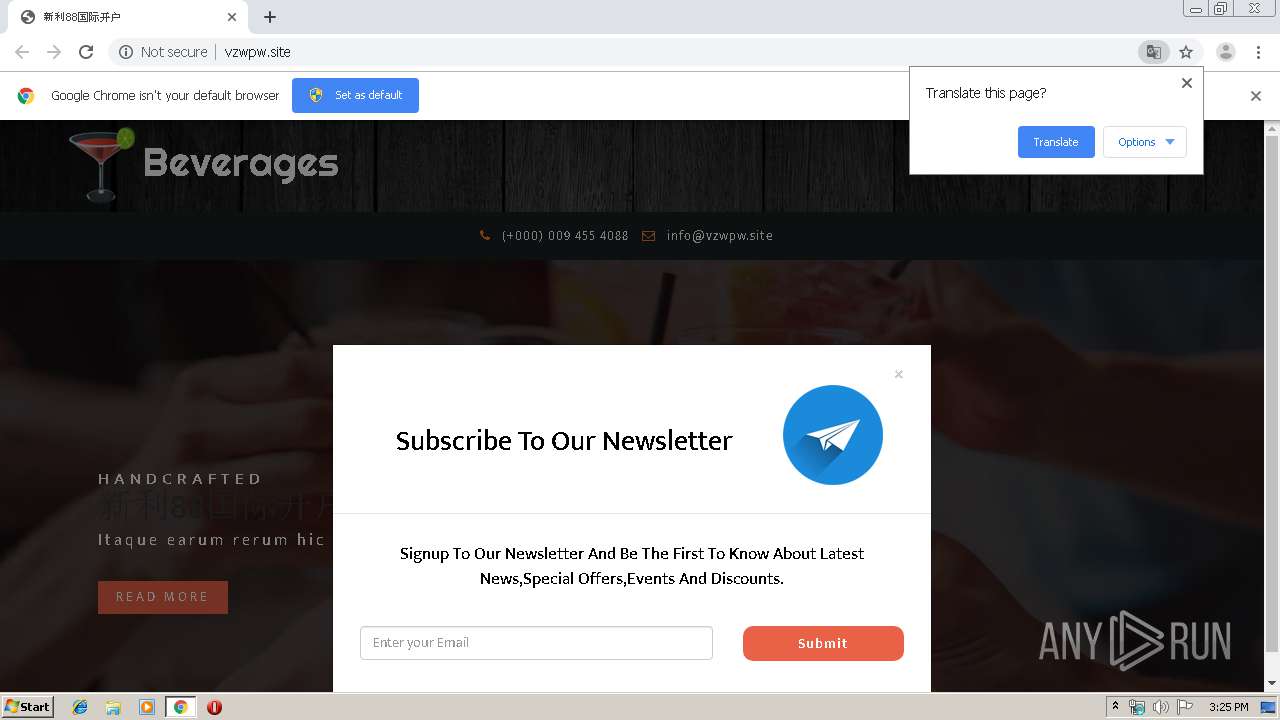
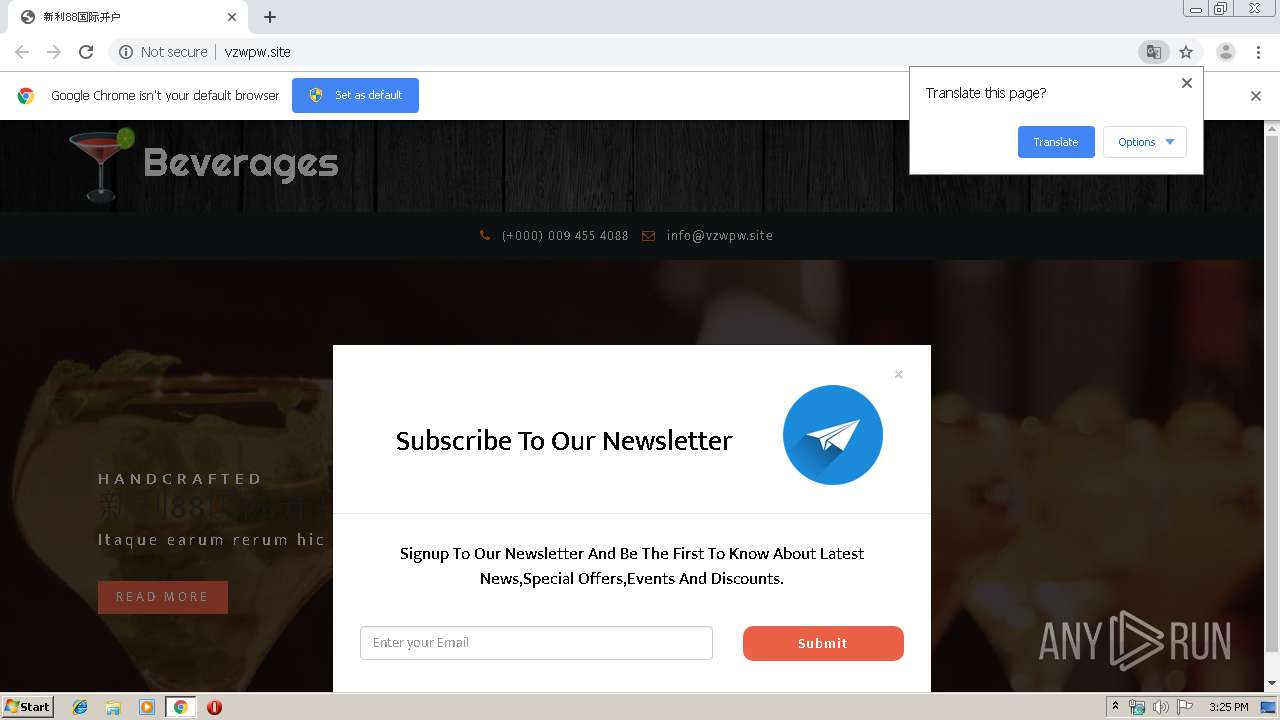
| URL: | http://vzwpw.site/ |
| Full analysis: | https://app.any.run/tasks/7c61e276-6893-4204-b648-2cdd18d8cc0d |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 15:24:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 199EE95C0D4ECCF72F2B91DD807570DF |
| SHA1: | 1CC987D37DB3505DC5031403BF9B488CE36AC513 |
| SHA256: | E1CB7AC7EB4D7D54CBD0CDD14BC51B590AFCE6AFB0F0821364D4BB38F0B39842 |
| SSDEEP: | 3:N1KI+bVK:CIIVK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3960)
INFO
Application launched itself
- chrome.exe (PID: 3960)
Reads the hosts file
- chrome.exe (PID: 3960)
- chrome.exe (PID: 3684)
Reads settings of System Certificates
- chrome.exe (PID: 3684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6746107062743733301 --mojo-platform-channel-handle=4304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3999893436110611478 --mojo-platform-channel-handle=4116 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14110273037746308400 --mojo-platform-channel-handle=4268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14517395518967354246 --mojo-platform-channel-handle=3848 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2828709717244423530 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10028671244813825635 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16594369844181811886 --mojo-platform-channel-handle=4012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5391971561006288413 --mojo-platform-channel-handle=4024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11977511684712355606 --mojo-platform-channel-handle=3732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,11071447129527600381,929086740463369956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11621363282450734538 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
623
Read events
522
Write events
96
Delete events
5
Modification events
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3960-13223748299577125 |
Value: 259 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
42
Text files
314
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a5333904-d326-43af-b03e-a3f3829155c7.tmp | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF38e1a5.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF38e166.TMP | text | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF38e118.TMP | text | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
31
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/21/css/bootstrap.css | ZA | text | 25.9 Kb | suspicious |
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/21/css/style.css | ZA | text | 11.1 Kb | suspicious |
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/ | ZA | html | 14.0 Kb | suspicious |
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/21/css/cm-overlay.css | ZA | text | 1.21 Kb | suspicious |
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/21/css/zoomslider.css | ZA | text | 1.12 Kb | suspicious |
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/21/css/owl.carousel.css | ZA | text | 2.07 Kb | suspicious |
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/21/js/modernizr-2.6.2.min.js | ZA | html | 7.76 Kb | suspicious |
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/21/js/jquery.zoomslider.min.js | ZA | text | 2.11 Kb | suspicious |
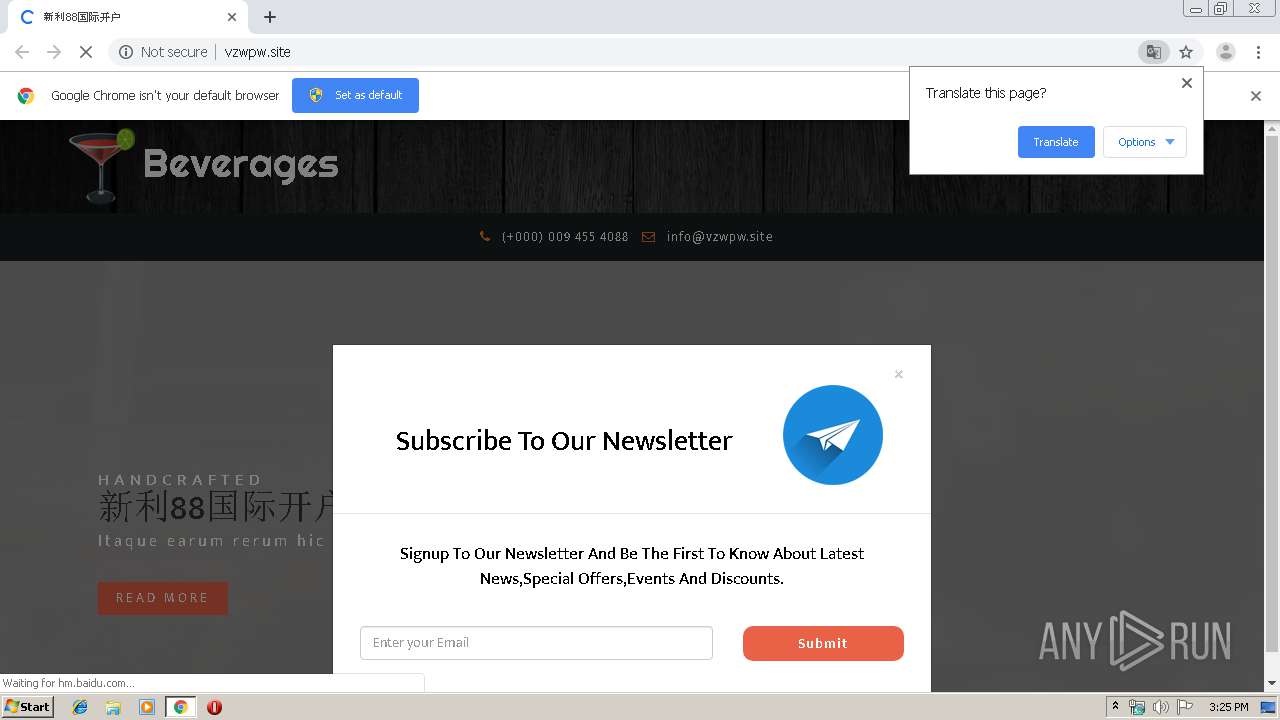
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/mypic.js | ZA | text | 677 b | suspicious |
3684 | chrome.exe | GET | 200 | 156.254.199.206:80 | http://vzwpw.site/21/css/font-awesome.css | ZA | text | 8.05 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3684 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3684 | chrome.exe | 156.254.199.206:80 | vzwpw.site | MacroLAN | ZA | suspicious |
3684 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3684 | chrome.exe | 172.217.16.131:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3684 | chrome.exe | 111.206.37.189:80 | push.zhanzhang.baidu.com | China Unicom Beijing Province Network | CN | malicious |
3684 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
3684 | chrome.exe | 172.217.23.138:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3684 | chrome.exe | 61.135.185.248:80 | push.zhanzhang.baidu.com | China Unicom Beijing Province Network | CN | unknown |
— | — | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vzwpw.site |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
push.zhanzhang.baidu.com |
| whitelisted |
hm.baidu.com |
| whitelisted |
clients1.google.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
3g.sbemt.site |
| unknown |