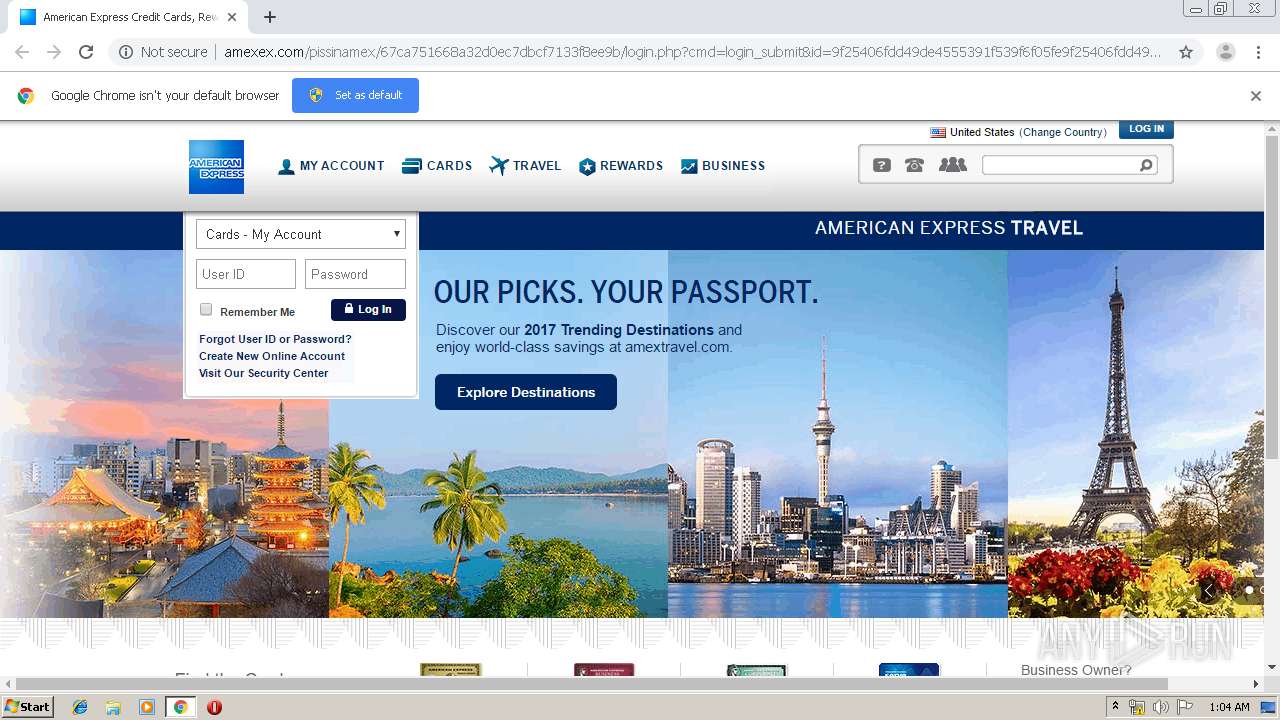
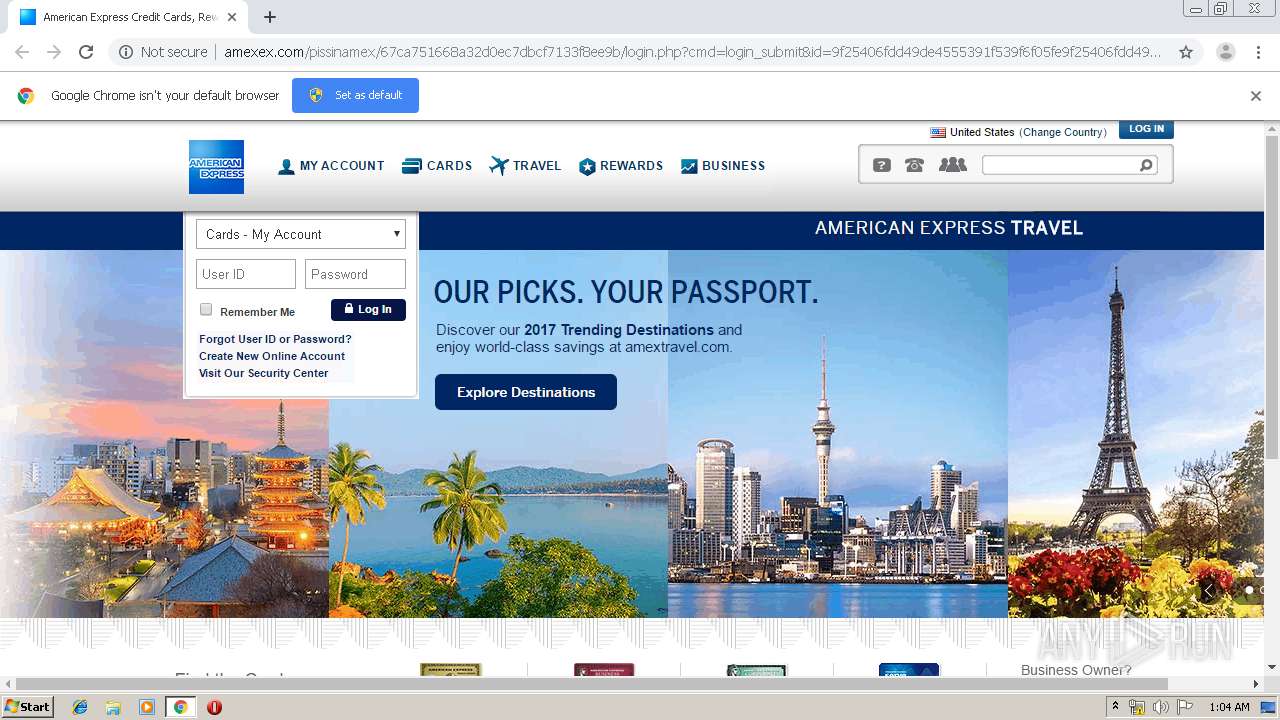
| URL: | http://r20.rs6.net/tn.jsp?f=001zqGIEUwJBuLskGc9NTNe2r0XWFMaYFuGE2Nc9phFZyTXsmvdhubZ_pTuFjnbRqIWarE4mJkBUQ13_LfcNOdUaUKAJsgvdSYNYJwdKUpSB2LoW6HCAZ1dHzDv8BWpAWls41aj30lx2CN3oQ3h8HZcvUYzQlcZFI8_&c=EhNEWK4-SoWED9Ftg86-GixghVl2OEnuXRr46bWMrAidNAEq-NRBBA==&ch=TOxRAi2SA5MEdK7yd7G_KMzRKQ0wJNK477PwSmMJJfJ45sMnTmEMsA== |
| Full analysis: | https://app.any.run/tasks/a07f2d99-8317-49da-90b8-223db79c0af1 |
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2019, 00:03:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D1217071A4245EB5B0500108A86A842D |
| SHA1: | 8E0E5687F26268D8CE4B688F32980508E51A12AC |
| SHA256: | E0EB20C7B5817974432122495B272019A1858B63042E092E6B96F85C74E3A195 |
| SSDEEP: | 6:CMXVBTmf7GXDtcvDbPbJkFwzsIXXiyJWfWj493eyu0Kod5cRBKmcxS2rgoWk1:ZFBqWROfPFSwscSdy499vcWR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 3280)
- chrome.exe (PID: 2756)
Application launched itself
- chrome.exe (PID: 3280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x7056a9d0,0x7056a9e0,0x7056a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2600 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1546789295348881139,5972475117698104143,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15107149811155069212 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1546789295348881139,5972475117698104143,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4269407647949230443 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1546789295348881139,5972475117698104143,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11039408200779801303 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1546789295348881139,5972475117698104143,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4850320223849567230 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1546789295348881139,5972475117698104143,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1278341489168640430 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1546789295348881139,5972475117698104143,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6795468903396329766 --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1546789295348881139,5972475117698104143,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4718119649084679341 --mojo-platform-channel-handle=3544 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://r20.rs6.net/tn.jsp?f=001zqGIEUwJBuLskGc9NTNe2r0XWFMaYFuGE2Nc9phFZyTXsmvdhubZ_pTuFjnbRqIWarE4mJkBUQ13_LfcNOdUaUKAJsgvdSYNYJwdKUpSB2LoW6HCAZ1dHzDv8BWpAWls41aj30lx2CN3oQ3h8HZcvUYzQlcZFI8_&c=EhNEWK4-SoWED9Ftg86-GixghVl2OEnuXRr46bWMrAidNAEq-NRBBA==&ch=TOxRAi2SA5MEdK7yd7G_KMzRKQ0wJNK477PwSmMJJfJ45sMnTmEMsA==" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
579
Read events
512
Write events
63
Delete events
4
Modification events
| (PID) Process: | (624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3280-13214966617799875 |
Value: 259 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
8
Text files
57
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\39273ef1-282a-4ad6-a3b2-f531f5d6da27.tmp | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFf46d3.TMP | text | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf46d3.TMP | text | |
MD5:— | SHA256:— | |||
| 3280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf46d3.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
20
DNS requests
11
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
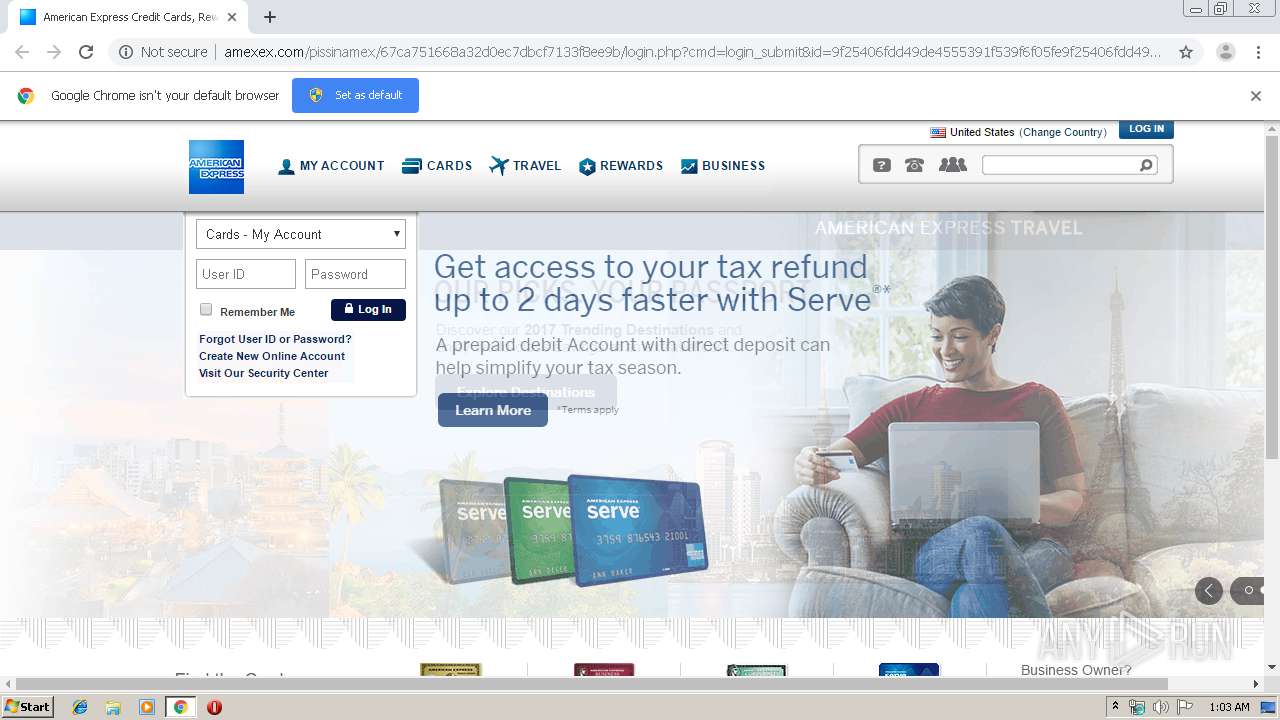
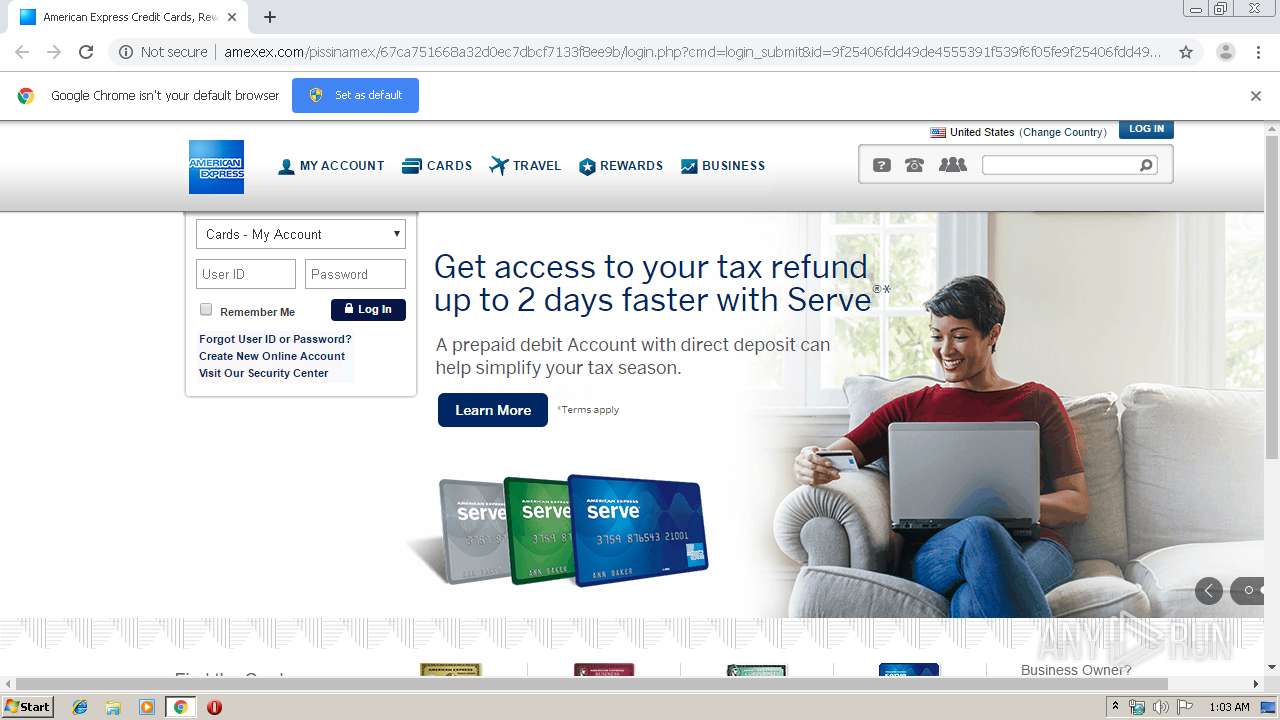
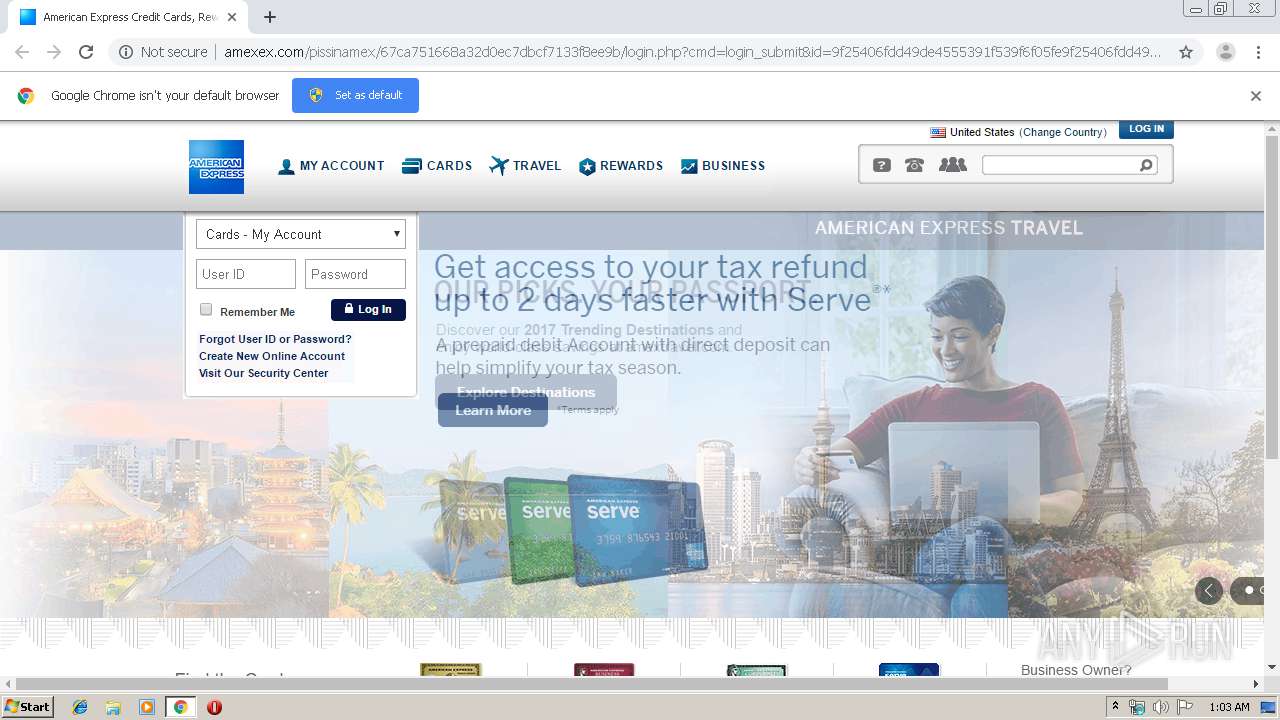
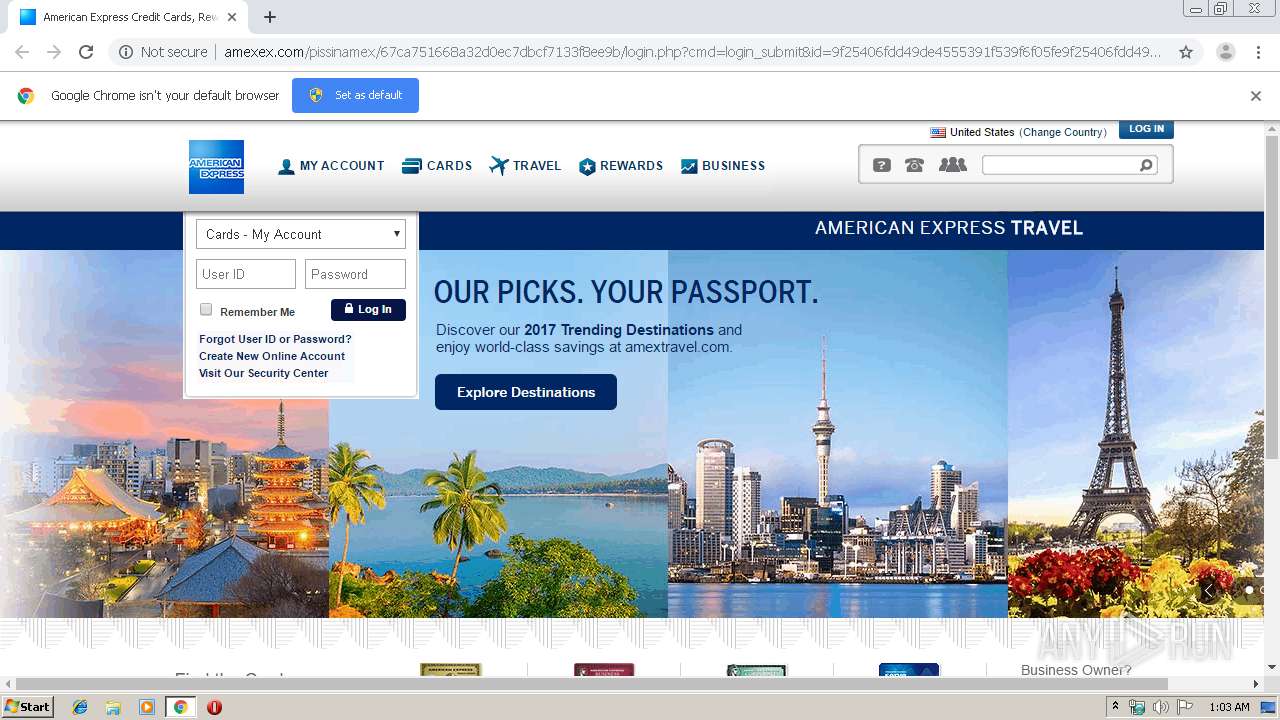
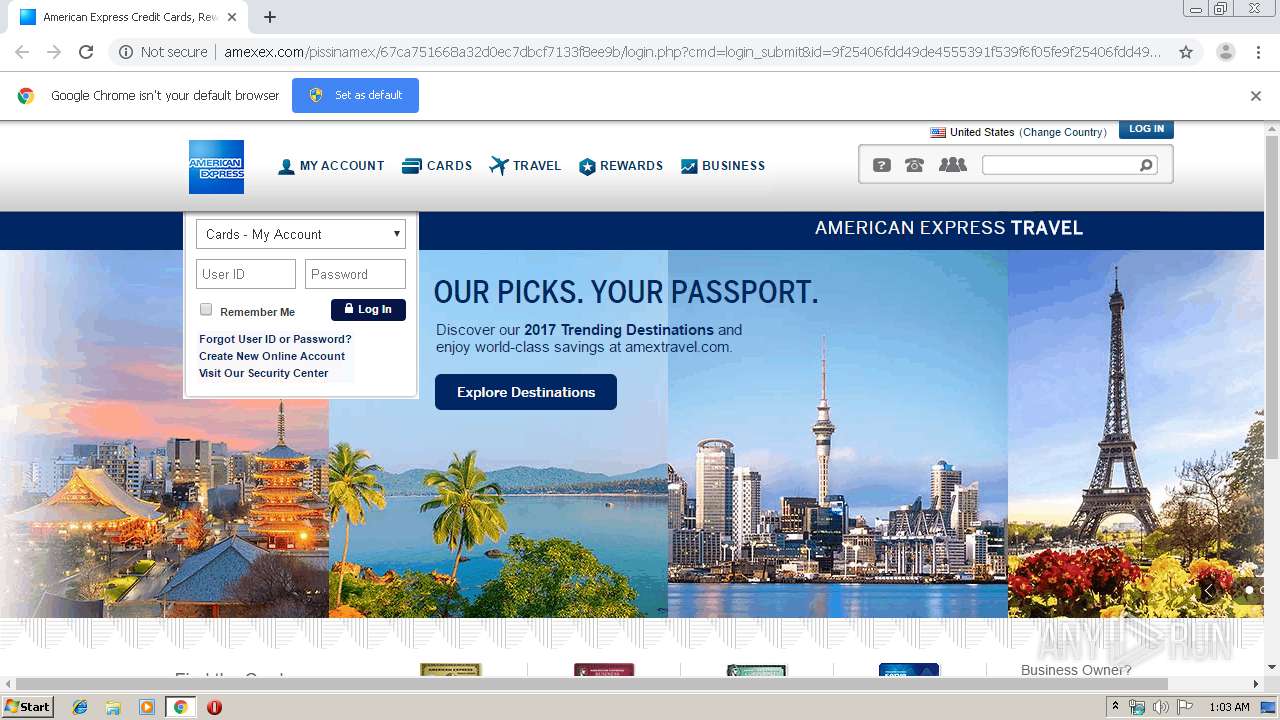
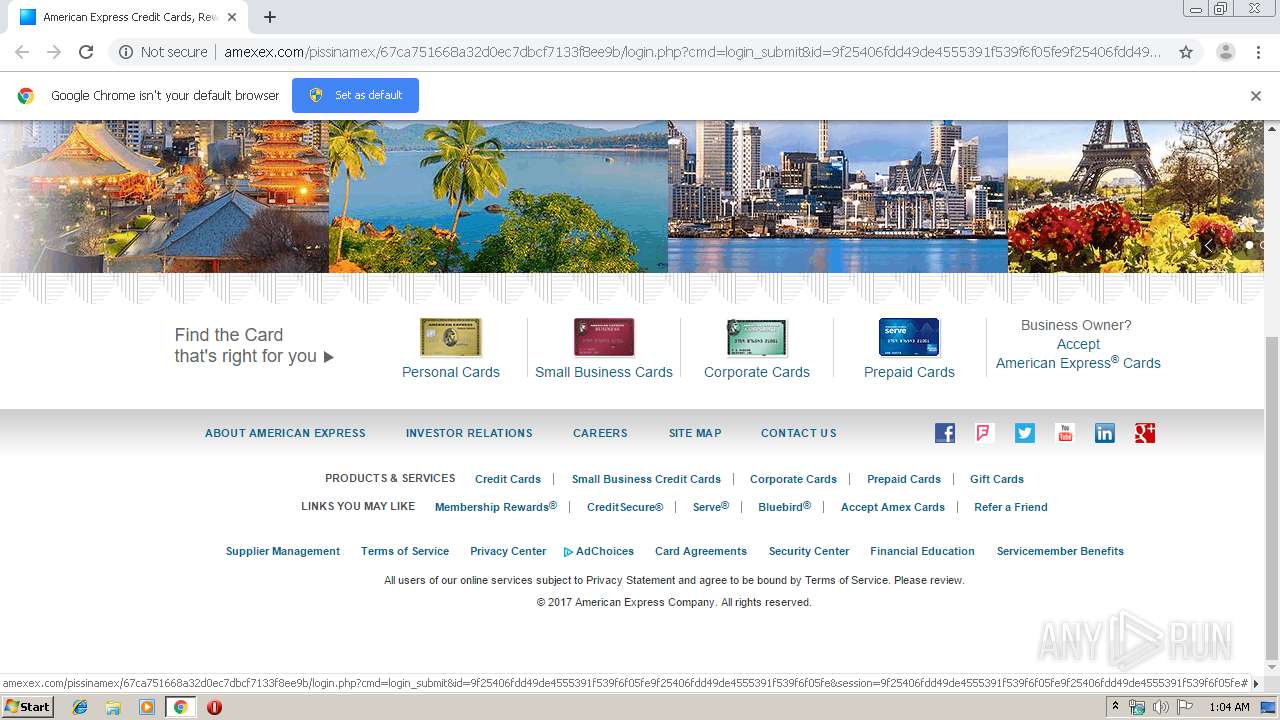
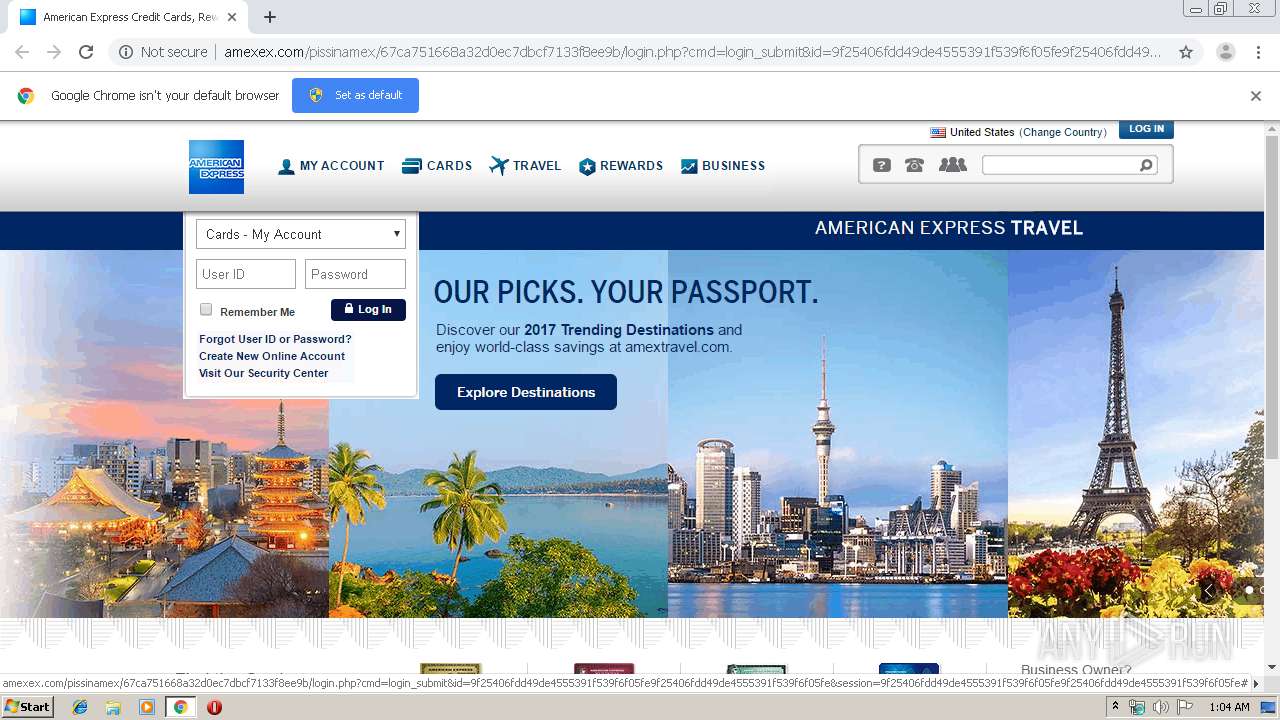
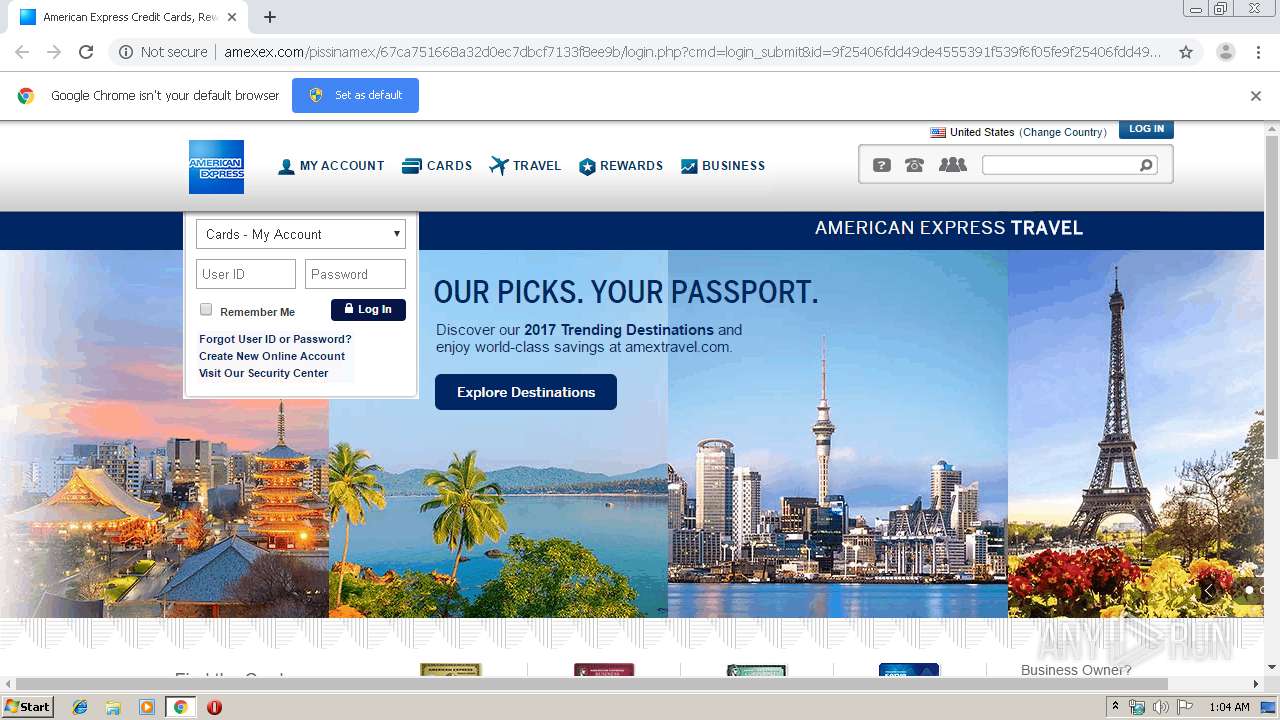
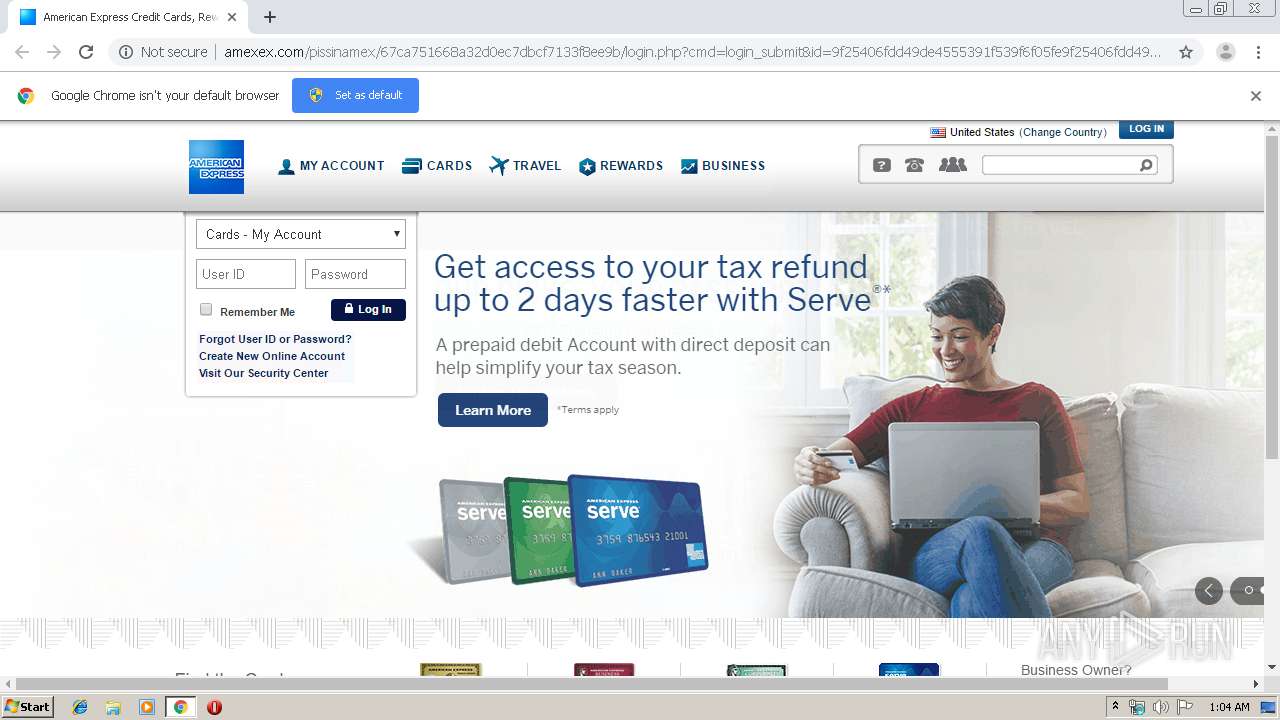
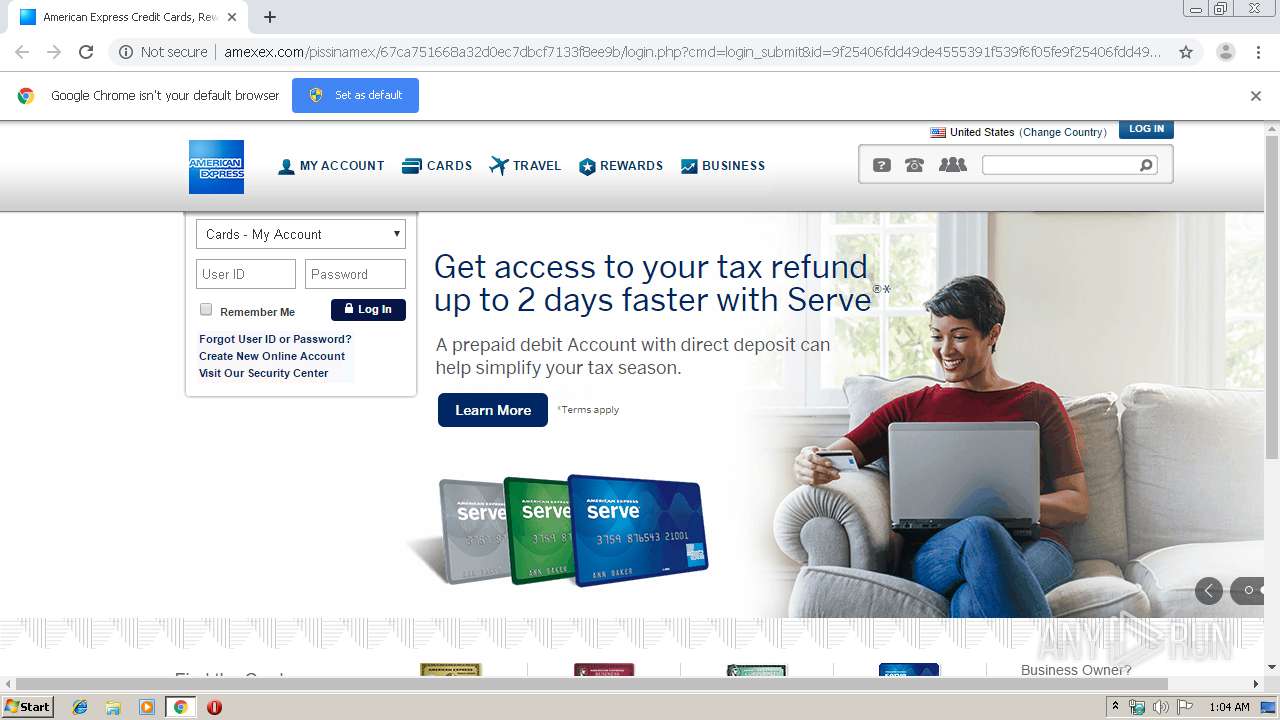
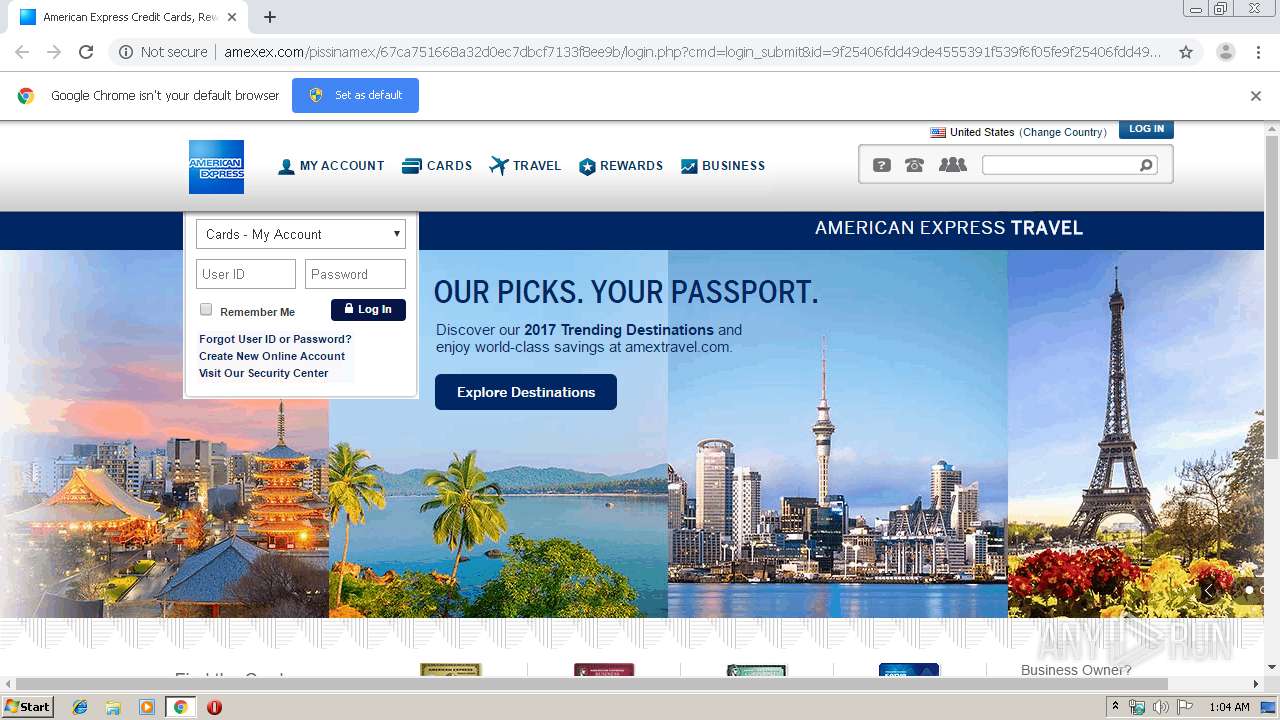
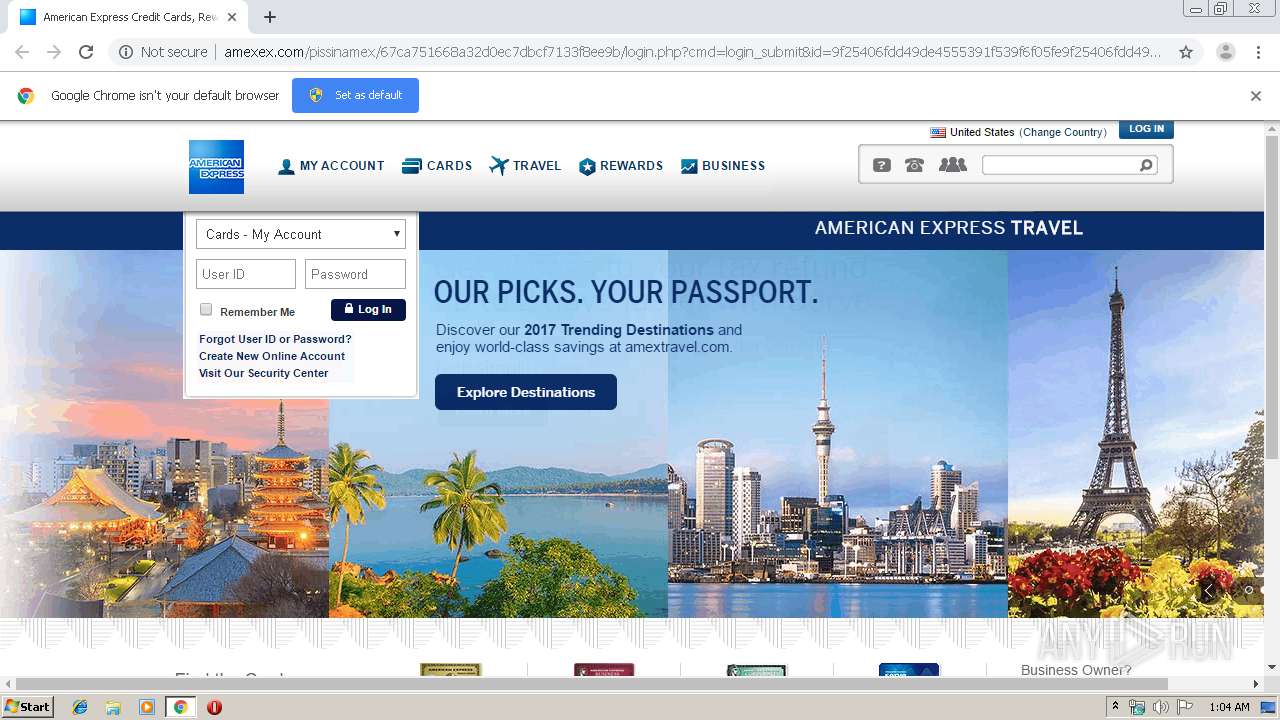
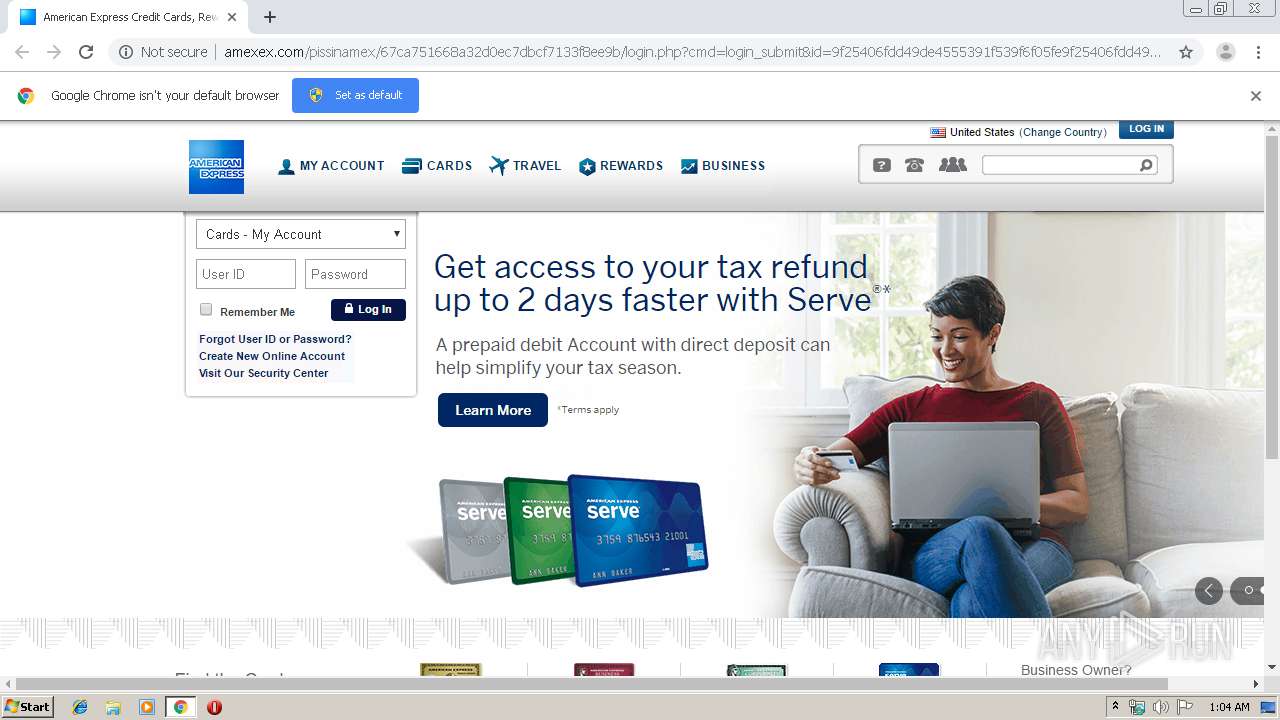
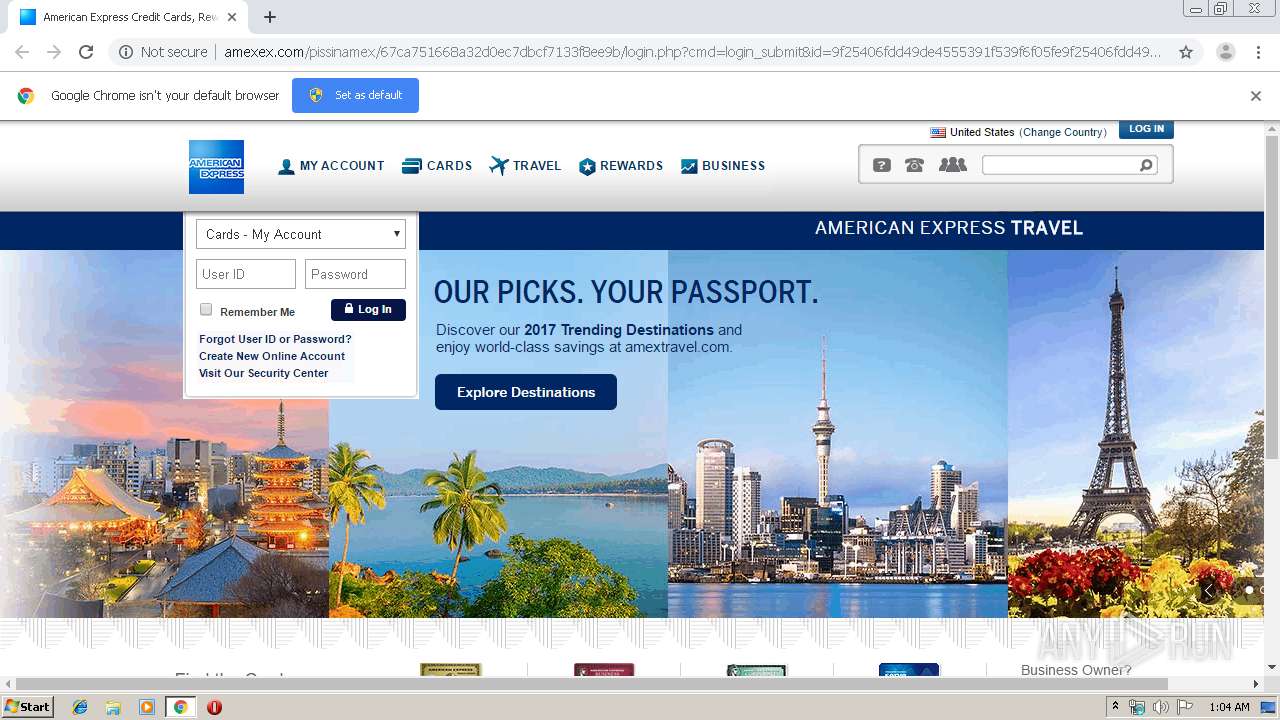
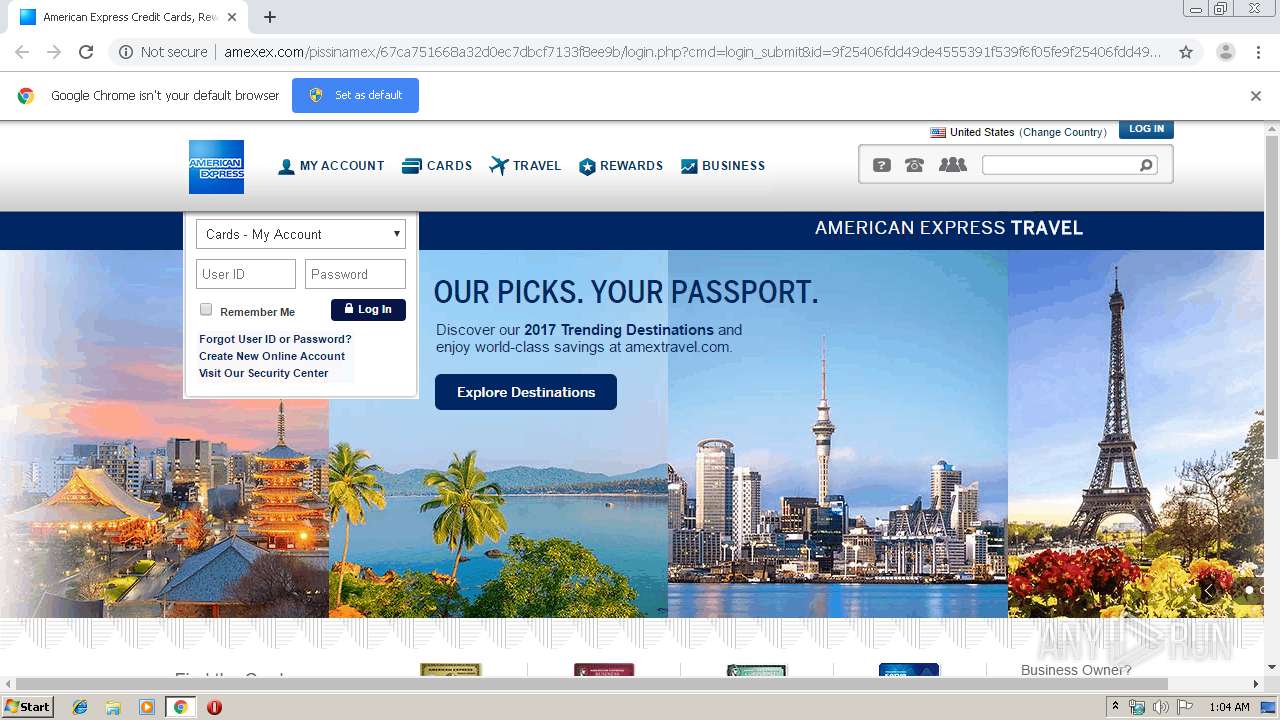
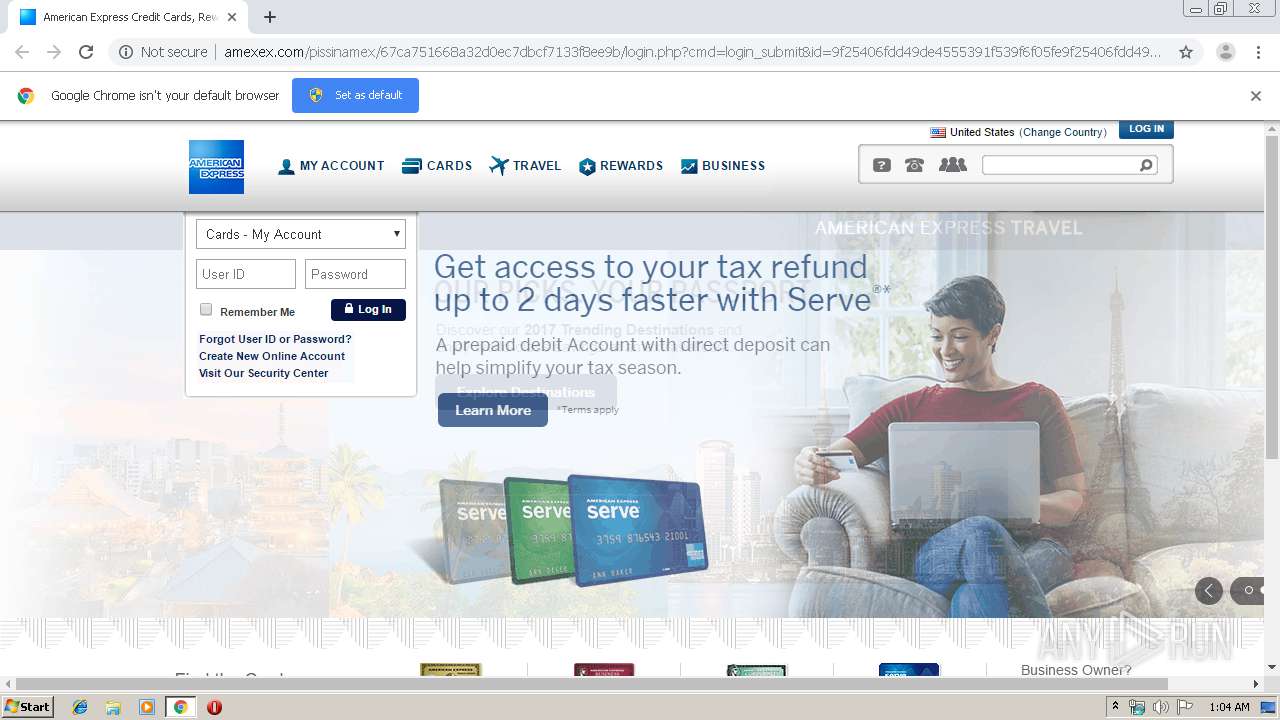
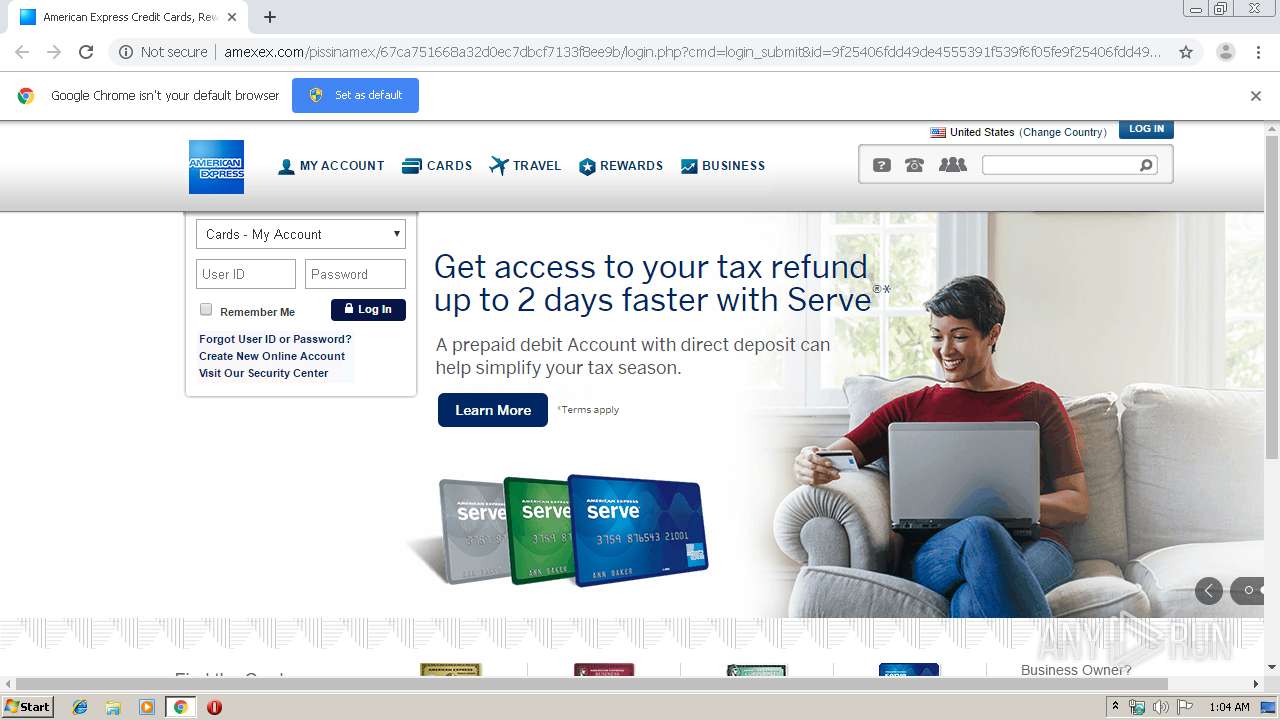
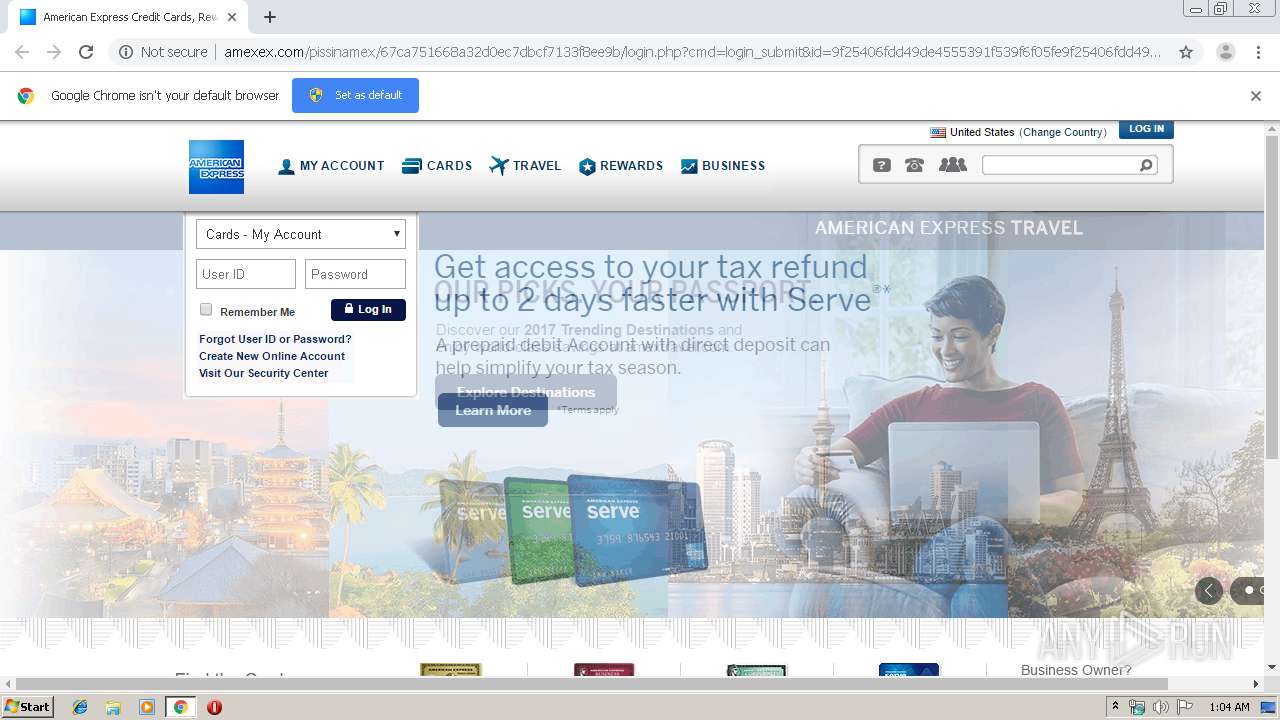
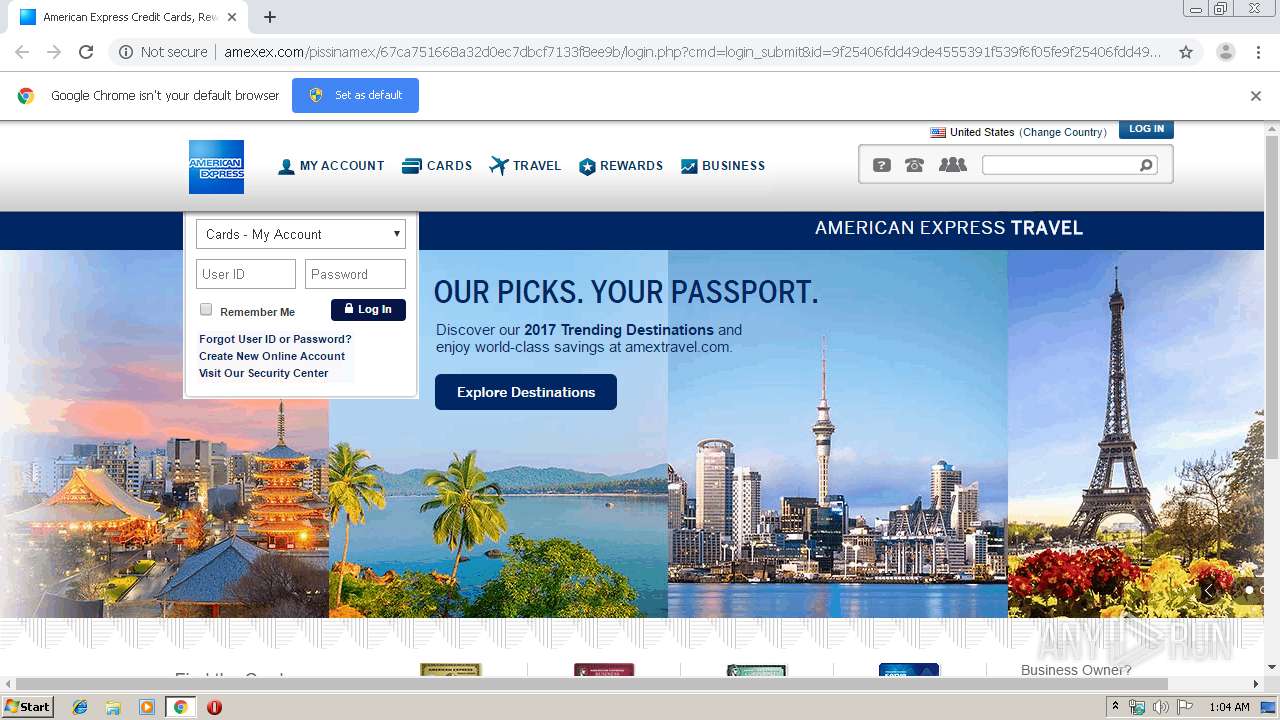
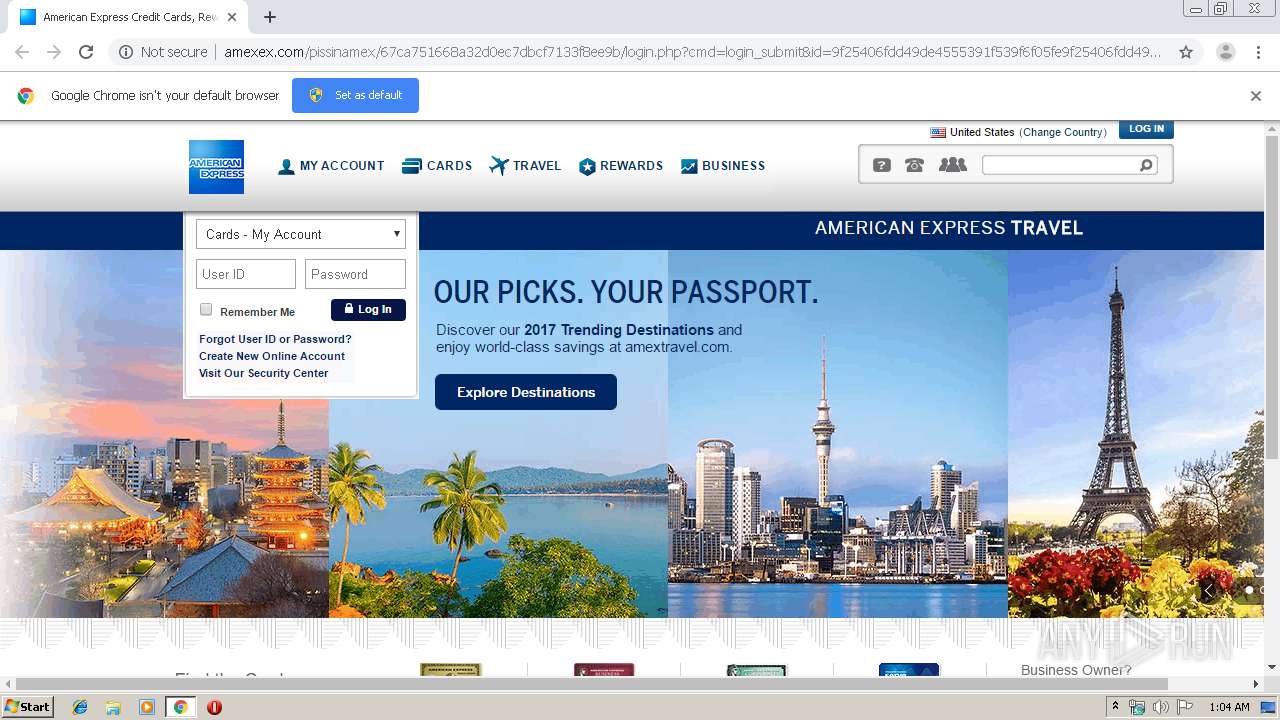
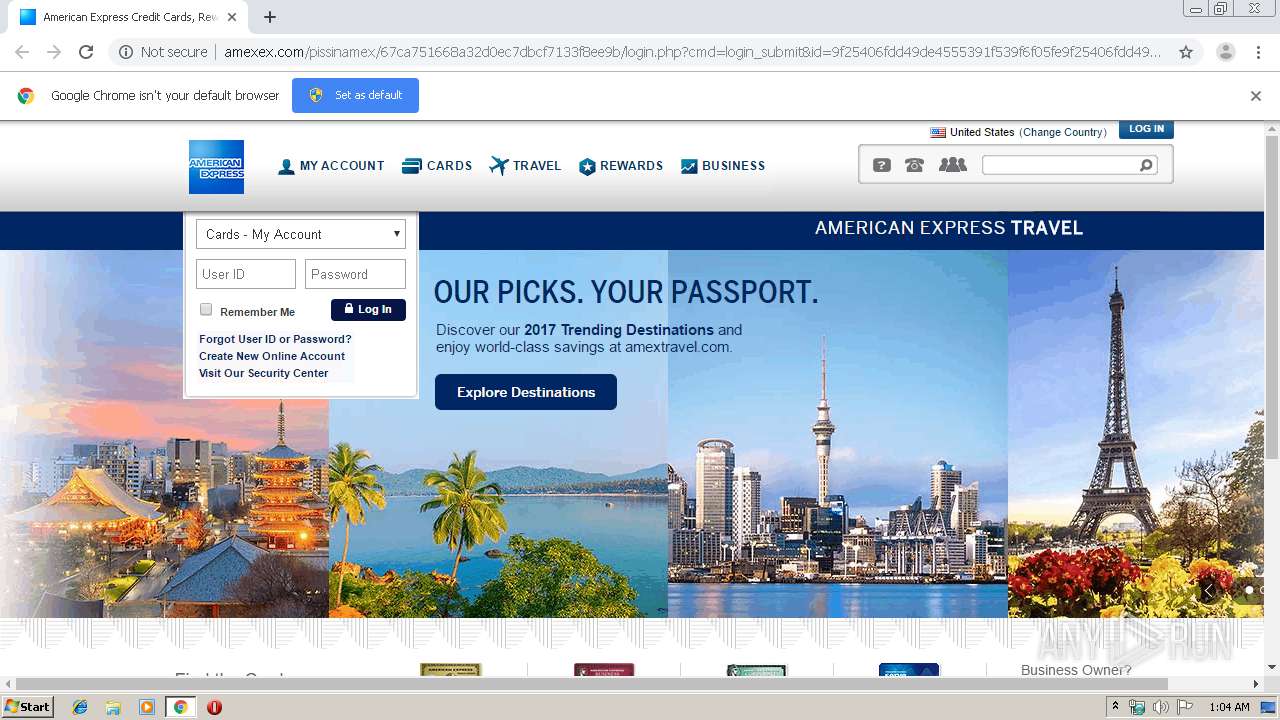
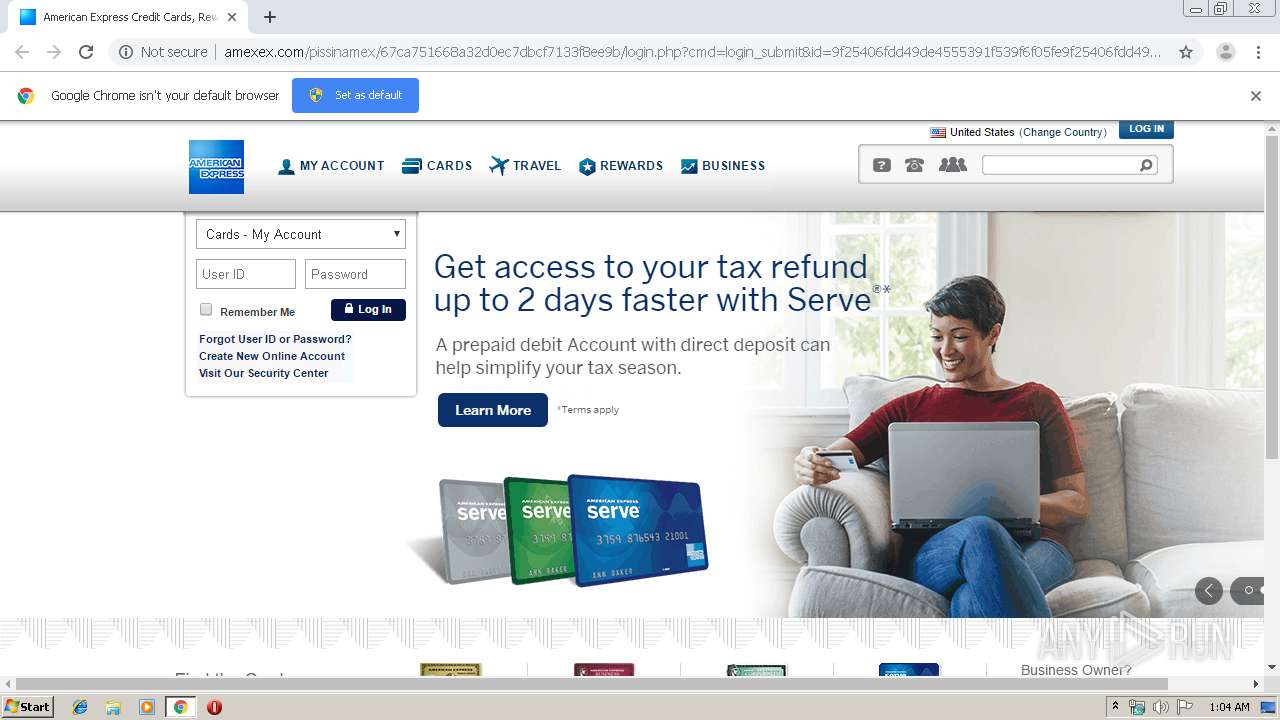
2756 | chrome.exe | GET | 302 | 143.95.235.141:80 | http://amexex.com/pissinamex/ | US | — | — | malicious |
2756 | chrome.exe | GET | 302 | 208.75.122.11:80 | http://r20.rs6.net/tn.jsp?f=001zqGIEUwJBuLskGc9NTNe2r0XWFMaYFuGE2Nc9phFZyTXsmvdhubZ_pTuFjnbRqIWarE4mJkBUQ13_LfcNOdUaUKAJsgvdSYNYJwdKUpSB2LoW6HCAZ1dHzDv8BWpAWls41aj30lx2CN3oQ3h8HZcvUYzQlcZFI8_&c=EhNEWK4-SoWED9Ftg86-GixghVl2OEnuXRr46bWMrAidNAEq-NRBBA==&ch=TOxRAi2SA5MEdK7yd7G_KMzRKQ0wJNK477PwSmMJJfJ45sMnTmEMsA== | US | — | — | whitelisted |
2756 | chrome.exe | GET | 301 | 143.95.235.141:80 | http://amexex.com/pissinamex/67ca751668a32d0ec7dbcf7133f8ee9b | US | html | 330 b | malicious |
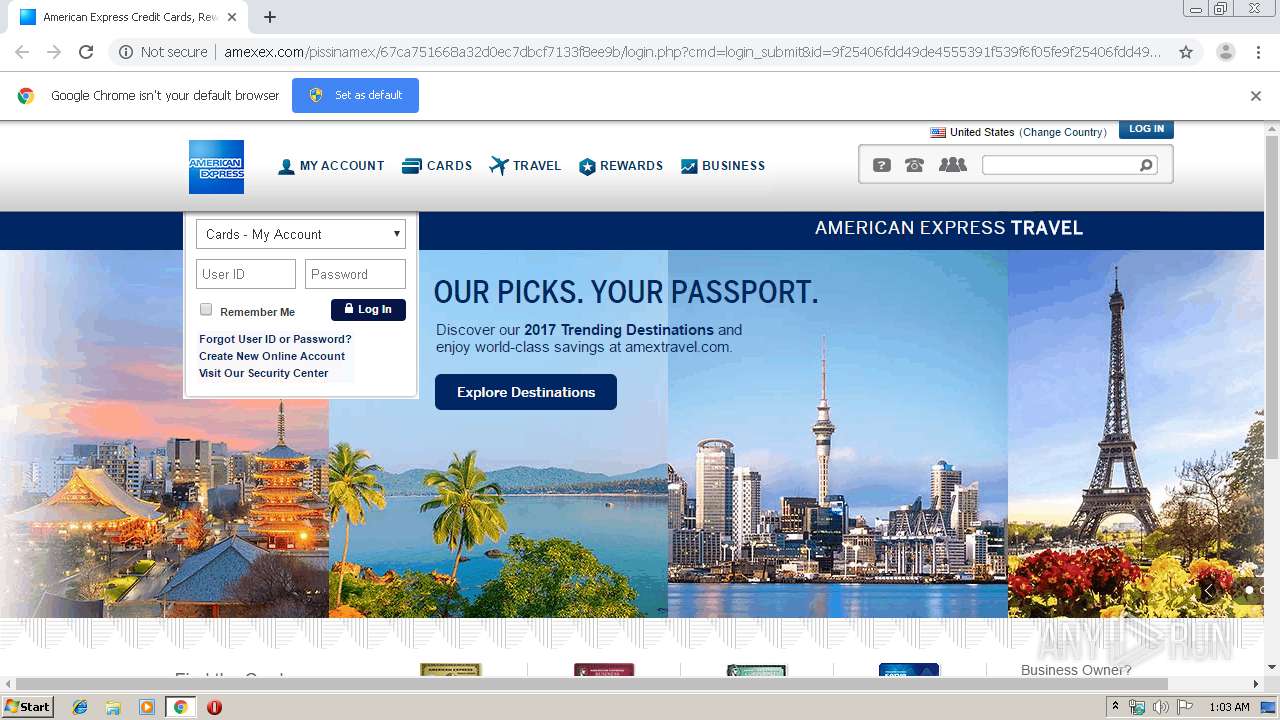
2756 | chrome.exe | GET | 200 | 143.95.235.141:80 | http://amexex.com/pissinamex/67ca751668a32d0ec7dbcf7133f8ee9b/images/ae3.png | US | image | 4.42 Kb | malicious |
2756 | chrome.exe | GET | 302 | 143.95.235.141:80 | http://amexex.com/pissinamex/67ca751668a32d0ec7dbcf7133f8ee9b/ | US | html | 330 b | malicious |
2756 | chrome.exe | GET | 200 | 143.95.235.141:80 | http://amexex.com/pissinamex/67ca751668a32d0ec7dbcf7133f8ee9b/login.php?cmd=login_submit&id=9f25406fdd49de4555391f539f6f05fe9f25406fdd49de4555391f539f6f05fe&session=9f25406fdd49de4555391f539f6f05fe9f25406fdd49de4555391f539f6f05fe | US | html | 1.79 Kb | malicious |
2756 | chrome.exe | GET | 200 | 151.101.12.193:80 | http://i.imgur.com/QmO2YTC.gif | US | image | 4.79 Mb | malicious |
2756 | chrome.exe | GET | 200 | 143.95.235.141:80 | http://amexex.com/pissinamex/67ca751668a32d0ec7dbcf7133f8ee9b/images/ae4.png | US | image | 7.13 Kb | malicious |
2756 | chrome.exe | GET | 200 | 143.95.235.141:80 | http://amexex.com/pissinamex/67ca751668a32d0ec7dbcf7133f8ee9b/images/ae10.png | US | image | 1.91 Kb | malicious |
2756 | chrome.exe | GET | 200 | 143.95.235.141:80 | http://amexex.com/pissinamex/67ca751668a32d0ec7dbcf7133f8ee9b/images/ae1.png | US | image | 16.5 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2756 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 151.101.12.193:80 | i.imgur.com | Fastly | US | malicious |
2756 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 208.75.122.11:80 | r20.rs6.net | Constant Contact, Inc | US | suspicious |
2756 | chrome.exe | 143.95.235.141:80 | 001-001-045.com | Colo4, LLC | US | malicious |
2756 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
r20.rs6.net |
| whitelisted |
accounts.google.com |
| shared |
001-001-045.com |
| malicious |
www.google.com |
| malicious |
amexex.com |
| malicious |
i.imgur.com |
| malicious |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2756 | chrome.exe | A Network Trojan was detected | ET WEB_CLIENT Possible Phishing Redirect Feb 09 2016 |
2756 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Google Drive Phishing Landing |
2756 | chrome.exe | A Network Trojan was detected | ET INFO Suspicious HTML Decimal Obfuscated Title - Possible Phishing Landing Apr 19 2017 |
2756 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Chalbhai Phishing Landing Oct 23 2017 |
2756 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Chalbhai (Multibrand) Phishing Landing 2018-05-10 |
2756 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Chalbhai Phishing Landing 2018-08-30 |