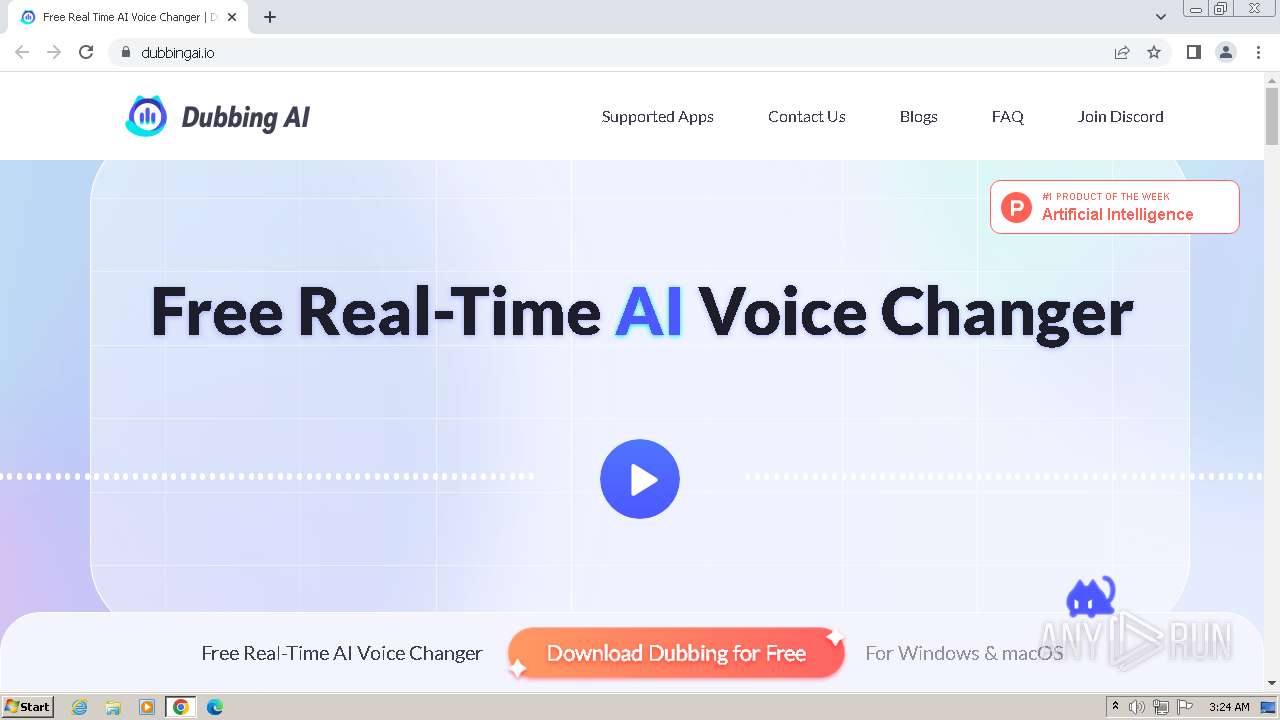
| URL: | https://dubbingai.io |
| Full analysis: | https://app.any.run/tasks/6c4460a0-5be2-4a57-953e-75ae41318dbf |
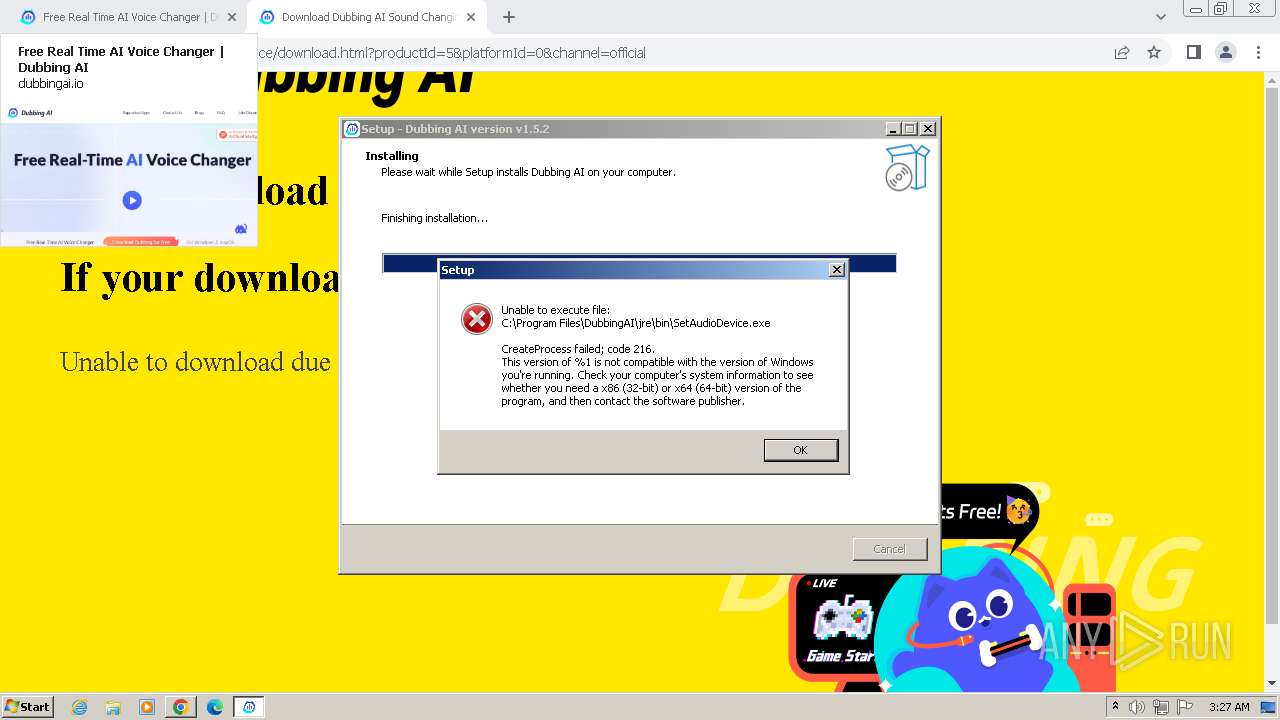
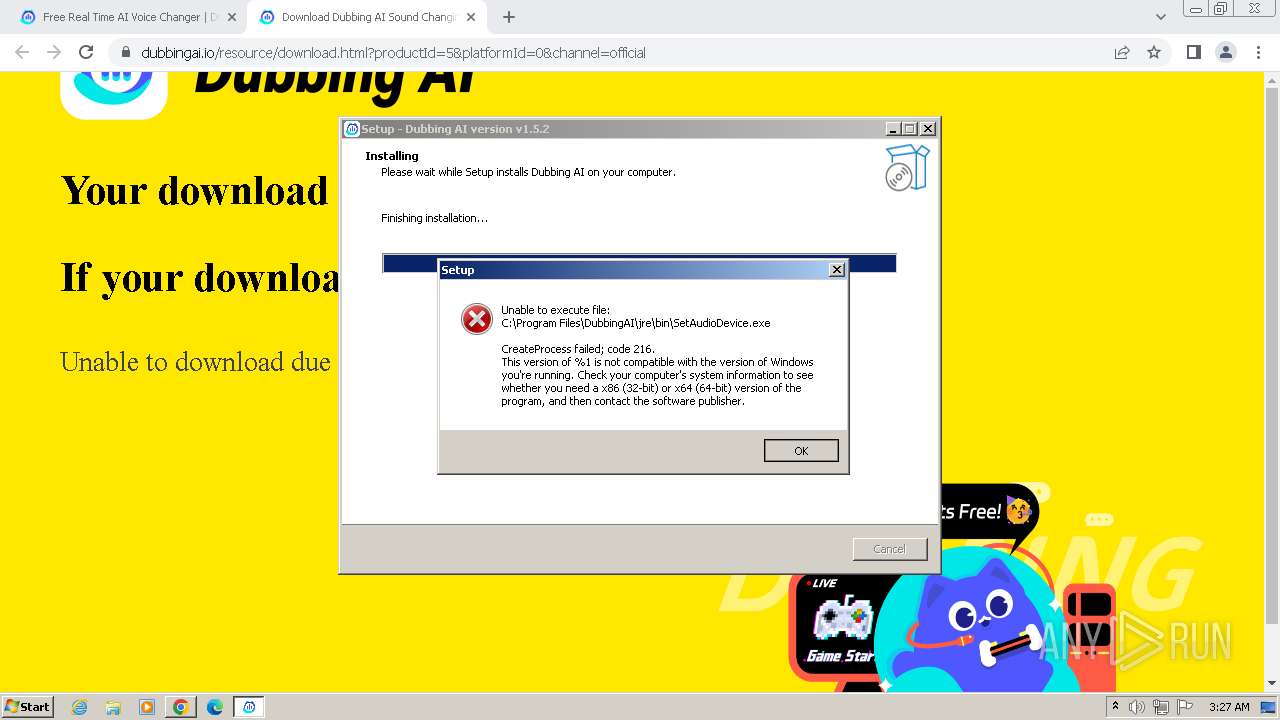
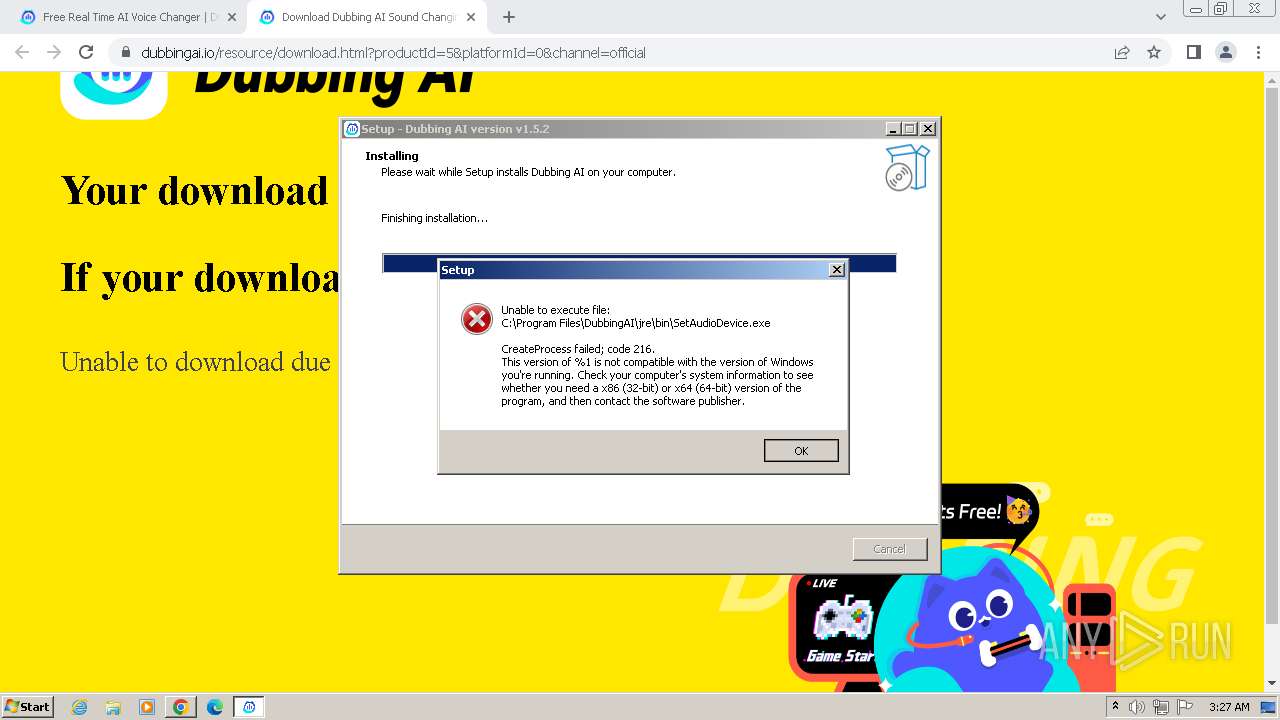
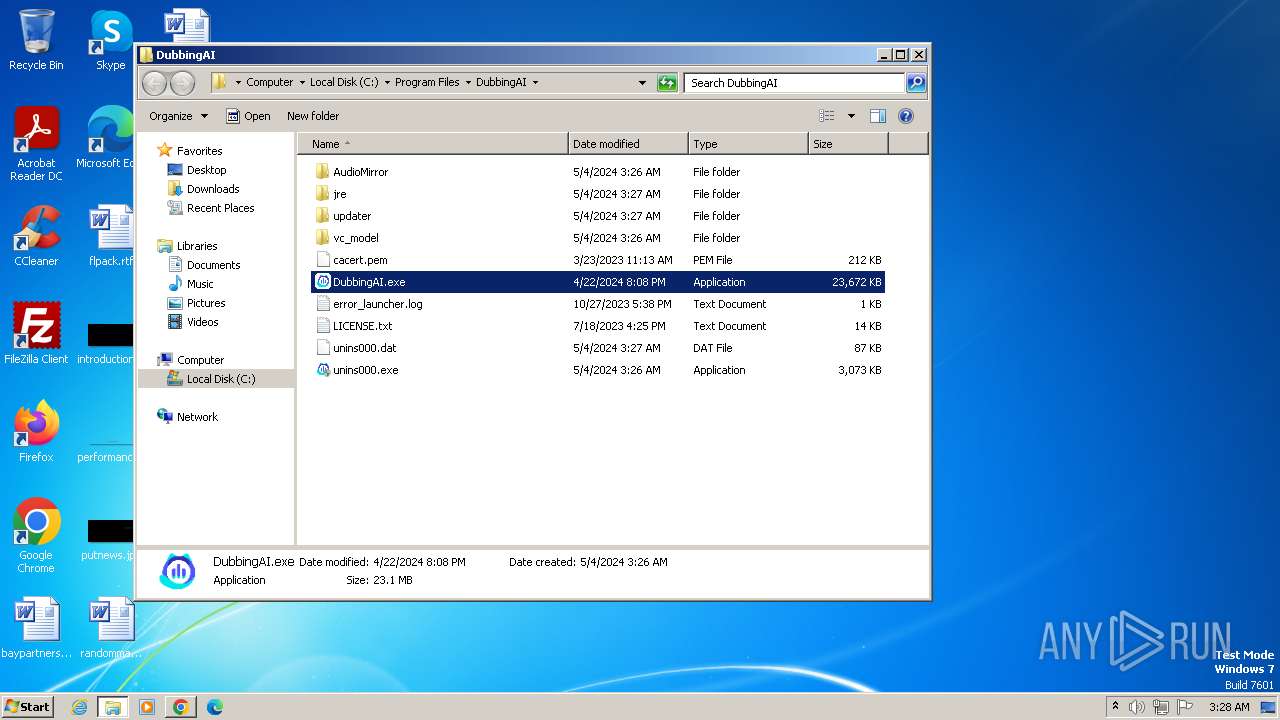
| Verdict: | Malicious activity |
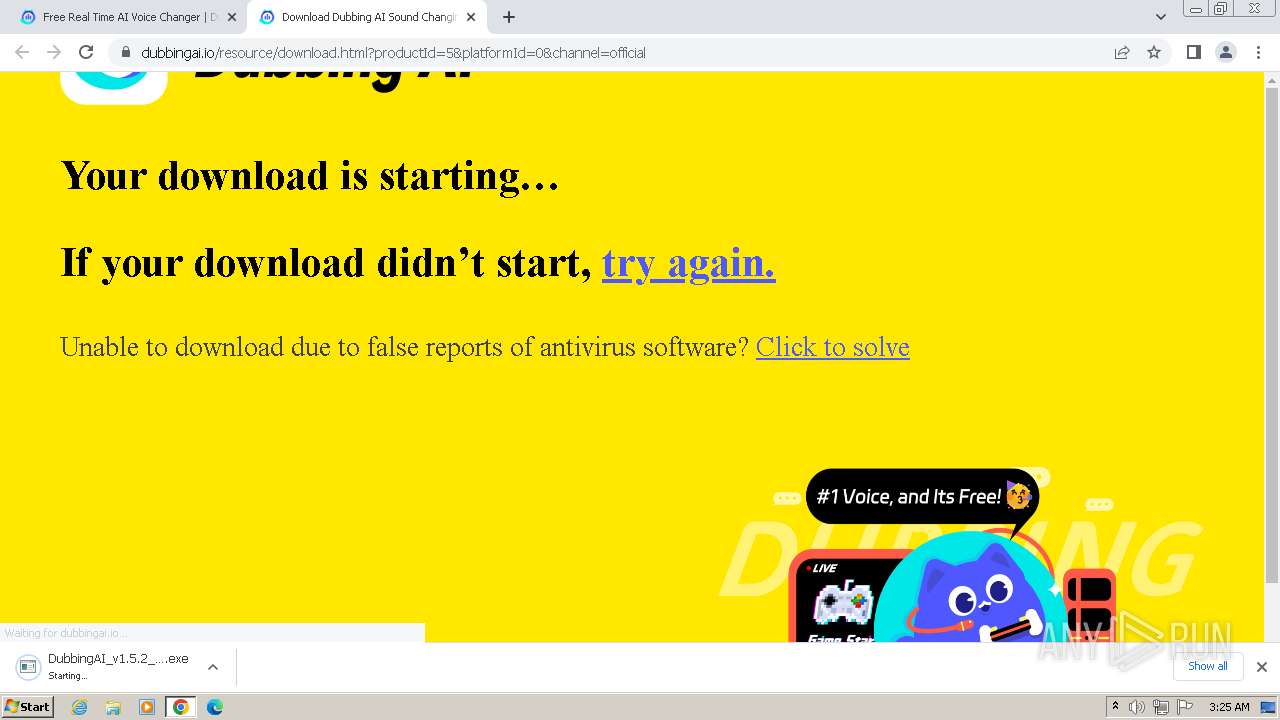
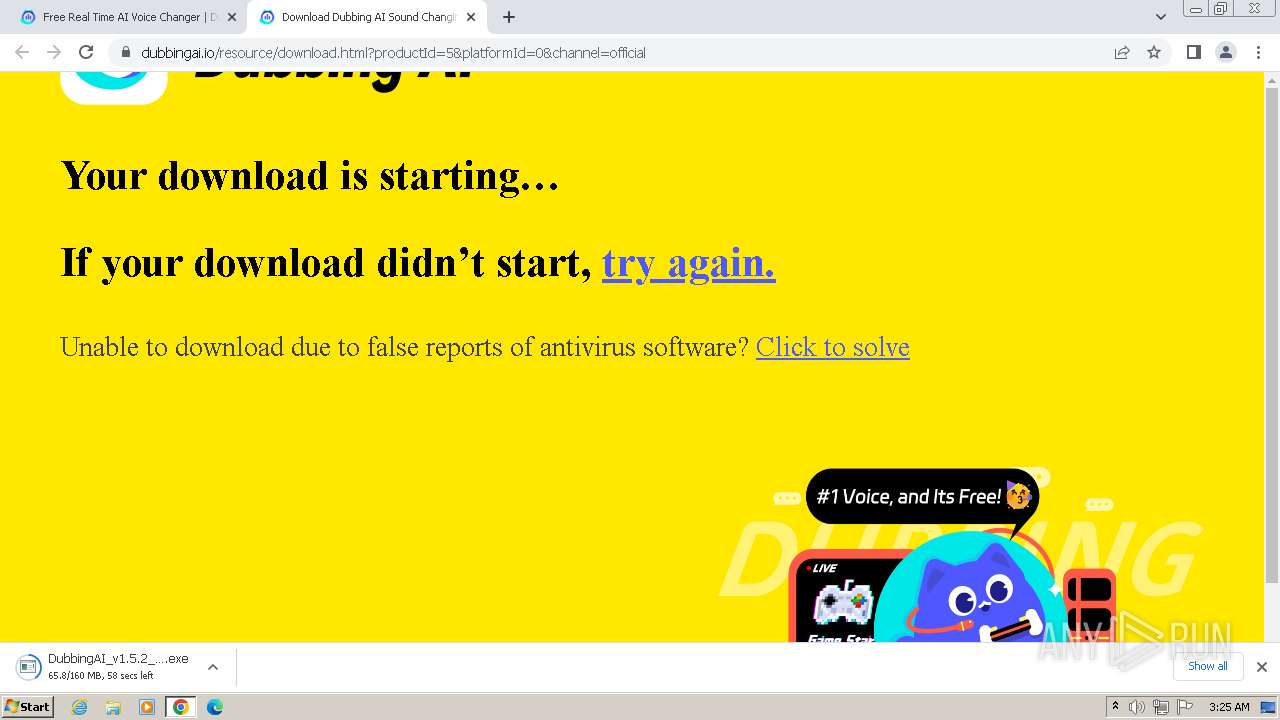
| Analysis date: | May 04, 2024, 02:24:34 |
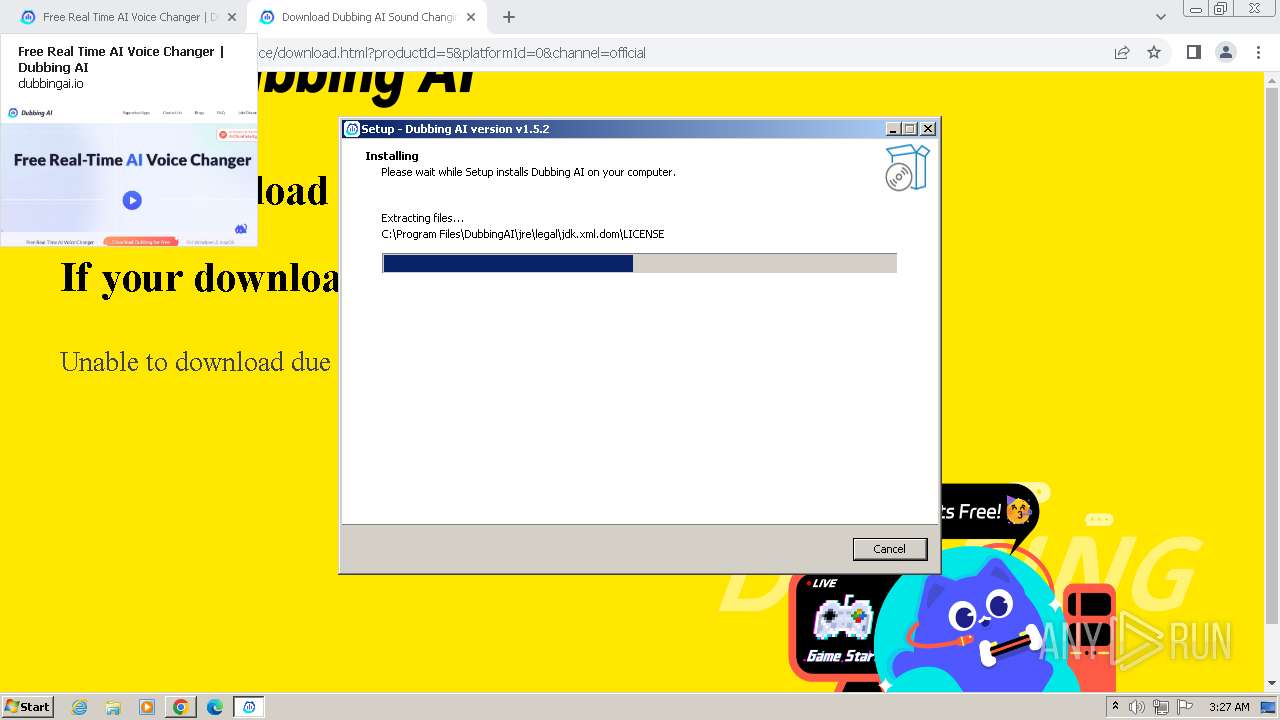
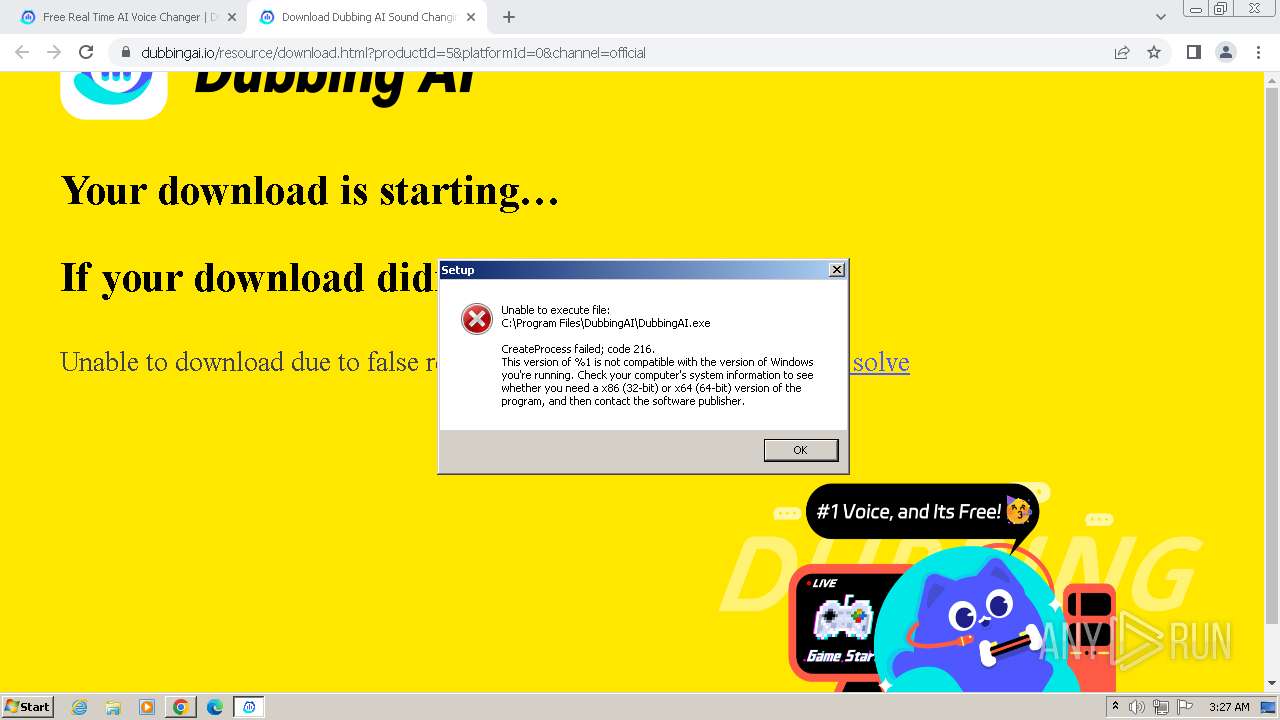
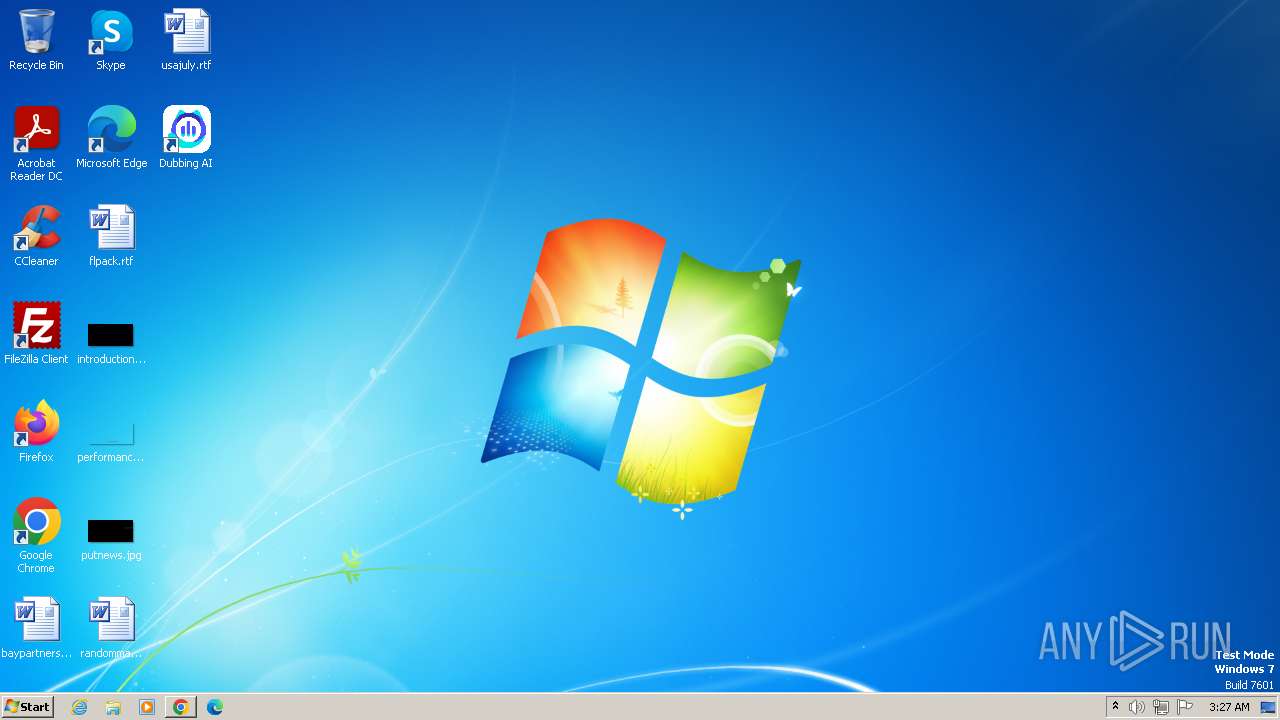
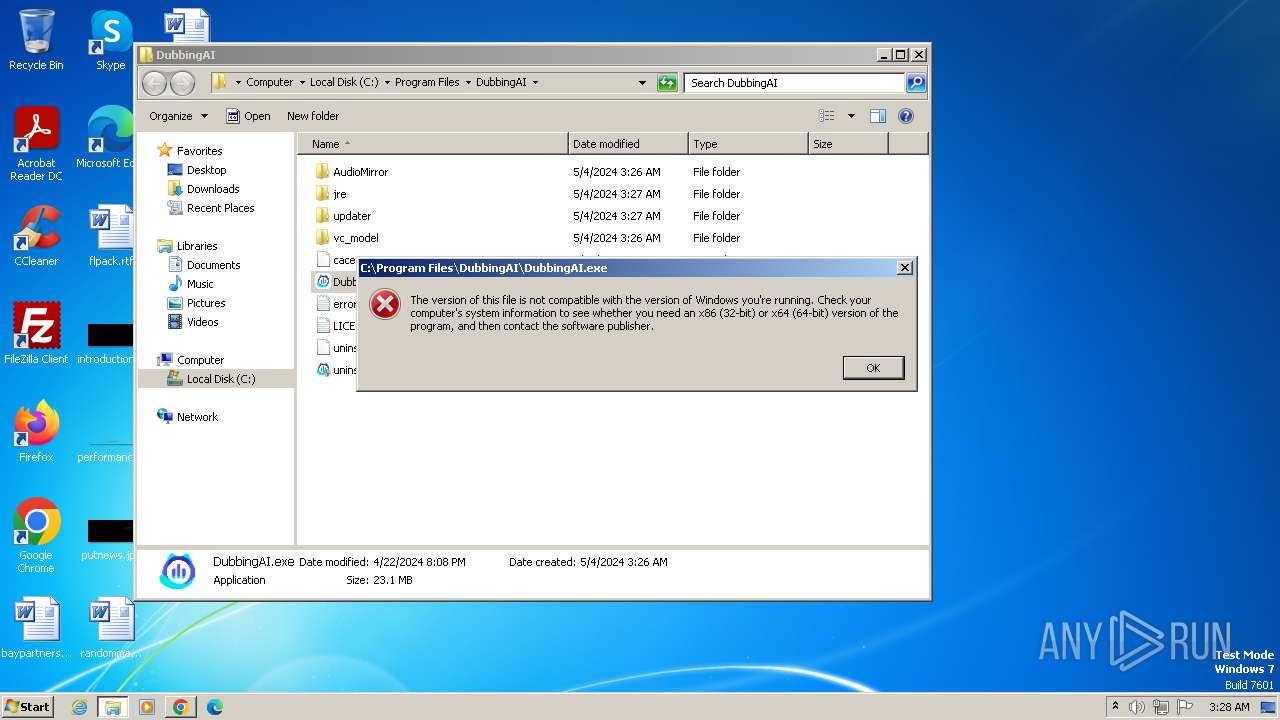
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DDD274AF43FFDE184CAE18546FBB61F2 |
| SHA1: | E056A303EB1A99552BF37D4045D6501CB0C4366F |
| SHA256: | E102BC19BA3829812D506EDF31EAEC8A1CC1750C21A0BE23016DA7EA94DB345E |
| SSDEEP: | 3:N8Inn4Kn:2InH |
MALICIOUS
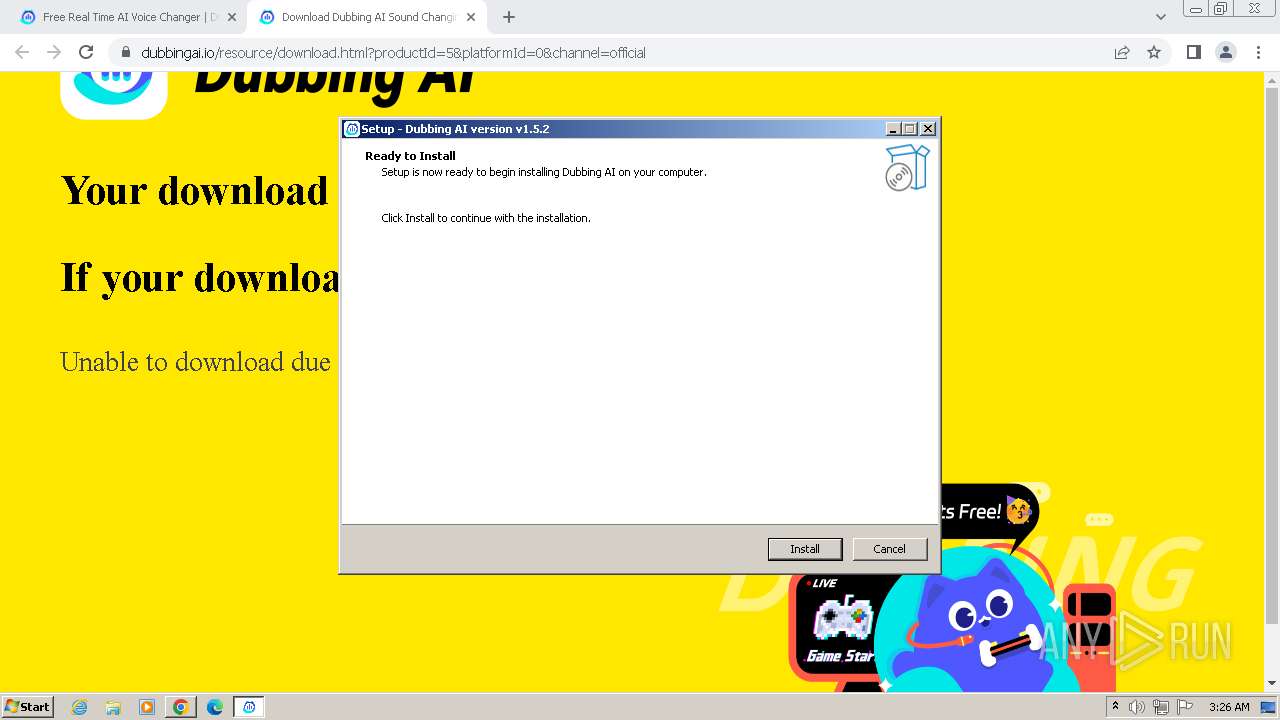
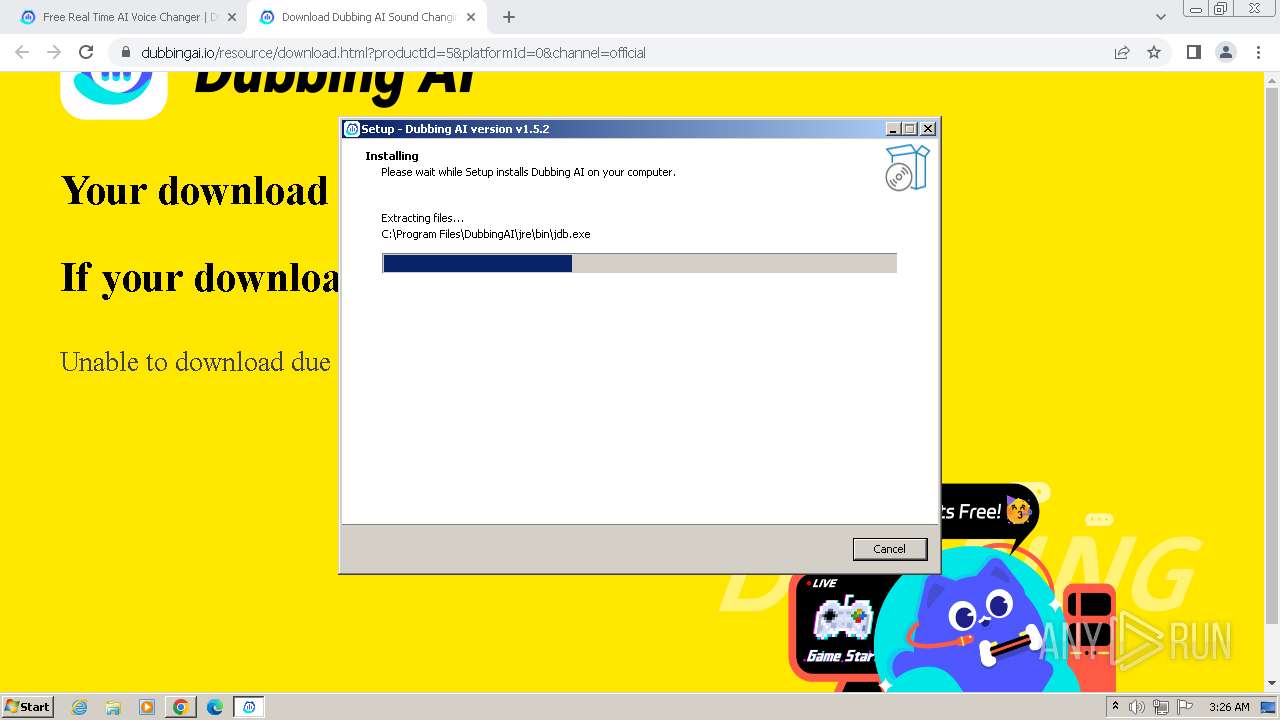
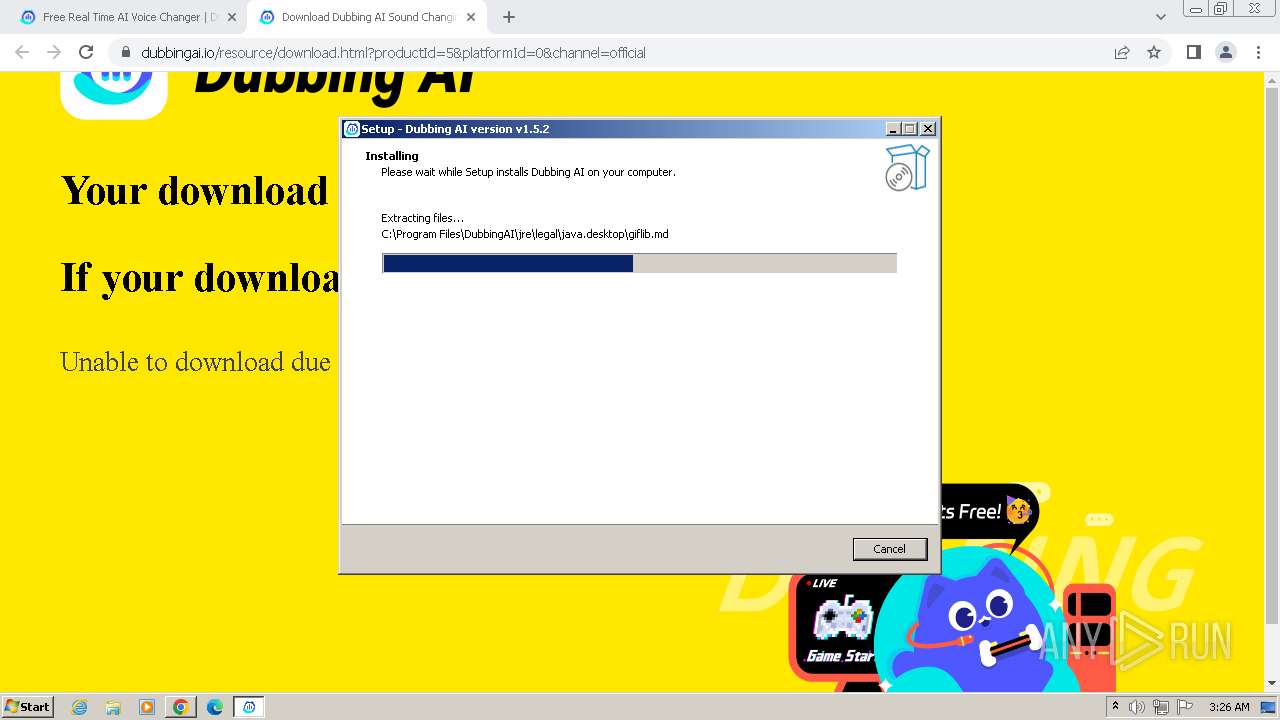
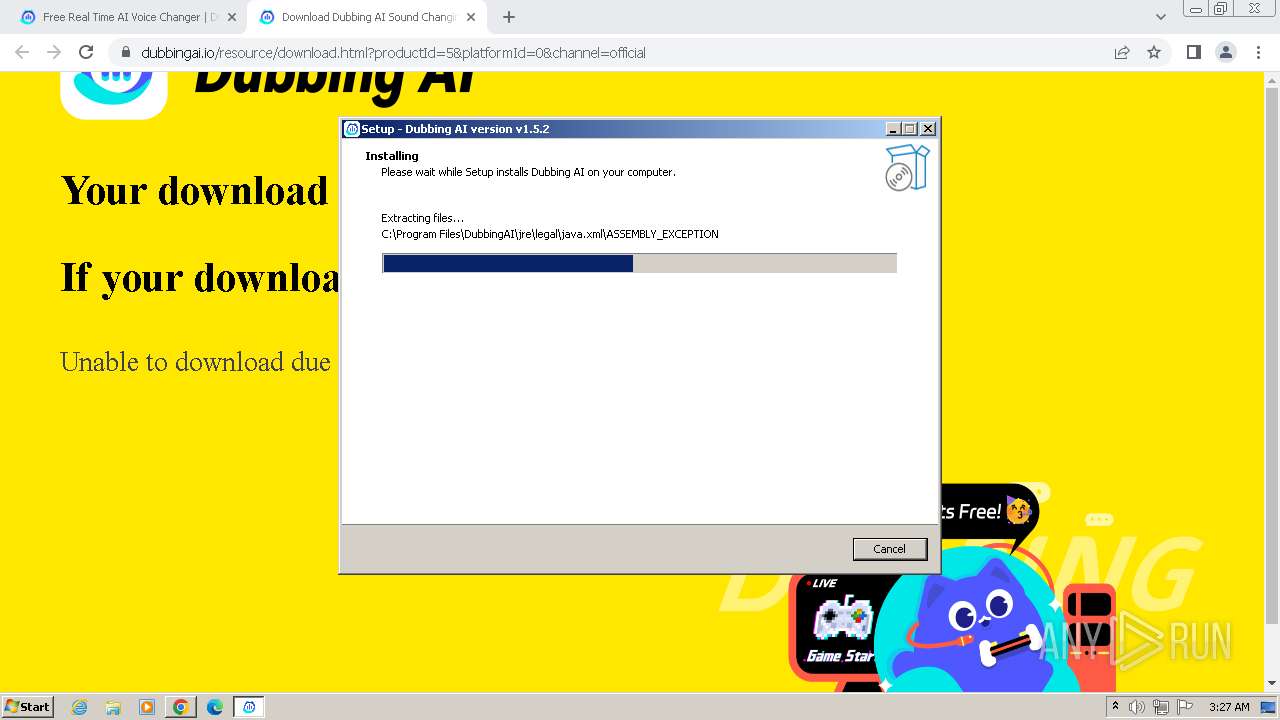
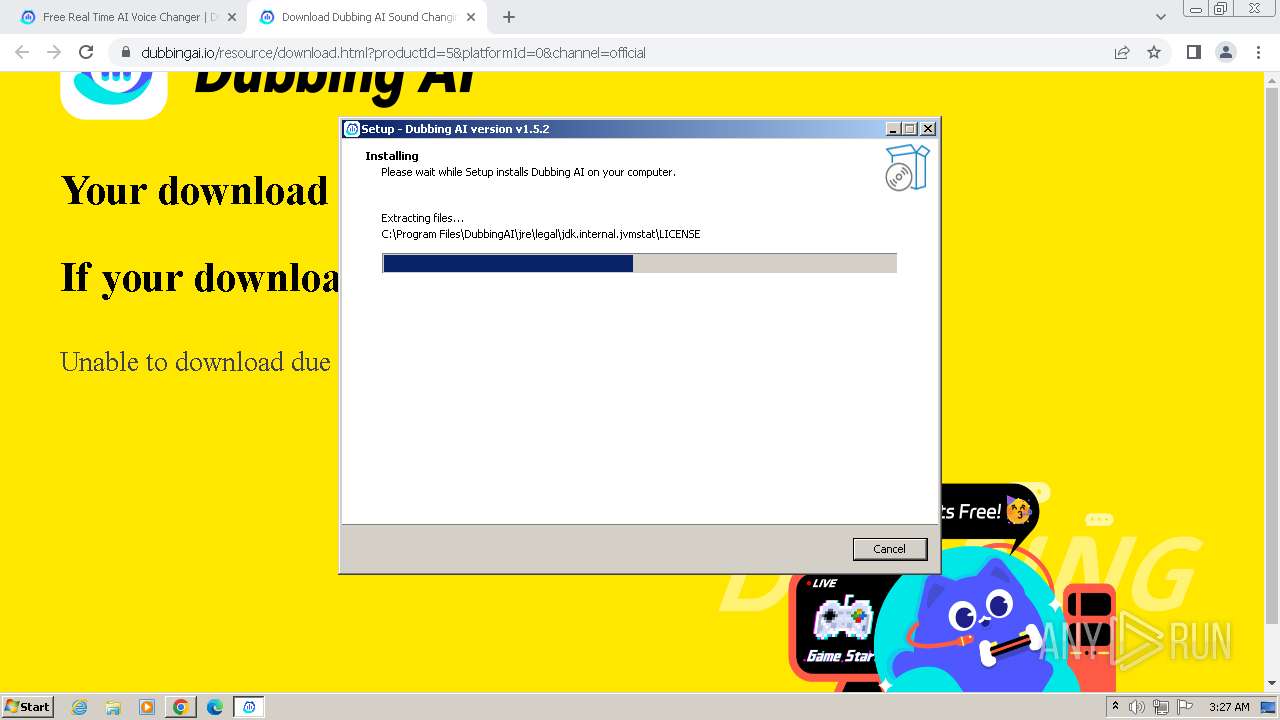
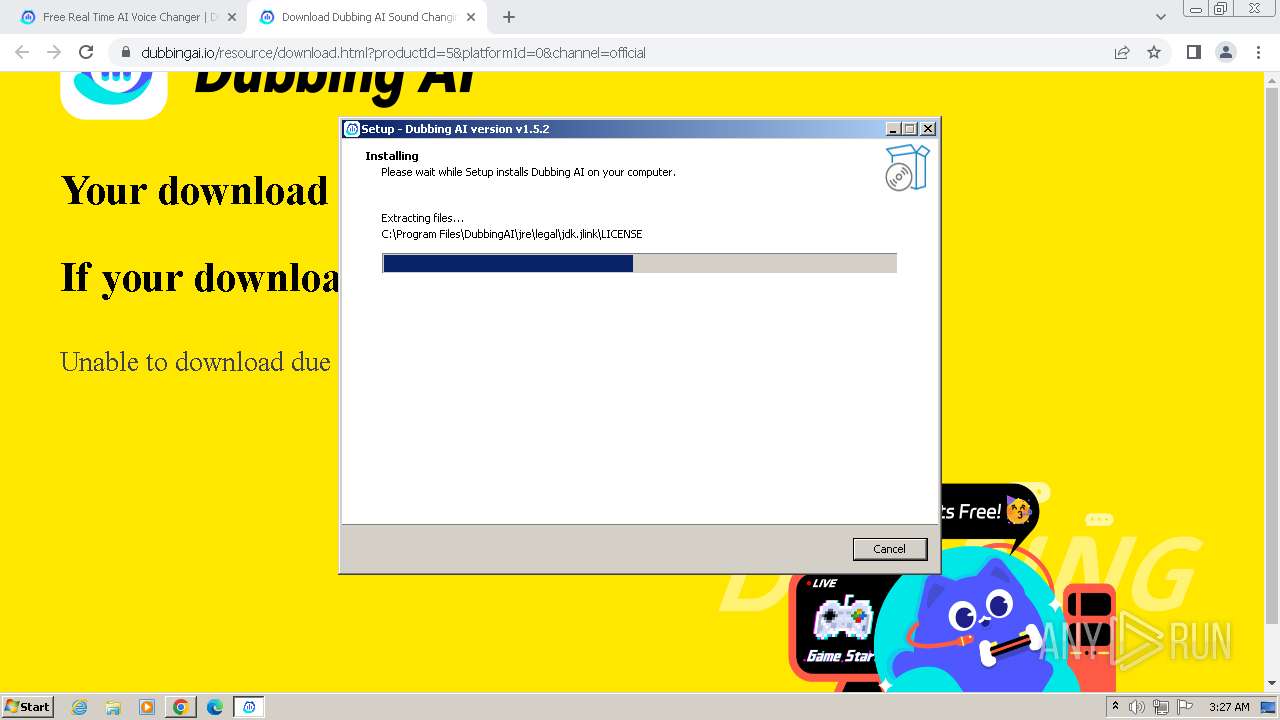
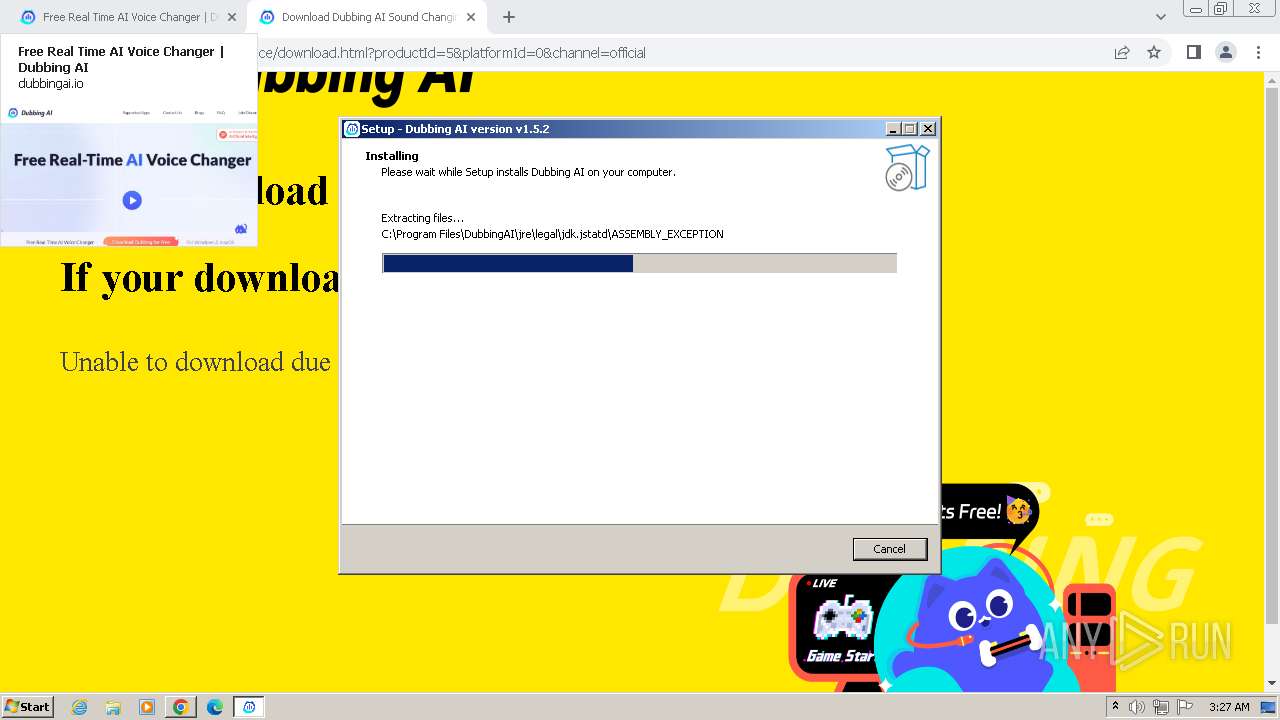
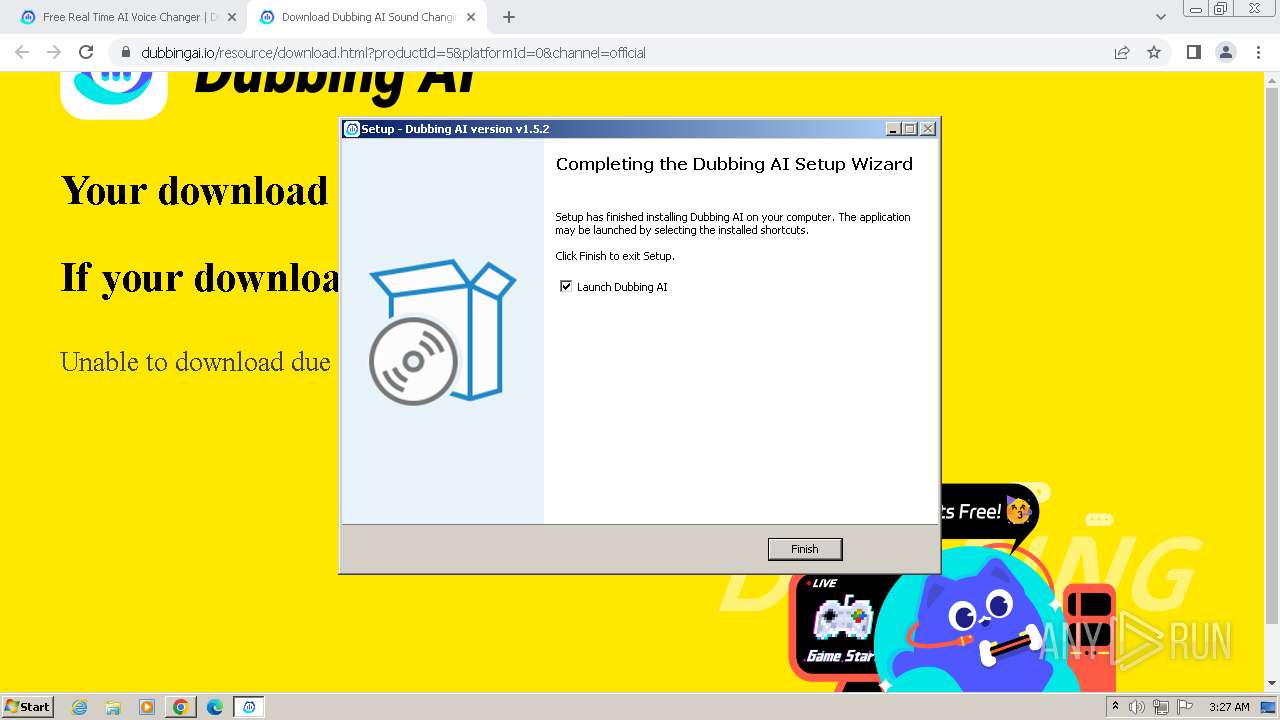
Drops the executable file immediately after the start
- DubbingAI_v1.5.2_04222009_Release_Setup.exe (PID: 3448)
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
- csc.exe (PID: 2168)
- csc.exe (PID: 1396)
- csc.exe (PID: 1876)
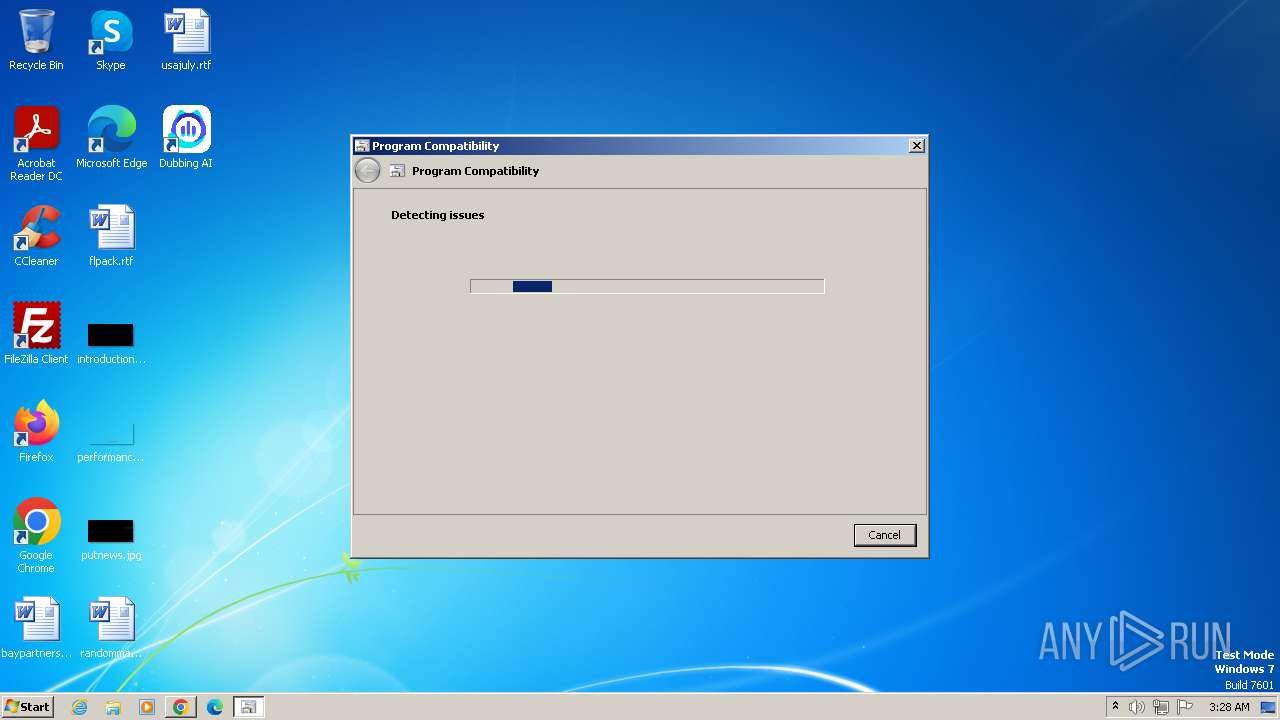
Starts Visual C# compiler
- sdiagnhost.exe (PID: 956)
SUSPICIOUS
Executable content was dropped or overwritten
- DubbingAI_v1.5.2_04222009_Release_Setup.exe (PID: 3448)
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
- csc.exe (PID: 1396)
- csc.exe (PID: 2168)
- csc.exe (PID: 1876)
Reads the Windows owner or organization settings
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
Drops a system driver (possible attempt to evade defenses)
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
The process drops C-runtime libraries
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
Process drops legitimate windows executable
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
Executing commands from a ".bat" file
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
Starts CMD.EXE for commands execution
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
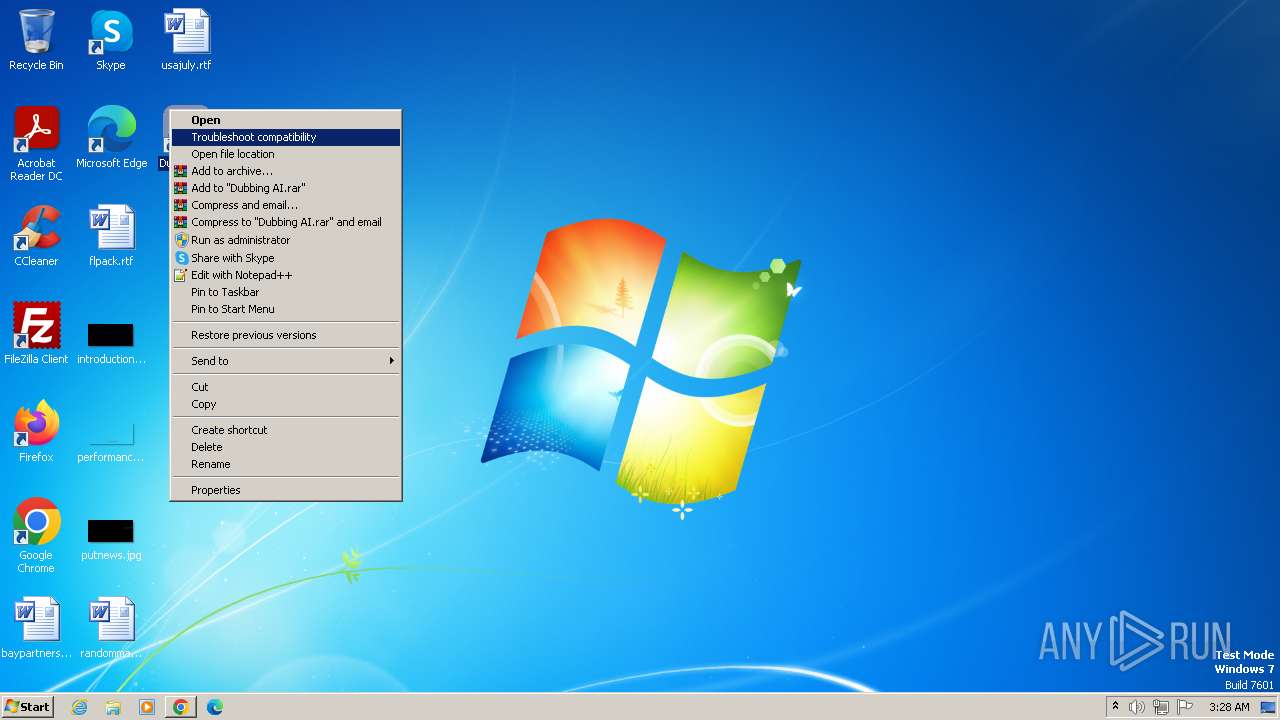
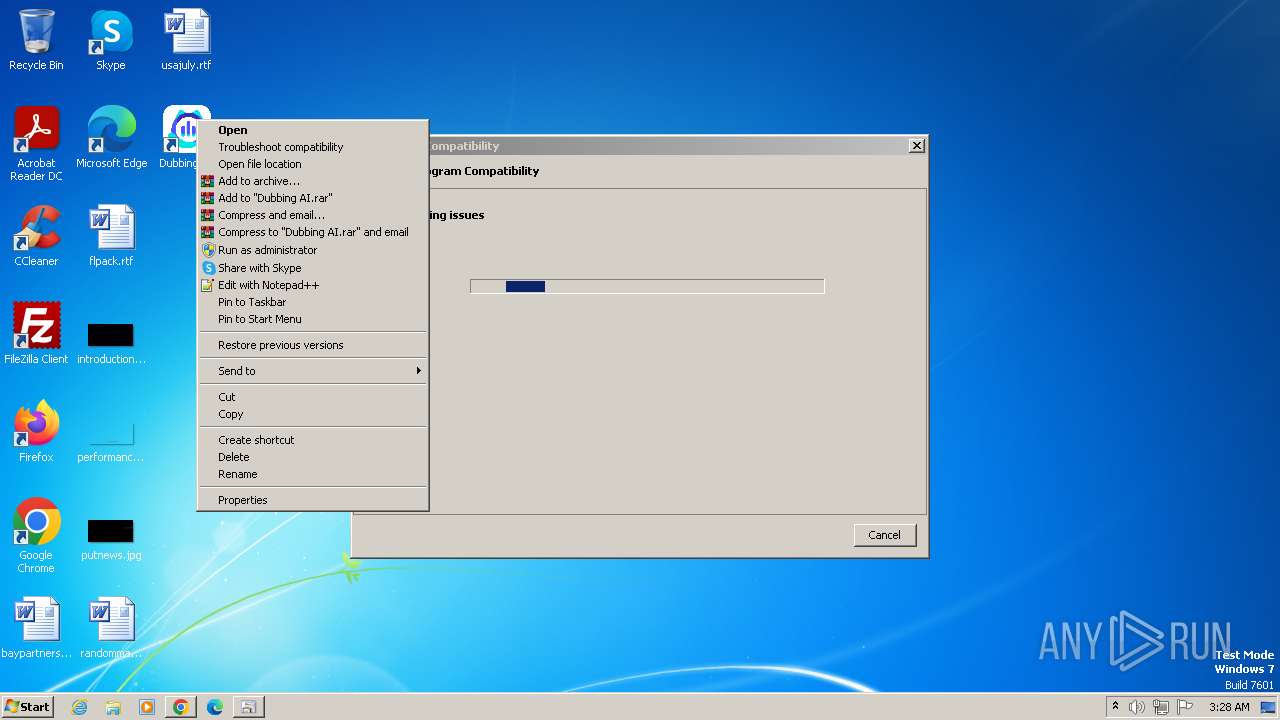
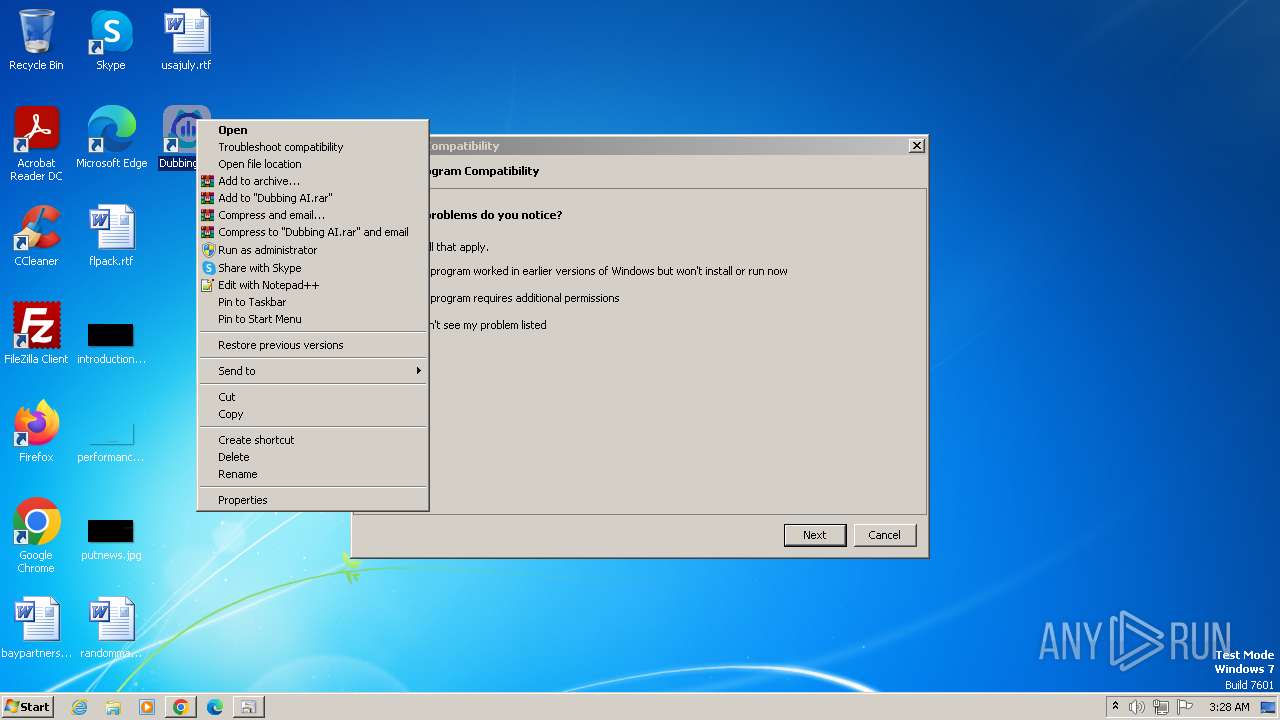
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 3240)
Reads the Internet Settings
- sdiagnhost.exe (PID: 956)
Uses .NET C# to load dll
- sdiagnhost.exe (PID: 956)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 580)
- DubbingAI_v1.5.2_04222009_Release_Setup.exe (PID: 3448)
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
- csc.exe (PID: 1396)
- cvtres.exe (PID: 1380)
- csc.exe (PID: 2168)
- cvtres.exe (PID: 856)
- csc.exe (PID: 1876)
- cvtres.exe (PID: 372)
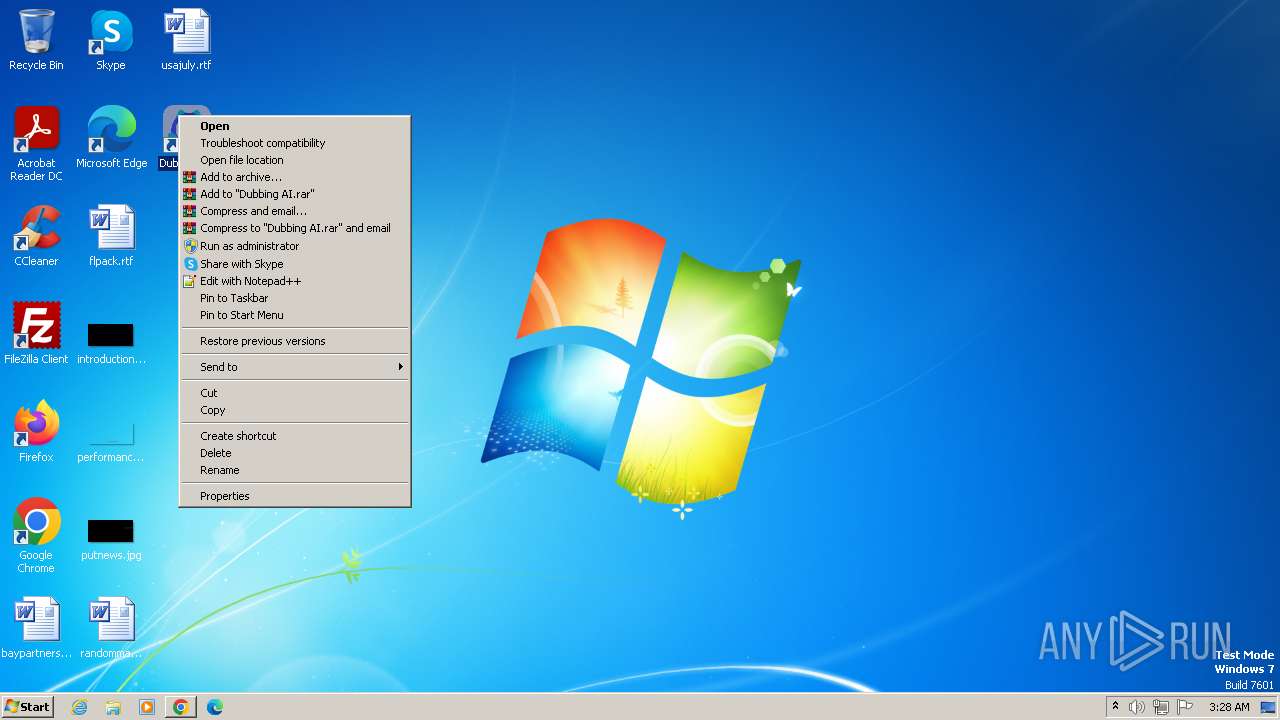
Manual execution by a user
- wmpnscfg.exe (PID: 580)
- pcwrun.exe (PID: 3240)
Reads the computer name
- wmpnscfg.exe (PID: 580)
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
Drops the executable file immediately after the start
- chrome.exe (PID: 3988)
- msdt.exe (PID: 2076)
Executable content was dropped or overwritten
- chrome.exe (PID: 3988)
The process uses the downloaded file
- chrome.exe (PID: 2820)
- chrome.exe (PID: 3988)
Create files in a temporary directory
- DubbingAI_v1.5.2_04222009_Release_Setup.exe (PID: 3448)
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
- pcwrun.exe (PID: 3240)
- msdt.exe (PID: 2076)
- sdiagnhost.exe (PID: 956)
- csc.exe (PID: 1396)
- cvtres.exe (PID: 1380)
- csc.exe (PID: 2168)
- cvtres.exe (PID: 856)
- csc.exe (PID: 1876)
- cvtres.exe (PID: 372)
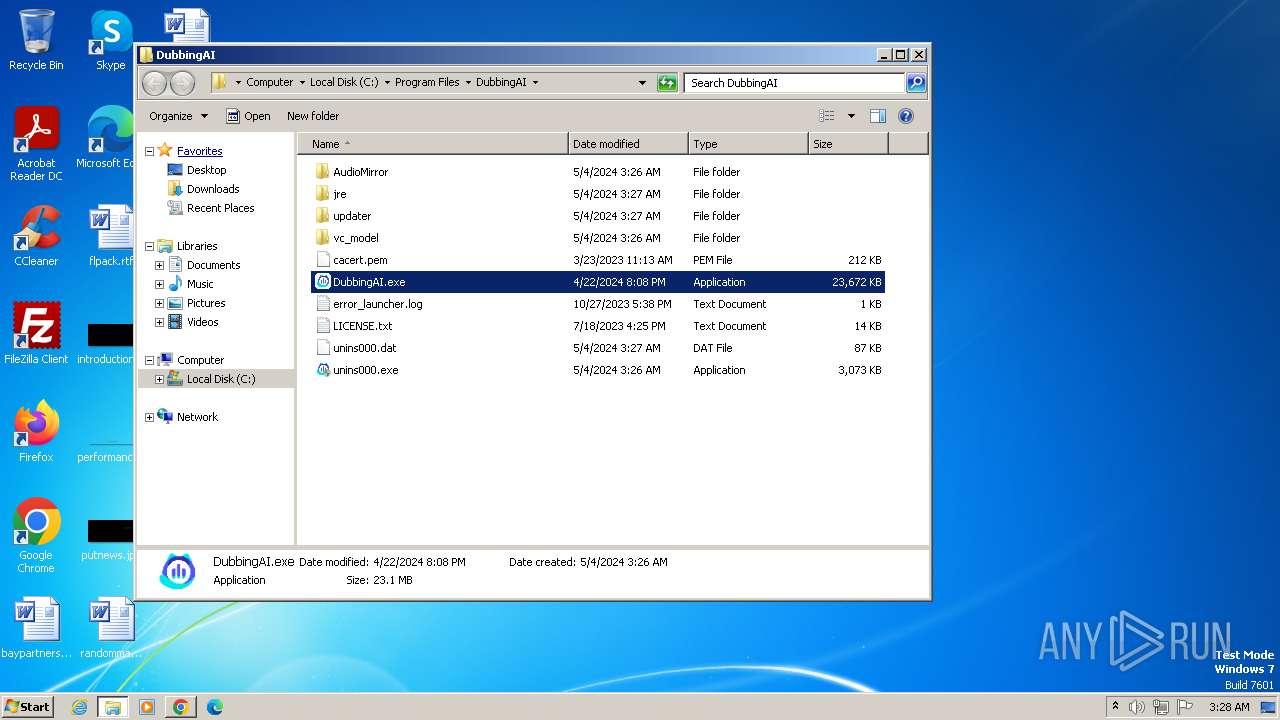
Creates files in the program directory
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
Application launched itself
- chrome.exe (PID: 3988)
Dropped object may contain TOR URL's
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
Creates a software uninstall entry
- DubbingAI_v1.5.2_04222009_Release_Setup.tmp (PID: 3420)
Reads the software policy settings
- msdt.exe (PID: 2076)
Reads security settings of Internet Explorer
- sdiagnhost.exe (PID: 956)
- msdt.exe (PID: 2076)
Reads the machine GUID from the registry
- cvtres.exe (PID: 1380)
- csc.exe (PID: 2168)
- cvtres.exe (PID: 856)
- csc.exe (PID: 1876)
- csc.exe (PID: 1396)
- cvtres.exe (PID: 372)
Creates files or folders in the user directory
- msdt.exe (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
39
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1516 --field-trial-handle=1160,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3116 --field-trial-handle=1160,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2028 --field-trial-handle=1160,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 372 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES4B84.tmp" "c:\Users\admin\AppData\Local\Temp\CSC4B74.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2040 --field-trial-handle=1160,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1296 --field-trial-handle=1160,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 856 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES4AC9.tmp" "c:\Users\admin\AppData\Local\Temp\CSC4AC8.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 956 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1060 --field-trial-handle=1160,i,13539599199737919351,5092840889132813259,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
19 195
Read events
19 027
Write events
154
Delete events
14
Modification events
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
313
Suspicious files
226
Text files
640
Unknown types
158
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1036b2.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\65482728-f01a-4ebd-9f34-1e561e58e309.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1040a5.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF1039ee.TMP | text | |
MD5:BF244CDEBD39A0D20444C1578C0200BE | SHA256:CC7E247D7764DA50D4137E894838F918281D4915FE0823B4FC0CB763BF582F4D | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF103980.TMP | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
40
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acezyjyt2fp2x53dhyqbvt3gxdlq_63/khaoiebndkojlmppeemjhbpbandiljpe_63_win_pz5ggrx6ddtwepg55hf2663jnu.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acezyjyt2fp2x53dhyqbvt3gxdlq_63/khaoiebndkojlmppeemjhbpbandiljpe_63_win_pz5ggrx6ddtwepg55hf2663jnu.crx3 | unknown | — | — | unknown |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
884 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acezyjyt2fp2x53dhyqbvt3gxdlq_63/khaoiebndkojlmppeemjhbpbandiljpe_63_win_pz5ggrx6ddtwepg55hf2663jnu.crx3 | unknown | — | — | unknown |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3988 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
748 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
748 | chrome.exe | 104.22.77.213:443 | dubbingai.io | CLOUDFLARENET | — | unknown |
748 | chrome.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | unknown |
748 | chrome.exe | 142.250.185.238:443 | www.youtube.com | GOOGLE | US | whitelisted |
748 | chrome.exe | 104.18.126.118:443 | api.producthunt.com | CLOUDFLARENET | — | unknown |
748 | chrome.exe | 216.58.206.35:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dubbingai.io |
| unknown |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
www.youtube.com |
| whitelisted |
api.producthunt.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
static.doubleclick.net |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|