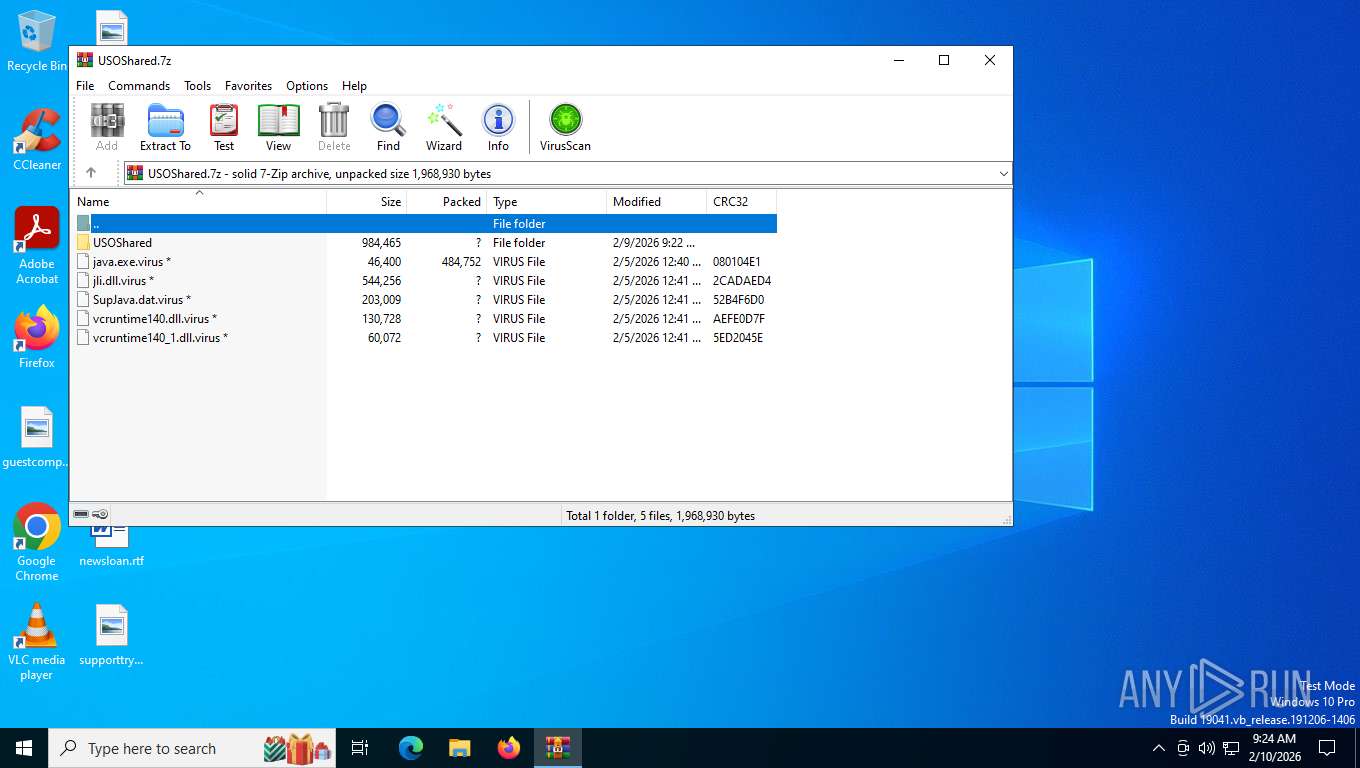
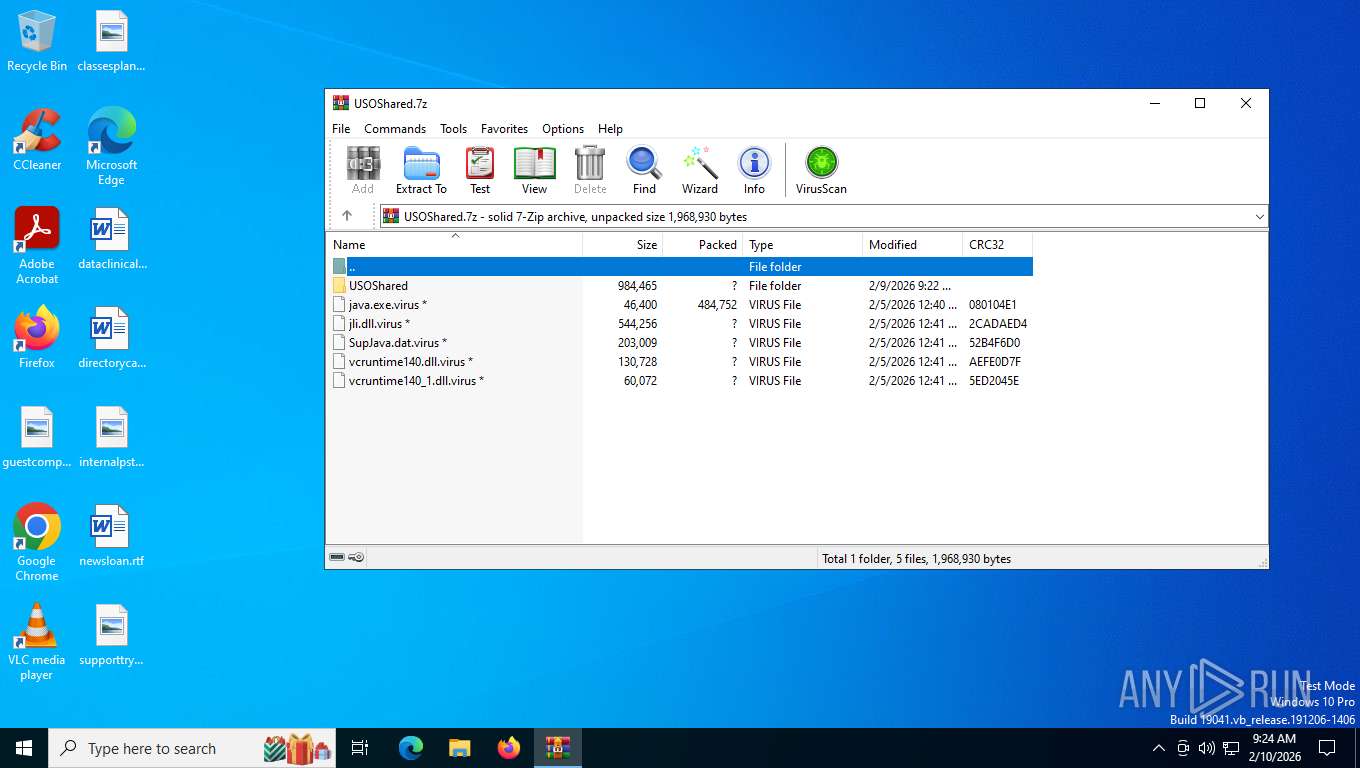
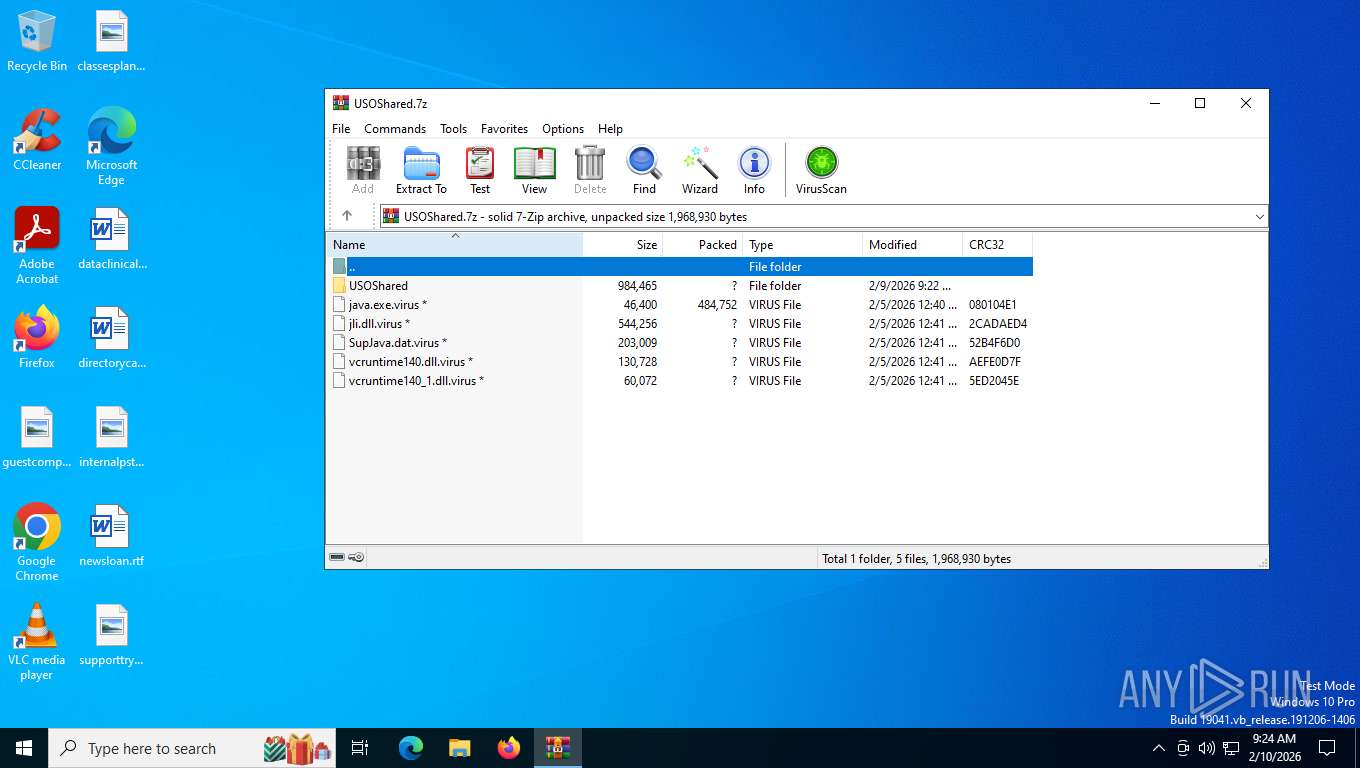
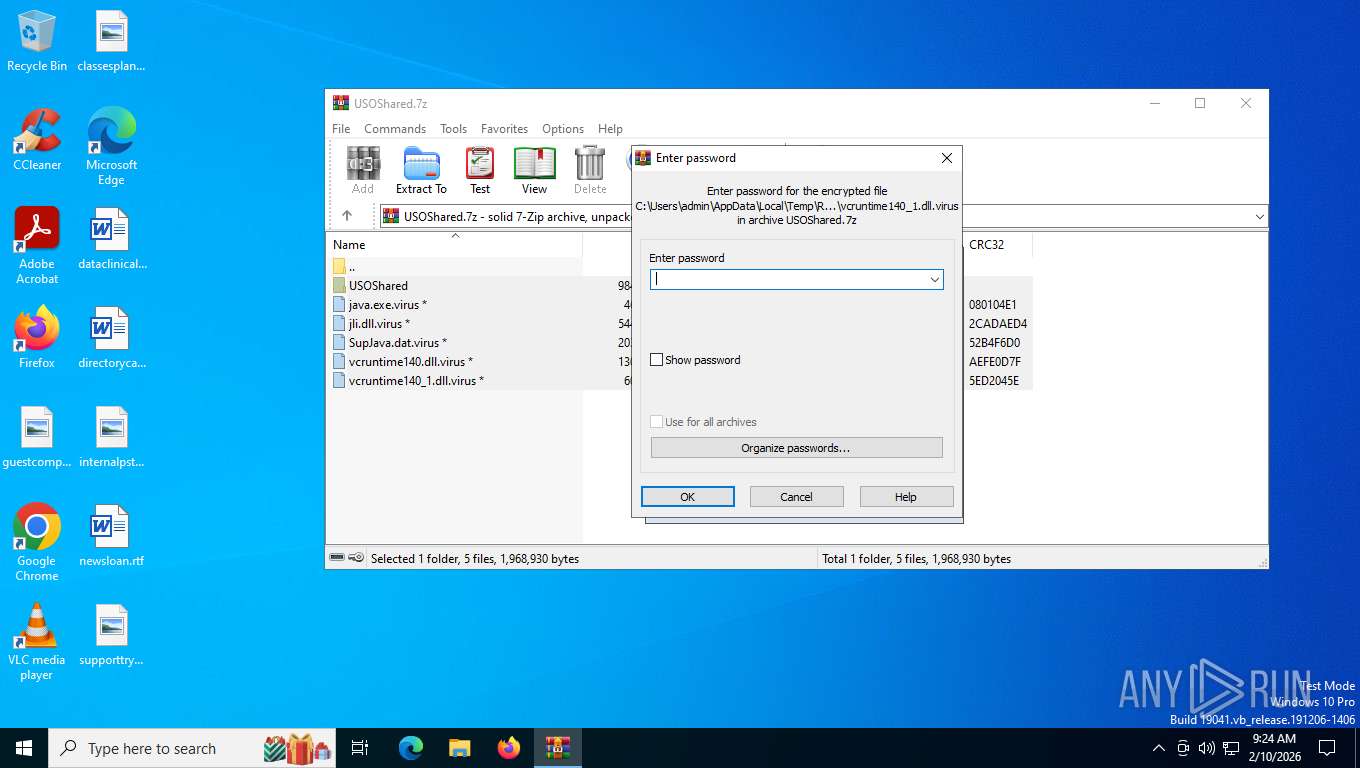
| File name: | USOShared.7z |
| Full analysis: | https://app.any.run/tasks/bc2eae94-b806-4df6-838e-668efc22c2c9 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2026, 14:24:00 |
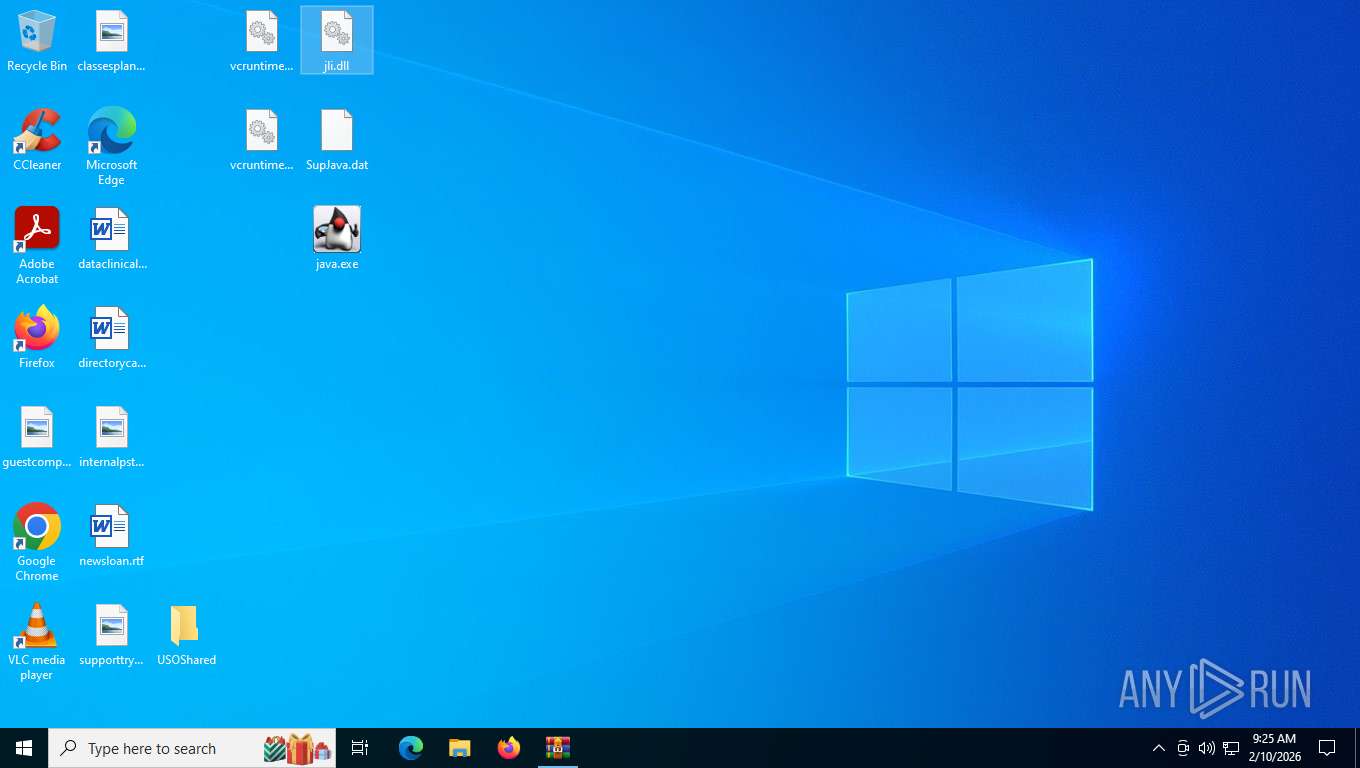
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 24F3CEF19EE60435C575ECB9951B0762 |
| SHA1: | 018E26A062DDBEACCED1E142E1AF55E3693B587C |
| SHA256: | E116967BBF601CB8524E0C9E87B94AFC9A738630200A793D76BD47612CF69BB3 |
| SSDEEP: | 49152:d1i7X6u+bkQZpocnApXEATuzfZC8udpB8yC11QLIsCis8TUHWcDzSqRlyvaWKMxA:d87X61QKO1pXEATESdpB8yC11QUsqw+1 |
MALICIOUS
XORed URL has been found (YARA)
- java.exe (PID: 1188)
- java.exe (PID: 6096)
- java.exe (PID: 6444)
SUSPICIOUS
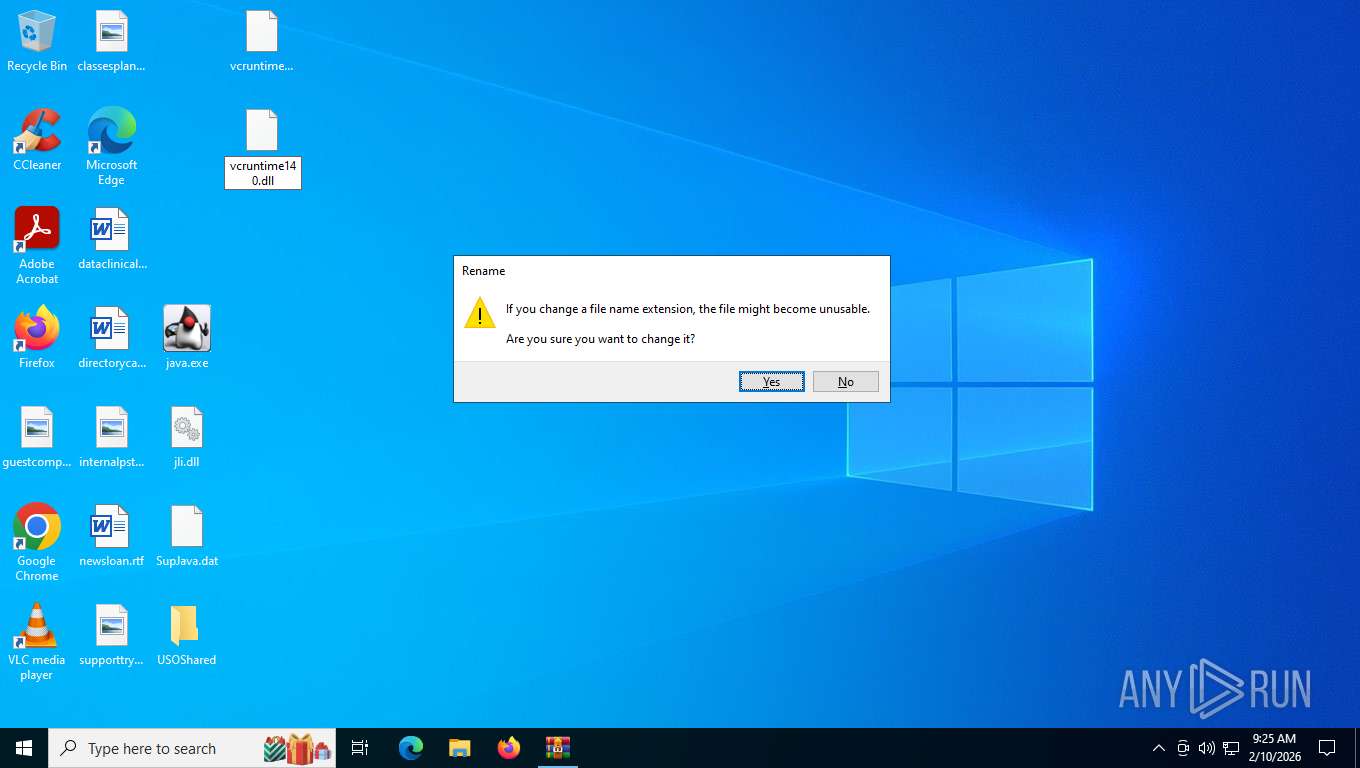
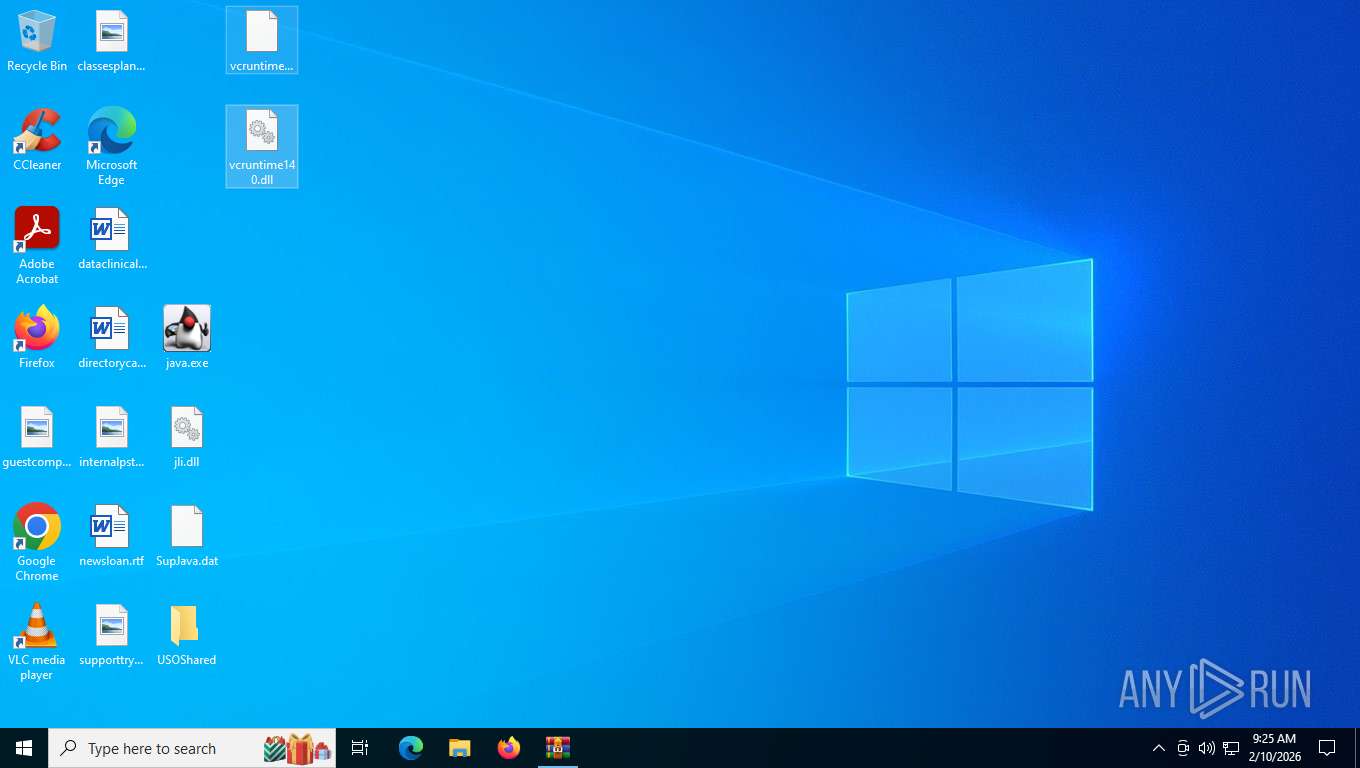
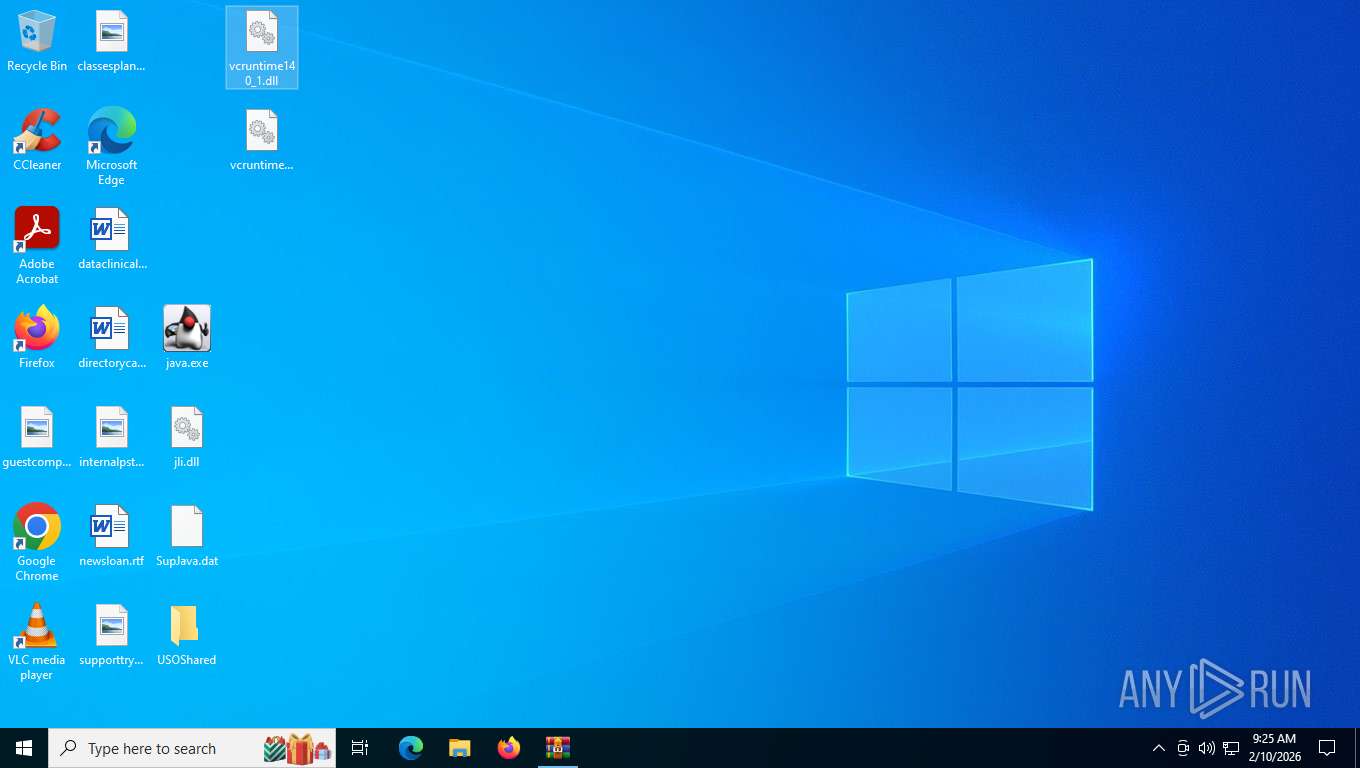
Process drops legitimate windows executable
- WinRAR.exe (PID: 8820)
Executes application which crashes
- java.exe (PID: 6096)
- java.exe (PID: 1188)
- java.exe (PID: 6444)
INFO
Checks proxy server information
- java.exe (PID: 1188)
- java.exe (PID: 6096)
- java.exe (PID: 6444)
- WerFault.exe (PID: 7544)
- slui.exe (PID: 8052)
- WerFault.exe (PID: 4140)
- WerFault.exe (PID: 2548)
Reads security settings of Internet Explorer
- java.exe (PID: 1188)
- java.exe (PID: 6096)
- java.exe (PID: 6444)
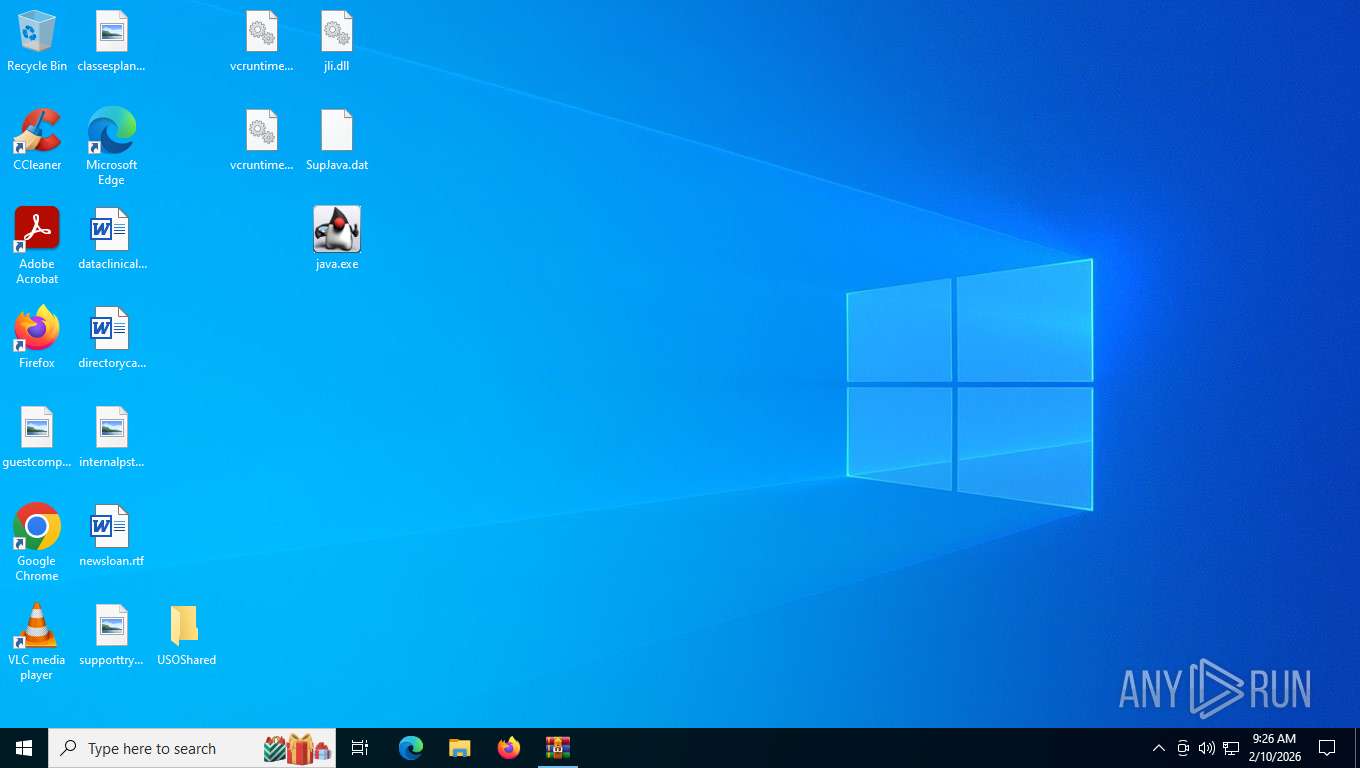
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8820)
Reads the computer name
- java.exe (PID: 6096)
- java.exe (PID: 1188)
- java.exe (PID: 6444)
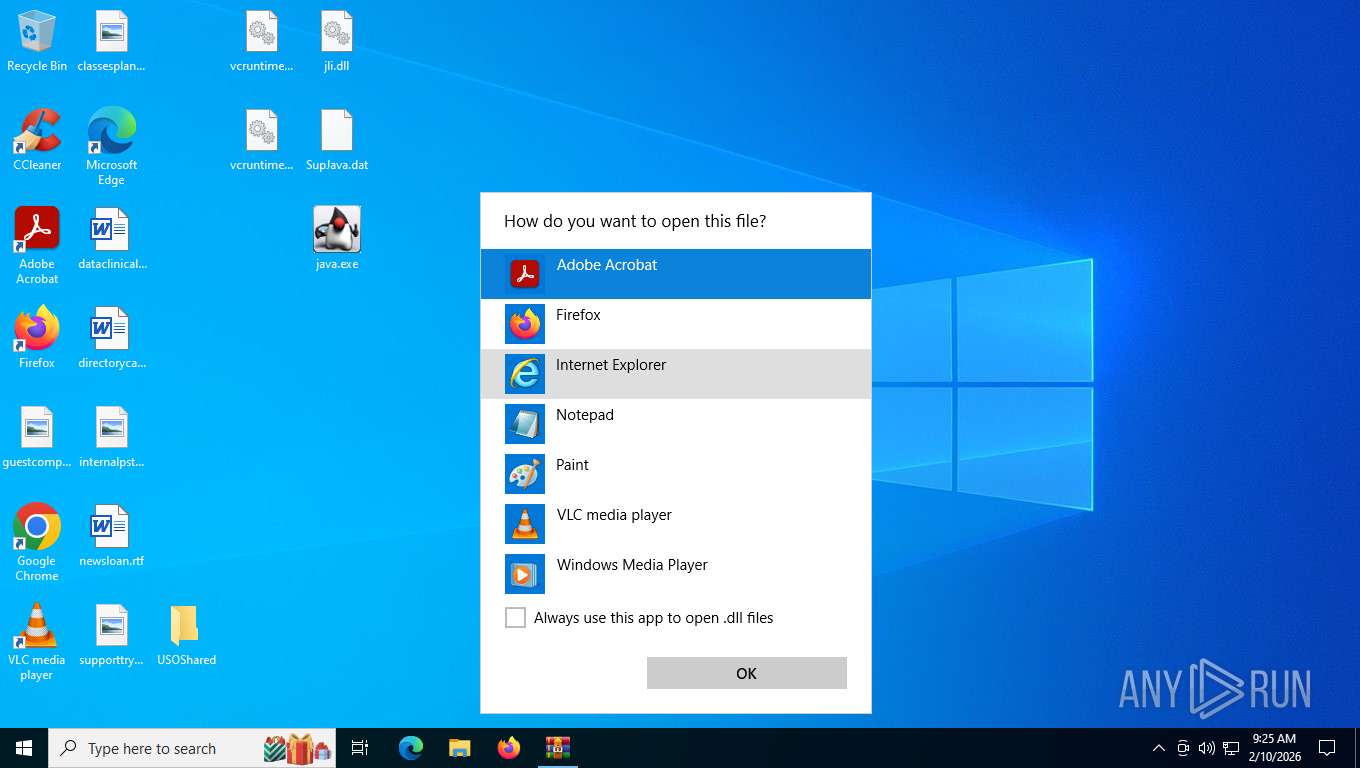
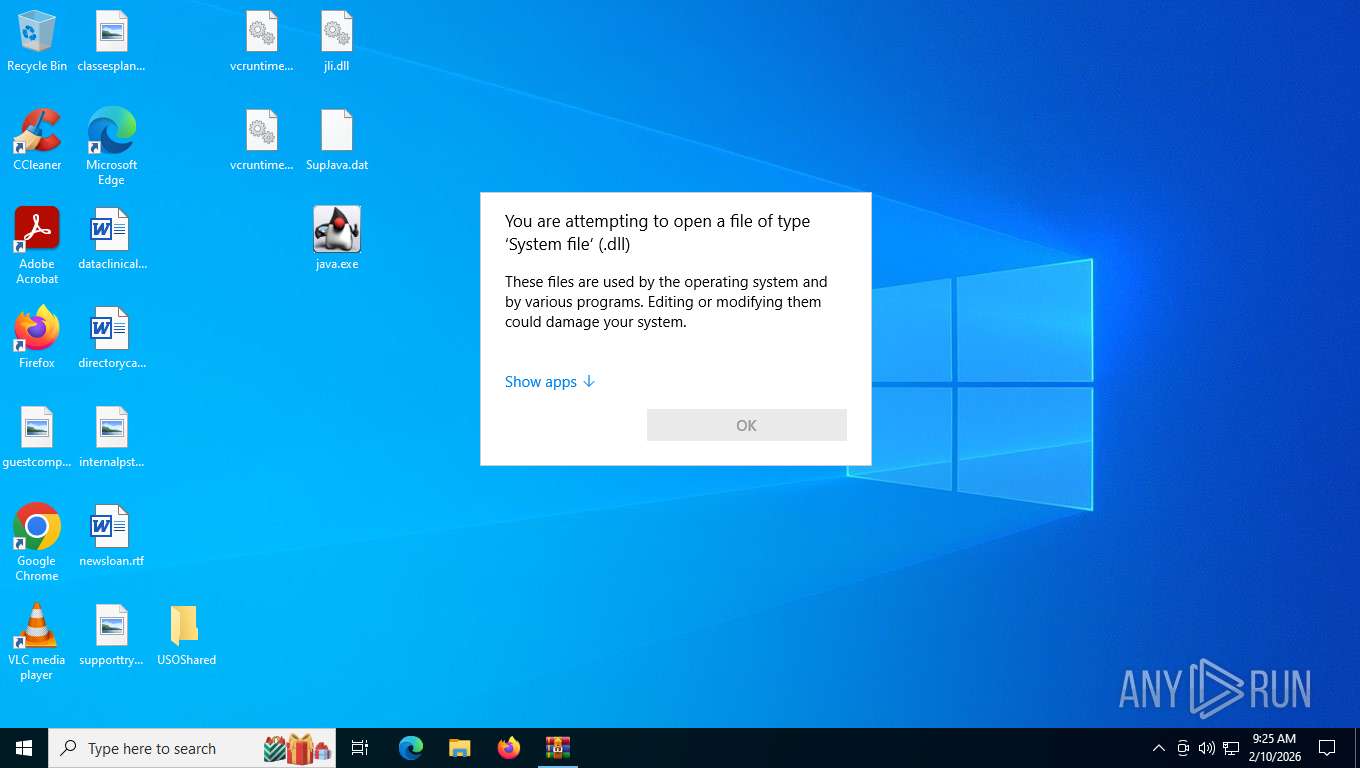
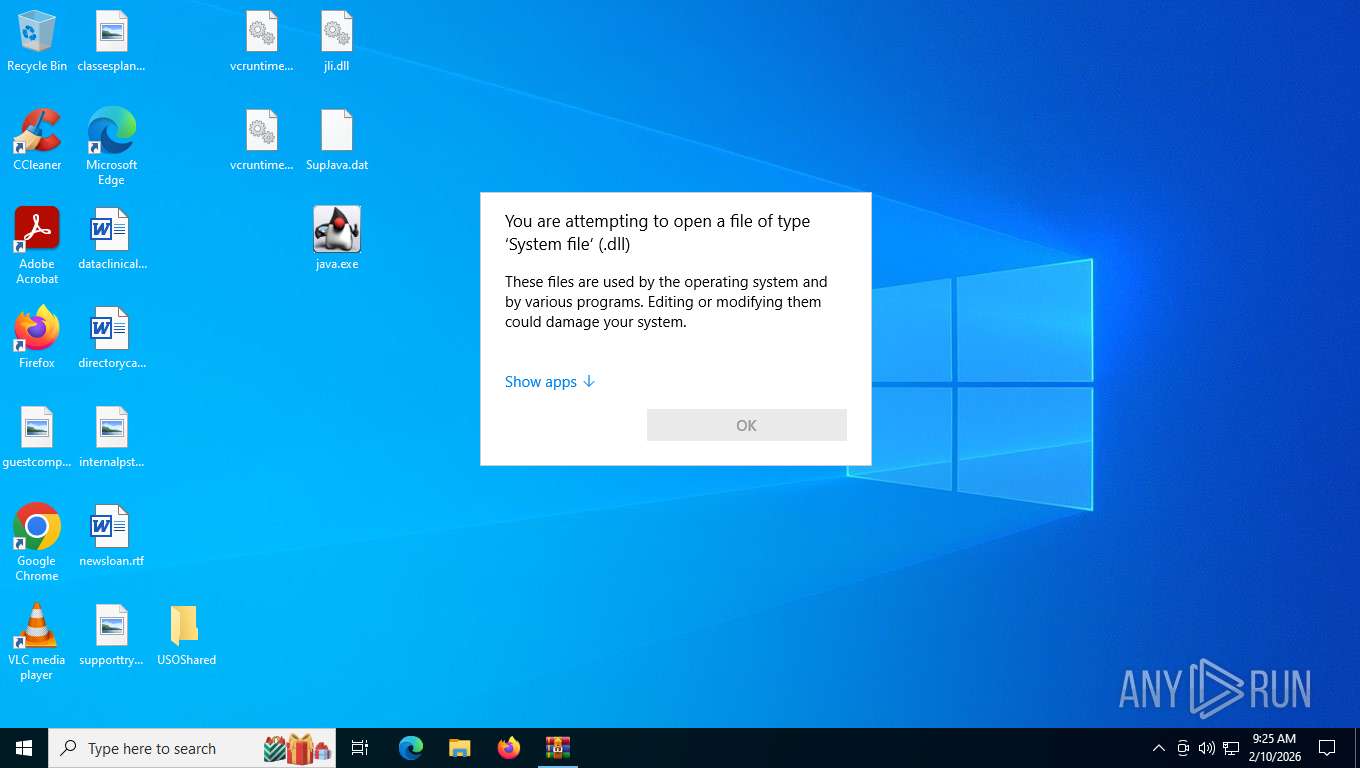
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5260)
- OpenWith.exe (PID: 8968)
- OpenWith.exe (PID: 5216)
The sample compiled with english language support
- WinRAR.exe (PID: 8820)
Checks supported languages
- java.exe (PID: 1188)
- java.exe (PID: 6444)
- java.exe (PID: 6096)
Reads the machine GUID from the registry
- java.exe (PID: 1188)
- java.exe (PID: 6096)
- java.exe (PID: 6444)
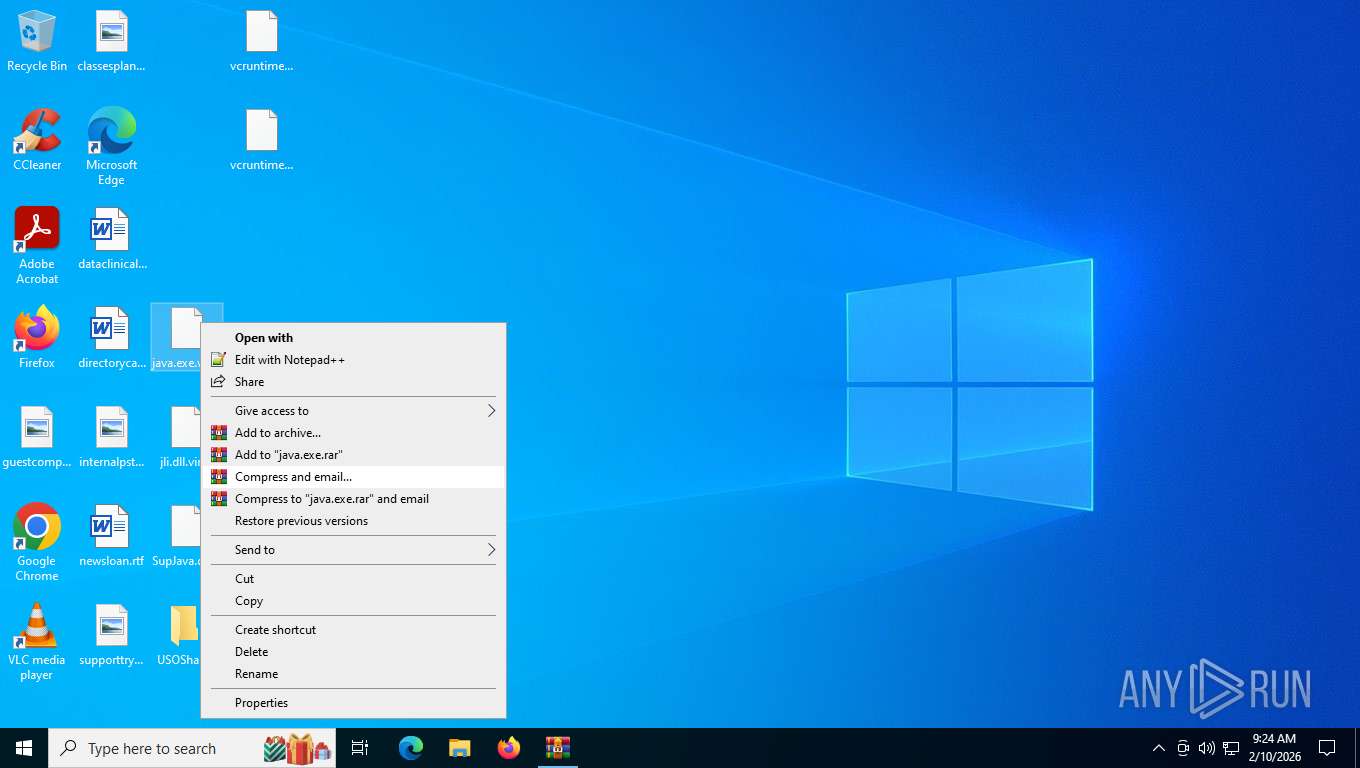
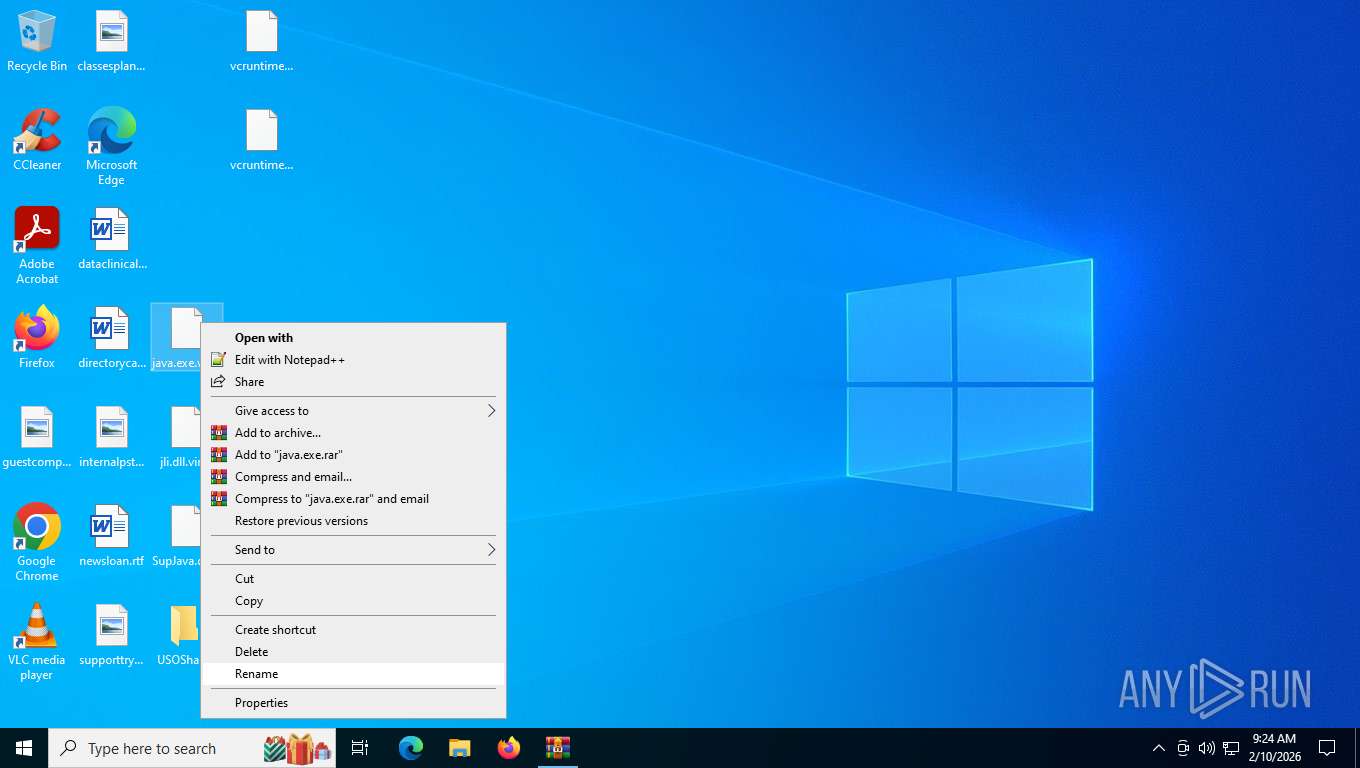
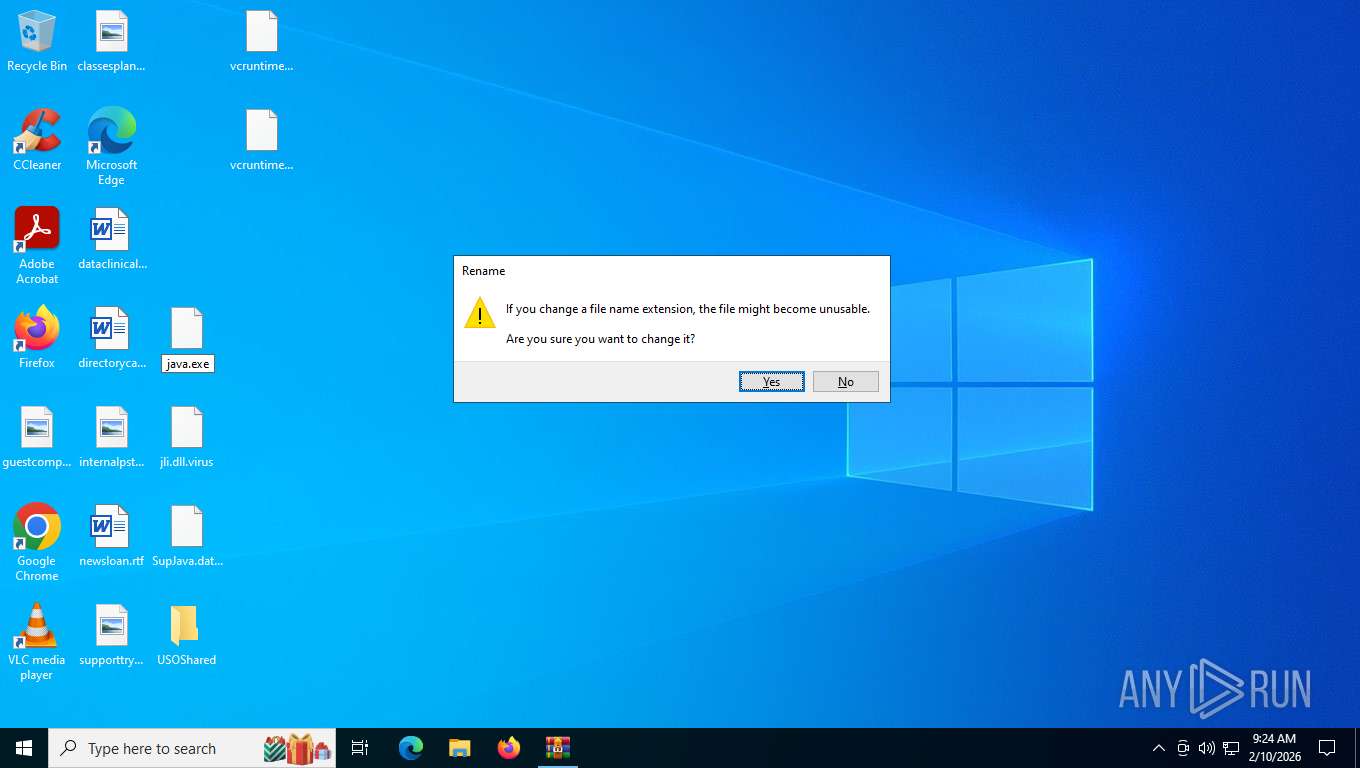
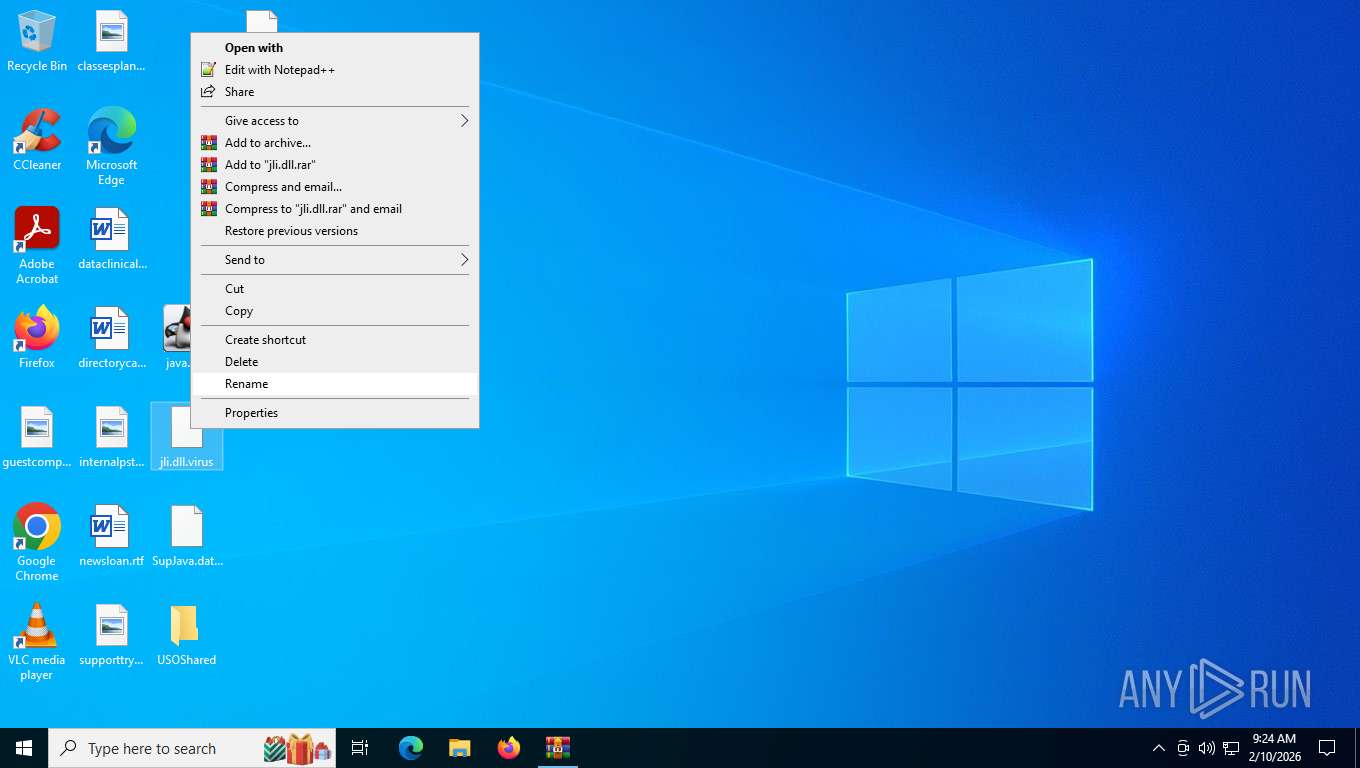
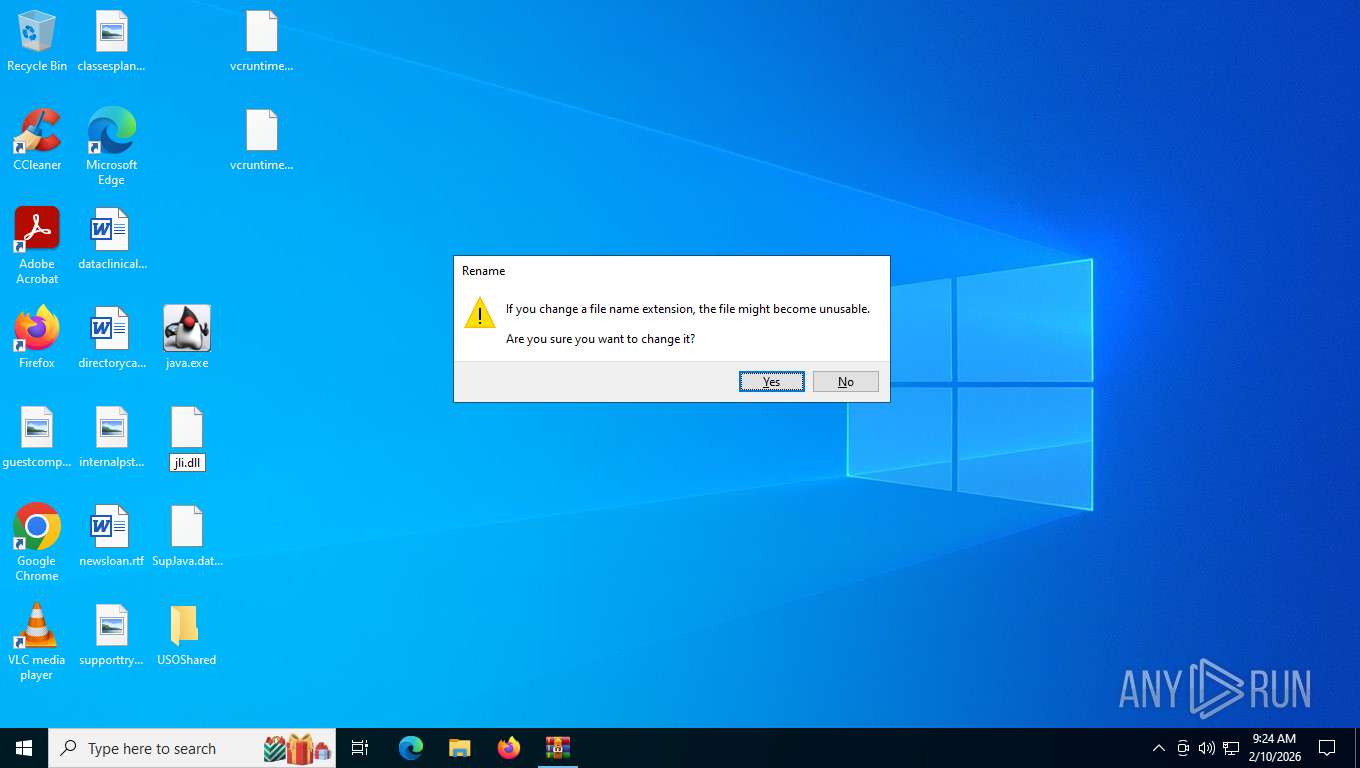
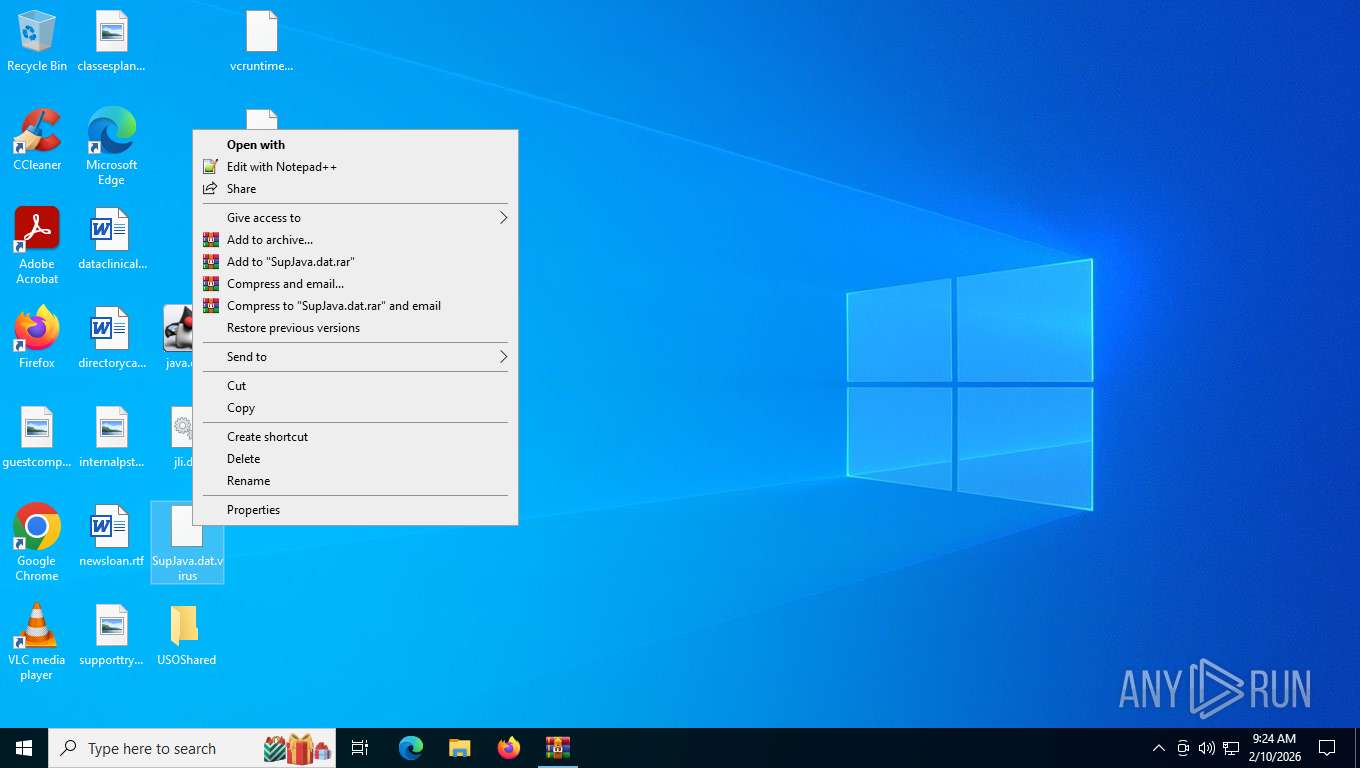
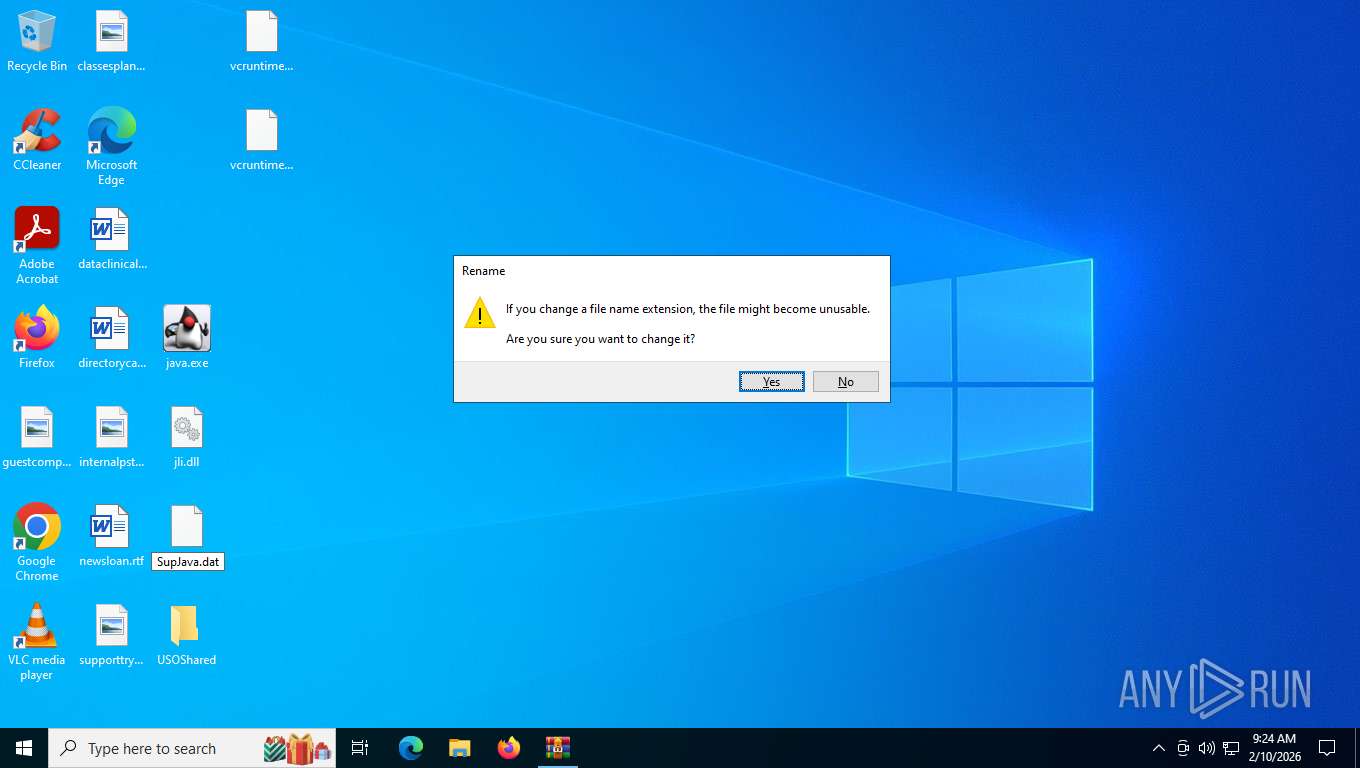
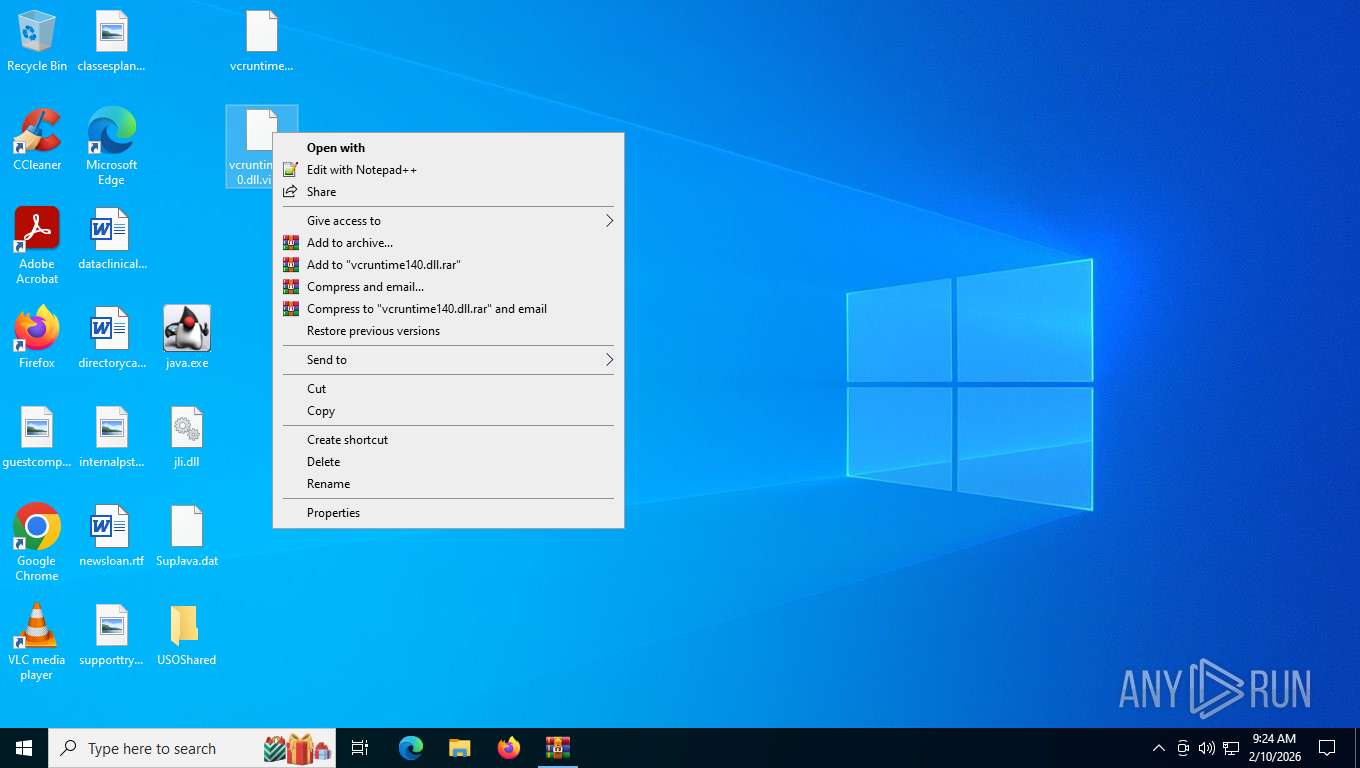
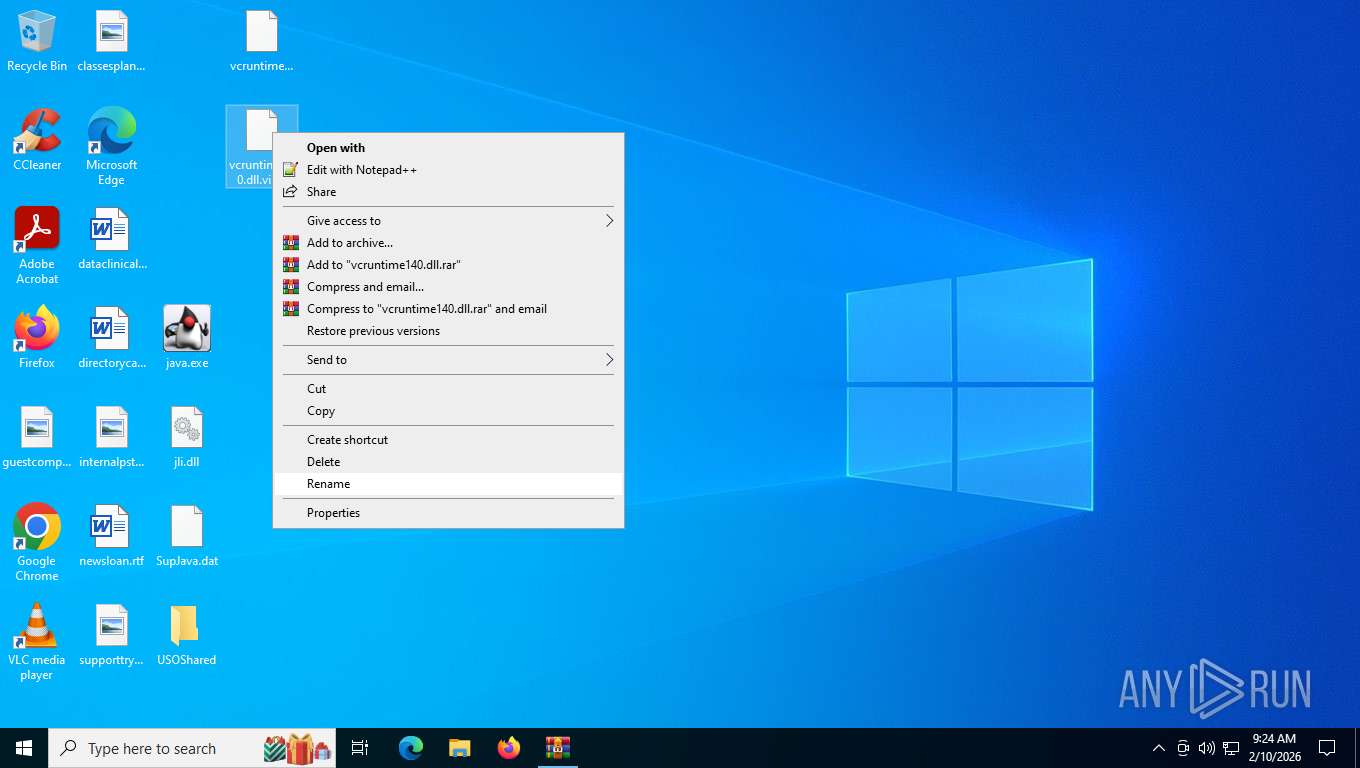
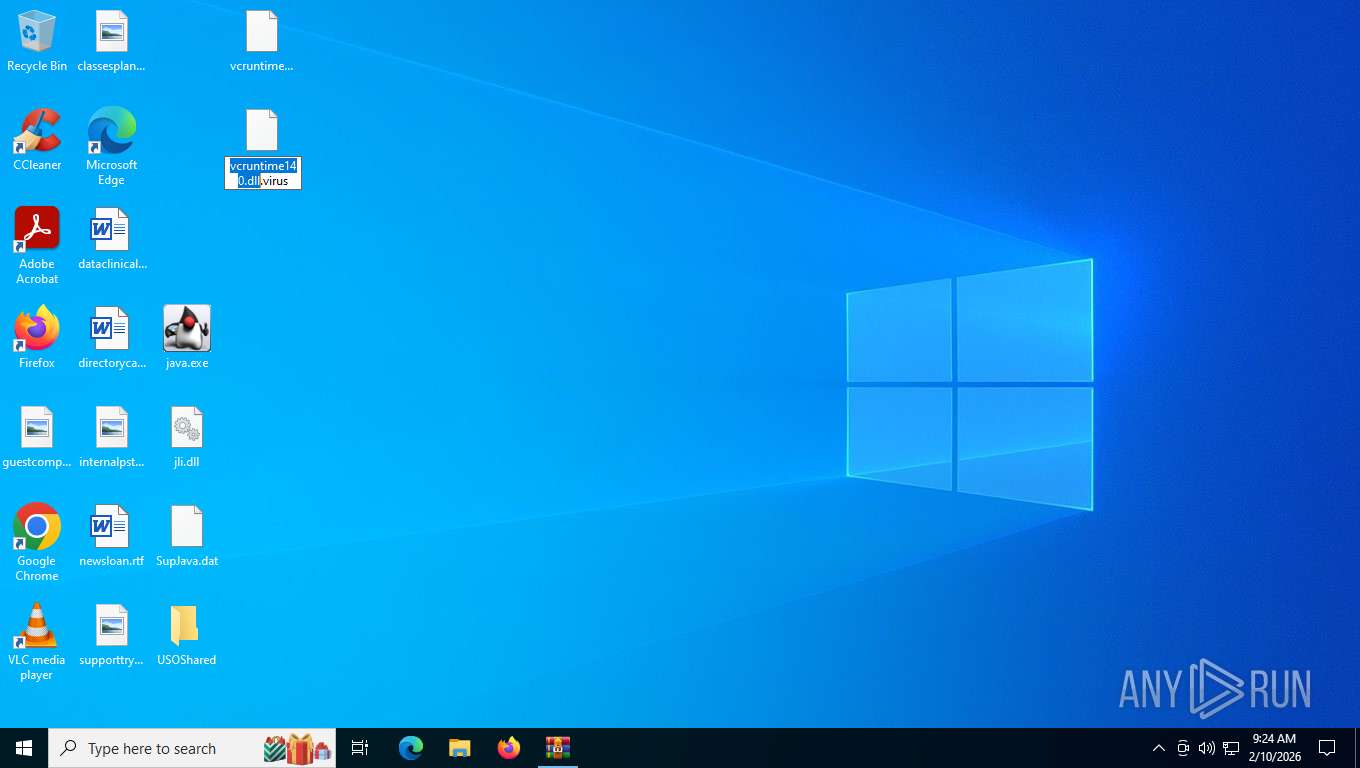
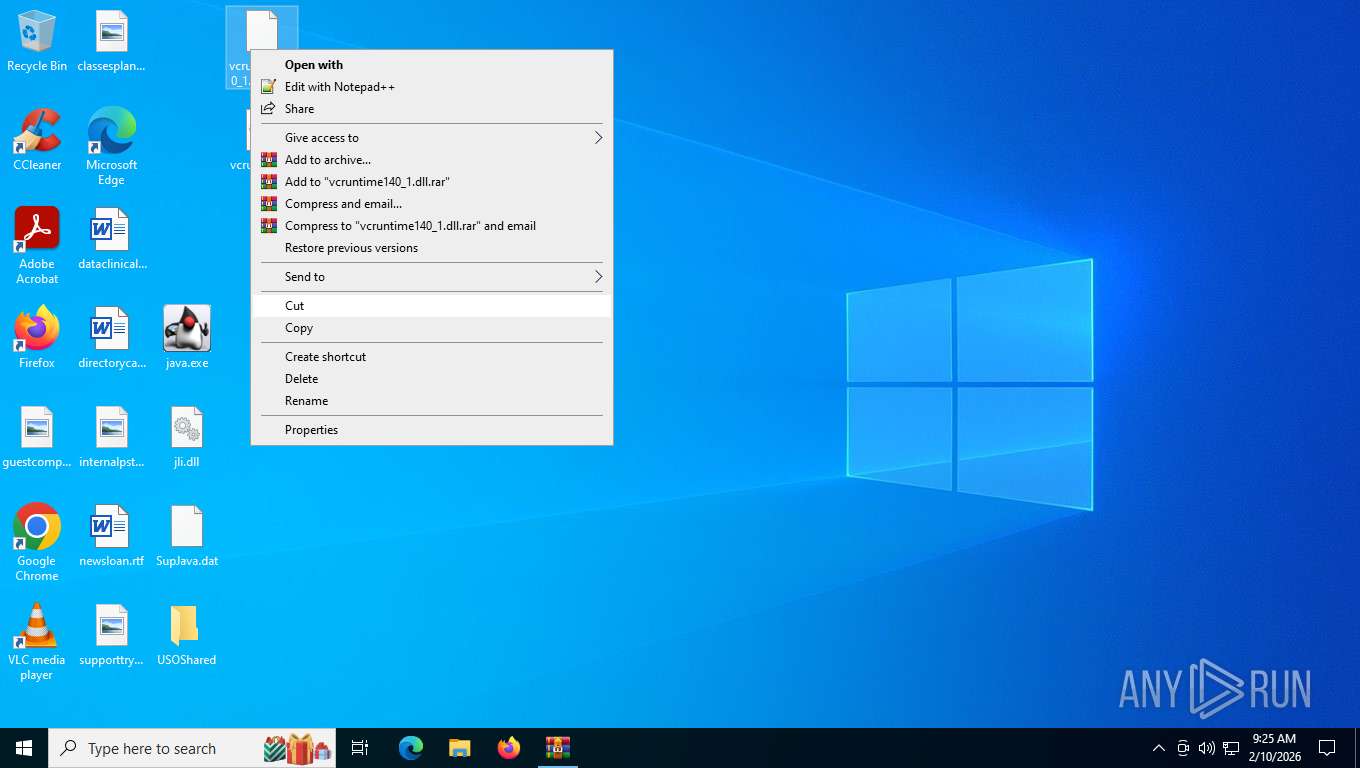
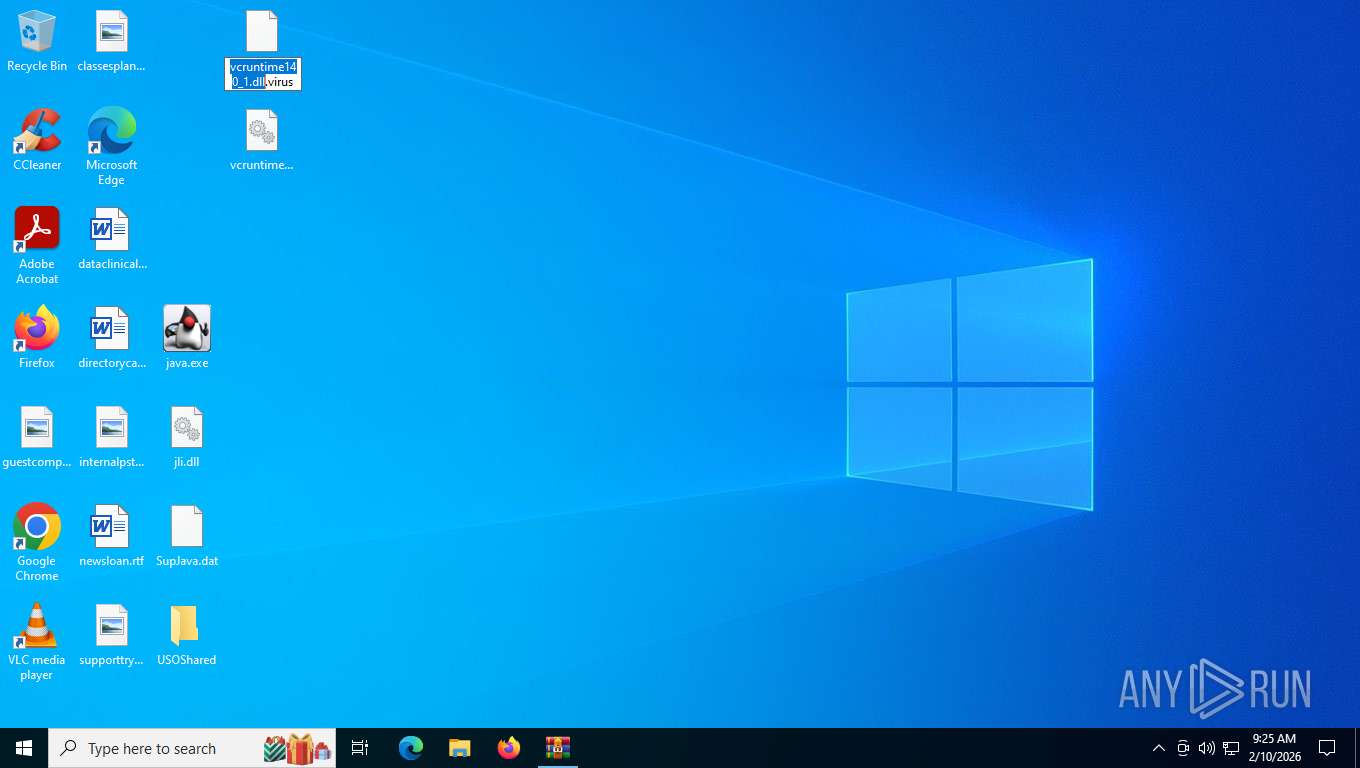
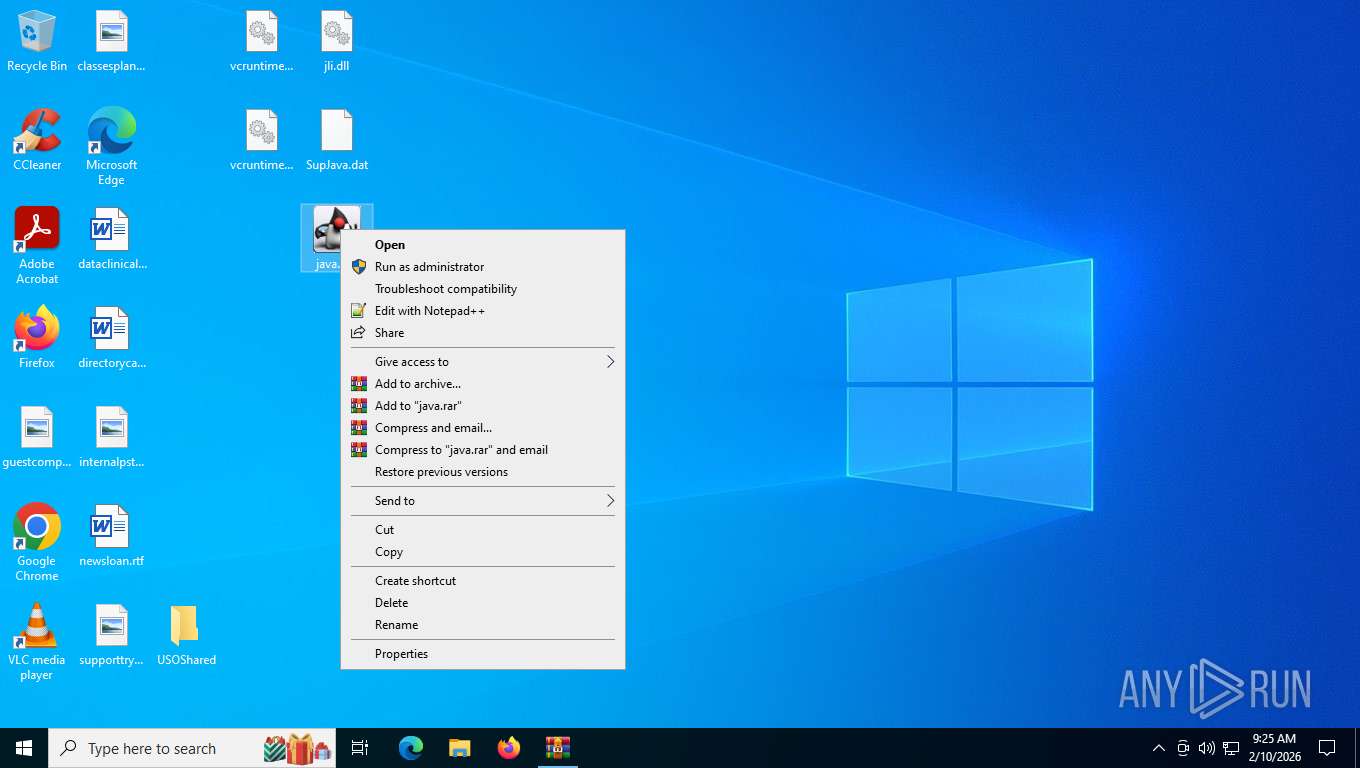
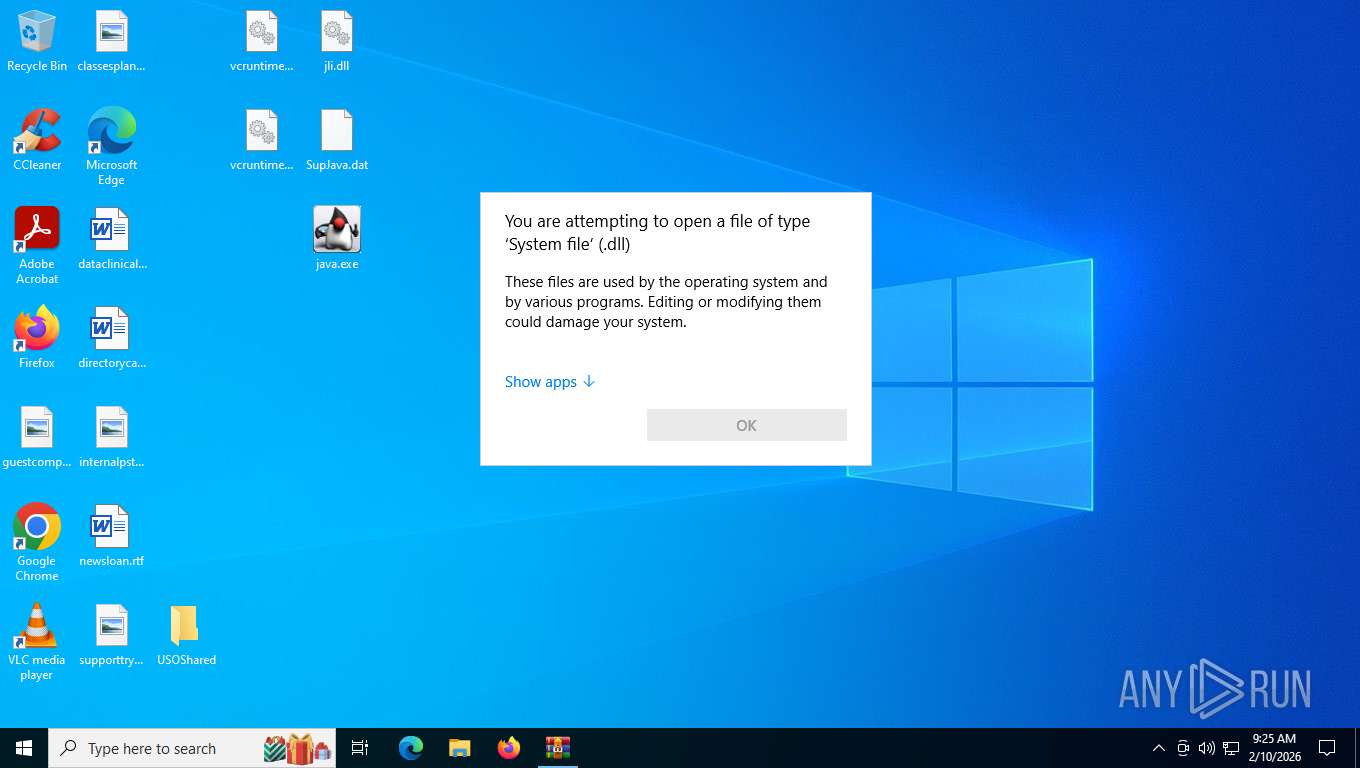
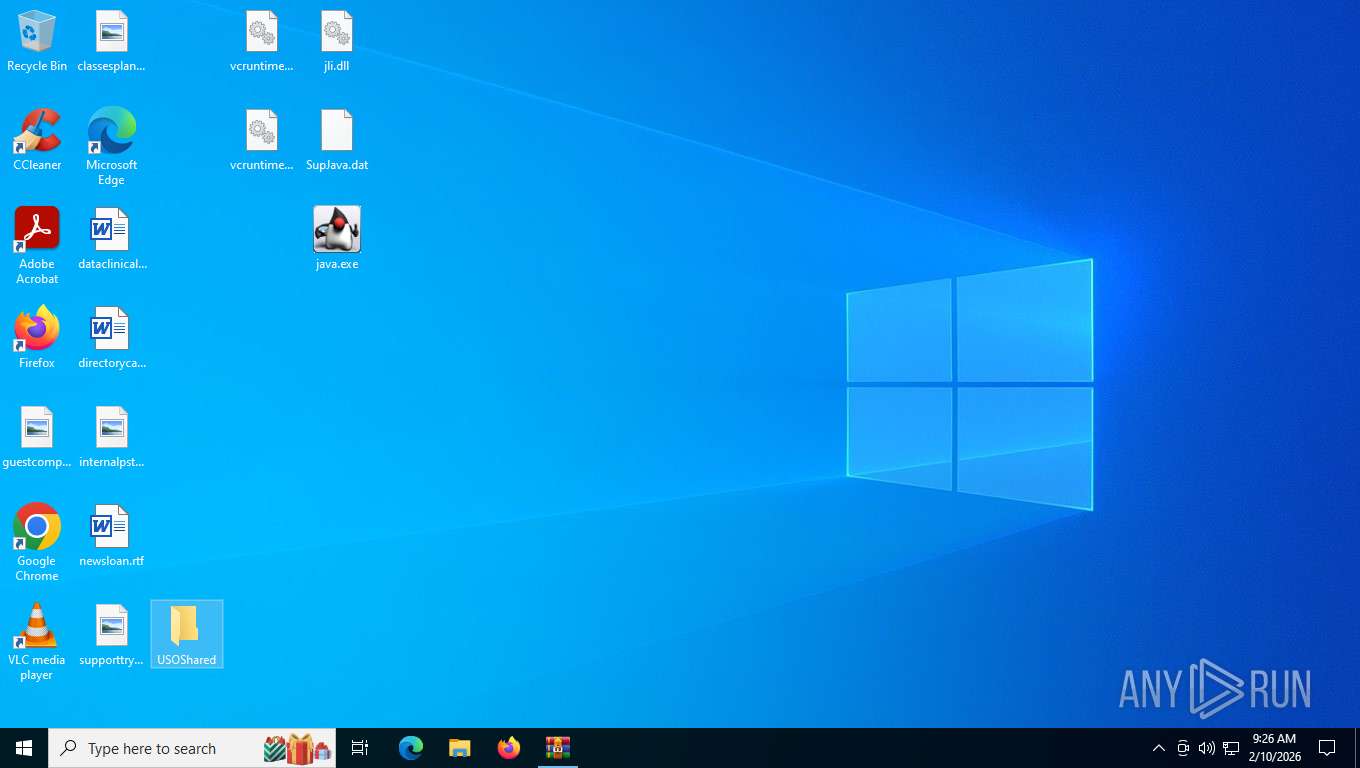
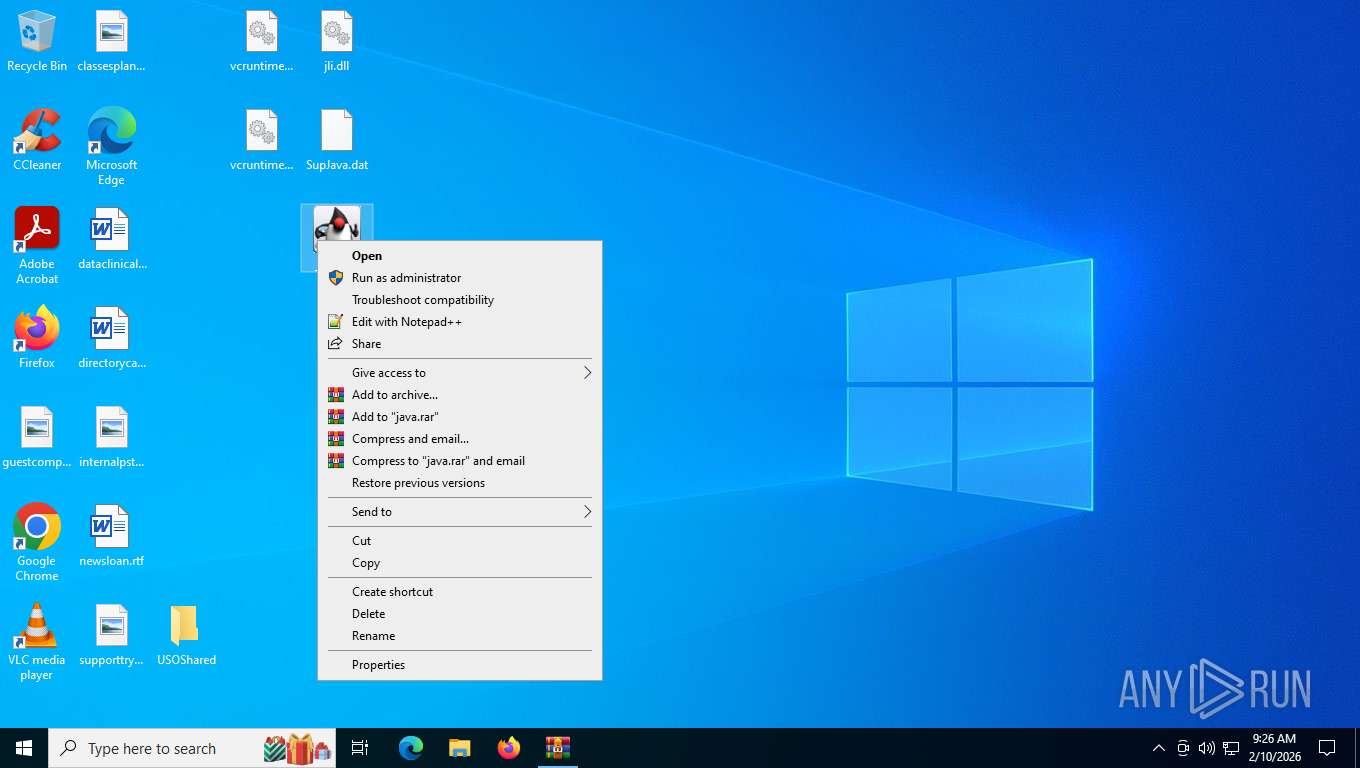
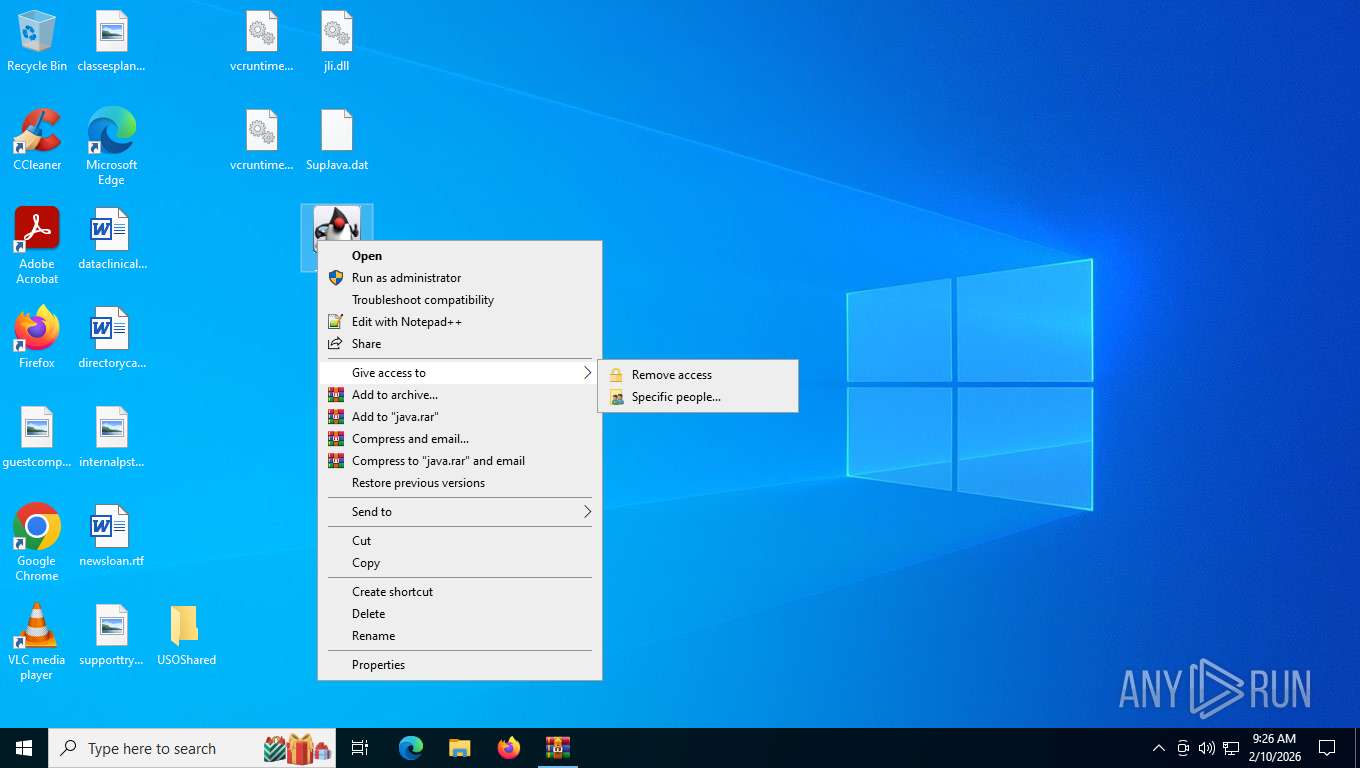
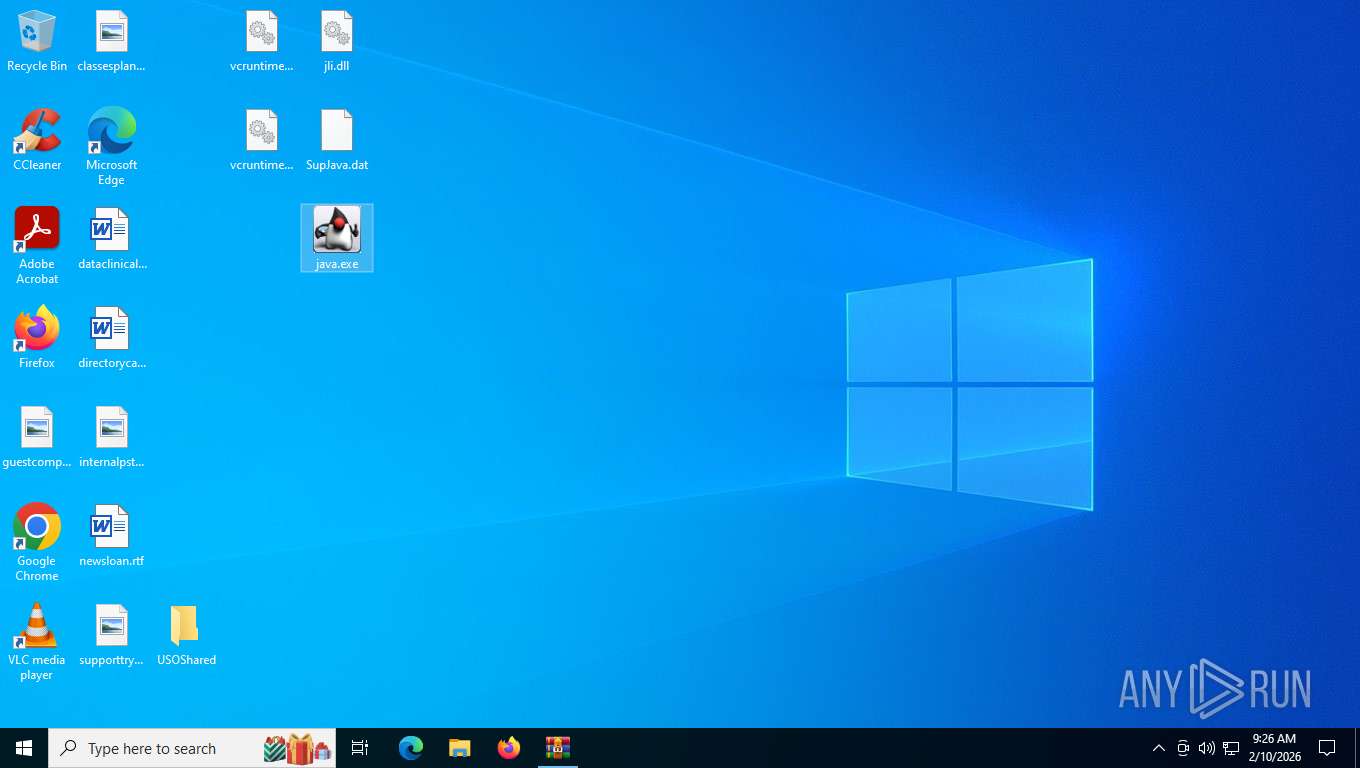
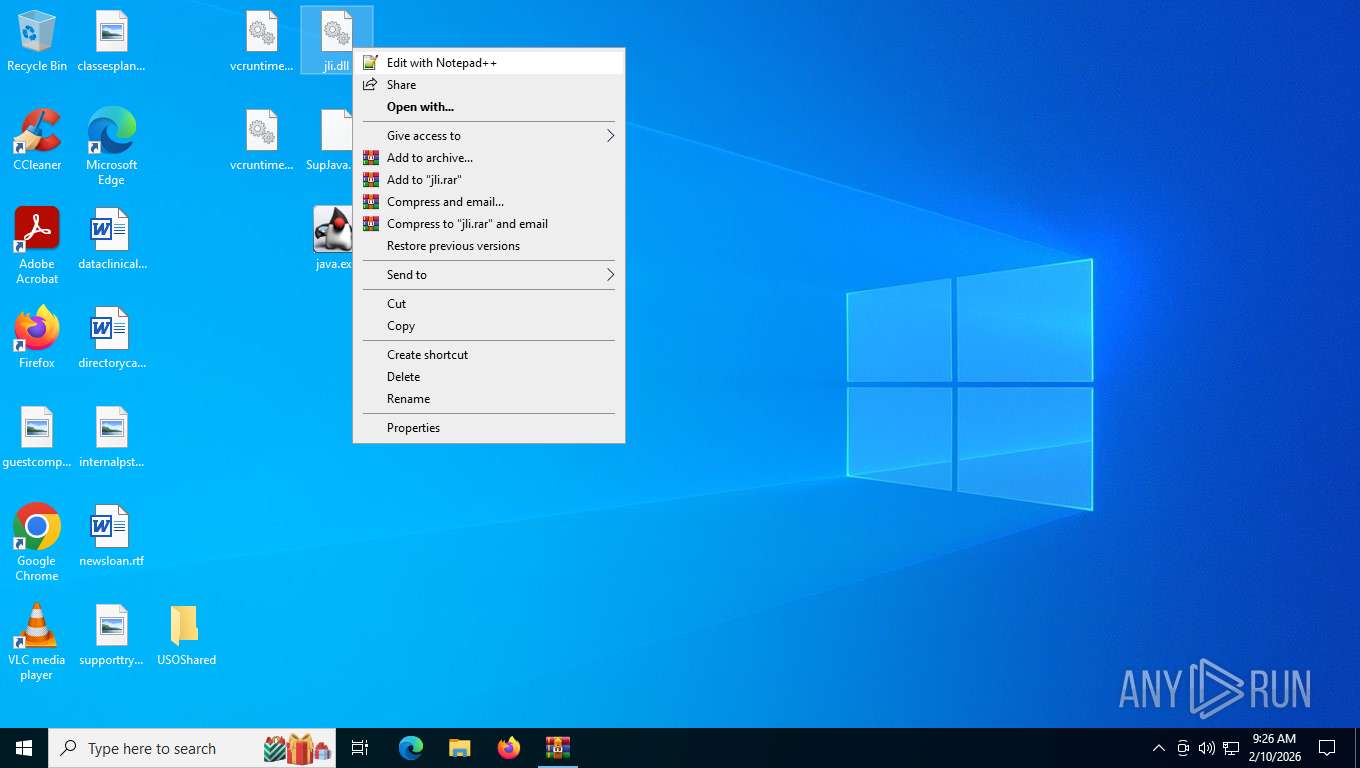
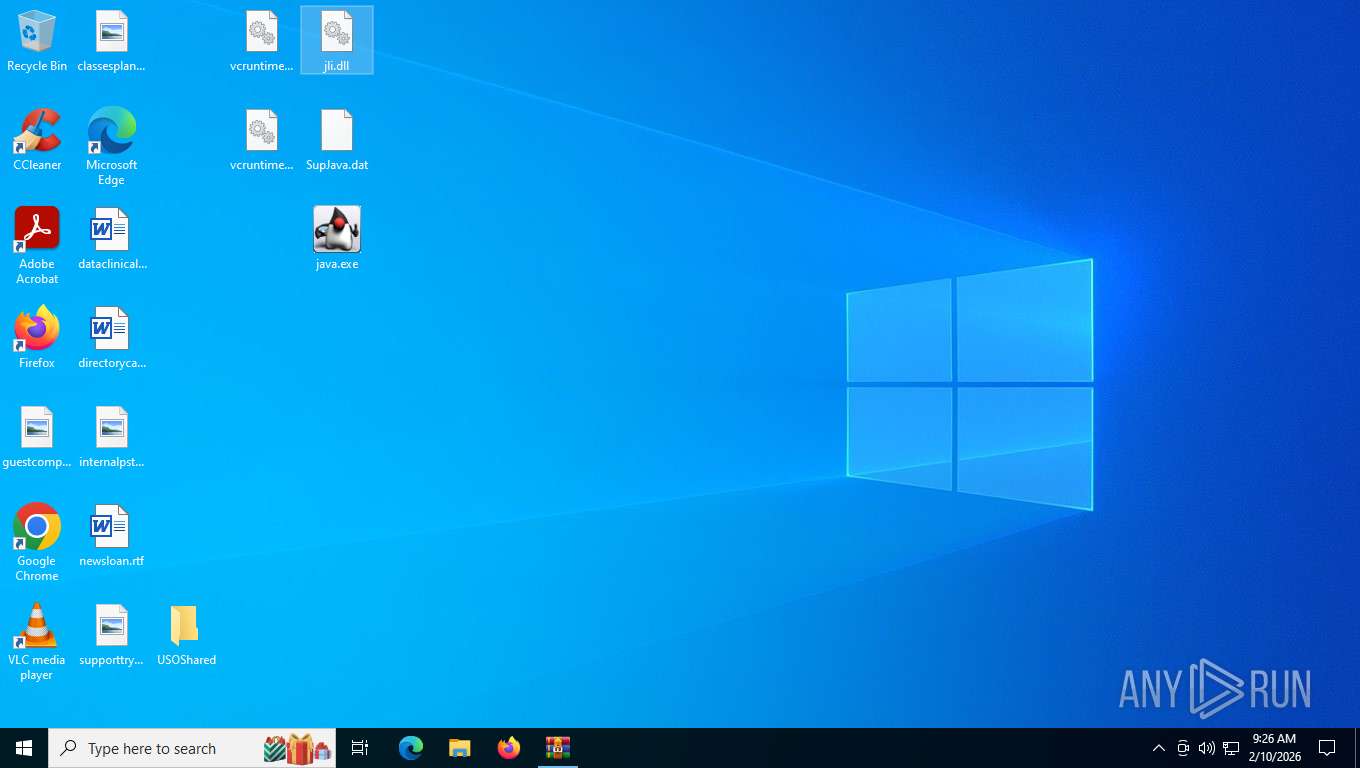
Manual execution by a user
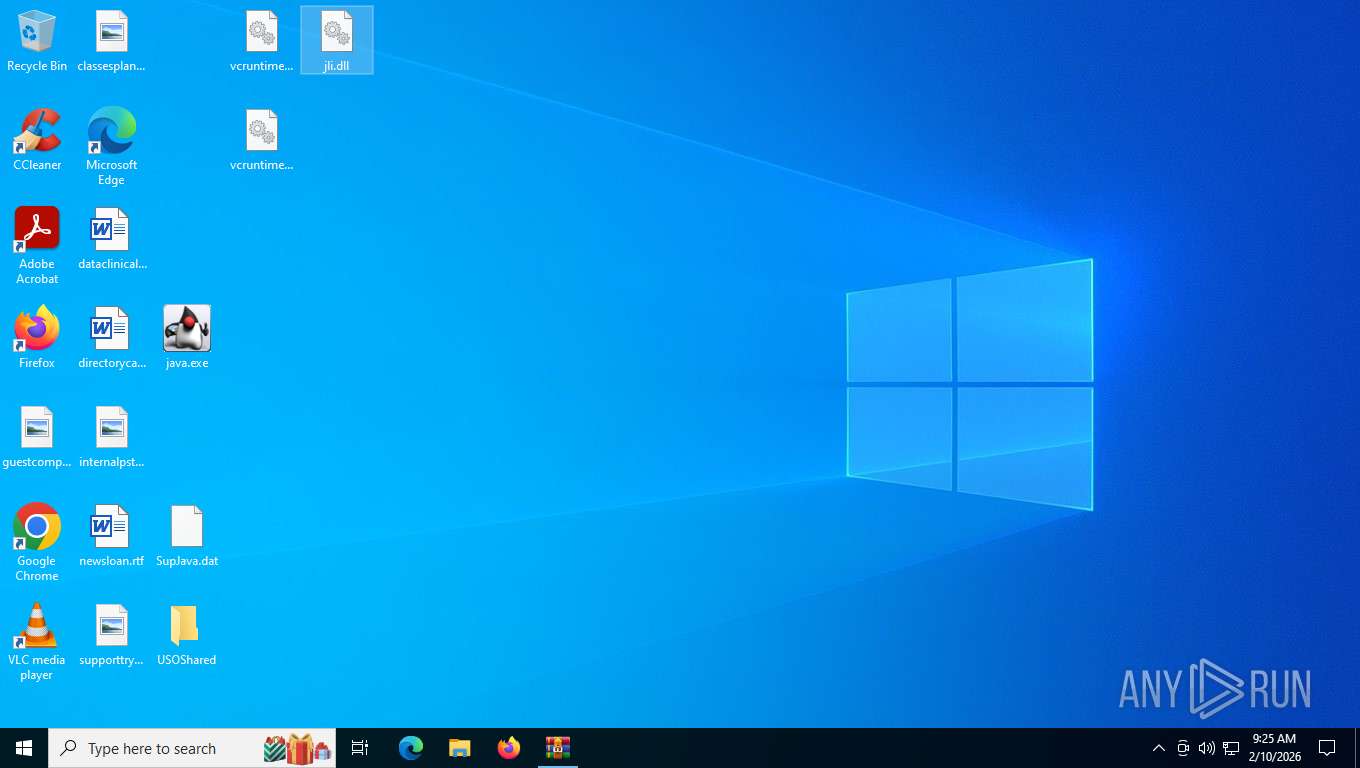
- java.exe (PID: 6096)
- java.exe (PID: 6444)
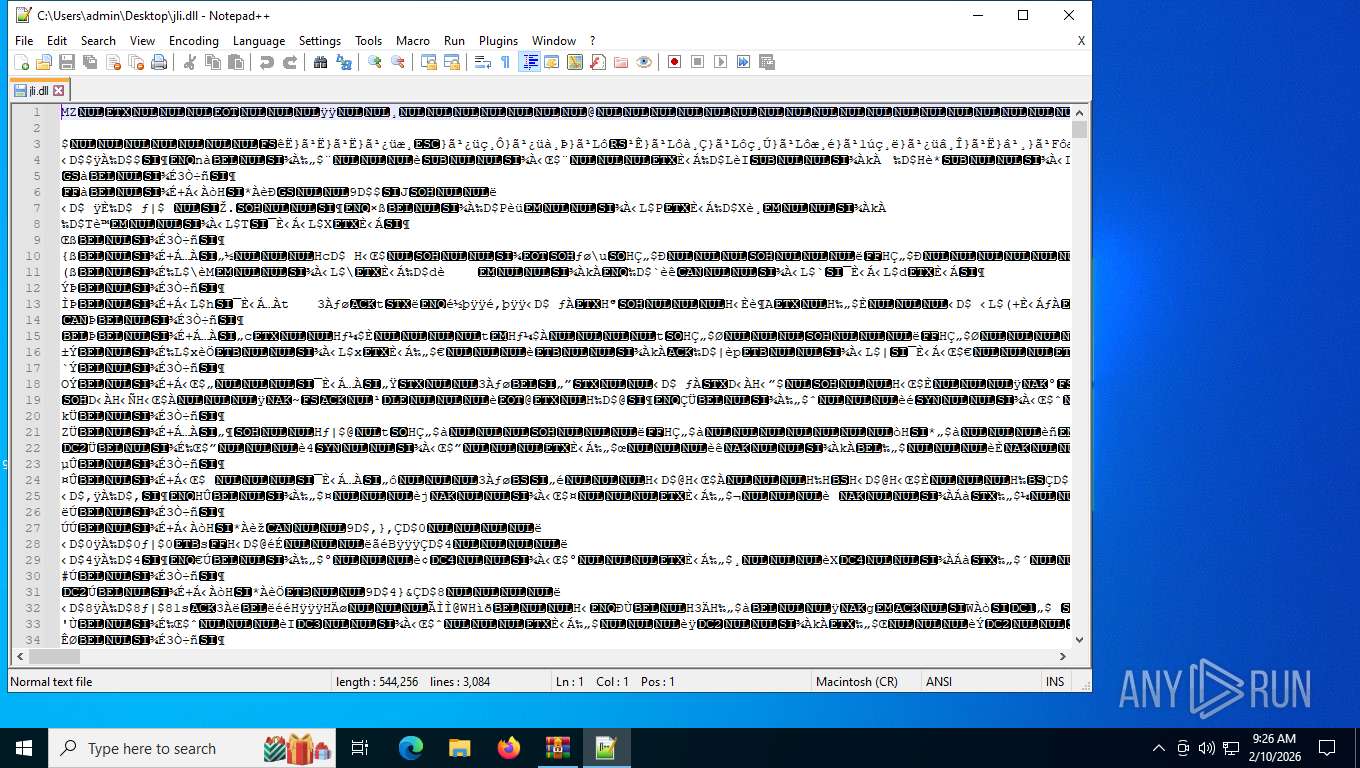
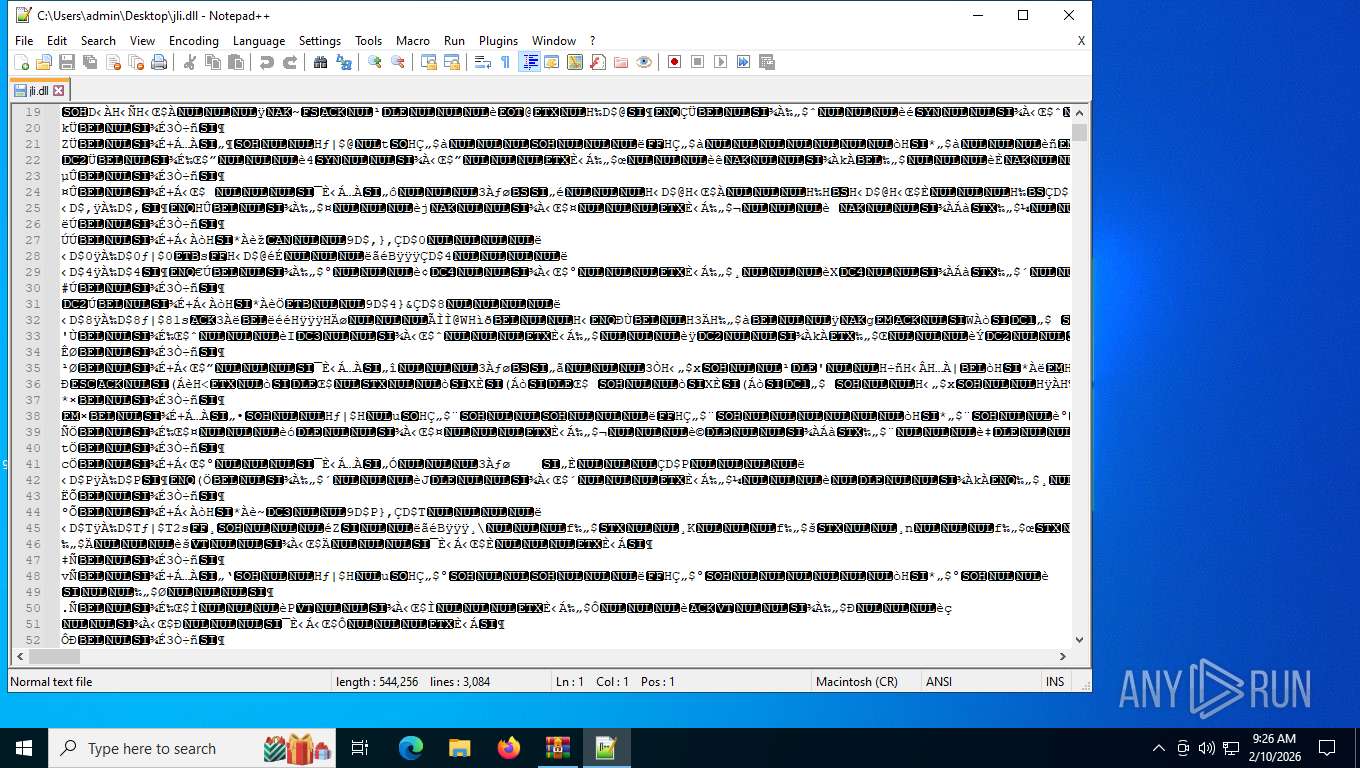
- notepad++.exe (PID: 8320)
- java.exe (PID: 1188)
Creates files or folders in the user directory
- WerFault.exe (PID: 4140)
- WerFault.exe (PID: 7544)
- WerFault.exe (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(1188) java.exe
Decrypted-URLs (1)https://www.google.com/?q=dj1
(PID) Process(6096) java.exe
Decrypted-URLs (1)https://www.google.com/?q=dj1
(PID) Process(6444) java.exe
Decrypted-URLs (1)https://www.google.com/?q=dj1
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2026:02:09 14:22:42+00:00 |
| ArchivedFileName: | USOShared |
Total processes
169
Monitored processes
15
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
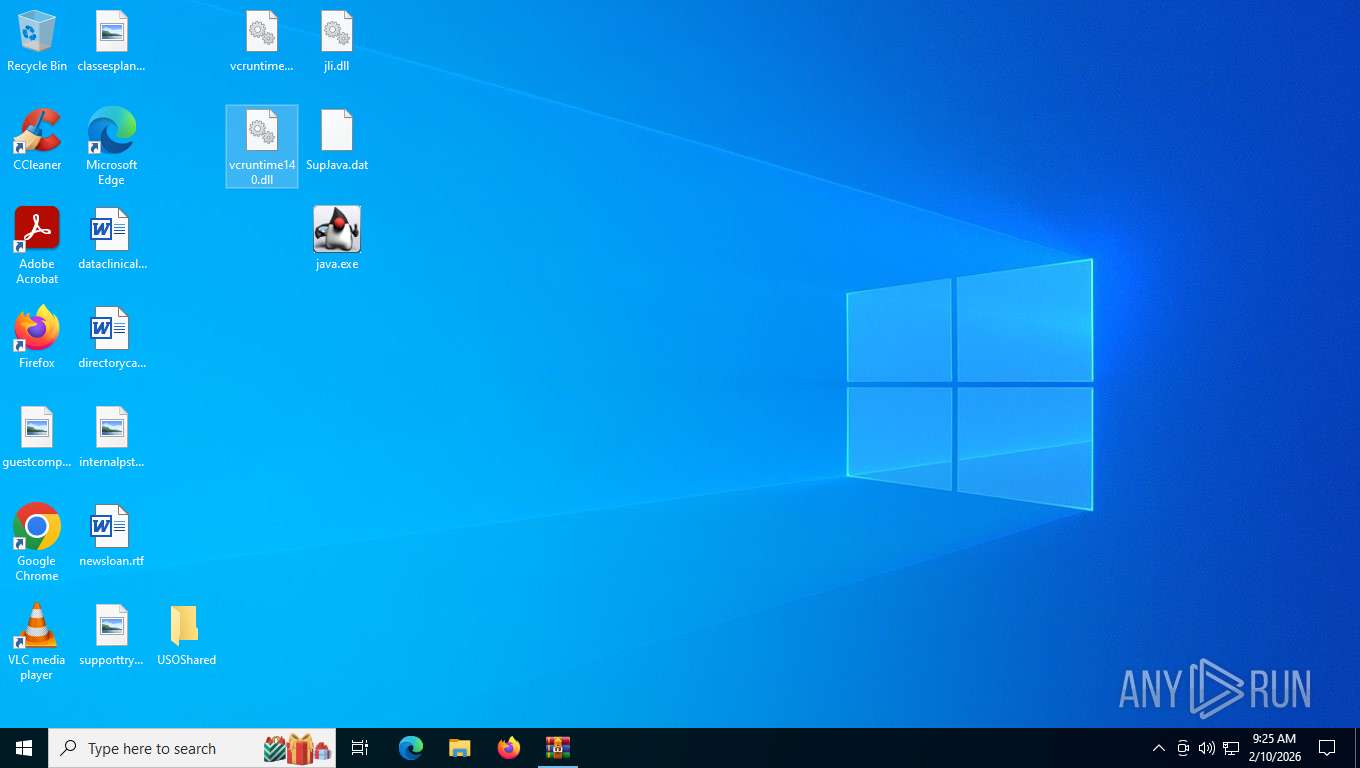
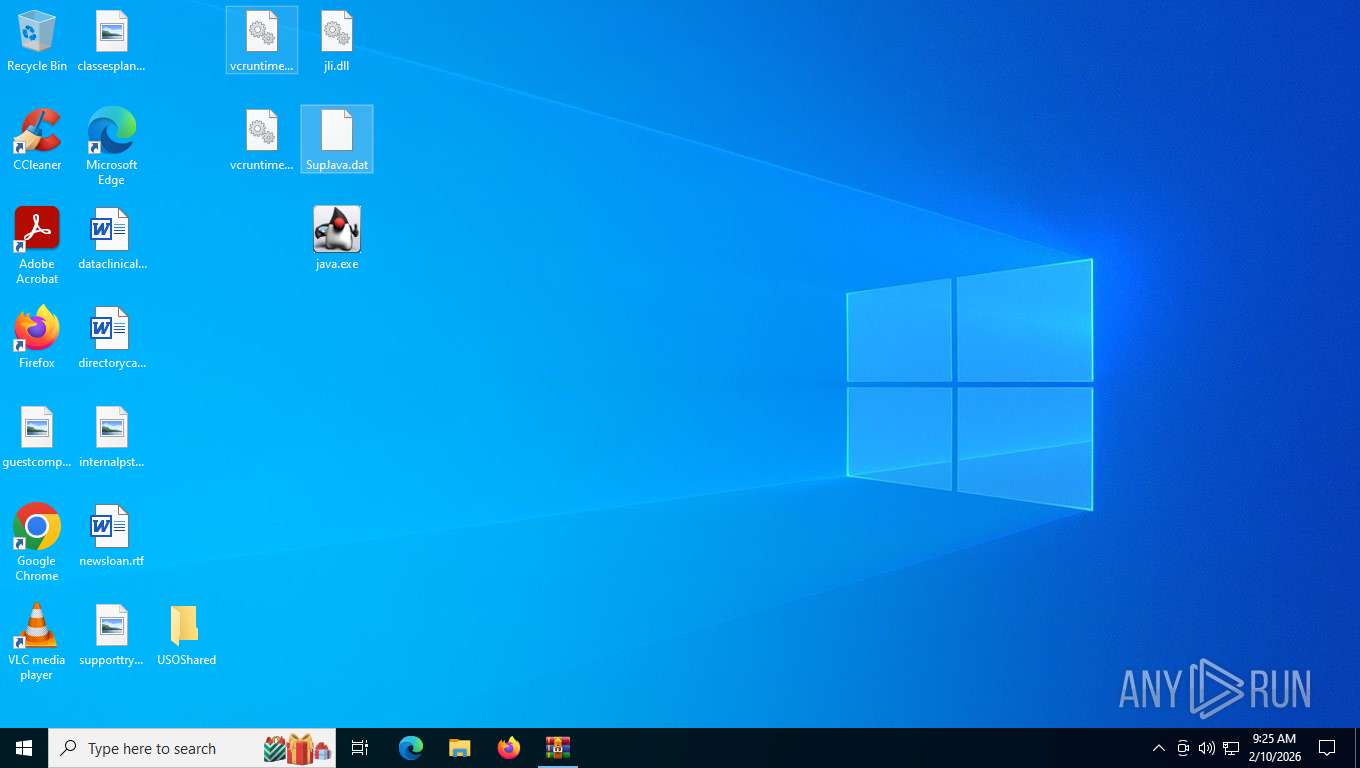
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | "C:\Users\admin\Desktop\java.exe" | C:\Users\admin\Desktop\java.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: OpenJDK Platform binary Exit code: 3221225477 Version: 16.0.2.0 Modules
xor-url(PID) Process(1188) java.exe Decrypted-URLs (1)https://www.google.com/?q=dj1 | |||||||||||||||
| 2548 | C:\WINDOWS\system32\WerFault.exe -u -p 6444 -s 972 | C:\Windows\System32\WerFault.exe | java.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4140 | C:\WINDOWS\system32\WerFault.exe -u -p 6096 -s 976 | C:\Windows\System32\WerFault.exe | java.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5216 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5260 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5580 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6096 | "C:\Users\admin\Desktop\java.exe" | C:\Users\admin\Desktop\java.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: OpenJDK Platform binary Exit code: 3221225477 Version: 16.0.2.0 Modules
xor-url(PID) Process(6096) java.exe Decrypted-URLs (1)https://www.google.com/?q=dj1 | |||||||||||||||
| 6300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
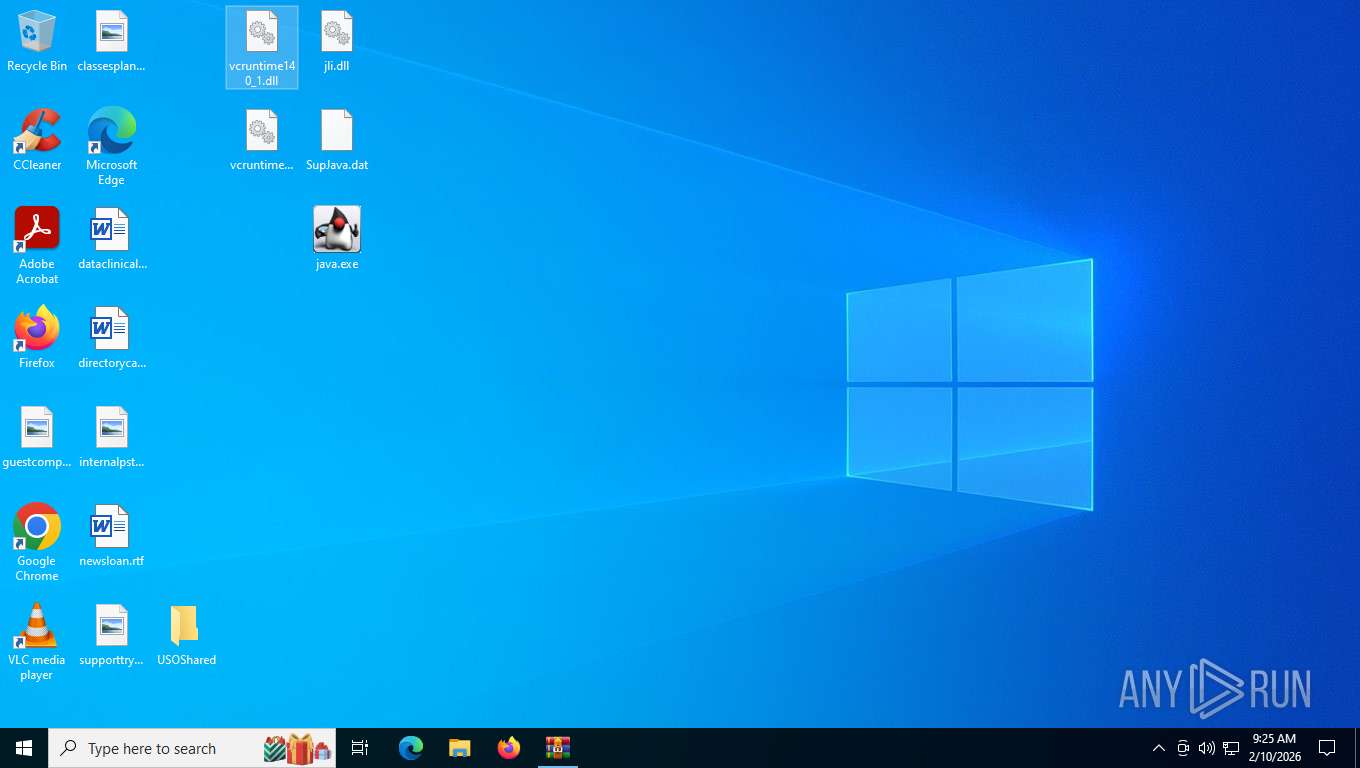
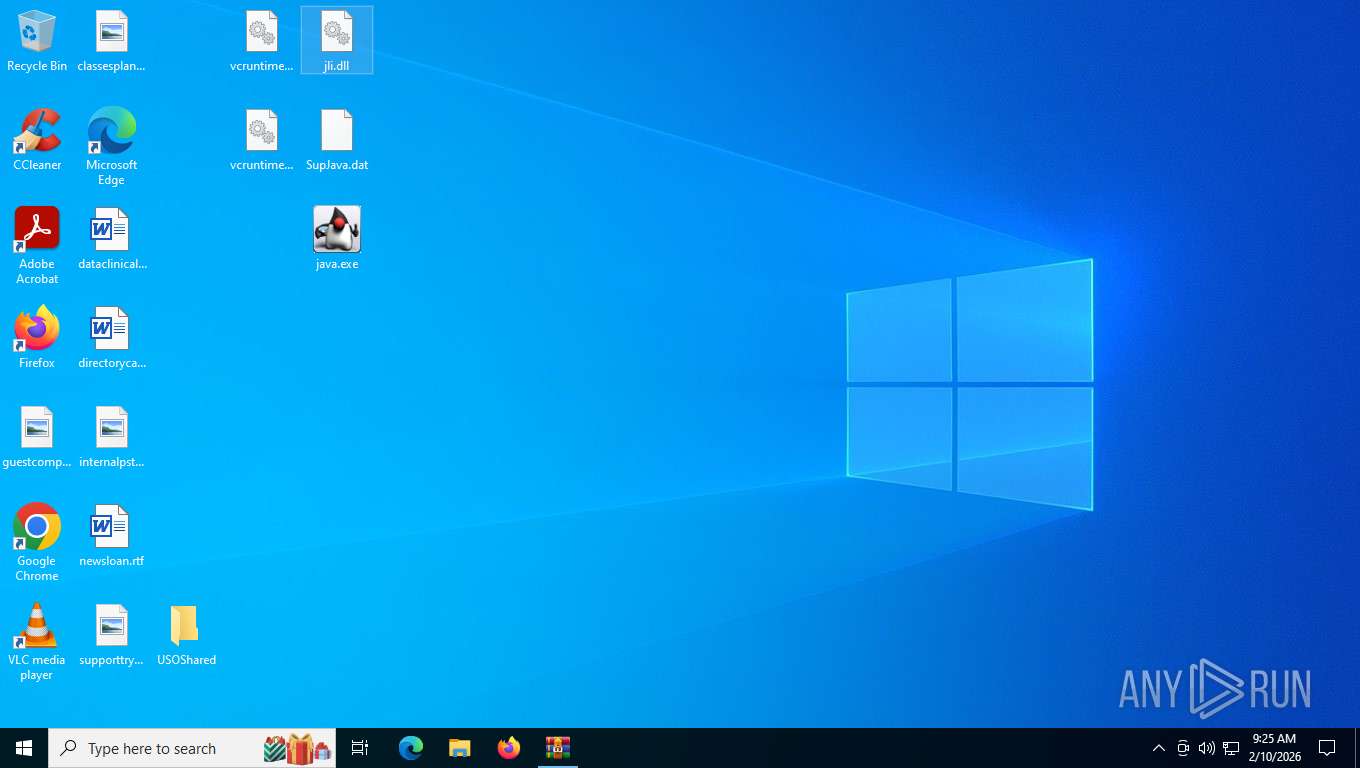
| 6444 | "C:\Users\admin\Desktop\java.exe" C:\Users\admin\Desktop\jli.dll | C:\Users\admin\Desktop\java.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: OpenJDK Platform binary Exit code: 3221225477 Version: 16.0.2.0 Modules
xor-url(PID) Process(6444) java.exe Decrypted-URLs (1)https://www.google.com/?q=dj1 | |||||||||||||||
| 7544 | C:\WINDOWS\system32\WerFault.exe -u -p 1188 -s 1516 | C:\Windows\System32\WerFault.exe | java.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 345
Read events
18 318
Write events
24
Delete events
3
Modification events
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\USOShared.7z | |||
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
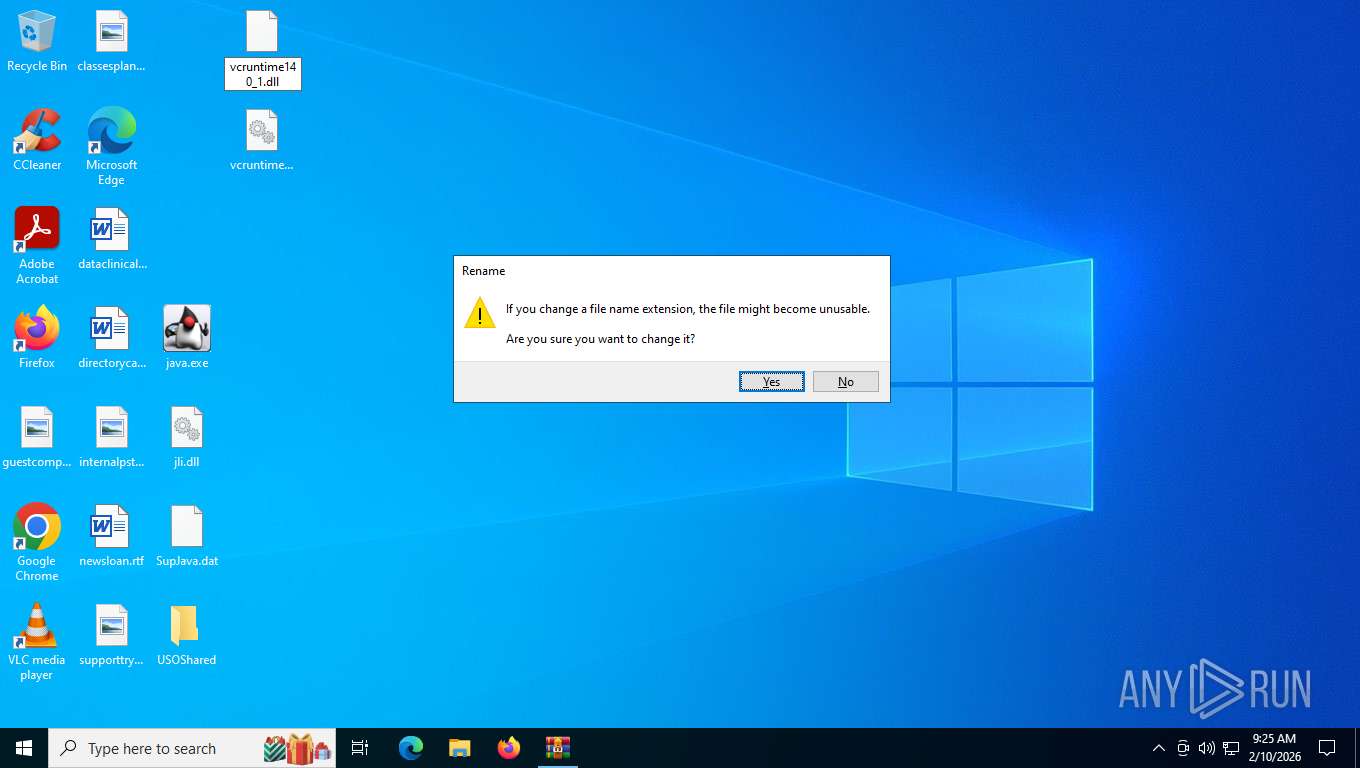
| (PID) Process: | (5216) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.dll\OpenWithProgids |
| Operation: | write | Name: | dllfile |
Value: | |||
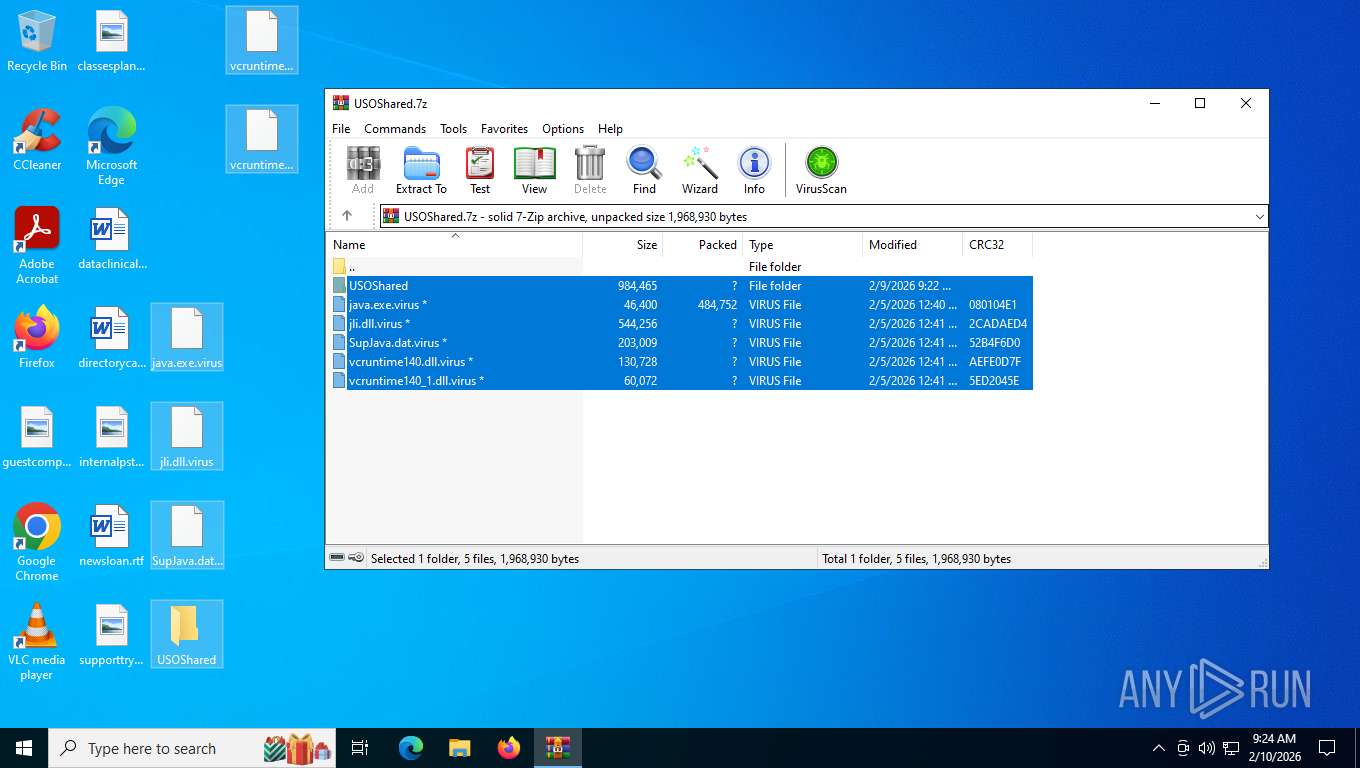
Executable files
8
Suspicious files
12
Text files
12
Unknown types
0
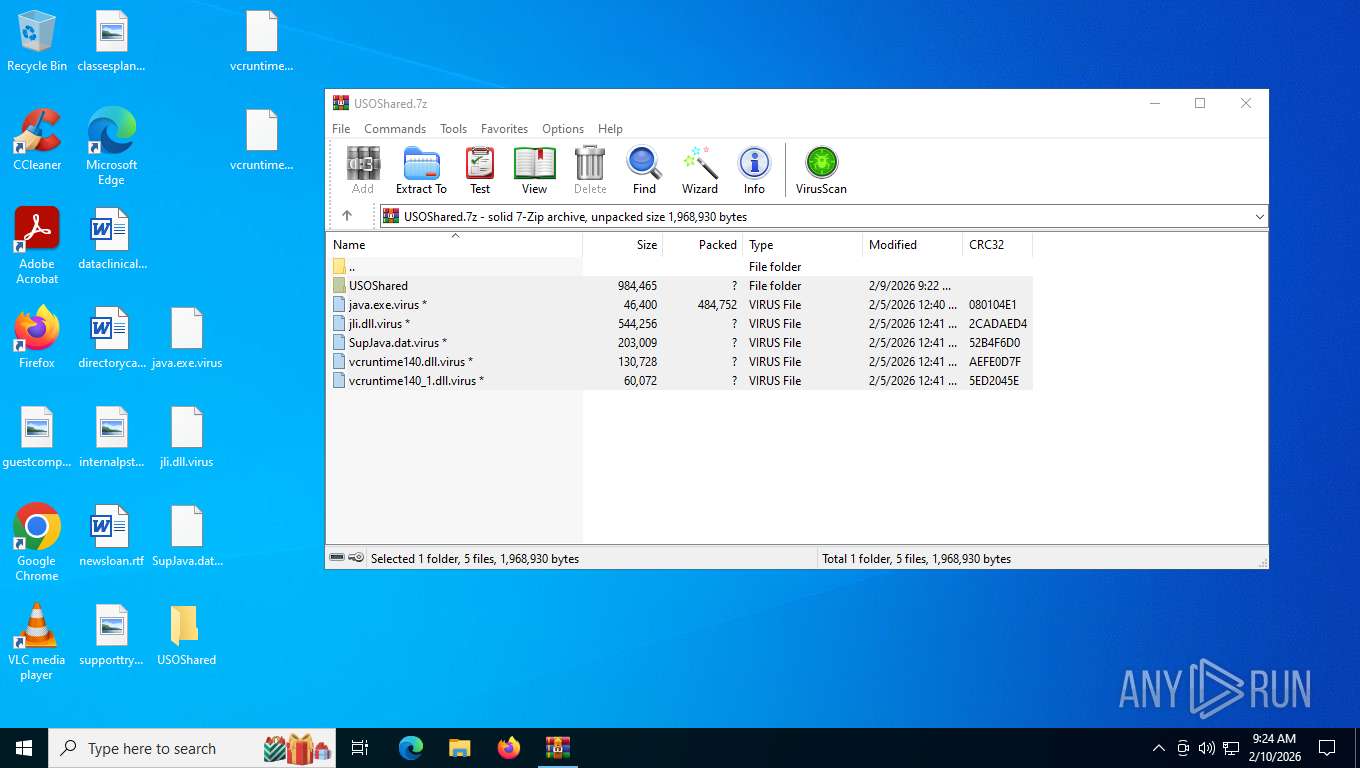
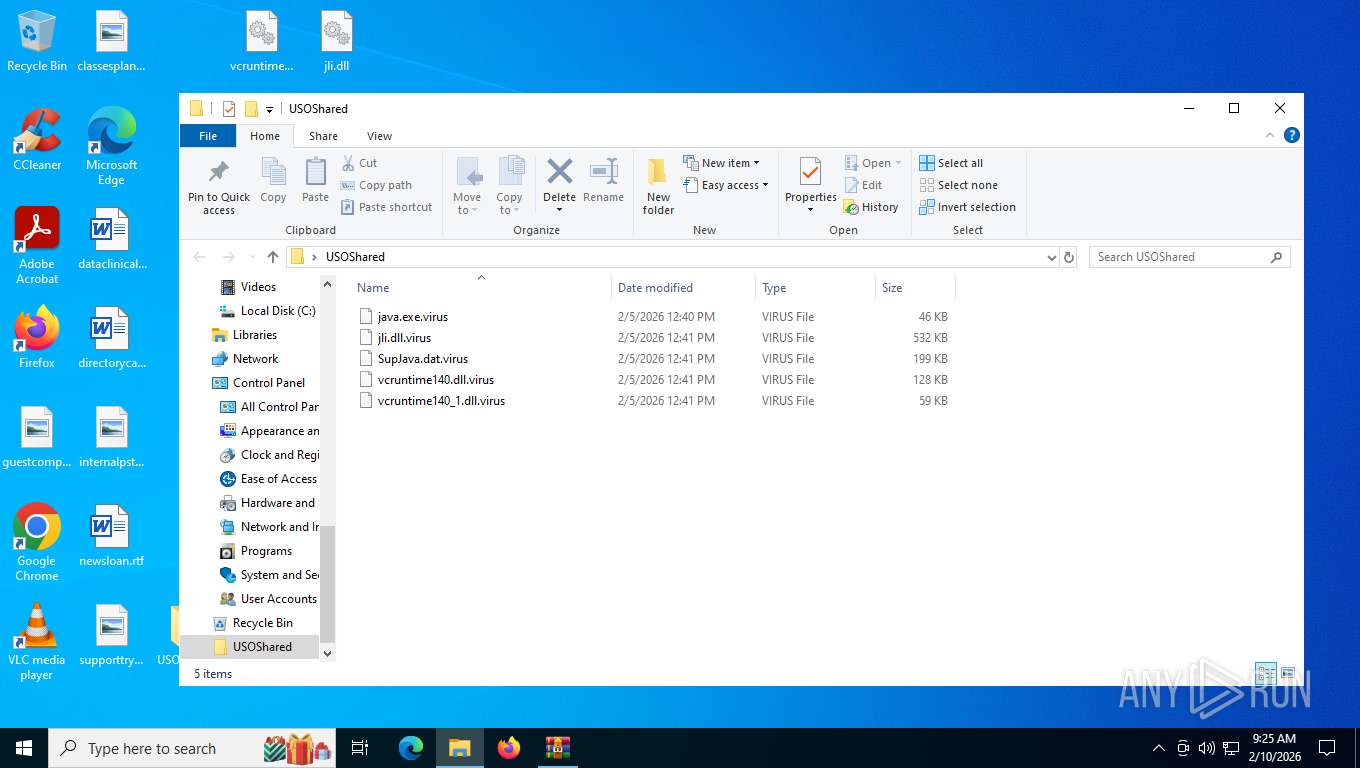
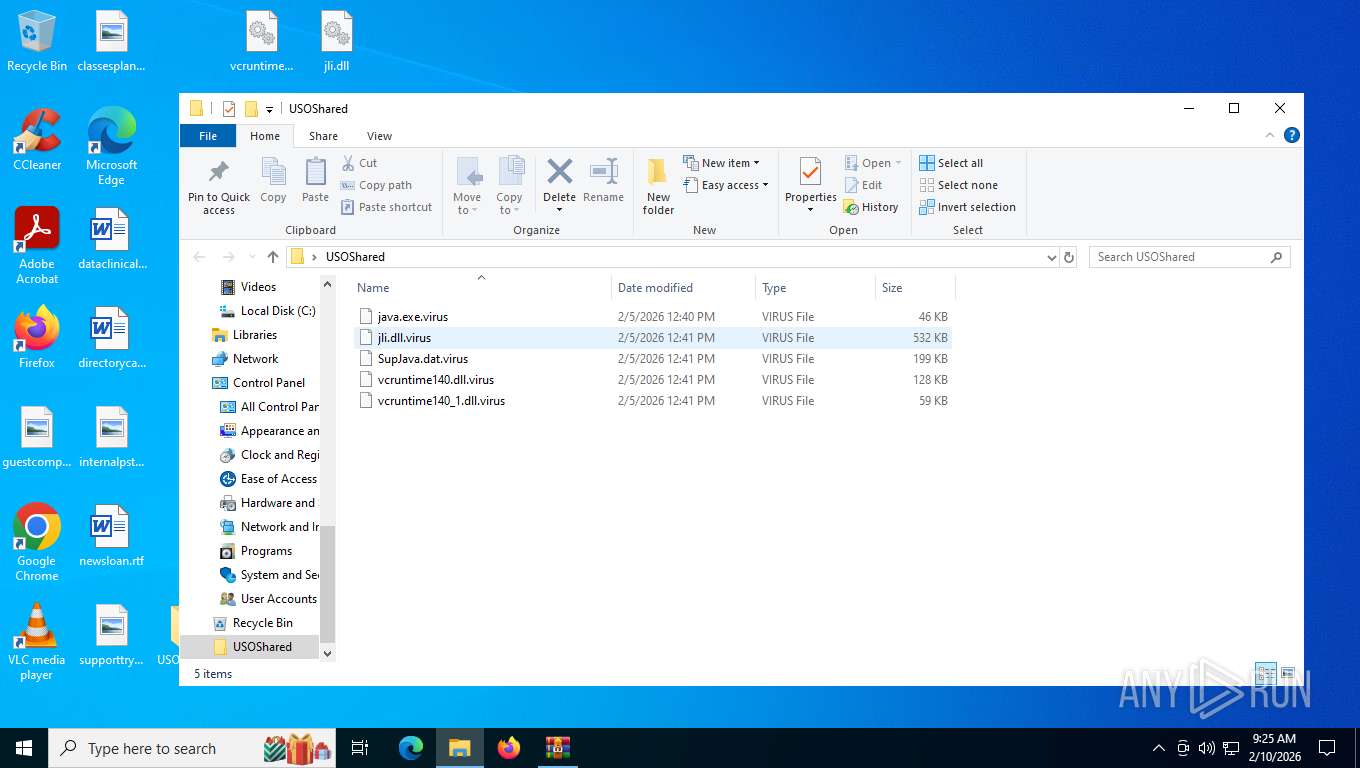
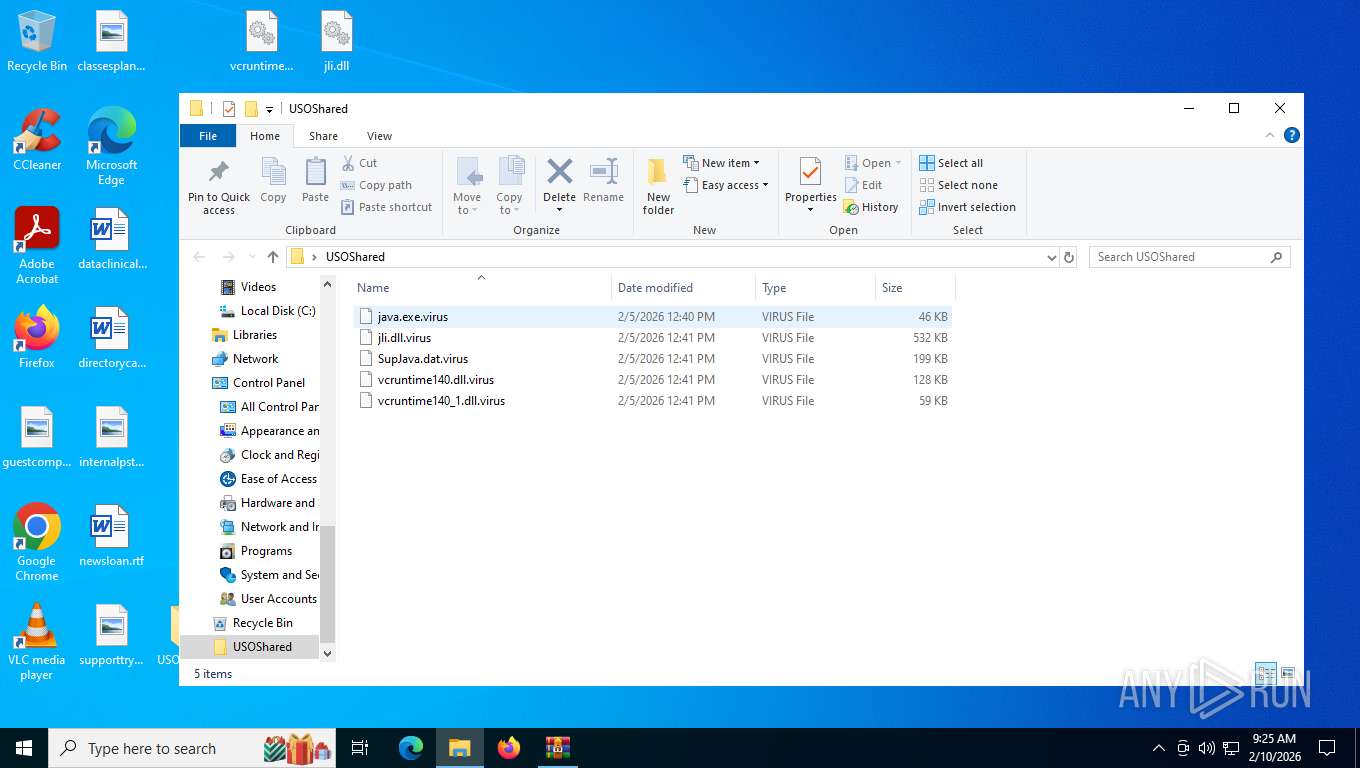
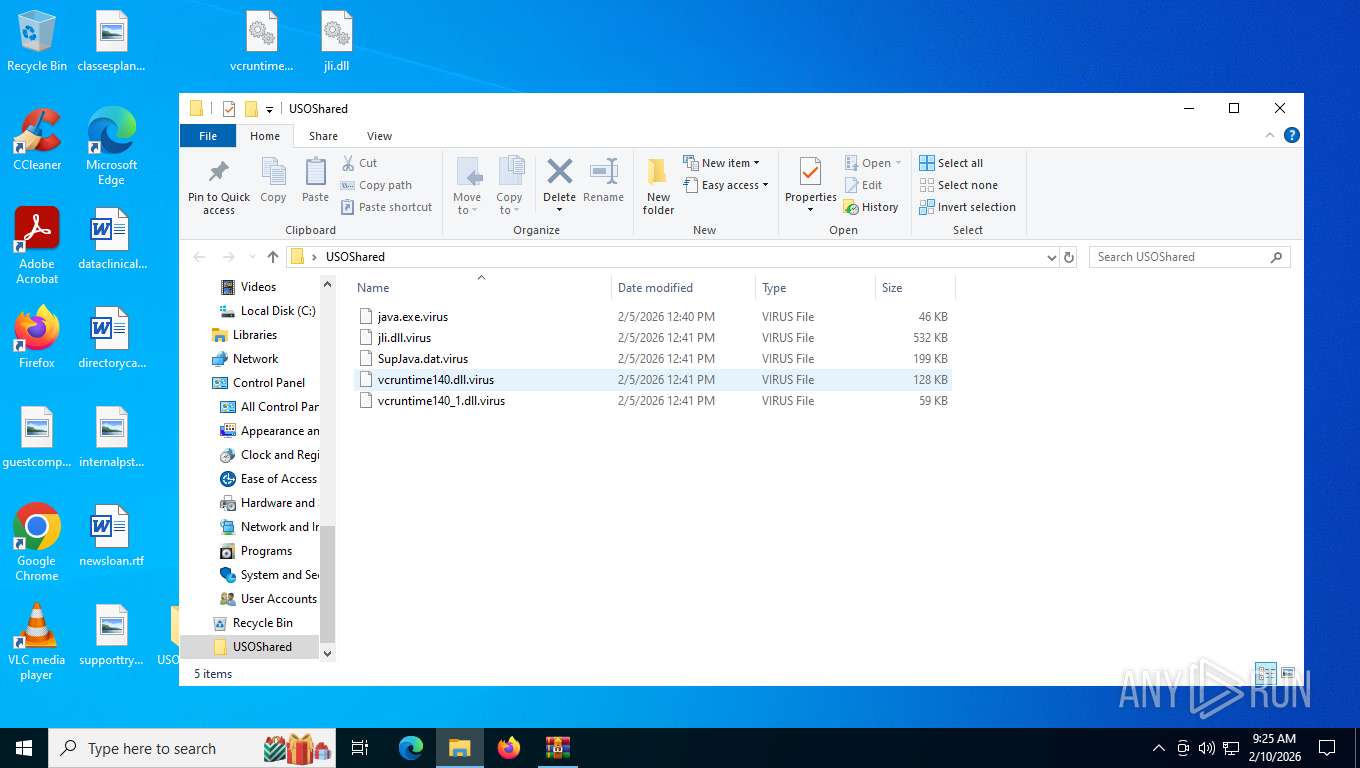
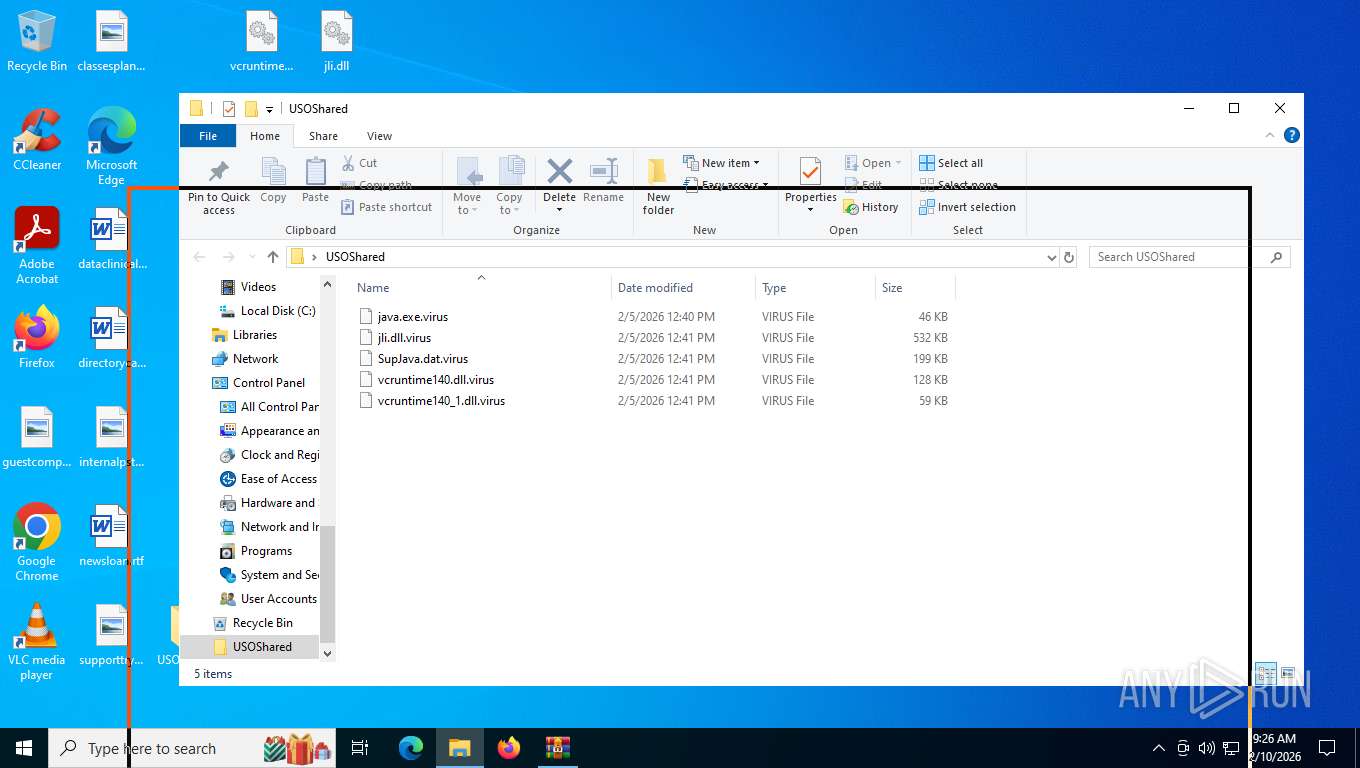
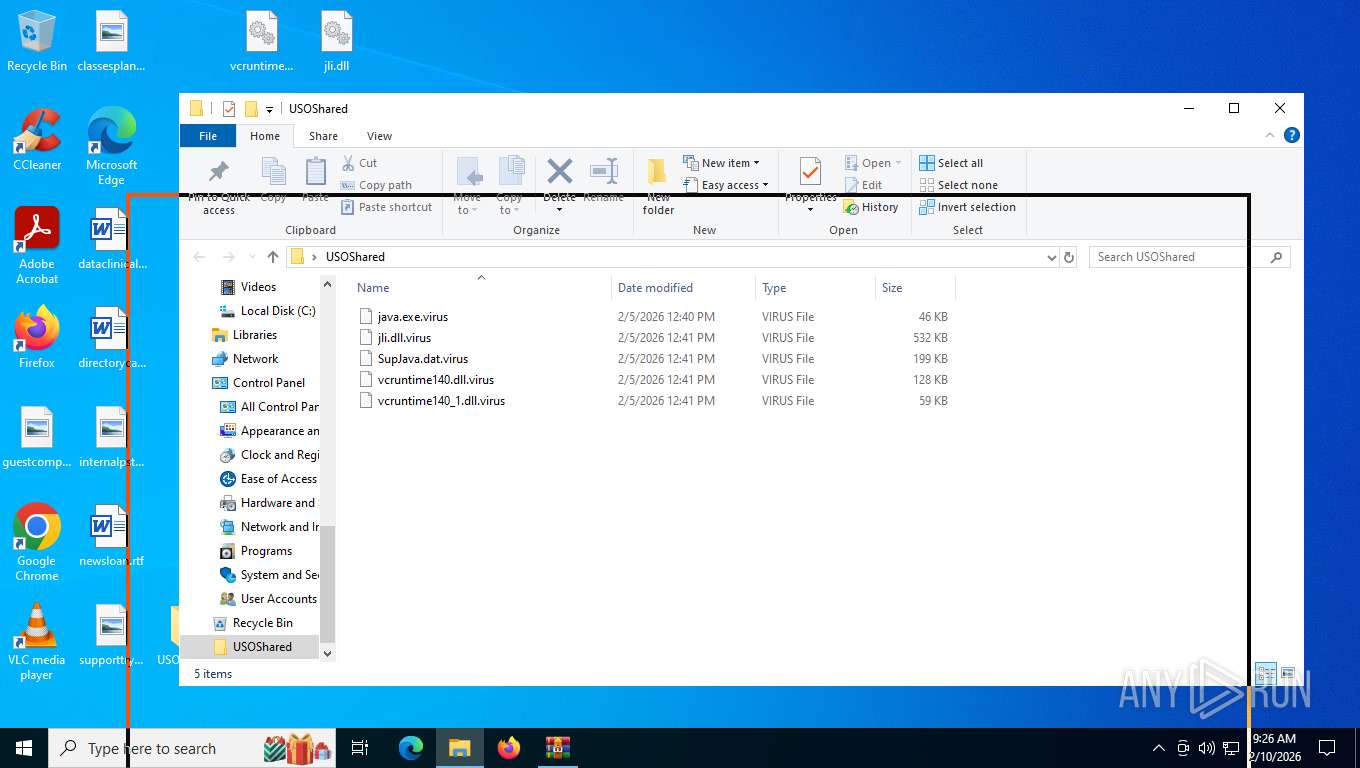
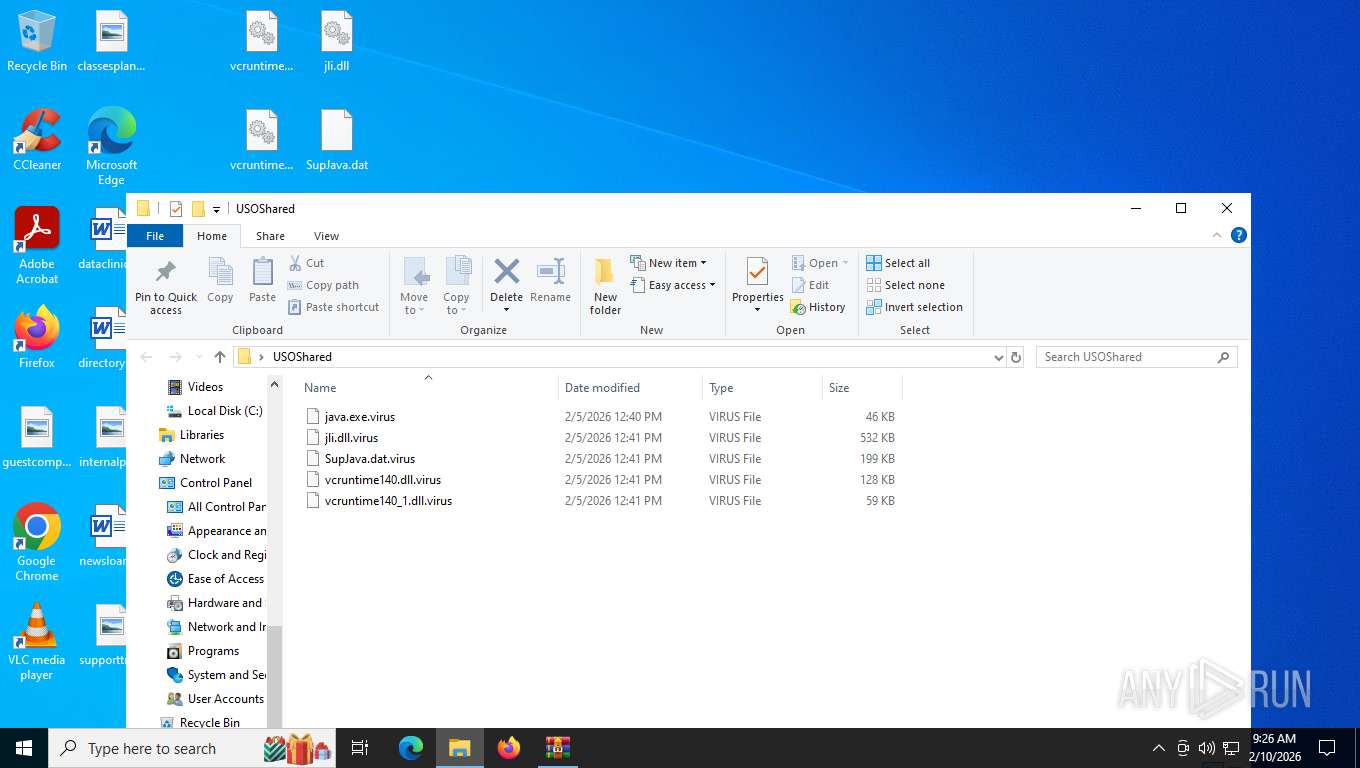
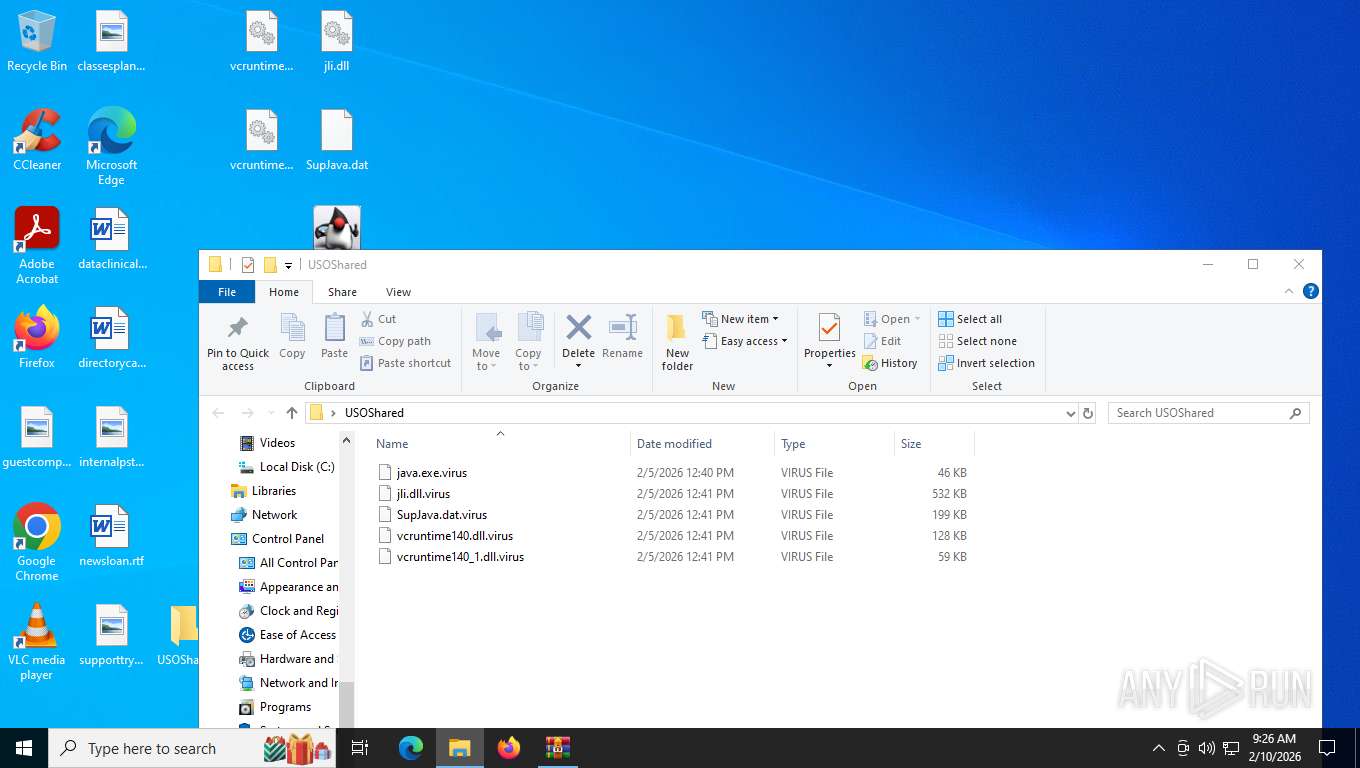
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8820.9912\USOShared\java.exe.virus | executable | |
MD5:2E84936E45F369557E129E396A470461 | SHA256:16B1819186F0803B9408D9A448A176142F8271A4BC0B42CDB78EB4489BCE16FE | |||
| 4140 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_java.exe_334dc5157ca910ab2bbc5d38a6d18ab31d58c3f_04b4b52c_0d5e7a39-f69e-4c7e-a96b-1d0b76590194\Report.wer | — | |
MD5:— | SHA256:— | |||
| 8820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8820.9912\USOShared\vcruntime140_1.dll.virus | executable | |
MD5:0E58231EF5DB2FC7BF9830B41673711D | SHA256:B7C45880C5A4055F425B1104239FDE14E7CBC7B80FE729EAAD454B4C353A164D | |||
| 7544 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_java.exe_334dc5157ca910ab2bbc5d38a6d18ab31d58c3f_04b4b52c_b7411a52-3b5a-4372-80e0-303a09e0400d\Report.wer | — | |
MD5:— | SHA256:— | |||
| 8820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8820.9912\SupJava.dat.virus | binary | |
MD5:8F9055F3E0F749F2EA23283C5C3F33FF | SHA256:E588A4C5E04A6A6CA0E6A48DFB644CC4EB877FCEBA0485E26F673F0E144EAA71 | |||
| 8820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8820.9912\java.exe.virus | executable | |
MD5:2E84936E45F369557E129E396A470461 | SHA256:16B1819186F0803B9408D9A448A176142F8271A4BC0B42CDB78EB4489BCE16FE | |||
| 7544 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERF007.tmp.WERInternalMetadata.xml | xml | |
MD5:4172A7F06D0E5983516215039D727A74 | SHA256:7610036EFF9199A9B373C7D908CAA6807792A2A77A8FFF0A9CA83D42AB29930C | |||
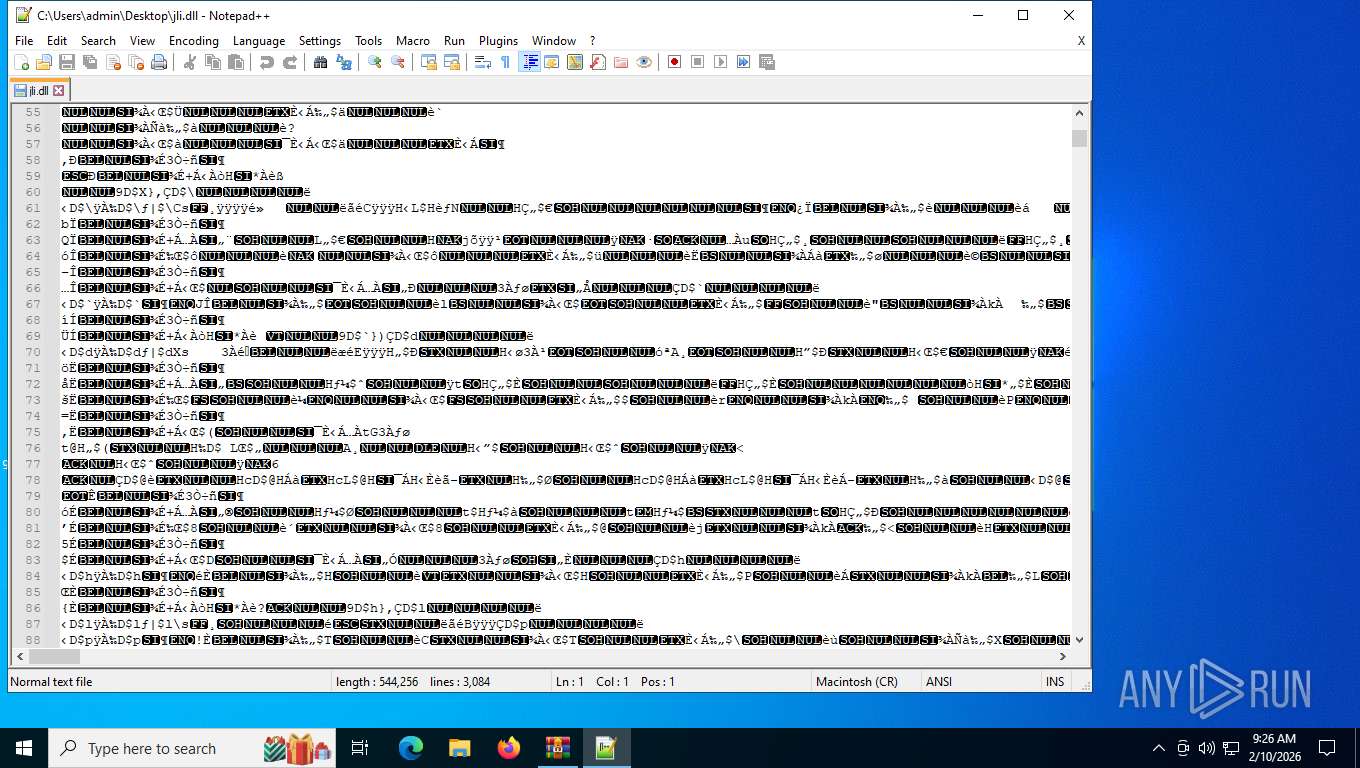
| 8820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb8820.9912\jli.dll.virus | executable | |
MD5:8EE15D2A892A68CE78351750D8173902 | SHA256:AC3465EF2ABC693B0A87BFA051D6C2139860802793AF61208DAE187B219FC0D2 | |||
| 2548 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_java.exe_334dc5157ca910ab2bbc5d38a6d18ab31d58c3f_04b4b52c_b6f3febc-8e4a-407b-a214-f3a91d16ad44\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4140 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:CA37EEB49B5B0D7CC9C87BBD3F941FD8 | SHA256:67FDCD05A6BF96CAE39207D682593F64FA203101833725D7D33FD95760A43938 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
42
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5900 | svchost.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
2428 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
2428 | SIHClient.exe | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
2428 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
2428 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
356 | svchost.exe | GET | 200 | 104.82.114.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5900 | svchost.exe | GET | 200 | 95.101.54.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WaaS/FeatureManagement?IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&CurrentBranch=vb_release&AccountFirstChar=&ActivationChannel=Retail&OEMModel=DELL&FlightRing=Retail&AttrDataVer=186&InstallLanguage=en-US&OSUILocale=en-US&WebExperience=1&FlightingBranchName=&ChassisTypeId=1&OSSkuId=48&App=CDM&InstallDate=1661339444&AppVer=&OSArchitecture=AMD64&DefaultUserRegion=244&TelemetryLevel=1&OSVersion=10.0.19045.4046&DeviceFamily=Windows.Desktop | unknown | text | 25.0 Kb | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/FlightSettings/FSService?ProcessorClockSpeed=3094&IsRetailOS=1&OEMManufacturerName=DELL&FlightingPolicyValue=3&EnablePreviewBuilds=4294967295&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&ManagePreviewBuilds=3&BranchReadinessLevelSource=0&AttrDataVer=186&ProcessorCores=6&BranchReadinessLevelRaw=16&TotalPhysicalRAM=6144&TPMVersion=0&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&DeviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&App=FSS&AppVer=10.0&SmartActiveHoursState=1&ActiveHoursStart=20&SecureBootCapable=0&ActiveHoursEnd=13&DeviceFamily=Windows.Desktop | unknown | text | 87.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5900 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
2036 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5900 | svchost.exe | 95.101.54.122:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 104.82.114.5:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2428 | SIHClient.exe | 135.232.92.137:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5900 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|