| File name: | Email-Worm.Win32.Pikachu.exe |
| Full analysis: | https://app.any.run/tasks/49c9bdb8-4da9-4c6d-adc5-ac5dd832838e |
| Verdict: | No threats detected |
| Analysis date: | September 08, 2019, 04:42:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 715614E09261B39DFA439FA1326C0CEC |
| SHA1: | 52D118A34DA7F5037CDE04C31FF491EB25933B18 |
| SHA256: | E1DFC005D5403FB2F356276F0ABE19DF68249CE10E5035450926D56C2F8D3652 |
| SSDEEP: | 384:JuttXvHydgJdONTjJJbIR1ozOtEZcrkTuztHTYhEWS6uyd:JaXfy2dmjJJcAaDkTEdjR6uy |
MALICIOUS
No malicious indicators.SUSPICIOUS
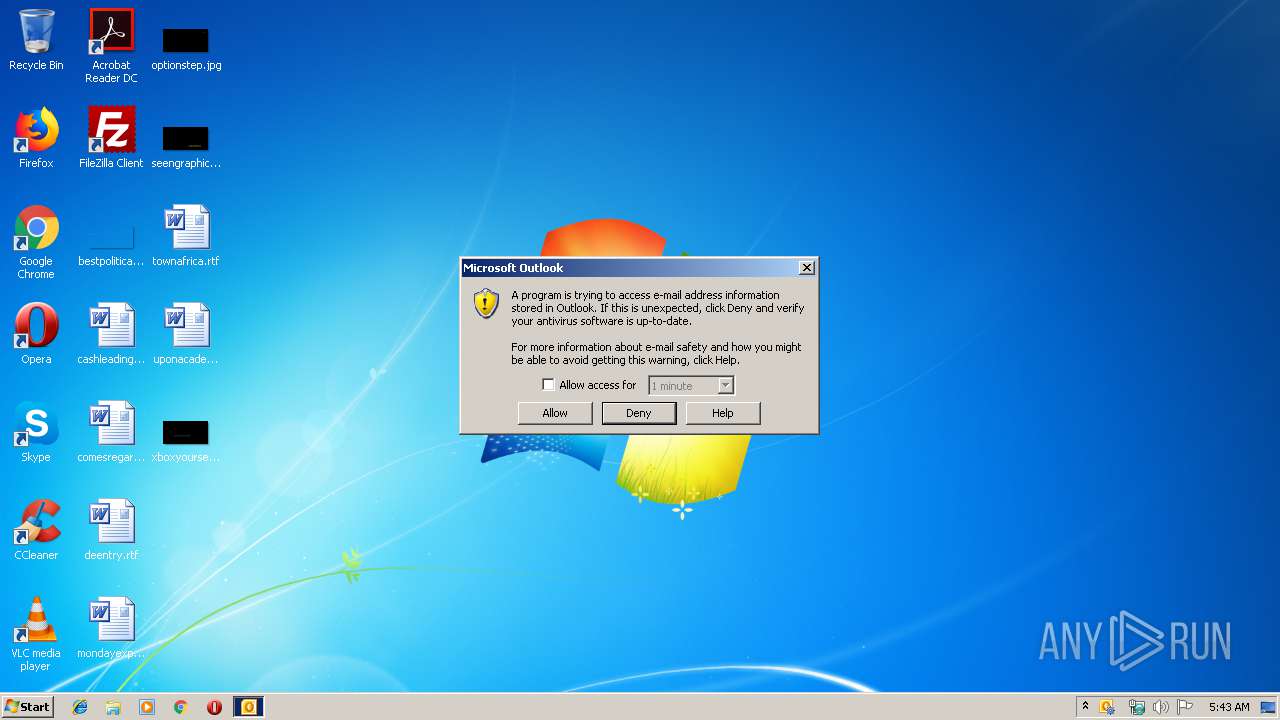
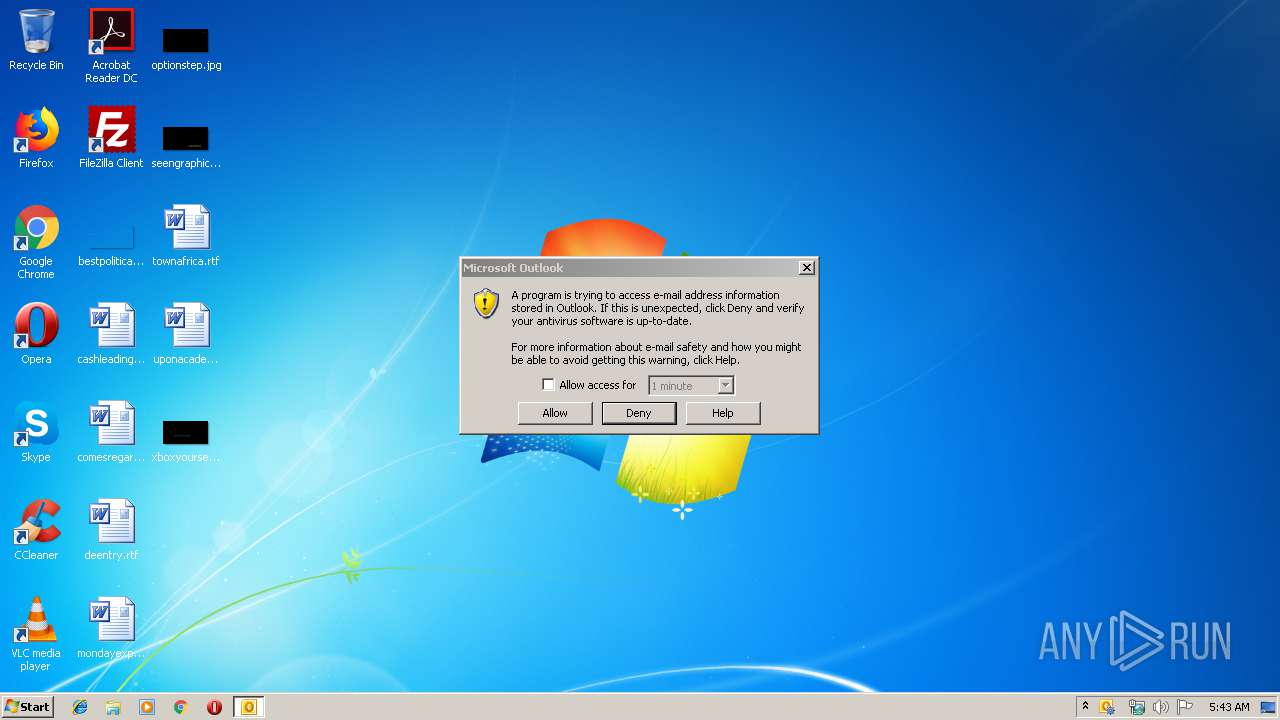
Executed via COM
- OUTLOOK.EXE (PID: 3136)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3136)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2000:05:09 06:27:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1340 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
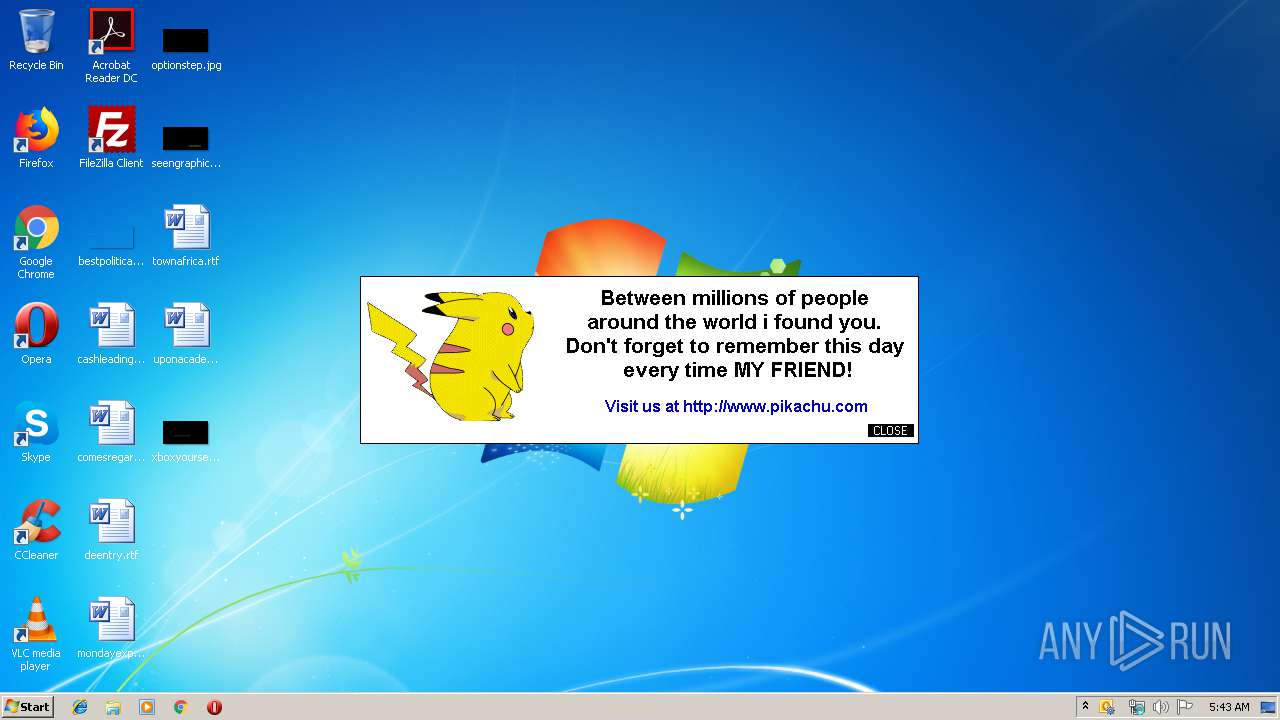
| ProductName: | PikachuPokemon |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | PikachuPokemon |
| OriginalFileName: | PikachuPokemon.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-May-2000 04:27:04 |
| Detected languages: |
|
| ProductName: | PikachuPokemon |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | PikachuPokemon |
| OriginalFilename: | PikachuPokemon.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 09-May-2000 04:27:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004318 | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.5798 |
.data | 0x00006000 | 0x00000A5C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00007000 | 0x000005F4 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.69293 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.12379 | 520 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 2.70964 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3136 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3648 | "C:\Users\admin\AppData\Local\Temp\Email-Worm.Win32.Pikachu.exe" | C:\Users\admin\AppData\Local\Temp\Email-Worm.Win32.Pikachu.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
668
Read events
573
Write events
82
Delete events
13
Modification events
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | f~" |
Value: 667E2200400C0000010000000000000000000000 | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 400C00002692EEE4FF65D50100000000 | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220206240 | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | delete value | Name: | f~" |
Value: 667E2200400C0000010000000000000000000000 | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Display Types\Balloons |
| Operation: | write | Name: | HWND64ForOrphanedNotIcon |
Value: 44010100 | |||
| (PID) Process: | (3136) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ca" |
Value: 63612200400C0000020000000000000000010000010000008C0000006800000063003A005C00700072006F006700720061006D002000660069006C00650073005C006D006900630072006F0073006F006600740020006F00660066006900630065005C006F0066006600690063006500310034005C0061006400640069006E0073005C0063006F006C006C006500610067007500650069006D0070006F00720074002E0064006C006C0000006D006900630072006F0073006F006600740020007300680061007200650070006F0069006E0074002000730065007200760065007200200063006F006C006C0065006100670075006500200069006D0070006F007200740020006100640064002D0069006E000000 | |||
Executable files
0
Suspicious files
1
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3136 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR96C6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3648 | Email-Worm.Win32.Pikachu.exe | C:\Users\admin\AppData\Local\Temp\~DFA1DDEC7AAA149875.TMP | — | |
MD5:— | SHA256:— | |||
| 3136 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | binary | |
MD5:74B3D4F0432452FBE9315EA836235498 | SHA256:0637332493693648B8E936825B2C74F0FF2195569AB7F95C6008CBD67C9E1B9E | |||
| 3136 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{AEEDF59F-3CDC-4B96-AF87-FBDDFB505140}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 3136 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_D0B7FB88D7FA3A42BCCFC7828597E7E0.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 3136 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_4857048C2EB09948A586E3C24A49EBFA.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3136 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_8FD05F5A0860514D898B71F65216DAED.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 3136 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_341047E9F1BCEE459235BDBA621D3296.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 3136 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_46A1C758042C1E47A123372DA25122FE.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 3136 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3136 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3136 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |