| File name: | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2 |
| Full analysis: | https://app.any.run/tasks/6d6a9724-cc53-4611-bef6-574372e199e2 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | February 19, 2019, 14:00:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2B68CBFE7D596810543AD81F62AFDC07 |
| SHA1: | 14645C94D55C781F7A14BBE9CD358211E4C7C356 |
| SHA256: | E0F008B4B5CD2DB006D8DCF841828FAFBACC6AAD6DACBC320DD71F893CFC71D2 |
| SSDEEP: | 1536:L55u555555555pmgSeGDjtQhnwmmB0ybMqqU+2bbbAV2/S2mr3IdE8mne0Avu5rJ:3MSjOnrmBTMqqDL2/mr3IdE8we0Avu5F |
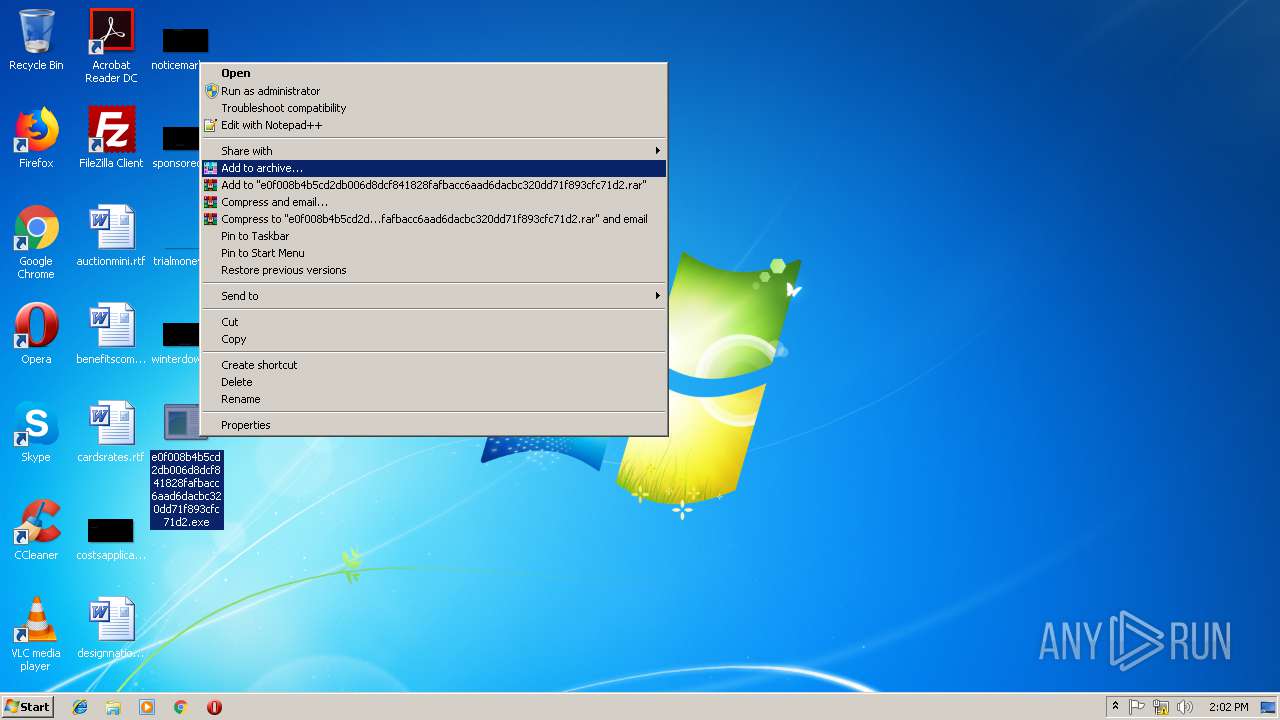
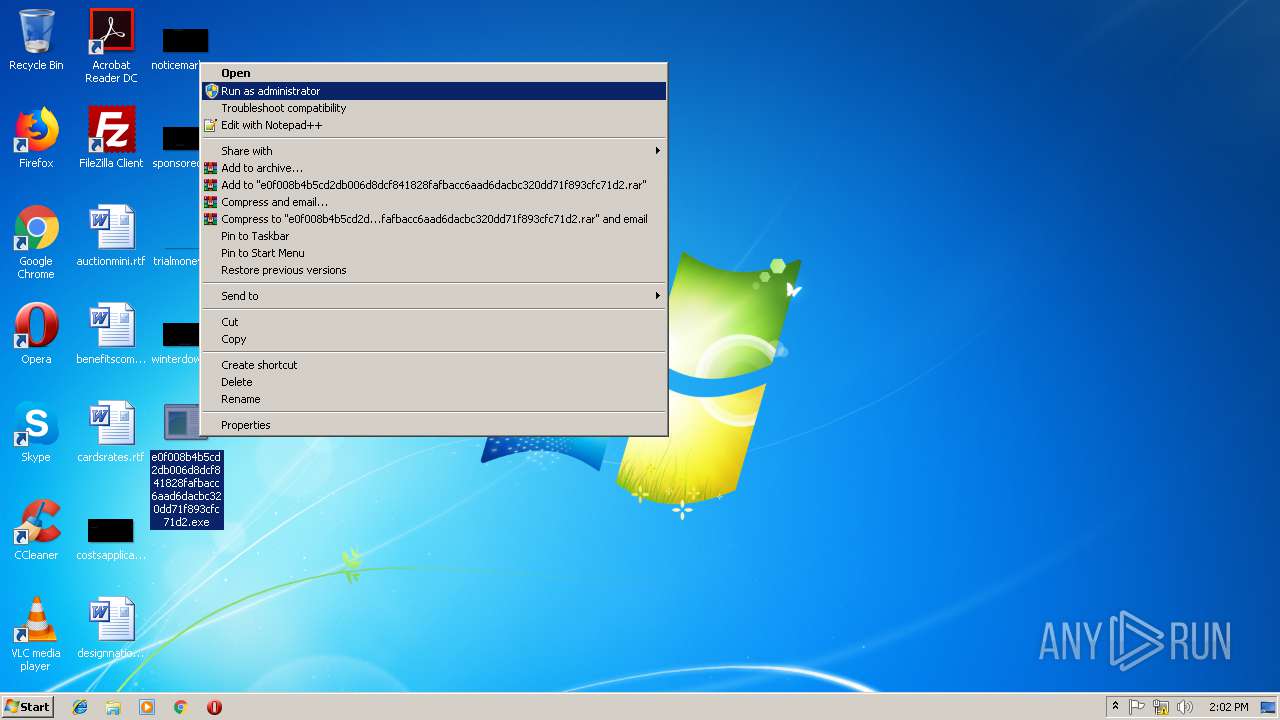
MALICIOUS
GANDCRAB was detected
- e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe (PID: 2820)
- nslookup.exe (PID: 2600)
- nslookup.exe (PID: 3948)
- nslookup.exe (PID: 2304)
- nslookup.exe (PID: 4008)
- nslookup.exe (PID: 4016)
- nslookup.exe (PID: 3444)
- nslookup.exe (PID: 756)
- nslookup.exe (PID: 3048)
- nslookup.exe (PID: 3808)
- nslookup.exe (PID: 3840)
- nslookup.exe (PID: 352)
- nslookup.exe (PID: 1576)
- nslookup.exe (PID: 2276)
- nslookup.exe (PID: 4044)
- nslookup.exe (PID: 364)
- nslookup.exe (PID: 3696)
- nslookup.exe (PID: 3992)
- nslookup.exe (PID: 1636)
- nslookup.exe (PID: 3044)
- nslookup.exe (PID: 1420)
- nslookup.exe (PID: 3324)
- nslookup.exe (PID: 1624)
- nslookup.exe (PID: 3424)
- nslookup.exe (PID: 3172)
- nslookup.exe (PID: 2328)
- nslookup.exe (PID: 3568)
- nslookup.exe (PID: 2660)
- nslookup.exe (PID: 2936)
- nslookup.exe (PID: 2636)
- nslookup.exe (PID: 3380)
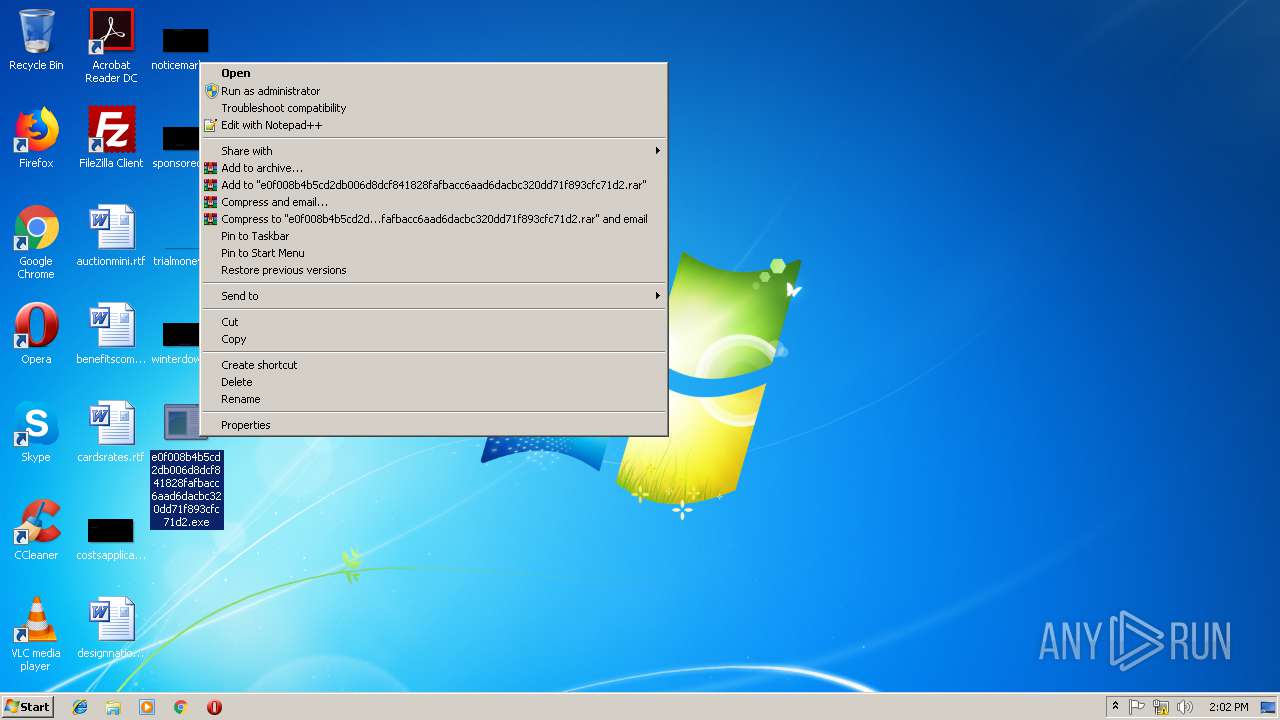
Changes the autorun value in the registry
- e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe (PID: 2820)
GandCrab detected
- e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe (PID: 2820)
SUSPICIOUS
Changes tracing settings of the file or console
- e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe (PID: 2820)
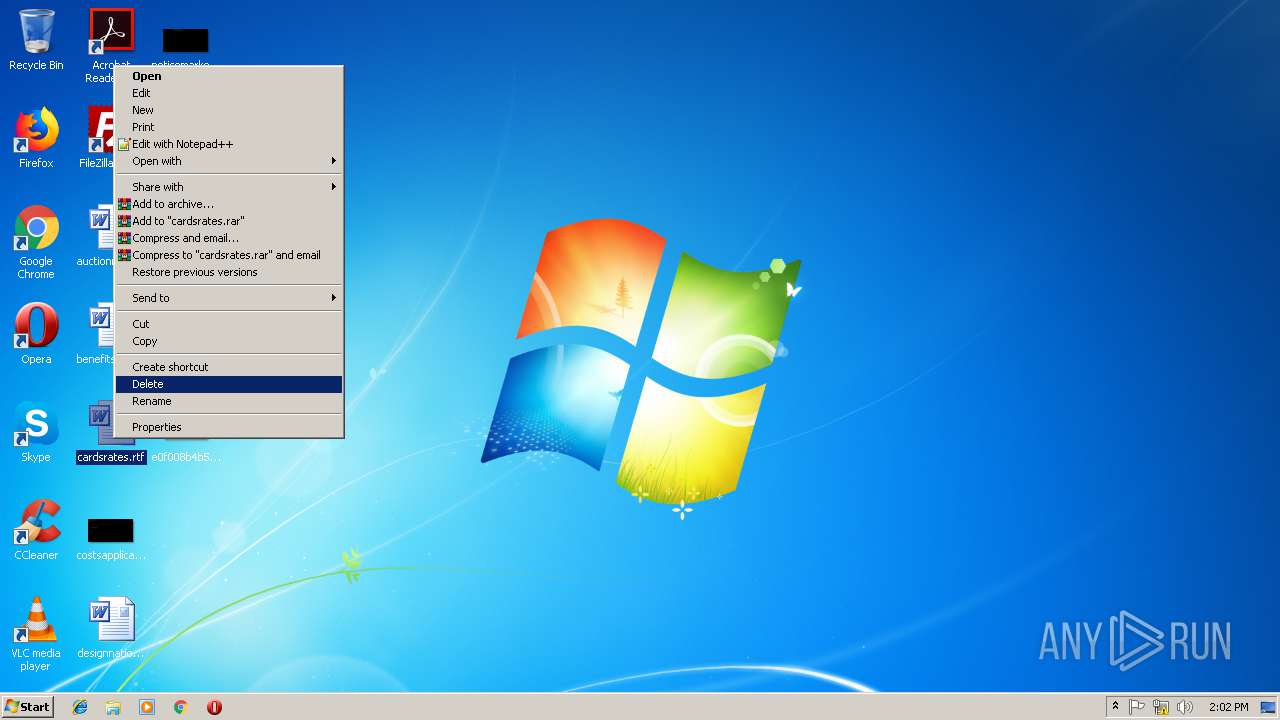
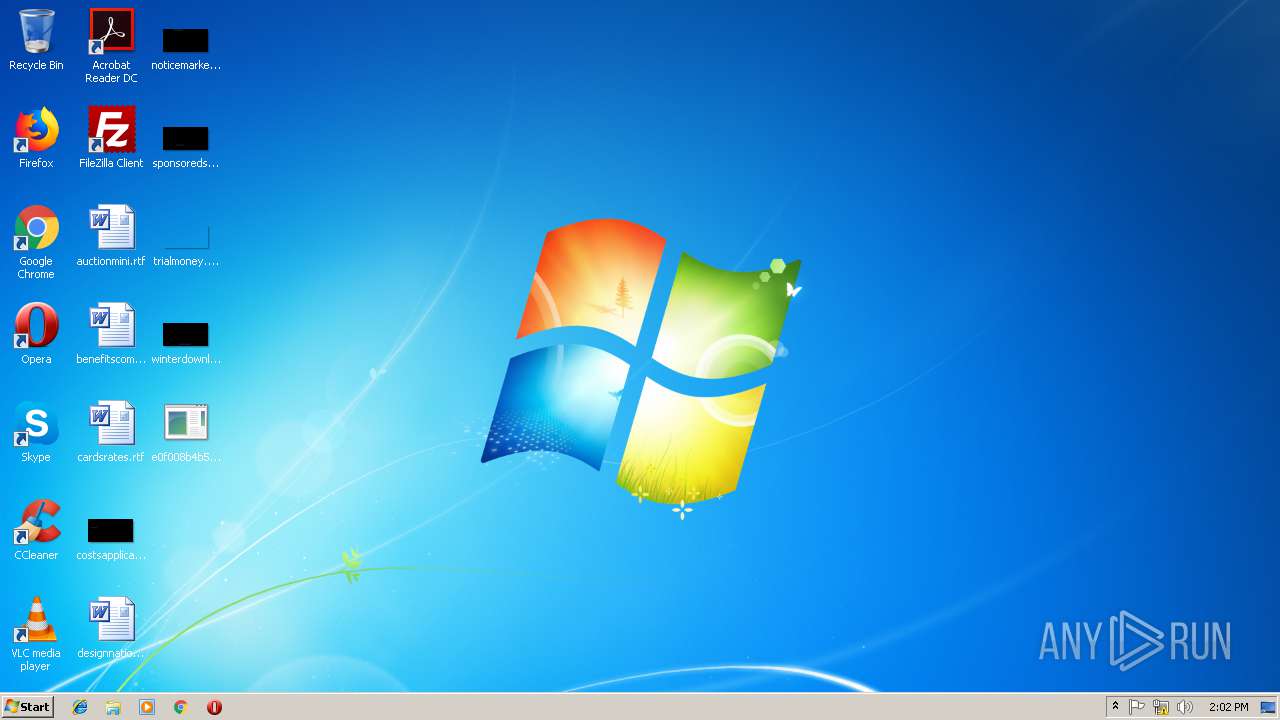
Executable content was dropped or overwritten
- e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe (PID: 2820)
Creates files in the user directory
- e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe (PID: 2820)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:03 19:58:37+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 32768 |
| InitializedDataSize: | 41472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4af0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Feb-2018 18:58:37 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 03-Feb-2018 18:58:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008000 | 0x00008000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.29686 |
.rdata | 0x00009000 | 0x00009000 | 0x00008600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.13221 |
.data | 0x00012000 | 0x00001000 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.4502 |
.CRT | 0x00013000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0611629 |
.rsrc | 0x00014000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71006 |
.reloc | 0x00015000 | 0x00001000 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.43441 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WININET.dll |
Total processes
95
Monitored processes
32
Malicious processes
31
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | nslookup emsisoft.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 364 | nslookup emsisoft.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | nslookup nomoreransom.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1420 | nslookup gandcrab.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1576 | nslookup gandcrab.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1624 | nslookup nomoreransom.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1636 | nslookup nomoreransom.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | nslookup emsisoft.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | nslookup nomoreransom.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | nslookup gandcrab.bit dns1.soprodns.ru | C:\Windows\system32\nslookup.exe | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
337
Read events
318
Write events
19
Delete events
0
Modification events
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | zhkzvenuhgr |
Value: "C:\Users\admin\AppData\Roaming\Microsoft\wojrhw.exe" | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2820) e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | — | |
MD5:— | SHA256:— | |||
| 2820 | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\ipv4bot_whatismyipaddress_com[1].htm | — | |
MD5:— | SHA256:— | |||
| 2820 | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | C:\Users\admin\AppData\Roaming\Microsoft\wojrhw.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
6
Threats
244
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2820 | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | GET | 200 | 66.171.248.178:80 | http://nomoreransom.bit/ | US | text | 11 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2820 | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | 66.171.248.178:80 | ipv4bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipv4bot.whatismyipaddress.com |
| shared |
dns1.soprodns.ru |
| shared |
gandcrab.bit |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2820 | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | A Network Trojan was detected | ET TROJAN Likely GandCrab Ransomware Domain in HTTP Host M1 |
2820 | e0f008b4b5cd2db006d8dcf841828fafbacc6aad6dacbc320dd71f893cfc71d2.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab External IP Request |
756 | nslookup.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
756 | nslookup.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
756 | nslookup.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
756 | nslookup.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
4008 | nslookup.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
4008 | nslookup.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
4008 | nslookup.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
4008 | nslookup.exe | Potentially Bad Traffic | ET CURRENT_EVENTS DNS Query Domain .bit |
82 ETPRO signatures available at the full report