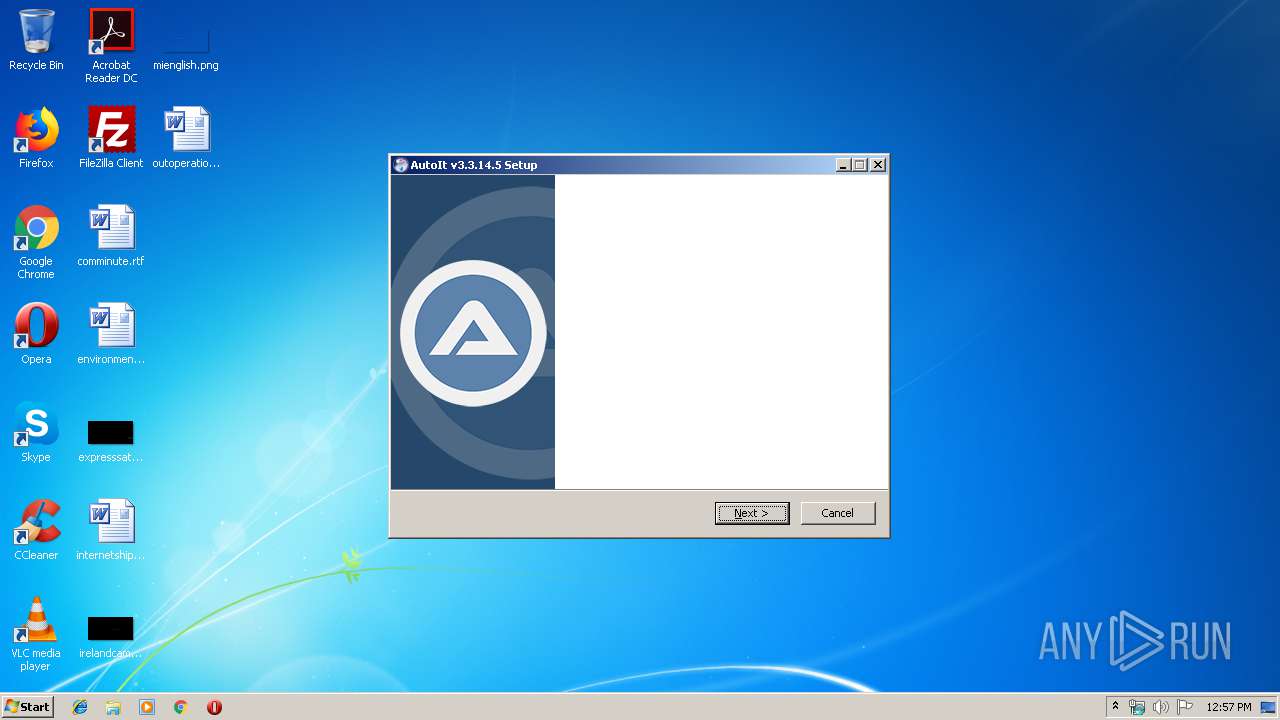
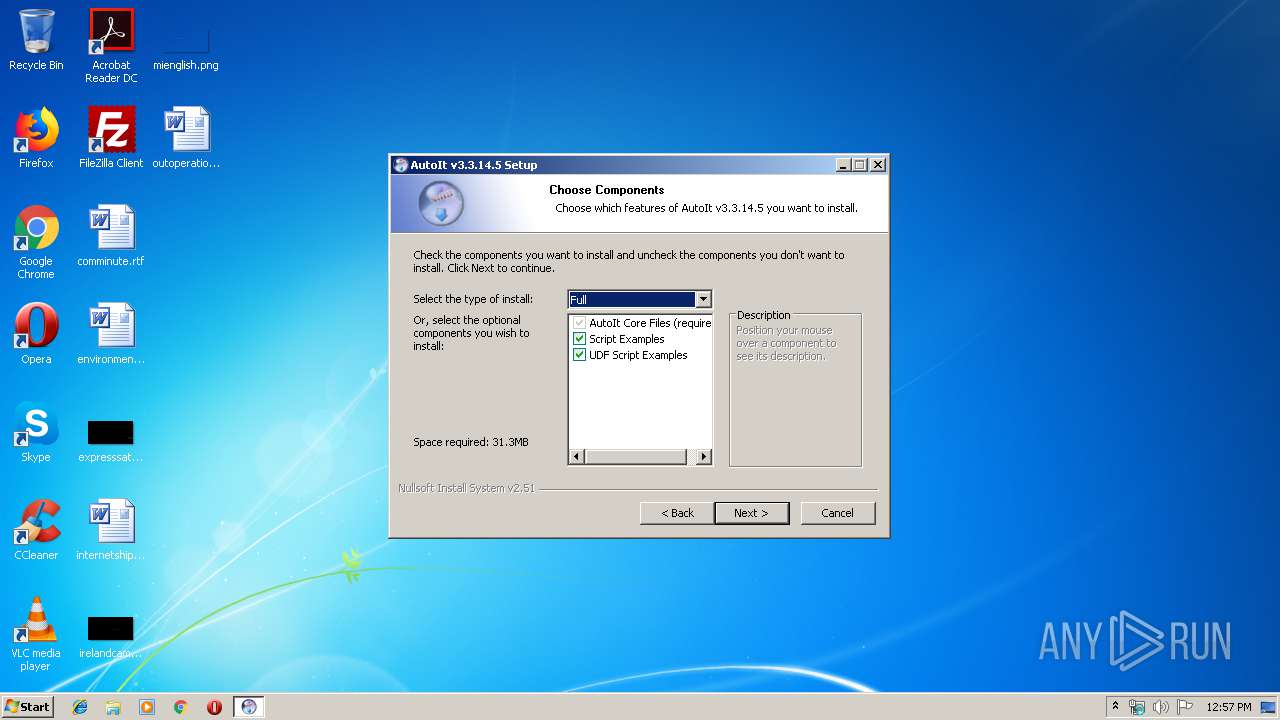
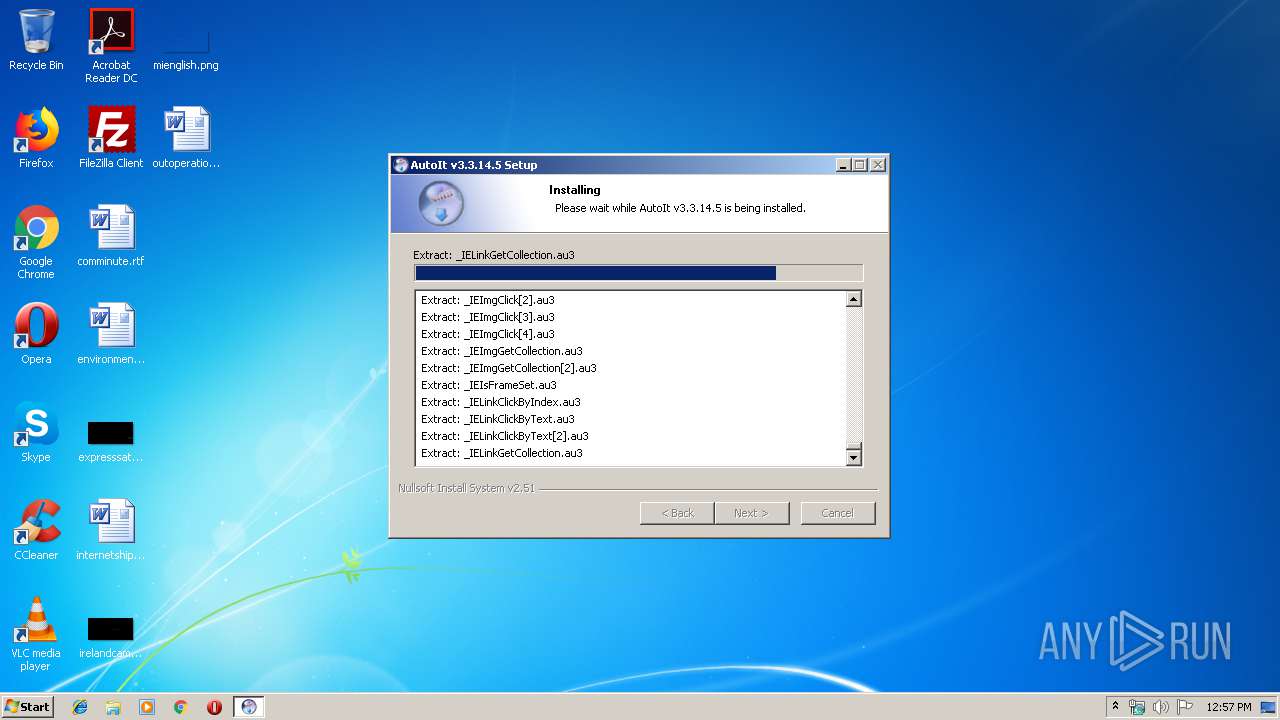
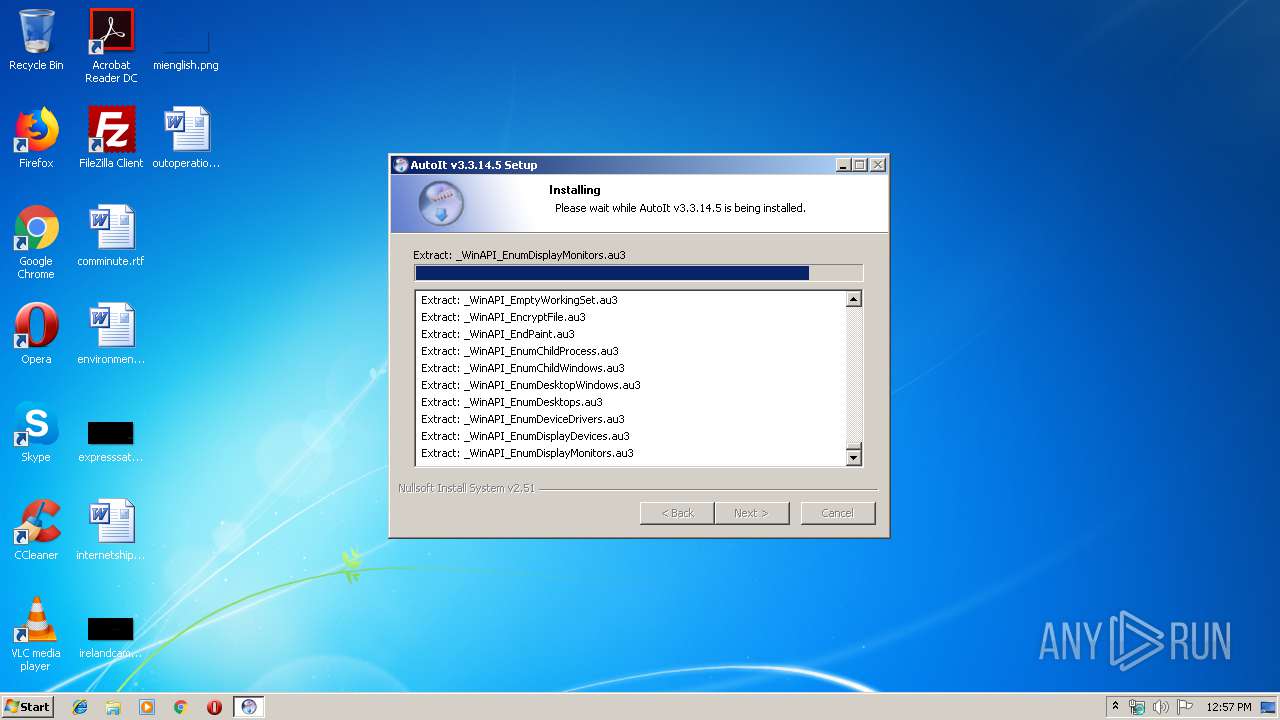
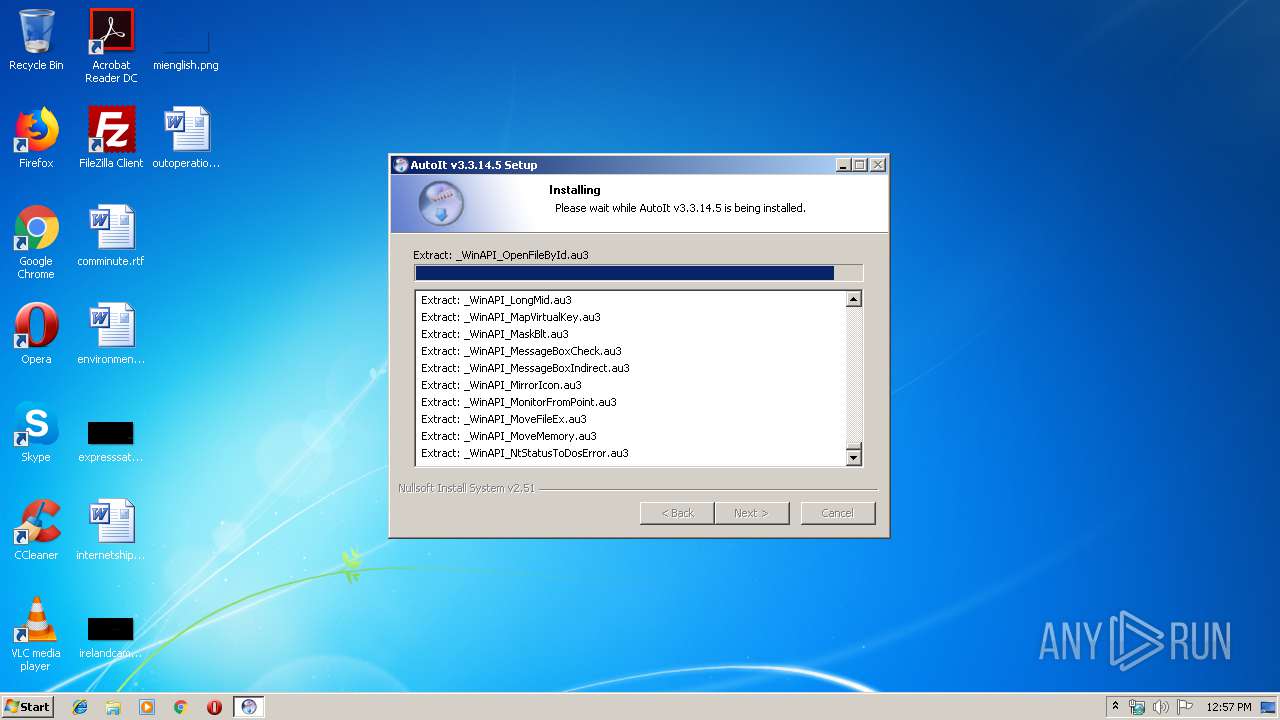
| File name: | autoit-v3-setup.exe |
| Full analysis: | https://app.any.run/tasks/8c6b711c-dc59-41f3-938c-d99e8905af8a |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 11:57:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D50D5712566F1DF16B5AEA21B9E0EE24 |
| SHA1: | F442AA68EC8D838625F382BCF273F5D0F66427EA |
| SHA256: | E102238100A8B97D22559065E3B19379757AEDA932C36916D2C84A4178921854 |
| SSDEEP: | 196608:RibMxSfOYFjizV+mKPdih/DuHKaJC9vdGFMiEXxHeJtMvU9Bi7SkEGIT9OOa5SPl:3xgjihkUhKHKr0M19lSBi7S02OOagDOe |
MALICIOUS
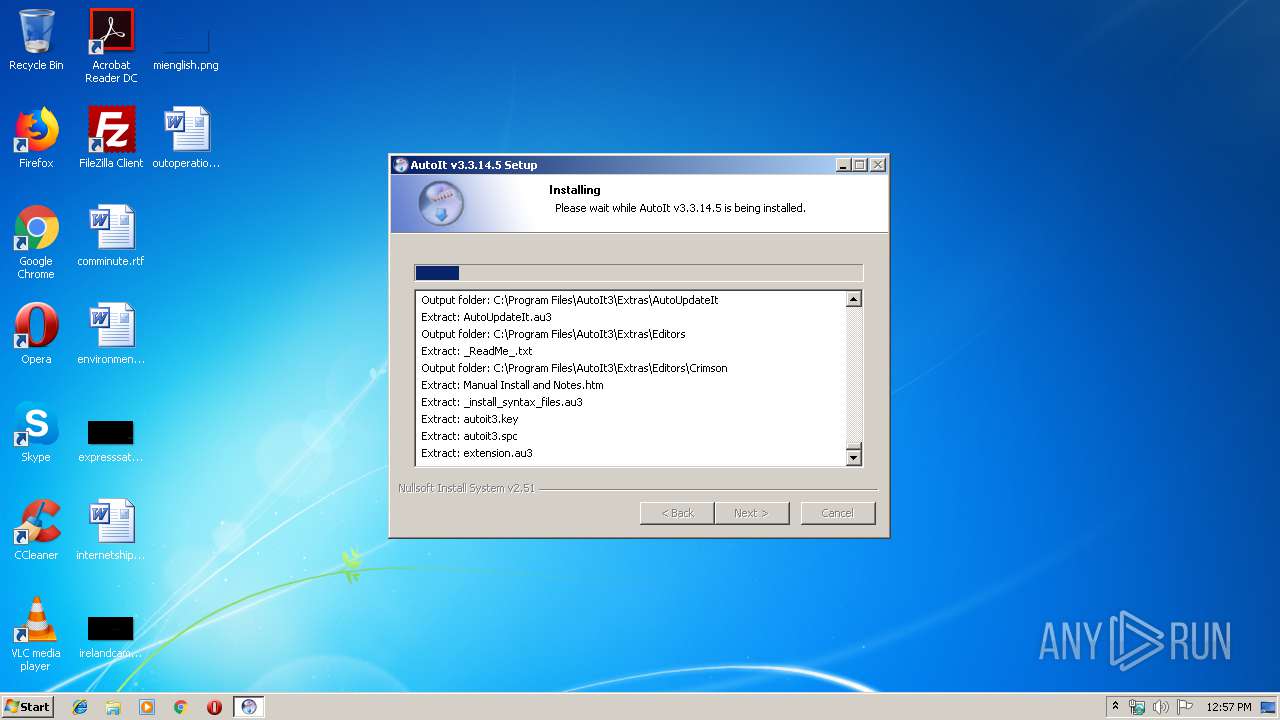
Loads dropped or rewritten executable
- autoit-v3-setup.exe (PID: 3988)
SUSPICIOUS
Creates files in the Windows directory
- autoit-v3-setup.exe (PID: 3988)
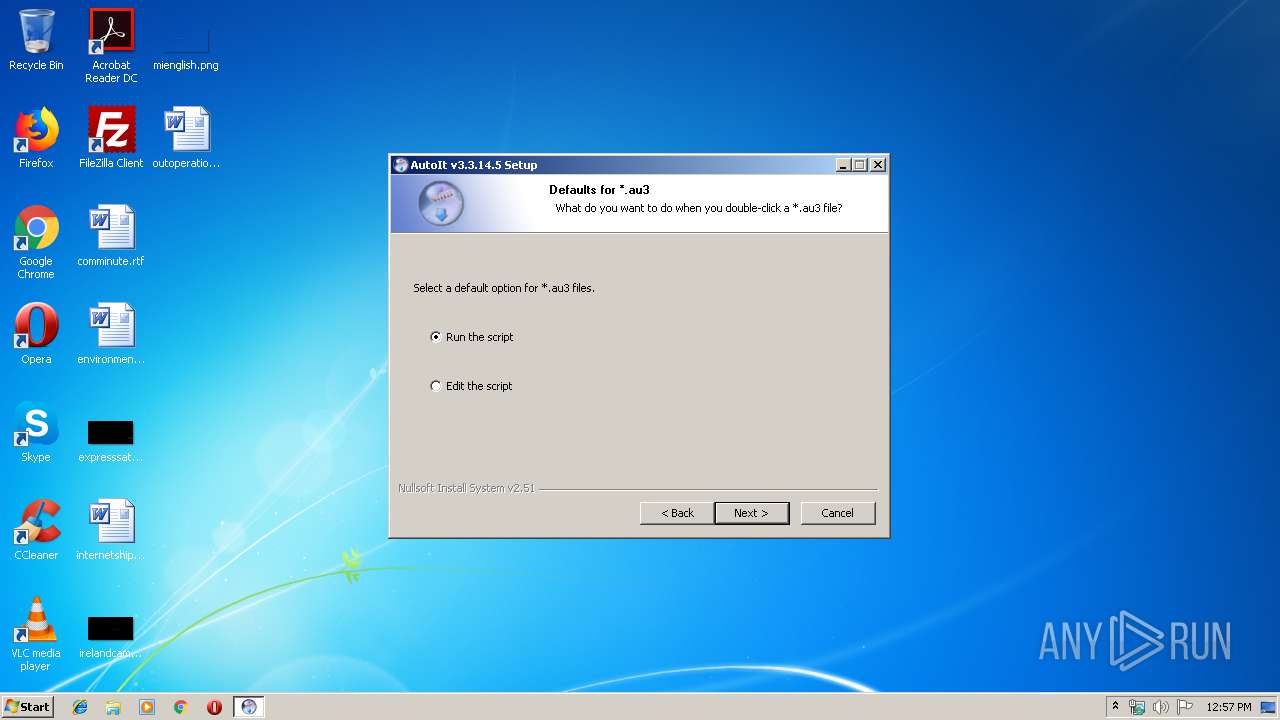
Modifies the open verb of a shell class
- autoit-v3-setup.exe (PID: 3988)
Creates COM task schedule object
- autoit-v3-setup.exe (PID: 3988)
Creates a software uninstall entry
- autoit-v3-setup.exe (PID: 3988)
Reads internet explorer settings
- hh.exe (PID: 2652)
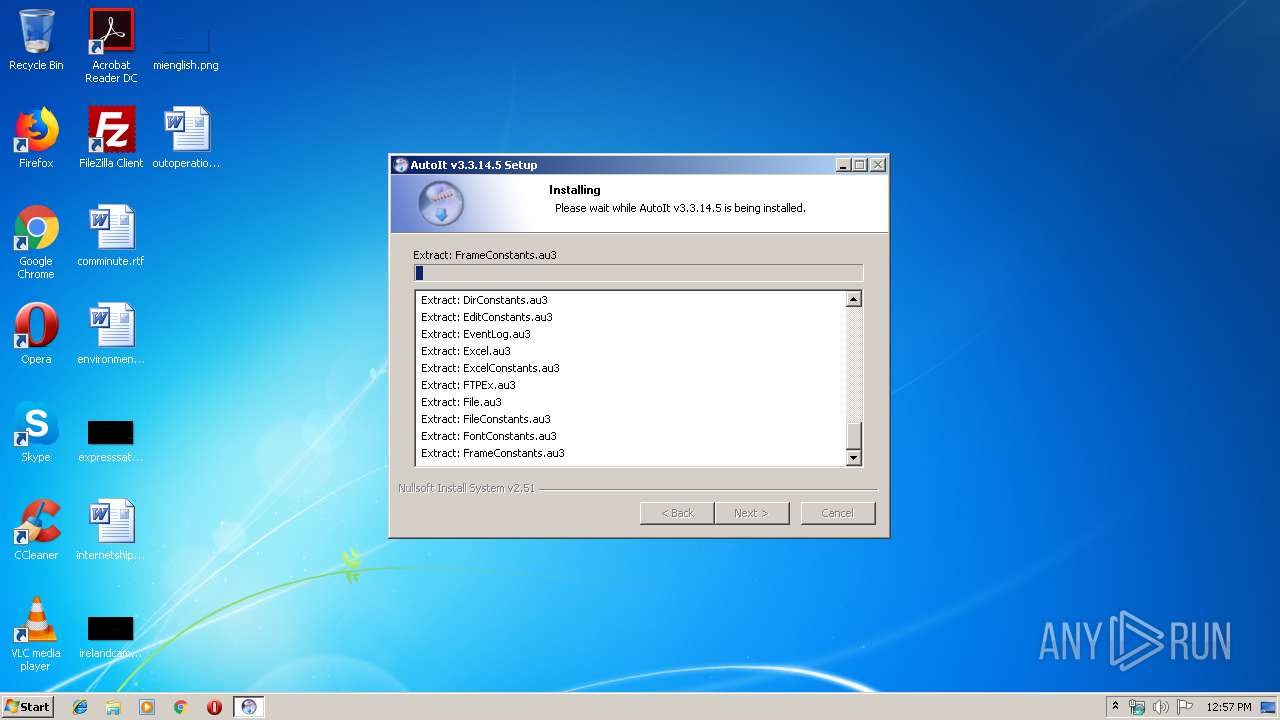
Drop AutoIt3 executable file
- autoit-v3-setup.exe (PID: 3988)
Reads Internet Cache Settings
- hh.exe (PID: 2652)
Executable content was dropped or overwritten
- autoit-v3-setup.exe (PID: 3988)
Creates files in the program directory
- autoit-v3-setup.exe (PID: 3988)
INFO
Dropped object may contain Bitcoin addresses
- autoit-v3-setup.exe (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x326c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.14.5 |
| ProductVersionNumber: | 3.3.14.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
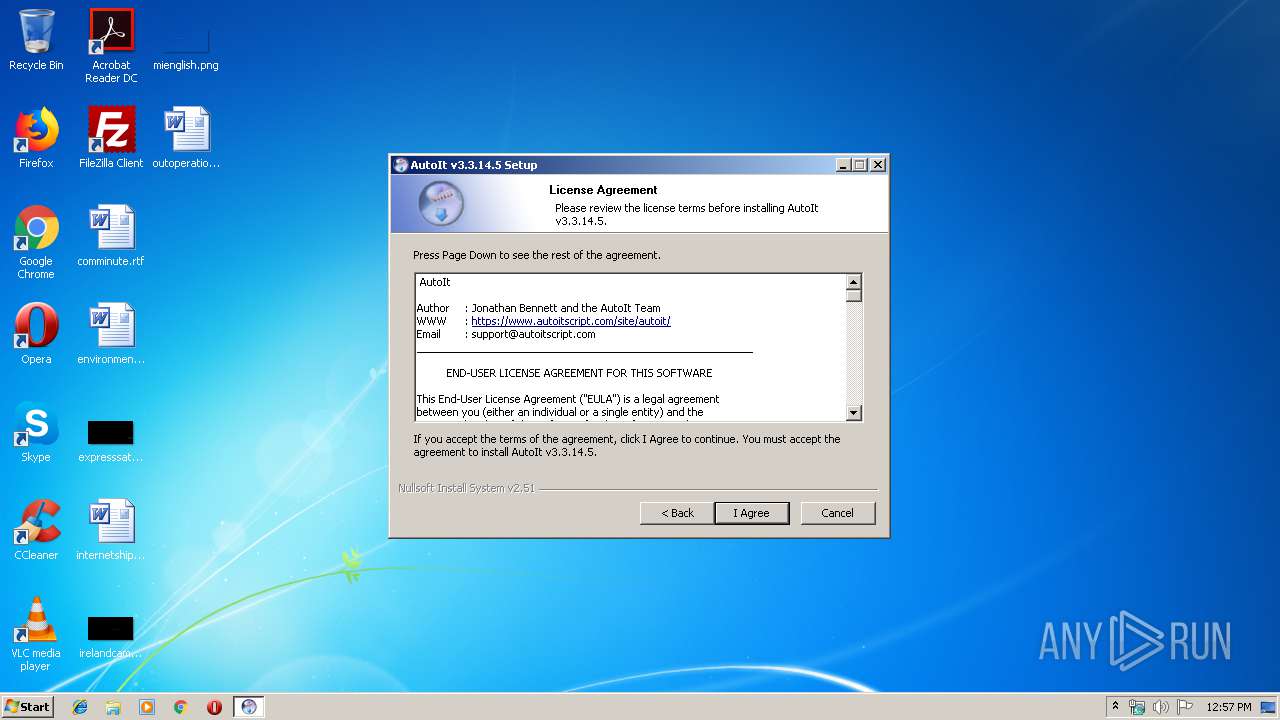
| CompanyName: | AutoIt Team |
| FileDescription: | AutoIt v3 Setup |
| FileVersion: | 3.3.14.5 |
| LegalCopyright: | (c)1999-2018 Jonathan Bennett & AutoIt Team |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:09 |
| Detected languages: |
|
| CompanyName: | AutoIt Team |
| FileDescription: | AutoIt v3 Setup |
| FileVersion: | 3.3.14.5 |
| LegalCopyright: | (c)1999-2018 Jonathan Bennett & AutoIt Team |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C74 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41039 |
.rdata | 0x00007000 | 0x00001196 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20374 |
.data | 0x00009000 | 0x0001B058 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13053 |
.ndata | 0x00025000 | 0x0000C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00031000 | 0x00004E30 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.68111 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21417 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.06944 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.33781 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.13165 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.1985 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70992 | 344 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
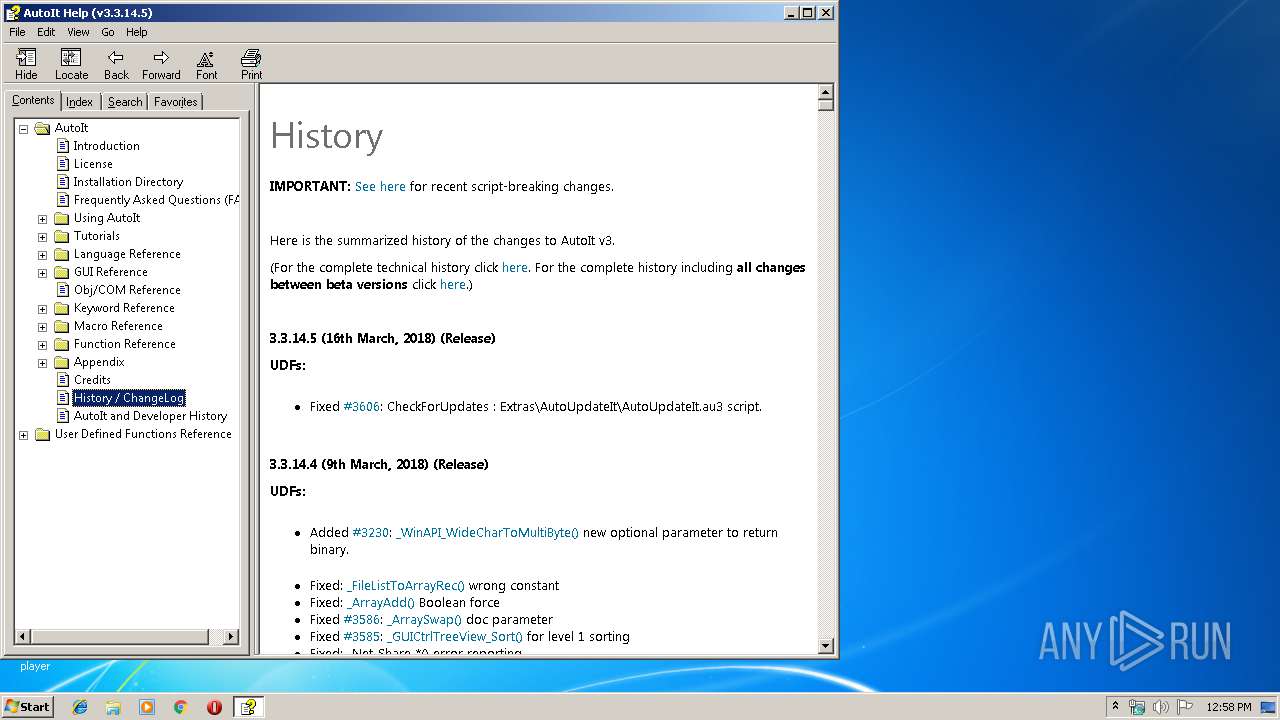
| 2652 | "C:\Windows\hh.exe" -mapid 1000 "C:\Program Files\AutoIt3\AutoIt.chm" | C:\Windows\hh.exe | — | autoit-v3-setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe" | C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Setup Exit code: 3221226540 Version: 3.3.14.5 Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe" | C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: HIGH Description: AutoIt v3 Setup Exit code: 0 Version: 3.3.14.5 Modules
| |||||||||||||||
Total events
521
Read events
435
Write events
85
Delete events
1
Modification events
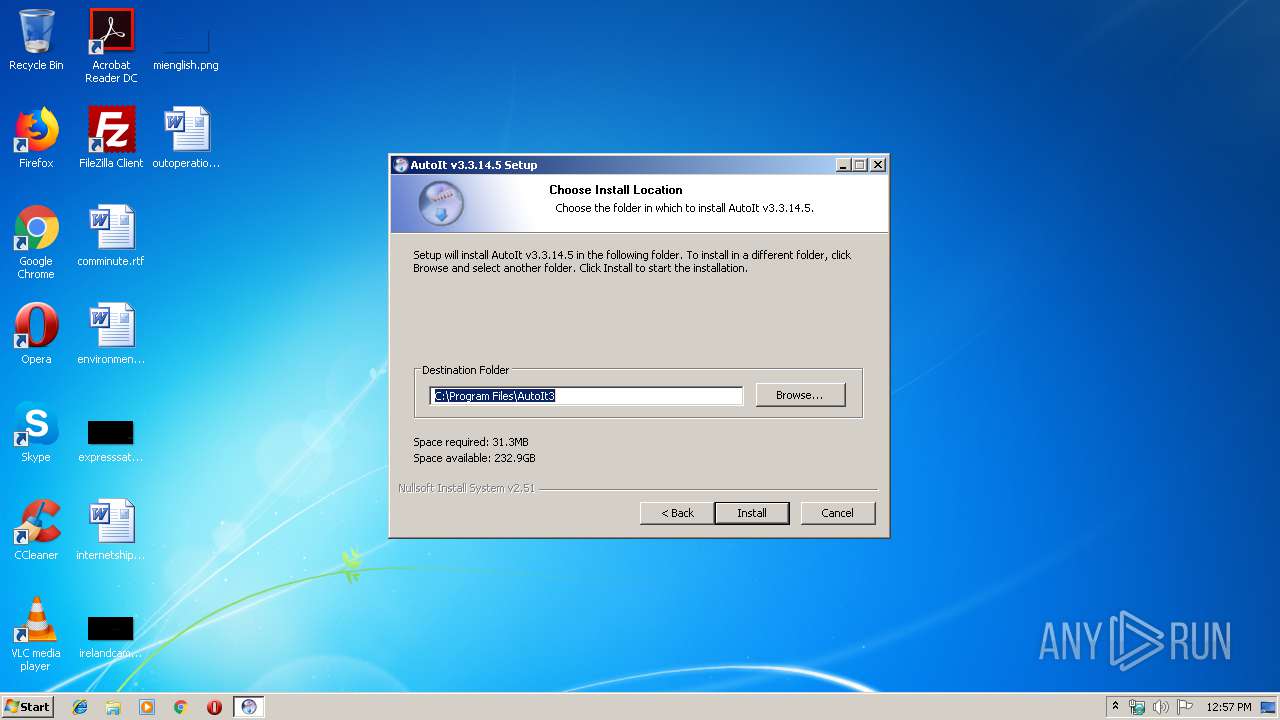
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AutoIt v3\AutoIt |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\AutoIt3 | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AutoIt v3\AutoIt |
| Operation: | write | Name: | Version |
Value: v3.3.14.5 | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.au3 |
| Operation: | write | Name: | PerceivedType |
Value: text | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.au3\PersistentHandler |
| Operation: | write | Name: | |
Value: {5e941d80-bf96-11cd-b579-08002b30bfeb} | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.au3 |
| Operation: | write | Name: | |
Value: AutoIt3Script | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.a3x |
| Operation: | write | Name: | |
Value: AutoIt3XScript | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.au3\ShellNew |
| Operation: | write | Name: | FileName |
Value: Template.au3 | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AutoIt3Script |
| Operation: | write | Name: | |
Value: AutoIt v3 Script | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AutoIt3Script\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\AutoIt3\Icons\au3script_v11.ico | |||
| (PID) Process: | (3988) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AutoIt3Script\Shell\Run |
| Operation: | write | Name: | |
Value: Run Script | |||
Executable files
20
Suspicious files
7
Text files
3 050
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\AutoIt.chm | — | |
MD5:— | SHA256:— | |||
| 3988 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsx153.tmp\ioDefaultOpen.ini | text | |
MD5:— | SHA256:— | |||
| 3988 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsx153.tmp\ioPreviousVersion.ini | text | |
MD5:— | SHA256:— | |||
| 3988 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsx153.tmp\ioX64Options.ini | text | |
MD5:— | SHA256:— | |||
| 3988 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsx153.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3988 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\Au3Info.exe | executable | |
MD5:0E74B9DC602E5C3540C3CE7E51C5717C | SHA256:CD7660502EE43FAB3E5AF883F21E2F03F78E462912CF14D23D105C3DE8E9D3CE | |||
| 3988 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\Au3Info_x64.exe | executable | |
MD5:600587FC345F0AAD0E69BA989DC92029 | SHA256:085F9631058901EF4CF75C3B683C833EDC46F0F57AB7CA274EDFBD6F79AAC13A | |||
| 3988 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\AutoIt3_x64.exe | executable | |
MD5:0C45B1AF9F410771BFD1740F40DC4173 | SHA256:3F1A80889FC13D98A26B8B6AC034D8FF4A04A5E3FE6C41C994585F5BA3E32BB2 | |||
| 3988 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsx153.tmp\UserInfo.dll | executable | |
MD5:E840E7F30C85E22B09A41098FF3F3343 | SHA256:6707E9E88DEC460C2CF421BD2BC6A314F15717527CB60DCAD2FBB7352AE711A3 | |||
| 3988 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsx153.tmp\modern-header.bmp | image | |
MD5:940C56737BF9BB69CE7A31C623D4E87A | SHA256:766A893FE962AEFD27C574CB05F25CF895D3FC70A00DB5A6FA73D573F571AEFC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report