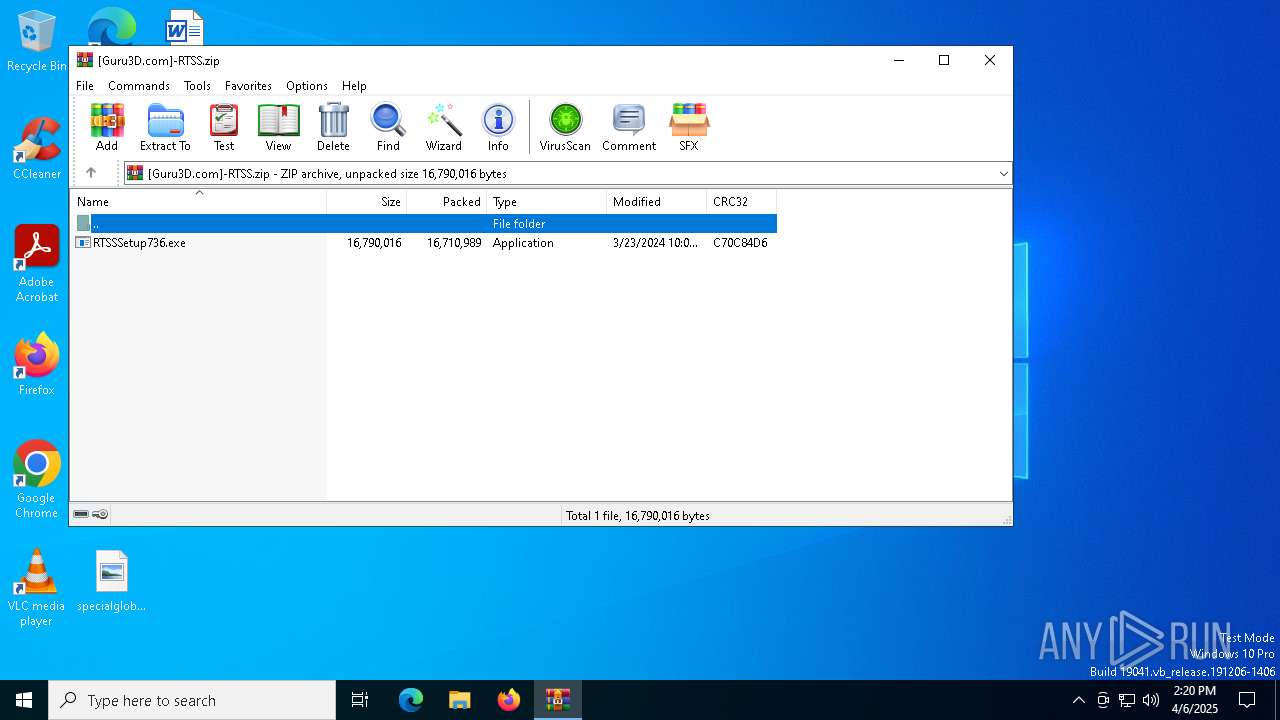
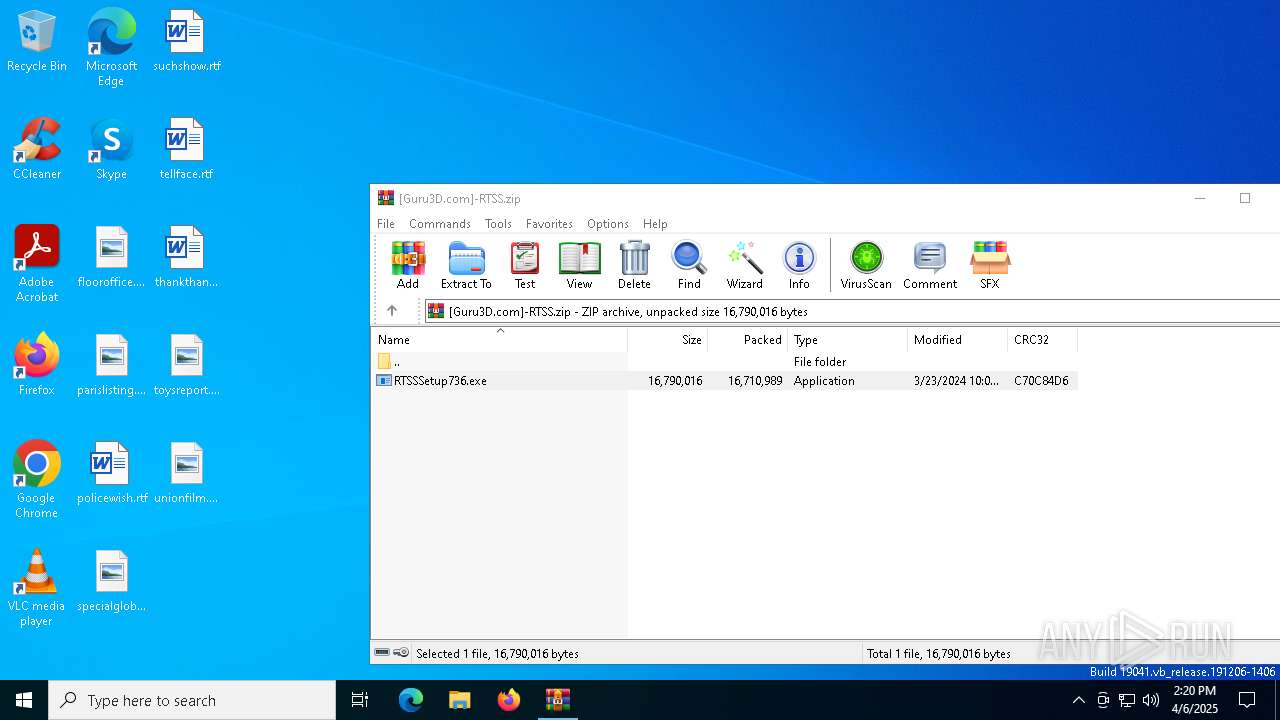
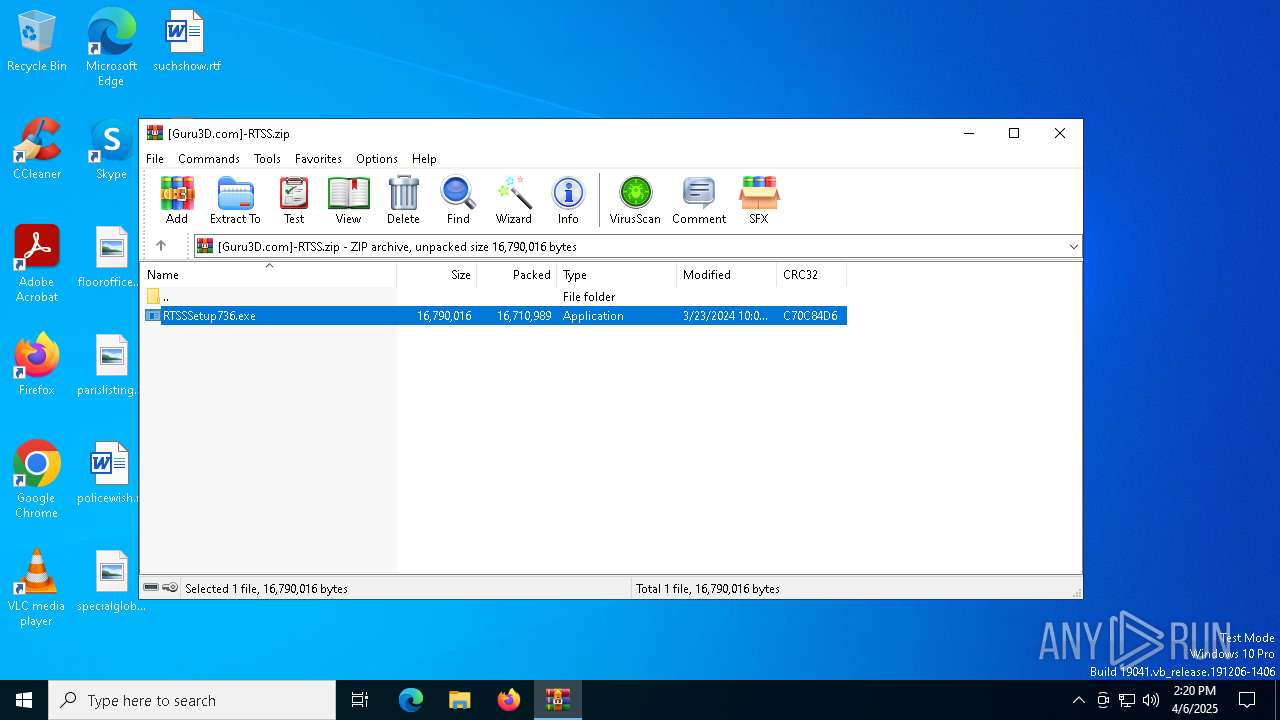
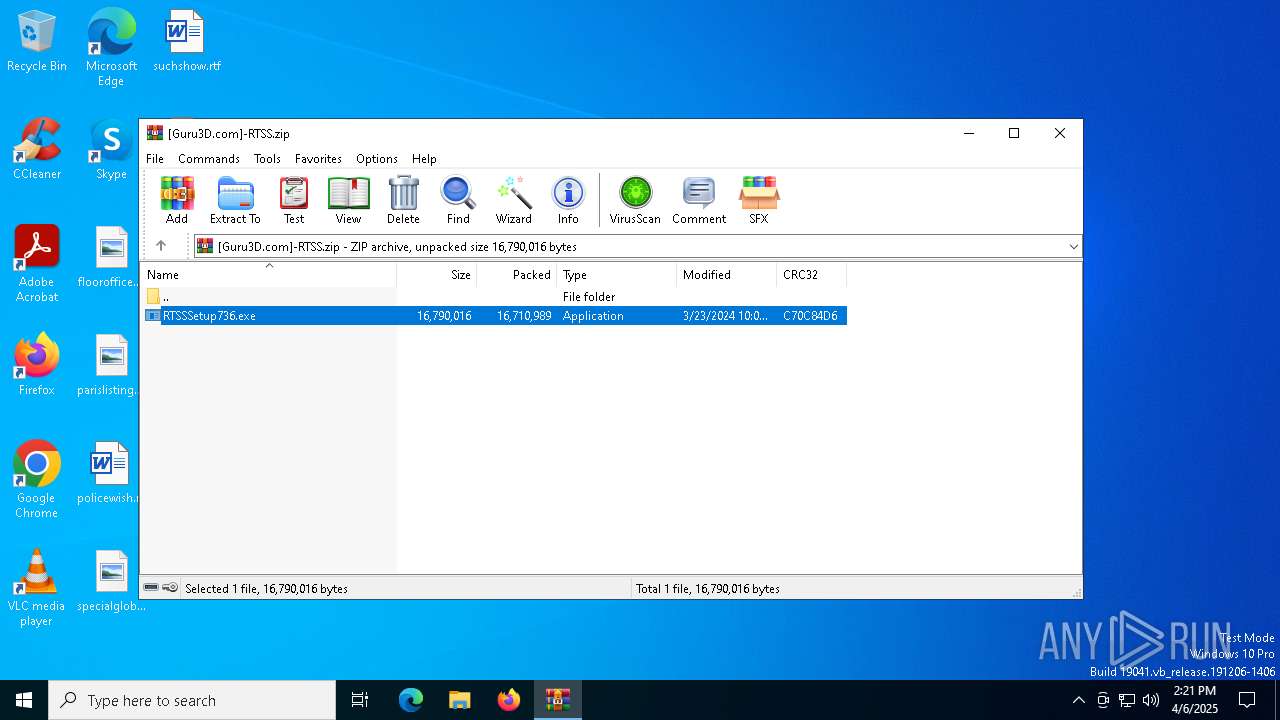
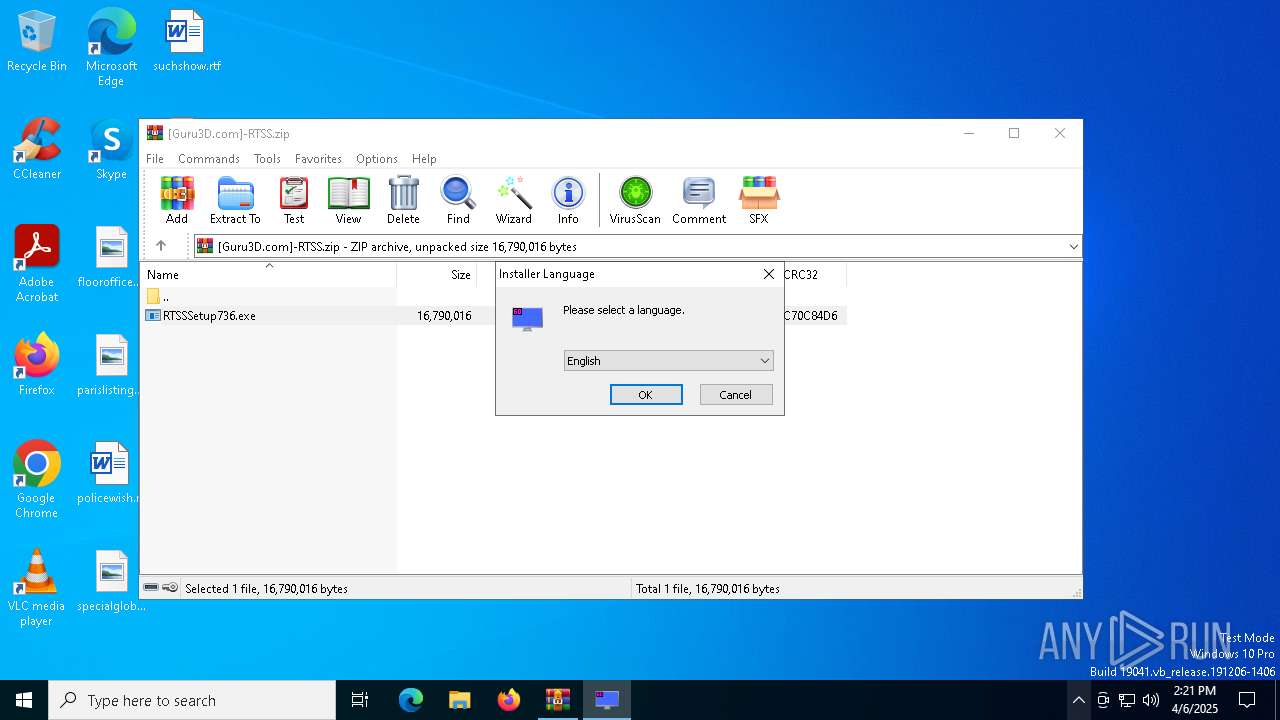
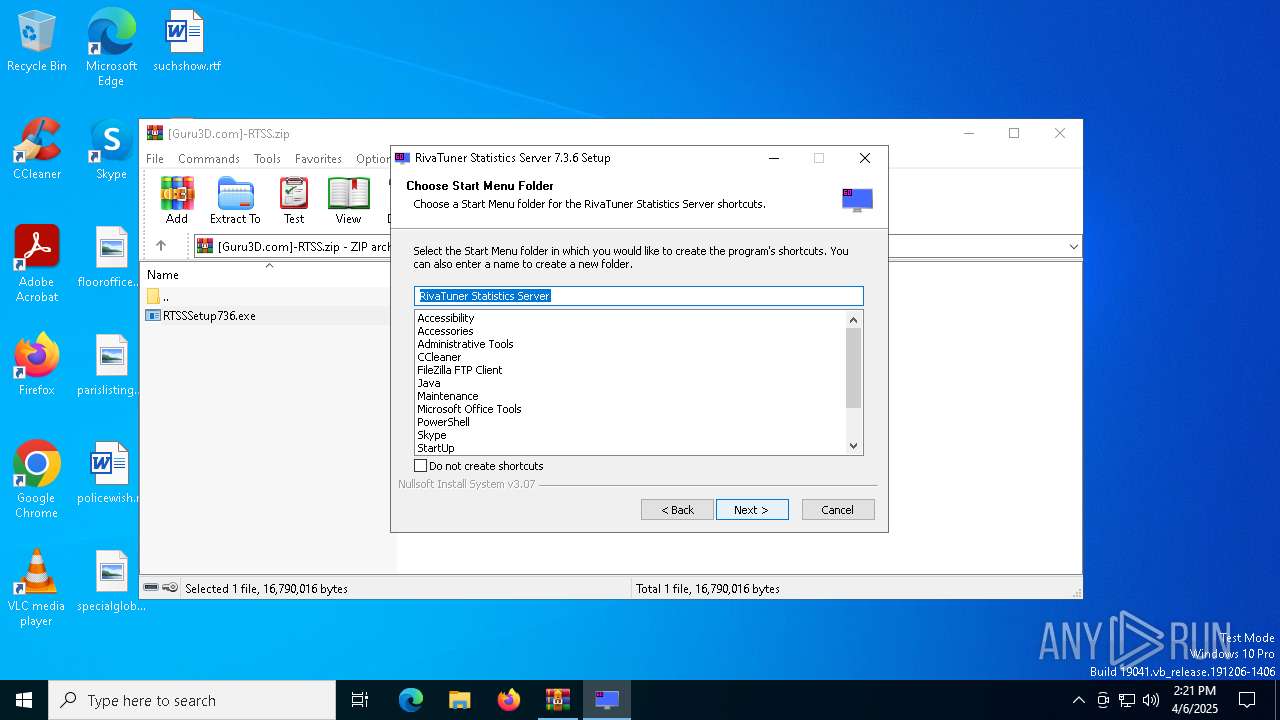
| File name: | [Guru3D.com]-RTSS.zip |
| Full analysis: | https://app.any.run/tasks/59bc7292-4a6e-4252-a2ec-d0d4d1bce744 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2025, 14:20:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 6127E45FB3202BE5675B1ADAD947F905 |
| SHA1: | 7DD8A12158649B37681490A7C5F16B818546B62A |
| SHA256: | E11FE1D98C2EE29A6E052EFA804FAA363774A09F8636073D0C81A7060DE1C09F |
| SSDEEP: | 98304:vDcP28p58u+mn6tiIsxbTCHgUkClFO7yo1YpsEL1v/M63kG+8O/I+LuPTN6uJmZN:/miDLRCGZoozCKwawkdj5T1Q6M8EFL |
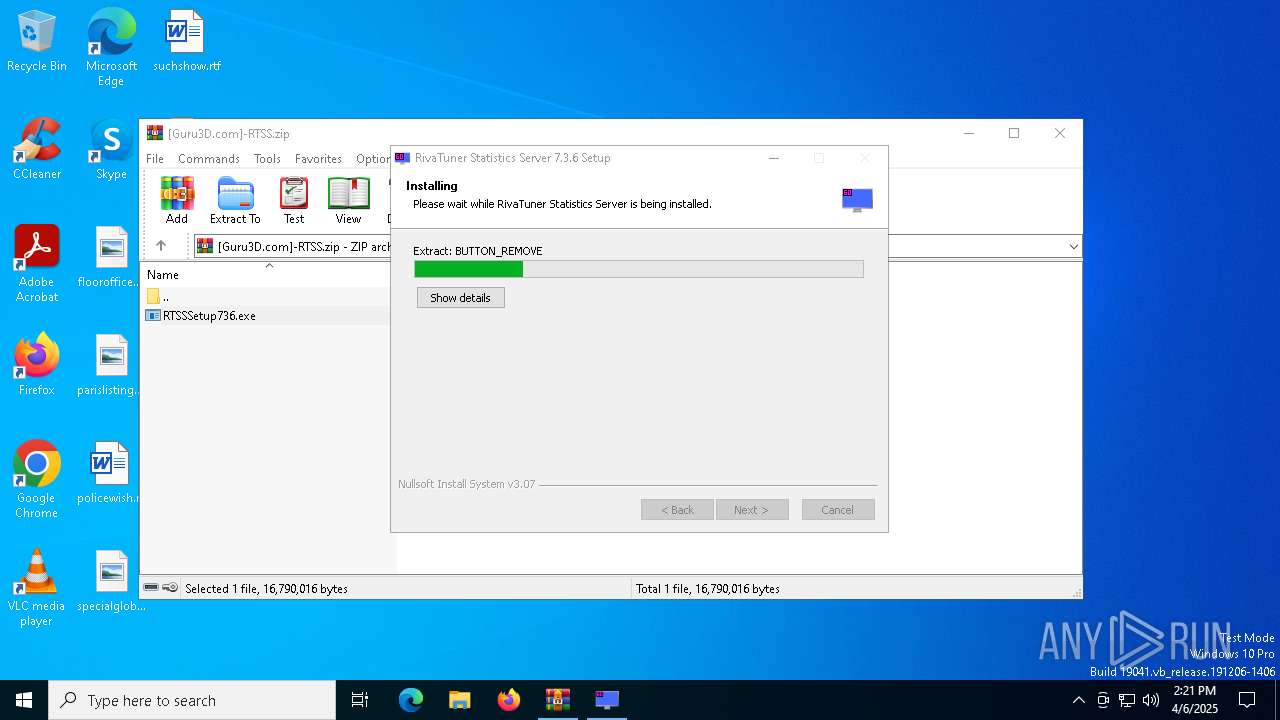
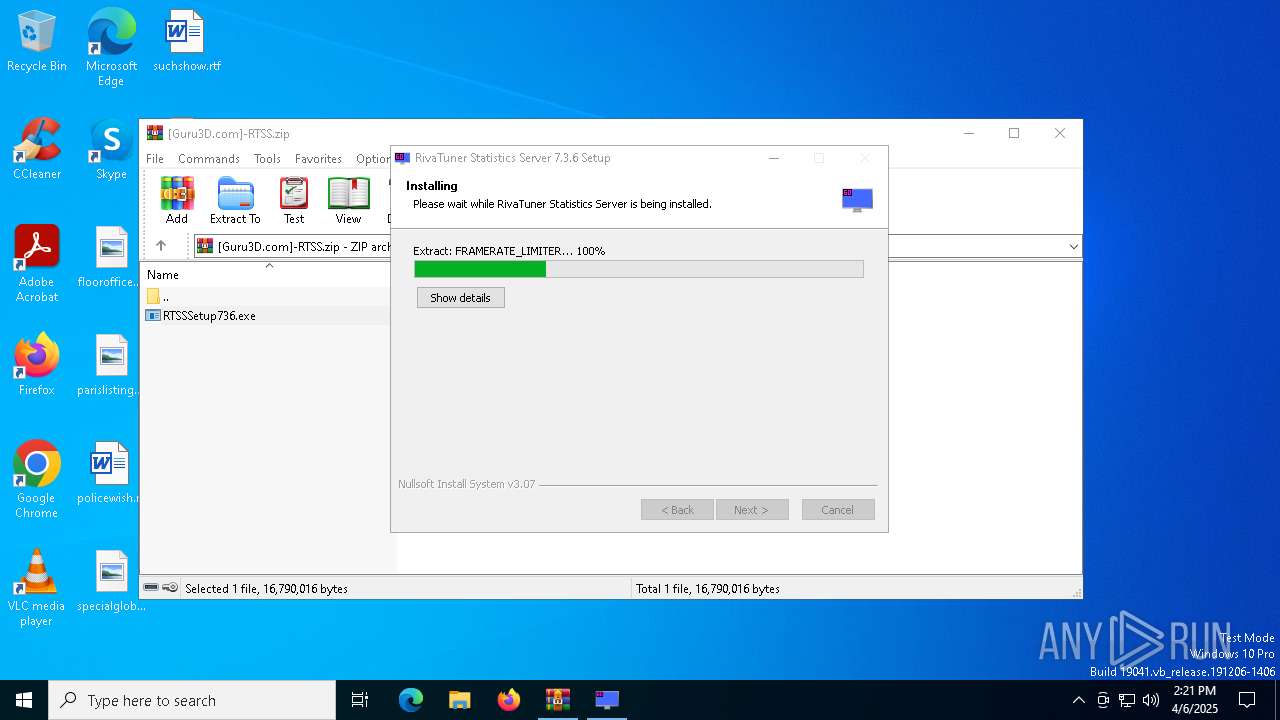
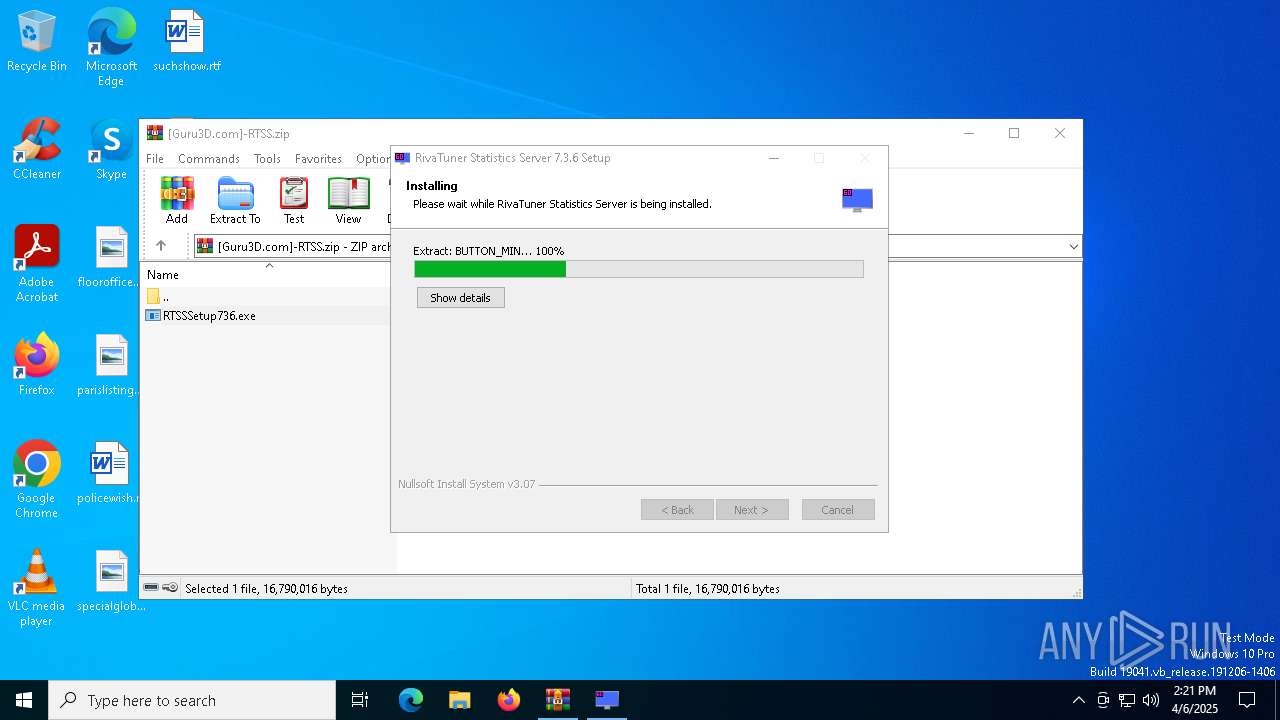
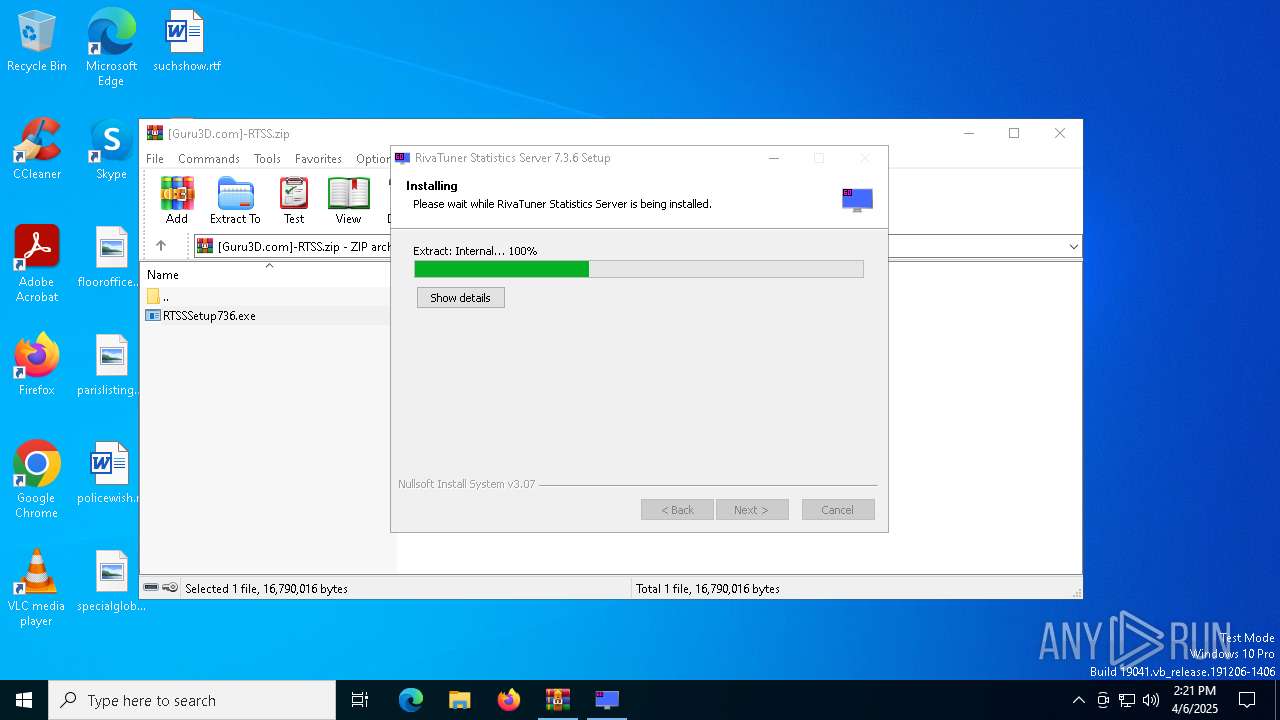
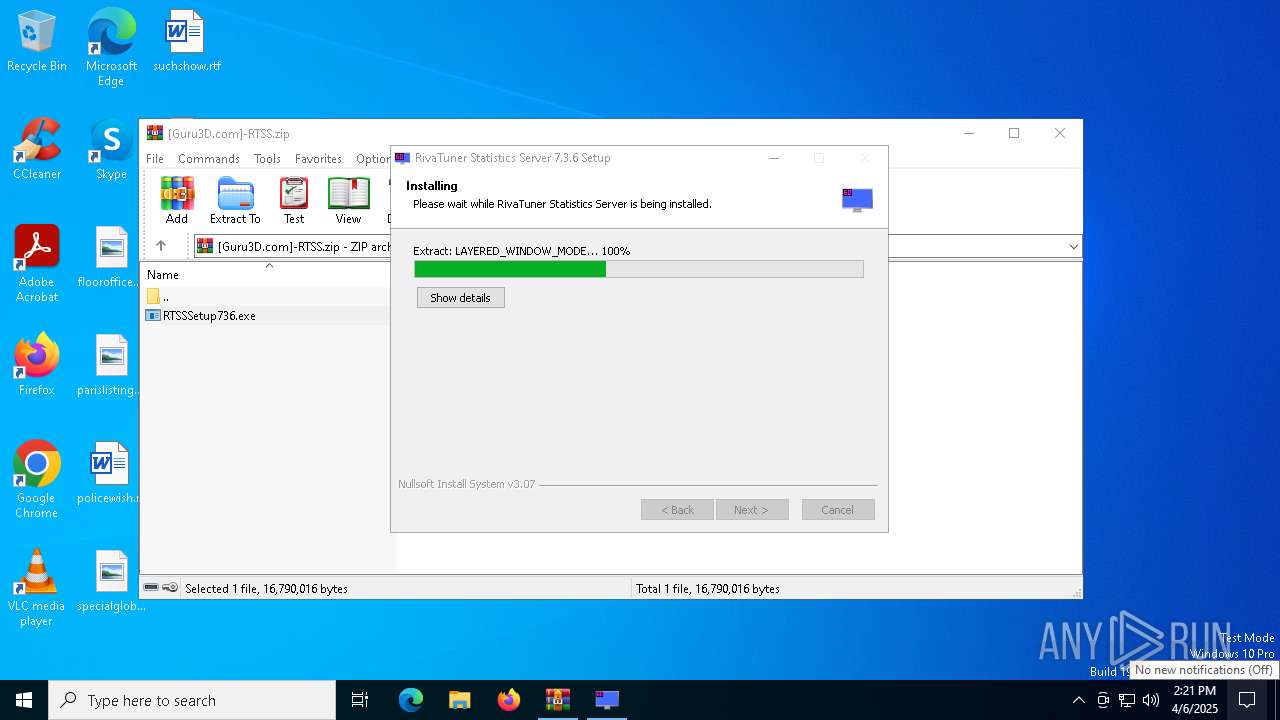
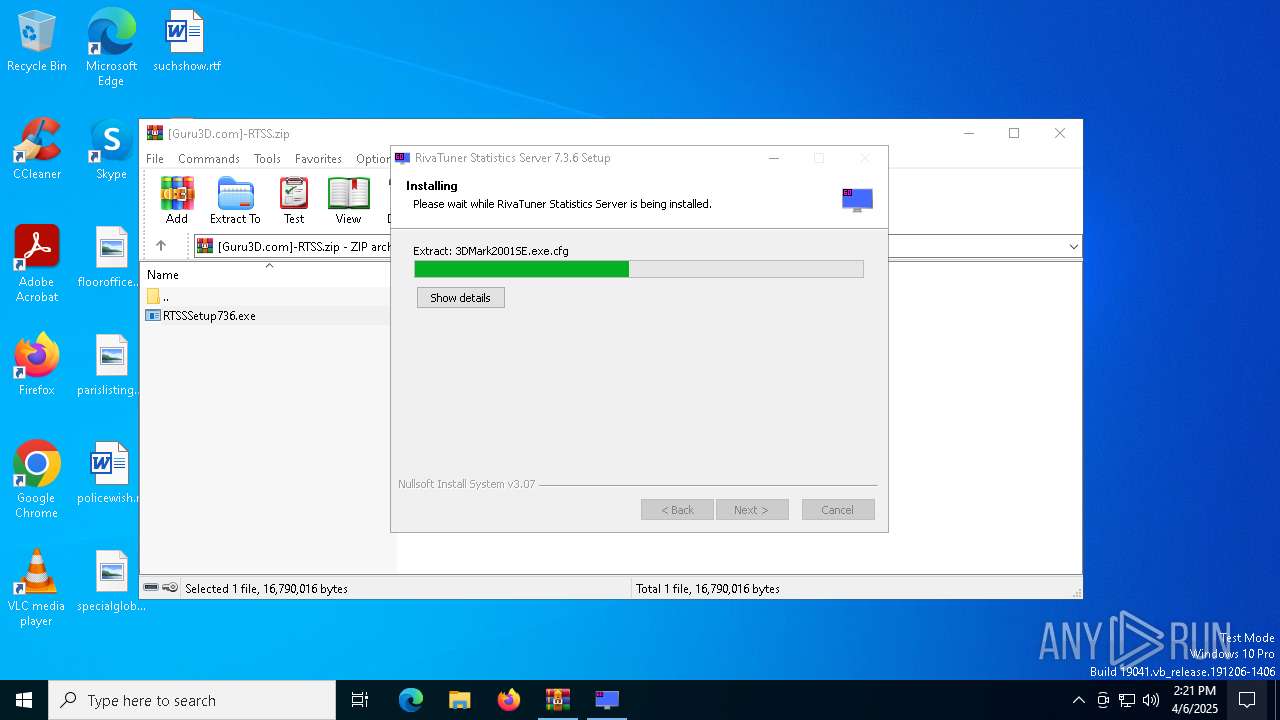
MALICIOUS
Vulnerable driver has been detected
- RTSSSetup736.exe (PID: 7896)
SUSPICIOUS
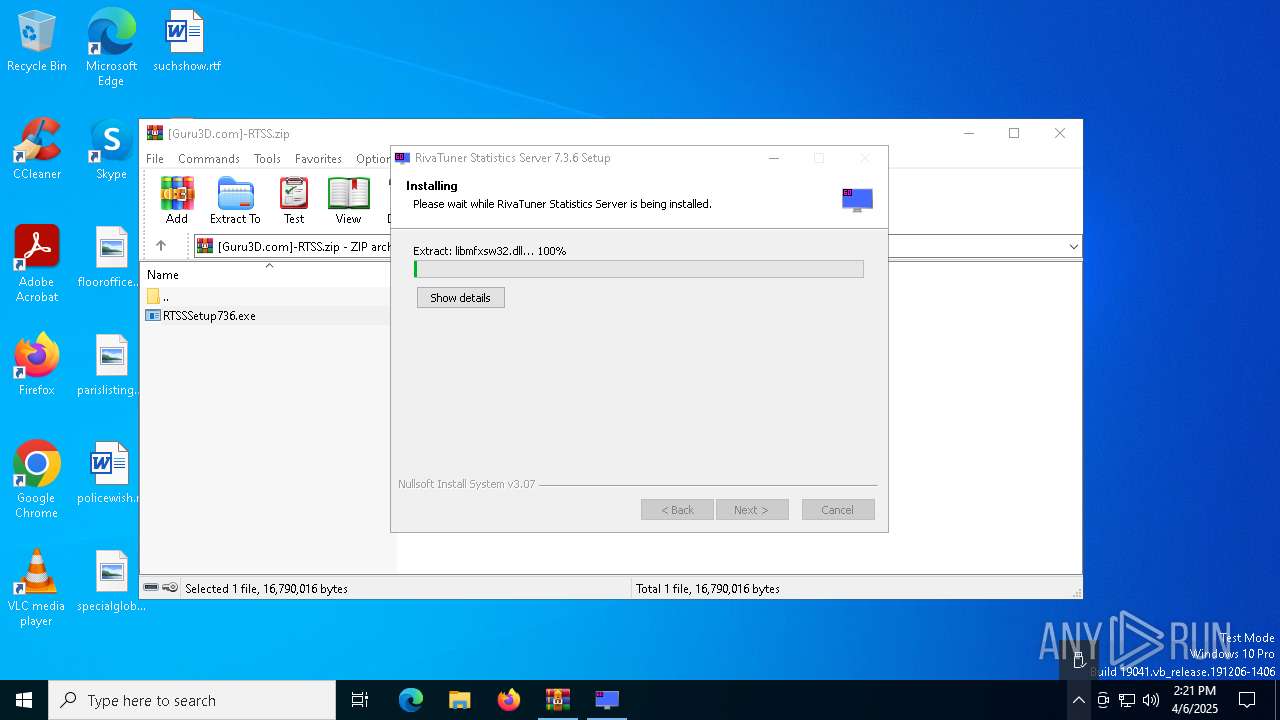
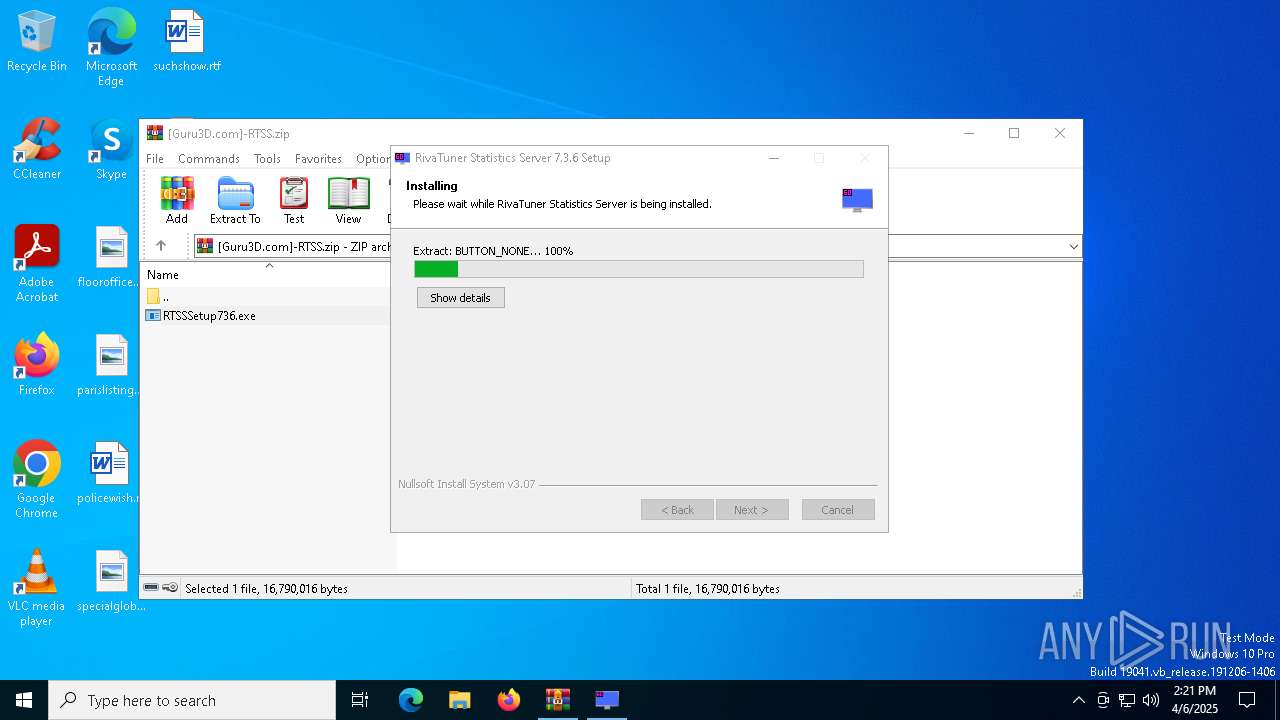
Executable content was dropped or overwritten
- RTSSSetup736.exe (PID: 7896)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7580)
- RTSSSetup736.exe (PID: 7896)
The process creates files with name similar to system file names
- RTSSSetup736.exe (PID: 7896)
There is functionality for taking screenshot (YARA)
- RTSSSetup736.exe (PID: 7896)
Malware-specific behavior (creating "System.dll" in Temp)
- RTSSSetup736.exe (PID: 7896)
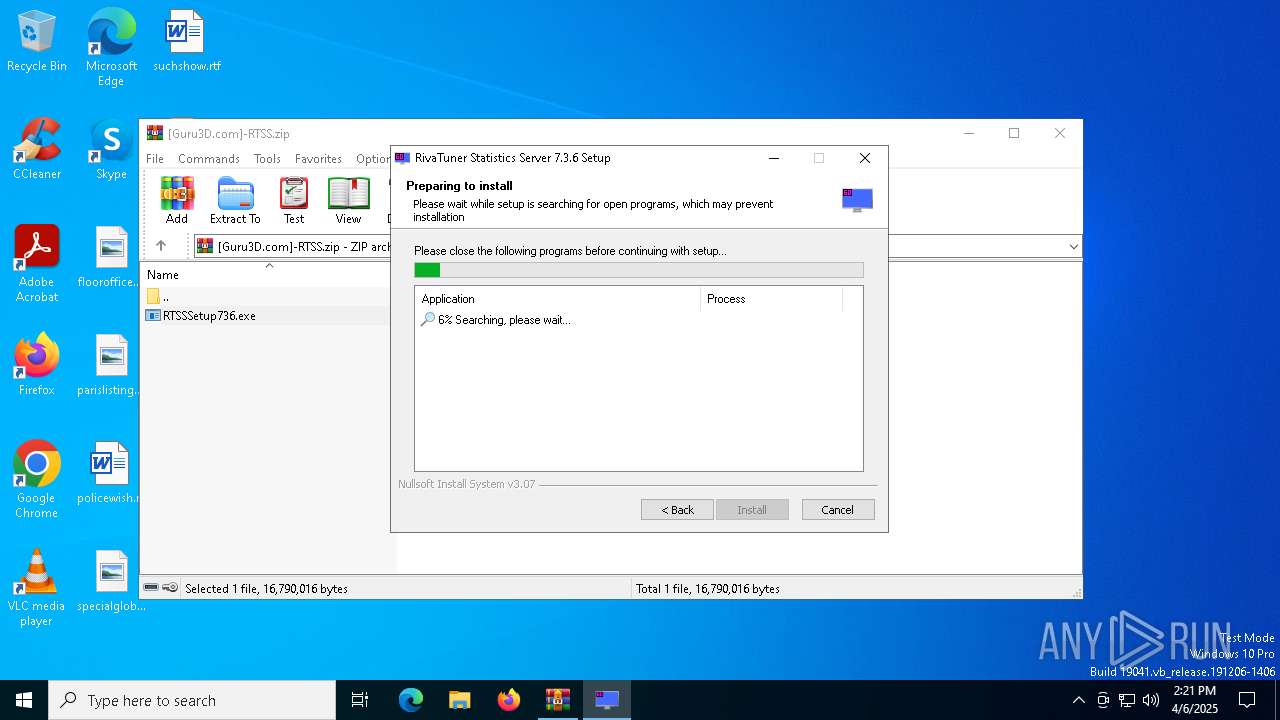
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 8008)
- RTSSSetup736.exe (PID: 7896)
Creates a software uninstall entry
- RTSSSetup736.exe (PID: 7896)
Drops a system driver (possible attempt to evade defenses)
- RTSSSetup736.exe (PID: 7896)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7580)
Checks supported languages
- RTSSSetup736.exe (PID: 7896)
Reads the computer name
- RTSSSetup736.exe (PID: 7896)
Create files in a temporary directory
- RTSSSetup736.exe (PID: 7896)
The sample compiled with english language support
- RTSSSetup736.exe (PID: 7896)
Process checks computer location settings
- RTSSSetup736.exe (PID: 7896)
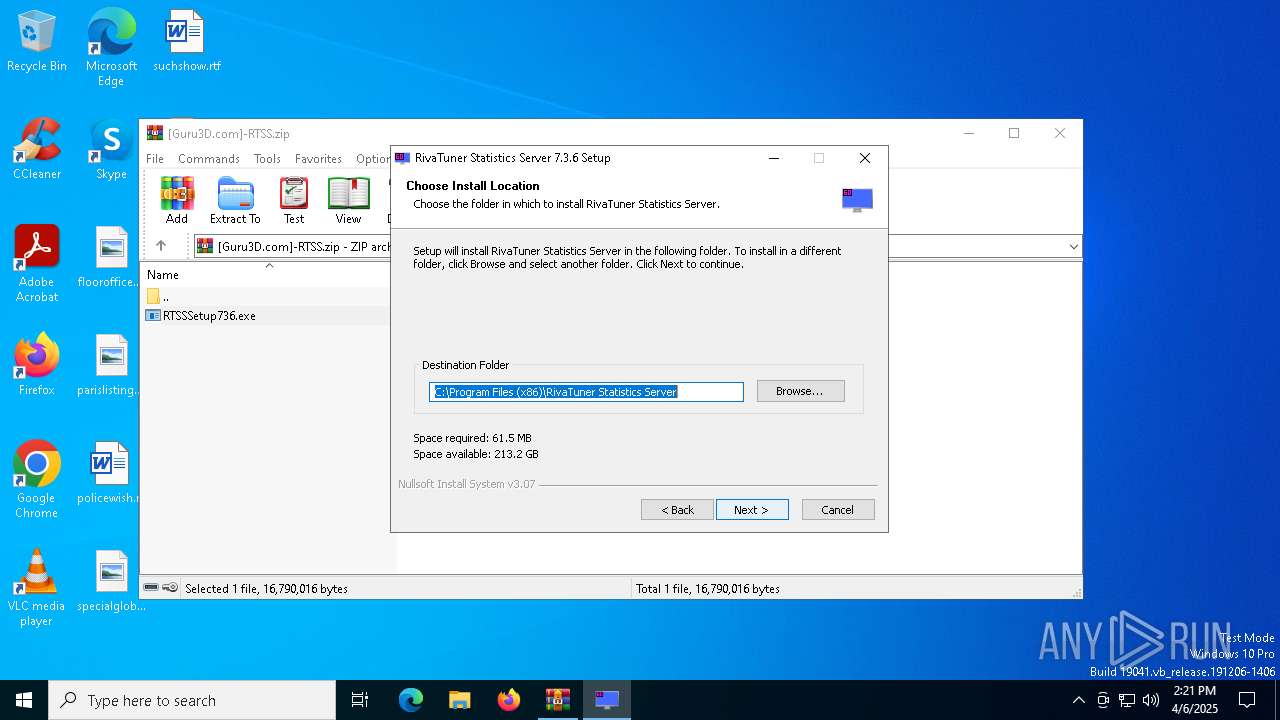
Creates files in the program directory
- RTSSSetup736.exe (PID: 7896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:03:23 10:04:06 |
| ZipCRC: | 0xc70c84d6 |
| ZipCompressedSize: | 16710989 |
| ZipUncompressedSize: | 16790016 |
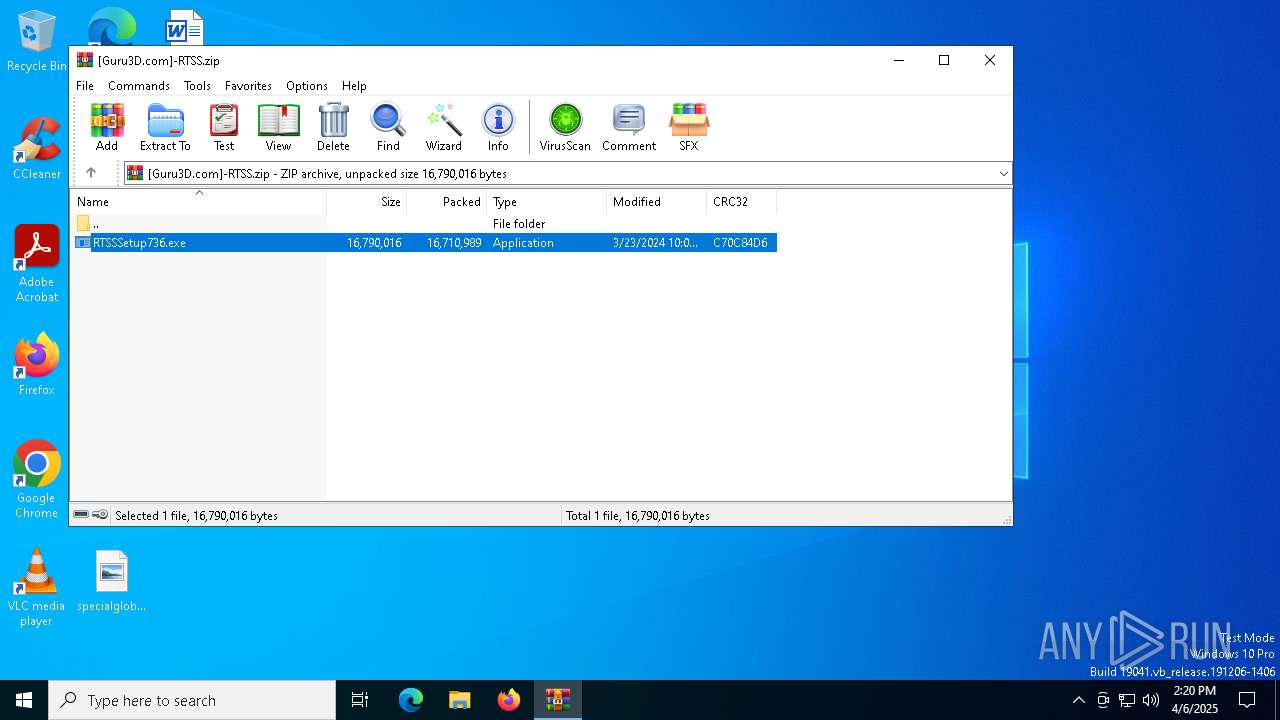
| ZipFileName: | RTSSSetup736.exe |
Total processes
136
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2852 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
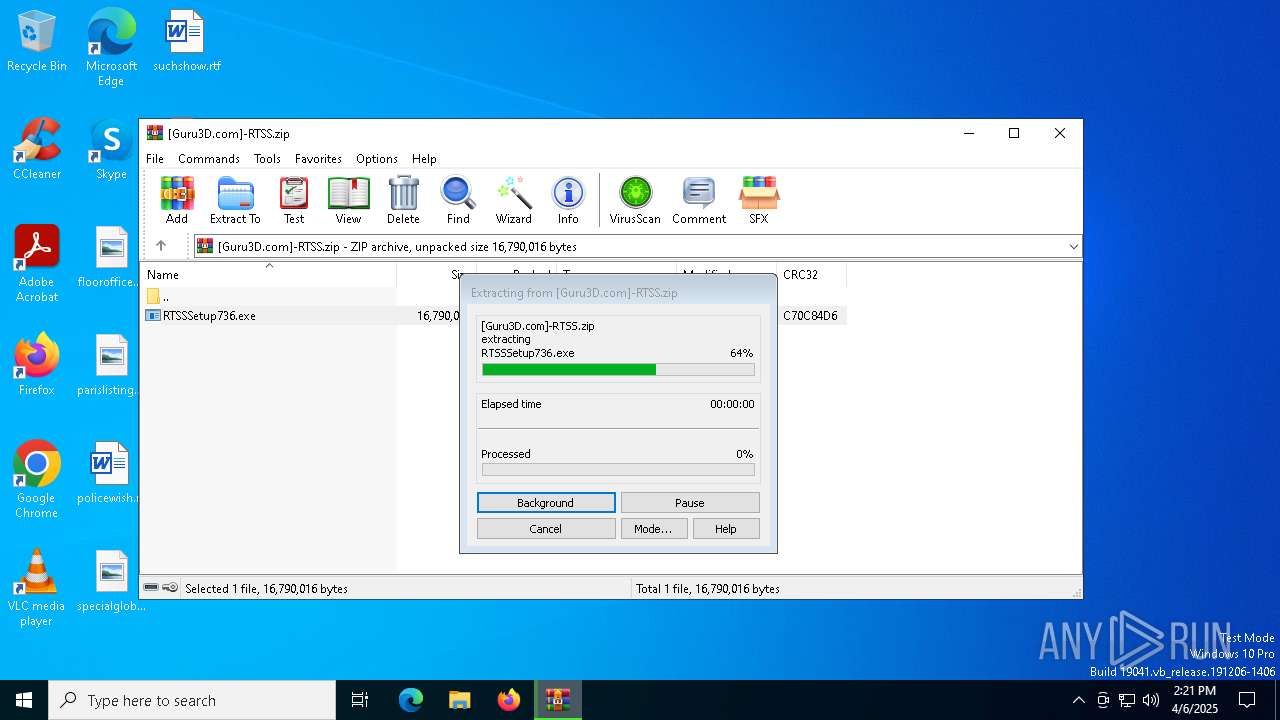
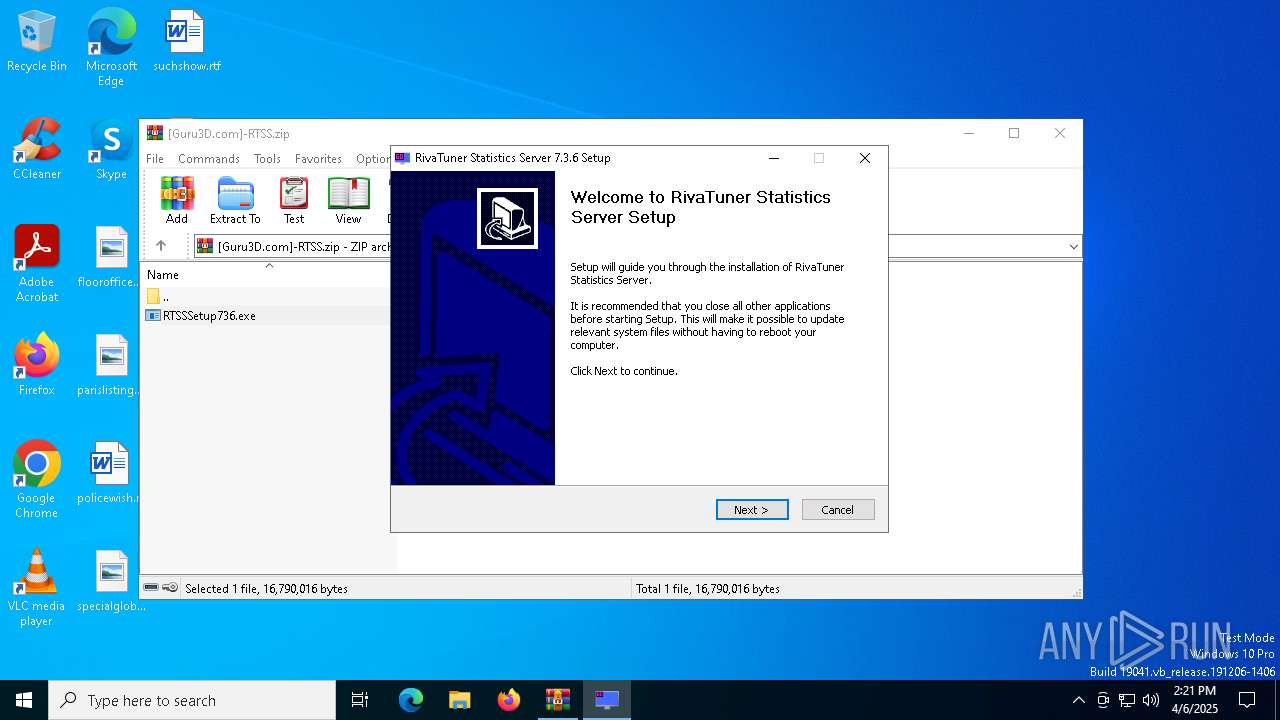
| 7580 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\[Guru3D.com]-RTSS.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7848 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7580.7045\RTSSSetup736.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7580.7045\RTSSSetup736.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
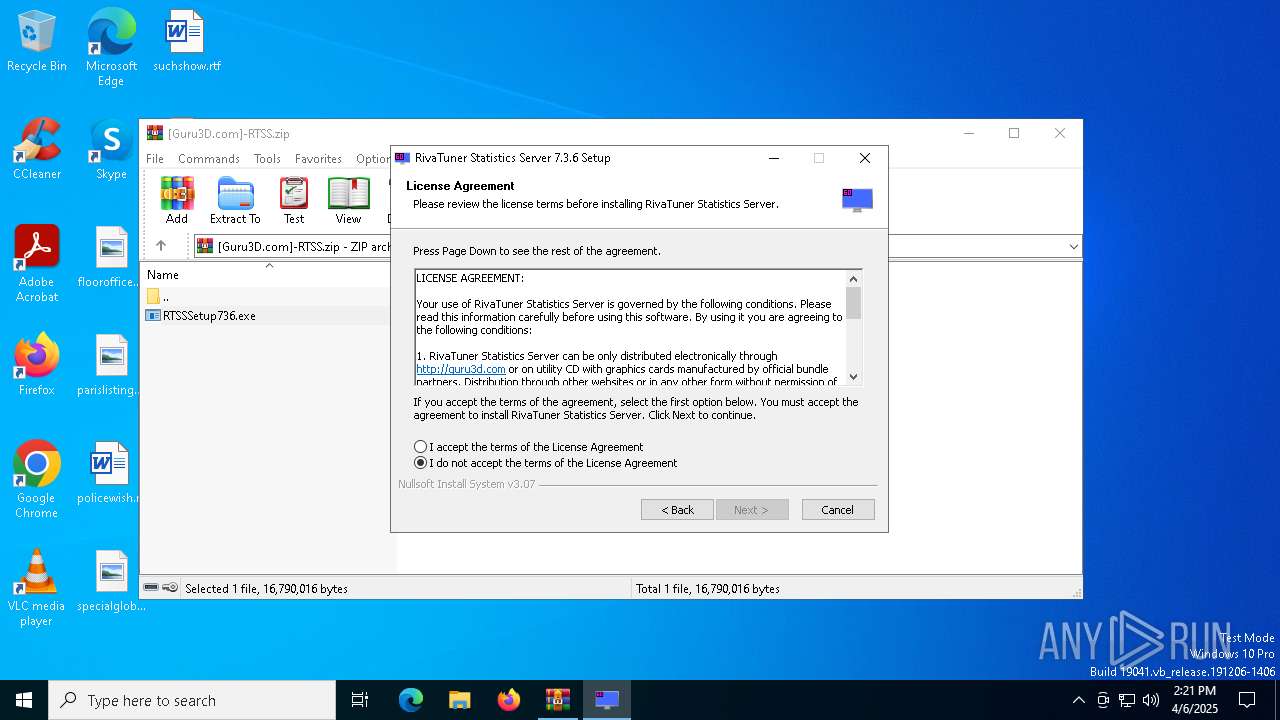
| 7896 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7580.7045\RTSSSetup736.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7580.7045\RTSSSetup736.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 8008 | "C:\Windows\System32\rundll32.exe" LockedList64.dll,GetSystemModulesCount64 0x001002D4 | C:\Windows\SysWOW64\rundll32.exe | — | RTSSSetup736.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8020 | "C:\Windows\System32\rundll32.exe" LockedList64.dll,GetSystemModulesCount64 0x001002D4 | C:\Windows\System32\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8052 | "C:\Windows\System32\rundll32.exe" LockedList64.dll,EnumSystemProcesses64 0x001102D4 1 1 | C:\Windows\System32\rundll32.exe | — | RTSSSetup736.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 552
Read events
2 539
Write events
13
Delete events
0
Modification events
| (PID) Process: | (7580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\[Guru3D.com]-RTSS.zip | |||
| (PID) Process: | (7580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7896) RTSSSetup736.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\RTSS |
| Operation: | write | Name: | Publisher |
Value: Unwinder | |||
| (PID) Process: | (7896) RTSSSetup736.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\RTSS |
| Operation: | write | Name: | DisplayName |
Value: RivaTuner Statistics Server 7.3.6 | |||
Executable files
61
Suspicious files
5
Text files
906
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7896 | RTSSSetup736.exe | C:\Users\admin\AppData\Local\Temp\nsfDD24.tmp\LockedList.dll | executable | |
MD5:84C93011C323095555FCFCBEBAB4DF83 | SHA256:CF1B3D307918E11F4C90888EF65F9CAD0302EABF7235187EAAD5764646874340 | |||
| 7580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7580.7045\RTSSSetup736.exe | executable | |
MD5:F57C07115788603CF14320F2632F6668 | SHA256:941CC44F629086310DBA8C9E96AB55994F230EEF6917A2E70EC6C9B698154D88 | |||
| 7896 | RTSSSetup736.exe | C:\Program Files (x86)\RivaTuner Statistics Server\Uninstall.exe | executable | |
MD5:EBC5A05C86A9D3B185FC516FB584000B | SHA256:F5D0134FF25A0BEAEF528F58749E944595F1714CC9BC559F23A422B6135A81D9 | |||
| 7896 | RTSSSetup736.exe | C:\Users\admin\AppData\Local\Temp\nsfDD24.tmp\System.dll | executable | |
MD5:6E55A6E7C3FDBD244042EB15CB1EC739 | SHA256:ACF90AB6F4EDC687E94AAF604D05E16E6CFB5E35873783B50C66F307A35C6506 | |||
| 7896 | RTSSSetup736.exe | C:\Program Files (x86)\RivaTuner Statistics Server\DesktopOverlayHostLoader.exe | executable | |
MD5:D9FF9504DA8B627B720FE8F62F3BD24D | SHA256:57DFCE7A5CFE97578A45B35731A327E88B22FEE0DBC4EC0B4DC1E919CC94E12F | |||
| 7896 | RTSSSetup736.exe | C:\Users\admin\AppData\Local\Temp\nsfDD24.tmp\StartMenu.dll | executable | |
MD5:6581C243481C0BA91EC1BD9FD93F1C30 | SHA256:72FA1A91185FDA8B68A49B9EBB8D5DDF00F899F590D1E657A58C229F9BD0A700 | |||
| 7896 | RTSSSetup736.exe | C:\Program Files (x86)\RivaTuner Statistics Server\DesktopOverlayHost.exe | executable | |
MD5:7057CAB5E1D3D38D3D5A1F8F2F0CD7EF | SHA256:D594B3870D81FFDCBDA2CB630061CAC915D239E921B4AF7BF19C4FCB26FFCECA | |||
| 7896 | RTSSSetup736.exe | C:\Program Files (x86)\RivaTuner Statistics Server\EncoderServer64.exe | executable | |
MD5:813F7094987655E2C6846EB1188AB420 | SHA256:F1BA5943A9010E879DBF832CB6741DAE3FC92E19F657CE69335AD904FDBDEAE4 | |||
| 7896 | RTSSSetup736.exe | C:\Users\admin\AppData\Local\Temp\nsfDD24.tmp\LockedList64.dll | executable | |
MD5:F982F688C44A109382504BE756E54A28 | SHA256:FBE4C84D389B32D3646991F0F59C987D5052ECC0ECBAA4DA2BBEBD922FD3762C | |||
| 7896 | RTSSSetup736.exe | C:\Program Files (x86)\RivaTuner Statistics Server\libmfxsw32.dll | executable | |
MD5:6980F97A2A92DCE04C5CCE88028BD160 | SHA256:39AA5129F3E61473DE411A3E286A8AB2A410436923BBAA9320610DE30EE1DF5F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8160 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8160 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.7.1.246:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8160 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8160 | SIHClient.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
8160 | SIHClient.exe | 40.69.42.241:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |