| File name: | genius.exe |
| Full analysis: | https://app.any.run/tasks/be11007f-ca6e-4443-bb61-eb32c2ced65b |
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2018, 03:10:59 |
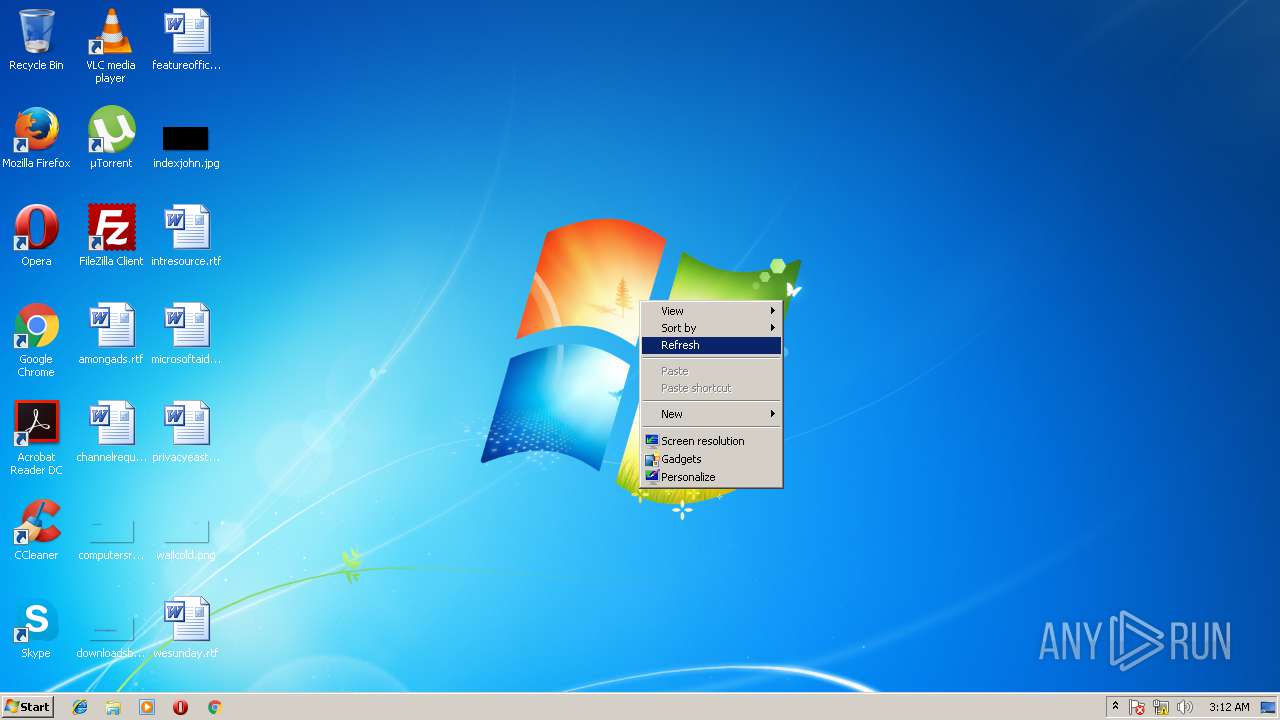
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F1DAF54B2F3AE72BEF15AAC0E64A311A |
| SHA1: | 59C1E9B83B4EB4B420B2D418856315F8D8A8652A |
| SHA256: | E1C2F3C638018E62D63D4018B8ED6D9CC1BBB4B33945DBED4AFD91998BAE72C4 |
| SSDEEP: | 1536:aCUm7KFP2QuXYdsLP0DgXJFibM4Tf2nDcWm2131JSdVyULY+3uTvqcf+ne:aCuFP2lXIHDgXJFqM4TOIWm21FQ3KvqE |
MALICIOUS
Application loaded dropped or rewritten executable
- genius.exe (PID: 2960)
- genius.exe (PID: 3260)
SUSPICIOUS
Executes scripts
- genius.exe (PID: 2960)
INFO
Application launched itself
- chrome.exe (PID: 3188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:53:24+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 169984 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x355e |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:53:24 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:53:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006396 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46884 |
.rdata | 0x00008000 | 0x000012EC | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14841 |
.data | 0x0000A000 | 0x000270D8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1759 |
.ndata | 0x00032000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003D000 | 0x000009E0 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.50936 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20956 | 716 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
39
Monitored processes
8
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2960 | "C:\Users\admin\AppData\Local\Temp\genius.exe" | C:\Users\admin\AppData\Local\Temp\genius.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3216 --on-initialized-event-handle=296 --parent-handle=300 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\genius.exe" /notify | C:\Users\admin\AppData\Local\Temp\genius.exe | — | wscript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 3304 | C:\Windows\system32\wscript.exe /e:jscript /b "C:\Users\admin\AppData\Local\Temp\genius.js" | C:\Windows\system32\wscript.exe | — | genius.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1604,8348977891804140633,17832837675187754757,131072 --service-pipe-token=2EFEAF80965EEAC11883AA48B8729A0B --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=2EFEAF80965EEAC11883AA48B8729A0B --renderer-client-id=4 --mojo-platform-channel-handle=1616 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 3976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1604,8348977891804140633,17832837675187754757,131072 --service-pipe-token=56DE531B6BBE9EE4636F47329A3AE86D --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=56DE531B6BBE9EE4636F47329A3AE86D --renderer-client-id=2 --mojo-platform-channel-handle=1744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 3984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.100 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f207d7c,0x6f207da4,0x6f207d8c | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
932
Read events
861
Write events
68
Delete events
3
Modification events
| (PID) Process: | (2960) genius.exe | Key: | HKEY_CURRENT_USER\Software\Genius |
| Operation: | write | Name: | LastTickCount |
Value: 1430046 | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2960) genius.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\genius_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
4
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | genius.exe | C:\Users\admin\AppData\Local\Temp\nsuD21F.tmp\info.txt | — | |
MD5:— | SHA256:— | |||
| 3260 | genius.exe | C:\Users\admin\AppData\Local\Temp\nsfEB74.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 3260 | genius.exe | C:\Users\admin\AppData\Local\Temp\nsfEB74.tmp\userid.dll | — | |
MD5:— | SHA256:— | |||
| 3260 | genius.exe | C:\Users\admin\AppData\Local\Temp\nsfEB74.tmp\nsJSON.dll | — | |
MD5:— | SHA256:— | |||
| 3260 | genius.exe | C:\Users\admin\AppData\Local\Temp\nsfEB74.tmp\inetc.dll | — | |
MD5:— | SHA256:— | |||
| 3260 | genius.exe | C:\Users\admin\AppData\Local\Temp\nsfEB74.tmp\info.txt | — | |
MD5:— | SHA256:— | |||
| 2960 | genius.exe | C:\Users\admin\AppData\Local\Temp\genius.js | text | |
MD5:— | SHA256:— | |||
| 2960 | genius.exe | C:\Users\admin\AppData\Local\Temp\nsuD21F.tmp\nsJSON.dll | executable | |
MD5:588DDECA425C424E21D07CA0C6BC3278 | SHA256:B8A48391A7CF1A04AC2928C9089D76375BCB9A773DB67388219558EE4872E902 | |||
| 2960 | genius.exe | C:\Users\admin\AppData\Local\Temp\nsuD21F.tmp\userid.dll | executable | |
MD5:— | SHA256:— | |||
| 3304 | wscript.exe | C:\Users\admin\AppData\Local\Temp\genius.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.224.66.119:80 | http://6bmd.com/query.php?product=5&channel=ffcvs&ss=1&id=33D6A71F28F6EF8D&version=&cmd=&custom1= | US | text | 7.64 Kb | suspicious |
— | — | GET | 200 | 34.224.66.119:80 | http://6bmd.com/query.php?product=5&channel=ffcvs&ss=1&id=33D6A71F28F6EF8D&version=¬ify=1&custom1= | US | text | 2 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 34.224.66.119:80 | 6bmd.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
6bmd.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
— | — | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |