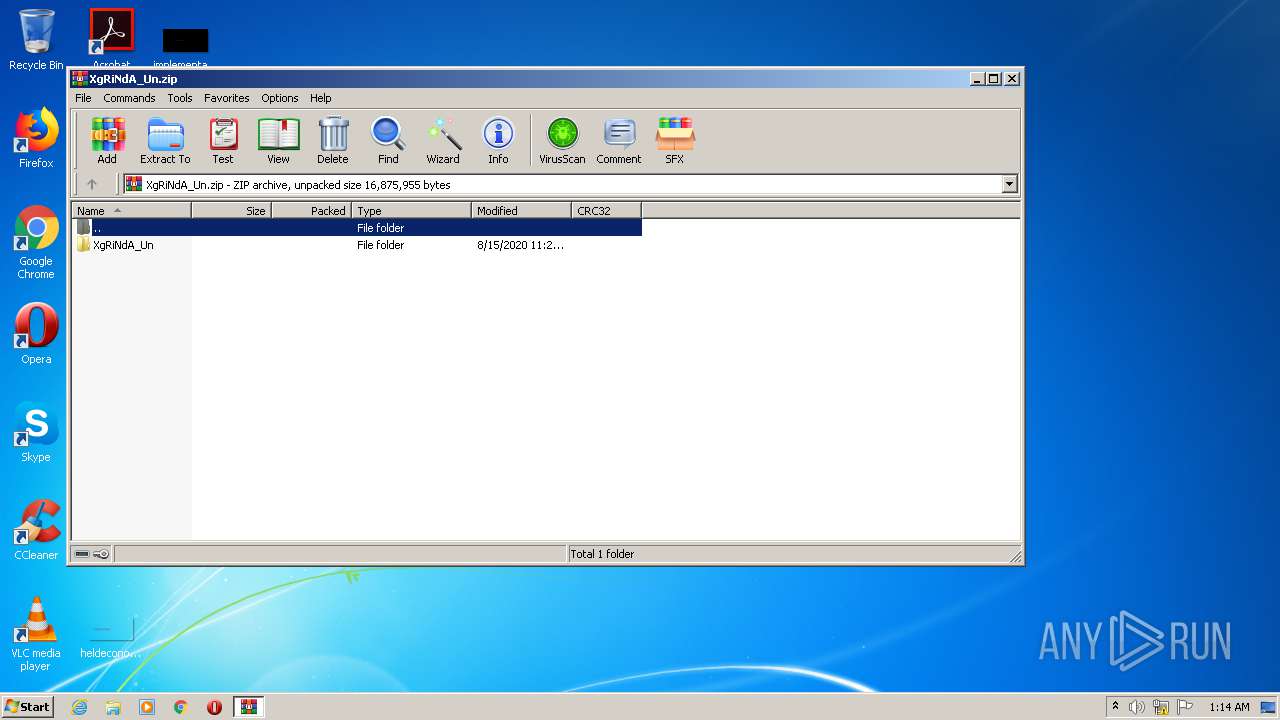
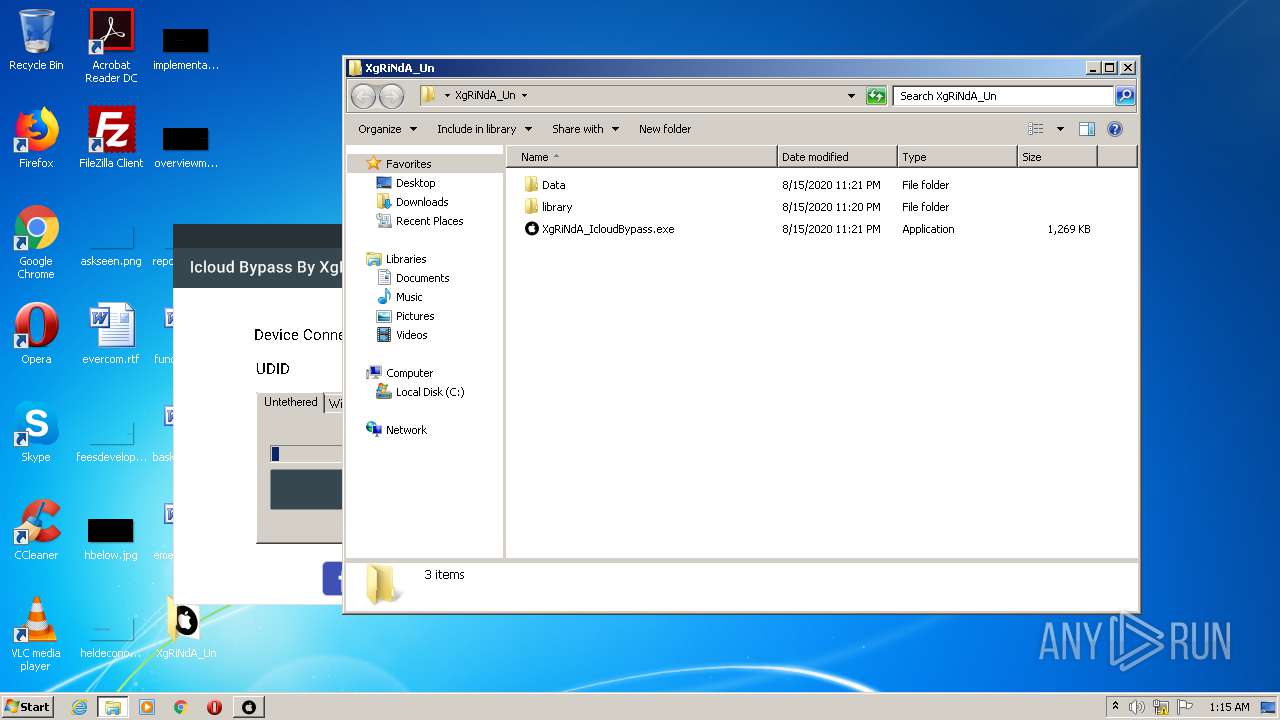
| File name: | XgRiNdA_Un.zip |
| Full analysis: | https://app.any.run/tasks/6cecd015-7361-4b83-b897-5263fab66494 |
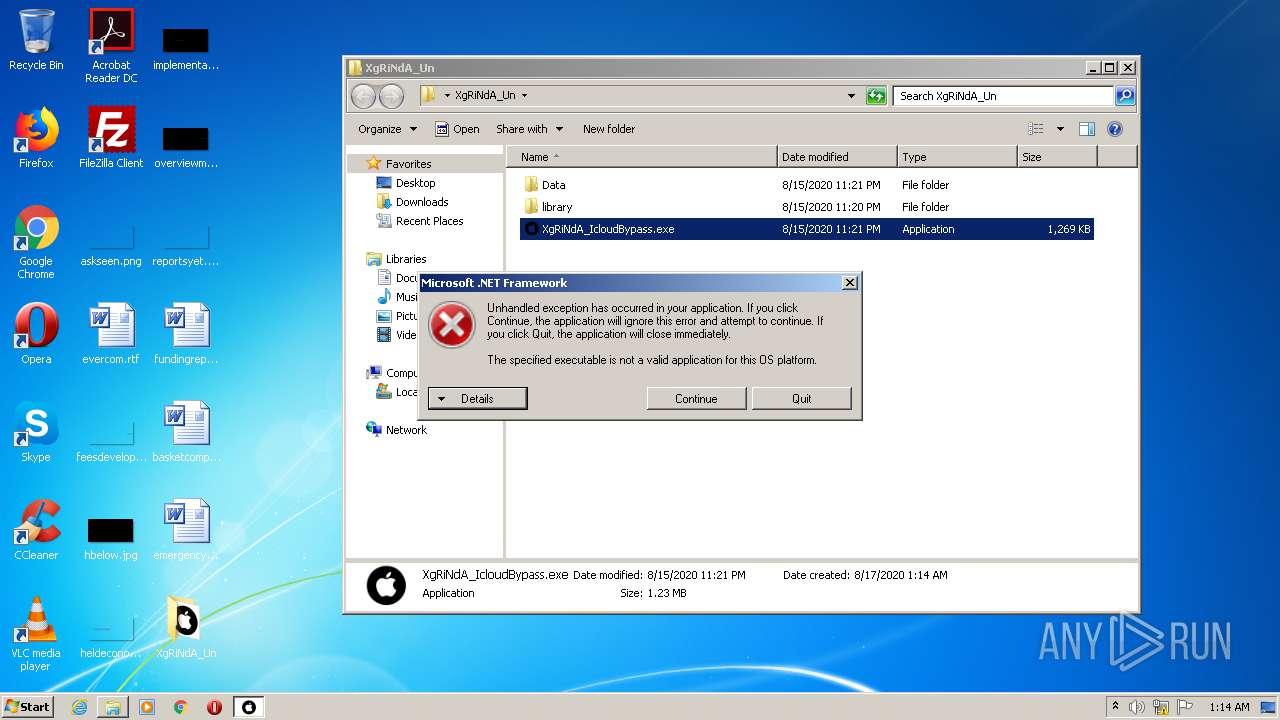
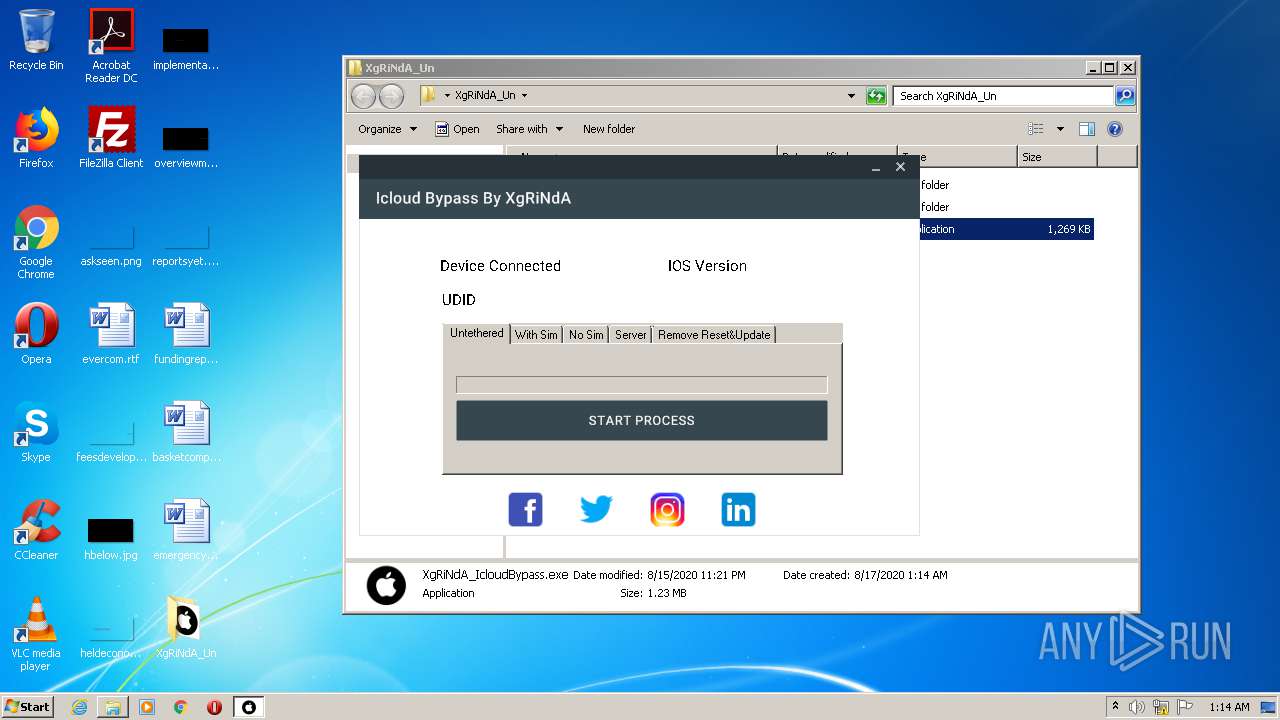
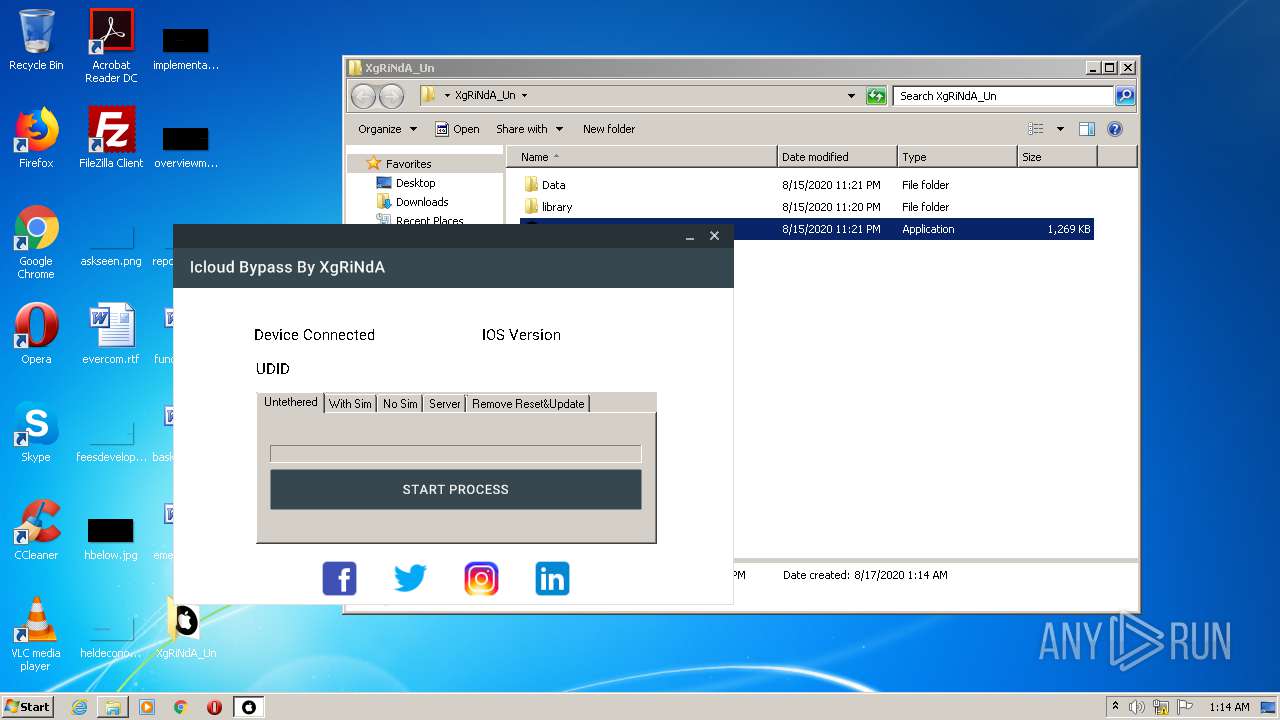
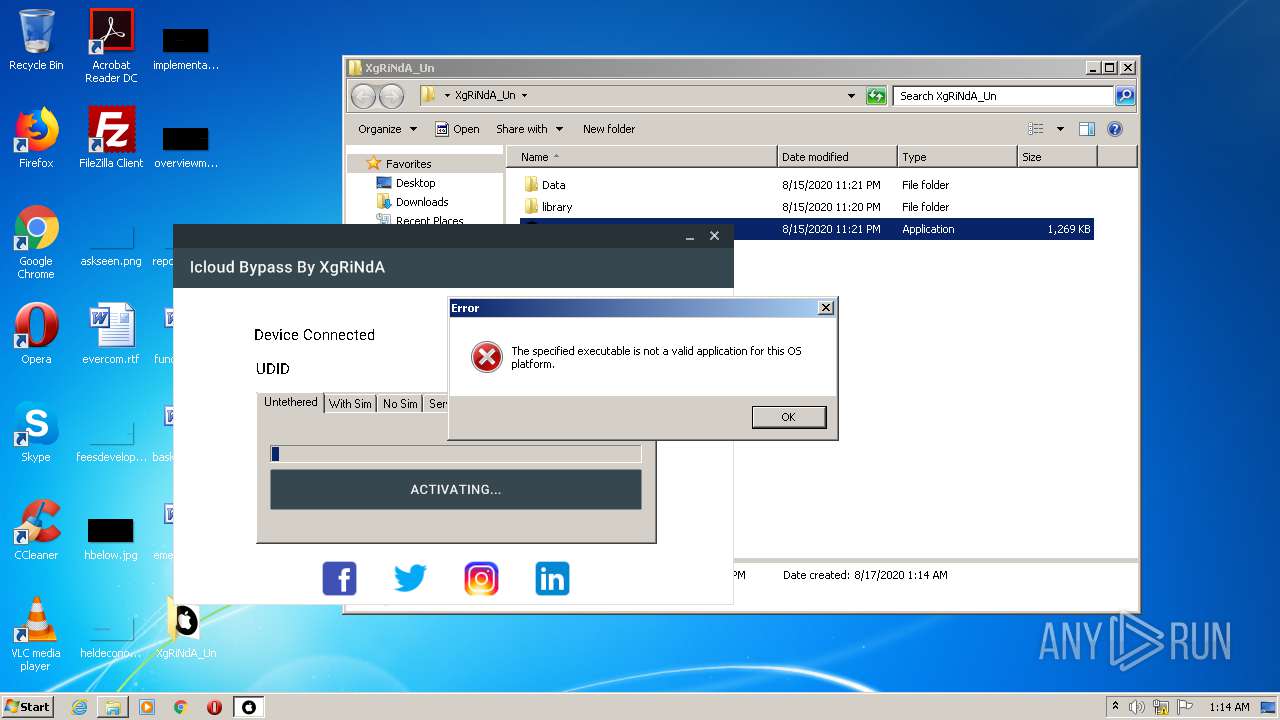
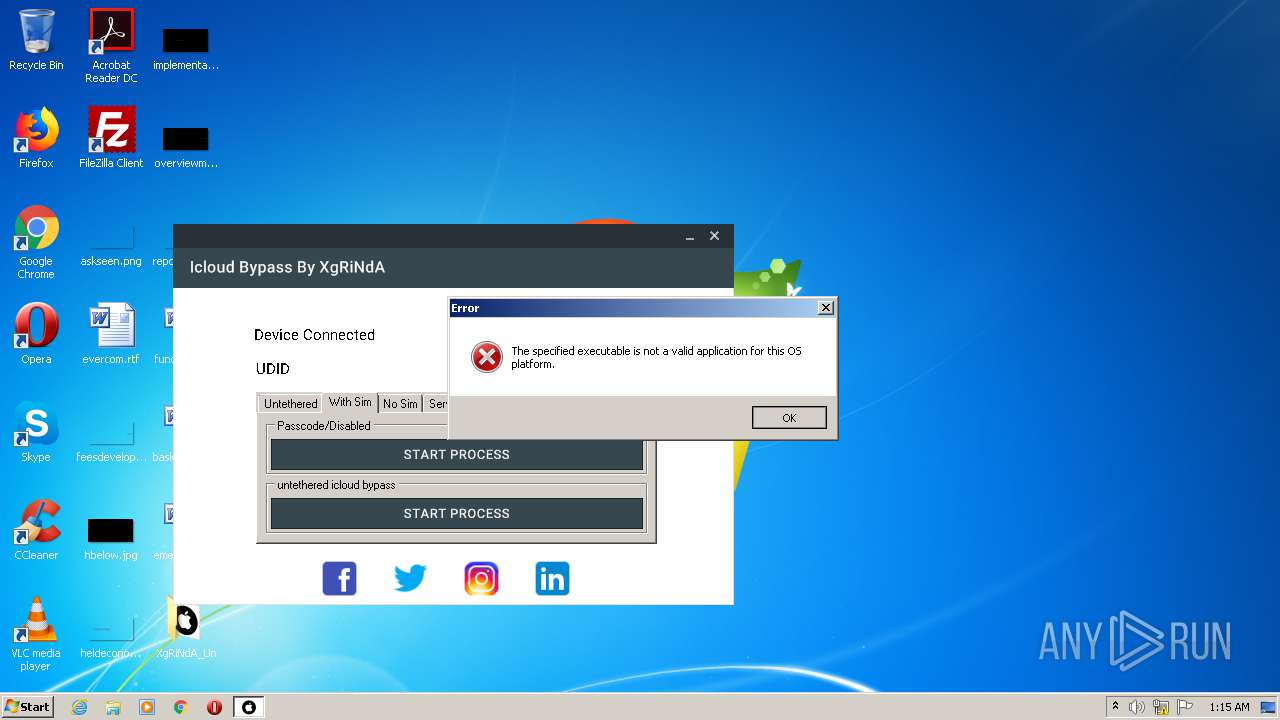
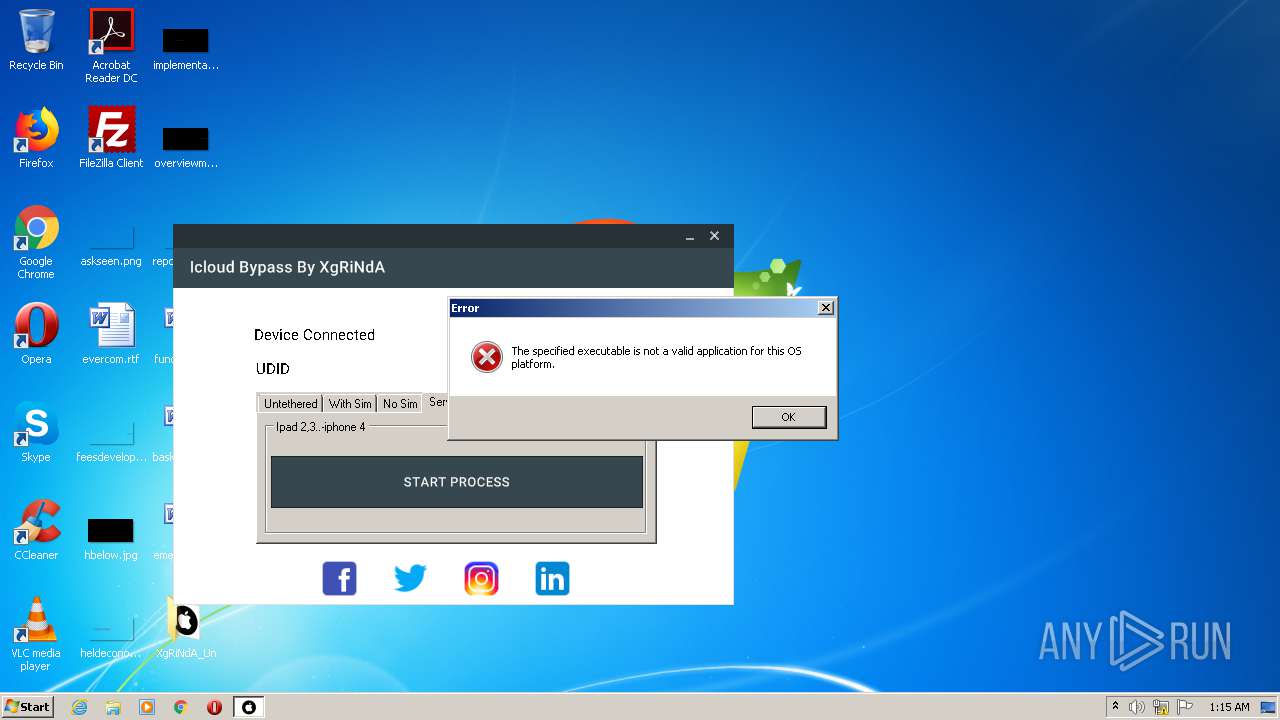
| Verdict: | Suspicious activity |
| Analysis date: | August 17, 2020, 00:14:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | E10D50200DDC68AA2852B05A939AC41E |
| SHA1: | F5A48C0C28B783C6073A85E43C9CD3BA0B44C8B5 |
| SHA256: | E17BC8637B6A0DCC0AE73AF1C28FB371F8DA96238302639876B35BC00901564C |
| SSDEEP: | 196608:OhhdH5Eolz5cfSWz7Y9YIWh+murnlnuljv+a1HuFsf9fh1pkRDDHP4sHaSC2Ee0U:Oh2ol6njfeluljvD1OF+9h/svXHEepXH |
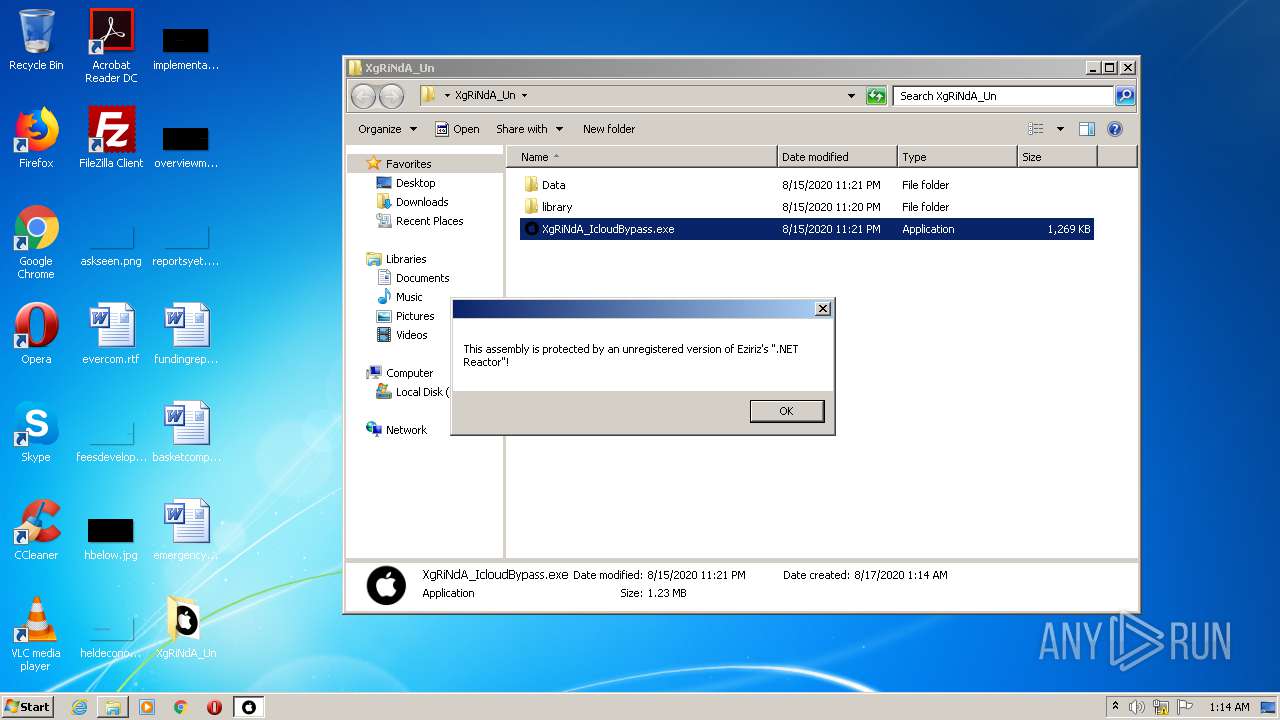
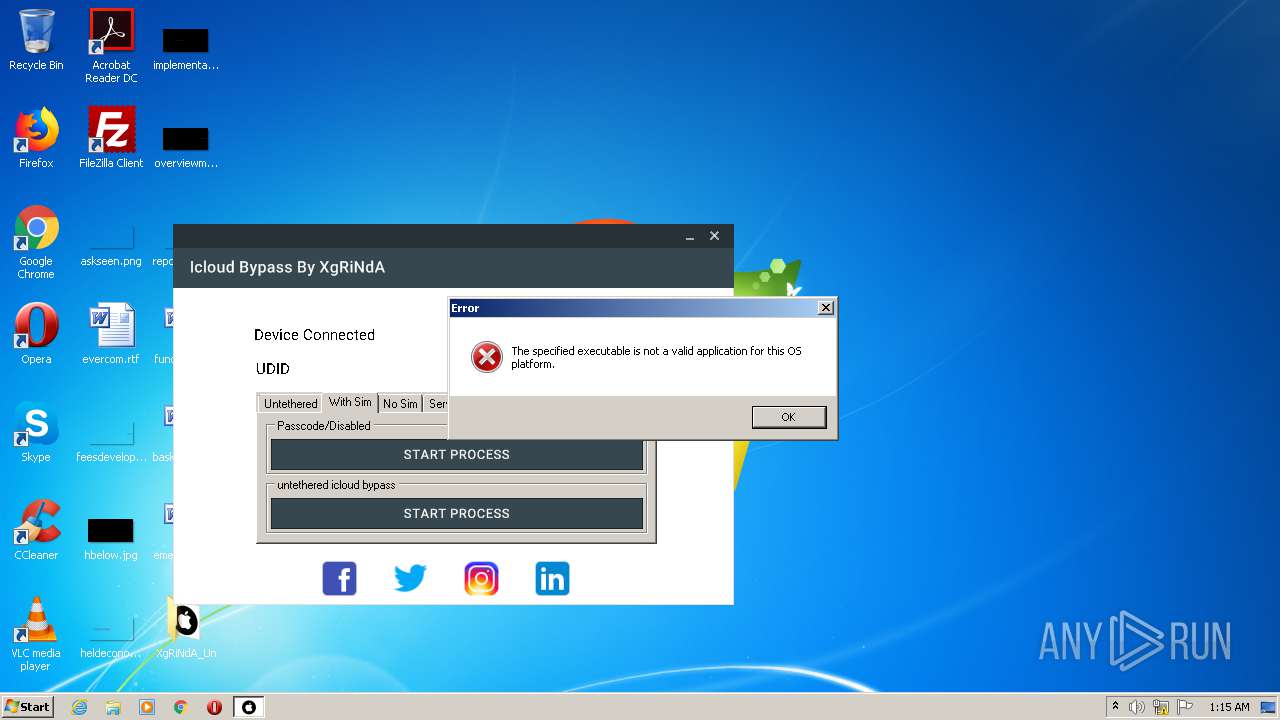
MALICIOUS
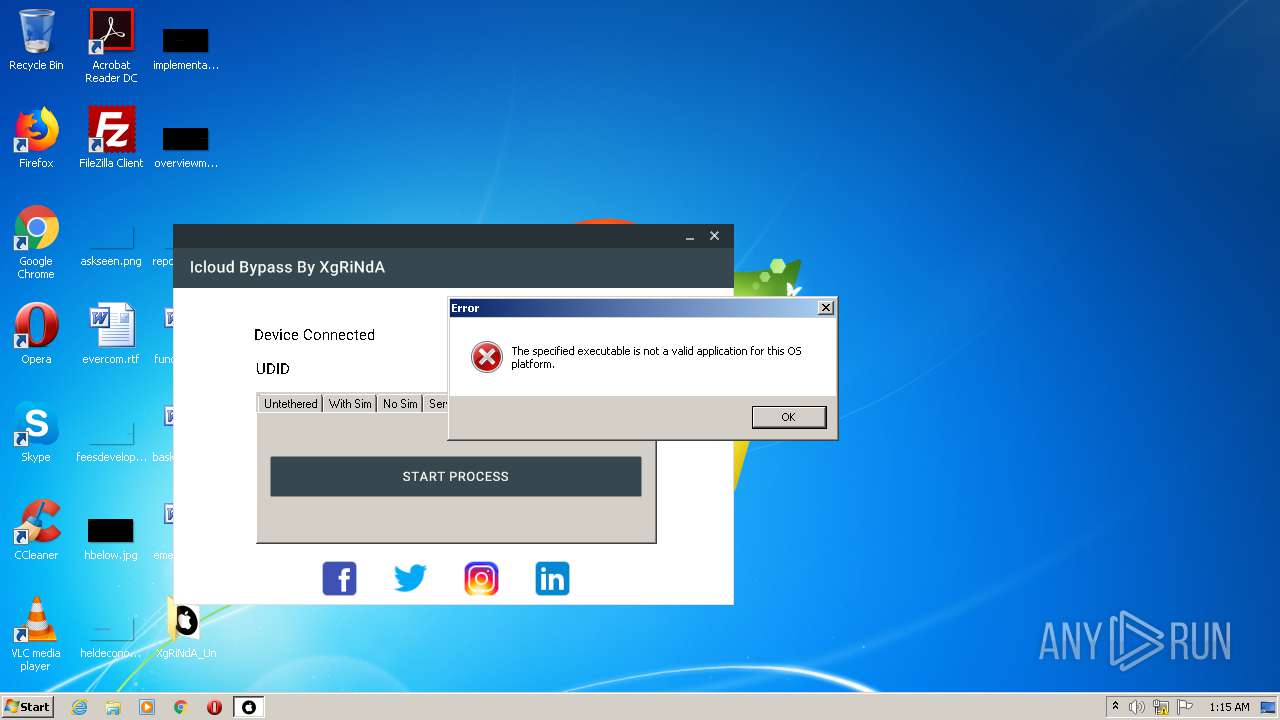
Application was dropped or rewritten from another process
- XgRiNdA_IcloudBypass.exe (PID: 3340)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2660)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2660)
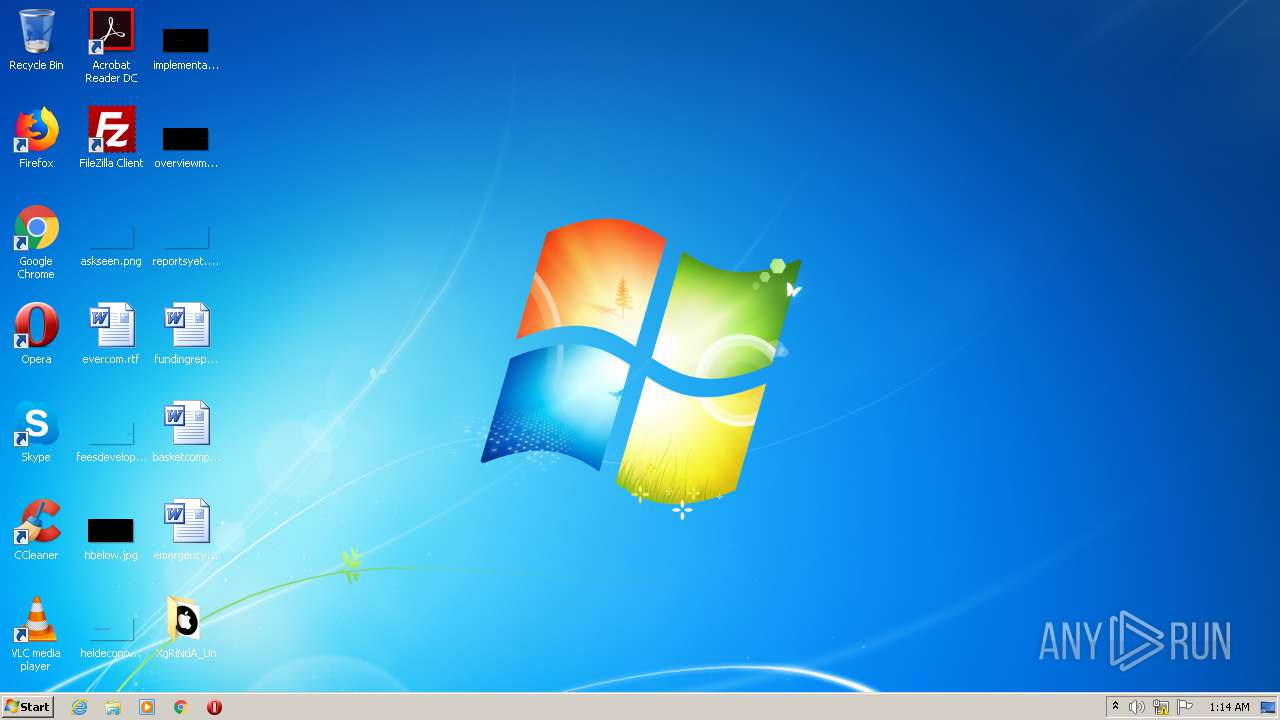
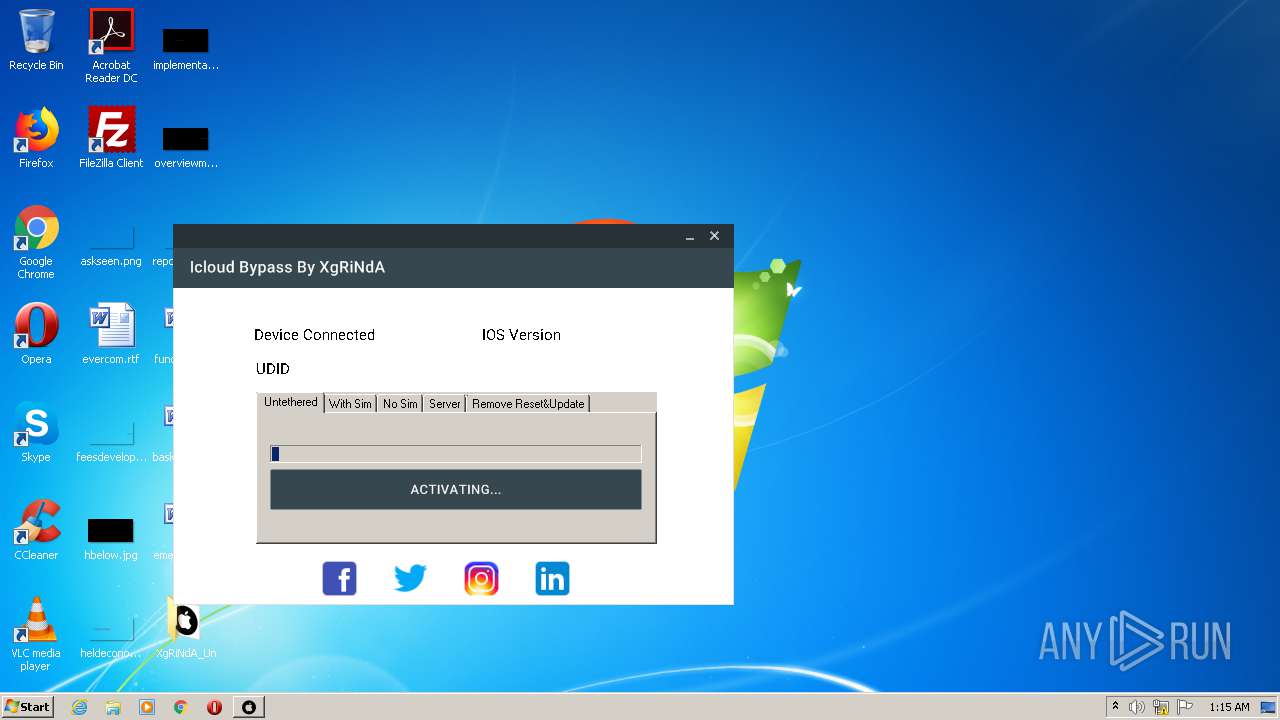
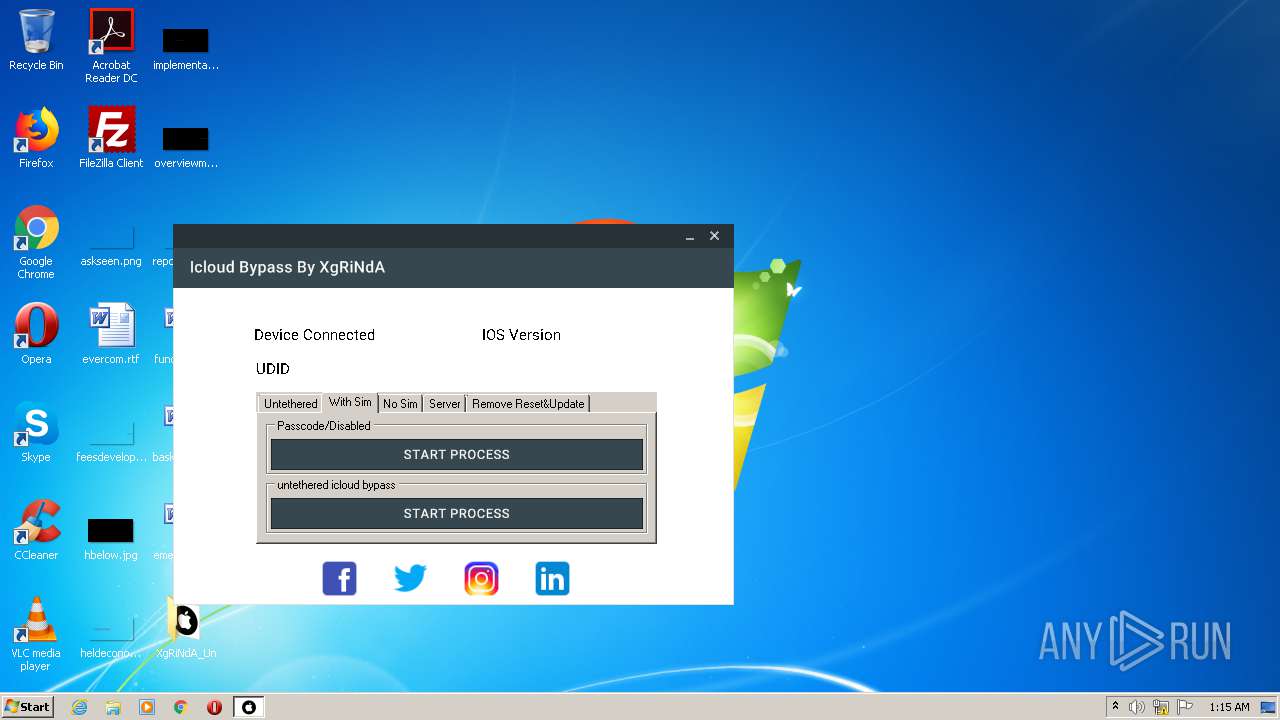
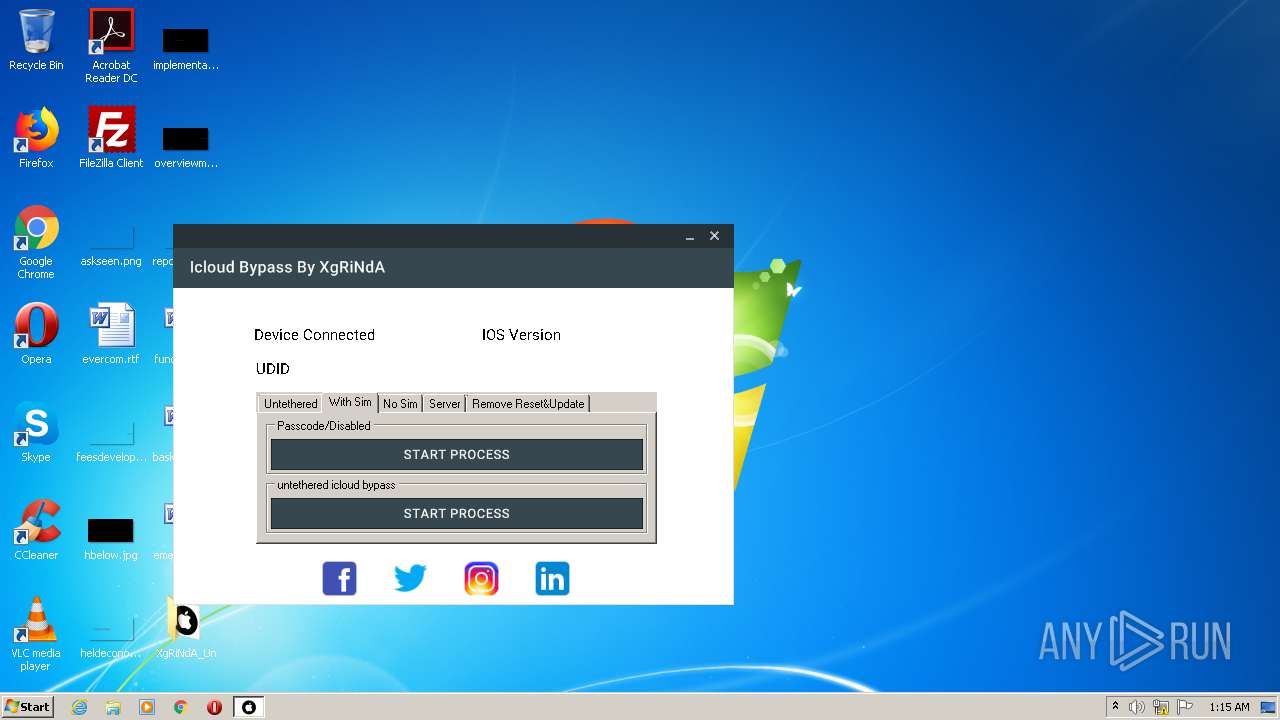
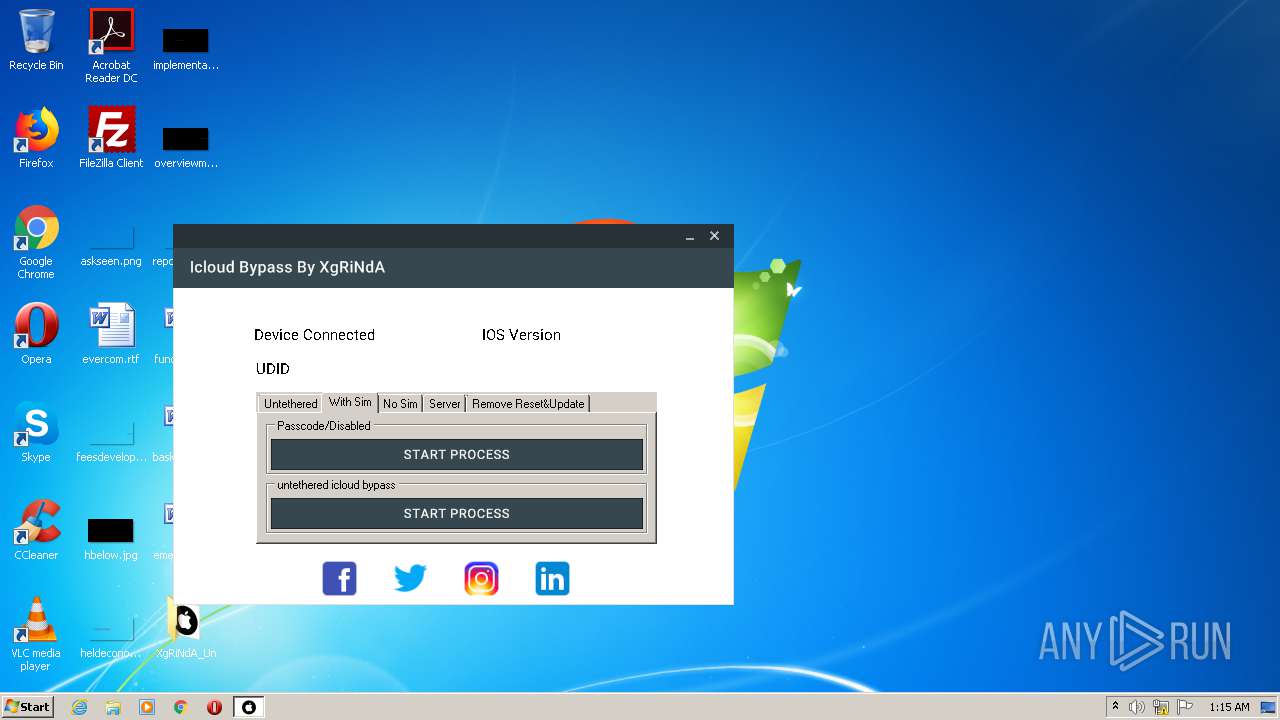
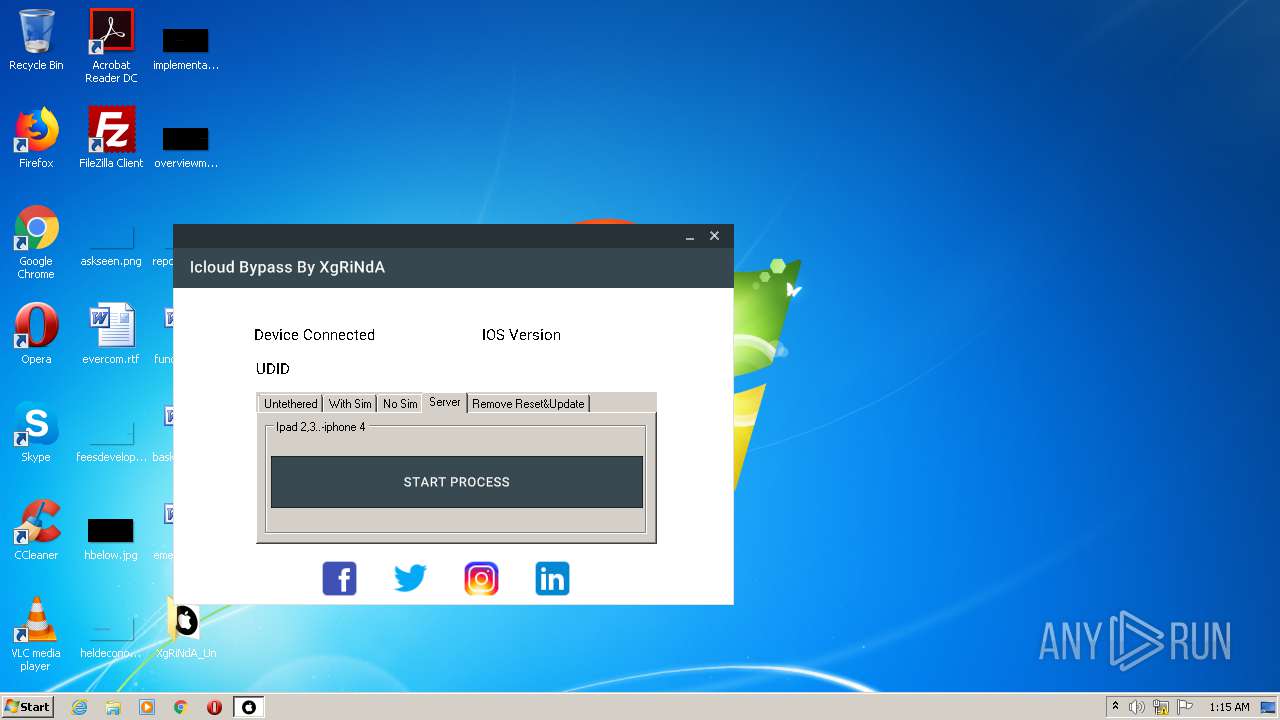
Manual execution by user
- XgRiNdA_IcloudBypass.exe (PID: 3340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
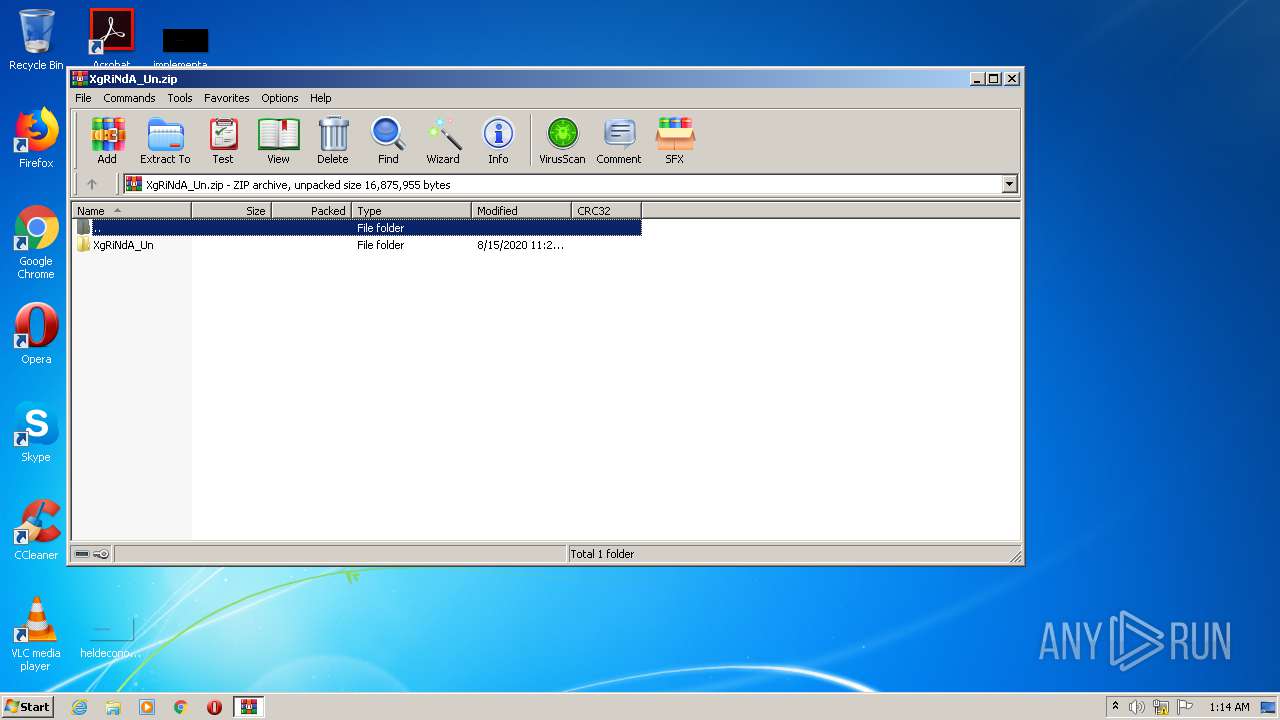
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:08:15 23:21:27 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | XgRiNdA_Un/ |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
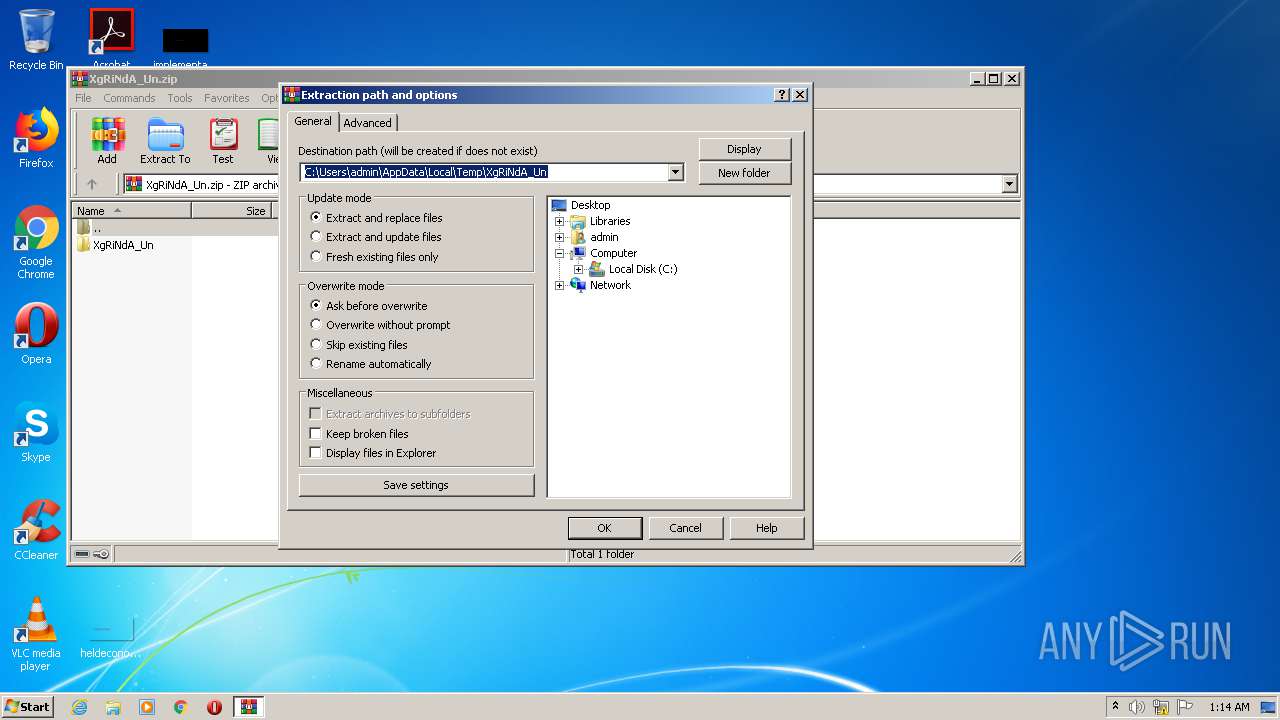
| 2660 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\XgRiNdA_Un.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
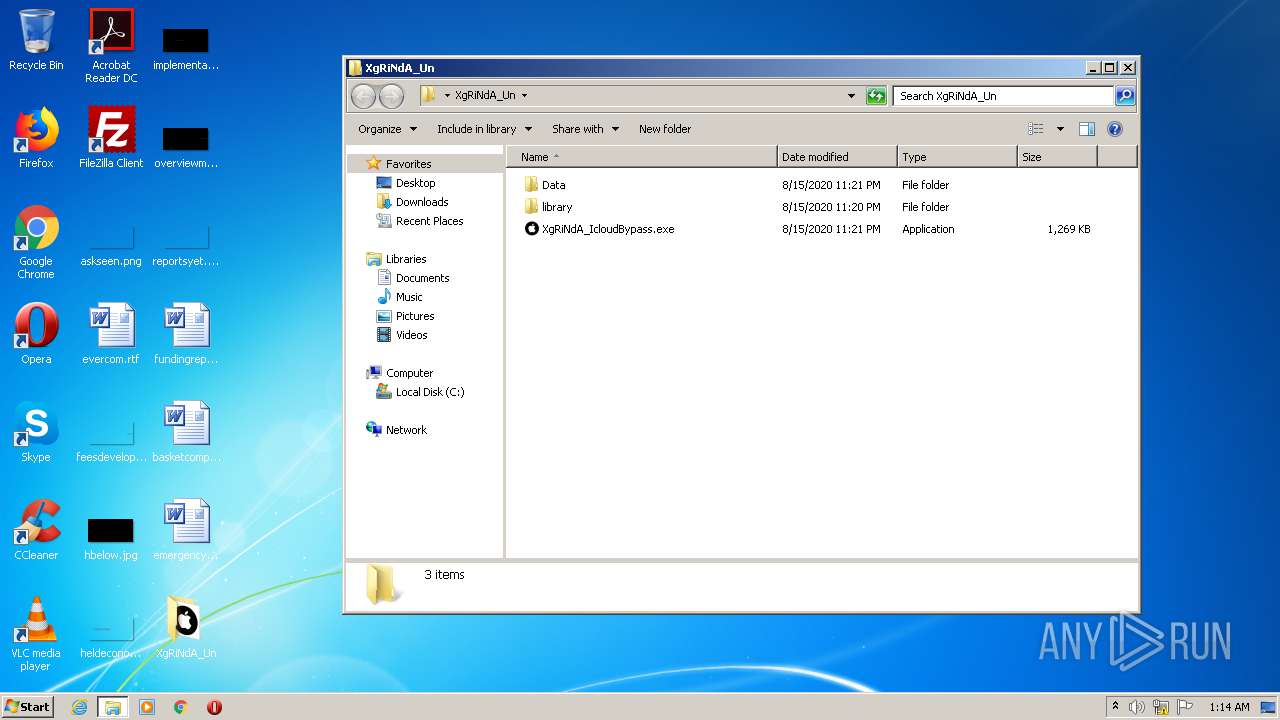
| 3340 | "C:\Users\admin\Desktop\XgRiNdA_Un\XgRiNdA_IcloudBypass.exe" | C:\Users\admin\Desktop\XgRiNdA_Un\XgRiNdA_IcloudBypass.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: BypassXgrinda Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
453
Read events
431
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\XgRiNdA_Un.zip | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
52
Suspicious files
11
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\0 | text | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\.irecovery | text | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\General.plist | binary | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\com.iro.mobileact.plist | xml | |
MD5:455093DB13EA83565DEADD9094A07CFA | SHA256:609941453E84C98CEA9E930AE7BB8DA0ECC5388A239F85457F56B04BBC5DC1FD | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\2 | binary | |
MD5:AFC0C8B0C9FD24BBA43E78C35AC6C6C3 | SHA256:BAFB841FF1AF687B7DA4575FFBFB6D2252AD902C6C3EBF7FD851FB4F5C5E777D | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\boot.tar.lzma | compressed | |
MD5:46AEB8D22BE99A88A5BB7C505EF160B4 | SHA256:27E7FB2F78299D10F063E64880B018CFEE1511A224AA279850416829380B04A3 | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\5 | text | |
MD5:E7886BE650577724A84C9D2CF01929B8 | SHA256:65366A3E17B53AEF3225BD31E32912829A6BE2F3F9E3B3A191423445930C8EBF | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\bz2.dll | executable | |
MD5:4811FFA767191513A35B889E3B162241 | SHA256:65EA387636C06133B02E3F6B9C776FEB2DA851C89D6796CFA172C79BC43DF319 | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\com.apple.purplebuddy.plist | binary | |
MD5:584612C28C4C88ADE71FE03F8412B16C | SHA256:AB66549F891D469F2DCD132F81FC43F6A1F54711D2CF81AA469B9252582969DF | |||
| 2660 | WinRAR.exe | C:\Users\admin\Desktop\XgRiNdA_Un\library\guid.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report