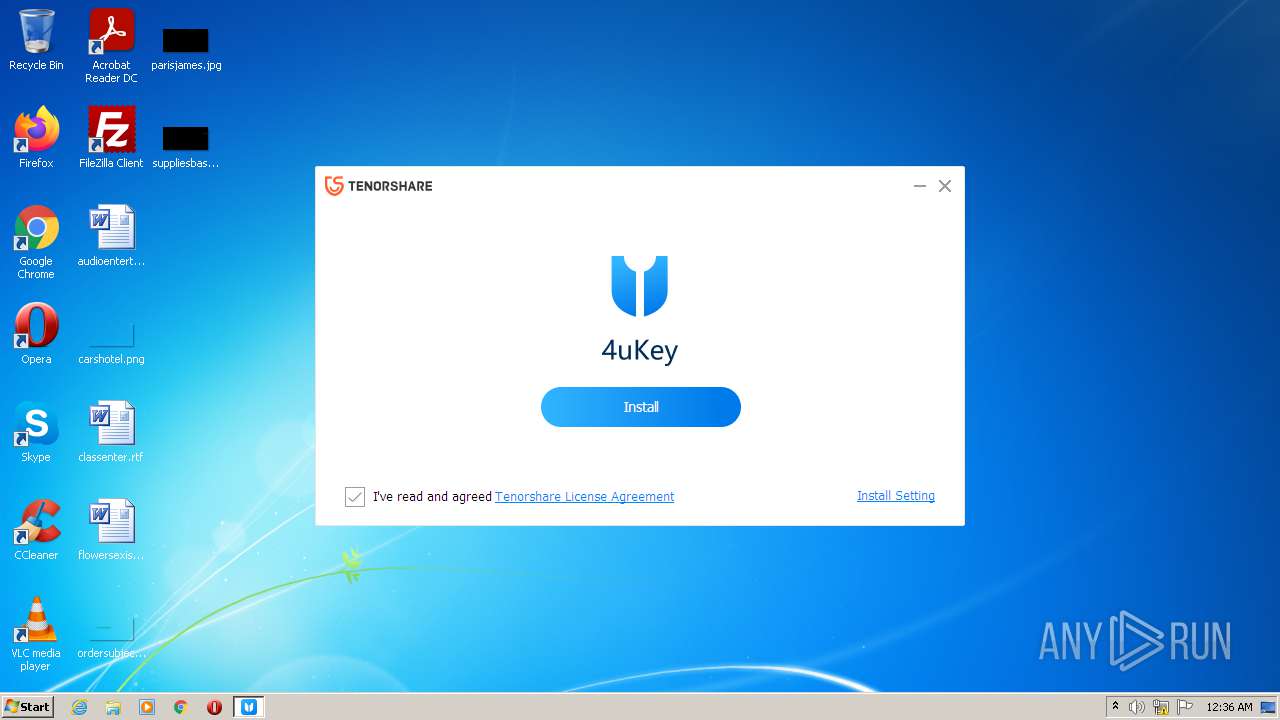
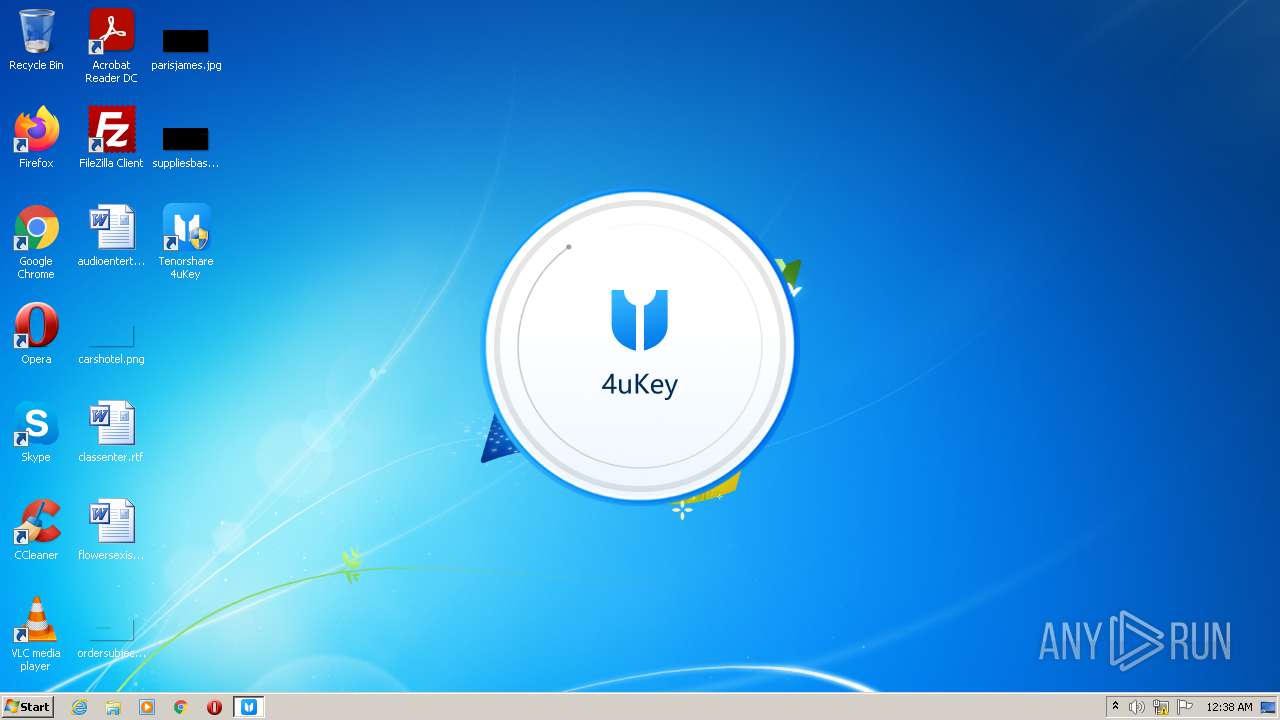
| File name: | 4ukey.exe |
| Full analysis: | https://app.any.run/tasks/207838ab-1443-4730-b67c-845cc48a38a4 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2021, 00:35:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | B4EF23D885178B7F9D96996568060126 |
| SHA1: | 9378C9BF4BFD3792BF8220AF4F13AA9577C46BE6 |
| SHA256: | E1943B5EAD71FC40FBE5F48988CA8E7B9668795788726AC2F19C7039DDF1F8C4 |
| SSDEEP: | 49152:S2DuSfVVglZ66XmuItxlwfm+GJfZtKs5rFxT61hjar40Kzz++BGtZUhVtoNXV+Uc:DDuSfV2+Twu+Ofms38Y40Kzz++BGtZUT |
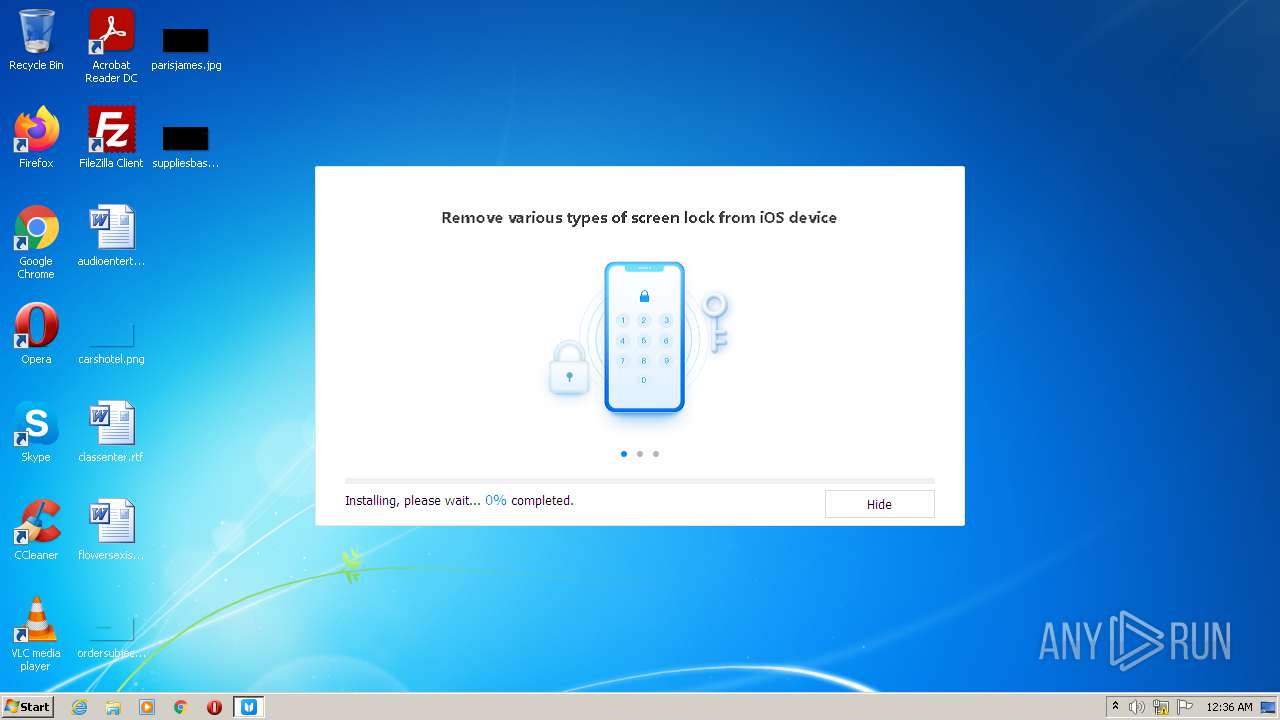
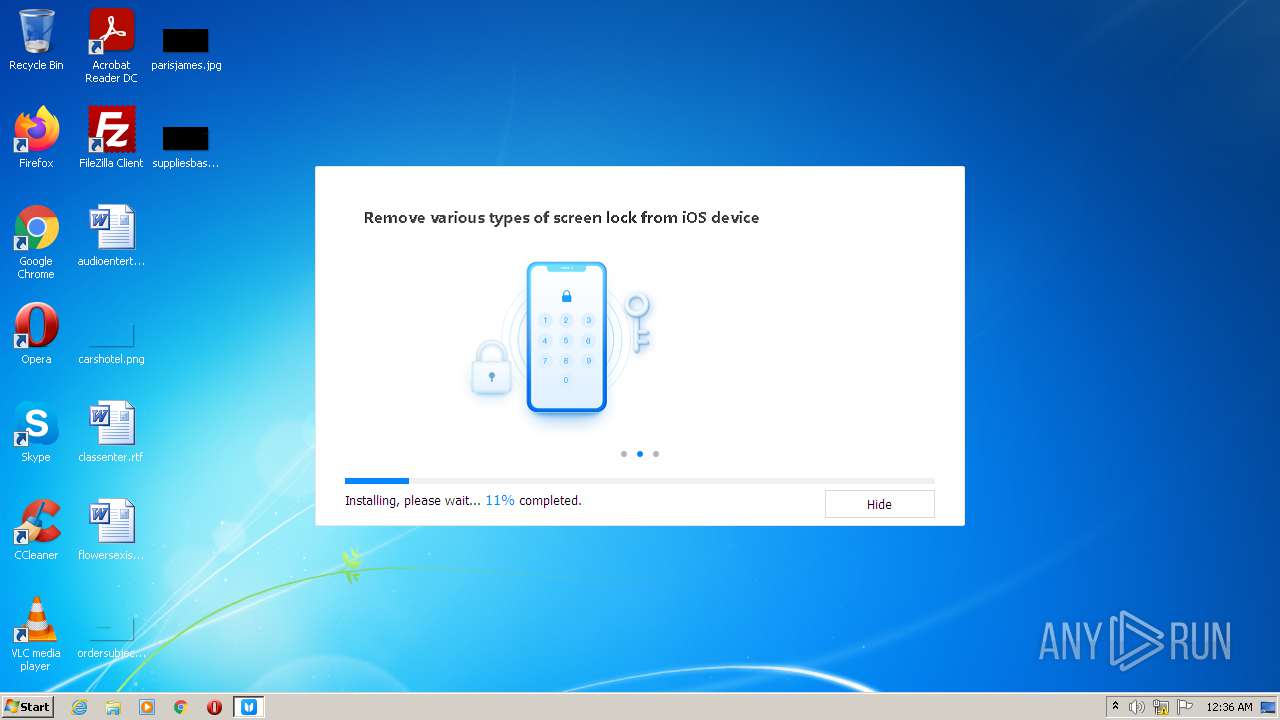
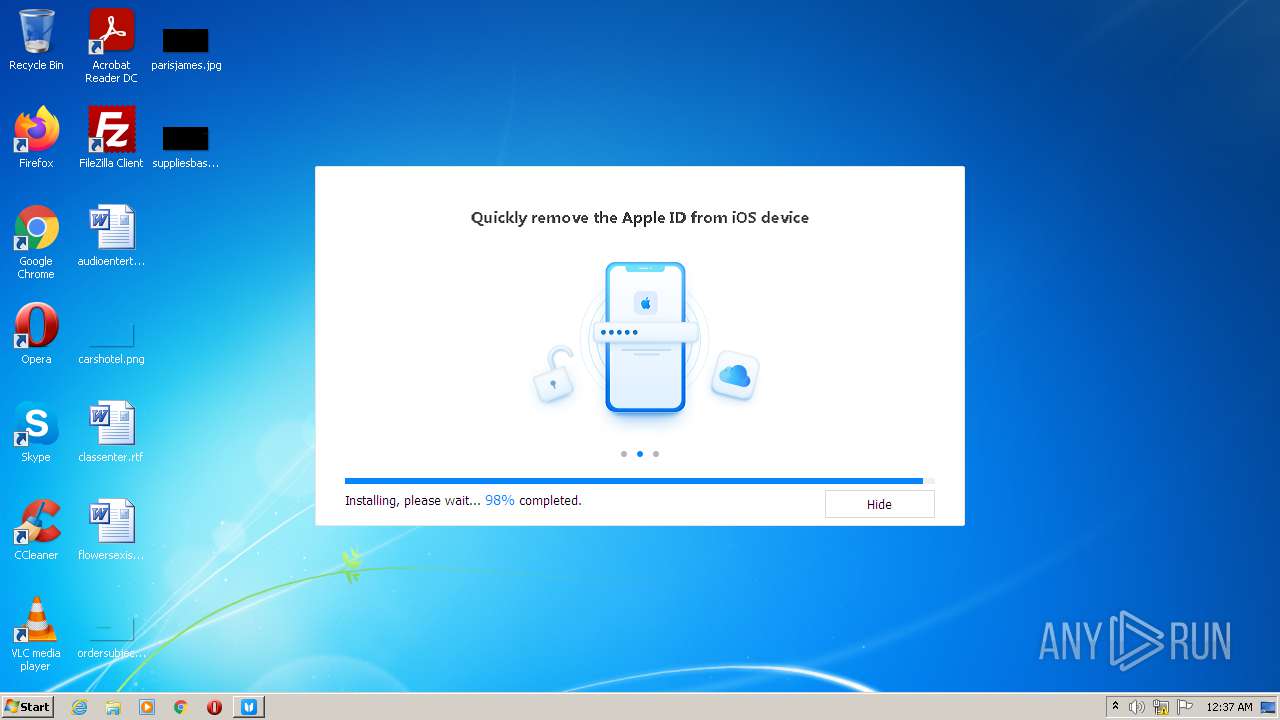
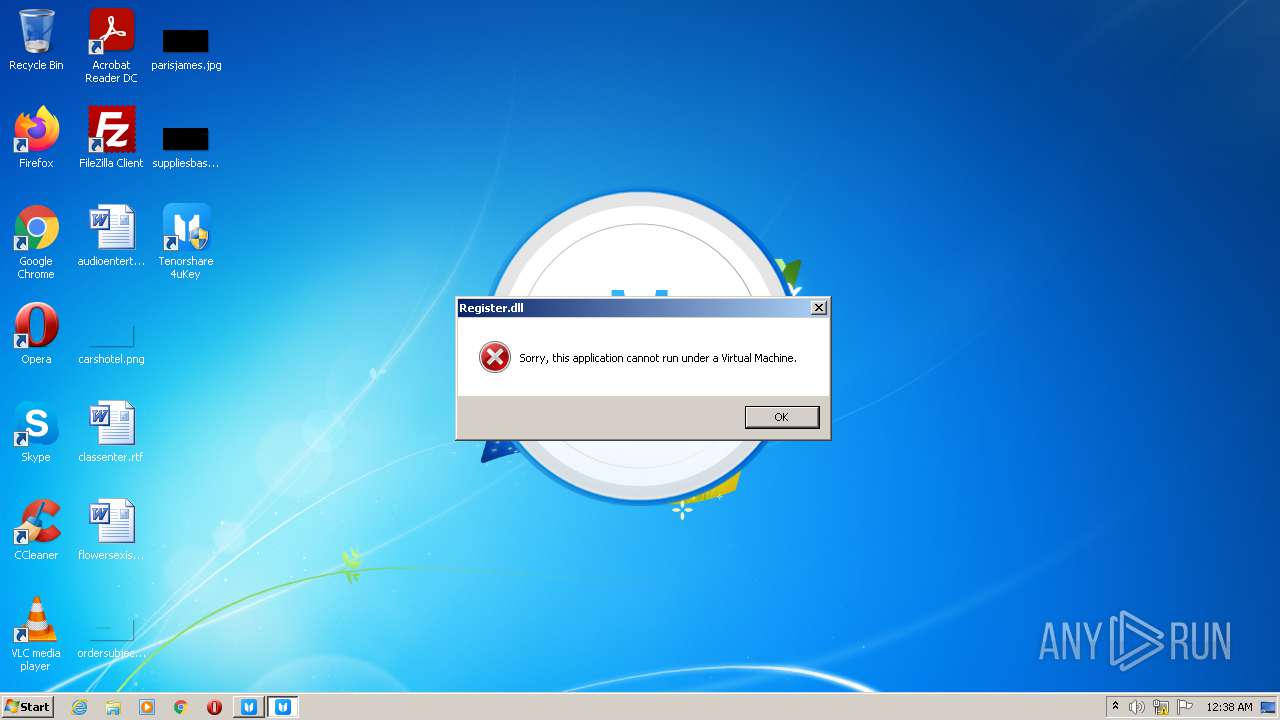
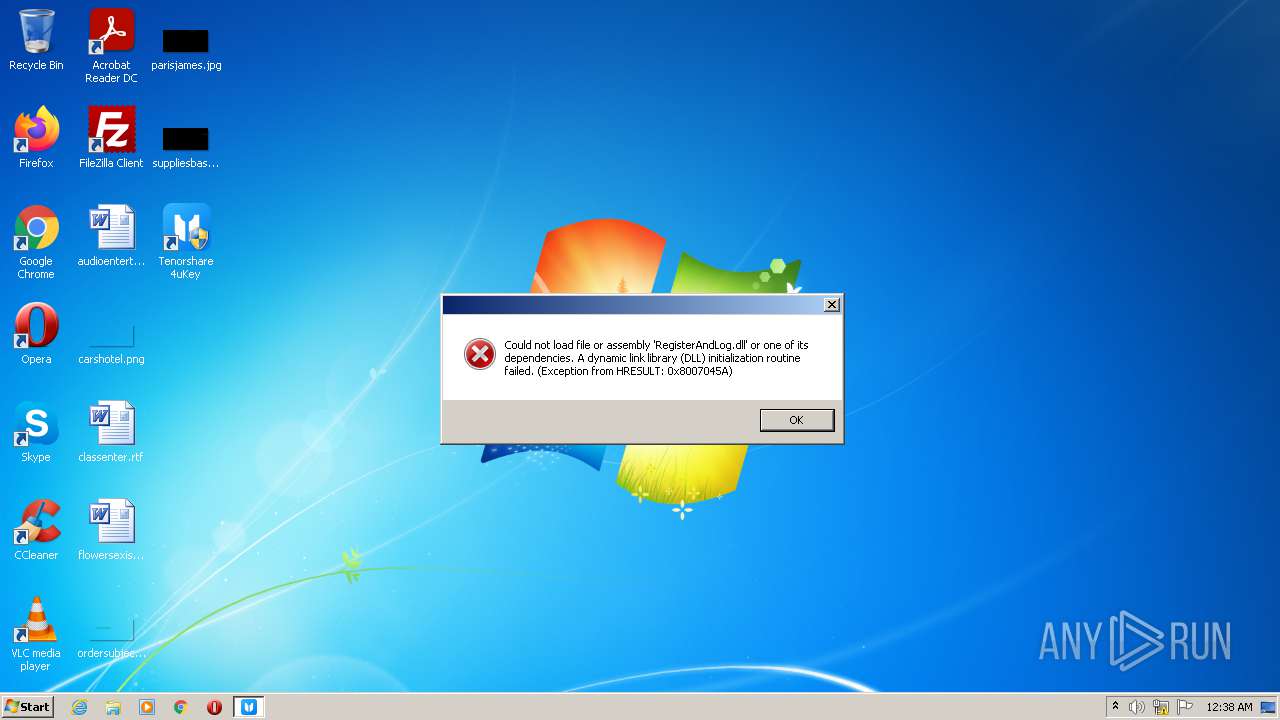
MALICIOUS
Drops executable file immediately after starts
- 4ukeyforios_ts3.0.11.exe (PID: 2132)
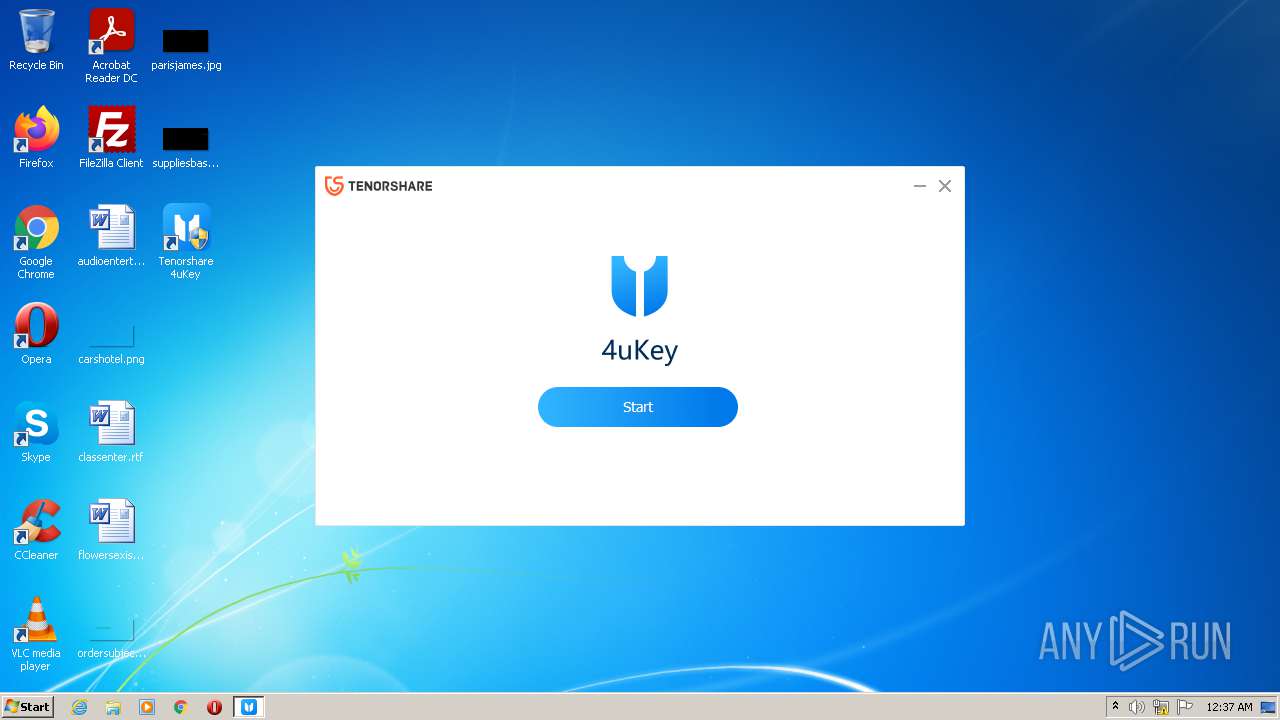
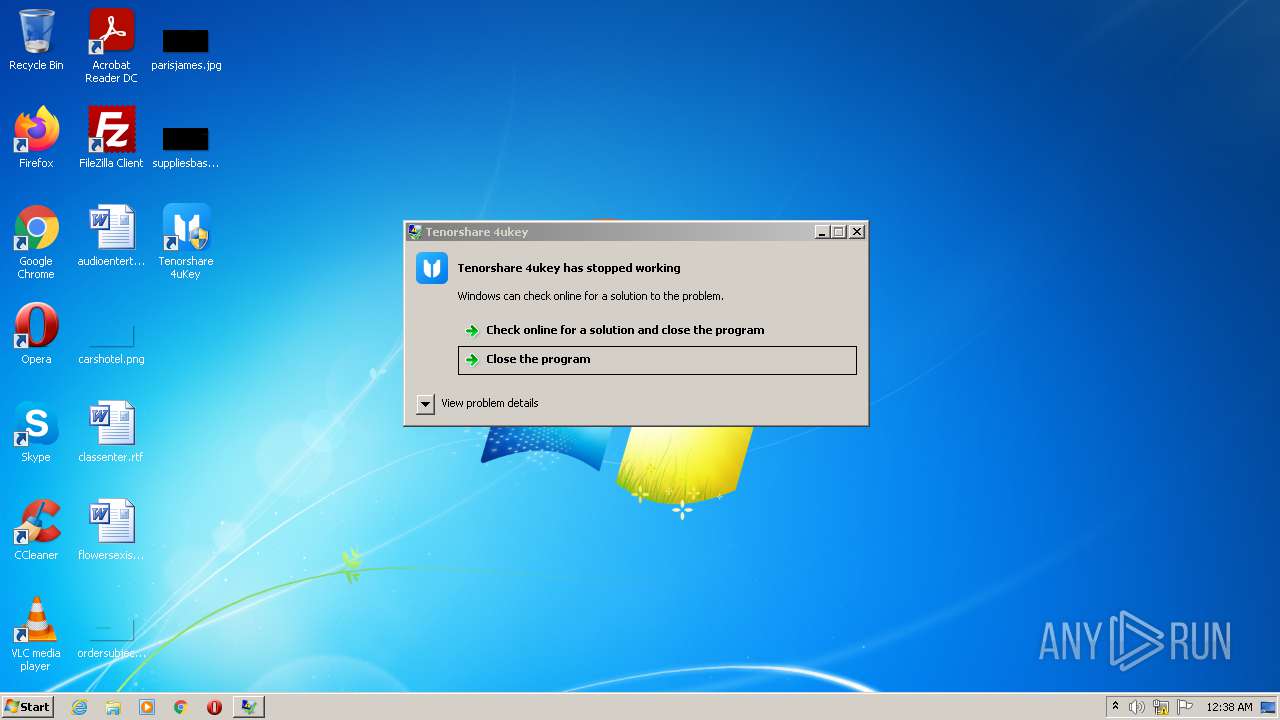
Loads dropped or rewritten executable
- Tenorshare 4uKey.exe (PID: 2544)
- WerFault.exe (PID: 2096)
Application was dropped or rewritten from another process
- Start.exe (PID: 3588)
SUSPICIOUS
Checks supported languages
- 4ukey.exe (PID: 872)
- 4ukeyforios_ts3.0.11.exe (PID: 2132)
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
- cmd.exe (PID: 1248)
- Start.exe (PID: 3588)
- Tenorshare 4uKey.exe (PID: 2544)
Reads the computer name
- 4ukey.exe (PID: 872)
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
- Start.exe (PID: 3588)
- Tenorshare 4uKey.exe (PID: 2544)
Creates files in the user directory
- 4ukey.exe (PID: 872)
Checks for external IP
- 4ukey.exe (PID: 872)
Creates a directory in Program Files
- 4ukey.exe (PID: 872)
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
- Start.exe (PID: 3588)
Reads Windows owner or organization settings
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Executable content was dropped or overwritten
- 4ukeyforios_ts3.0.11.exe (PID: 2132)
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Reads the Windows organization settings
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Starts CMD.EXE for commands execution
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1248)
Drops a file with too old compile date
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Drops a file with a compile date too recent
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Creates files in the program directory
- Start.exe (PID: 3588)
- Tenorshare 4uKey.exe (PID: 2544)
- WerFault.exe (PID: 2096)
Creates a software uninstall entry
- 4ukey.exe (PID: 872)
Drops a file that was compiled in debug mode
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
INFO
Reads settings of System Certificates
- 4ukey.exe (PID: 872)
Checks Windows Trust Settings
- 4ukey.exe (PID: 872)
Reads the computer name
- taskkill.exe (PID: 3628)
- WerFault.exe (PID: 2096)
Checks supported languages
- taskkill.exe (PID: 3628)
- WerFault.exe (PID: 2096)
Application was dropped or rewritten from another process
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Creates a software uninstall entry
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Creates files in the program directory
- 4ukeyforios_ts3.0.11.tmp (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:09 10:29:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1732608 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | 2002944 |
| EntryPoint: | 0x390590 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.5.1.5 |
| ProductVersionNumber: | 2.5.1.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Tenorshare Co., Ltd. |
| FileVersion: | 2.5.1.5 |
| LegalCopyright: | Copyright © 2007-2021 Tenorshare Co.,Ltd. |
| ProductVersion: | 2.5.1.5 |
| FileDescription: | 4uKey |
| ProductName: | 20210909162931 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Sep-2021 08:29:55 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000148 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 09-Sep-2021 08:29:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x001E9000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x001EA000 | 0x001A7000 | 0x001A6800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90413 |
.rsrc | 0x00391000 | 0x0002A000 | 0x00029C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.26087 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
53
Monitored processes
9
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Users\admin\AppData\Local\Temp\4ukey.exe" | C:\Users\admin\AppData\Local\Temp\4ukey.exe | Explorer.EXE | ||||||||||||
User: admin Company: Tenorshare Co., Ltd. Integrity Level: HIGH Description: 4uKey Exit code: 0 Version: 2.5.1.5 Modules
| |||||||||||||||
| 1248 | "C:\Windows\system32\cmd.exe" /c taskkill /f /t /im "Tenorshare 4uKey.exe" | C:\Windows\system32\cmd.exe | — | 4ukeyforios_ts3.0.11.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2096 | C:\Windows\system32\WerFault.exe -u -p 2544 -s 984 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | /VERYSILENT /SP- /NORESTART /DIR="C:\Program Files\Tenorshare\4uKey\" /LANG=en /LOG="C:\Users\admin\AppData\Local\Temp\4uKey_Setup_20211124003732.log" | C:\Users\admin\AppData\Local\Temp\4ukeyforios_ts\4ukeyforios_ts3.0.11.exe | 4ukey.exe | ||||||||||||
User: admin Company: Tenorshare, Inc. Integrity Level: HIGH Description: Tenorshare 4uKey Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Tenorshare\4uKey\Tenorshare 4uKey.exe" | C:\Program Files\Tenorshare\4uKey\Tenorshare 4uKey.exe | Start.exe | ||||||||||||
User: admin Company: Tenorshare Integrity Level: HIGH Description: Tenorshare 4ukey Exit code: 3762504530 Version: 3.0.11.2 Modules
| |||||||||||||||
| 3252 | "C:\Users\admin\AppData\Local\Temp\is-65SUM.tmp\4ukeyforios_ts3.0.11.tmp" /SL5="$20136,82048696,284672,C:\Users\admin\AppData\Local\Temp\4ukeyforios_ts\4ukeyforios_ts3.0.11.exe" /VERYSILENT /SP- /NORESTART /DIR="C:\Program Files\Tenorshare\4uKey\" /LANG=en /LOG="C:\Users\admin\AppData\Local\Temp\4uKey_Setup_20211124003732.log" | C:\Users\admin\AppData\Local\Temp\is-65SUM.tmp\4ukeyforios_ts3.0.11.tmp | 4ukeyforios_ts3.0.11.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3588 | "C:\Program Files\Tenorshare\4uKey\Start.exe" | C:\Program Files\Tenorshare\4uKey\Start.exe | — | 4ukey.exe | |||||||||||
User: admin Company: Tenorshare Integrity Level: HIGH Description: 4uKey Exit code: 0 Version: 2.0.0.4 Modules
| |||||||||||||||
| 3624 | "C:\Users\admin\AppData\Local\Temp\4ukey.exe" | C:\Users\admin\AppData\Local\Temp\4ukey.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Tenorshare Co., Ltd. Integrity Level: MEDIUM Description: 4uKey Exit code: 3221226540 Version: 2.5.1.5 Modules
| |||||||||||||||
| 3628 | taskkill /f /t /im "Tenorshare 4uKey.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 276
Read events
6 171
Write events
99
Delete events
6
Modification events
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tenorshare\Downloader2.5.0 |
| Operation: | write | Name: | GA_PC |
Value: 1 | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (872) 4ukey.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
367
Suspicious files
22
Text files
95
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 872 | 4ukey.exe | C:\Users\admin\AppData\Local\Temp\4ukeyforios_ts\4ukeyforios_ts3.0.11.exe | — | |
MD5:— | SHA256:— | |||
| 872 | 4ukey.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\GGIWI0HO.txt | text | |
MD5:09602E81F1441FEC984597C8F761ADD3 | SHA256:5D398F4D8A341B93A44B9A7FFAE6C622A4345ECA2B846C8A068D0A9FCDF0D69A | |||
| 872 | 4ukey.exe | C:\Users\admin\AppData\Local\Temp\4ukeyforios_ts\4ukeyforios_ts3.0.11.exe.xml | text | |
MD5:8820F7ADBDAB3CED4F0762DE0BF13AA6 | SHA256:89E4FEDC512FB715EE5D47FE614304732F4232306F5391E7609EAAA7453891C8 | |||
| 872 | 4ukey.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:409B248E3061ACB946EF87CA503CF25C | SHA256:AFFF1A4B5933FE010F096CF8DC1F8602E897BD6611F05F50FE0D2DA4AC685A82 | |||
| 872 | 4ukey.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:8357277AE436663720E038E67393E287 | SHA256:4BB756605D1E7F50DEFBC64AA4645A390D5BCE6AF593AB53806F19350B2746F8 | |||
| 872 | 4ukey.exe | C:\Users\admin\AppData\Local\Temp\4ukeyforios_ts\4ukeyforios_ts3.0.11.exe.db | text | |
MD5:1355376EA2BCA8E4CE4261291060B006 | SHA256:9CBEA2630B40A9B83CF55946CA7FFD9583D7F6780862BE143EB0B9A5B7E23B13 | |||
| 2132 | 4ukeyforios_ts3.0.11.exe | C:\Users\admin\AppData\Local\Temp\is-65SUM.tmp\4ukeyforios_ts3.0.11.tmp | executable | |
MD5:2026C8AE443CCE55970462B5C31B6F3D | SHA256:3ED949E22291747284B1303DA38104AF2A9A72414839EDC270CDB0F795ED2668 | |||
| 3252 | 4ukeyforios_ts3.0.11.tmp | C:\Program Files\Tenorshare\4uKey\iTunesRepairResources\x64\autoInstall64.exe | executable | |
MD5:98248B8E2B141D88EC625D20BF0CDF21 | SHA256:CA35E99FEB8CB40D86DA442F91BEC0896D03D3FBBA988E9060EAB84412F8807B | |||
| 3252 | 4ukeyforios_ts3.0.11.tmp | C:\Program Files\Tenorshare\4uKey\iTunesRepairResources\x64\infinstallx64.exe | executable | |
MD5:34A2311DA295D54BDC3A070DF8F4374C | SHA256:40C870A5AB44E560FA919D795E6225B6C7CBE61BC6A92EEA65E6C719412B71DF | |||
| 872 | 4ukey.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:0AEF5A177E8B23FEF980F6F061EC00DA | SHA256:727A6AED72564CF0816C9B53DB4F17475D9AF58C71BE5723397045868CB8422D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
122
DNS requests
7
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | 4ukey.exe | POST | 200 | 142.250.186.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
872 | 4ukey.exe | POST | 200 | 142.250.186.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
872 | 4ukey.exe | POST | 200 | 142.250.186.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
872 | 4ukey.exe | POST | 200 | 142.250.186.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
872 | 4ukey.exe | POST | 200 | 142.250.186.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
872 | 4ukey.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
872 | 4ukey.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d27e2e2685e6ebad | US | compressed | 4.70 Kb | whitelisted |
872 | 4ukey.exe | POST | 200 | 142.250.186.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
872 | 4ukey.exe | POST | 200 | 142.250.186.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
872 | 4ukey.exe | POST | 200 | 142.250.186.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
872 | 4ukey.exe | 104.18.25.249:80 | www.tenorshare.com | Cloudflare Inc | US | suspicious |
872 | 4ukey.exe | 104.18.24.249:80 | www.tenorshare.com | Cloudflare Inc | US | suspicious |
872 | 4ukey.exe | 104.18.24.30:443 | check.mobie.app | Cloudflare Inc | US | unknown |
872 | 4ukey.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
872 | 4ukey.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
872 | 4ukey.exe | 142.250.186.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
872 | 4ukey.exe | 104.18.25.249:443 | www.tenorshare.com | Cloudflare Inc | US | suspicious |
872 | 4ukey.exe | 104.18.24.249:443 | www.tenorshare.com | Cloudflare Inc | US | suspicious |
872 | 4ukey.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
872 | 4ukey.exe | 104.18.25.30:443 | check.mobie.app | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.tenorshare.com |
| whitelisted |
check.mobie.app |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ip-api.com |
| malicious |
www.google-analytics.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
download.tenorshare.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
872 | 4ukey.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
872 | 4ukey.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
872 | 4ukey.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
872 | 4ukey.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2 ETPRO signatures available at the full report