| File name: | SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574 |
| Full analysis: | https://app.any.run/tasks/3eb3d30b-7a37-4e7f-b0a1-21d74dc84de2 |
| Verdict: | Malicious activity |
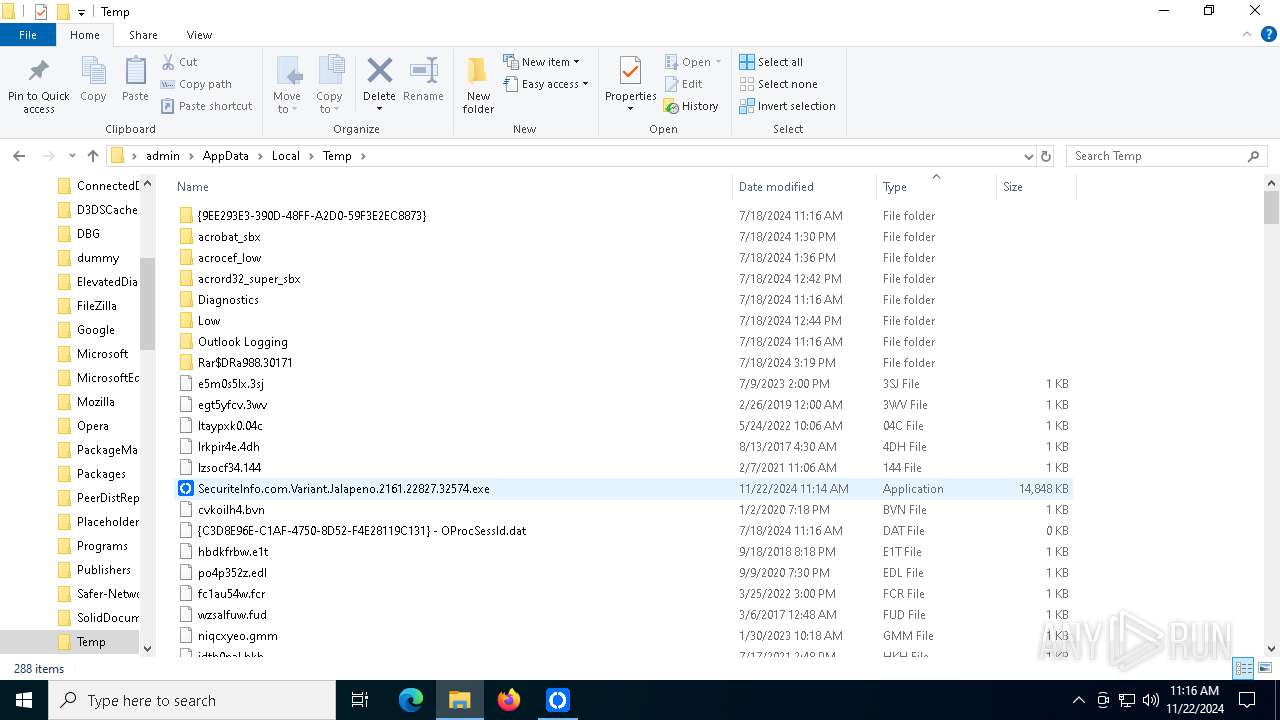
| Analysis date: | November 22, 2024, 11:14:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 1E817B1AF7B8C64D86C34177899447F7 |
| SHA1: | 9602B3DDD8D0E2225CDF7D807AB635CE66A47197 |
| SHA256: | E126B0E363751575835D4C97D211251407FE1B9AC05060885FF556529F52EEF7 |
| SSDEEP: | 98304:kTMOfYUTgpUscoDXDfk0+gLlxpFX0XAF6d6UGZaaYTEnmb78deBfKXF13i2yWQXJ:a0rm4Qy1q |
MALICIOUS
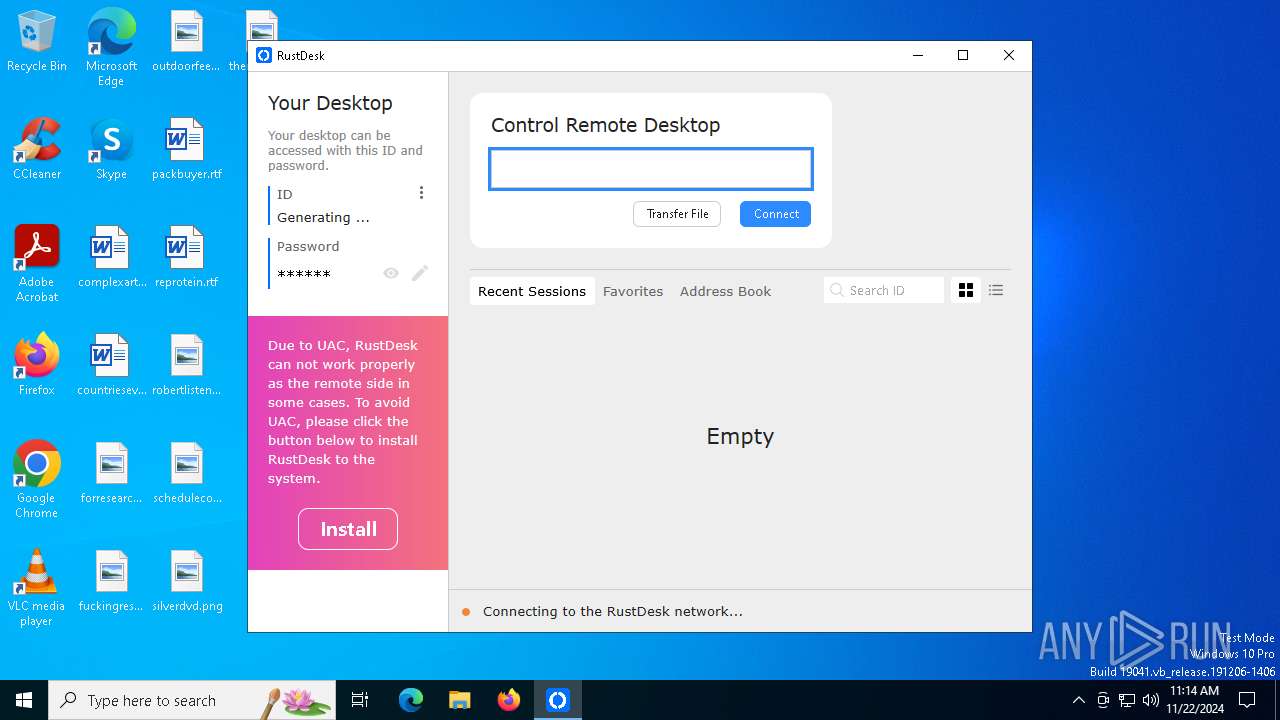
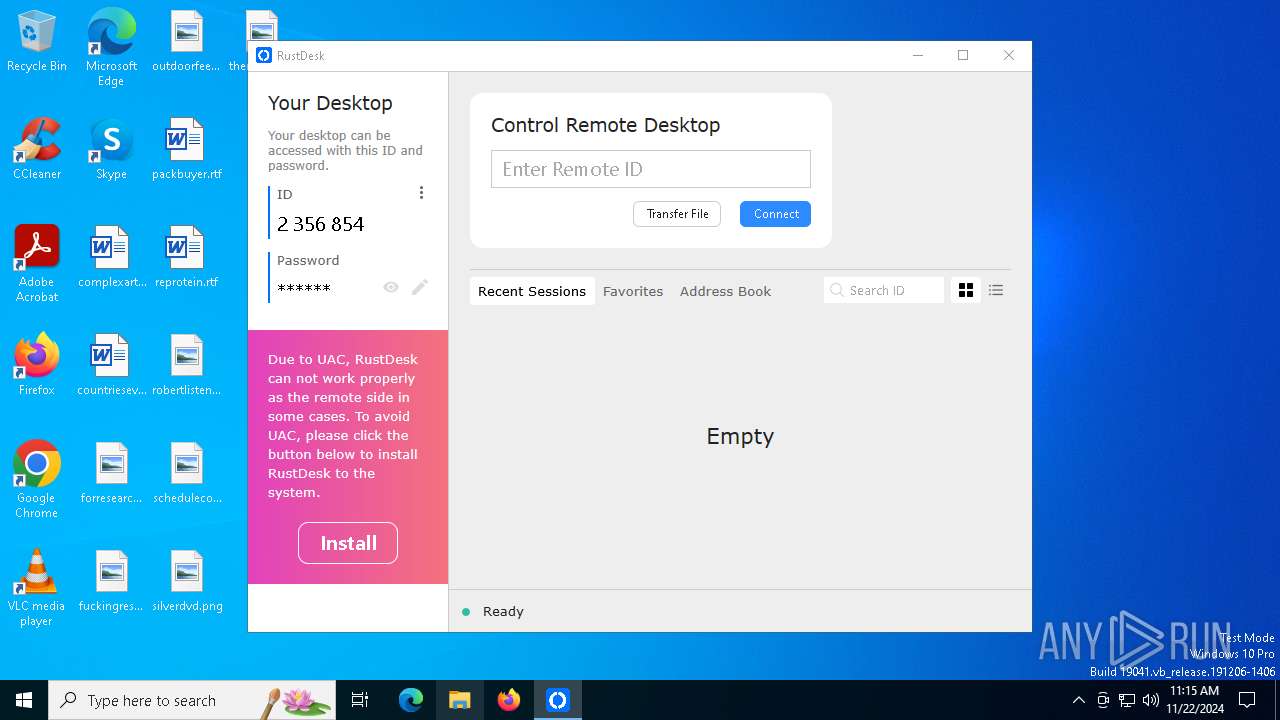
RUSTDESK has been detected (SURICATA)
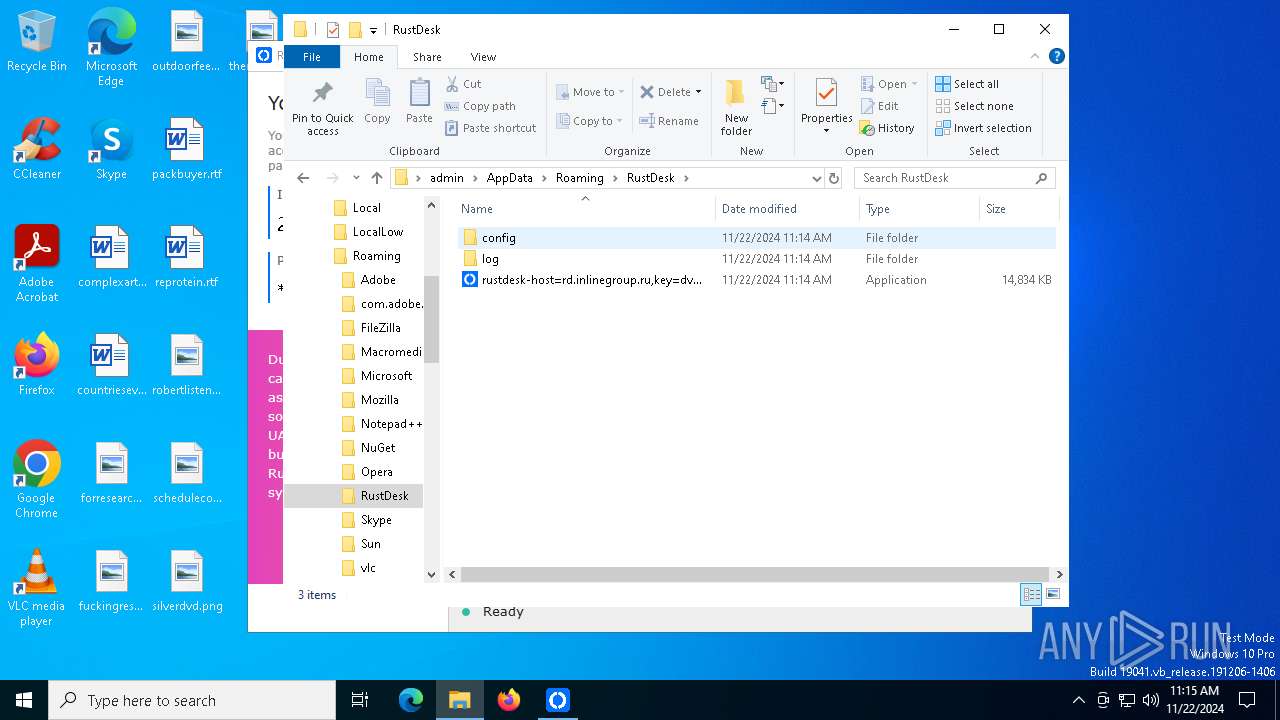
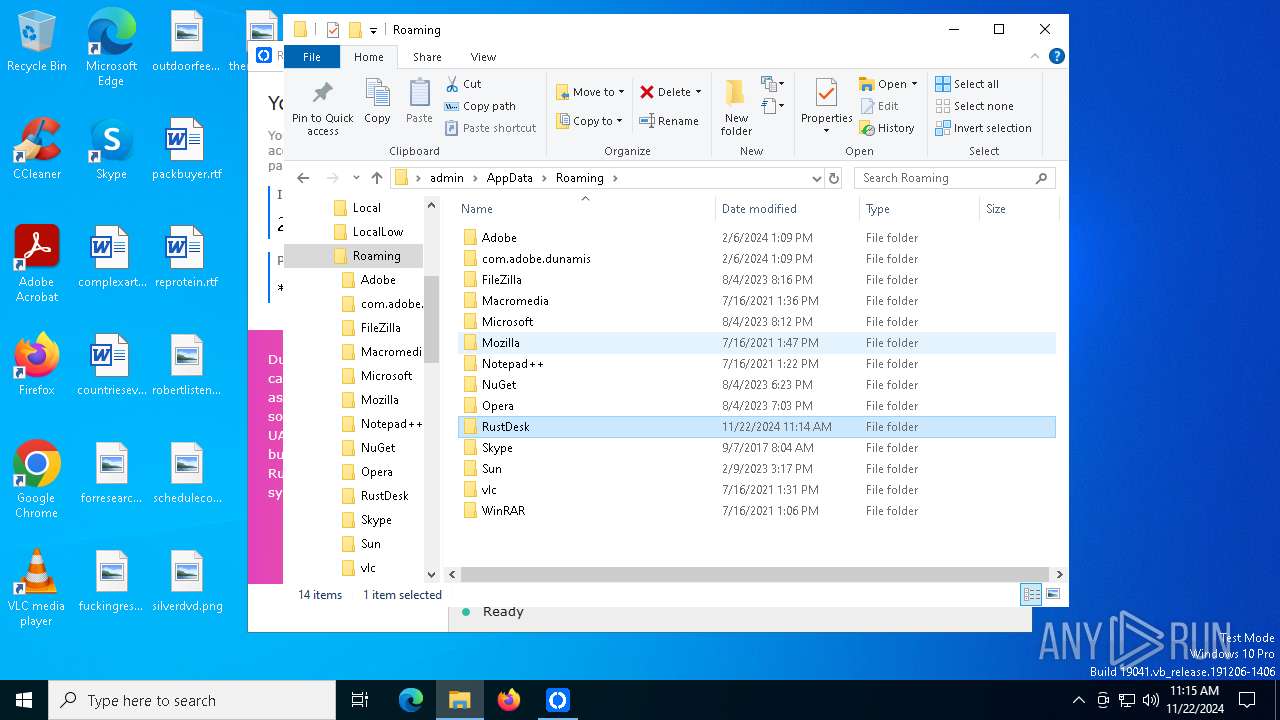
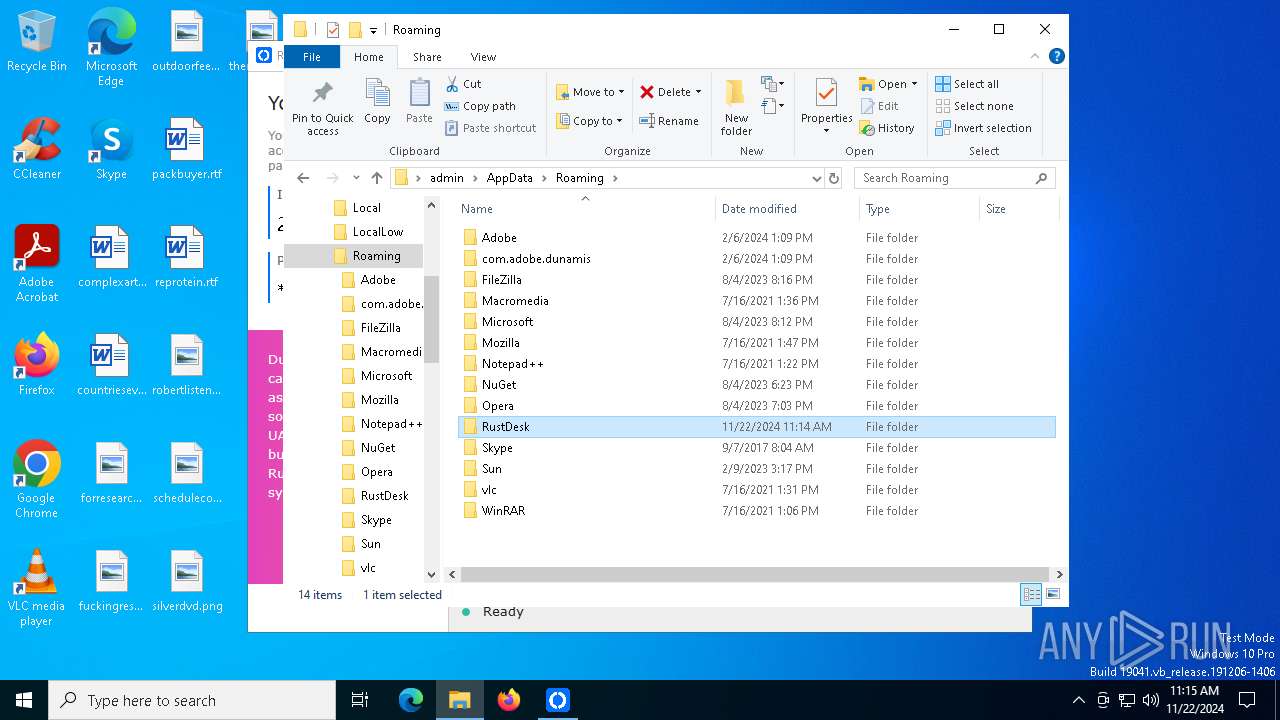
- rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe (PID: 5012)
SUSPICIOUS
Reads security settings of Internet Explorer
- SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe (PID: 4300)
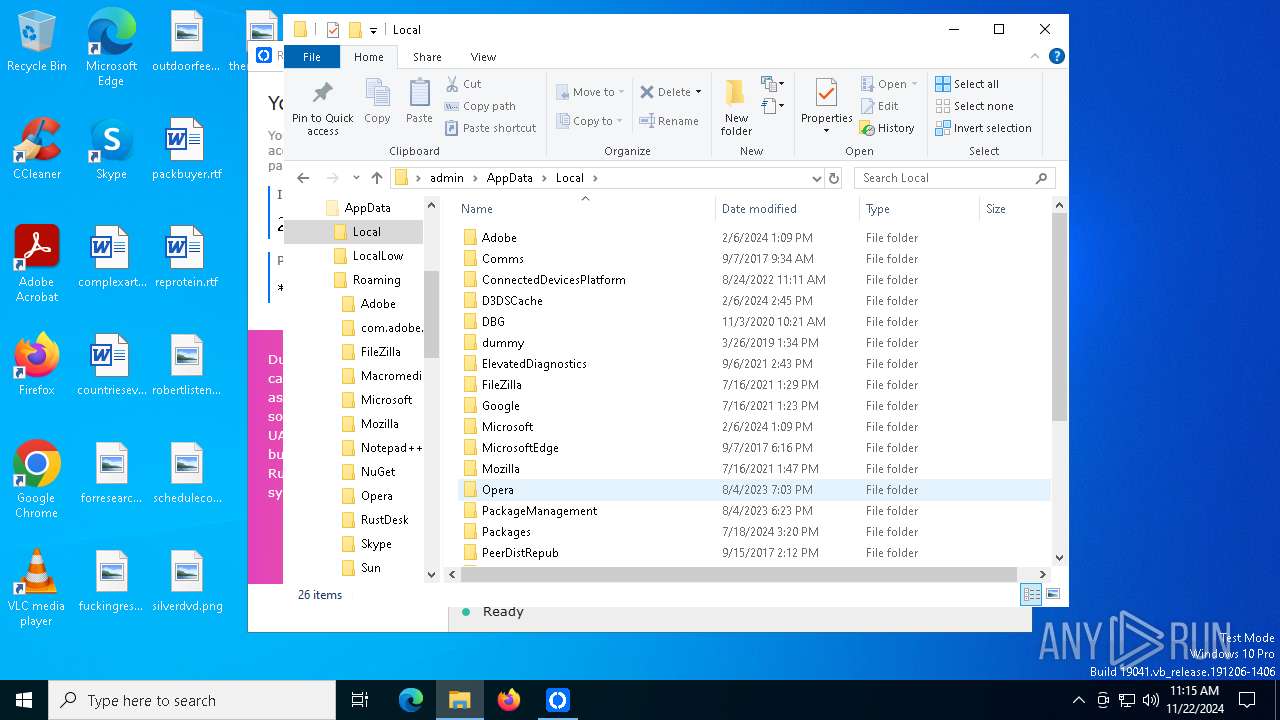
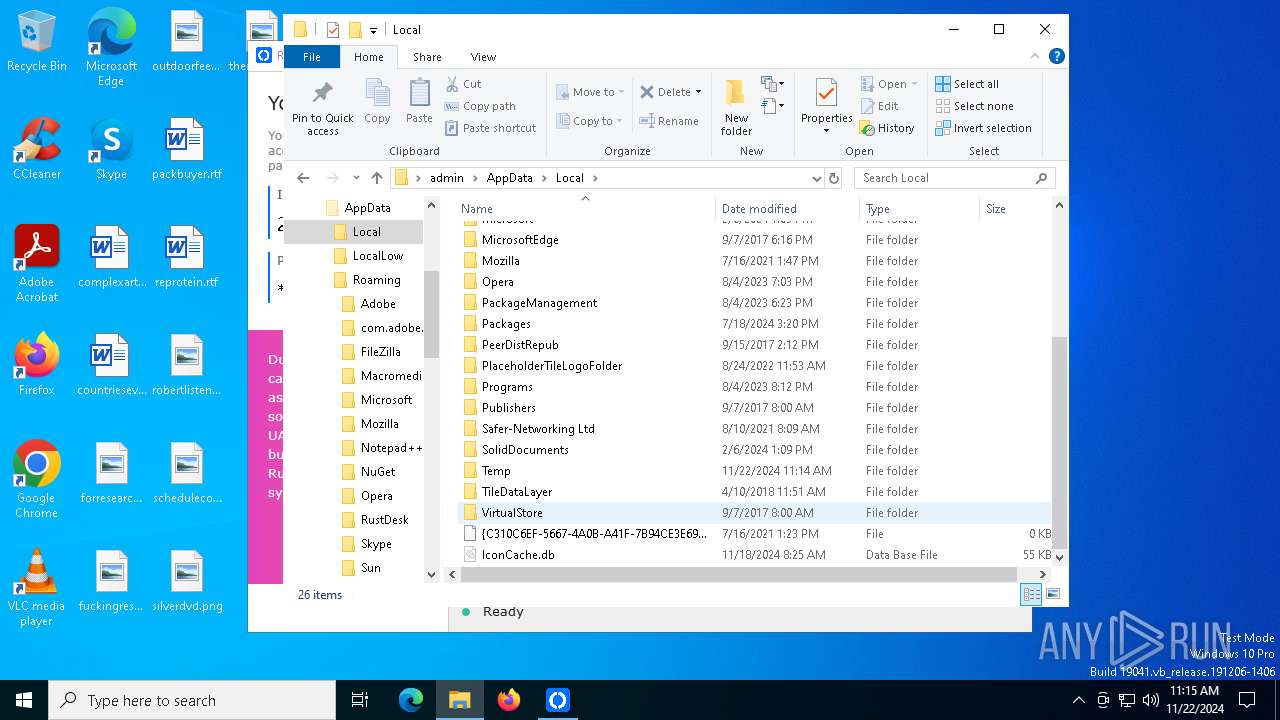
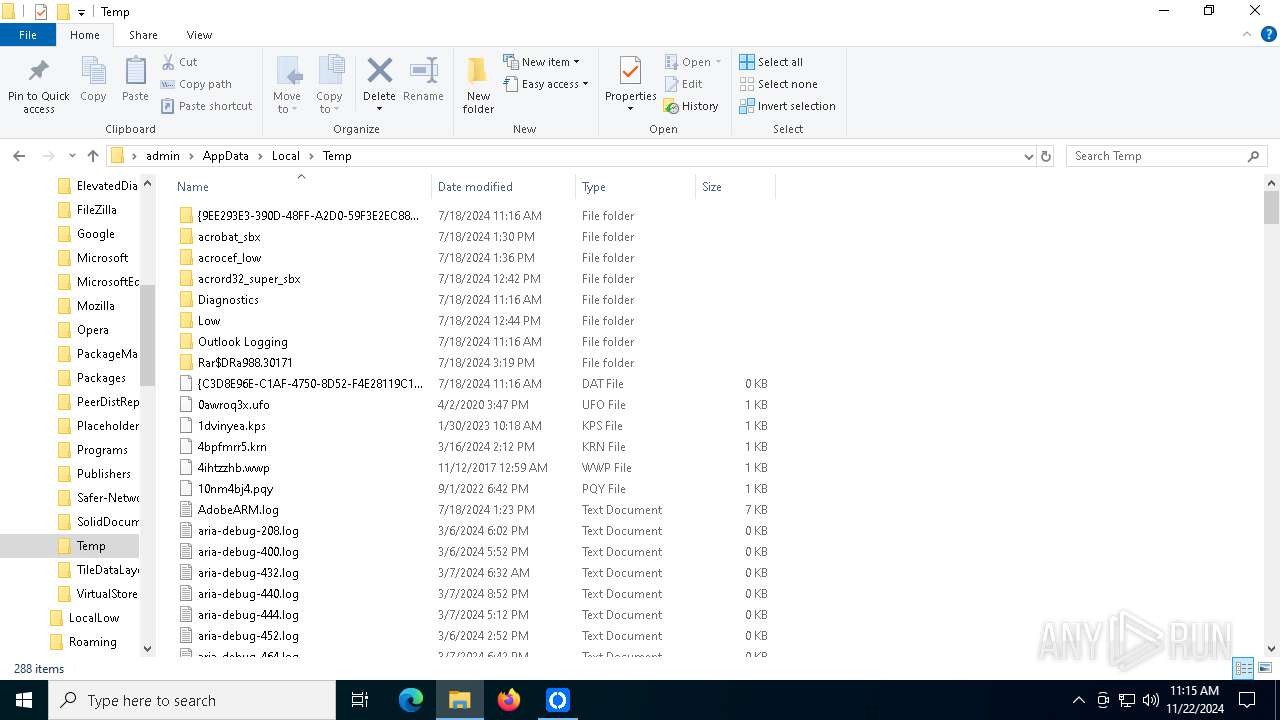
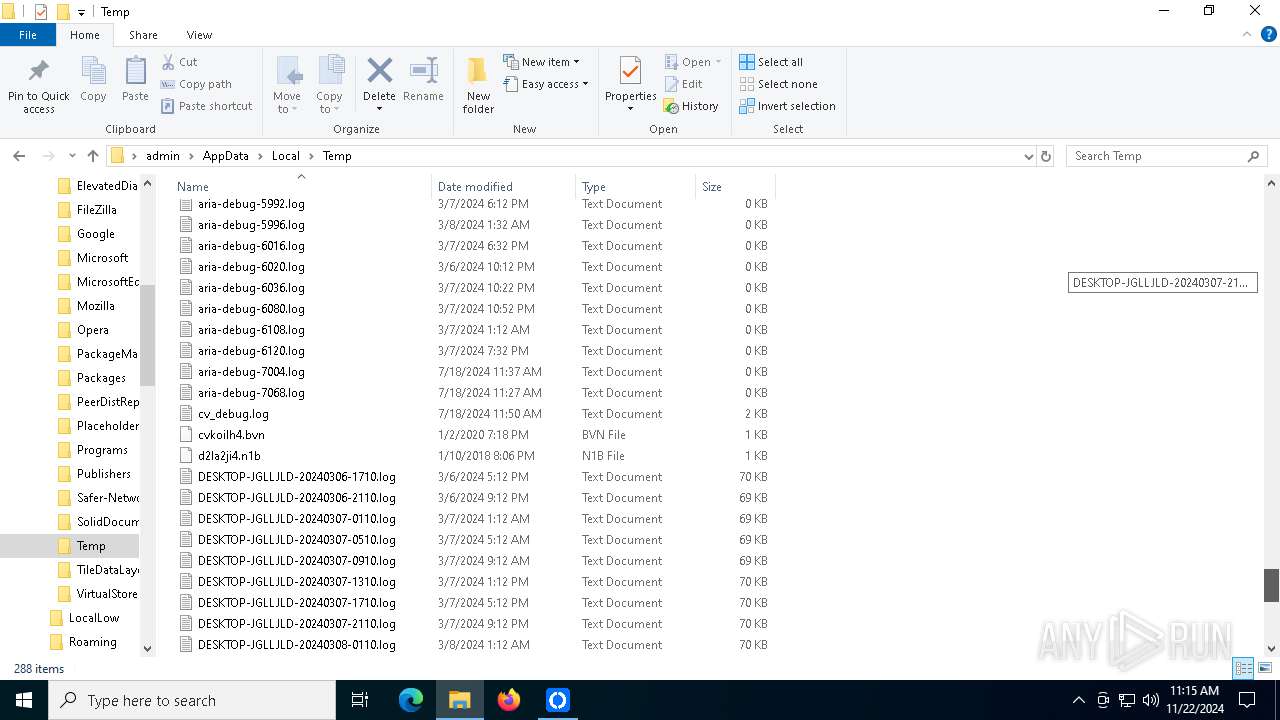
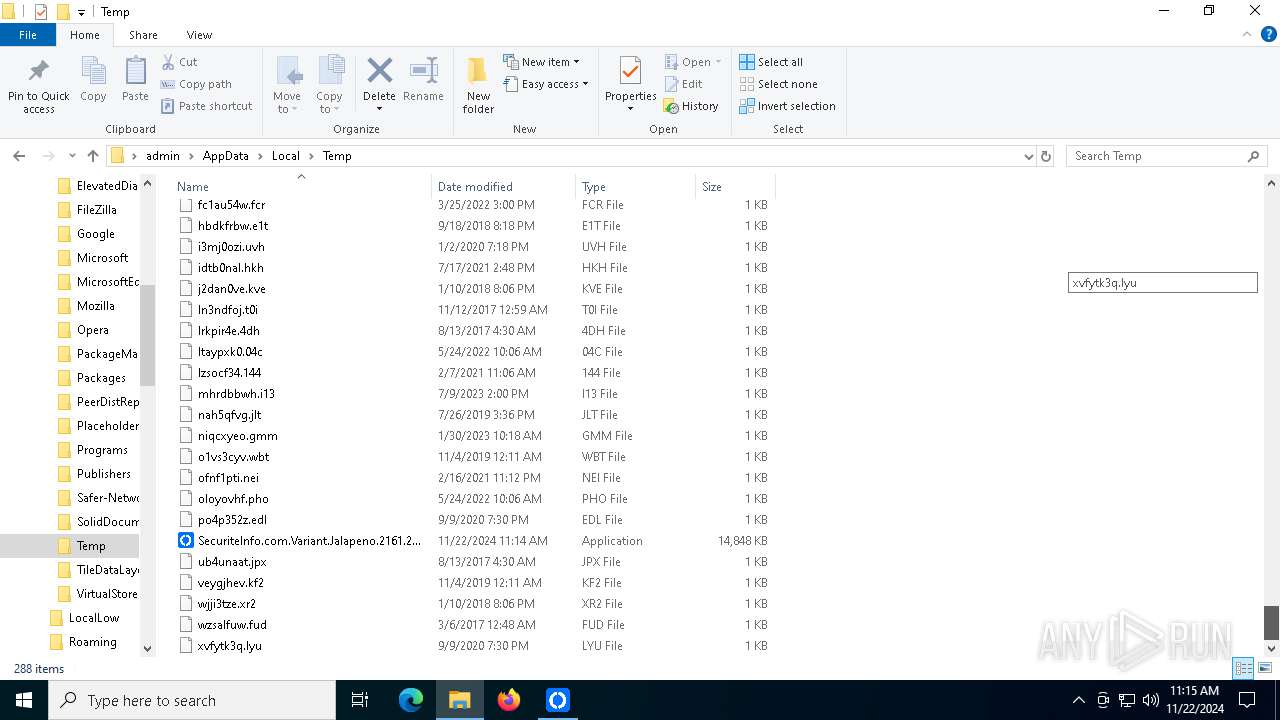
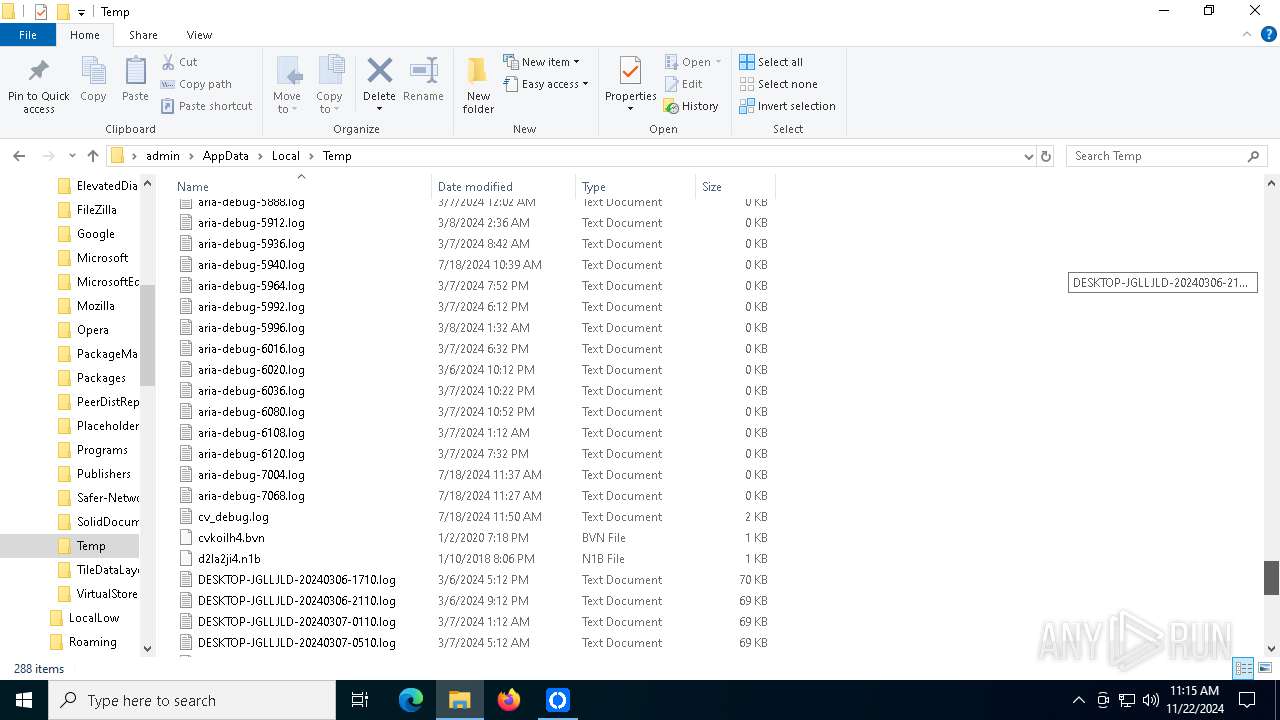
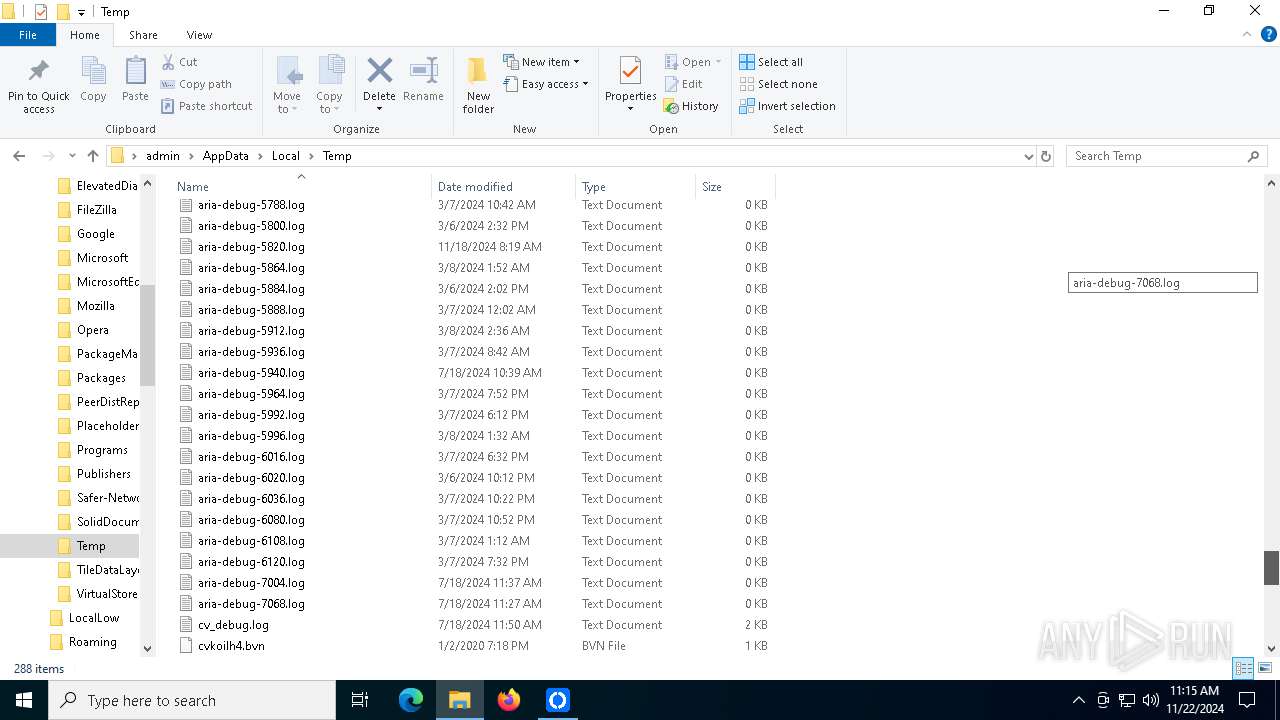
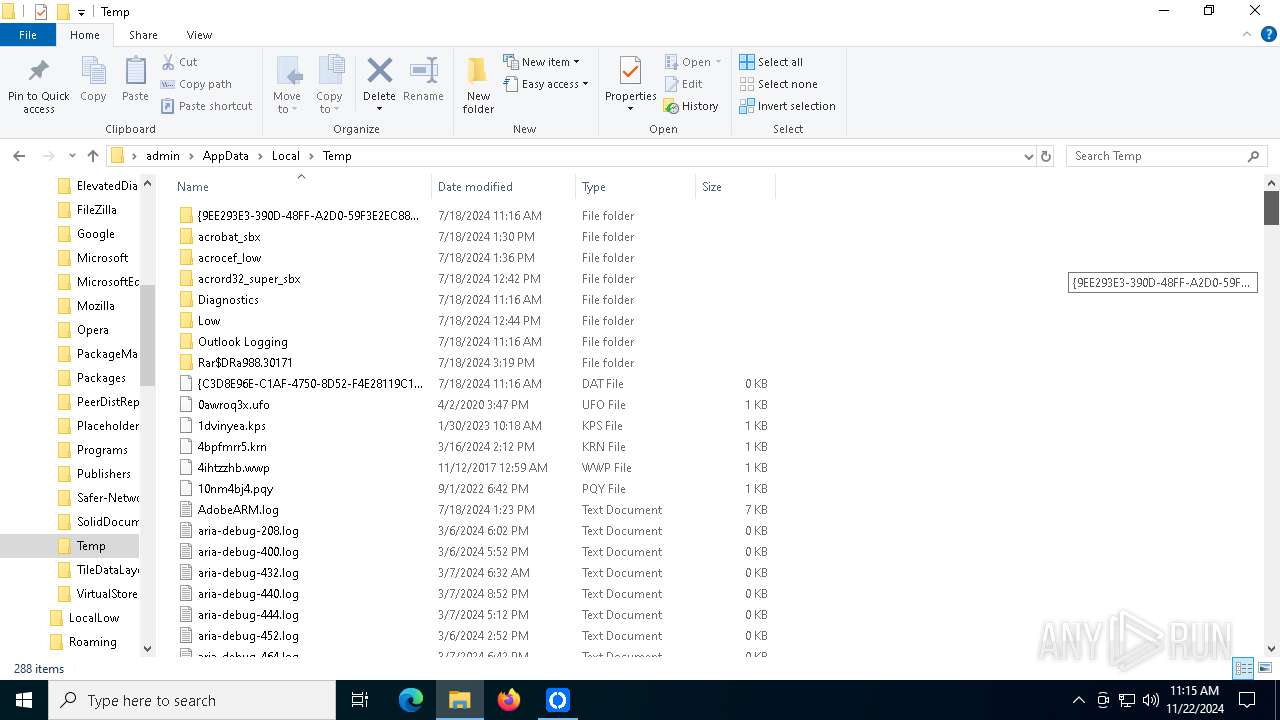
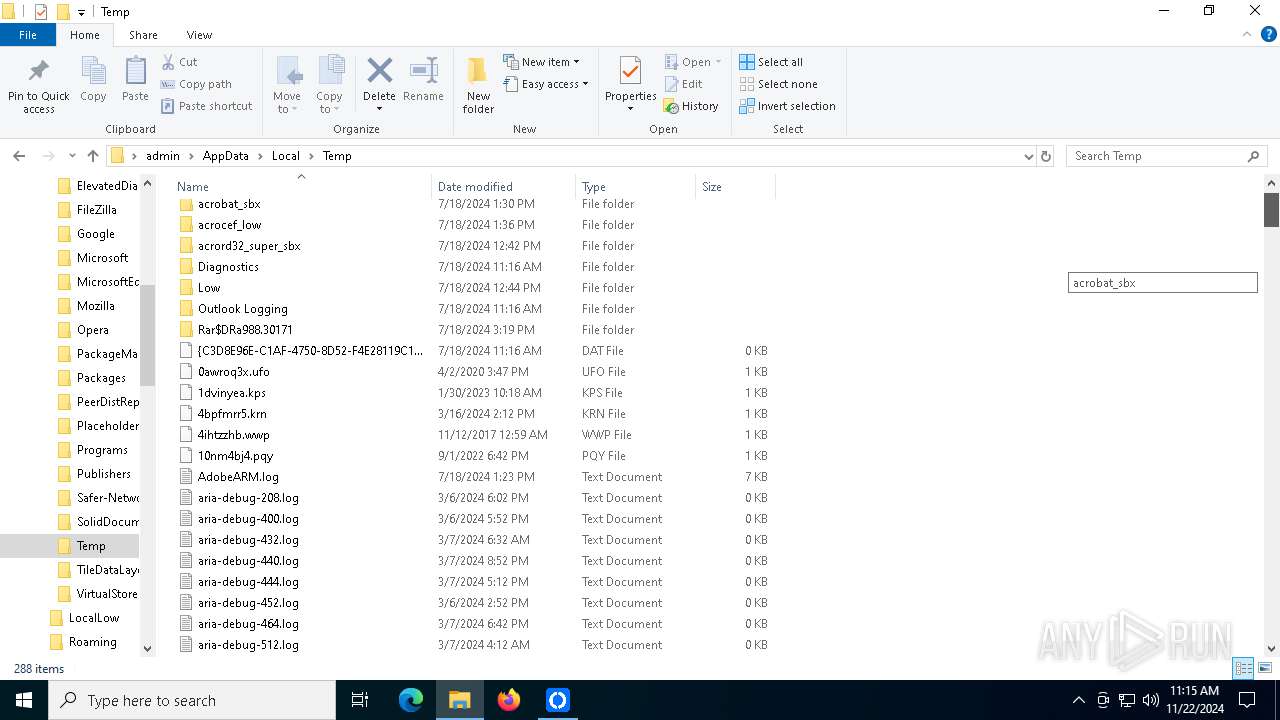
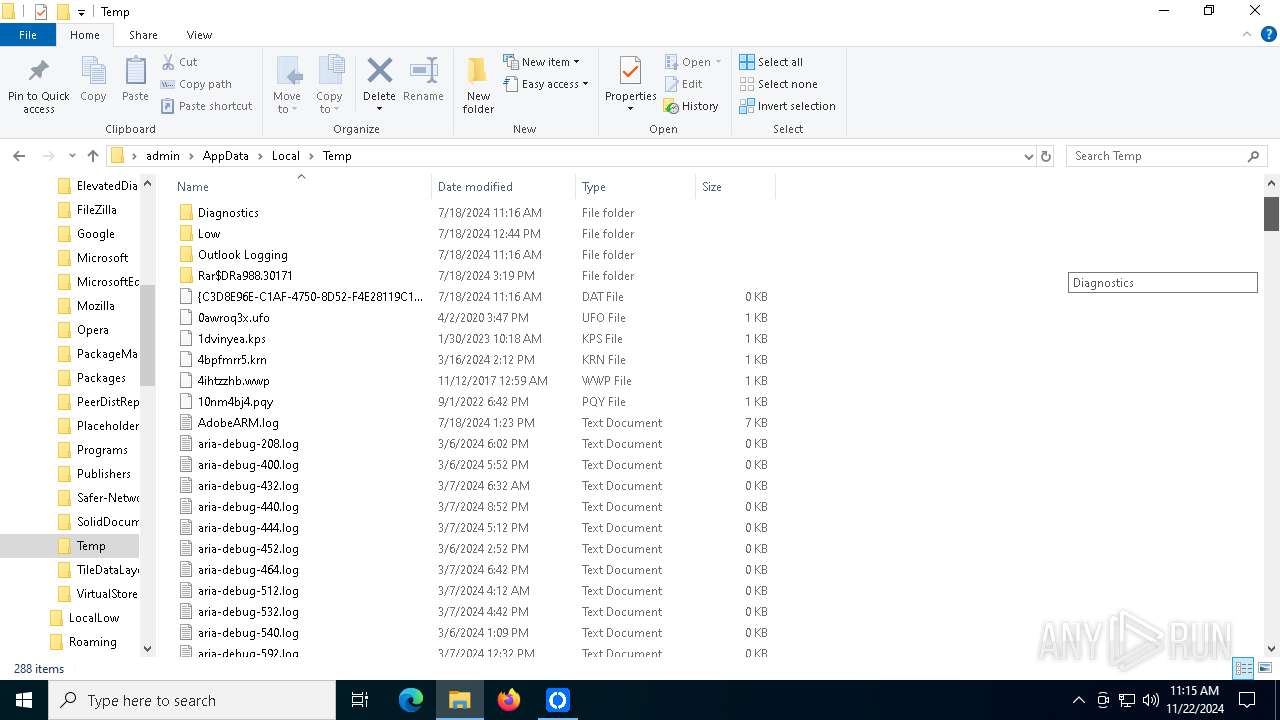
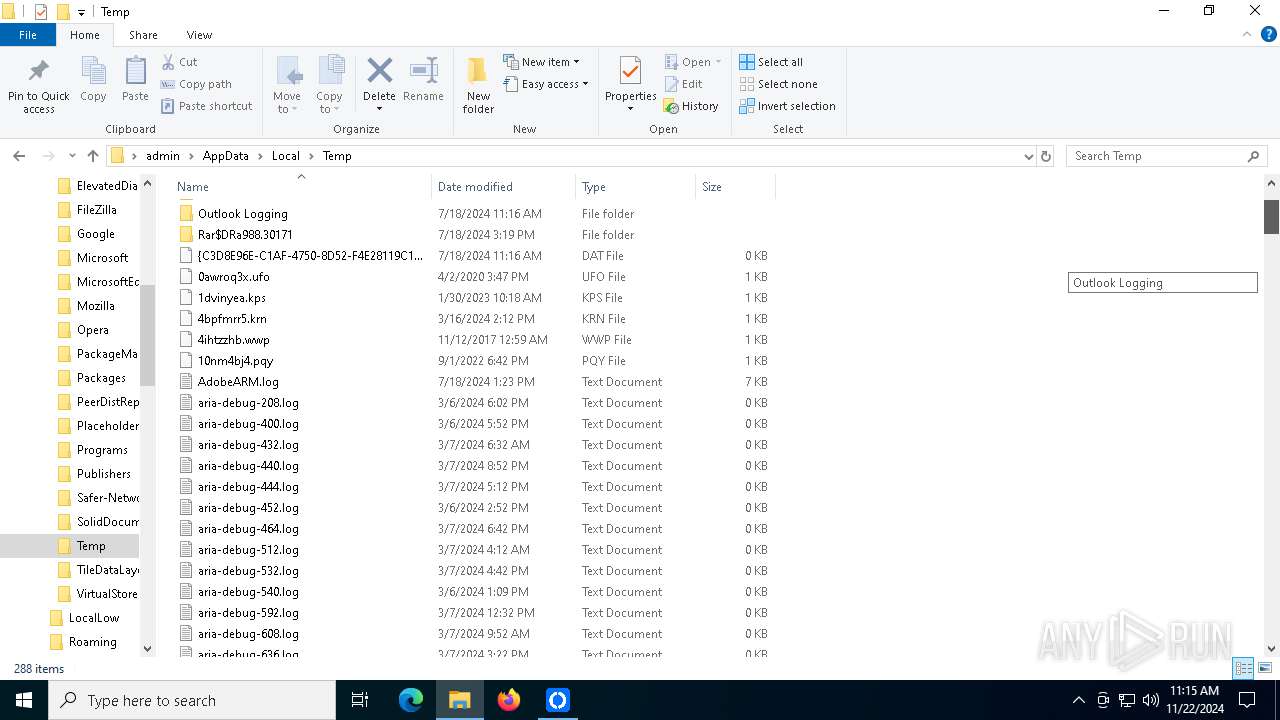
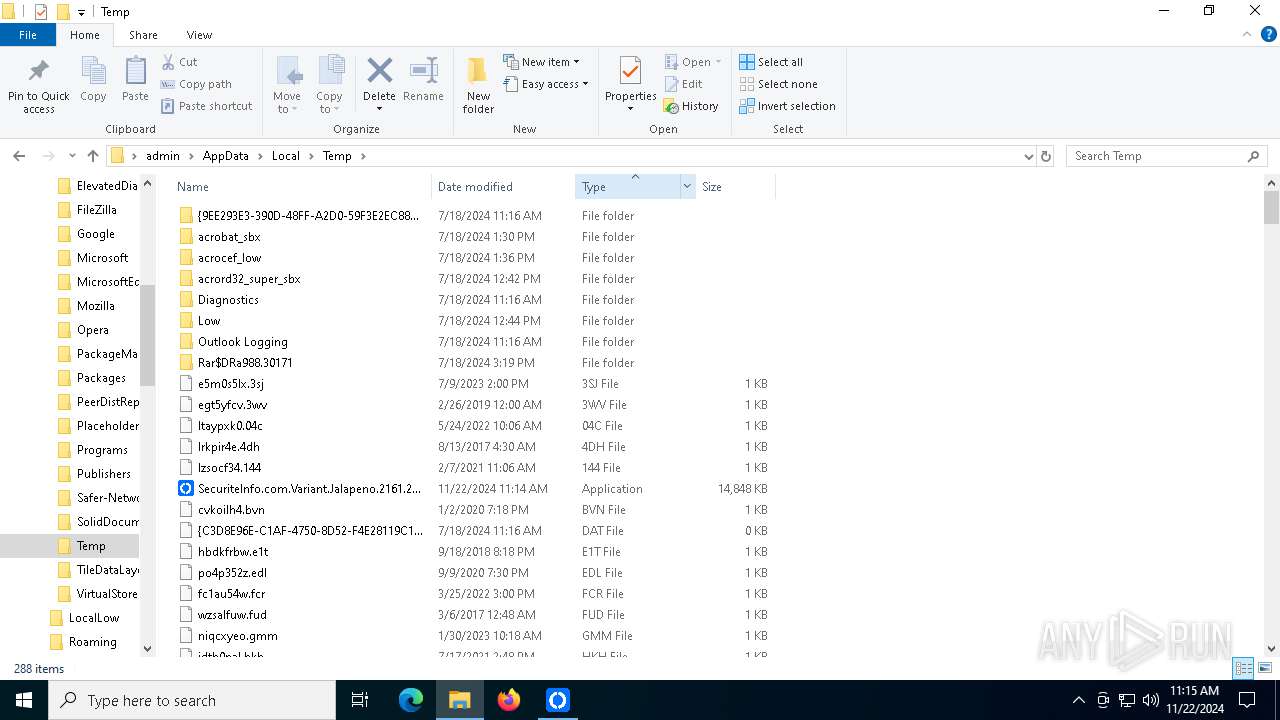
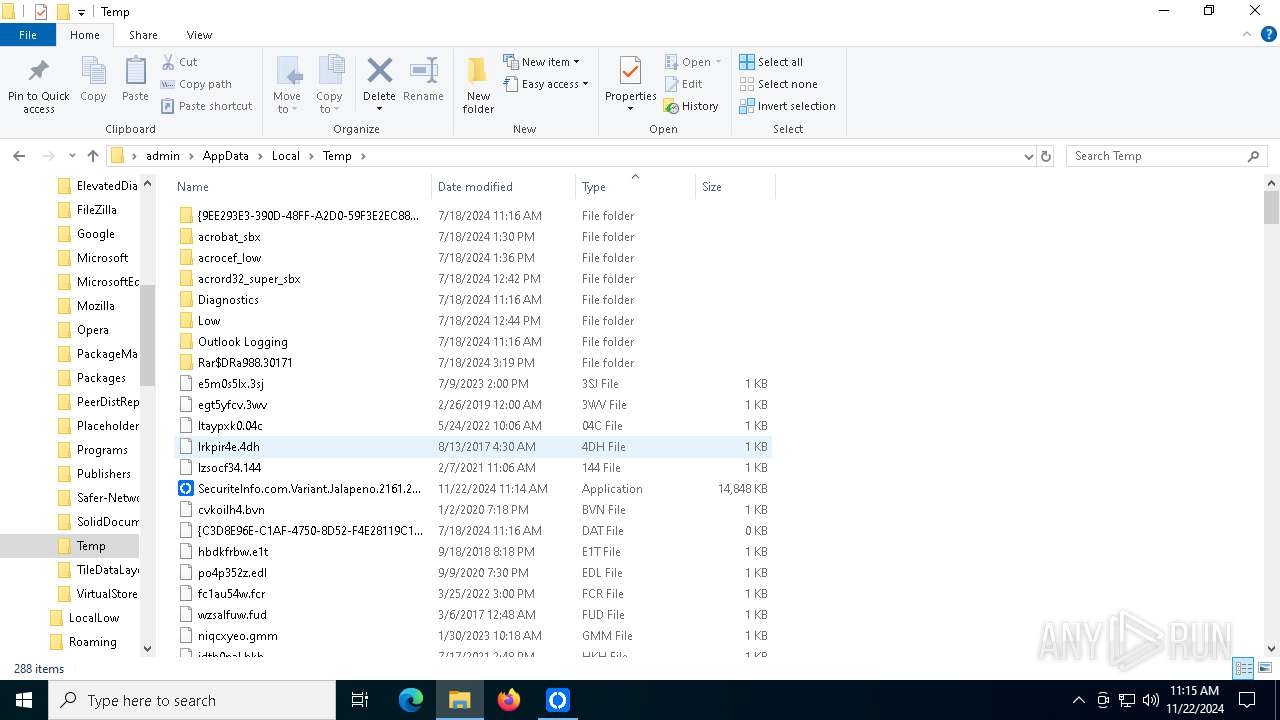
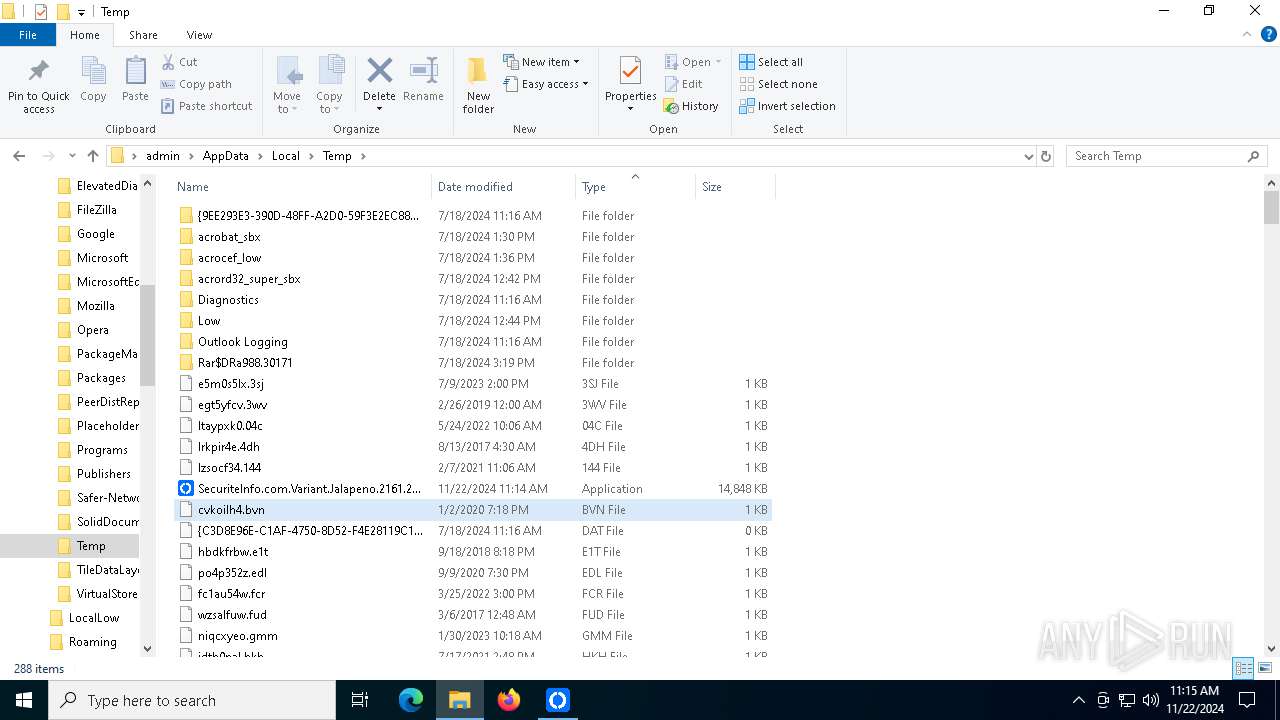
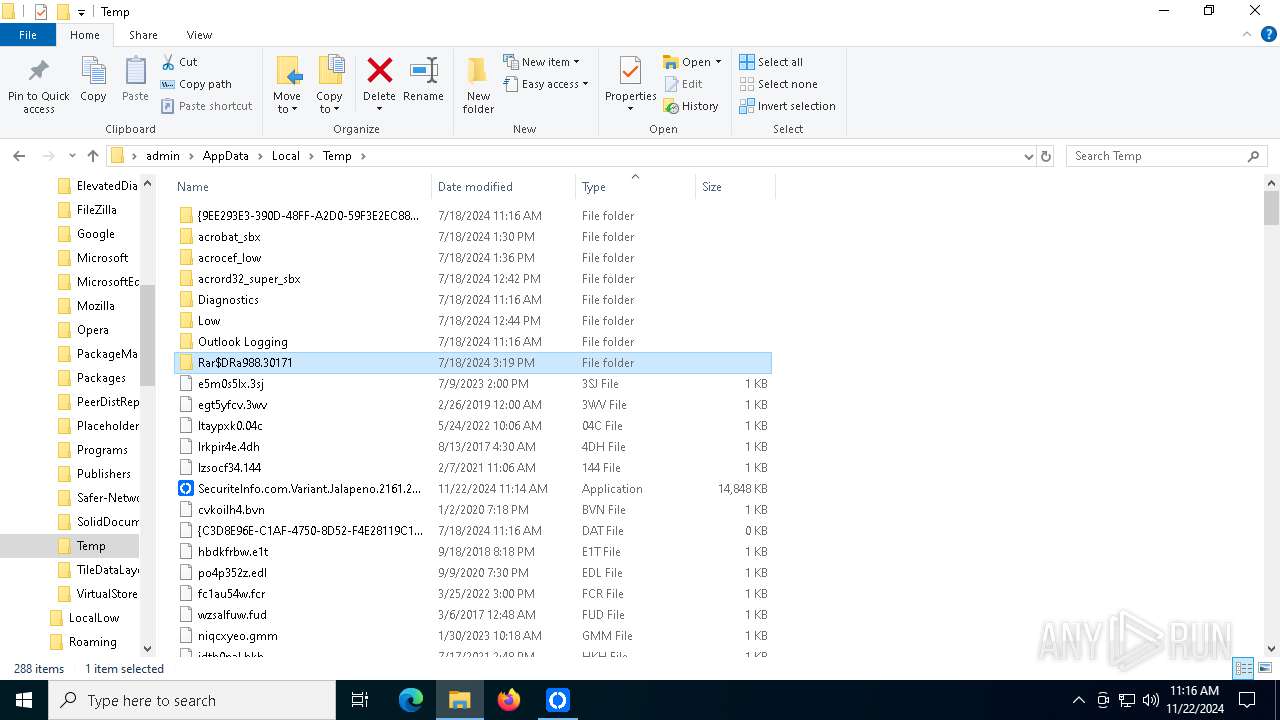
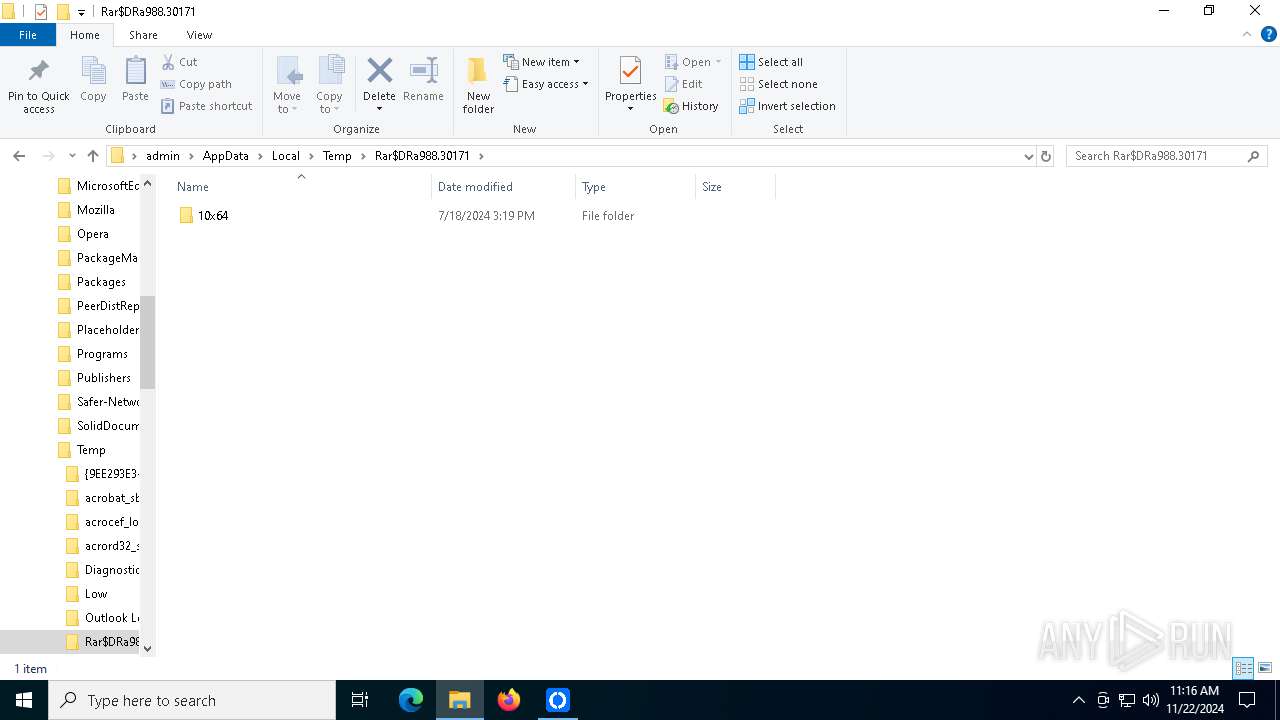
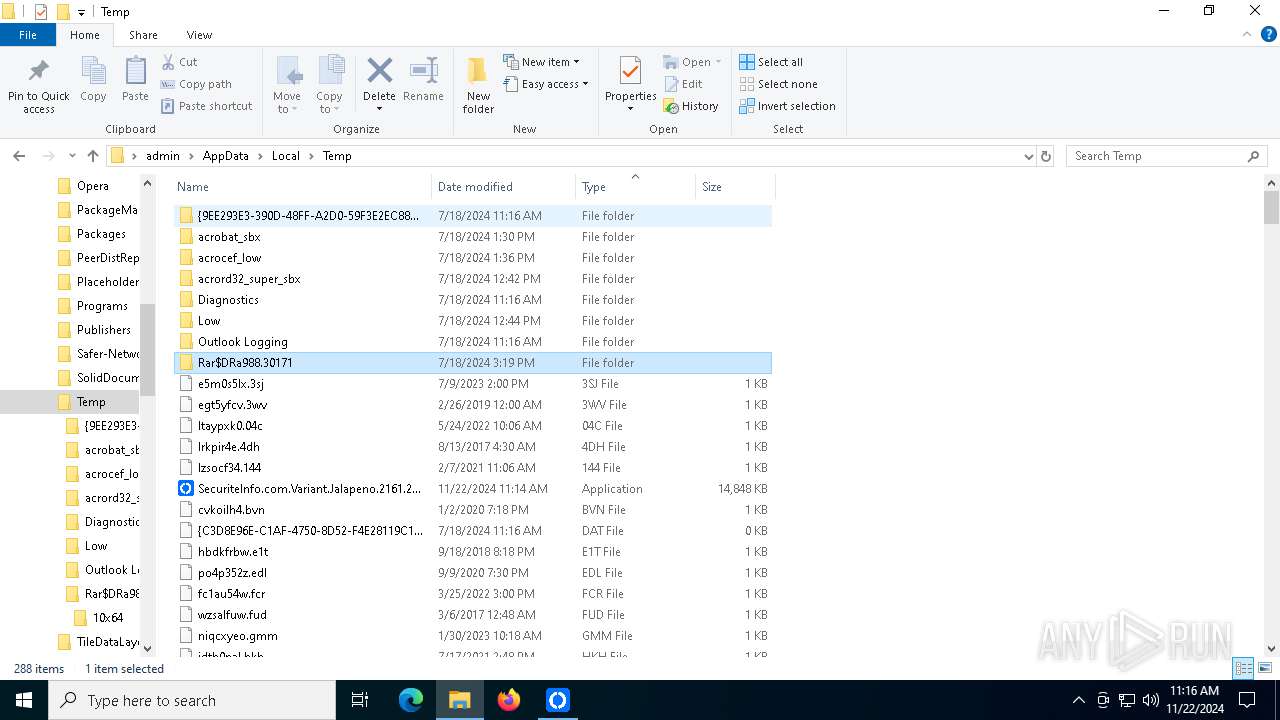
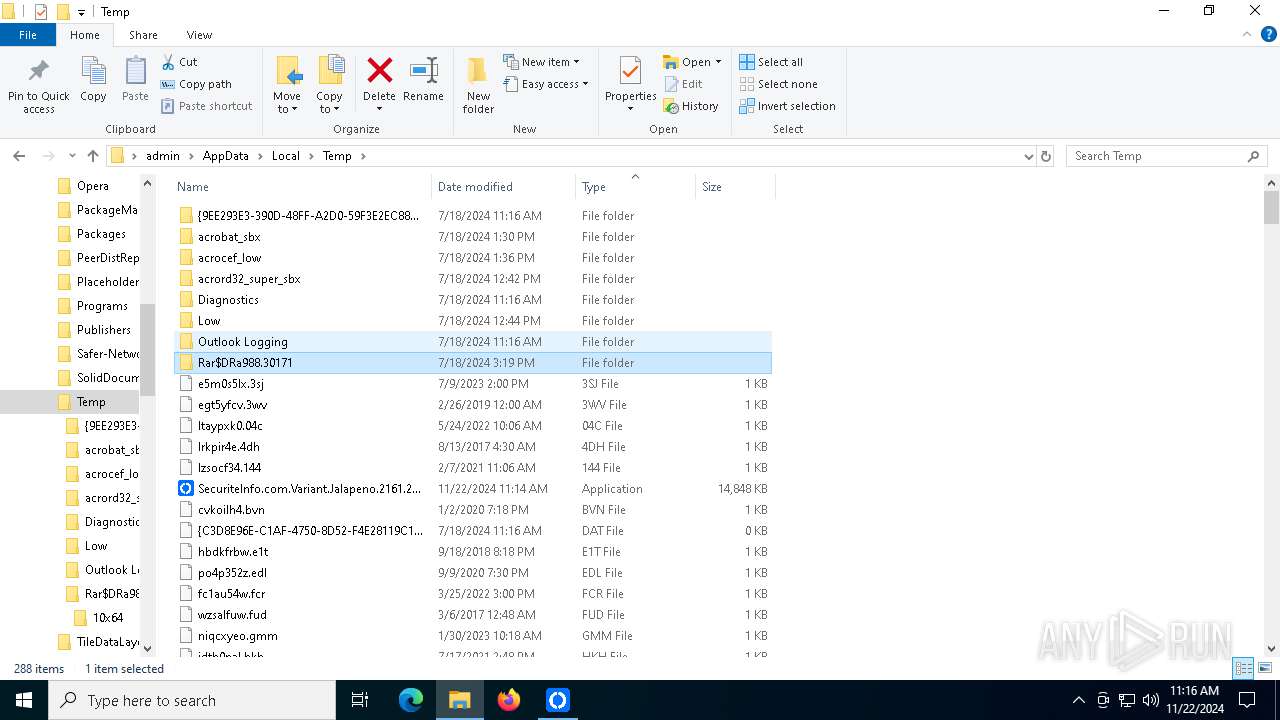
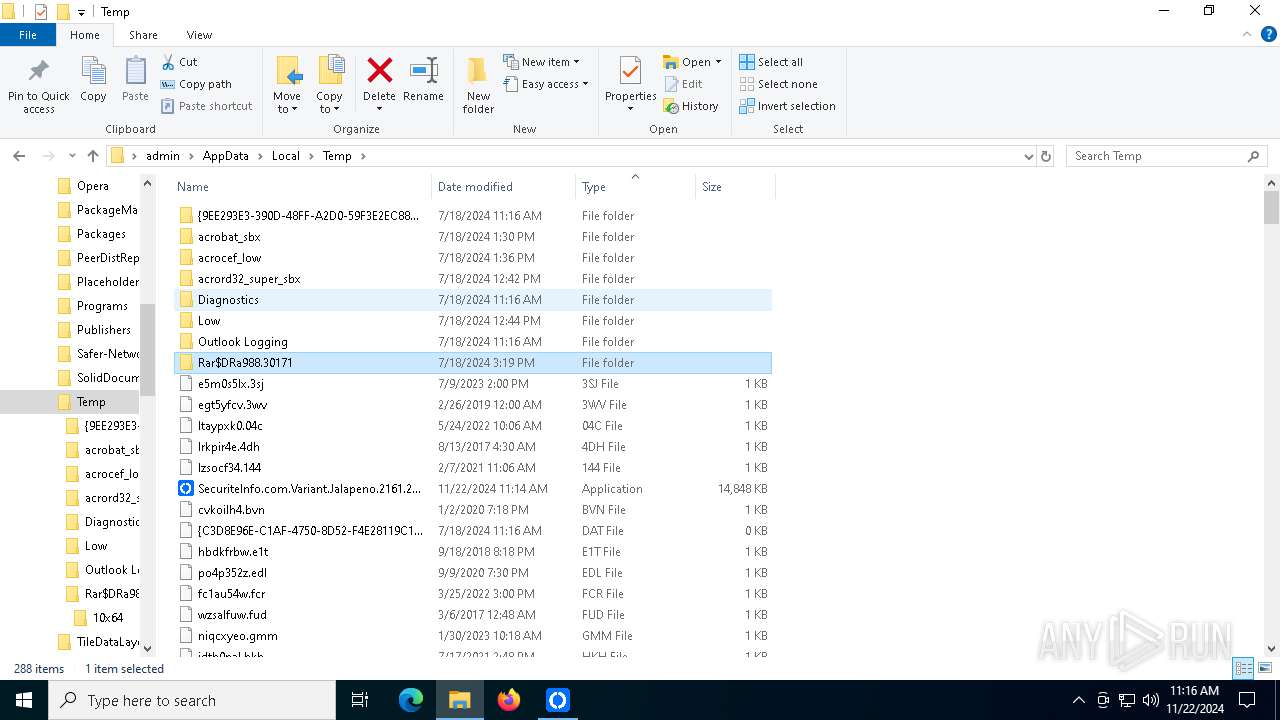
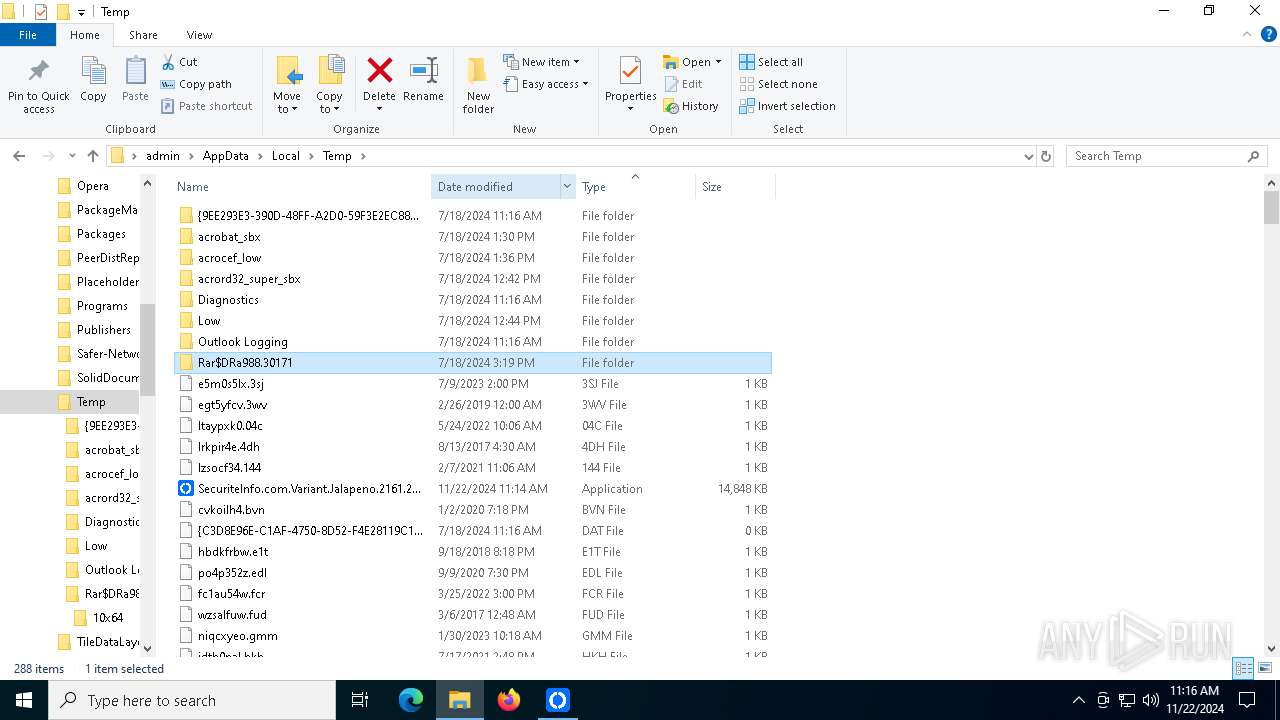
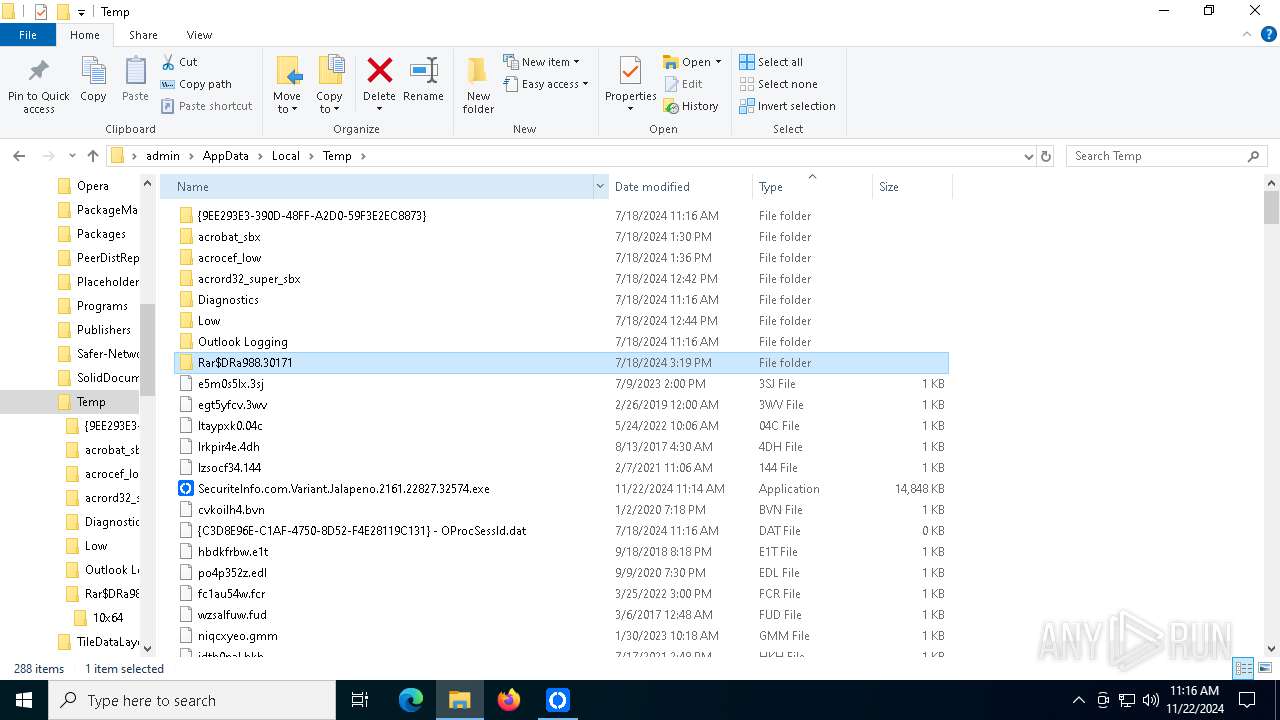
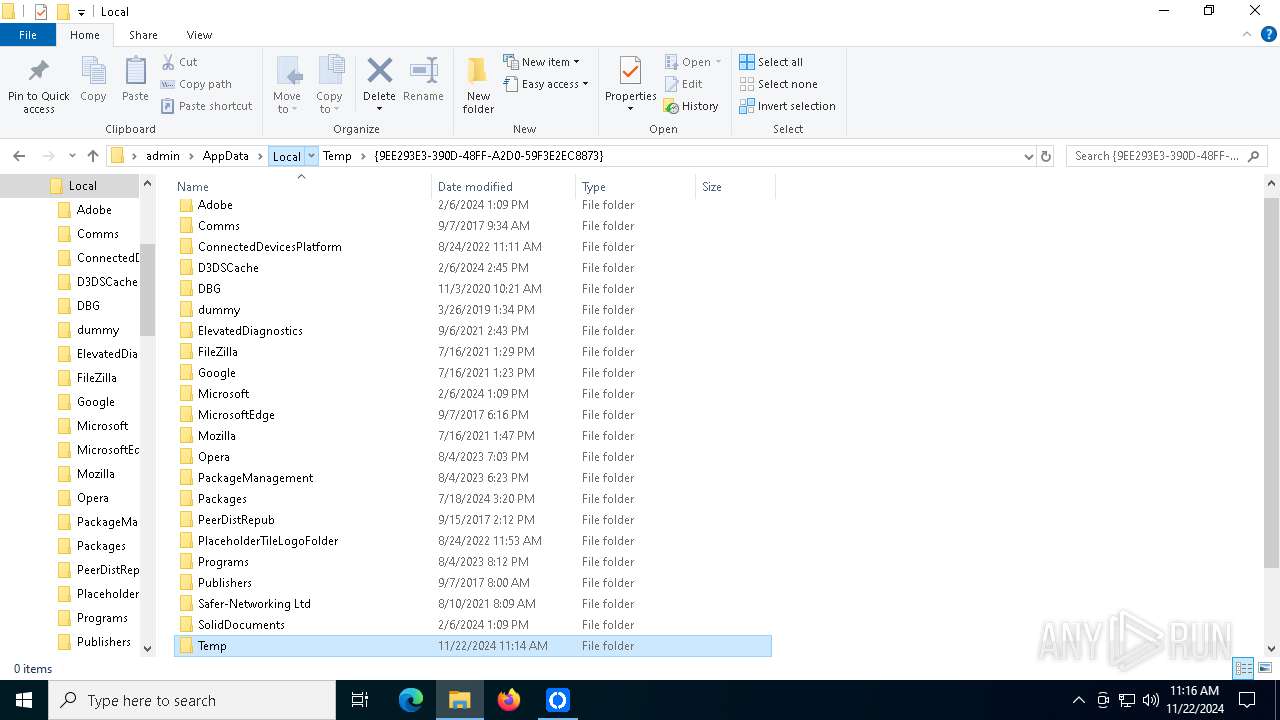
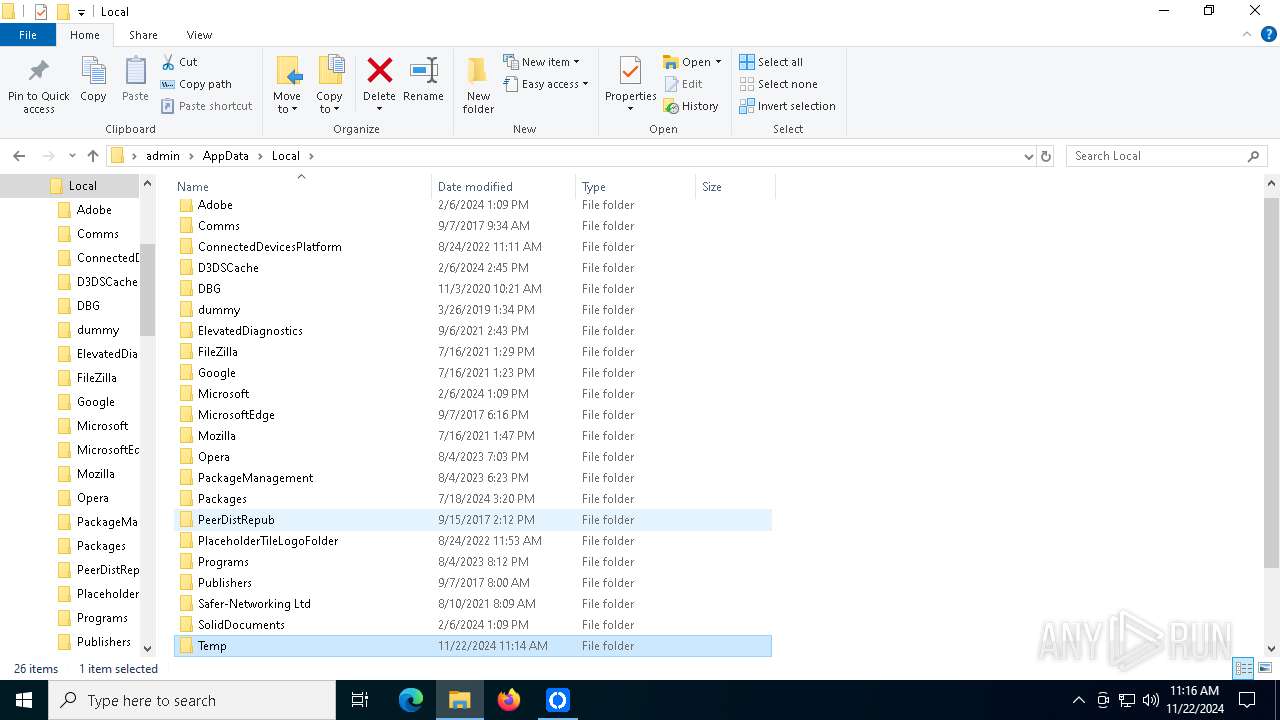
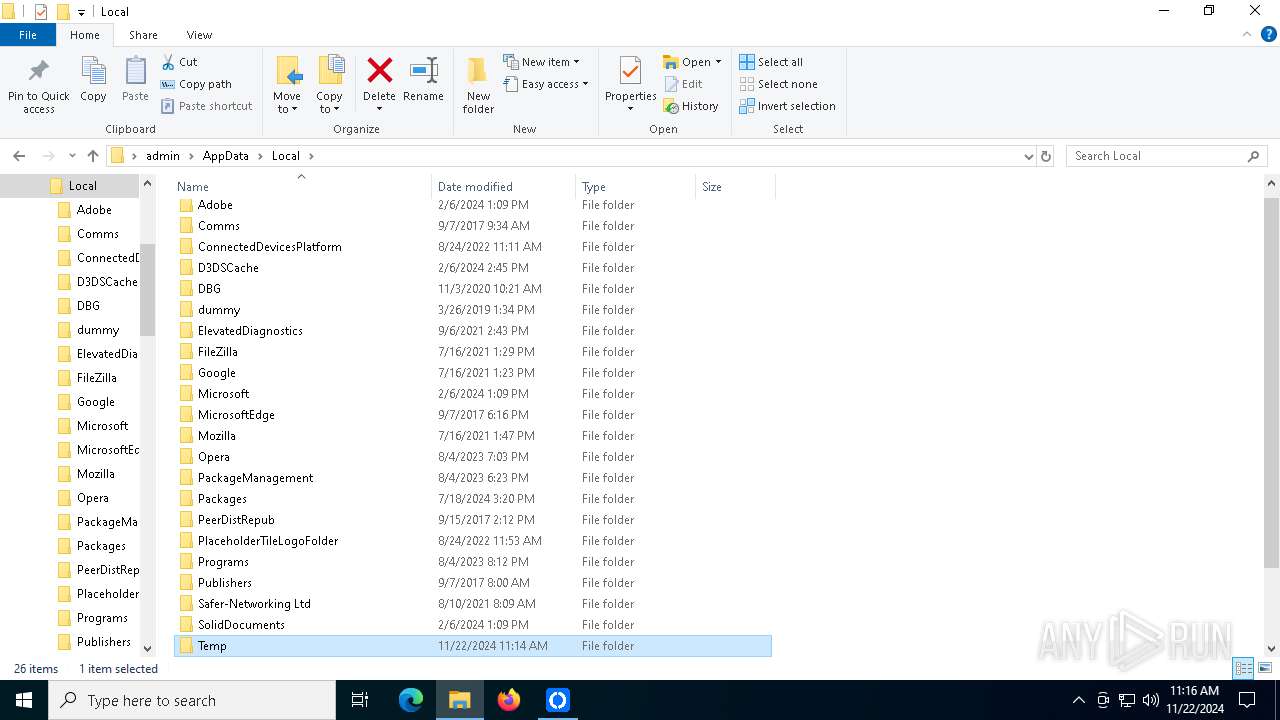
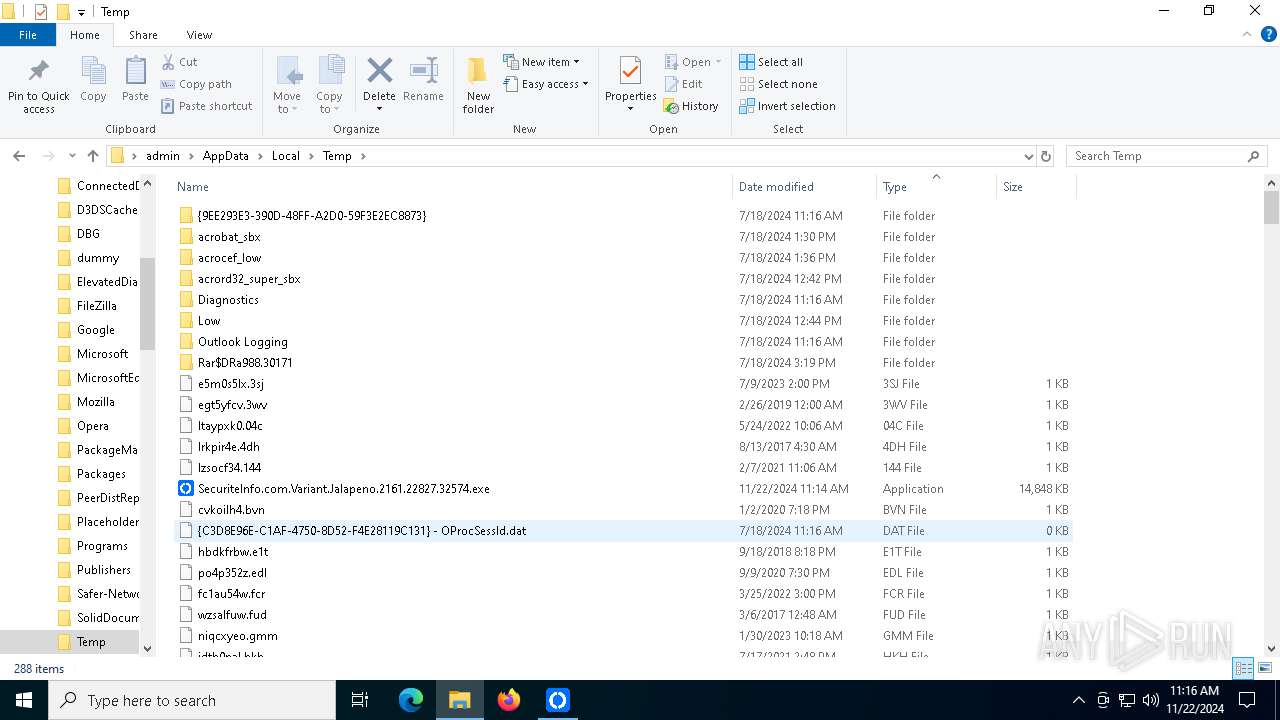
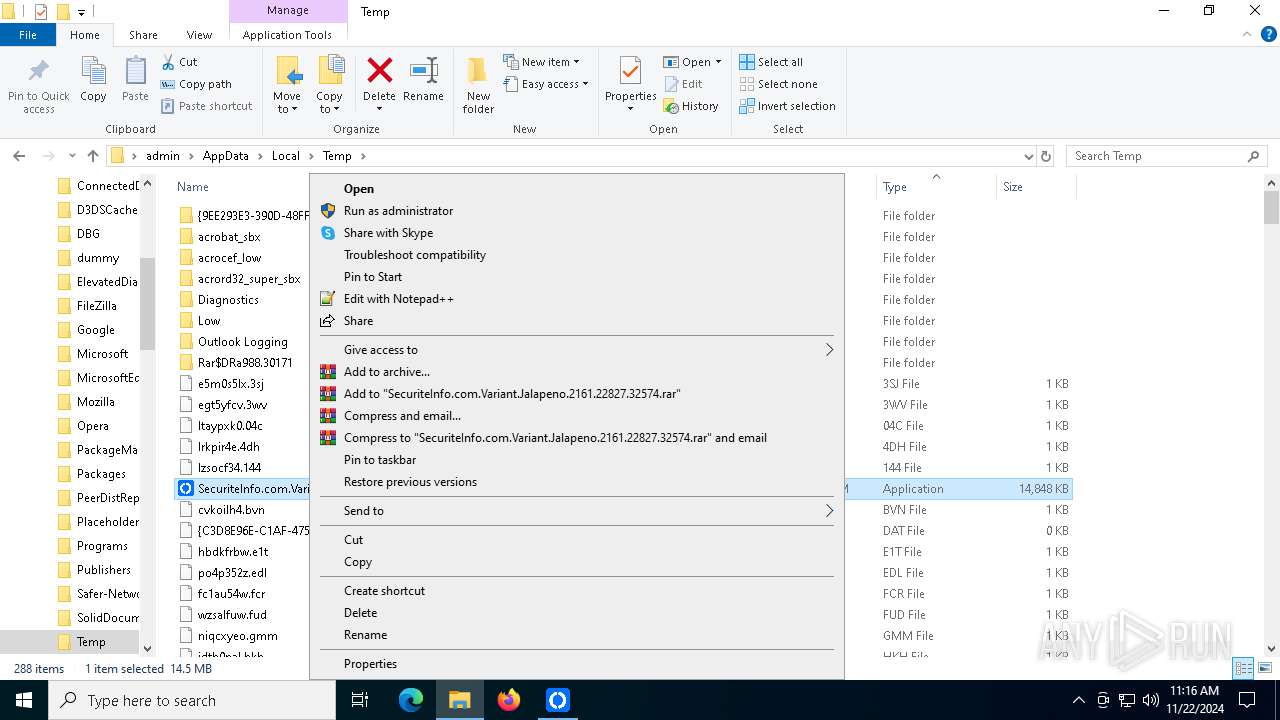
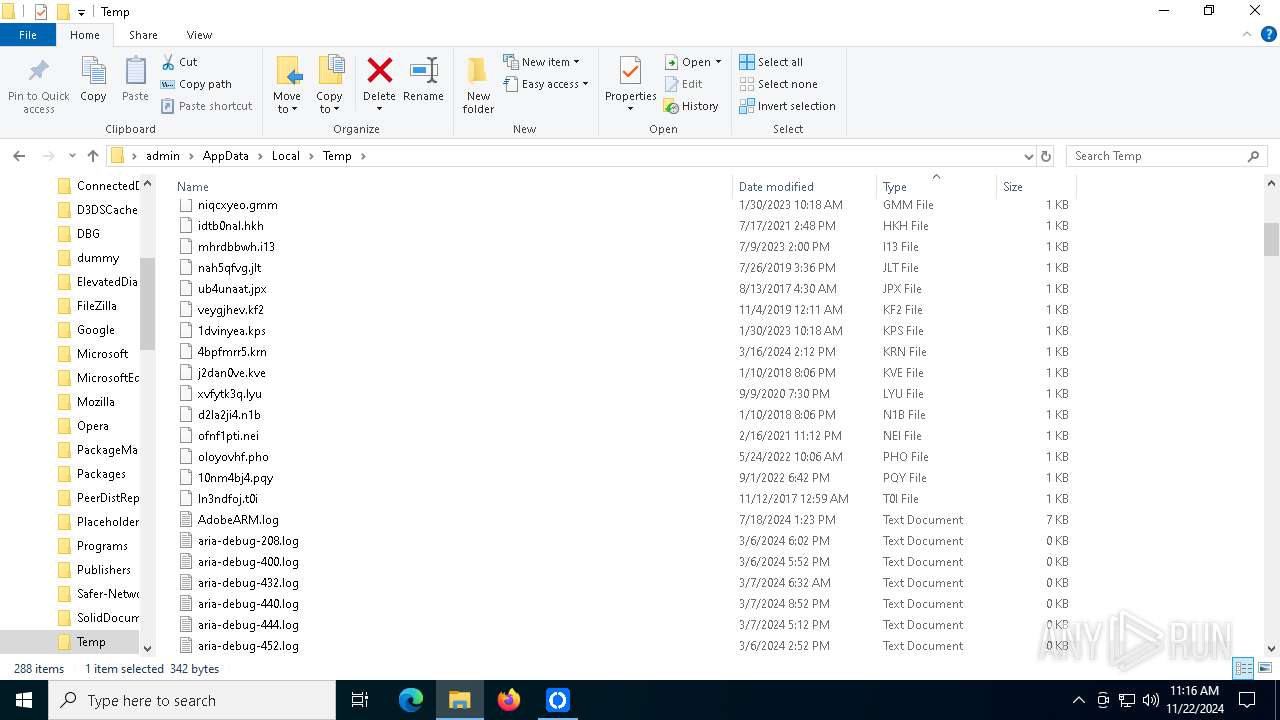
Executable content was dropped or overwritten
- SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe (PID: 4300)
Reads the date of Windows installation
- SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe (PID: 4300)
Connects to unusual port
- rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe (PID: 5012)
INFO
Checks supported languages
- SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe (PID: 4300)
- rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe (PID: 5012)
Reads the computer name
- SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe (PID: 4300)
- rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe (PID: 5012)
The process uses the downloaded file
- SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe (PID: 4300)
Process checks computer location settings
- SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe (PID: 4300)
Reads the machine GUID from the registry
- rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe (PID: 5012)
Application based on Rust
- rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe (PID: 5012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:07:29 09:22:50+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 15193600 |
| InitializedDataSize: | 10240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe7f47e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | rustdesk_package |
| FileVersion: | 1.0.0.0 |
| InternalName: | rustdesk_package.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | rustdesk_package.exe |
| ProductName: | rustdesk_package |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
122
Monitored processes
4
Malicious processes
2
Suspicious processes
0
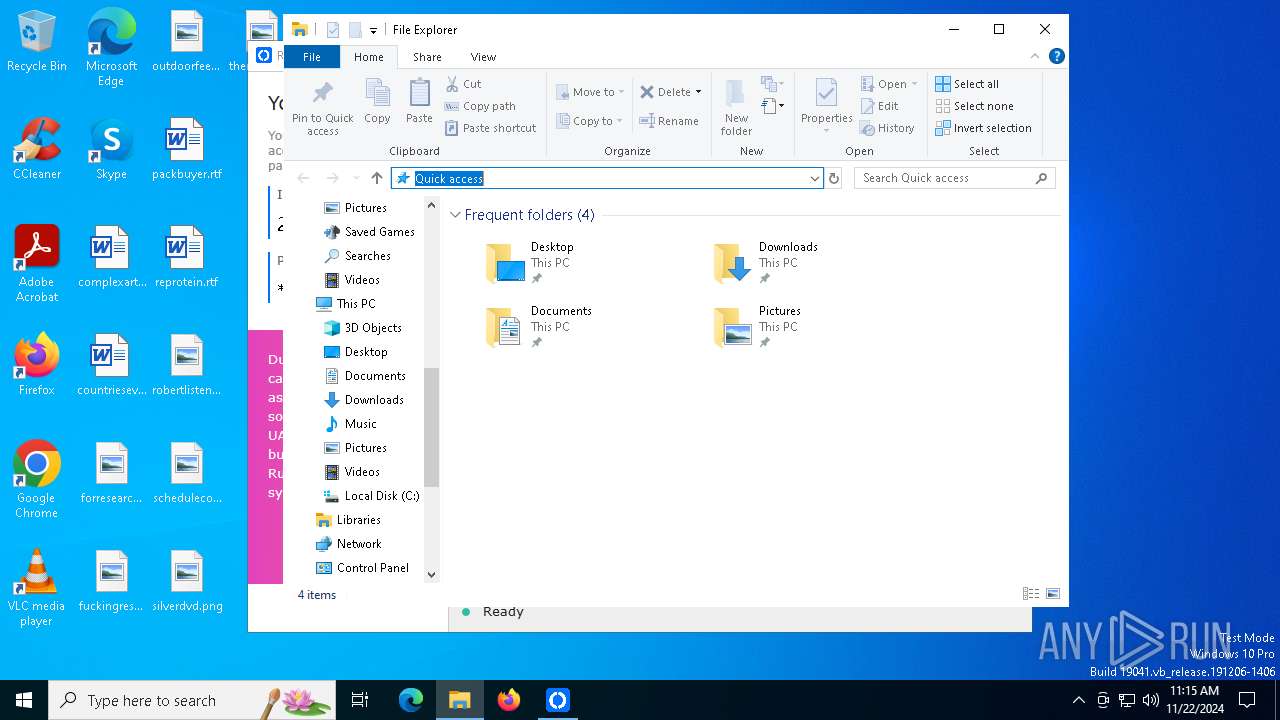
Behavior graph
Click at the process to see the details
Process information
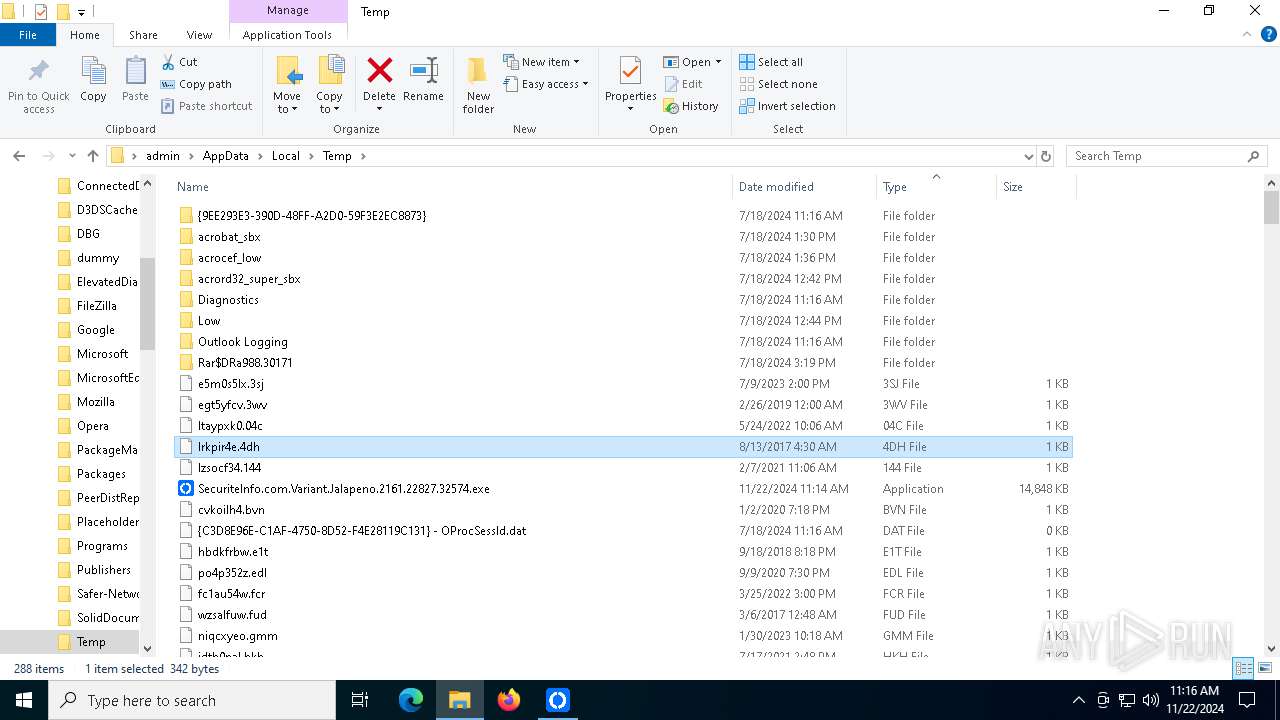
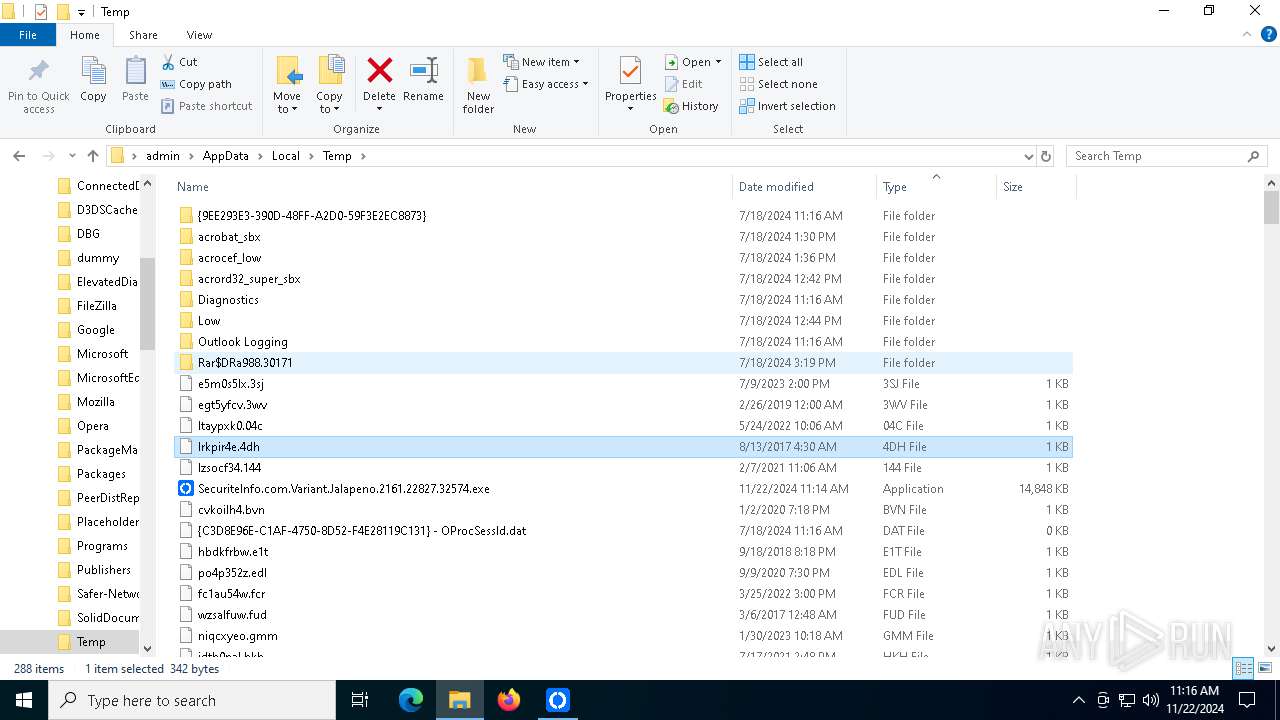
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2796 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
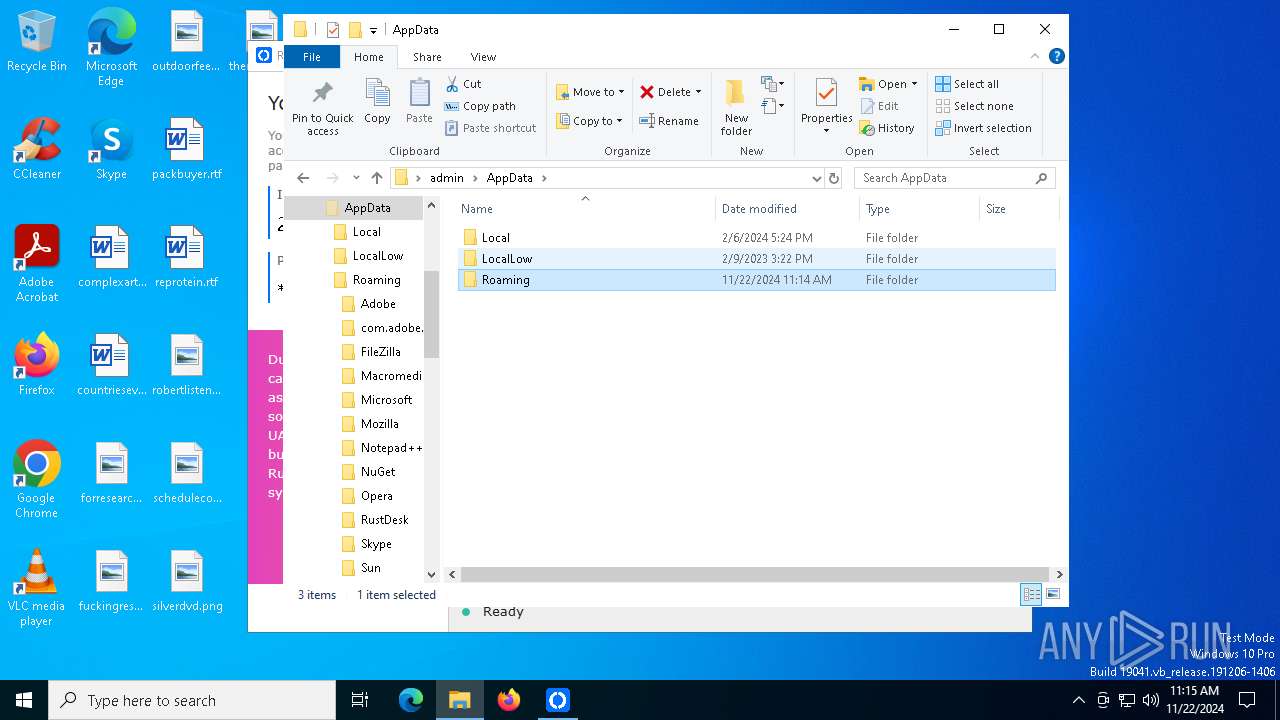
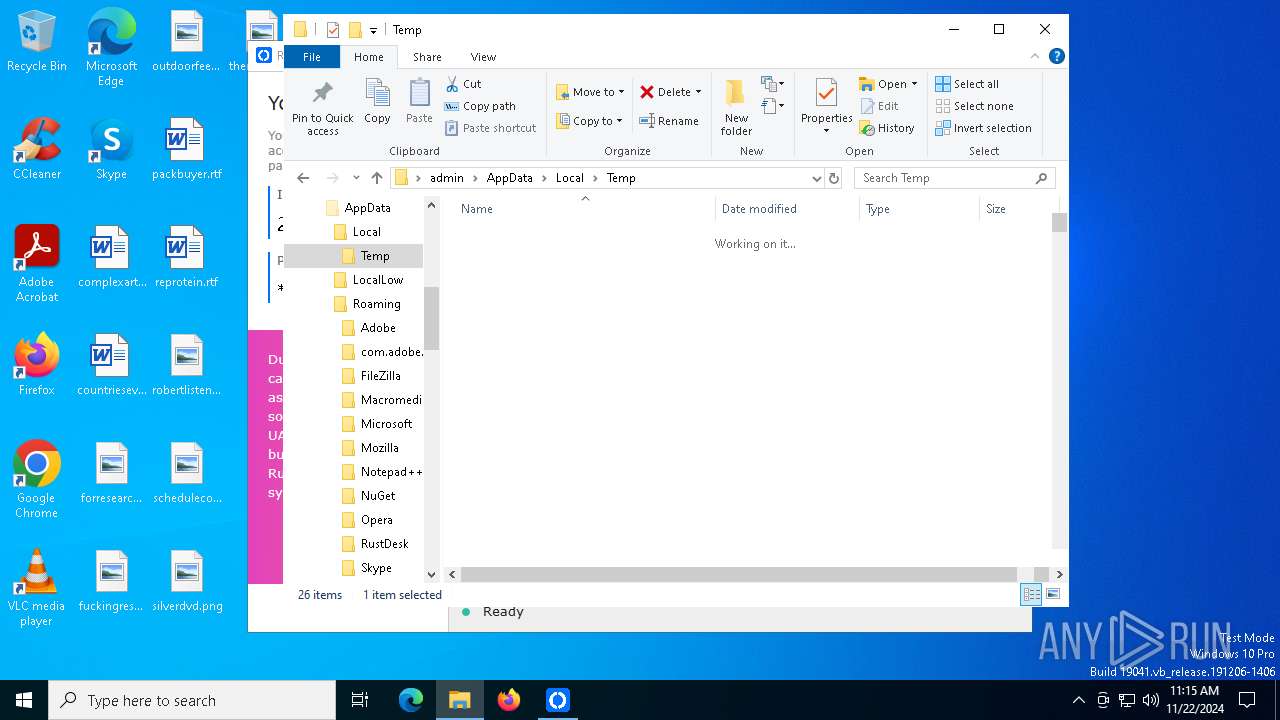
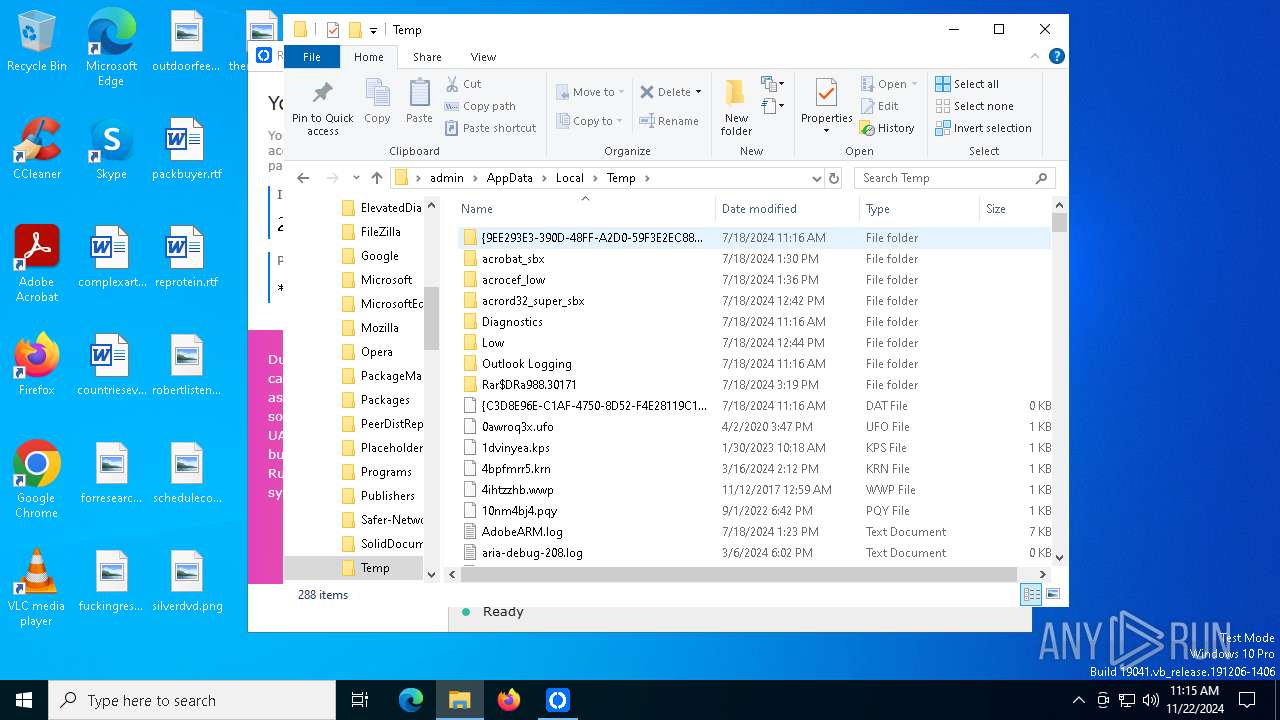
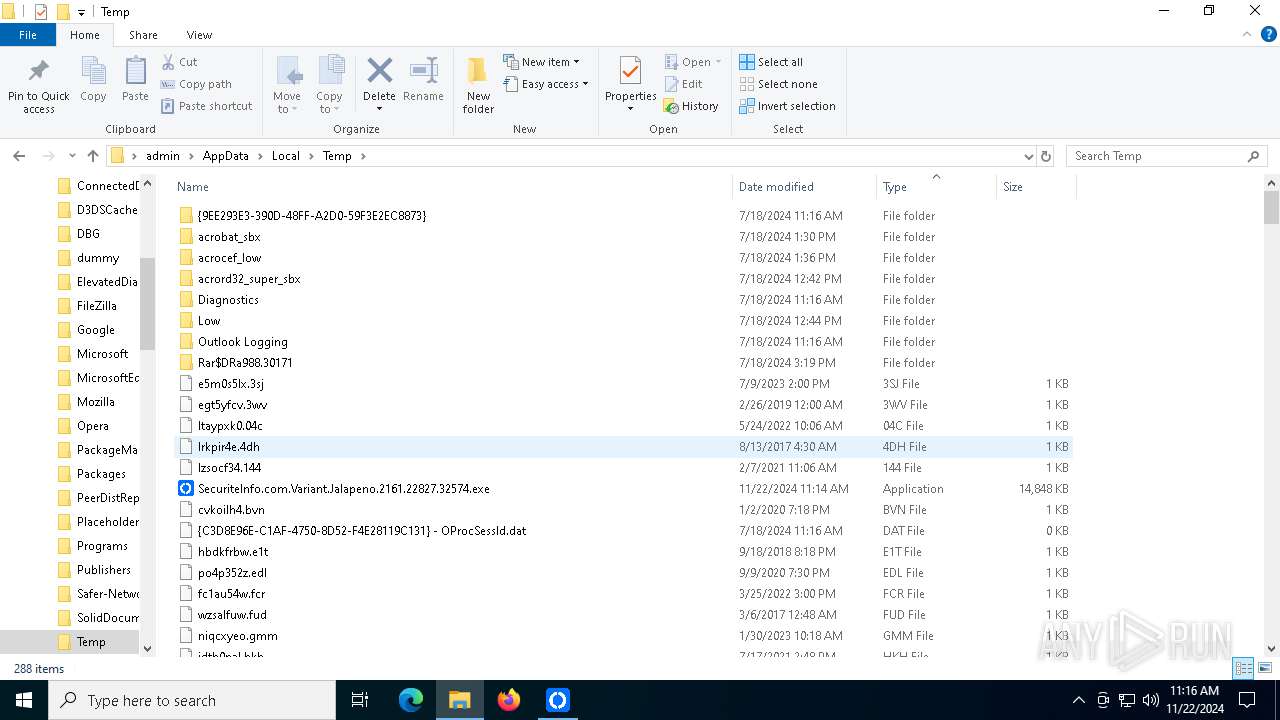
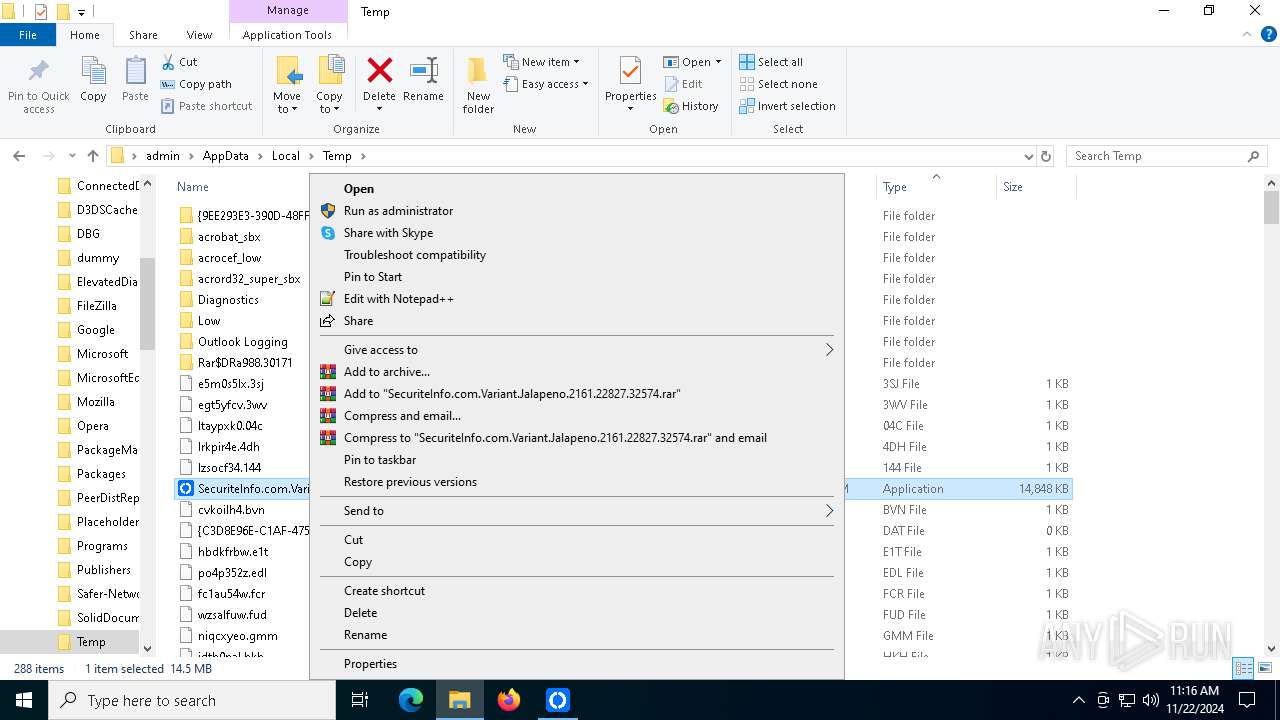
| 4300 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: rustdesk_package Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
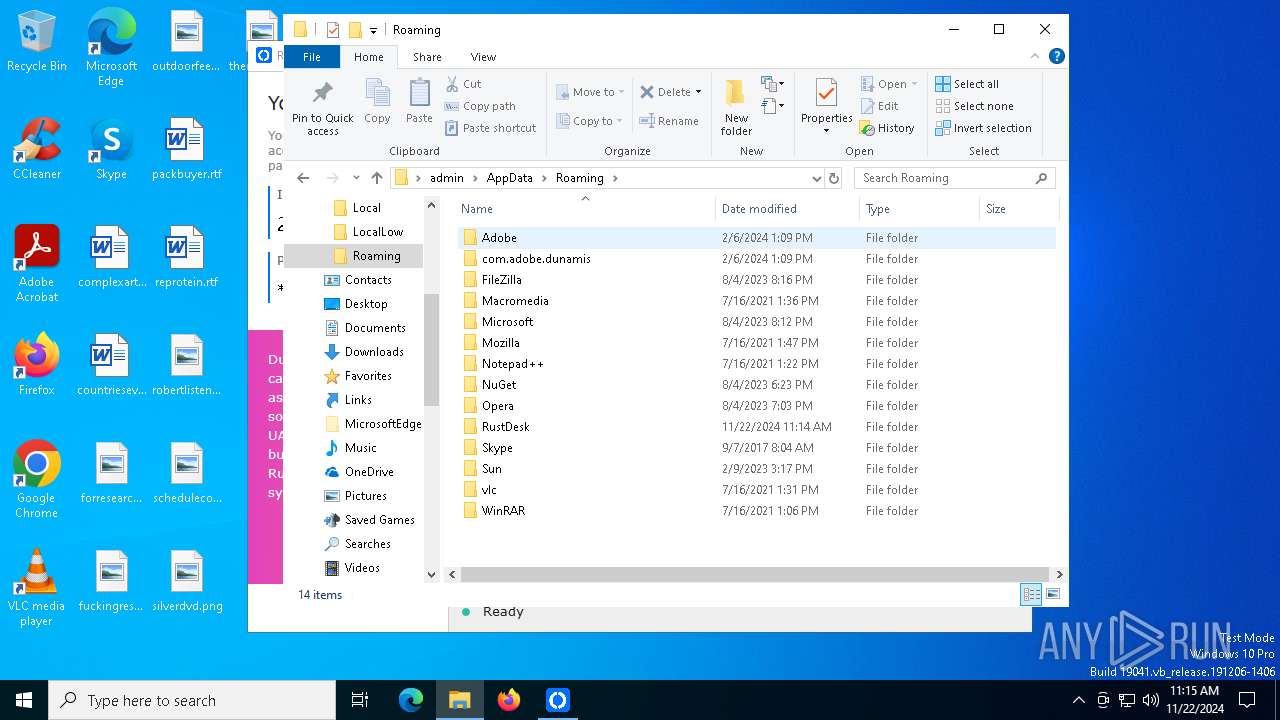
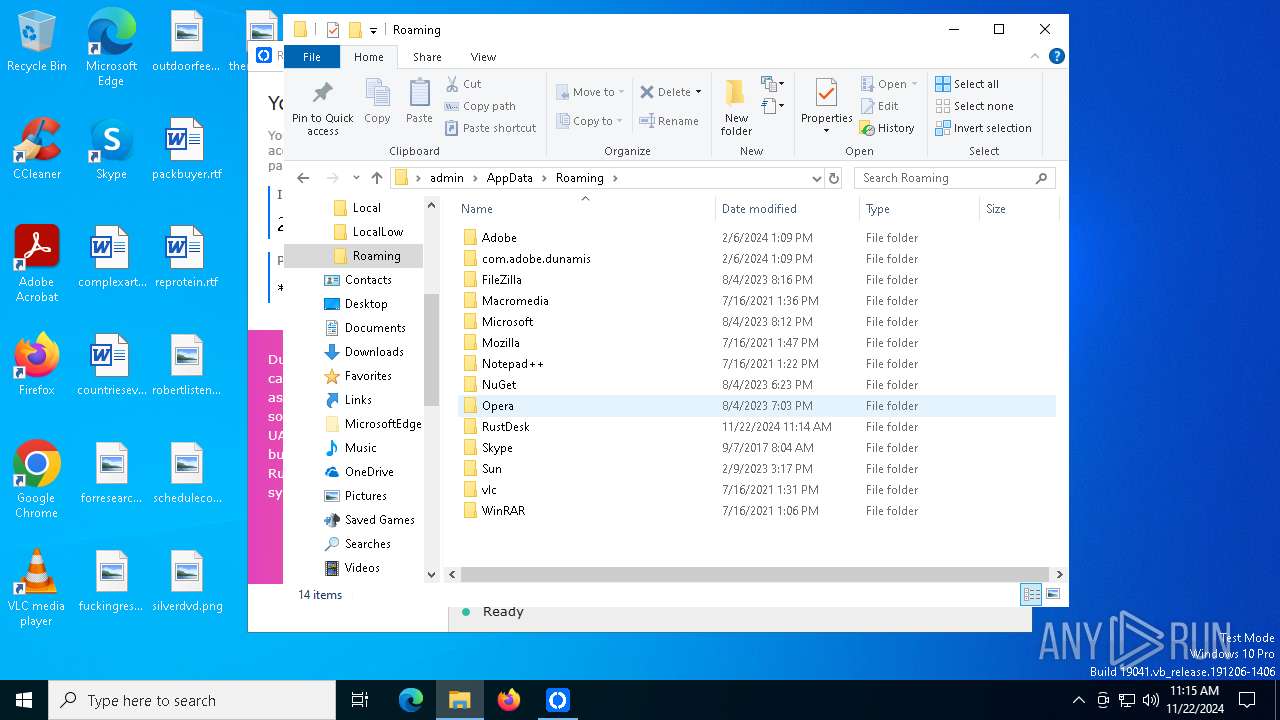
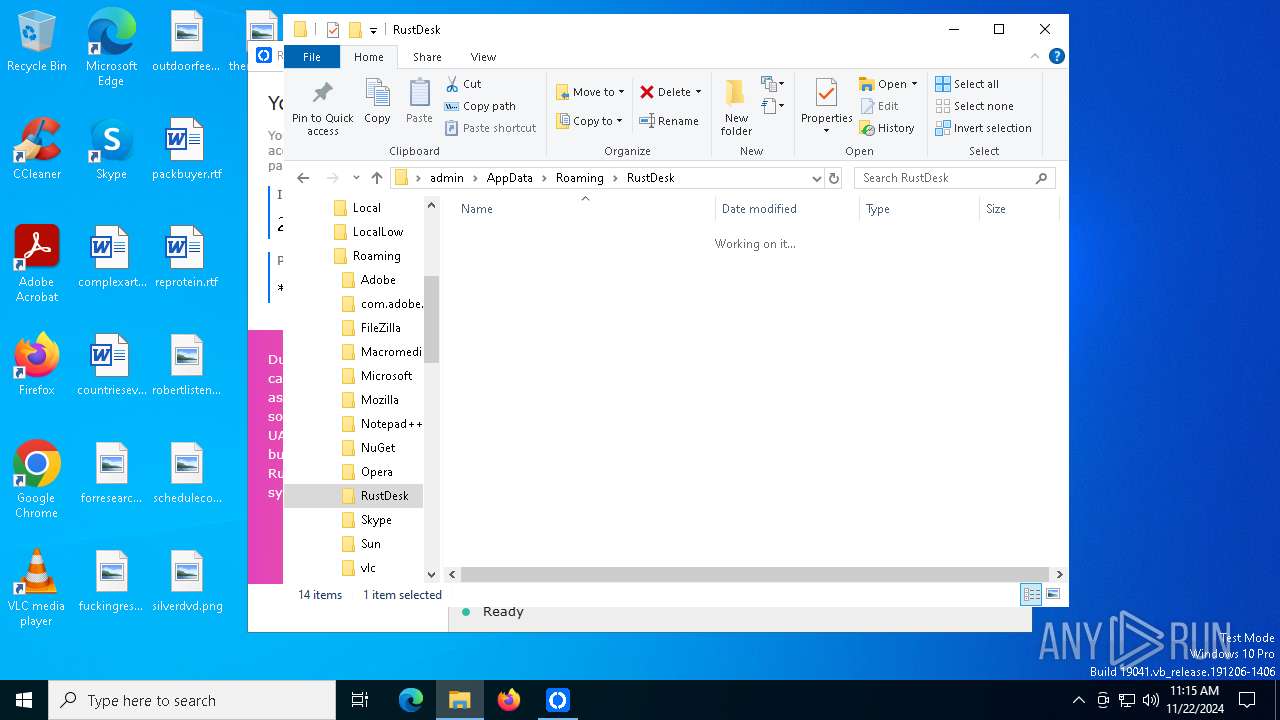
| 5012 | "C:\Users\admin\AppData\Roaming\RustDesk\rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe" | C:\Users\admin\AppData\Roaming\RustDesk\rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RustDesk Version: 1.1.9 Modules
| |||||||||||||||
| 6208 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
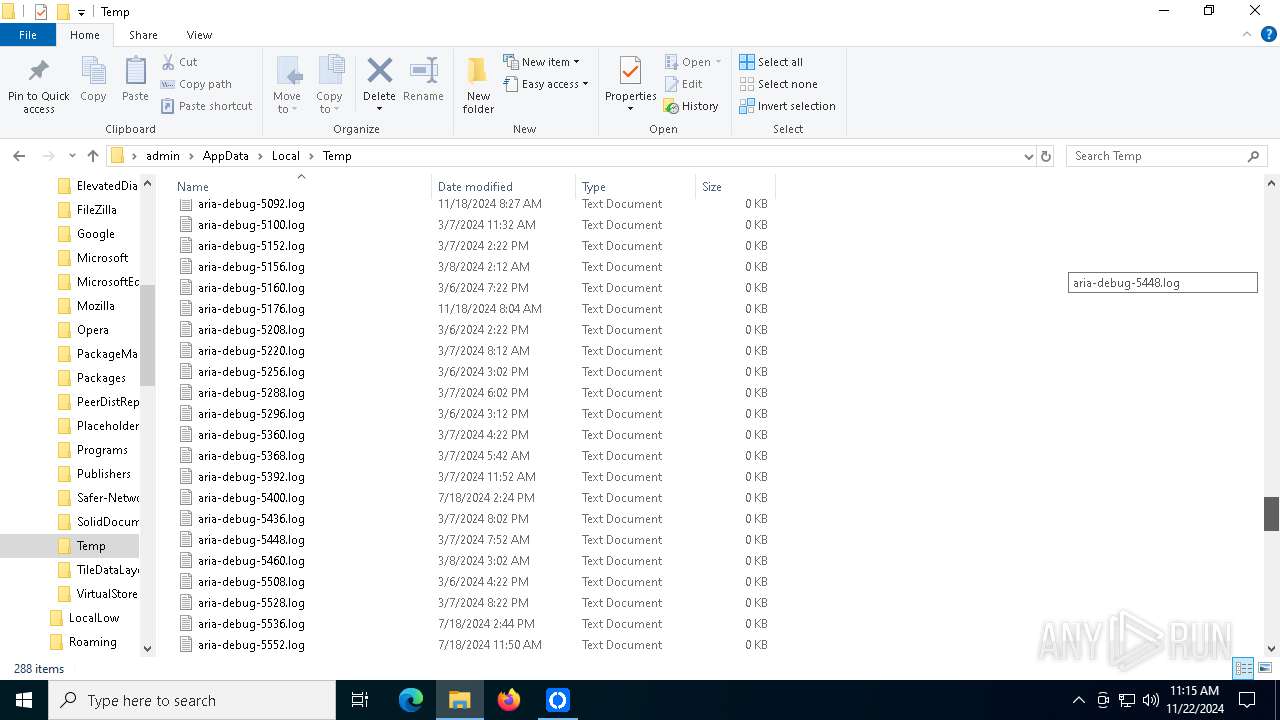
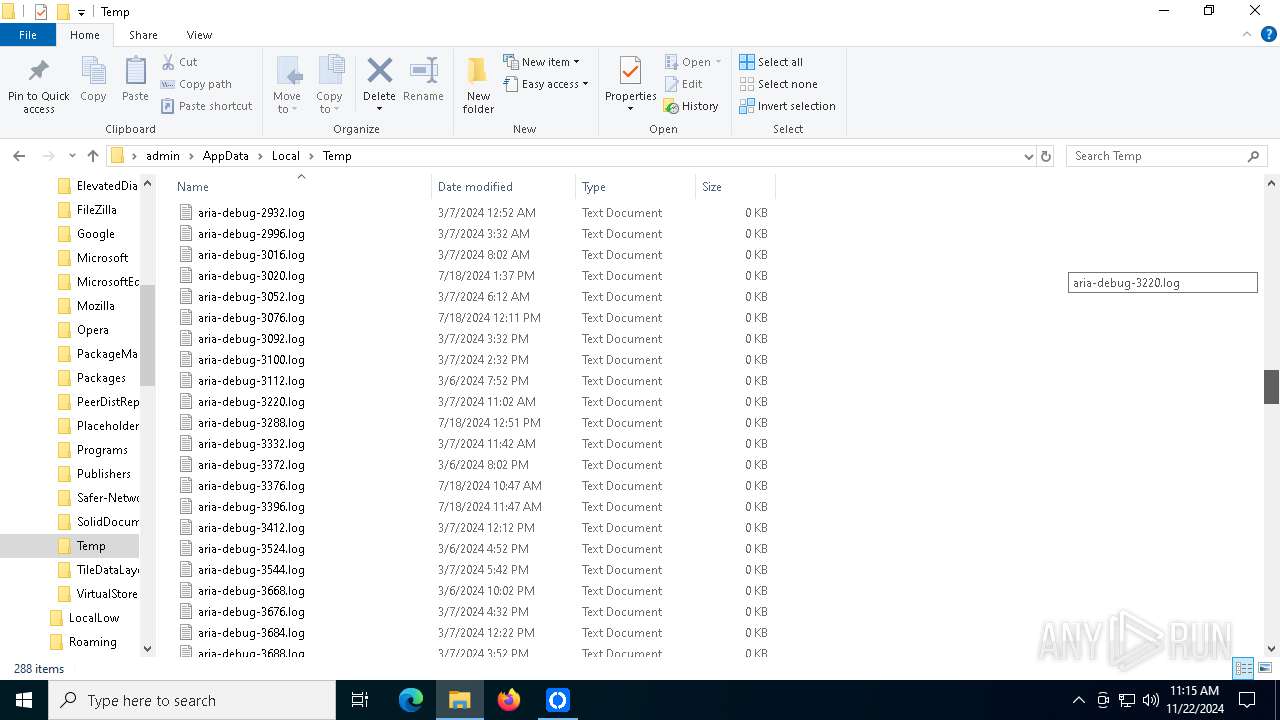
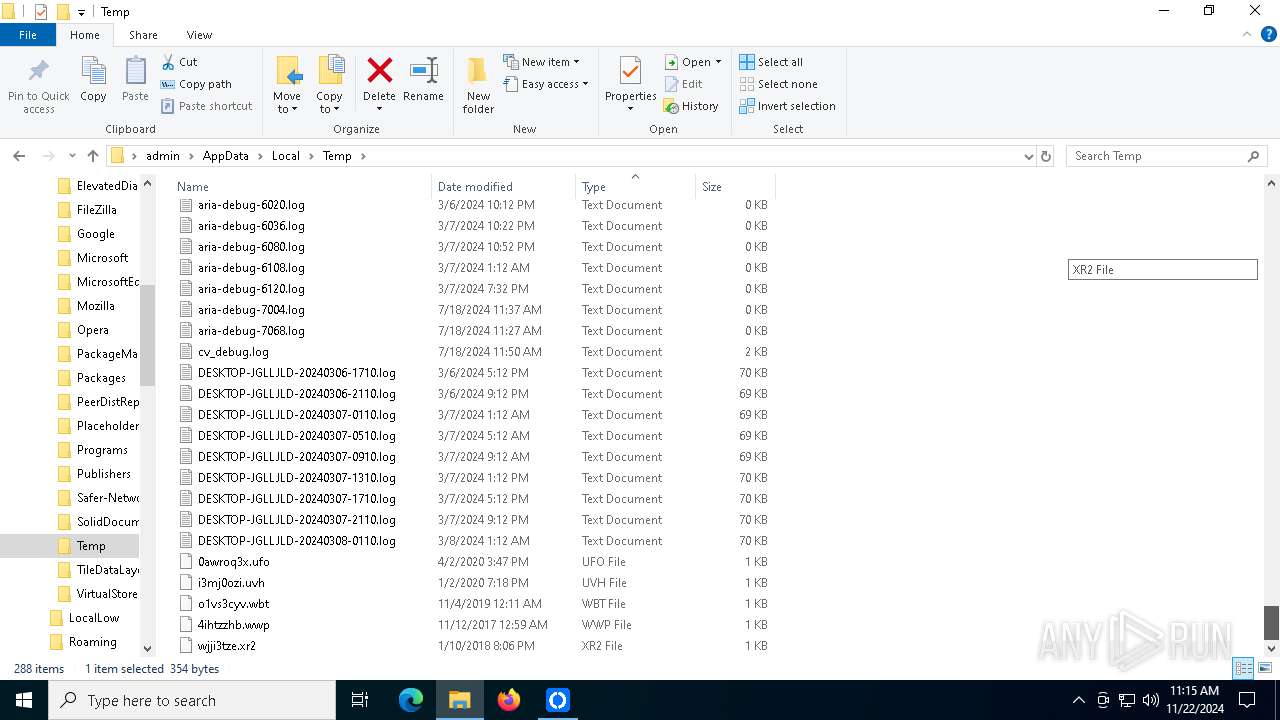
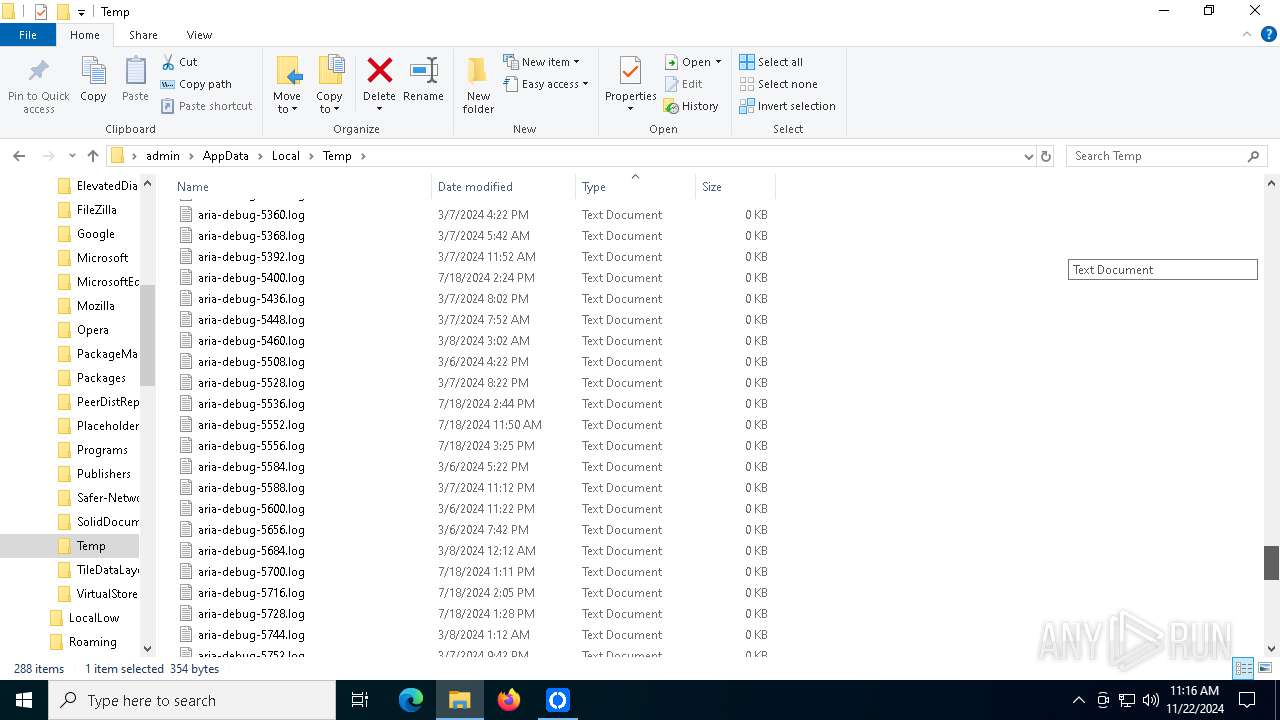
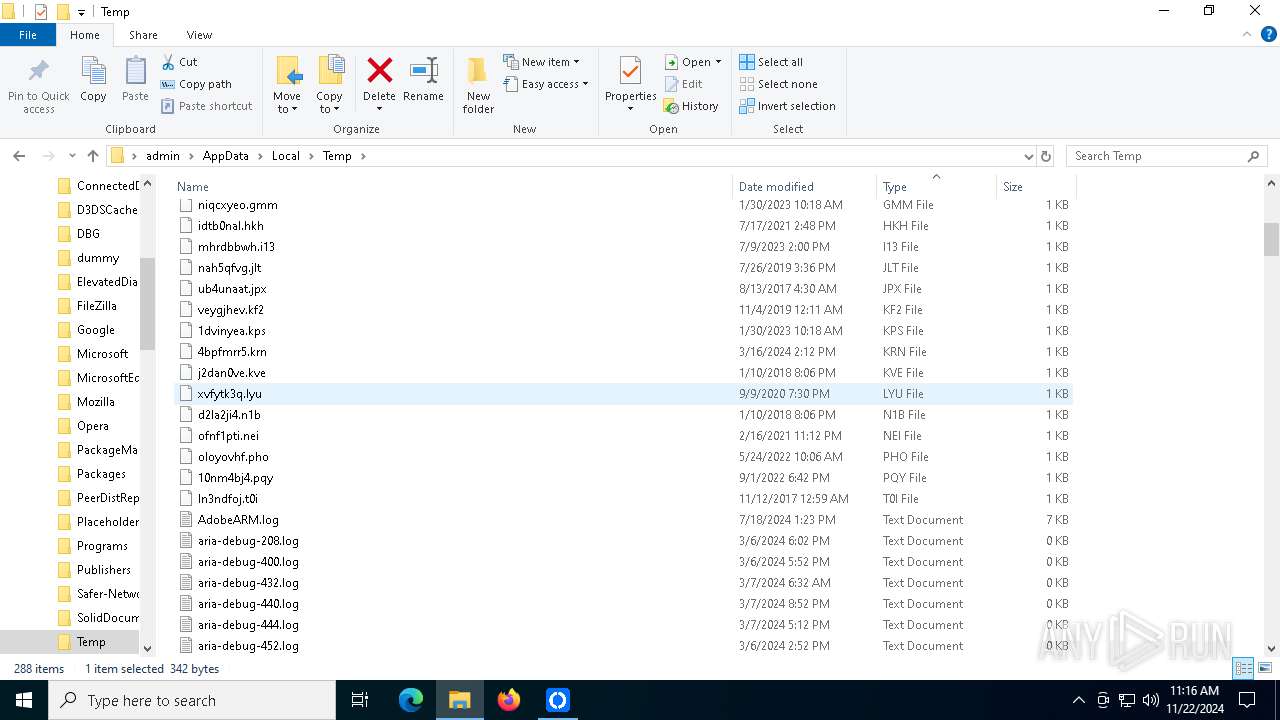
Total events
730
Read events
730
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk_local.5012_ThreadId(1)_1732274096942214800 | text | |
MD5:FE15184A9910E06F5A5BD76A0C982DE7 | SHA256:E930F4AFAAA9573D22938FDC00B8FDF73ADBD1B82A20E1E0078E5FC2614168F7 | |||
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk2.5012_ThreadId(23)_1732274097139995300 | text | |
MD5:DFF5B098268866CC8344A19EEE0811CA | SHA256:C4D4CF2713250E7645669A1D67A1AE1F5E266C83329F3BD3D5FB819622F3919D | |||
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk.toml | text | |
MD5:6AA983BC7FE8B7CF3B69418B182A542A | SHA256:935190DDD9A2A8CD27D77CA613E174585DE0EF07FA6DA3EA115EECB593AD5B89 | |||
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk2.5012_ThreadId(9)_1732274096823065900 | text | |
MD5:7E65E186C1FD1E4B9634F8D54CDE92D3 | SHA256:828AC47651ACDAA5632E40D79FC4DB0F7B87E487976DC68E7680BE93424EC1AE | |||
| 4300 | SecuriteInfo.com.Variant.Jalapeno.2161.22827.32574.exe | C:\Users\admin\AppData\Roaming\RustDesk\rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | executable | |
MD5:B85D3C97069FC306A172DF4E03F6354E | SHA256:0DDC782574CB7D109477365D7B98535A52057373A7325A8A6104F95C6E7A61DD | |||
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk.5012_ThreadId(14)_1732274097951404800 | text | |
MD5:0AD2F93915984D77E72AD216B16A4C12 | SHA256:A862DE30C8D656E4DAE0428C36855030FBD7B544D6C5521CAE2707D0AF46641D | |||
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk.5012_ThreadId(14)_1732274096902885600 | text | |
MD5:6AA983BC7FE8B7CF3B69418B182A542A | SHA256:935190DDD9A2A8CD27D77CA613E174585DE0EF07FA6DA3EA115EECB593AD5B89 | |||
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk.5012_ThreadId(14)_1732274096922628600 | text | |
MD5:925BFDD2BCF555149FAD2E2F5F3BA4C5 | SHA256:23CBA294D268C43A81342D66F6484D07382058DAF22A8C9130A66E0A500122A0 | |||
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk2.toml | text | |
MD5:7E65E186C1FD1E4B9634F8D54CDE92D3 | SHA256:828AC47651ACDAA5632E40D79FC4DB0F7B87E487976DC68E7680BE93424EC1AE | |||
| 5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | C:\Users\admin\AppData\Roaming\RustDesk\config\RustDesk2.5012_ThreadId(10)_1732274096998493800 | text | |
MD5:87B48853BC278FADFC098FA6EDD14EDD | SHA256:69716A52DC7AB32B3A4383B7BBF30071B3D6F07B9D0C7936E9DA9CDDD25EF3DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
36
DNS requests
21
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6440 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6440 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
644 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4932 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | 193.232.152.78:21116 | rd.inlinegroup.ru | Ao Inline Group | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
rd.inlinegroup.ru |
| unknown |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | Misc activity | ET INFO RustDesk Check NAT Type |
5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | Misc activity | ET INFO RustDesk Check NAT Type |
5012 | rustdesk-host=rd.inlinegroup.ru,key=dvX1IfSm1JsVwllETsLPyVv4XSHJPxclbDjUulUs1nY=.exe | Misc activity | ET INFO RustDesk Get Software Update URL |