| File name: | parsec-windows.exe |
| Full analysis: | https://app.any.run/tasks/a59b5f7c-06df-409f-96ac-fd3253b201dc |
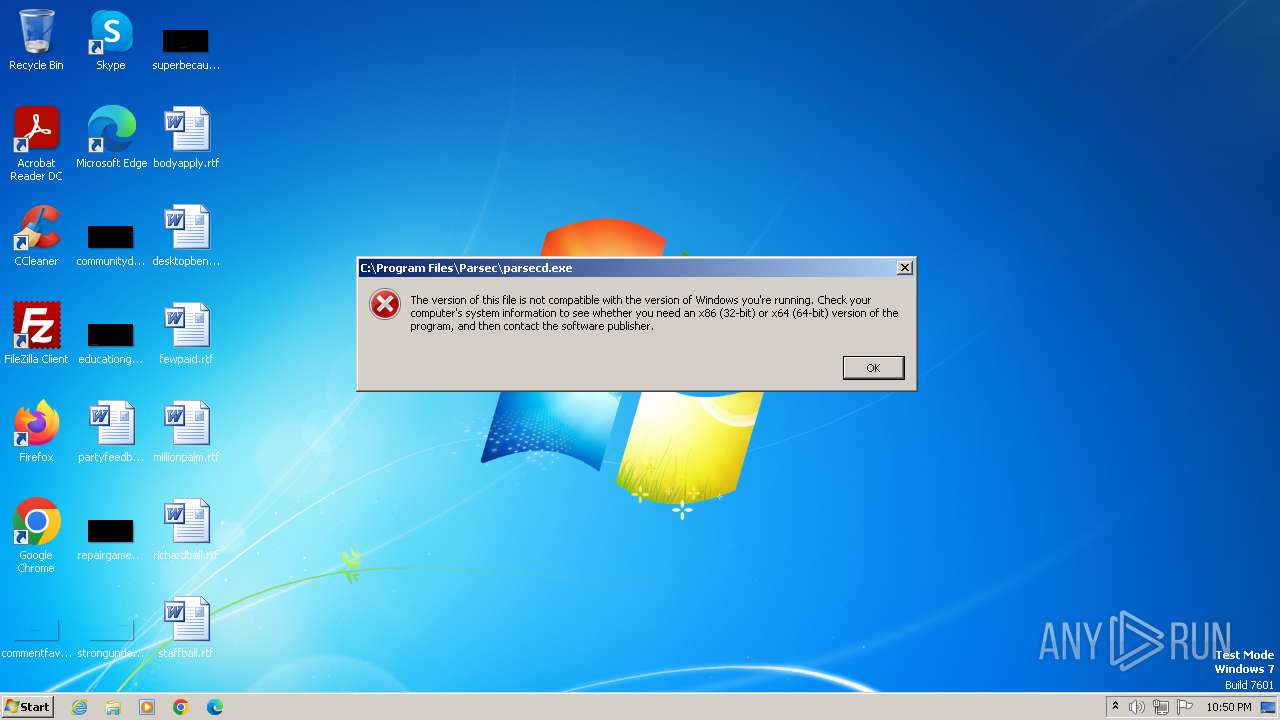
| Verdict: | Malicious activity |
| Analysis date: | October 18, 2023, 21:50:18 |
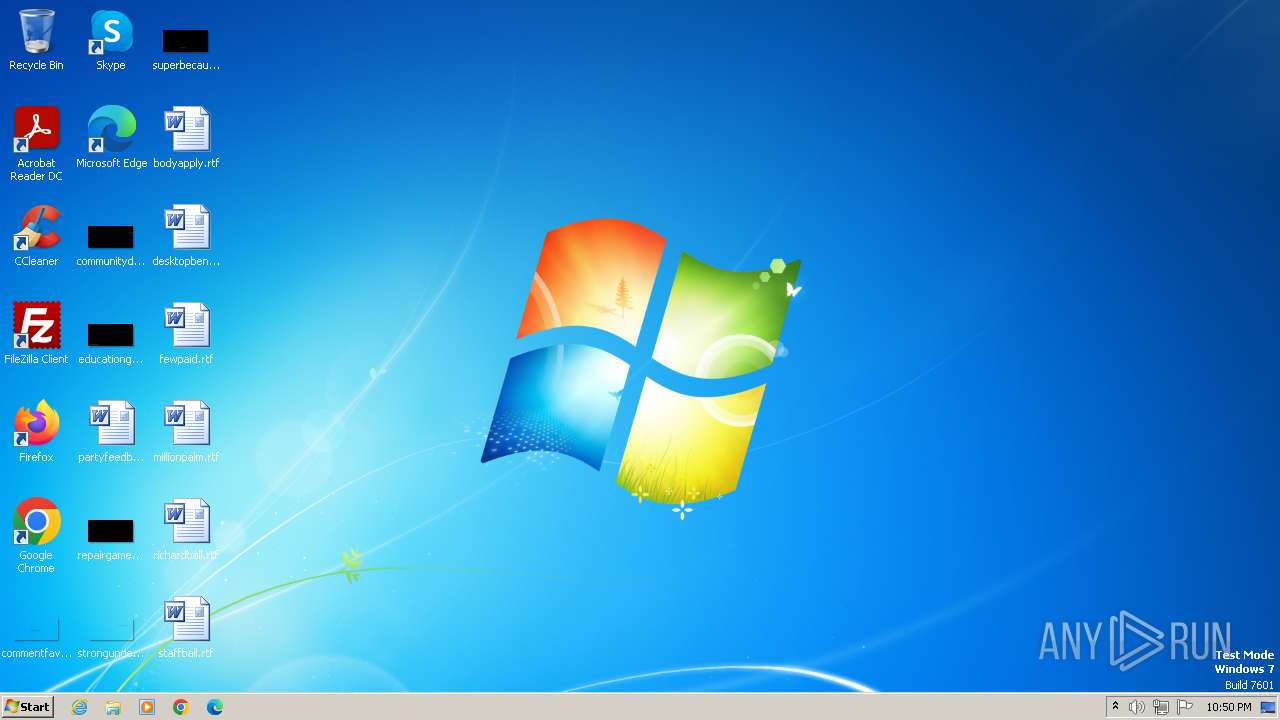
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E3D98621FBC033B7BFE47523F91A37E0 |
| SHA1: | 179C72F991B6610ECD8B6E0D50161A1B30D84F8D |
| SHA256: | E1346B9CC2ED444075655C5DFC484F2B2706ED509CE3C1F732383529EA763334 |
| SSDEEP: | 98304:CUflo/2X77Yy2a4DJXYXe0Uf3rdeKEatfPHcx4L0zu4qobFiKB02j8OM6pjeTmWv:kMwYoH |
MALICIOUS
Loads dropped or rewritten executable
- parsec-windows.exe (PID: 1484)
Drops the executable file immediately after the start
- parsec-windows.exe (PID: 1484)
Uses Task Scheduler to run other applications
- wscript.exe (PID: 2952)
SUSPICIOUS
The process creates files with name similar to system file names
- parsec-windows.exe (PID: 1484)
Malware-specific behavior (creating "System.dll" in Temp)
- parsec-windows.exe (PID: 1484)
Process drops legitimate windows executable
- parsec-windows.exe (PID: 1484)
The process executes VB scripts
- parsec-windows.exe (PID: 1484)
Reads the Internet Settings
- wscript.exe (PID: 2424)
- wscript.exe (PID: 2740)
- wscript.exe (PID: 604)
- wscript.exe (PID: 4076)
- wscript.exe (PID: 1588)
- wscript.exe (PID: 2952)
Starts SC.EXE for service management
- wscript.exe (PID: 2424)
- wscript.exe (PID: 1588)
- wscript.exe (PID: 4076)
Uses TASKKILL.EXE to kill process
- wscript.exe (PID: 2424)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- wscript.exe (PID: 2740)
Uses NETSH.EXE to add a firewall rule or allowed programs
- wscript.exe (PID: 604)
INFO
Checks supported languages
- parsec-windows.exe (PID: 1484)
Reads the computer name
- parsec-windows.exe (PID: 1484)
Create files in a temporary directory
- parsec-windows.exe (PID: 1484)
Creates files in the program directory
- parsec-windows.exe (PID: 1484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 23:57:46+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
71
Monitored processes
19
Malicious processes
1
Suspicious processes
0
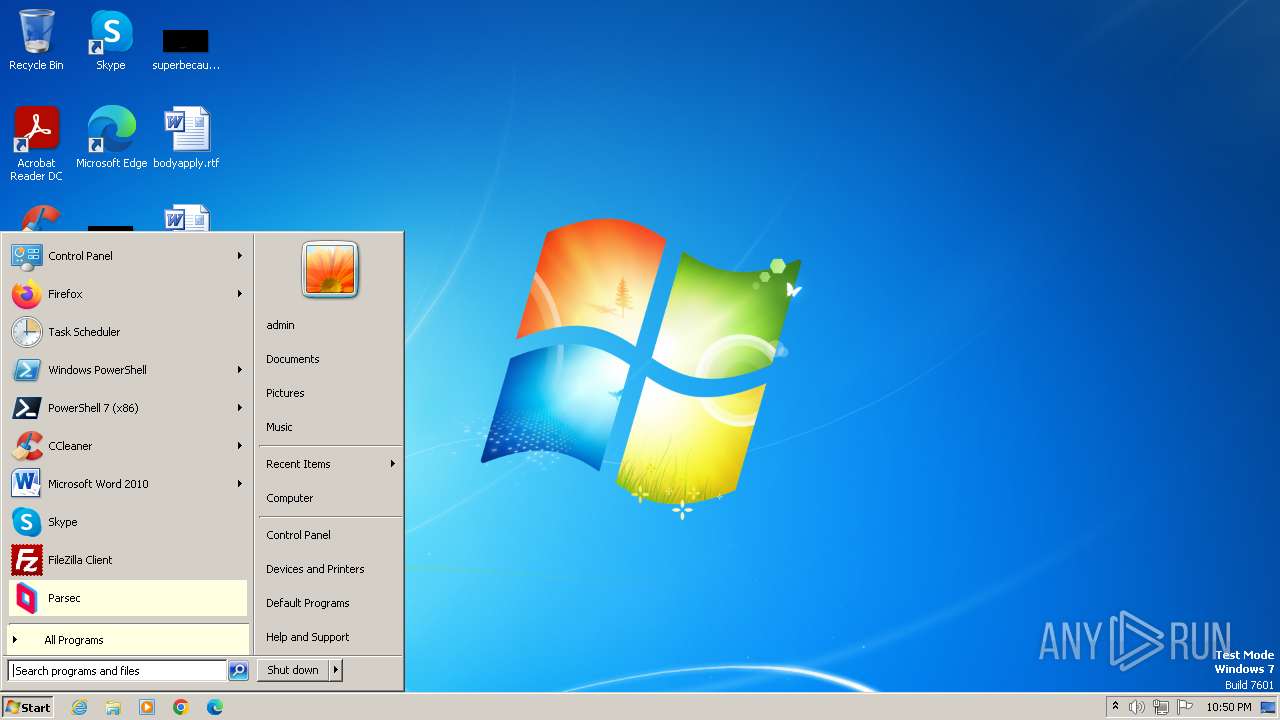
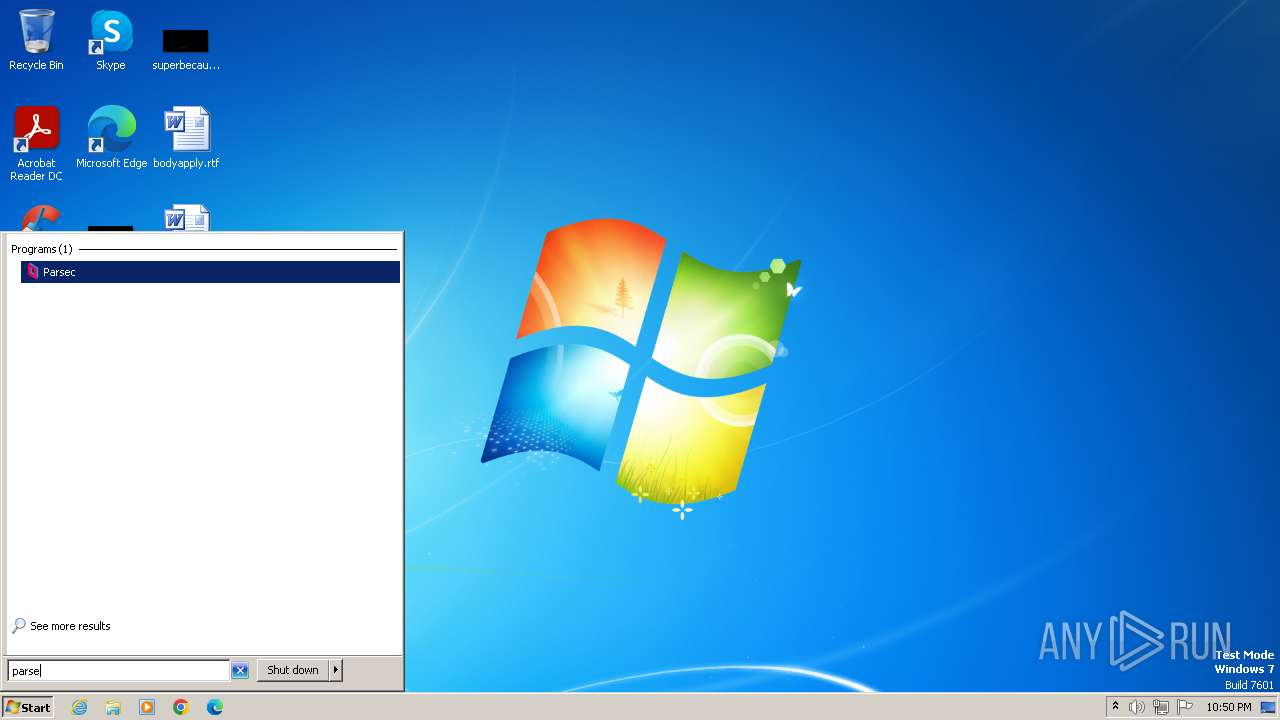
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
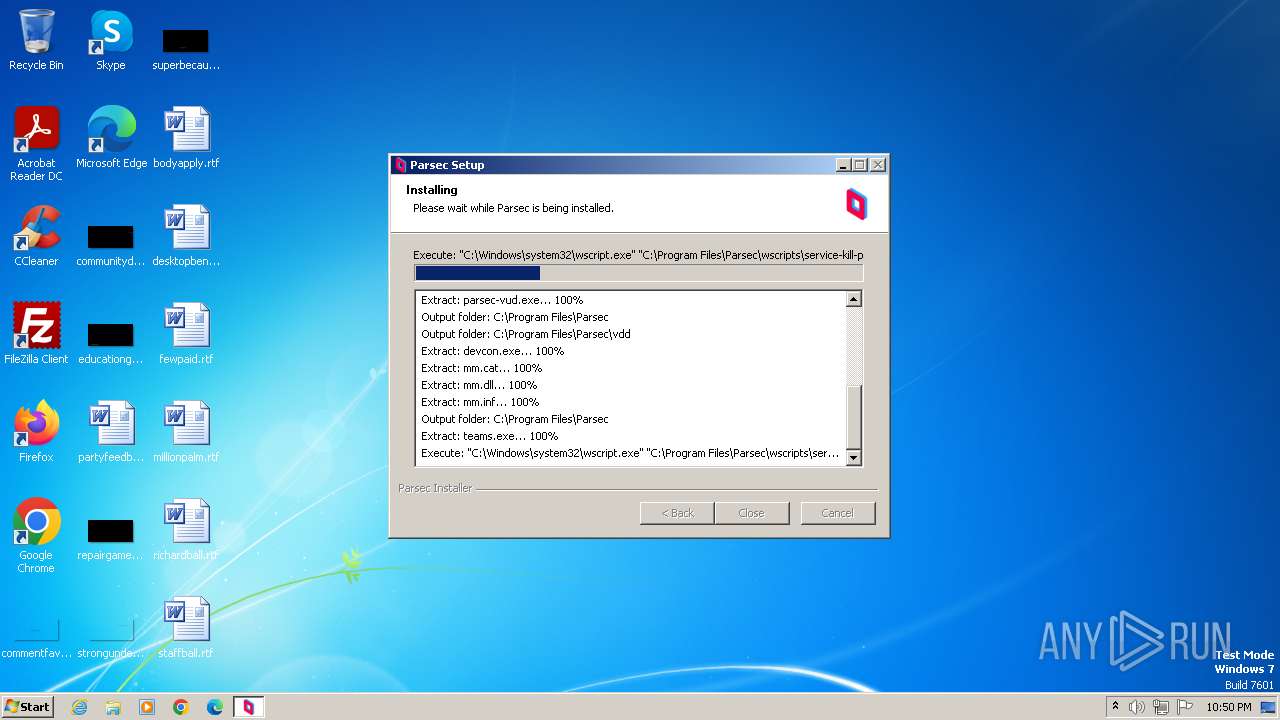
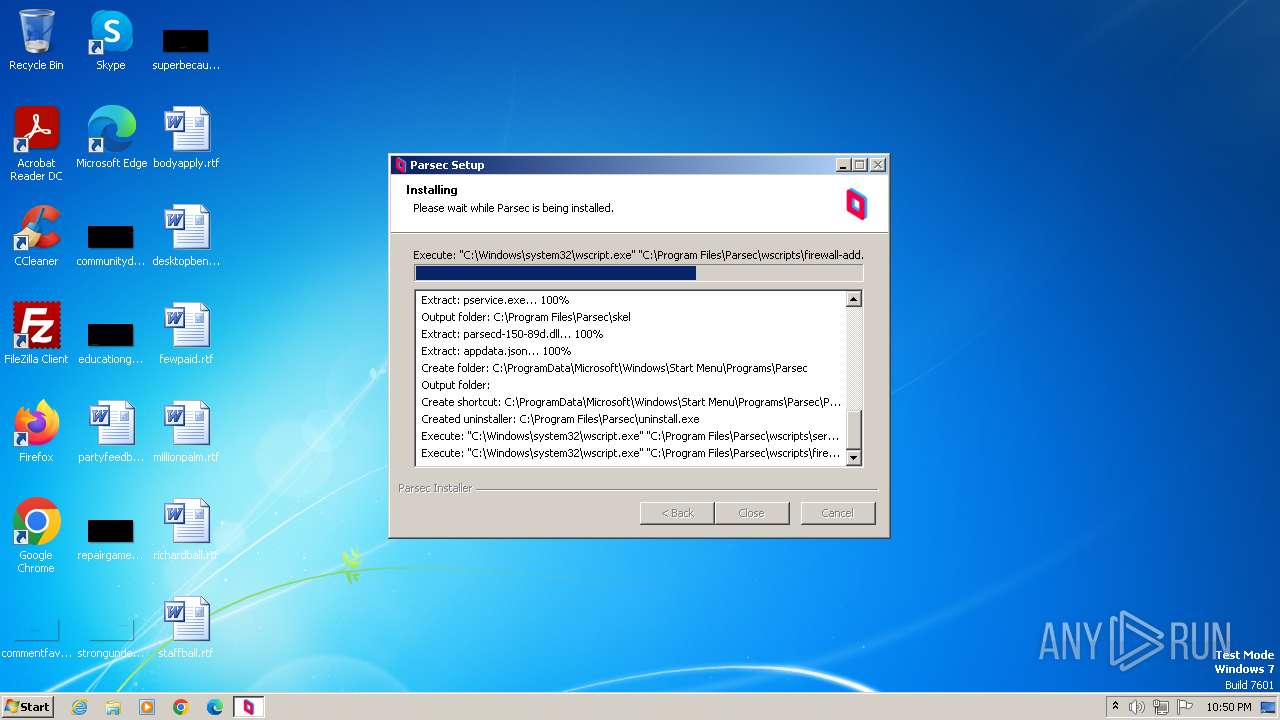
| 604 | "C:\Windows\system32\wscript.exe" "C:\Program Files\Parsec\wscripts\firewall-add.vbs" "C:\Program Files\Parsec\parsecd.exe" | C:\Windows\System32\wscript.exe | — | parsec-windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1044 | "C:\Windows\System32\sc.exe" create Parsec binPath= "\"C:\Program Files\Parsec\pservice.exe\"" start= auto type= interact type= own | C:\Windows\System32\sc.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1408 | "C:\Windows\System32\taskkill.exe" /F /IM parsecd.exe | C:\Windows\System32\taskkill.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Users\admin\AppData\Local\Temp\parsec-windows.exe" | C:\Users\admin\AppData\Local\Temp\parsec-windows.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1588 | "C:\Windows\system32\wscript.exe" "C:\Program Files\Parsec\wscripts\service-remove.vbs" | C:\Windows\System32\wscript.exe | — | parsec-windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2424 | "C:\Windows\system32\wscript.exe" "C:\Program Files\Parsec\wscripts\service-kill-parsec.vbs" | C:\Windows\System32\wscript.exe | — | parsec-windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2600 | "C:\Windows\System32\netsh.exe" advfirewall firewall add rule name=Parsec dir=in action=allow program="C:\Program Files\Parsec\parsecd.exe" enable=yes profile=public,private,domain | C:\Windows\System32\netsh.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | "C:\Windows\System32\schtasks.exe" /delete /tn ParsecTeams /f | C:\Windows\System32\schtasks.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | "C:\Windows\system32\wscript.exe" "C:\Program Files\Parsec\wscripts\firewall-remove.vbs" | C:\Windows\System32\wscript.exe | — | parsec-windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2824 | "C:\Windows\System32\sc.exe" start Parsec | C:\Windows\System32\sc.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 216 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 747
Read events
3 523
Write events
224
Delete events
0
Modification events
| (PID) Process: | (2424) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2424) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2424) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2424) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1588) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1588) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1588) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1588) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2740) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2740) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
11
Suspicious files
5
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1484 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\firewall-remove.vbs | text | |
MD5:5D4D70CDF36FCDAA292DA1DA9133320C | SHA256:75F1DECE4FDA689A907F6D74B513ADB0C1771C1B79EA71160179542C9C4AB2F0 | |||
| 1484 | parsec-windows.exe | C:\Users\admin\AppData\Local\Temp\nsuCB5D.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 1484 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\vdd-install.vbs | text | |
MD5:D94A4CC11C1440FE009058D5248E606A | SHA256:71E283E98F875E4CEB9012E7BA7950D8D65A9D8D72BB916CAA37FD1FE6C405BD | |||
| 1484 | parsec-windows.exe | C:\Users\admin\AppData\Local\Temp\nsuCB5D.tmp\nsDialogs.dll | executable | |
MD5:6C3F8C94D0727894D706940A8A980543 | SHA256:56B96ADD1978B1ABBA286F7F8982B0EFBE007D4A48B3DED6A4D408E01D753FE2 | |||
| 1484 | parsec-windows.exe | C:\Program Files\Parsec\vusb\parsec-vud.exe | executable | |
MD5:563B76A686309756D913FD36D54394D2 | SHA256:400540AE33428D45B901B22F6015575DFB204803342EA974310FB894124789AF | |||
| 1484 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\legacy-cleanup.vbs | text | |
MD5:C78520C3162C1962F3164714B37EB4D0 | SHA256:DEA38BD553ABE93C689DE42D0220ADD18F9BE3E3D2FA53F97EB8649F586DF4F3 | |||
| 1484 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\service-install.vbs | text | |
MD5:971E2A344A6E17347A81EEB21ADA7BA7 | SHA256:01F62A12DE3307B375DFF3EBCD6961D76FFCBC24F70682C7875655A811CE76A1 | |||
| 1484 | parsec-windows.exe | C:\Program Files\Parsec\vdd\devcon.exe | executable | |
MD5:A9B2B49CC4457AD9D63B10C4FD6C9748 | SHA256:270836795917367E22D843DF92A535004143515E9EA9BBDEB056A27C82AD6DAA | |||
| 1484 | parsec-windows.exe | C:\Program Files\Parsec\skel\appdata.json | binary | |
MD5:6ABD040C6D51BC71741D6FA1881BCCAB | SHA256:E73CF0DC49110895F1709BB9A13168D0485FFEC68E421F75B486509931BA272C | |||
| 1484 | parsec-windows.exe | C:\Program Files\Parsec\vdd\mm.cat | binary | |
MD5:E33BF4612C58C029678D51C37CE15BB1 | SHA256:5852D0C23EC74A2F5594BC498525E7BEB29CE25BD7ADAC4906DDBDCBF539B1F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |