| download: | amtlib.dll |
| Full analysis: | https://app.any.run/tasks/fe00a463-1d10-49e7-ae72-267fd0210bd6 |
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2018, 01:19:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 381078A5EA3C9C0BE046D382C92233C1 |
| SHA1: | C1AEECE29BE4CCBABFB3E39EACFA4983C0F8358C |
| SHA256: | E1189544E7FE546133D119A141F1D1EC74A1FED2317C7DFB211C2B779887C03E |
| SSDEEP: | 49152:lwMzzudPmkGIHkyRUHxjNF3AVcc3qVAfuz6/Fq3+bEc:/kGIEyO93AVt3nL/1 |
MALICIOUS
Loads dropped or rewritten executable
- WerFault.exe (PID: 4060)
SUSPICIOUS
No suspicious indicators.INFO
Loads main object executable
- rundll32.exe (PID: 4044)
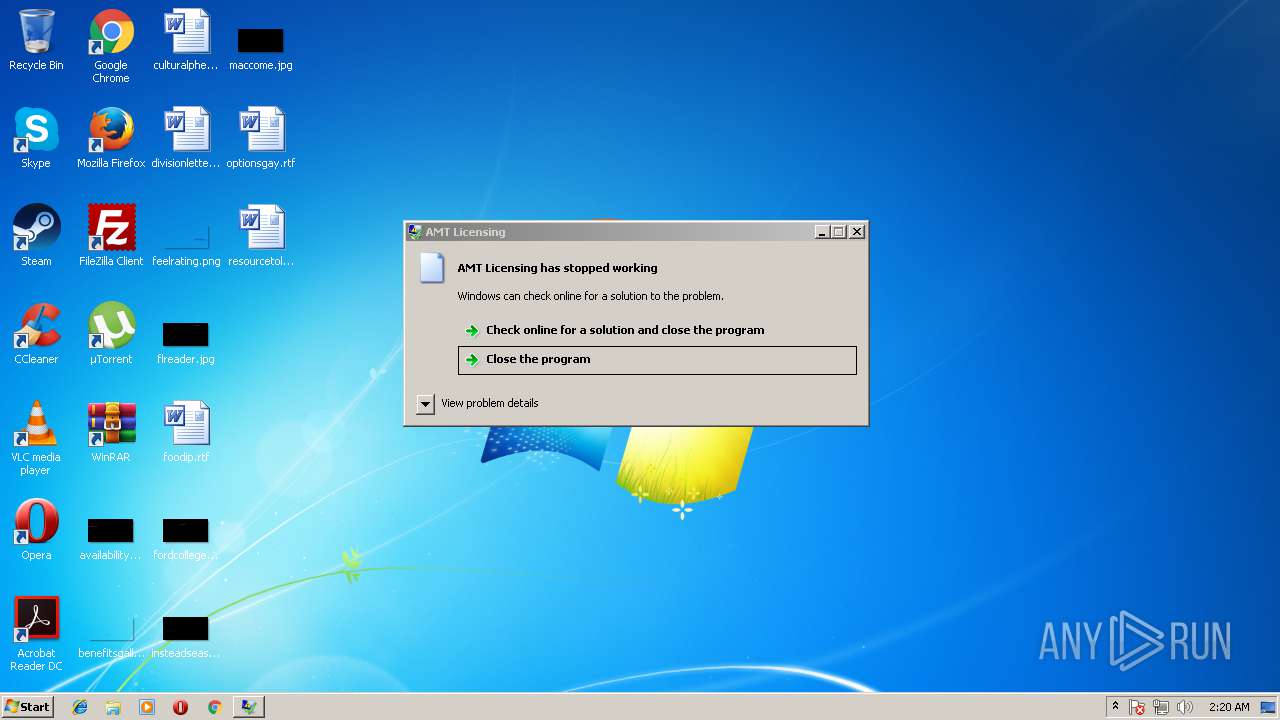
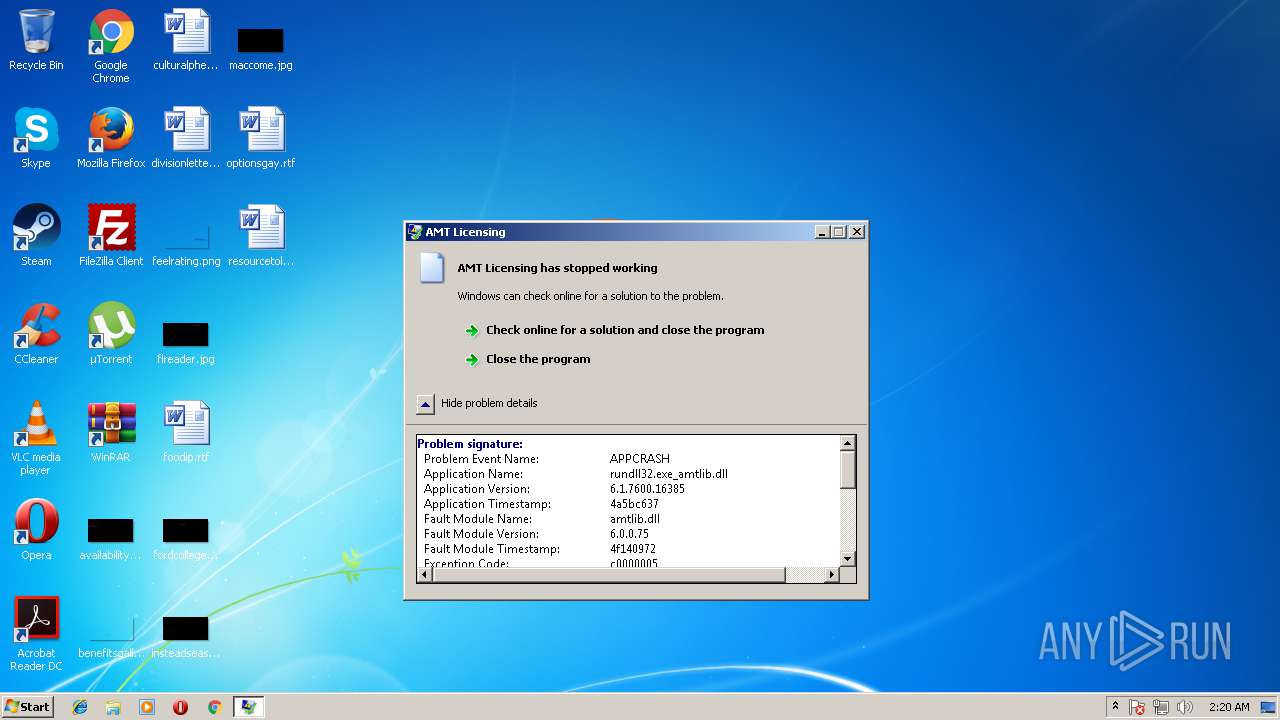
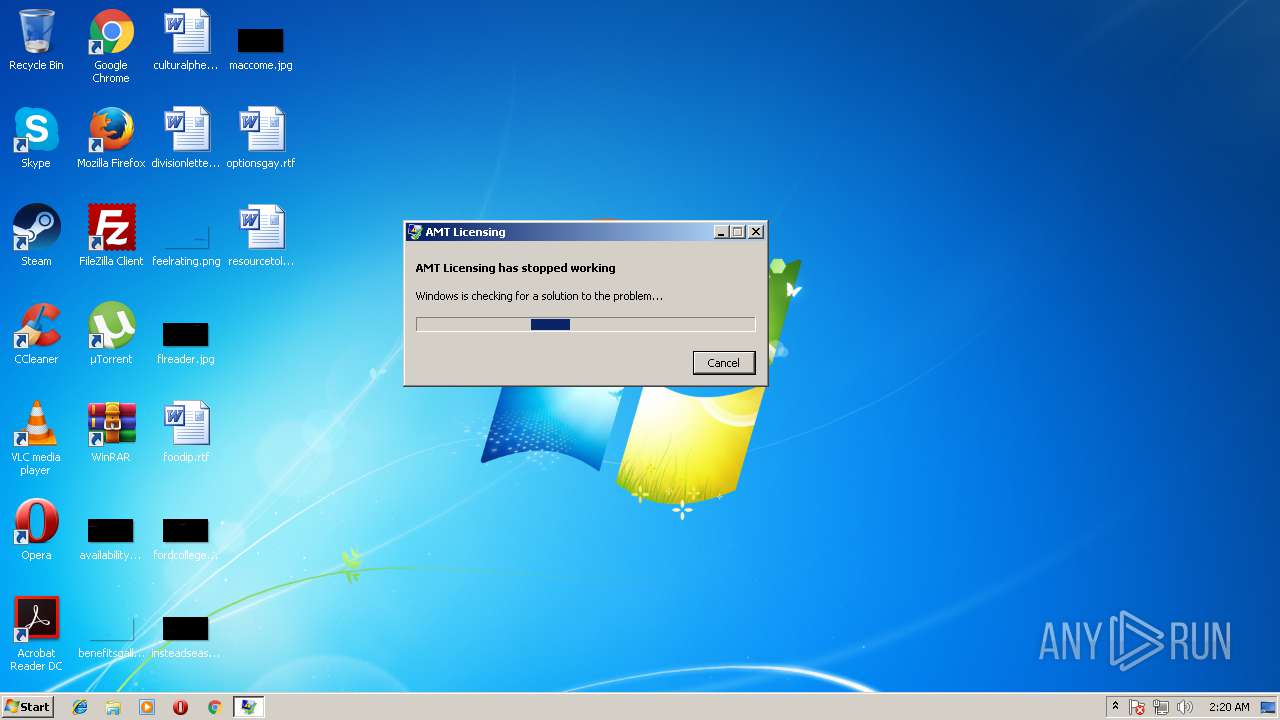
Application was crashed
- rundll32.exe (PID: 4044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:01:16 12:26:42+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 1480192 |
| InitializedDataSize: | 306688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1296b9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.0.75 |
| ProductVersionNumber: | 6.0.0.75 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Adobe Systems, Incorporated |
| FileDescription: | AMT Licensing |
| FileVersion: | 6.0.0.75 |
| InternalName: | amtlib |
| LegalCopyright: | Copyright 2006-2011 Adobe Systems Incorporated. All rights reserved. |
| OriginalFileName: | amtlib.dll |
| ProductName: | AMTLib |
| ProductVersion: | 6.0.0.75 (BuildVersion: 6.0; BuildDate: Mon Jan 16 2012 18:00:00) |
| BuildDate: | Mon Jan 16 2012 18:00:00 |
| BuildVersion: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jan-2012 11:26:42 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Adobe Systems, Incorporated |
| FileDescription: | AMT Licensing |
| FileVersion: | 6.0.0.75 |
| InternalName: | amtlib |
| LegalCopyright: | Copyright 2006-2011 Adobe Systems Incorporated. All rights reserved. |
| OriginalFilename: | amtlib.dll |
| ProductName: | AMTLib |
| ProductVersion: | 6.0.0.75 (BuildVersion: 6.0; BuildDate: Mon Jan 16 2012 18:00:00) |
| BuildDate: | Mon Jan 16 2012 18:00:00 |
| BuildVersion: | 1.000000 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Jan-2012 11:26:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00169451 | 0x00169600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63513 |
.rdata | 0x0016B000 | 0x00033AD5 | 0x00033C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10219 |
.data | 0x0019F000 | 0x0000D708 | 0x00007800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.67797 |
.rsrc | 0x001AD000 | 0x00000624 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49709 |
.reloc | 0x001AE000 | 0x0000F030 | 0x0000F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56726 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.47787 | 1064 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
SETUPAPI.dll |
SHELL32.dll |
USER32.dll |
WINHTTP.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
AMTGetLibVersion | 1 | 0x00089390 |
AMTGetParentLEIDLicenseStatus | 2 | 0x00089450 |
AMTGetProductClearSerialNumber | 3 | 0x000894E0 |
AMTObtainProductLicense | 4 | 0x00089E90 |
AMTPlugPlugRequest | 5 | 0x000893D0 |
AMTPreObtainProductLicense | 6 | 0x000898A0 |
AMTPreValidateProductLicense | 7 | 0x000892D0 |
AMTReleaseProductLicense | 8 | 0x00089780 |
AMTRetrieveAdobeID | 9 | 0x00089710 |
AMTValidateProductLicense | 10 | 0x0008A060 |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4044 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\amtlib.dll", AMTGetLibVersion | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | C:\Windows\system32\WerFault.exe -u -p 4044 -s 200 | C:\Windows\system32\WerFault.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
31
Read events
31
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER87BD.tmp.appcompat.txt | — | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER881C.tmp.hdmp | — | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER88E8.tmp.mdmp | — | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_amt_e6e71c8f3be79a0db2f2ee2459cefafacba51_cab_0f908981\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_amt_e6e71c8f3be79a0db2f2ee2459cefafacba51_cab_0f908981\WER87BD.tmp.appcompat.txt | xml | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\rundll32.exe.4044.dmp | dmp | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER6C4.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_amt_e6e71c8f3be79a0db2f2ee2459cefafacba51_cab_0f908981\WER881C.tmp.hdmp | dmp | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_amt_e6e71c8f3be79a0db2f2ee2459cefafacba51_cab_0f908981\WER88E8.tmp.mdmp | dmp | |
MD5:— | SHA256:— | |||
| 4060 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_amt_e6e71c8f3be79a0db2f2ee2459cefafacba51_cab_0f908981\WER6C4.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4060 | WerFault.exe | GET | — | 51.143.22.239:80 | http://watson.microsoft.com/StageOne/rundll32_exe_amtlib_dll/6_1_7600_16385/4a5bc637/amtlib_dll/6_0_0_75/4f140972/c0000005/0008939a.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4060 | WerFault.exe | 51.143.22.239:80 | watson.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4060 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |