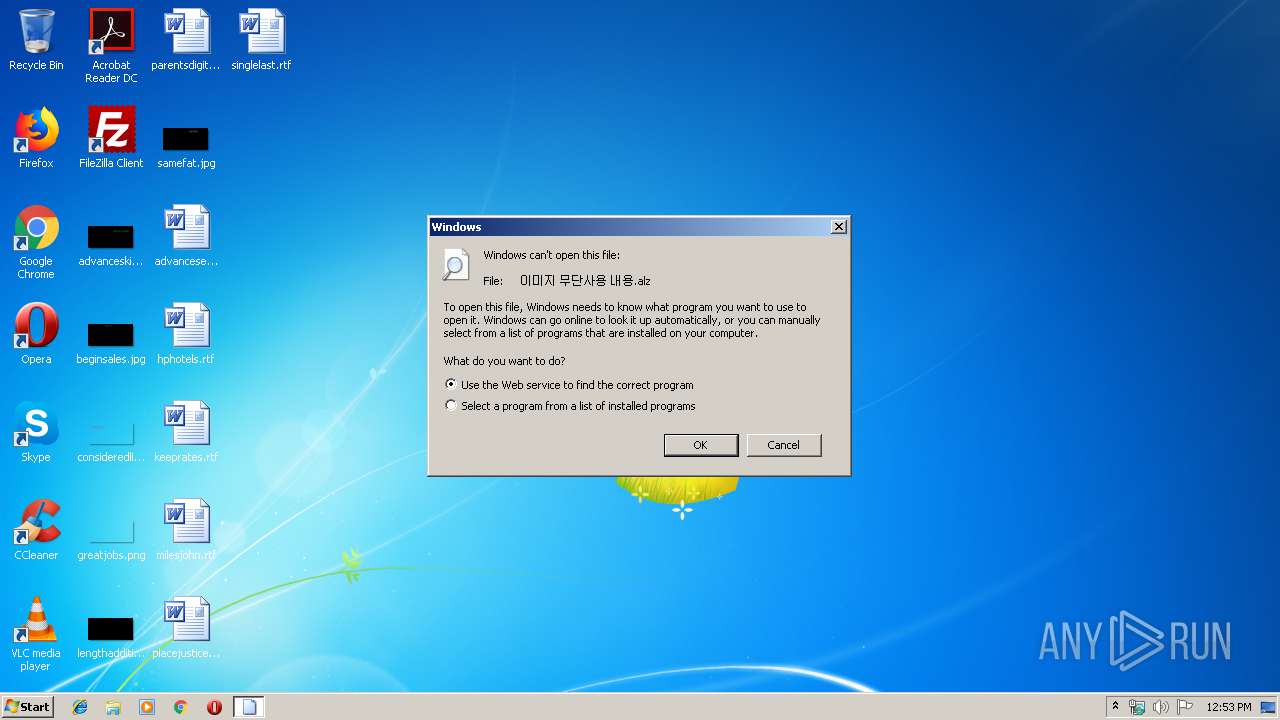
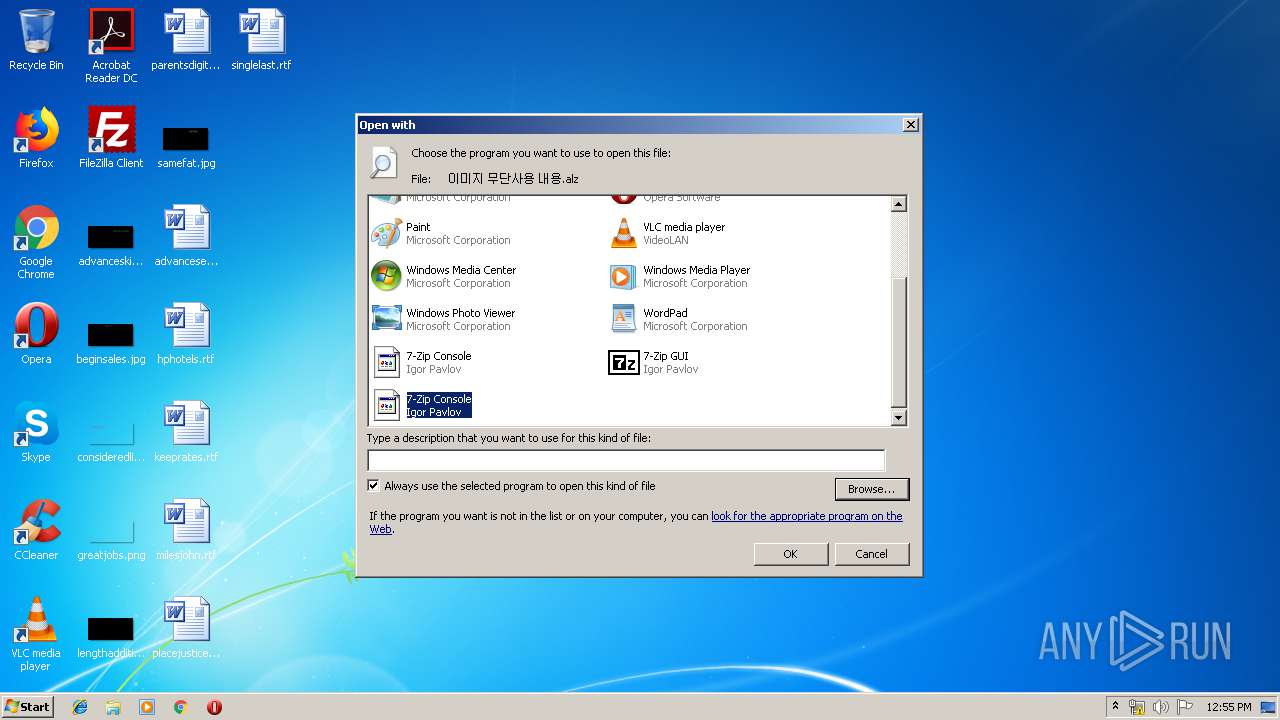
| File name: | 이미지 무단사용 내용.alz |
| Full analysis: | https://app.any.run/tasks/0c4b7164-56bd-4d7e-8d3d-26ab2a0b3f80 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 12:53:31 |
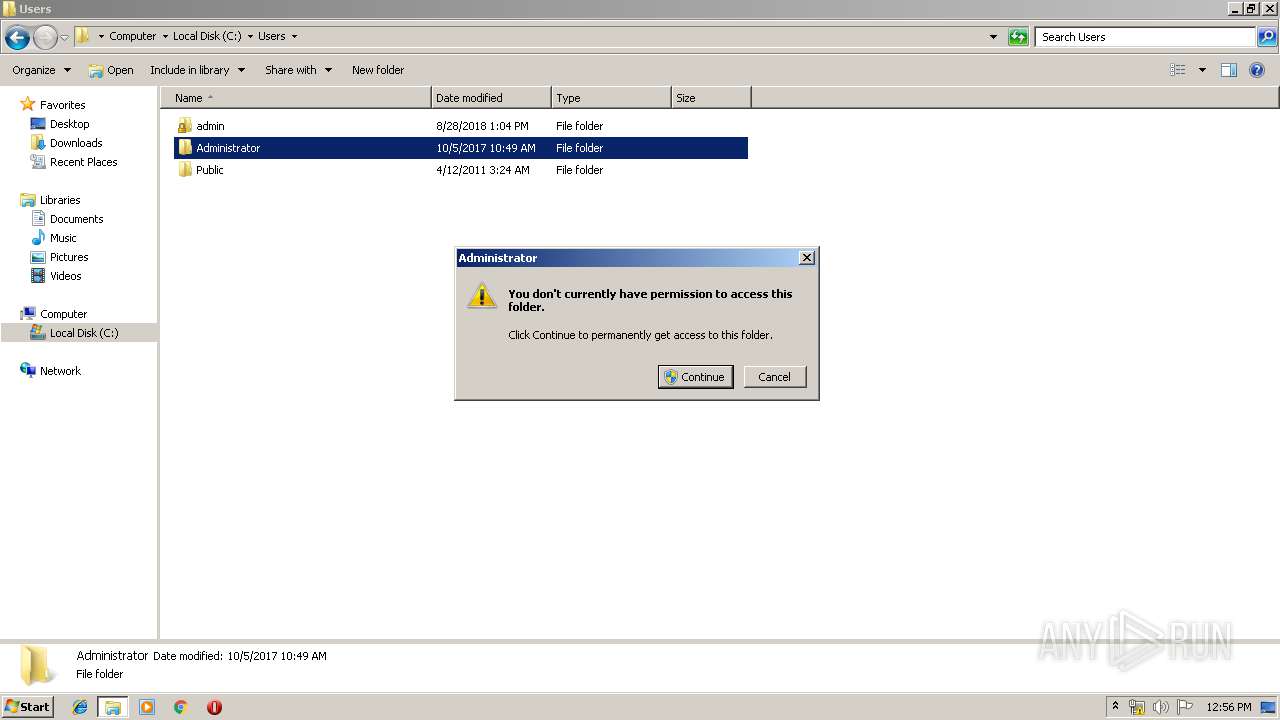
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 4750C2CB9FA898107A233CE9B94B1572 |
| SHA1: | 68025D73DD51EAF889BAC0444205B5D0E4A0075C |
| SHA256: | E1E0885BC8D30C9BFB6A86C5983ADA67BB5572665FCA86FD676FA8BD646C02C6 |
| SSDEEP: | 6144:646bIwgtdm3AsIqGA/iMOW946bIwgtdm3AsIqGA/iMOWJ:6tIwg2wsNG1MOitIwg2wsNG1MOm |
MALICIOUS
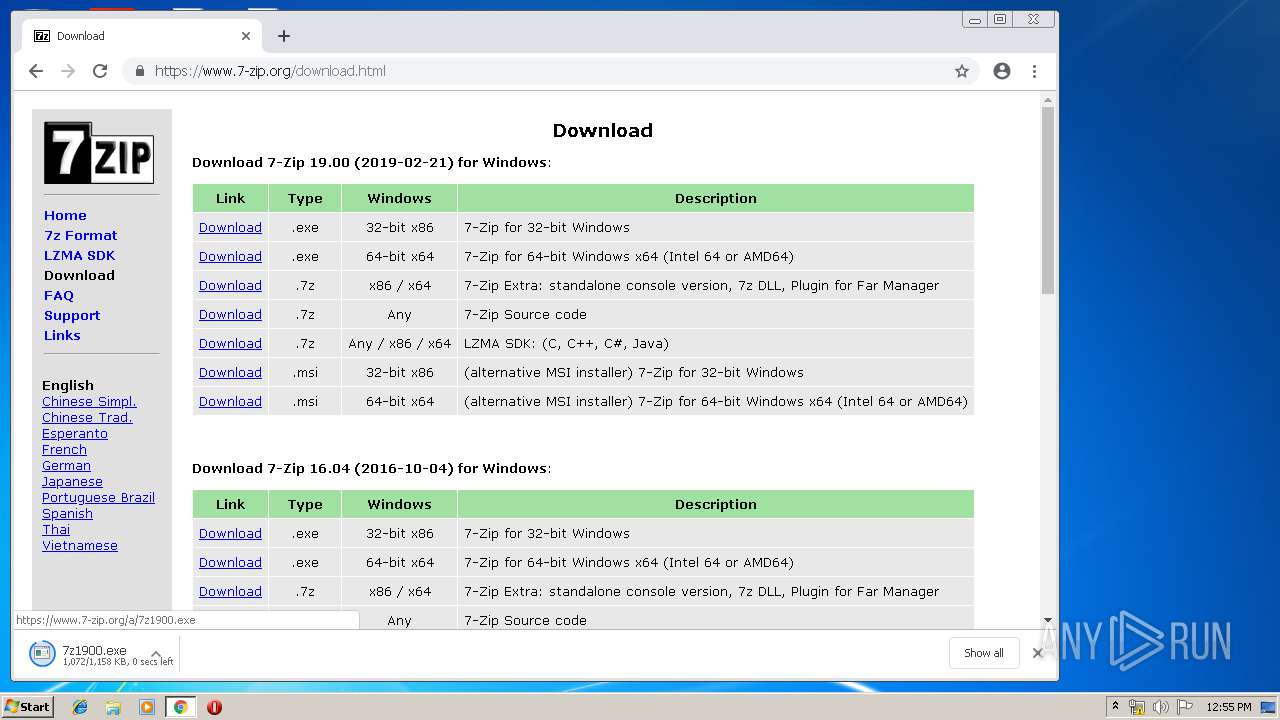
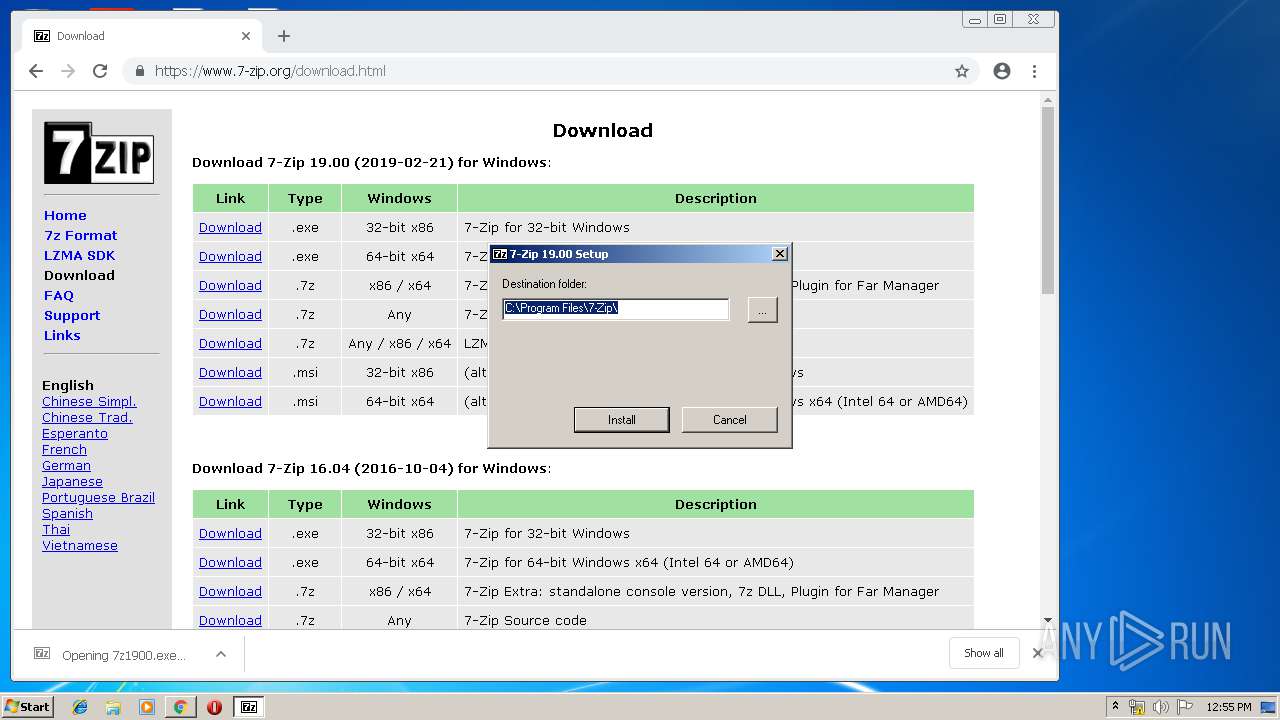
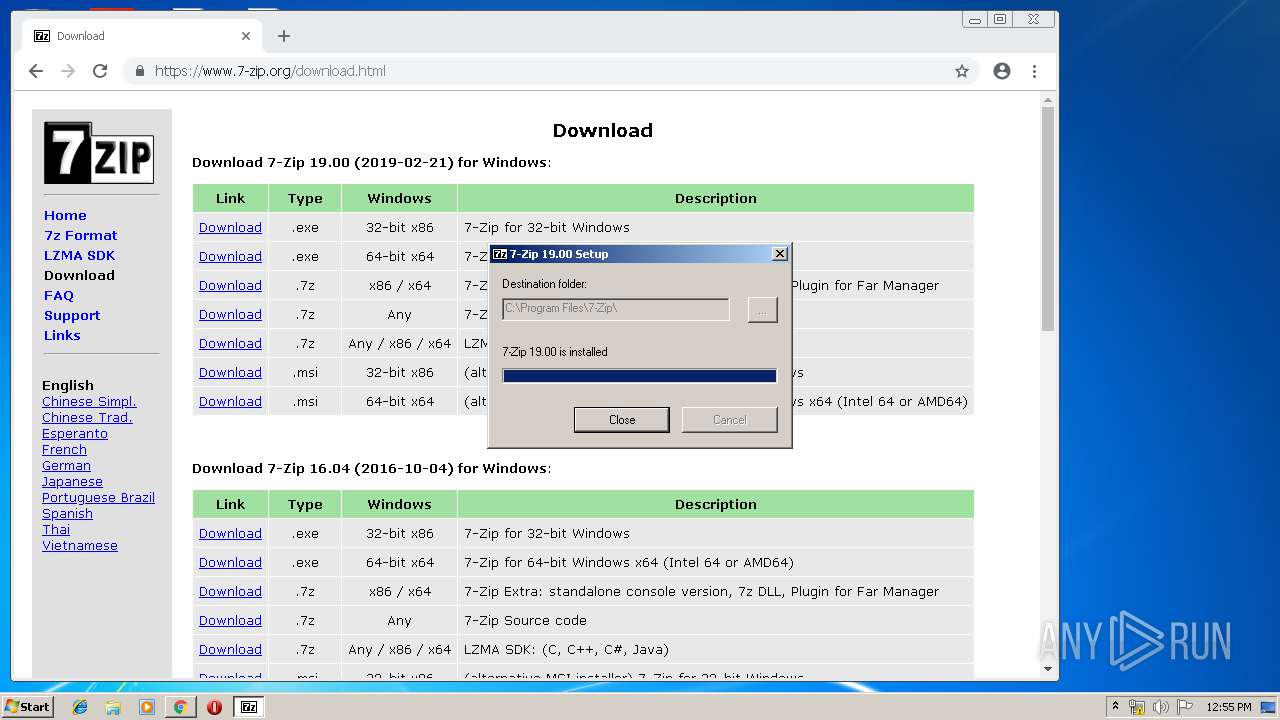
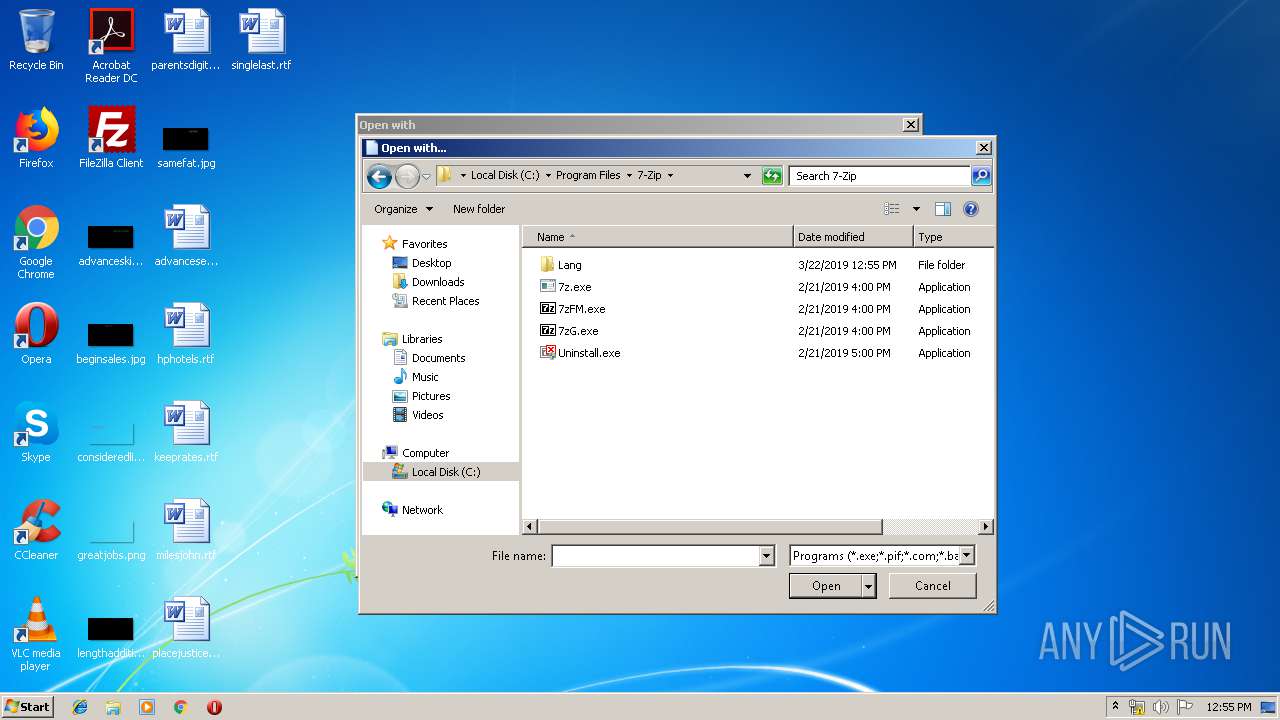
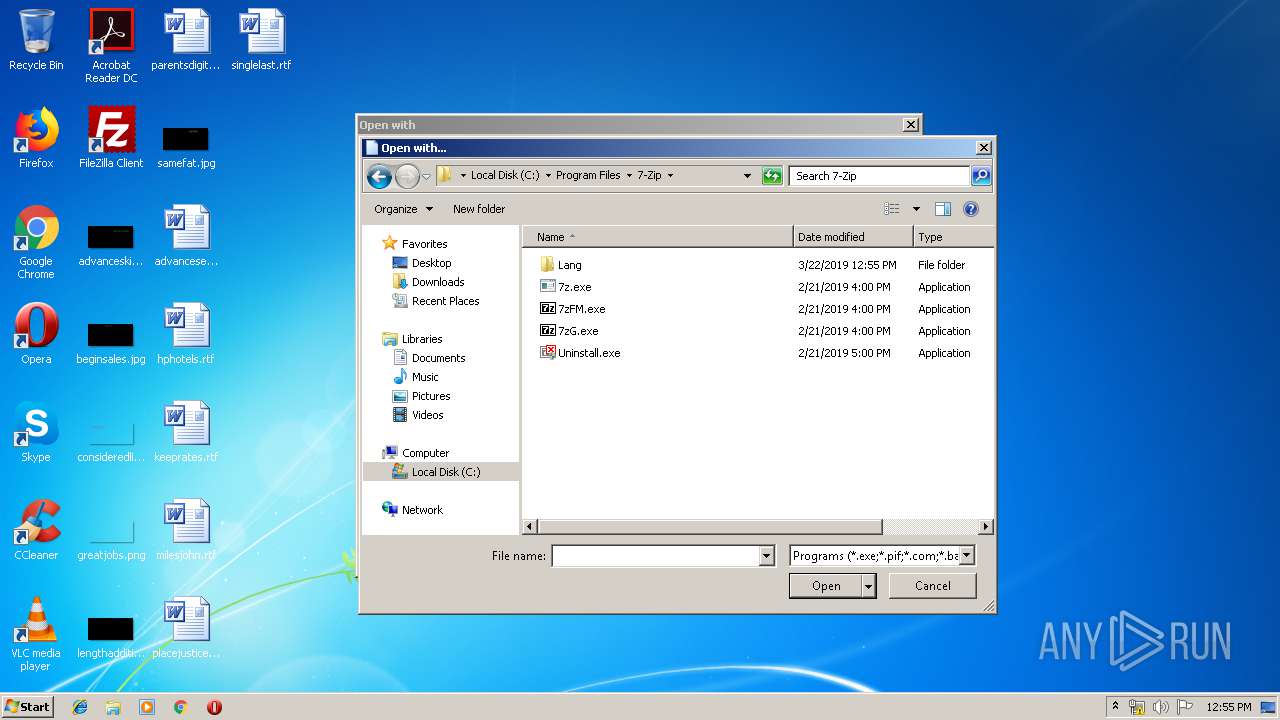
Application was dropped or rewritten from another process
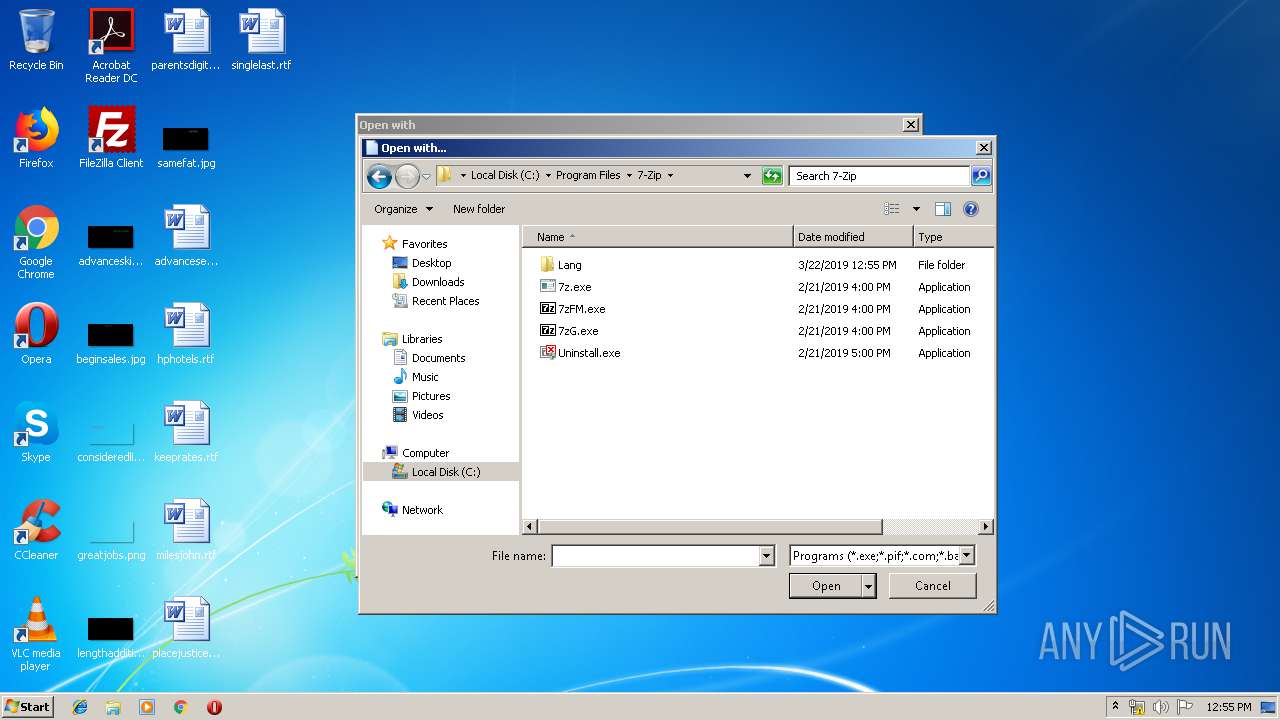
- 7z1900.exe (PID: 2952)
- 7z1900.exe (PID: 1620)
- 7z.exe (PID: 3676)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1192)
- 7z1900.exe (PID: 2952)
- chrome.exe (PID: 2864)
Creates a software uninstall entry
- 7z1900.exe (PID: 2952)
Creates COM task schedule object
- 7z1900.exe (PID: 2952)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1192)
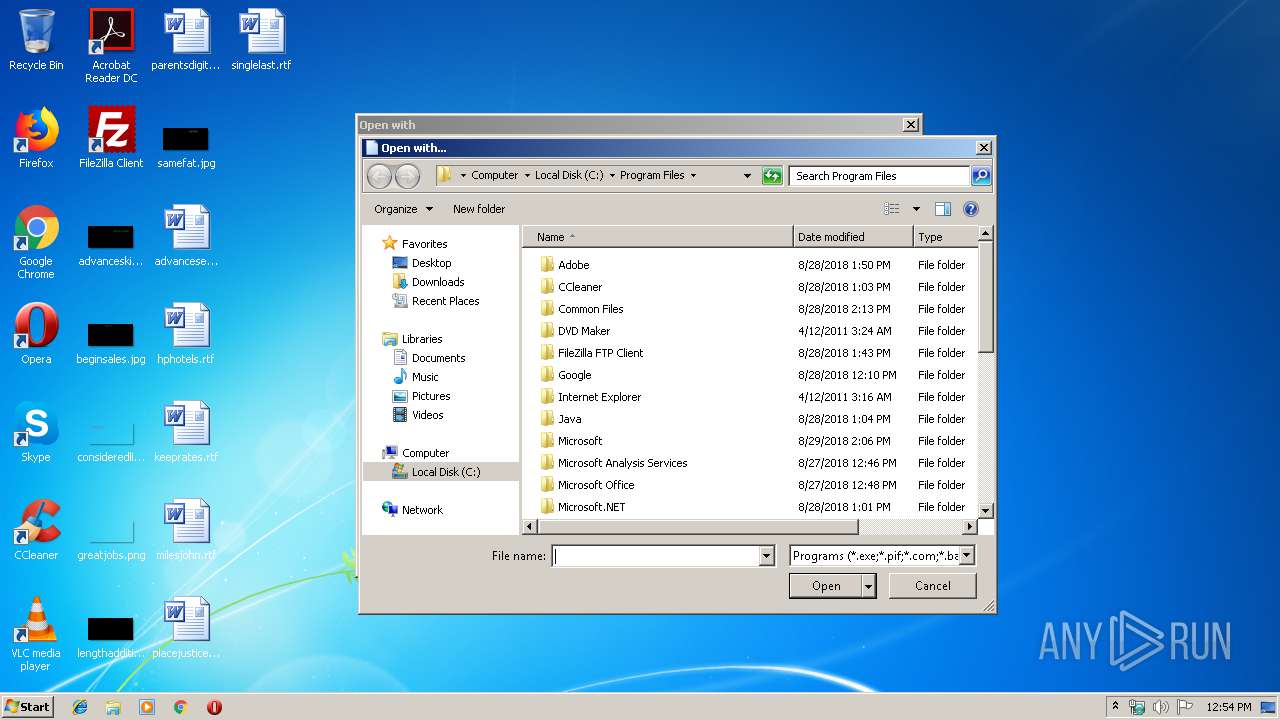
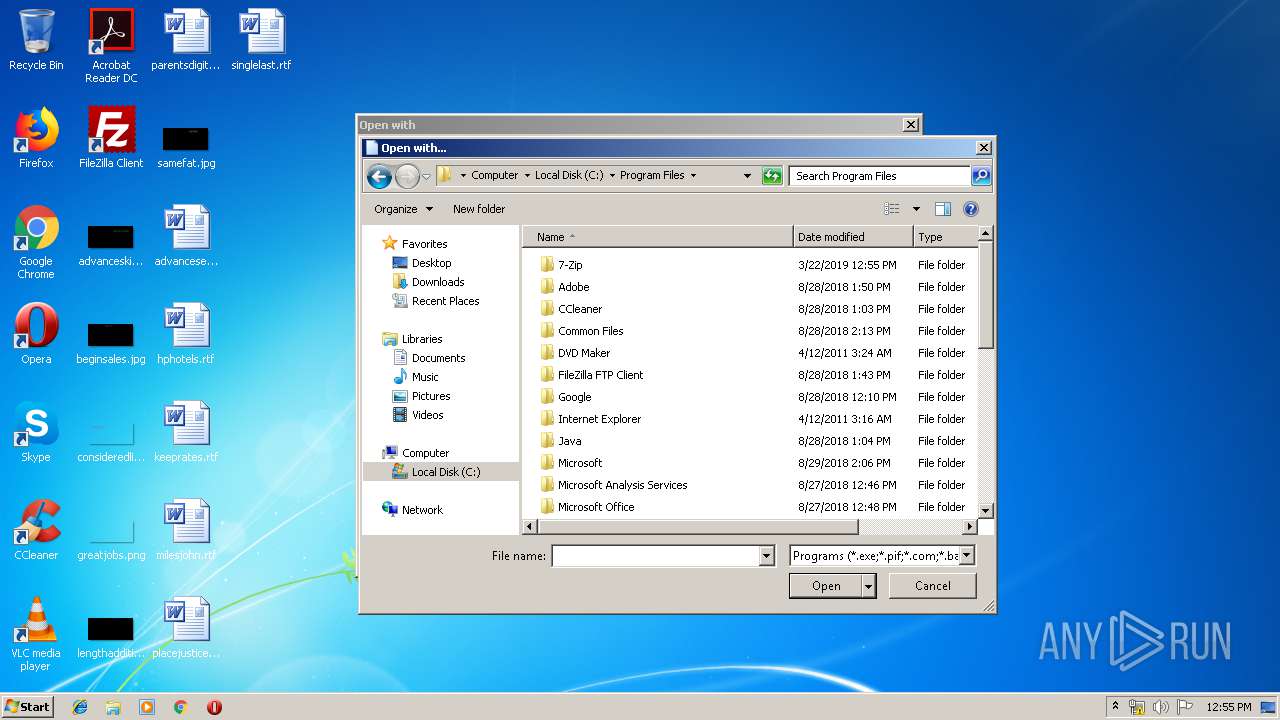
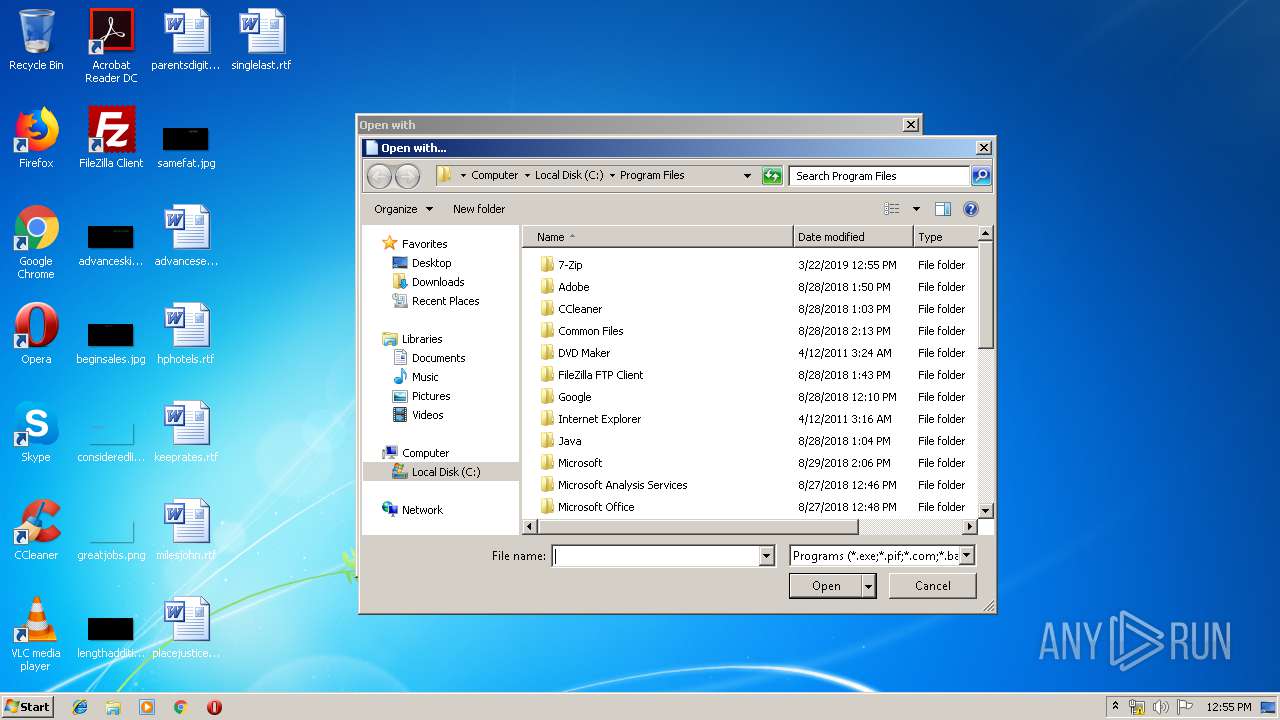
Creates files in the program directory
- 7z1900.exe (PID: 2952)
INFO
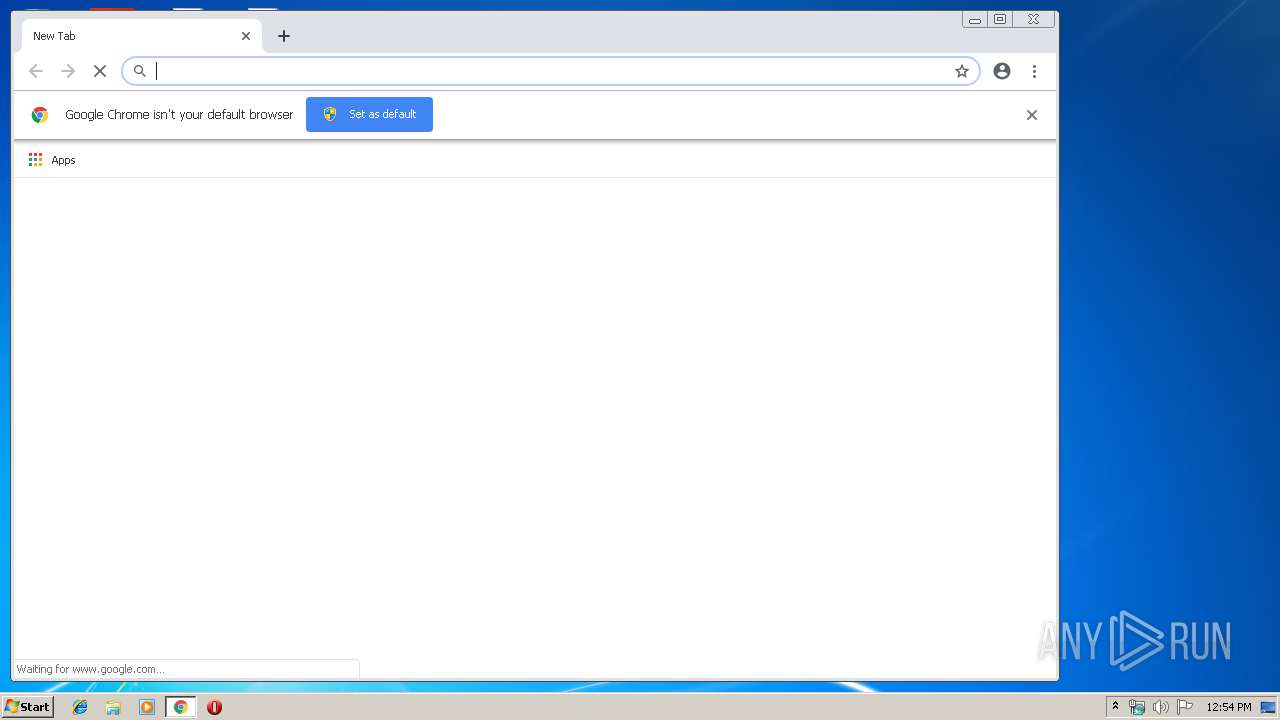
Application launched itself
- chrome.exe (PID: 1192)
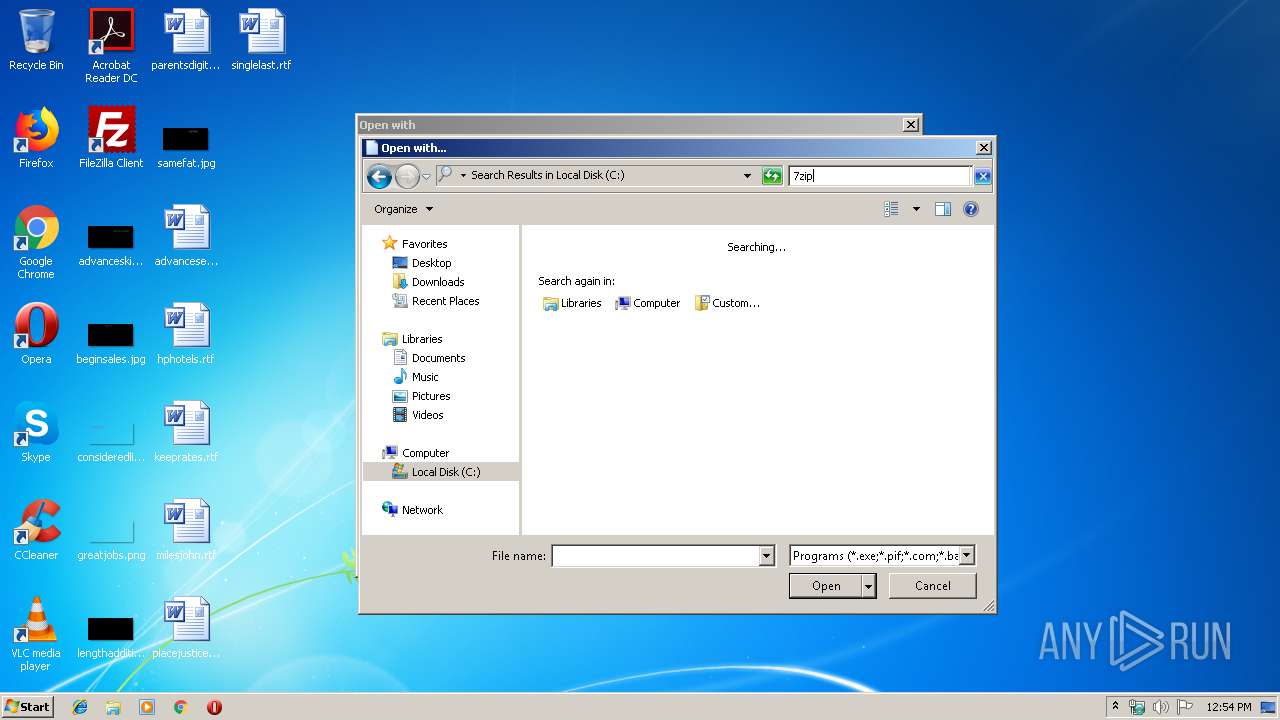
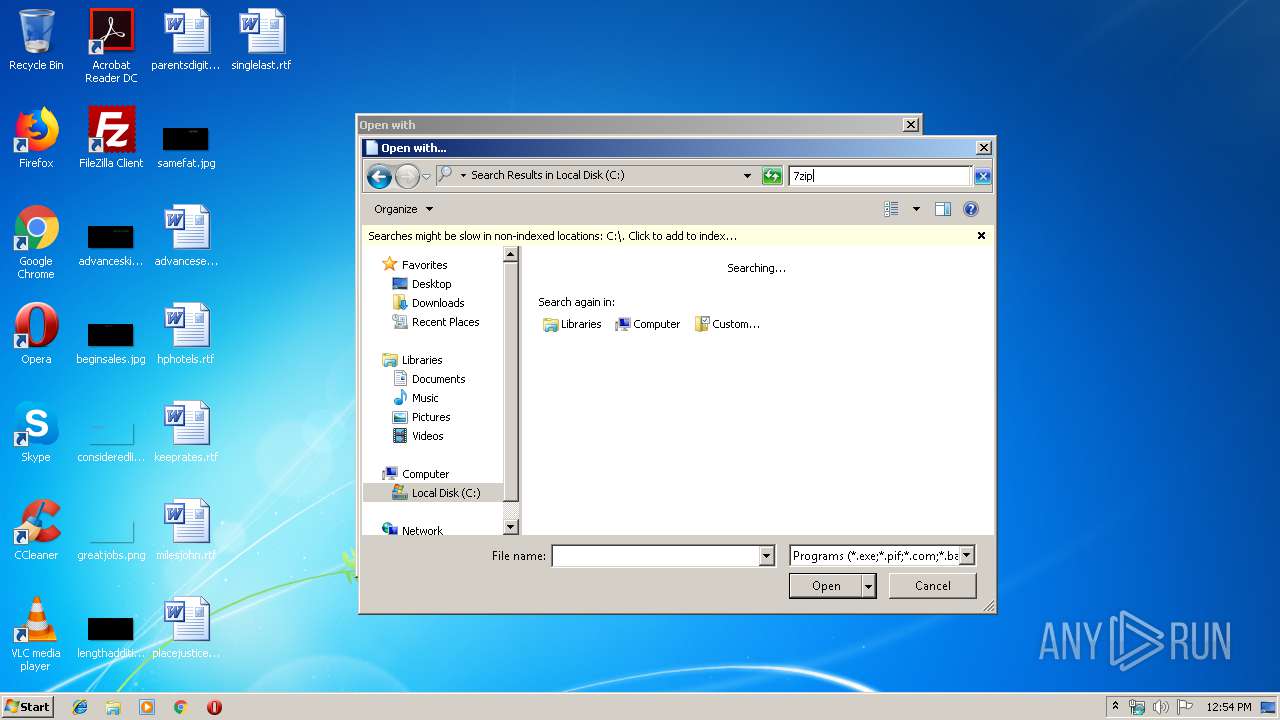
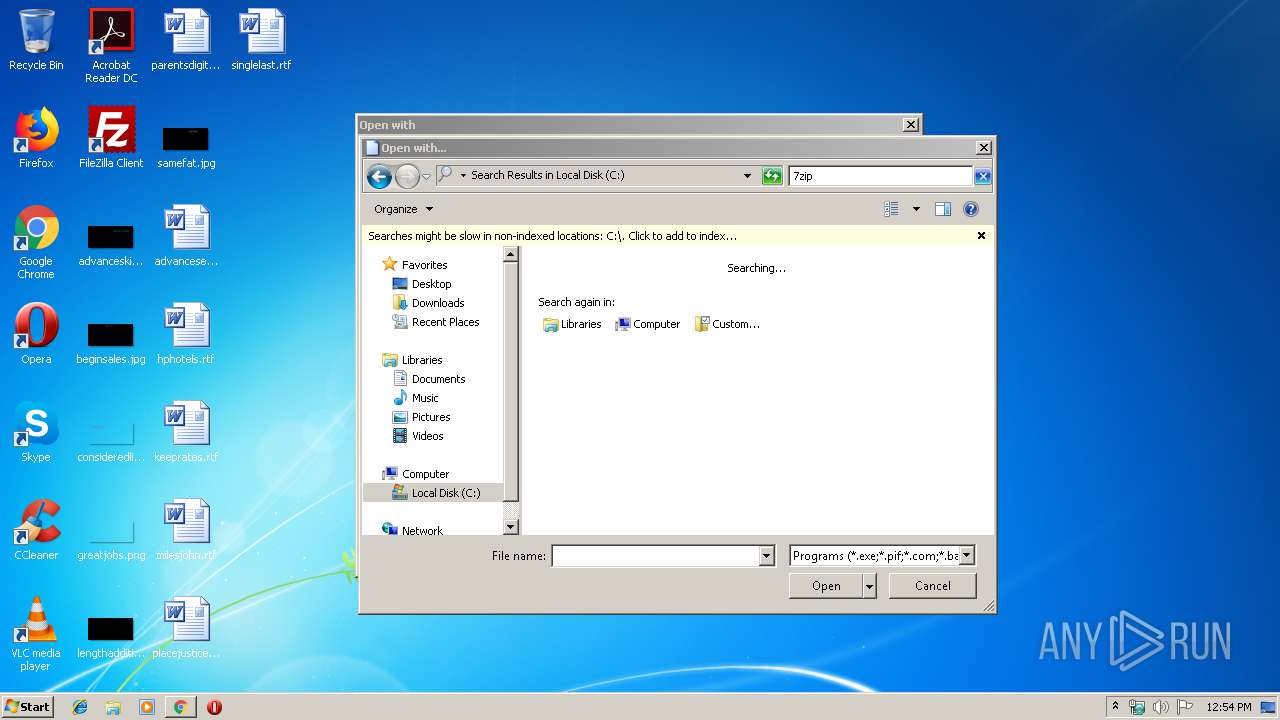
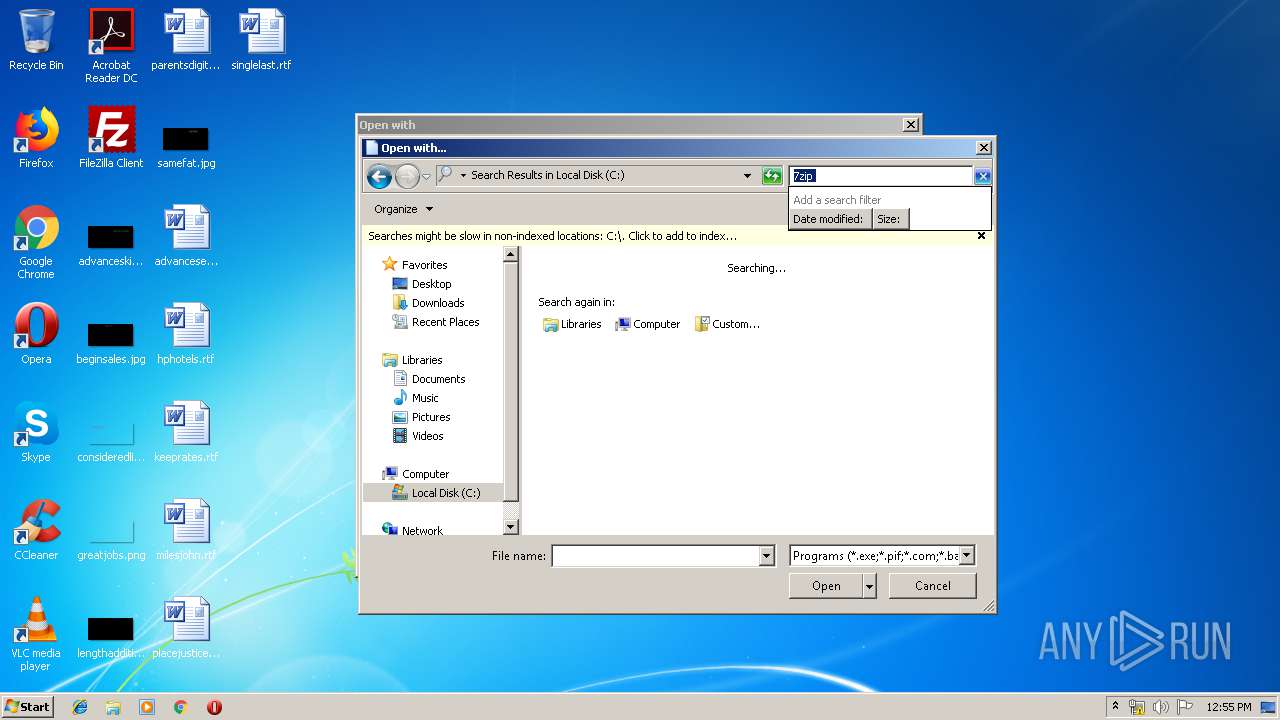
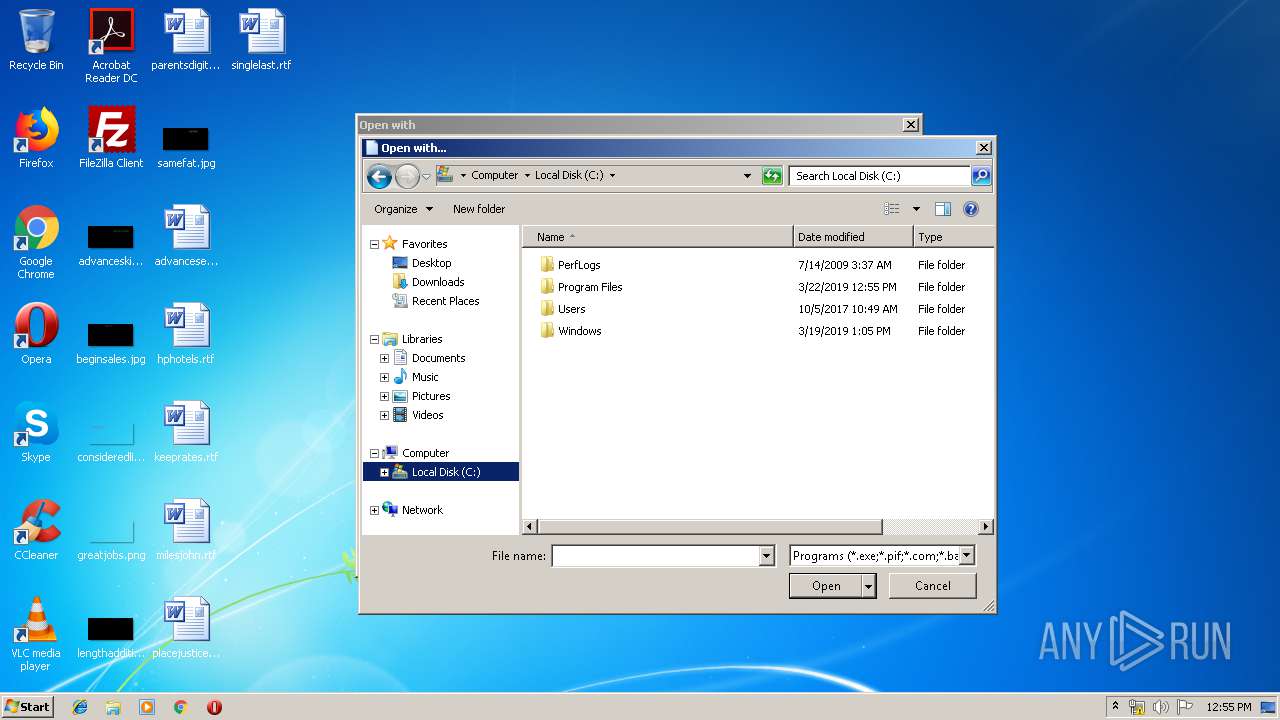
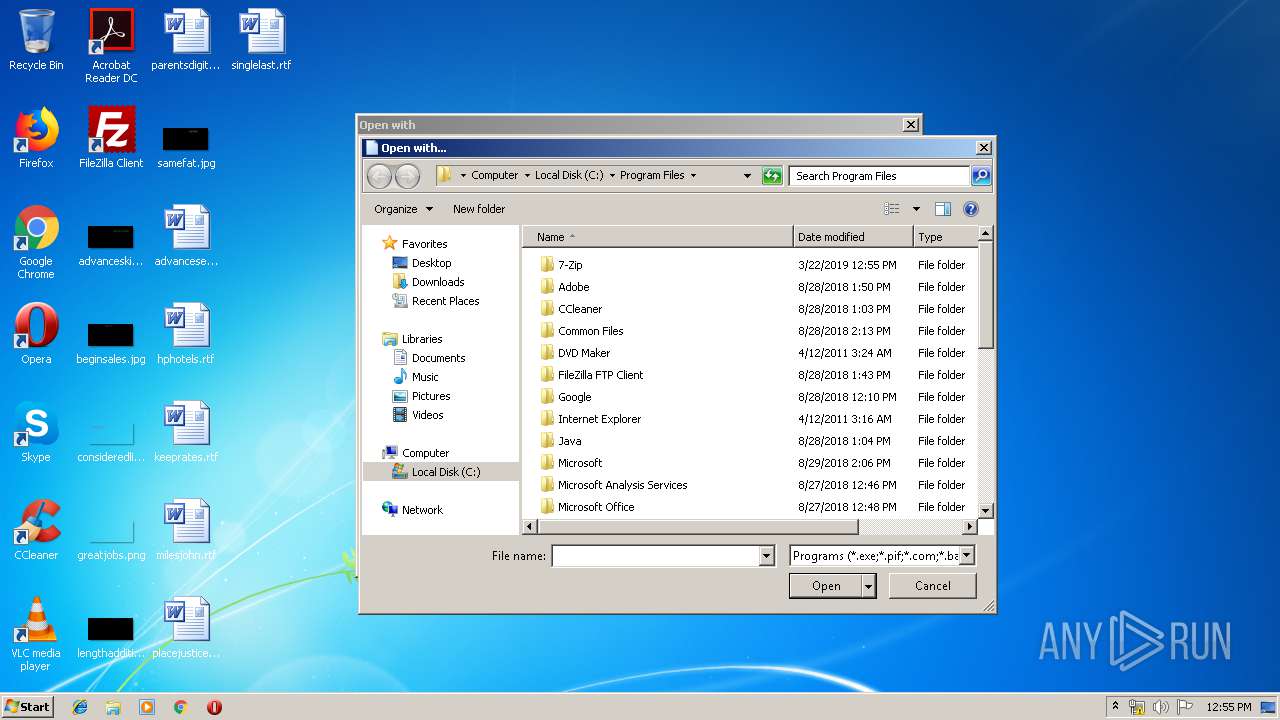
Modifies the open verb of a shell class
- rundll32.exe (PID: 2304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .alz | | | ALZip compressed archive (100) |
|---|
Total processes
62
Monitored processes
23
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2040 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,17026727961991616764,7352326689199850736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12180939934365541142 --mojo-platform-channel-handle=3408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,17026727961991616764,7352326689199850736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15898583460786882948 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,17026727961991616764,7352326689199850736,131072 --enable-features=PasswordImport --service-pipe-token=12659230752233407907 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12659230752233407907 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,17026727961991616764,7352326689199850736,131072 --enable-features=PasswordImport --service-pipe-token=4201032666796251217 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4201032666796251217 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
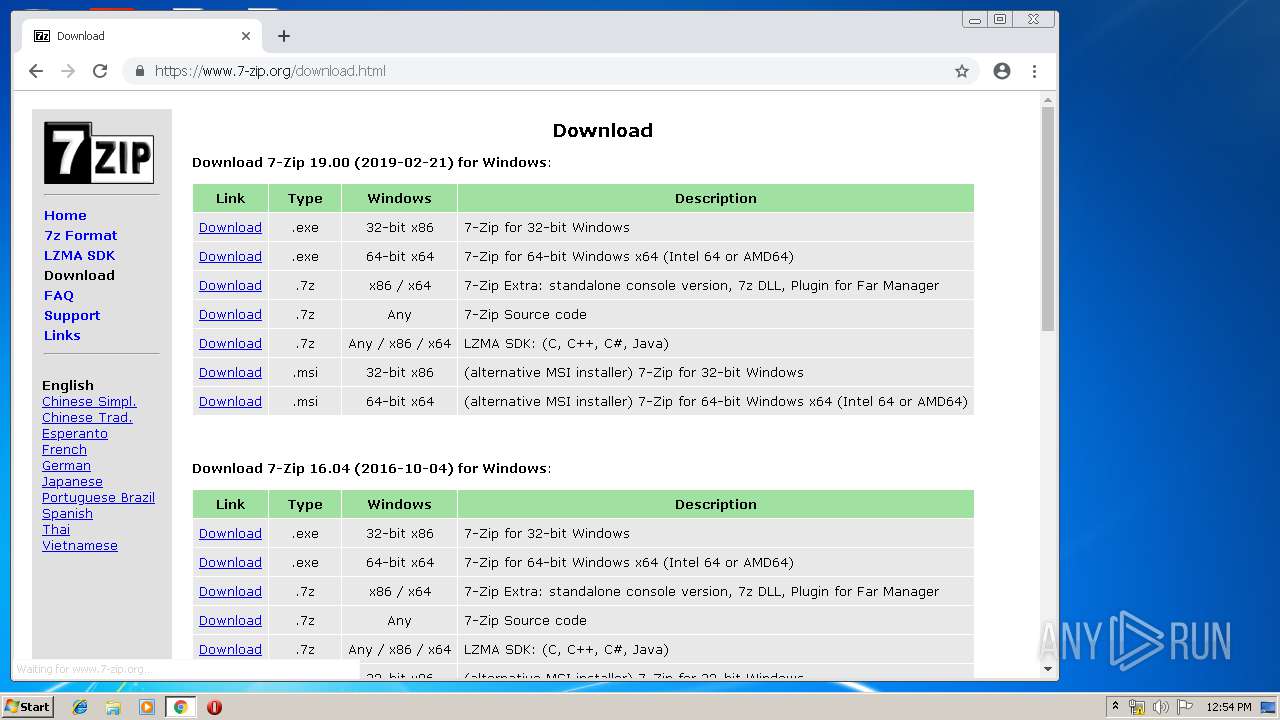
| 1620 | "C:\Users\admin\Downloads\7z1900.exe" | C:\Users\admin\Downloads\7z1900.exe | — | chrome.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Installer Exit code: 3221226540 Version: 19.00 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,17026727961991616764,7352326689199850736,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9697539246609344838 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9697539246609344838 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,17026727961991616764,7352326689199850736,131072 --enable-features=PasswordImport --service-pipe-token=8185629721546460633 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8185629721546460633 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,17026727961991616764,7352326689199850736,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12945188761672603654 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 288
Read events
1 437
Write events
835
Delete events
16
Modification events
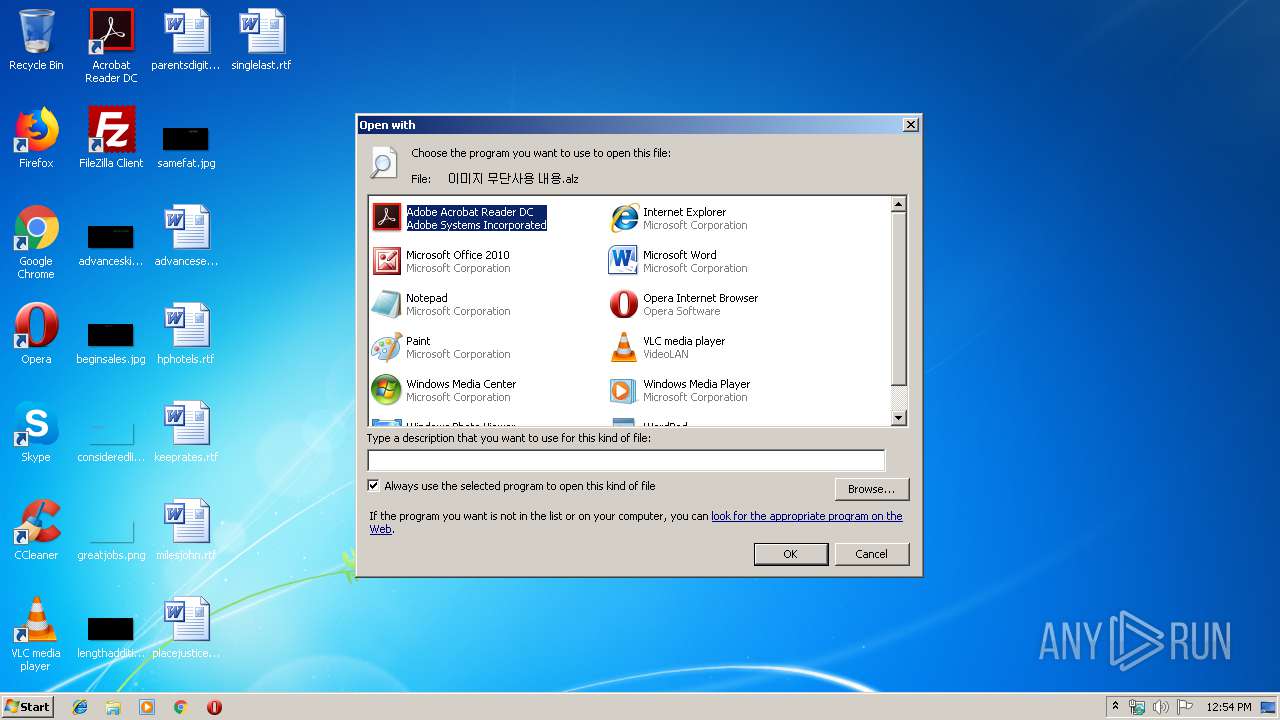
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2304) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
11
Suspicious files
71
Text files
244
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1049dc.TMP | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c3611958-943d-4450-a401-b85770670dc3.tmp | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
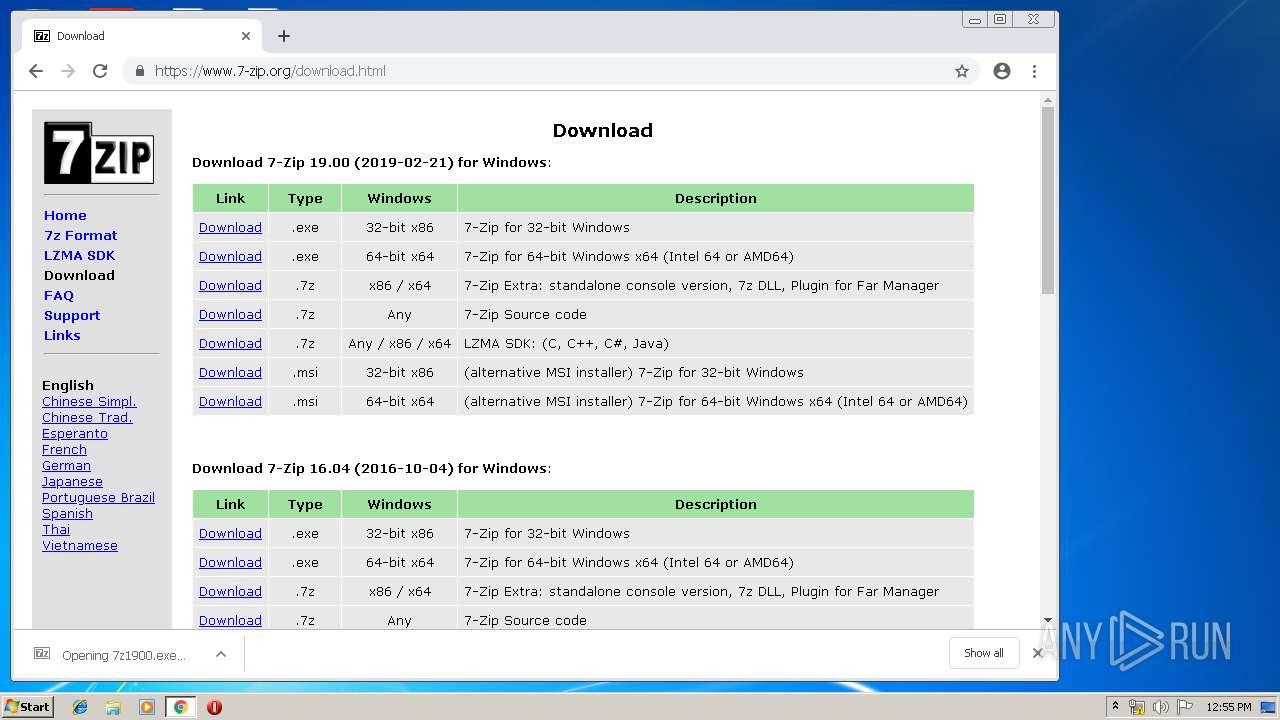
HTTP(S) requests
2
TCP/UDP connections
23
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2864 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2864 | chrome.exe | GET | 200 | 173.194.150.219:80 | http://r5---sn-5goeen7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.22.104&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1553259204&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2864 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 172.217.18.110:443 | consent.google.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 172.217.22.3:443 | id.google.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 216.58.207.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2864 | chrome.exe | 159.65.89.65:443 | www.7-zip.org | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
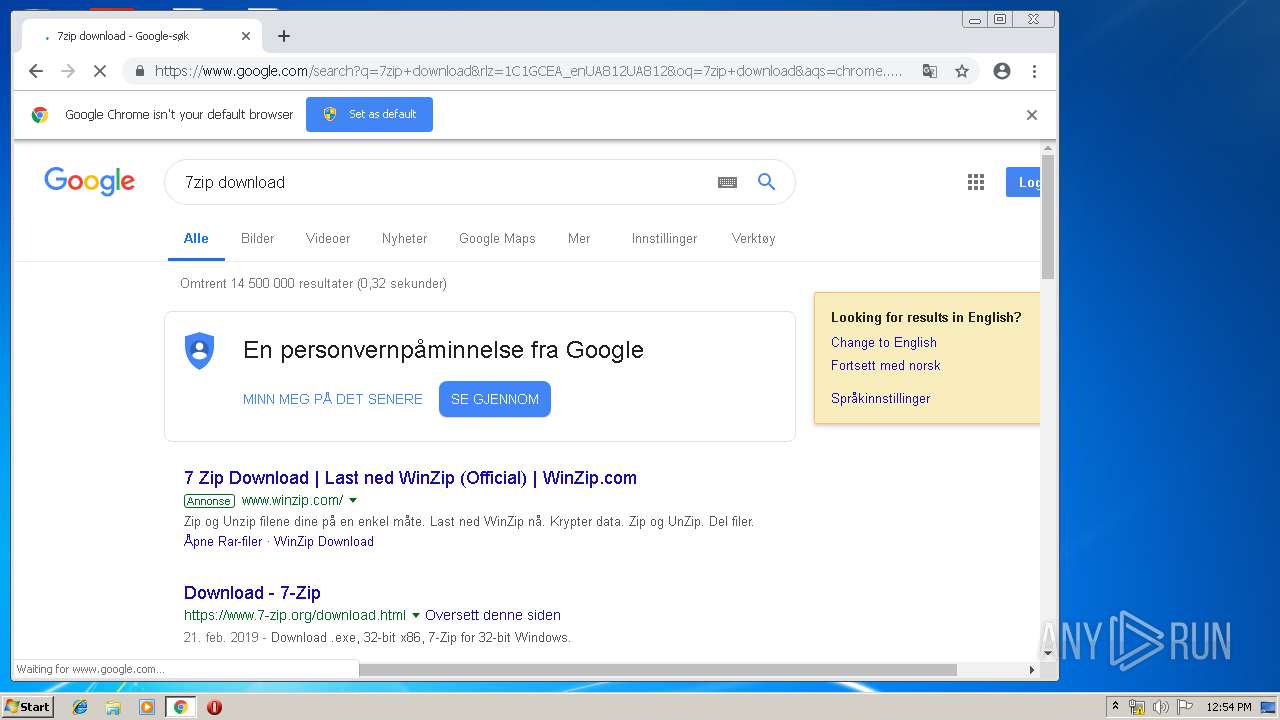
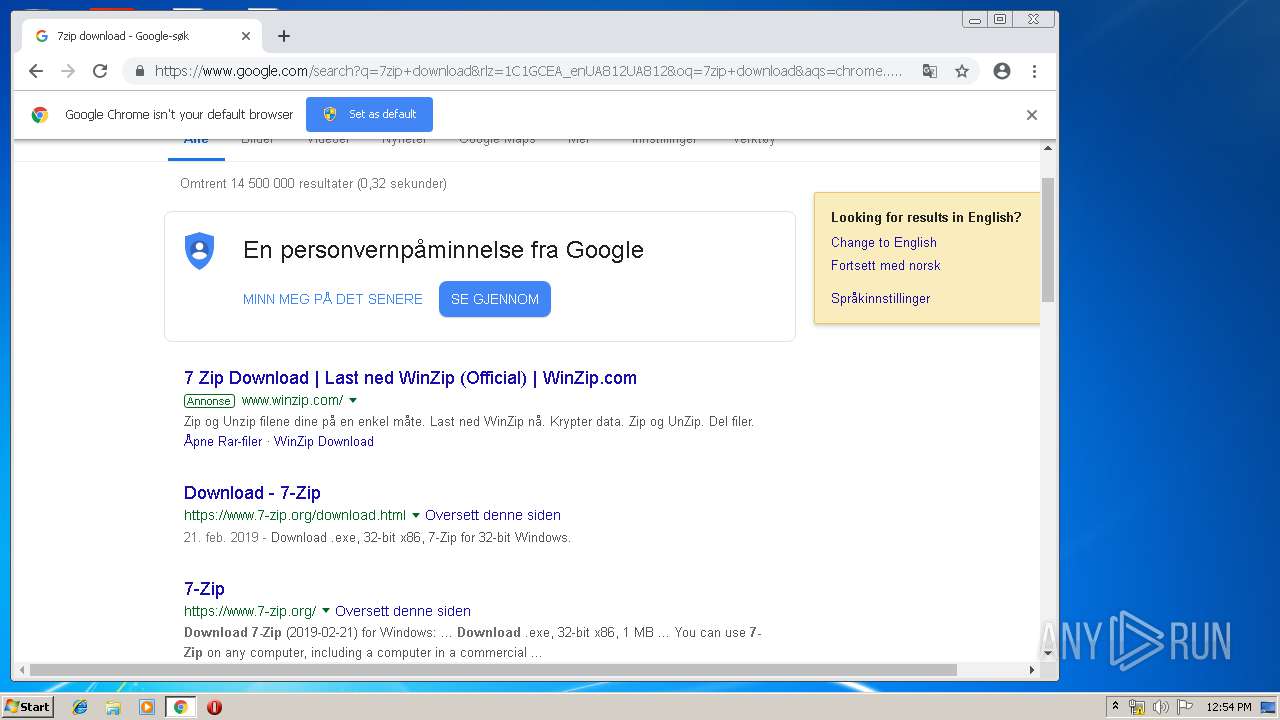
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
consent.google.com |
| shared |
id.google.com |
| whitelisted |
www.google.no |
| whitelisted |
www.googleadservices.com |
| whitelisted |