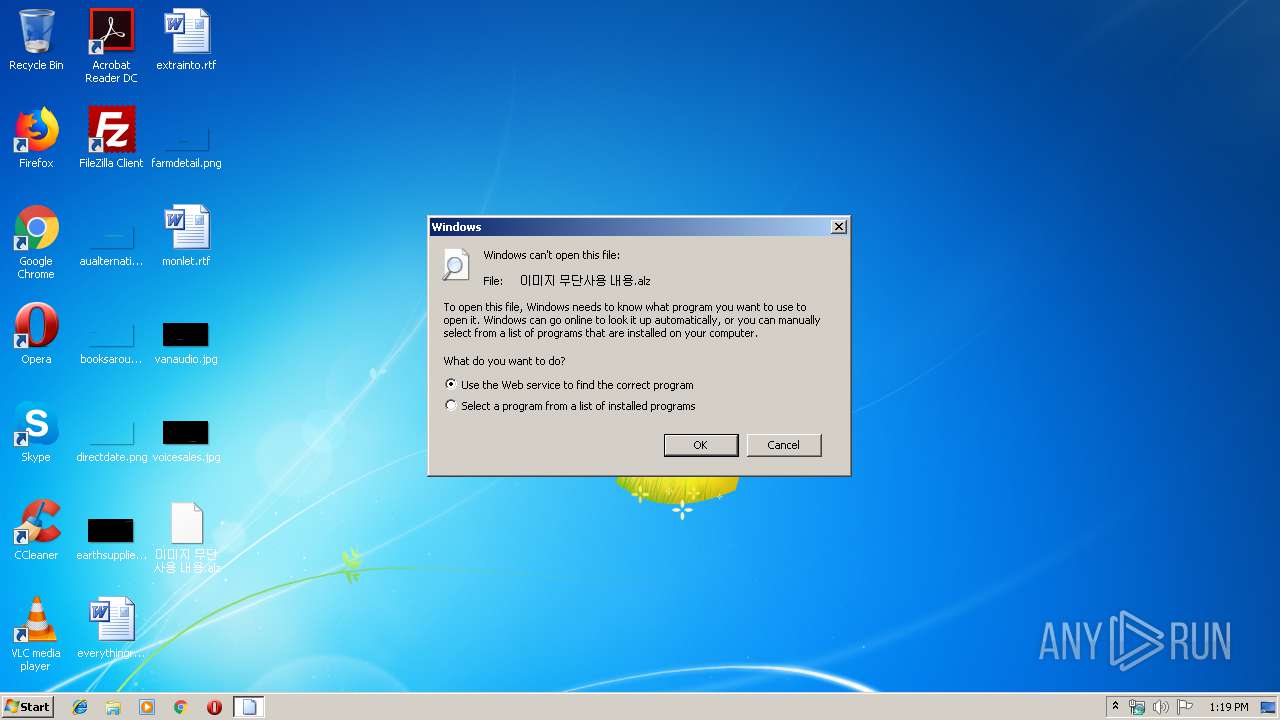
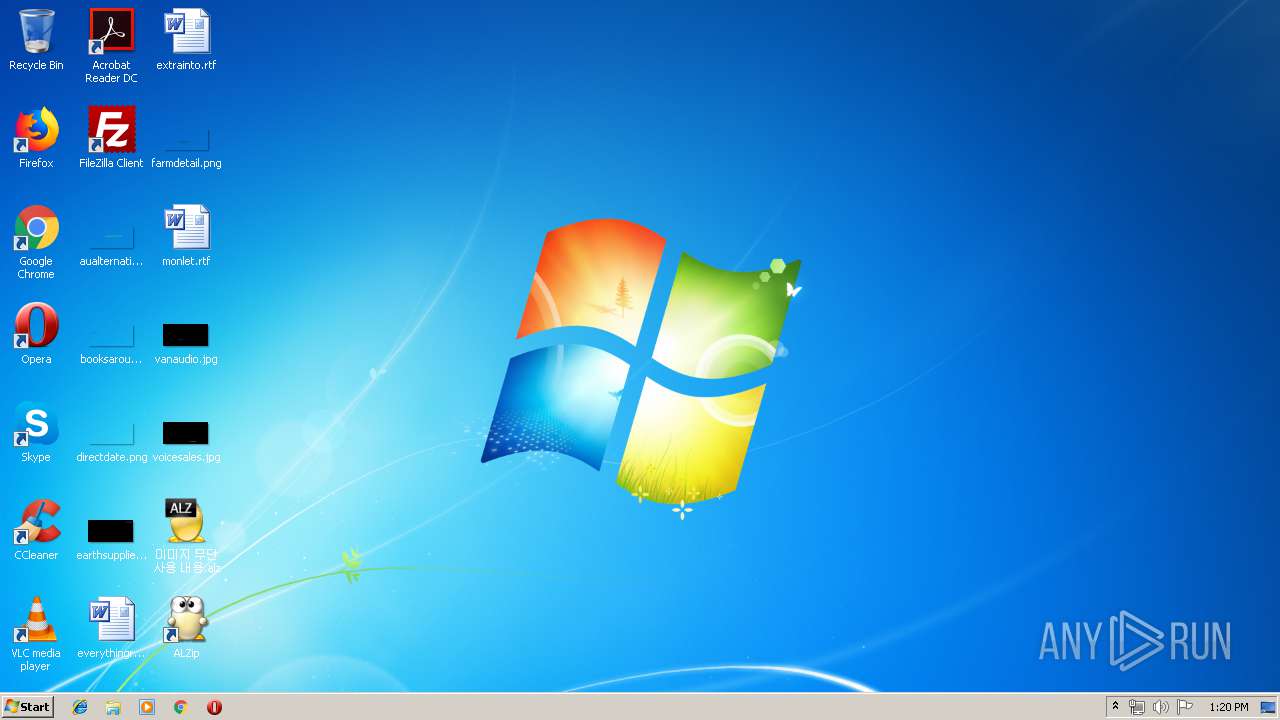
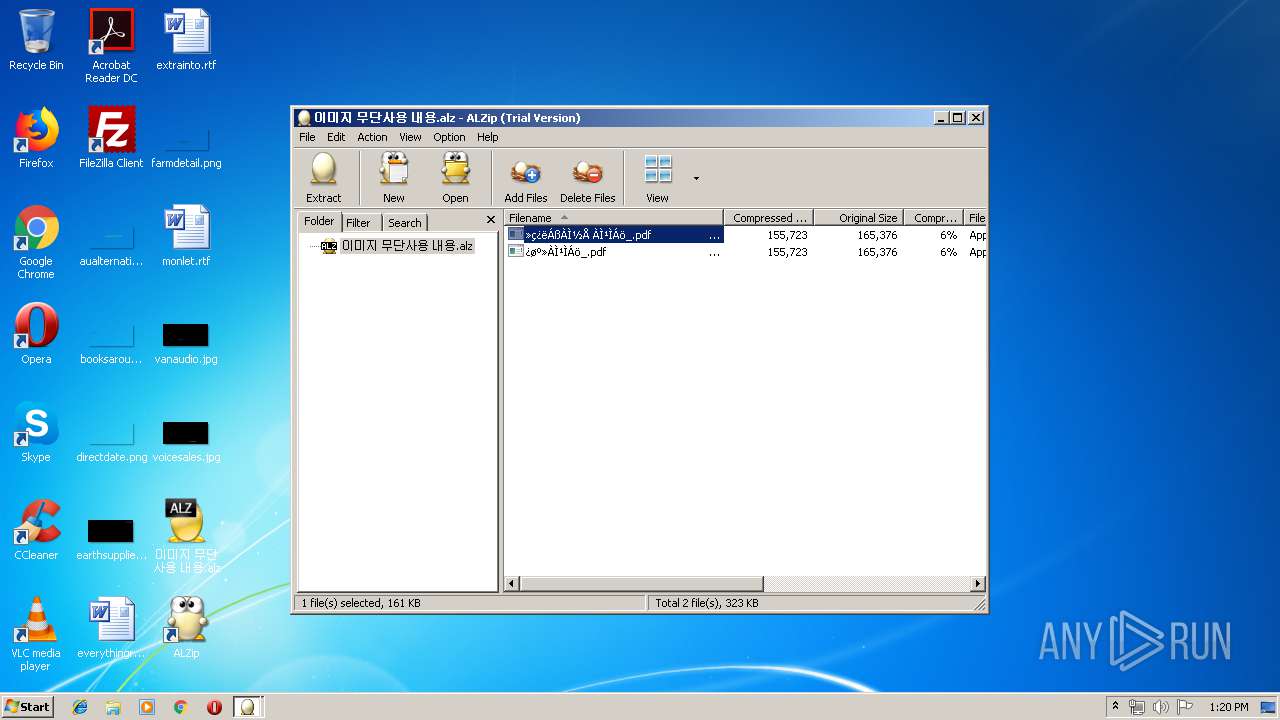
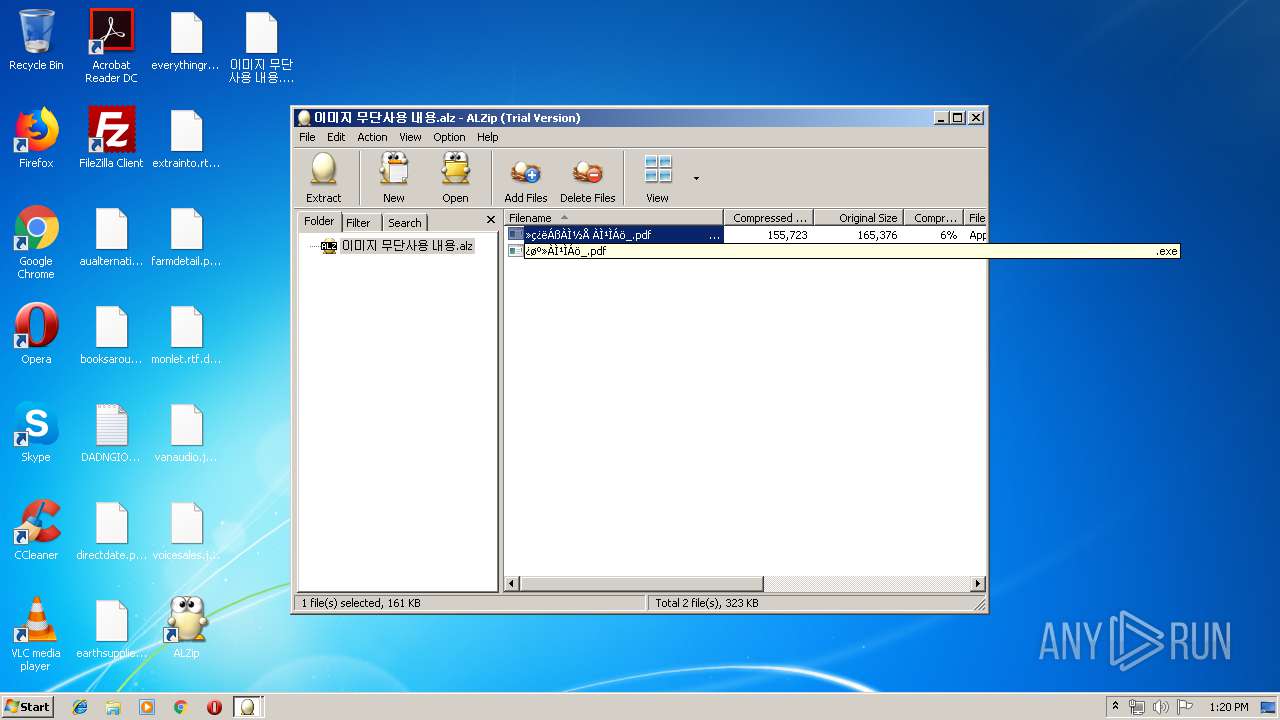
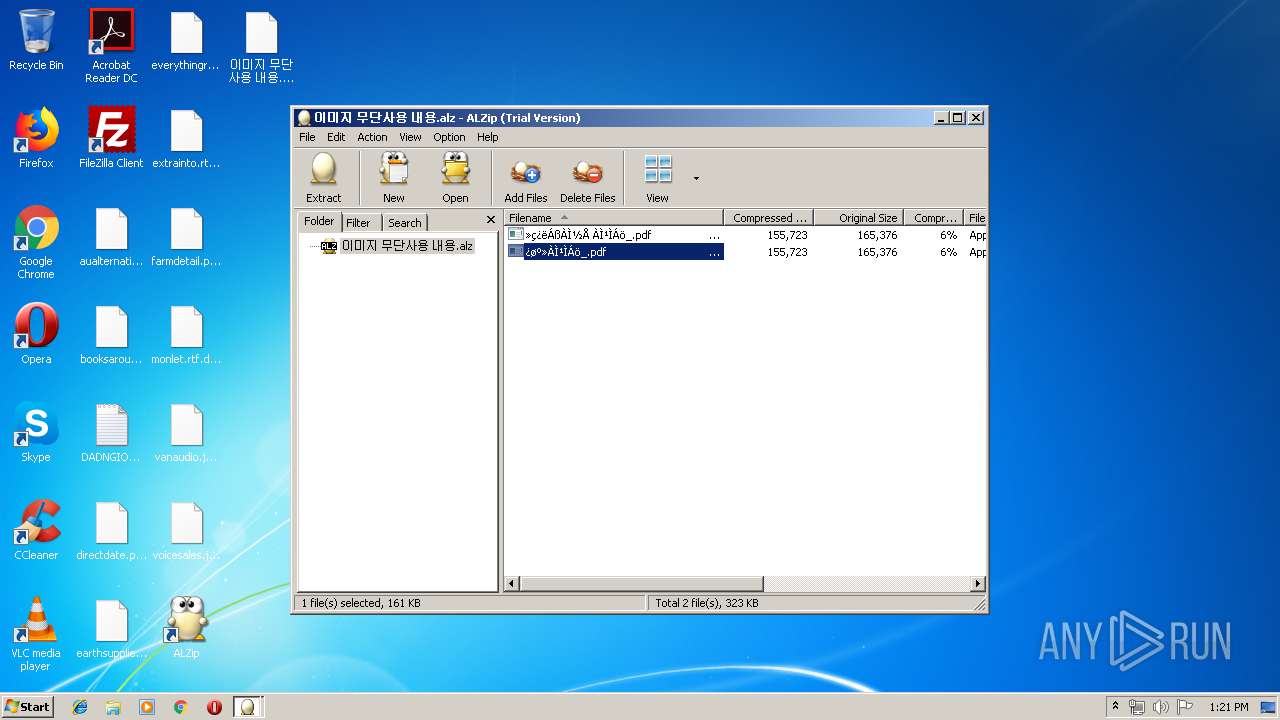
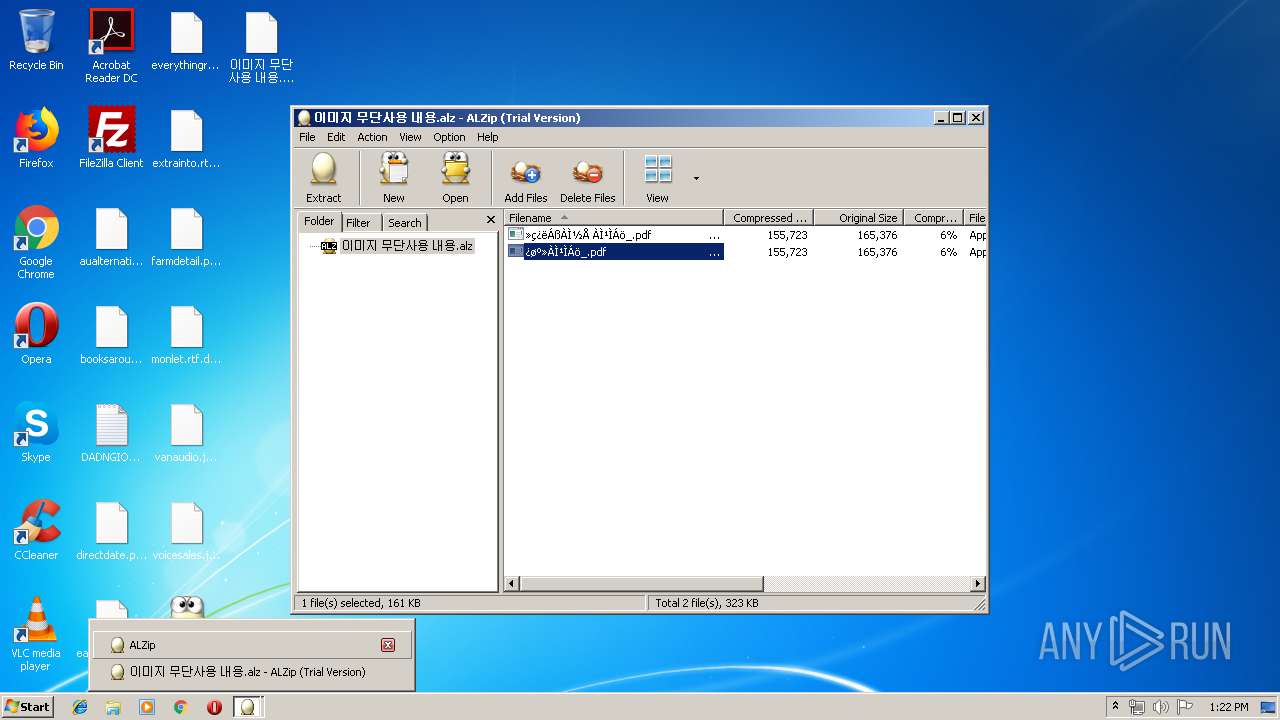
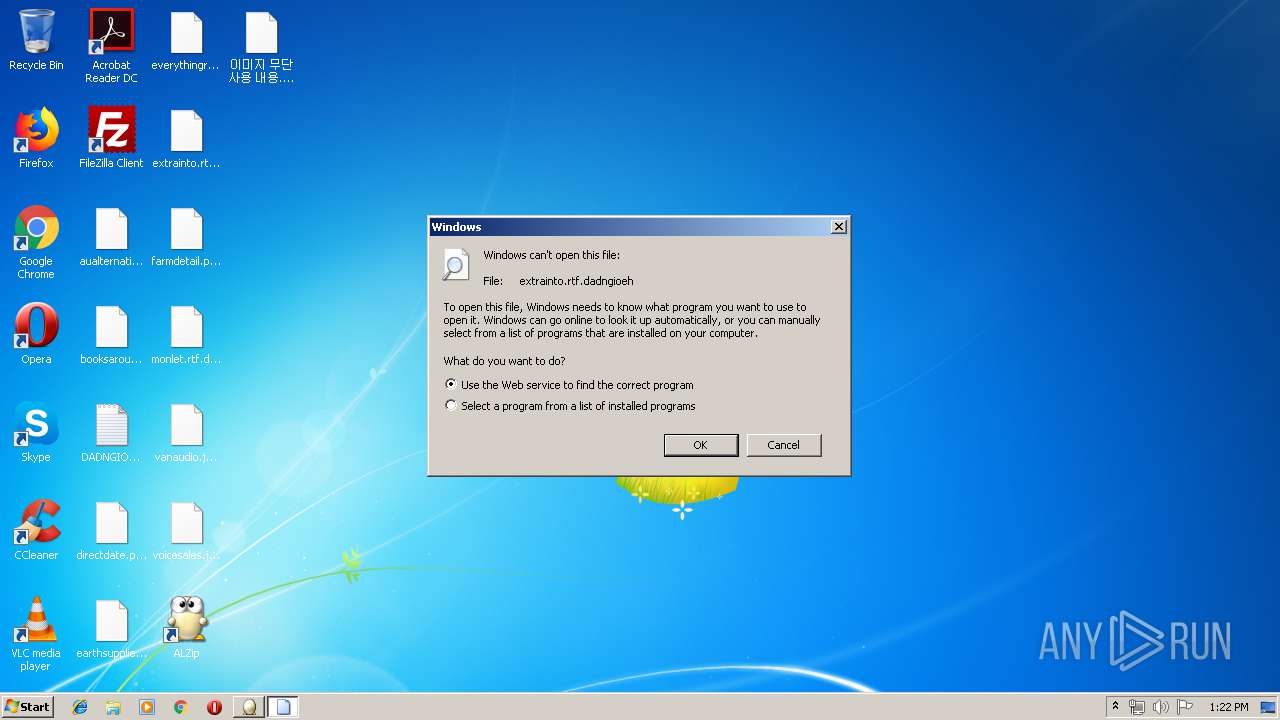
| File name: | 이미지 무단사용 내용.alz |
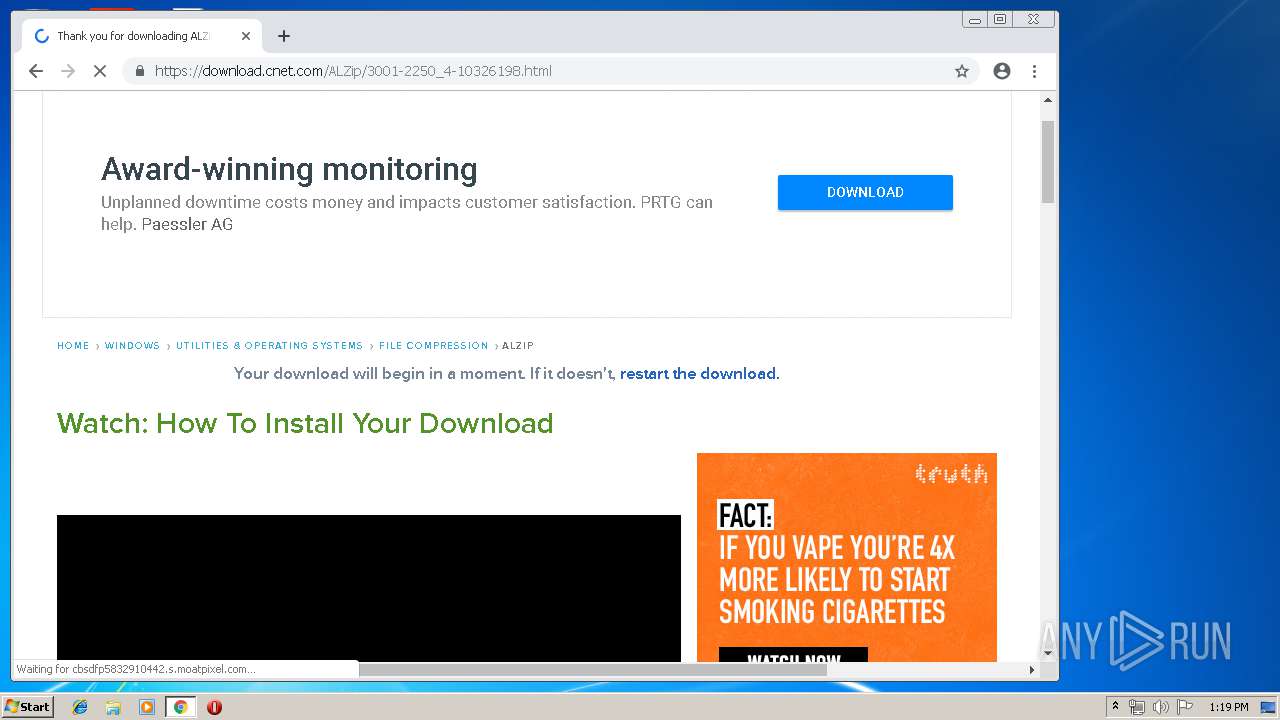
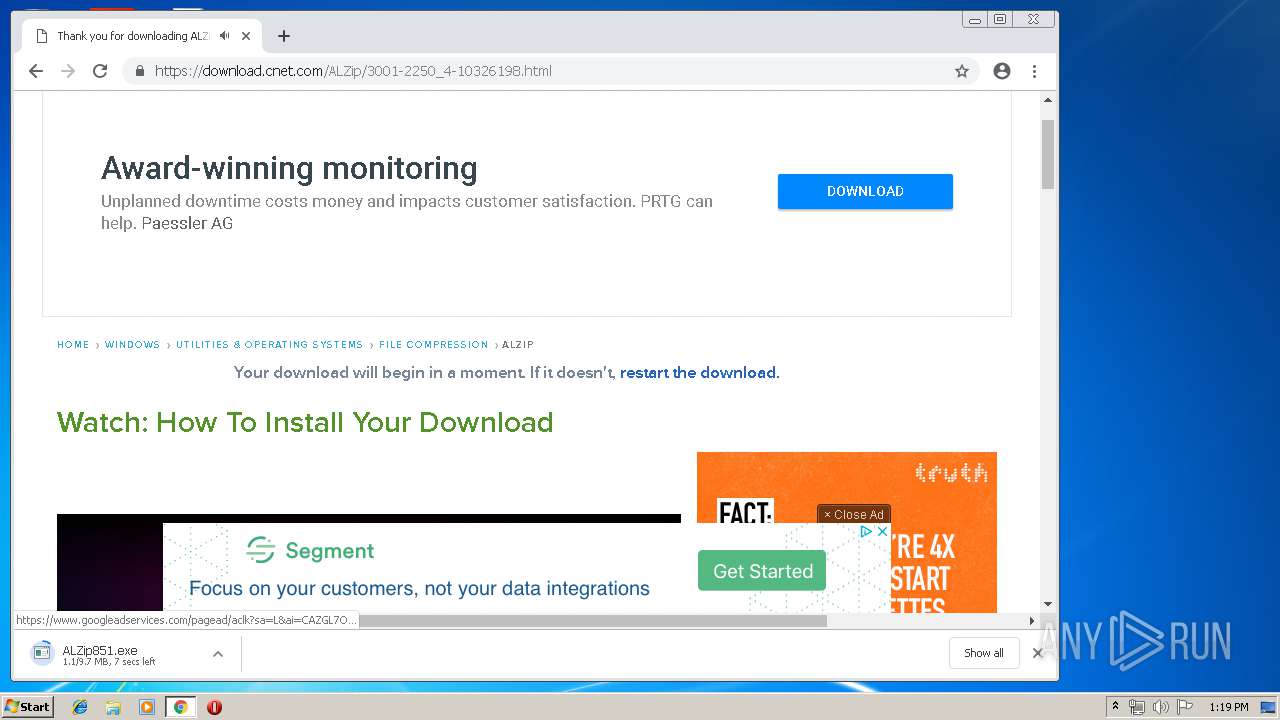
| Full analysis: | https://app.any.run/tasks/97597861-1c14-4362-9dd4-f5a9f909e914 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | March 22, 2019, 13:18:58 |
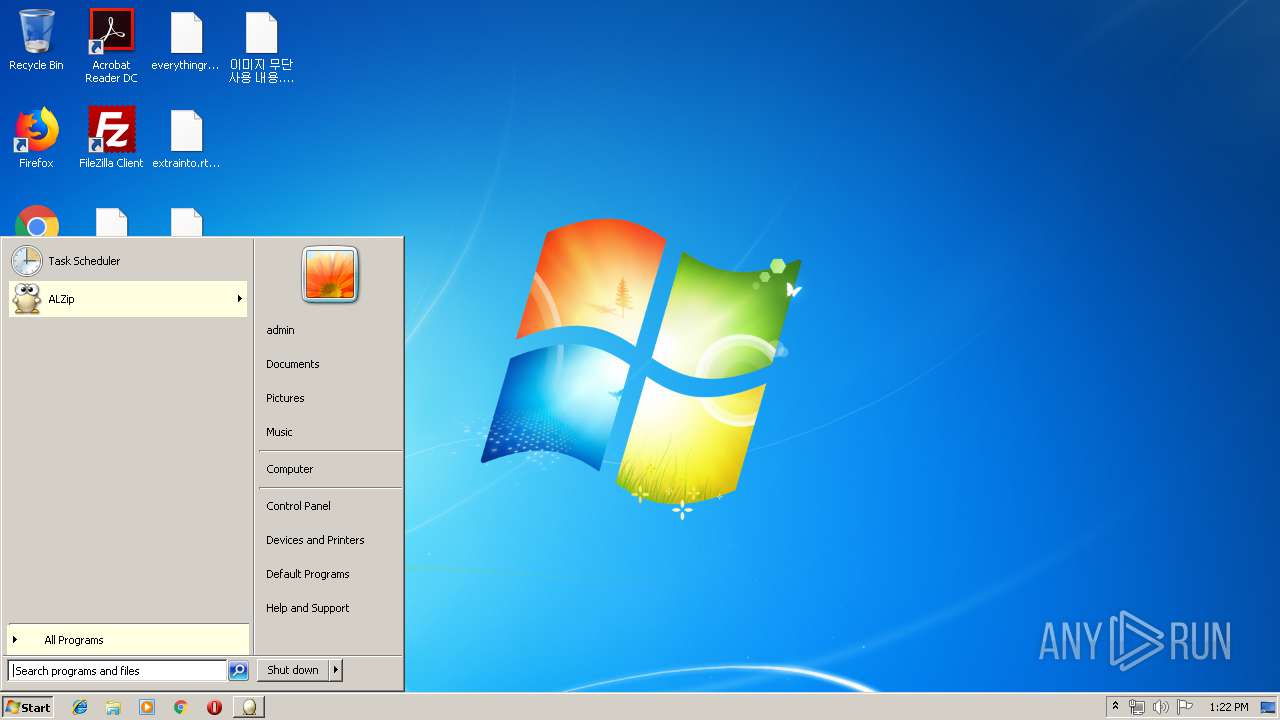
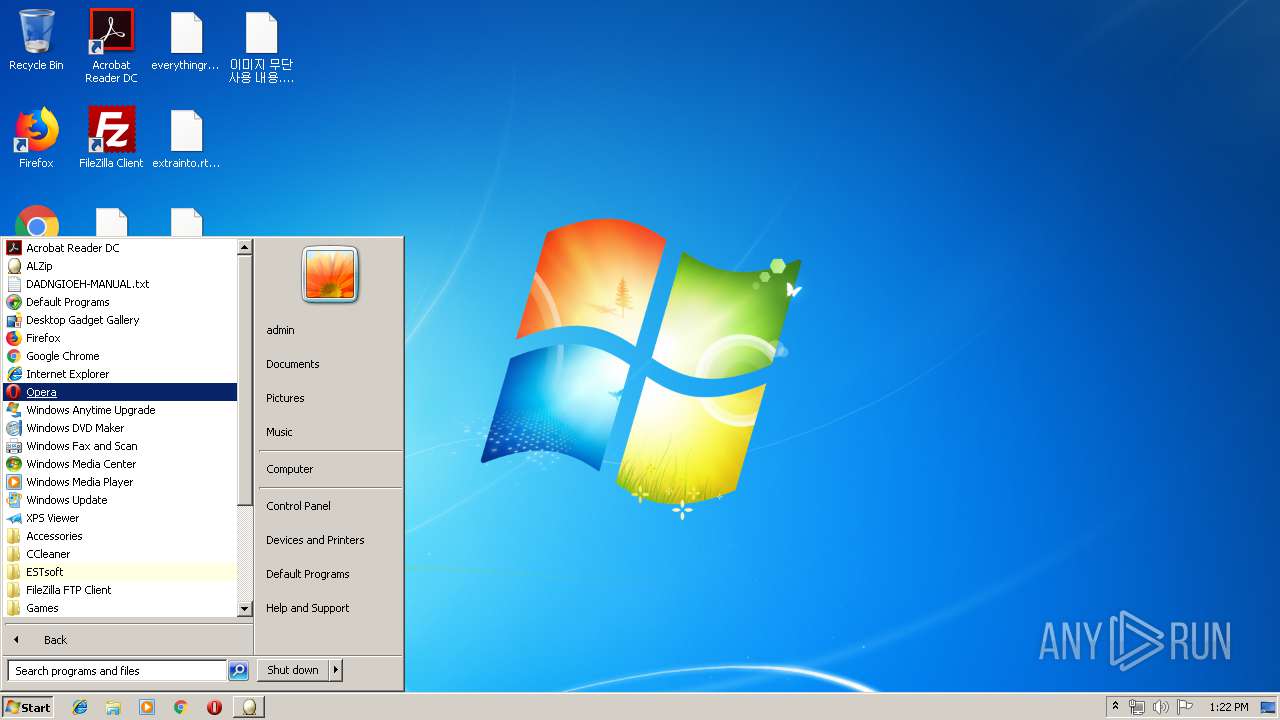
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 4750C2CB9FA898107A233CE9B94B1572 |
| SHA1: | 68025D73DD51EAF889BAC0444205B5D0E4A0075C |
| SHA256: | E1E0885BC8D30C9BFB6A86C5983ADA67BB5572665FCA86FD676FA8BD646C02C6 |
| SSDEEP: | 6144:646bIwgtdm3AsIqGA/iMOW946bIwgtdm3AsIqGA/iMOWJ:6tIwg2wsNG1MOitIwg2wsNG1MOm |
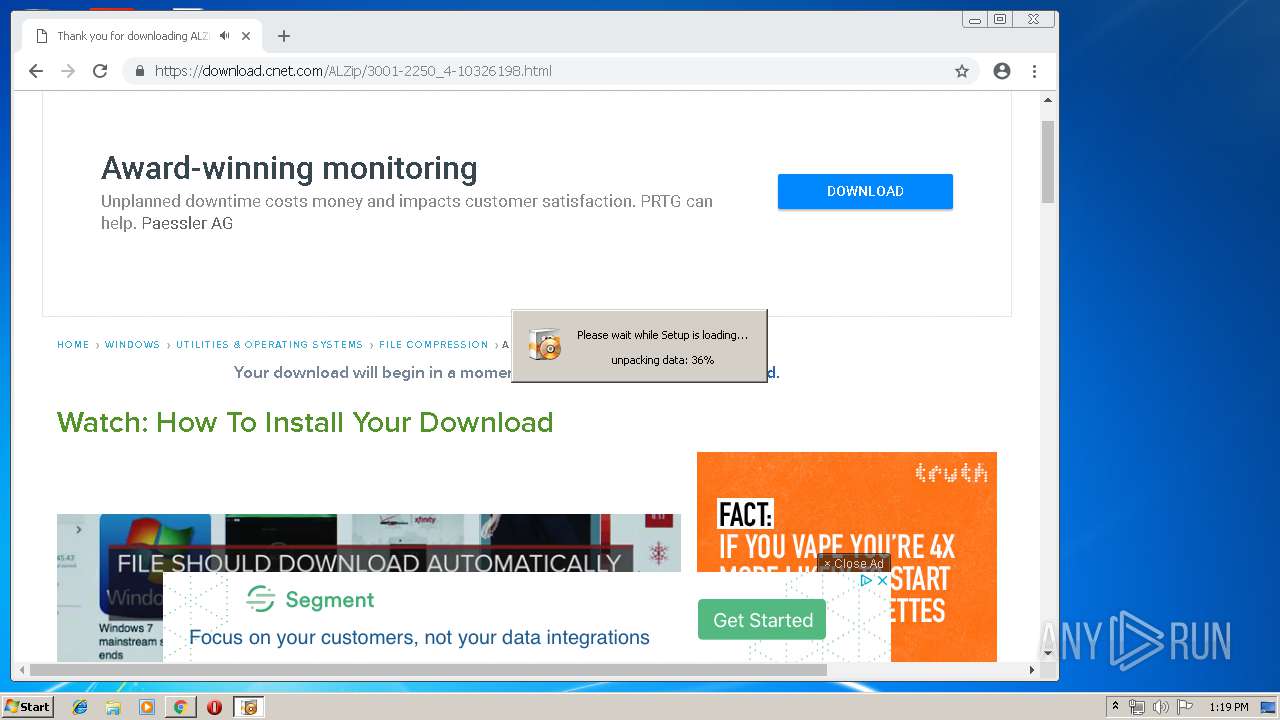
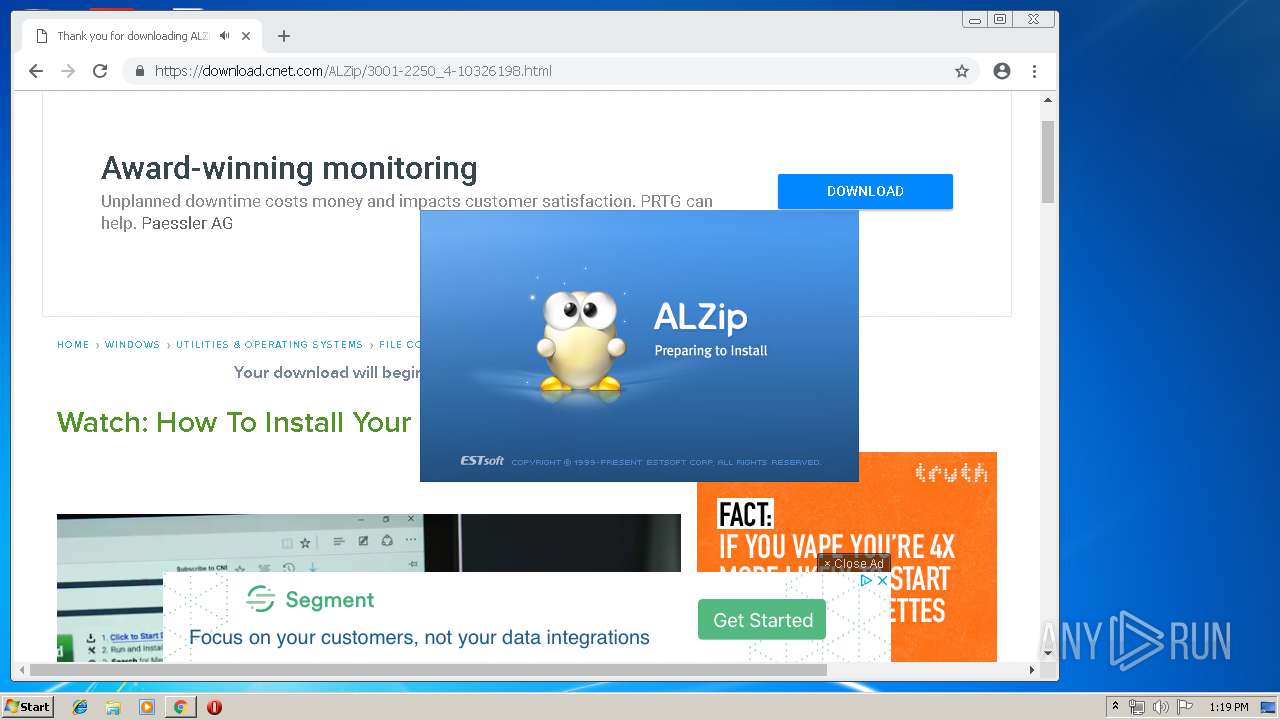
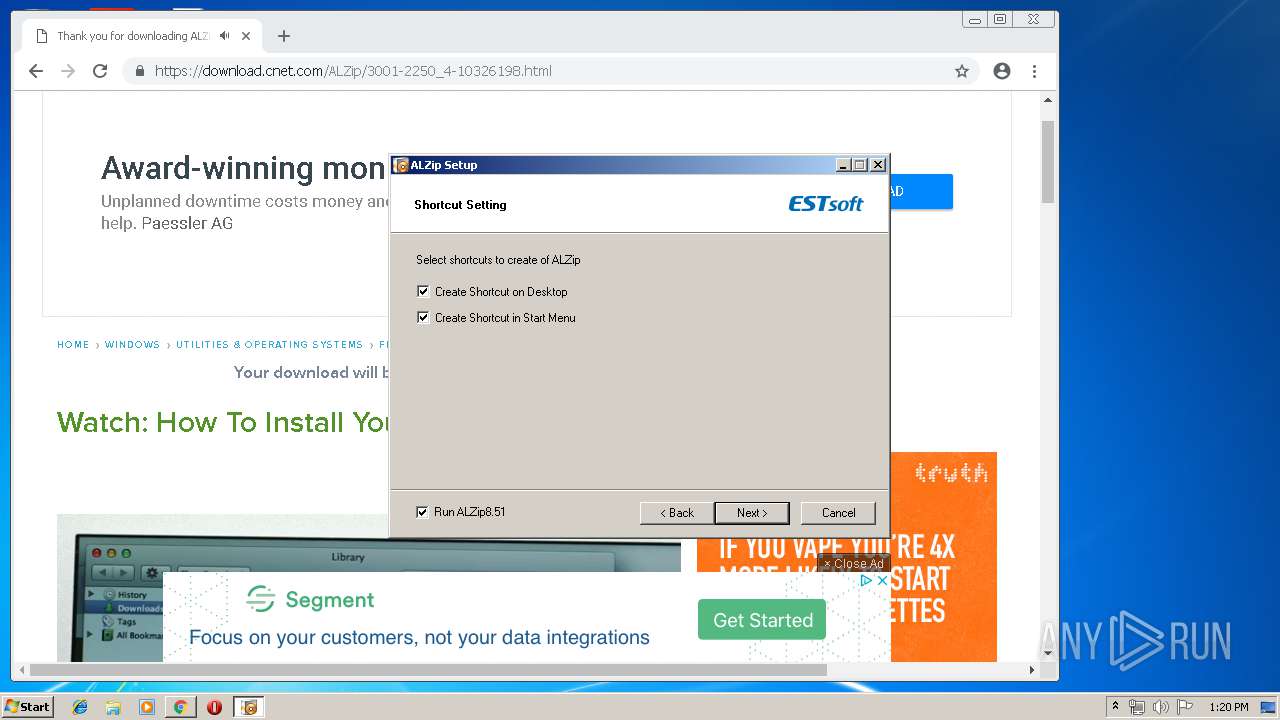
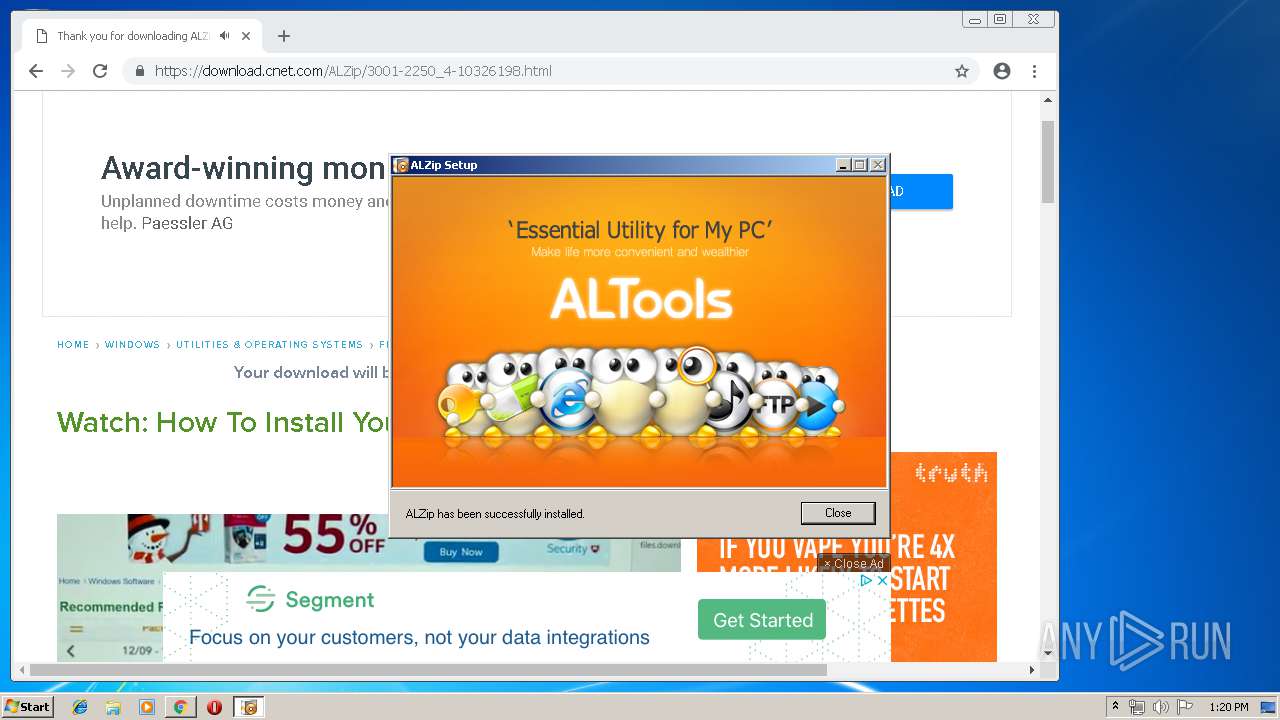
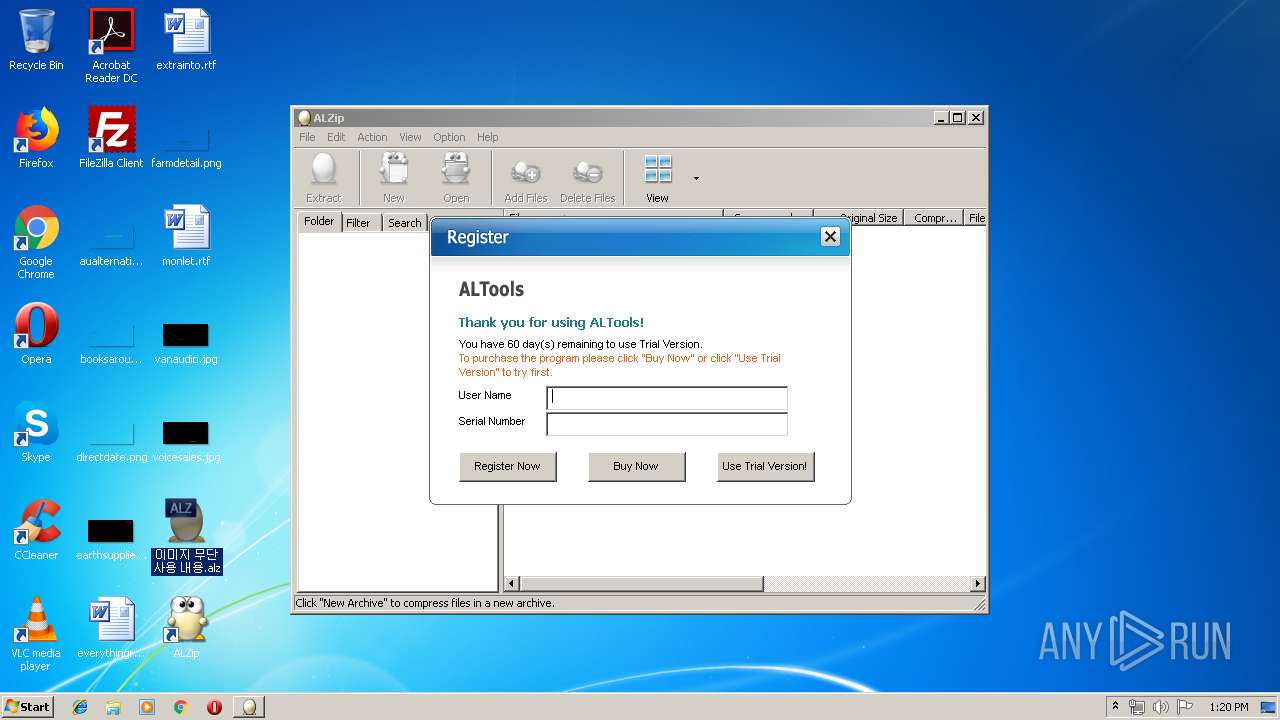
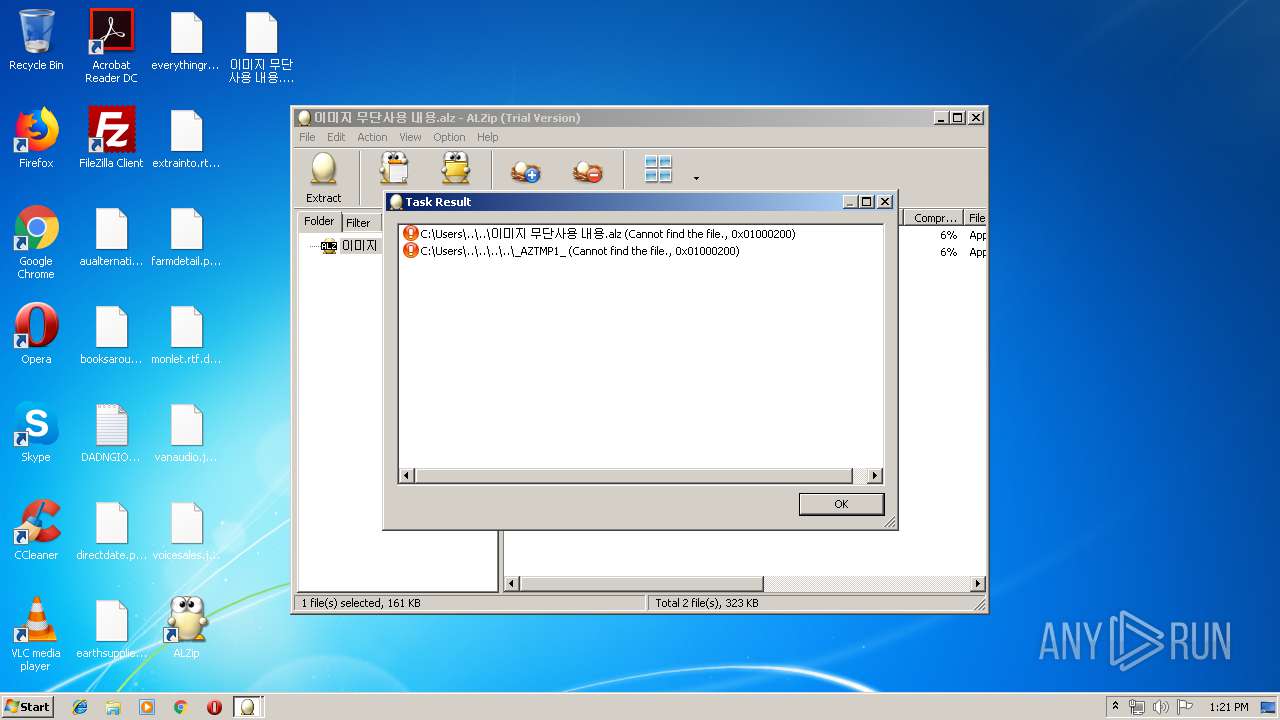
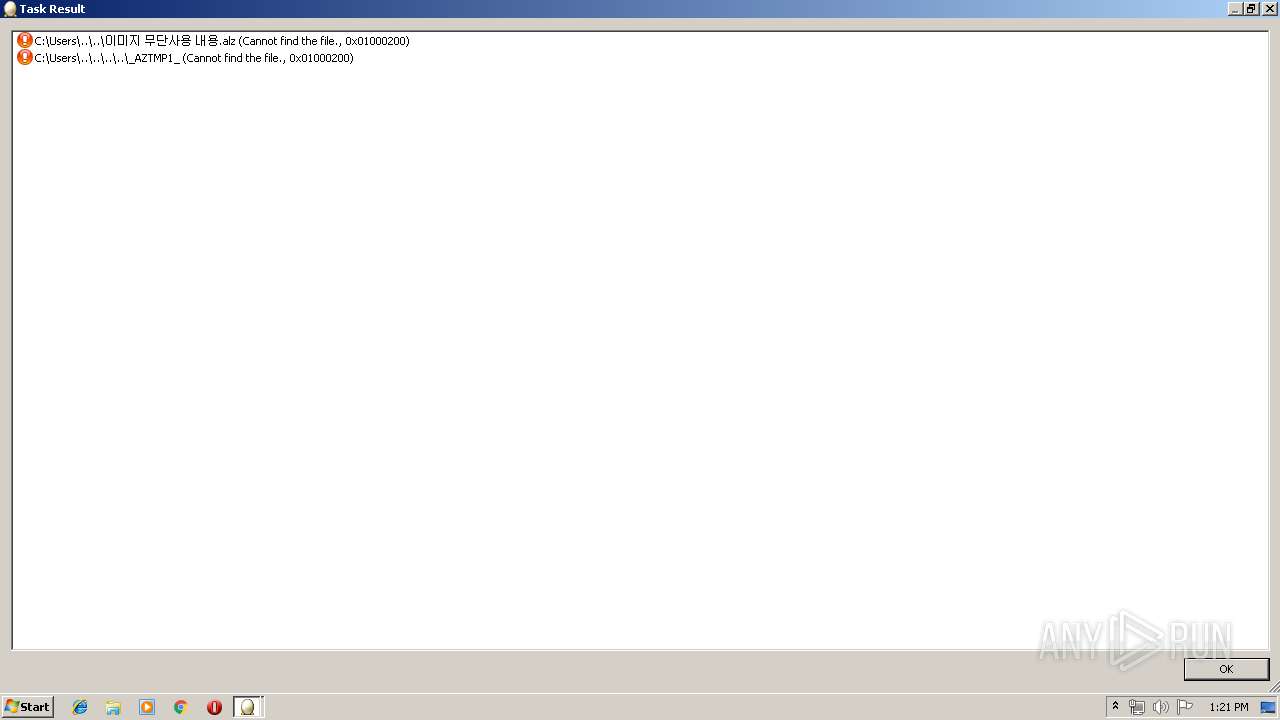
MALICIOUS
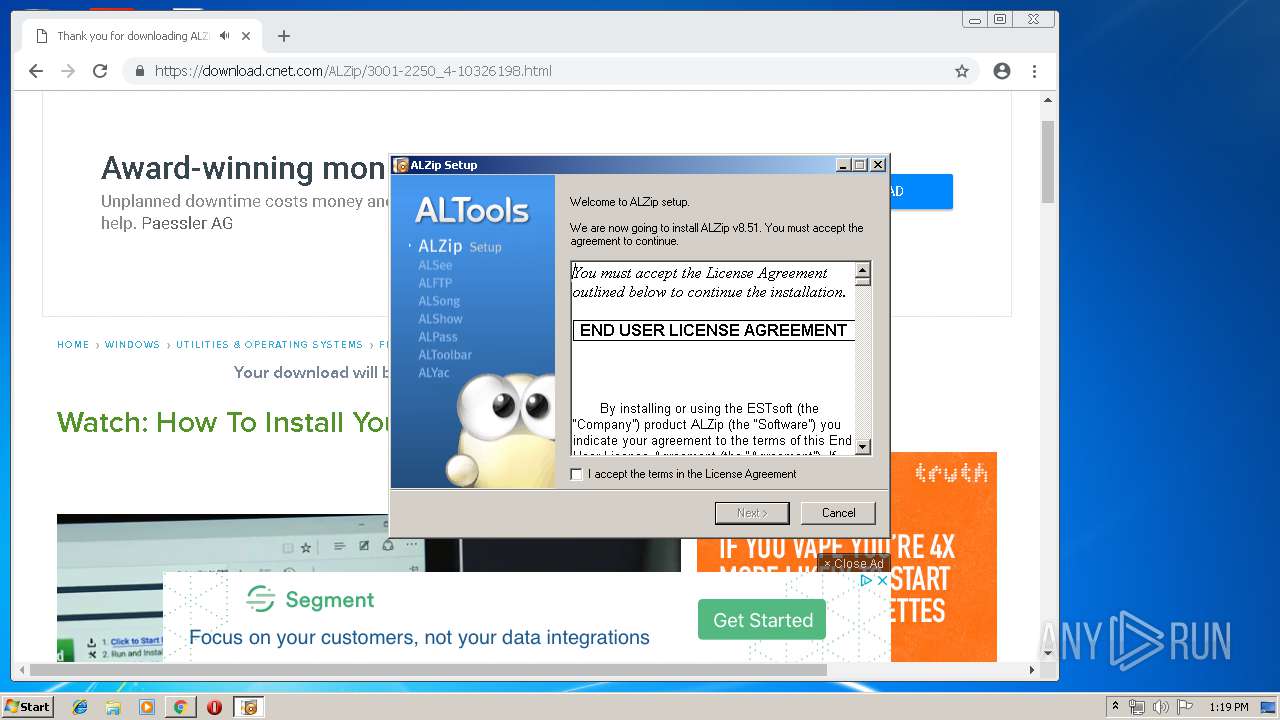
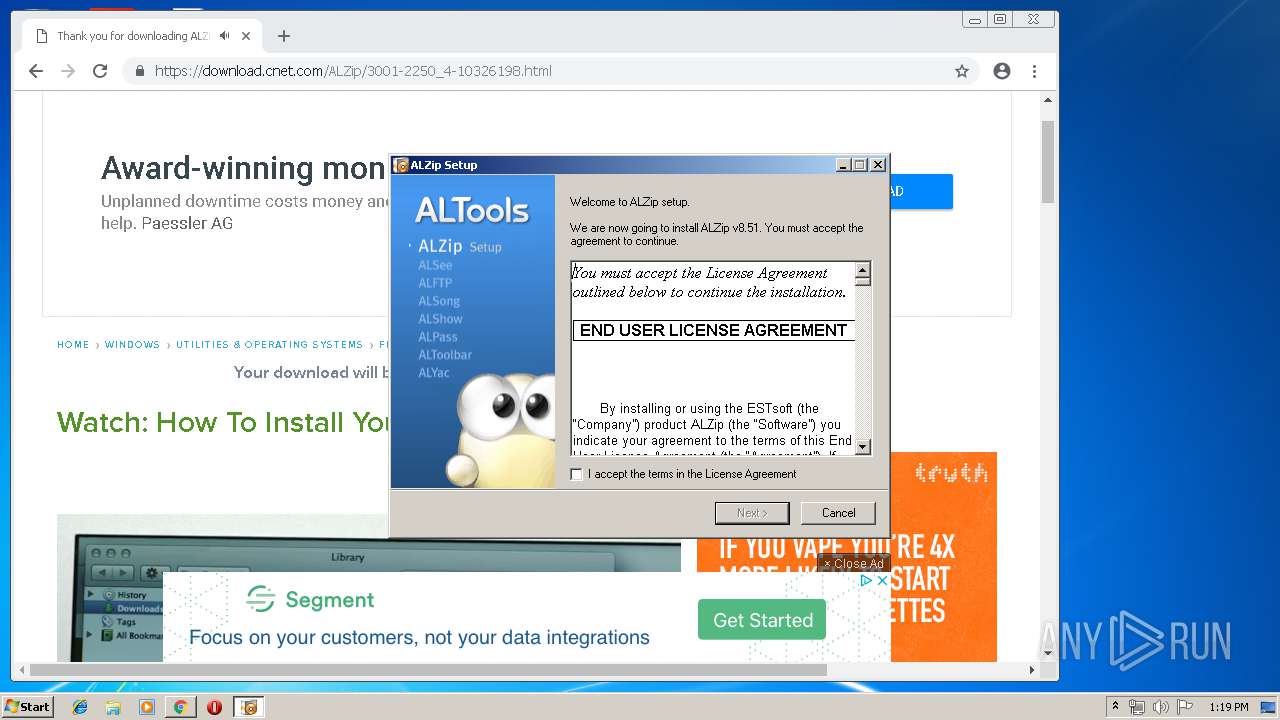
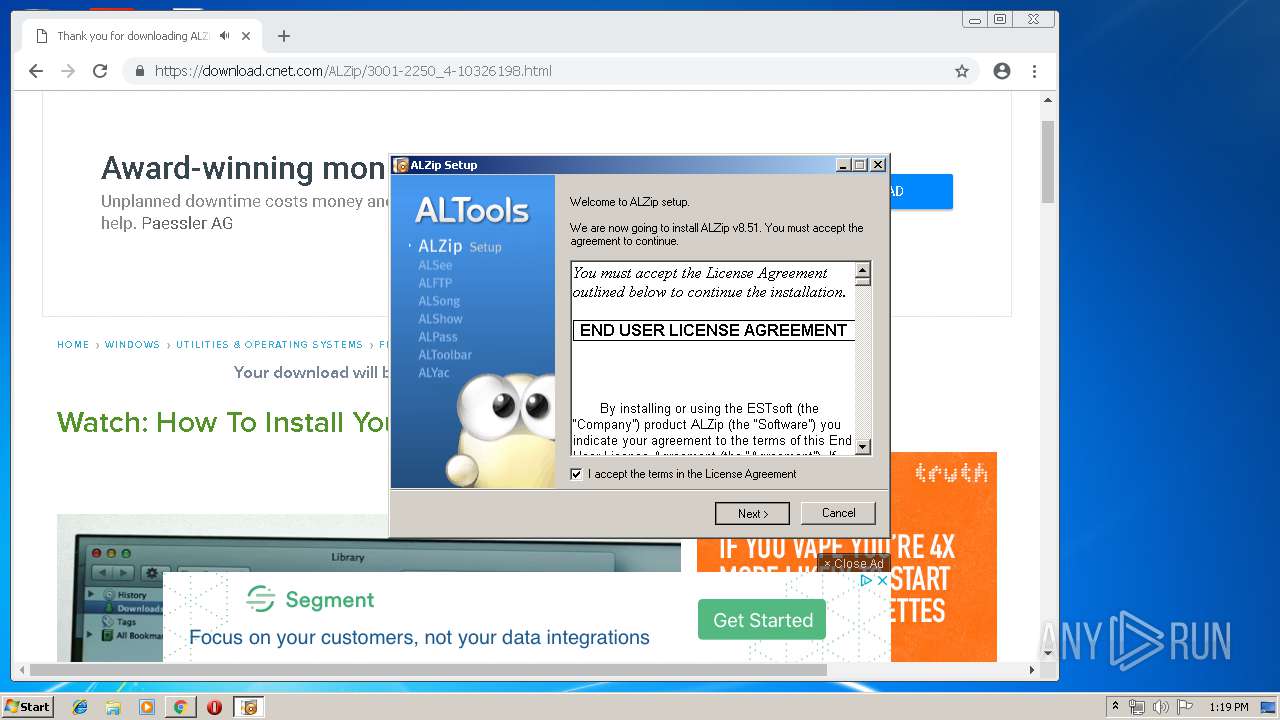
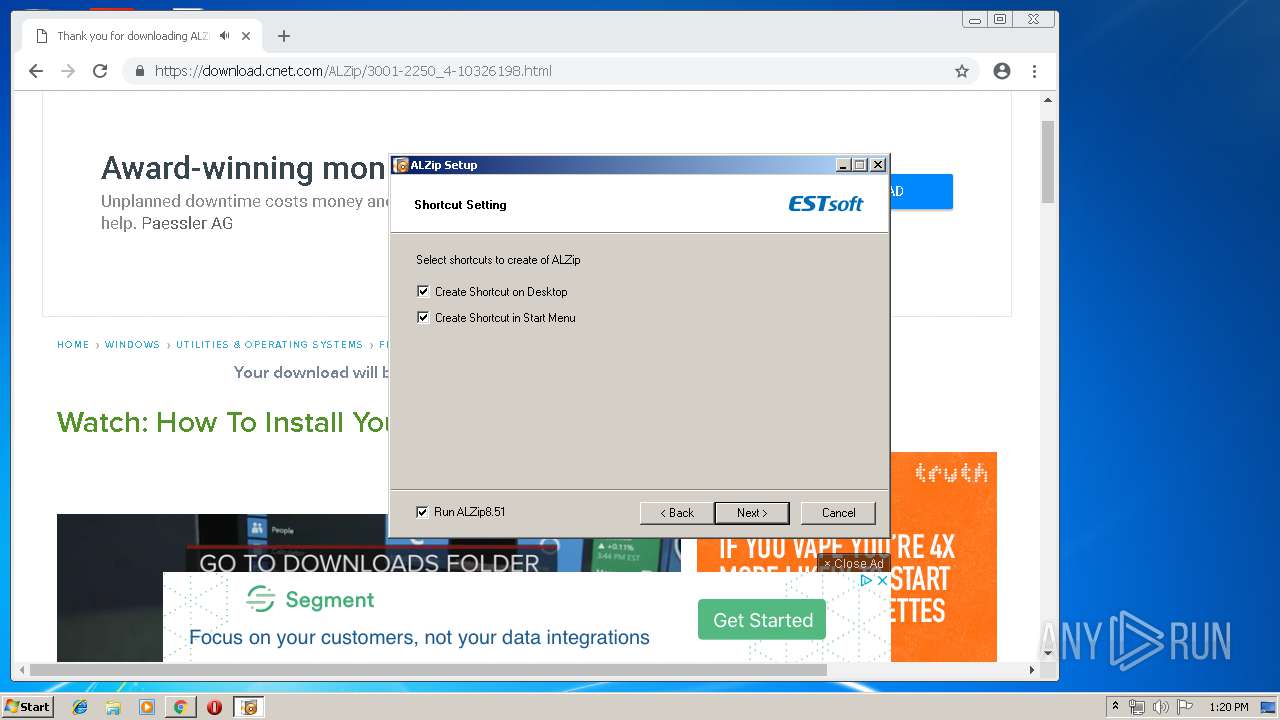
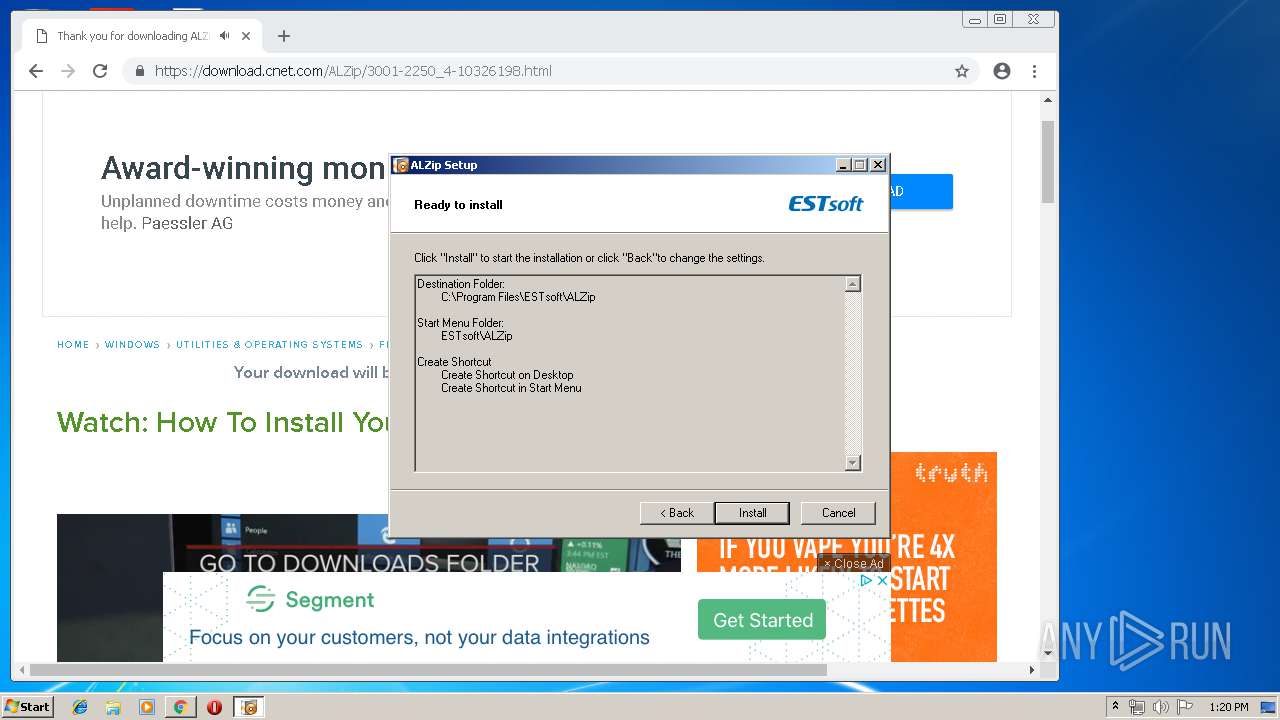
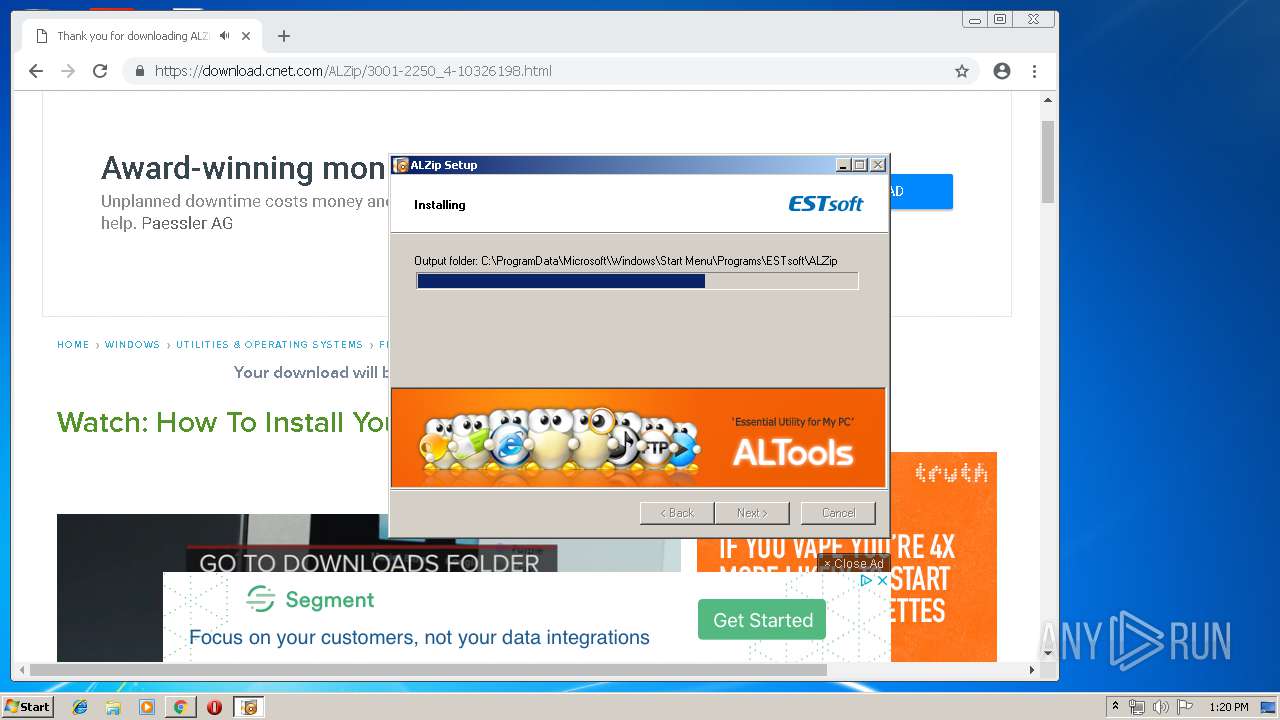
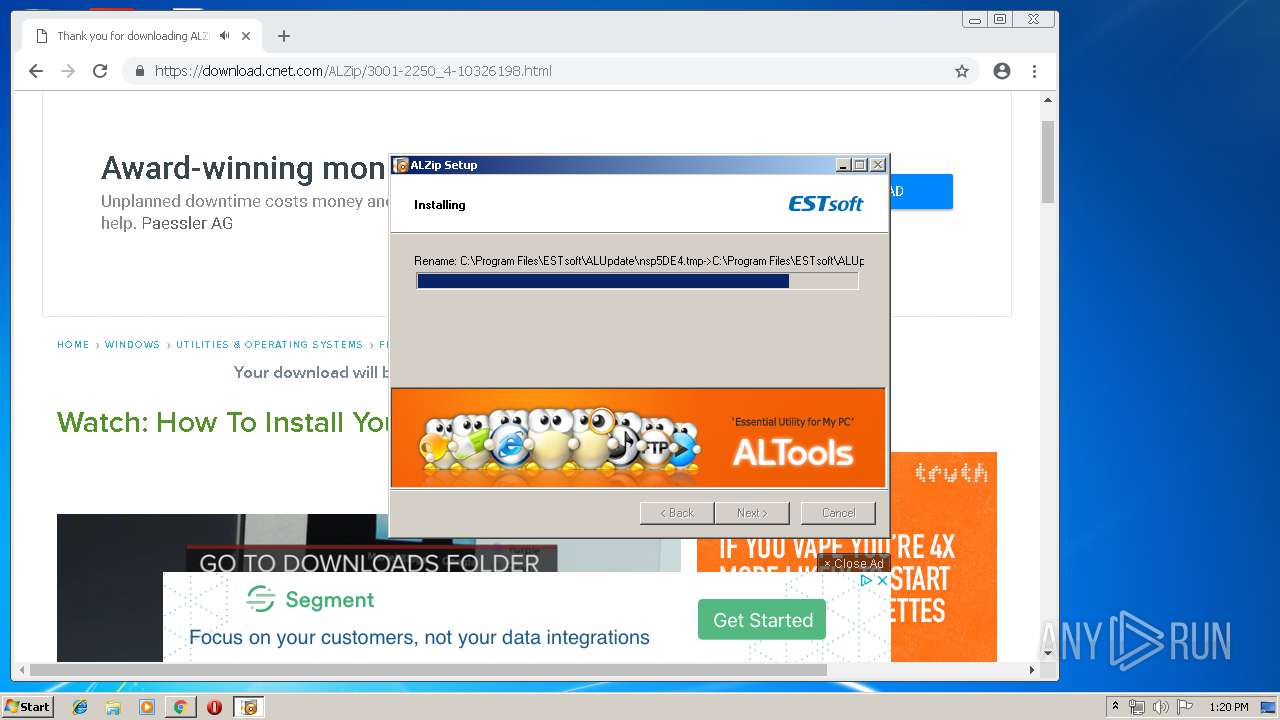
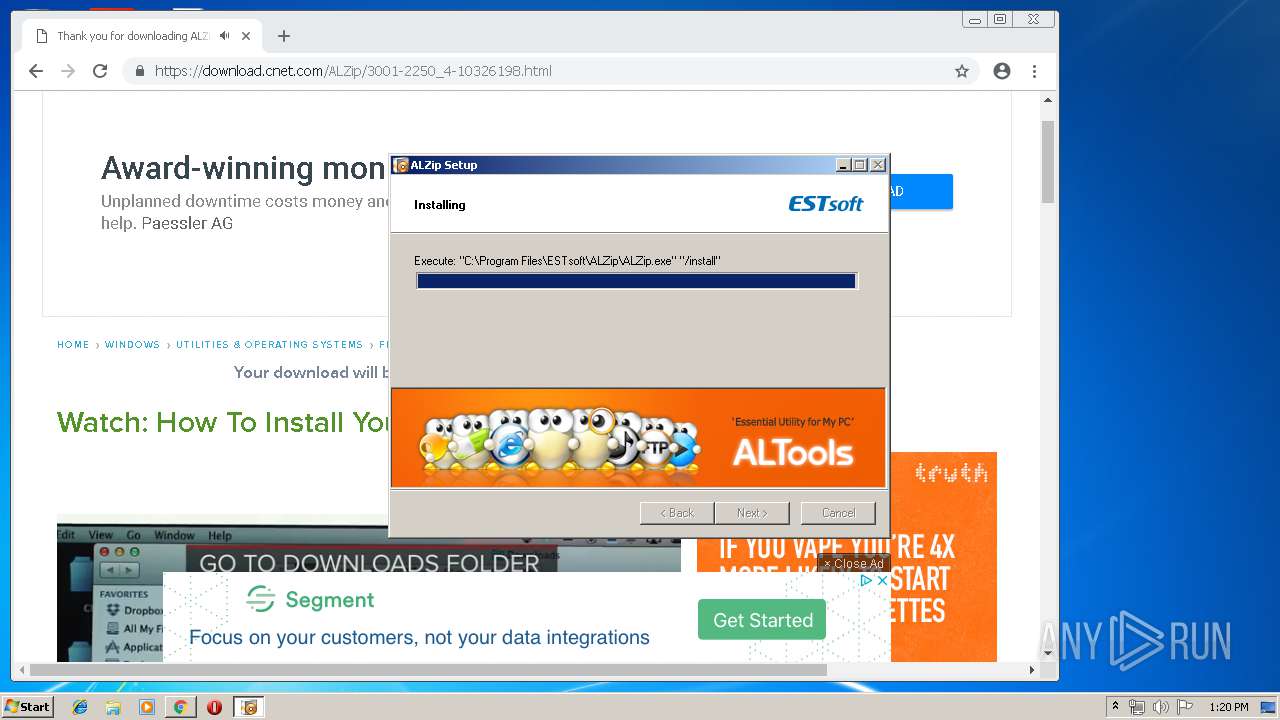
Application was dropped or rewritten from another process
- ALZip851.exe (PID: 2888)
- ALZip851.exe (PID: 3568)
- ALZip.exe (PID: 2740)
- ALUpdate.exe (PID: 2584)
- ALUpdate.exe (PID: 3568)
- ALZip.exe (PID: 3252)
- ALCMUpdate.exe (PID: 2556)
- Alupdate.exe (PID: 3536)
- ALZip.exe (PID: 2124)
- ALCMUpdate.exe (PID: 2992)
- AuthSerialReg.exe (PID: 2080)
- ALSTSCollector.exe (PID: 2752)
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
- AuthSerialReg.exe (PID: 3324)
Loads dropped or rewritten executable
- ALZip851.exe (PID: 2888)
- explorer.exe (PID: 1696)
- ALZip.exe (PID: 2740)
- ALZip.exe (PID: 3252)
- ALZip.exe (PID: 2124)
Registers / Runs the DLL via REGSVR32.EXE
- ALZip851.exe (PID: 2888)
Writes file to Word startup folder
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Actions looks like stealing of personal data
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Changes settings of System certificates
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Renames files like Ransomware
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Dropped file may contain instructions of ransomware
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Deletes shadow copies
- cmd.exe (PID: 1500)
Connects to CnC server
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
GANDCRAB detected
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 1696)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2440)
Executable content was dropped or overwritten
- ALZip851.exe (PID: 2888)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2092)
- ALZip.exe (PID: 2124)
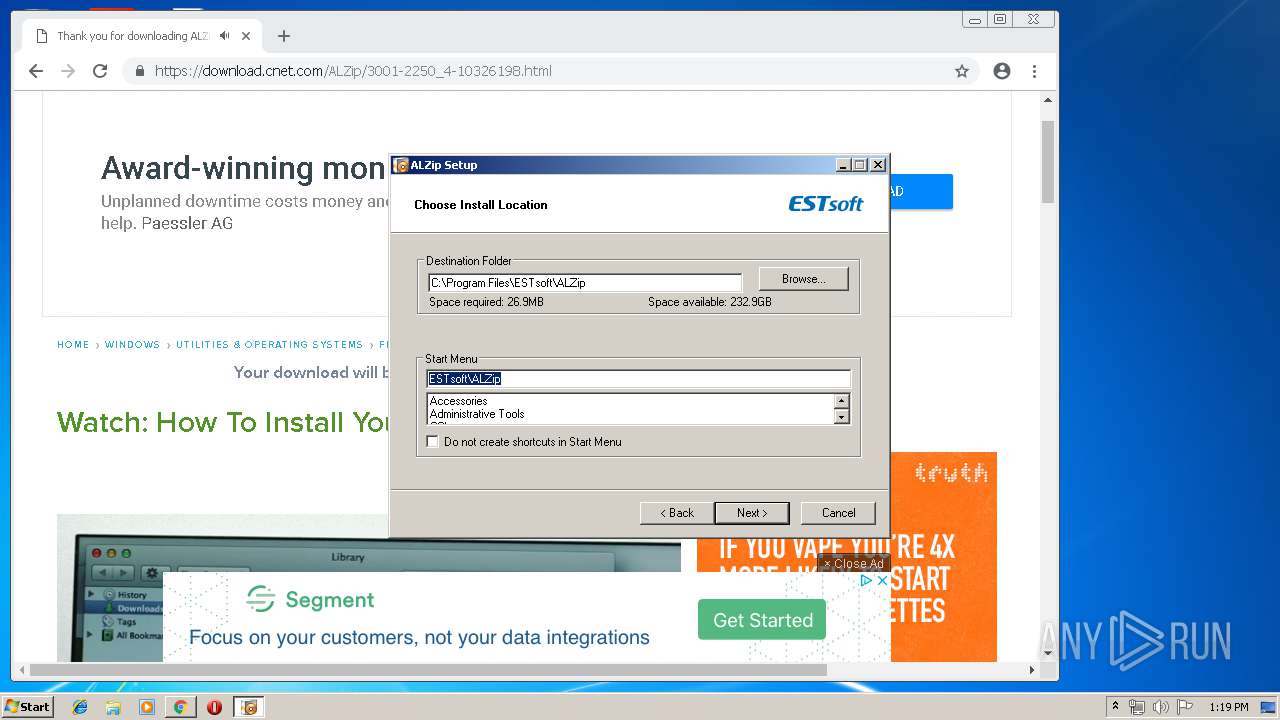
Creates files in the program directory
- ALZip851.exe (PID: 2888)
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Reads internet explorer settings
- ALZip851.exe (PID: 2888)
Creates COM task schedule object
- regsvr32.exe (PID: 2940)
Creates a software uninstall entry
- ALZip851.exe (PID: 2888)
Application launched itself
- ALUpdate.exe (PID: 3568)
Reads Internet Cache Settings
- ALZip851.exe (PID: 2888)
- explorer.exe (PID: 1696)
Creates files in the user directory
- ALUpdate.exe (PID: 3568)
- ALZip.exe (PID: 2740)
- Alupdate.exe (PID: 3536)
- ALCMUpdate.exe (PID: 2556)
- explorer.exe (PID: 1696)
- ALZip.exe (PID: 2124)
- ALZip.exe (PID: 3252)
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Modifies the open verb of a shell class
- ALZip.exe (PID: 2740)
Reads the cookies of Mozilla Firefox
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Starts CMD.EXE for commands execution
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Adds / modifies Windows certificates
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
INFO
Application launched itself
- chrome.exe (PID: 2440)
Reads settings of System Certificates
- chrome.exe (PID: 2092)
Dropped object may contain Bitcoin addresses
- ALZip851.exe (PID: 2888)
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Dropped object may contain TOR URL's
- »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe (PID: 580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .alz | | | ALZip compressed archive (100) |
|---|
Total processes
91
Monitored processes
53
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 260 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\이미지 무단사용 내용.alz | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12401439106555713538,17846197939623014234,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5545750307223571319 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5545750307223571319 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12401439106555713538,17846197939623014234,131072 --enable-features=PasswordImport --service-pipe-token=12207593012773850831 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12207593012773850831 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 360 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12401439106555713538,17846197939623014234,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7495085303058569380 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7495085303058569380 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 580 | "C:\Users\admin\AppData\Local\Temp\_AZTMP0_\»ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe" | C:\Users\admin\AppData\Local\Temp\_AZTMP0_\»ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe | ALZip.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12401439106555713538,17846197939623014234,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10882634309209922616 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12401439106555713538,17846197939623014234,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15306079804095282509 --mojo-platform-channel-handle=3324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12401439106555713538,17846197939623014234,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1406487918501448640 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1406487918501448640 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12401439106555713538,17846197939623014234,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10317817048837602744 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10317817048837602744 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
11 795
Read events
10 353
Write events
1 419
Delete events
23
Modification events
| (PID) Process: | (2440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Puebzr |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605B1EDBB1E0D40100000000 | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000004000000020000001B5400000200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F02 | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605B1EDBB1E0D40100000000 | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000300000000000000020000000200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D880060200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D880060200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D88006 | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 00000000010000000000000001000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605B1EDBB1E0D40100000000 | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000300000000000000030000000200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D880060200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D880060200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D88006 | |||
Executable files
73
Suspicious files
835
Text files
627
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\66d440aa-d0a0-4537-87d7-0a90be2a0248.tmp | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFfa280.TMP | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
336
DNS requests
205
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2092 | chrome.exe | GET | 200 | 217.146.165.205:80 | http://r2---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.150&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1553260650&mv=m&pl=20&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
2092 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2092 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2092 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
2092 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
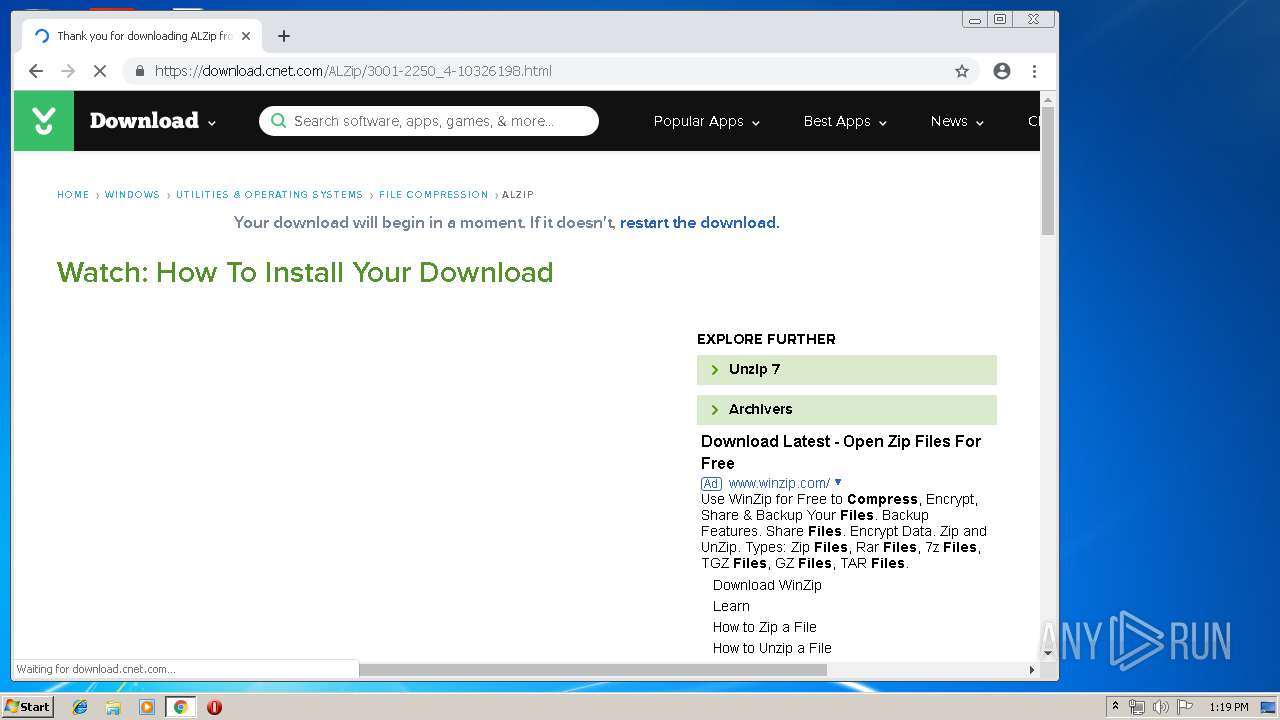
2888 | ALZip851.exe | POST | 400 | 218.153.8.119:80 | http://en-us.altoolsinst.altools.com/show/public_run.aspx | KR | text | 39 b | malicious |
2888 | ALZip851.exe | POST | 400 | 218.153.8.119:80 | http://en-us.altoolsinst.altools.com/show/public_addin.aspx | KR | text | 39 b | malicious |
2888 | ALZip851.exe | POST | 400 | 218.153.8.119:80 | http://en-us.altoolsinst.altools.com/start/setupset.aspx | KR | text | 39 b | malicious |
2092 | chrome.exe | GET | 200 | 23.111.11.204:80 | http://repository.certum.pl/ctnca.cer | US | der | 959 b | whitelisted |
2888 | ALZip851.exe | POST | 400 | 218.153.8.119:80 | http://en-us.altoolsinst.altools.com/data/SetData.aspx | KR | text | 39 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2092 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 172.217.21.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 216.58.207.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 217.146.165.205:80 | r2---sn-oun-1gie.gvt1.com | NTS workspace AG | CH | whitelisted |
2092 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 216.58.206.14:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 172.217.22.14:443 | consent.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2888 | ALZip851.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
580 | »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
580 | »ç¿ëÁßÀ̽ŠÀ̹ÌÁö_.pdf .exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
8 ETPRO signatures available at the full report
Process | Message |
|---|---|
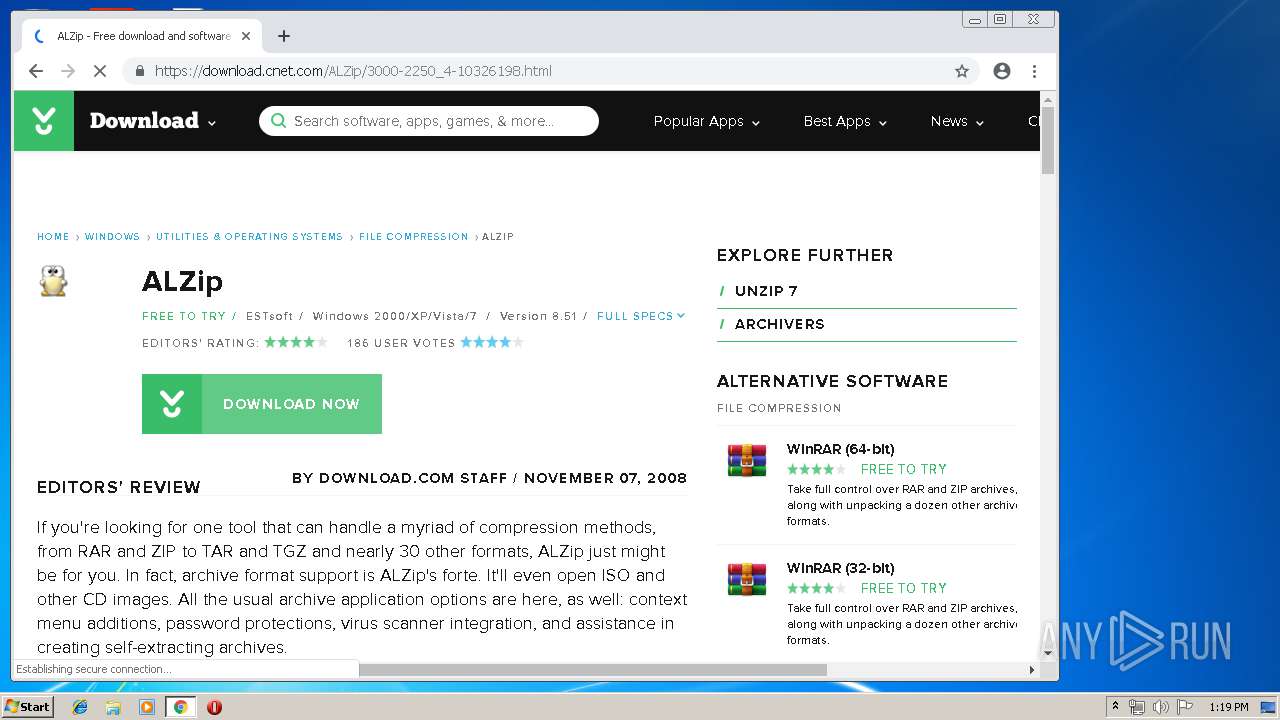
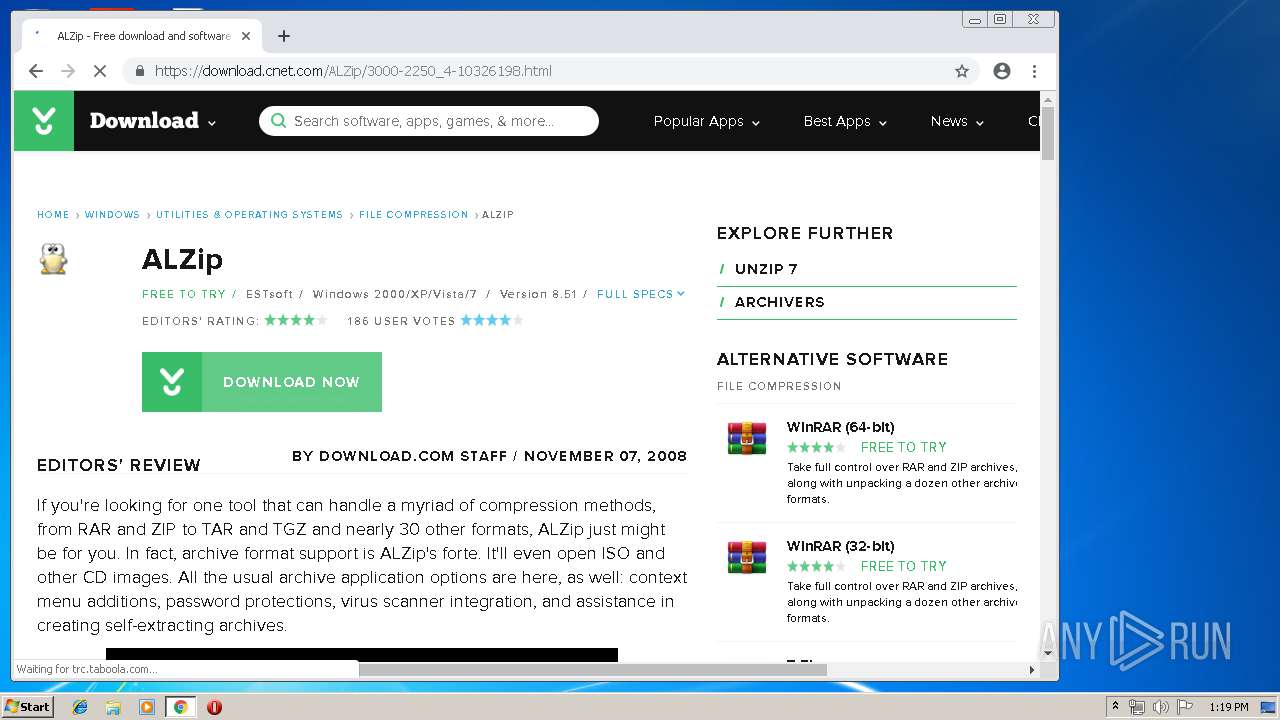
ALZip851.exe | URL |
ALZip851.exe | Name |
ALZip851.exe | checkurl |
ALZip851.exe | sendurl |
ALZip851.exe | changename |
ALZip851.exe | default |
ALZip851.exe | Free |
ALZip851.exe | C:\Program Files\ESTsoft\ALZip\nss5828.tmp |
ALZip851.exe | stemp1 |
ALZip851.exe | stemp2 |