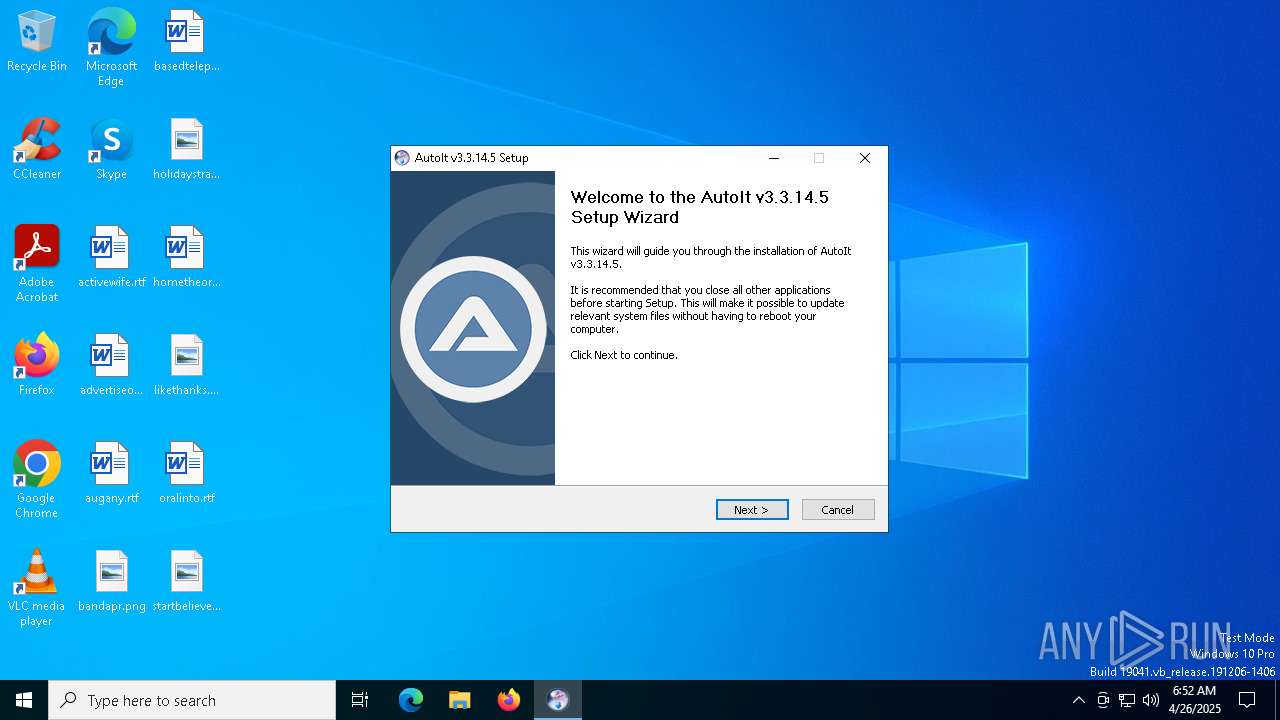
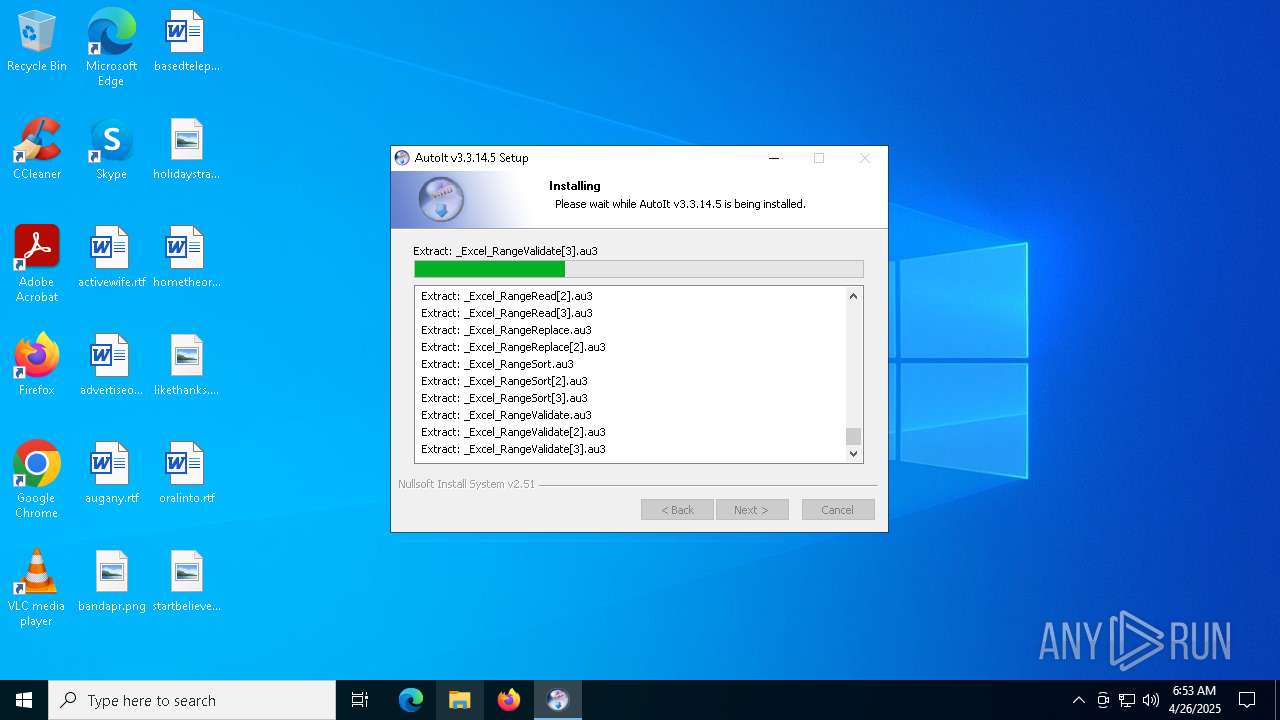
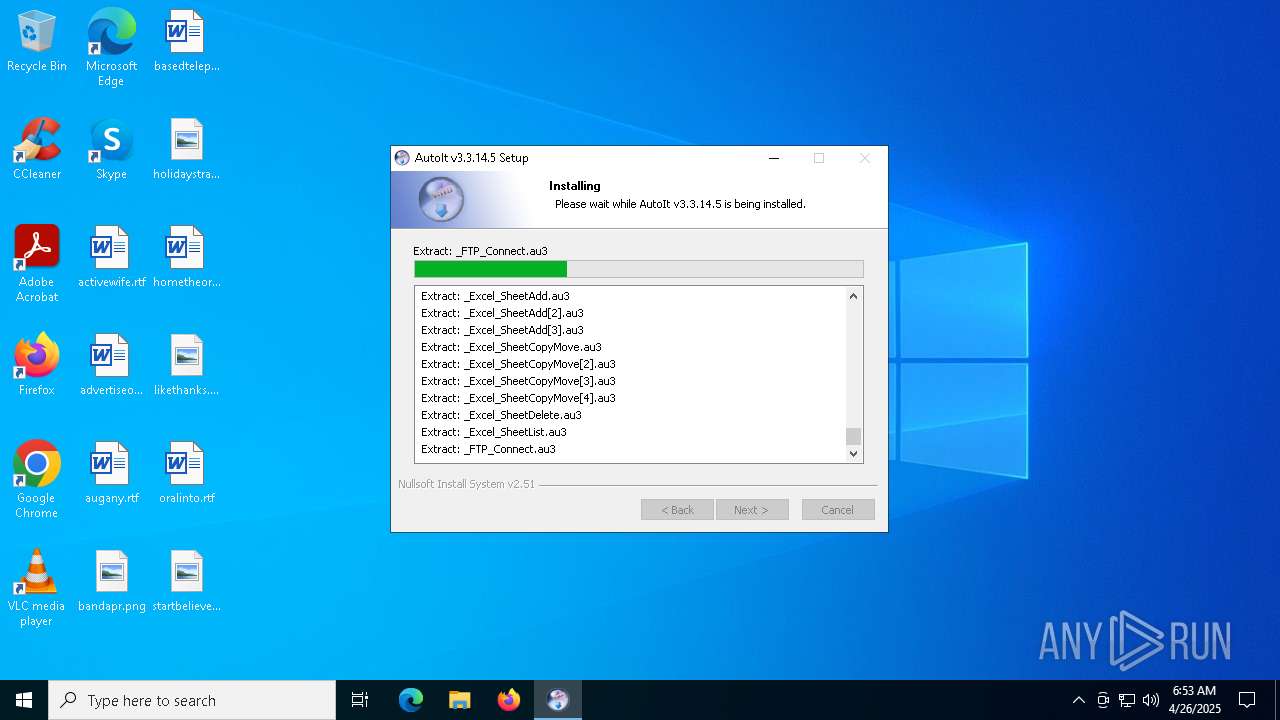
| File name: | autoit-v3-setup.exe |
| Full analysis: | https://app.any.run/tasks/4948d1c0-00c0-4d07-a657-6e2a815996cf |
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2025, 06:51:54 |
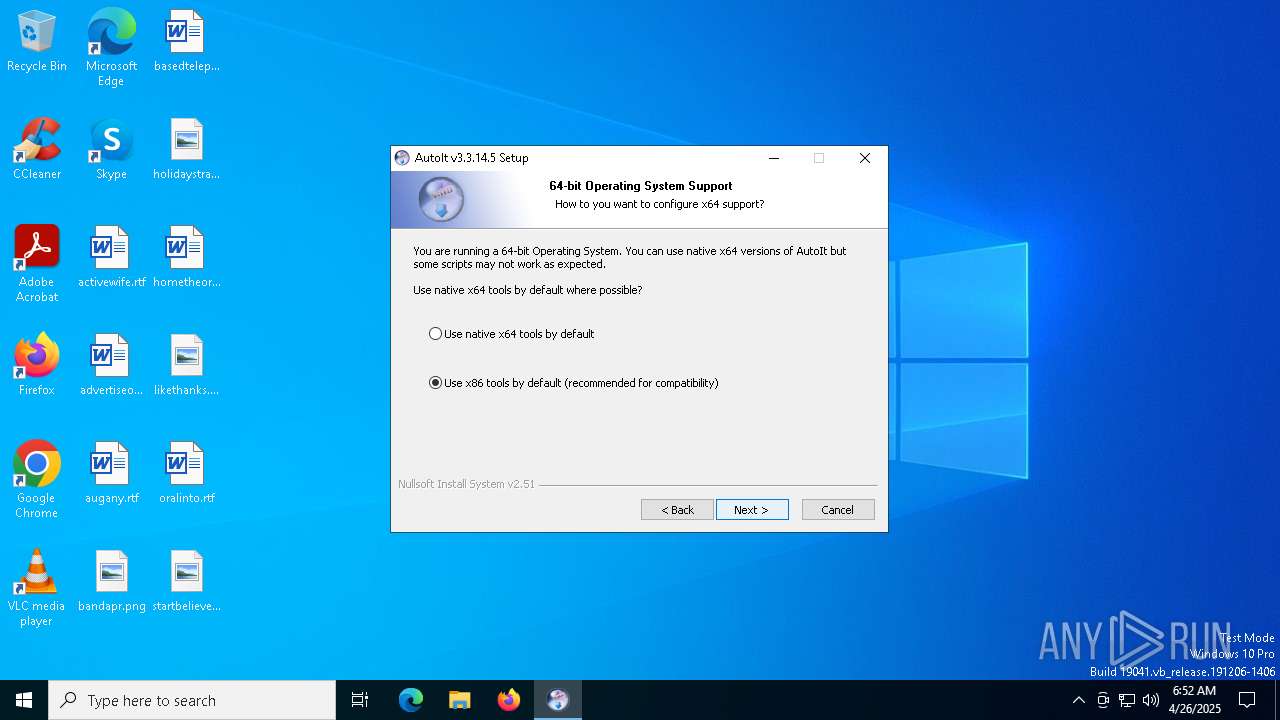
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
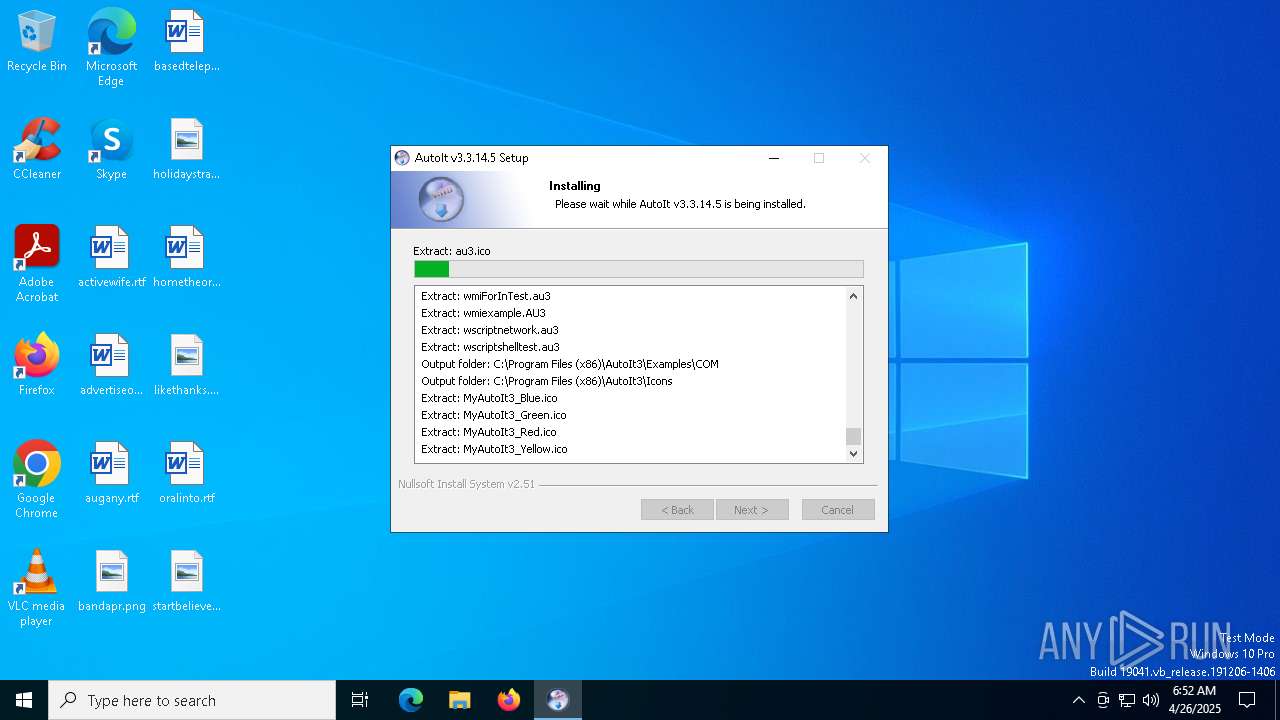
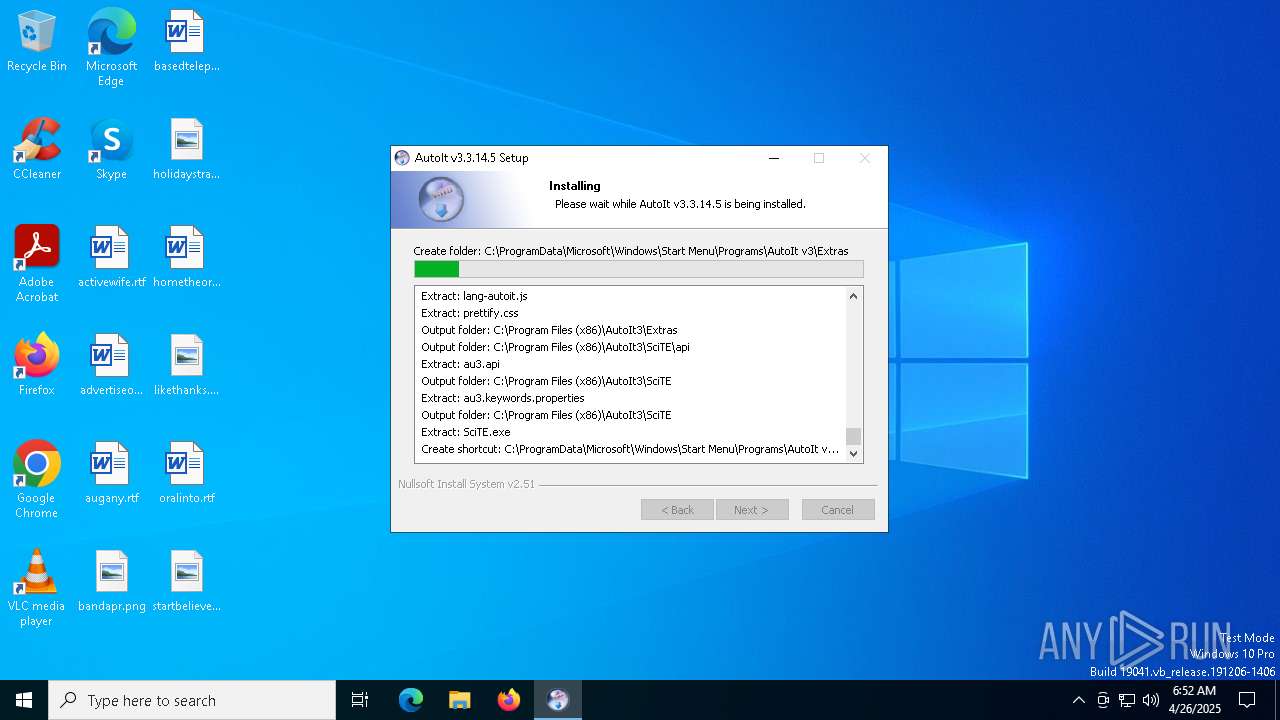
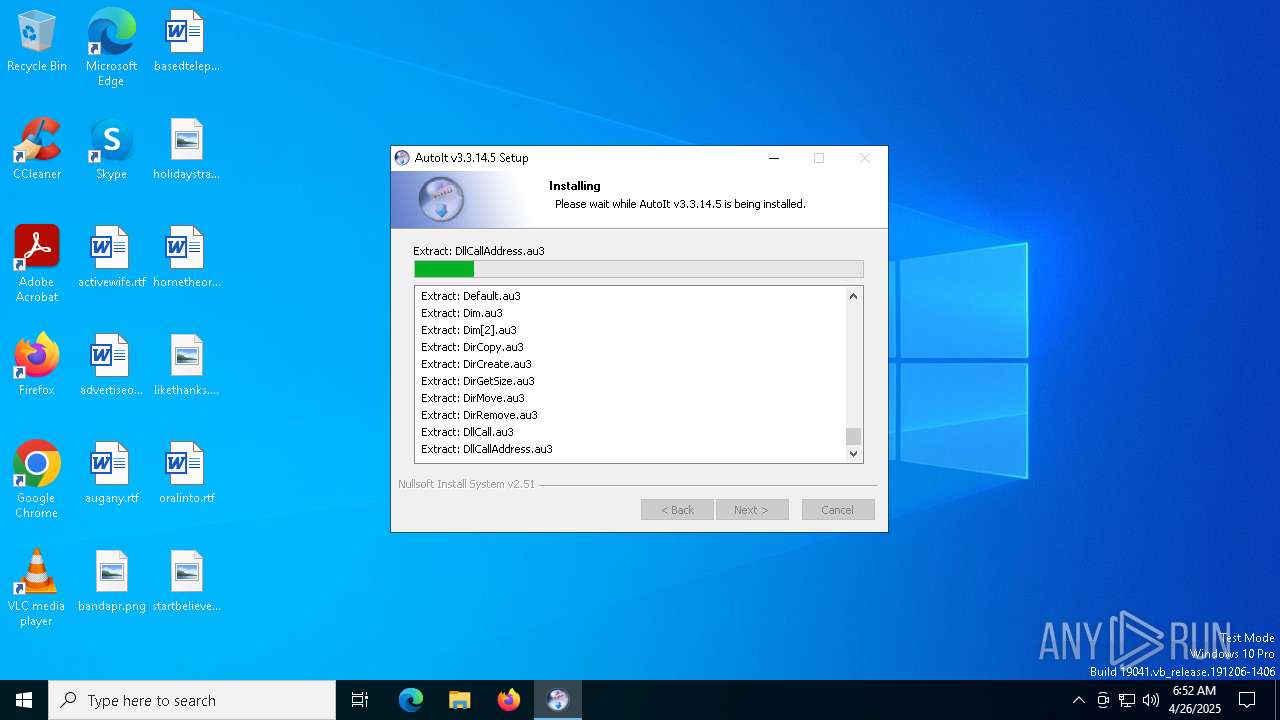
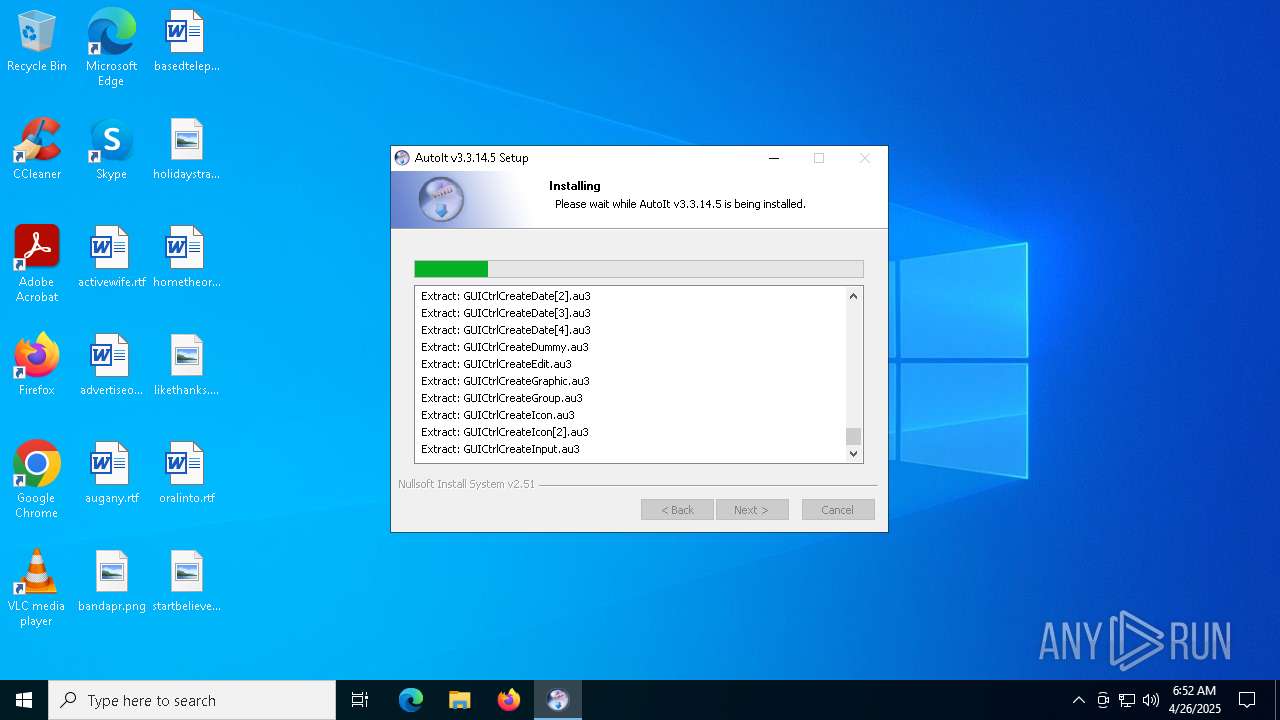
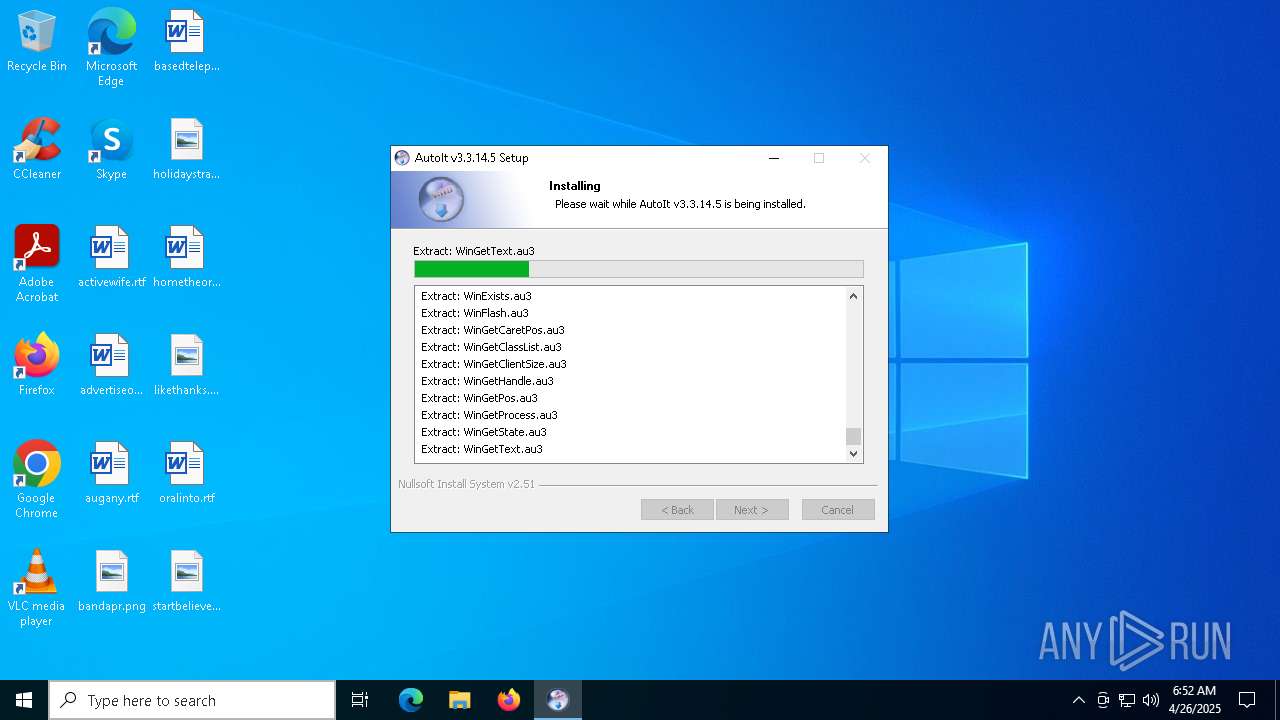
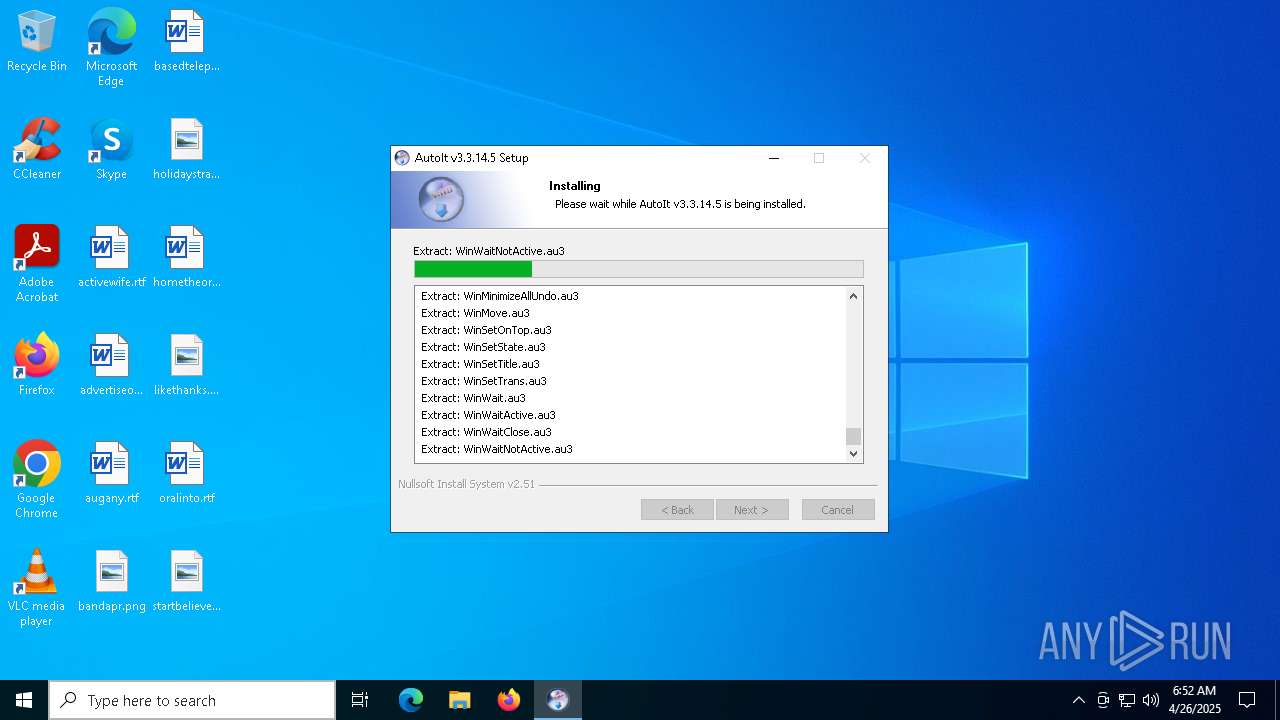
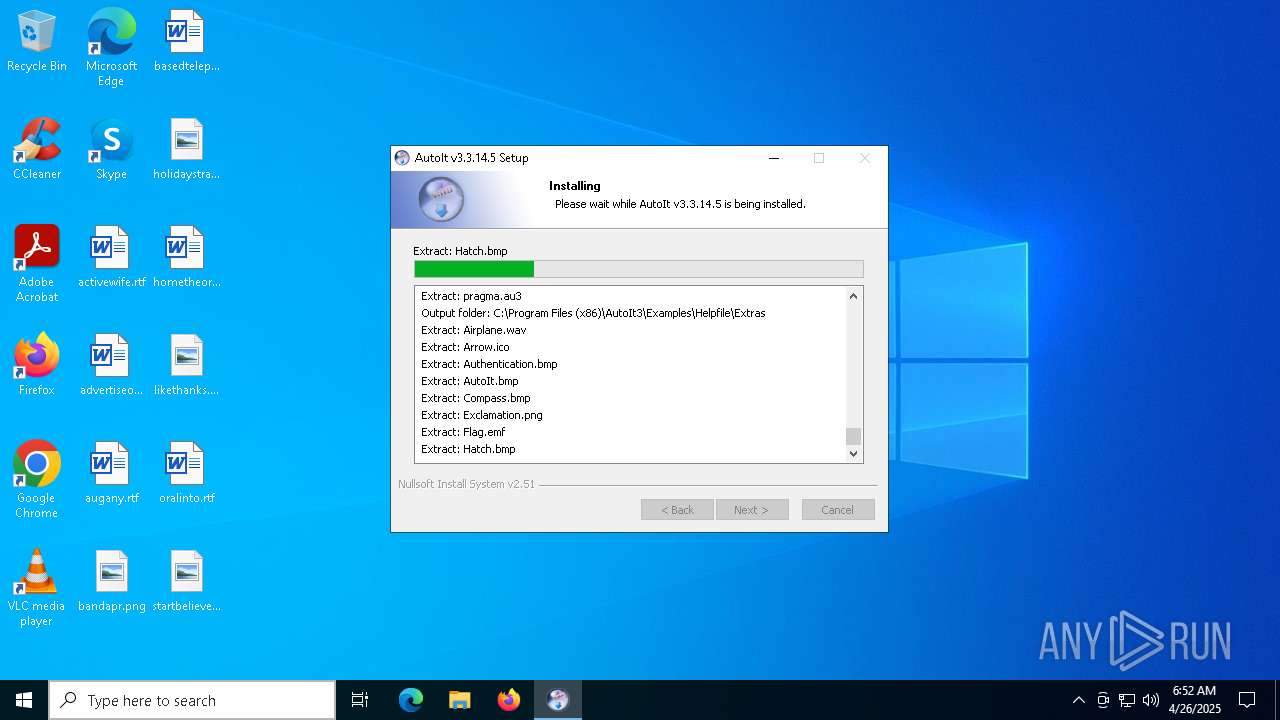
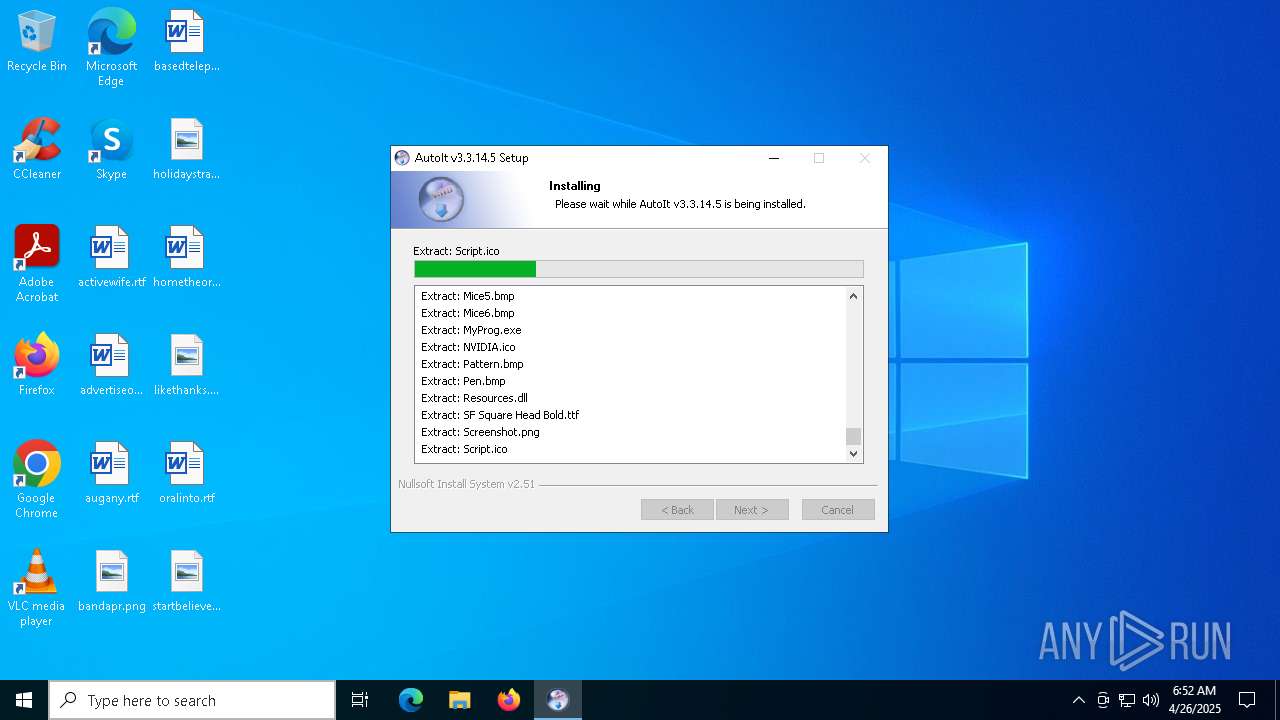
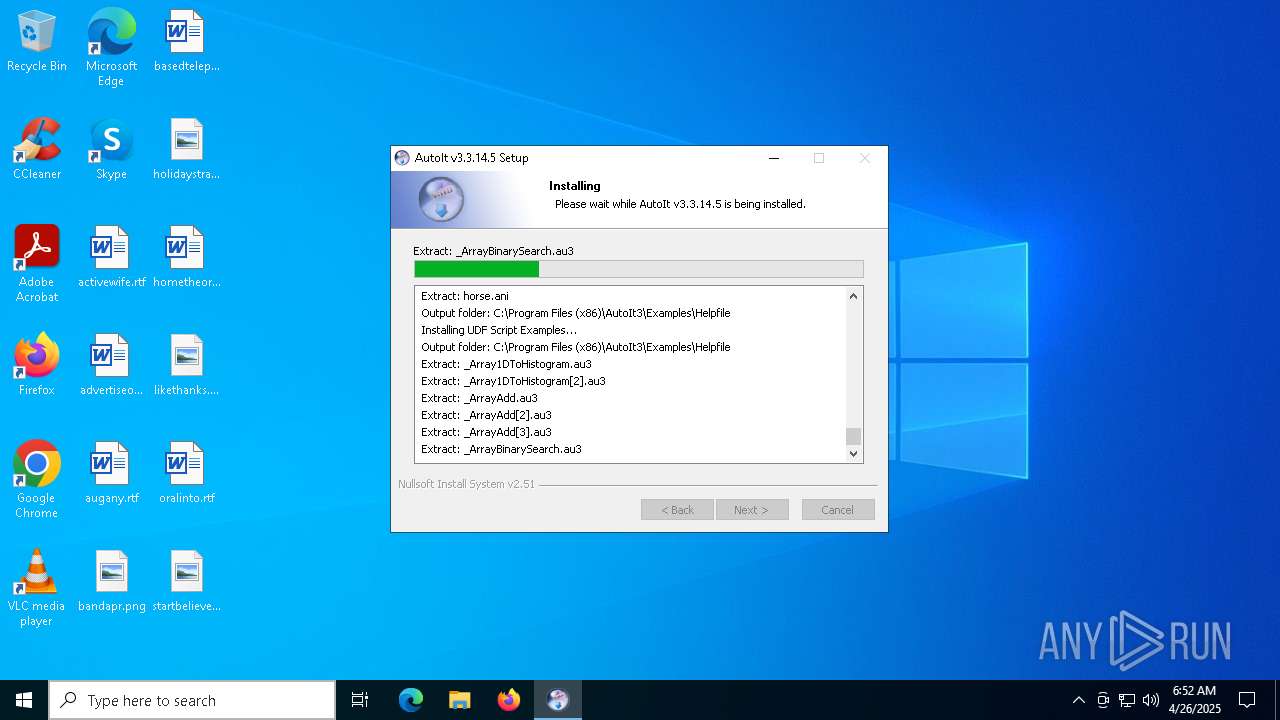
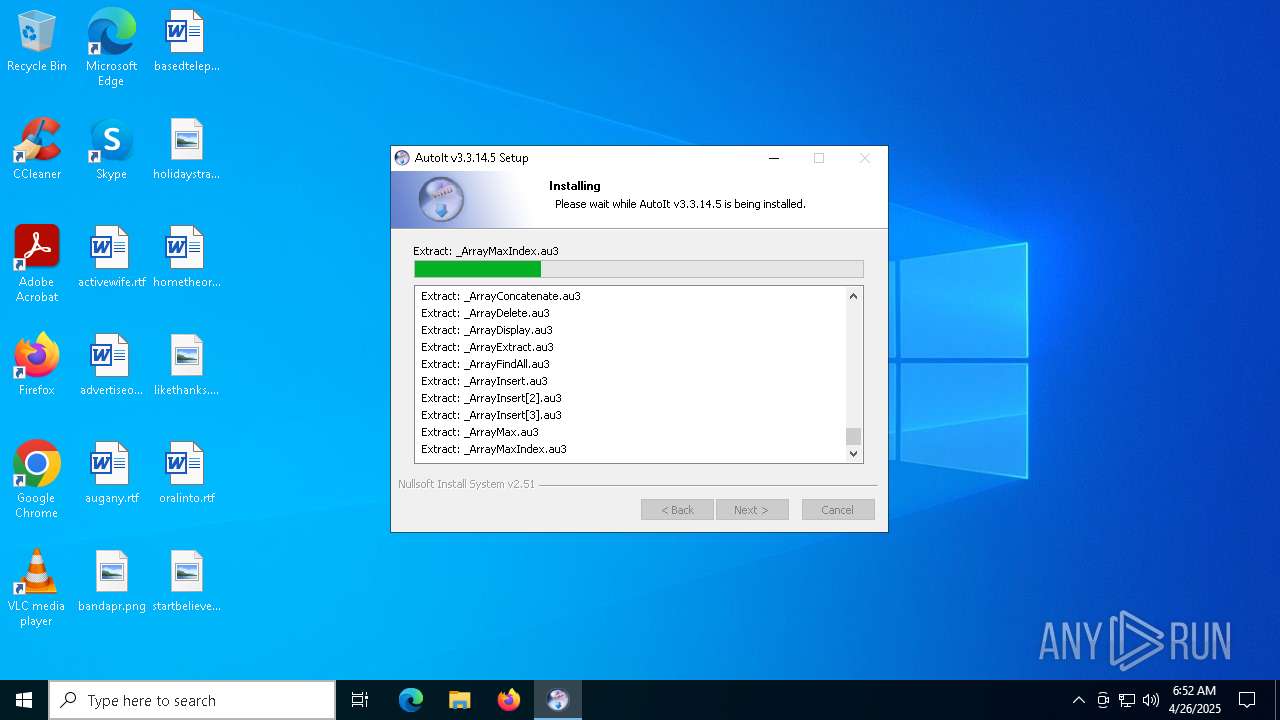
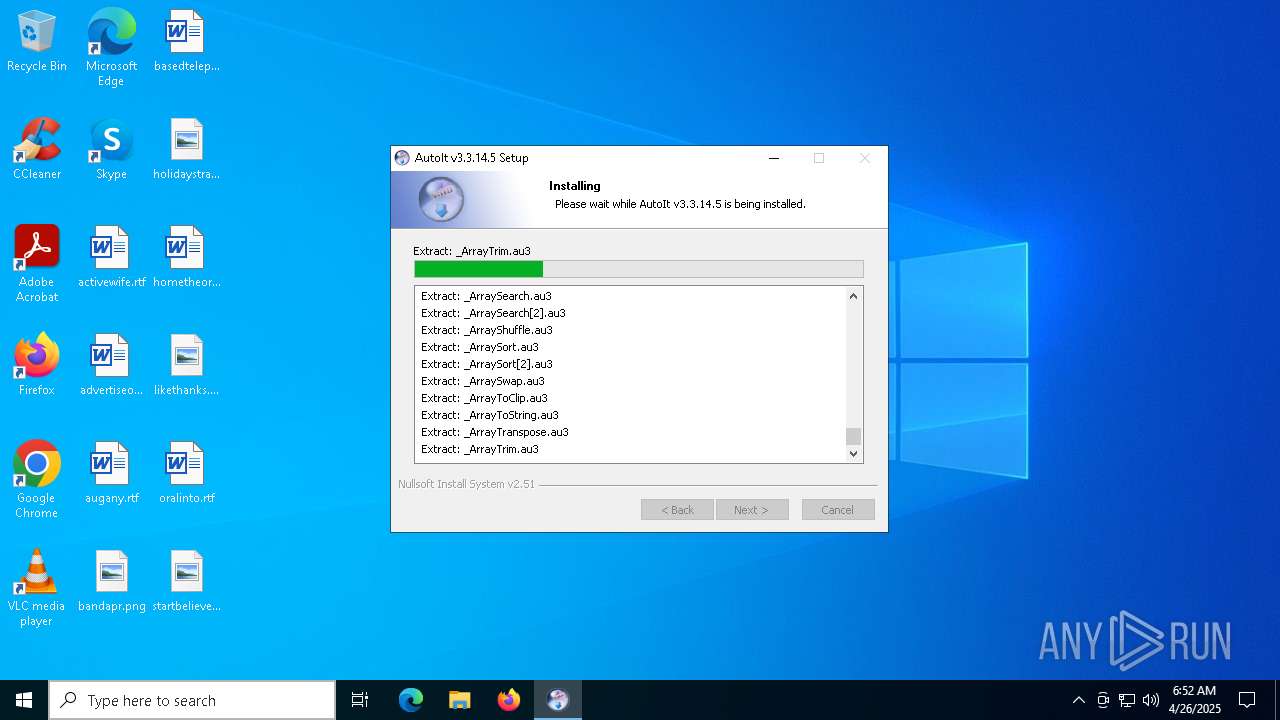
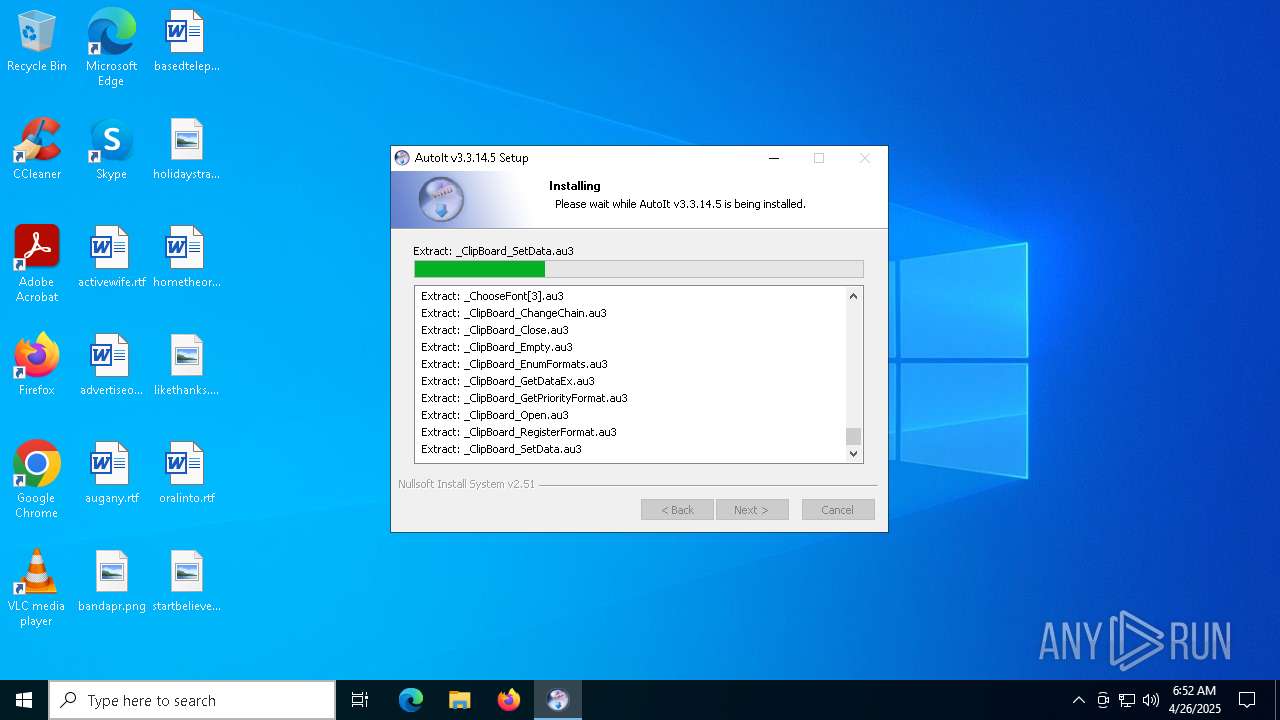
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | D50D5712566F1DF16B5AEA21B9E0EE24 |
| SHA1: | F442AA68EC8D838625F382BCF273F5D0F66427EA |
| SHA256: | E102238100A8B97D22559065E3B19379757AEDA932C36916D2C84A4178921854 |
| SSDEEP: | 196608:RibMxSfOYFjizV+mKPdih/DuHKaJC9vdGFMiEXxHeJtMvU9Bi7SkEGIT9OOa5SPl:3xgjihkUhKHKr0M19lSBi7S02OOagDOe |
MALICIOUS
No malicious indicators.SUSPICIOUS
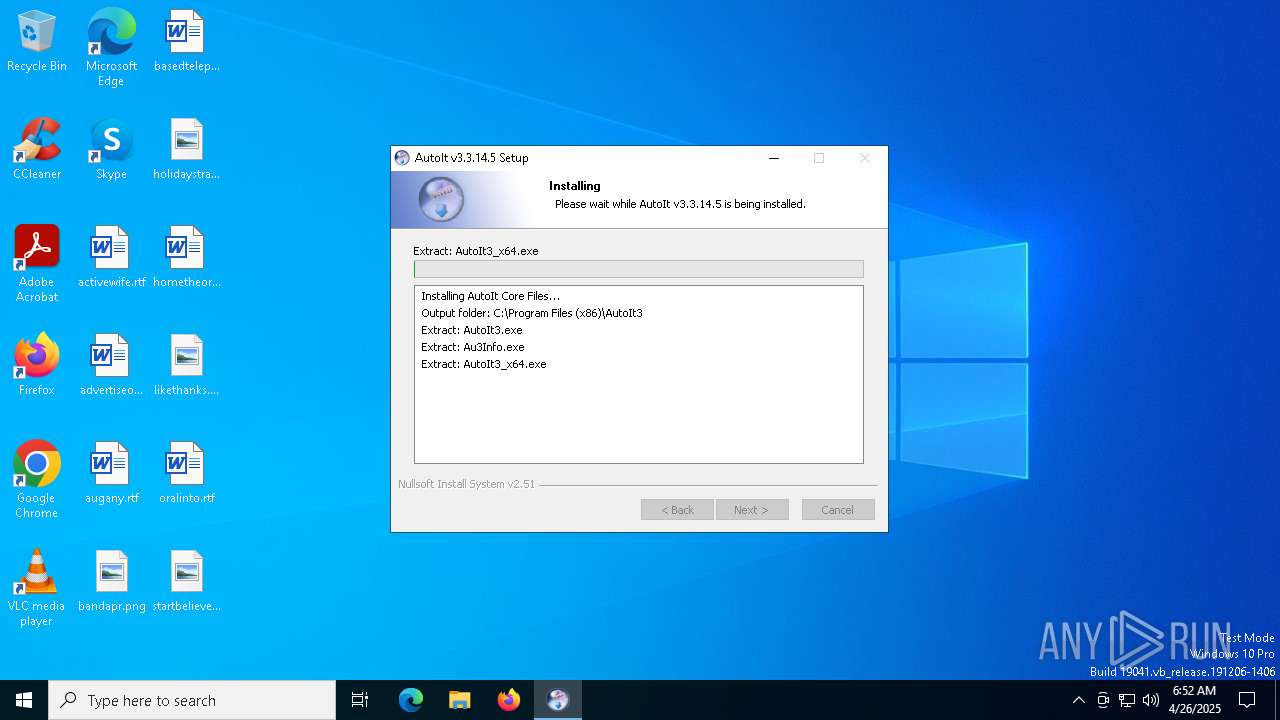
Executable content was dropped or overwritten
- autoit-v3-setup.exe (PID: 7428)
There is functionality for taking screenshot (YARA)
- autoit-v3-setup.exe (PID: 7428)
Creates a software uninstall entry
- autoit-v3-setup.exe (PID: 7428)
The process creates files with name similar to system file names
- autoit-v3-setup.exe (PID: 7428)
Malware-specific behavior (creating "System.dll" in Temp)
- autoit-v3-setup.exe (PID: 7428)
Creates/Modifies COM task schedule object
- autoit-v3-setup.exe (PID: 7428)
INFO
Reads the computer name
- autoit-v3-setup.exe (PID: 7428)
Create files in a temporary directory
- autoit-v3-setup.exe (PID: 7428)
Creates files in the program directory
- autoit-v3-setup.exe (PID: 7428)
The sample compiled with german language support
- autoit-v3-setup.exe (PID: 7428)
The sample compiled with english language support
- autoit-v3-setup.exe (PID: 7428)
Checks supported languages
- autoit-v3-setup.exe (PID: 7428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 03:20:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x326c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.14.5 |
| ProductVersionNumber: | 3.3.14.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
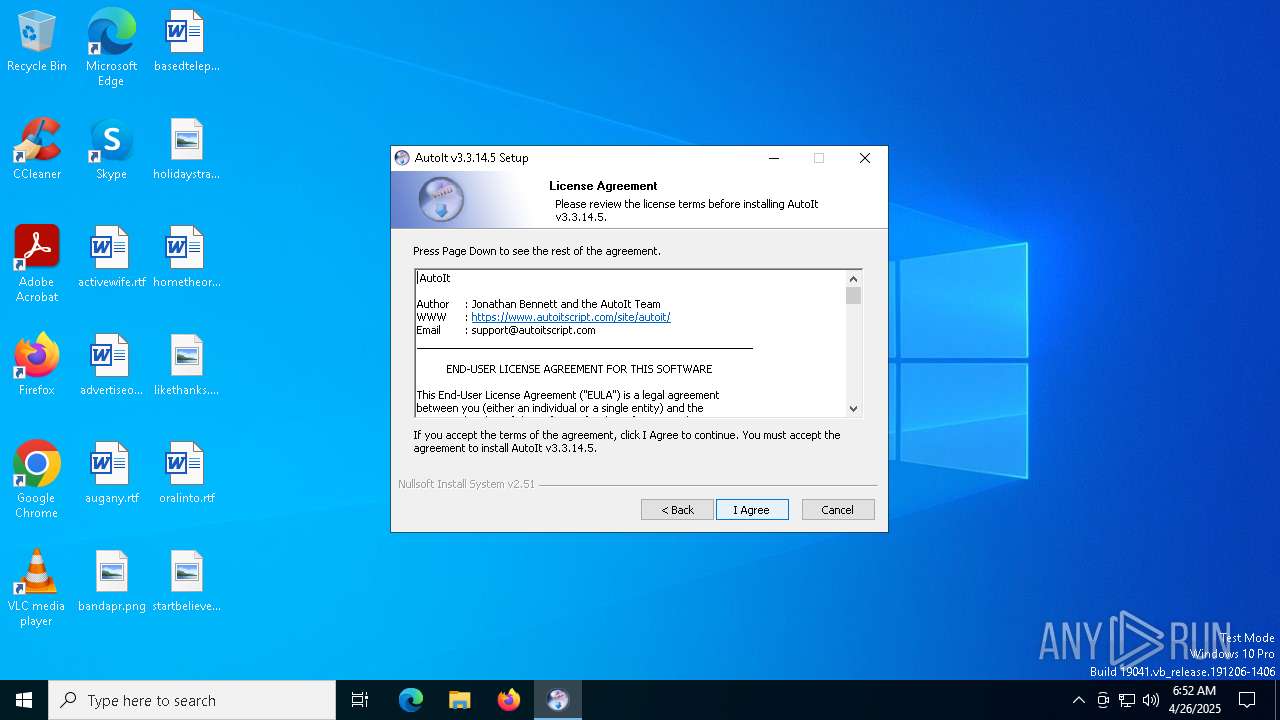
| CompanyName: | AutoIt Team |
| FileDescription: | AutoIt v3 Setup |
| FileVersion: | 3.3.14.5 |
| LegalCopyright: | (c)1999-2018 Jonathan Bennett & AutoIt Team |
Total processes
133
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7368 | "C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe" | C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Setup Exit code: 3221226540 Version: 3.3.14.5 Modules
| |||||||||||||||
| 7428 | "C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe" | C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: HIGH Description: AutoIt v3 Setup Version: 3.3.14.5 Modules
| |||||||||||||||
| 7476 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7508 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
407
Read events
382
Write events
25
Delete events
0
Modification events
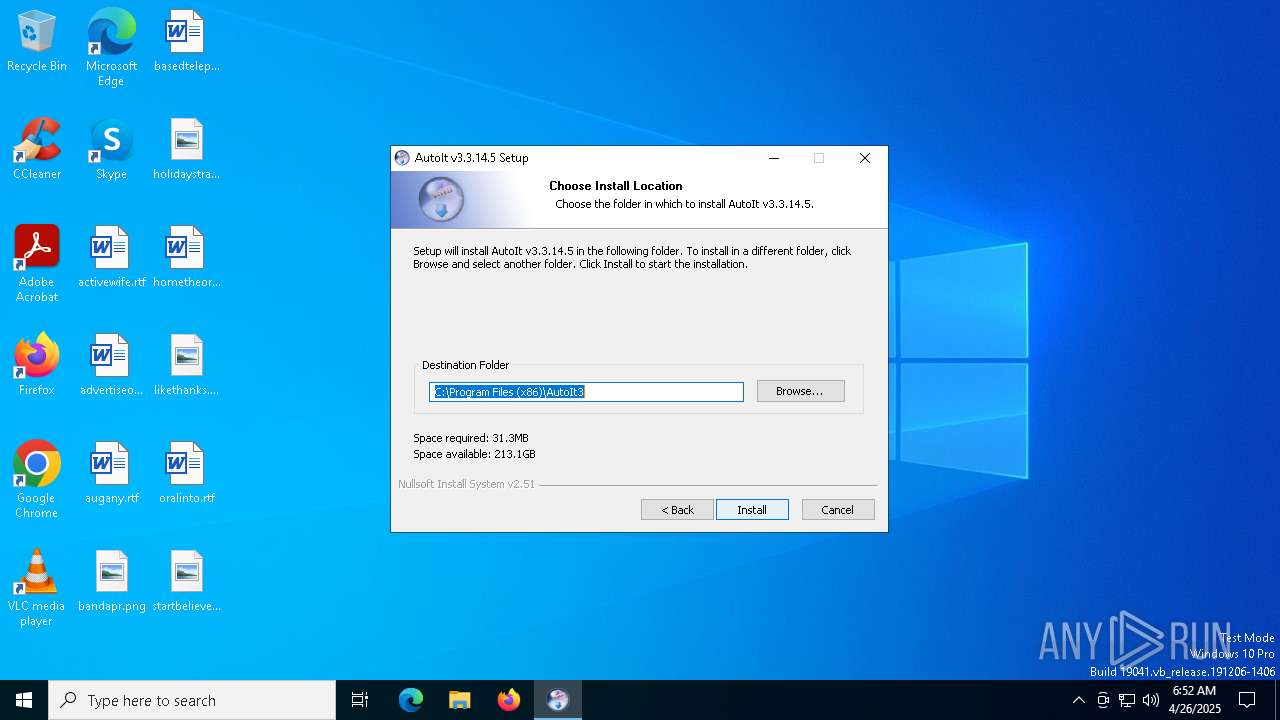
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\AutoIt v3\AutoIt |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files (x86)\AutoIt3 | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\AutoIt v3\AutoIt |
| Operation: | write | Name: | Version |
Value: v3.3.14.5 | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.au3 |
| Operation: | write | Name: | PerceivedType |
Value: text | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.au3\ShellNew |
| Operation: | write | Name: | FileName |
Value: Template.au3 | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastExeDir |
Value: My Documents | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastScriptDir |
Value: My Documents | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastIconDir |
Value: C:\Program Files (x86)\AutoIt3\Aut2Exe\Icons | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastIcon |
Value: | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastCompression |
Value: 2 | |||
| (PID) Process: | (7428) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | AllowDecompile |
Value: 1 | |||
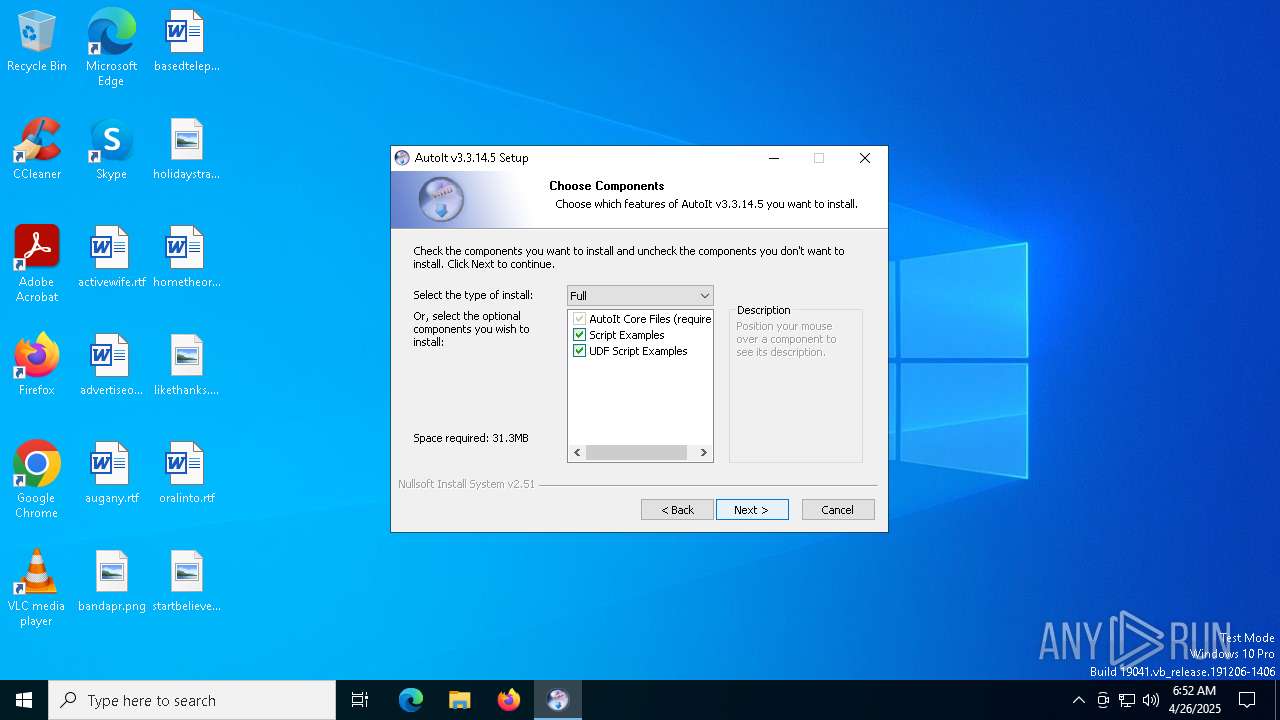
Executable files
24
Suspicious files
36
Text files
1 024
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7428 | autoit-v3-setup.exe | C:\Program Files (x86)\AutoIt3\AutoIt.chm | — | |
MD5:— | SHA256:— | |||
| 7428 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nswBB16.tmp\System.dll | executable | |
MD5:56A321BD011112EC5D8A32B2F6FD3231 | SHA256:BB6DF93369B498EAA638B0BCDC4BB89F45E9B02CA12D28BCEDF4629EA7F5E0F1 | |||
| 7428 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nswBB16.tmp\ioPreviousVersion.ini | text | |
MD5:8C032D104411DA01E43D8E8B9AD88EB4 | SHA256:659CAD01FE631A96E0856C44D4114E12AC0E5402F863C2B1213A87D375C26F59 | |||
| 7428 | autoit-v3-setup.exe | C:\Program Files (x86)\AutoIt3\AutoIt3.exe | executable | |
MD5:C56B5F0201A3B3DE53E561FE76912BFD | SHA256:237D1BCA6E056DF5BB16A1216A434634109478F882D3B1D58344C801D184F95D | |||
| 7428 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nswBB16.tmp\ioSpecial.ini | text | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 7428 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nswBB16.tmp\InstallOptions.dll | executable | |
MD5:D753362649AECD60FF434ADF171A4E7F | SHA256:8F24C6CF0B06D18F3C07E7BFCA4E92AFCE71834663746CFAA9DDF52A25D5C586 | |||
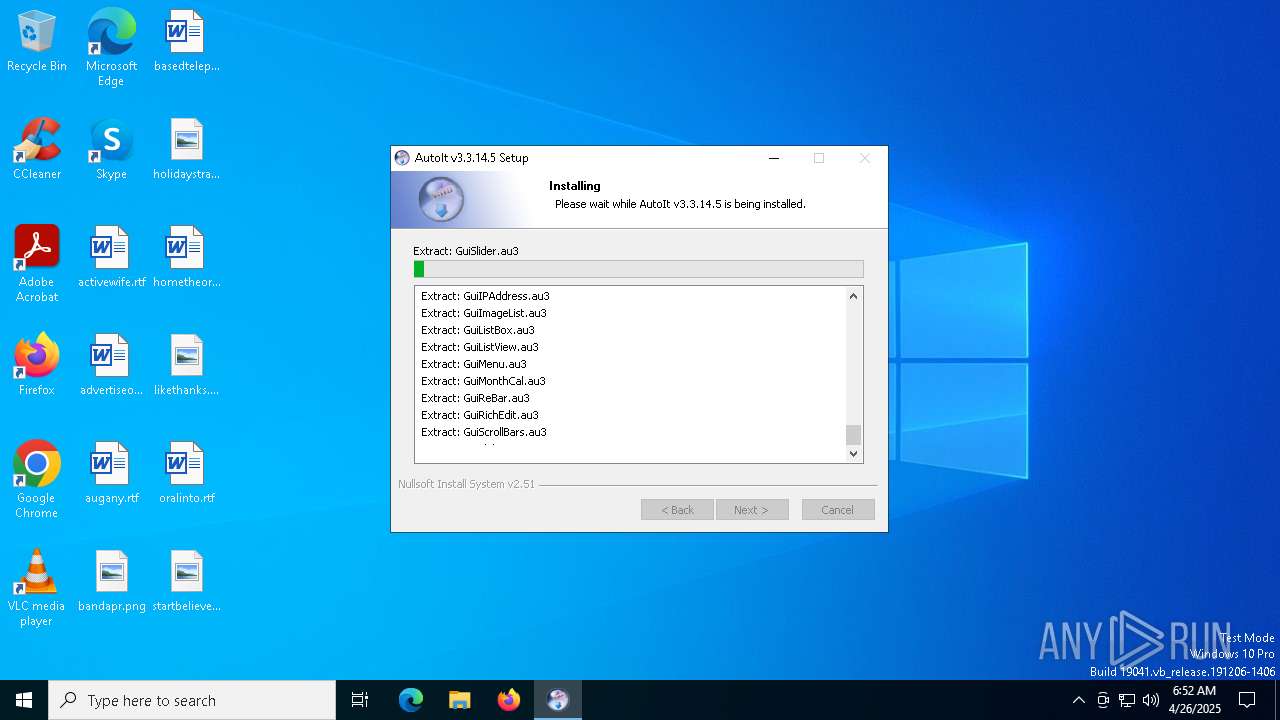
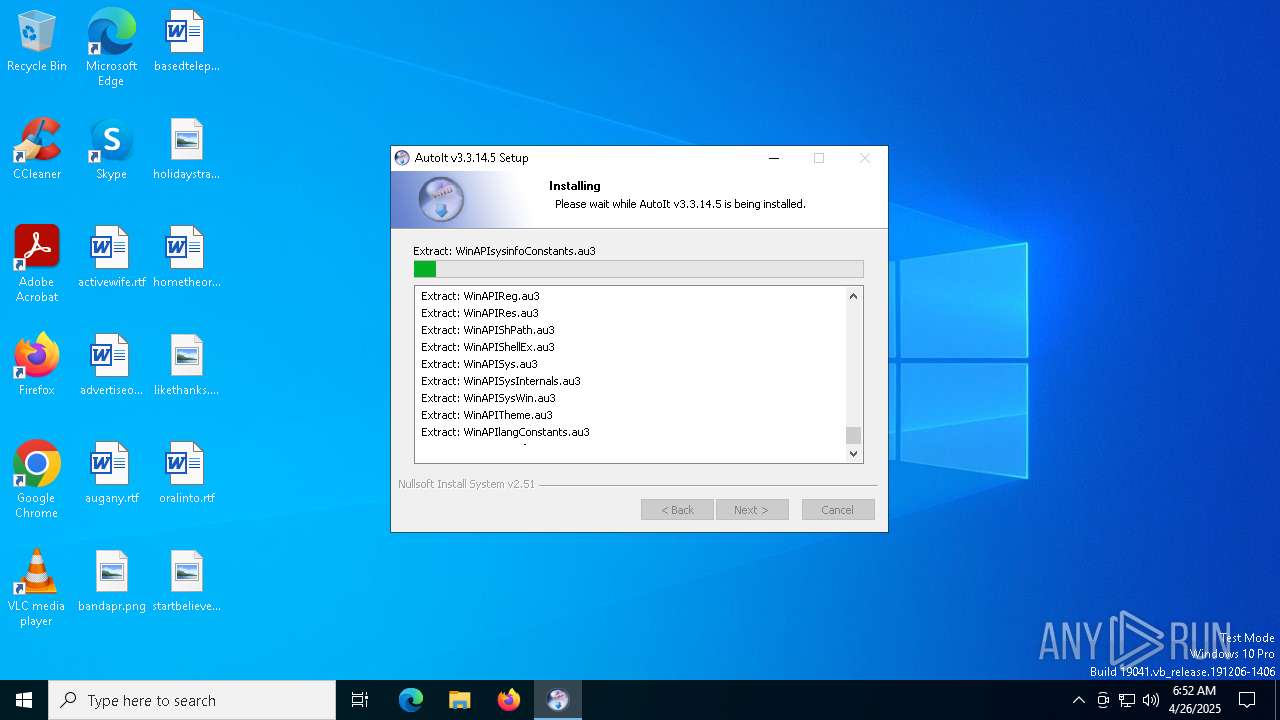
| 7428 | autoit-v3-setup.exe | C:\Program Files (x86)\AutoIt3\Include\APIComConstants.au3 | text | |
MD5:2FFBA31B7301A02079993CFE9933E55E | SHA256:080DBC5CD1F12AF1E3DEBF0AAB0C282A43767D88E5097C83F0DB97B5F9E8A266 | |||
| 7428 | autoit-v3-setup.exe | C:\Program Files (x86)\AutoIt3\AutoIt v3 Website.url | binary | |
MD5:7B6871AD1DE81E0201386EEB8A71498F | SHA256:A8697C79934FF08407412D2C0C0492217709841638F1FD7FC6D8A68C105EED0B | |||
| 7428 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nswBB16.tmp\UserInfo.dll | executable | |
MD5:E840E7F30C85E22B09A41098FF3F3343 | SHA256:6707E9E88DEC460C2CF421BD2BC6A314F15717527CB60DCAD2FBB7352AE711A3 | |||
| 7428 | autoit-v3-setup.exe | C:\Program Files (x86)\AutoIt3\Include\APIErrorsConstants.au3 | text | |
MD5:7385CF721E87FAE7918568FBC9BE36DF | SHA256:1AD04A034FDC59A80585A76B830C572CF9FF73479F2864DCD1AD184CA2ABA484 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
19
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8012 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8012 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |