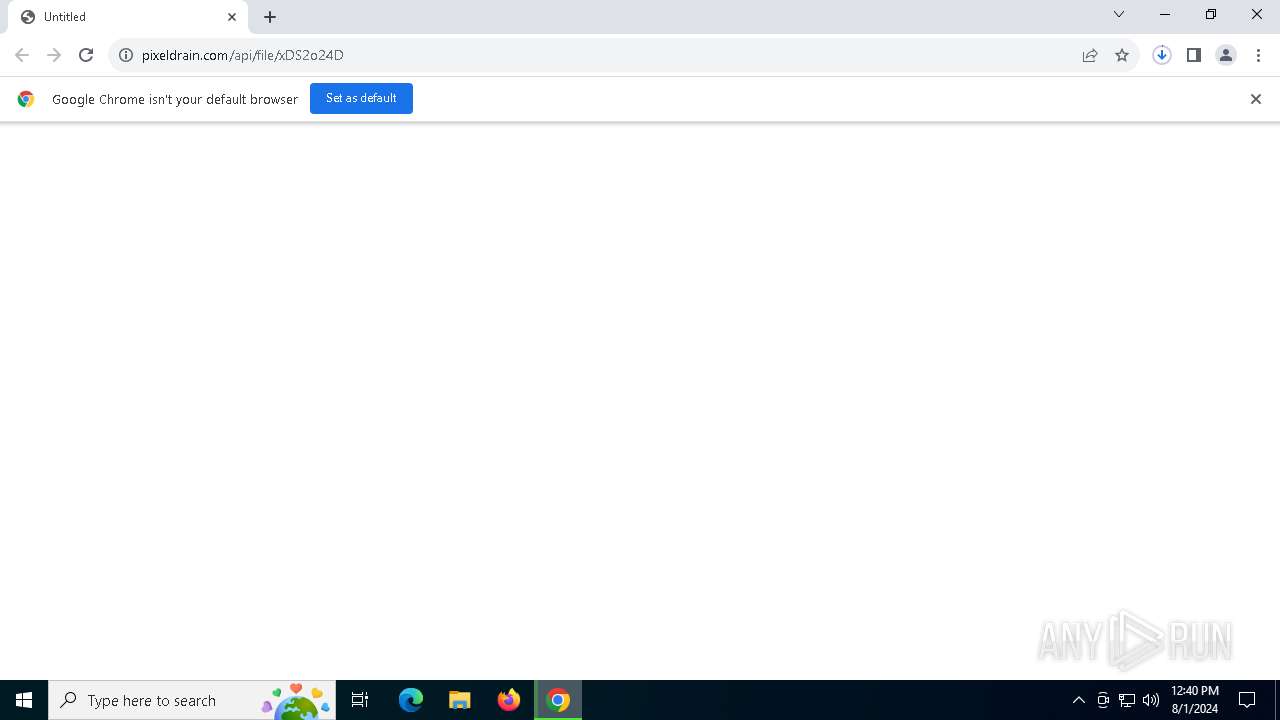
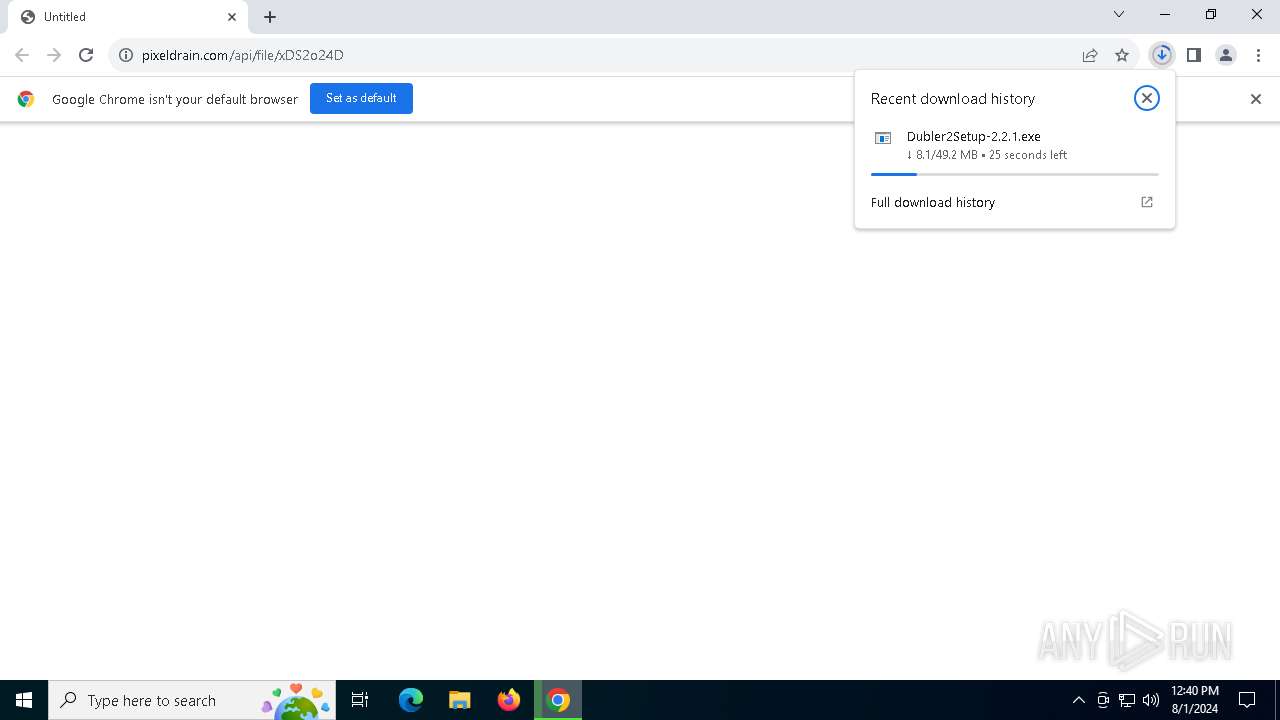
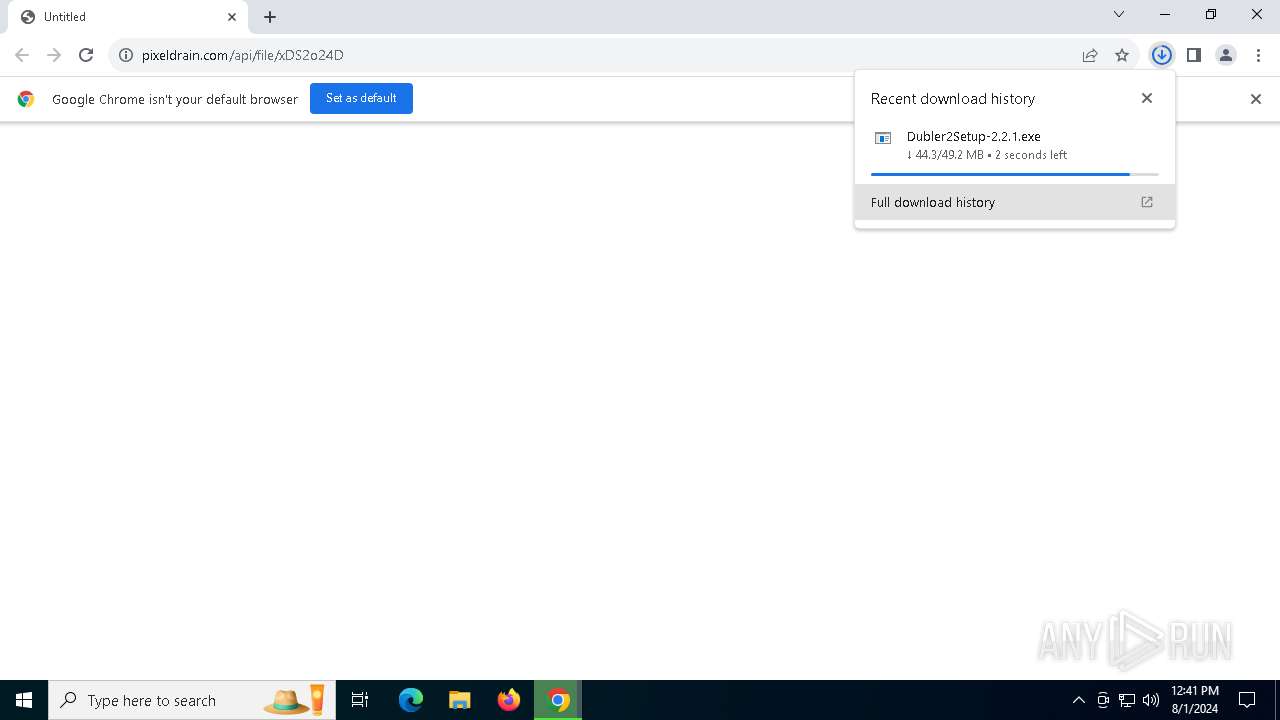
| URL: | https://pixeldrain.com/api/file/xDS2o24D |
| Full analysis: | https://app.any.run/tasks/5fb831fe-3973-4ae0-9fb3-b8a81513dab7 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2024, 12:40:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 154B1D7AFAE038DCD7253D602AC0FD2B |
| SHA1: | A2D5CEA99FA3532B7318DBFCC5C3CBAA65B78CBE |
| SHA256: | E11248279EEE442BBD94724562BD1019FC6C6341EC585936A3EC2EA33E12B238 |
| SSDEEP: | 3:N8Icl/GK09r0n:2IG/d0y |
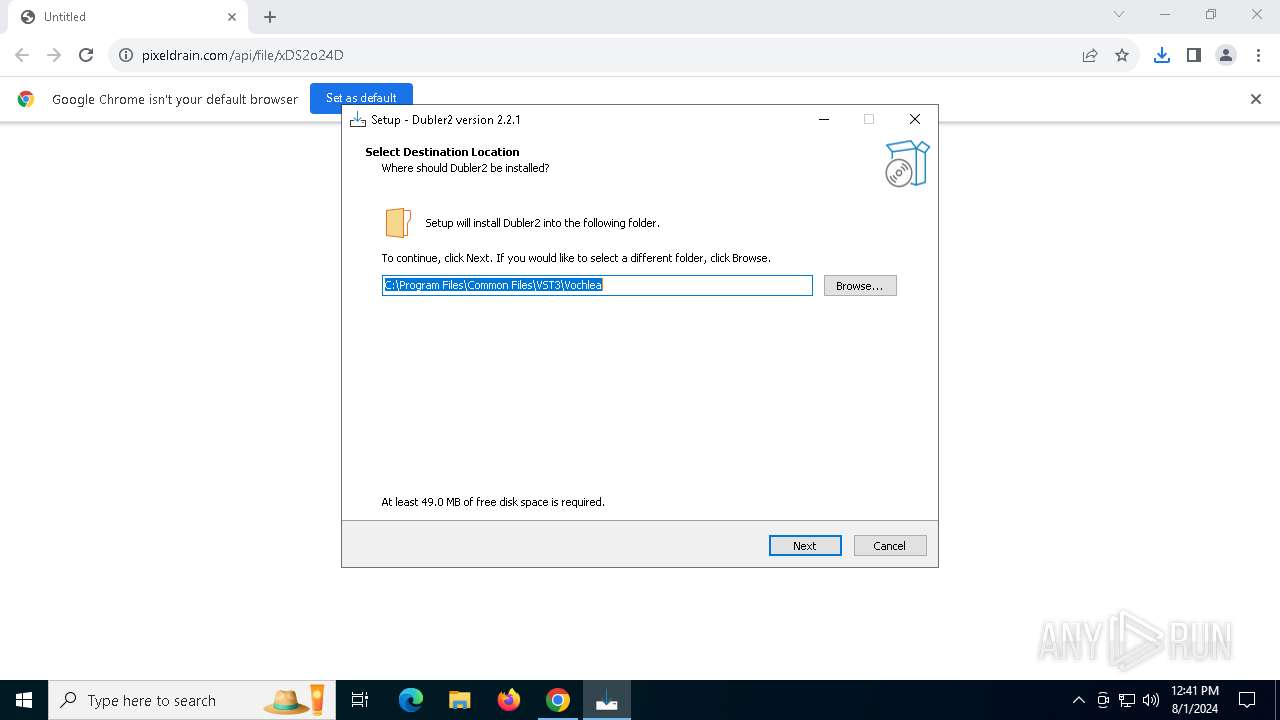
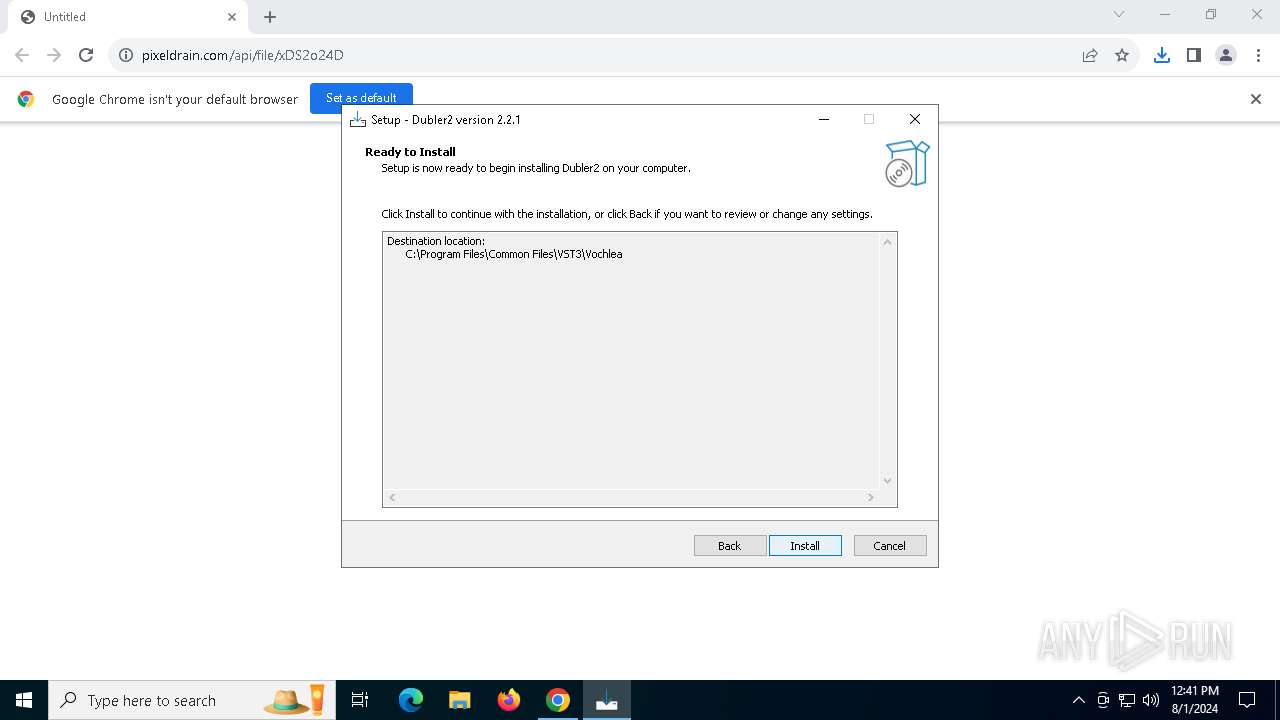
MALICIOUS
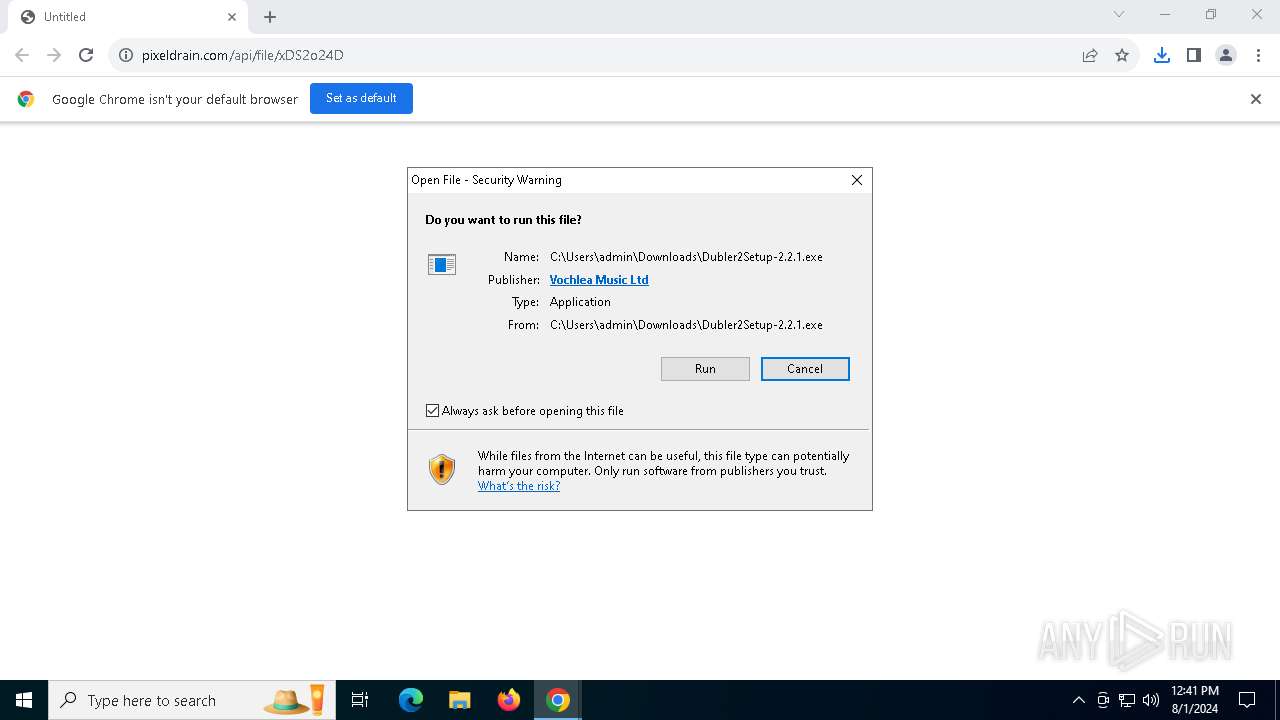
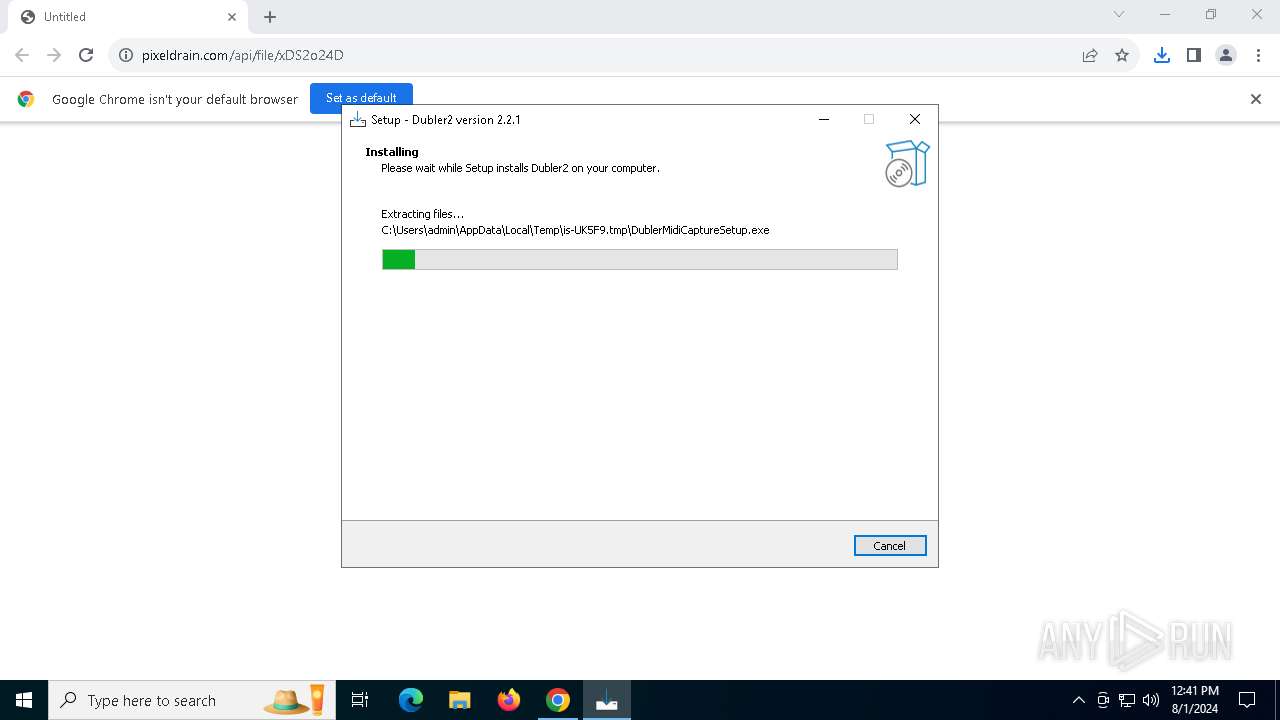
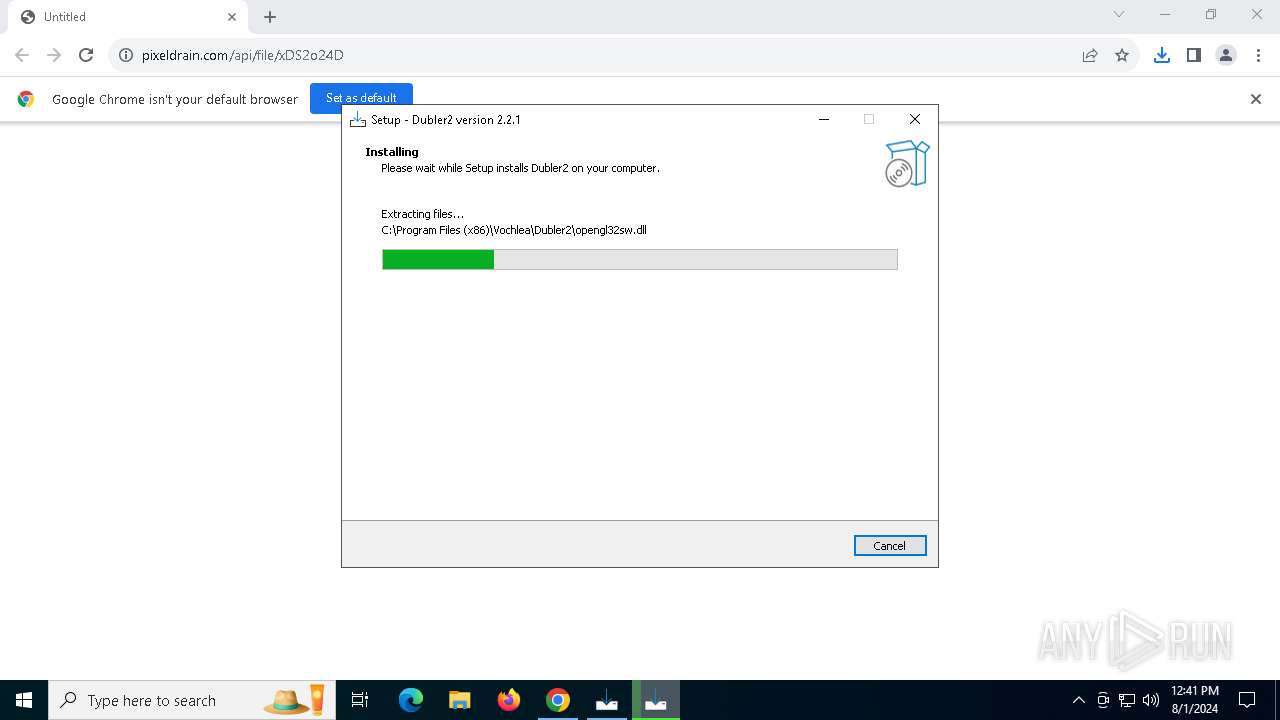
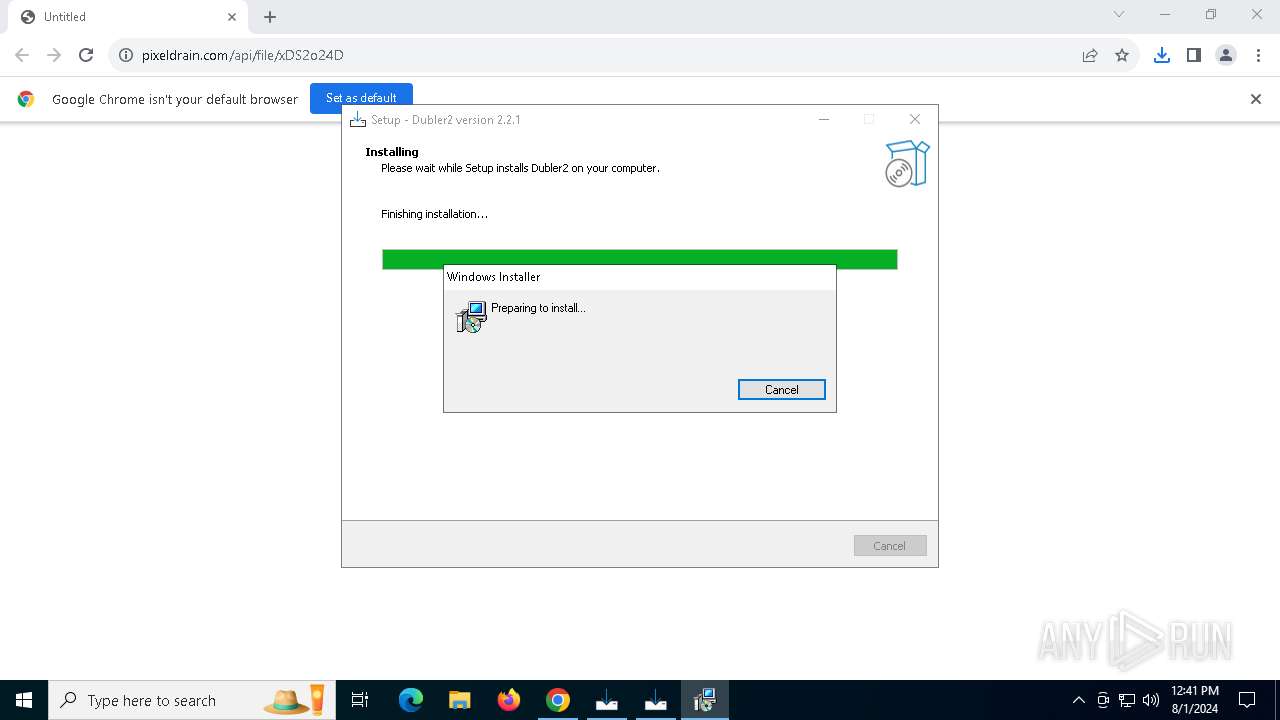
Drops the executable file immediately after the start
- Dubler2Setup-2.2.1.exe (PID: 7656)
- Dubler2Setup-2.2.1.exe (PID: 7880)
- Dubler2Setup-2.2.1.tmp (PID: 7904)
- Dubler2Setup.exe (PID: 7944)
- Dubler2Setup.tmp (PID: 7964)
- msiexec.exe (PID: 2680)
- drvinst.exe (PID: 3520)
- drvinst.exe (PID: 2092)
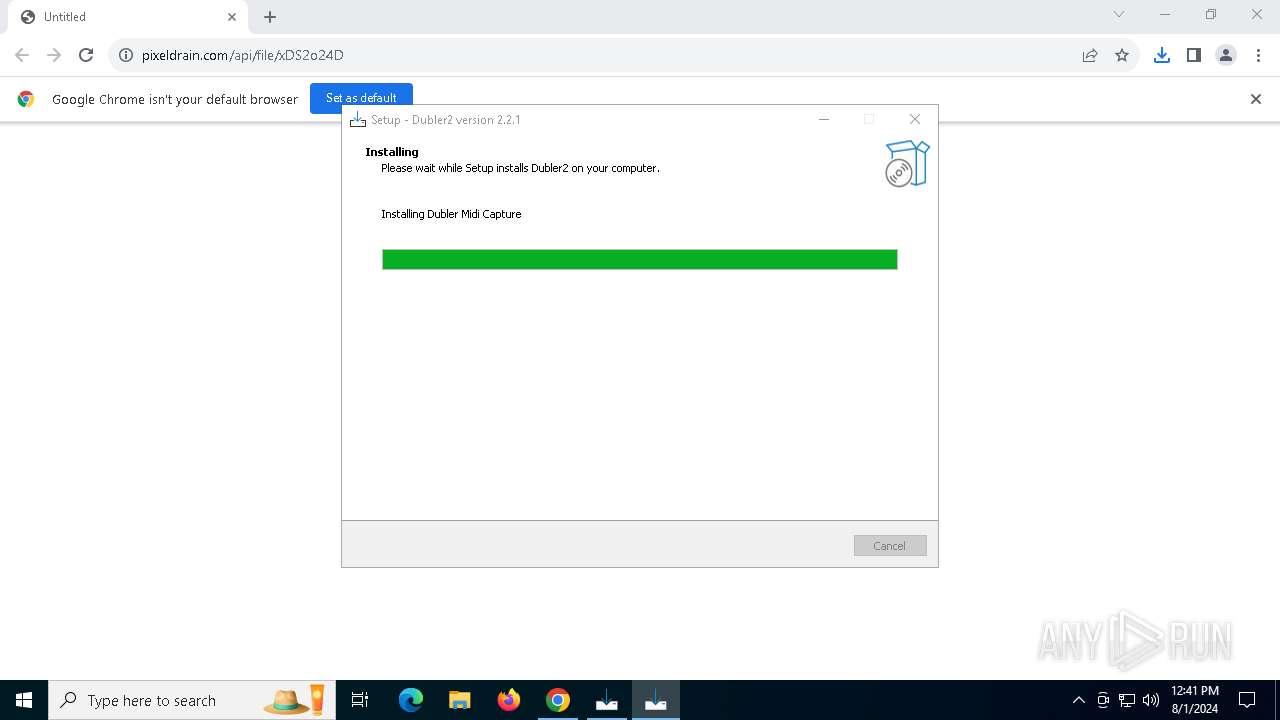
- DublerMidiCaptureSetup.exe (PID: 8032)
- DublerMidiCaptureSetup.tmp (PID: 8044)
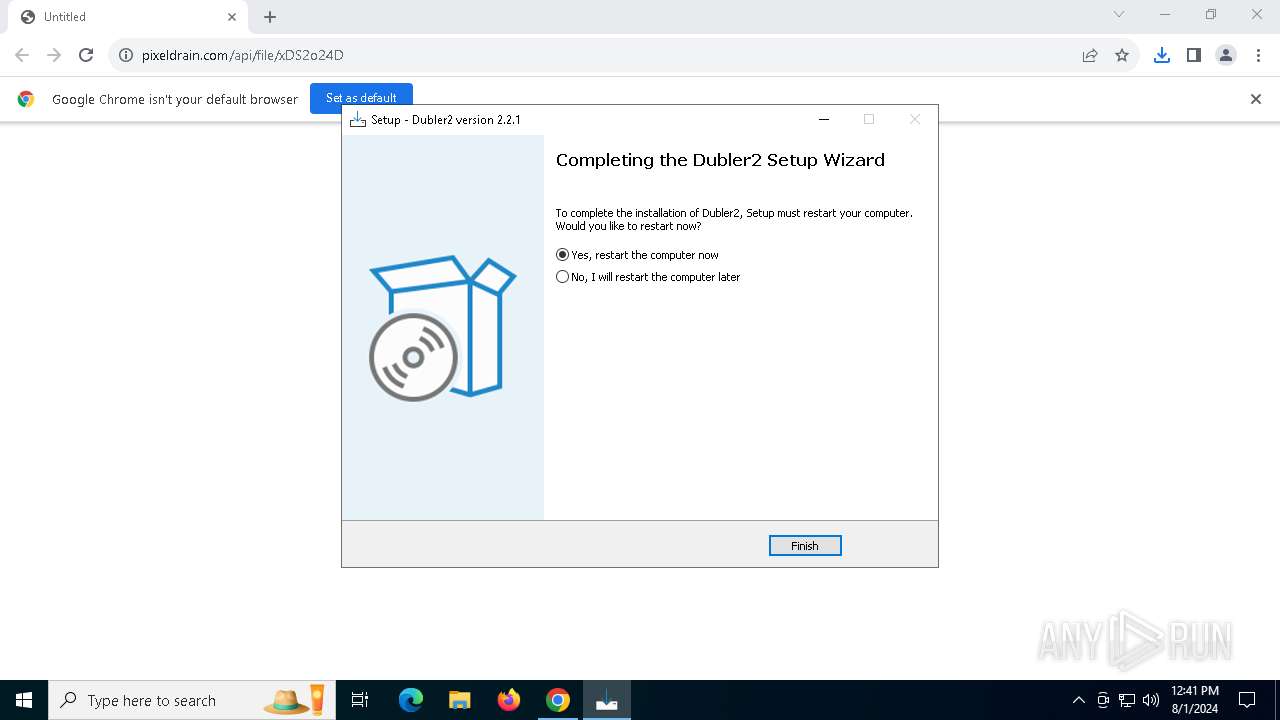
Changes the autorun value in the registry
- Dubler2Setup.tmp (PID: 7964)
SUSPICIOUS
Executable content was dropped or overwritten
- Dubler2Setup-2.2.1.exe (PID: 7656)
- Dubler2Setup-2.2.1.exe (PID: 7880)
- Dubler2Setup-2.2.1.tmp (PID: 7904)
- Dubler2Setup.exe (PID: 7944)
- Dubler2Setup.tmp (PID: 7964)
- drvinst.exe (PID: 3520)
- DublerMidiCaptureSetup.exe (PID: 8032)
- DublerMidiCaptureSetup.tmp (PID: 8044)
- drvinst.exe (PID: 2092)
Reads security settings of Internet Explorer
- Dubler2Setup-2.2.1.tmp (PID: 7680)
Reads the date of Windows installation
- Dubler2Setup-2.2.1.tmp (PID: 7680)
Reads the Windows owner or organization settings
- Dubler2Setup-2.2.1.tmp (PID: 7904)
- Dubler2Setup.tmp (PID: 7964)
- msiexec.exe (PID: 2680)
- DublerMidiCaptureSetup.tmp (PID: 8044)
Process drops legitimate windows executable
- Dubler2Setup.tmp (PID: 7964)
Executes as Windows Service
- VSSVC.exe (PID: 3164)
Checks Windows Trust Settings
- msiexec.exe (PID: 2680)
- msiexec.exe (PID: 2336)
- drvinst.exe (PID: 3520)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 2680)
- drvinst.exe (PID: 3520)
- drvinst.exe (PID: 2092)
Adds/modifies Windows certificates
- msiexec.exe (PID: 7632)
- msiexec.exe (PID: 2336)
Creates files in the driver directory
- drvinst.exe (PID: 3520)
- msiexec.exe (PID: 2336)
- drvinst.exe (PID: 2092)
Creates or modifies Windows services
- drvinst.exe (PID: 2092)
INFO
Application launched itself
- chrome.exe (PID: 6456)
- msiexec.exe (PID: 2680)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6456)
Executable content was dropped or overwritten
- chrome.exe (PID: 6456)
- msiexec.exe (PID: 2680)
The process uses the downloaded file
- chrome.exe (PID: 7564)
- chrome.exe (PID: 6456)
Drops the executable file immediately after the start
- chrome.exe (PID: 6456)
Checks supported languages
- Dubler2Setup-2.2.1.exe (PID: 7656)
- Dubler2Setup-2.2.1.tmp (PID: 7680)
- Dubler2Setup-2.2.1.exe (PID: 7880)
- Dubler2Setup-2.2.1.tmp (PID: 7904)
- Dubler2Setup.exe (PID: 7944)
- Dubler2Setup.tmp (PID: 7964)
- msiexec.exe (PID: 2680)
- msiexec.exe (PID: 7588)
- msiexec.exe (PID: 7632)
- msiexec.exe (PID: 2336)
- drvinst.exe (PID: 3520)
- drvinst.exe (PID: 2092)
- DublerMidiCaptureSetup.exe (PID: 8032)
- DublerMidiCaptureSetup.tmp (PID: 8044)
Create files in a temporary directory
- Dubler2Setup-2.2.1.exe (PID: 7656)
- Dubler2Setup-2.2.1.exe (PID: 7880)
- Dubler2Setup-2.2.1.tmp (PID: 7904)
- Dubler2Setup.tmp (PID: 7964)
- Dubler2Setup.exe (PID: 7944)
- DublerMidiCaptureSetup.exe (PID: 8032)
- DublerMidiCaptureSetup.tmp (PID: 8044)
Reads the computer name
- Dubler2Setup-2.2.1.tmp (PID: 7680)
- Dubler2Setup.tmp (PID: 7964)
- Dubler2Setup-2.2.1.tmp (PID: 7904)
- msiexec.exe (PID: 2680)
- msiexec.exe (PID: 7588)
- msiexec.exe (PID: 7632)
- msiexec.exe (PID: 2336)
- drvinst.exe (PID: 3520)
- drvinst.exe (PID: 2092)
- DublerMidiCaptureSetup.tmp (PID: 8044)
Process checks computer location settings
- Dubler2Setup-2.2.1.tmp (PID: 7680)
Creates files in the program directory
- Dubler2Setup-2.2.1.tmp (PID: 7904)
- Dubler2Setup.tmp (PID: 7964)
- DublerMidiCaptureSetup.tmp (PID: 8044)
Creates a software uninstall entry
- Dubler2Setup.tmp (PID: 7964)
- msiexec.exe (PID: 2680)
- DublerMidiCaptureSetup.tmp (PID: 8044)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 8164)
Checks proxy server information
- msiexec.exe (PID: 8164)
Creates files or folders in the user directory
- msiexec.exe (PID: 8164)
Reads the software policy settings
- msiexec.exe (PID: 2680)
- msiexec.exe (PID: 8164)
- drvinst.exe (PID: 3520)
- msiexec.exe (PID: 2336)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2680)
- msiexec.exe (PID: 2336)
- drvinst.exe (PID: 3520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
175
Monitored processes
30
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4128 --field-trial-handle=1820,i,3539426638778261934,17900108816965567427,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2092 | DrvInst.exe "2" "11" "ROOT\MEDIA\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:ed86ca11475f2e68:teVMIDI:1.2.12.42:tevirtualmidi," "4da725177" "00000000000001D4" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2204 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2336 | C:\Windows\System32\MsiExec.exe -Embedding F4FB2B17563905304ED0C99E9DCFE791 E Global\MSI0000 | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2680 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3164 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3520 | DrvInst.exe "4" "1" "c:\program files\tobias erichsen\tevirtualmidi\tevirtualmidi.inf" "9" "4da725177" "0000000000000170" "WinSta0\Default" "00000000000001DC" "208" "c:\program files\tobias erichsen\tevirtualmidi" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4604 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4960 --field-trial-handle=1820,i,3539426638778261934,17900108816965567427,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4648 --field-trial-handle=1820,i,3539426638778261934,17900108816965567427,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
33 005
Read events
31 973
Write events
981
Delete events
51
Modification events
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6456) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
61
Suspicious files
101
Text files
29
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe609a.TMP | — | |
MD5:— | SHA256:— | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe60c9.TMP | — | |
MD5:— | SHA256:— | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:723783C35EAEEE1492EDB30847AE6750 | SHA256:C29323F784CF873BF34992E7A2B4630B19641BF42980109E31D5AF2D487DF6F8 | |||
| 6456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe608a.TMP | text | |
MD5:8F45965291AB2DA10EEB049FB6E917C6 | SHA256:8A0DE526945B27CDBBD87357C85FDDD37B572370F894CB0A5AC533FD465D2166 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
71
DNS requests
40
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8164 | msiexec.exe | GET | 200 | 151.101.66.133:80 | http://crl.globalsign.net/root.crl | unknown | — | — | whitelisted |
7700 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nhetl6idyntppkmxh3rl5szhre_8989/hfnkpimlhhgieaddgfemjhofmfblmnib_8989_all_adog2s4slg6a7uvhvkqq5ho6fpma.crx3 | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nhetl6idyntppkmxh3rl5szhre_8989/hfnkpimlhhgieaddgfemjhofmfblmnib_8989_all_adog2s4slg6a7uvhvkqq5ho6fpma.crx3 | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nhetl6idyntppkmxh3rl5szhre_8989/hfnkpimlhhgieaddgfemjhofmfblmnib_8989_all_adog2s4slg6a7uvhvkqq5ho6fpma.crx3 | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nhetl6idyntppkmxh3rl5szhre_8989/hfnkpimlhhgieaddgfemjhofmfblmnib_8989_all_adog2s4slg6a7uvhvkqq5ho6fpma.crx3 | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nhetl6idyntppkmxh3rl5szhre_8989/hfnkpimlhhgieaddgfemjhofmfblmnib_8989_all_adog2s4slg6a7uvhvkqq5ho6fpma.crx3 | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nhetl6idyntppkmxh3rl5szhre_8989/hfnkpimlhhgieaddgfemjhofmfblmnib_8989_all_adog2s4slg6a7uvhvkqq5ho6fpma.crx3 | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nhetl6idyntppkmxh3rl5szhre_8989/hfnkpimlhhgieaddgfemjhofmfblmnib_8989_all_adog2s4slg6a7uvhvkqq5ho6fpma.crx3 | unknown | — | — | whitelisted |
7700 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2804 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2272 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6456 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6724 | chrome.exe | 50.7.22.10:443 | pixeldrain.com | COGENT-174 | NL | unknown |
6724 | chrome.exe | 173.194.69.84:443 | accounts.google.com | GOOGLE | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2804 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
pixeldrain.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6724 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
6724 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
6724 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
Process | Message |
|---|---|
msiexec.exe | teDevInstCA: DLL_PROCESS_ATTACH |
msiexec.exe | teDevInstCA: DLL_PROCESS_DETACH |