| URL: | https://ya.ru/ |
| Full analysis: | https://app.any.run/tasks/bef7fe90-eb1a-45cc-9f56-6249ab4a63fa |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2019, 14:33:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6056C0E911424CF9A9AEEFC8B3408D85 |
| SHA1: | E233761D91FD949E7FB41F57BC421D2DA724AA62 |
| SHA256: | E12F5F6CA7E5F8A0C0EF190A2631B8CECDDB69385A37766046A325A5CF982F2B |
| SSDEEP: | 3:N8zfn:2bn |
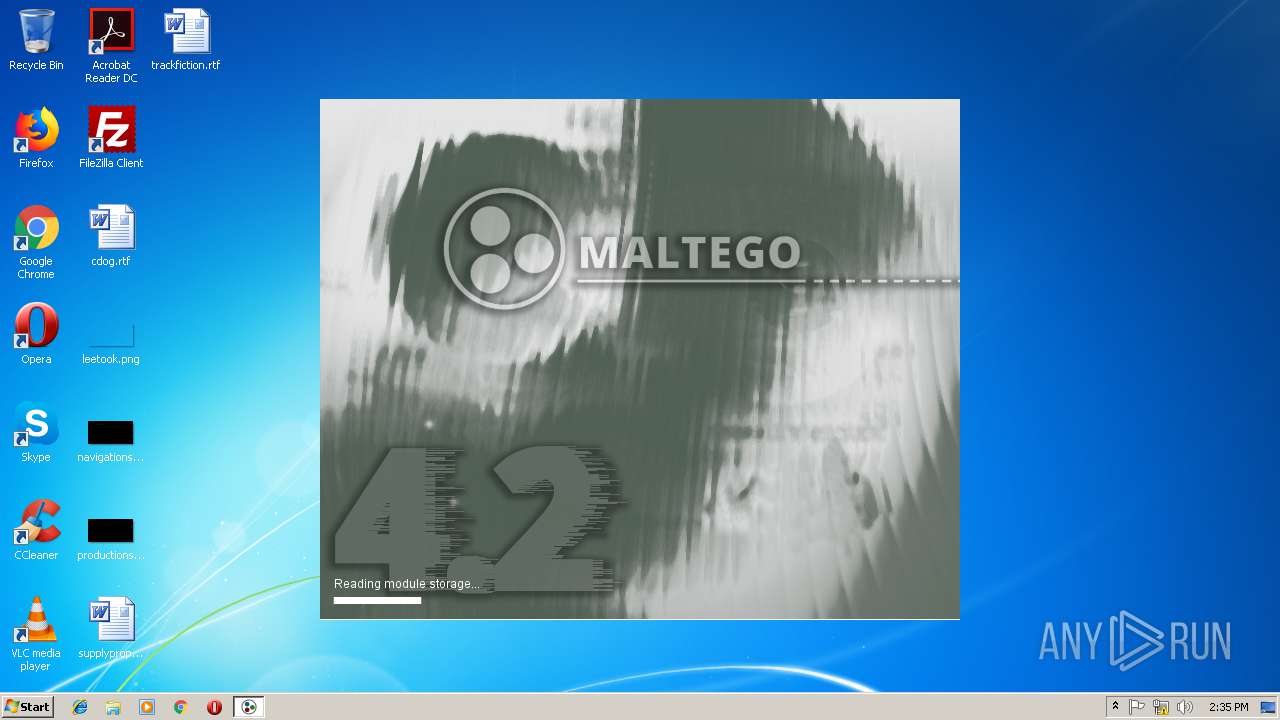
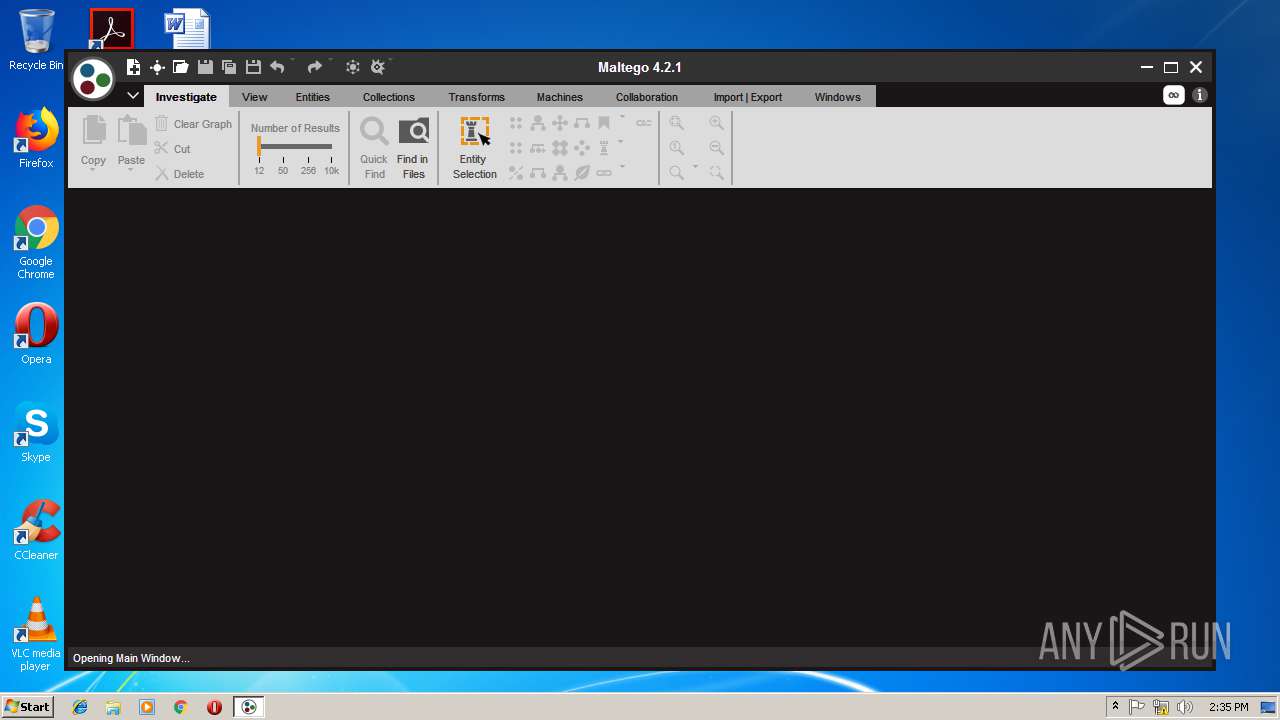
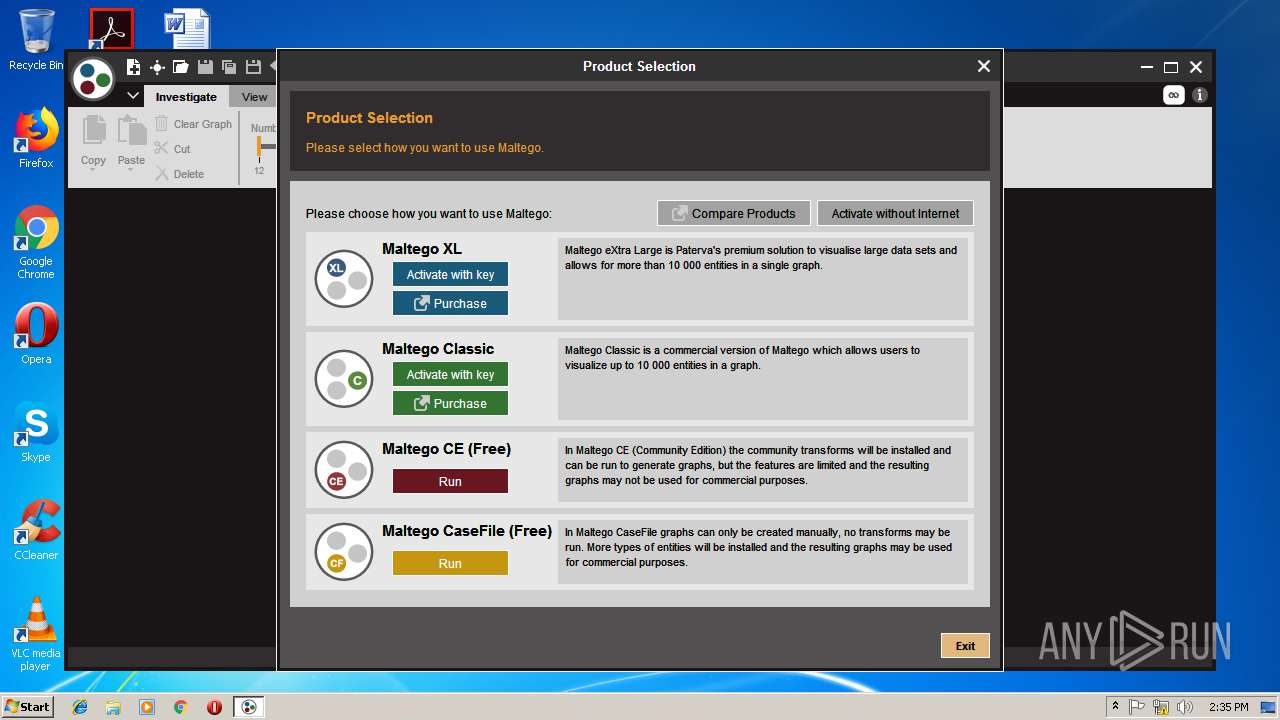
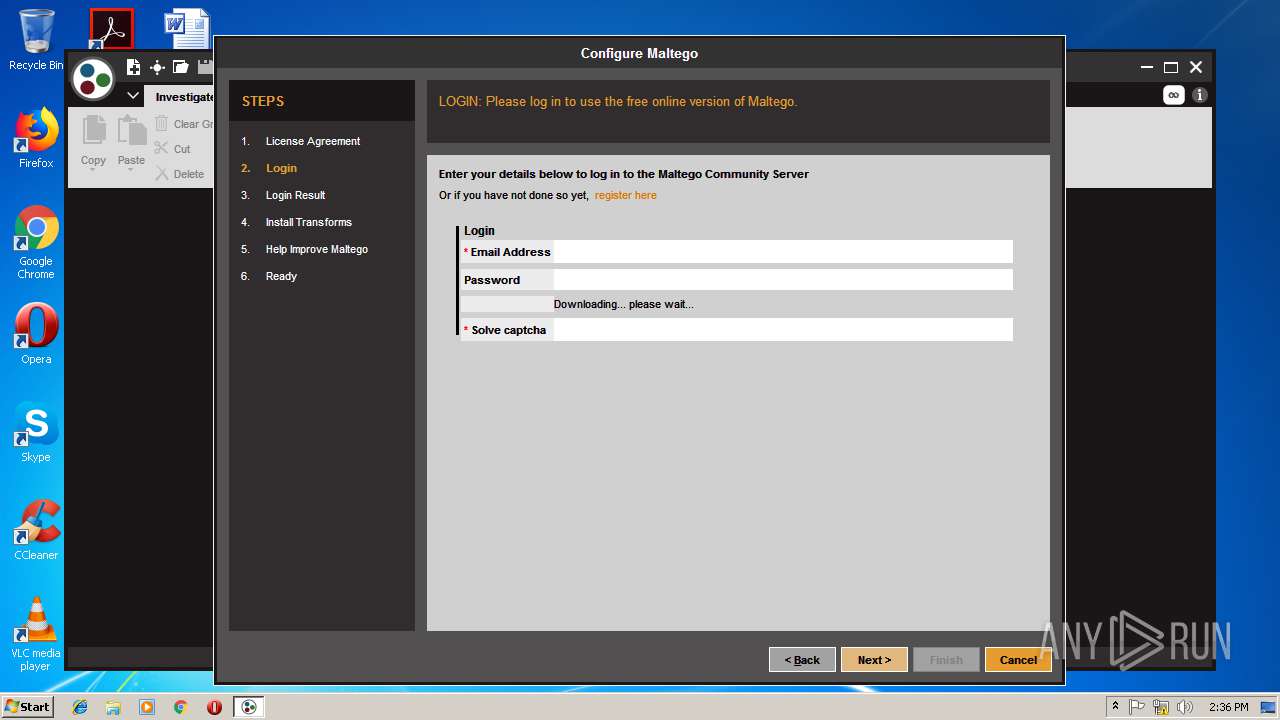
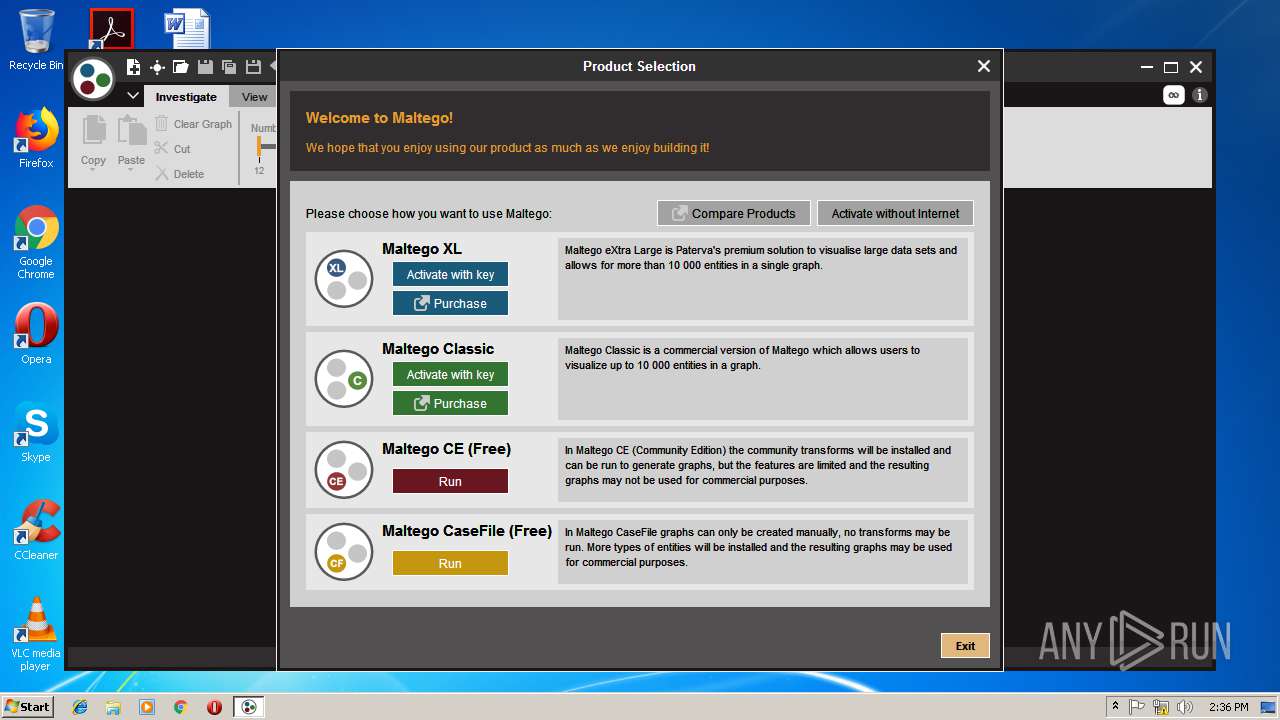
MALICIOUS
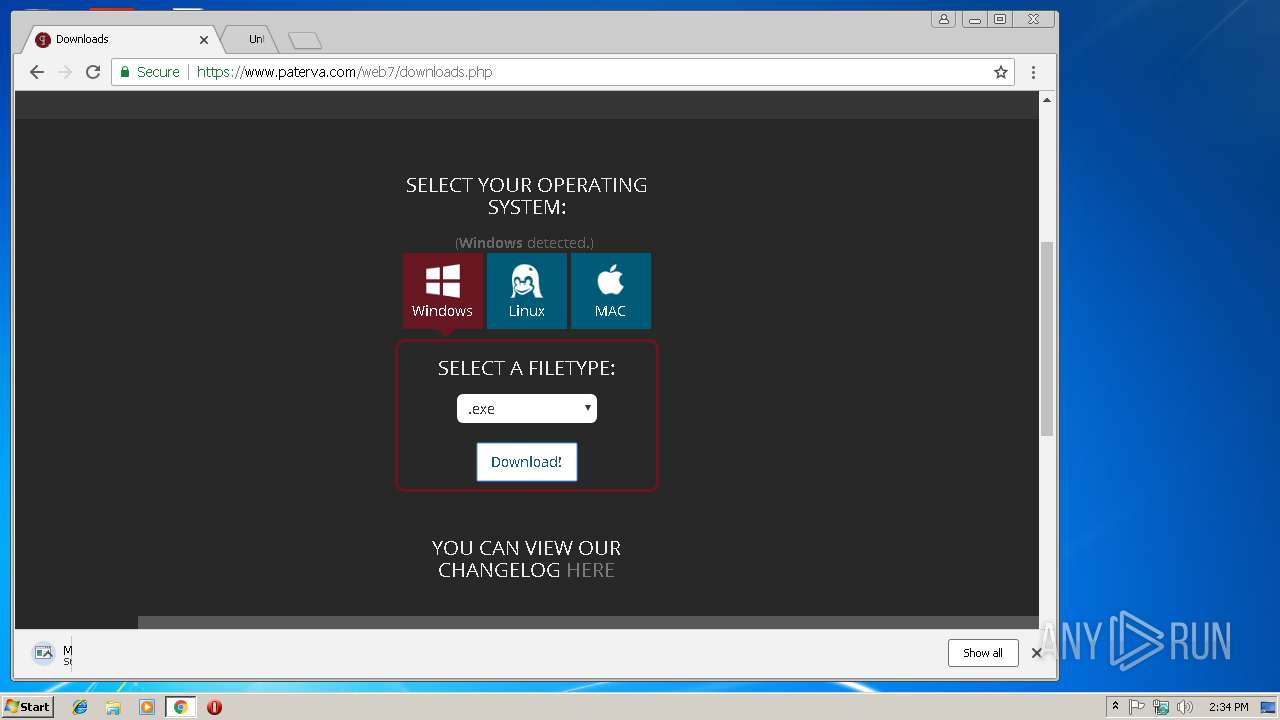
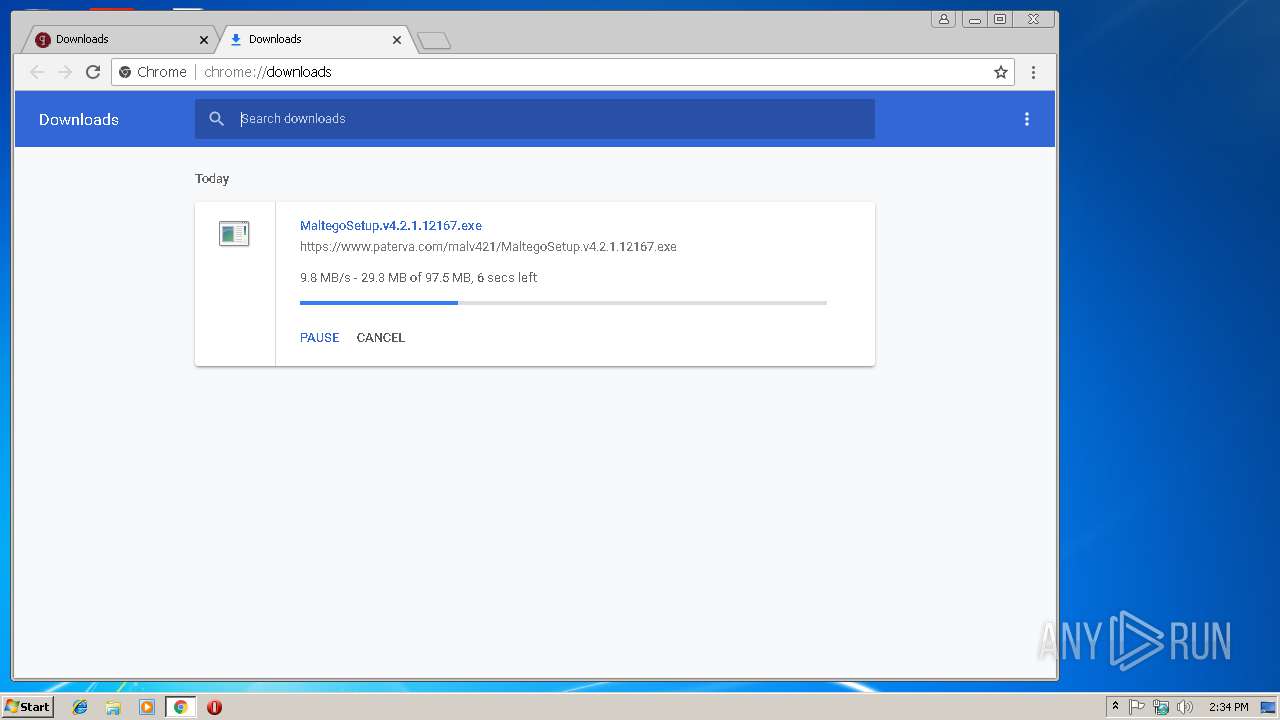
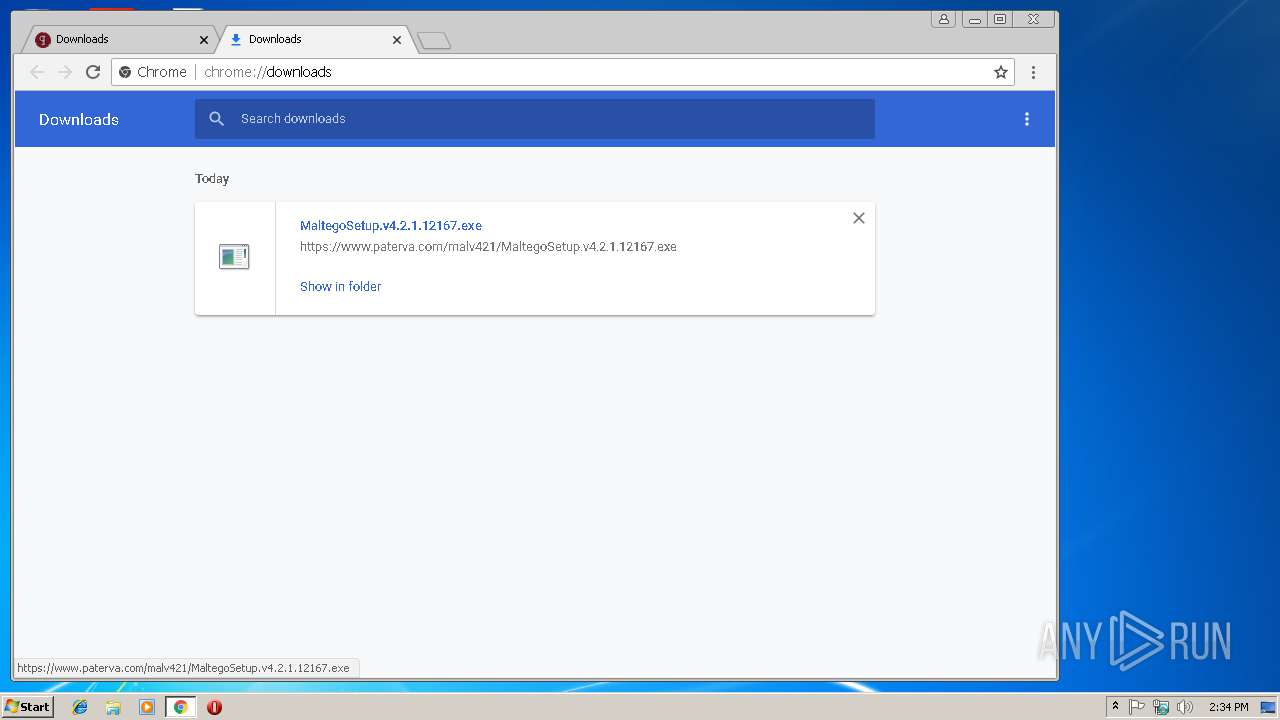
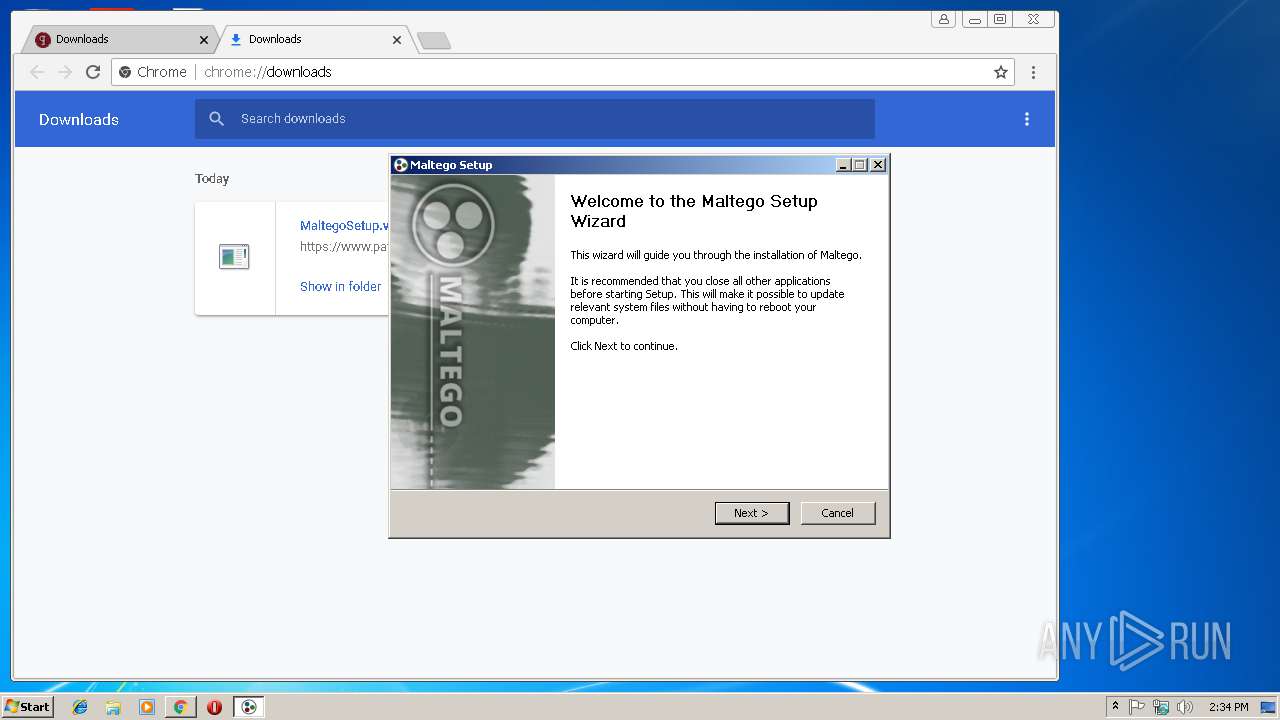
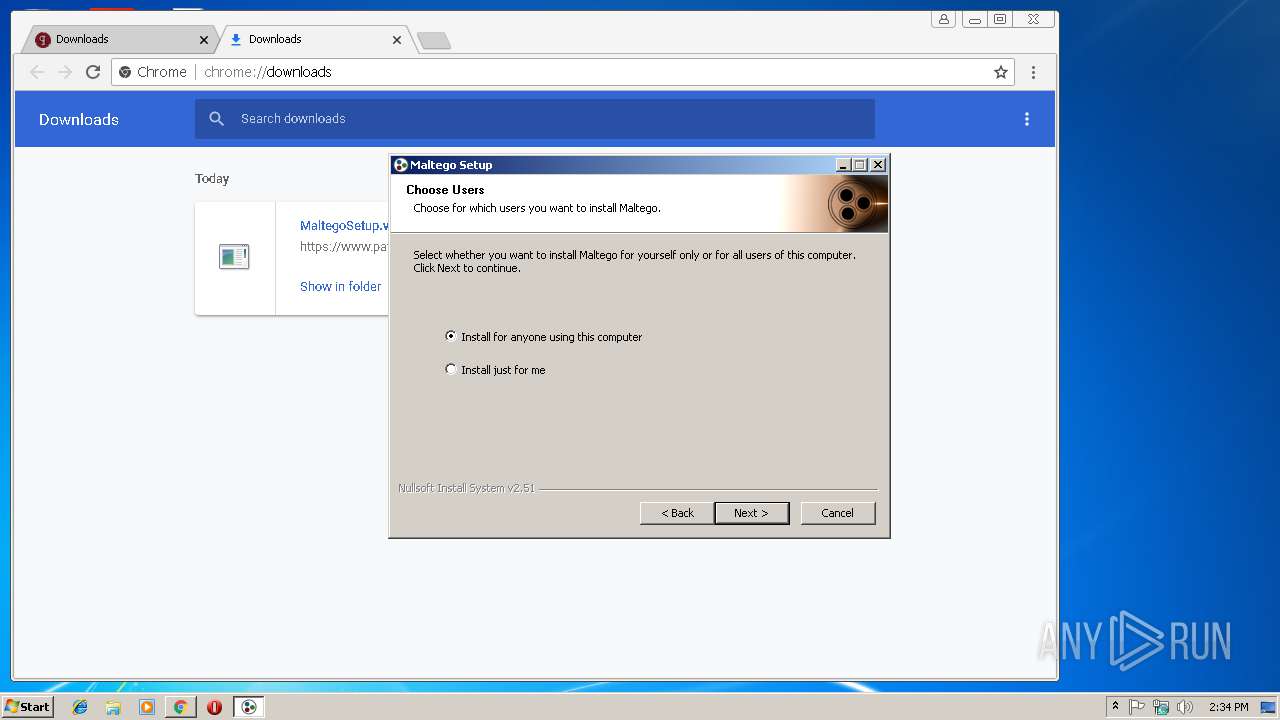
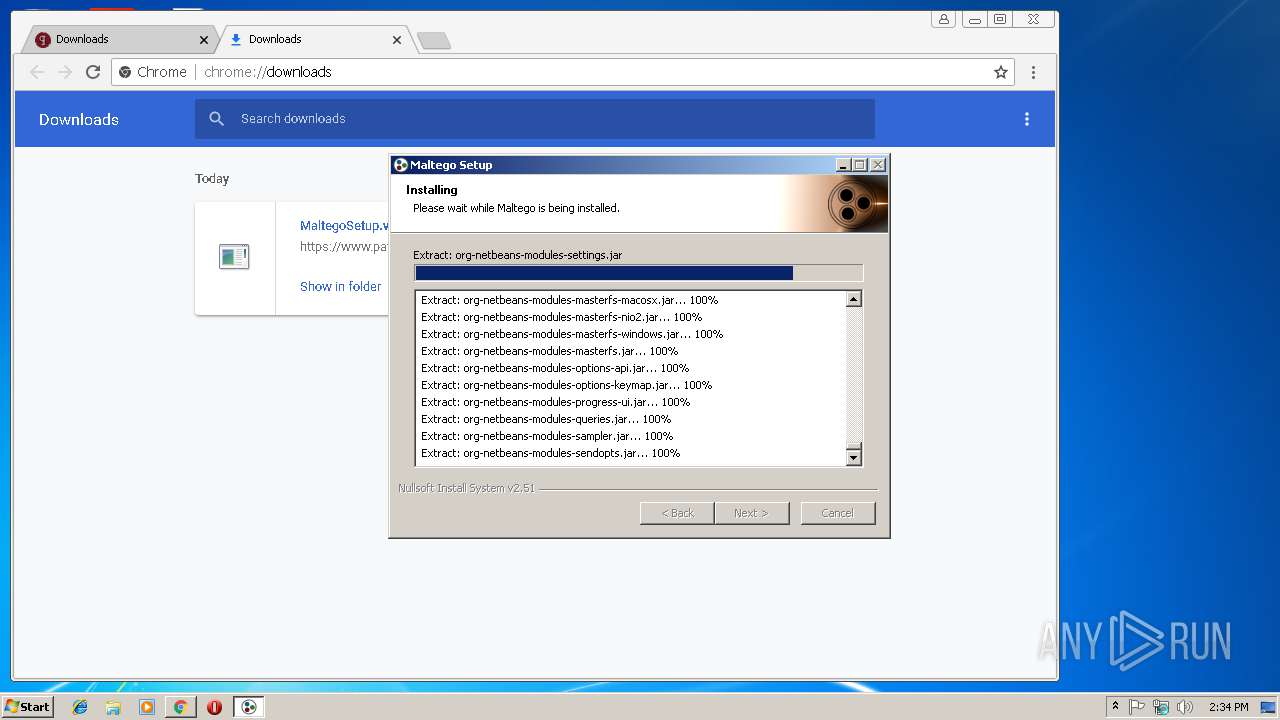
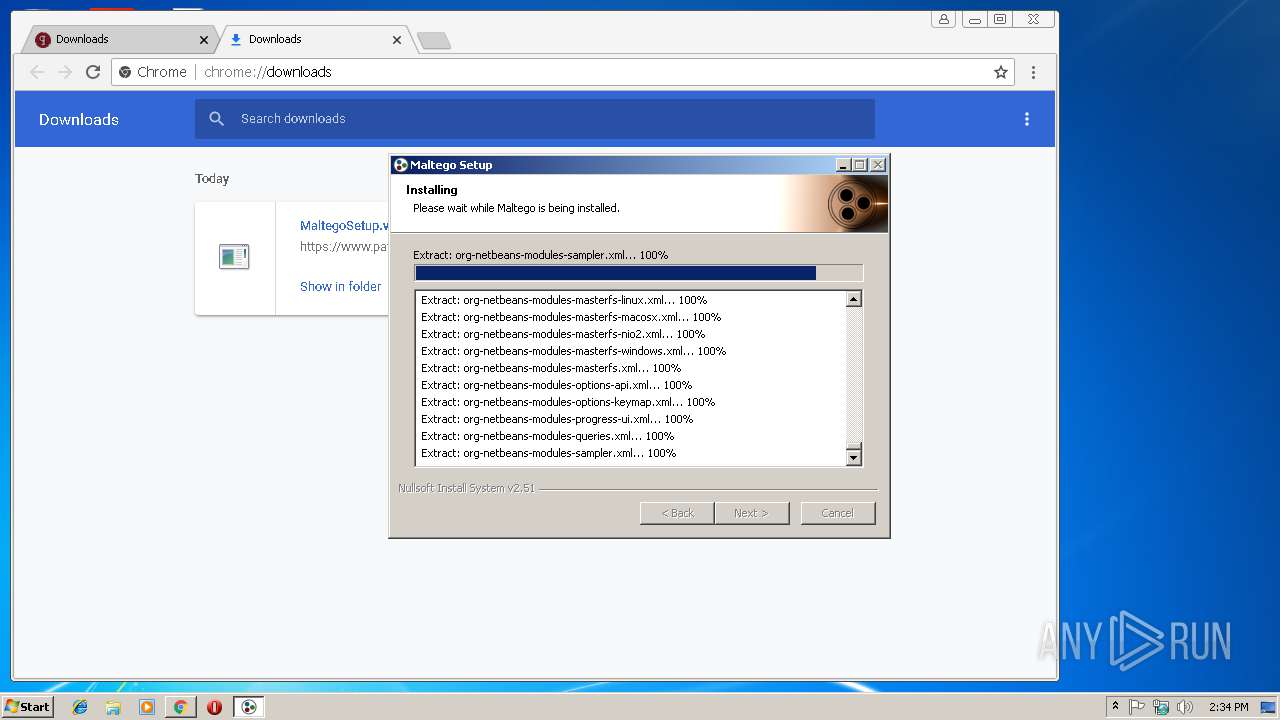
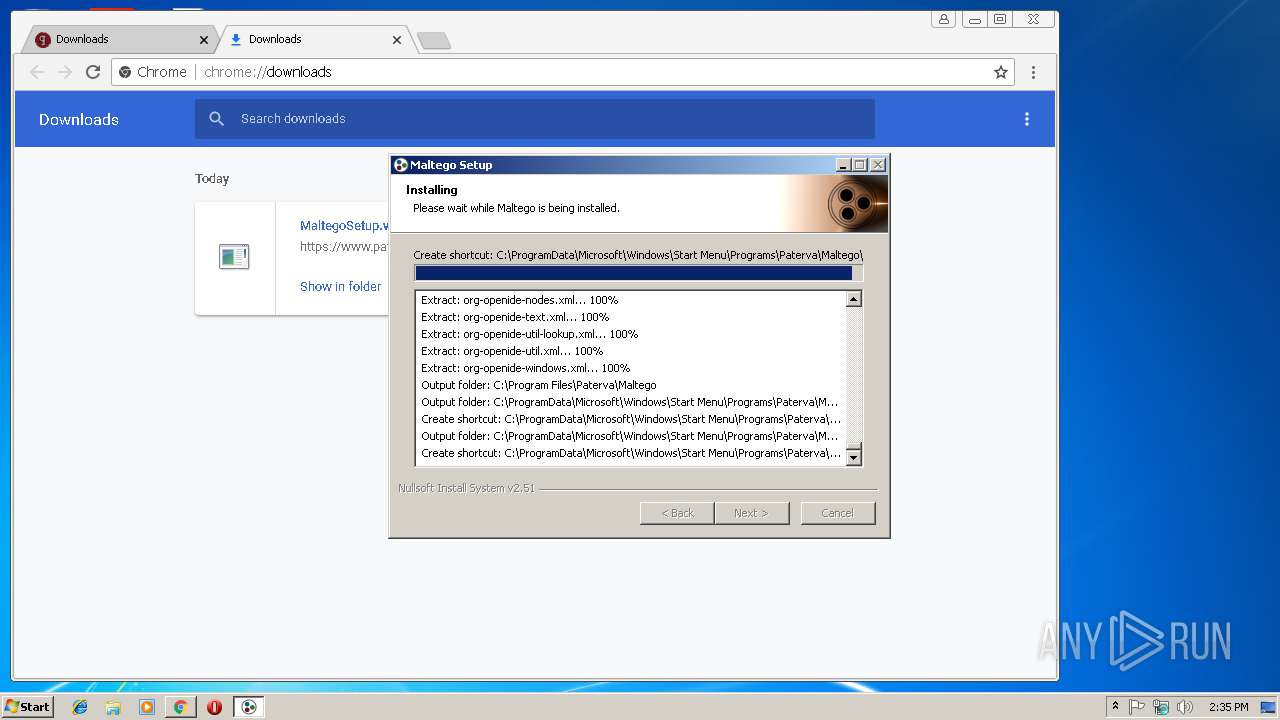
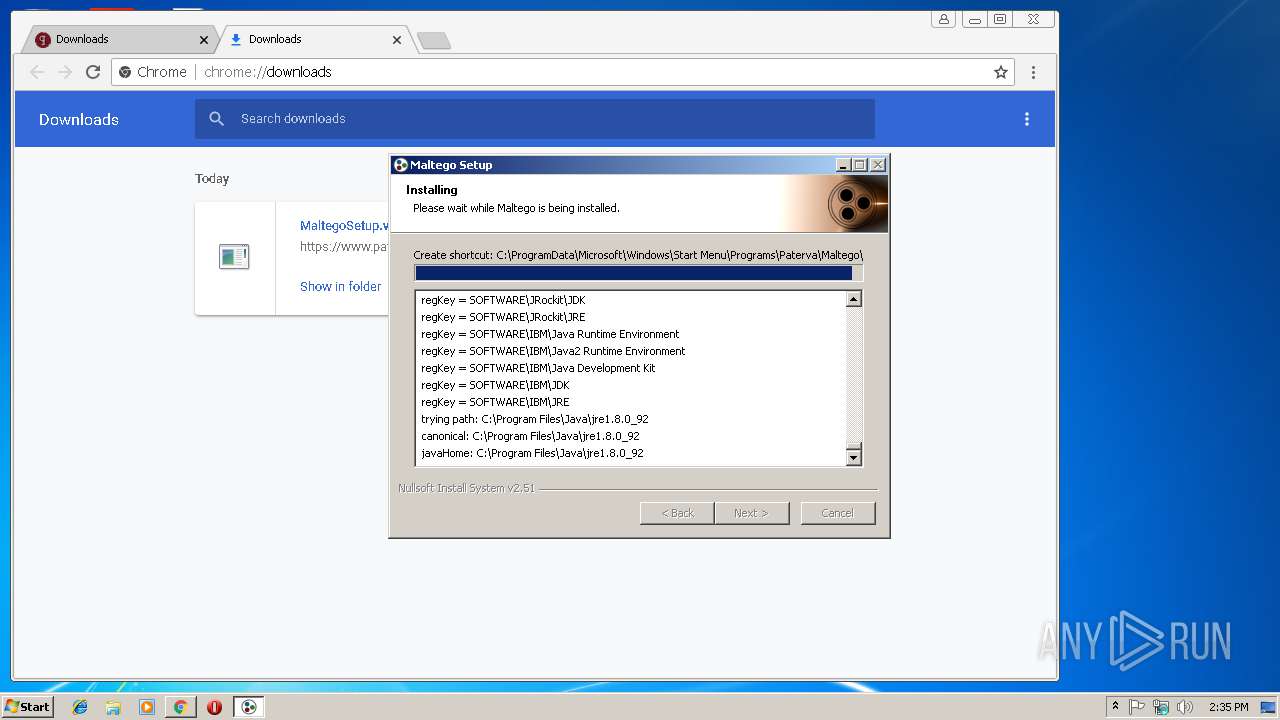
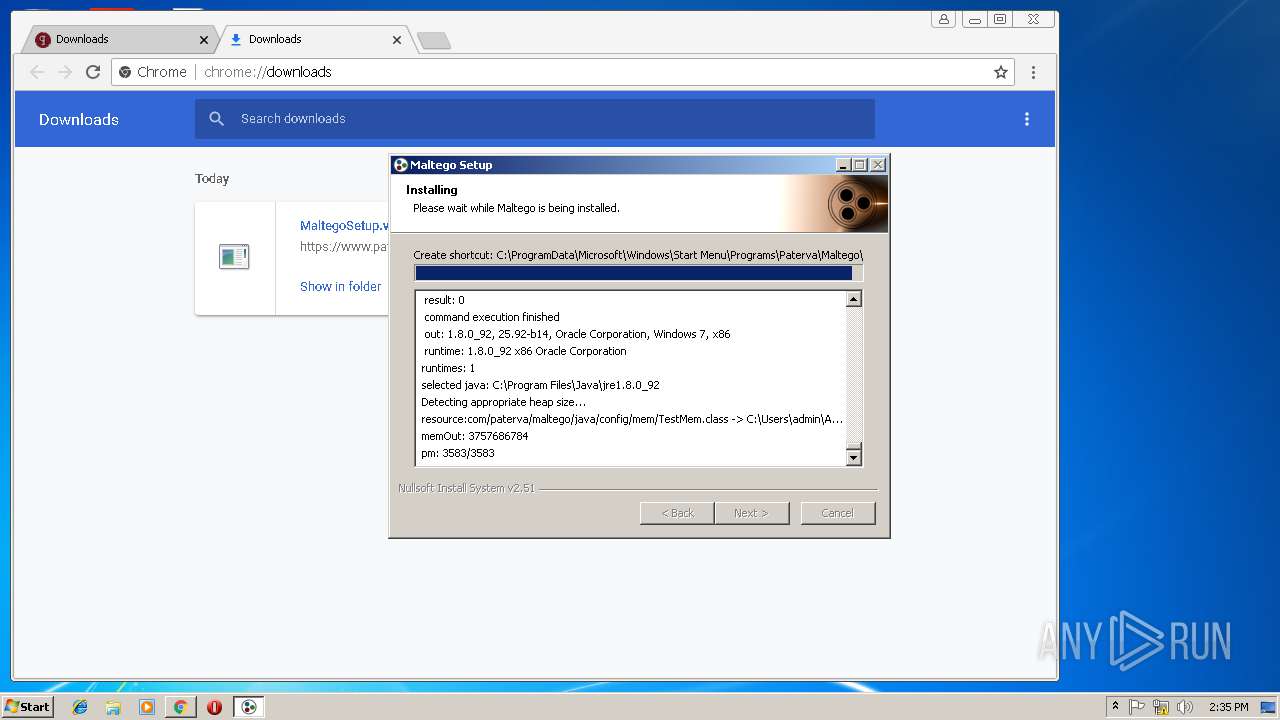
Loads dropped or rewritten executable
- MaltegoSetup.v4.2.1.12167.exe (PID: 3148)
- maltego.exe (PID: 3780)
Application was dropped or rewritten from another process
- ns4B64.tmp (PID: 2672)
- MaltegoSetup.v4.2.1.12167.exe (PID: 3380)
- MaltegoSetup.v4.2.1.12167.exe (PID: 3148)
- maltego.exe (PID: 3780)
SUSPICIOUS
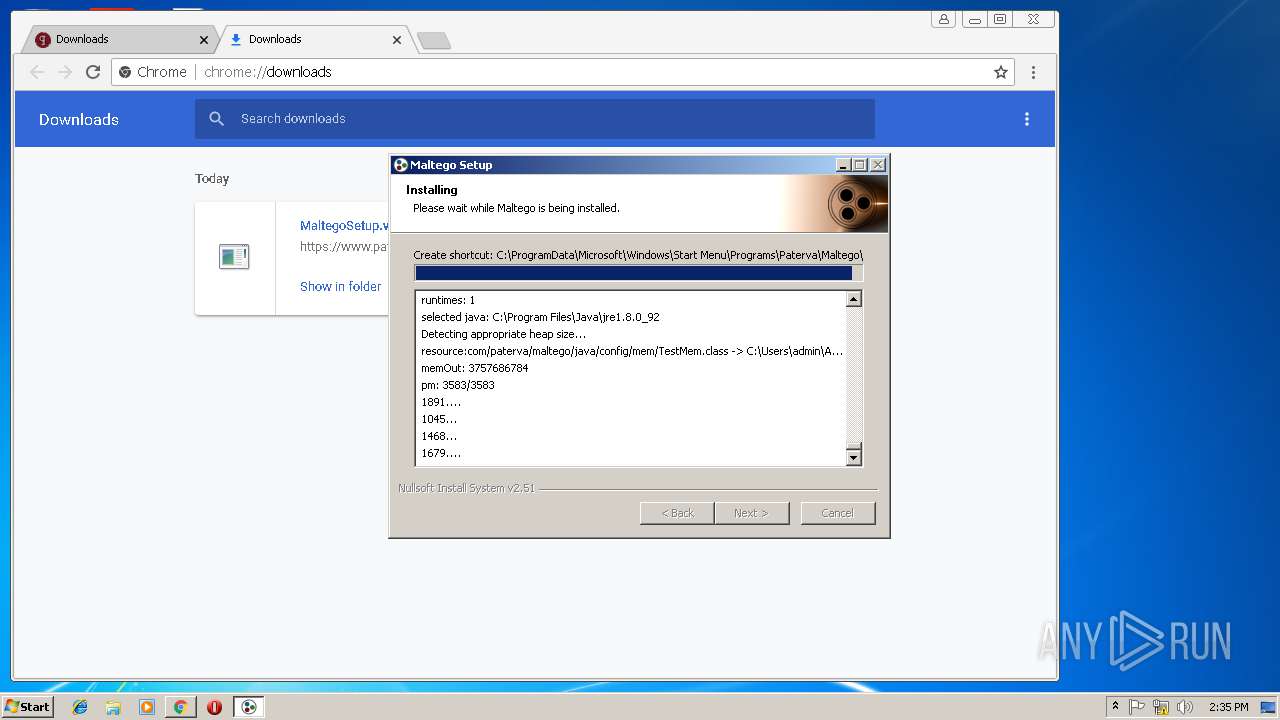
Executable content was dropped or overwritten
- MaltegoSetup.v4.2.1.12167.exe (PID: 3148)
Modifies the open verb of a shell class
- MaltegoSetup.v4.2.1.12167.exe (PID: 3148)
Starts application with an unusual extension
- MaltegoSetup.v4.2.1.12167.exe (PID: 3148)
Creates files in the user directory
- java.exe (PID: 3952)
- maltego.exe (PID: 3780)
Starts itself from another location
- java.exe (PID: 3952)
Executes JAVA applets
- java.exe (PID: 3952)
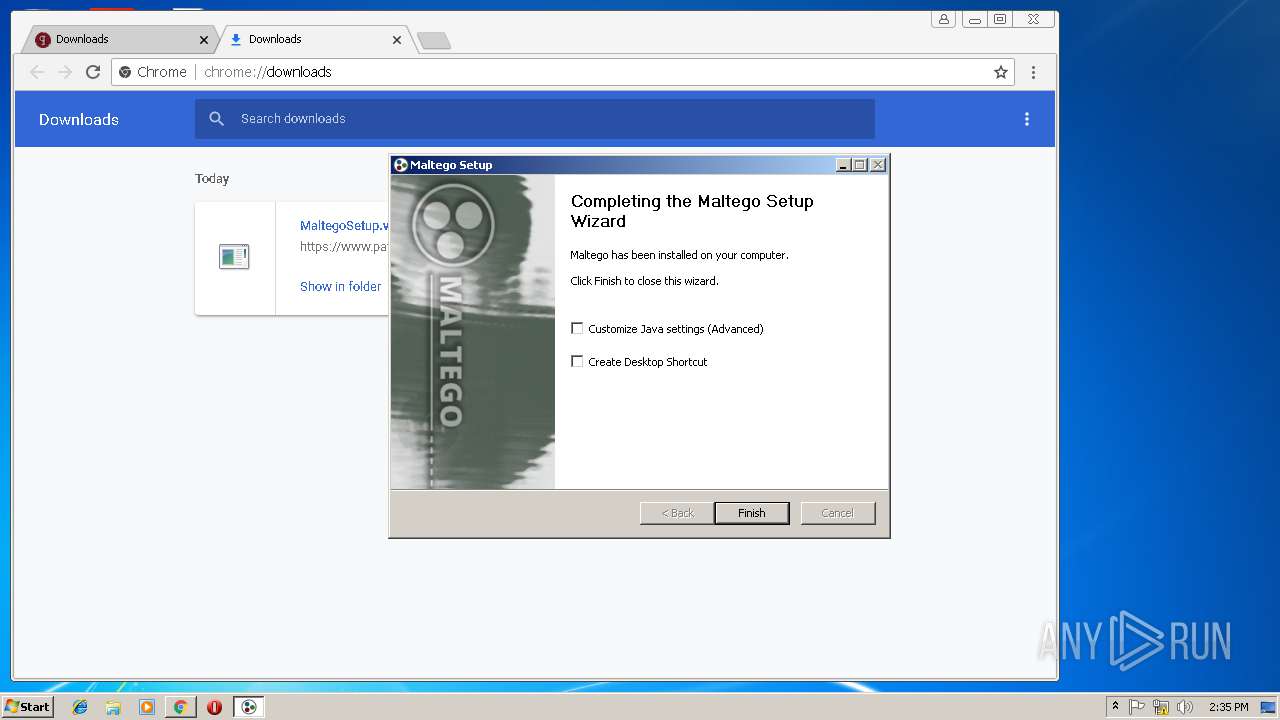
Creates a software uninstall entry
- MaltegoSetup.v4.2.1.12167.exe (PID: 3148)
Creates files in the program directory
- MaltegoSetup.v4.2.1.12167.exe (PID: 3148)
INFO
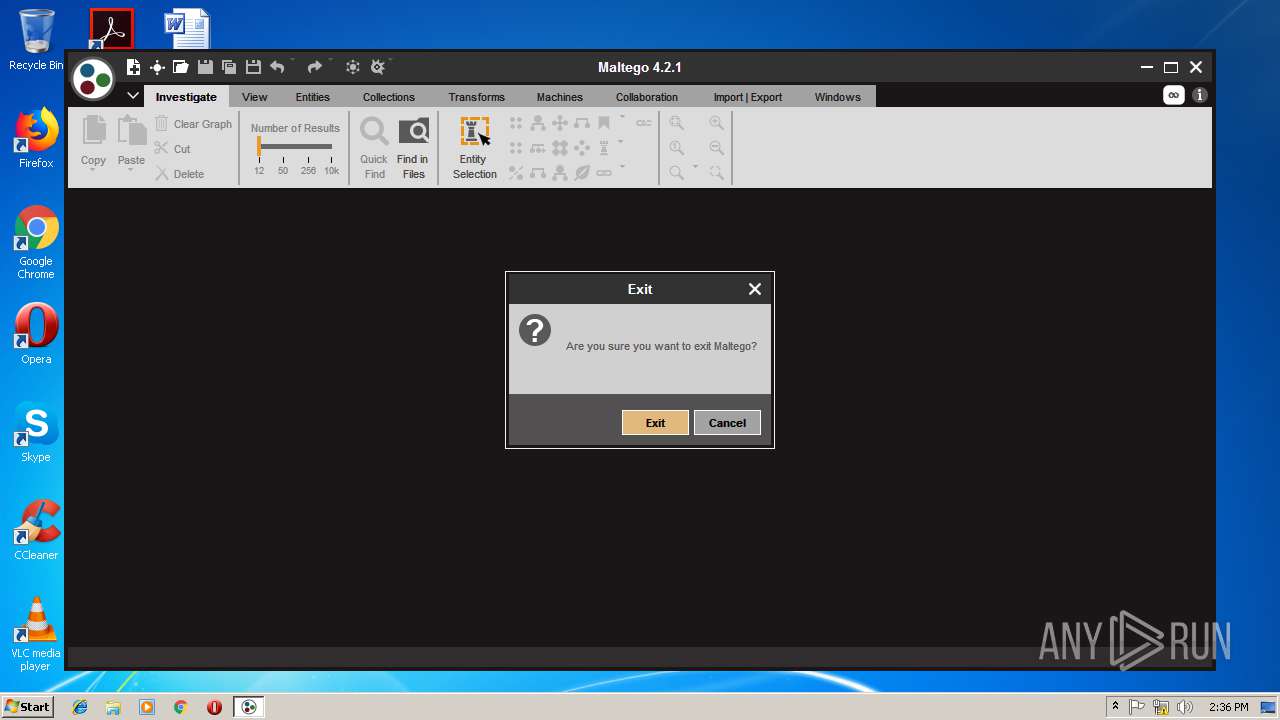
Application launched itself
- iexplore.exe (PID: 3376)
- chrome.exe (PID: 2316)
Changes internet zones settings
- iexplore.exe (PID: 3376)
Creates files in the user directory
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 3688)
Reads settings of System Certificates
- chrome.exe (PID: 2316)
Reads Internet Cache Settings
- iexplore.exe (PID: 3688)
- chrome.exe (PID: 2316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
32
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,10223456036928154460,1778625805881381990,131072 --enable-features=PasswordImport --service-pipe-token=9F4CBBE52CFA12922550556C8DDD0371 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9F4CBBE52CFA12922550556C8DDD0371 --renderer-client-id=3 --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,10223456036928154460,1778625805881381990,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2C43892D6E5FDFC68172E73423BD5AD6 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2C43892D6E5FDFC68172E73423BD5AD6 --renderer-client-id=6 --mojo-platform-channel-handle=2796 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=888,10223456036928154460,1778625805881381990,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=5E1002EC39C2EDF819785055D719BD0C --mojo-platform-channel-handle=864 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\AppData\Local\Temp\nsi10CB.tmp\ns4B64.tmp" java -jar "C:\Program Files\Paterva\Maltego\v4.2.1\maltego-ui\modules\ext\Java_Config_App.jar" -nogui | C:\Users\admin\AppData\Local\Temp\nsi10CB.tmp\ns4B64.tmp | — | MaltegoSetup.v4.2.1.12167.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -Xmx1665m -classpath C:\Users\admin\AppData\Local\Temp\temp75271765011126502261726776535193 TestJDK | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | java.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,10223456036928154460,1778625805881381990,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E804B07011ACB4979BA58B21C83E6C1F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E804B07011ACB4979BA58B21C83E6C1F --renderer-client-id=13 --mojo-platform-channel-handle=2336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -classpath C:\Users\admin\AppData\Local\Temp\temp75271765011126502261726776535193 TestJDK | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | java.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,10223456036928154460,1778625805881381990,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F379C7CC30079D39AF2BB1D988F7B92F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F379C7CC30079D39AF2BB1D988F7B92F --renderer-client-id=9 --mojo-platform-channel-handle=3964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -Xmx1573m -classpath C:\Users\admin\AppData\Local\Temp\temp75271765011126502261726776535193 TestJDK | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | java.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
1 603
Read events
1 468
Write events
131
Delete events
4
Modification events
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {69CE308F-390A-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200010019000E0022000B00F601 | |||
Executable files
337
Suspicious files
259
Text files
611
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4879351d-c451-4921-96b3-0fed3d2d514e.tmp | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\01eccaec-8810-411e-87fb-c0930e29d6a9.tmp | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model | — | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8C945F28AF5520EF.TMP | — | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{4BBB6F4B-AC5C-11E8-969E-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9A02E4FF03C88C78.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
44
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
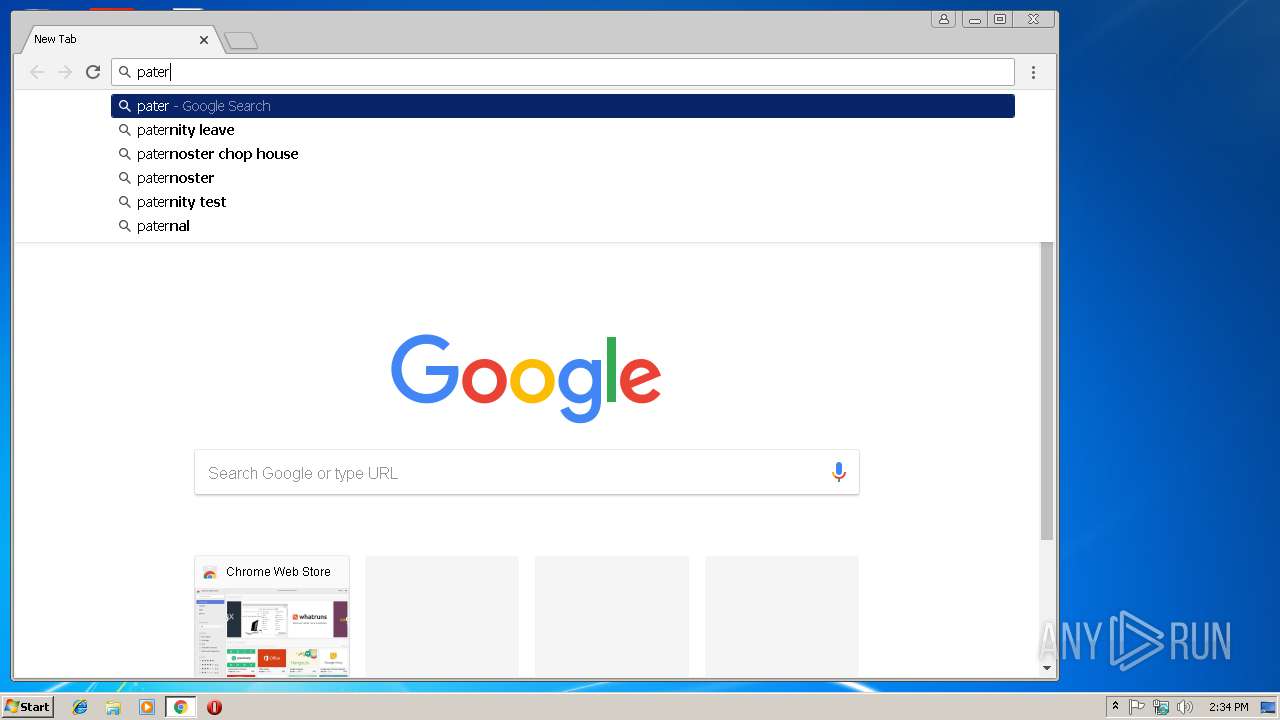
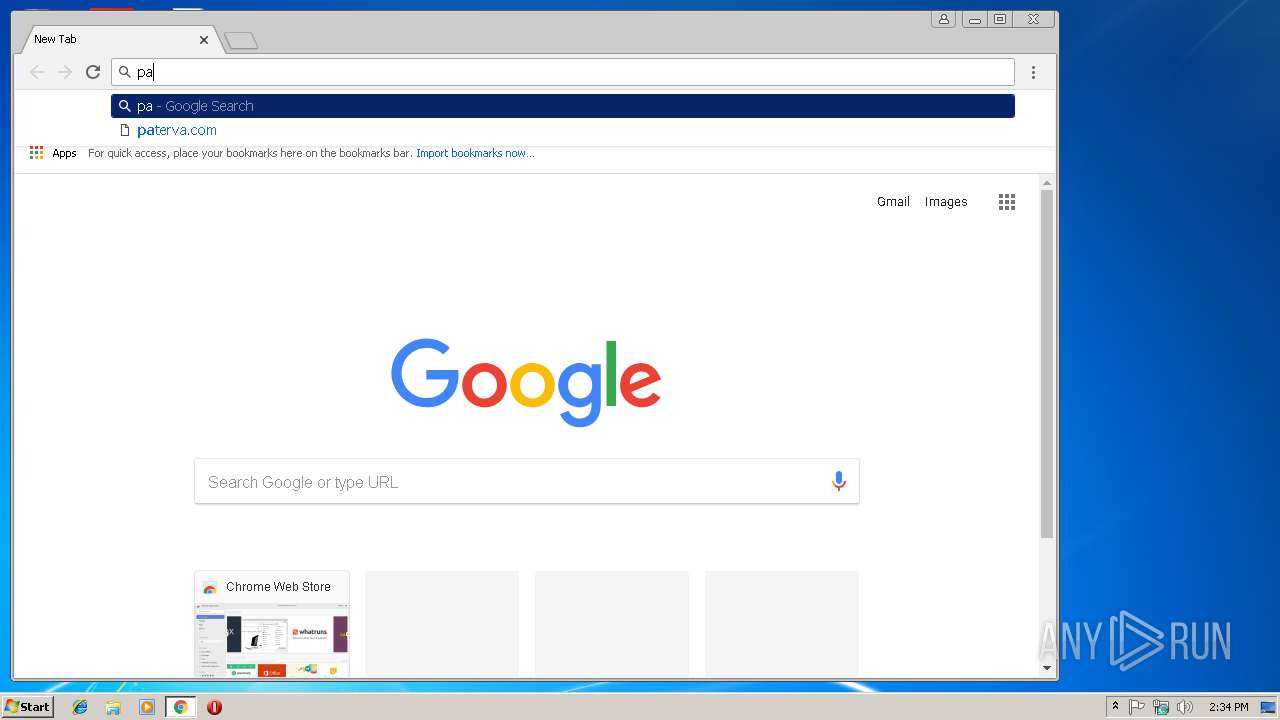
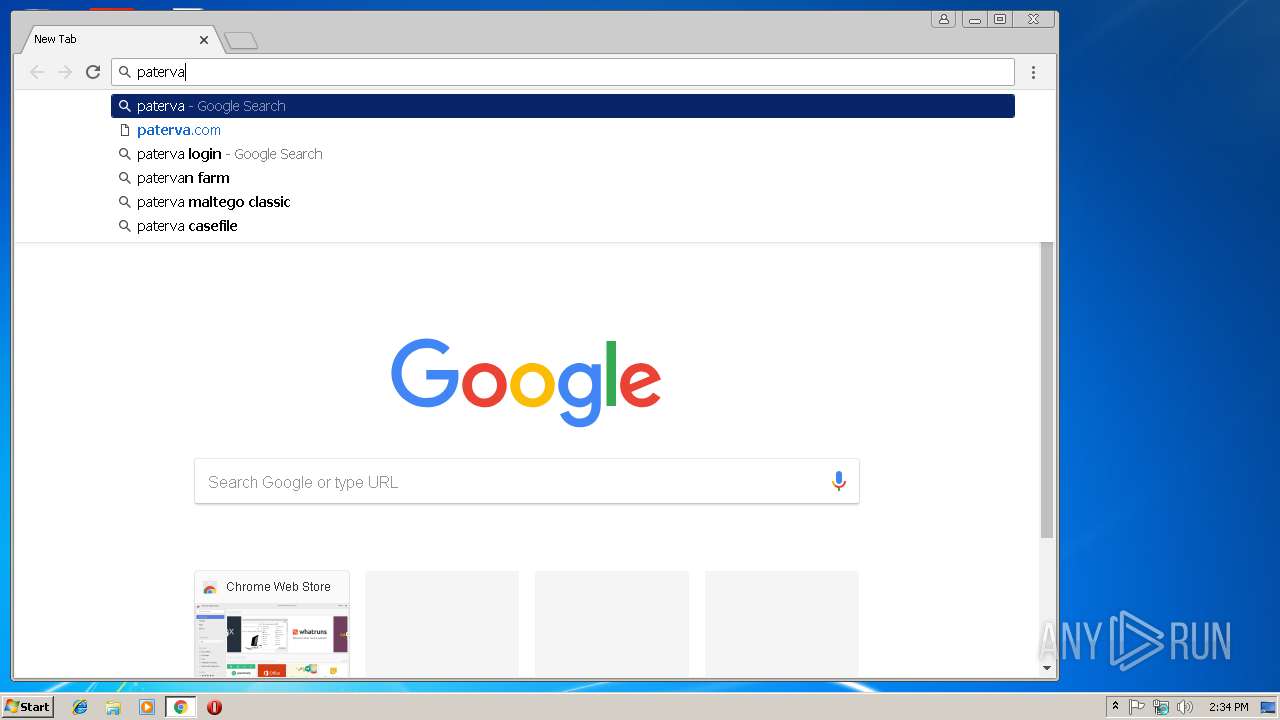
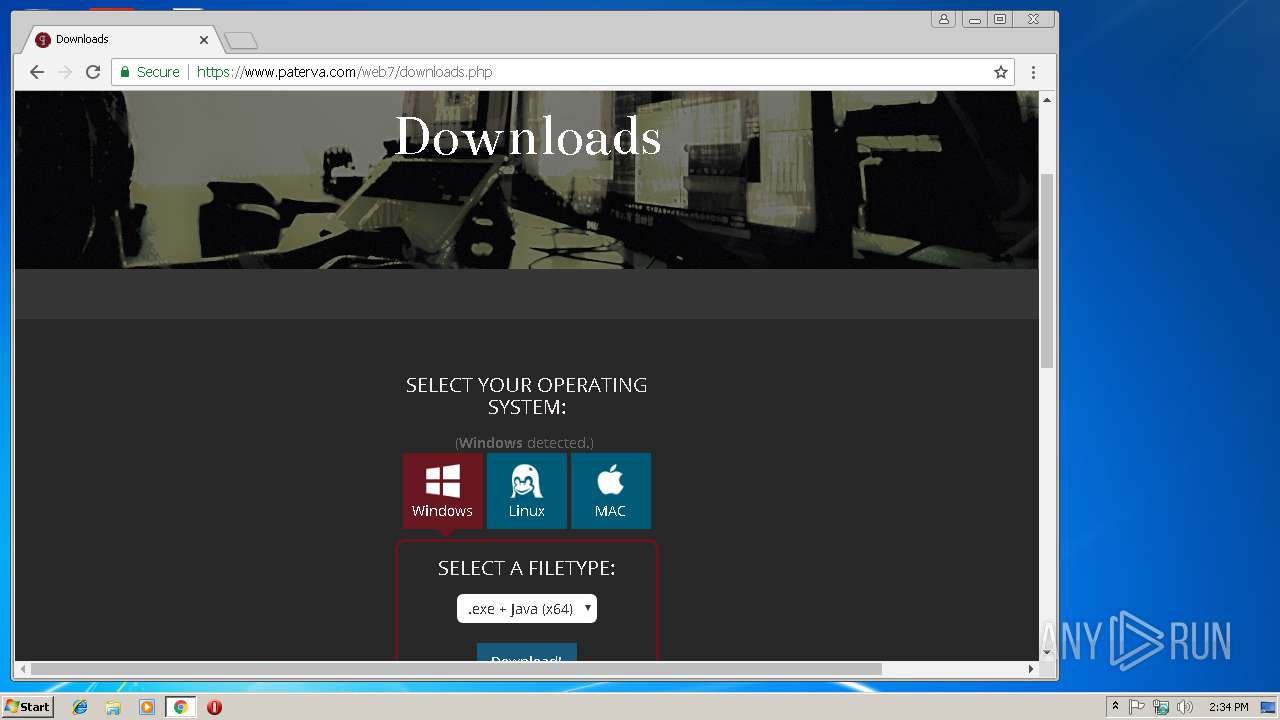
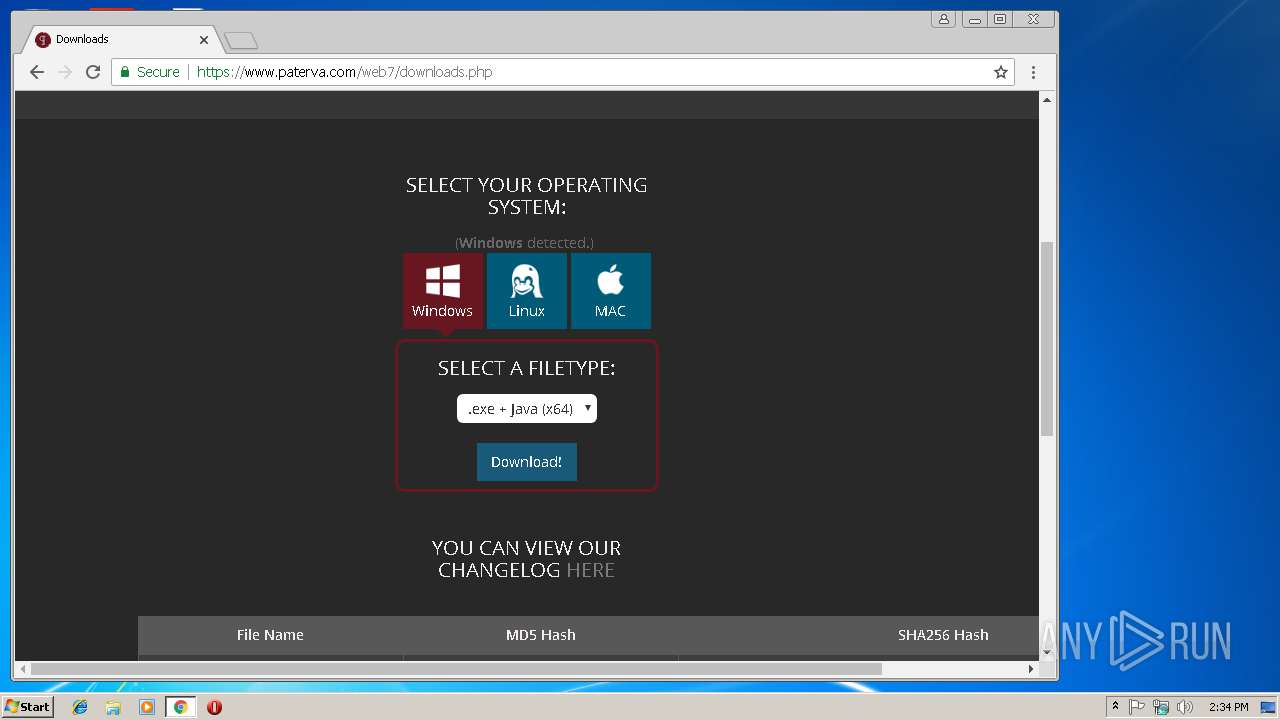
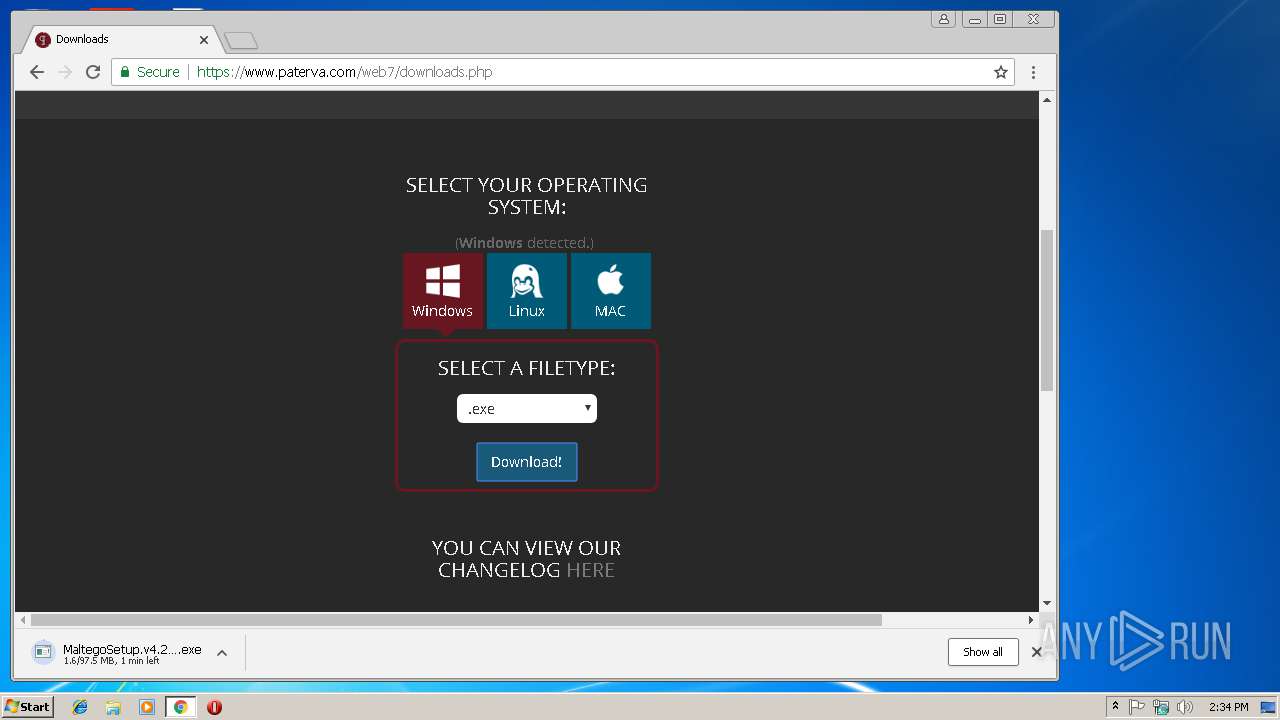
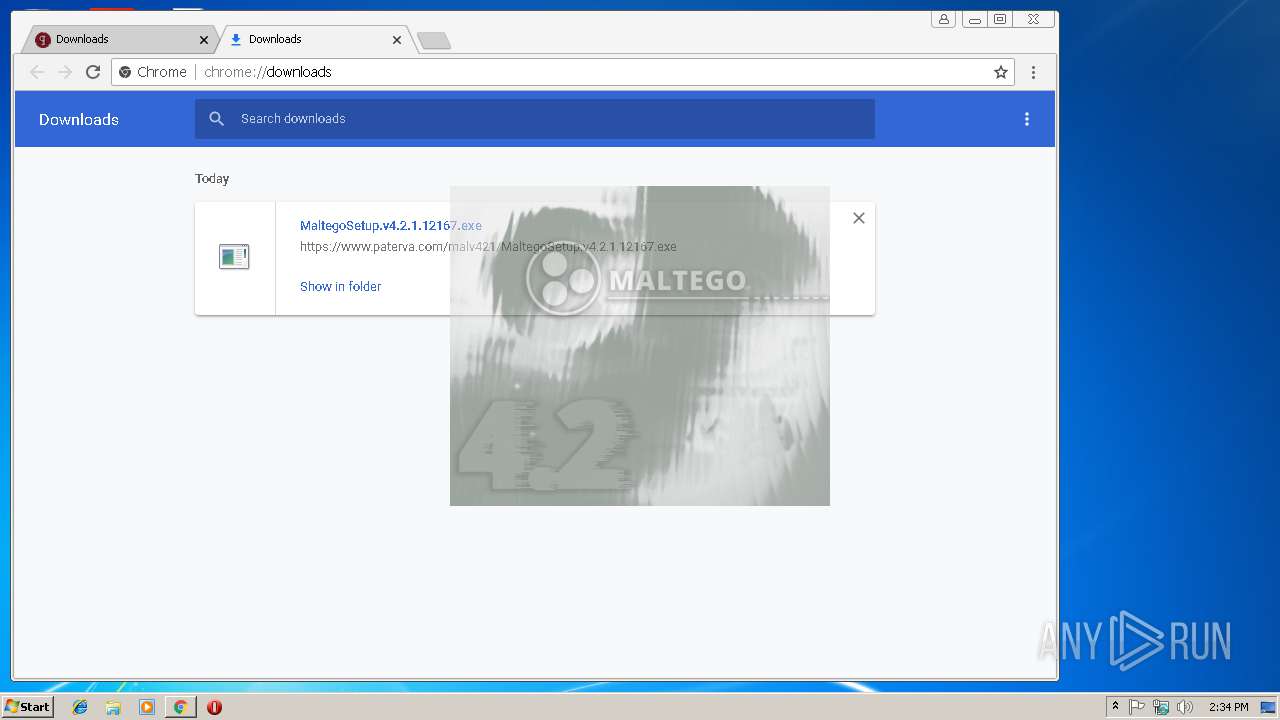
2316 | chrome.exe | GET | — | 104.200.18.205:80 | http://paterva.com/ | US | — | — | whitelisted |
2316 | chrome.exe | GET | 302 | 104.200.18.205:80 | http://paterva.com/ | US | — | — | whitelisted |
2316 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3376 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2316 | chrome.exe | GET | 301 | 104.200.18.205:80 | http://www.paterva.com/web7/ | US | html | 16 b | whitelisted |
2316 | chrome.exe | GET | 301 | 104.200.18.205:80 | http://paterva.com/web7/ | US | html | 236 b | whitelisted |
2316 | chrome.exe | GET | 200 | 52.222.146.100:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3688 | iexplore.exe | 87.250.250.242:443 | ya.ru | YANDEX LLC | RU | whitelisted |
3376 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2316 | chrome.exe | 172.217.16.131:443 | www.google.de | Google Inc. | US | whitelisted |
2316 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 172.217.21.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 172.217.18.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 104.200.18.205:80 | paterva.com | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ya.ru |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
paterva.com |
| whitelisted |