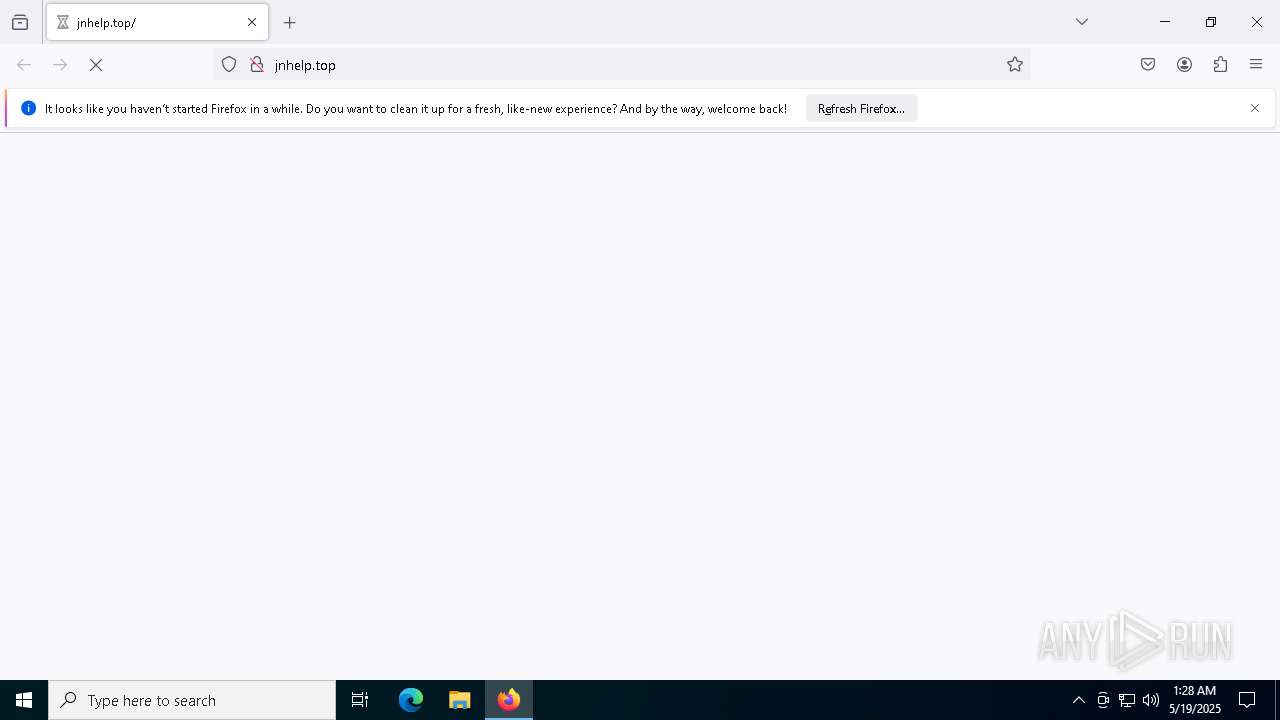
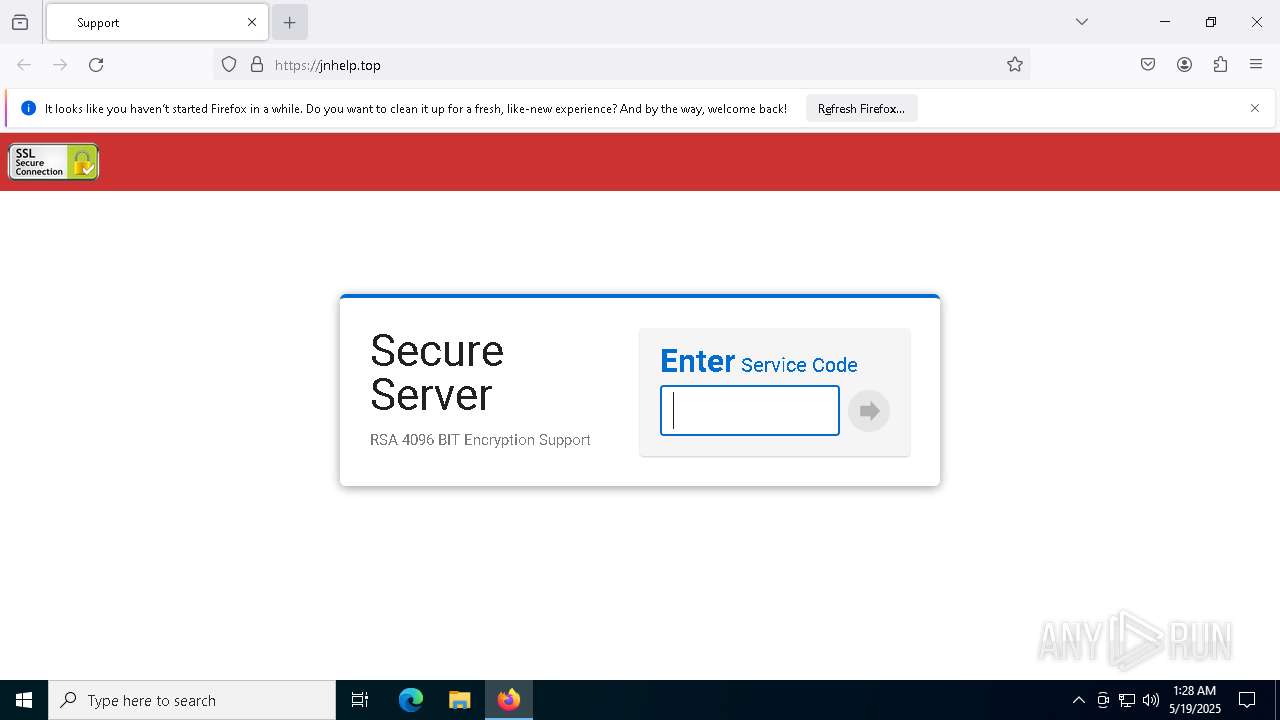
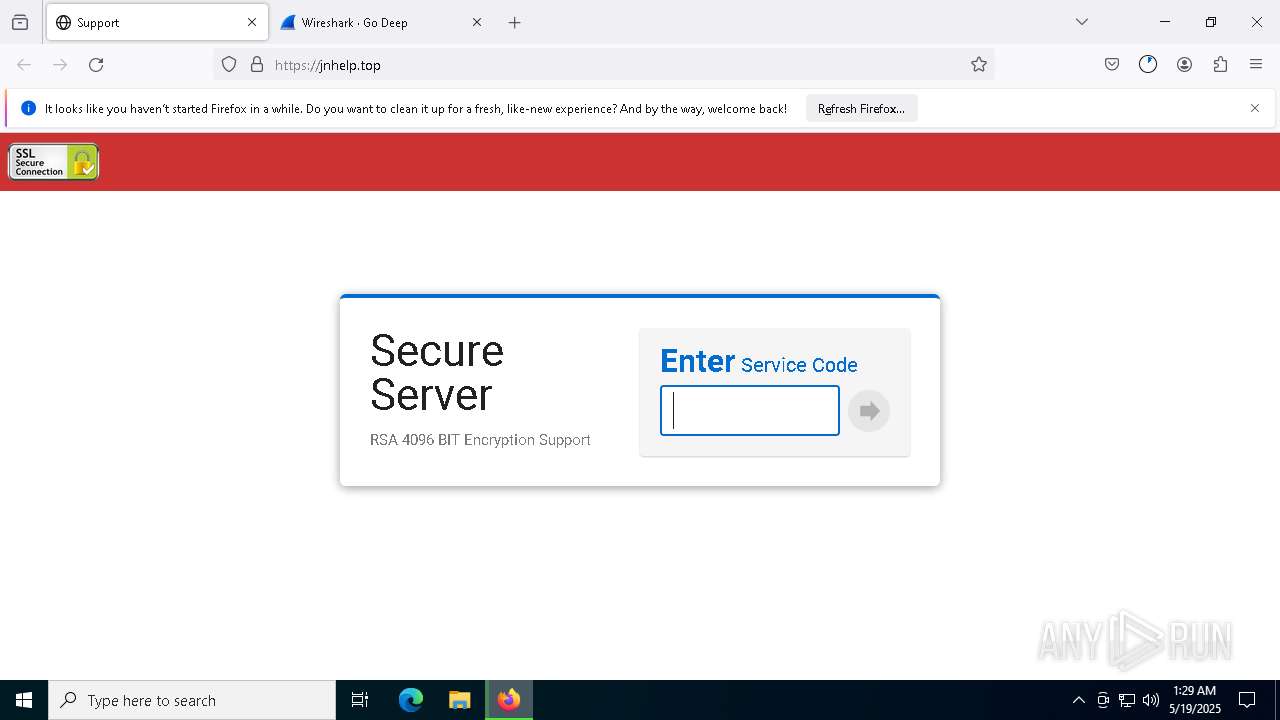
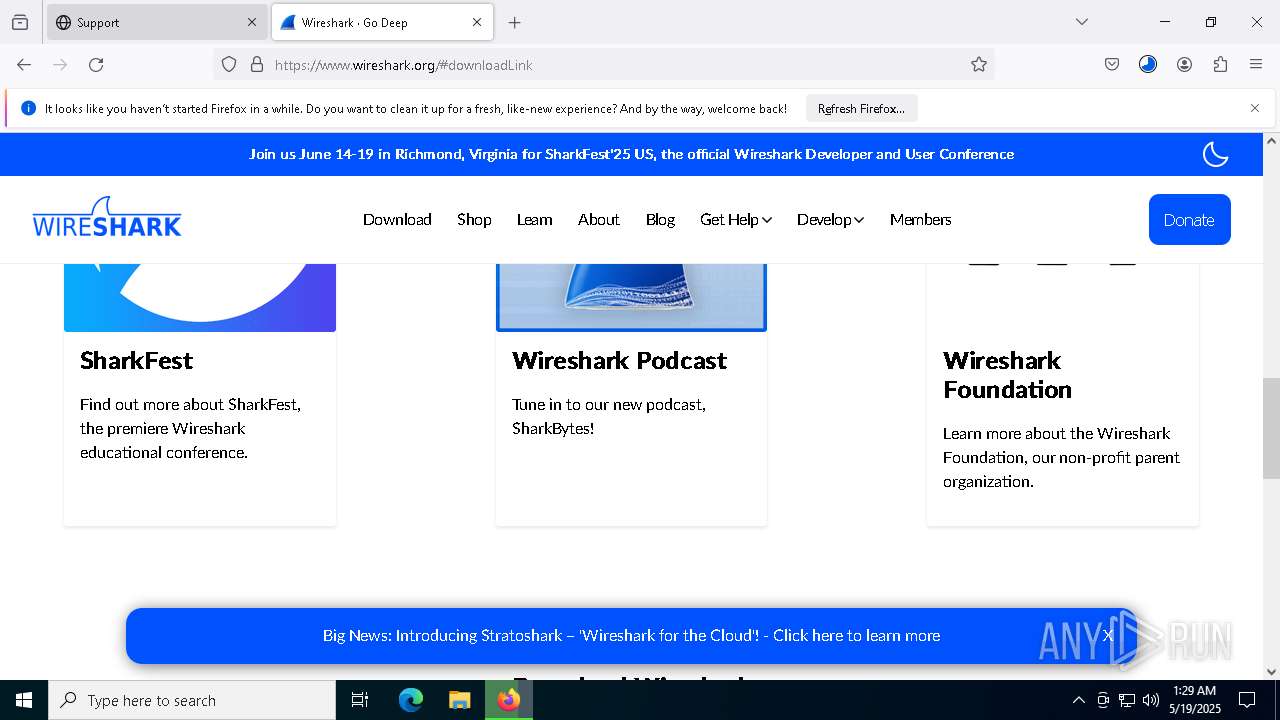
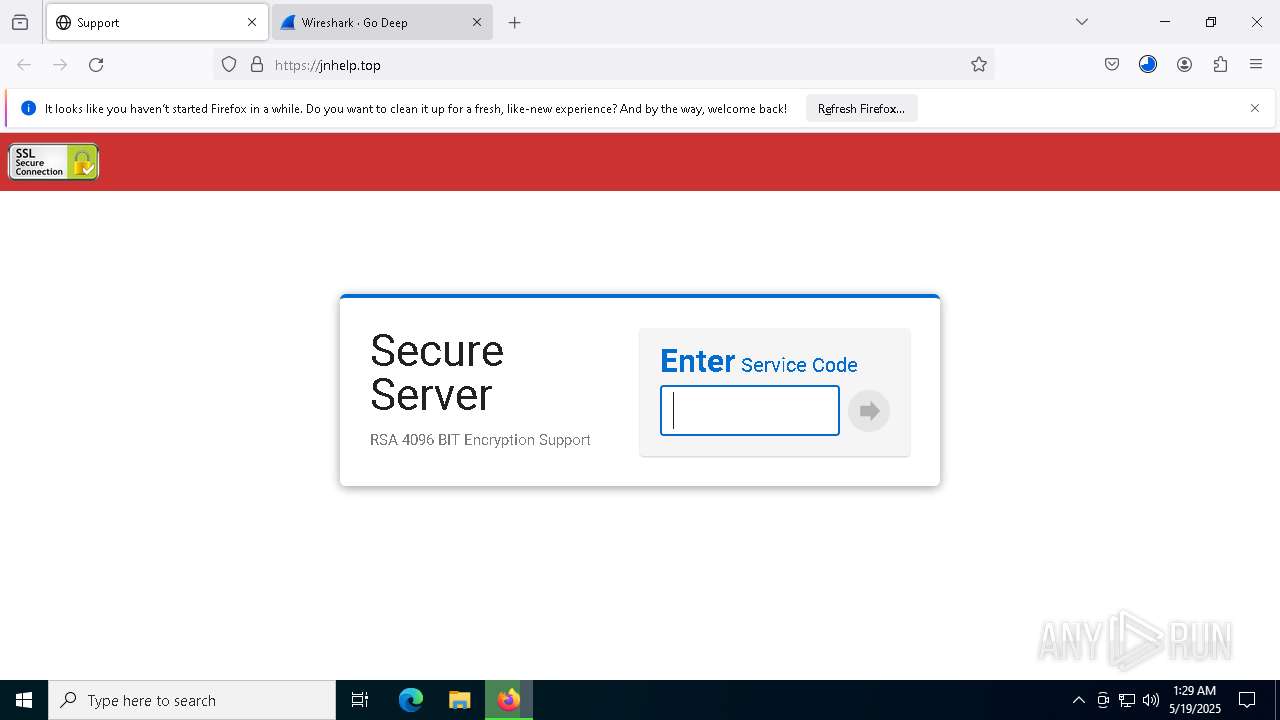
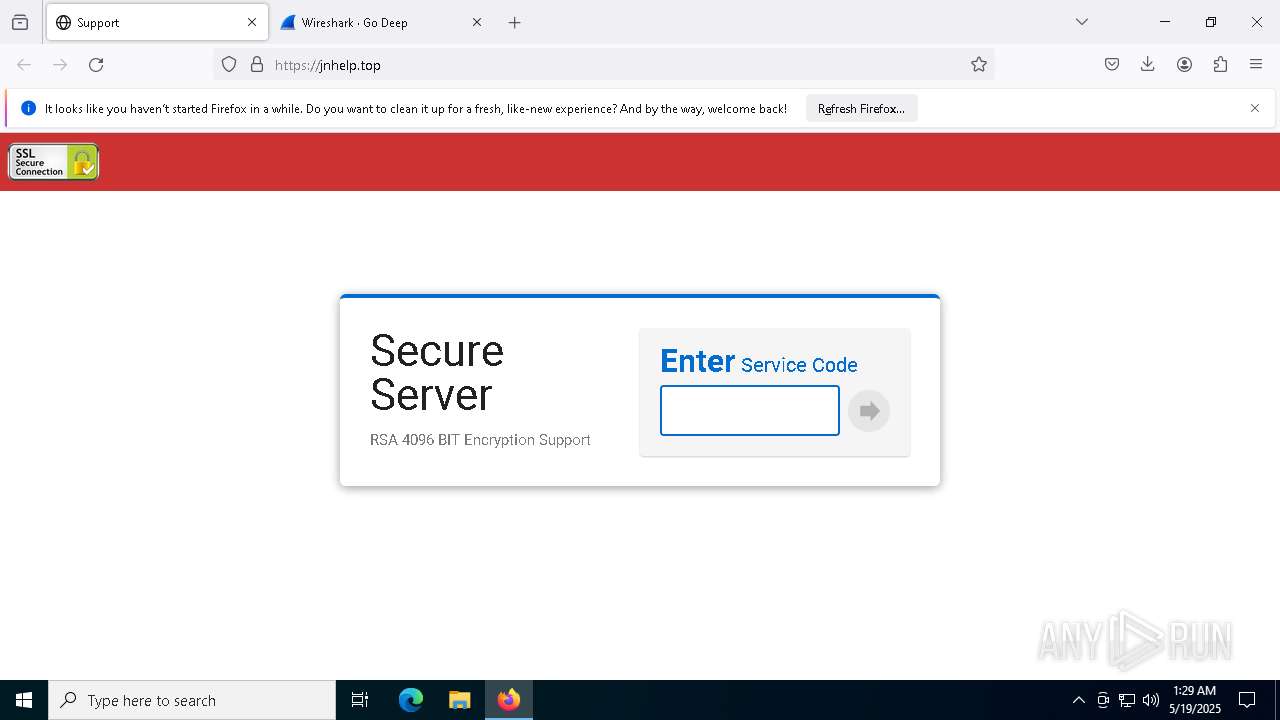
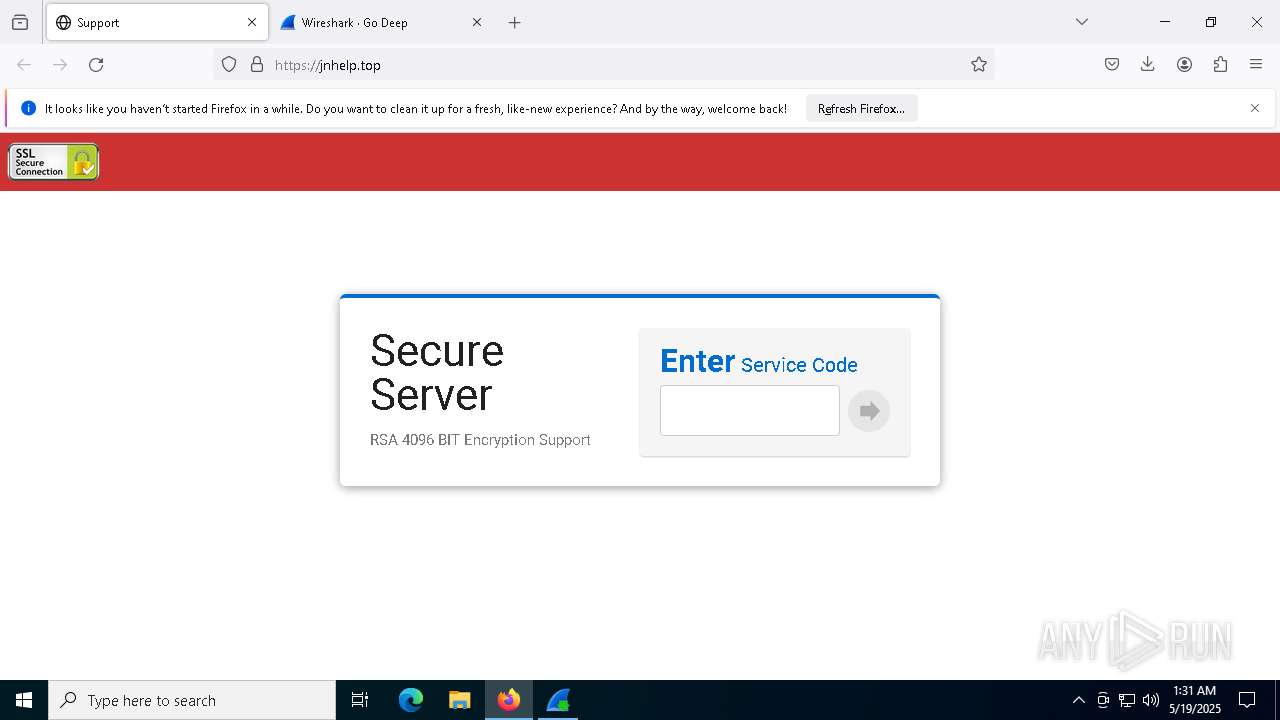
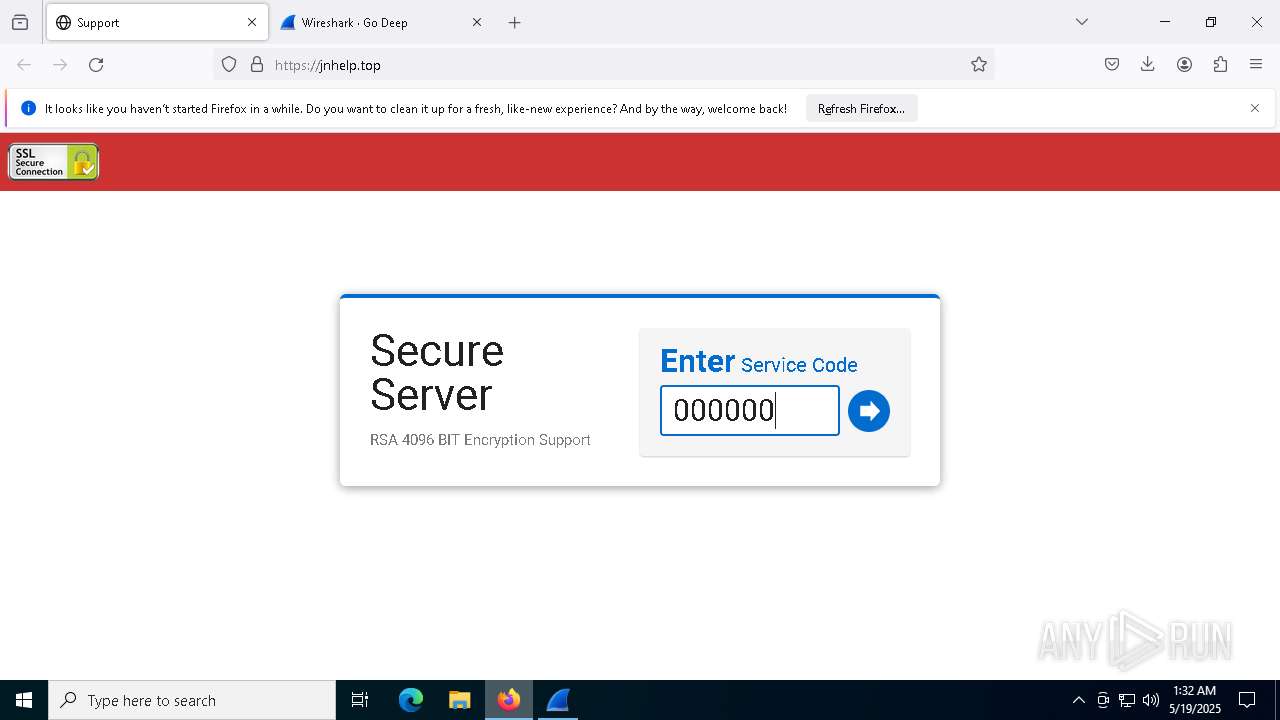
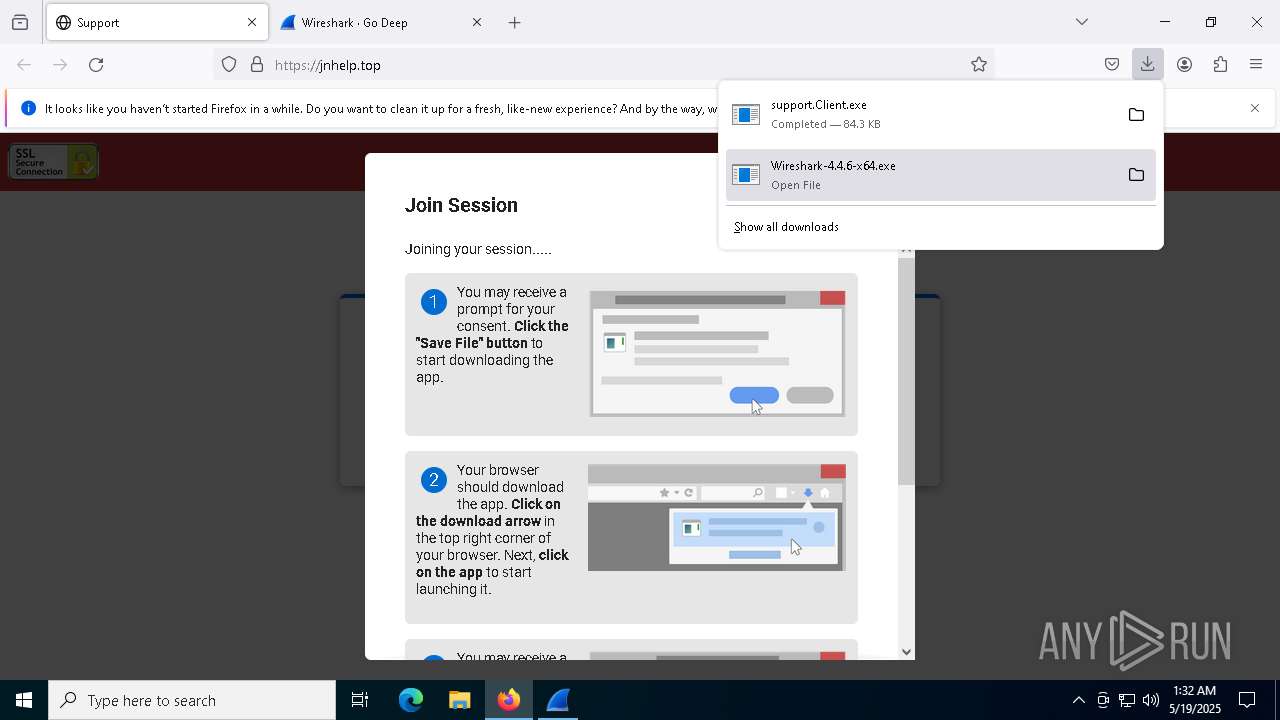
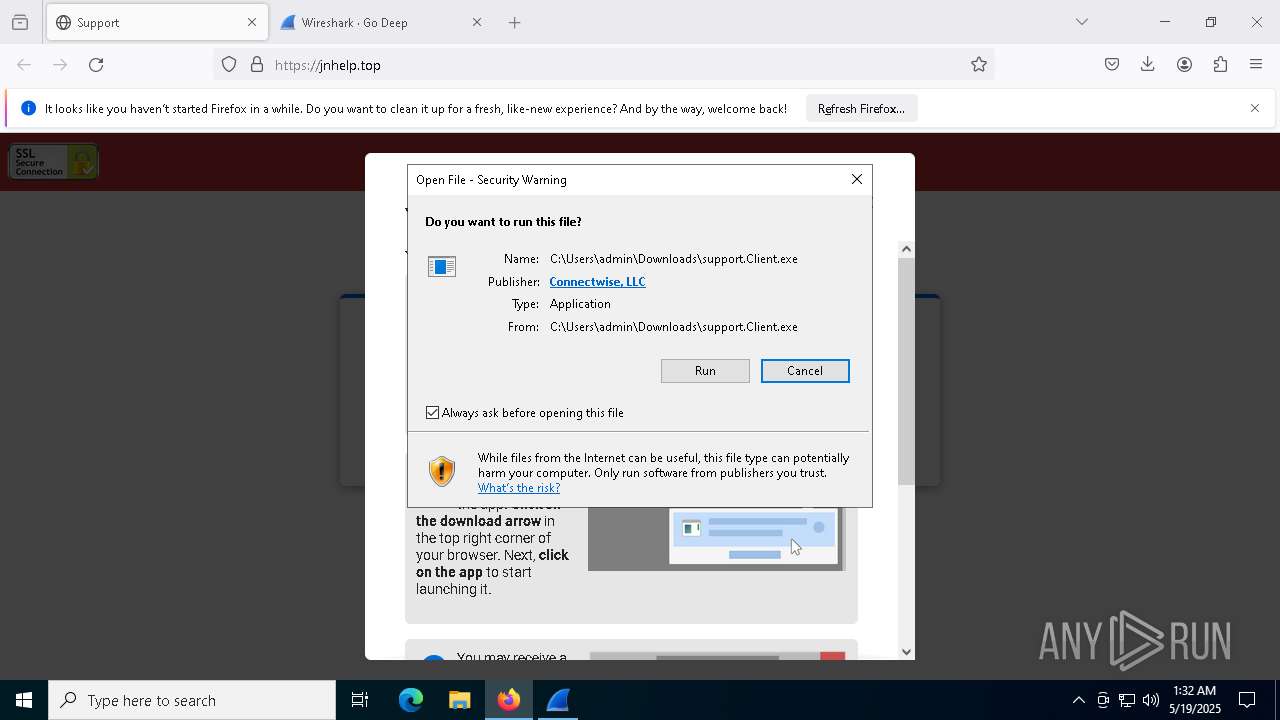
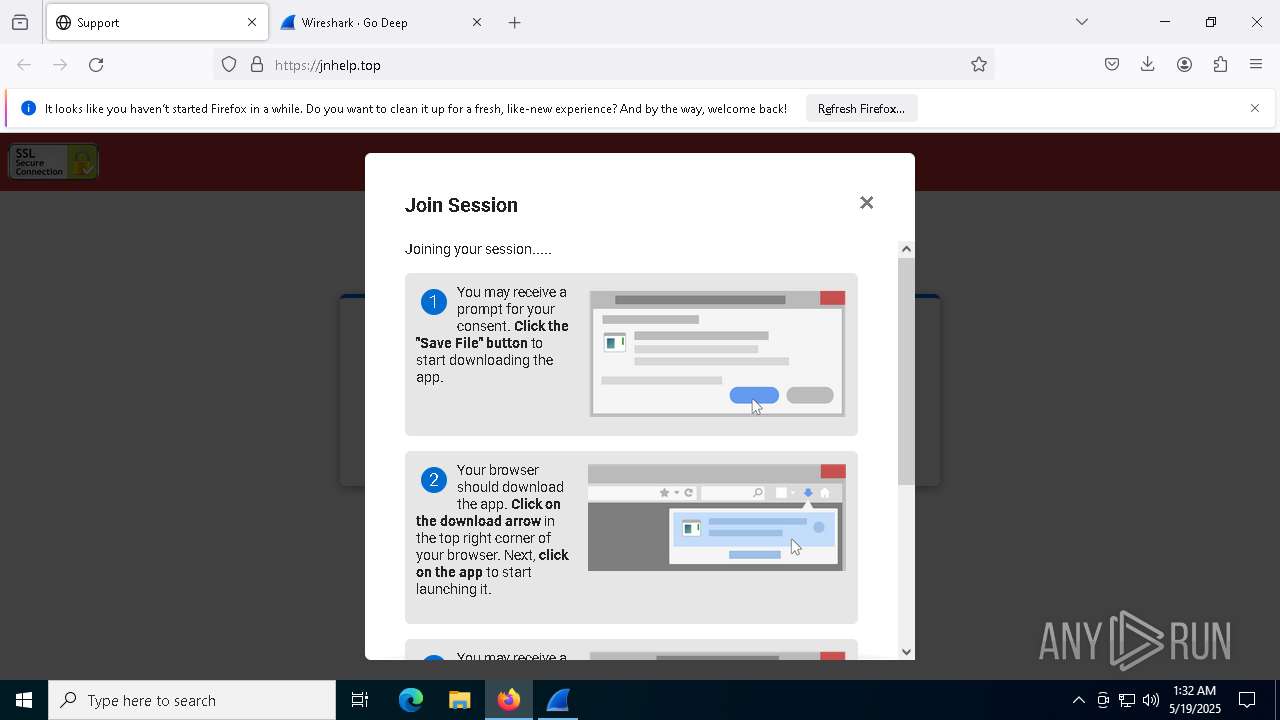
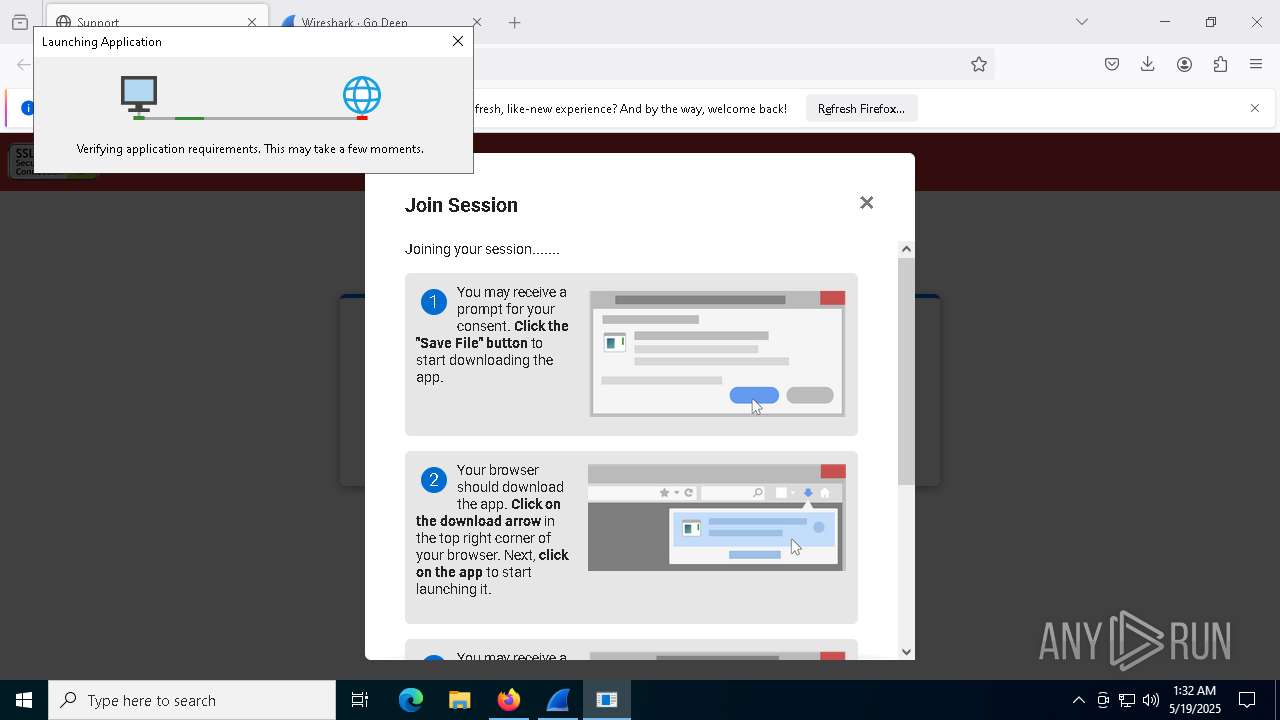
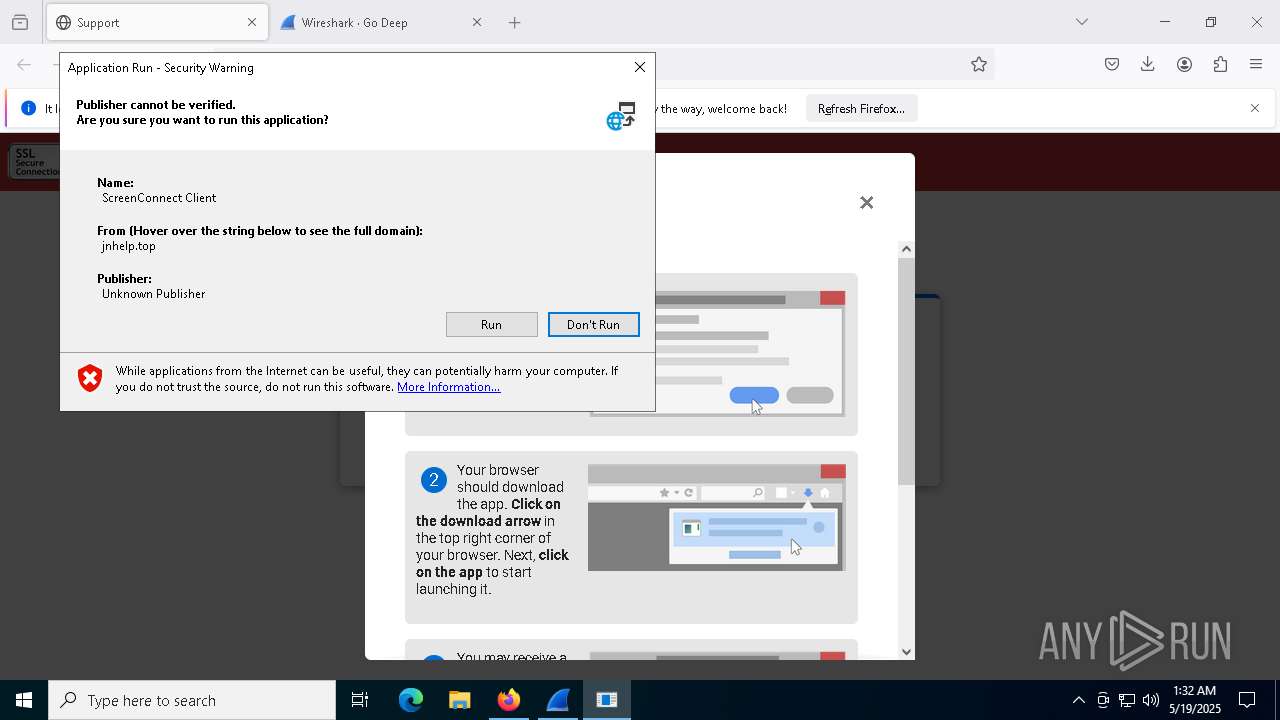
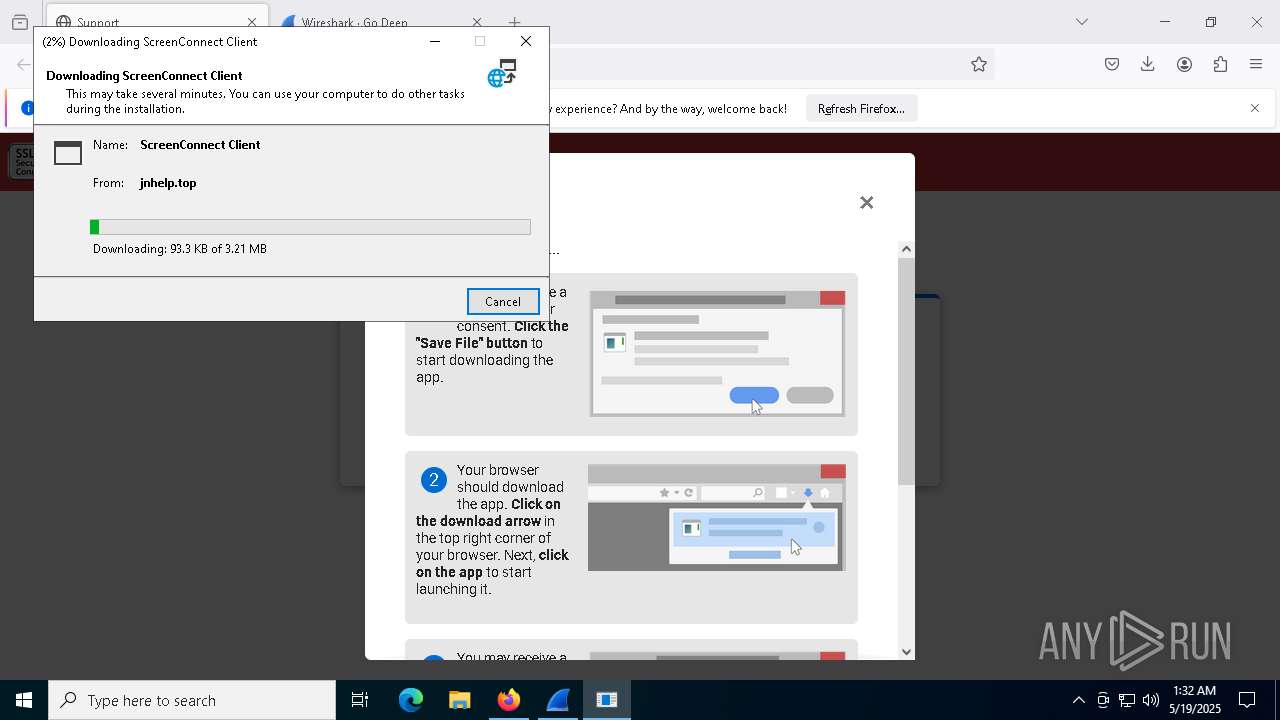
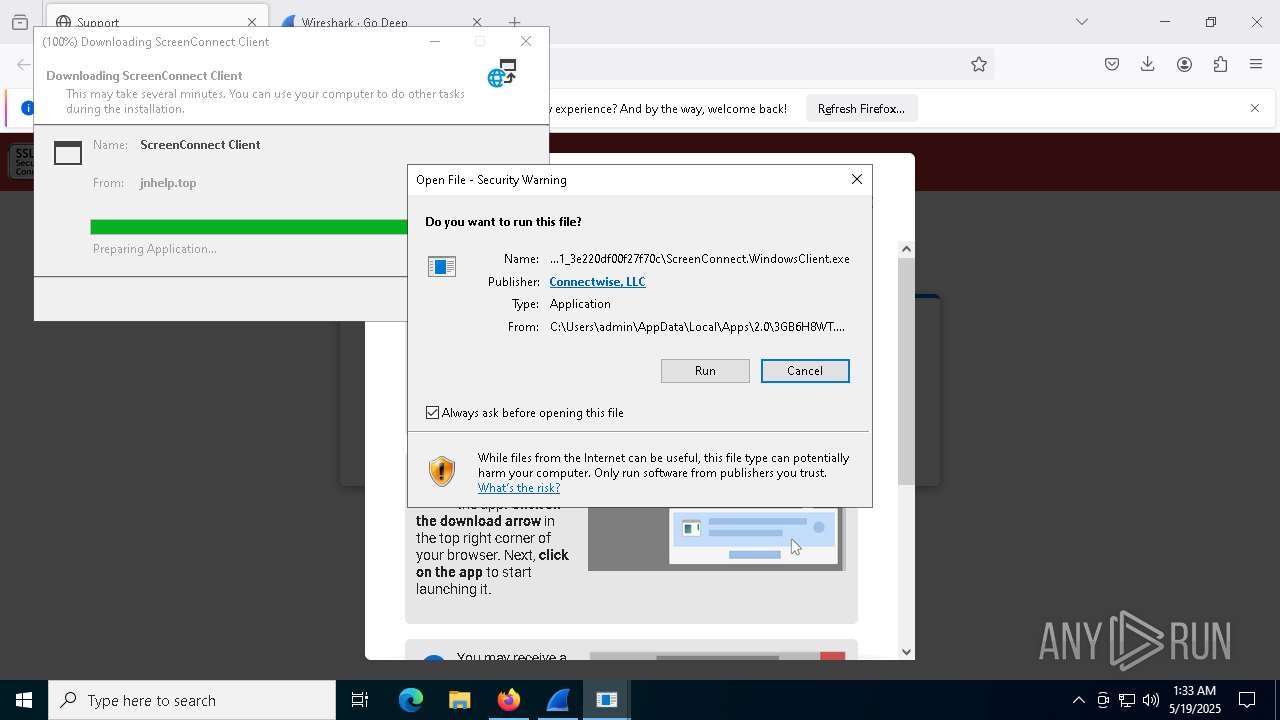
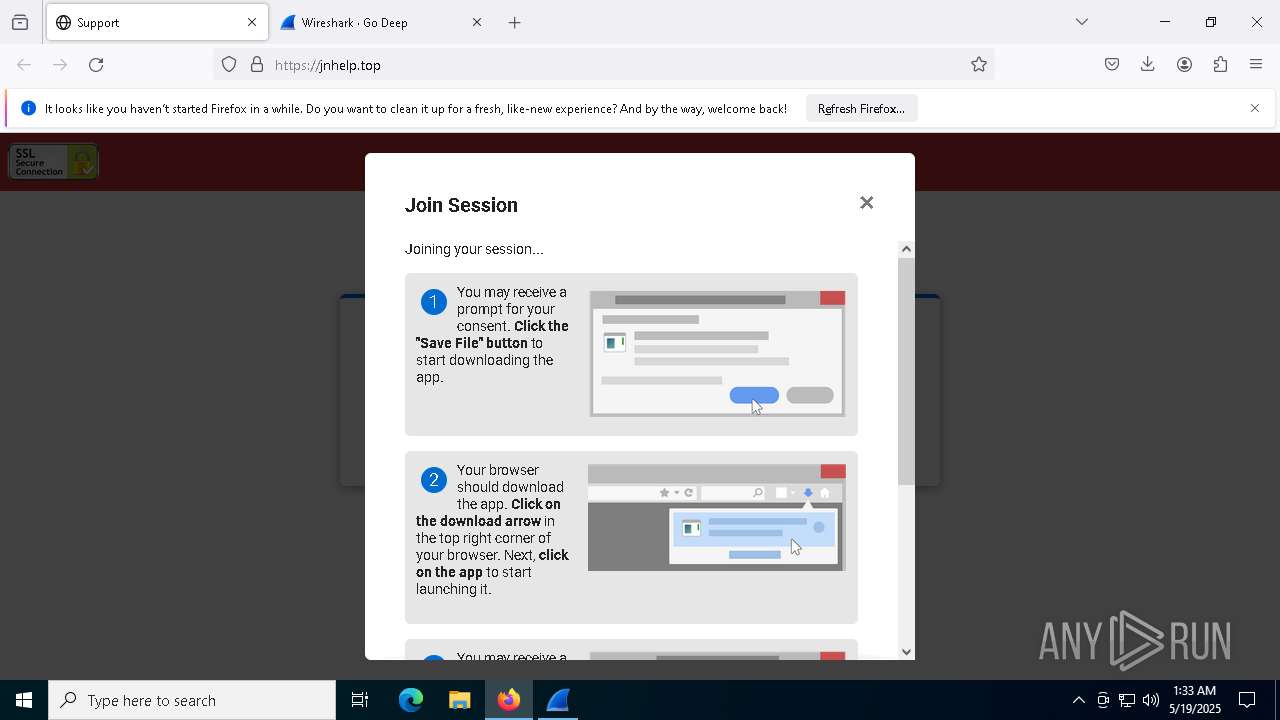
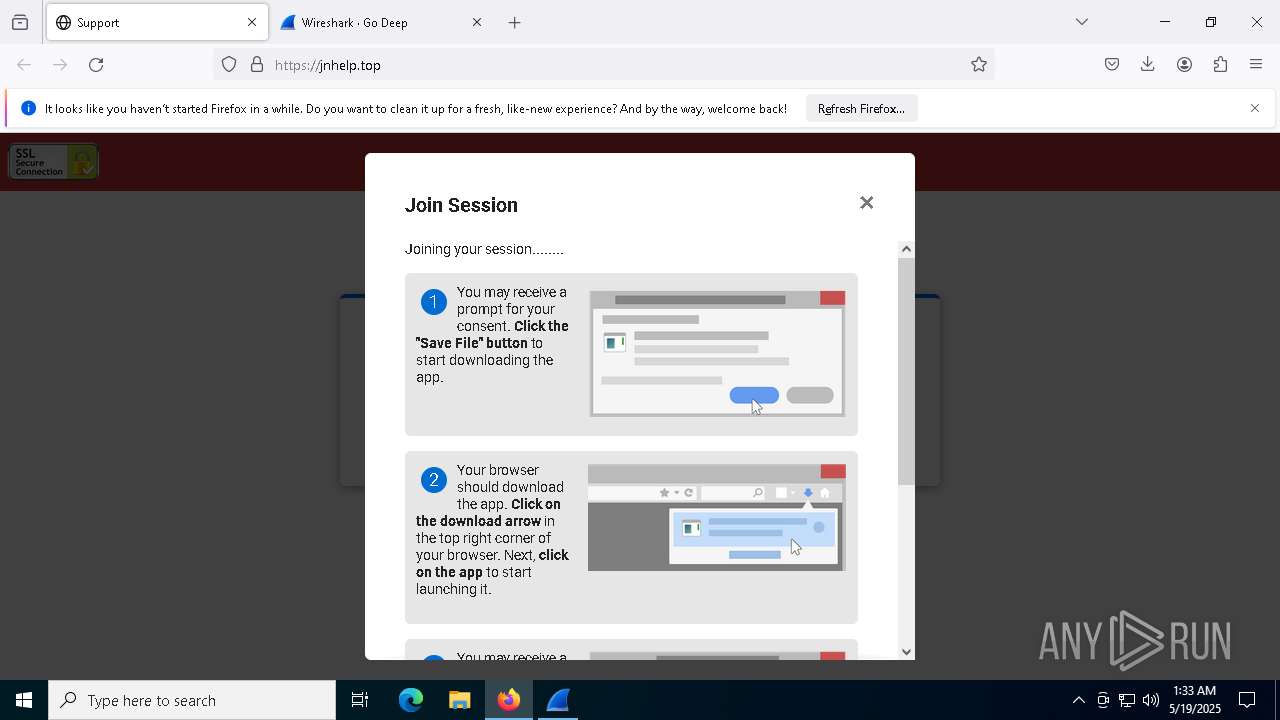
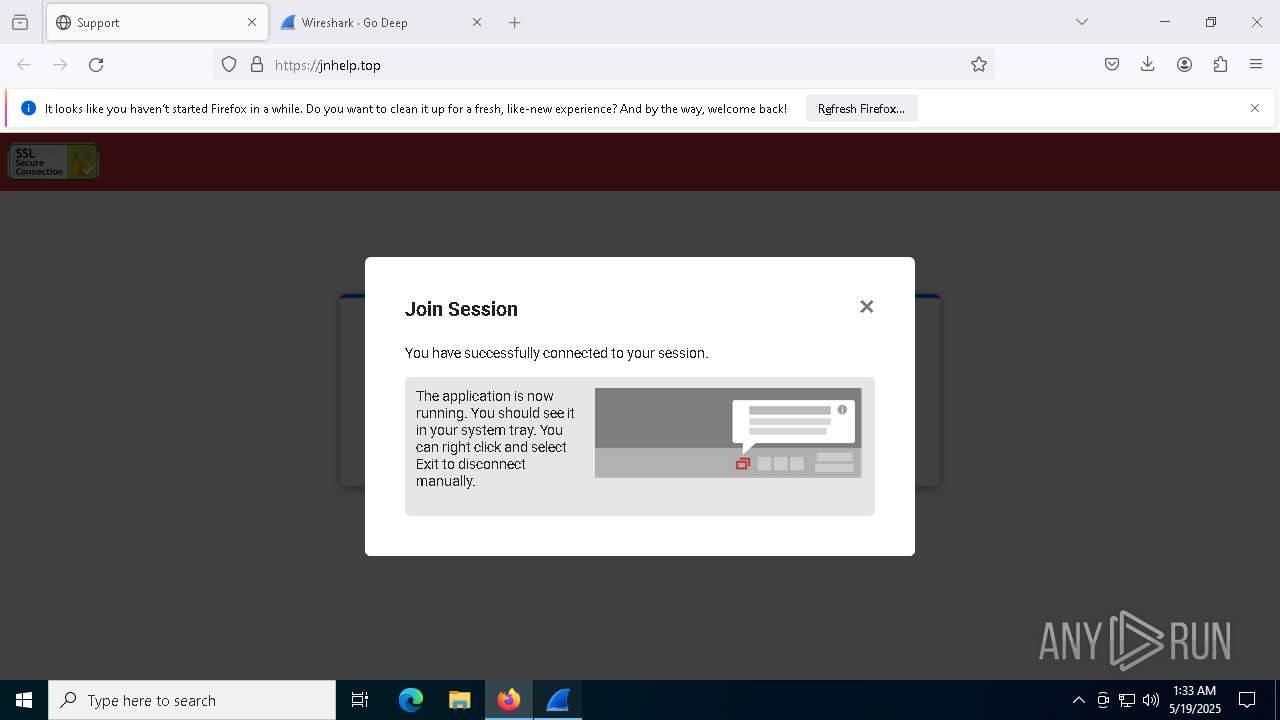
| URL: | jnhelp.top |
| Full analysis: | https://app.any.run/tasks/fa5bf792-e415-4aa4-b52c-a5a4ca48685b |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 01:28:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8E4D69690930B7A7515F905EB88CB274 |
| SHA1: | 3FE62DD7DF8B91957DA58B62D4AB0C6C657A9961 |
| SHA256: | E1EA6E876D46A571D1BC8B2A40B966F5786470AF761519409D9D4E414BD92C26 |
| SSDEEP: | 3:OVQV:Ou |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 736)
- powershell.exe (PID: 8732)
- powershell.exe (PID: 7148)
- powershell.exe (PID: 9164)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 8772)
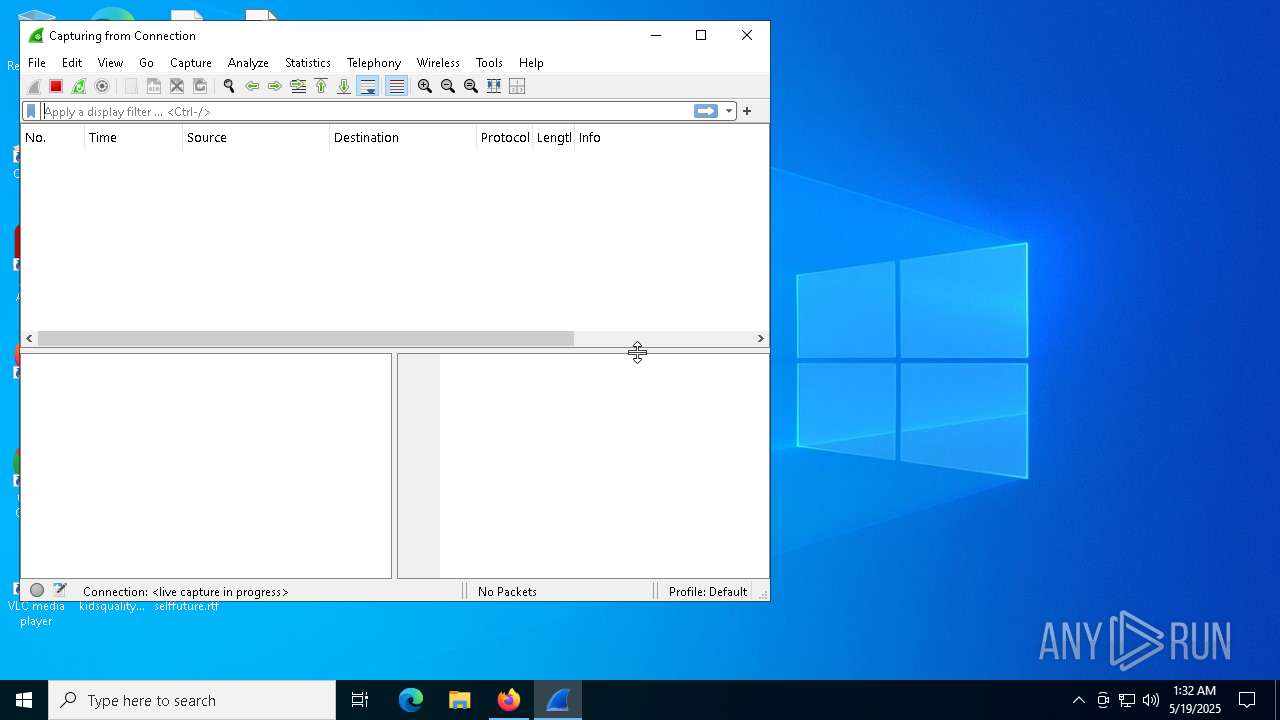
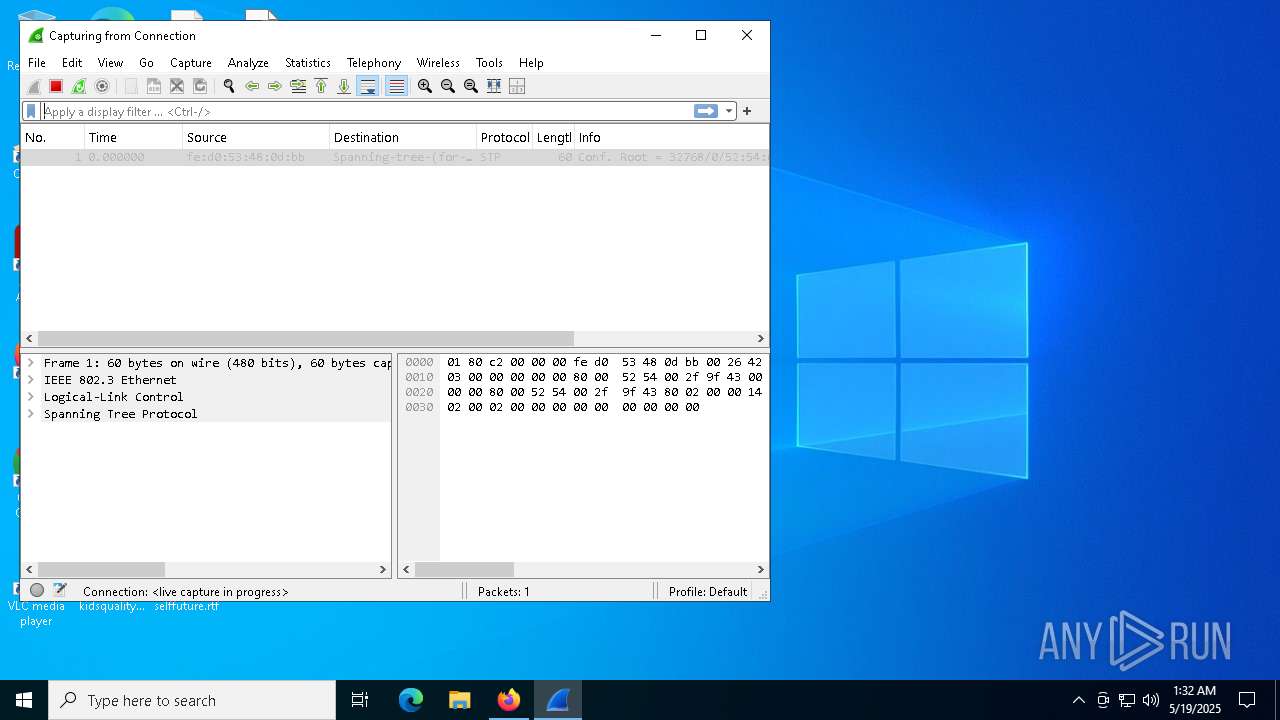
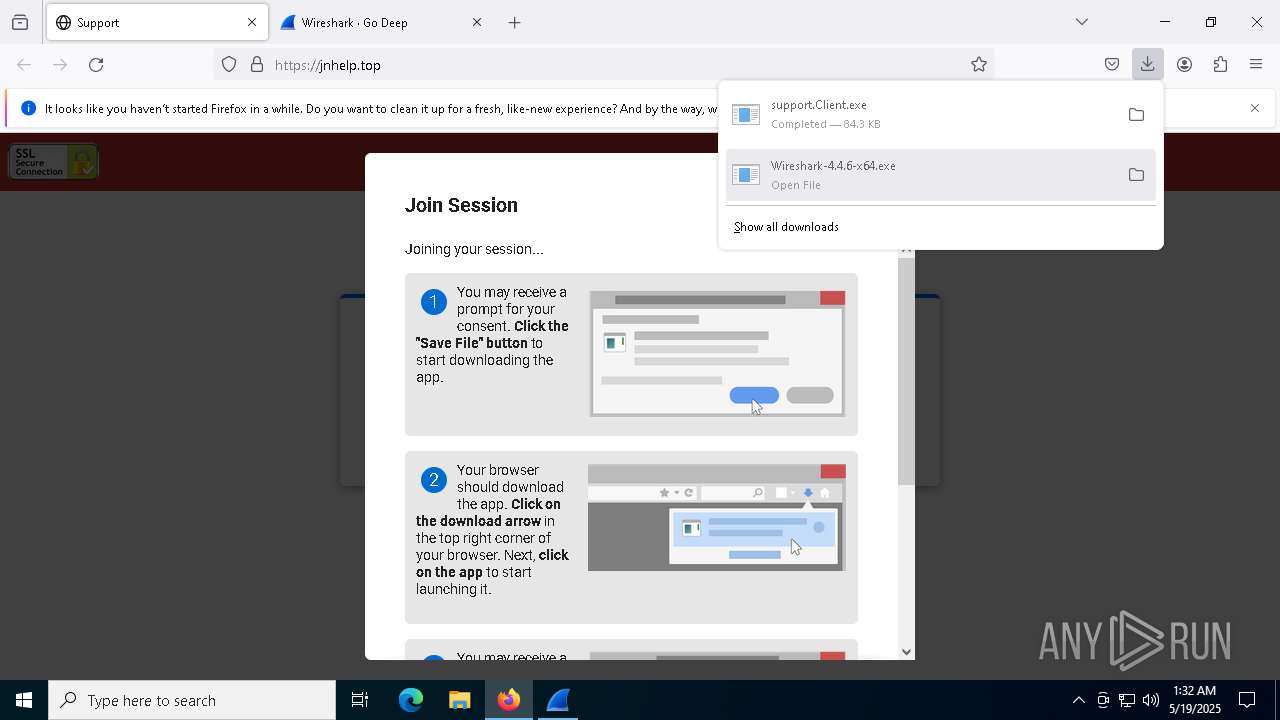
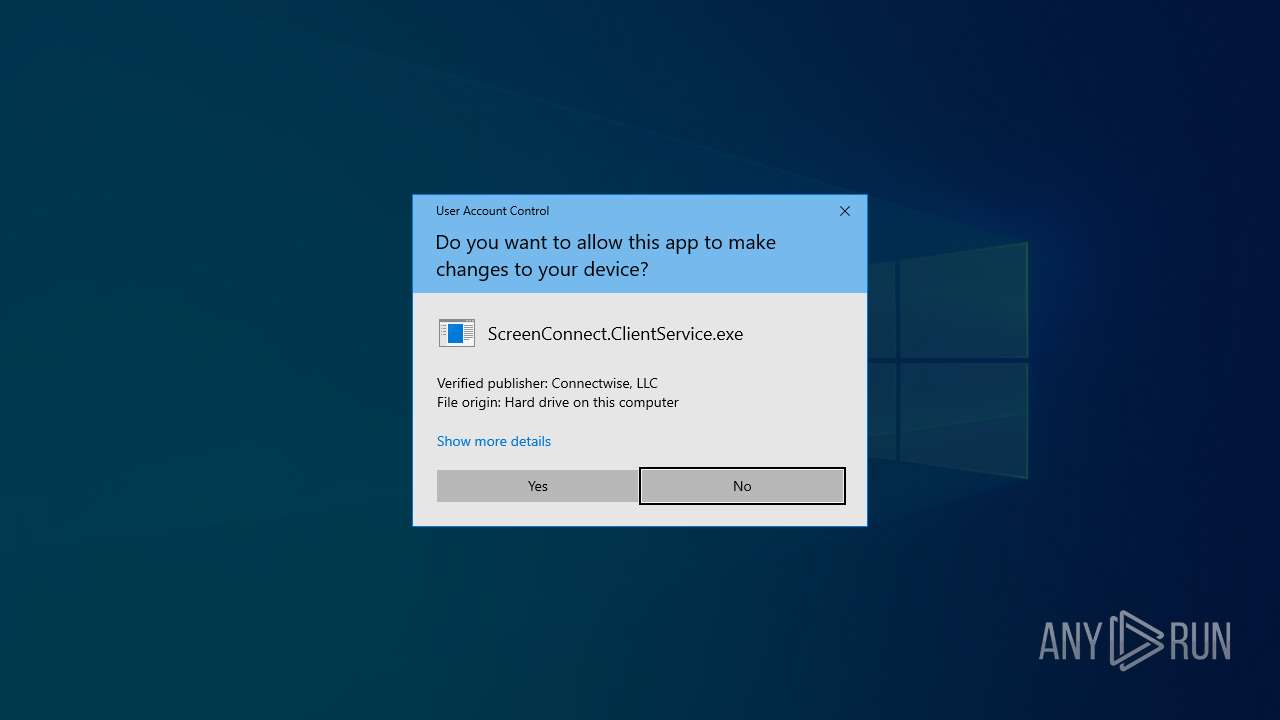
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 4572)
SUSPICIOUS
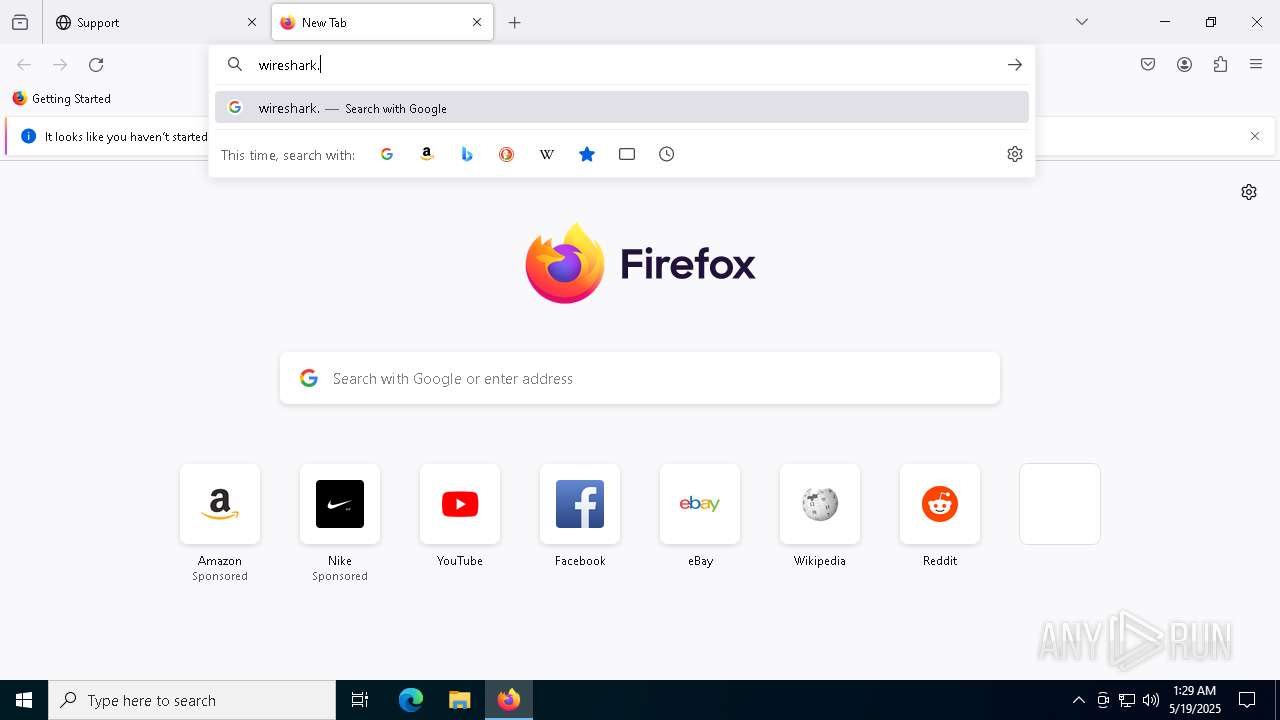
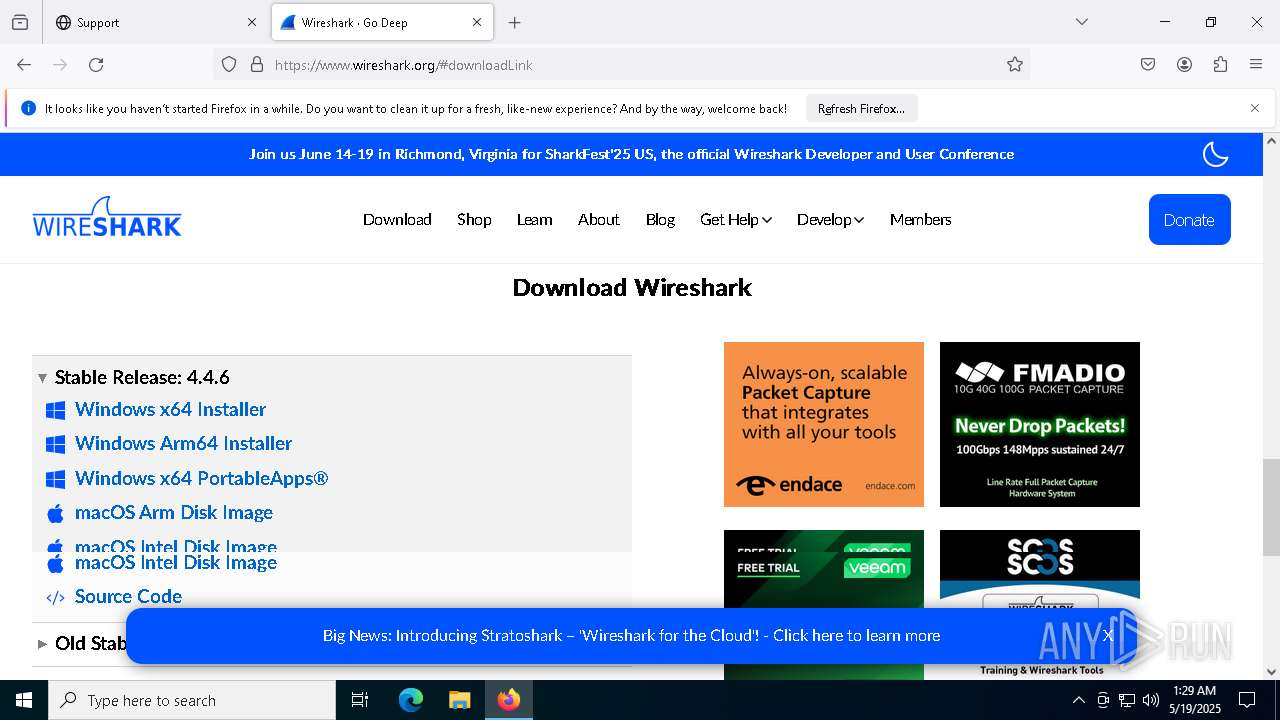
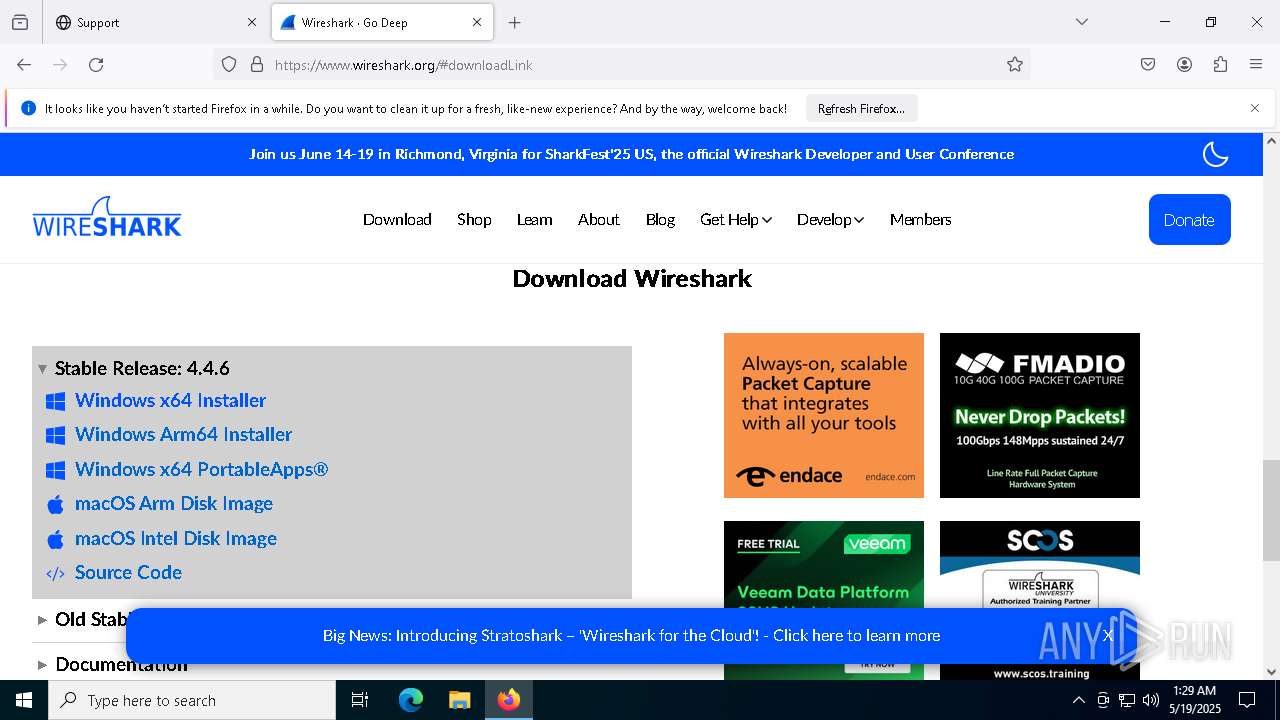
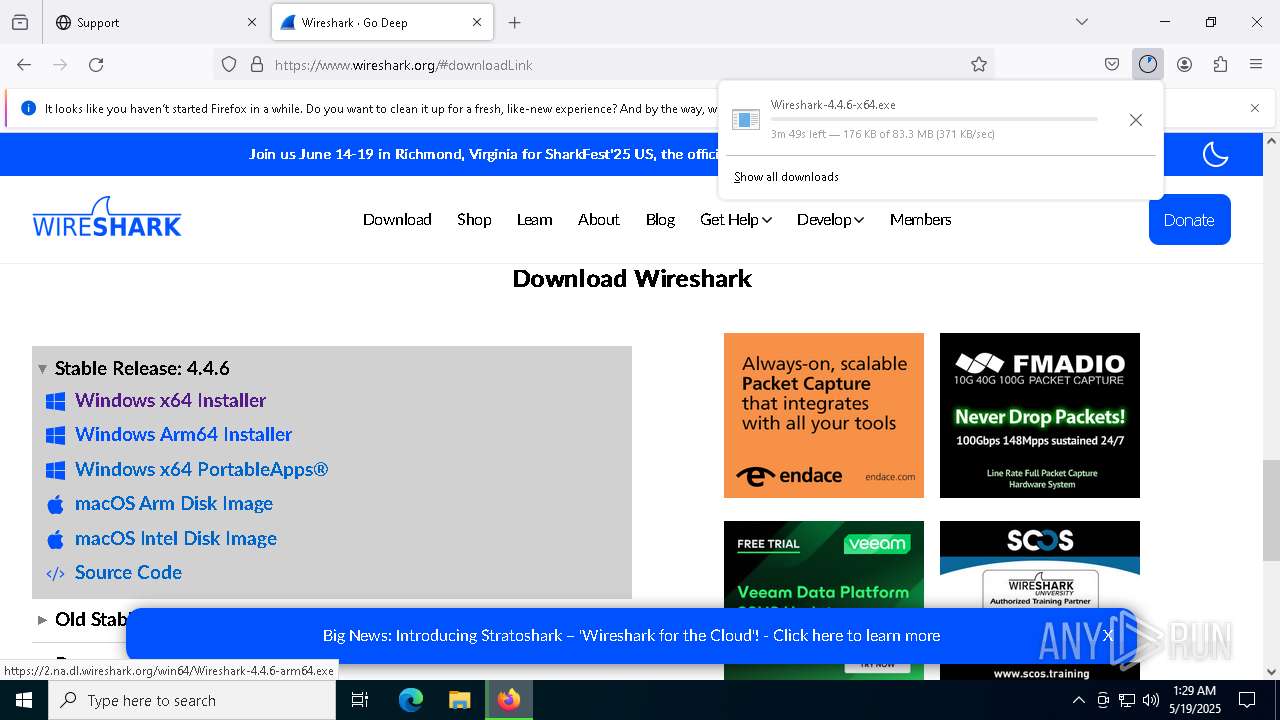
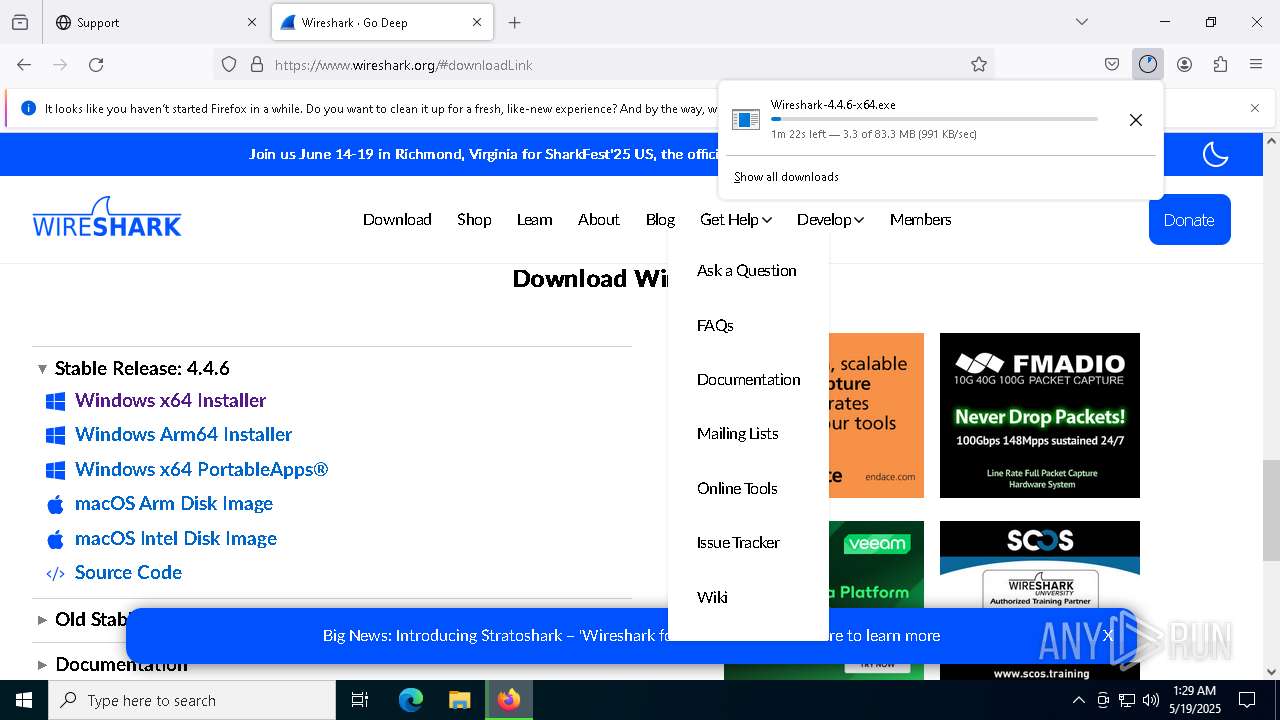
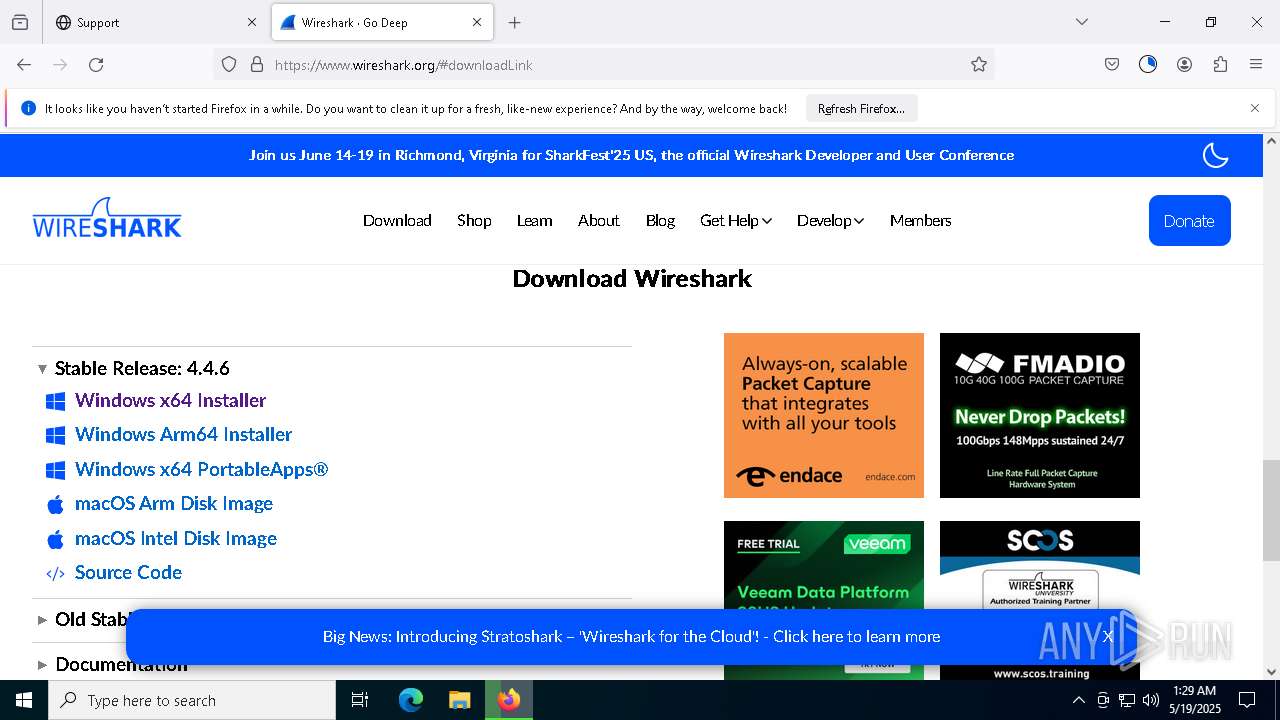
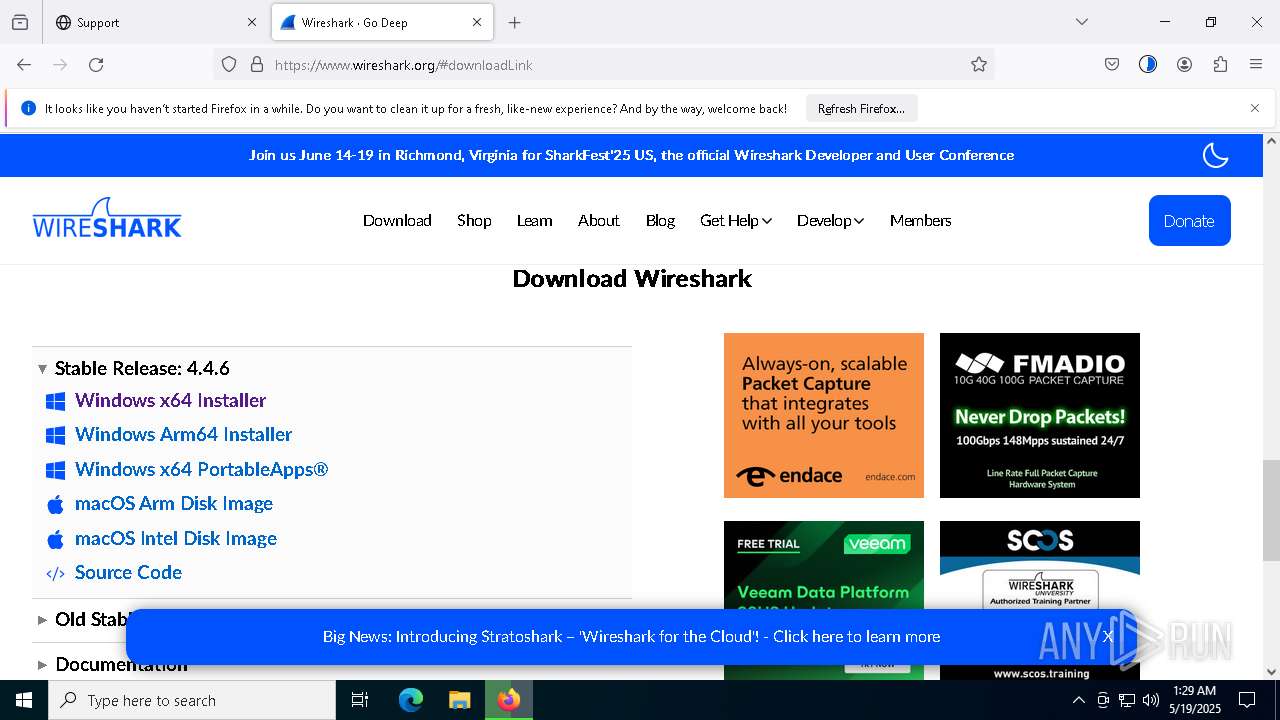
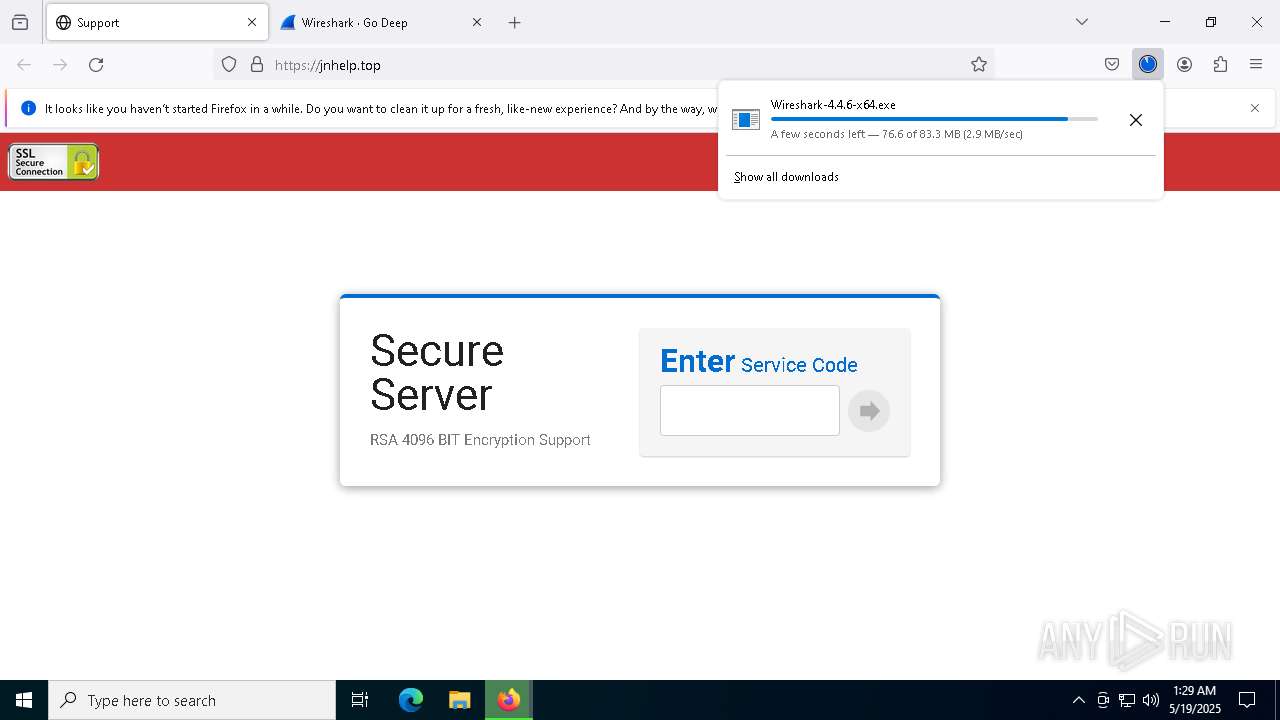
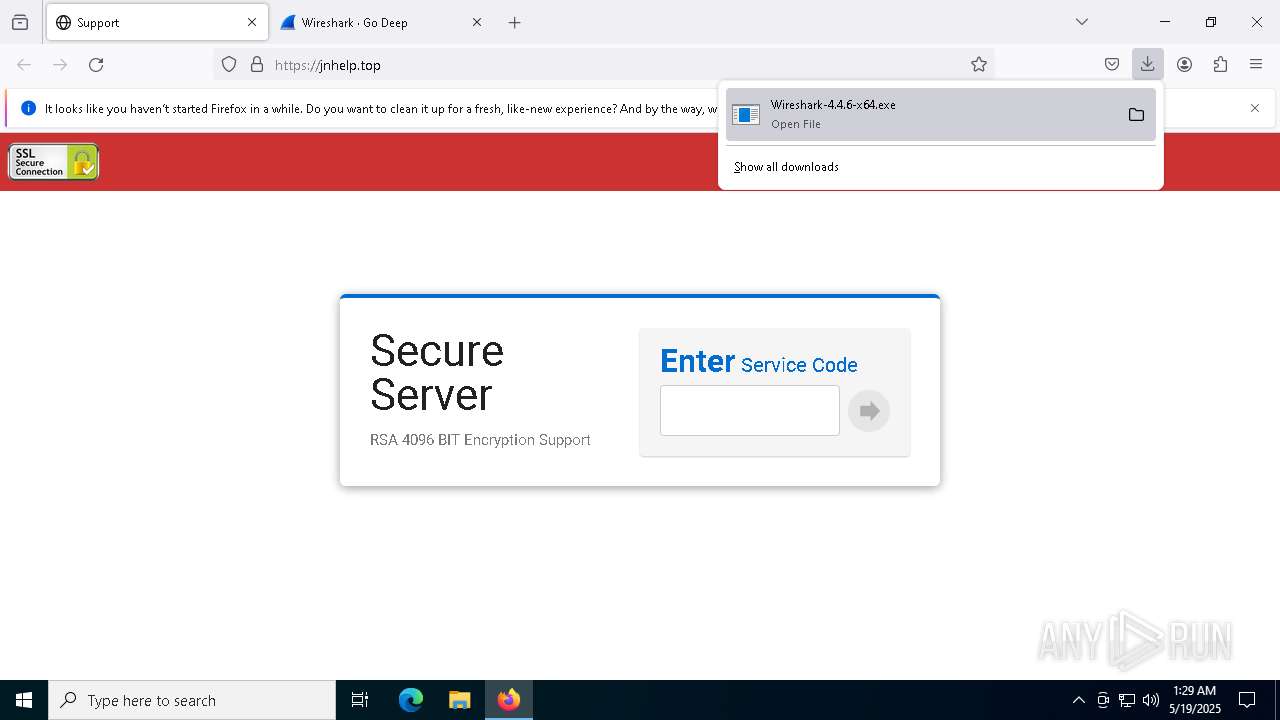
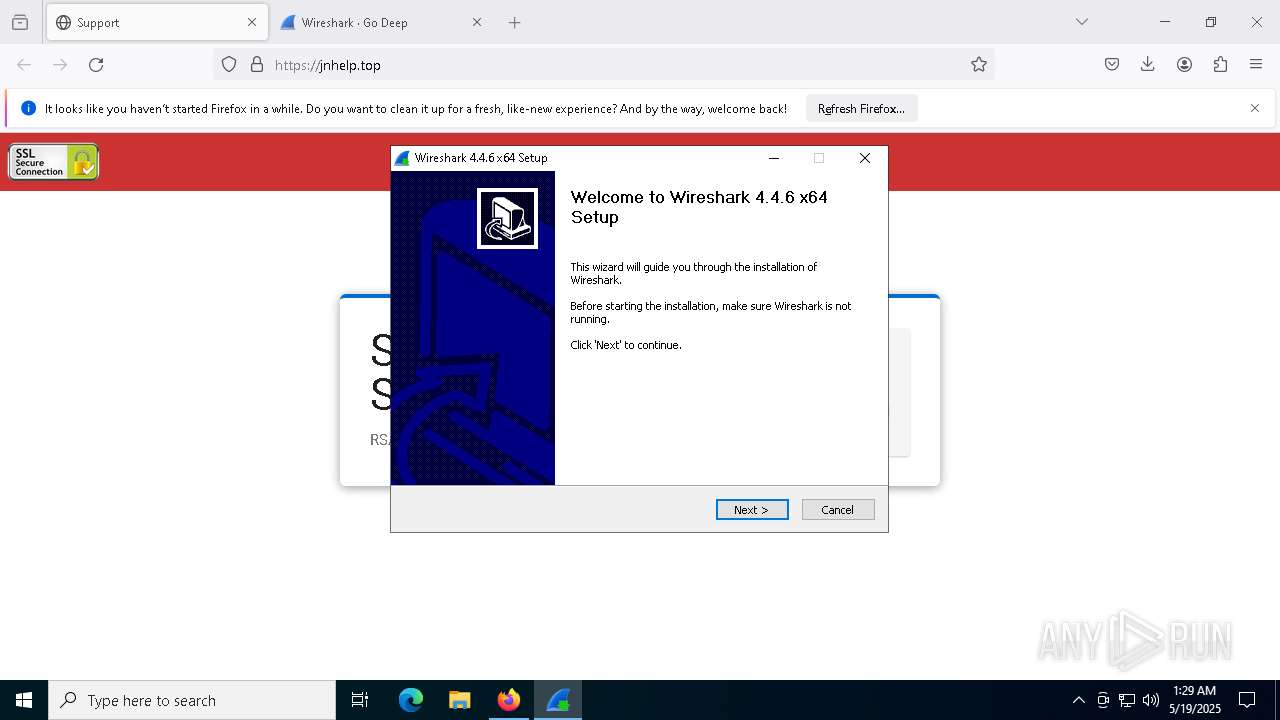
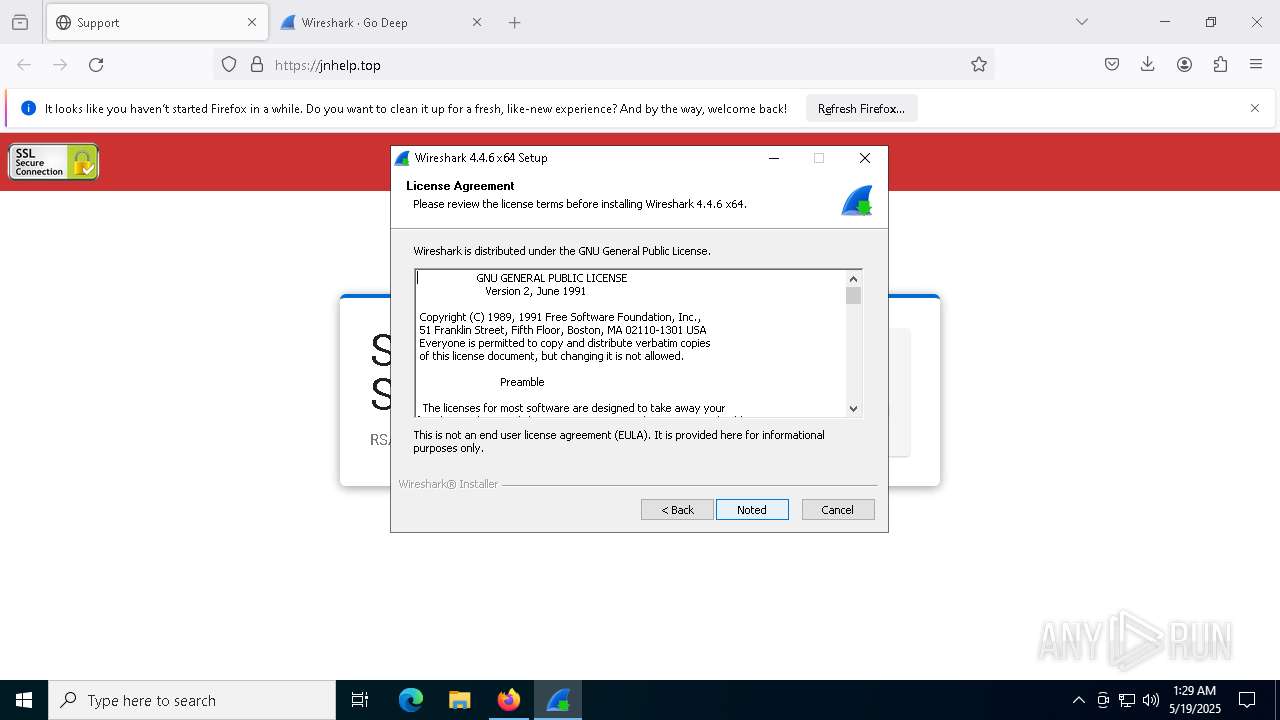
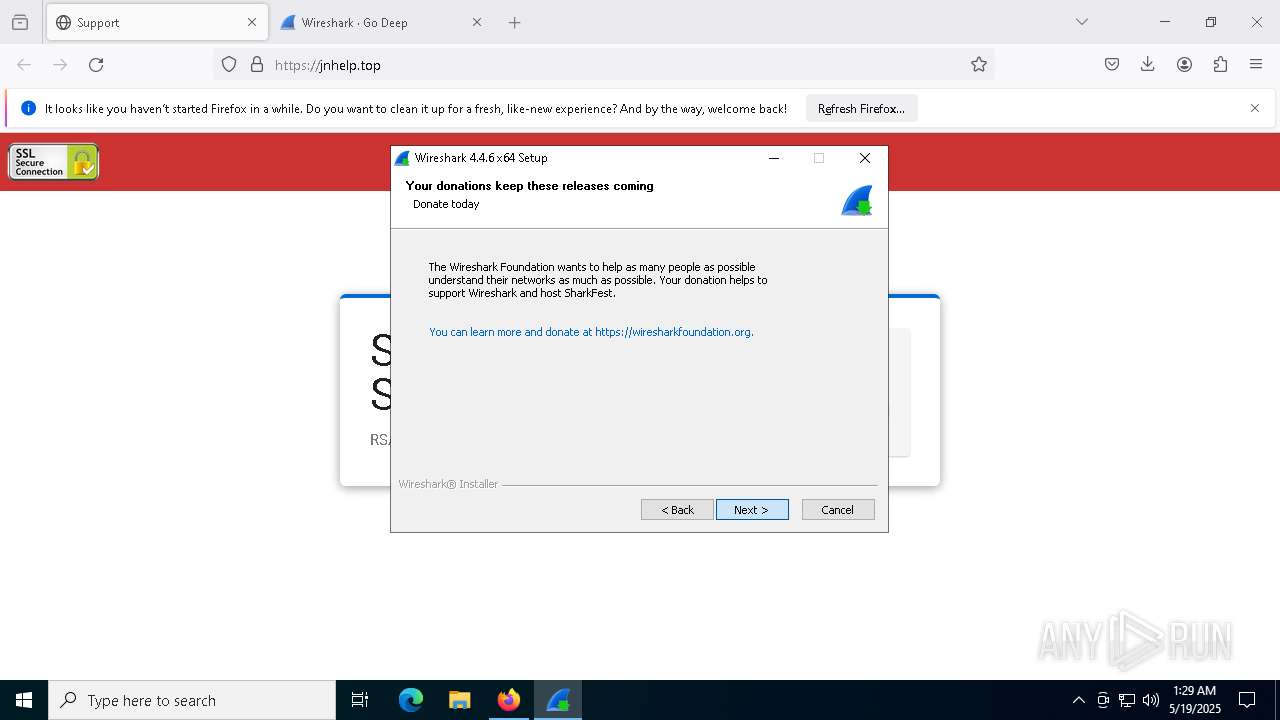
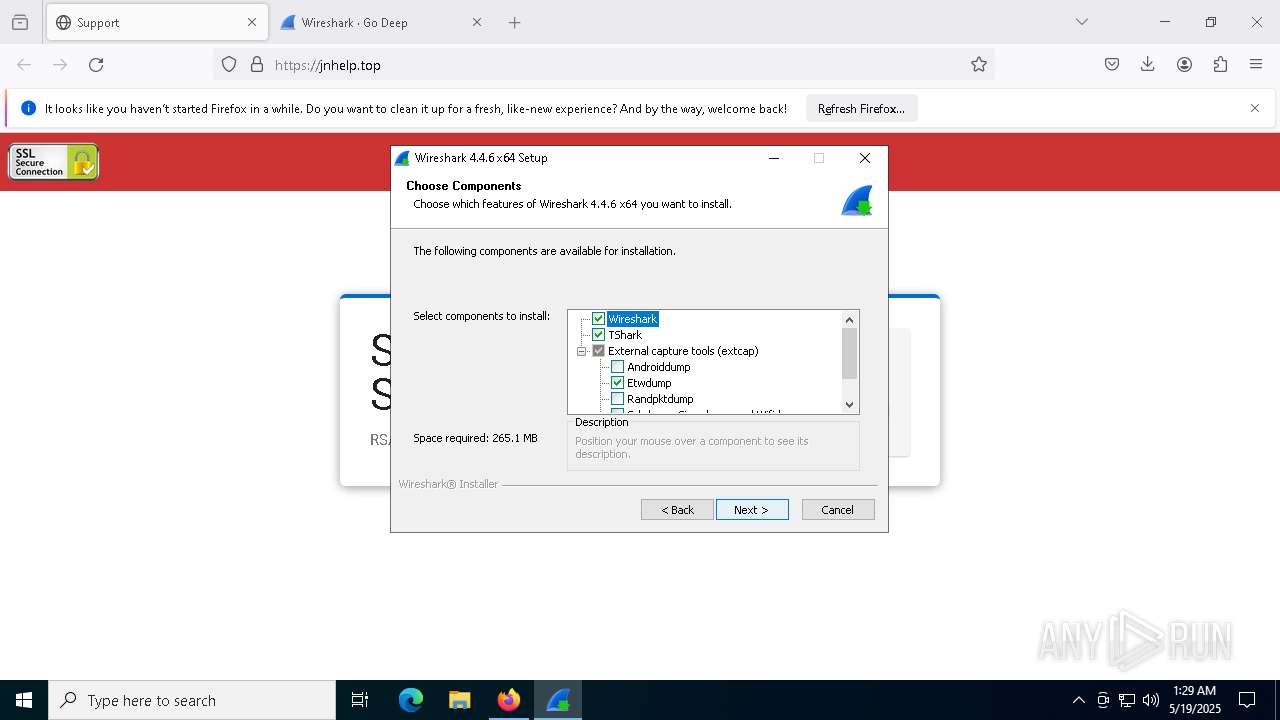
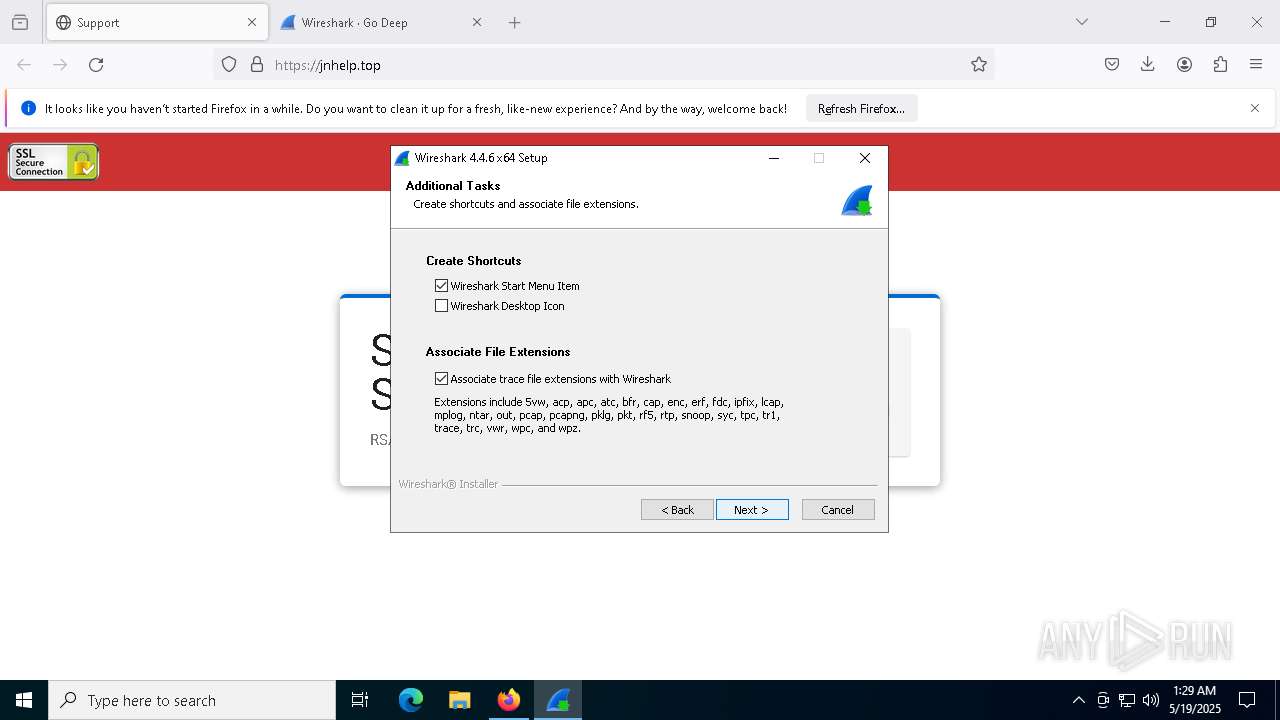
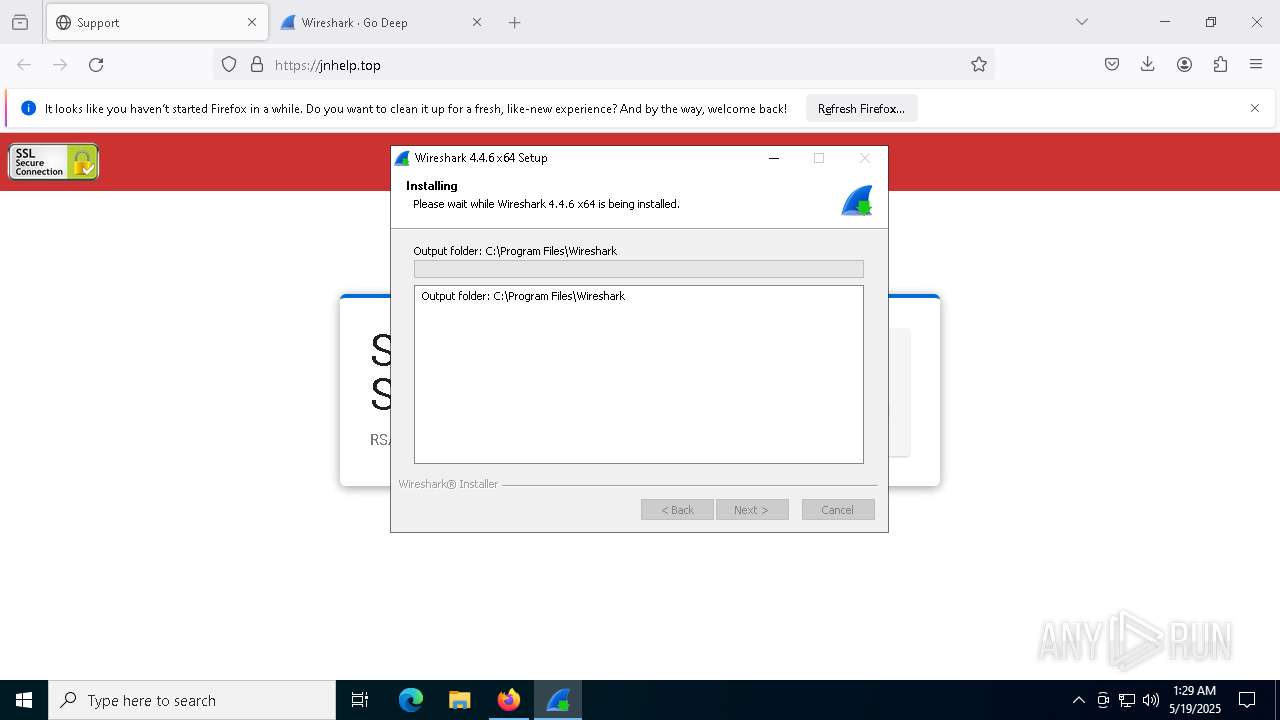
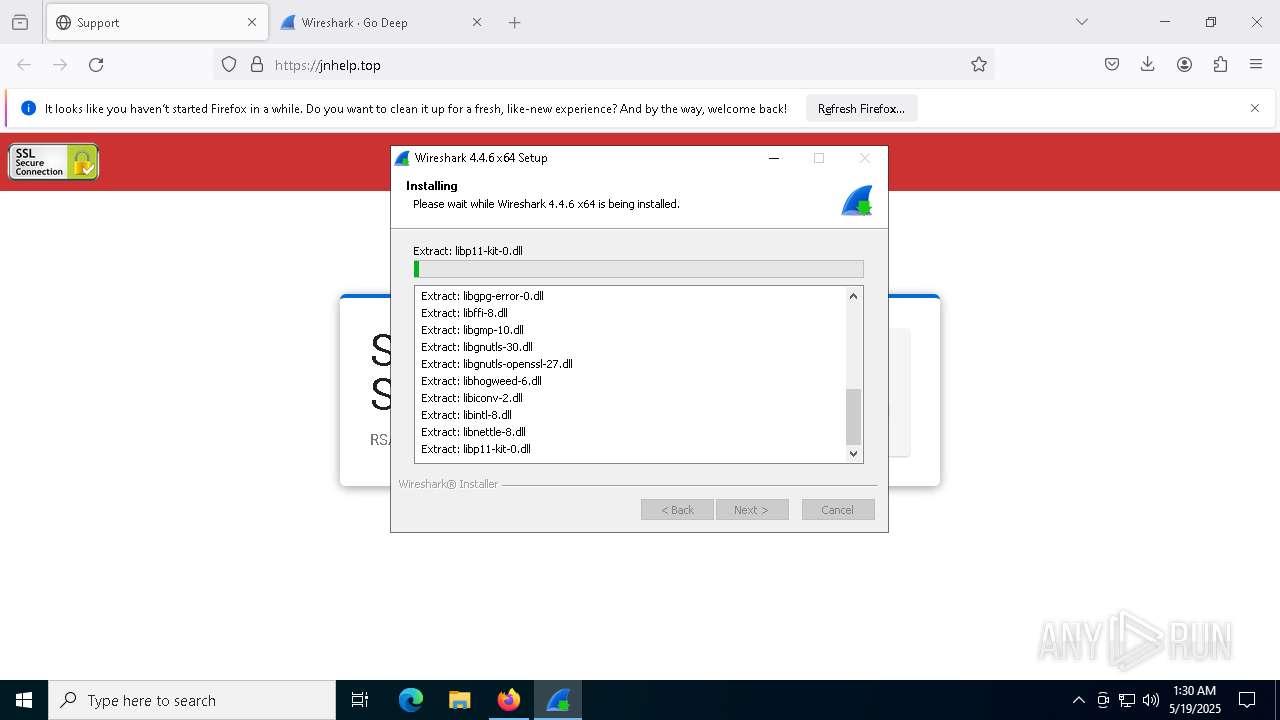
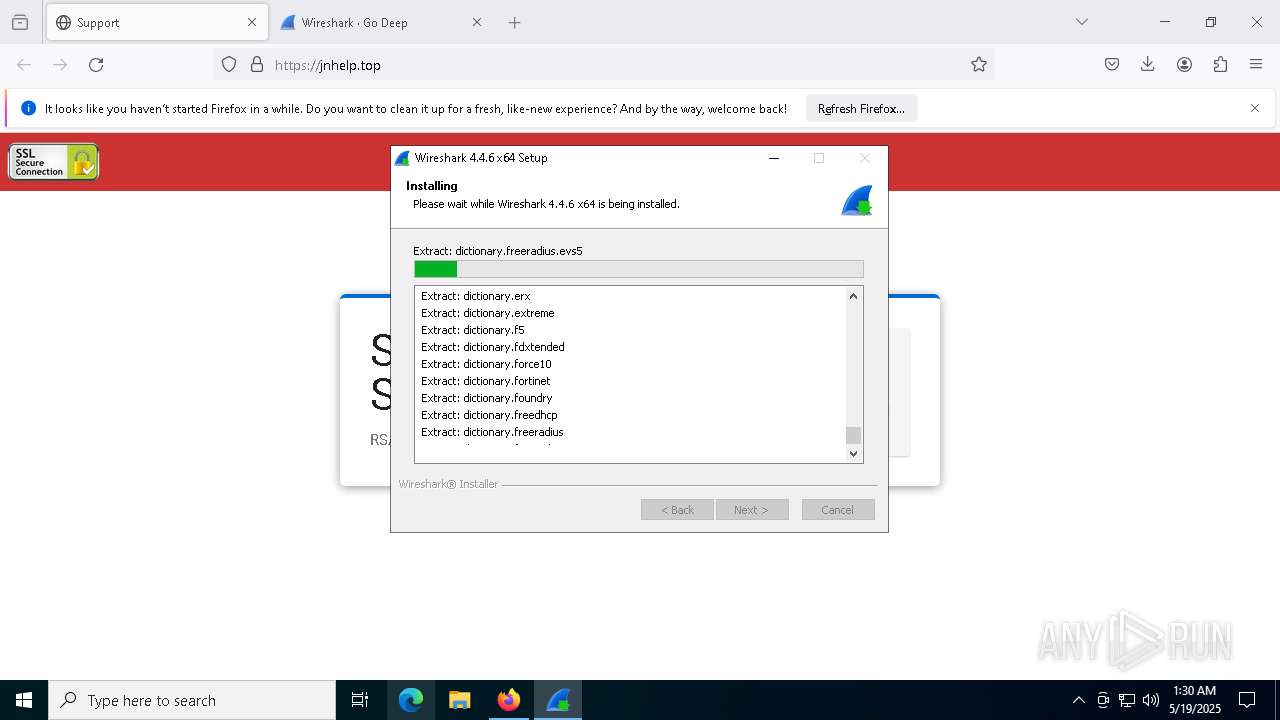
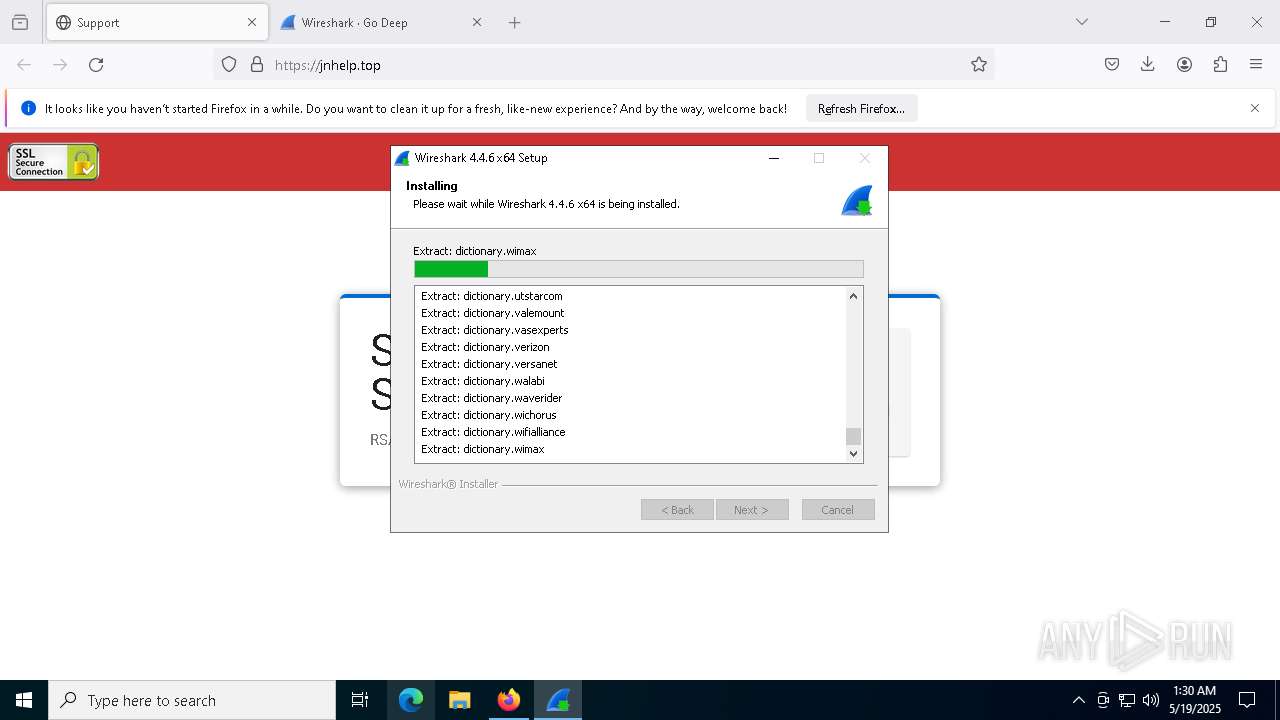
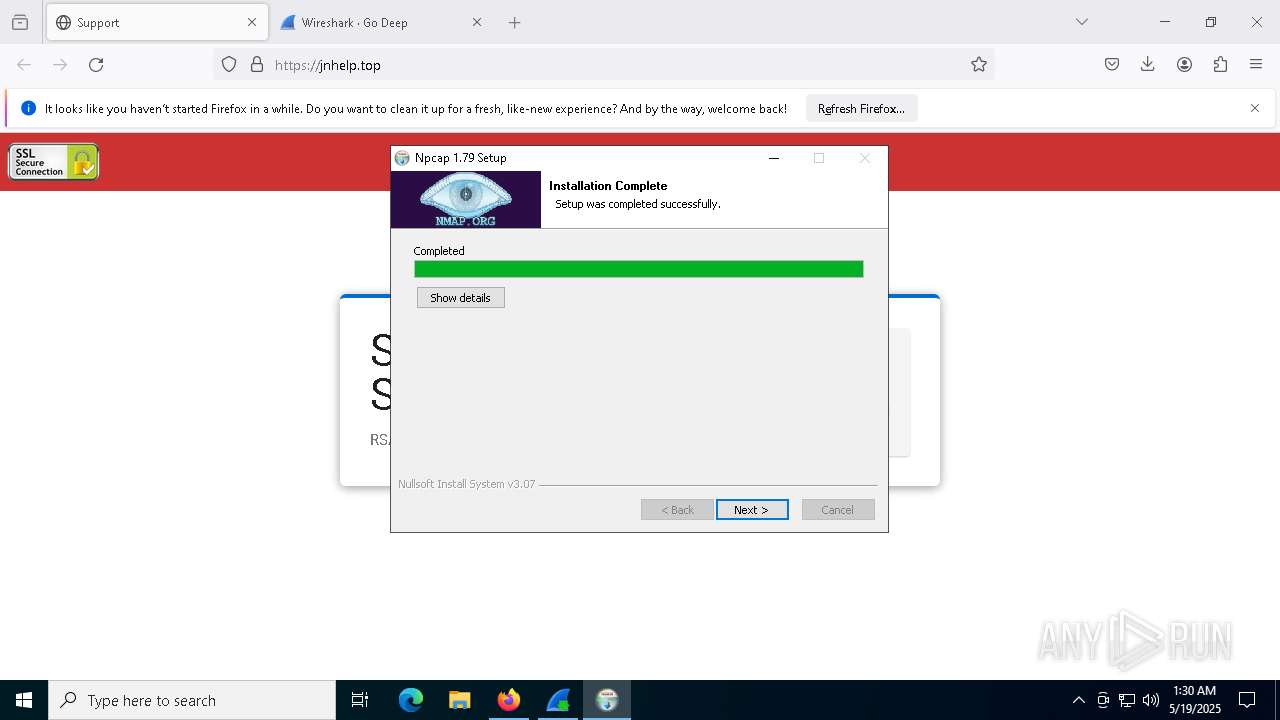
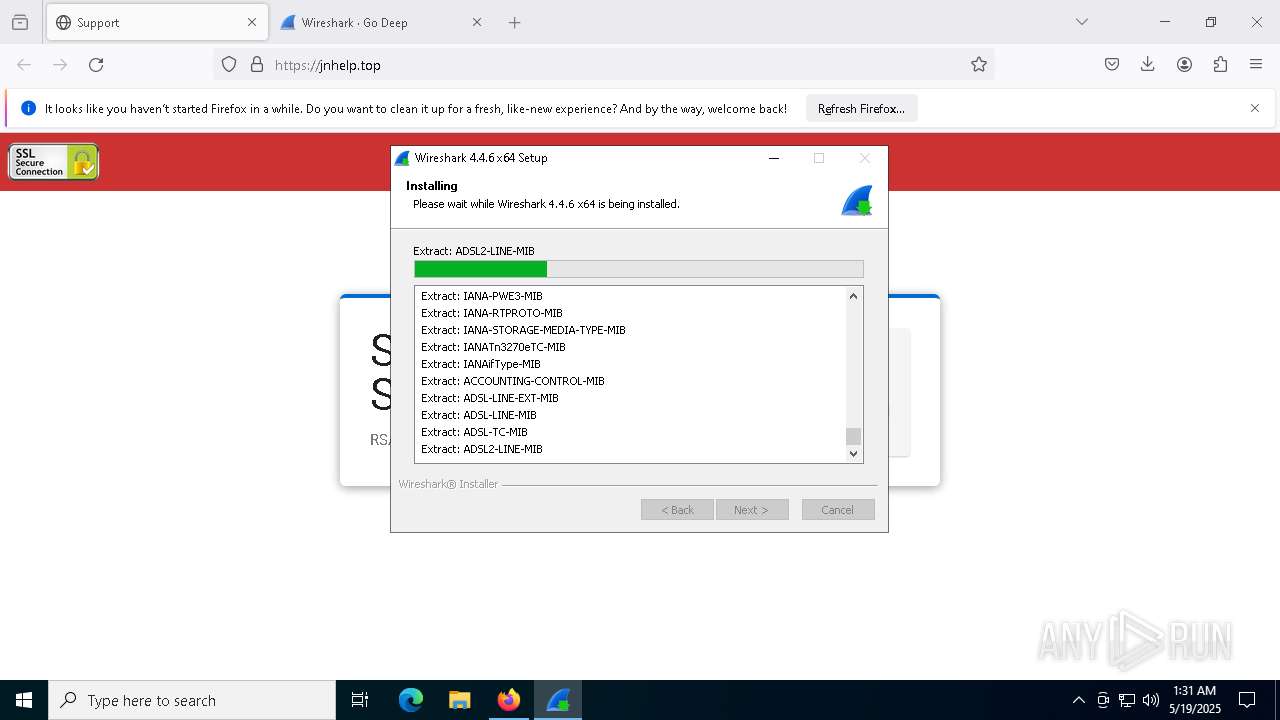
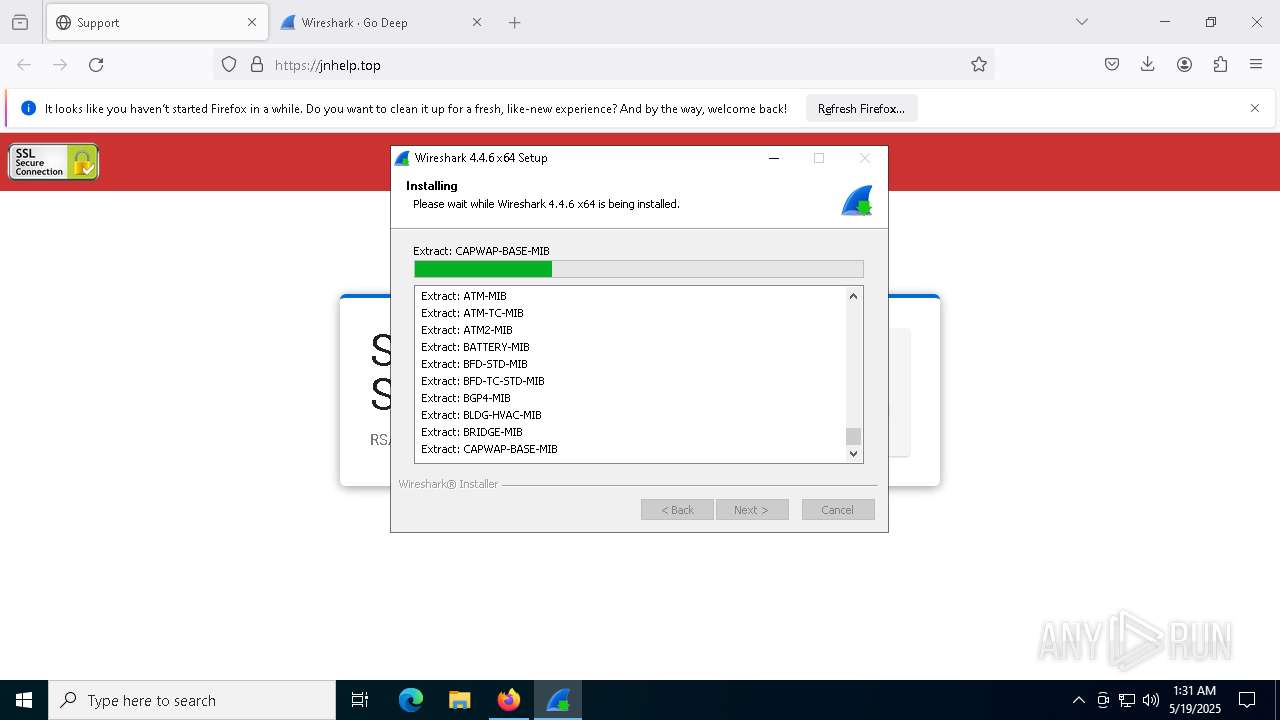
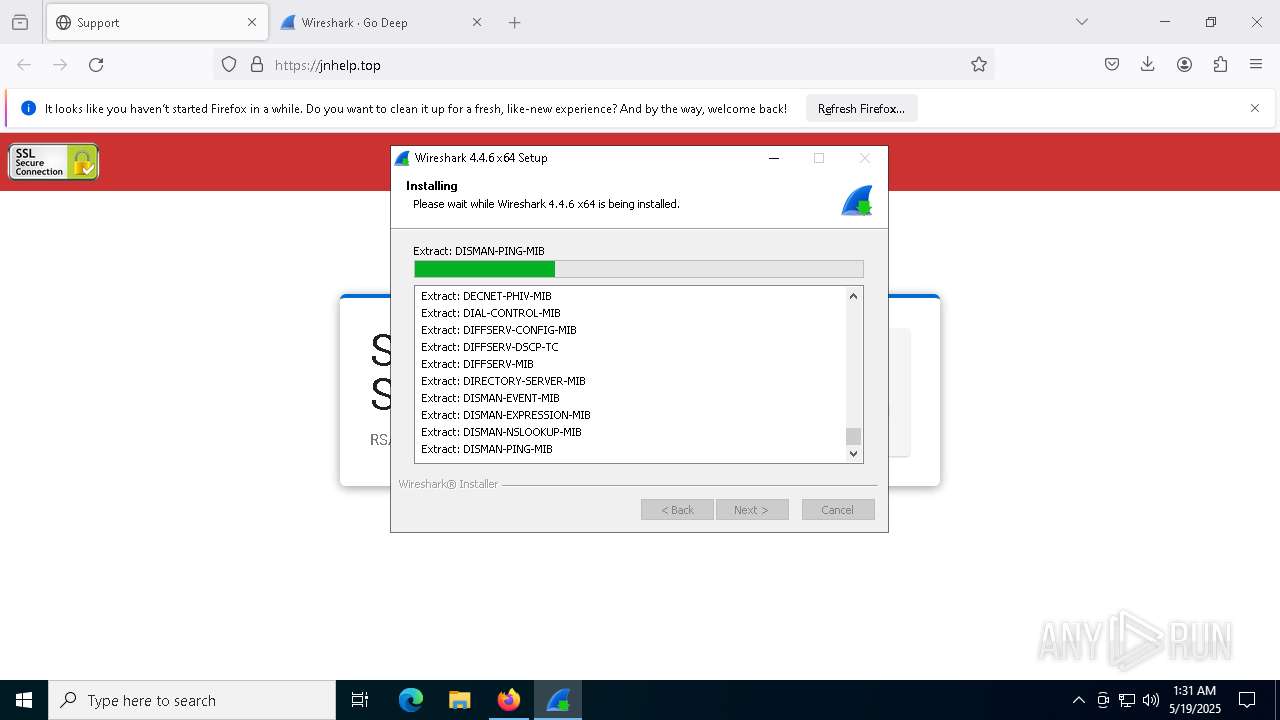
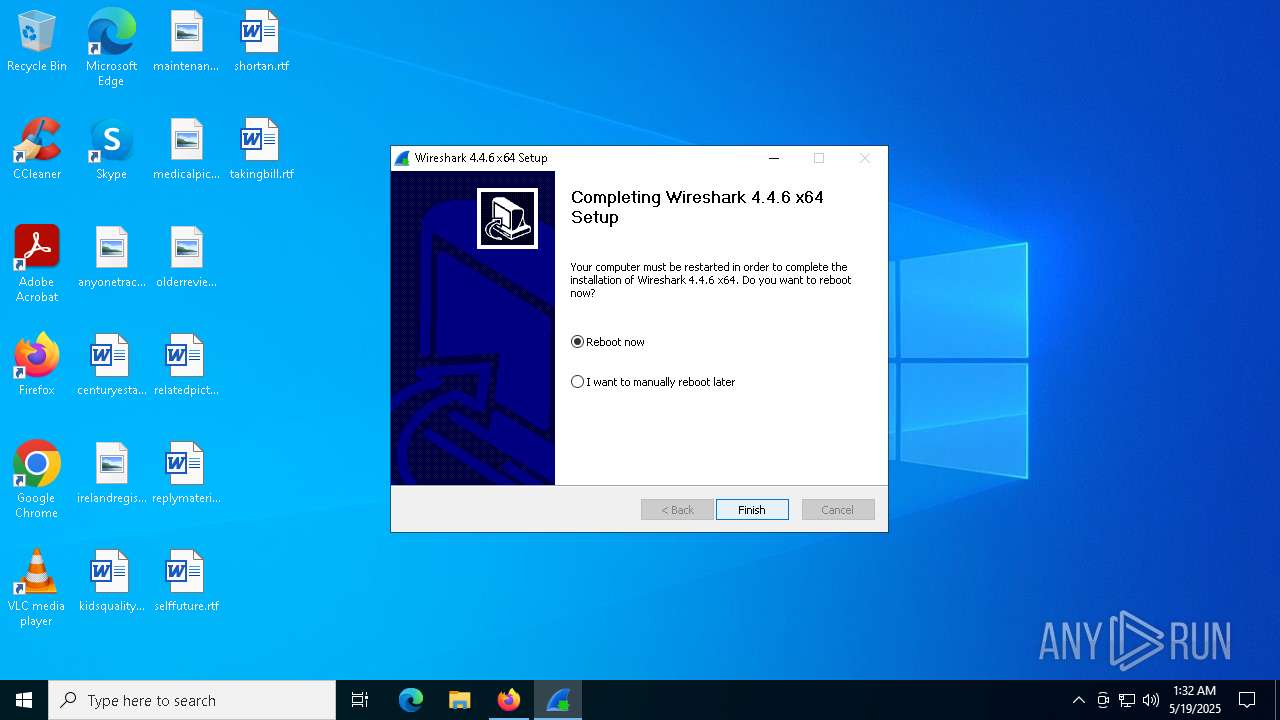
Malware-specific behavior (creating "System.dll" in Temp)
- Wireshark-4.4.6-x64.exe (PID: 8872)
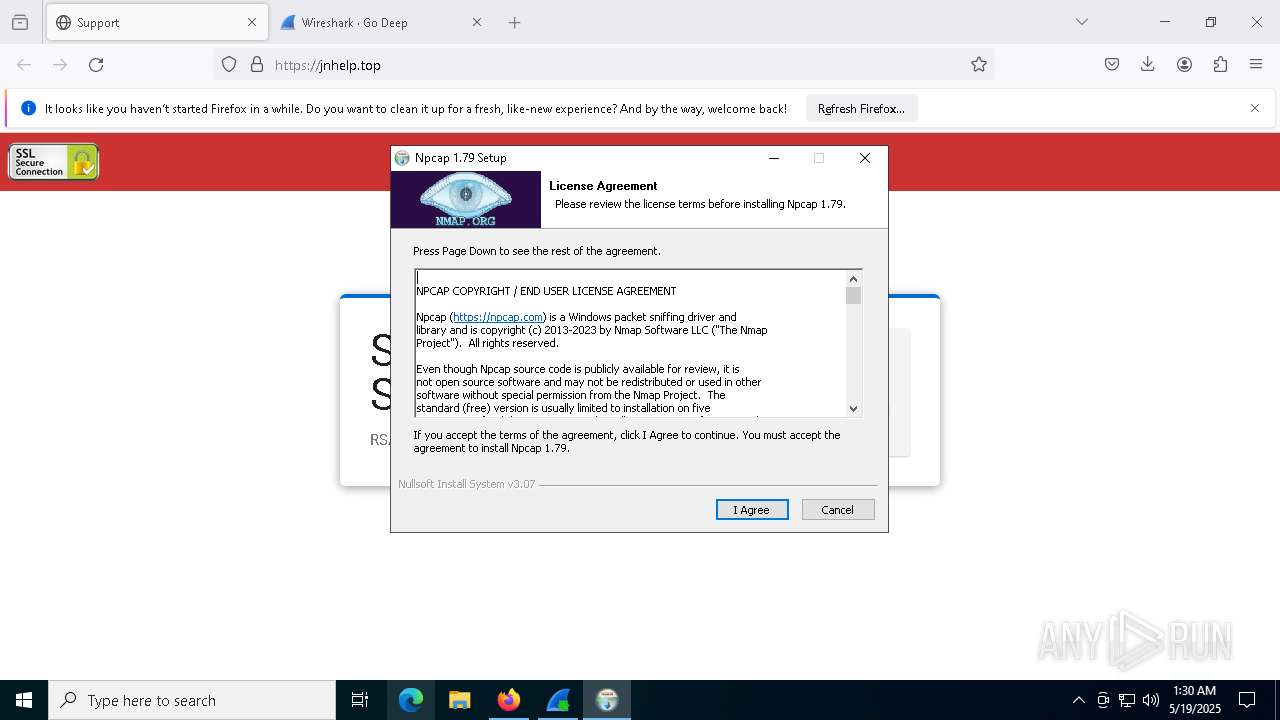
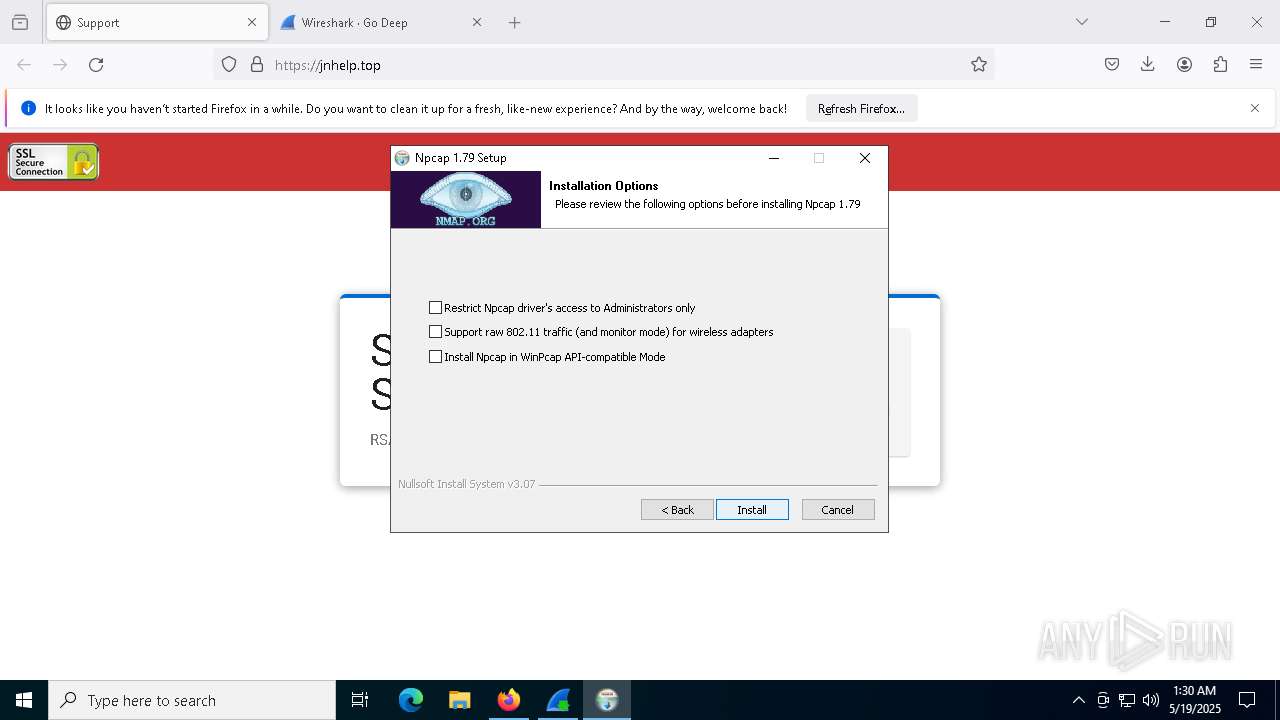
- npcap-1.79.exe (PID: 7676)
The process creates files with name similar to system file names
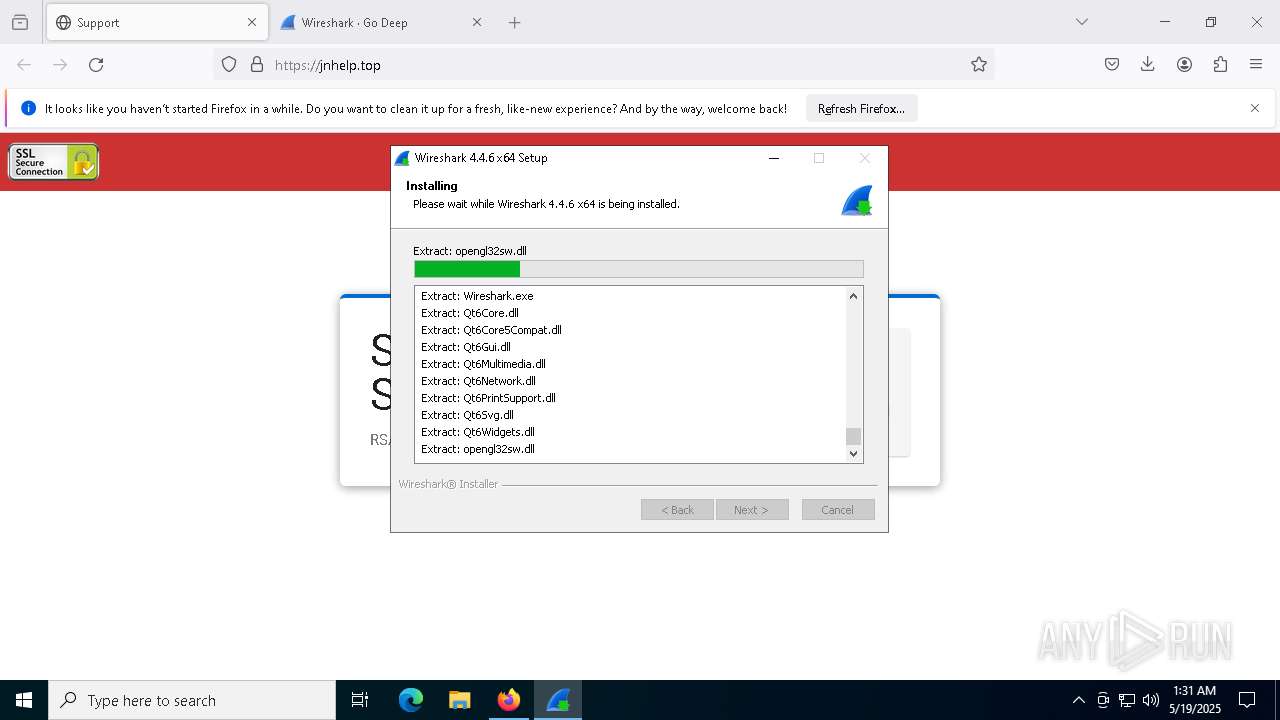
- Wireshark-4.4.6-x64.exe (PID: 8872)
There is functionality for taking screenshot (YARA)
- Wireshark-4.4.6-x64.exe (PID: 8872)
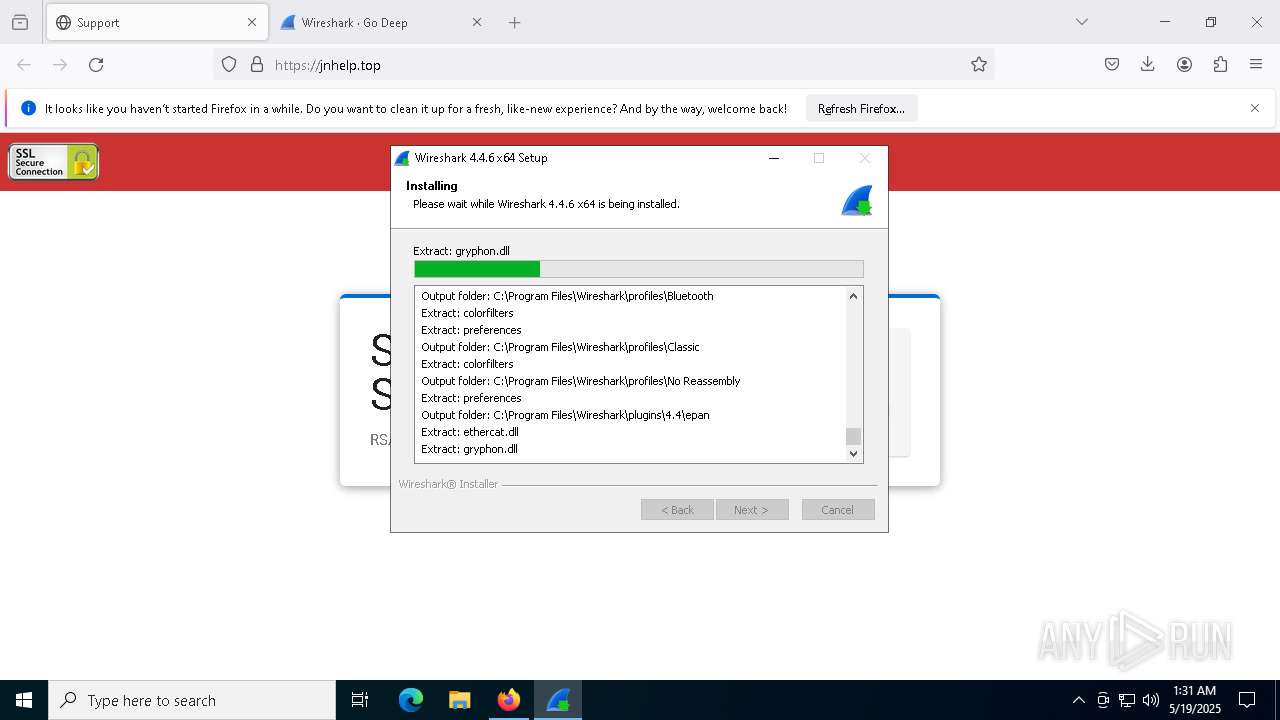
Executable content was dropped or overwritten
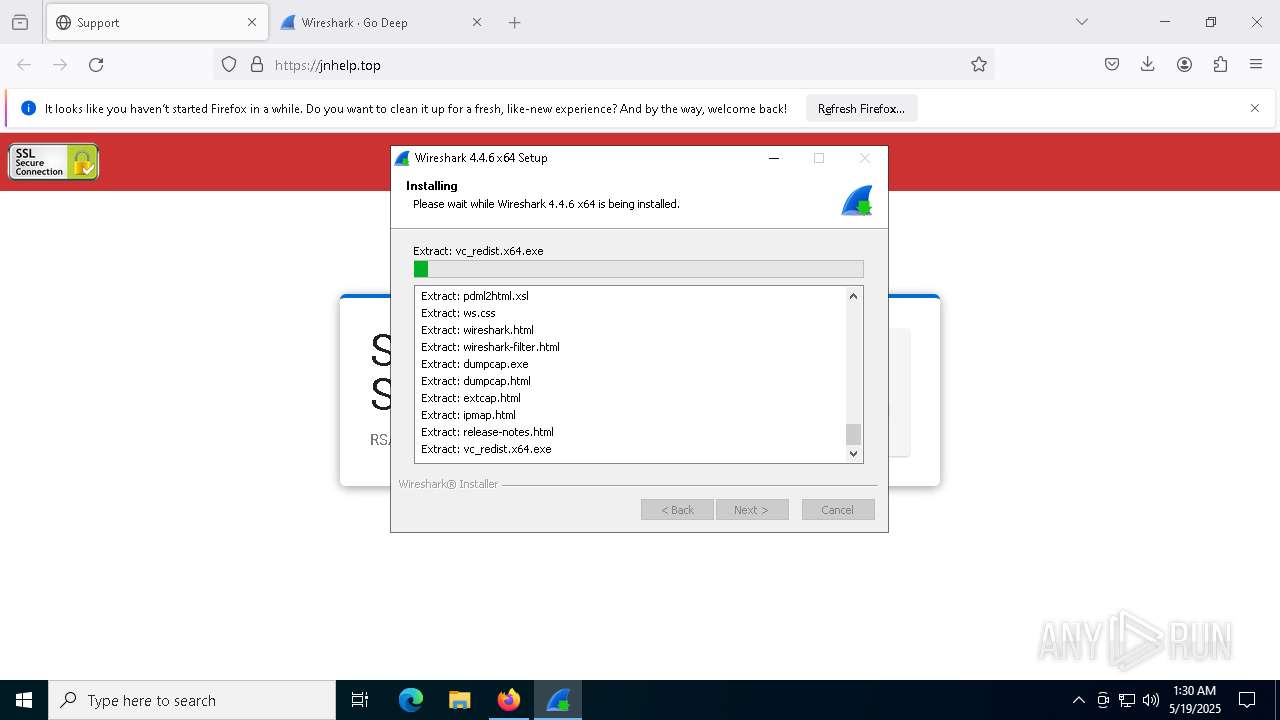
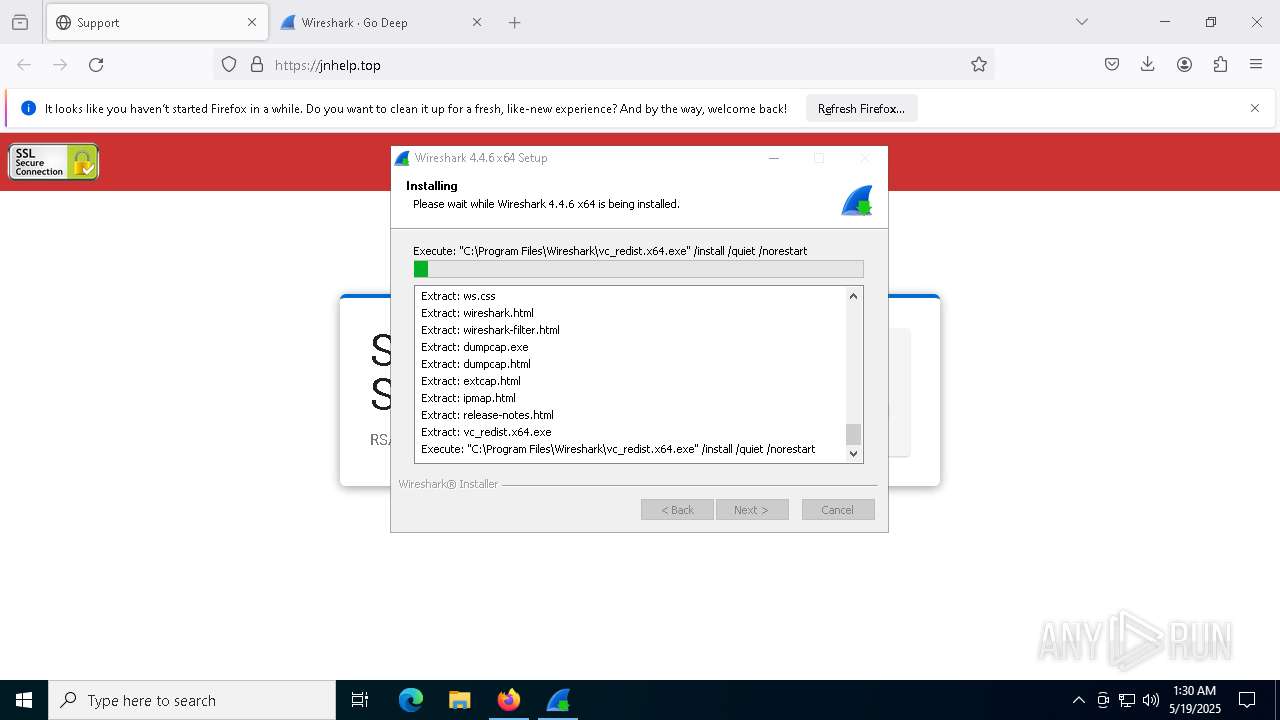
- Wireshark-4.4.6-x64.exe (PID: 8872)
- vc_redist.x64.exe (PID: 9072)
- vc_redist.x64.exe (PID: 9096)
- VC_redist.x64.exe (PID: 9144)
- VC_redist.x64.exe (PID: 6540)
- VC_redist.x64.exe (PID: 8252)
- npcap-1.79.exe (PID: 7676)
- NPFInstall.exe (PID: 8560)
- drvinst.exe (PID: 7728)
- dfsvc.exe (PID: 9004)
Starts a Microsoft application from unusual location
- vc_redist.x64.exe (PID: 9096)
- VC_redist.x64.exe (PID: 9144)
Searches for installed software
- Wireshark-4.4.6-x64.exe (PID: 8872)
- vc_redist.x64.exe (PID: 9096)
- dllhost.exe (PID: 9188)
Process drops legitimate windows executable
- Wireshark-4.4.6-x64.exe (PID: 8872)
- vc_redist.x64.exe (PID: 9072)
- VC_redist.x64.exe (PID: 9144)
- msiexec.exe (PID: 904)
- vc_redist.x64.exe (PID: 9096)
- VC_redist.x64.exe (PID: 8252)
Starts itself from another location
- vc_redist.x64.exe (PID: 9096)
Executes as Windows Service
- VSSVC.exe (PID: 7552)
- ScreenConnect.ClientService.exe (PID: 4572)
Reads security settings of Internet Explorer
- vc_redist.x64.exe (PID: 9096)
Application launched itself
- VC_redist.x64.exe (PID: 6540)
- VC_redist.x64.exe (PID: 6760)
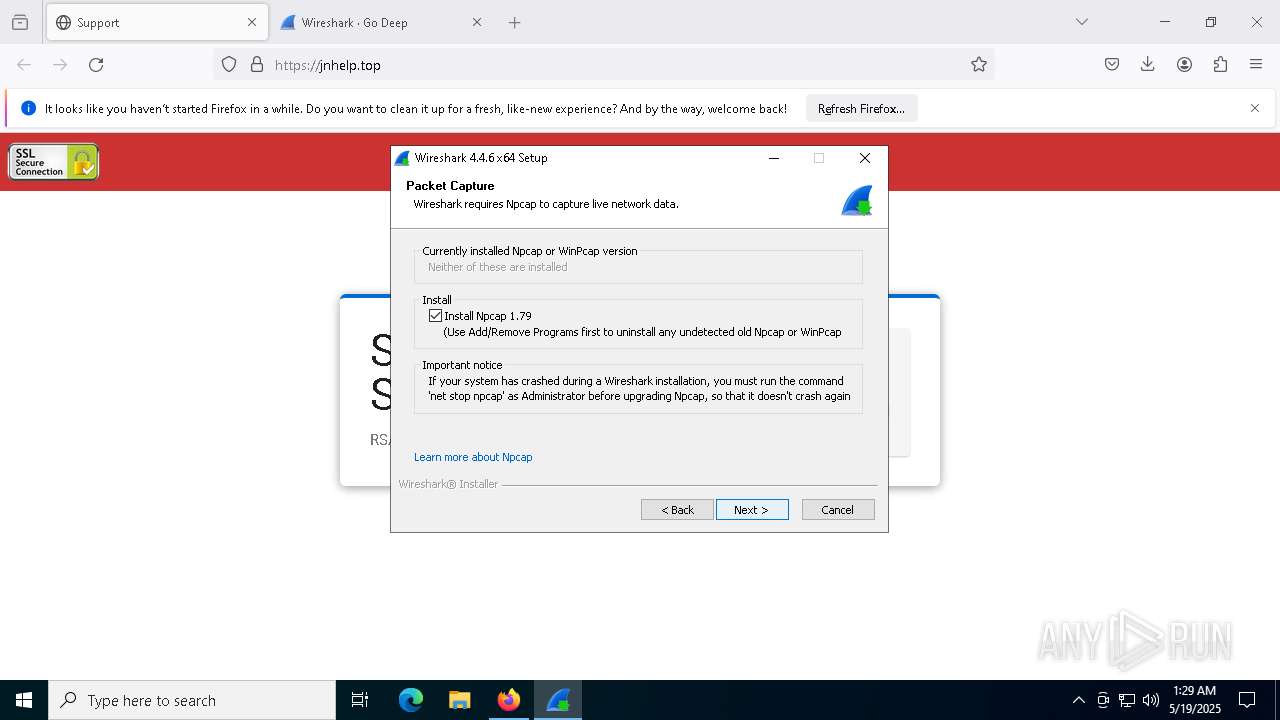
Drops a system driver (possible attempt to evade defenses)
- npcap-1.79.exe (PID: 7676)
- NPFInstall.exe (PID: 8560)
- drvinst.exe (PID: 7728)
The process drops C-runtime libraries
- msiexec.exe (PID: 904)
Removes files via Powershell
- powershell.exe (PID: 8732)
- powershell.exe (PID: 9164)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 8732)
- powershell.exe (PID: 7148)
- powershell.exe (PID: 9164)
- powershell.exe (PID: 736)
The process bypasses the loading of PowerShell profile settings
- npcap-1.79.exe (PID: 7676)
Starts POWERSHELL.EXE for commands execution
- npcap-1.79.exe (PID: 7676)
The process hide an interactive prompt from the user
- npcap-1.79.exe (PID: 7676)
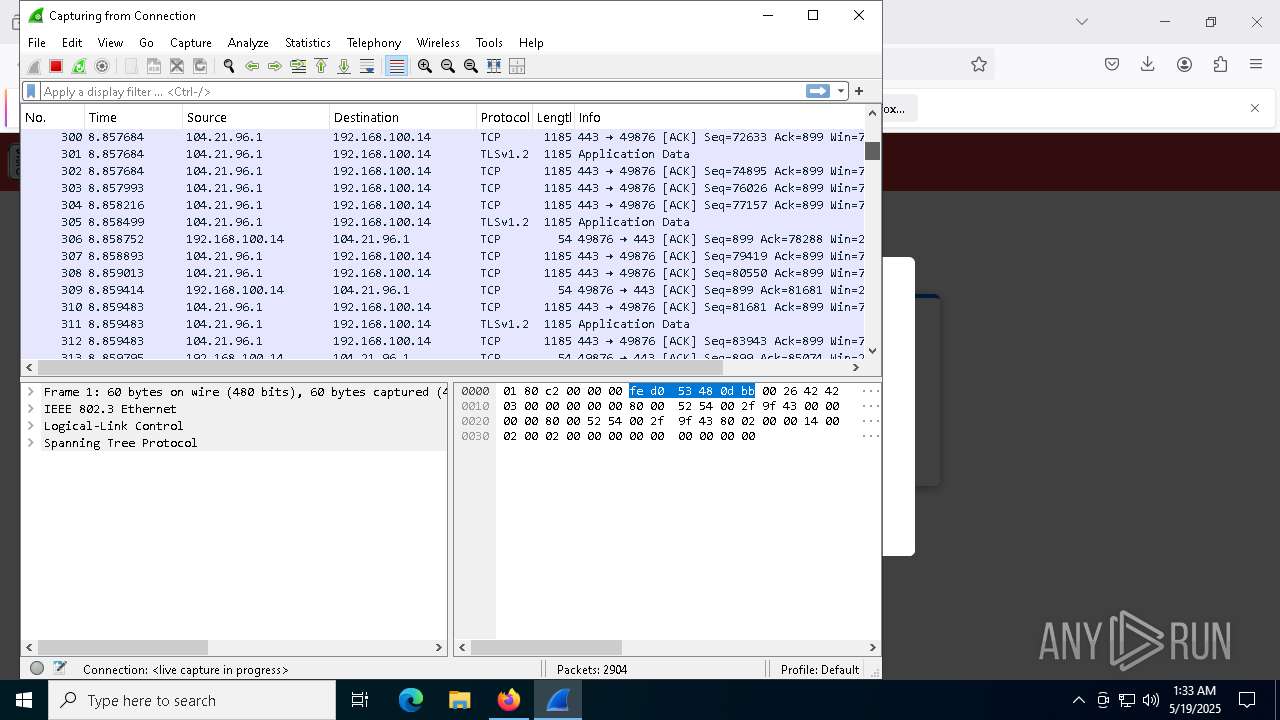
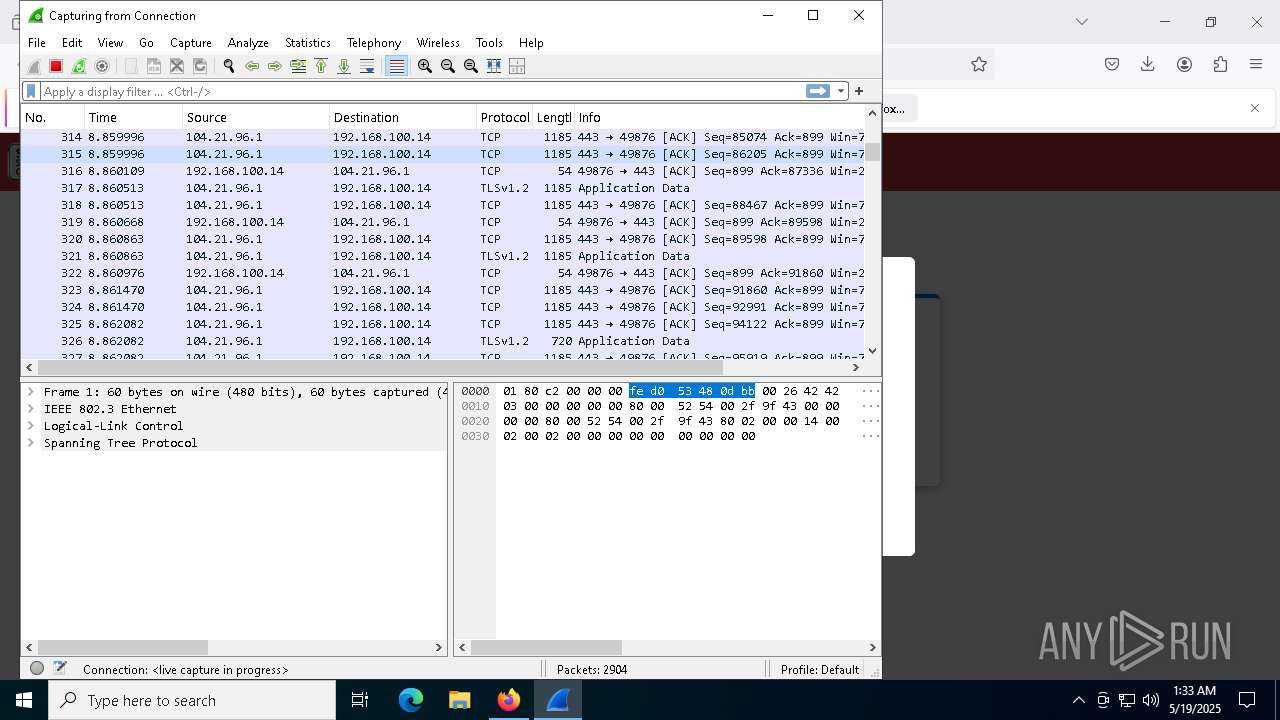
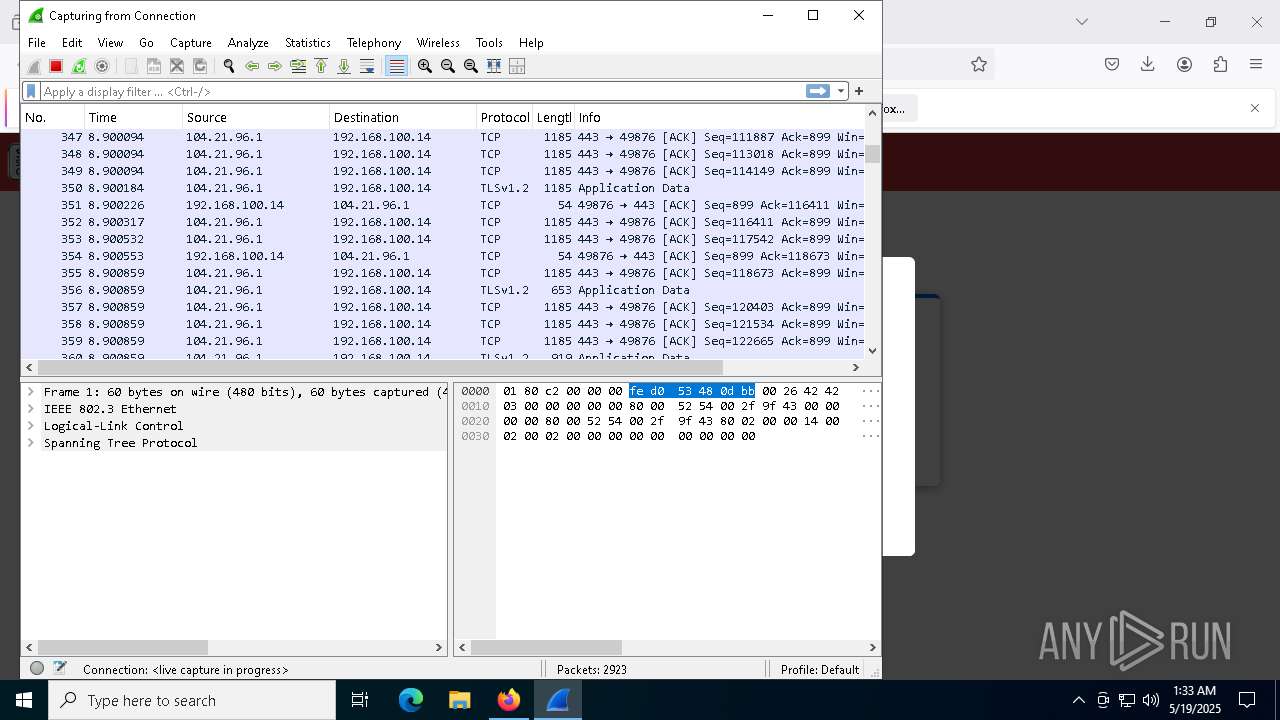
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 4572)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 4572)
INFO
Checks supported languages
- Wireshark-4.4.6-x64.exe (PID: 8872)
- vc_redist.x64.exe (PID: 9096)
- vc_redist.x64.exe (PID: 9072)
- VC_redist.x64.exe (PID: 9144)
Application launched itself
- firefox.exe (PID: 2384)
- firefox.exe (PID: 896)
WIRESHARK mutex has been found
- Wireshark-4.4.6-x64.exe (PID: 8872)
Executable content was dropped or overwritten
- firefox.exe (PID: 2384)
- msiexec.exe (PID: 904)
Reads the computer name
- Wireshark-4.4.6-x64.exe (PID: 8872)
- vc_redist.x64.exe (PID: 9096)
- vc_redist.x64.exe (PID: 9072)
- VC_redist.x64.exe (PID: 9144)
Create files in a temporary directory
- Wireshark-4.4.6-x64.exe (PID: 8872)
- vc_redist.x64.exe (PID: 9096)
Reads the software policy settings
- slui.exe (PID: 1072)
Creates files in the program directory
- Wireshark-4.4.6-x64.exe (PID: 8872)
The sample compiled with english language support
- Wireshark-4.4.6-x64.exe (PID: 8872)
- vc_redist.x64.exe (PID: 9072)
- VC_redist.x64.exe (PID: 9144)
- vc_redist.x64.exe (PID: 9096)
- msiexec.exe (PID: 904)
- VC_redist.x64.exe (PID: 6540)
- VC_redist.x64.exe (PID: 8252)
- npcap-1.79.exe (PID: 7676)
Process checks computer location settings
- vc_redist.x64.exe (PID: 9096)
Manages system restore points
- SrTasks.exe (PID: 472)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 3024)
- conhost.exe (PID: 5036)
- conhost.exe (PID: 8104)
- conhost.exe (PID: 5796)
- conhost.exe (PID: 8736)
- conhost.exe (PID: 5680)
- conhost.exe (PID: 8408)
- conhost.exe (PID: 6184)
- conhost.exe (PID: 8052)
- conhost.exe (PID: 3240)
- conhost.exe (PID: 8388)
- conhost.exe (PID: 8452)
- conhost.exe (PID: 4424)
- conhost.exe (PID: 6148)
- powershell.exe (PID: 8772)
- conhost.exe (PID: 6656)
- conhost.exe (PID: 9100)
- conhost.exe (PID: 7564)
- conhost.exe (PID: 8744)
- conhost.exe (PID: 7860)
- conhost.exe (PID: 736)
- conhost.exe (PID: 6988)
- conhost.exe (PID: 8564)
- conhost.exe (PID: 9072)
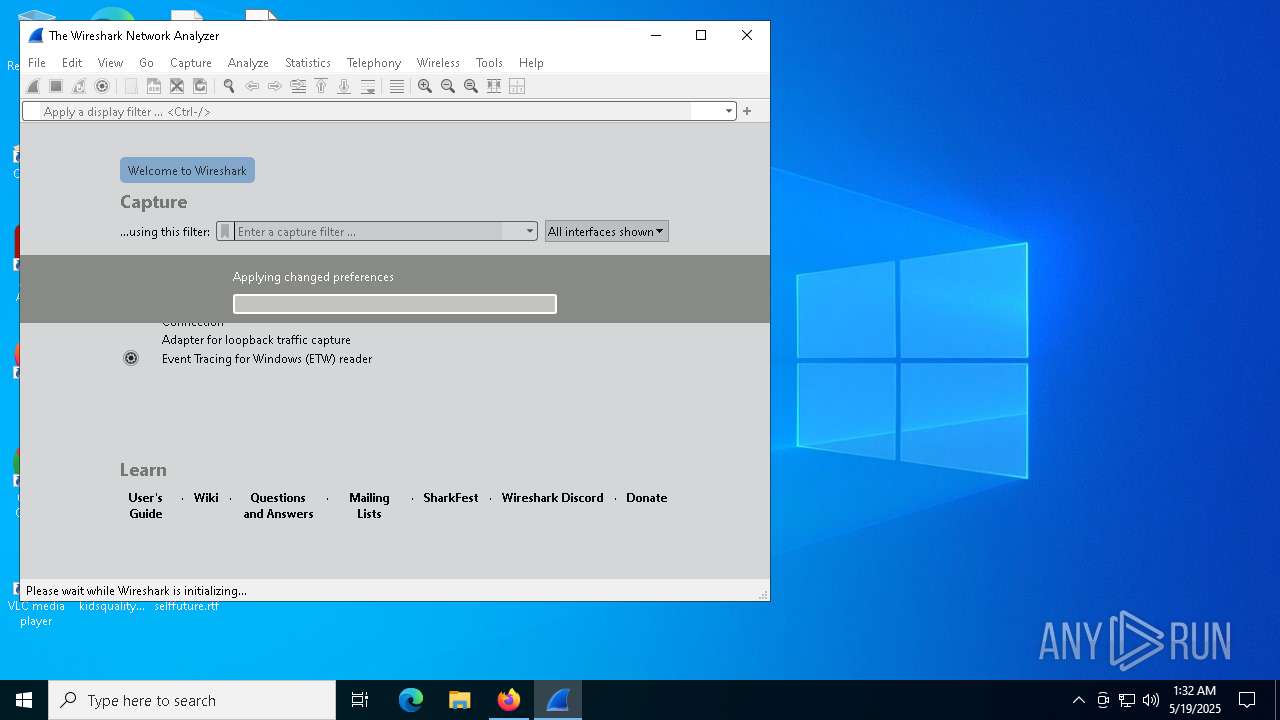
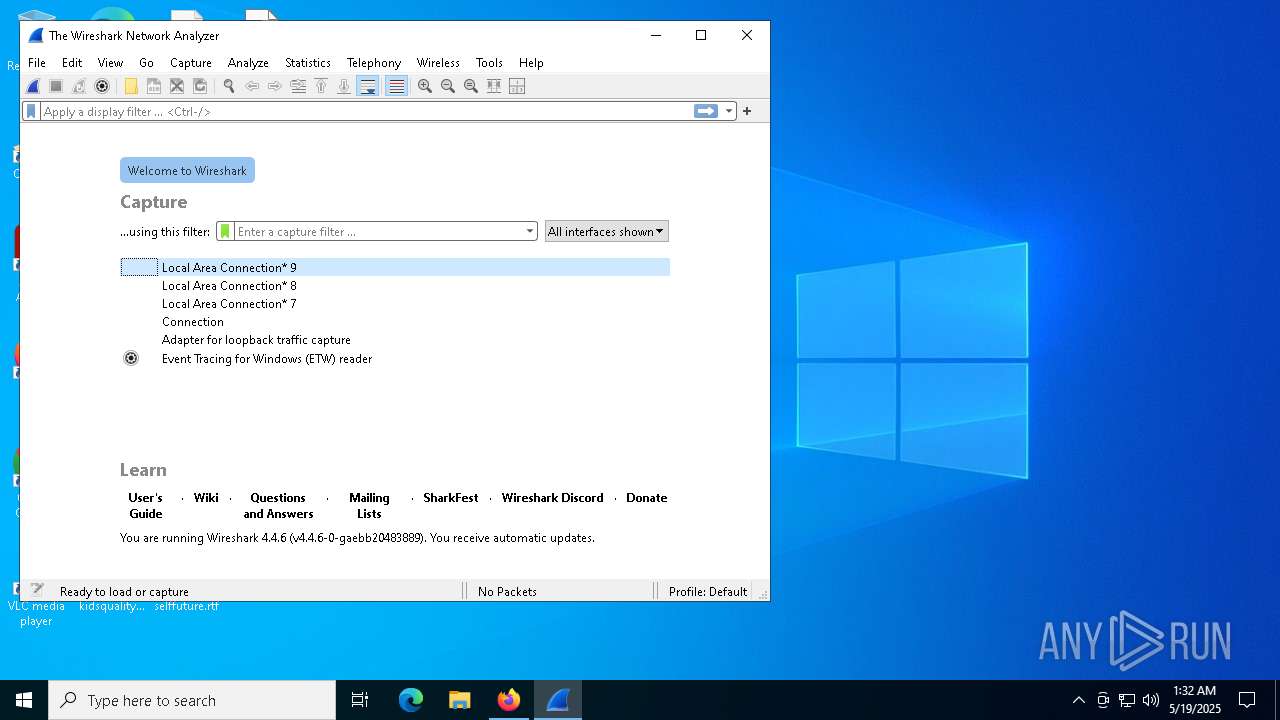
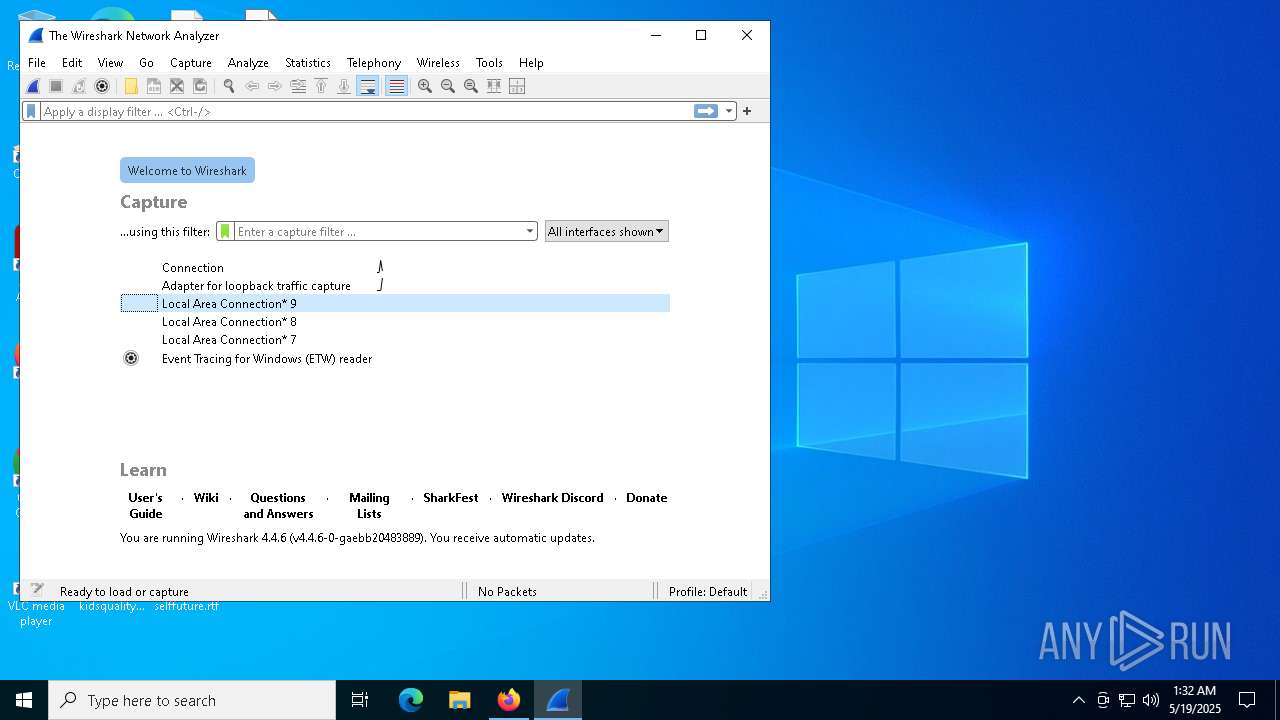
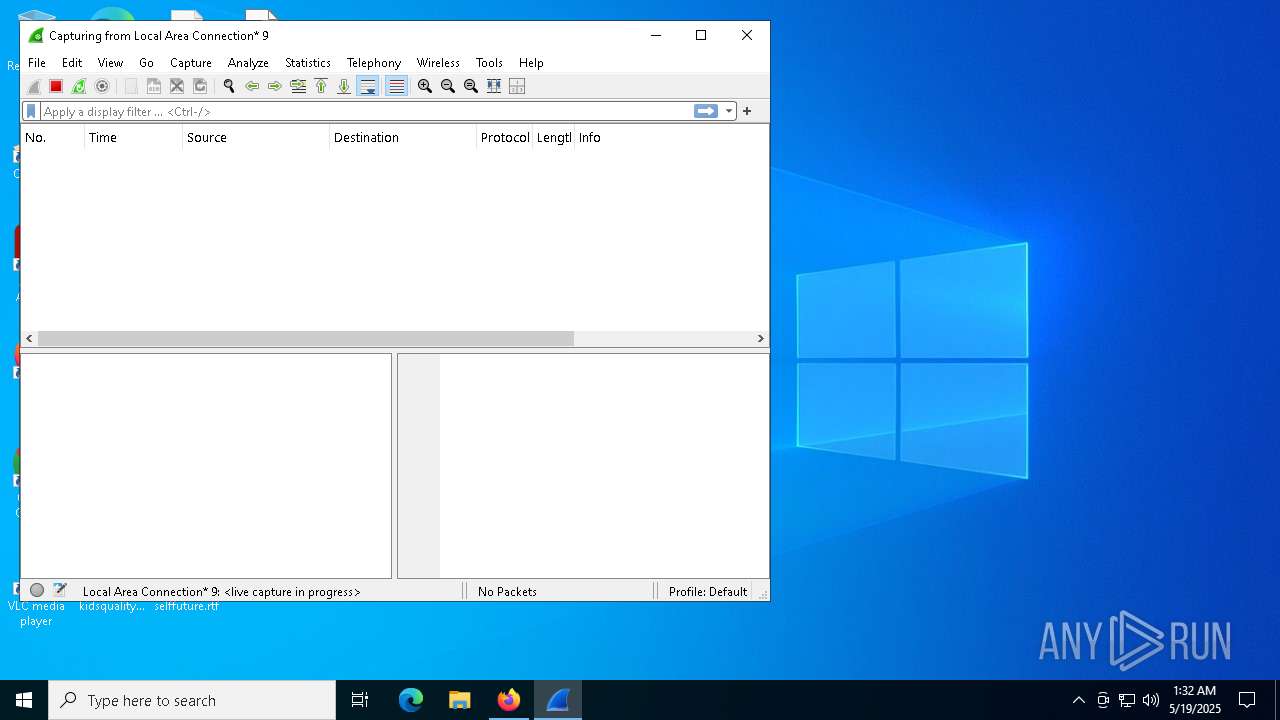
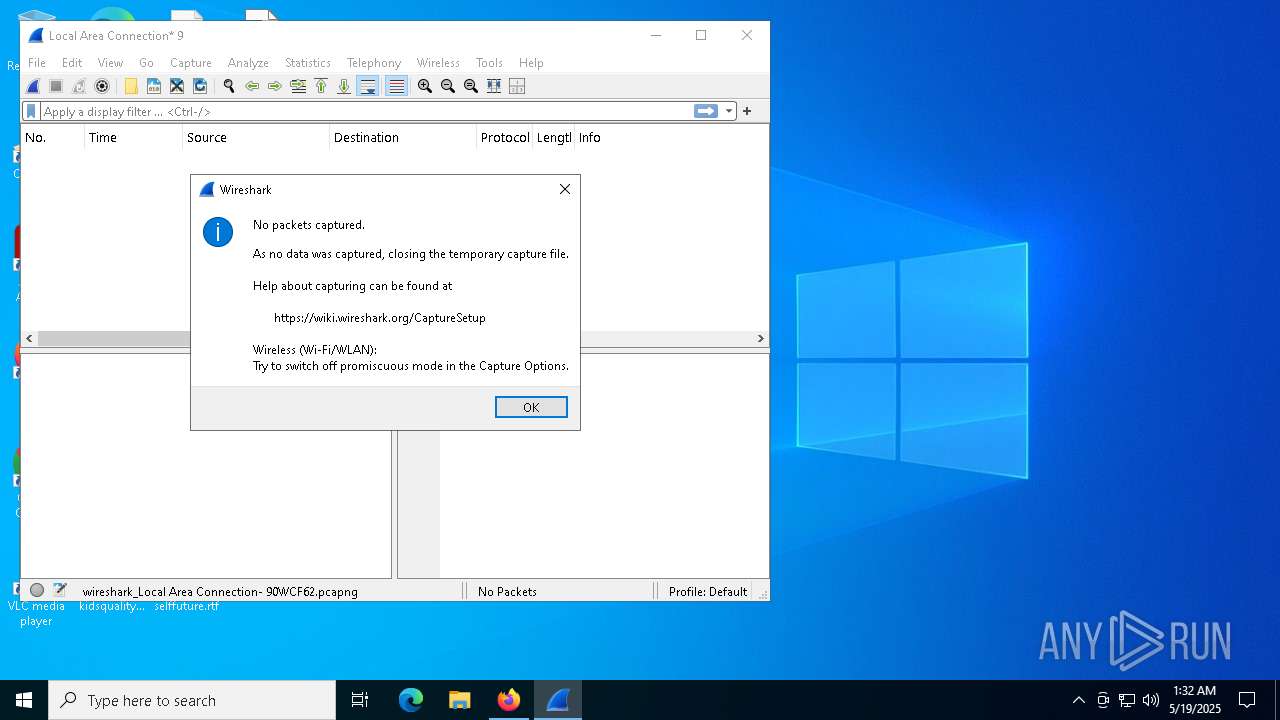
Manual execution by a user
- Wireshark.exe (PID: 8960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
239
Monitored processes
93
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | "C:\Users\admin\AppData\Local\Apps\2.0\3GB6H8WT.W5D\2GN10ZL7.YHN\scre..tion_25b0fbb6ef7eb094_0018.0001_3e220df00f27f70c\ScreenConnect.WindowsClient.exe" | C:\Users\admin\AppData\Local\Apps\2.0\3GB6H8WT.W5D\2GN10ZL7.YHN\scre..tion_25b0fbb6ef7eb094_0018.0001_3e220df00f27f70c\ScreenConnect.WindowsClient.exe | — | dfsvc.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 24.1.7.8892 Modules
| |||||||||||||||
| 736 | powershell.exe -NoProfile -WindowStyle Hidden -NonInteractive -Command "Get-ChildItem Cert:\LocalMachine\Root | Where-Object {$_.Thumbprint -eq '0563b8630d62d75abbc8ab1e4bdfb5a899b24d43'} | Sort-Object -Descending -Property FriendlyName | Select-Object -Skip 1 | Remove-Item" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | npcap-1.79.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5456 -childID 7 -isForBrowser -prefsHandle 5300 -prefMapHandle 5296 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2b1ee5fa-3f65-4179-8c81-685288a0fbba} 2384 "\\.\pipe\gecko-crash-server-pipe.2384" 204b87b5850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Mozilla Firefox\firefox.exe" "jnhelp.top" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 904 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "C:\Program Files\Wireshark\dumpcap.exe" --log-level MESSAGE -F pcapng -i \Device\NPF_{026886EB-3843-4EDD-9164-7A9F9FB69F1E} --ifdescr "Local Area Connection* 9" -y EN10MB --signal-pipe 8960 -Z 2776 | C:\Program Files\Wireshark\dumpcap.exe | — | Wireshark.exe | |||||||||||
User: admin Company: The Wireshark developer community Integrity Level: MEDIUM Description: Dumpcap Exit code: 0 Version: 4.4.6 Modules
| |||||||||||||||
| 1072 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
94 039
Read events
92 711
Write events
909
Delete events
419
Modification events
| (PID) Process: | (2384) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (2384) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (9144) VC_redist.x64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000BC97678F5DC8DB01B8230000BC230000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (9188) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000ED61698F5DC8DB01E4230000FC230000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (9188) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000E0ABF68F5DC8DB01E4230000FC230000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (9188) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000FF42FA8F5DC8DB01E4230000FC230000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (9188) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (9188) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000024E8F38F5DC8DB01E4230000FC230000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (9188) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000024E8F38F5DC8DB01E4230000FC230000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (9188) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000323D56905DC8DB01E4230000FC230000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
226
Suspicious files
388
Text files
1 297
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 2384 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
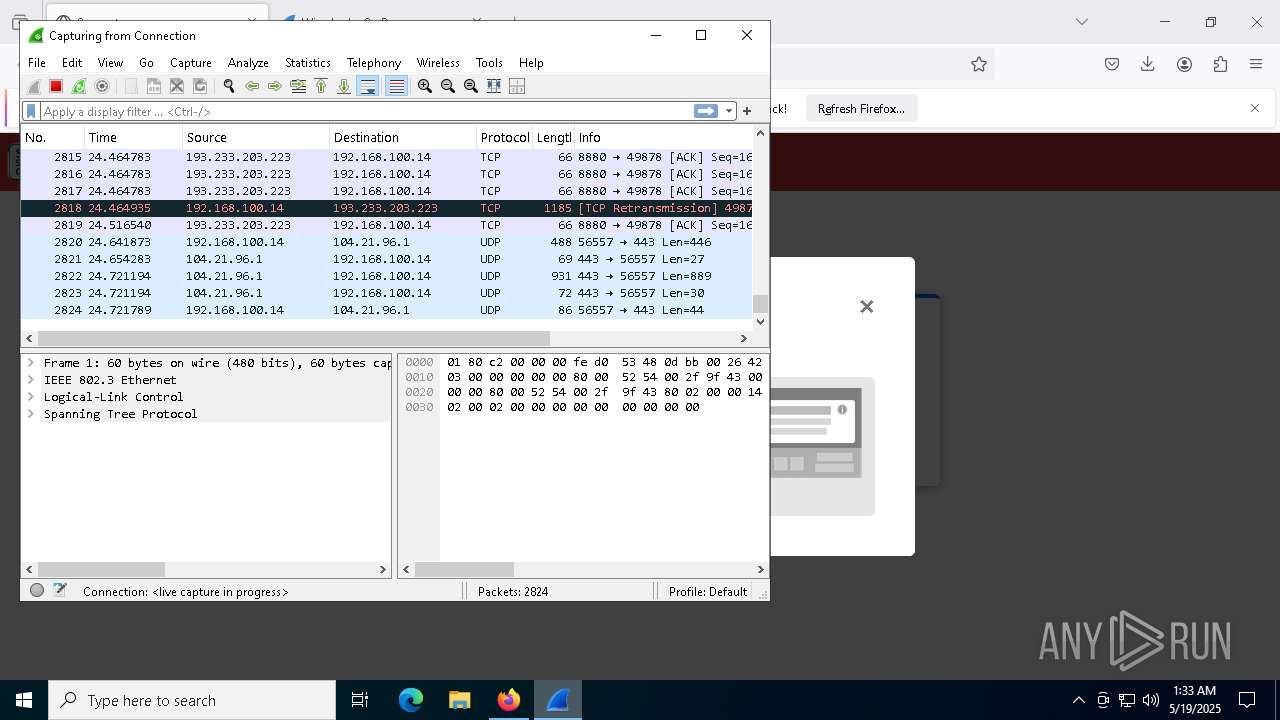
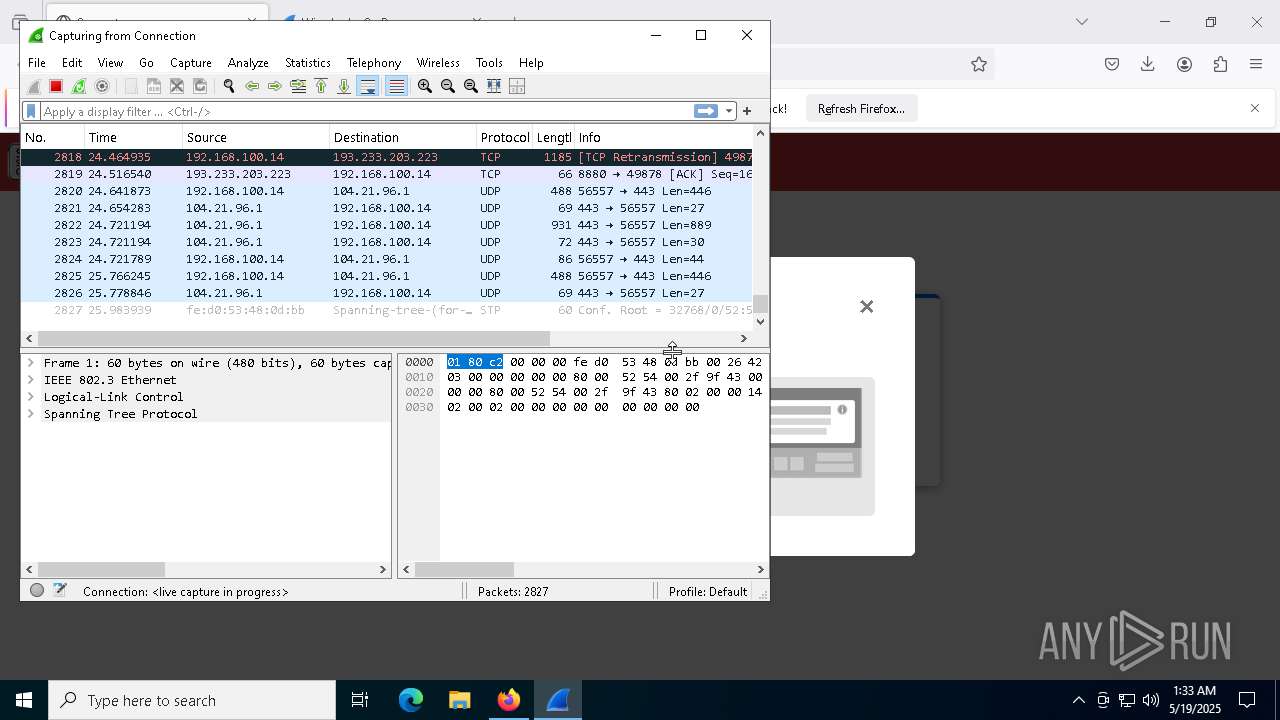
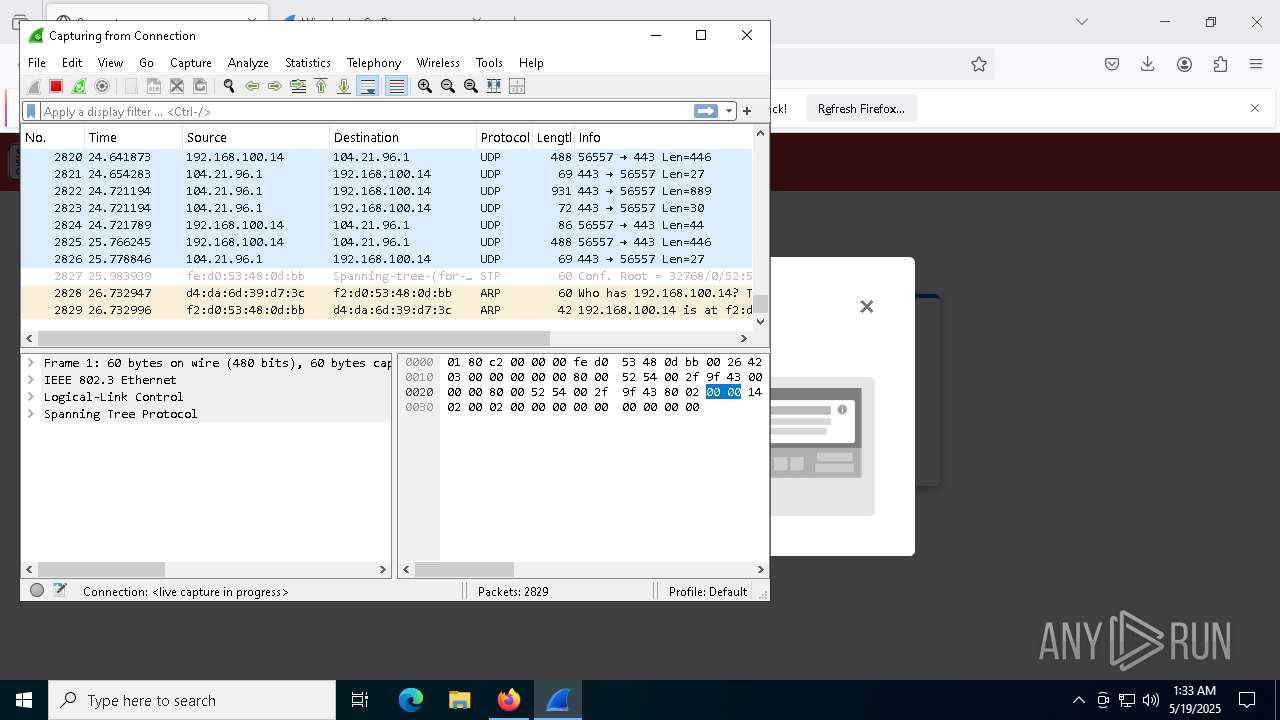
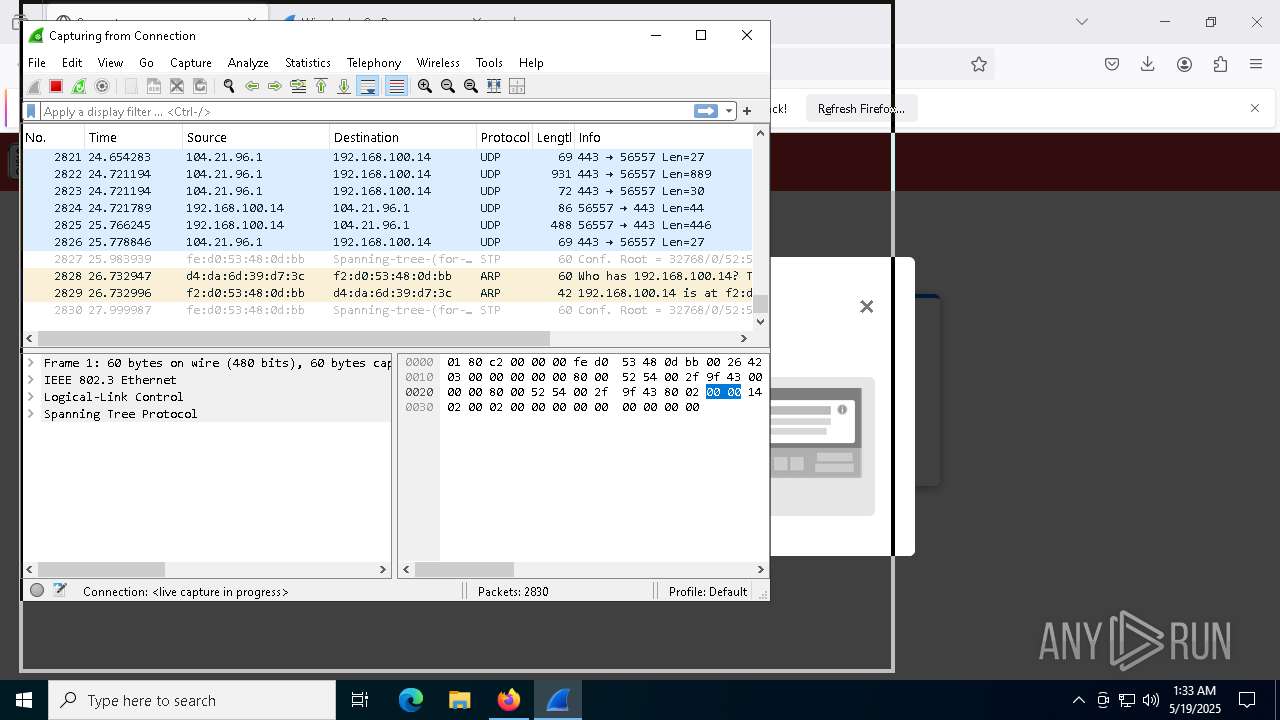
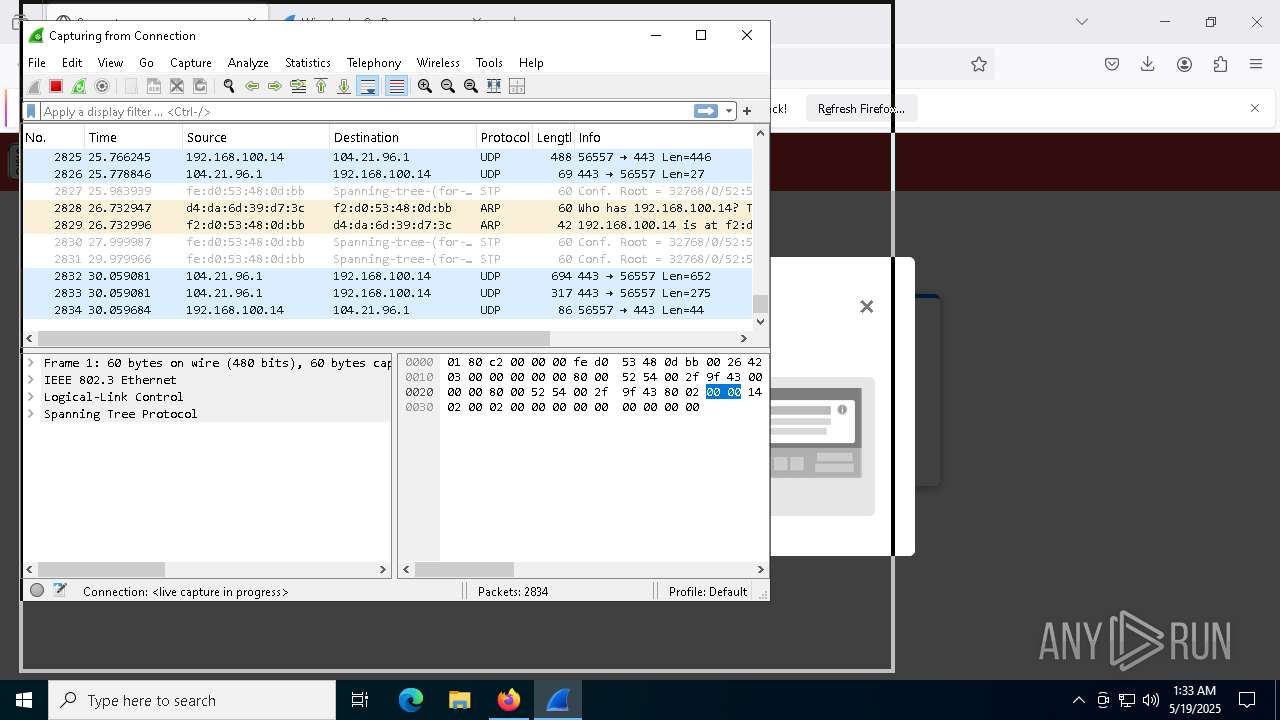
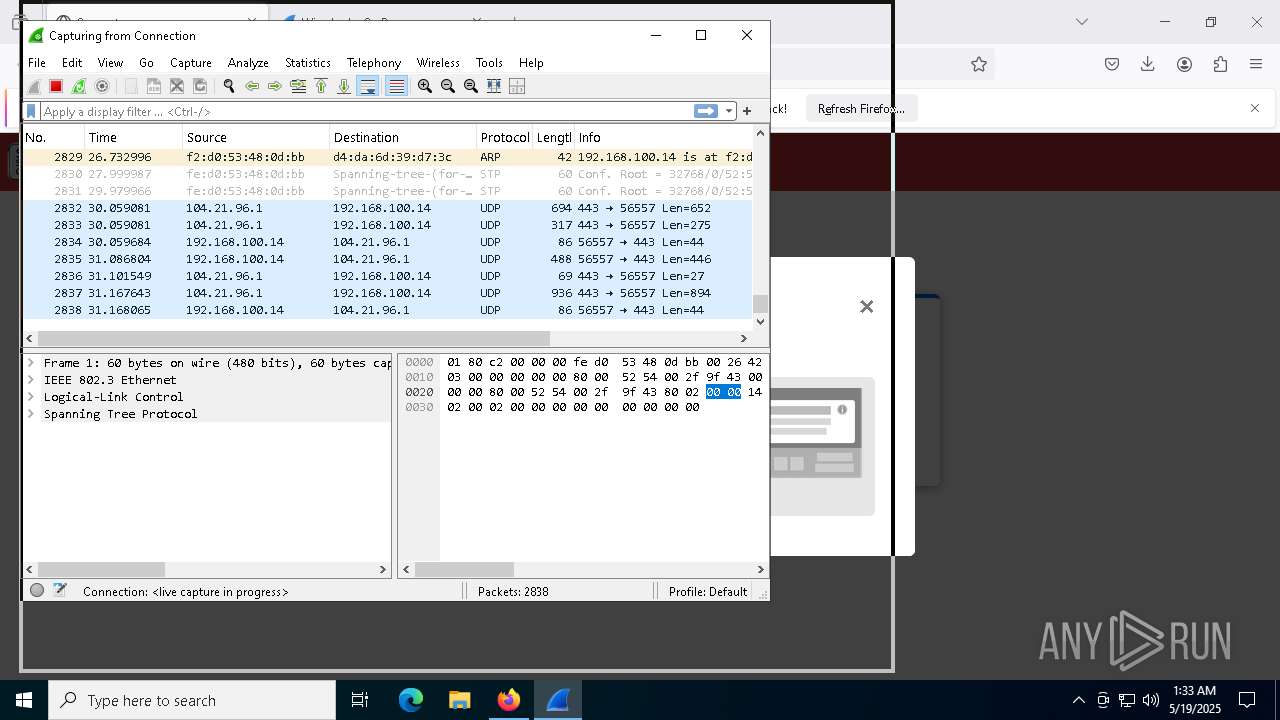
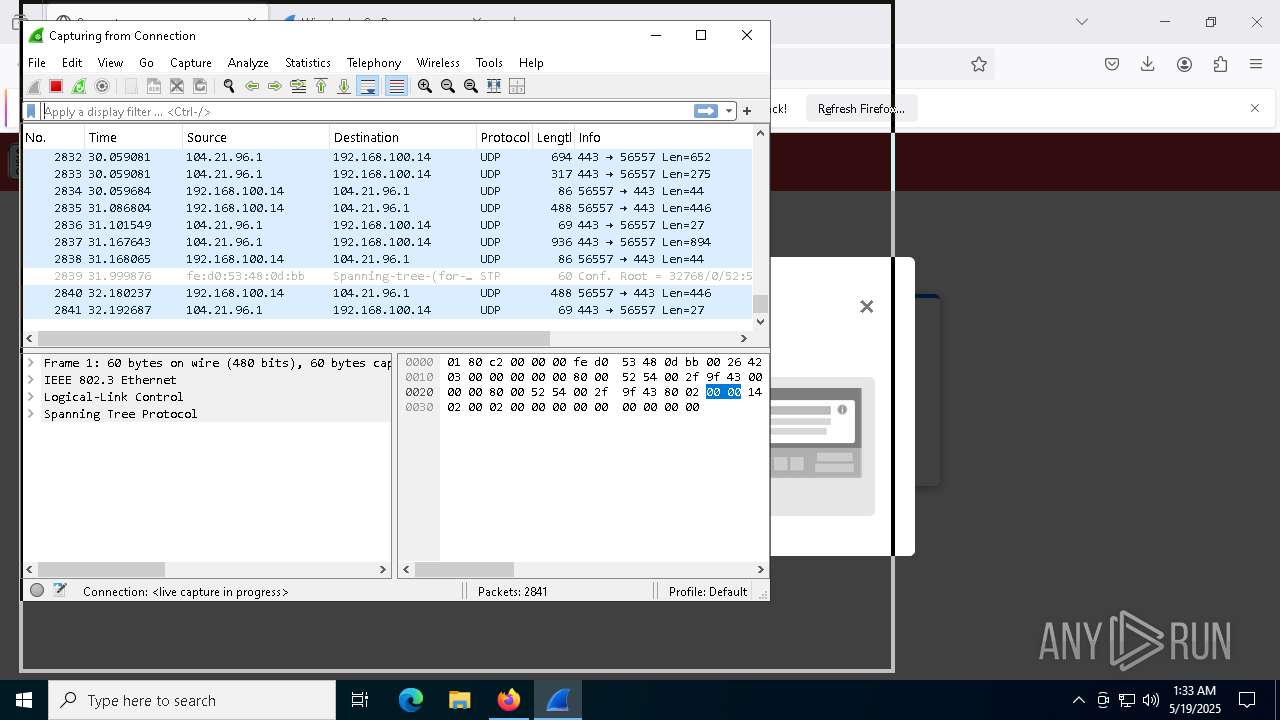
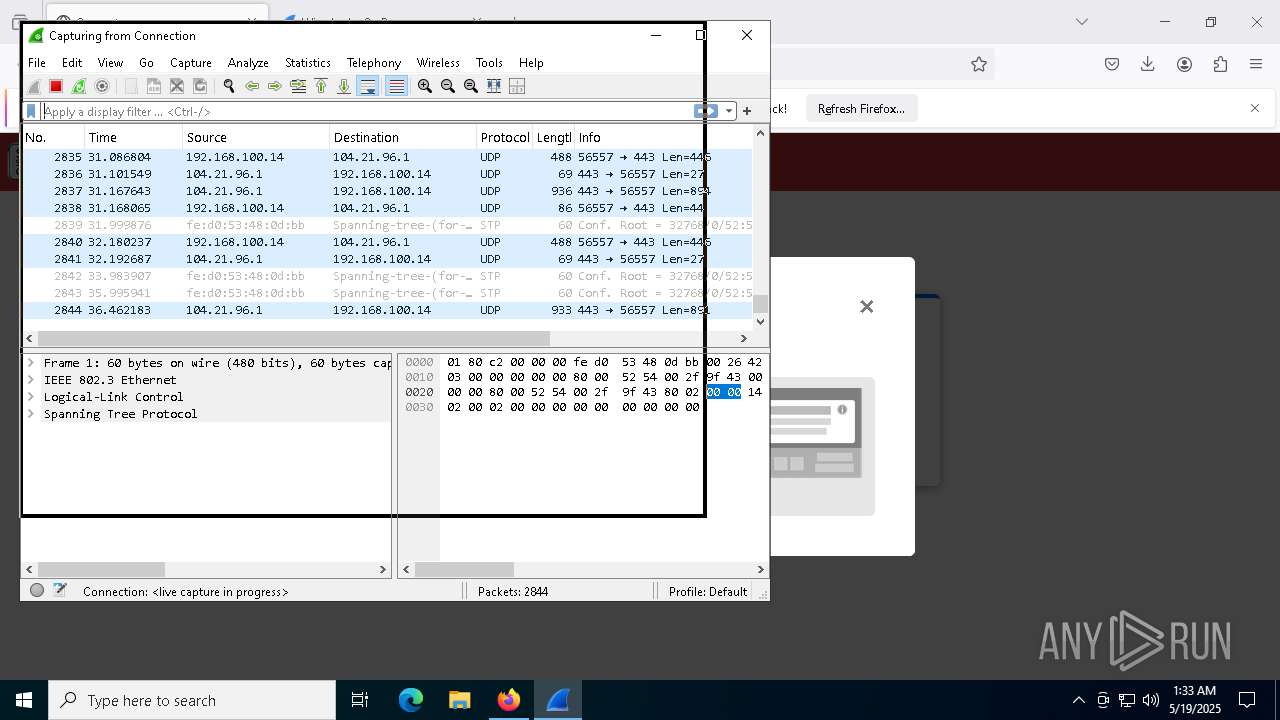
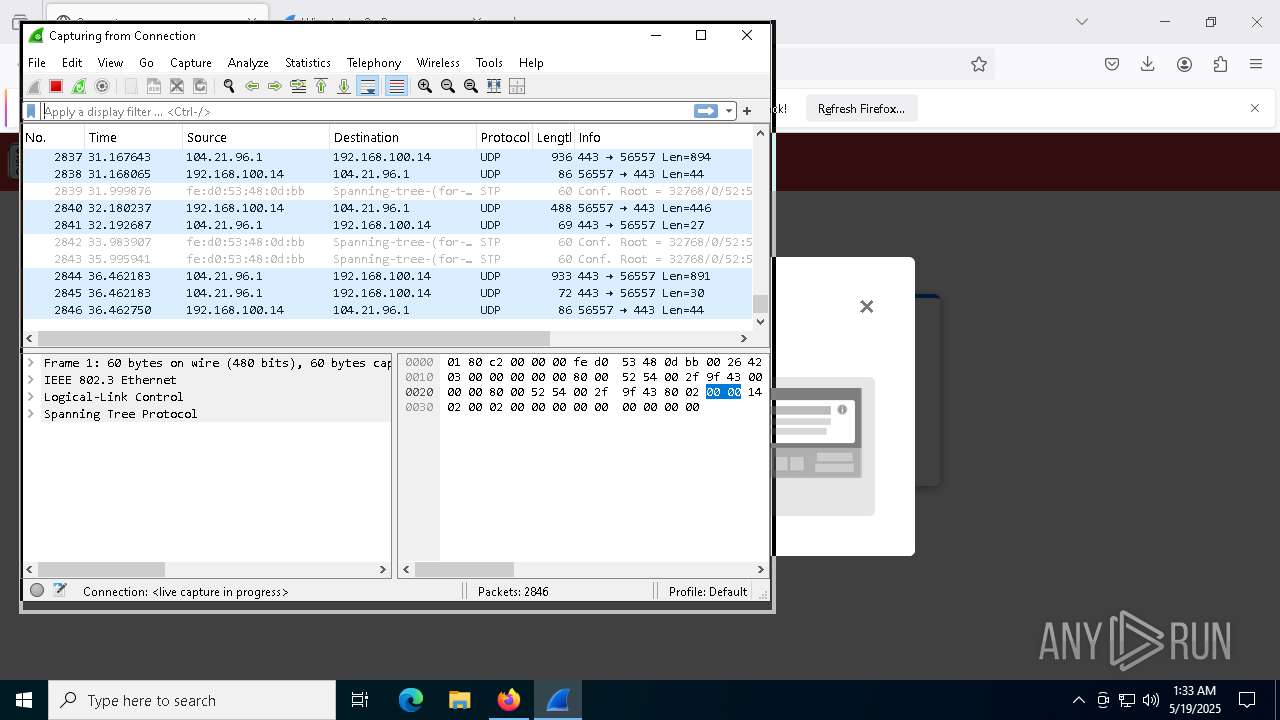
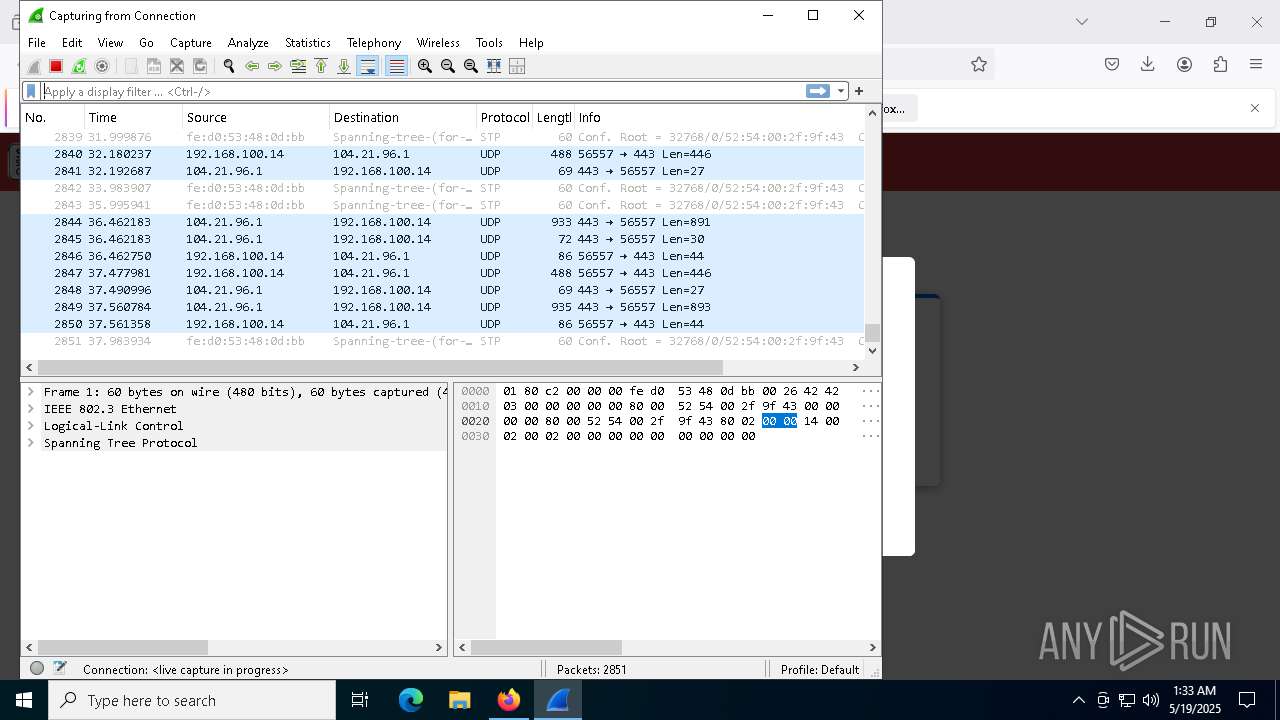
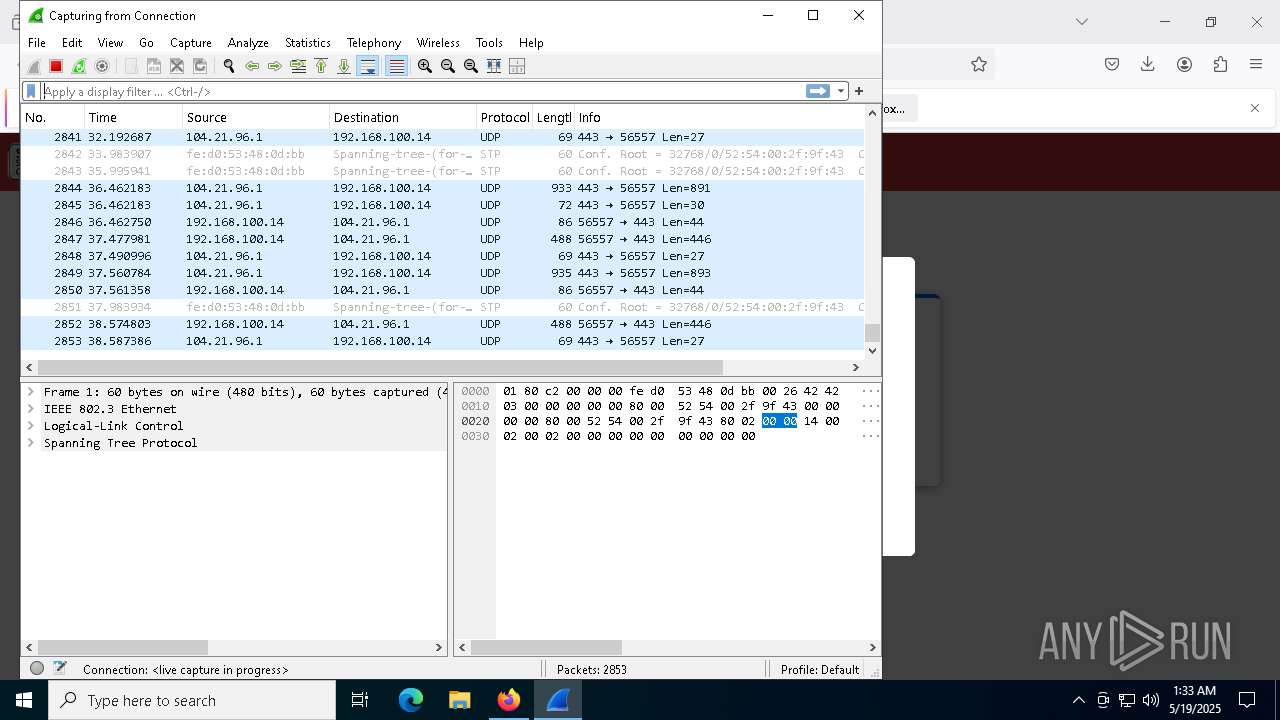
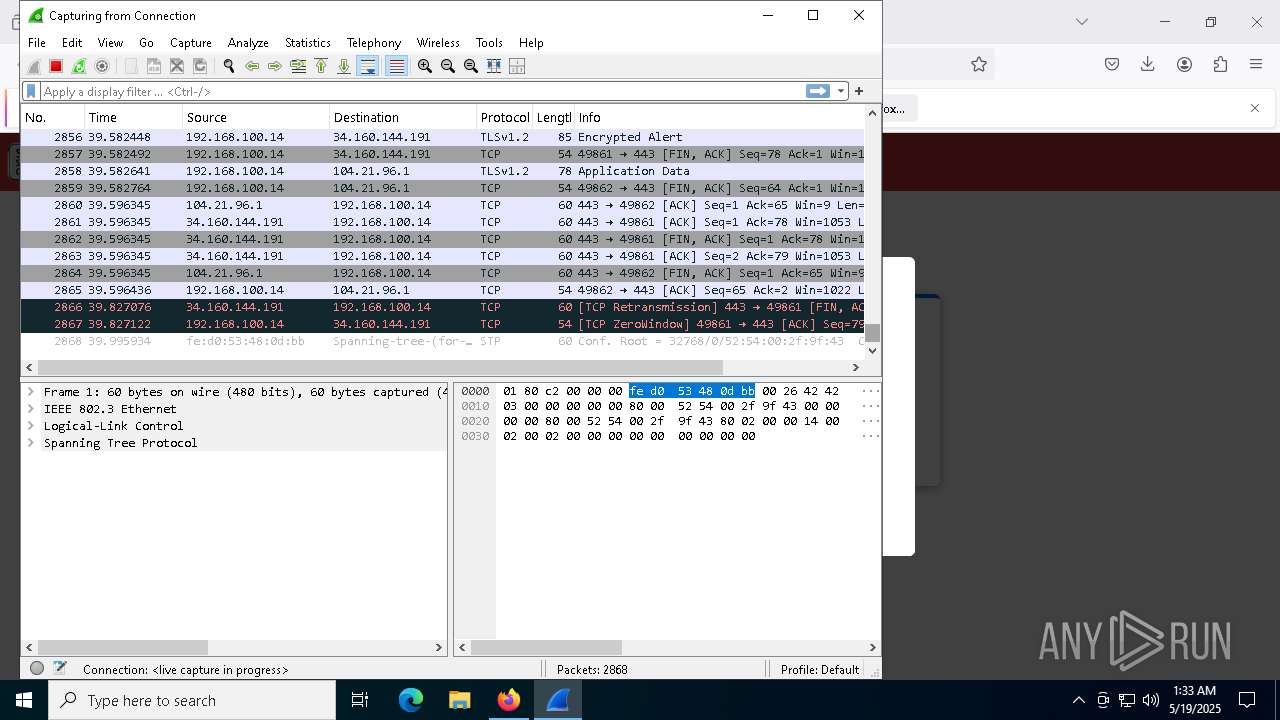
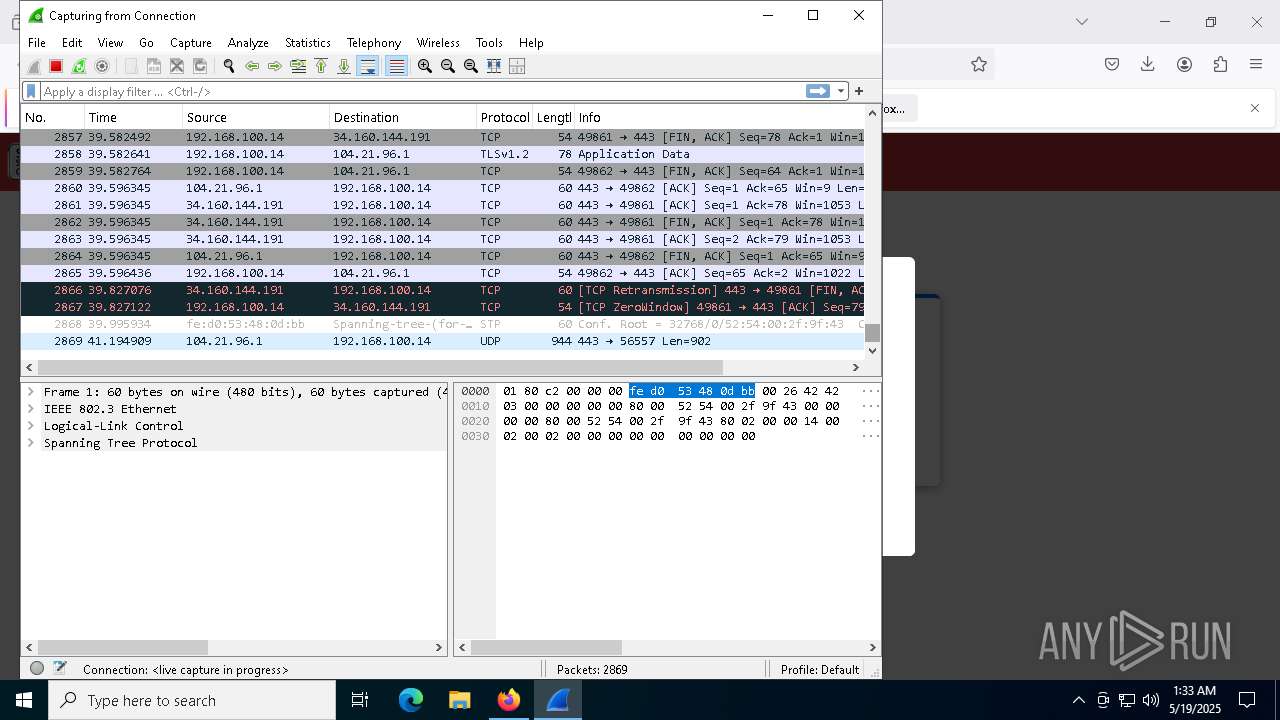
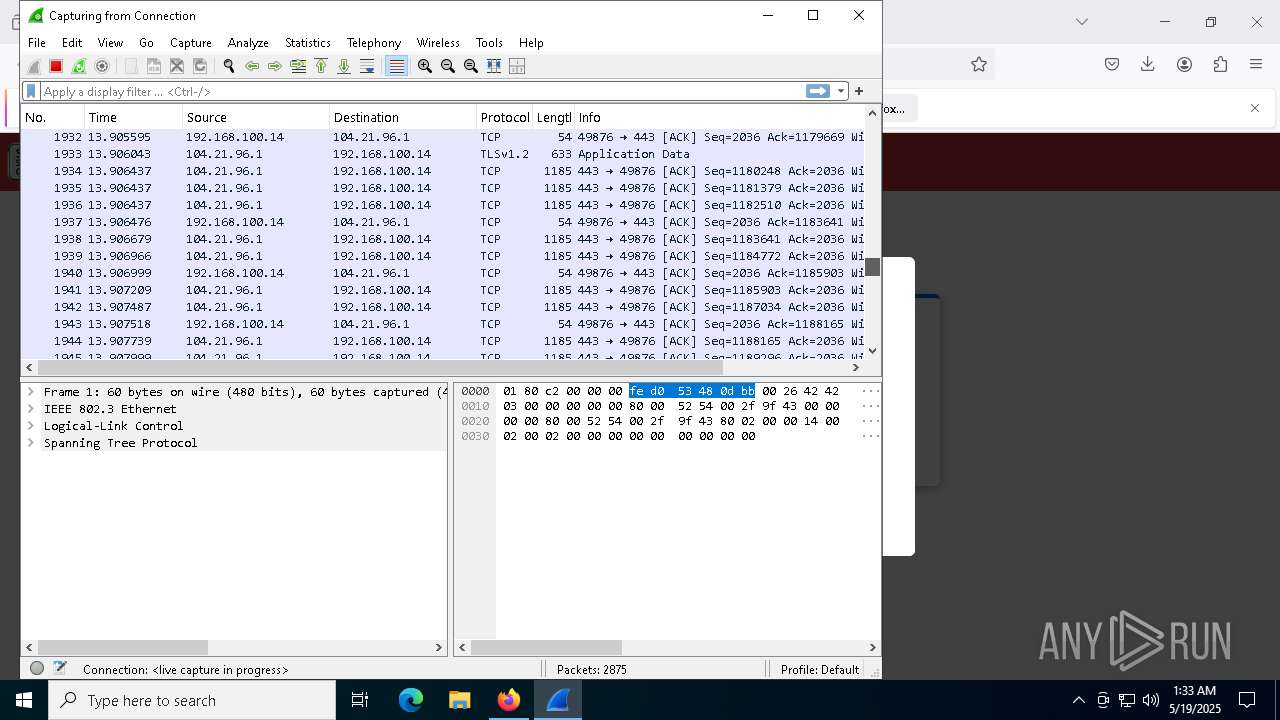
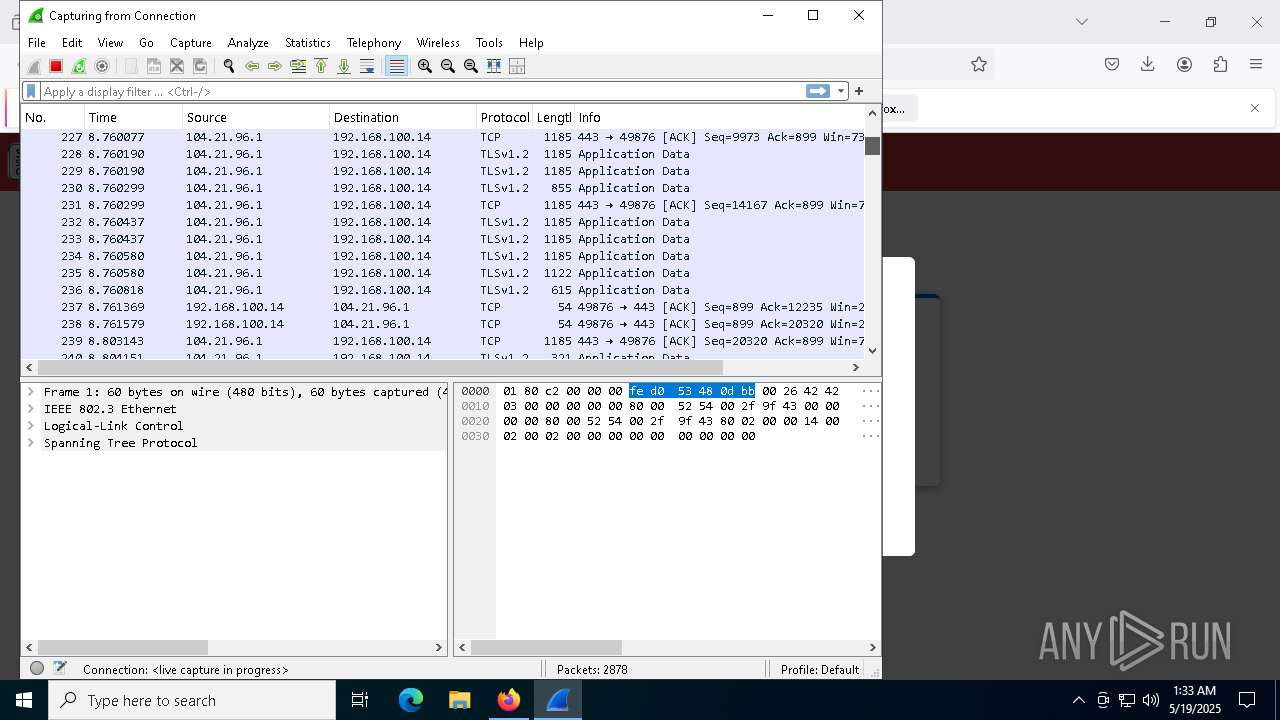
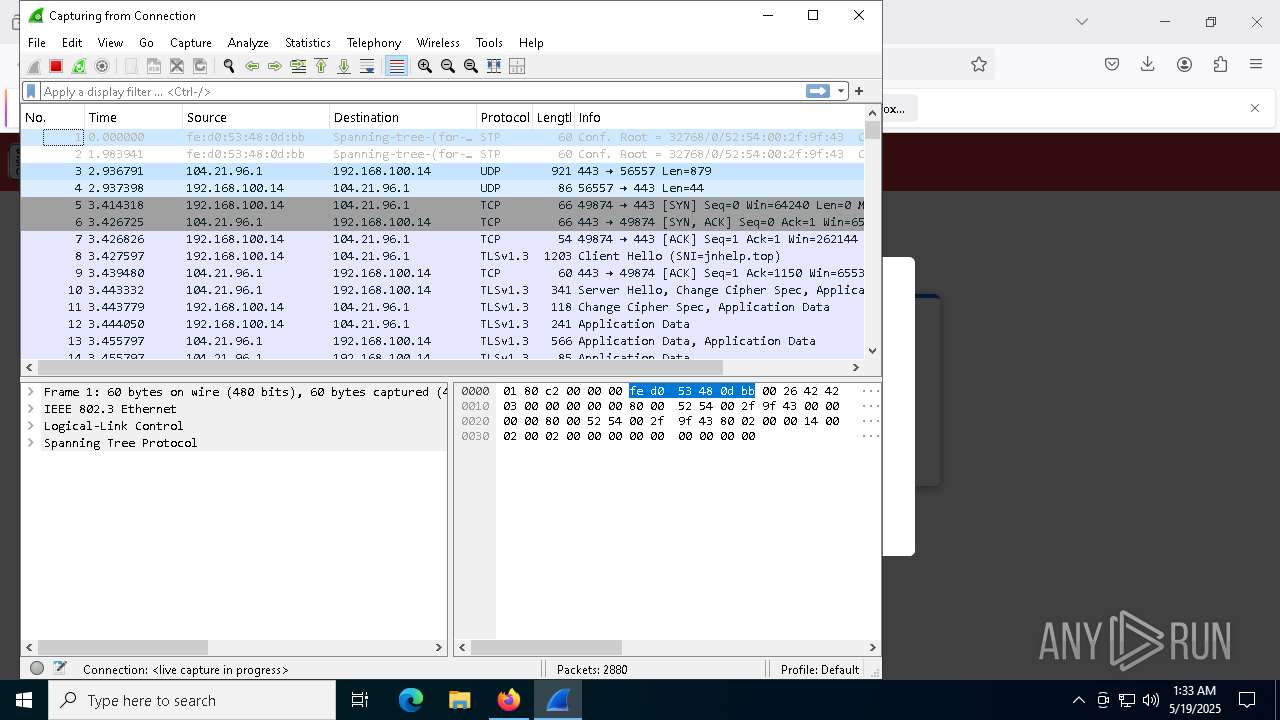
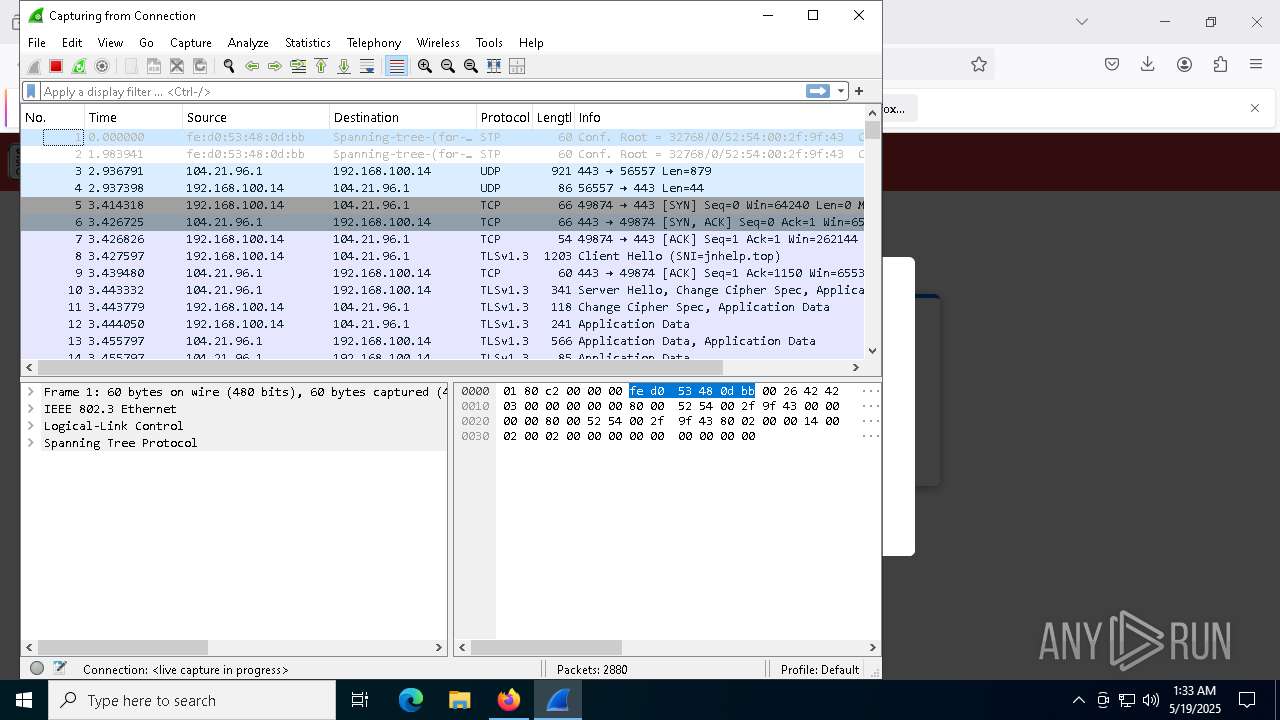
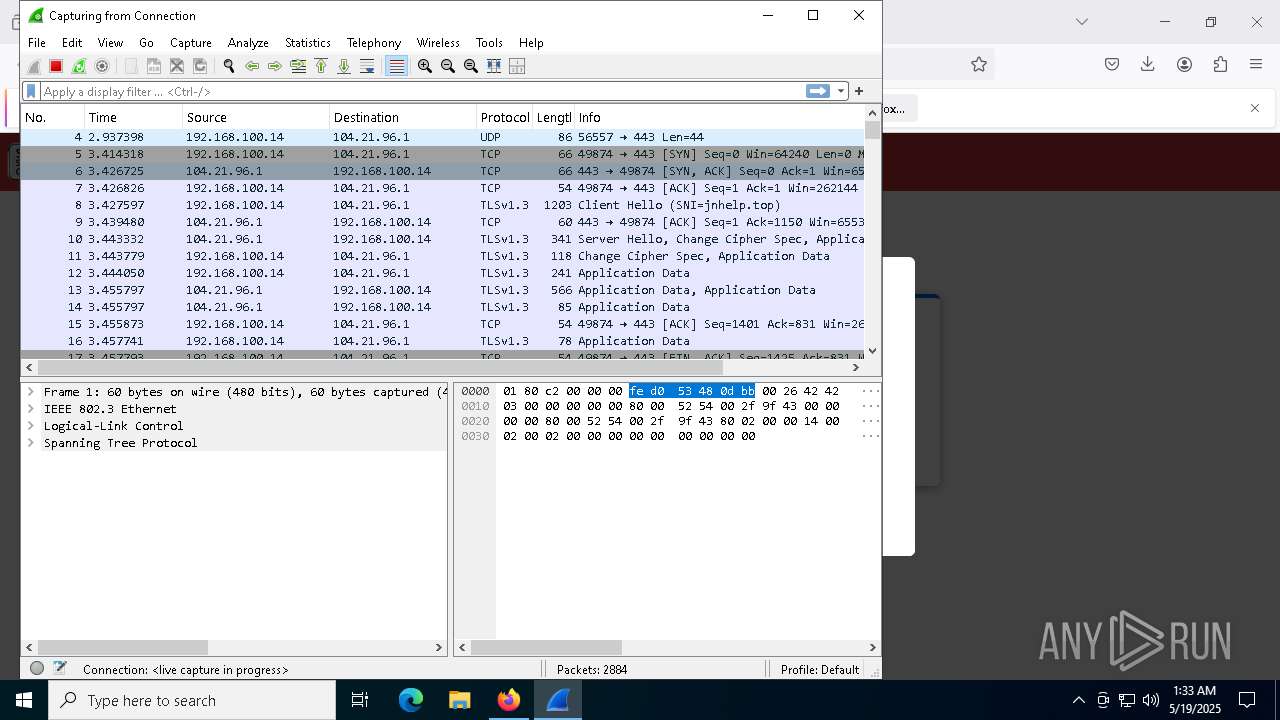
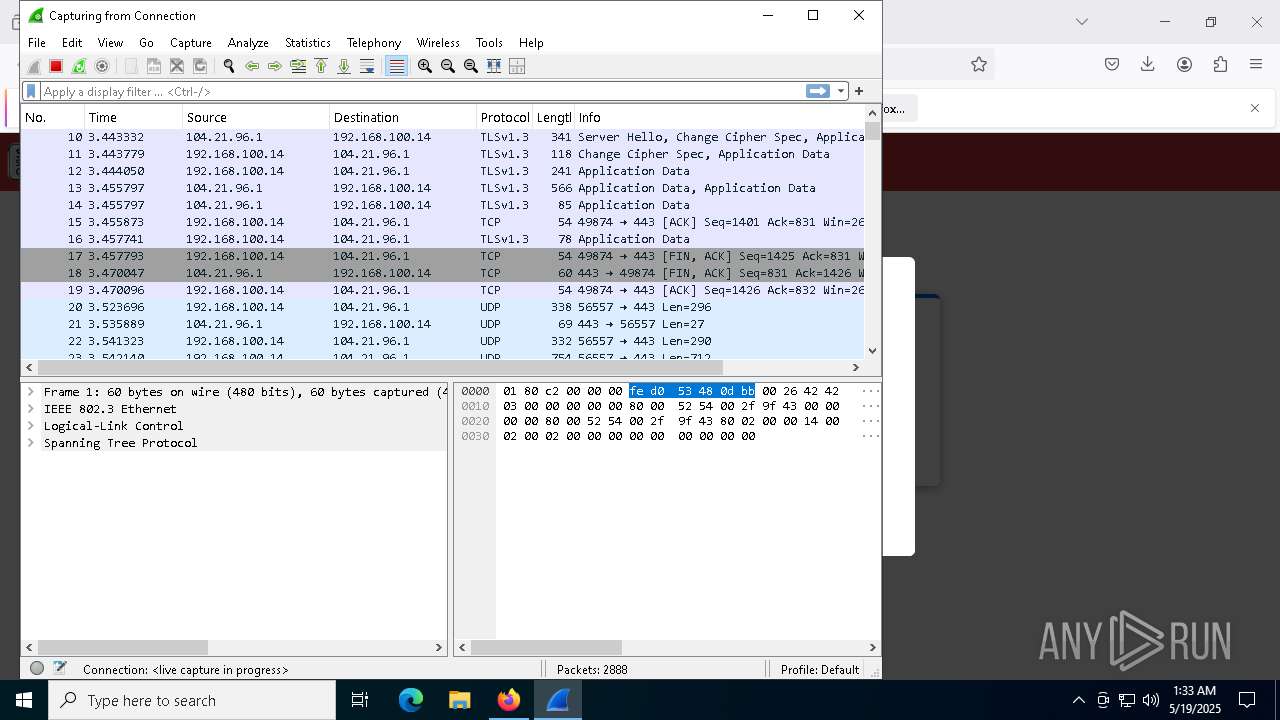
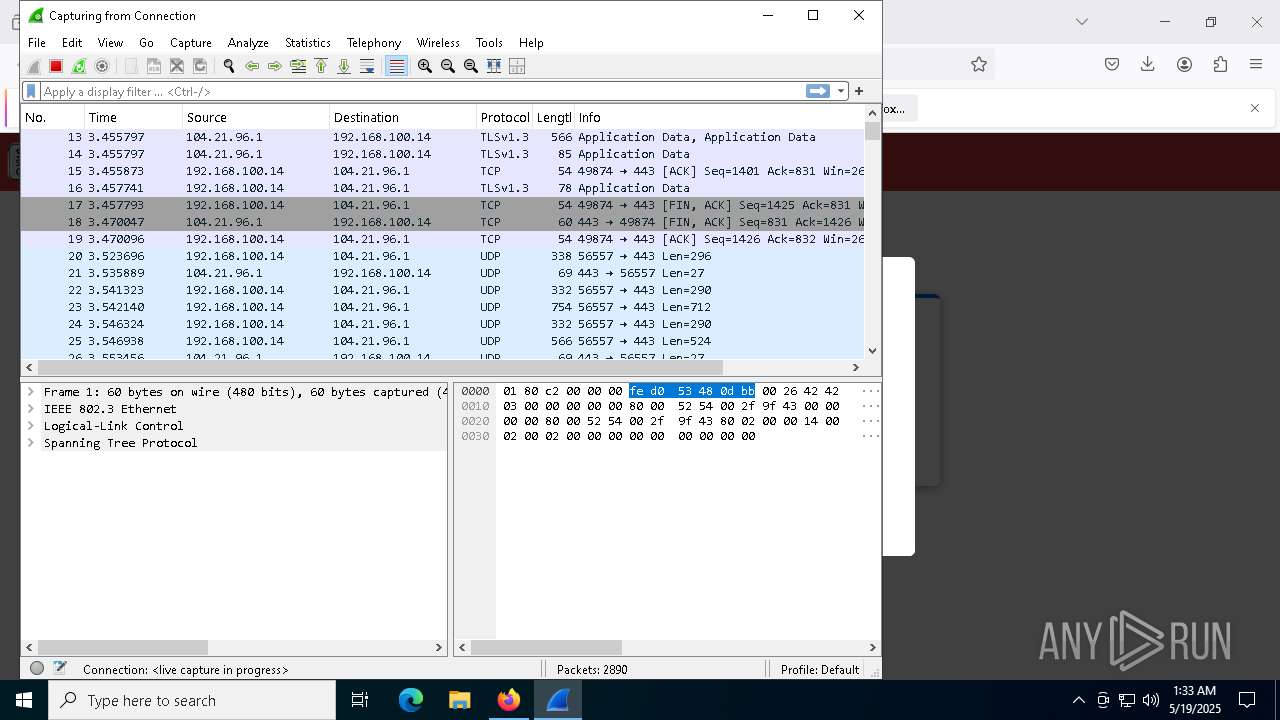
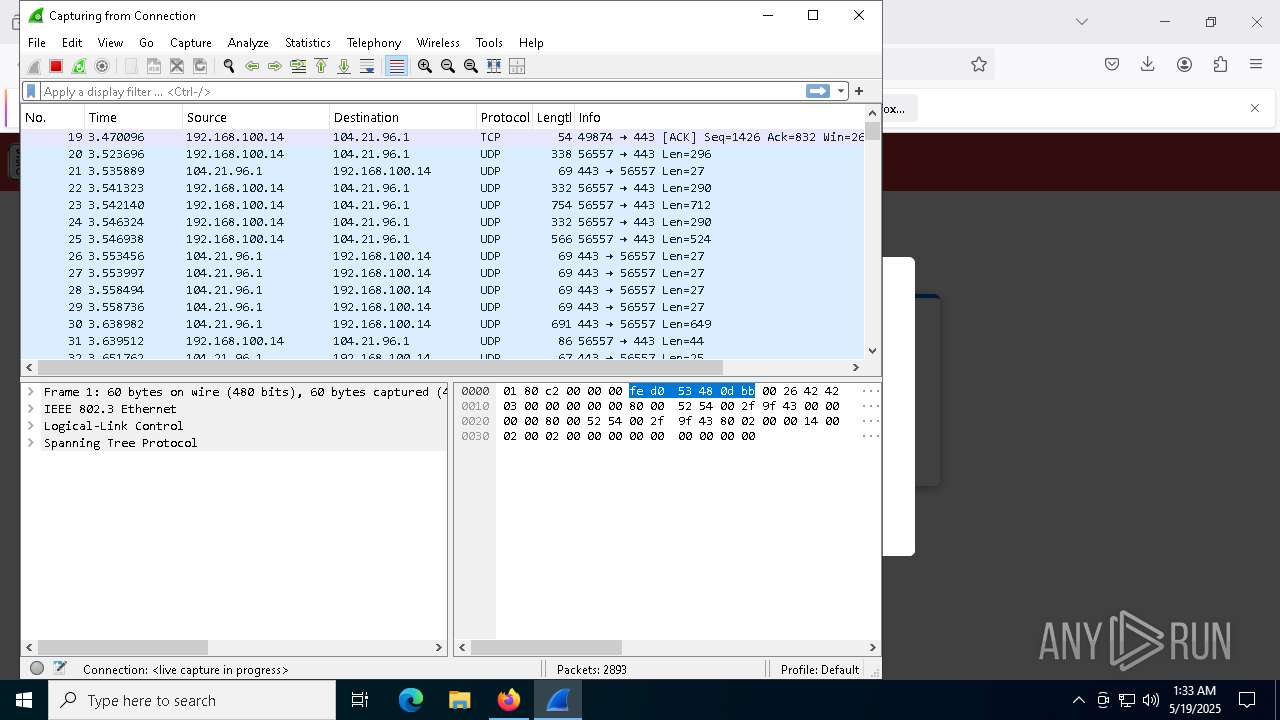
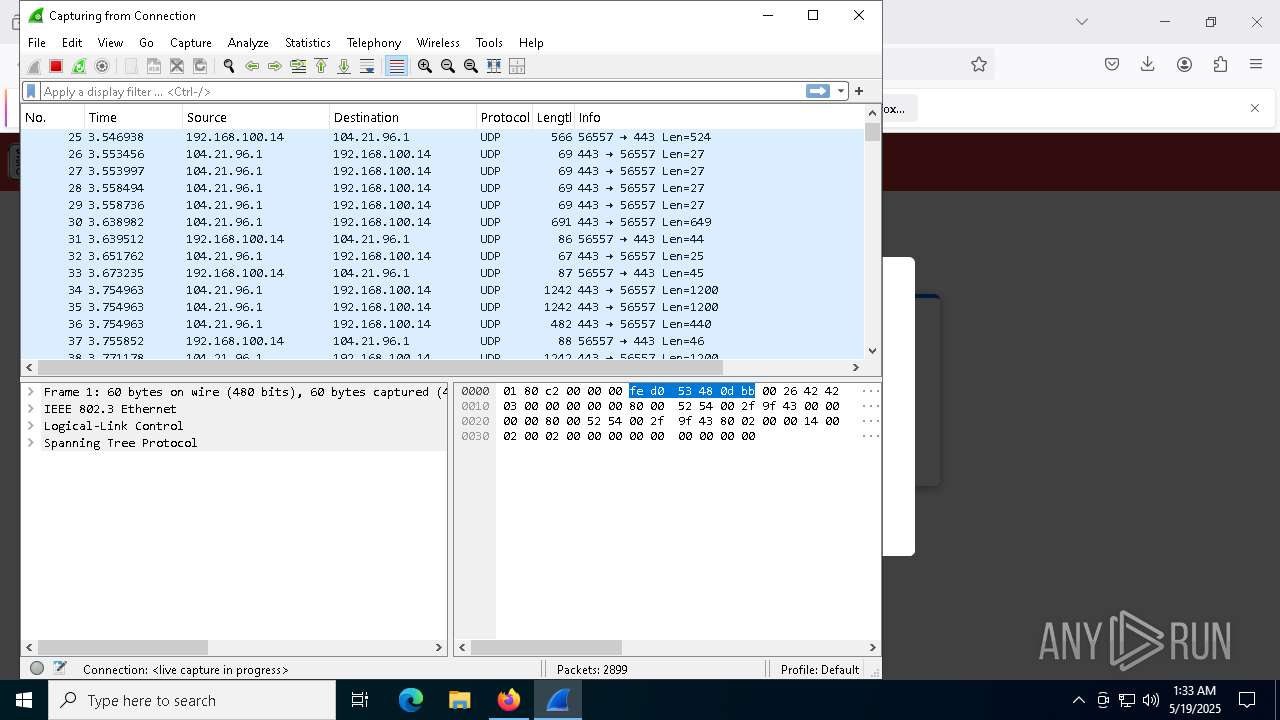
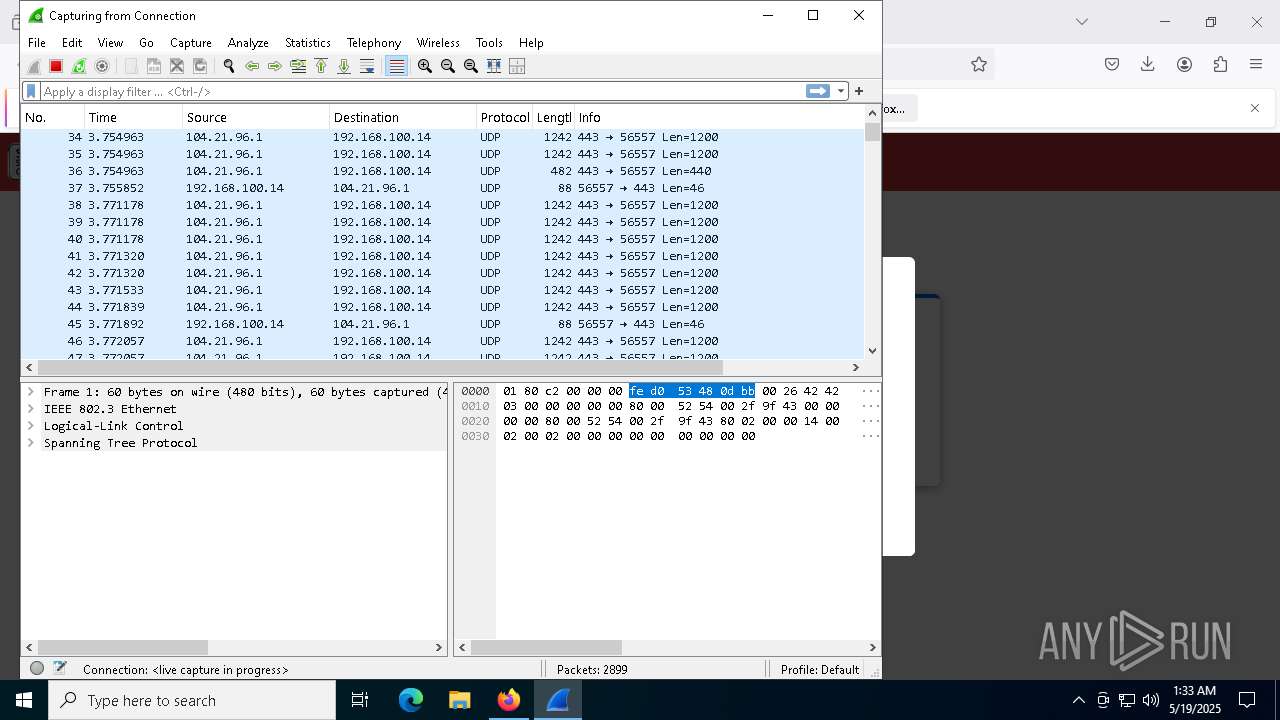
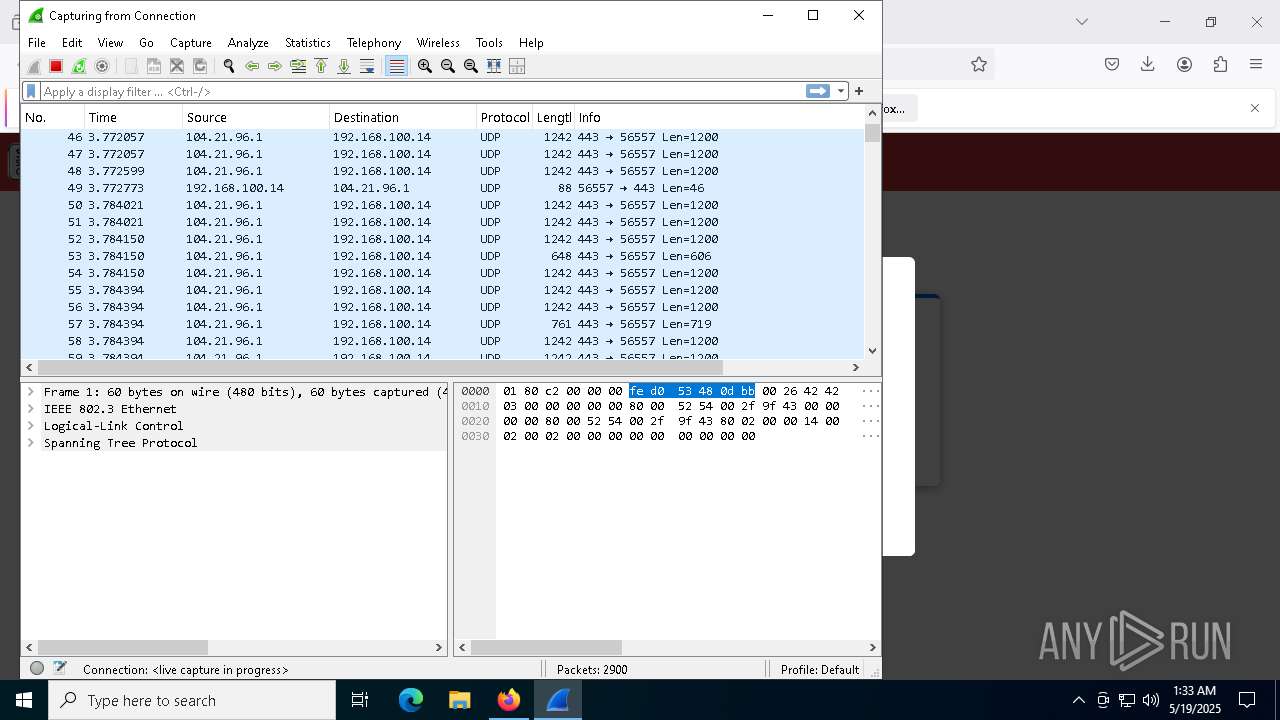
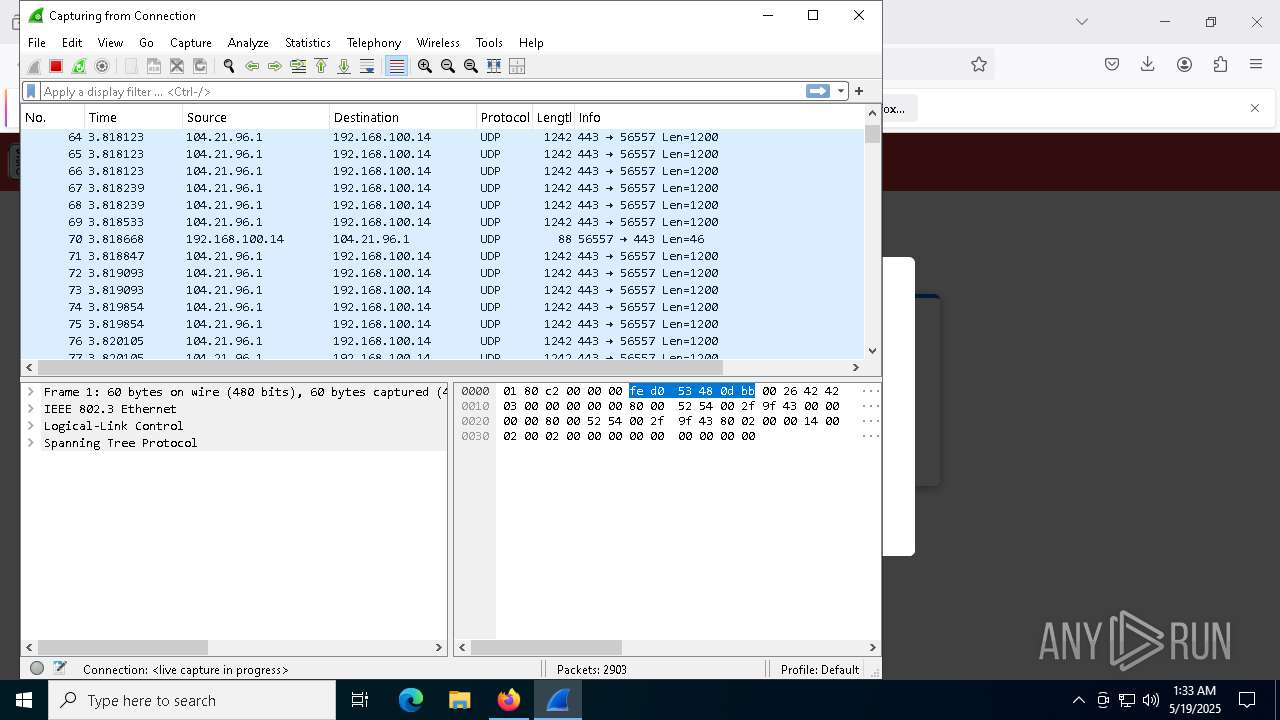
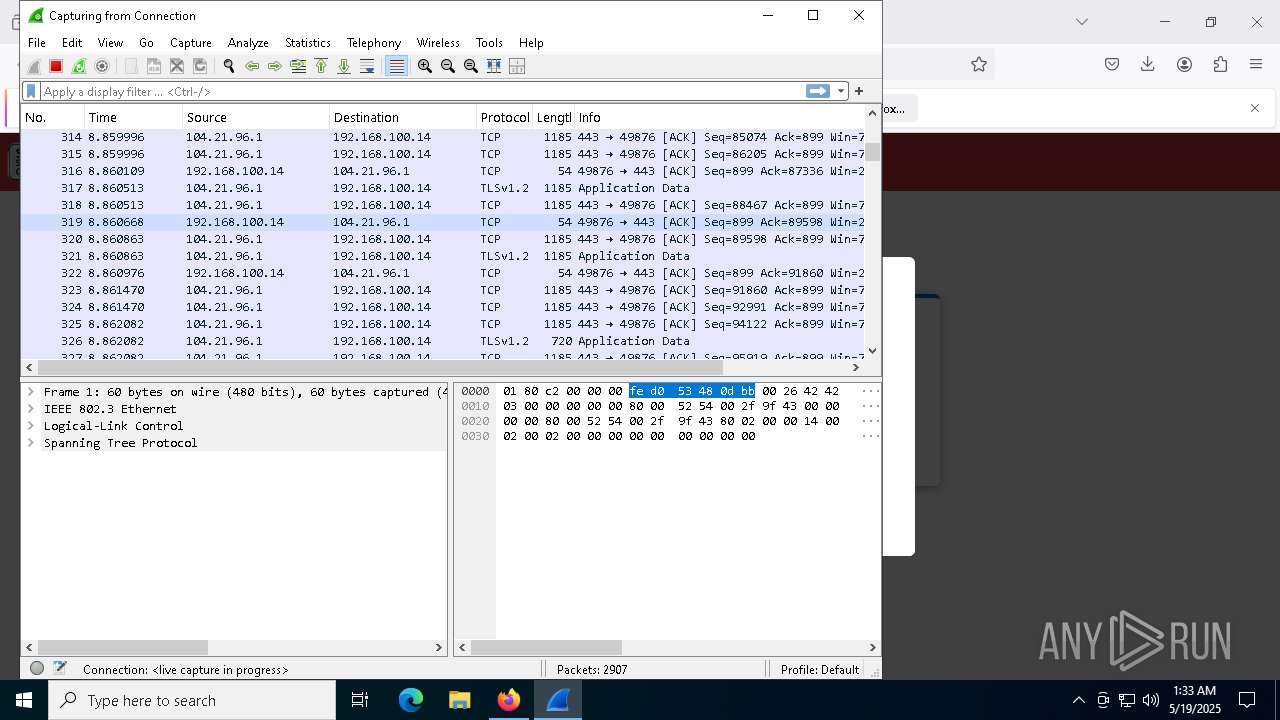
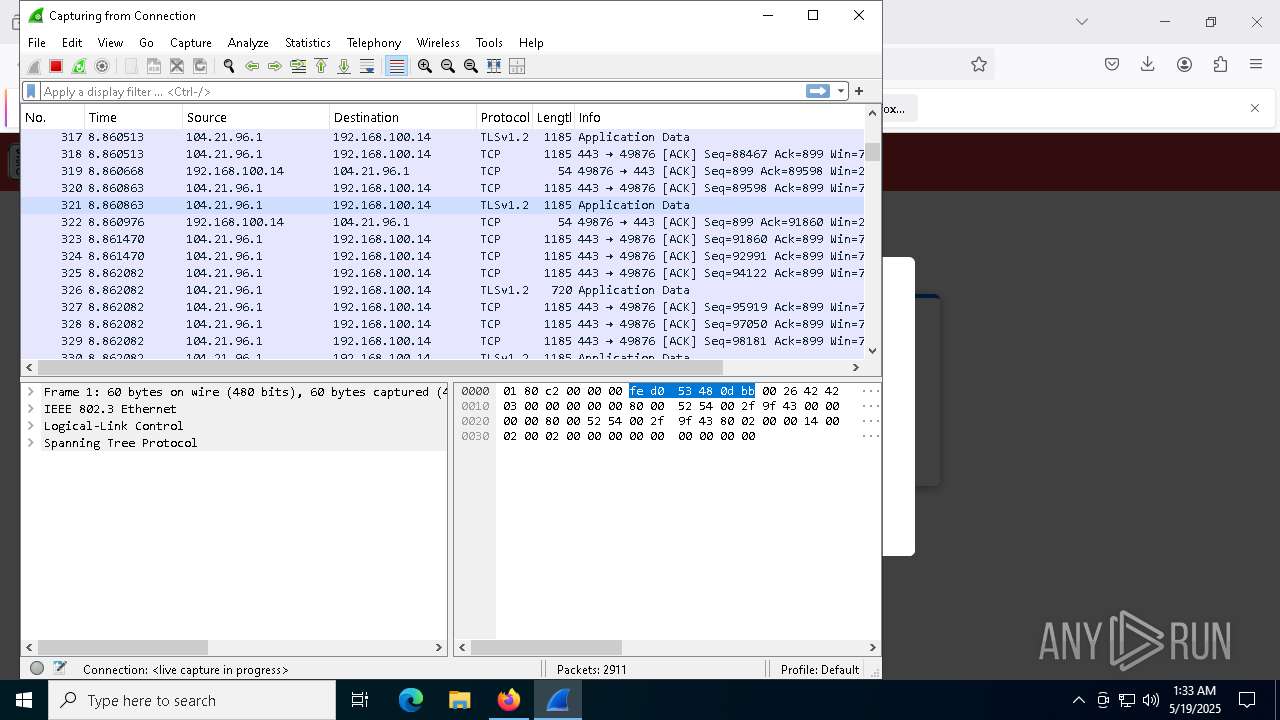
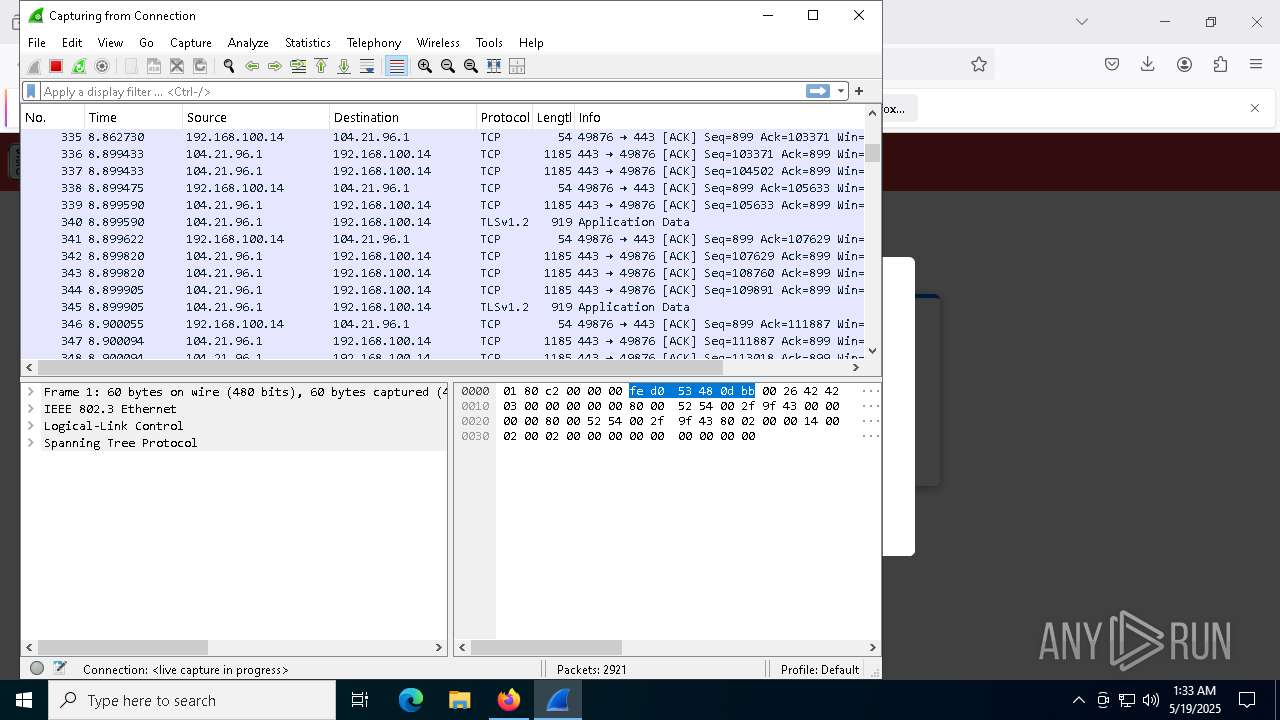
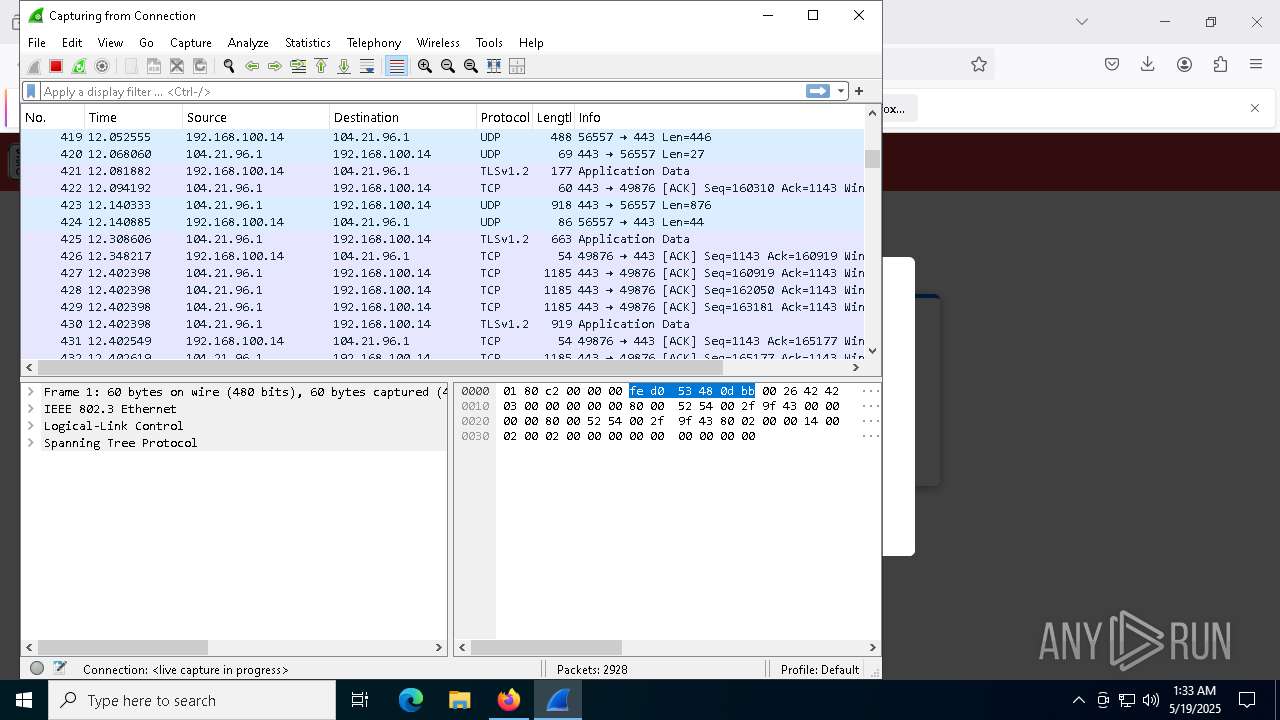
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
172
DNS requests
182
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2384 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2384 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
2384 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2384 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2384 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
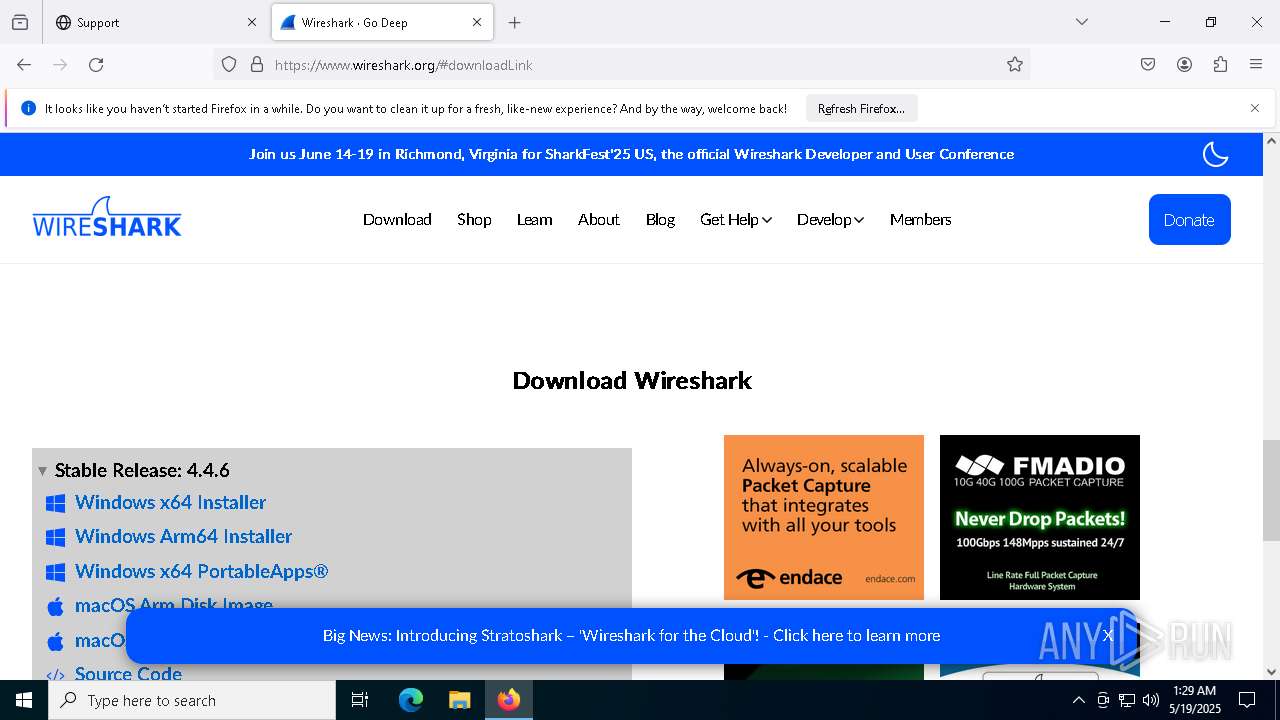
2384 | firefox.exe | GET | 301 | 104.21.96.1:80 | http://jnhelp.top/ | unknown | — | — | malicious |
2384 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2384 | firefox.exe | 104.21.96.1:80 | jnhelp.top | CLOUDFLARENET | — | malicious |
2384 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2384 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
jnhelp.top |
| malicious |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2384 | firefox.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4572 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|