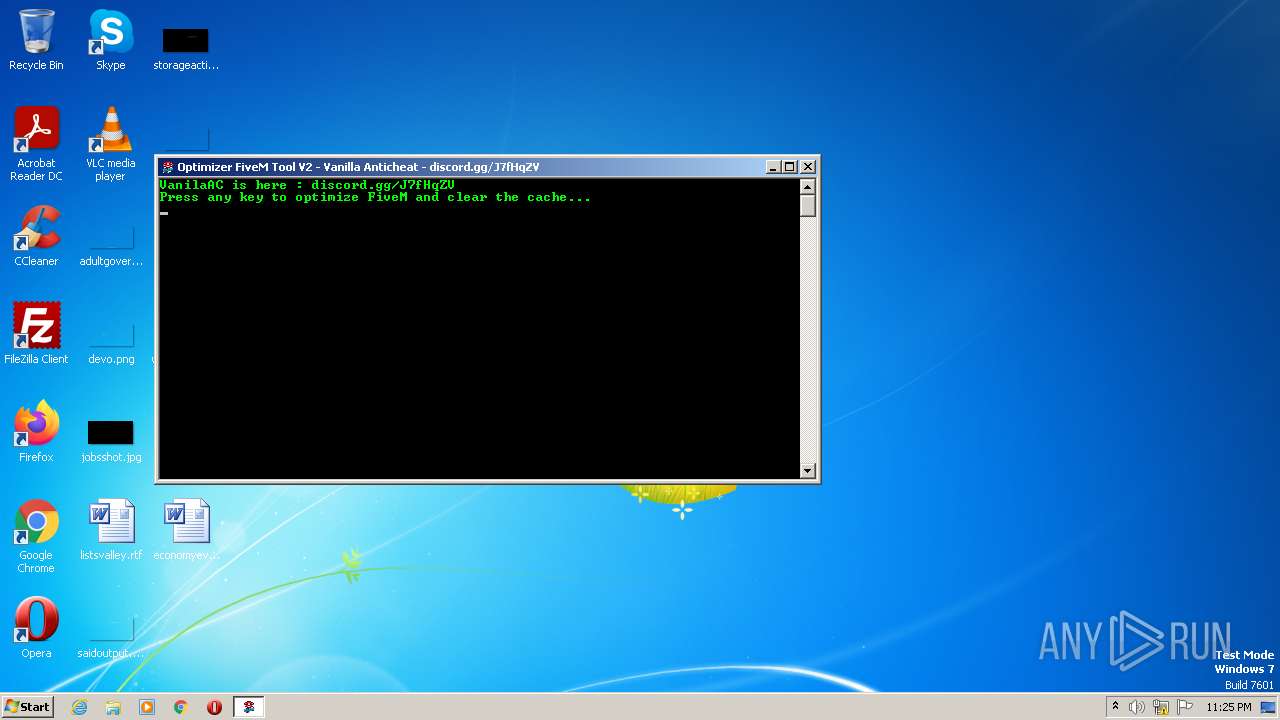
| File name: | FiveM Tool.exe |
| Full analysis: | https://app.any.run/tasks/fb12fcd9-e99b-413d-9850-daf7ebdc56ff |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2023, 22:25:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 68D5949BB558DFDE6F6CFCDFFBBE4B0E |
| SHA1: | E79B30A43932D1CF9D2B9C66808839A290FFEC2E |
| SHA256: | E1685665BA5B1148C4E3E93DEBC86036324BC3854B0CC86FAD859DE3E6C9BE3F |
| SSDEEP: | 3072:L7DhdC6kzWypvaQ0FxyNTBfX35KEa4SjbTsxhC4FuIspgi12:LBlkZvaF4NTBv359a9jboxhCbIspy |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- FiveM Tool.exe (PID: 1900)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2908)
Reads the Internet Settings
- WMIC.exe (PID: 2964)
- cmd.exe (PID: 2908)
- WMIC.exe (PID: 3176)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2908)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 2908)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 2908)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 2908)
Executing commands from a ".bat" file
- FiveM Tool.exe (PID: 1900)
INFO
Checks supported languages
- FiveM Tool.exe (PID: 1900)
Application launched itself
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 2988)
Create files in a temporary directory
- iexplore.exe (PID: 3636)
- FiveM Tool.exe (PID: 1900)
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 1748)
The process checks LSA protection
- taskkill.exe (PID: 3716)
- taskkill.exe (PID: 1736)
- WMIC.exe (PID: 2964)
- WMIC.exe (PID: 3176)
- taskkill.exe (PID: 3444)
- taskkill.exe (PID: 1848)
- taskkill.exe (PID: 4076)
- taskkill.exe (PID: 1020)
- taskkill.exe (PID: 3208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 290816 |
| CodeSize: | 70656 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2019:07:30 08:52:45+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 30-Jul-2019 08:52:45 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jul-2019 08:52:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0000387E | 0x00003A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.52922 |
.text | 0x00005000 | 0x0000D962 | 0x0000DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56249 |
.rdata | 0x00013000 | 0x000033A5 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11184 |
.data | 0x00017000 | 0x0000178C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1014 |
.rsrc | 0x00019000 | 0x00042940 | 0x00042A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.20443 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
9F595F0CFA45AC02862E4D7AEE3782B217DC9F23 | 3.80735 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
A62A3AA26771AF5B1966A7DDB78FD534 | 3.23593 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
C9325682BE9924A548A74A580F544DDA | 7.89439 | 2029 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
CA079E82BD | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
57
Monitored processes
19
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | taskkill /f /im opera.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1736 | taskkill /f /im GTAVLauncher.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2988 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1848 | taskkill /f /im TeamWiever_Service.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | "C:\Users\admin\AppData\Local\Temp\FiveM Tool.exe" | C:\Users\admin\AppData\Local\Temp\FiveM Tool.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2396 | powercfg -s 8c5e7fda-e8bf-4a96-9a85-a6e23a8c635c | C:\Windows\System32\powercfg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Power Settings Command-Line Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2908 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\F4F0.tmp\F4F1.tmp\F4F2.bat "C:\Users\admin\AppData\Local\Temp\FiveM Tool.exe"" | C:\Windows\System32\cmd.exe | — | FiveM Tool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2964 | wmic process where name="FiveM.exe" CALL setpriority 128 | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2988 | "C:\Program Files\Internet Explorer\iexplore.exe" https://vanilla-ac.com/ | C:\Program Files\Internet Explorer\iexplore.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3056 | TIMEOUT /T 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
59 394
Read events
59 030
Write events
364
Delete events
0
Modification events
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
26
Text files
48
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1900 | FiveM Tool.exe | C:\Users\admin\AppData\Local\Temp\F4F0.tmp\F4F1.tmp\F4F2.bat | text | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\W9B3SMQM.txt | text | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\b78079c27a27a2d44a5c[1].js | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\40532.5cd71fbb998e1972823e[1].css | text | |
MD5:— | SHA256:— | |||
| 1748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Z7JD78WR.txt | text | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\55b45a2ebeae4d2bae48[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
29
DNS requests
12
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3284 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3284 | iexplore.exe | GET | 200 | 8.248.133.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d8cd13cda5fd3dd8 | US | compressed | 4.70 Kb | whitelisted |
1748 | iexplore.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?246174d39fb73def | US | compressed | 61.1 Kb | whitelisted |
3636 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3284 | iexplore.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ed69952bc2d0a33e | US | compressed | 4.70 Kb | whitelisted |
1748 | iexplore.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?55471c8af730ef87 | US | compressed | 61.1 Kb | whitelisted |
1748 | iexplore.exe | GET | 200 | 23.37.41.57:80 | http://x2.c.lencr.org/ | NL | der | 300 b | whitelisted |
2988 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1748 | iexplore.exe | GET | 200 | 23.37.41.57:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1748 | iexplore.exe | 104.21.82.97:443 | vanilla-ac.com | CLOUDFLARENET | — | unknown |
3284 | iexplore.exe | 162.159.138.232:443 | discord.com | CLOUDFLARENET | — | malicious |
3284 | iexplore.exe | 67.27.233.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3284 | iexplore.exe | 8.248.133.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | malicious |
3284 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1748 | iexplore.exe | 23.37.41.57:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
1748 | iexplore.exe | 67.27.233.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3636 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3636 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
3636 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vanilla-ac.com |
| unknown |
discord.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
3284 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3284 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3284 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3284 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3636 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3636 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3284 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |