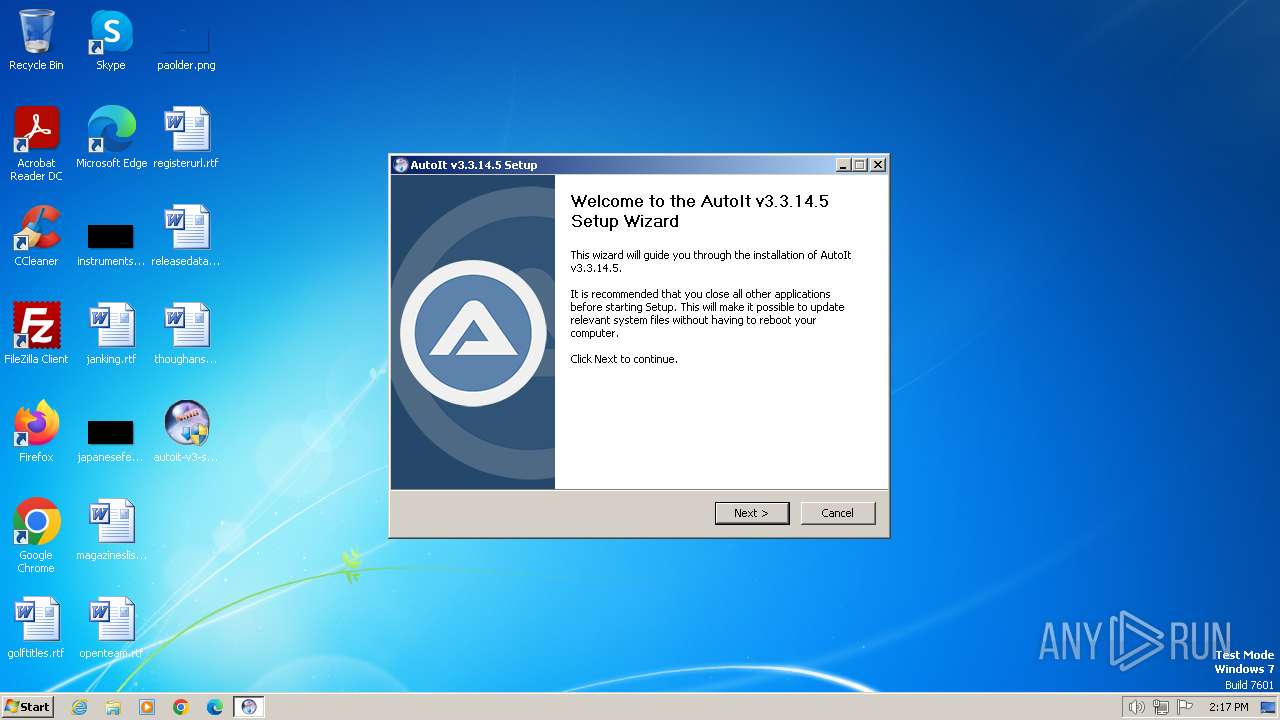
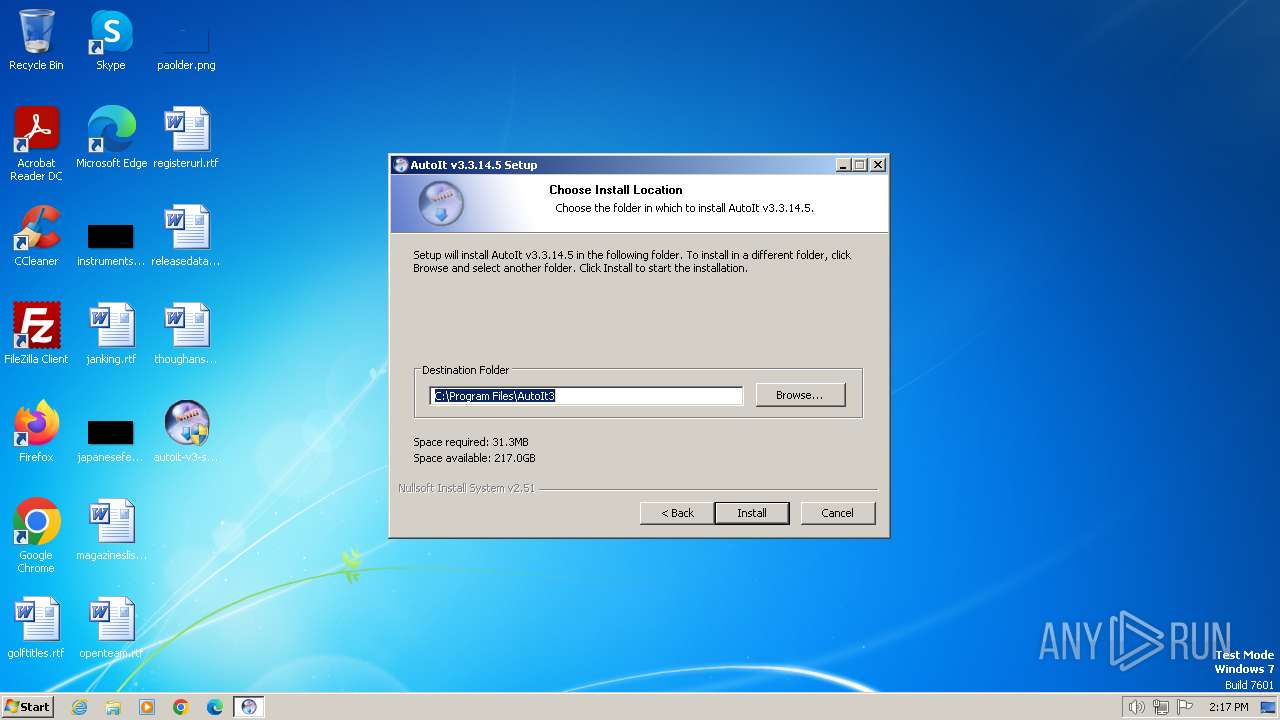
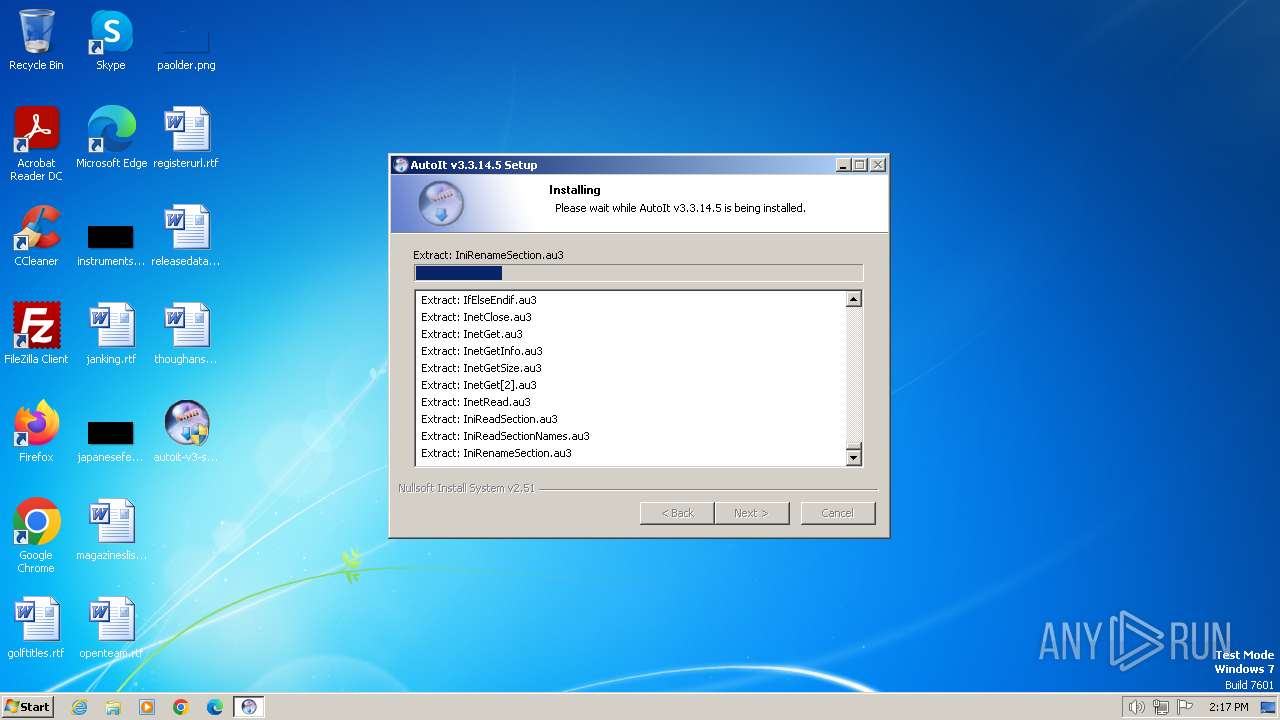
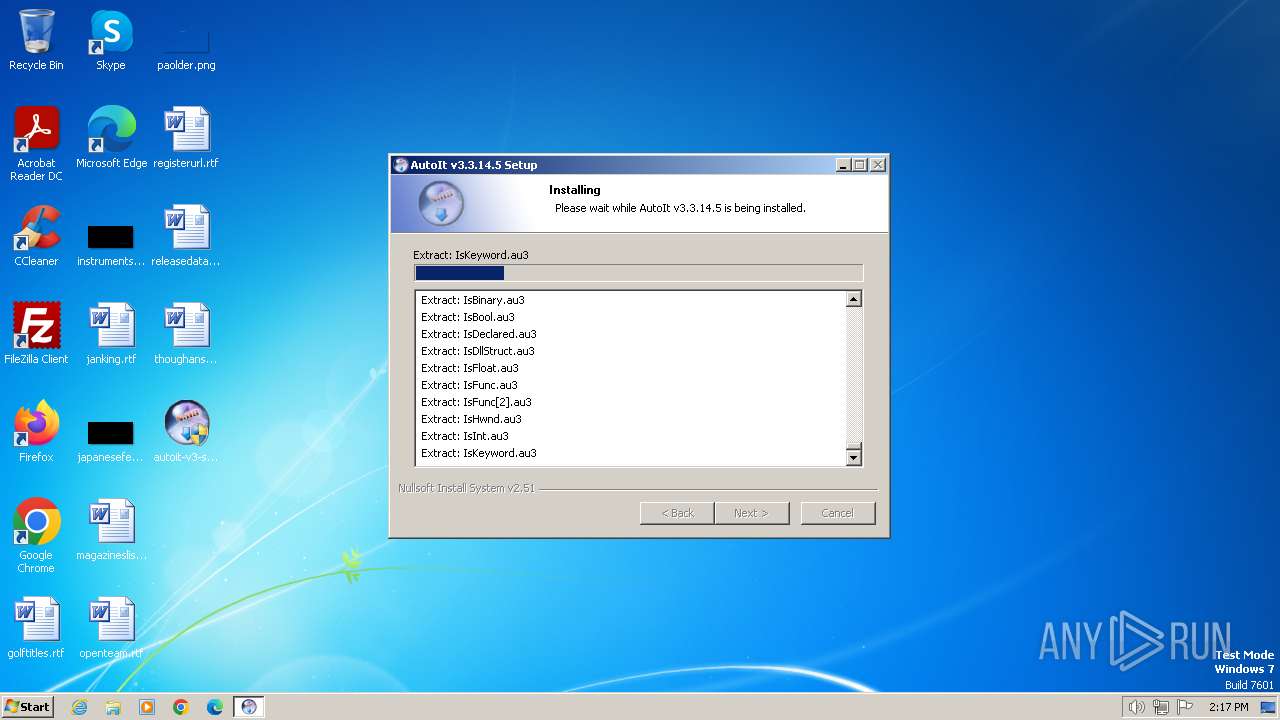
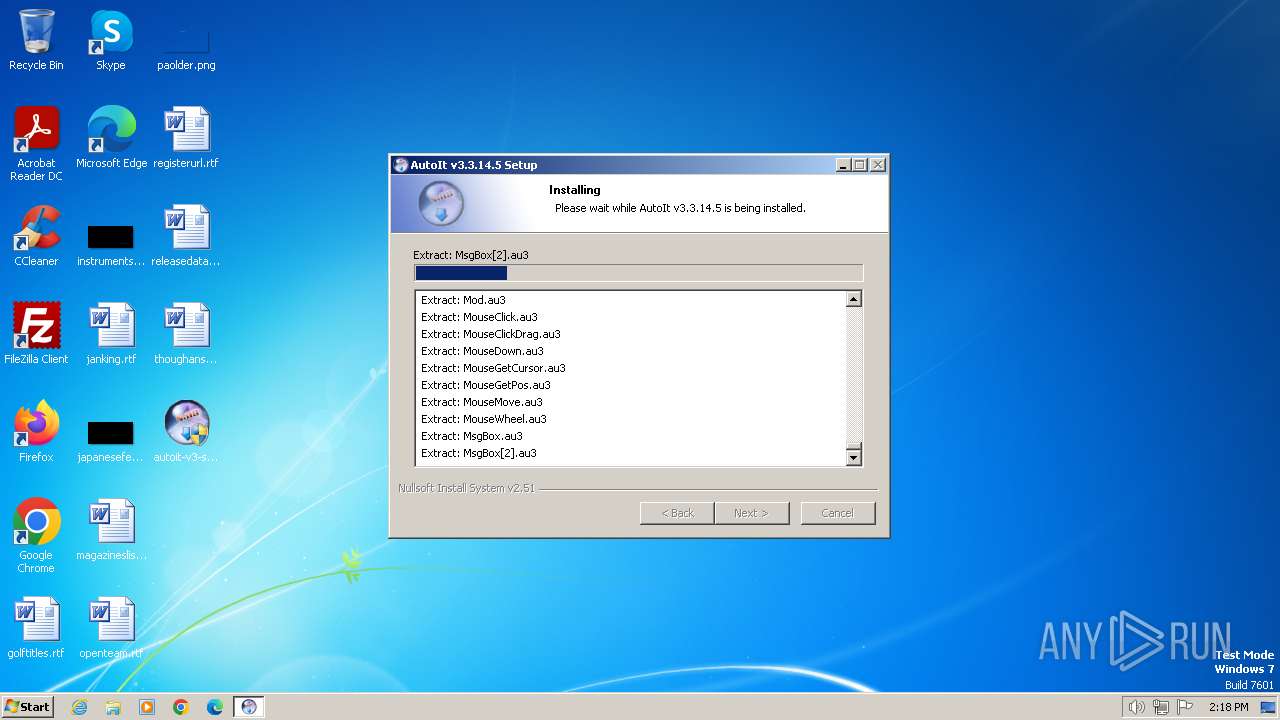
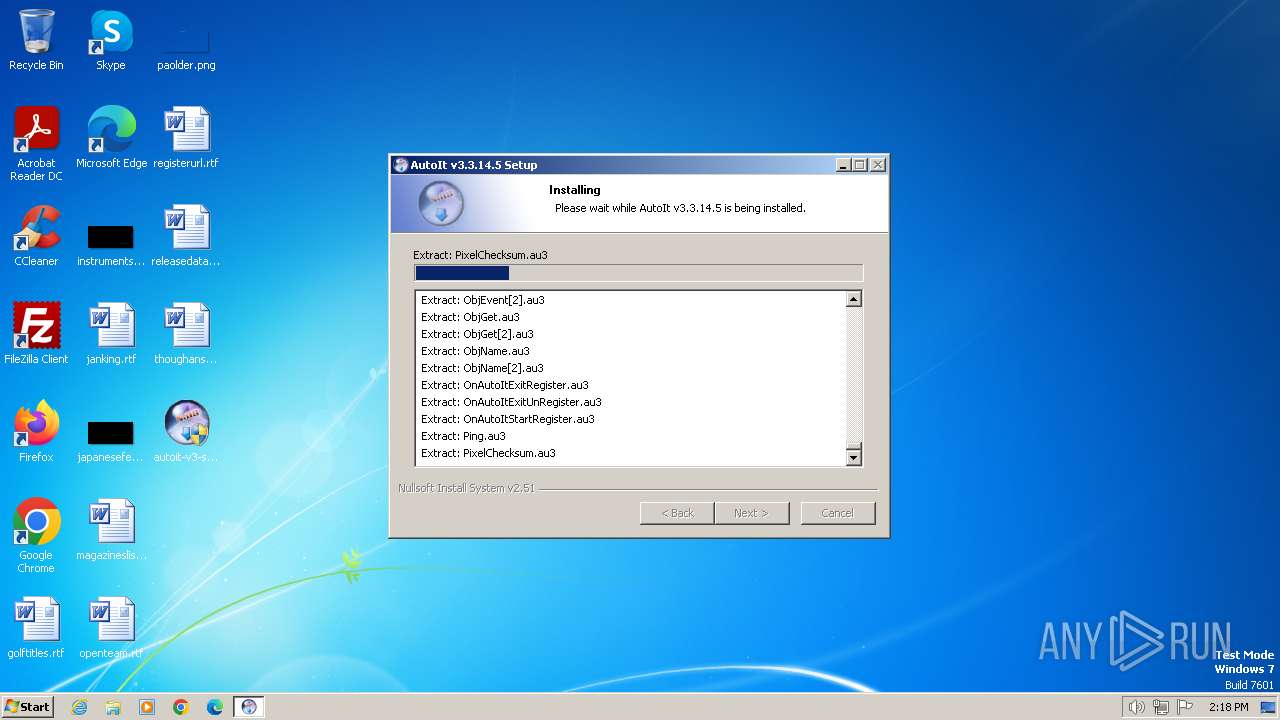
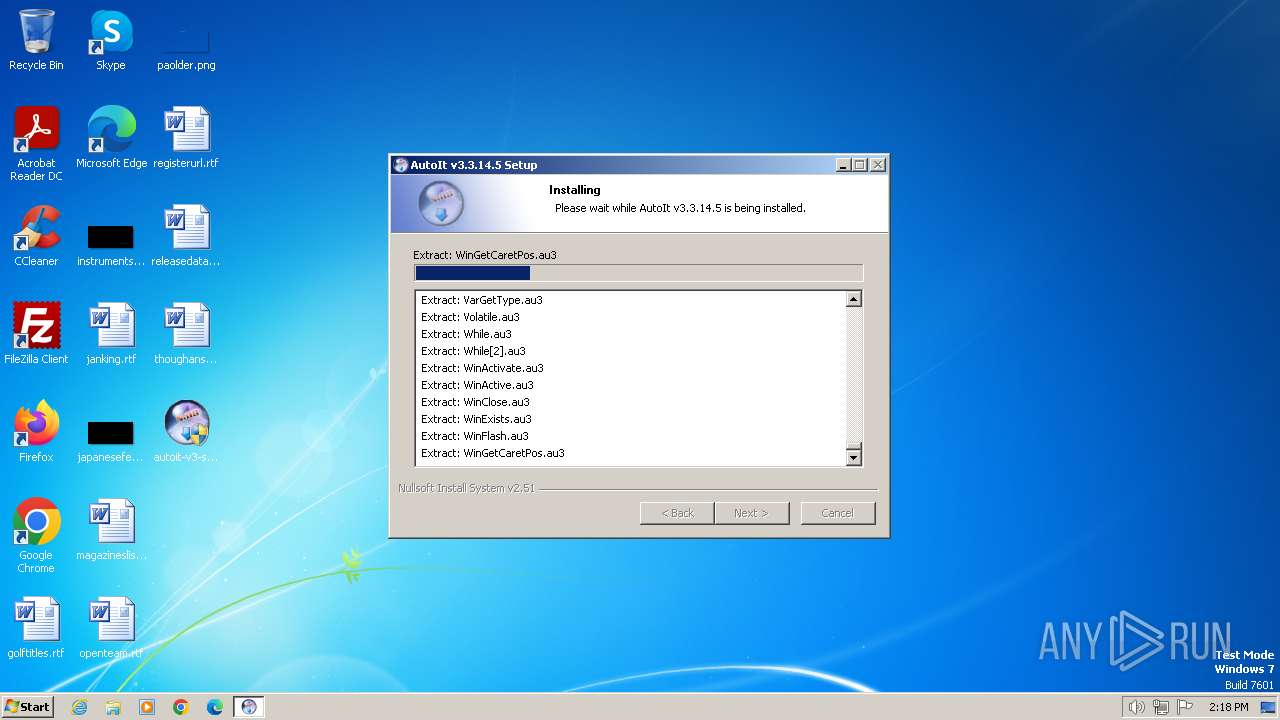
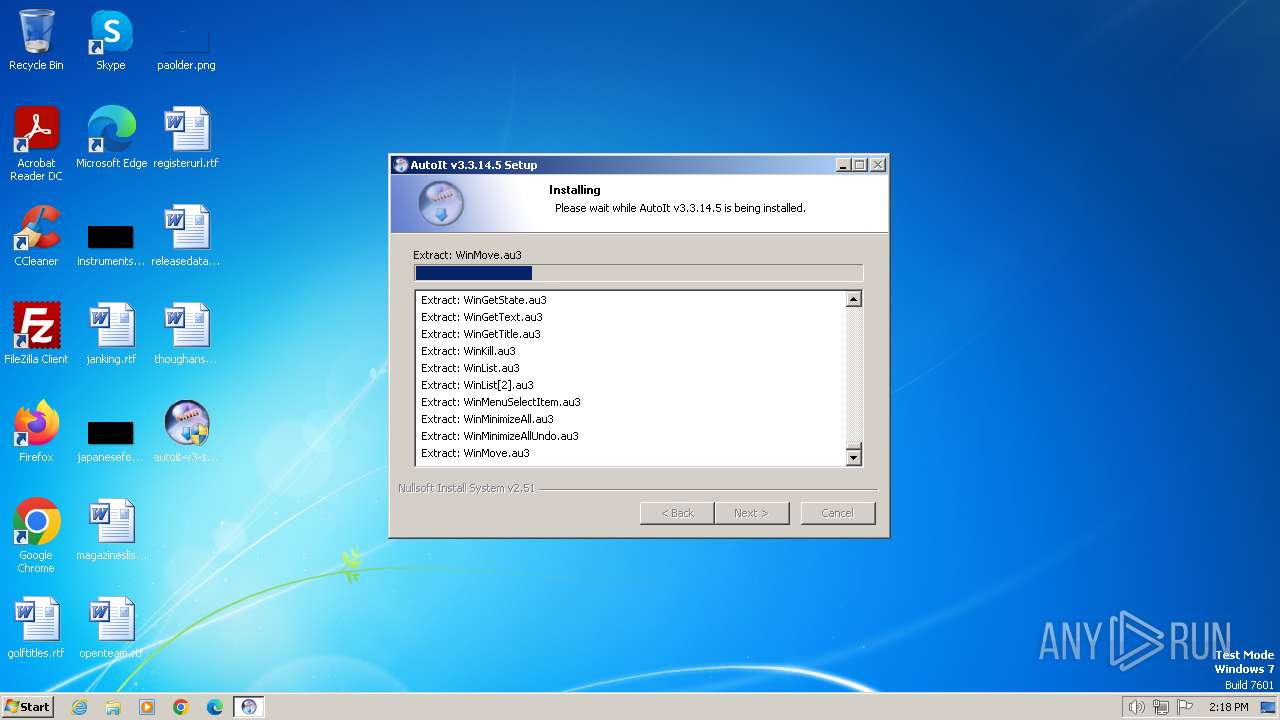
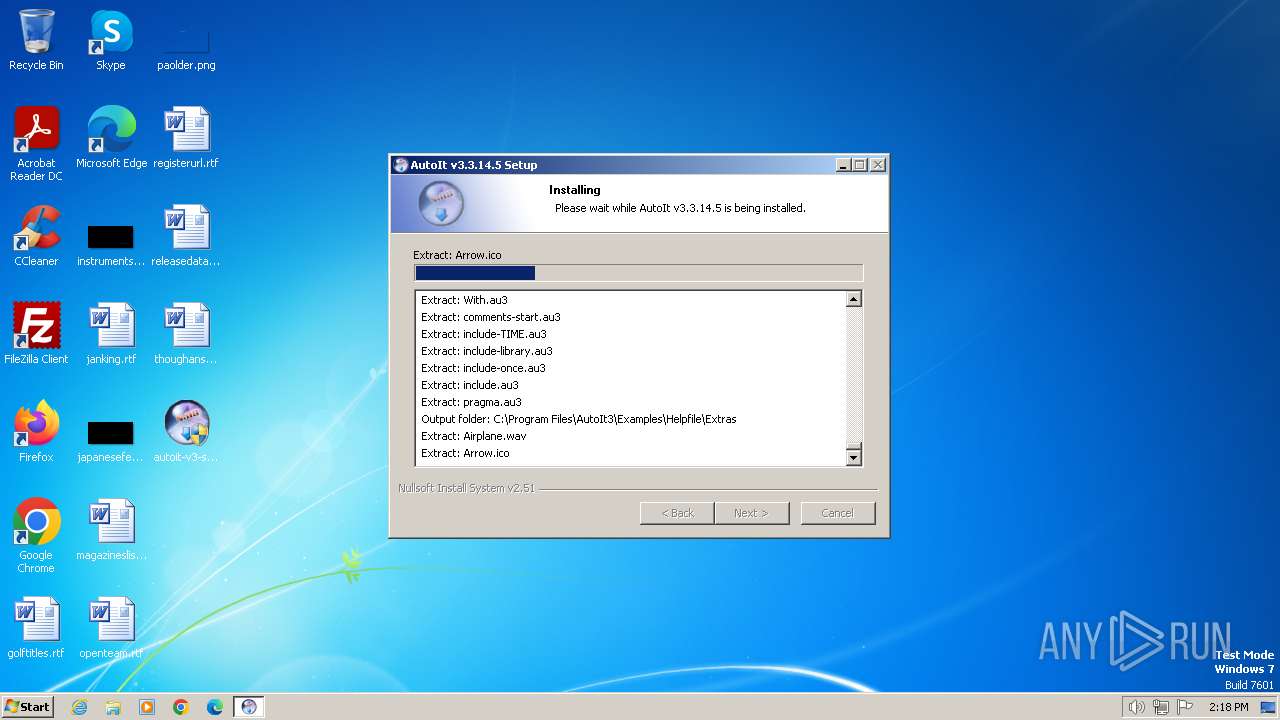
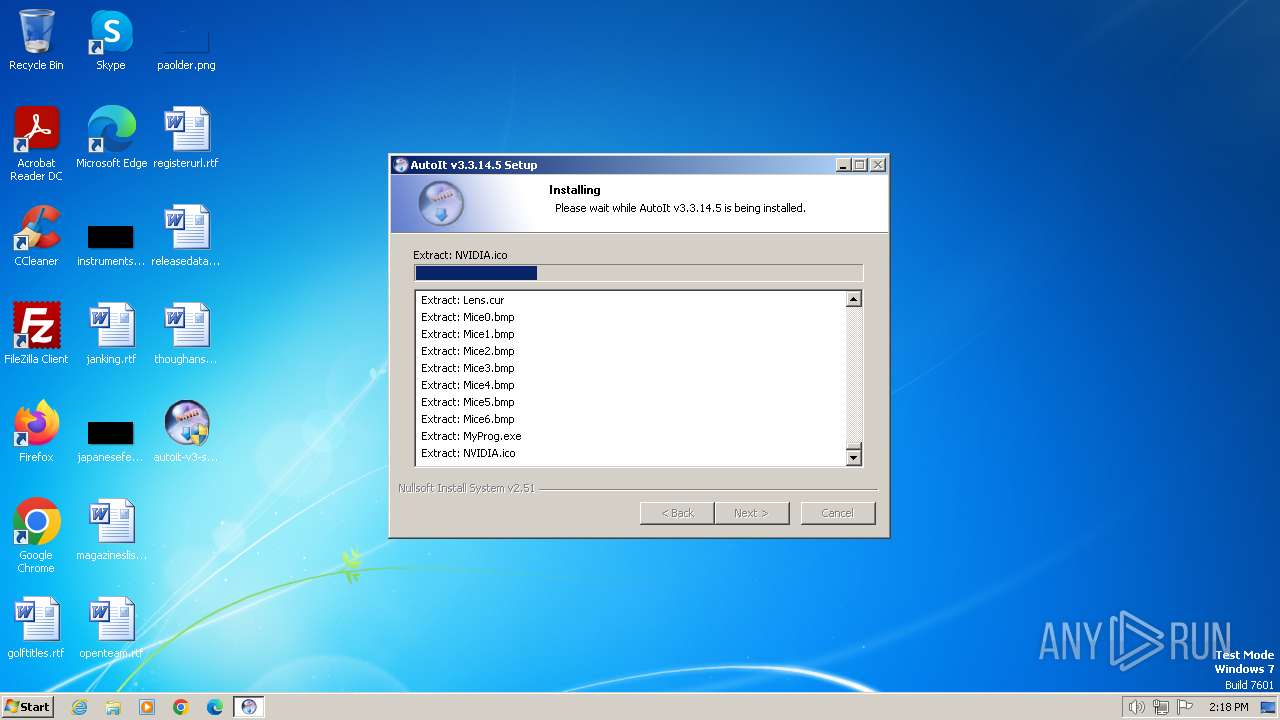
| File name: | autoit-v3-setup.exe |
| Full analysis: | https://app.any.run/tasks/0233e2ee-3613-4047-9db2-314dda9763a2 |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2024, 14:17:16 |
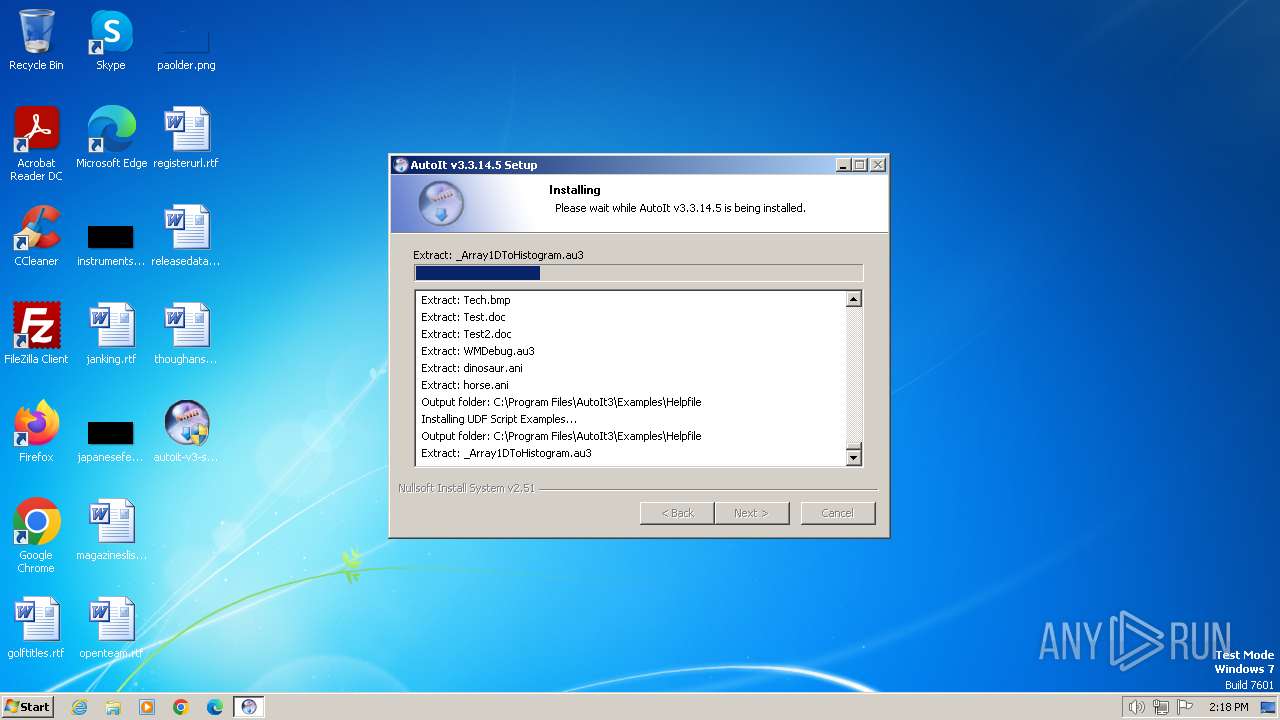
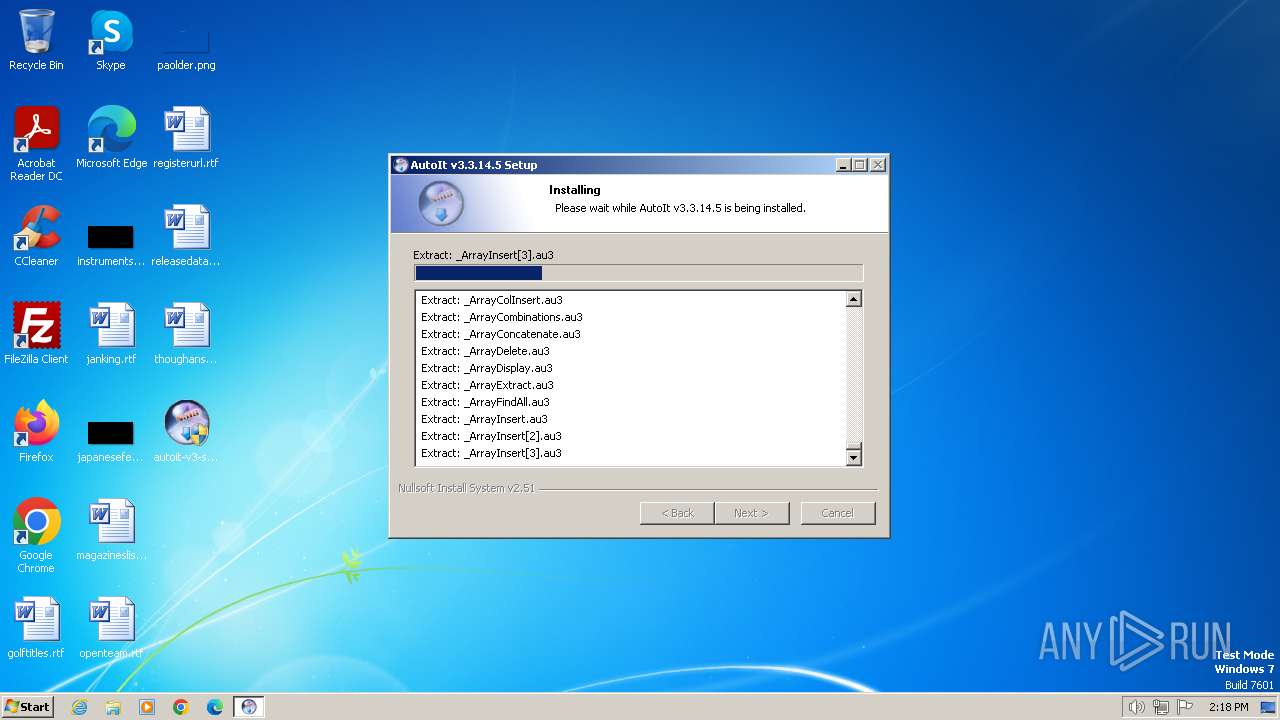
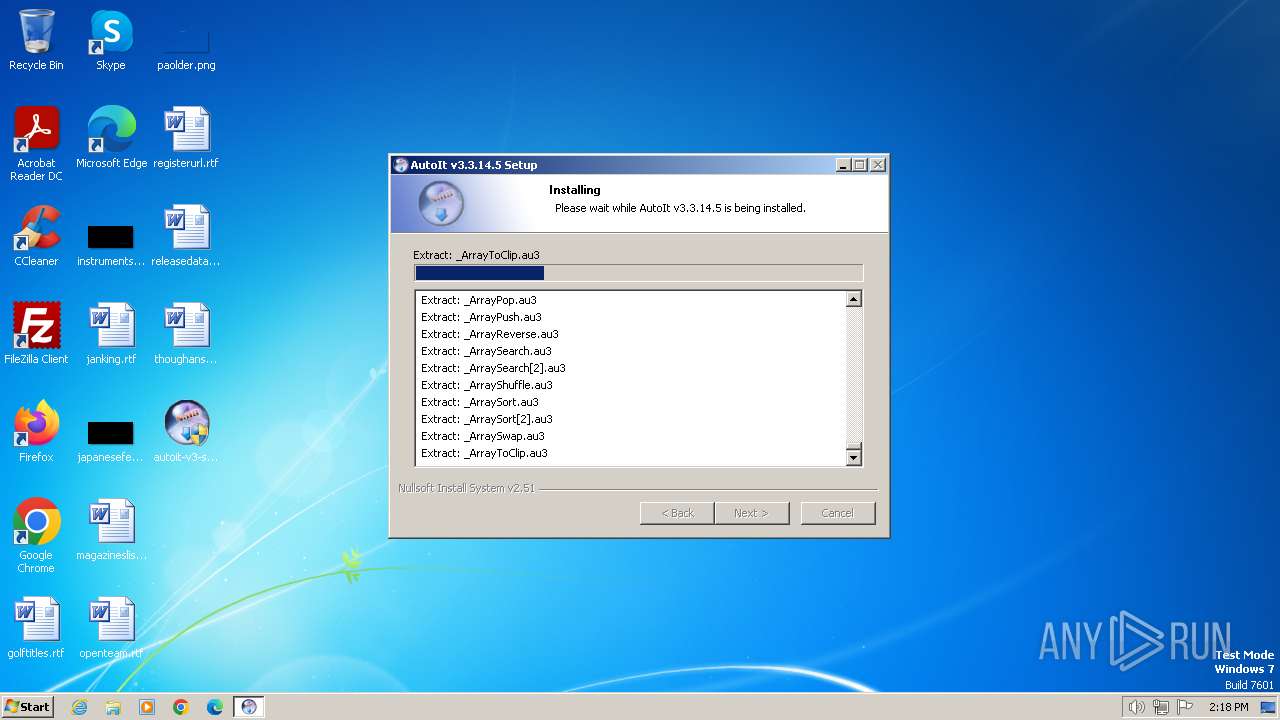
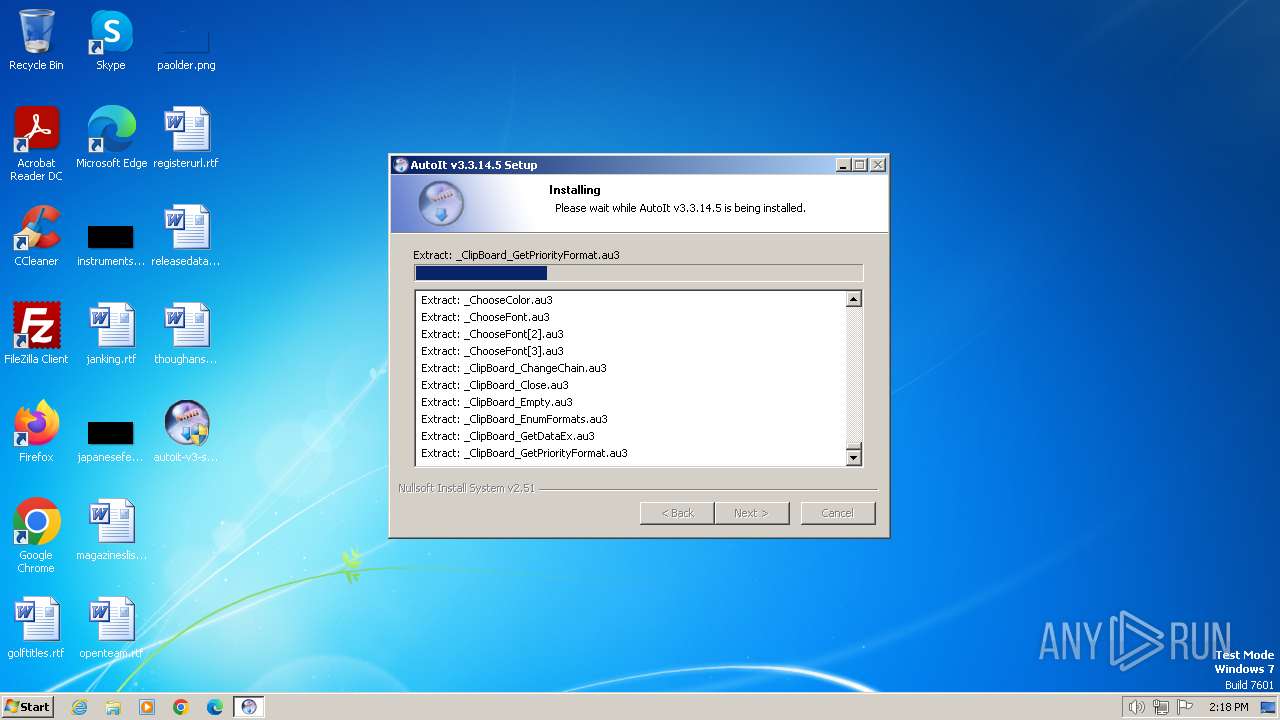
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D50D5712566F1DF16B5AEA21B9E0EE24 |
| SHA1: | F442AA68EC8D838625F382BCF273F5D0F66427EA |
| SHA256: | E102238100A8B97D22559065E3B19379757AEDA932C36916D2C84A4178921854 |
| SSDEEP: | 196608:RibMxSfOYFjizV+mKPdih/DuHKaJC9vdGFMiEXxHeJtMvU9Bi7SkEGIT9OOa5SPl:3xgjihkUhKHKr0M19lSBi7S02OOagDOe |
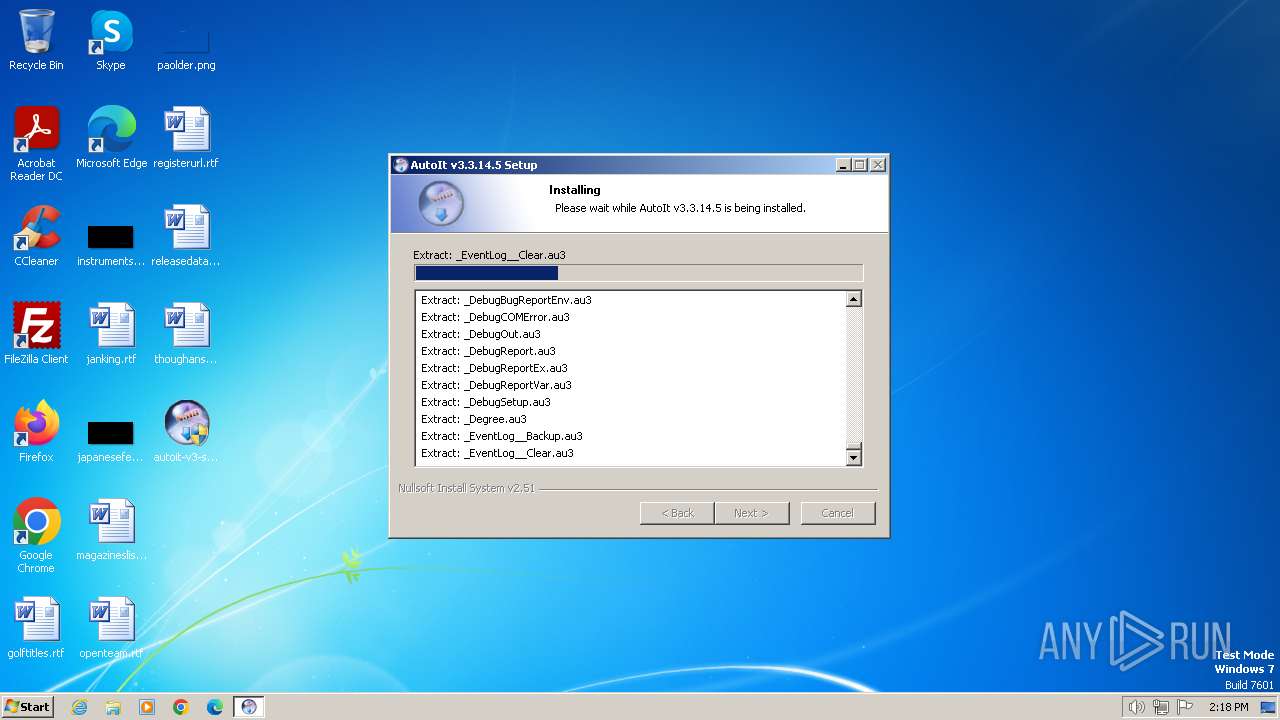
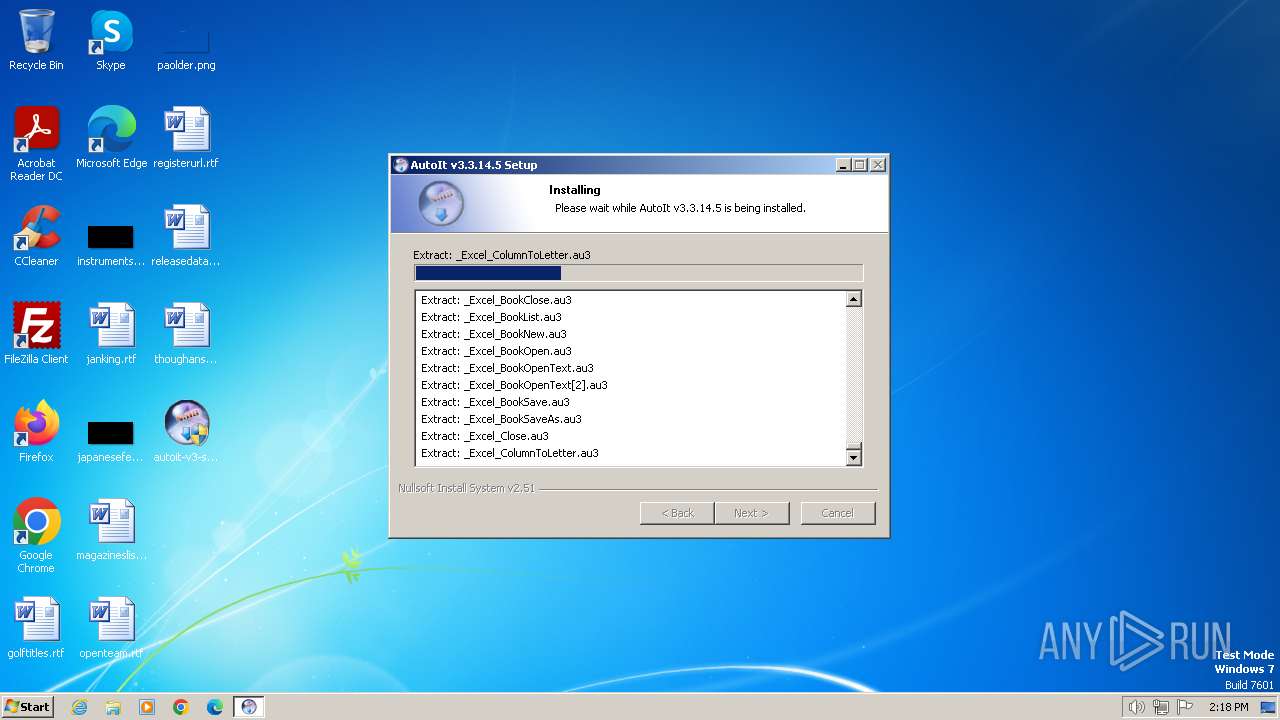
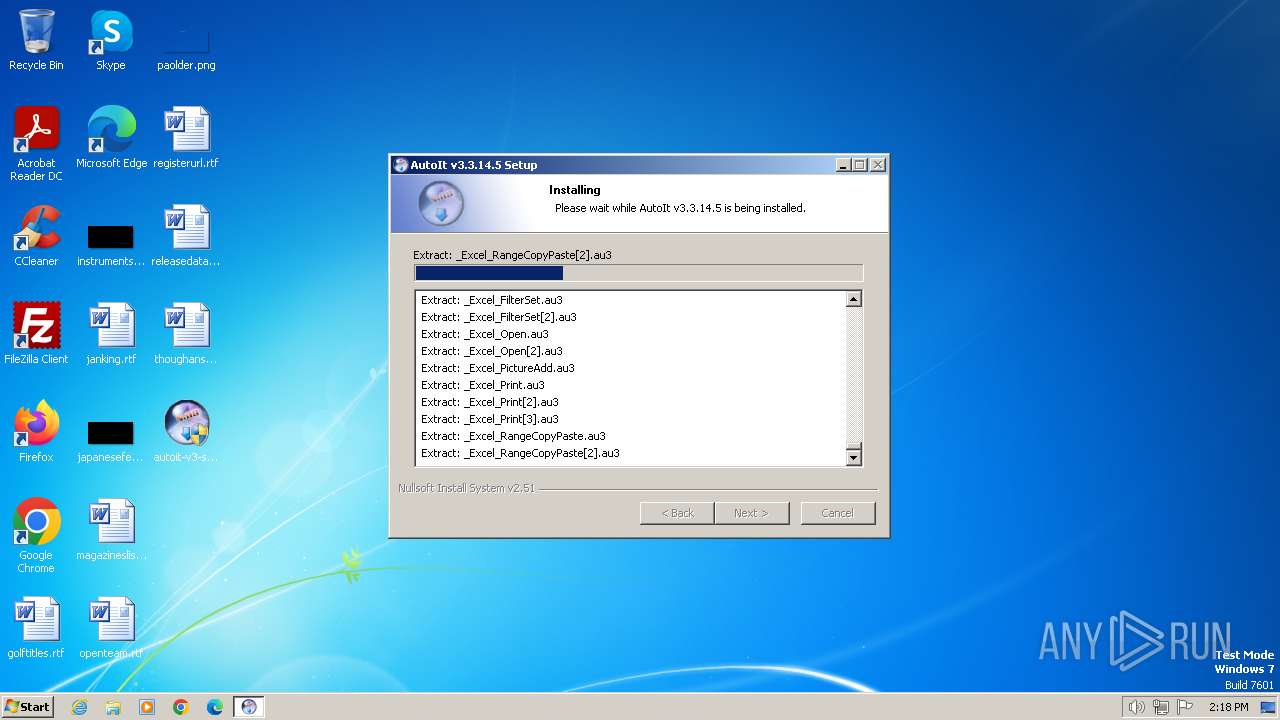
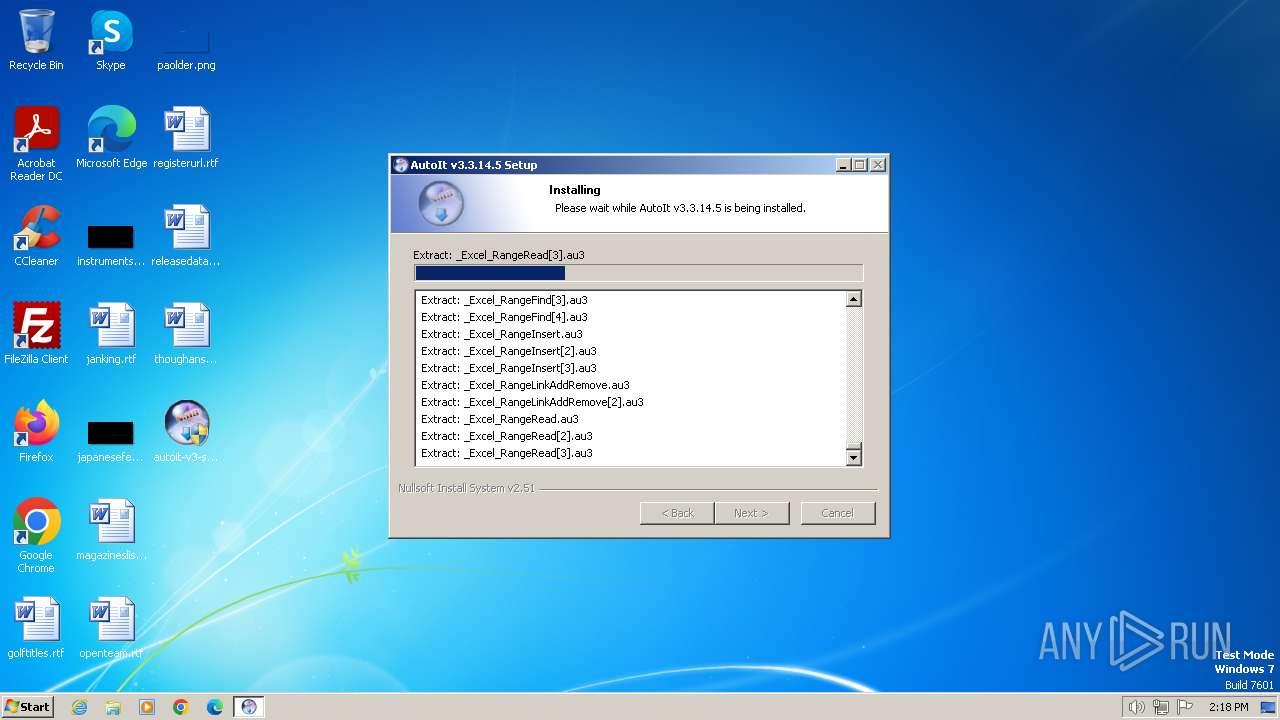
MALICIOUS
Drops the executable file immediately after the start
- autoit-v3-setup.exe (PID: 1492)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- autoit-v3-setup.exe (PID: 1492)
The process creates files with name similar to system file names
- autoit-v3-setup.exe (PID: 1492)
Executable content was dropped or overwritten
- autoit-v3-setup.exe (PID: 1492)
Creates/Modifies COM task schedule object
- autoit-v3-setup.exe (PID: 1492)
Creates a software uninstall entry
- autoit-v3-setup.exe (PID: 1492)
INFO
Checks supported languages
- autoit-v3-setup.exe (PID: 1492)
Reads the computer name
- autoit-v3-setup.exe (PID: 1492)
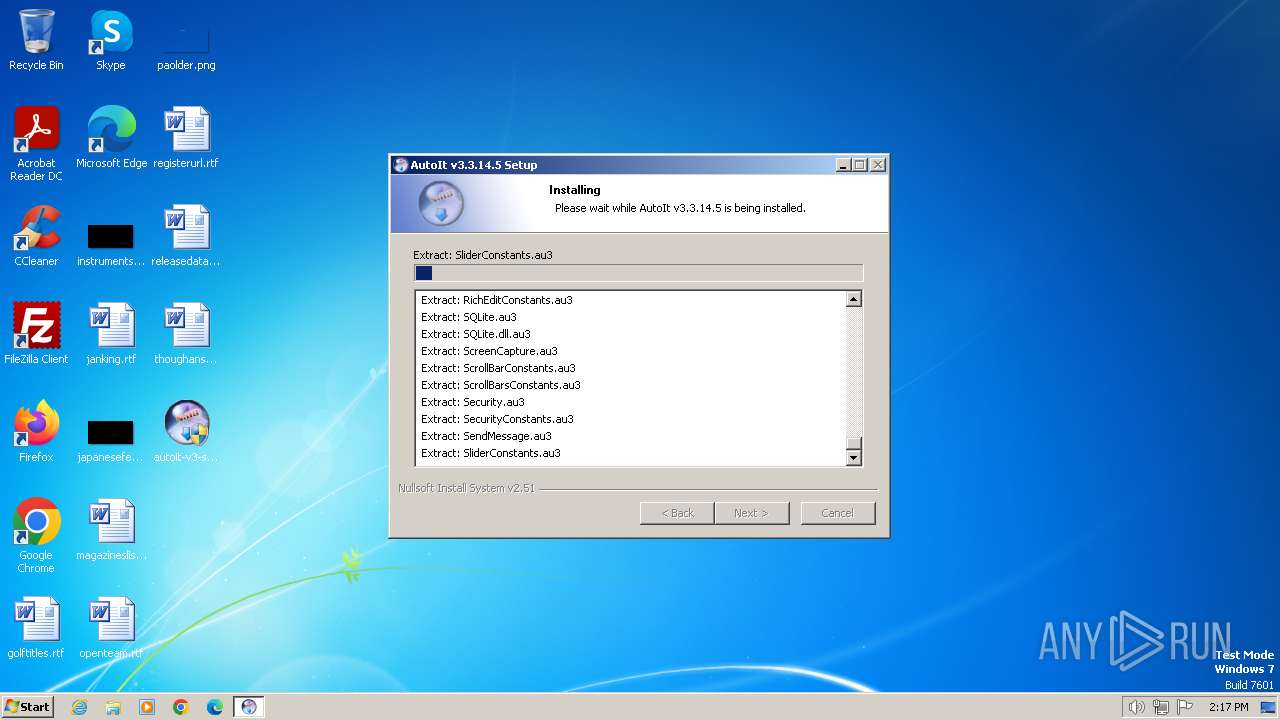
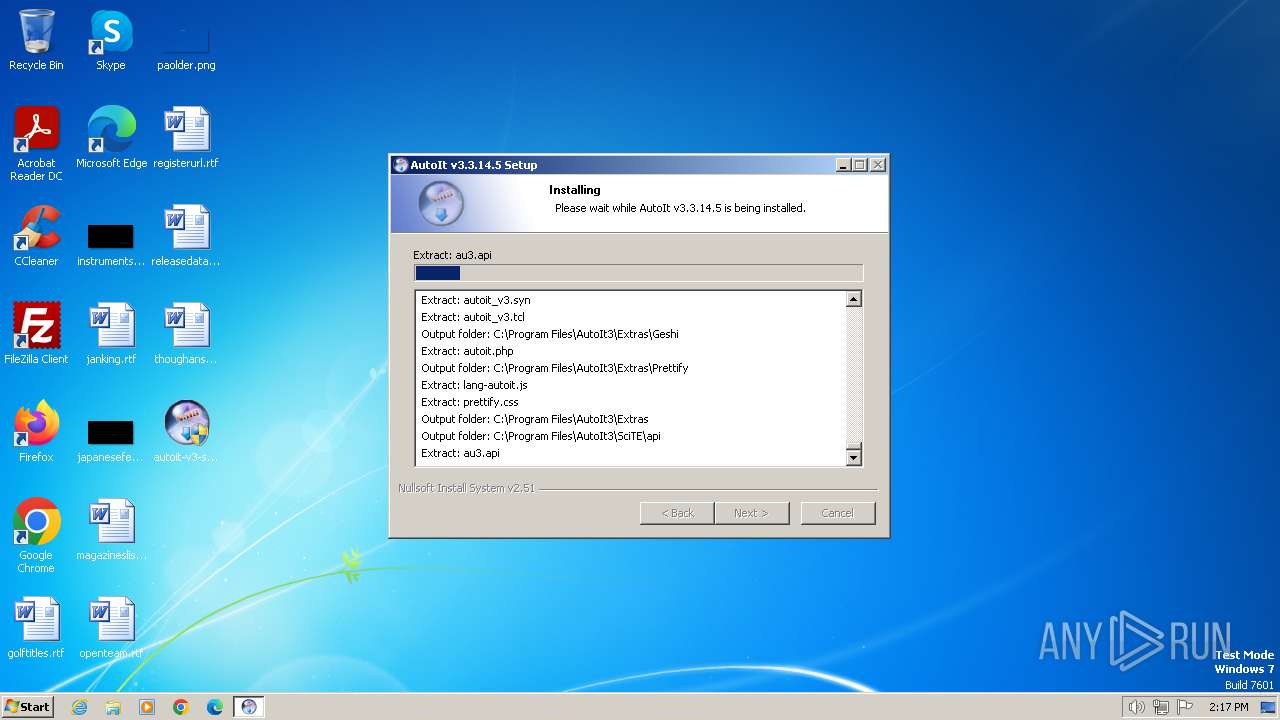
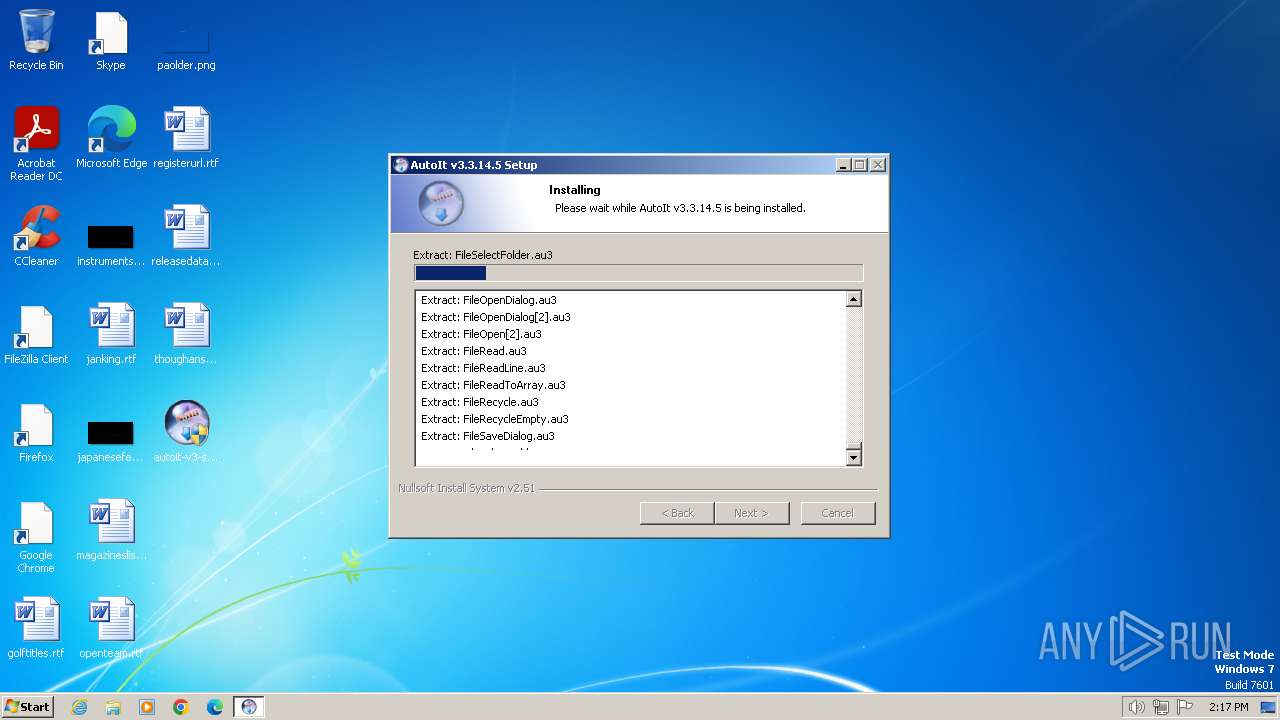
Create files in a temporary directory
- autoit-v3-setup.exe (PID: 1492)
Creates files in the program directory
- autoit-v3-setup.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 03:20:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x326c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.14.5 |
| ProductVersionNumber: | 3.3.14.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
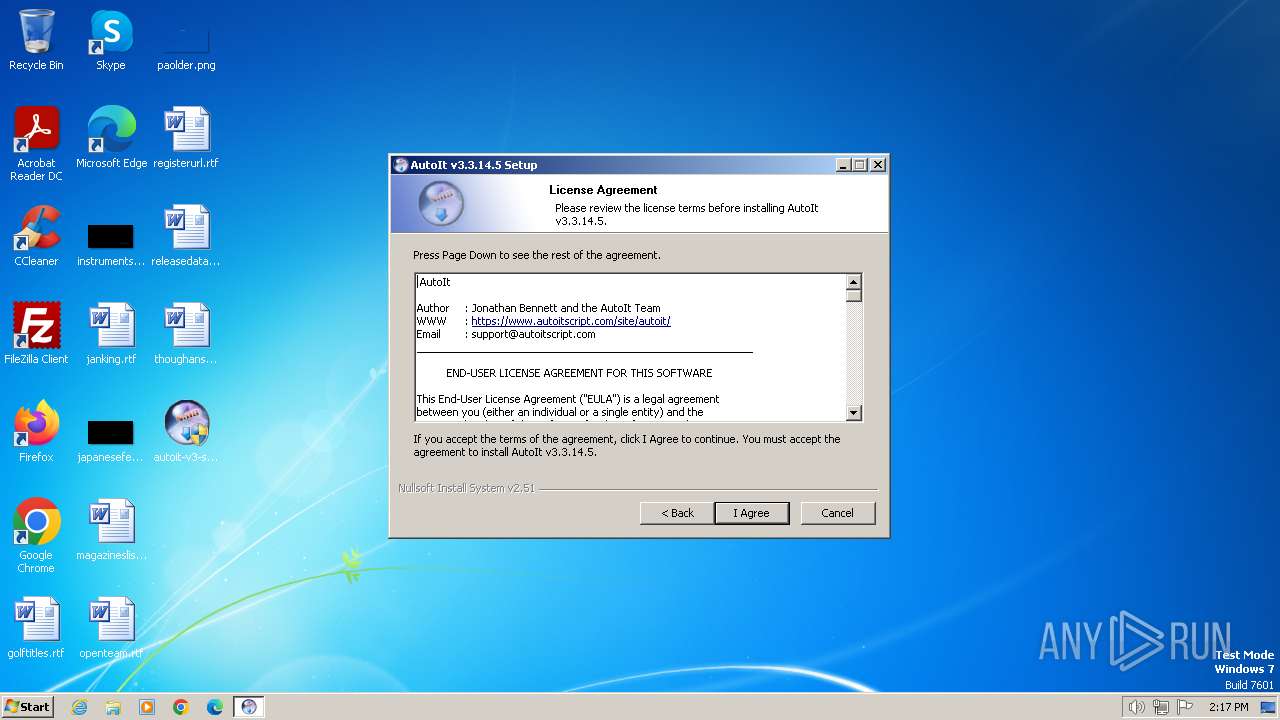
| CompanyName: | AutoIt Team |
| FileDescription: | AutoIt v3 Setup |
| FileVersion: | 3.3.14.5 |
| LegalCopyright: | (c)1999-2018 Jonathan Bennett & AutoIt Team |
Total processes
42
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | "C:\Users\admin\Desktop\autoit-v3-setup.exe" | C:\Users\admin\Desktop\autoit-v3-setup.exe | explorer.exe | ||||||||||||
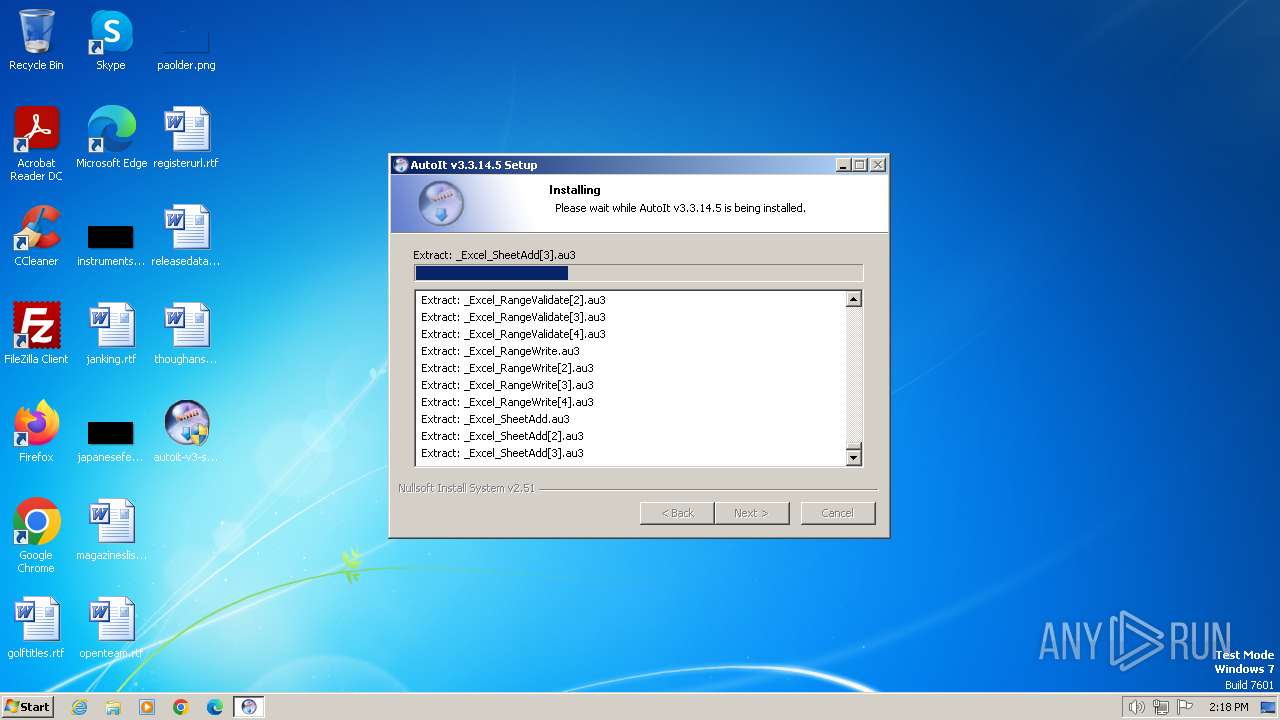
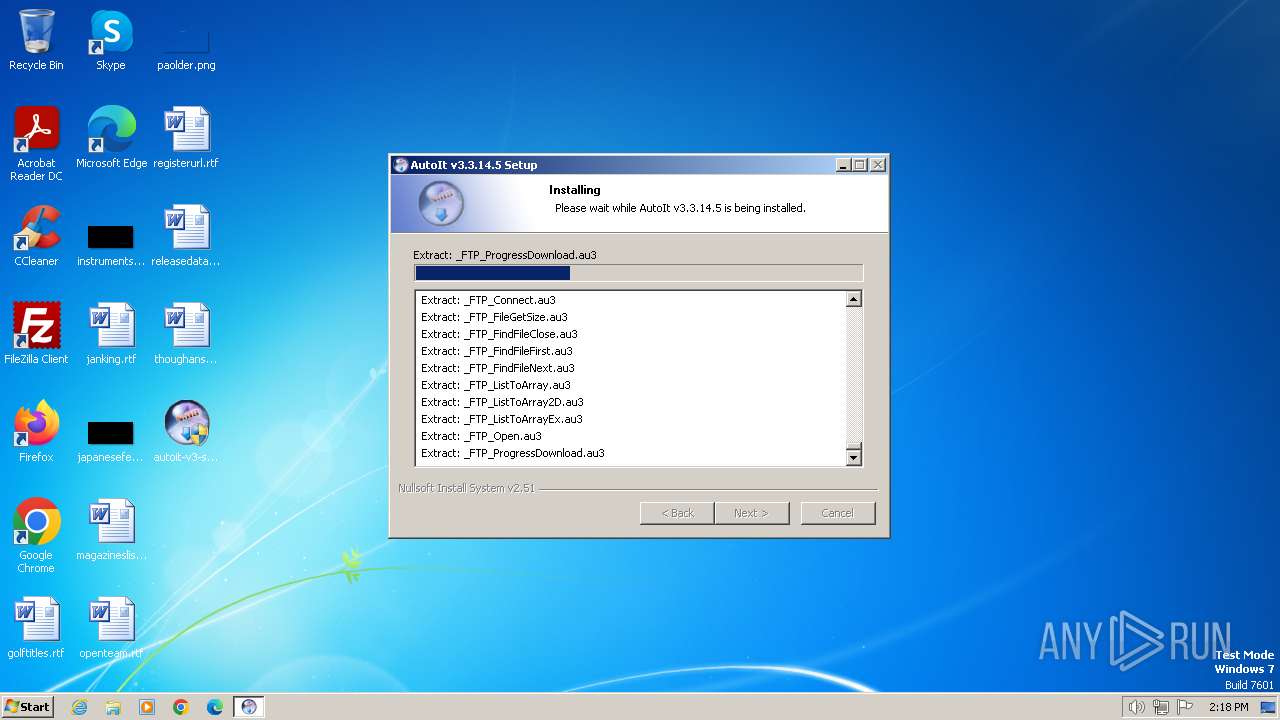
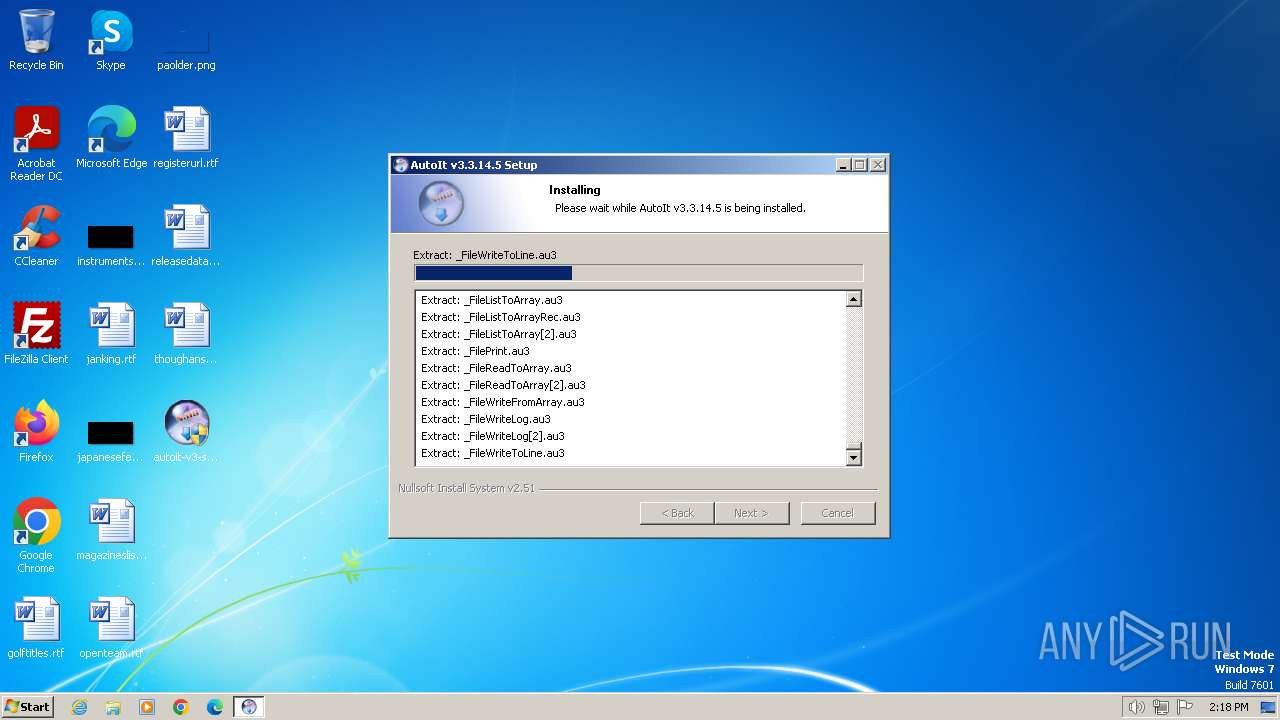
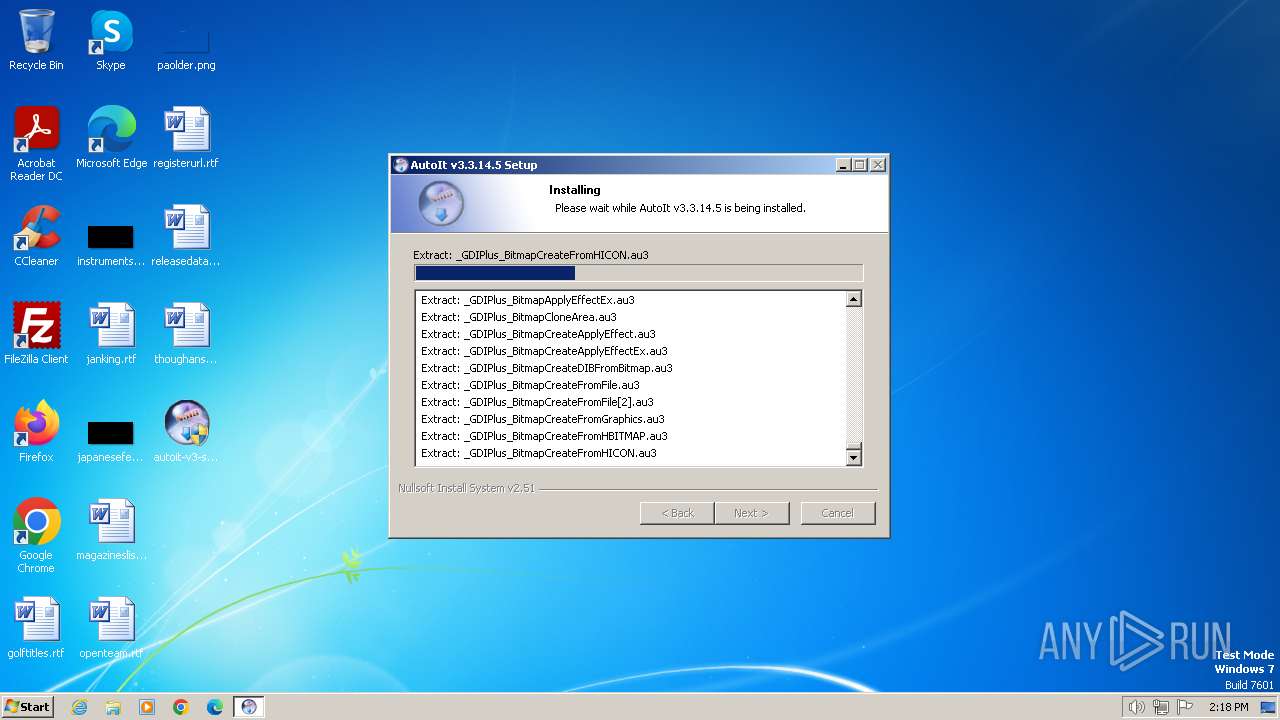
User: admin Company: AutoIt Team Integrity Level: HIGH Description: AutoIt v3 Setup Exit code: 0 Version: 3.3.14.5 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\Desktop\autoit-v3-setup.exe" | C:\Users\admin\Desktop\autoit-v3-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Setup Exit code: 3221226540 Version: 3.3.14.5 Modules
| |||||||||||||||
Total events
971
Read events
945
Write events
26
Delete events
0
Modification events
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AutoIt v3\AutoIt |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\AutoIt3 | |||
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AutoIt v3\AutoIt |
| Operation: | write | Name: | Version |
Value: v3.3.14.5 | |||
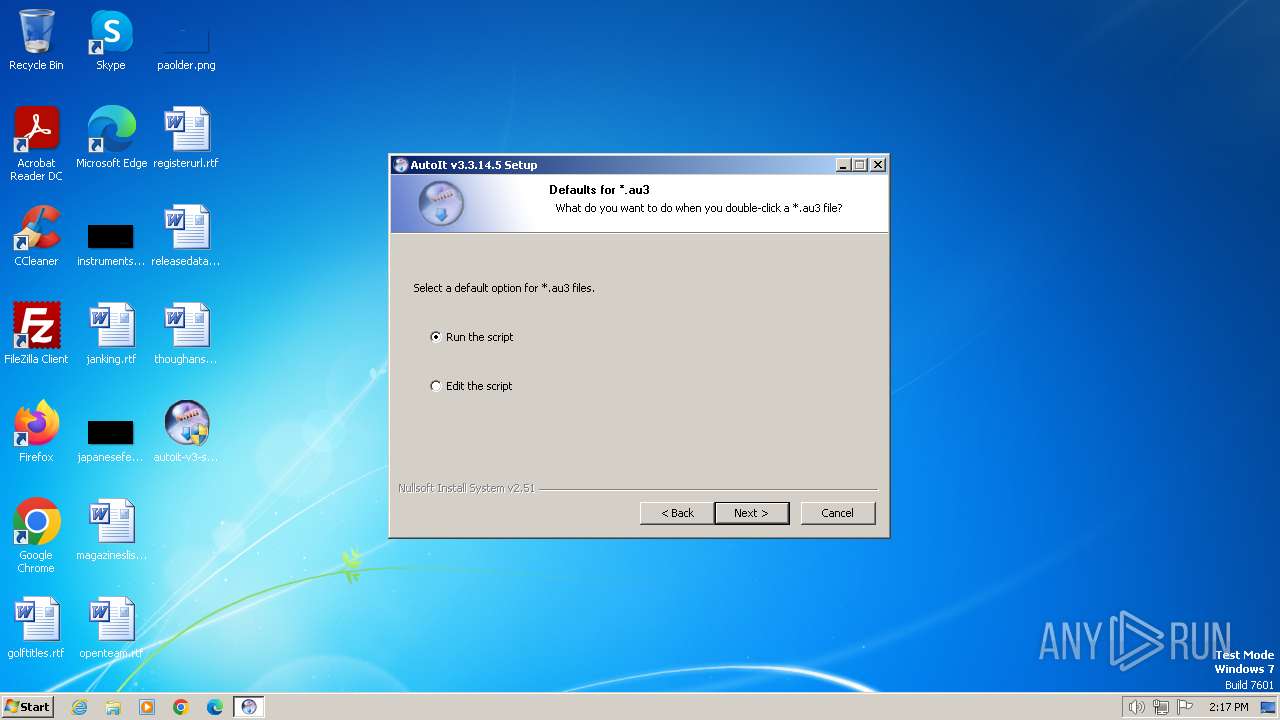
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.au3 |
| Operation: | write | Name: | PerceivedType |
Value: text | |||
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.au3\ShellNew |
| Operation: | write | Name: | FileName |
Value: Template.au3 | |||
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 116 | |||
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\Software\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastExeDir |
Value: My Documents | |||
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\Software\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastScriptDir |
Value: My Documents | |||
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\Software\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastIconDir |
Value: C:\Program Files\AutoIt3\Aut2Exe\Icons | |||
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\Software\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastIcon |
Value: | |||
| (PID) Process: | (1492) autoit-v3-setup.exe | Key: | HKEY_CURRENT_USER\Software\AutoIt v3\Aut2Exe |
| Operation: | write | Name: | LastCompression |
Value: 2 | |||
Executable files
24
Suspicious files
29
Text files
1 023
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1492 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\AutoIt.chm | — | |
MD5:— | SHA256:— | |||
| 1492 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsr443.tmp\System.dll | executable | |
MD5:56A321BD011112EC5D8A32B2F6FD3231 | SHA256:BB6DF93369B498EAA638B0BCDC4BB89F45E9B02CA12D28BCEDF4629EA7F5E0F1 | |||
| 1492 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsr443.tmp\ioPreviousVersion.ini | text | |
MD5:8C032D104411DA01E43D8E8B9AD88EB4 | SHA256:659CAD01FE631A96E0856C44D4114E12AC0E5402F863C2B1213A87D375C26F59 | |||
| 1492 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsr443.tmp\modern-header.bmp | image | |
MD5:940C56737BF9BB69CE7A31C623D4E87A | SHA256:766A893FE962AEFD27C574CB05F25CF895D3FC70A00DB5A6FA73D573F571AEFC | |||
| 1492 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsr443.tmp\UserInfo.dll | executable | |
MD5:E840E7F30C85E22B09A41098FF3F3343 | SHA256:6707E9E88DEC460C2CF421BD2BC6A314F15717527CB60DCAD2FBB7352AE711A3 | |||
| 1492 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\Au3Info.exe | executable | |
MD5:0E74B9DC602E5C3540C3CE7E51C5717C | SHA256:CD7660502EE43FAB3E5AF883F21E2F03F78E462912CF14D23D105C3DE8E9D3CE | |||
| 1492 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsr443.tmp\ioSpecial.ini | text | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 1492 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\Include\APIComConstants.au3 | text | |
MD5:2FFBA31B7301A02079993CFE9933E55E | SHA256:080DBC5CD1F12AF1E3DEBF0AAB0C282A43767D88E5097C83F0DB97B5F9E8A266 | |||
| 1492 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\AutoIt3Help.exe | executable | |
MD5:EB39F039A6423A8B522775F264254385 | SHA256:829AAEAD9E89B65F3905E64F73C362FCF58EFD1A9CBEC4917B75C92397186CC8 | |||
| 1492 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsr443.tmp\ioDefaultOpen.ini | text | |
MD5:8C032D104411DA01E43D8E8B9AD88EB4 | SHA256:659CAD01FE631A96E0856C44D4114E12AC0E5402F863C2B1213A87D375C26F59 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |