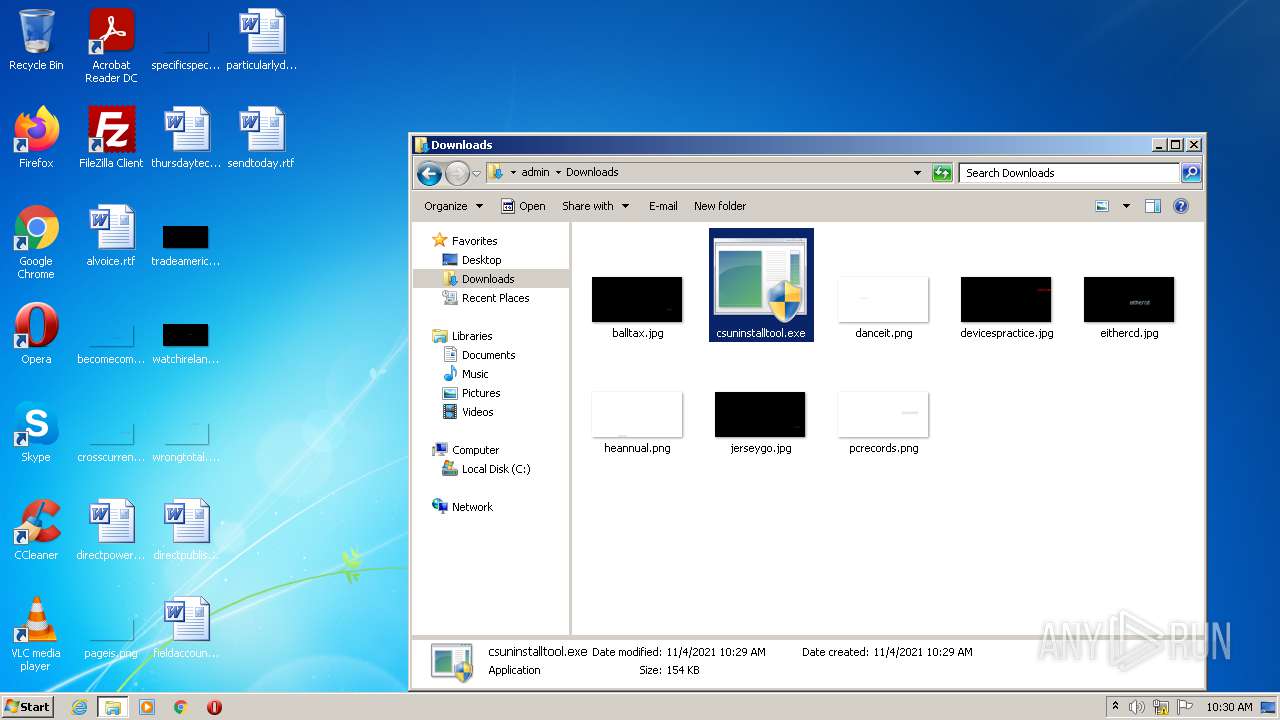
| File name: | csuninstalltool.exe |
| Full analysis: | https://app.any.run/tasks/dc3d2838-ca4b-4858-8e56-58cfc464bc93 |
| Verdict: | Malicious activity |
| Analysis date: | November 04, 2021, 10:29:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | E5FDDF6F8EE48D84FC03BDCD94606D61 |
| SHA1: | 0904F9E46A007DE7805958AD62564F9EBB143A05 |
| SHA256: | E127F23DDA6F2C3F48E9D2AD55A9D245B3FE6E6E607ED2572A4DD2BE819A8235 |
| SSDEEP: | 3072:eDMRjZ5xQfXvsLvewGSr9X5jfd7NkGer4MnwU4fZcX7g41wMrGbpwQl:N/ev4ftQ43M7u/yq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- csuninstalltool.exe (PID: 4028)
- csuninstalltool.exe (PID: 2868)
- csuninstalltool.exe (PID: 2788)
Searches for installed software
- csuninstalltool.exe (PID: 4028)
- csuninstalltool.exe (PID: 2868)
- csuninstalltool.exe (PID: 2788)
Executed via COM
- DllHost.exe (PID: 1272)
INFO
Checks supported languages
- explorer.exe (PID: 3384)
- DllHost.exe (PID: 1272)
Reads the computer name
- explorer.exe (PID: 3384)
- DllHost.exe (PID: 1272)
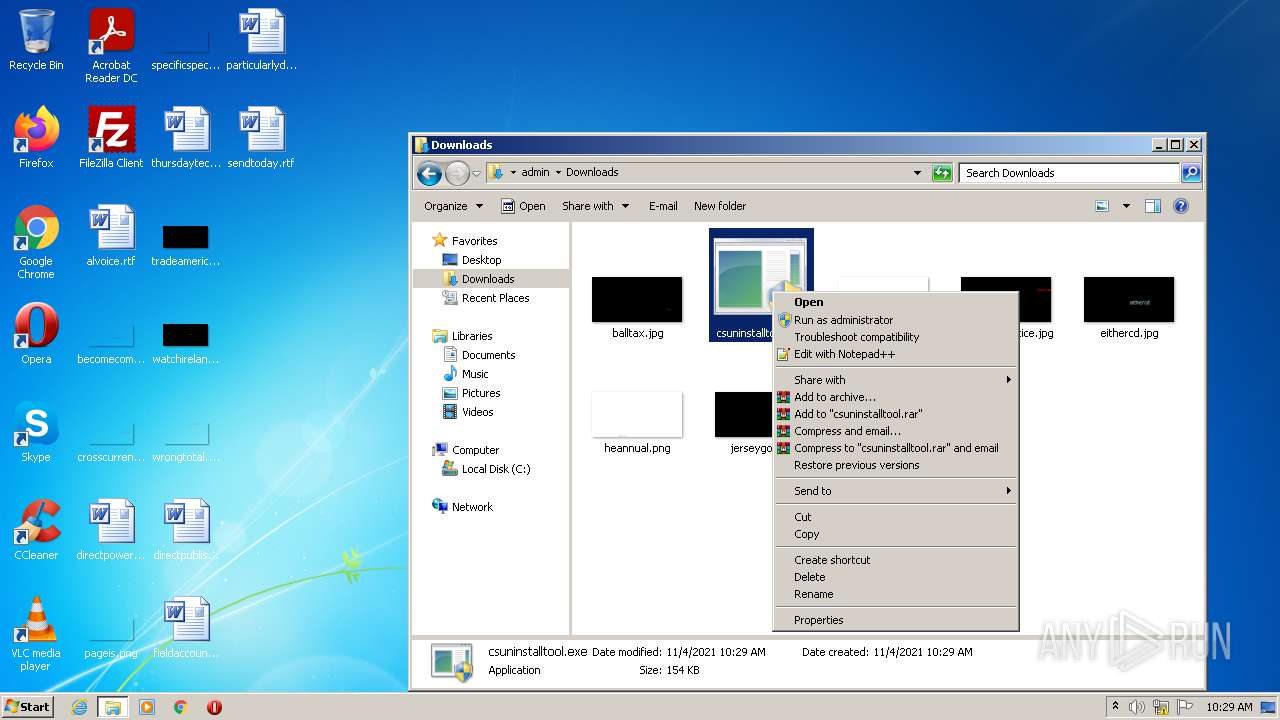
Manual execution by user
- explorer.exe (PID: 3384)
- csuninstalltool.exe (PID: 2216)
- csuninstalltool.exe (PID: 2868)
- csuninstalltool.exe (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:30 00:43:34+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 89600 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4980 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 29-Jul-2018 22:43:34 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 29-Jul-2018 22:43:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015C89 | 0x00015E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60778 |
.rdata | 0x00017000 | 0x00007570 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27925 |
.data | 0x0001F000 | 0x0000147C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.02628 |
.reloc | 0x00021000 | 0x000011F8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55535 |
Imports
ADVAPI32.dll |
KERNEL32.dll |
VERSION.dll |
msi.dll |
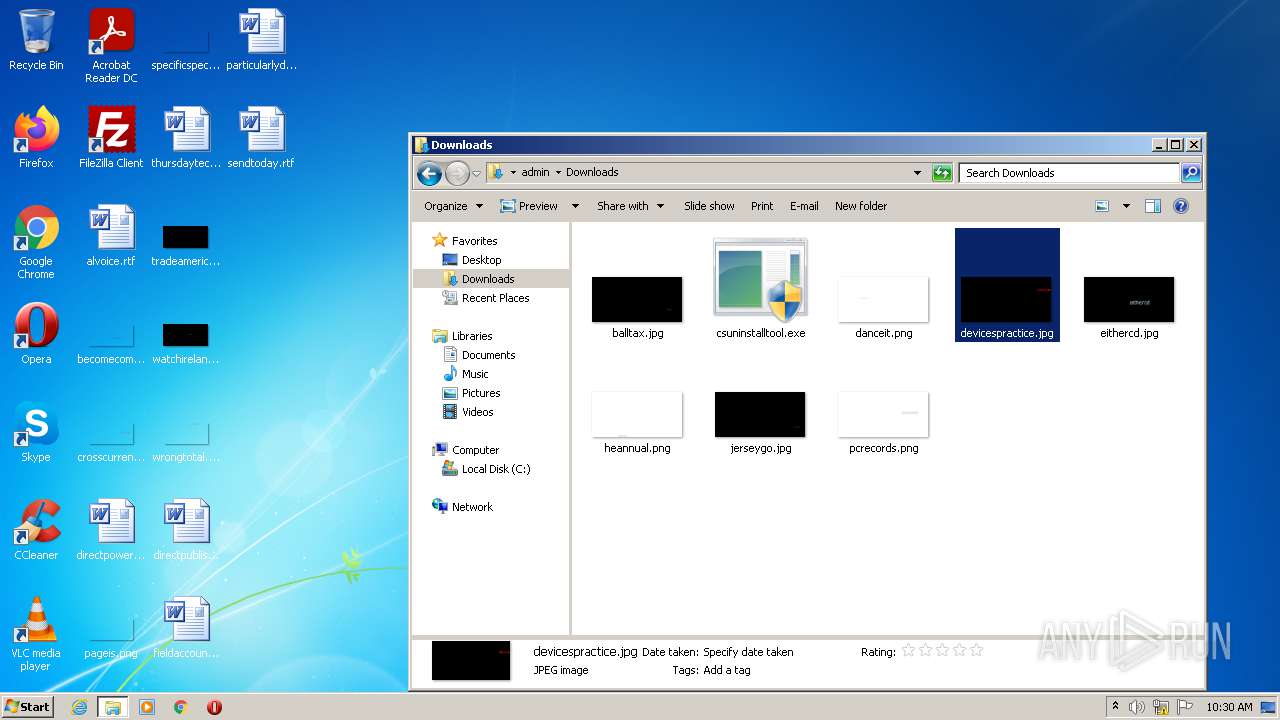
Total processes
53
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1272 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
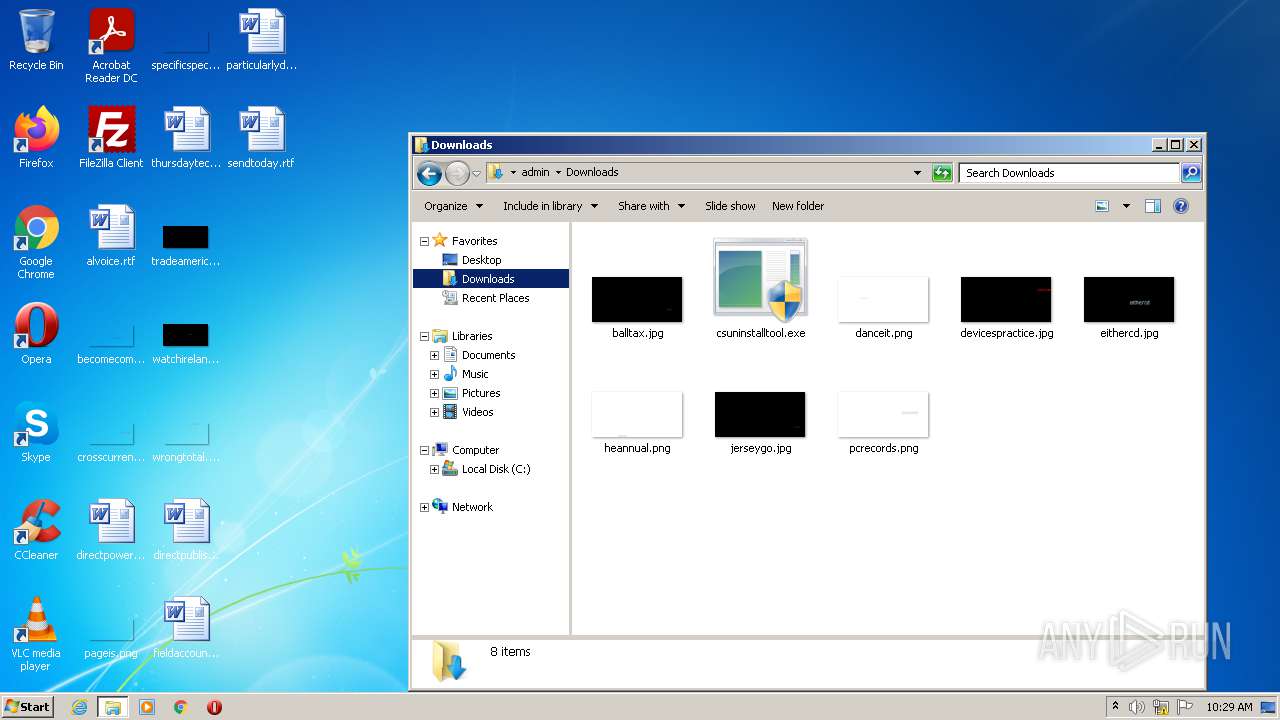
| 2216 | "C:\Users\admin\Downloads\csuninstalltool.exe" | C:\Users\admin\Downloads\csuninstalltool.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2788 | "C:\Users\admin\Downloads\csuninstalltool.exe" | C:\Users\admin\Downloads\csuninstalltool.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2868 | "C:\Users\admin\Downloads\csuninstalltool.exe" | C:\Users\admin\Downloads\csuninstalltool.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3384 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3452 | "C:\Users\admin\Downloads\csuninstalltool.exe" | C:\Users\admin\Downloads\csuninstalltool.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4028 | "C:\Users\admin\Downloads\csuninstalltool.exe" | C:\Users\admin\Downloads\csuninstalltool.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
819
Read events
817
Write events
2
Delete events
0
Modification events
| (PID) Process: | (1272) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (1272) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 60000000330000009F0400008002000000000000 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report