| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/86449d0f-8a1a-43e9-b3ec-b963200073a3 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 18:10:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 12DDA5EB62F51E7EC006B7D115A9CCCB |
| SHA1: | 5D6BB5914C2965035FABBF18F813D5B129B81F7A |
| SHA256: | E104898560558E7442FB21E8C19B1B8720FAB3202D820A57C99BE88021005D50 |
| SSDEEP: | 98304:mgT81bkzA6yF6K/axXA+VdwVHBSK6FCExd+iXKcigylBSxrKunjSWw:Yk8FtaxXA+VdwZyCAKgkBAKPWw |
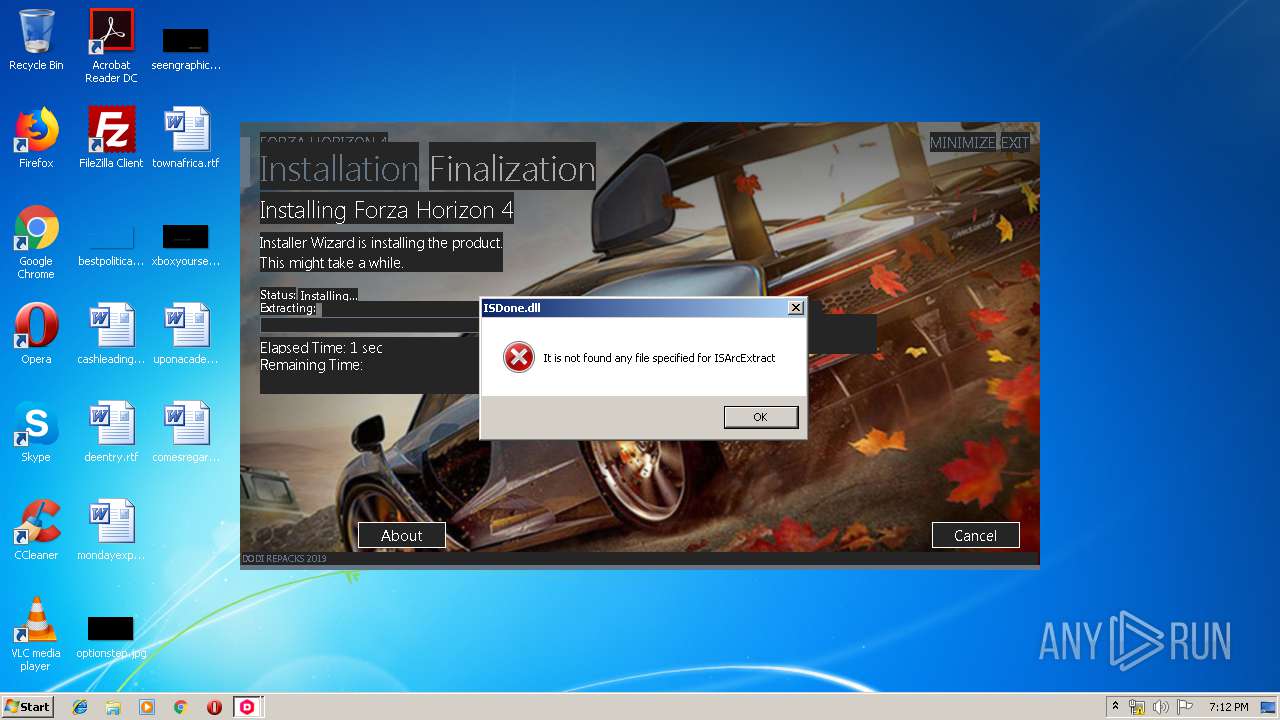
MALICIOUS
Application was dropped or rewritten from another process
- unins000.exe (PID: 2388)
- _iu14D2N.tmp (PID: 3008)
Loads dropped or rewritten executable
- _iu14D2N.tmp (PID: 3008)
SUSPICIOUS
Reads Windows owner or organization settings
- Setup.tmp (PID: 3264)
- _iu14D2N.tmp (PID: 3008)
Executable content was dropped or overwritten
- Setup.exe (PID: 2788)
- Setup.tmp (PID: 3264)
- _iu14D2N.tmp (PID: 3008)
- unins000.exe (PID: 2388)
Reads the Windows organization settings
- Setup.tmp (PID: 3264)
- _iu14D2N.tmp (PID: 3008)
Starts application with an unusual extension
- unins000.exe (PID: 2388)
Starts itself from another location
- unins000.exe (PID: 2388)
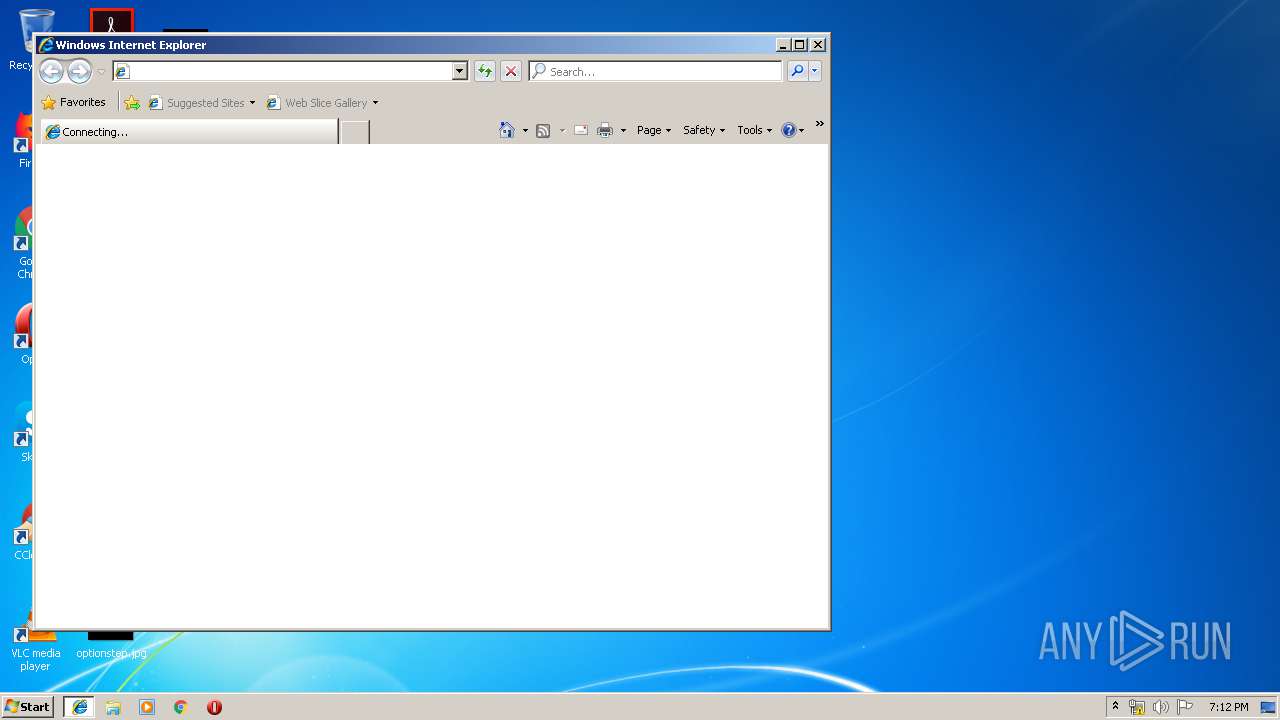
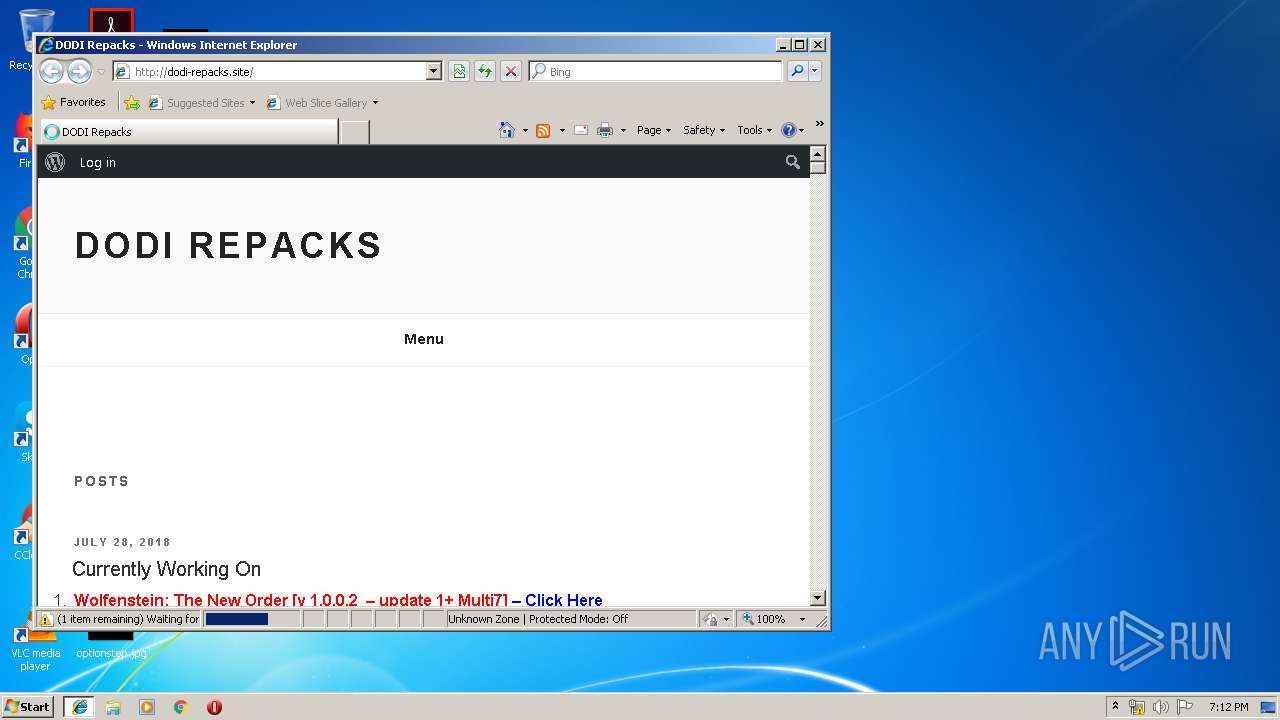
Starts Internet Explorer
- Setup.tmp (PID: 3264)
INFO
Application was dropped or rewritten from another process
- Setup.tmp (PID: 3264)
Creates files in the program directory
- Setup.tmp (PID: 3264)
Loads dropped or rewritten executable
- Setup.tmp (PID: 3264)
Creates a software uninstall entry
- Setup.tmp (PID: 3264)
Application launched itself
- iexplore.exe (PID: 2440)
Changes internet zones settings
- iexplore.exe (PID: 2440)
Reads Internet Cache Settings
- iexplore.exe (PID: 2864)
Reads internet explorer settings
- iexplore.exe (PID: 2864)
Creates files in the user directory
- iexplore.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 07:04:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 140800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
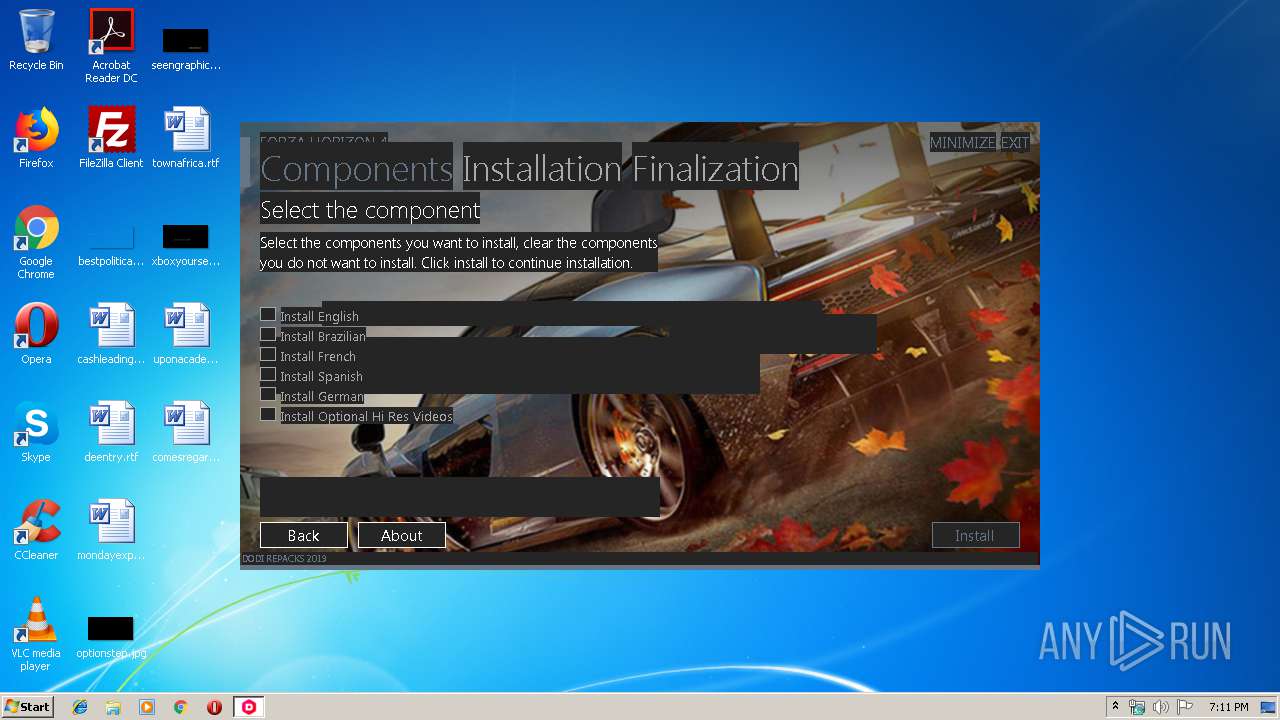
| CompanyName: | DODI-Repacks |
| FileDescription: | Forza Horizon 4 Setup |
| FileVersion: | 0.0.0 |
| LegalCopyright: | DODI-Repacks |
| ProductName: | Forza Horizon 4 |
| ProductVersion: | 0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2012 05:04:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | DODI-Repacks |
| FileDescription: | Forza Horizon 4 Setup |
| FileVersion: | 0.0.0 |
| LegalCopyright: | DODI-Repacks |
| ProductName: | Forza Horizon 4 |
| ProductVersion: | 0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 02-Oct-2012 05:04:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000143F8 | 0x00014400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4822 |
.itext | 0x00016000 | 0x00000BE8 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.01516 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.66929 |
.bss | 0x00018000 | 0x00005750 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.rsrc | 0x00021000 | 0x00020544 | 0x00020600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.05046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06505 | 1376 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.41985 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.41604 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.80966 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.27161 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.94551 | 39679 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.14112 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.281 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.42988 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.70493 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
43
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
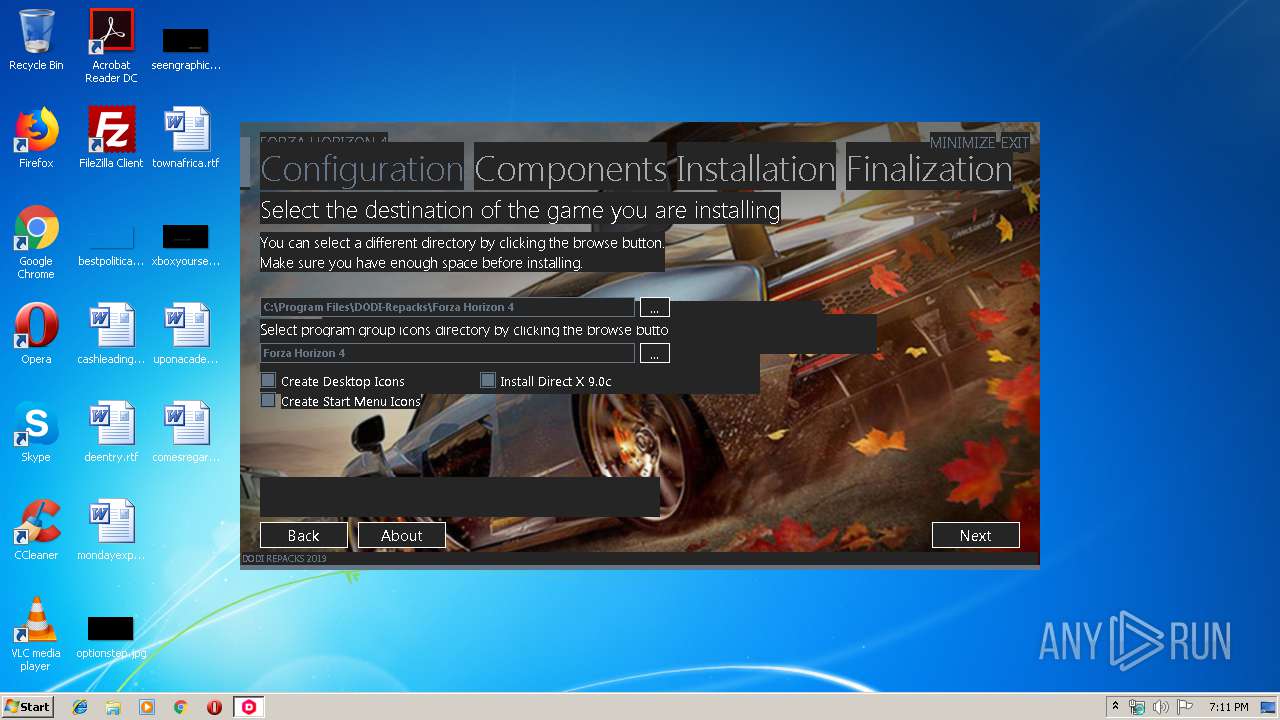
| 2388 | "C:\Program Files\DODI-Repacks\Forza Horizon 4\Uninstall\unins000.exe" /verysilent | C:\Program Files\DODI-Repacks\Forza Horizon 4\Uninstall\unins000.exe | Setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Setup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
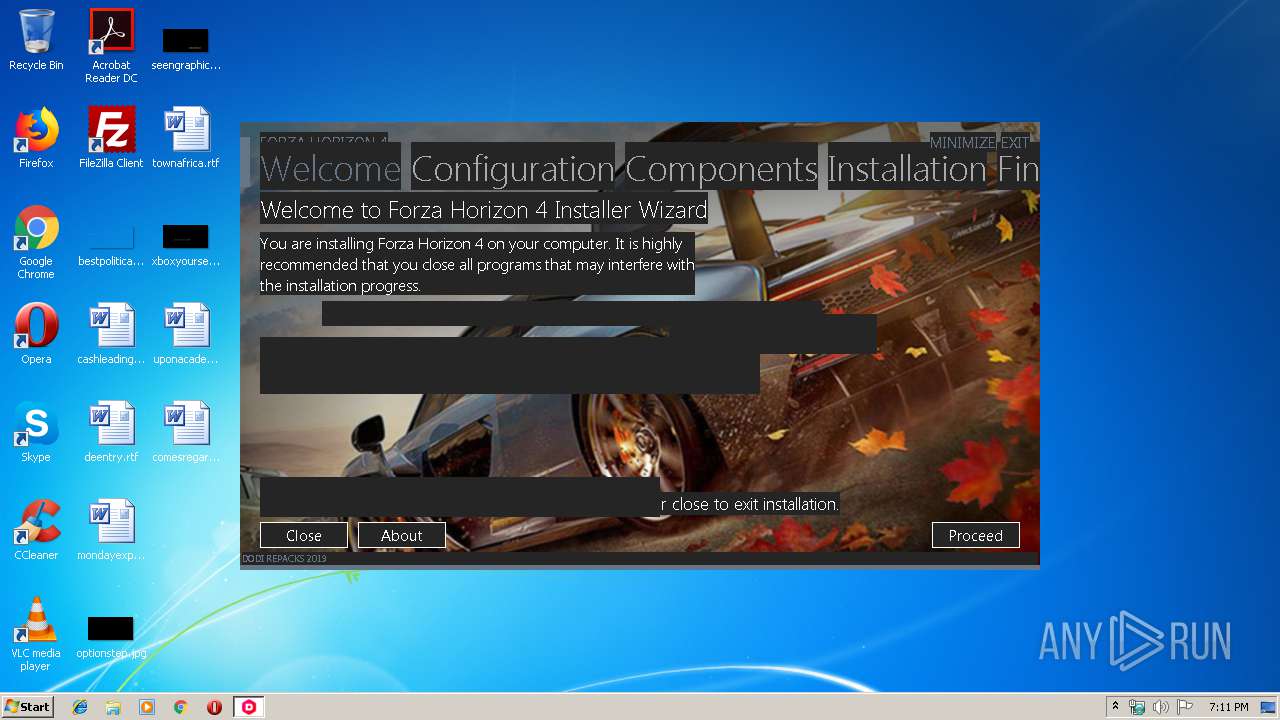
| 2788 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: DODI-Repacks Integrity Level: HIGH Description: Forza Horizon 4 Setup Exit code: 0 Version: 0.0.0 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2440 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Program Files\DODI-Repacks\Forza Horizon 4\Uninstall\unins000.exe" /FIRSTPHASEWND=$20218 /verysilent | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3264 | "C:\Users\admin\AppData\Local\Temp\is-7HANH.tmp\Setup.tmp" /SL5="$30134,5911190,227840,C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\is-7HANH.tmp\Setup.tmp | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: DODI-Repacks Integrity Level: MEDIUM Description: Forza Horizon 4 Setup Exit code: 3221226540 Version: 0.0.0 Modules
| |||||||||||||||
Total events
431
Read events
330
Write events
95
Delete events
6
Modification events
| (PID) Process: | (3264) Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: C00C0000E6F68E7D705BD501 | |||
| (PID) Process: | (3264) Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 4F2F0E4803470996B971BCF7D7F958D5B5F0A0B8184E359349649D163C96AC66 | |||
| (PID) Process: | (3264) Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3008) _iu14D2N.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Forza Horizon 4_is1 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2388) unins000.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | |||
| (PID) Process: | (3264) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Forza Horizon 4_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1.ee2 (u) | |||
| (PID) Process: | (3264) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Forza Horizon 4_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\DODI-Repacks\Forza Horizon 4 | |||
| (PID) Process: | (3264) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Forza Horizon 4_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\DODI-Repacks\Forza Horizon 4\ | |||
| (PID) Process: | (3264) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Forza Horizon 4_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Forza Horizon 4 | |||
| (PID) Process: | (3264) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Forza Horizon 4_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
29
Suspicious files
0
Text files
66
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\logo.png | image | |
MD5:— | SHA256:— | |||
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\Lockscreen.jpg | image | |
MD5:— | SHA256:— | |||
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\Autorun1.jpg | image | |
MD5:— | SHA256:— | |||
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\Setup1.jpg | image | |
MD5:— | SHA256:— | |||
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\botva2.dll | executable | |
MD5:619BF9DDCB5FE39EE9E5B0167E7F4F0D | SHA256:609661A14733F6E9C2C2F2FF9C274F8A4CBEDAFF4DD32049AA5161F8D7083D6A | |||
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\Tile1_Background.jpg | image | |
MD5:— | SHA256:— | |||
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\Exit.png | image | |
MD5:91F97AA4B051E7B2991E5456D2C8655B | SHA256:0FF3FBFBB177D5FFC8B577F821A91F9D39F13F5F548F9570C12CB85CCEF526E3 | |||
| 3264 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-EJ3RC.tmp\english.ini | text | |
MD5:0C5C10616319C1B339255391B4E59A4F | SHA256:18D197E13C0EDEEDAE84D09F3AA64A308CC74C41F8F8D4299548D8D37D811099 | |||
| 2788 | Setup.exe | C:\Users\admin\AppData\Local\Temp\is-7HANH.tmp\Setup.tmp | executable | |
MD5:6E4E83302159EC46E10280ABE1D62CE1 | SHA256:BB22238B9DE45D10013CDF18B66D13646137BF5DDC075C781A160EF8739B2FD7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
20
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-content/plugins/buddypress/bp-templates/bp-nouveau/css/buddypress.min.css?ver=3.1.0 | US | text | 14.5 Kb | malicious |
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-includes/css/admin-bar.min.css?ver=5.0.4 | US | text | 3.84 Kb | malicious |
2864 | iexplore.exe | GET | 200 | 216.58.210.2:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 34.0 Kb | whitelisted |
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-includes/css/dashicons.min.css?ver=5.0.4 | US | text | 27.9 Kb | malicious |
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-content/plugins/buddypress/bp-core/css/admin-bar.min.css?ver=3.1.0 | US | text | 450 b | malicious |
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-content/plugins/buddypress/bp-core/js/jquery-query.min.js?ver=3.1.0 | US | text | 119 b | malicious |
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-includes/js/jquery/jquery.js?ver=1.12.4 | US | text | 33.0 Kb | malicious |
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-content/plugins/jetpack/css/jetpack.css?ver=6.3.3 | US | text | 11.7 Kb | malicious |
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-content/themes/twentyseventeen/assets/css/ie8.css?ver=1.0 | US | text | 1.17 Kb | malicious |
2864 | iexplore.exe | GET | 200 | 107.189.5.177:80 | http://dodi-repacks.site/wp-content/plugins/jetpack/modules/widgets/social-icons/social-icons.css?ver=20170506 | US | text | 563 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 107.189.5.177:80 | www.dodi-repacks.site | FranTech Solutions | US | suspicious |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2864 | iexplore.exe | 107.189.5.177:80 | www.dodi-repacks.site | FranTech Solutions | US | suspicious |
2864 | iexplore.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2864 | iexplore.exe | 216.58.210.2:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 192.0.78.17:443 | wordpress.com | Automattic, Inc | US | unknown |
— | — | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
— | — | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
— | — | 192.0.73.2:443 | secure.gravatar.com | Automattic, Inc | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dodi-repacks.site |
| malicious |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
wordpress.com |
| whitelisted |
s0.wp.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |
stats.wp.com |
| whitelisted |
2.gravatar.com |
| whitelisted |