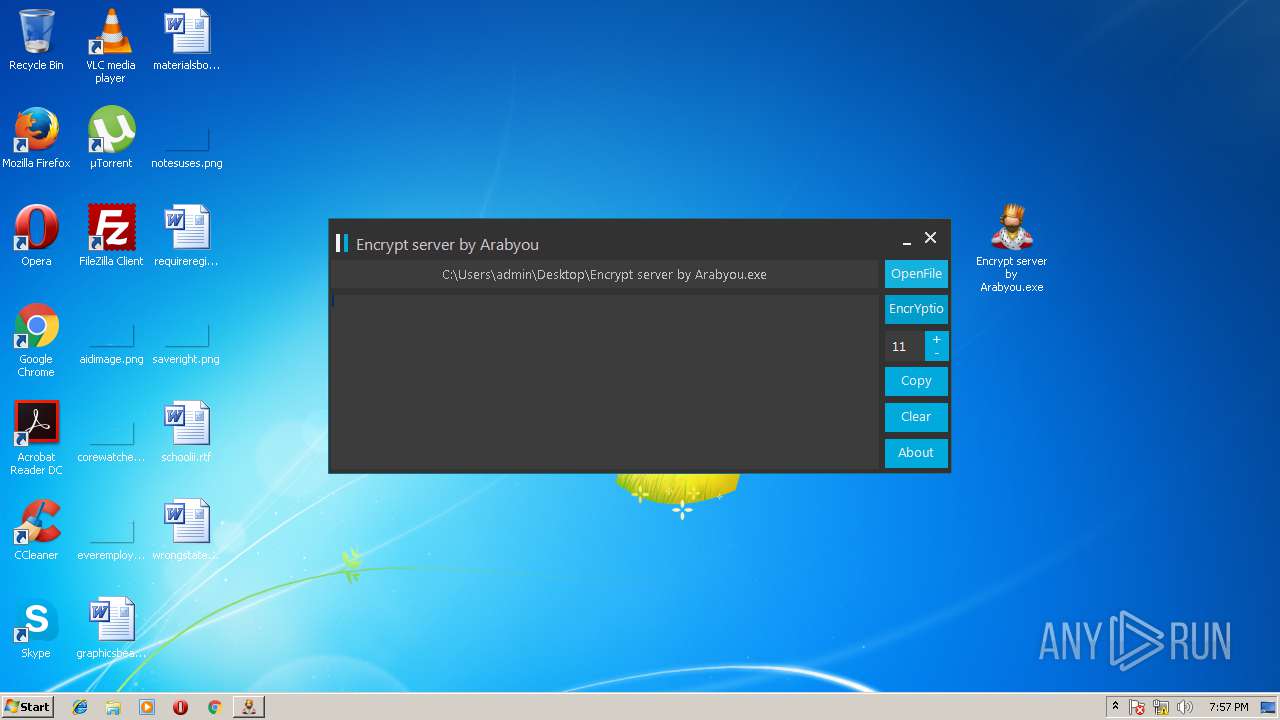
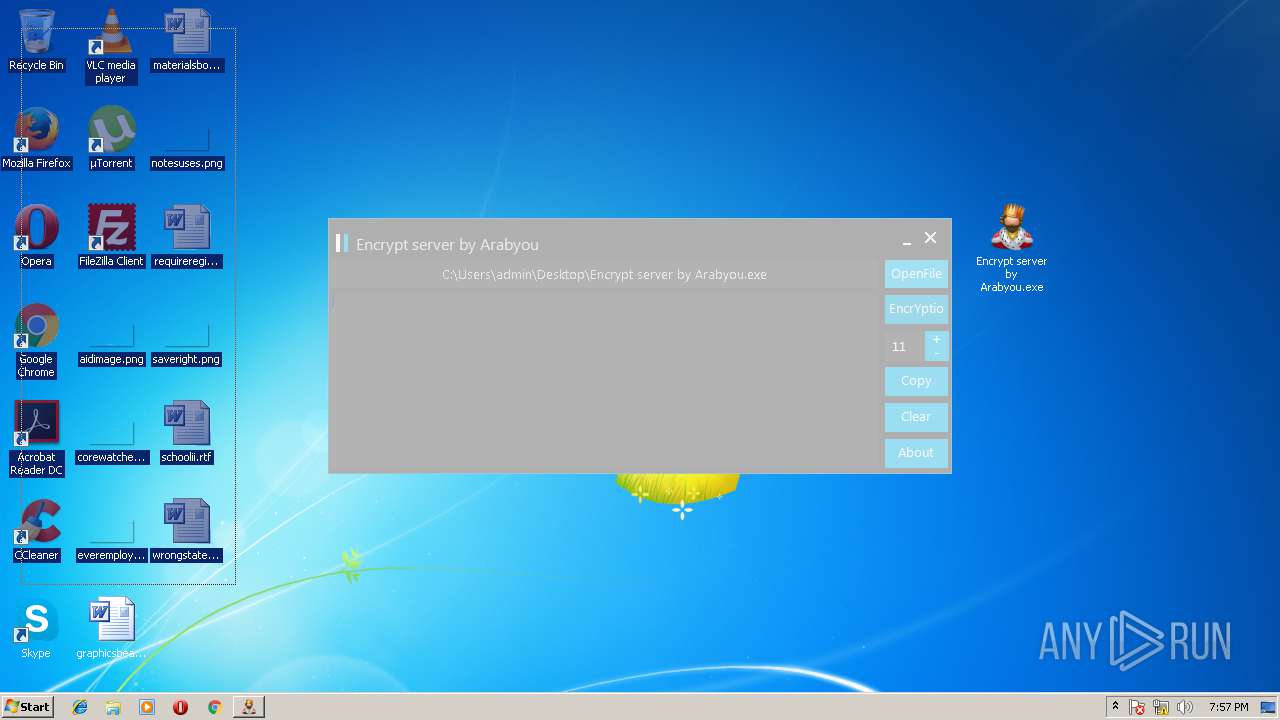
| File name: | Encrypt server by Arabyou.rar |
| Full analysis: | https://app.any.run/tasks/4e5fd0df-f152-4443-9015-46d875b8ca69 |
| Verdict: | Malicious activity |
| Analysis date: | May 05, 2018, 18:56:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | AE4605023B87B8A697C63E626DB59F52 |
| SHA1: | A591DEDAE64568ACD40C7BF8F60BB80114AC9DA3 |
| SHA256: | E1A7498079FD36797BA7B206A29AB3C44036C80CEAE5D7836FBFB068BA54B821 |
| SSDEEP: | 3072:wGSZw+GVVDvLpnK+/+a8R/OfSeX7/yjn1urQsF9sTWahC:wGiGVR0M0cfSeL/yTZcw14 |
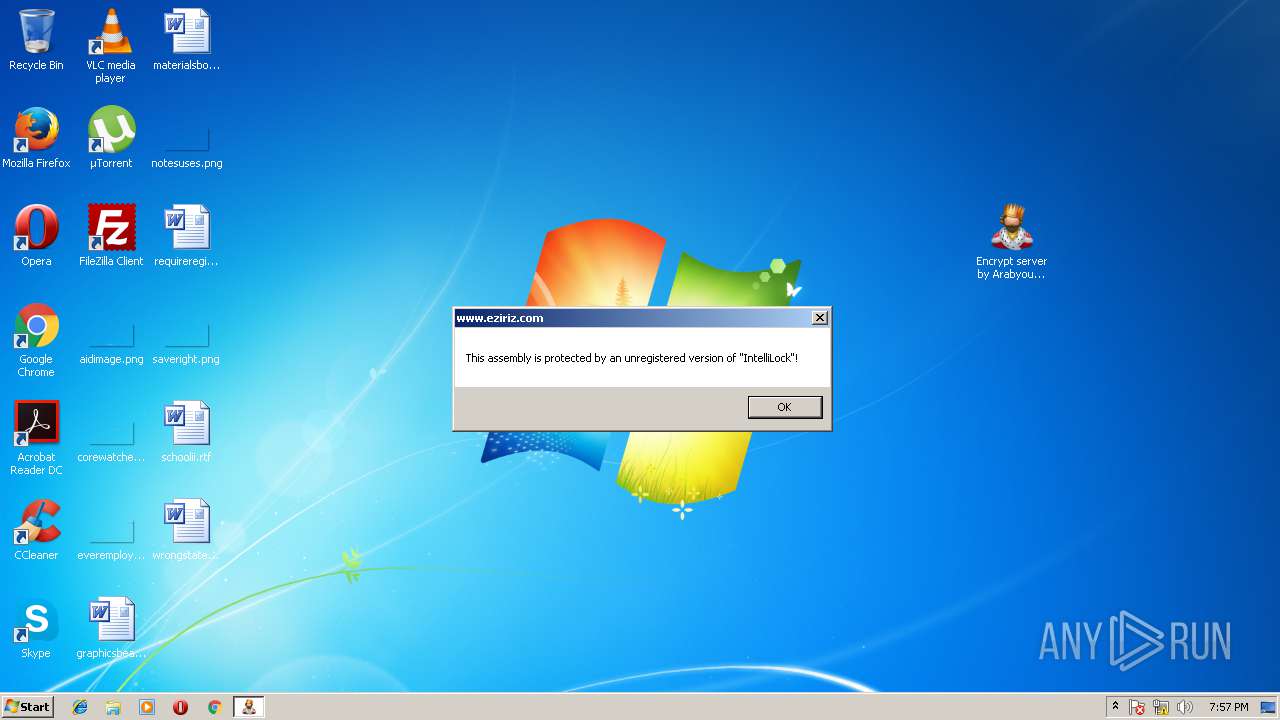
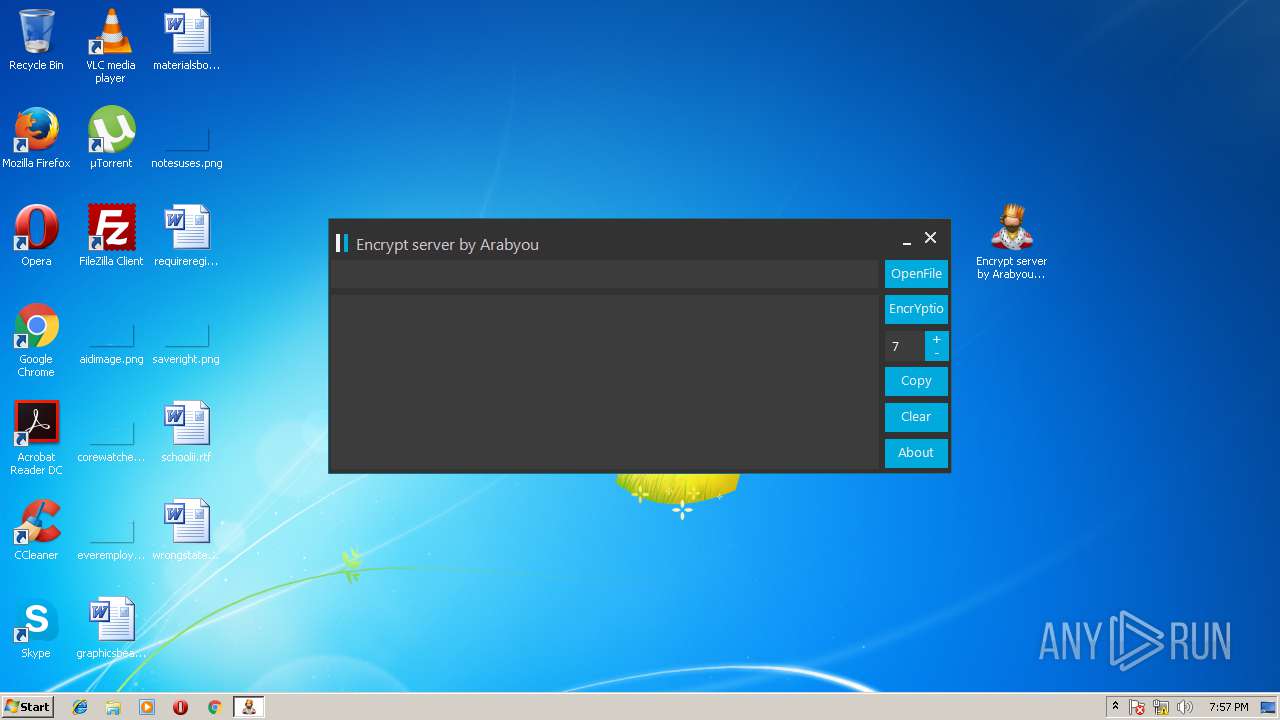
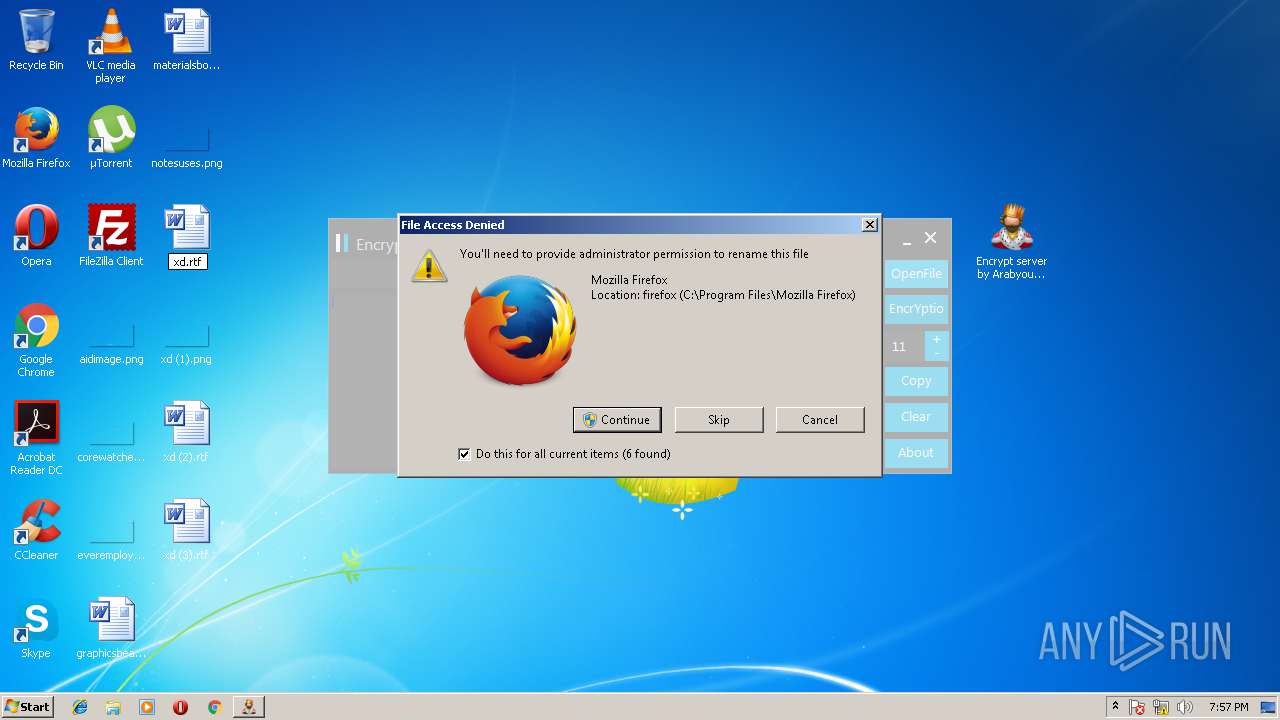
MALICIOUS
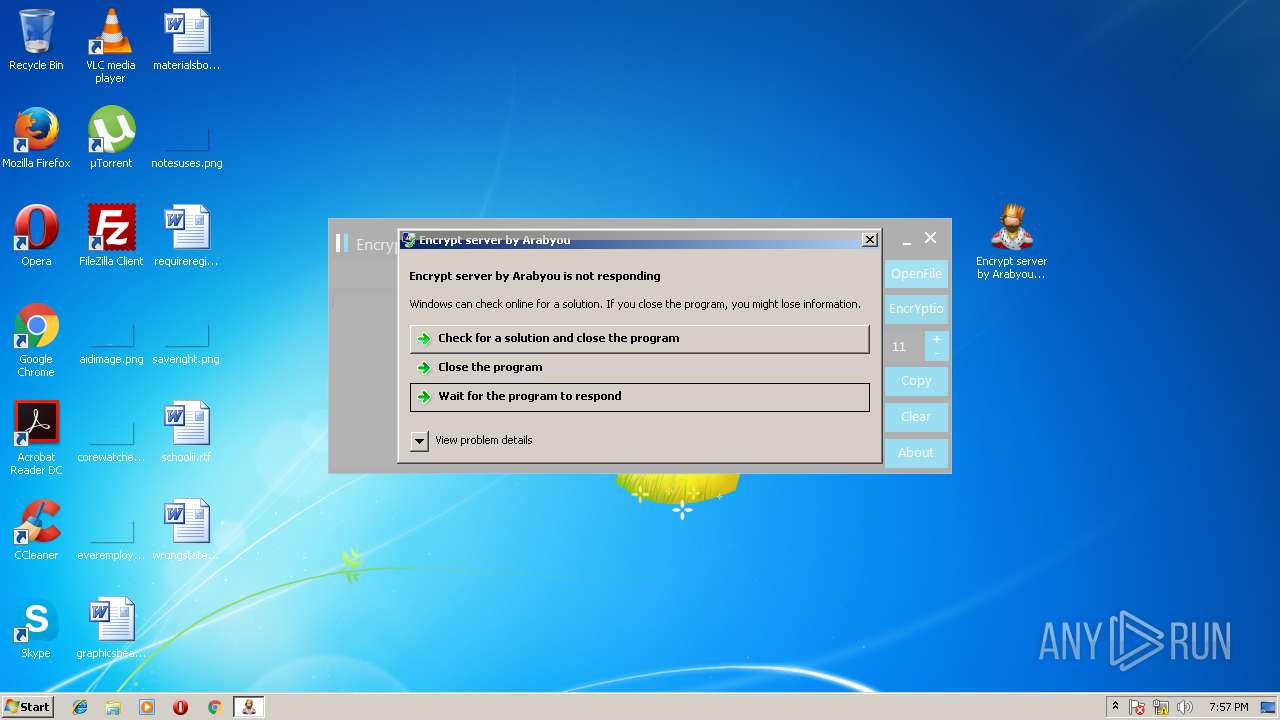
Application was dropped or rewritten from another process
- Encrypt server by Arabyou.exe (PID: 2892)
SUSPICIOUS
No suspicious indicators.INFO
Loads rich edit control libraries
- Encrypt server by Arabyou.exe (PID: 2892)
Loads the .NET runtime environment
- Encrypt server by Arabyou.exe (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
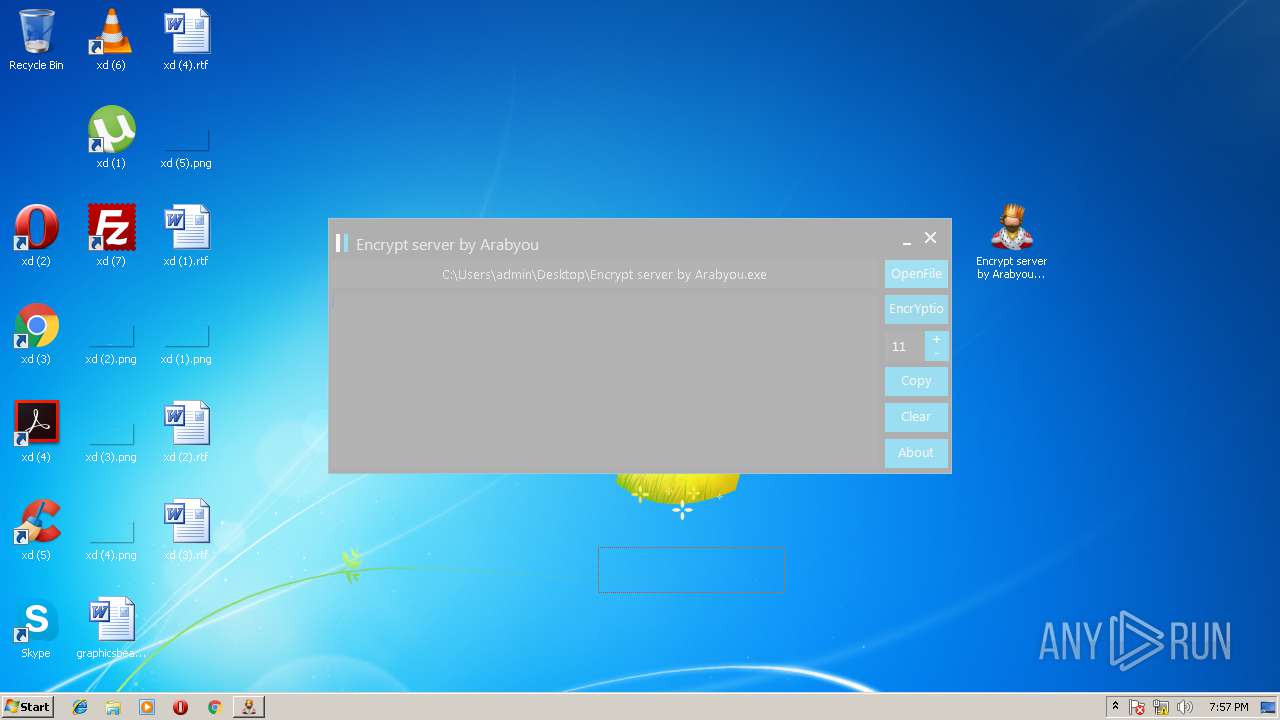
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
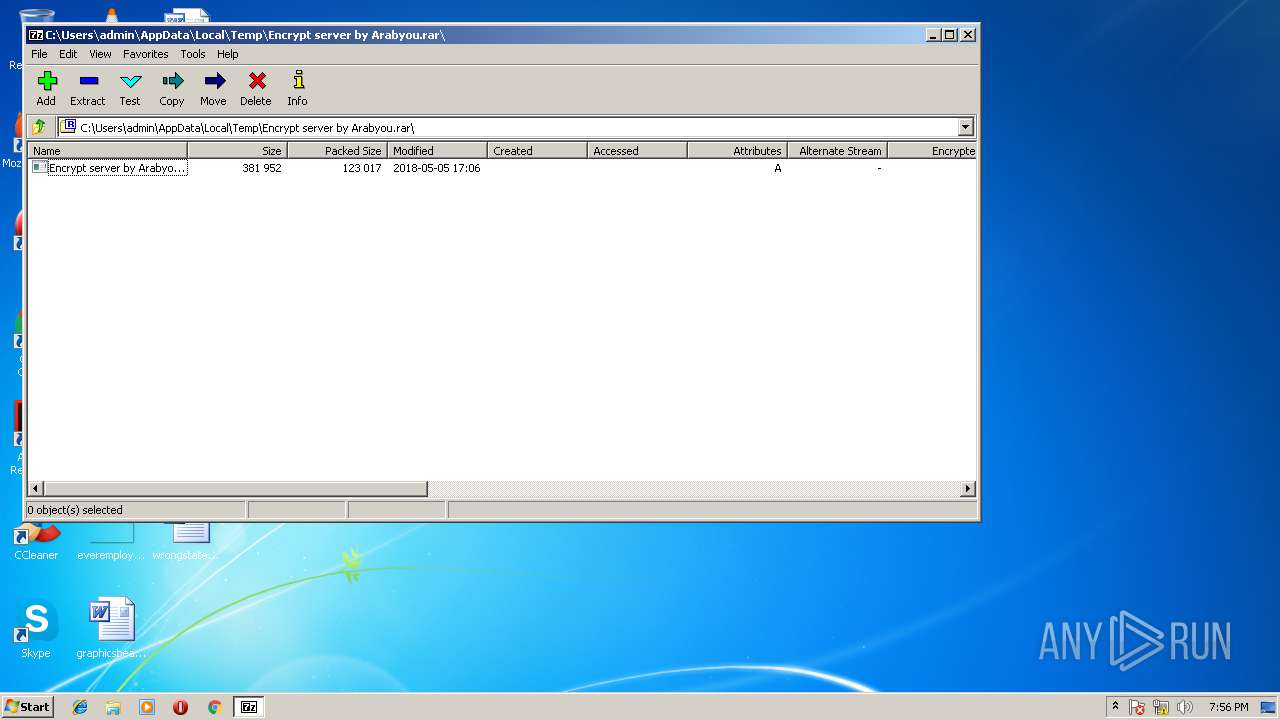
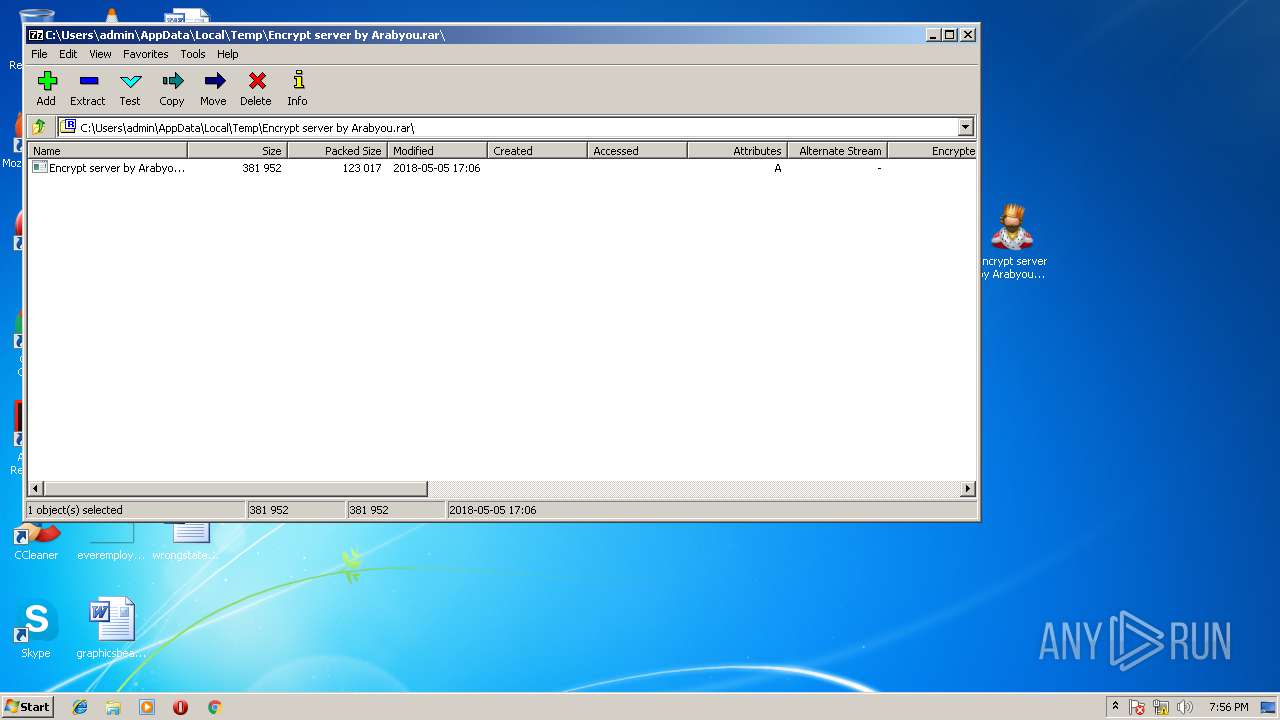
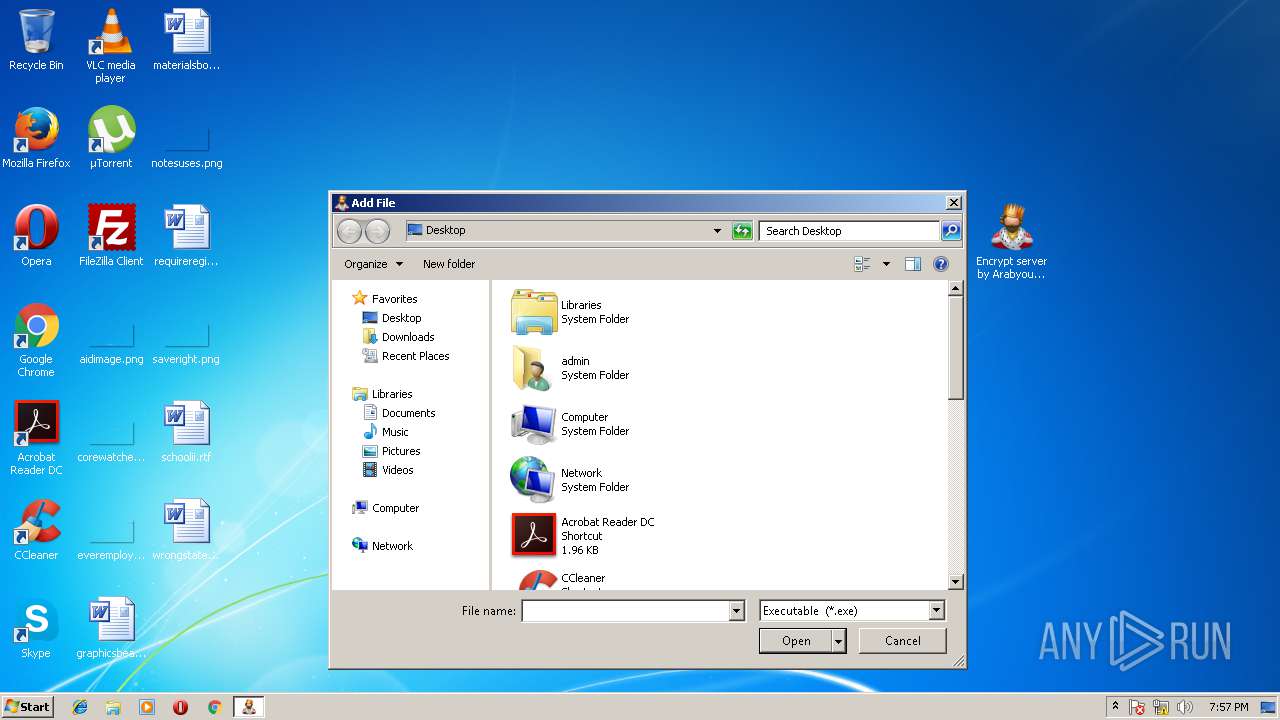
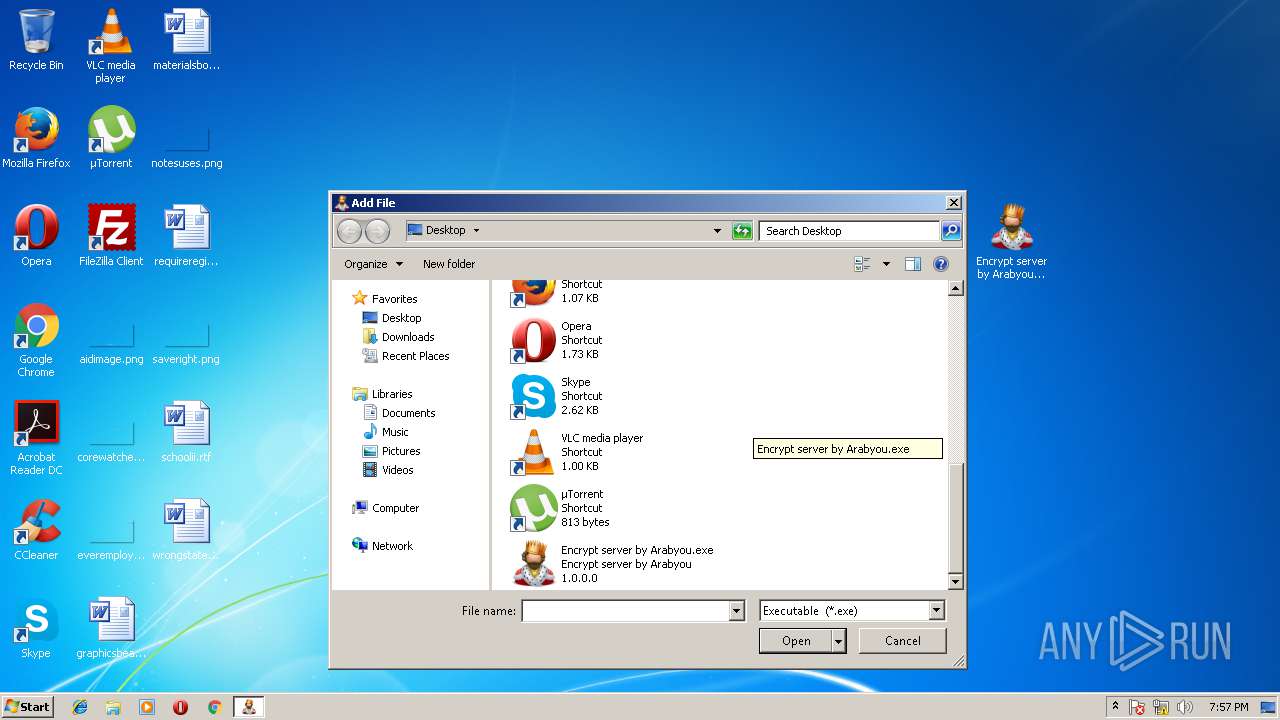
| 2668 | "C:\Program Files\7-Zip\7zFM.exe" "C:\Users\admin\AppData\Local\Temp\Encrypt server by Arabyou.rar" | C:\Program Files\7-Zip\7zFM.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
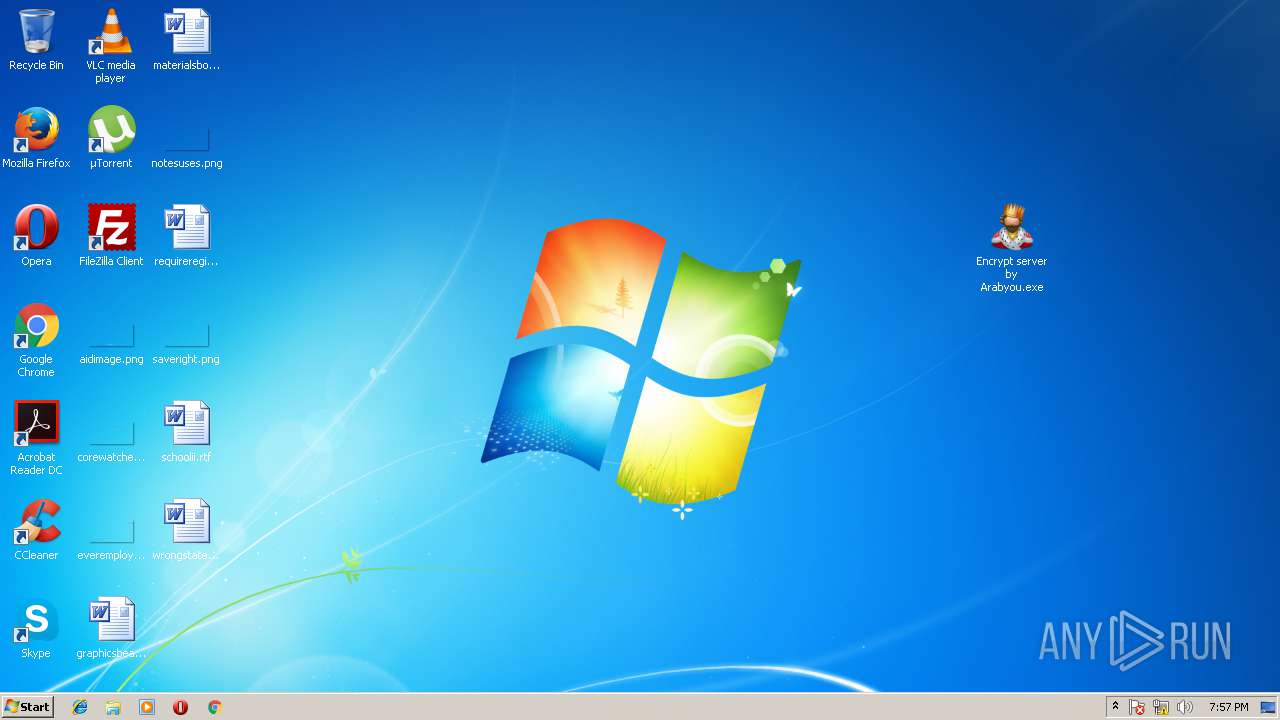
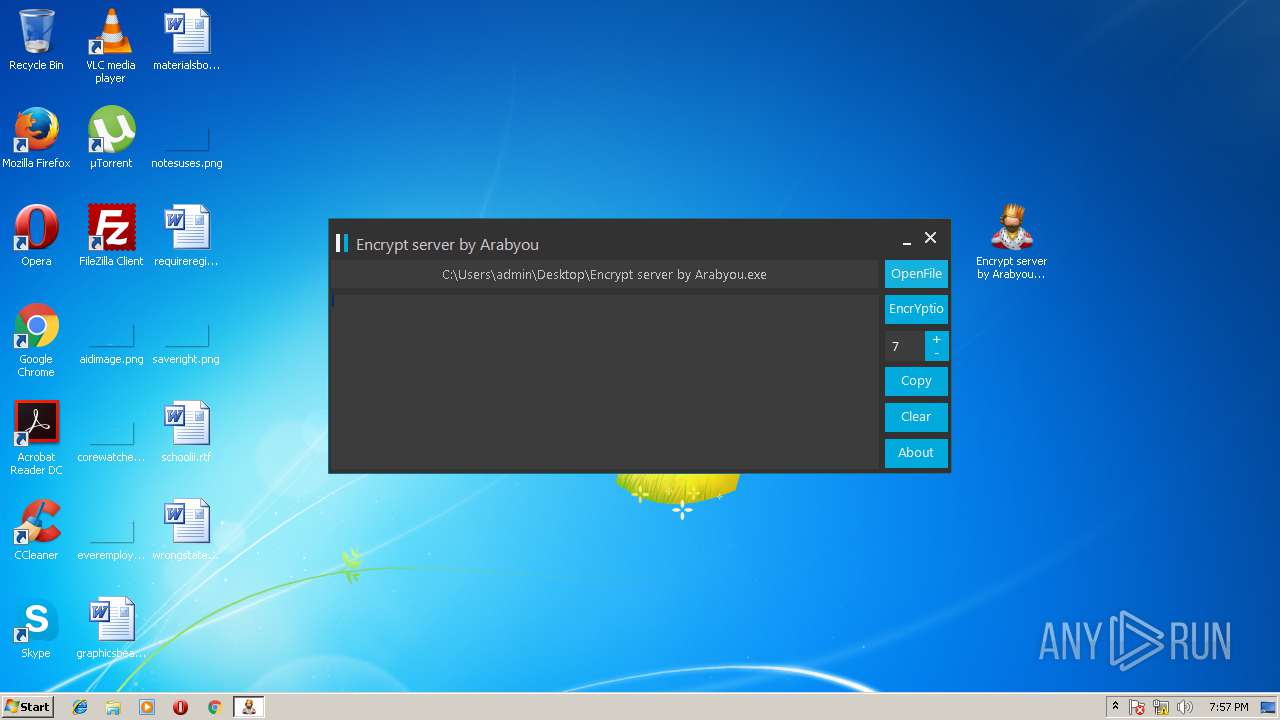
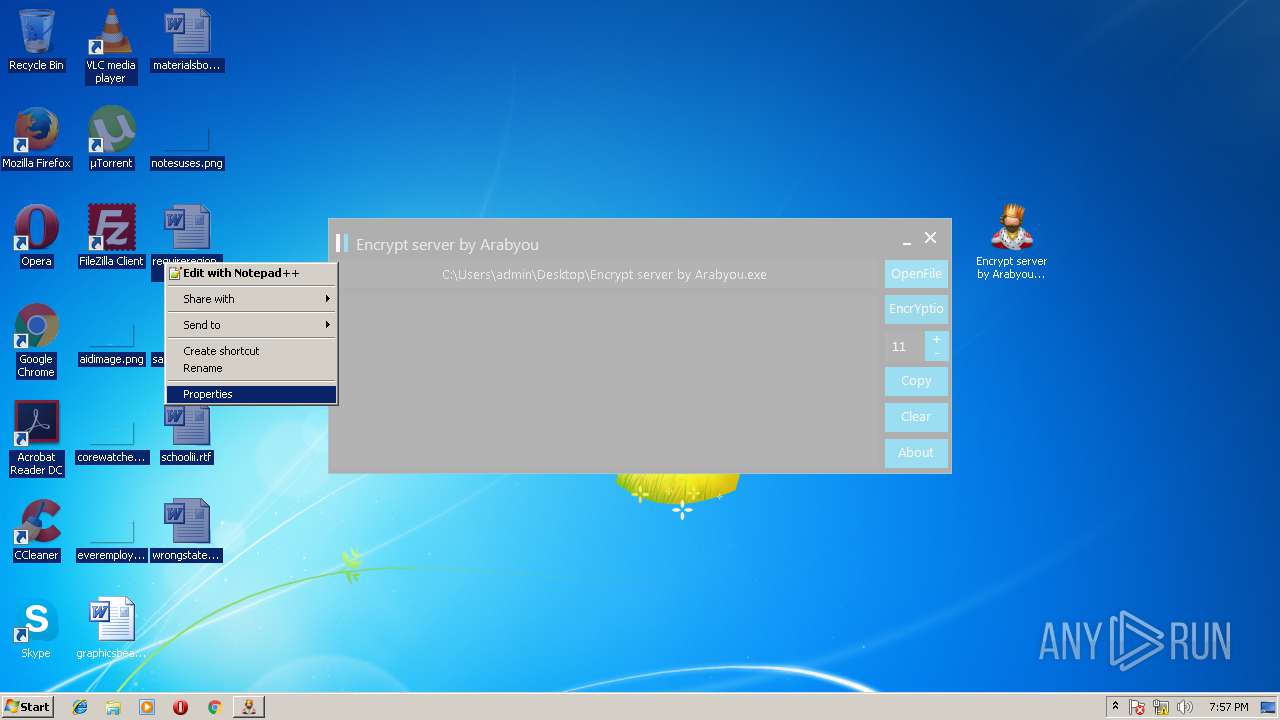
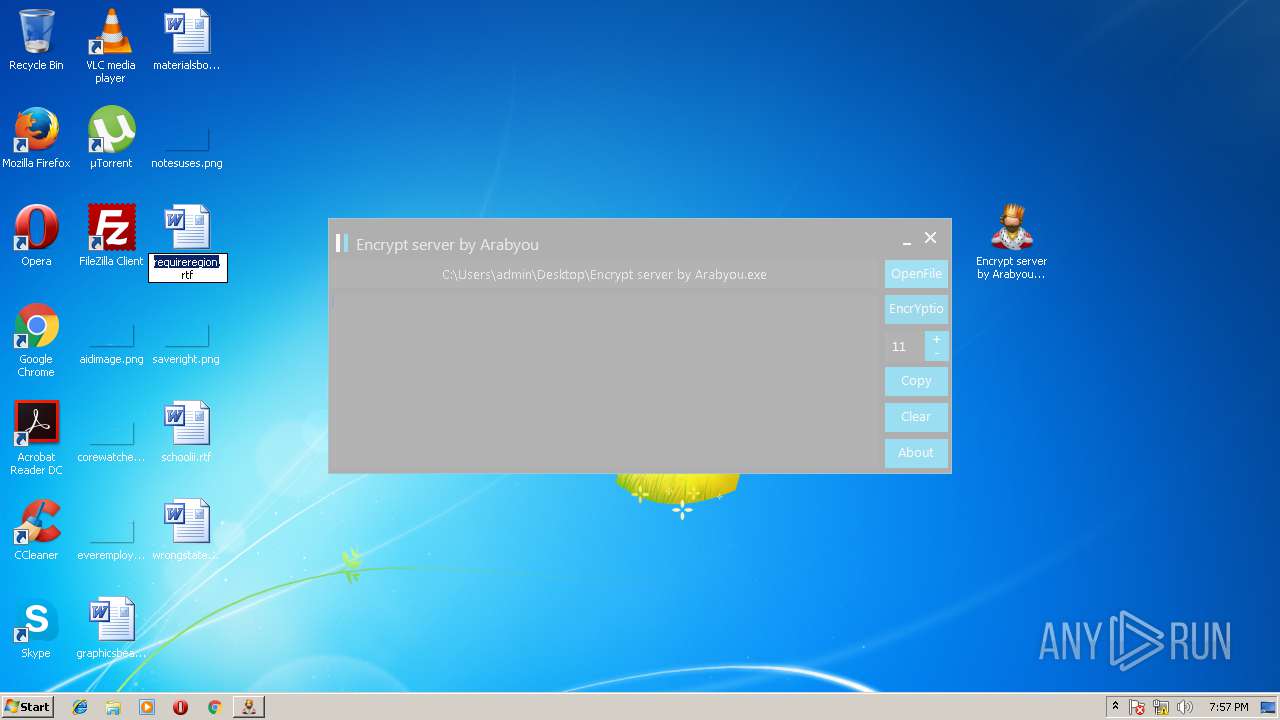
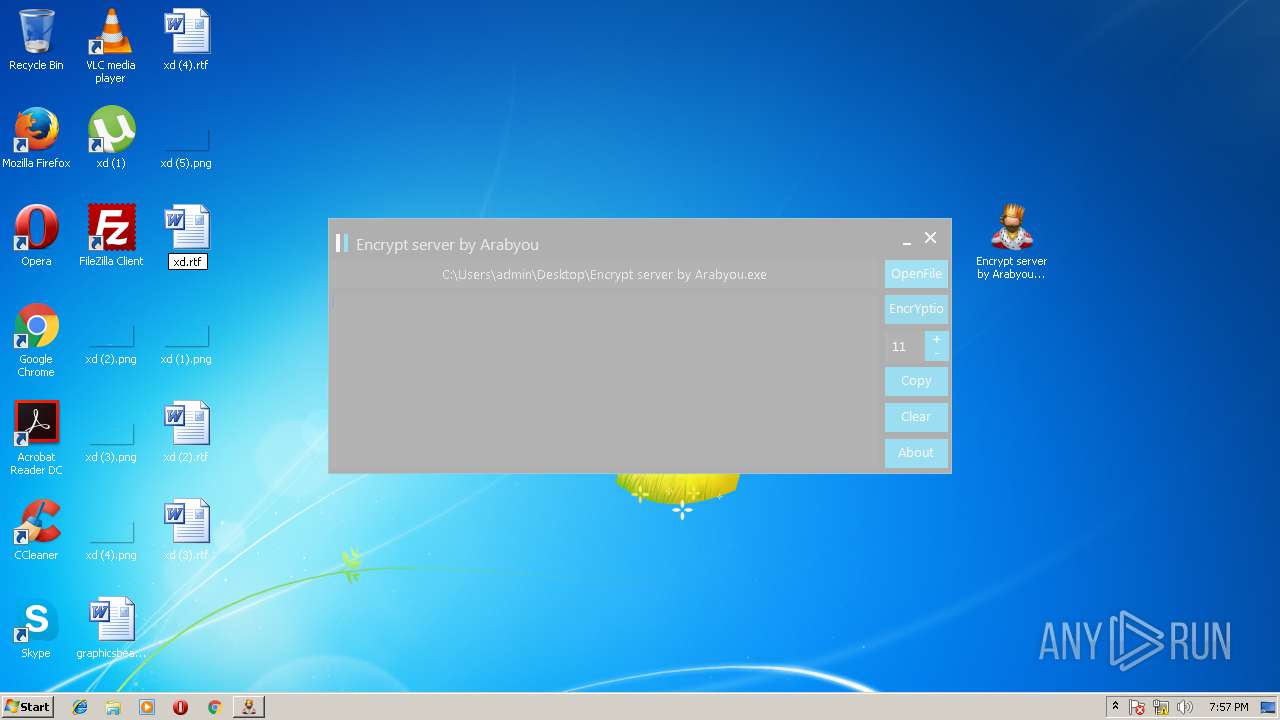
| 2892 | "C:\Users\admin\Desktop\Encrypt server by Arabyou.exe" | C:\Users\admin\Desktop\Encrypt server by Arabyou.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Encrypt server by Arabyou Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3928 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
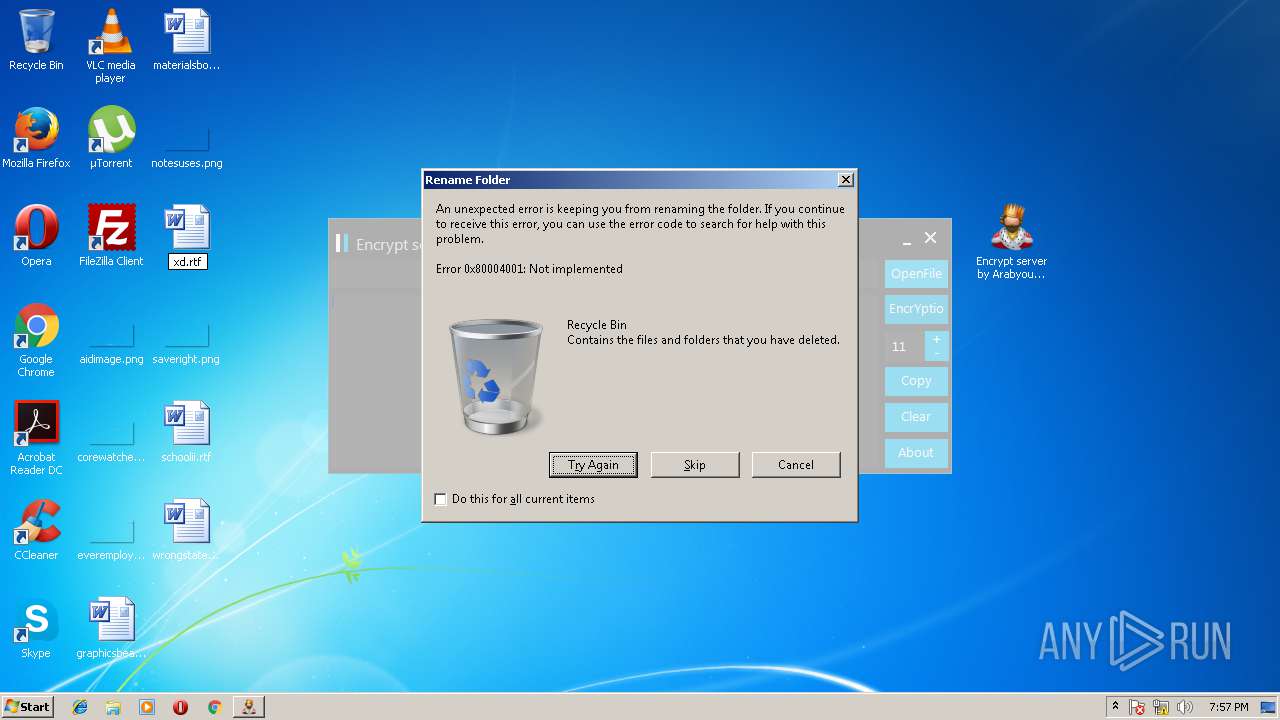
Total events
561
Read events
513
Write events
47
Delete events
1
Modification events
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderShortcuts |
Value: | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderHistory |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0045006E006300720079007000740020007300650072007600650072002000620079002000410072006100620079006F0075002E007200610072005C000000 | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath0 |
Value: C:\Users\admin\AppData\Local\Temp\ | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc0 |
Value: 0 | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath1 |
Value: | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc1 |
Value: 0 | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | ListMode |
Value: 771 | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Position |
Value: 1600000016000000D60300000B02000000000000 | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Panels |
Value: 0100000000000000DA010000 | |||
| (PID) Process: | (2668) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM\Columns |
| Operation: | write | Name: | 7-Zip.Rar5 |
Value: 0100000004000000010000000400000001000000A00000000700000001000000640000000800000001000000640000000C00000001000000640000000A00000001000000640000000B00000001000000640000000900000001000000640000003F00000001000000640000000F00000001000000640000000D00000001000000640000001000000001000000640000001100000001000000640000001300000001000000640000001700000001000000640000001600000001000000640000003600000001000000640000005A00000001000000640000005F00000001000000640000001F00000001000000640000002000000001000000640000002E00000001000000640000003E0000000100000064000000 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | DllHost.exe | C:\Users\Public\Desktop\xd (7).lnk | lnk | |
MD5:— | SHA256:— | |||
| 2668 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC6AC338F\Encrypt server by Arabyou.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | DllHost.exe | C:\Users\Public\Desktop\xd (4).lnk | lnk | |
MD5:— | SHA256:— | |||
| 3928 | DllHost.exe | C:\Users\Public\Desktop\xd (1).lnk | lnk | |
MD5:— | SHA256:— | |||
| 3928 | DllHost.exe | C:\Users\Public\Desktop\xd (6).lnk | lnk | |
MD5:— | SHA256:— | |||
| 3928 | DllHost.exe | C:\Users\Public\Desktop\xd (3).lnk | lnk | |
MD5:— | SHA256:— | |||
| 3928 | DllHost.exe | C:\Users\Public\Desktop\xd (2).lnk | lnk | |
MD5:— | SHA256:— | |||
| 3928 | DllHost.exe | C:\Users\Public\Desktop\xd (5).lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report