| File name: | ssu.exe |
| Full analysis: | https://app.any.run/tasks/d0a59edd-94cc-4bc1-b211-68fed258a156 |
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2021, 15:37:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | B300CEAE379544D8FFBF6D2B6EEB1F6A |
| SHA1: | 0976ED9DB45832F05E560B8DCCA0782CD72E8B1D |
| SHA256: | E1182DEEC71195E11FD4580F435DC461DD194A3AE9954DC441235C2F138377E1 |
| SSDEEP: | 6144:aBlkZvaF4NTBRBLMX9kQyHWbsoYQtyDUb09fcgL0XDl4FVGBxboXhMknx:aoSWNTTBQkGs7QtxinLwDODGBgSe |
MALICIOUS
Application was dropped or rewritten from another process
- amidewin.exe (PID: 2664)
Drops executable file immediately after starts
- ssu.exe (PID: 2772)
SUSPICIOUS
Executable content was dropped or overwritten
- ssu.exe (PID: 2772)
Starts CMD.EXE for commands execution
- ssu.exe (PID: 2772)
Drops a file that was compiled in debug mode
- ssu.exe (PID: 2772)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 346112 |
| CodeSize: | 70656 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2019:07:30 10:52:45+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 30-Jul-2019 08:52:45 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jul-2019 08:52:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0000387E | 0x00003A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.52922 |
.text | 0x00005000 | 0x0000D962 | 0x0000DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56249 |
.rdata | 0x00013000 | 0x000033A5 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11184 |
.data | 0x00017000 | 0x0000178C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.10106 |
.rsrc | 0x00019000 | 0x0005018C | 0x00050200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99862 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
002C06F137251DBA8D84D93D348F82ED112E93F5 | 7.99864 | 146452 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
5A085F348E4D19AA9E2439146E9BAD9485C3A186 | 7.98731 | 16252 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
6BC5E8B2F97B15B0F5F0BEA32F7A4C05878E4729 | 7.99879 | 158228 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
6DBEE010343858B6E3DE8CC9A915CC41 | 7.00366 | 200 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
800489E779B6B17EB6F6210910D1D543 | 7.48862 | 395 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
AD34B25D24DC274E658D991CD503E67B9CAF6699 | 7.96055 | 4650 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
E1A72E6DF0 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
E328971209A215A368FFDCC16BD33DB5E0506479 | 4.36852 | 22 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F0D44049961FA8F93E7338B4126F7408 | 3.80776 | 17 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
0
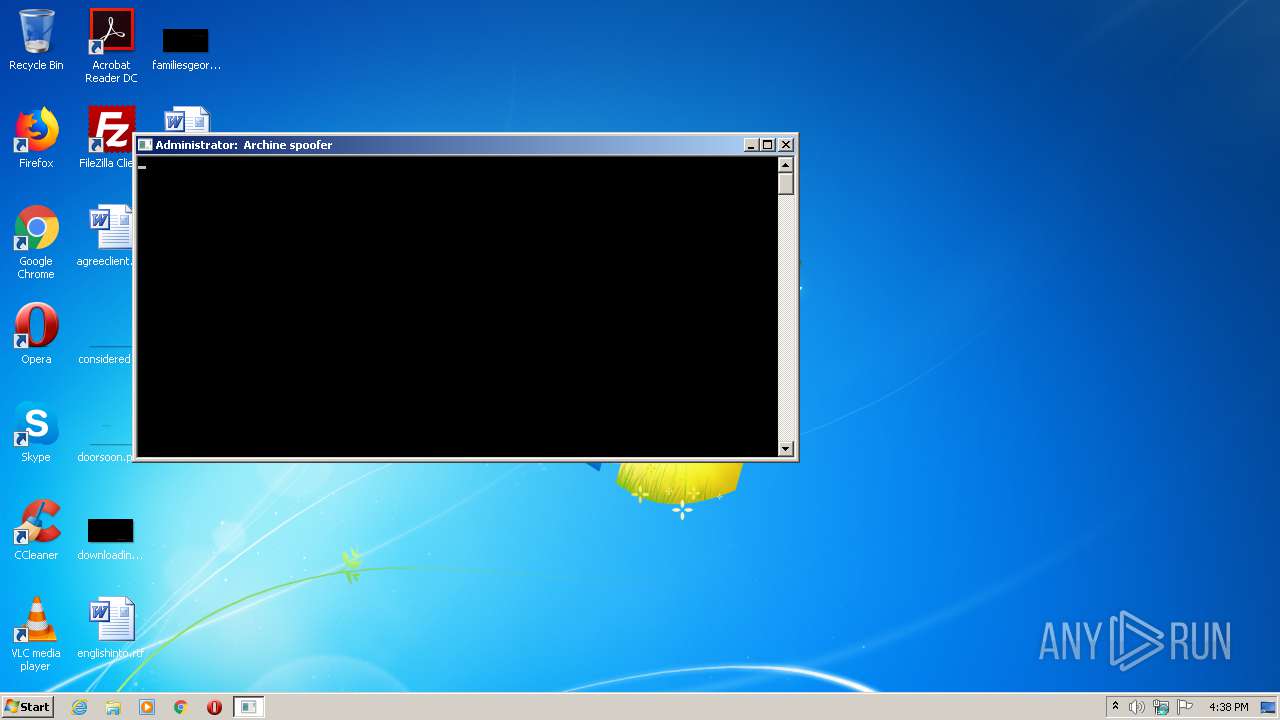
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2100 | timeout 2 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Users\admin\AppData\Local\Temp\ssu.exe" | C:\Users\admin\AppData\Local\Temp\ssu.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2664 | amidewin.exe /SS 290731433215580 | C:\Users\admin\AppData\Local\Temp\amidewin.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2772 | "C:\Users\admin\AppData\Local\Temp\ssu.exe" | C:\Users\admin\AppData\Local\Temp\ssu.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4028 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\F446.tmp\F447.tmp\F448.bat C:\Users\admin\AppData\Local\Temp\ssu.exe" | C:\Windows\system32\cmd.exe | — | ssu.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
6
Read events
6
Write events
0
Delete events
0
Modification events
Executable files
4
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | ssu.exe | C:\Users\admin\AppData\Local\Temp\amidewin.exe | executable | |
MD5:2A9F489FA0834B84B16BD6C8CEAB69C5 | SHA256:0E73FA53B6251A40937C44EFCA836C17A1B8CF6E7991258B4B1973C9129F1177 | |||
| 2772 | ssu.exe | C:\Users\admin\AppData\Local\Temp\AMIFLDRV32.SYS | executable | |
MD5:453731A68C6D305C4D3BBBCE684D148C | SHA256:B7067533886109B47F6A18EDEA5919C17E1C6F77DDC00D88EAE8879EE4E9BCBD | |||
| 2772 | ssu.exe | C:\Users\admin\AppData\Local\Temp\amidewin64.exe | executable | |
MD5:F17ECF761E70FEB98C7F628857EEDFE7 | SHA256:311F5C844746D4270B5B971CCEF8D74DDEDCA873EB45F34A1A55F1EA4A3BAFCF | |||
| 2772 | ssu.exe | C:\Users\admin\AppData\Local\Temp\amifldrv64.sys | executable | |
MD5:F22740BA54A400FD2BE7690BB204AA08 | SHA256:65C26276CADDA7A36F8977D1D01120EDB5C3418BE2317D501761092D5F9916C9 | |||
| 2772 | ssu.exe | C:\Users\admin\AppData\Local\Temp\F446.tmp\F447.tmp\F448.bat | text | |
MD5:05DE1DAE5E34444A22ABE9E587B8C2ED | SHA256:F5B8428DEE5107C5721D4A2AD1B4DFD040EC4381384D983BB2804ED3AA4643D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report