| File name: | Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_ |
| Full analysis: | https://app.any.run/tasks/558a0925-83b9-4961-b6c3-9e09326bb827 |
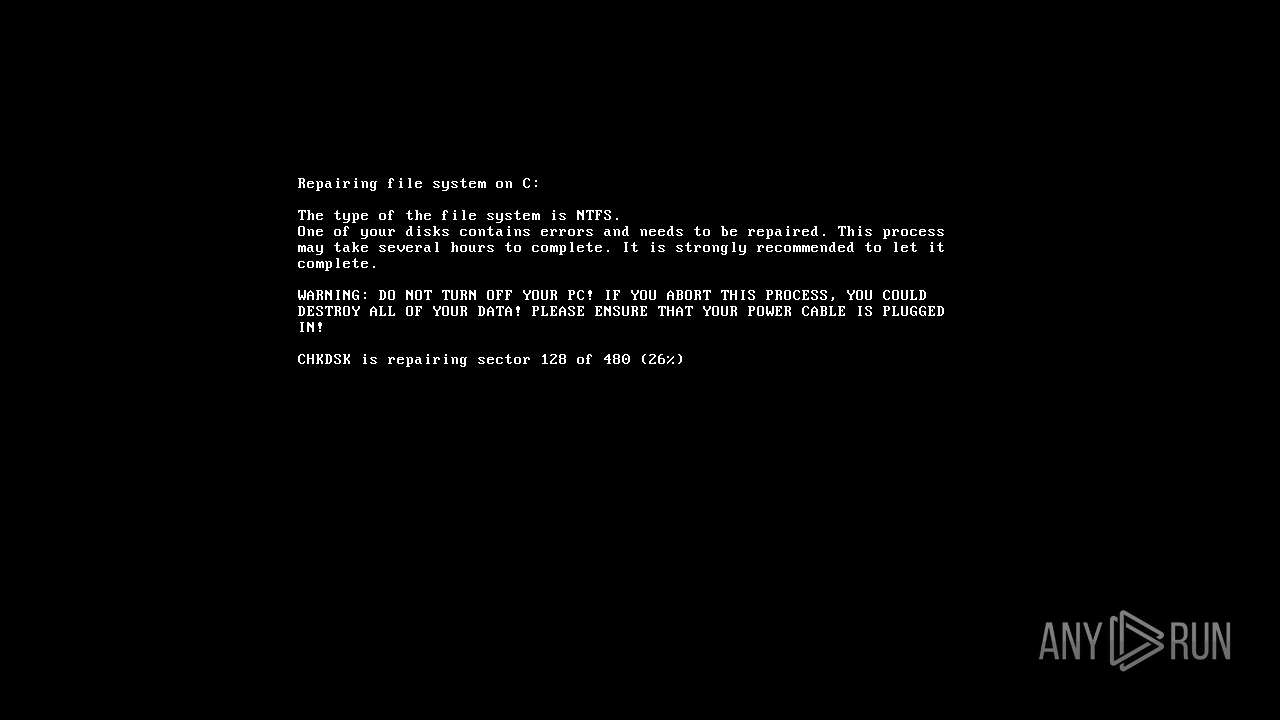
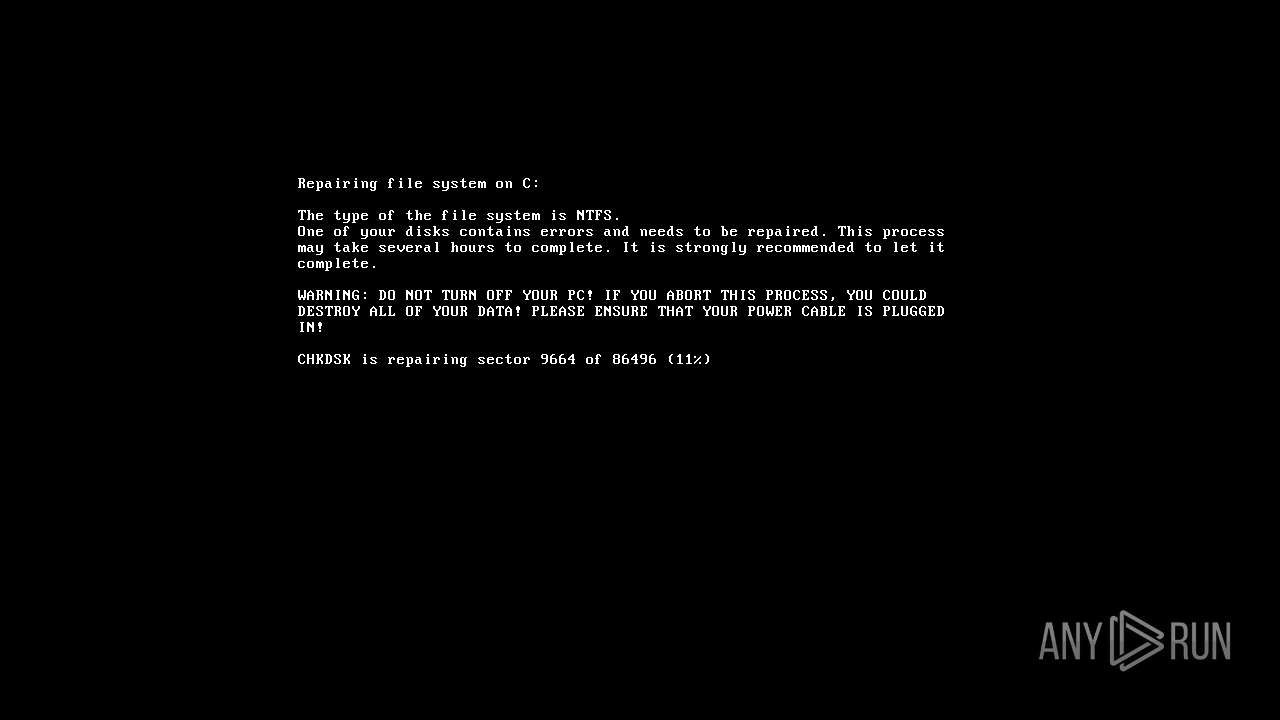
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2024, 15:42:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | AA5D0BAF4263EB4FB94B6814973E3B0C |
| SHA1: | 2F24A64D9445AF574832B1A32495AD7AA6C53C66 |
| SHA256: | E0FCB5F1A4CD87484ADFE6E42E4439DD43932AFEC78C6FC5E8CB99A4DBDC8CF0 |
| SSDEEP: | 12288:vGq5RaafEKcvLJEGGE2gxoiuyPyDbXYjpj1ICVW+EIQghhVSWc+RZ8ZmZIZdZZZA:vGq5RRfKEGG/gxoiuKyDbXYjpjzVd |
MALICIOUS
XORed URL has been found (YARA)
- rasautou.exe (PID: 1744)
SUSPICIOUS
Starts a Microsoft application from unusual location
- Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe (PID: 2296)
- Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe (PID: 1824)
Process drops legitimate windows executable
- Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe (PID: 2296)
Executable content was dropped or overwritten
- Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe (PID: 2296)
INFO
Creates files or folders in the user directory
- Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe (PID: 2296)
Reads the computer name
- Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe (PID: 2296)
- wmpnscfg.exe (PID: 2244)
- rasautou.exe (PID: 1744)
Checks supported languages
- wmpnscfg.exe (PID: 2244)
- Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe (PID: 2296)
- rasautou.exe (PID: 1744)
Reads the machine GUID from the registry
- Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe (PID: 2296)
- rasautou.exe (PID: 1744)
Manual execution by a user
- wmpnscfg.exe (PID: 2244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(1744) rasautou.exe
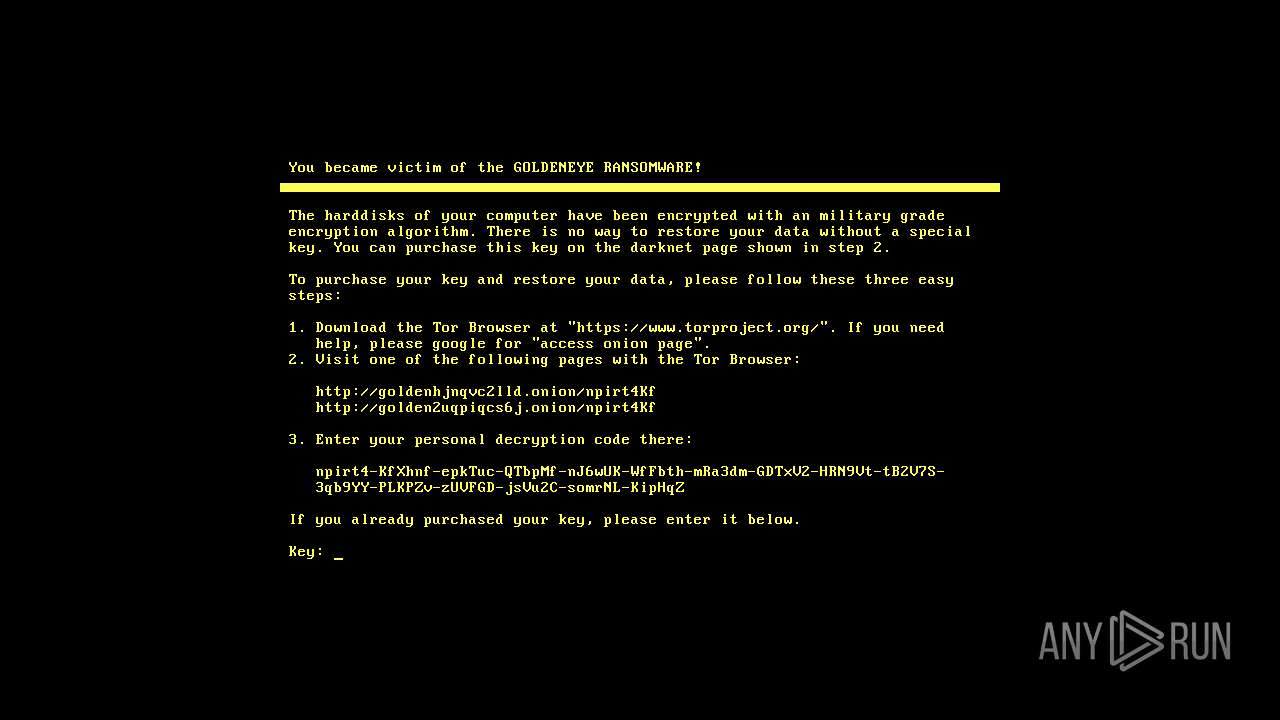
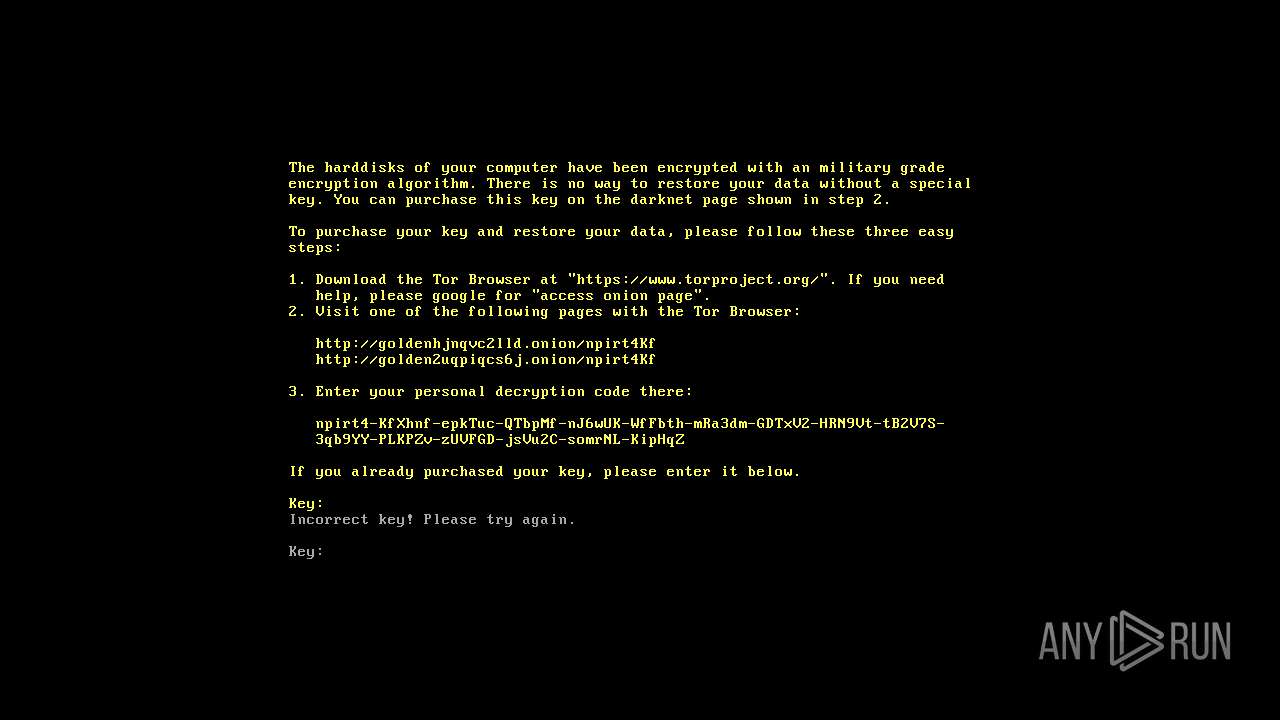
Decrypted-URLs (1)https://www.torproject.org/
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:18 21:01:49+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 194560 |
| InitializedDataSize: | 1099776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc424 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.2600.2180 |
| ProductVersionNumber: | 5.1.2600.2180 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Network Command Shell |
| FileVersion: | 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) |
| InternalName: | netsh.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | netsh.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 5.1.2600.2180 |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1744 | "C:\Users\admin\AppData\Roaming\{d50e1752-4a70-404e-8c01-dff914a26a83}\rasautou.exe" | C:\Users\admin\AppData\Roaming\{d50e1752-4a70-404e-8c01-dff914a26a83}\rasautou.exe | Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Remote Access Dialer Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
xor-url(PID) Process(1744) rasautou.exe Decrypted-URLs (1)https://www.torproject.org/ | |||||||||||||||
| 1824 | "C:\Users\admin\Desktop\Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe" | C:\Users\admin\Desktop\Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 3221226540 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | "C:\Users\admin\Desktop\Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe" | C:\Users\admin\Desktop\Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
Total events
104
Read events
104
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1744 | rasautou.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 2296 | Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe | C:\Users\admin\AppData\Roaming\{d50e1752-4a70-404e-8c01-dff914a26a83}\rasautou.exe | executable | |
MD5:AA5D0BAF4263EB4FB94B6814973E3B0C | SHA256:E0FCB5F1A4CD87484ADFE6E42E4439DD43932AFEC78C6FC5E8CB99A4DBDC8CF0 | |||
| 2296 | Petya.E_e0fcb5f1a4cd87484adfe6e42e4439dd43932afec78c6fc5e8cb99a4dbdc8cf0.exe_.exe | C:\Users\admin\AppData\Roaming\{d50e1752-4a70-404e-8c01-dff914a26a83}\RCXB2A8.tmp | executable | |
MD5:4C18F4DAB9ED8C42F3D41816B203C037 | SHA256:89188EA2CCAB15EDA7F14AA639A7B52F532EE92B1685239BDD835DDD7B954014 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |