| File name: | rundll32.exe_ |
| Full analysis: | https://app.any.run/tasks/a0c325a5-7d80-4aad-9f39-e32b94d57fbb |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2024, 06:14:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2EB5D76180CE7B3241B281FA79AB3483 |
| SHA1: | 06293DEA80E39C7EB7EE2BDB00D60B58D932FA8A |
| SHA256: | E1B9BEB4617A720D55AFAEC364941BB18EA2C456A8B06B30A736F0CBB5C297E8 |
| SSDEEP: | 12288:DTyjXW+48qWywrU4kGFezOAVuJ5PIGww7F5DO3HYffS:fIXW/8yw1ez54lIYF5SXYHS |
MALICIOUS
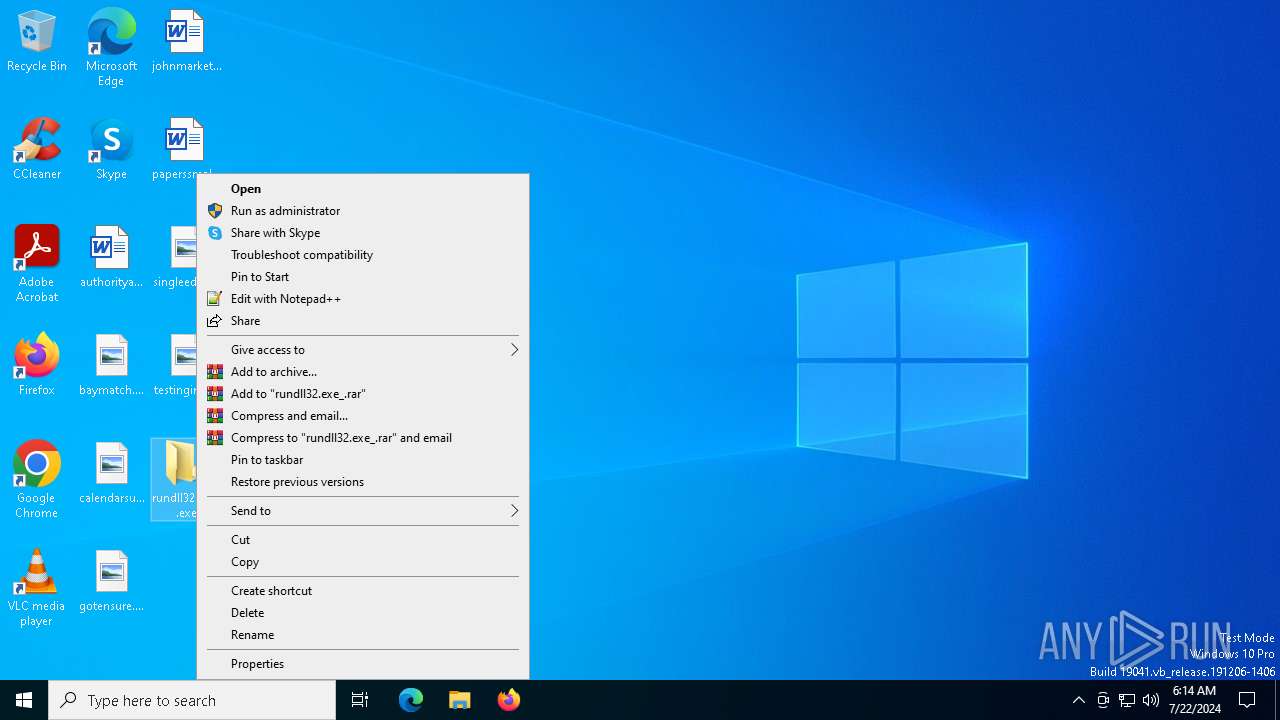
Changes appearance of the Explorer extensions
- rundll32.exe (PID: 7212)
- rundll32.exe_.exe (PID: 2116)
- rundll32.exe (PID: 8048)
Drops the executable file immediately after the start
- rundll32.exe_.exe (PID: 2116)
SUSPICIOUS
Reads security settings of Internet Explorer
- rundll32.exe (PID: 7212)
- rundll32.exe (PID: 8048)
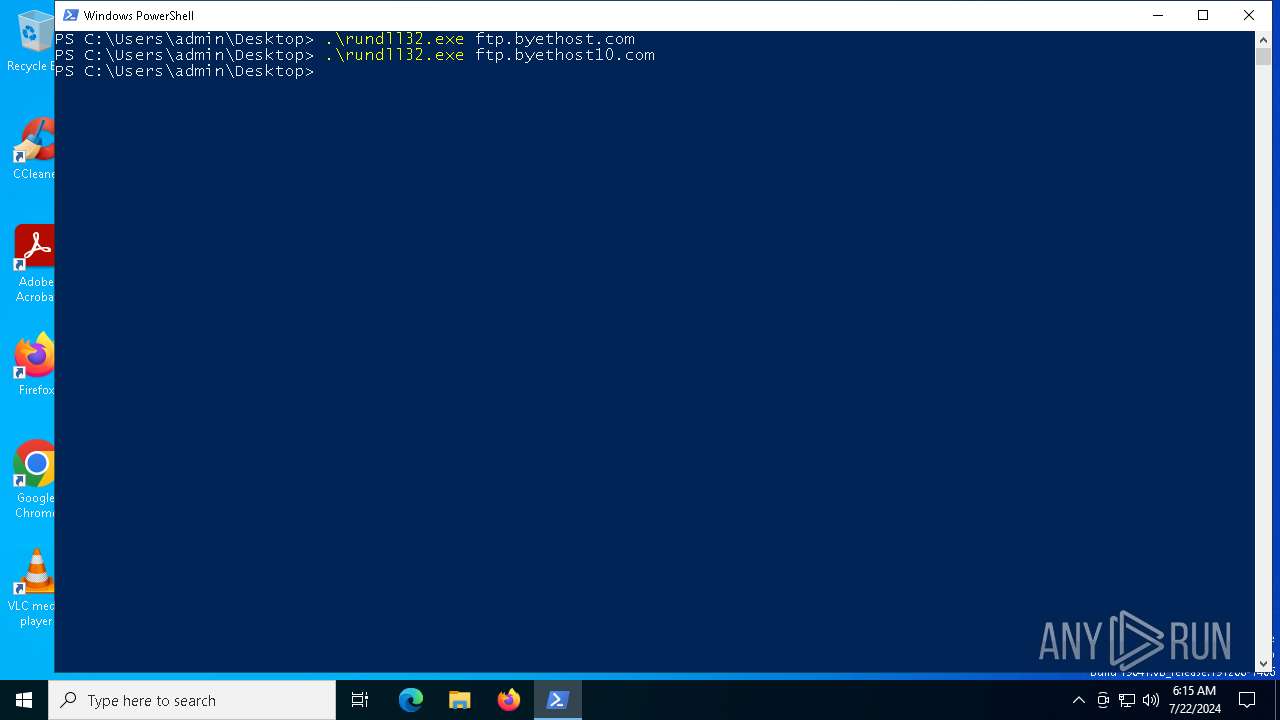
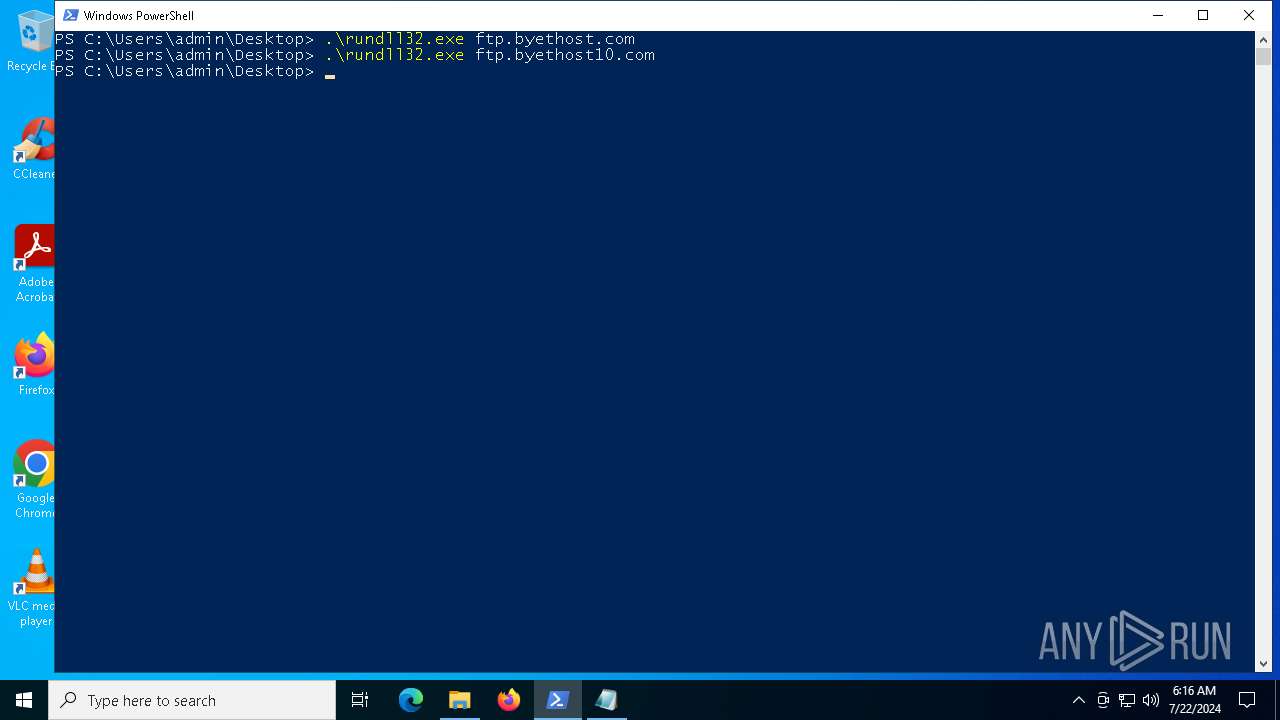
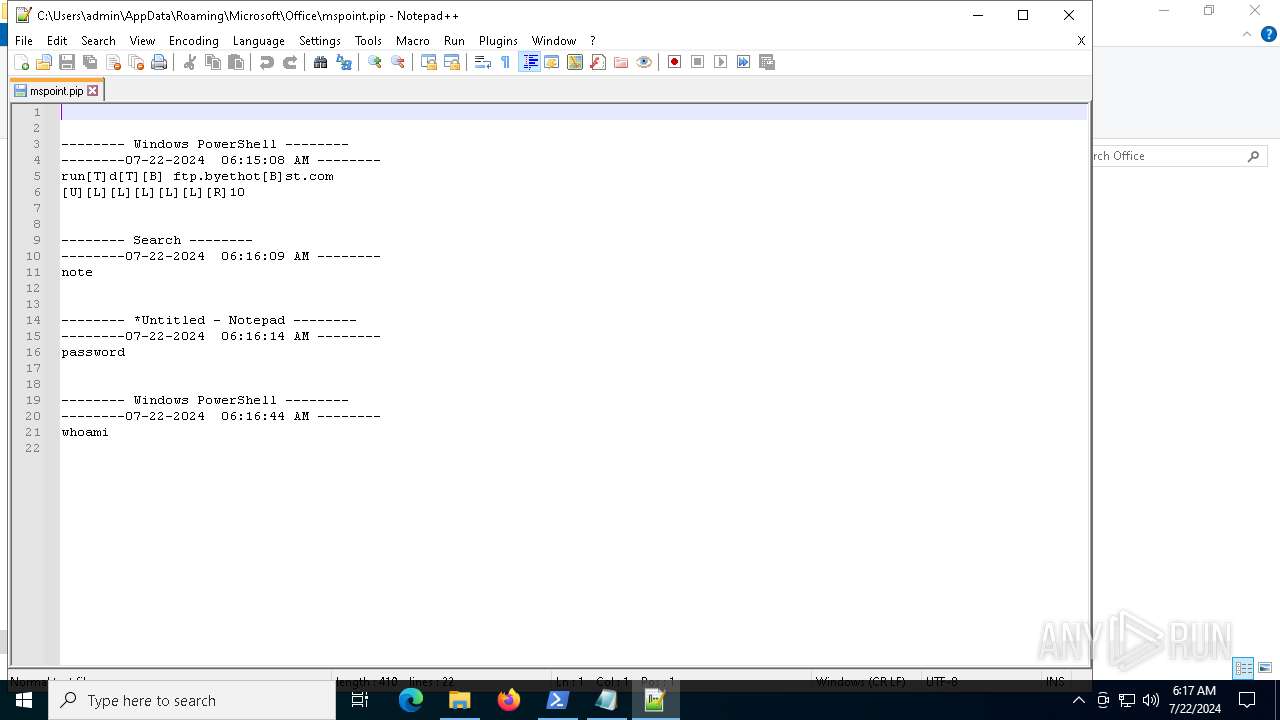
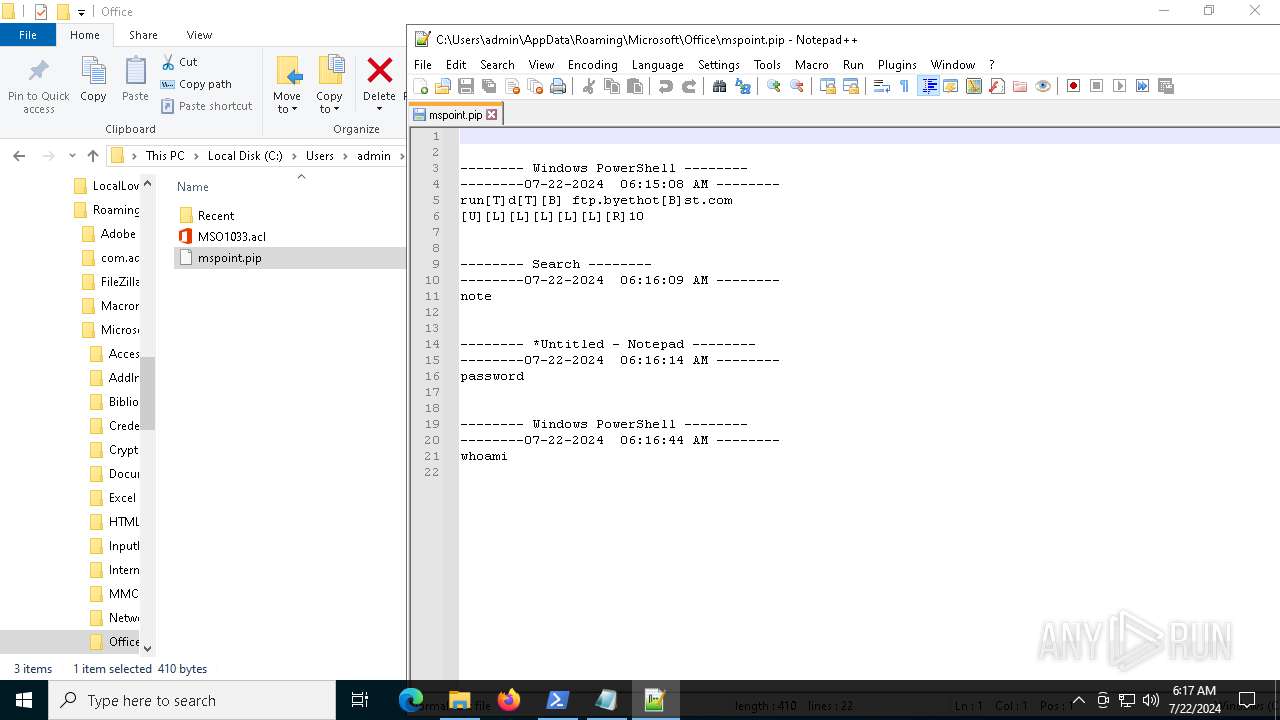
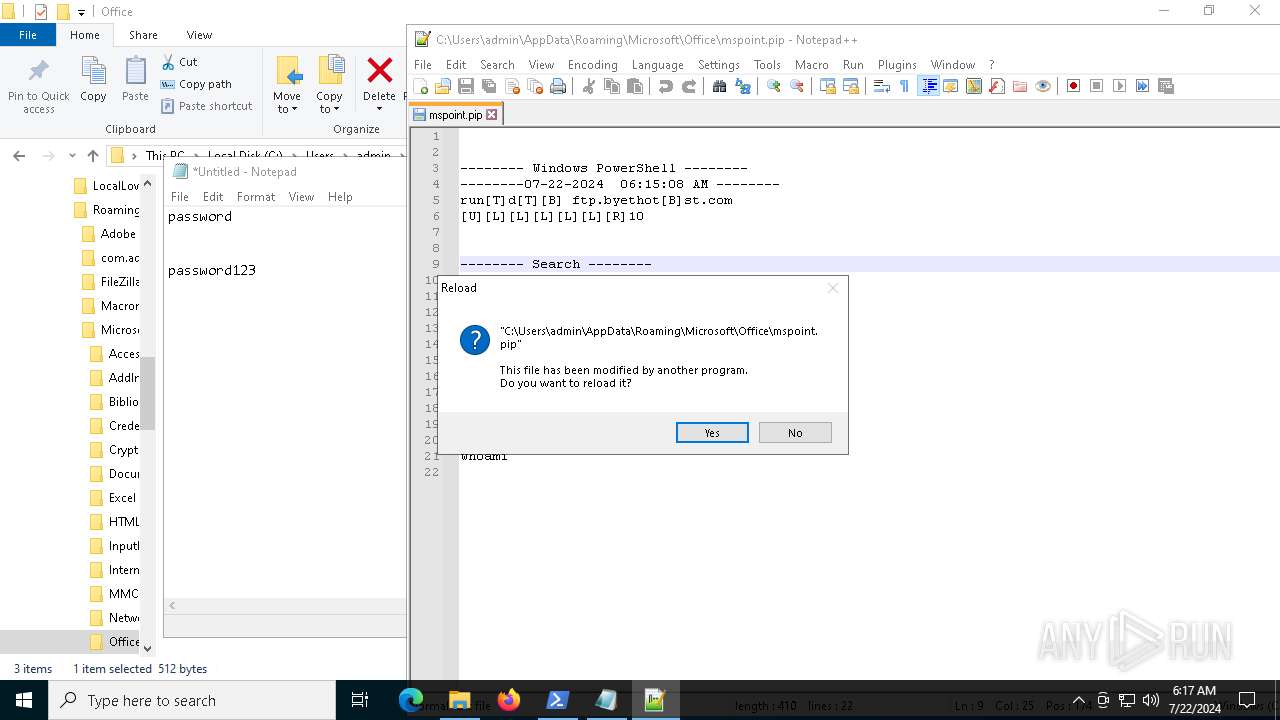
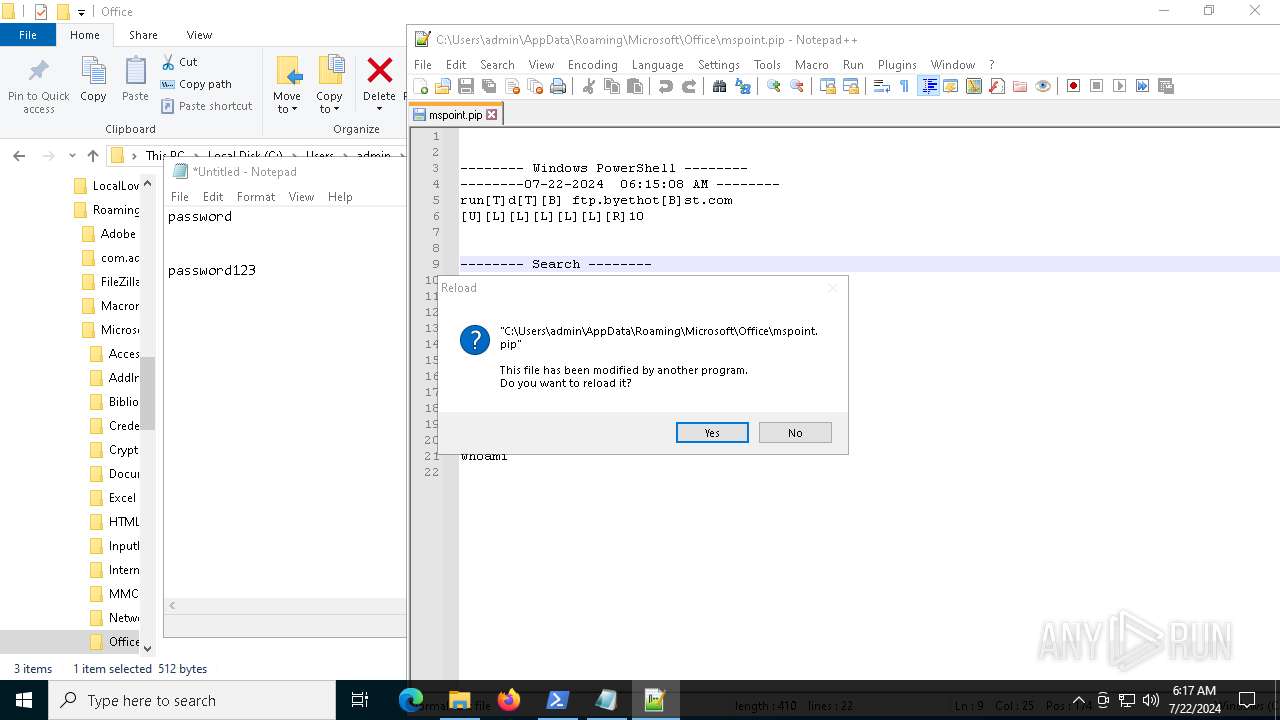
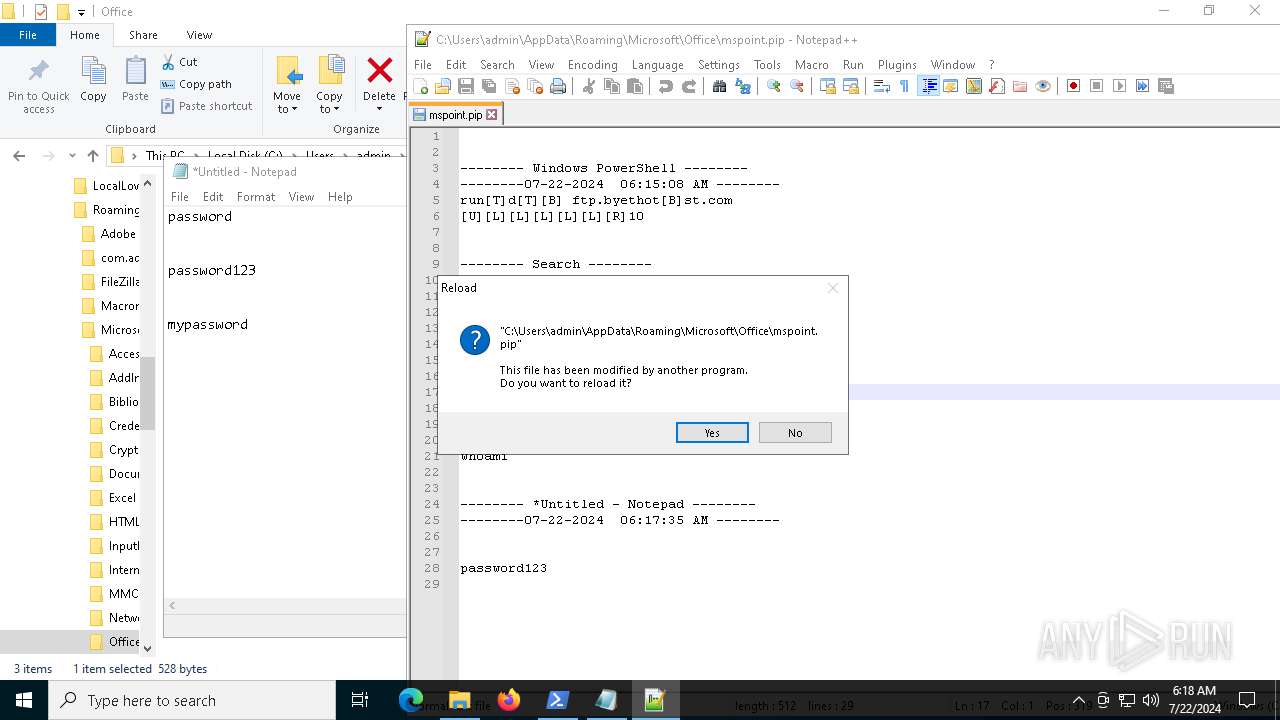
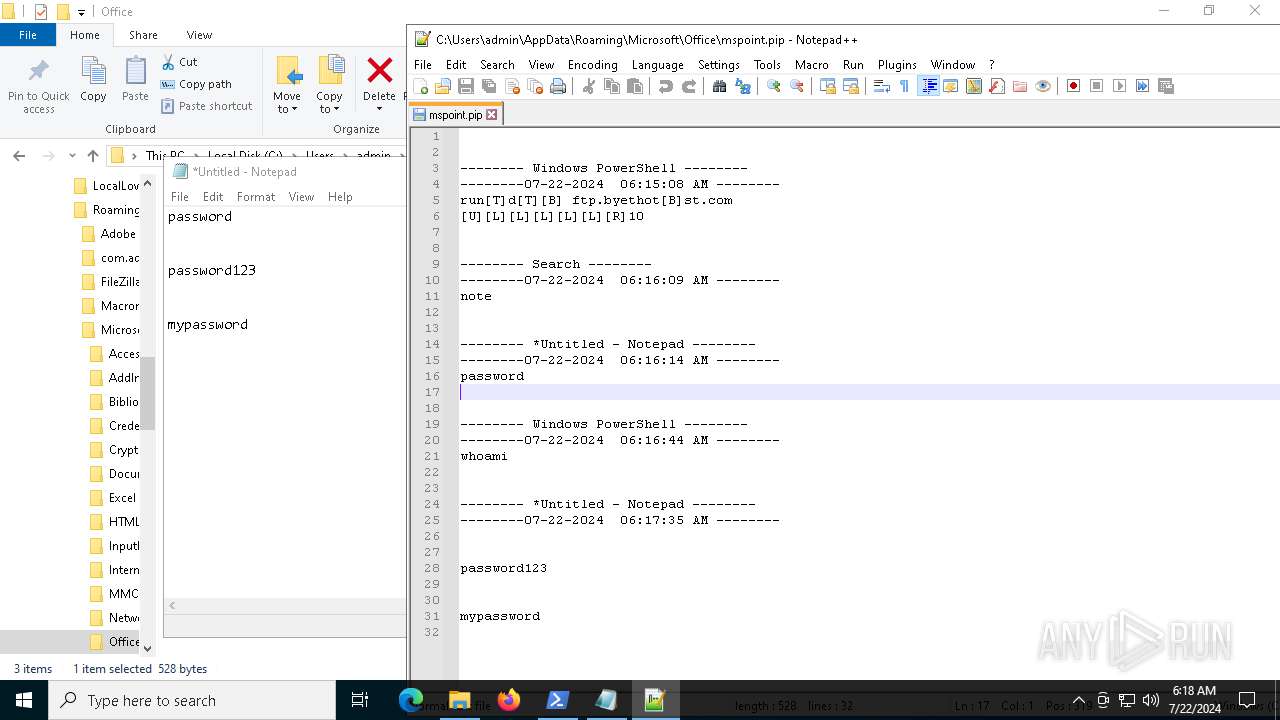
Connects to FTP
- rundll32.exe (PID: 7212)
- rundll32.exe (PID: 8048)
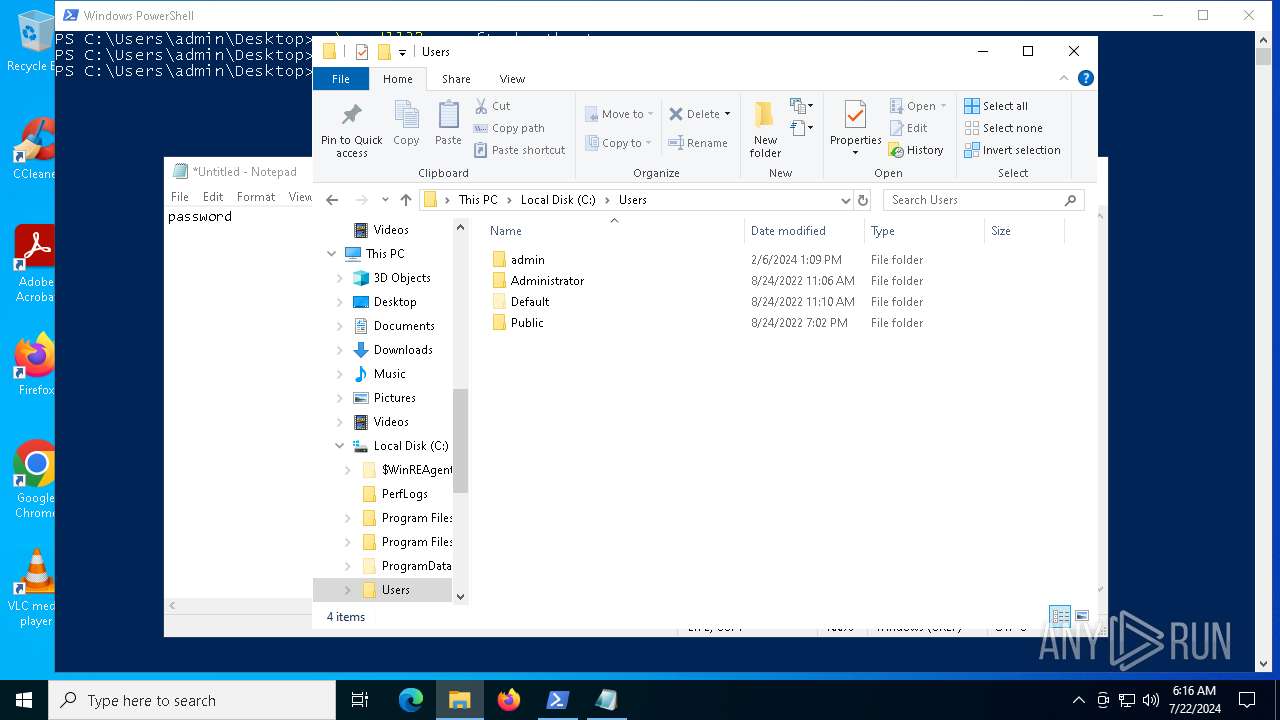
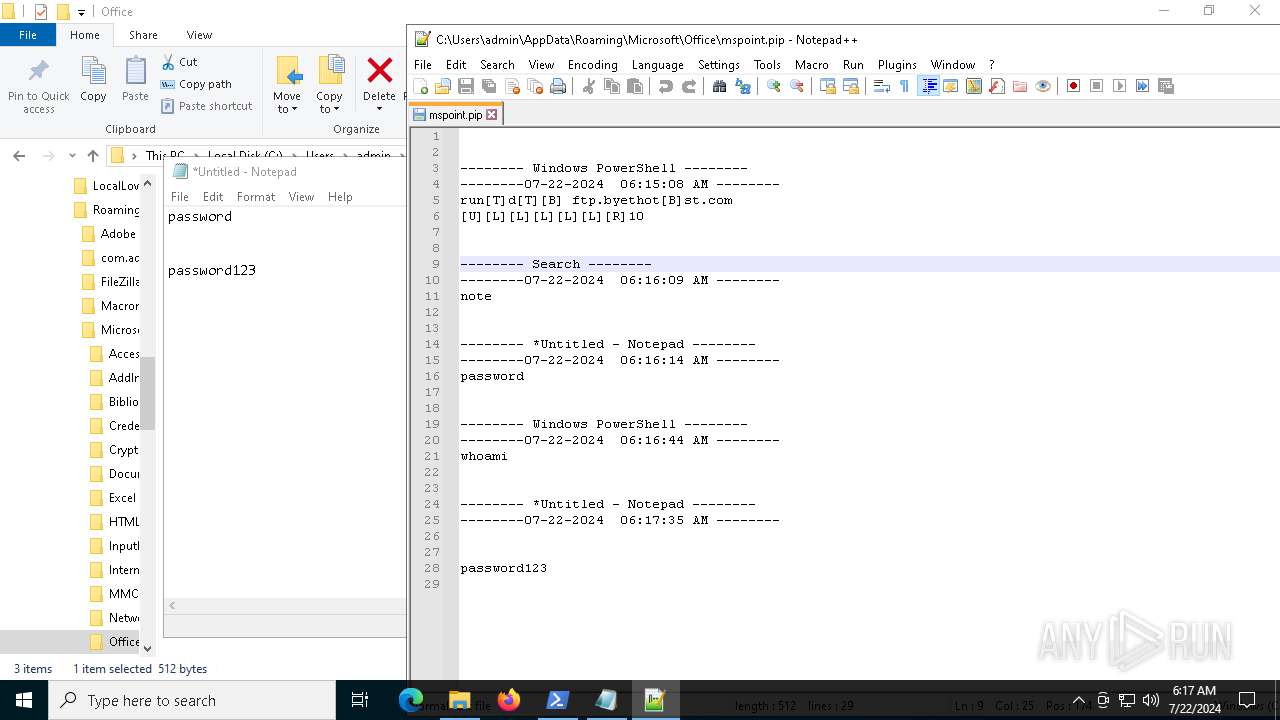
Identifying current user with WHOAMI command
- powershell.exe (PID: 6232)
INFO
Checks supported languages
- rundll32.exe_.exe (PID: 2116)
- rundll32.exe (PID: 7212)
- rundll32.exe (PID: 8048)
Reads the computer name
- rundll32.exe_.exe (PID: 2116)
- rundll32.exe (PID: 7212)
- rundll32.exe (PID: 8048)
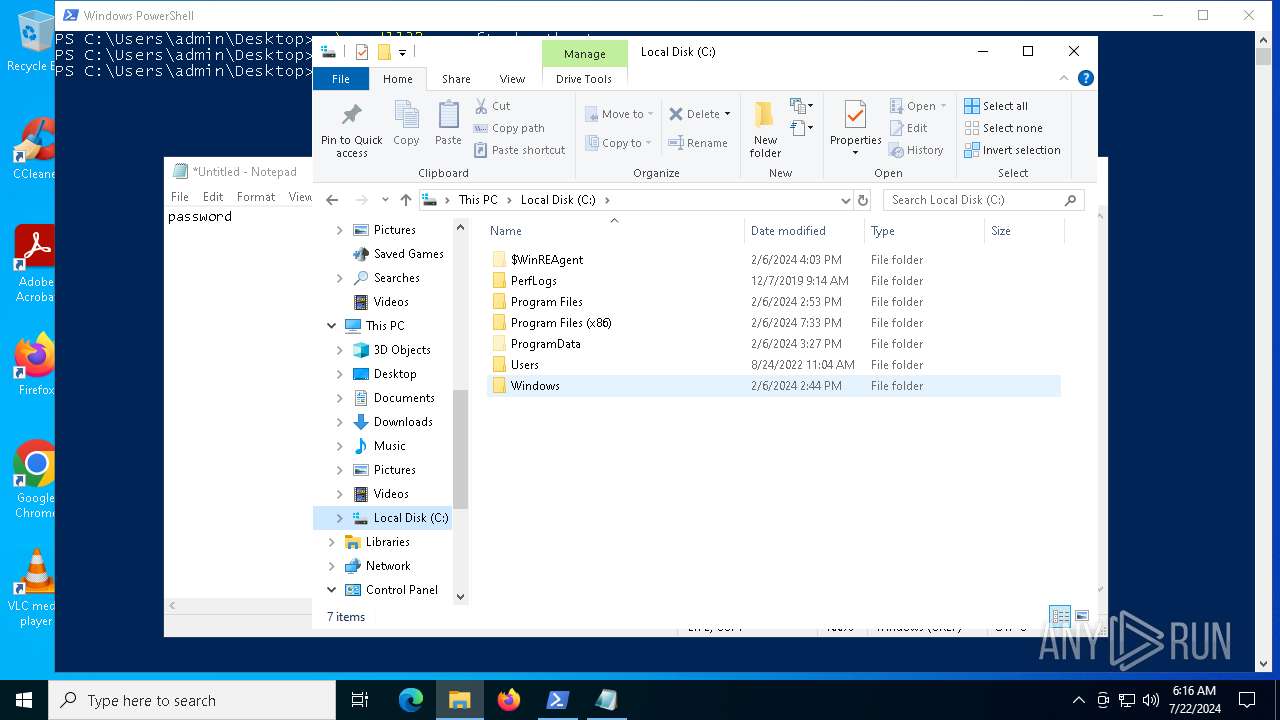
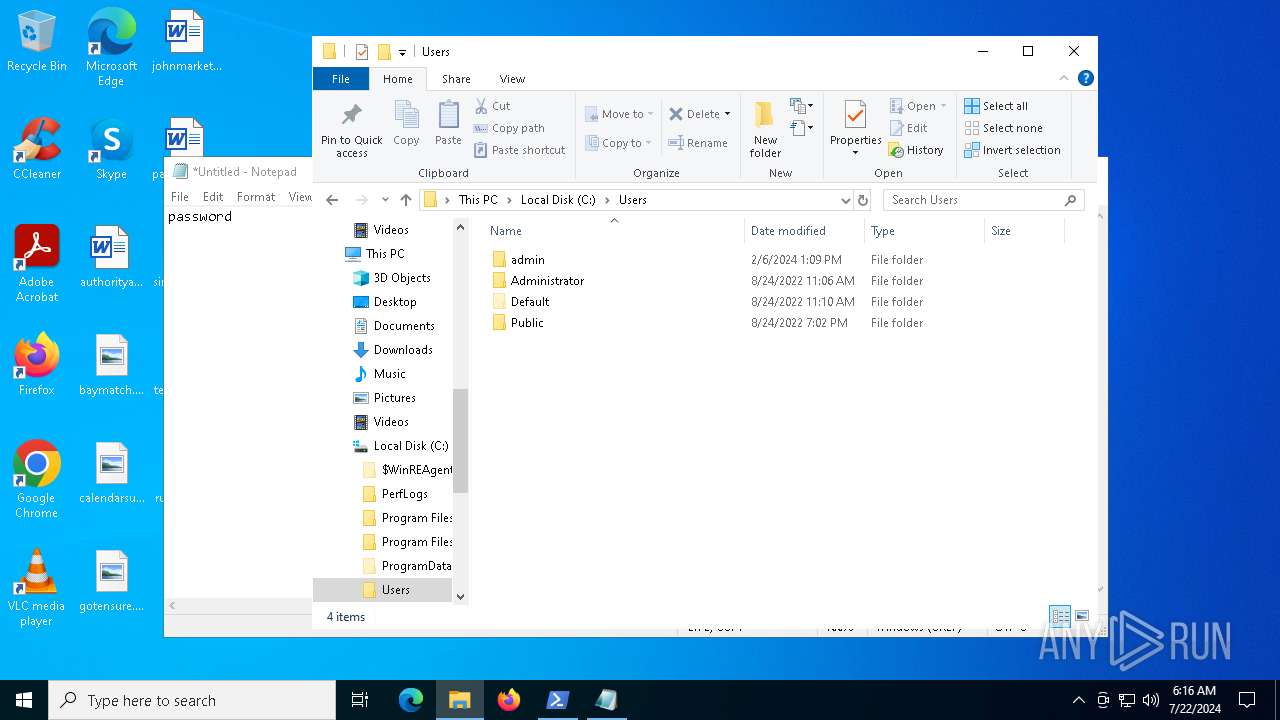
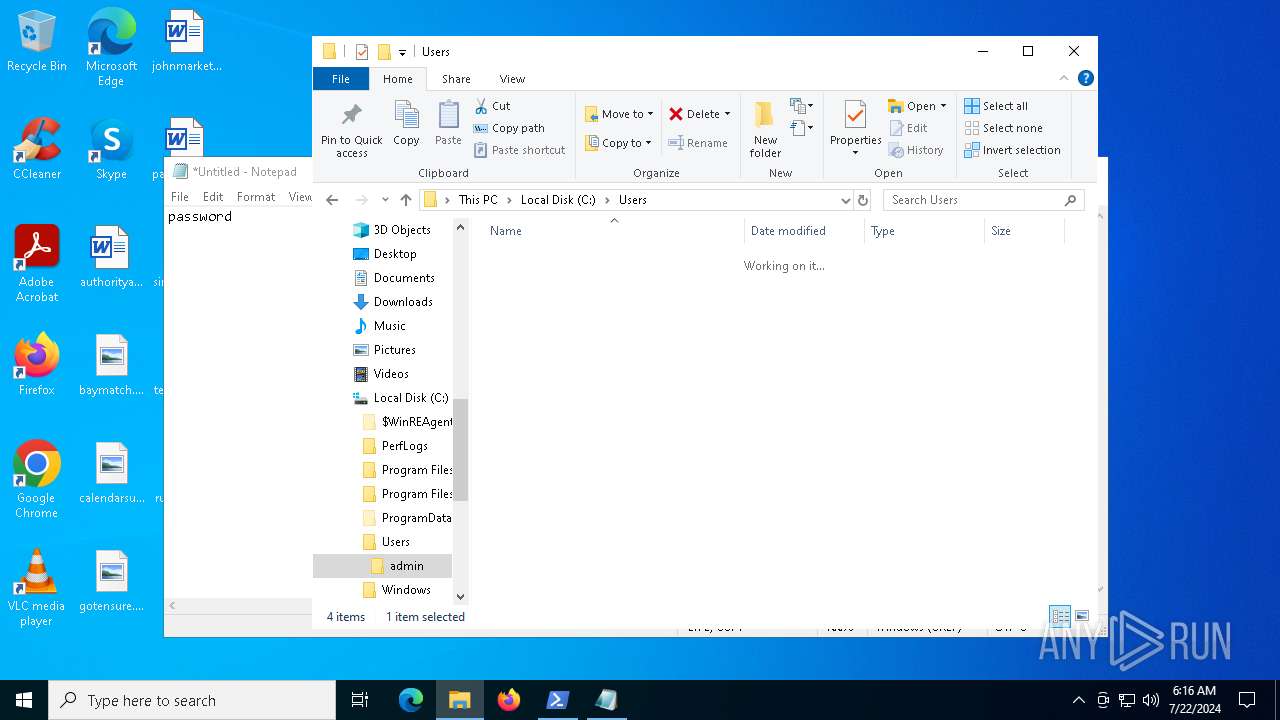
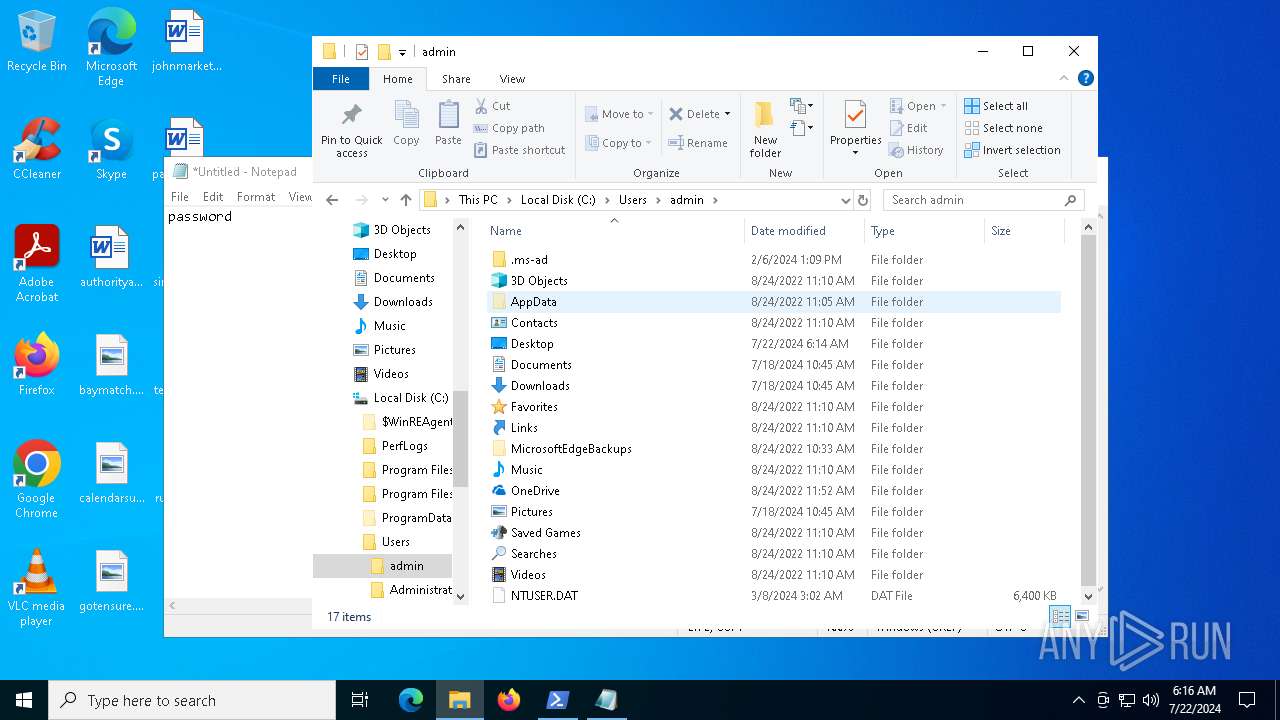
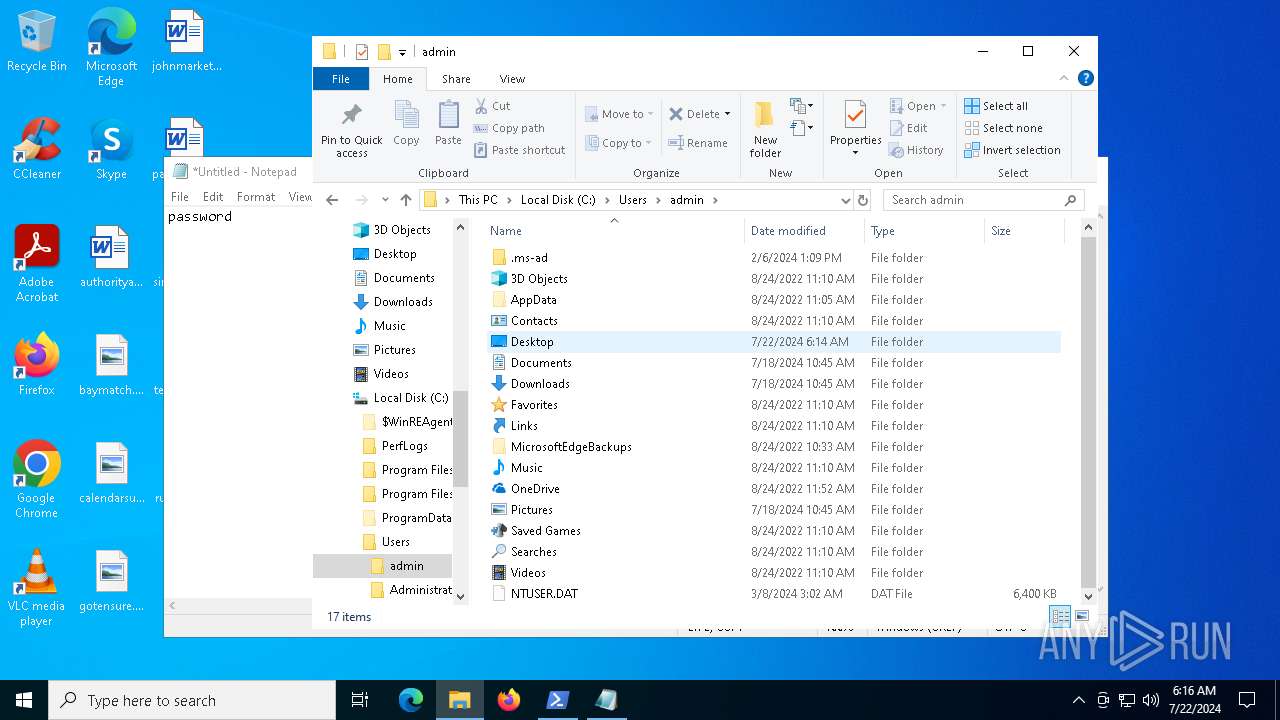
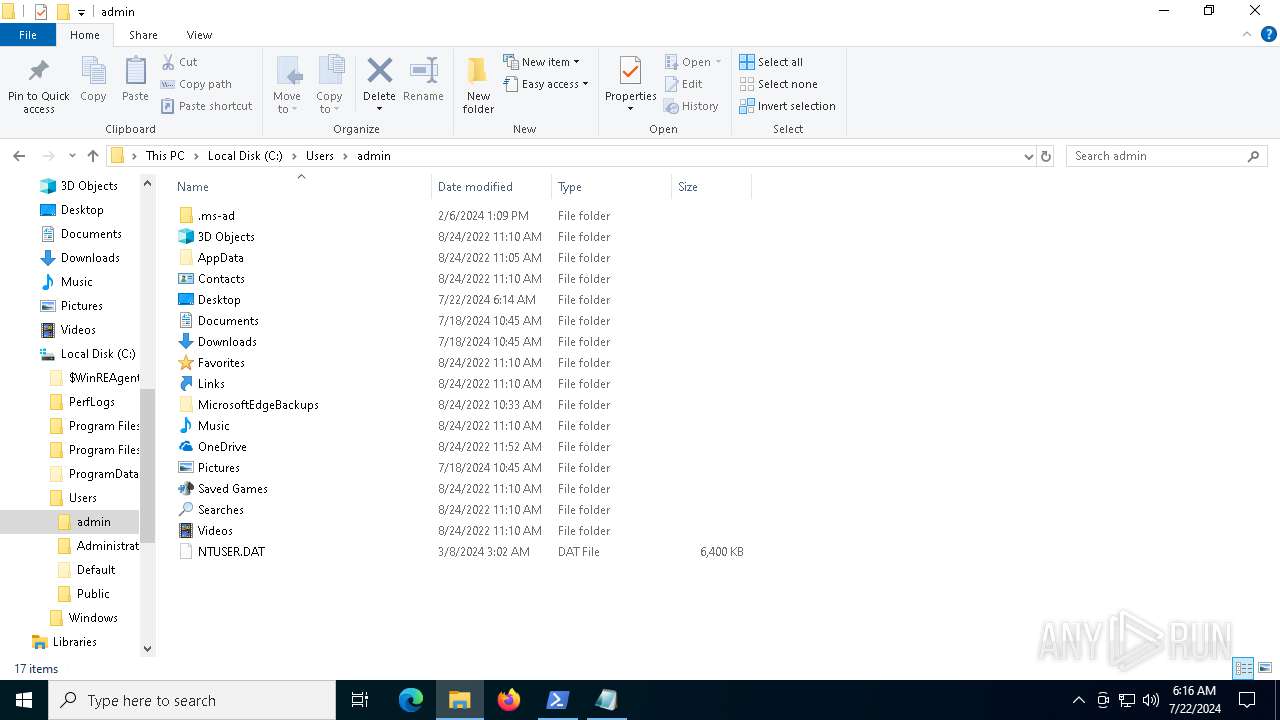
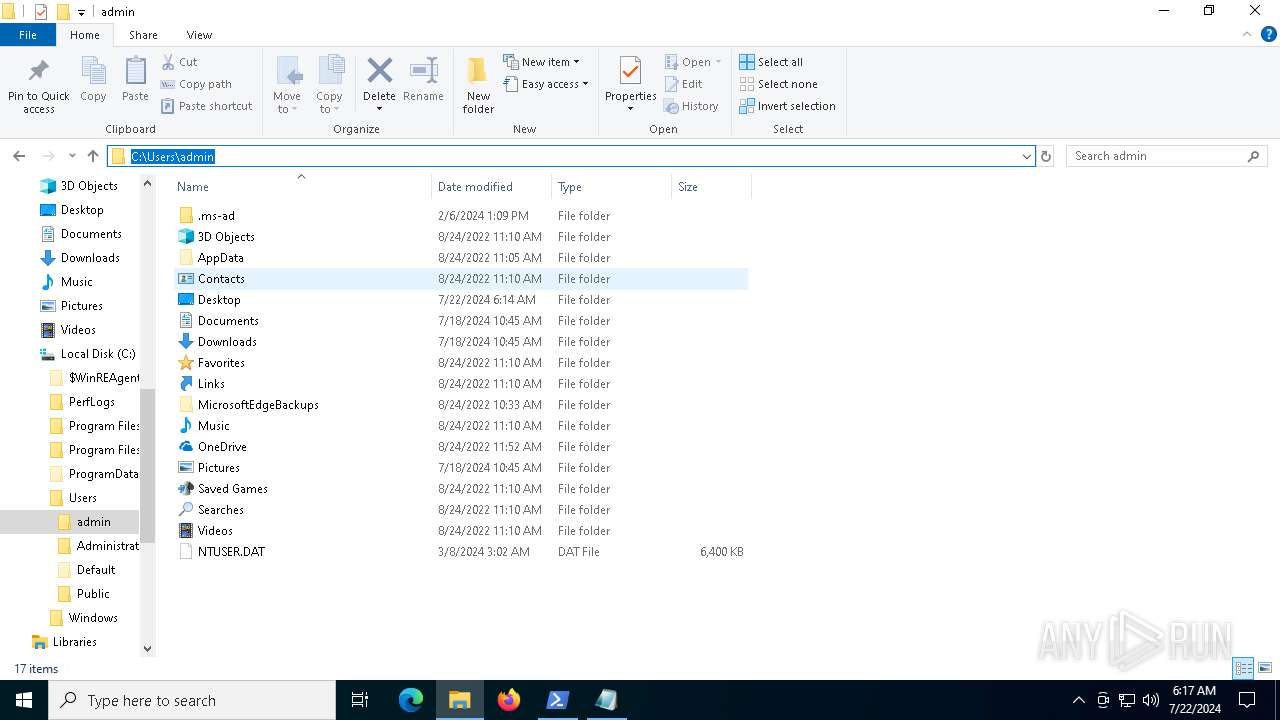
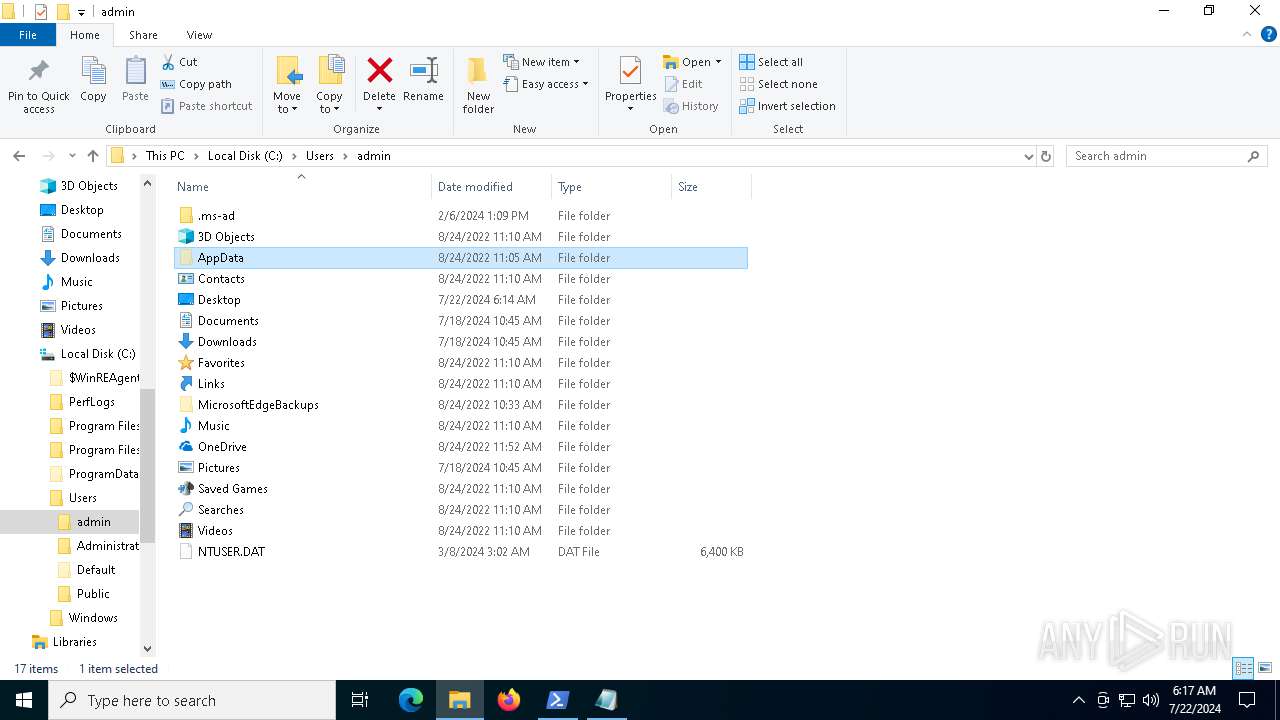
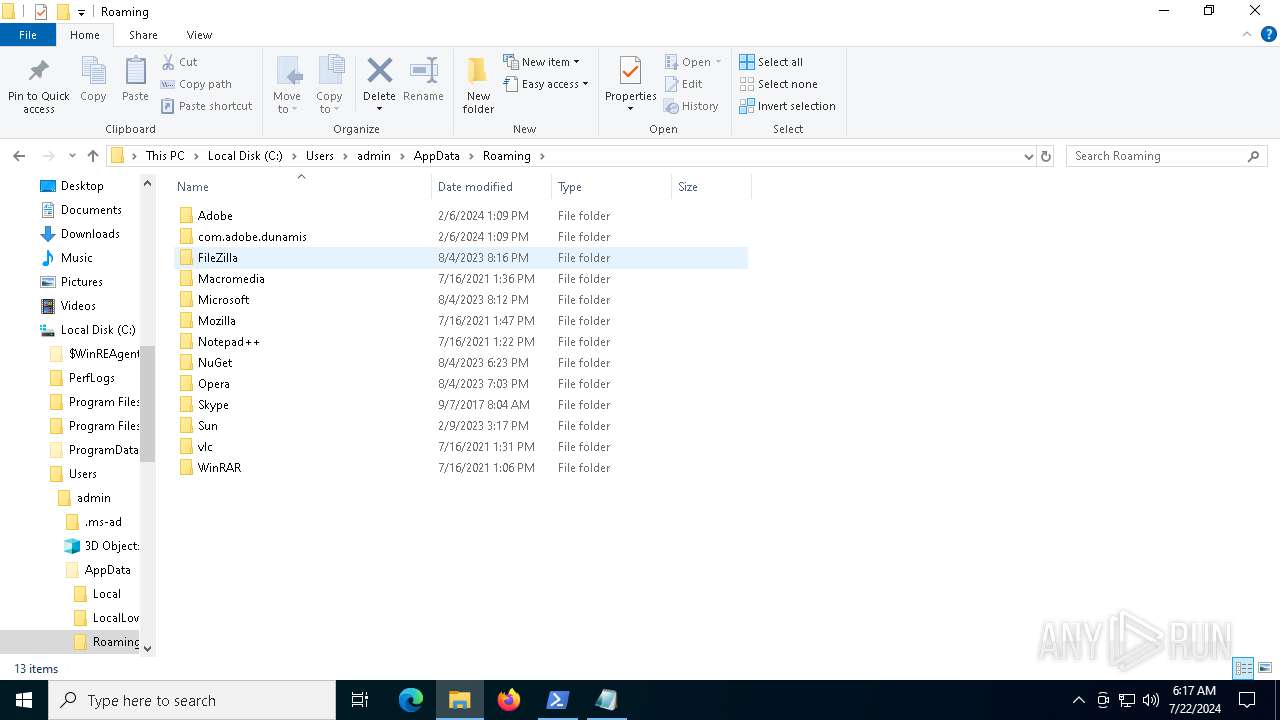
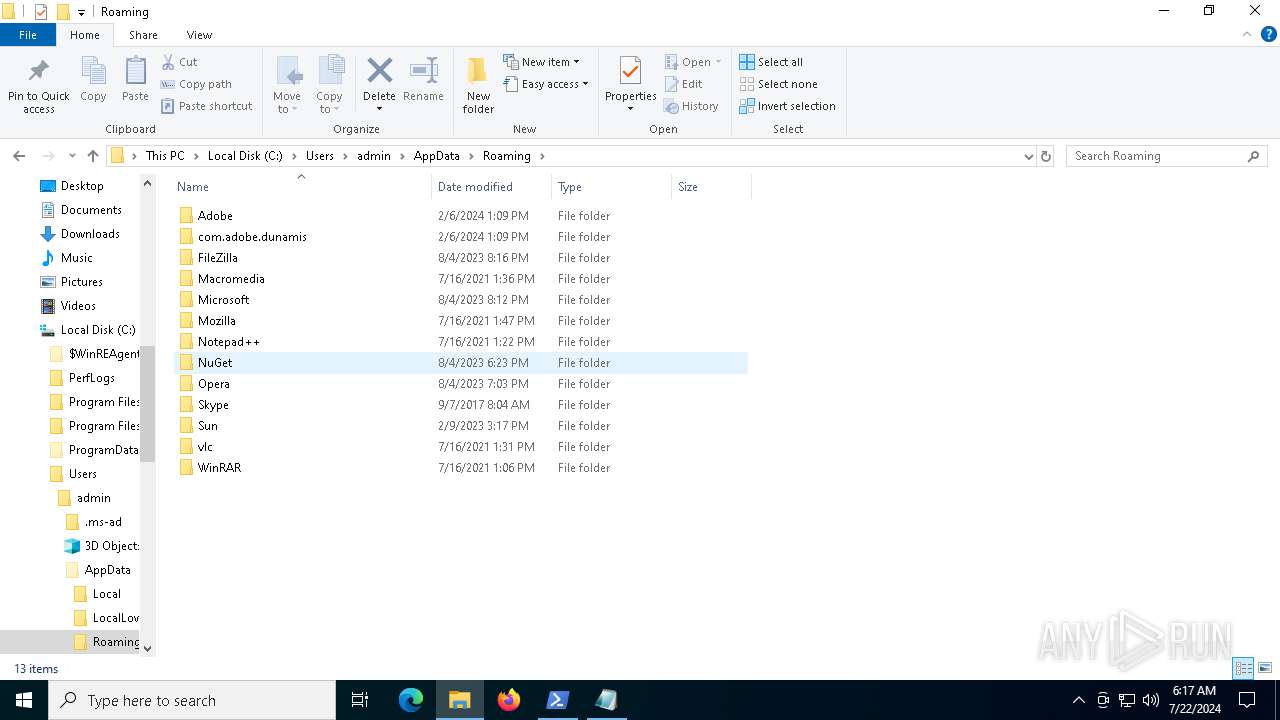
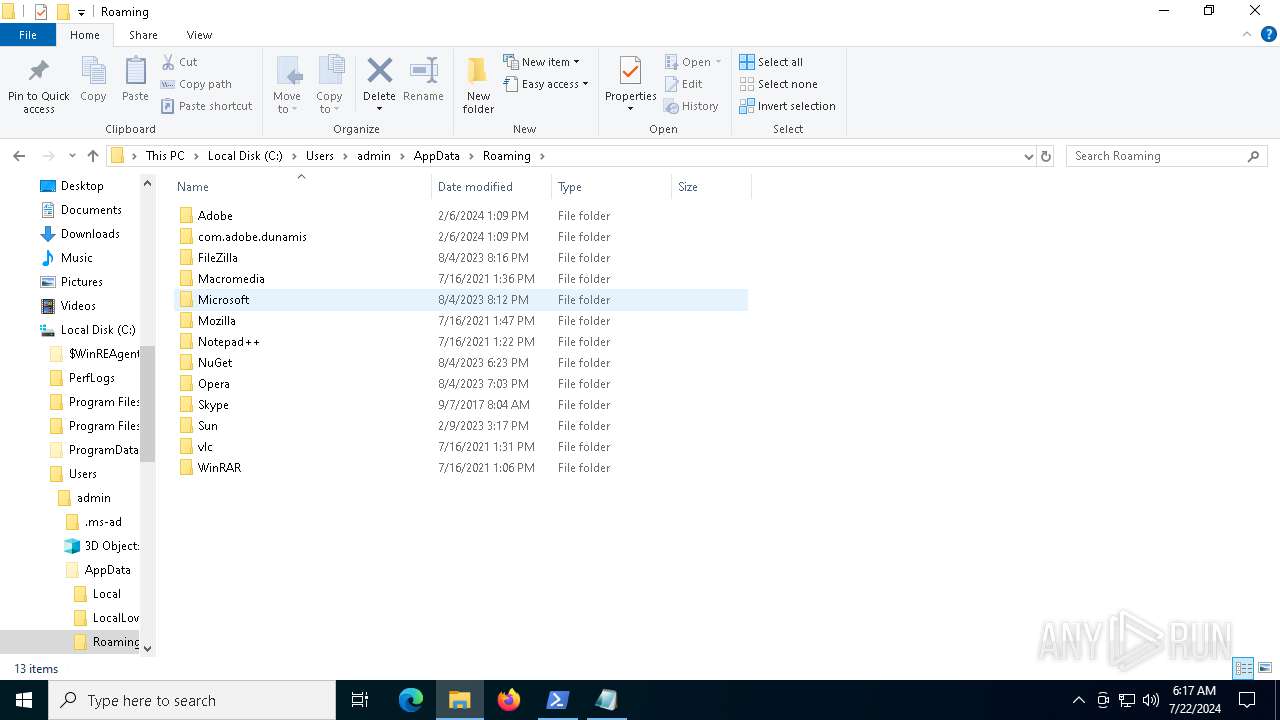
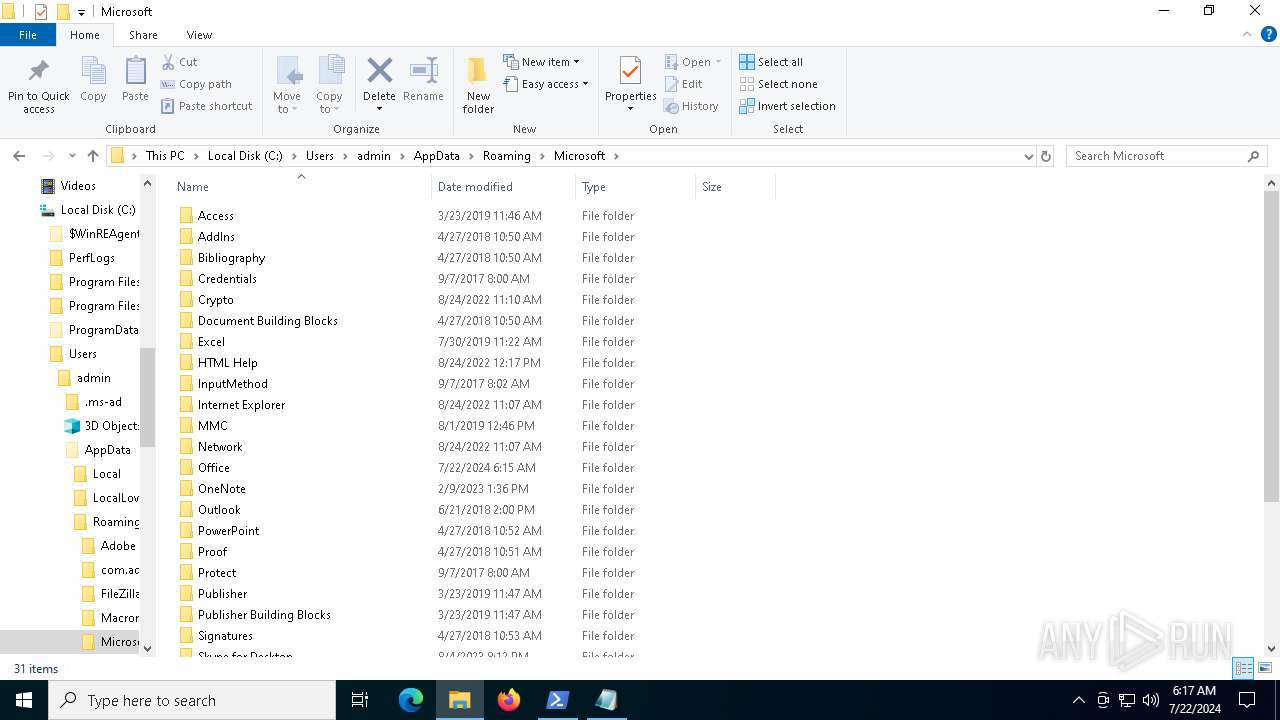
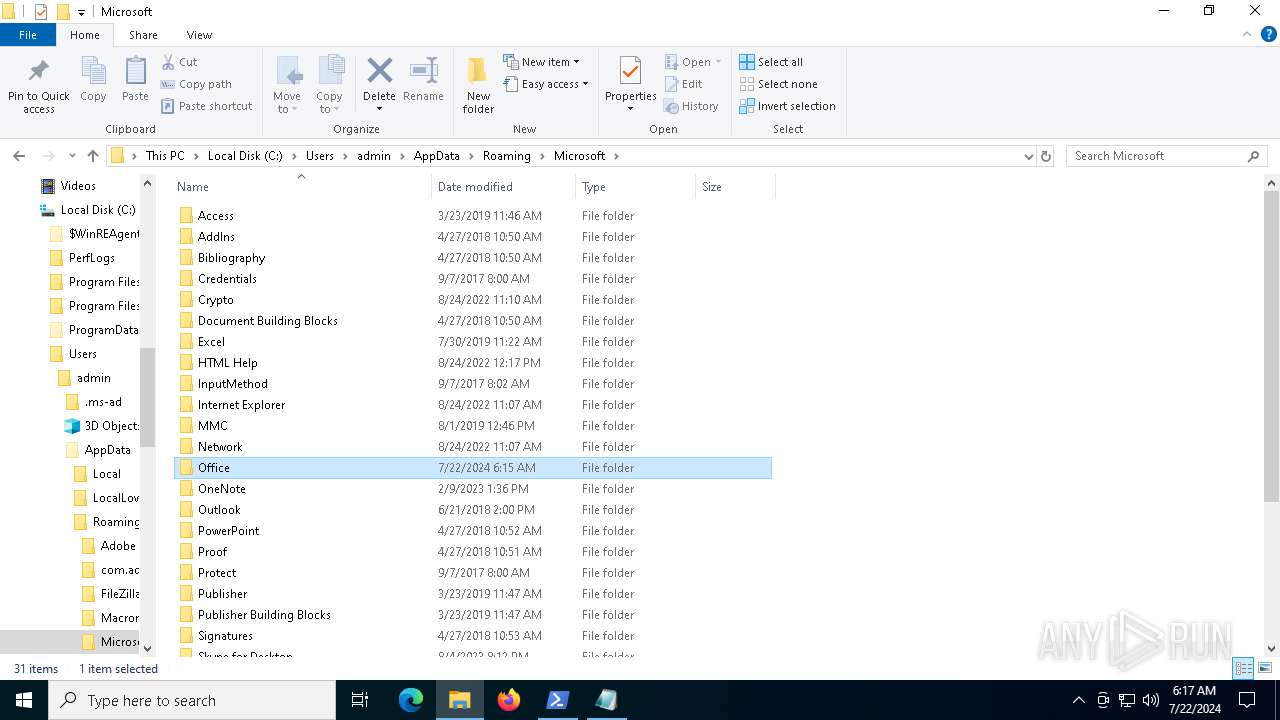
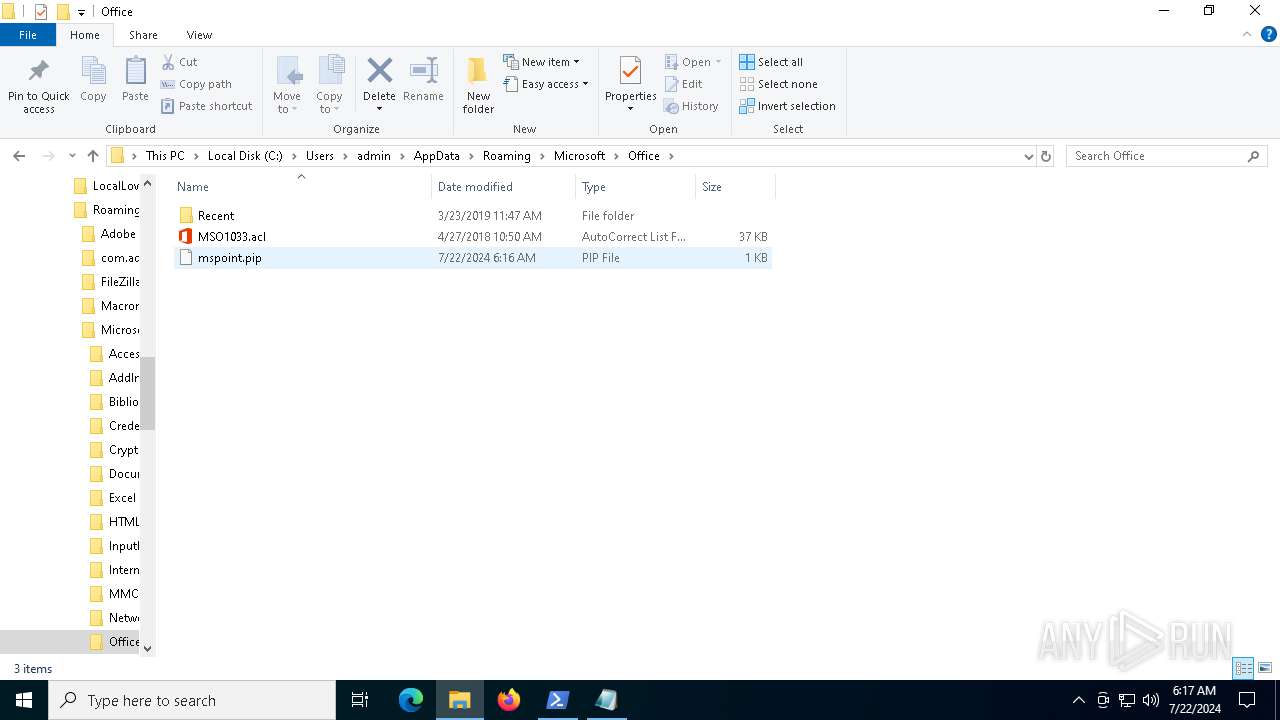
Creates files or folders in the user directory
- rundll32.exe_.exe (PID: 2116)
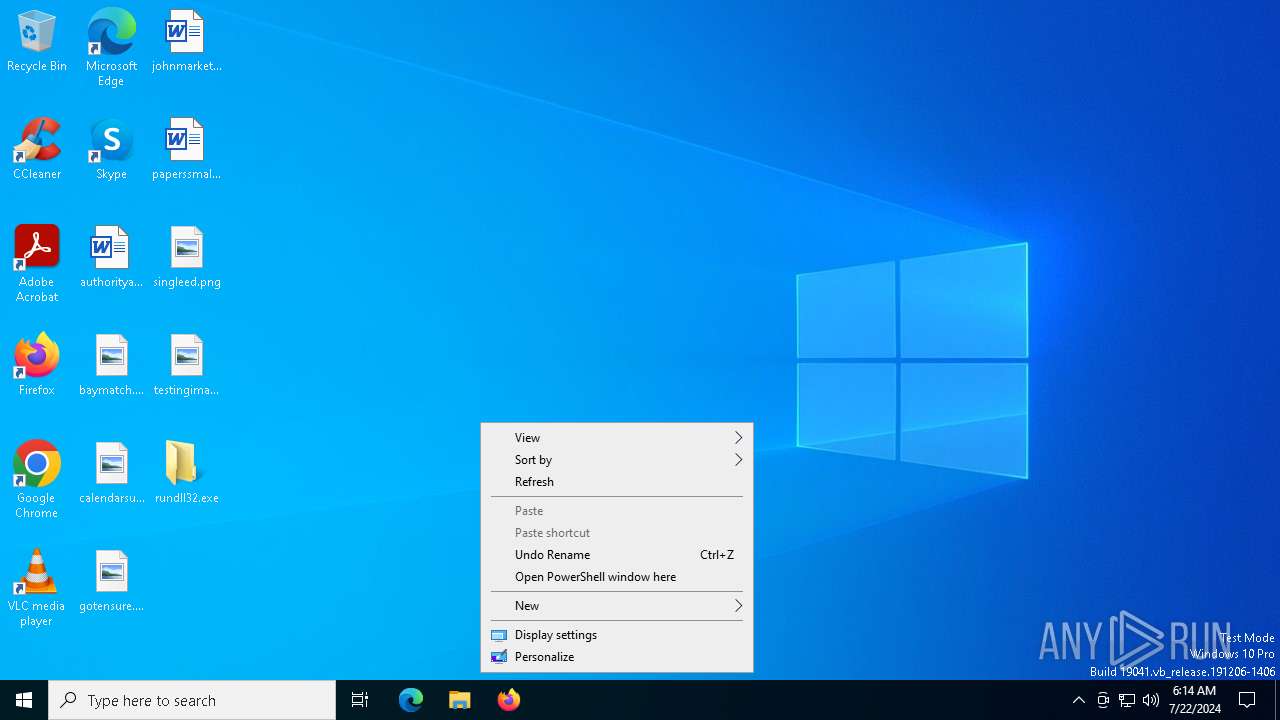
Checks current location (POWERSHELL)
- powershell.exe (PID: 6232)
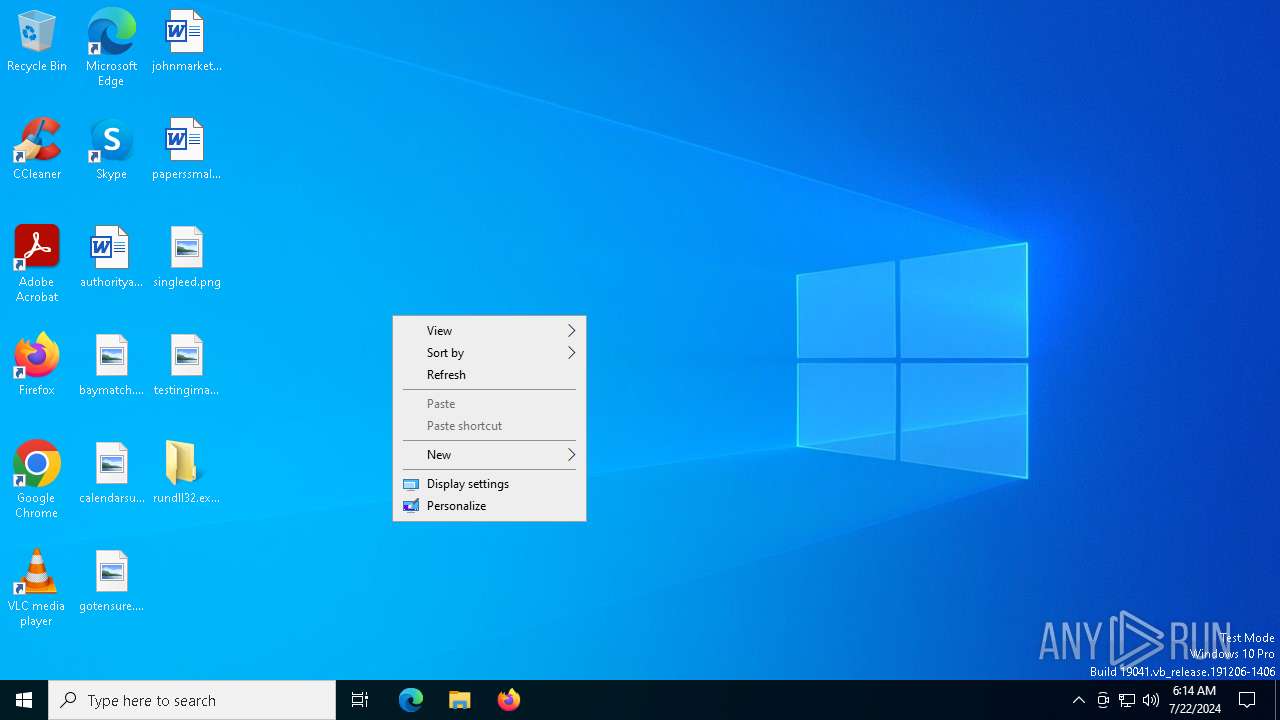
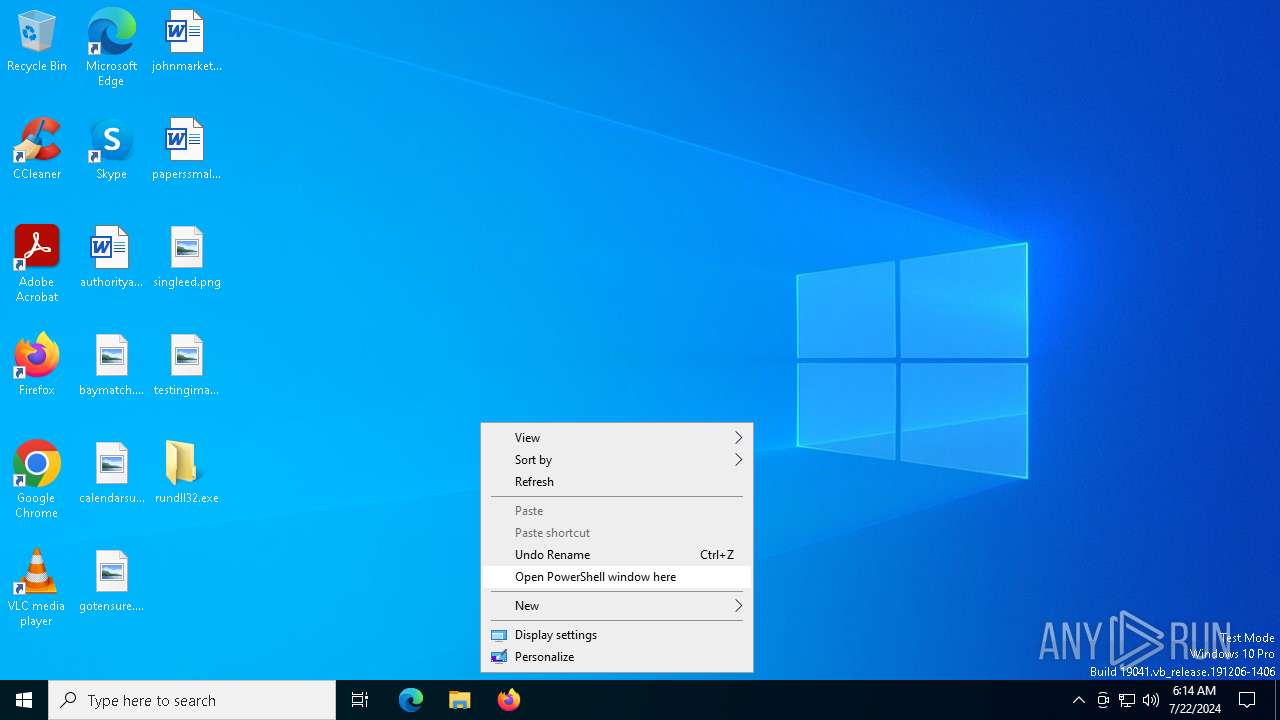
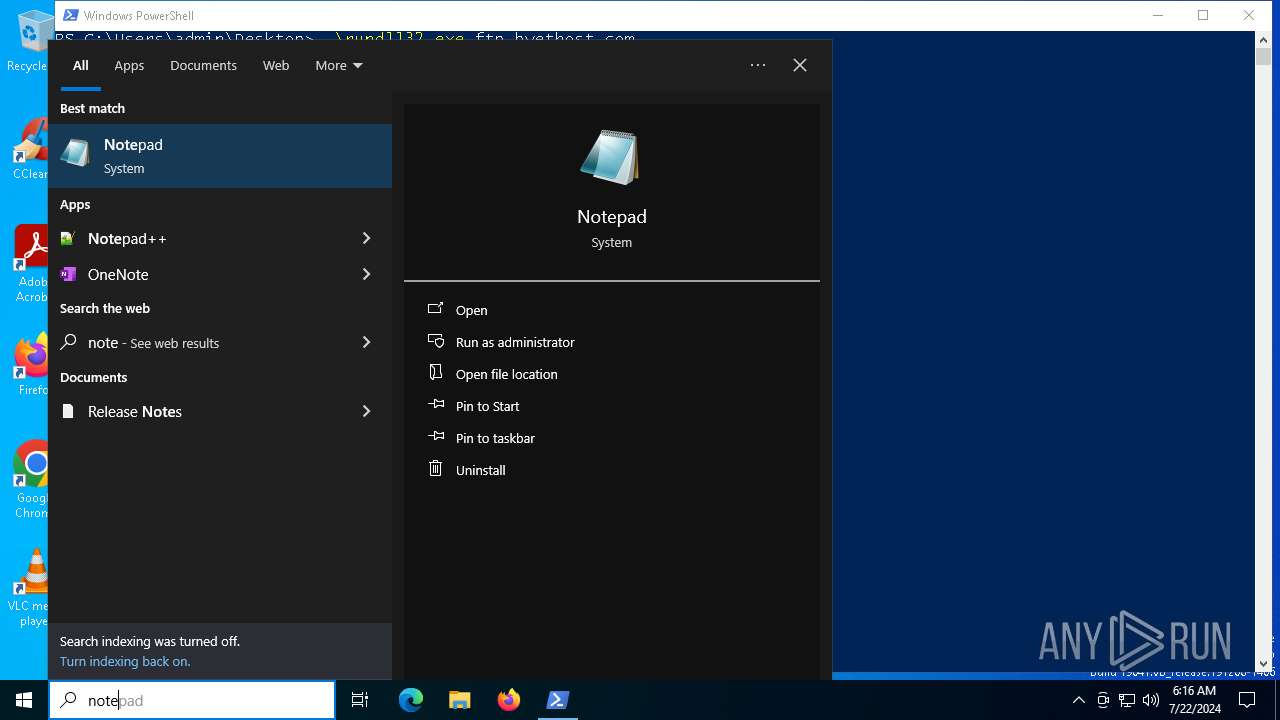
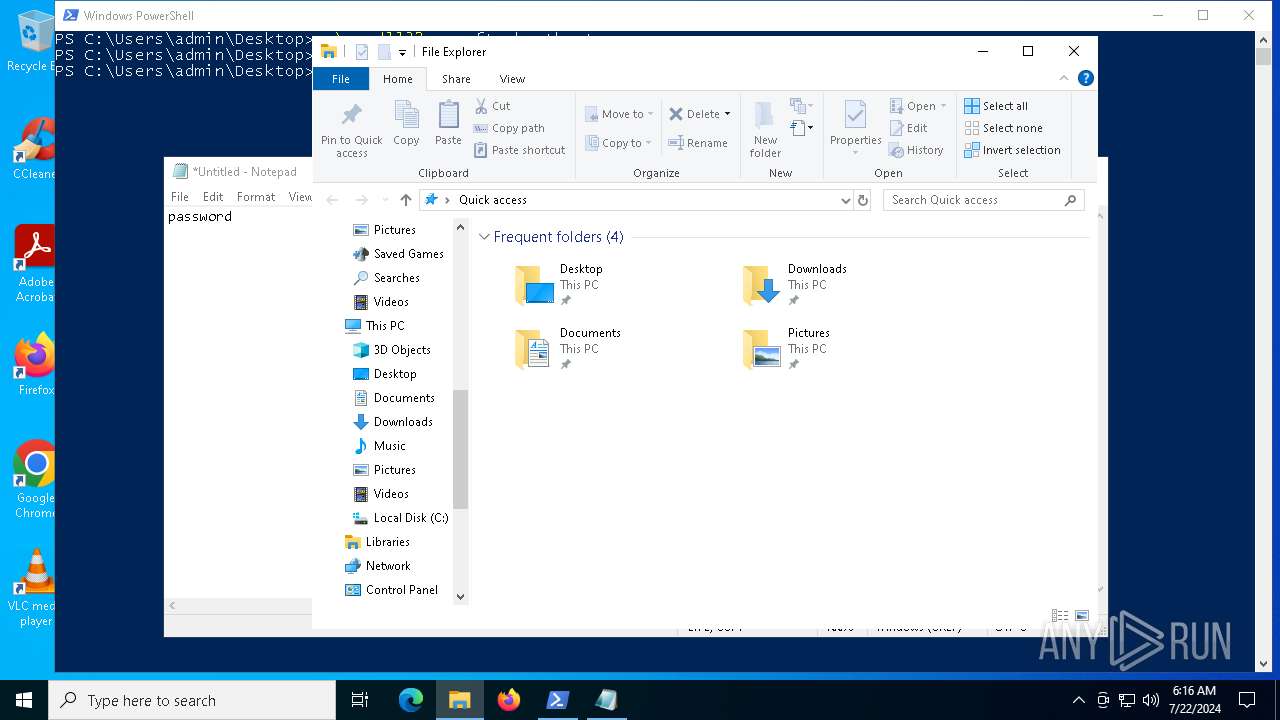
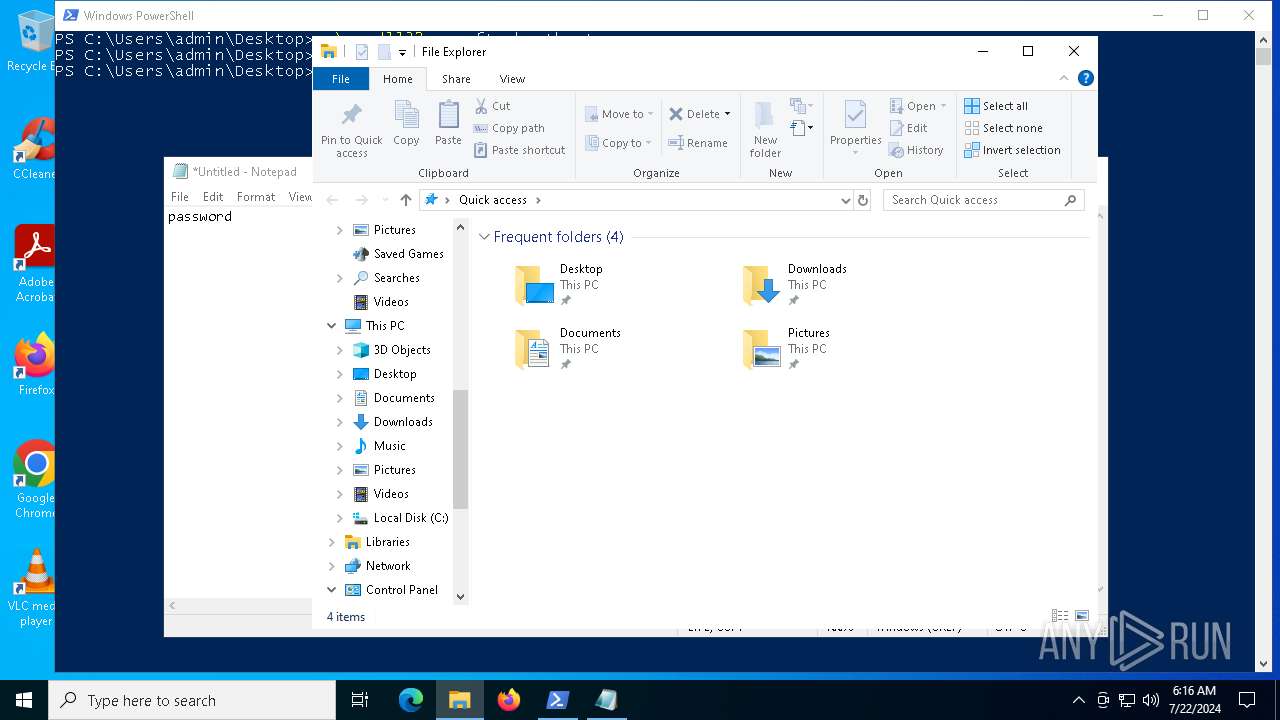
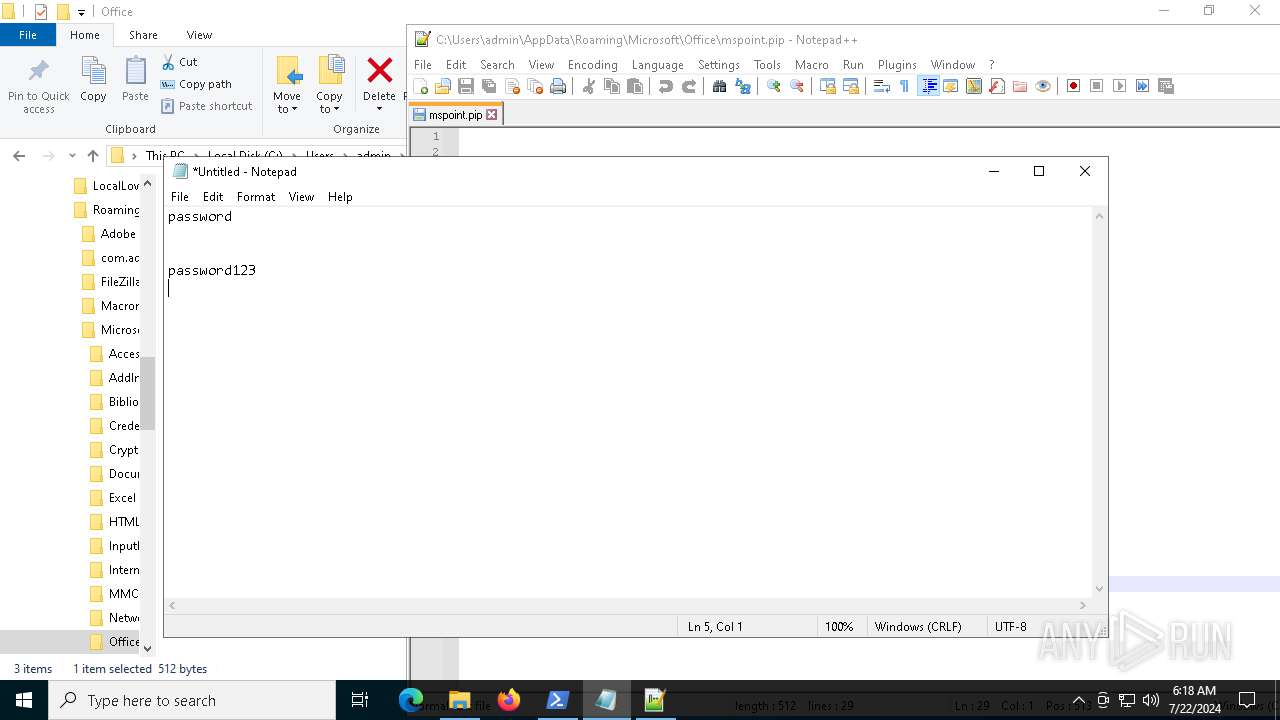
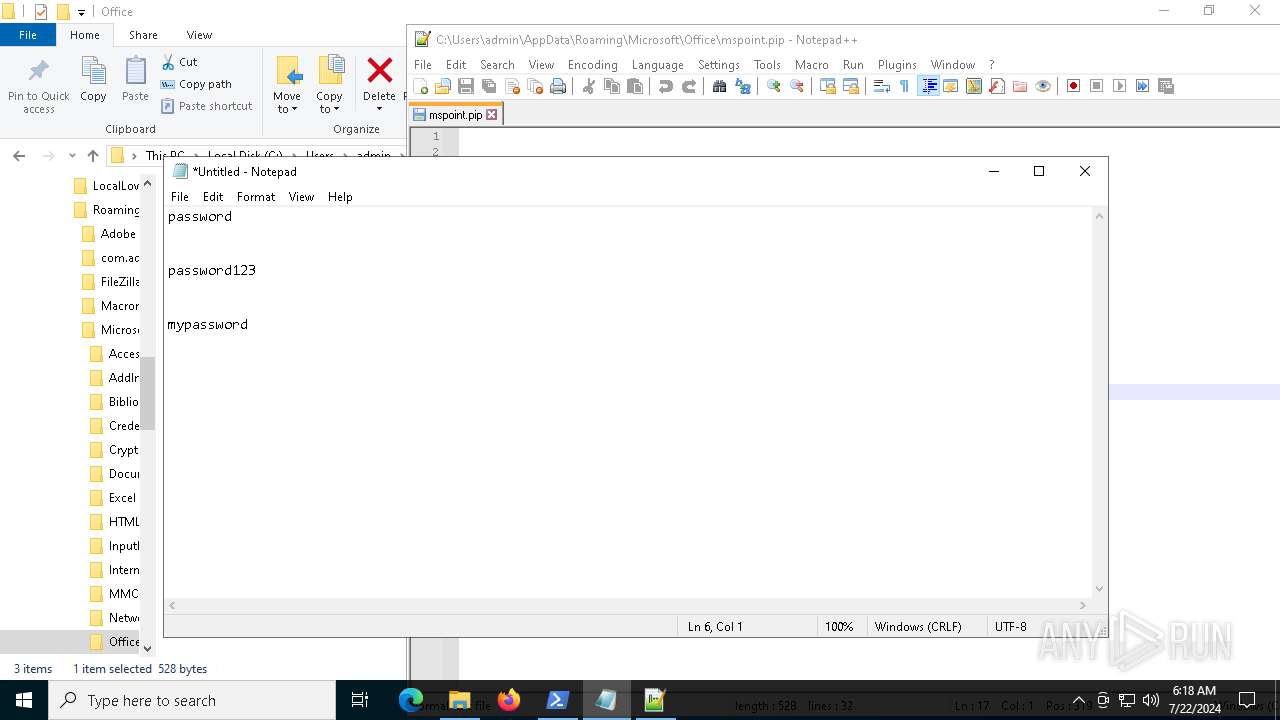
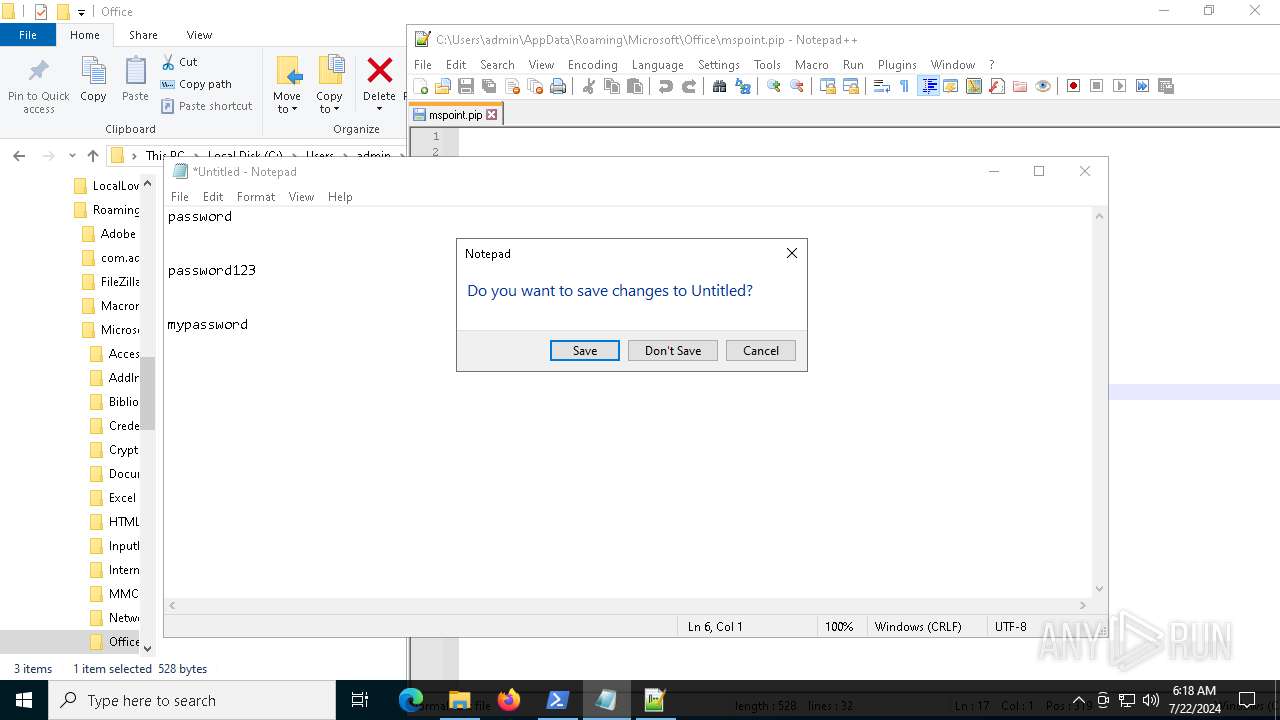
Manual execution by a user
- notepad++.exe (PID: 5016)
- powershell.exe (PID: 6232)
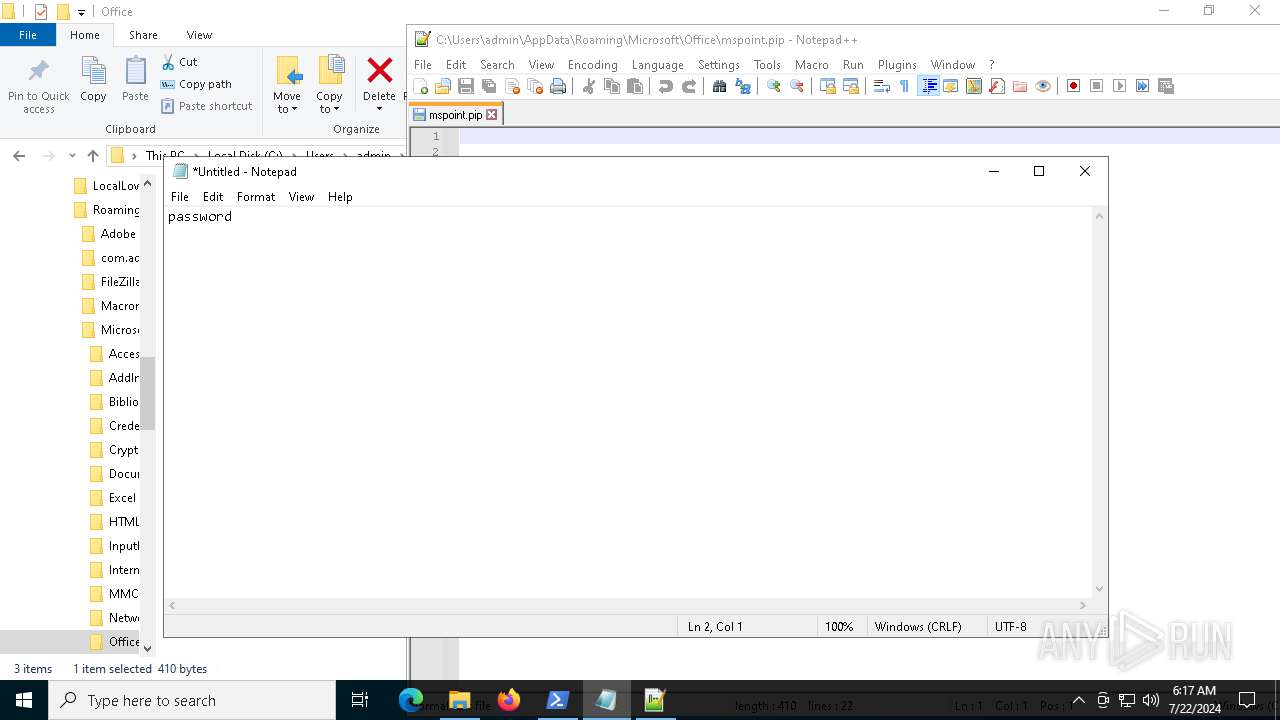
- notepad.exe (PID: 1484)
Checks proxy server information
- rundll32.exe (PID: 8048)
- rundll32.exe (PID: 7212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:01:18 14:44:33+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 569856 |
| InitializedDataSize: | 105472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7add4 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
151
Monitored processes
10
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
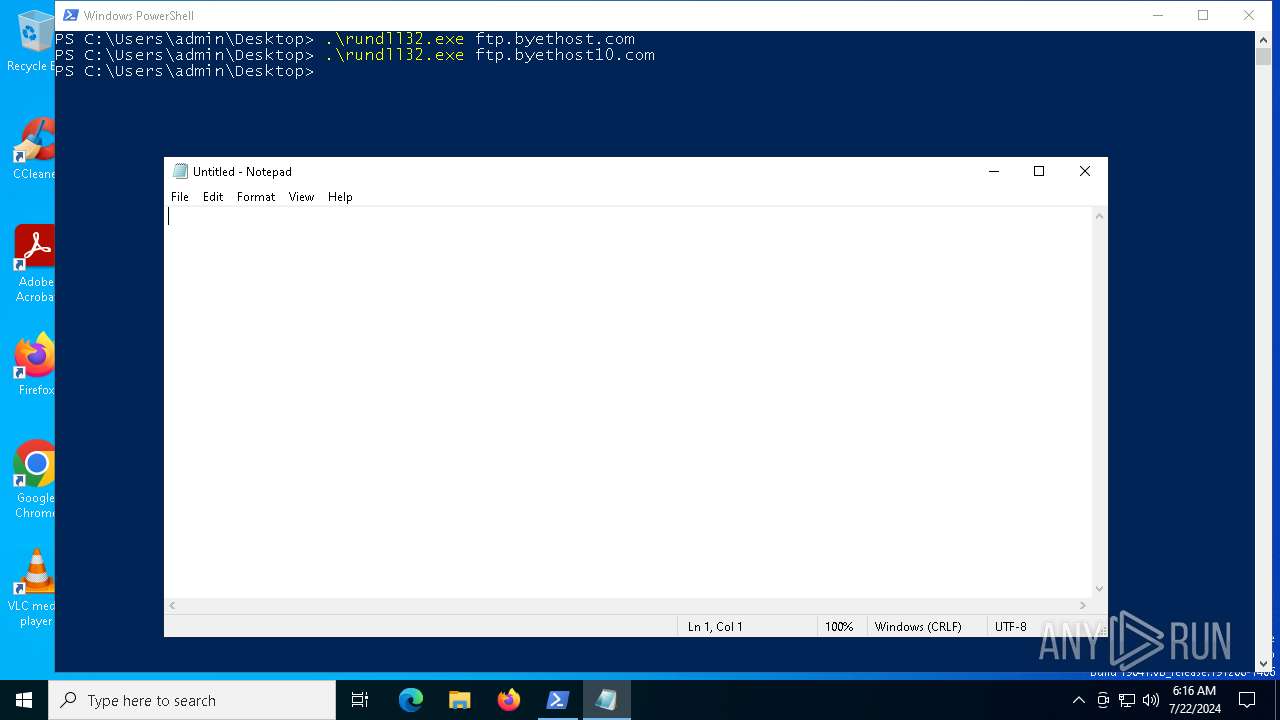
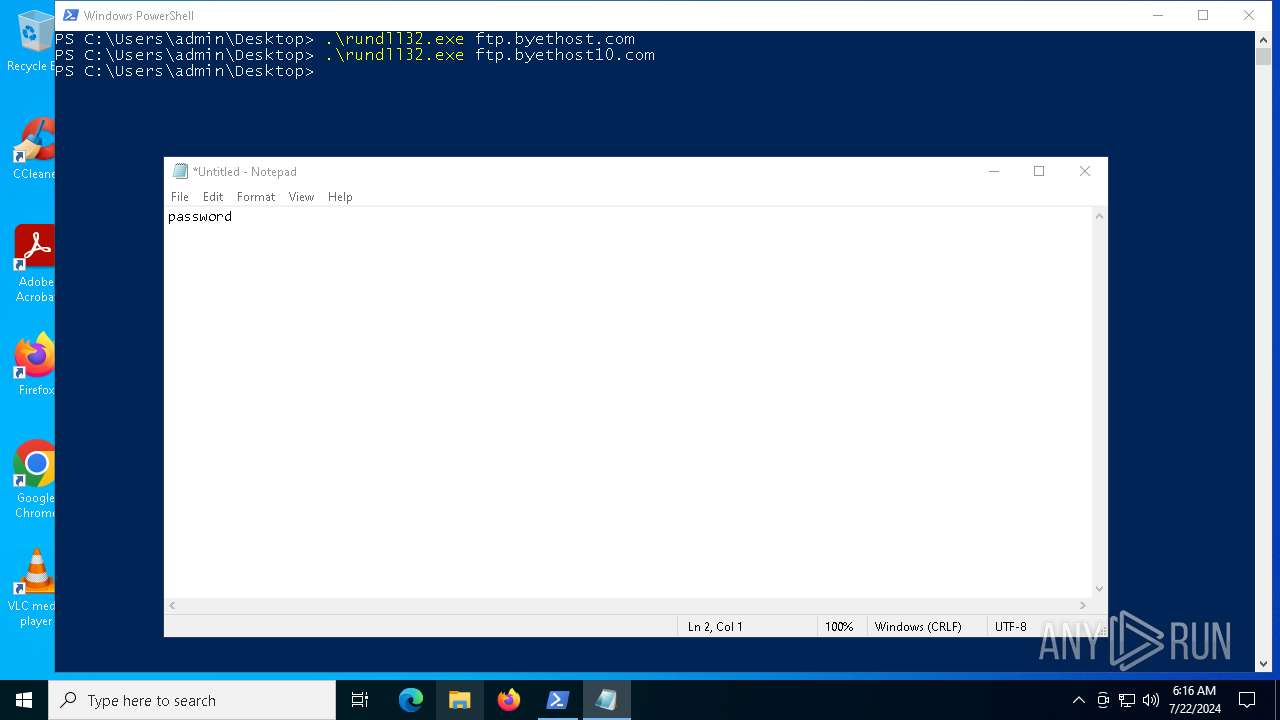
| 1484 | "C:\WINDOWS\system32\notepad.exe" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2116 | "C:\Users\admin\Desktop\rundll32.exe_.exe" | C:\Users\admin\Desktop\rundll32.exe_.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3024 | "C:\WINDOWS\system32\whoami.exe" | C:\Windows\System32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
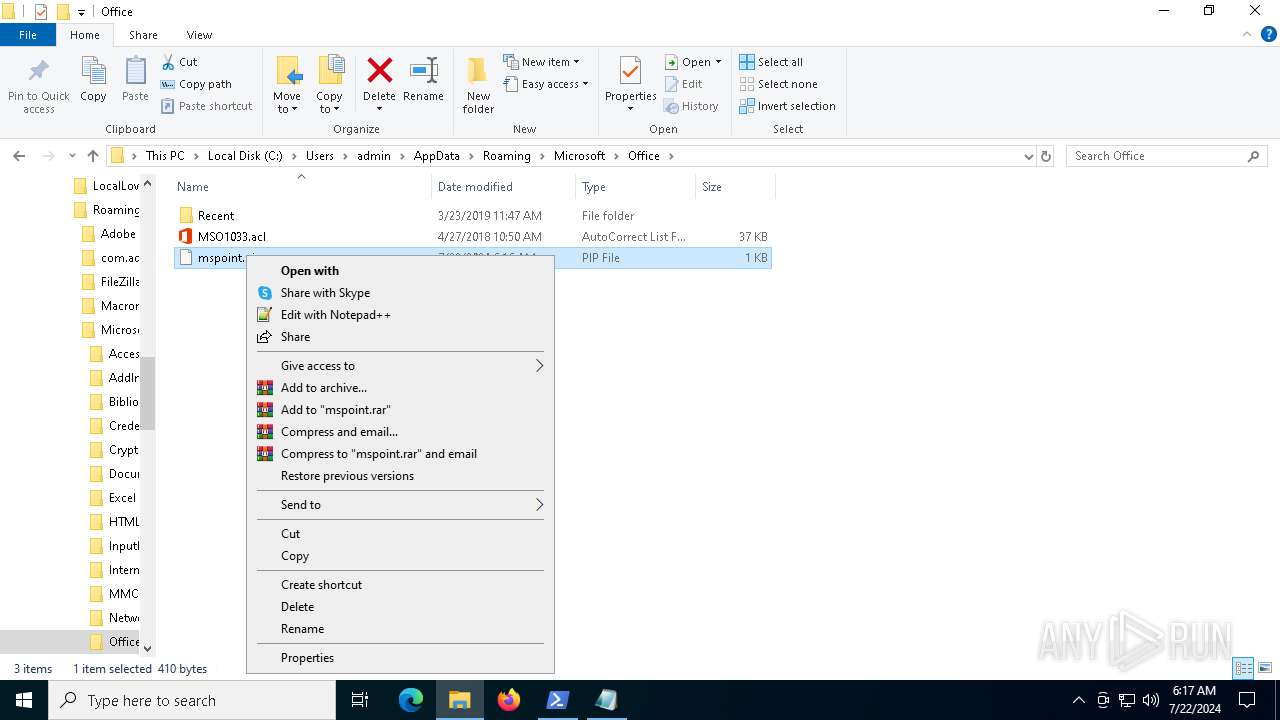
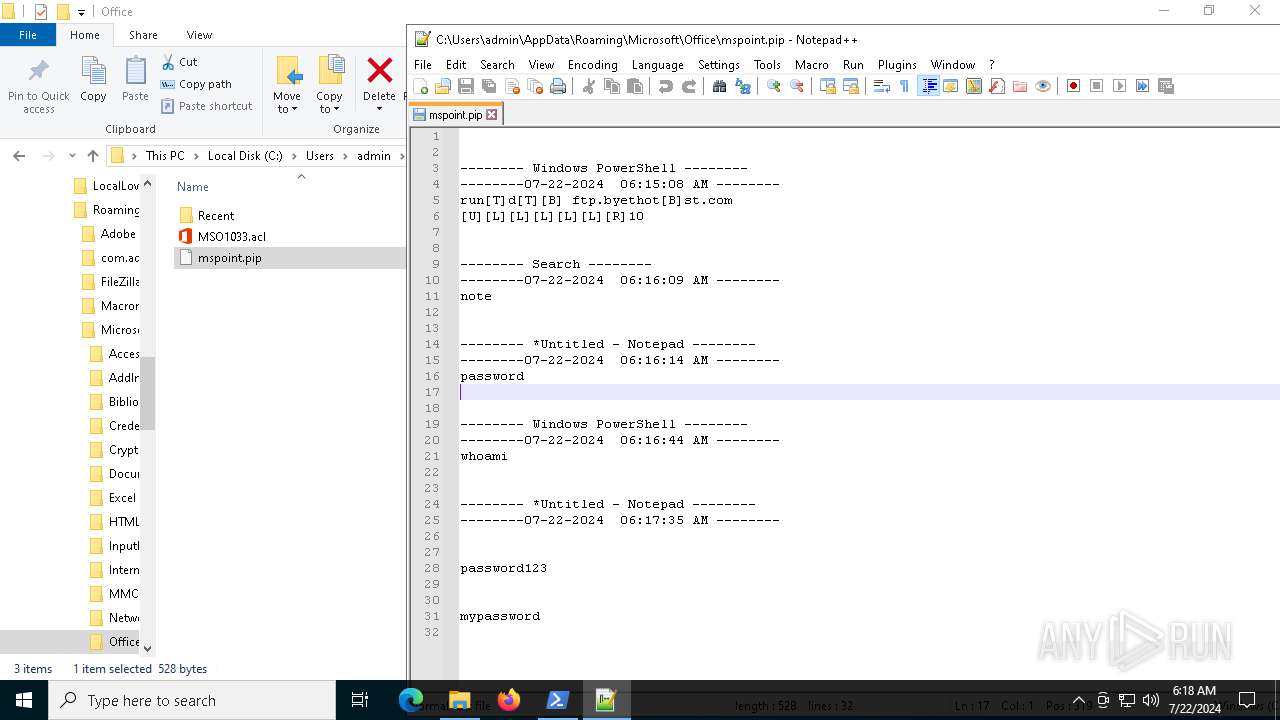
| 5016 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Office\mspoint.pip" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 6044 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
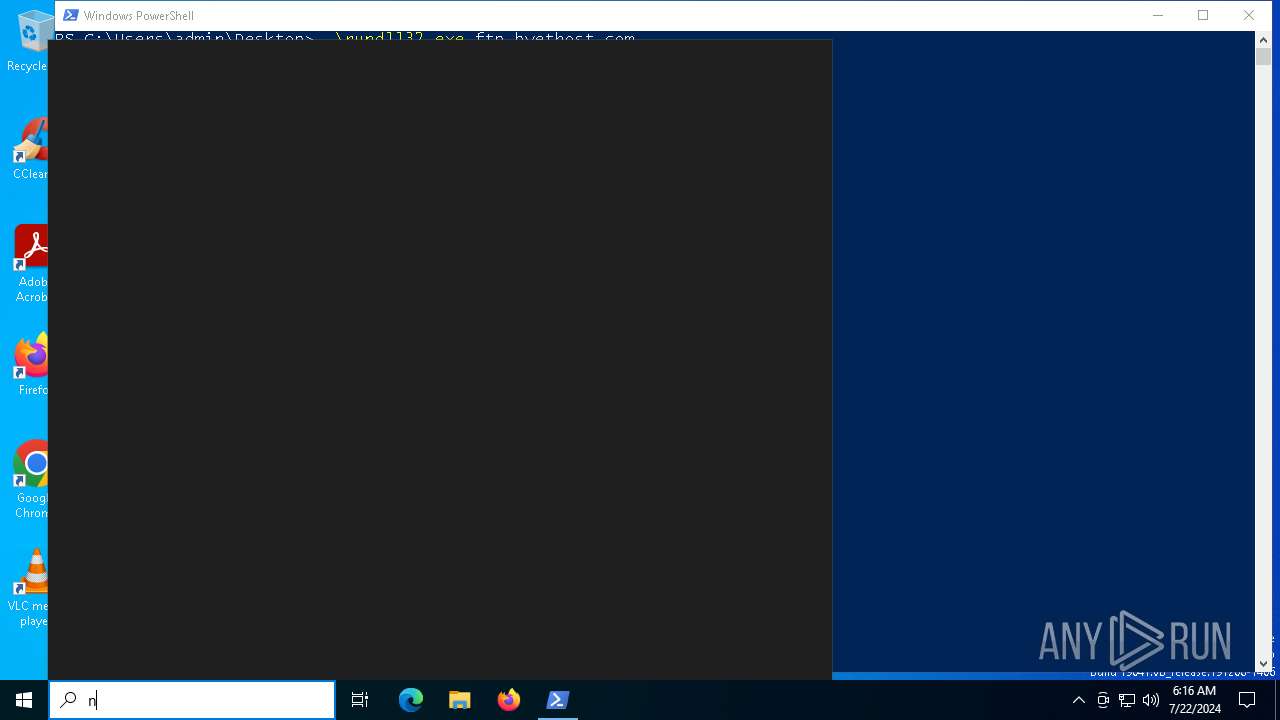
| 6232 | "PowerShell.exe" -noexit -command Set-Location -literalPath 'C:\Users\admin\Desktop' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6936 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | "C:\Users\admin\Desktop\rundll32.exe" ftp.byethost.com | C:\Users\admin\Desktop\rundll32.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 8048 | "C:\Users\admin\Desktop\rundll32.exe" ftp.byethost10.com | C:\Users\admin\Desktop\rundll32.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
11 578
Read events
11 567
Write events
11
Delete events
0
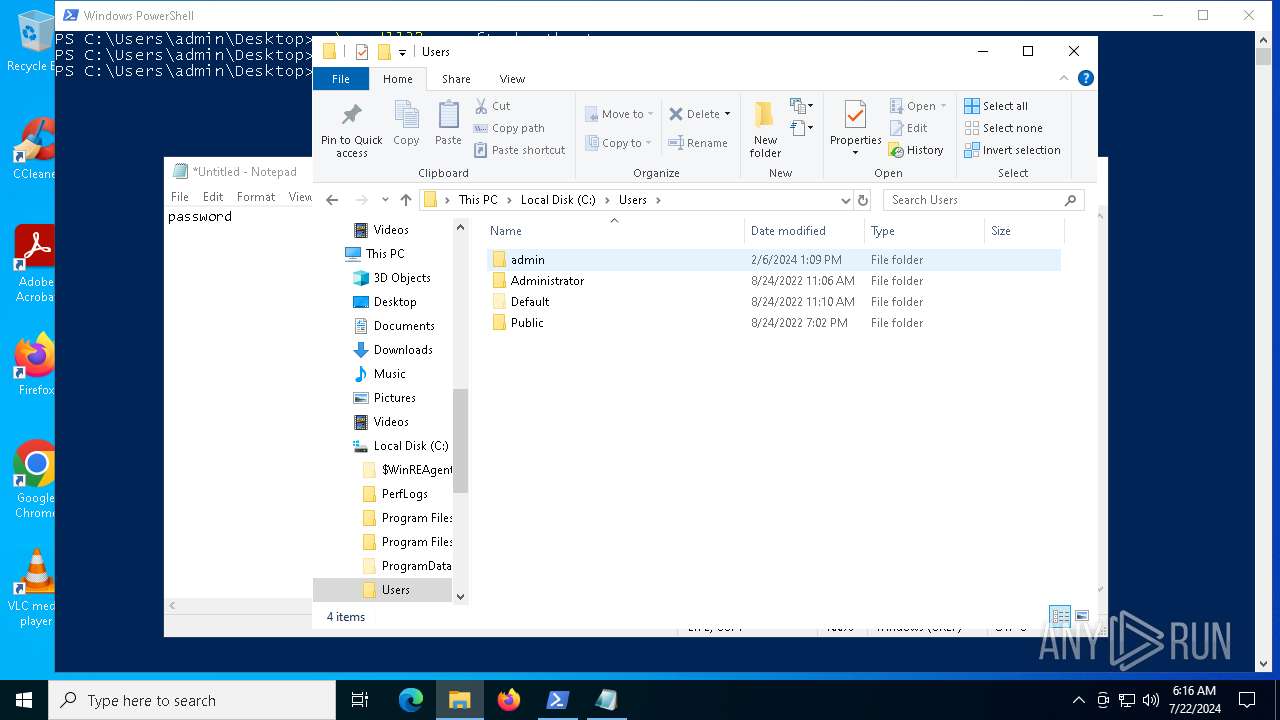
Modification events
| (PID) Process: | (2116) rundll32.exe_.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | ShowSuperHidden |
Value: 0 | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6232) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7212) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | ShowSuperHidden |
Value: 0 | |||
| (PID) Process: | (8048) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | ShowSuperHidden |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
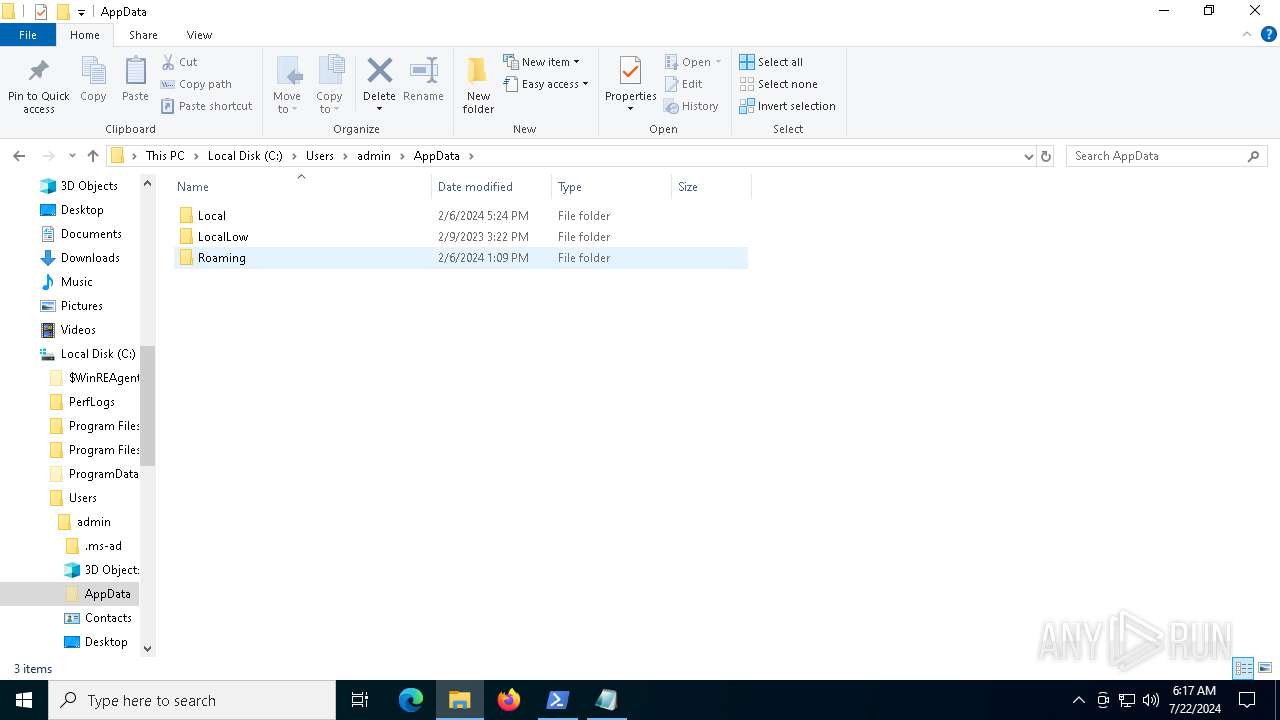
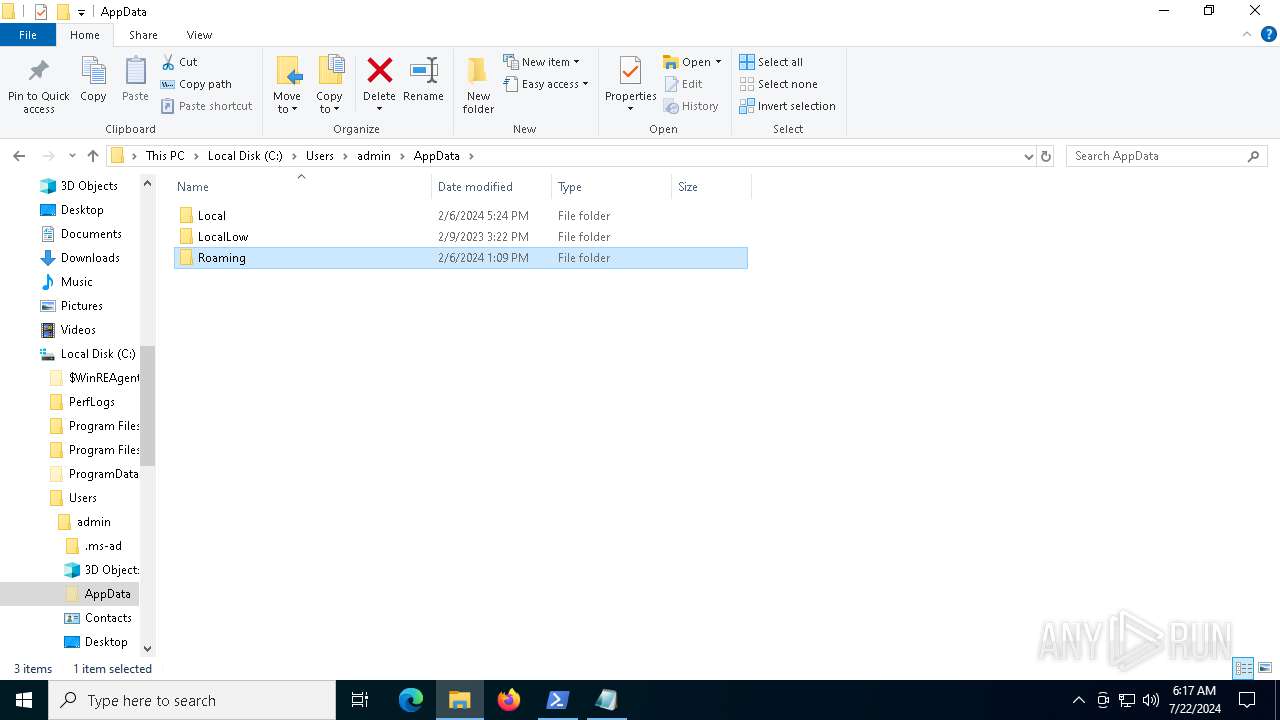
| 6232 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LFZP1O9JPP16EG4BPNY1.temp | binary | |
MD5:B6CB03AF1C776E0858457C4FF8C38229 | SHA256:F9A8CF8F5DD543BB50E86D7676AB4A2291C4FFBE8180F56950898294E6F93CAD | |||
| 6232 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF42fc41.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6232 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ht3toqsi.mn0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
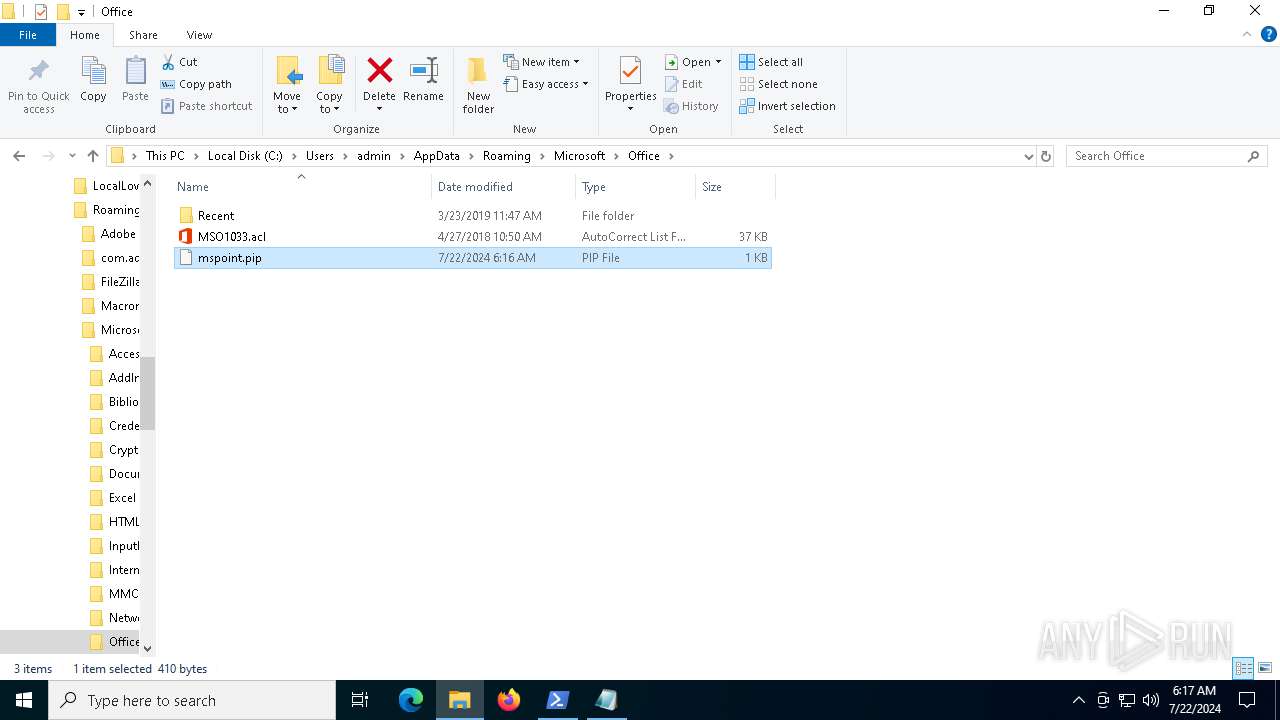
| 2116 | rundll32.exe_.exe | C:\Users\admin\AppData\Roaming\Microsoft\Office\mspoint.pip | text | |
MD5:4C96C144F259C0DAF0EC78AD947C40F3 | SHA256:77F8CE76AAFAF692FFEFF3BBC25FF4209F7348079BE41E608E02D485E968096D | |||
| 5016 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 6232 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gwmff52g.yyo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5016 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 6232 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadLine\ConsoleHost_history.txt | text | |
MD5:55C43A39DB0A15661A82240A9A76DE2B | SHA256:F8FD7252DD4B5EEAD4DAB53EF4554DCF1933491E698596E0205A6C8DC49B7E69 | |||
| 5016 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
| 5016 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
41
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5628 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7856 | svchost.exe | 20.247.184.142:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4716 | svchost.exe | 20.190.160.22:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5620 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2760 | svchost.exe | 40.113.103.199:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5820 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4716 | svchost.exe | 40.126.32.72:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5620 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
ftp.byethost10.com |
| unknown |
arm-ring.msedge.net |
| unknown |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7212 | rundll32.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |