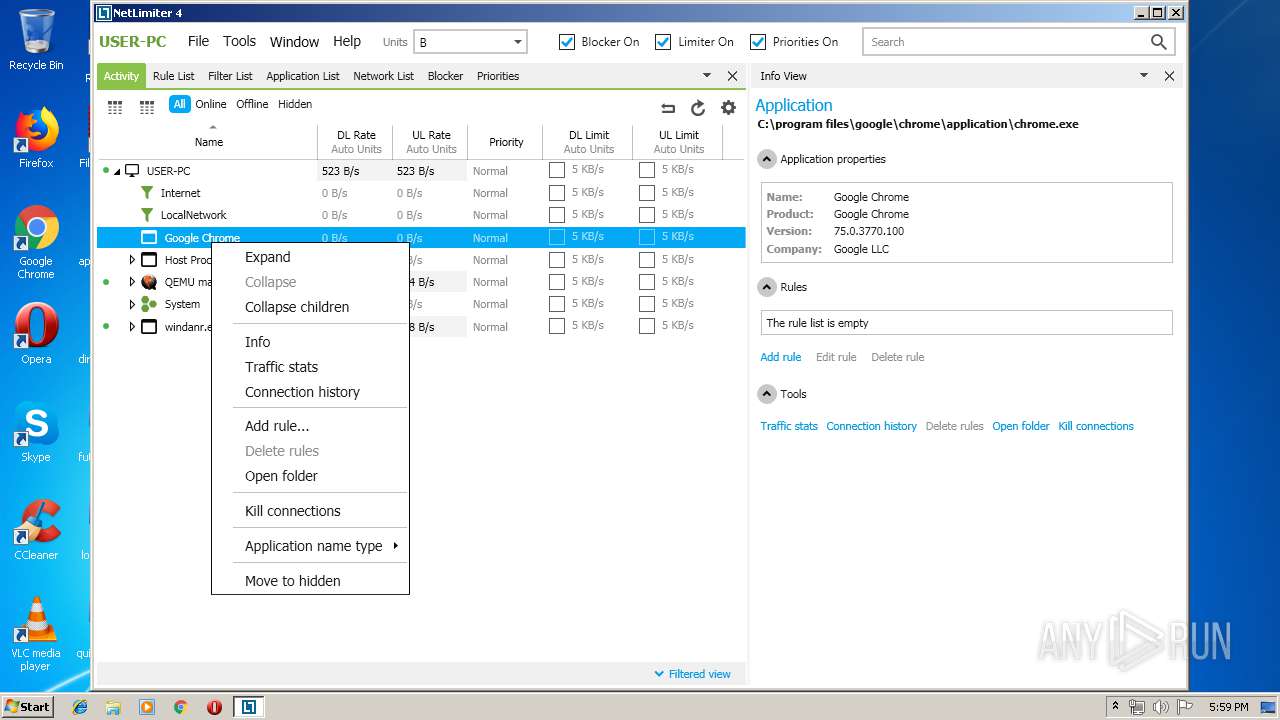
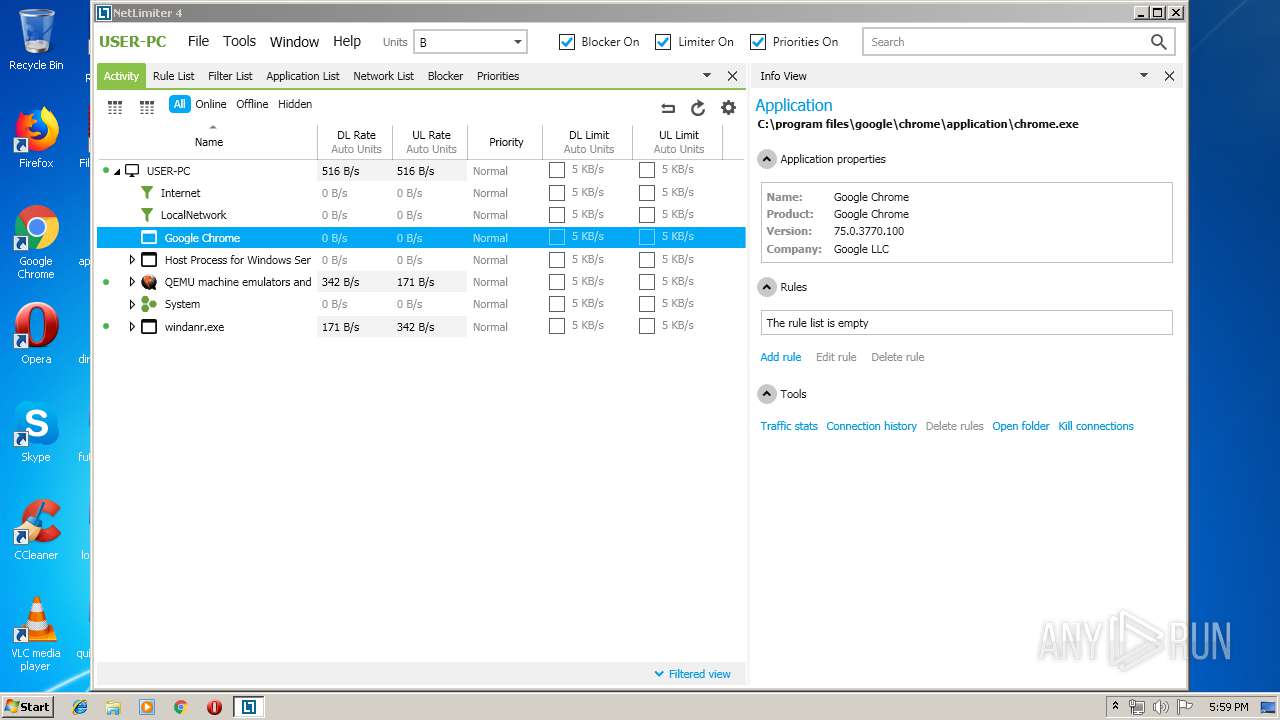
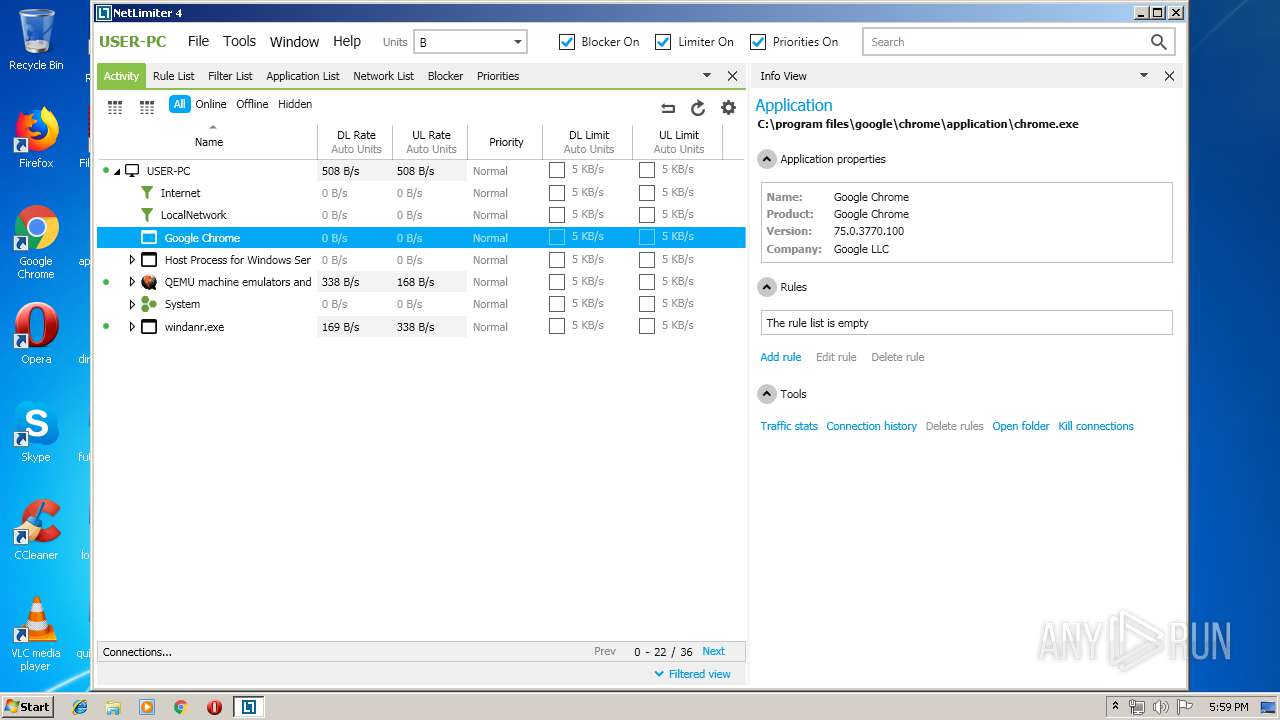
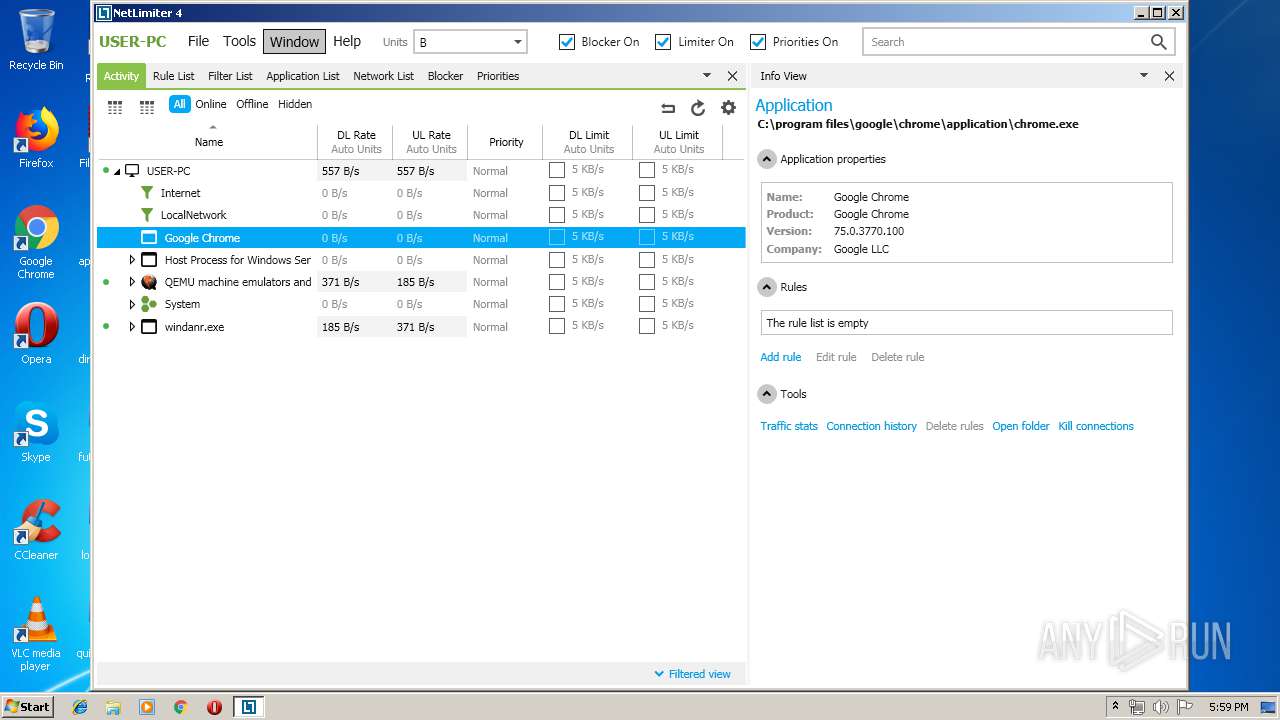
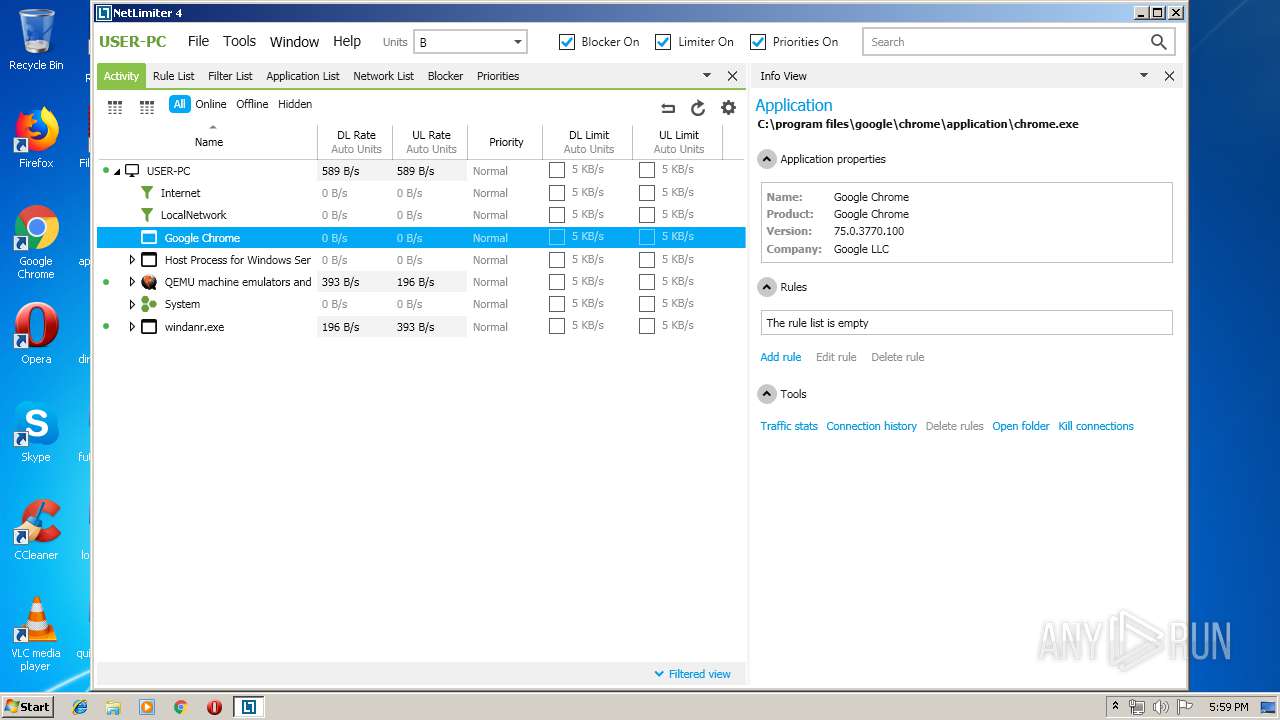
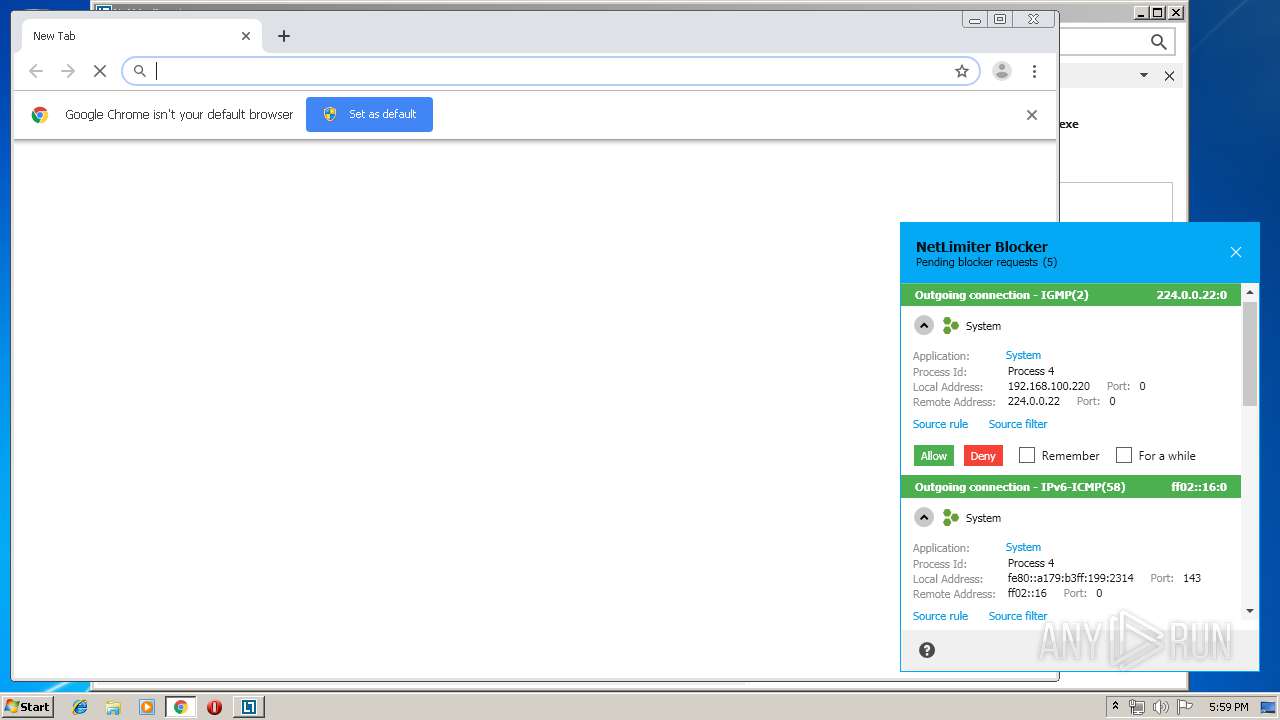
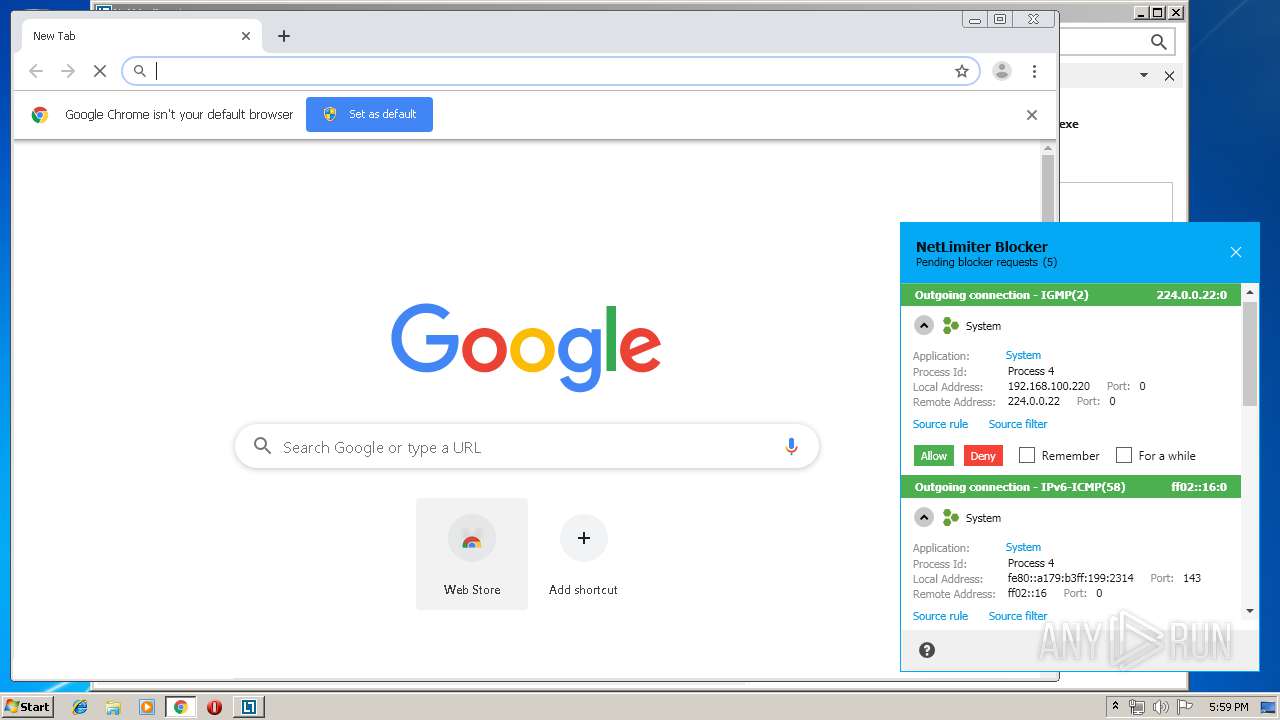
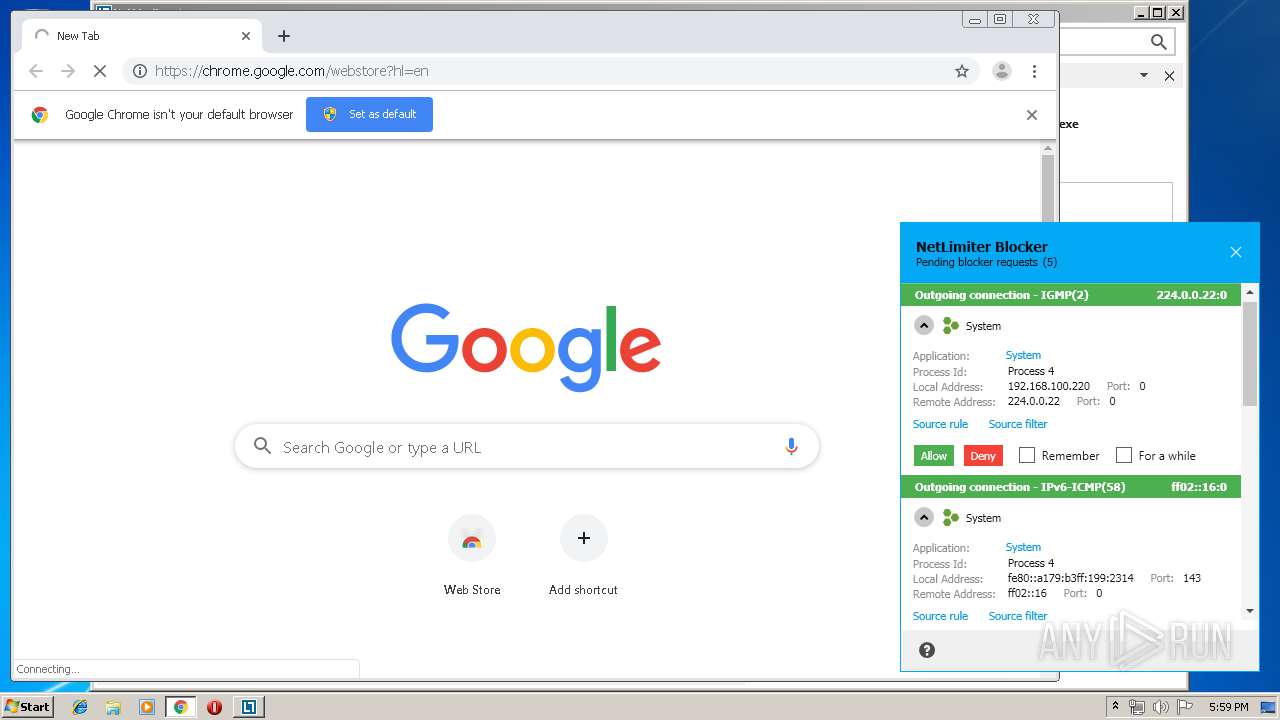
Modifies files in Chrome extension folder
- chrome.exe (PID: 2164)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3008)
- MsiExec.exe (PID: 3468)
- MsiExec.exe (PID: 3440)
- msiexec.exe (PID: 3488)
Searches for installed software
- msiexec.exe (PID: 3488)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3396)
Application launched itself
- msiexec.exe (PID: 3488)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 1004)
Creates files in the program directory
- msiexec.exe (PID: 3488)
Creates a software uninstall entry
- msiexec.exe (PID: 3488)
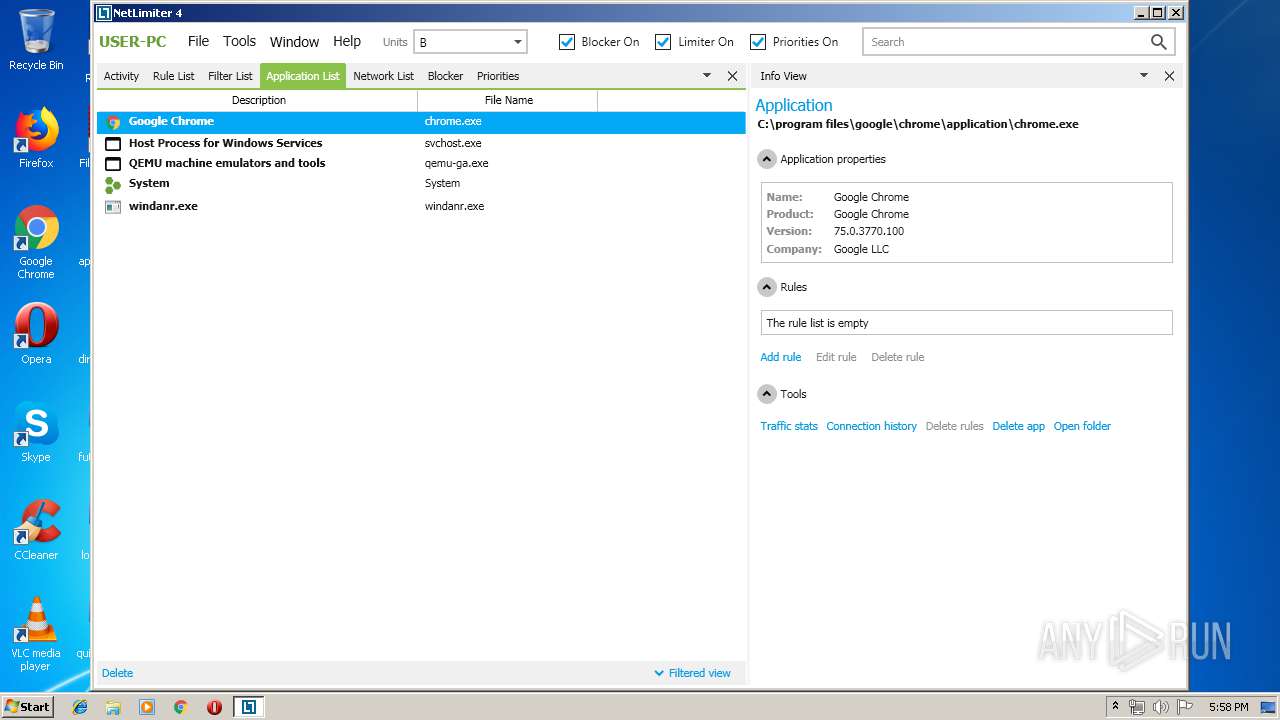
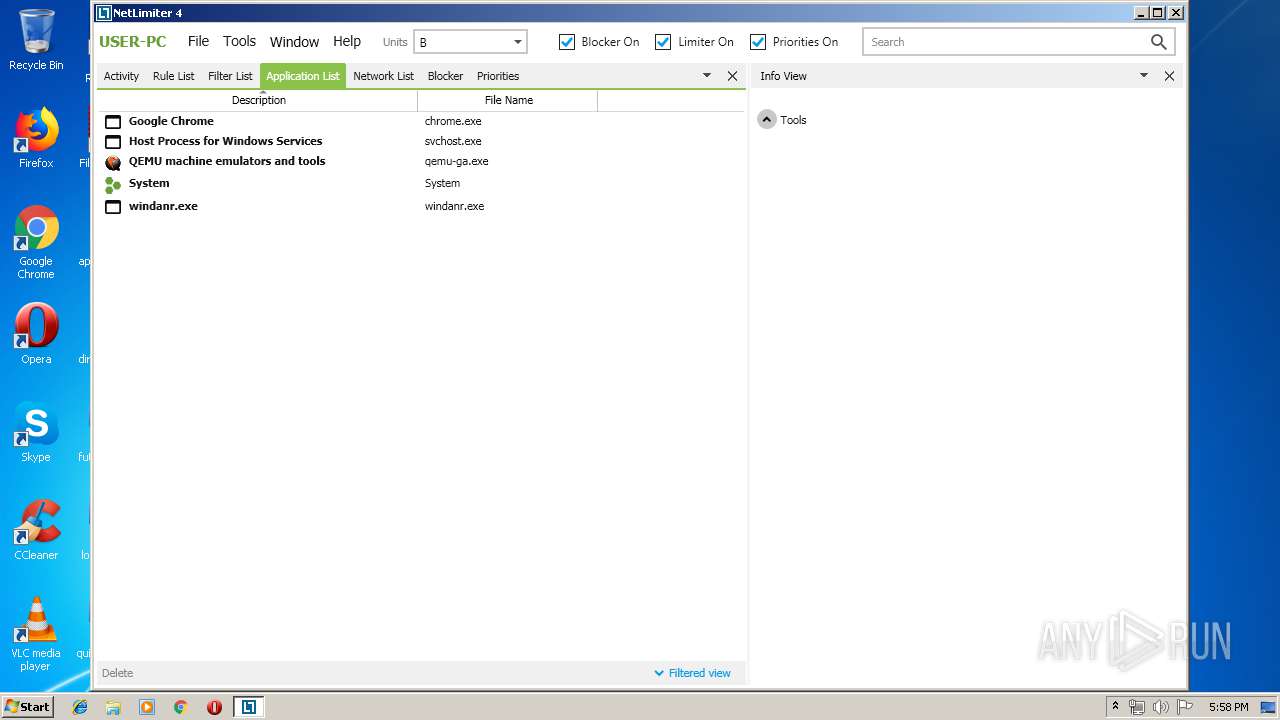
Manual execution by user
- NLClientApp.exe (PID: 2308)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 2164)
- NLClientApp.exe (PID: 2744)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 1004)
Reads the hosts file
- chrome.exe (PID: 2164)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 544)
Reads settings of System Certificates
- chrome.exe (PID: 4020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:14 12:20:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1129472 |
| InitializedDataSize: | 582656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcc1f8 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.53.0 |
| ProductVersionNumber: | 4.0.53.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Locktime Software |
| FileDescription: | This installer database contains the logic and data required to install NetLimiter 4. |
| FileVersion: | 4.0.53.0 |
| InternalName: | netlimiter-4.0.53.0 |
| LegalCopyright: | Copyright (C) 2019 Locktime Software |
| OriginalFileName: | netlimiter-4.0.53.0.exe |
| ProductName: | NetLimiter 4 |
| ProductVersion: | 4.0.53.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Dec-2016 11:20:38 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Locktime Software |
| FileDescription: | This installer database contains the logic and data required to install NetLimiter 4. |
| FileVersion: | 4.0.53.0 |
| InternalName: | netlimiter-4.0.53.0 |
| LegalCopyright: | Copyright (C) 2019 Locktime Software |
| OriginalFileName: | netlimiter-4.0.53.0.exe |
| ProductName: | NetLimiter 4 |
| ProductVersion: | 4.0.53.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 14-Dec-2016 11:20:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00113B5C | 0x00113C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63264 |
.rdata | 0x00115000 | 0x00053334 | 0x00053400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.54312 |
.data | 0x00169000 | 0x000071E4 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.12128 |
.gfids | 0x00171000 | 0x000003F0 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.00634 |
.tls | 0x00172000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00173000 | 0x00020950 | 0x00020A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.46681 |
.reloc | 0x00194000 | 0x00014A3C | 0x00014C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58944 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18998 | 1909 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 1.58455 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 1.59297 | 5672 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.34109 | 1000 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
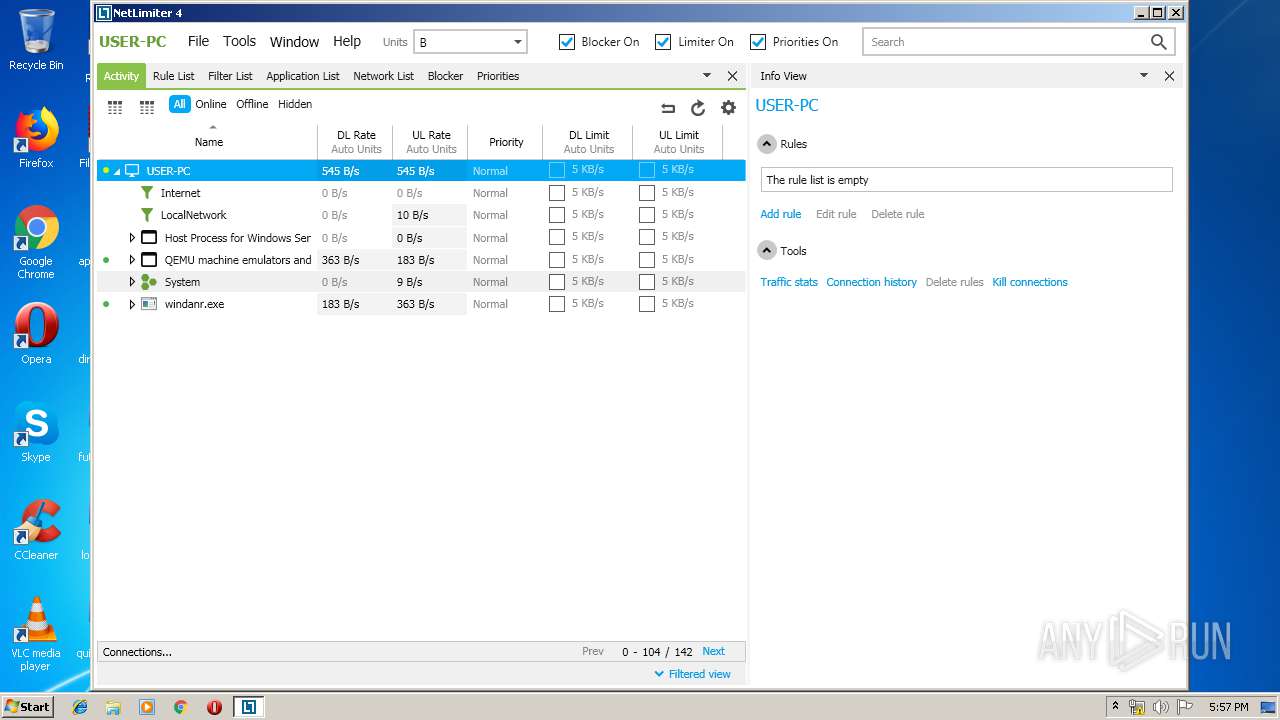
Total processes
149
Monitored processes
100
Malicious processes
20
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,5218927547628734201,9745161647067712287,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9269862556866318212 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,7491578607707093075,8479543659400533518,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13992733919114982594 --mojo-platform-channel-handle=3920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,6795258199043636296,13596743796541196246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7581909574730119651 --mojo-platform-channel-handle=2512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,6795258199043636296,13596743796541196246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18011507375980156491 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1484 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
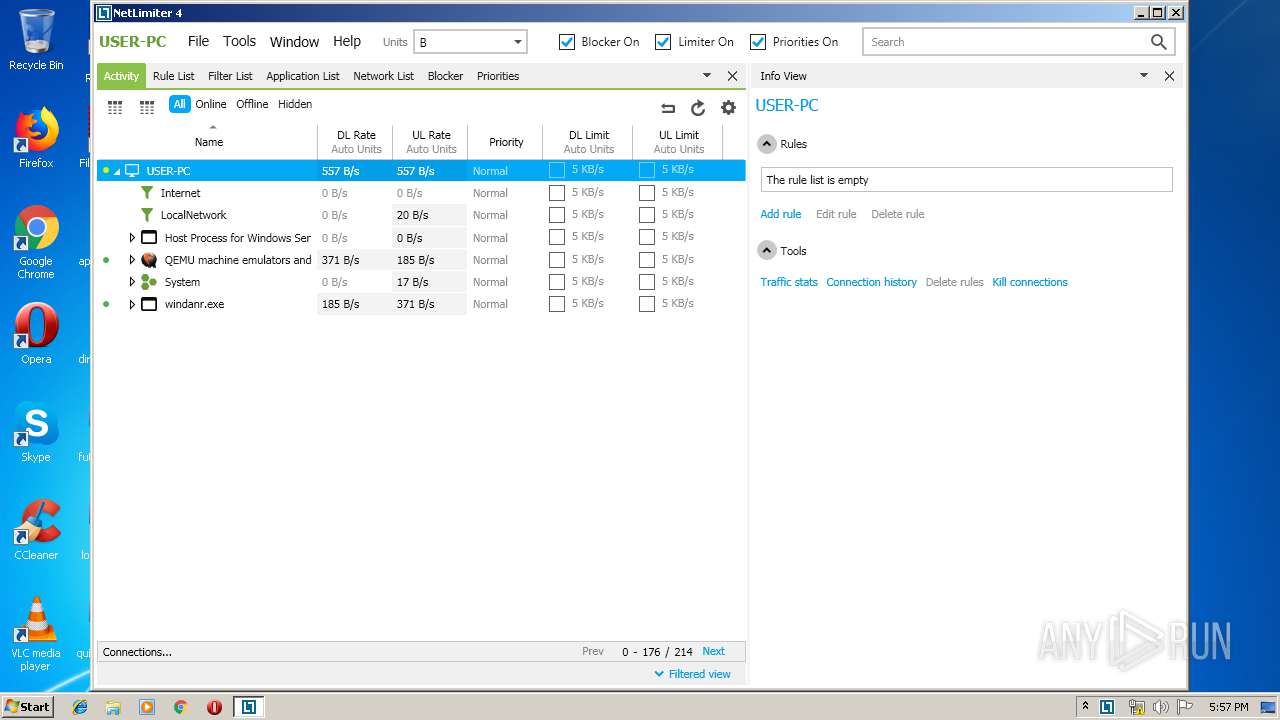
| 324 | "C:\Program Files\Locktime Software\NetLimiter 4\NLSvc.exe" | C:\Program Files\Locktime Software\NetLimiter 4\NLSvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: Locktime Software Integrity Level: SYSTEM Description: NetLimiter Service Exit code: 0 Version: 4.0.53.0 Modules
| |||||||||||||||
| 348 | cmd /c ""C:\Users\admin\AppData\Local\Temp\EXED46E.tmp.bat" " | C:\Windows\system32\cmd.exe | — | netlimiter-4.0.53.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,5218927547628734201,9745161647067712287,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5515782374422320339 --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,6795258199043636296,13596743796541196246,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11505688284005901666 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,6795258199043636296,13596743796541196246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7186959230231185667 --mojo-platform-channel-handle=4104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 773
Read events
2 089
Write events
657
Delete events
27
Modification events
| (PID) Process: | (2596) netlimiter-4.0.53.0.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2596) netlimiter-4.0.53.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000C5DFB849CA051355EE2DBA1AC33EB0280F00000001000000200000005229BA15B31B0C6F4CCA89C2985177974327D1B689A3B935A0BD975532AF22AB090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B06010505070308060A2B0601040182370A030406082B0601050507030606082B060105050703070B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D0020005200330000005300000001000000230000003021301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0620000000100000020000000CBB522D7B7F127AD6A0113865BDF1CD4102E7D0759AF635A7CF4720DC963C53B1400000001000000140000008FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC1D000000010000001000000001728E1ECF7A9D86FB3CEC8948ABA953030000000100000014000000D69B561148F01C77C54578C10926DF5B856976AD190000000100000010000000D0FD3C9C380D7B65E26B9A3FEDD39B8F2000000001000000630300003082035F30820247A003020102020B04000000000121585308A2300D06092A864886F70D01010B0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3039303331383130303030305A170D3239303331383130303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820122300D06092A864886F70D01010105000382010F003082010A0282010100CC2576907906782216F5C083B684CA289EFD057611C5AD8872FC460243C7B28A9D045F24CB2E4BE1608246E152AB0C8147706CDD64D1EBF52CA30F823D0C2BAE97D7B614861079BB3B1380778C08E149D26A622F1F5EFA9668DF892795389F06D73EC9CB26590D73DEB0C8E9260E8315C6EF5B8BD20460CA49A628F6693BF6CBC82891E59D8A615737AC7414DC74E03AEE722F2E9CFBD0BBBFF53D00E10633E8822BAE53A63A16738CDD410E203AC0B4A7A1E9B24F902E3260E957CBB904926868E538266075B29F77FF9114EFAE2049FCAD401548D1023161195EB897EFAD77B7649A7ABF5FC113EF9B62FB0D6CE0546916A903DA6EE983937176C6698582170203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604148FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC300D06092A864886F70D01010B050003820101004B40DBC050AAFEC80CEFF796544549BB96000941ACB3138686280733CA6BE674B9BA002DAEA40AD3F5F1F10F8ABF73674A83C7447B78E0AF6E6C6F03298E333945C38EE4B9576CAAFC1296EC53C62DE4246CB99463FBDC536867563E83B8CF3521C3C968FECEDAC253AACC908AE9F05D468C95DD7A58281A2F1DDECD0037418FED446DD75328977EF367041E15D78A96B4D3DE4C27A44C1B737376F41799C21F7A0EE32D08AD0A1C2CFF3CAB550E0F917E36EBC35749BEE12E2D7C608BC3415113239DCEF7326B9401A899E72C331F3A3B25D28640CE3B2C8678C9612F14BAEEDB556FDF84EE05094DBD28D872CED36250651EEB92978331D9B3B5CA47583F5F | |||
| (PID) Process: | (2596) netlimiter-4.0.53.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2596) netlimiter-4.0.53.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1632) netlimiter-4.0.53.0.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3488) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000002C4CD2FE2F7DD501A00D0000F40B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3488) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000002C4CD2FE2F7DD501A00D0000F40B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3488) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 24 | |||
| (PID) Process: | (3488) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000007ABE25FF2F7DD501A00D0000F40B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3488) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D42028FF2F7DD501A00D0000CC090000E8030000010000000000000000000000FF3571D6EA747D49AC041E603206DF670000000000000000 | |||
Executable files
136
Suspicious files
95
Text files
568
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Roaming\Locktime Software\NetLimiter 4 4.0.53.0\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Local\Temp\MSI21B4.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Roaming\Locktime Software\NetLimiter 4 4.0.53.0\install\4269DEF\netlimiter-4.0.53.0.msi | executable | |
MD5:E6AACA3C388920A5AE2B6BF4C3C624CD | SHA256:1E0945F47AA5C518C882A288C23C4067DE4B27F76D18D955AC90636FECA23860 | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Roaming\Locktime Software\NetLimiter 4 4.0.53.0\install\4269DEF\Microsoft_VC141_CRT_x86.cab | compressed | |
MD5:DA6D4CAED78770CA349C69EB80209D25 | SHA256:25F8A5F02455FB0F36A17A4852AEE1E8A3A5DF874252B4EDB912AD2FE6BC0854 | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2596\frame_bottom_left.bmp | image | |
MD5:1FB3755FE9676FCA35B8D3C6A8E80B45 | SHA256:384EBD5800BECADF3BD9014686E6CC09344F75CE426E966D788EB5473B28AA21 | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2596\frame_bottom_left_inactive.bmp | image | |
MD5:821930553EF406B0C82D9420D3351C78 | SHA256:D5E9F3533CB7D727611AAFAA5AF22FA07EFEAEC0391A011ECF9803BED867DE7A | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2596\frame_caption_inactive.bmp | image | |
MD5:8641F45594B8D413BF1DA25CE59F1207 | SHA256:0403ED31D75DCC182DD98F2B603DA4C36B6325E9D159CAC4371E1448244BB707 | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2596\frame_left.bmp | image | |
MD5:30384472AE83FF8A7336B987292D8349 | SHA256:F545EC56BC9B690A6B952471669A8316E18274D64E2EBC9E365FCF44363A125A | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2596\frame_bottom_right_inactive.bmp | image | |
MD5:1FB3755FE9676FCA35B8D3C6A8E80B45 | SHA256:384EBD5800BECADF3BD9014686E6CC09344F75CE426E966D788EB5473B28AA21 | |||
| 2596 | netlimiter-4.0.53.0.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2596\frame_right.bmp | image | |
MD5:30384472AE83FF8A7336B987292D8349 | SHA256:F545EC56BC9B690A6B952471669A8316E18274D64E2EBC9E365FCF44363A125A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
53
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4020 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
4020 | chrome.exe | GET | 200 | 173.194.7.57:80 | http://r3---sn-p5qlsnsr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qlsnsr&ms=nvh&mt=1570467377&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
4020 | chrome.exe | GET | 200 | 172.217.135.6:80 | http://r1---sn-p5qlsndk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qlsndk&ms=nvh&mt=1570467377&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
4020 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 507 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4020 | chrome.exe | 172.217.135.6:80 | r1---sn-p5qlsndk.gvt1.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 216.58.210.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.18.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 173.194.7.57:80 | r3---sn-p5qlsnsr.gvt1.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
redirector.gvt1.com |
| whitelisted |
r1---sn-p5qlsndk.gvt1.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
MsiExec.exe | DBGHELP: Symbol Search Path: .
|
MsiExec.exe | DBGHELP: Symbol Search Path: C:\Windows\system32
|
MsiExec.exe | DBGHELP: SymSrv load failure: symsrv.dll
|
MsiExec.exe | DBGHELP: C:\Windows\system32\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: C:\Windows\system32\dll\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: C:\Windows\system32\symbols\dll\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: ntdll - export symbols
|
NLSvc.exe | Service installed successfully: n
|
NLSvc.exe | [s (54)] C: Start control dispatcher
|