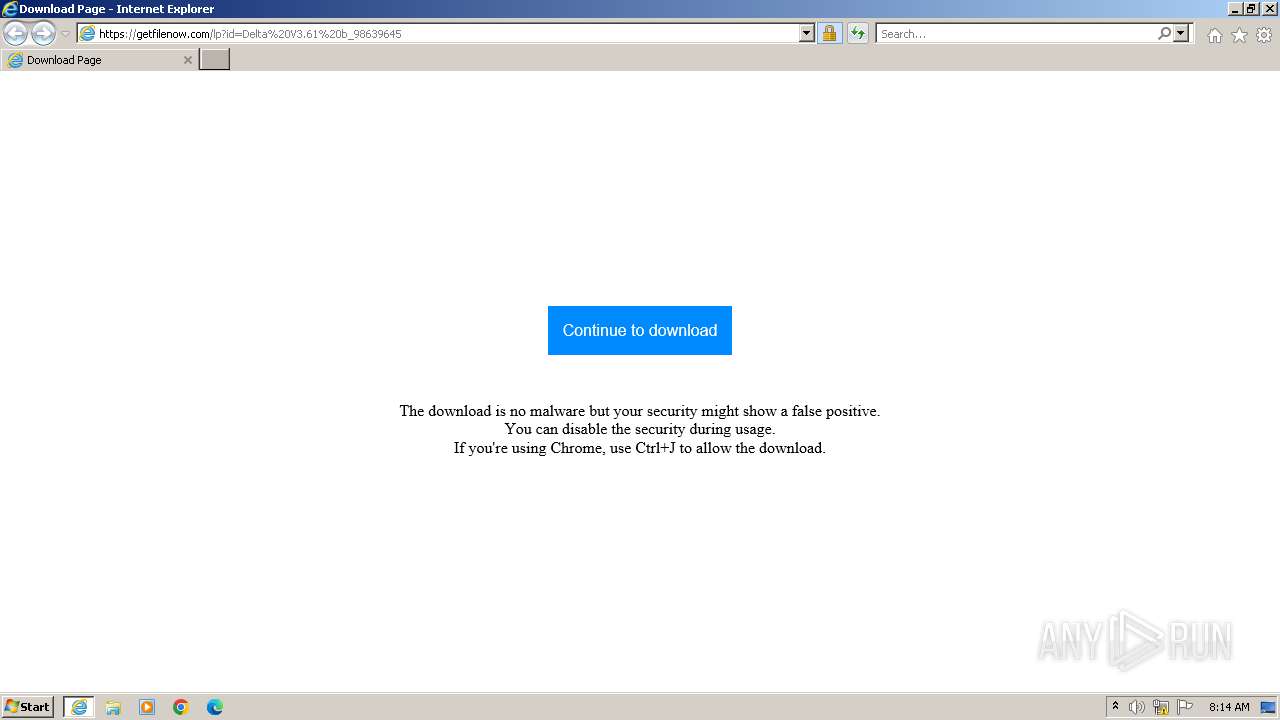
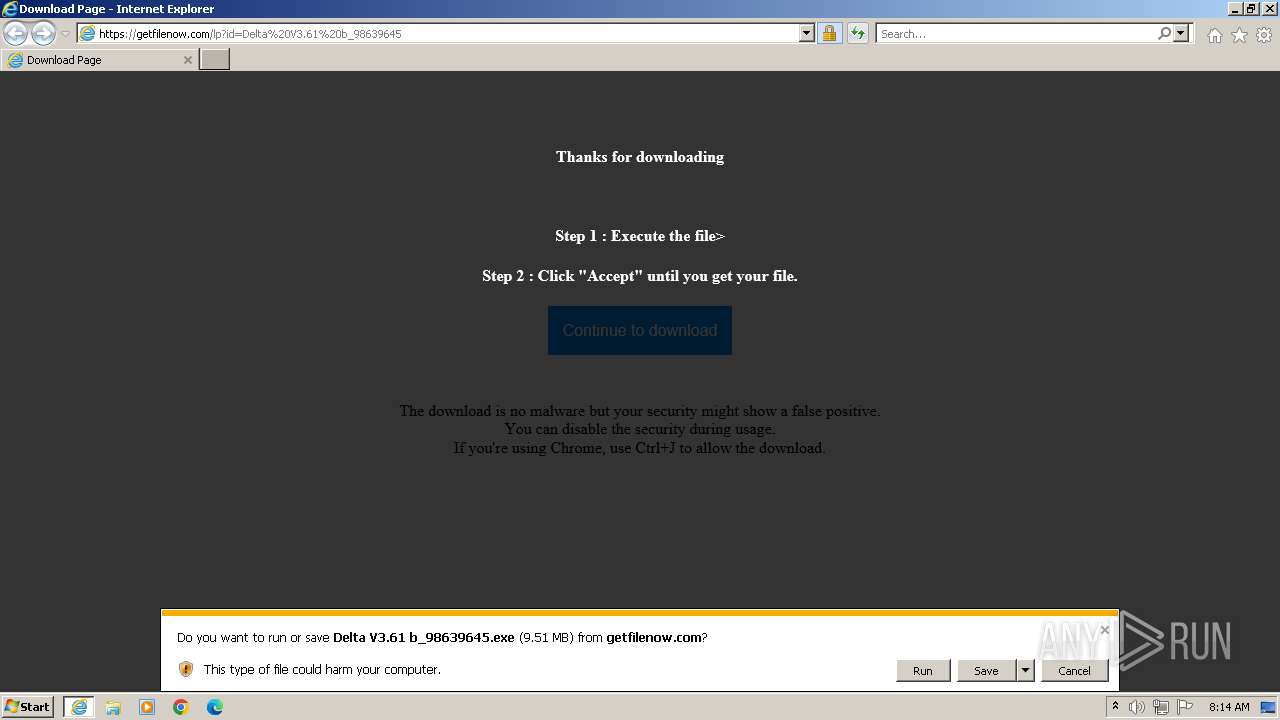
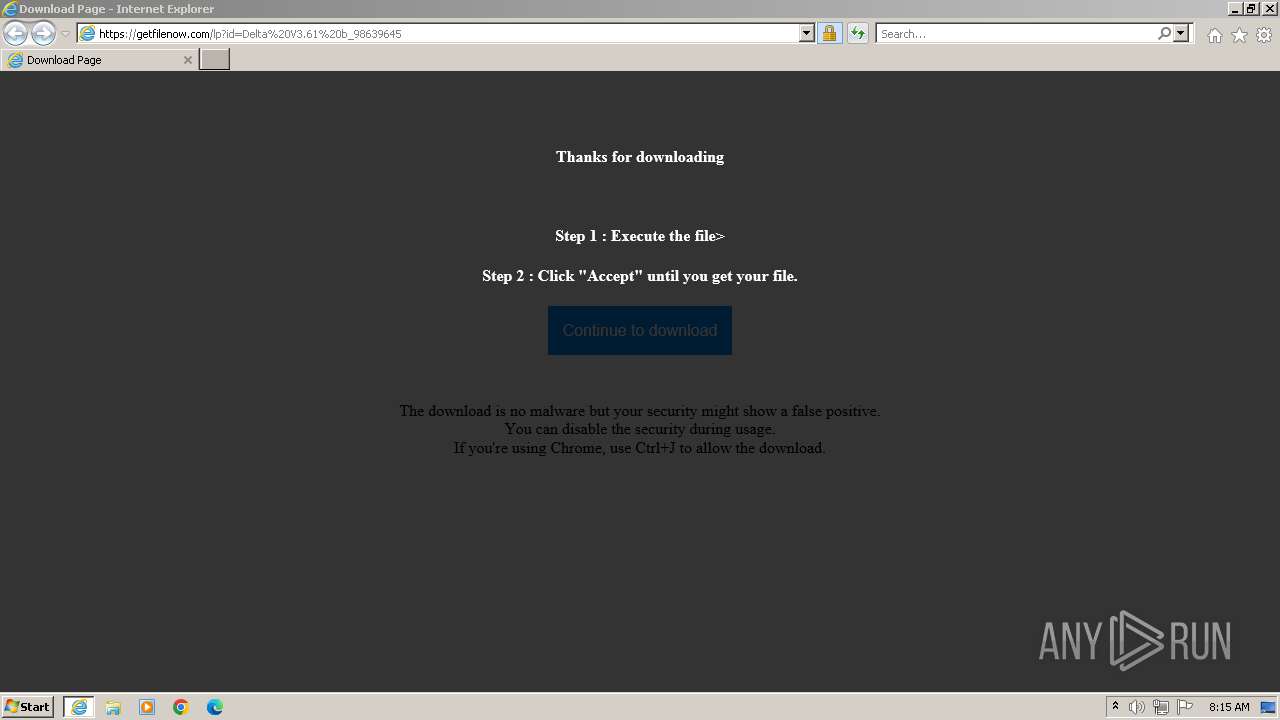
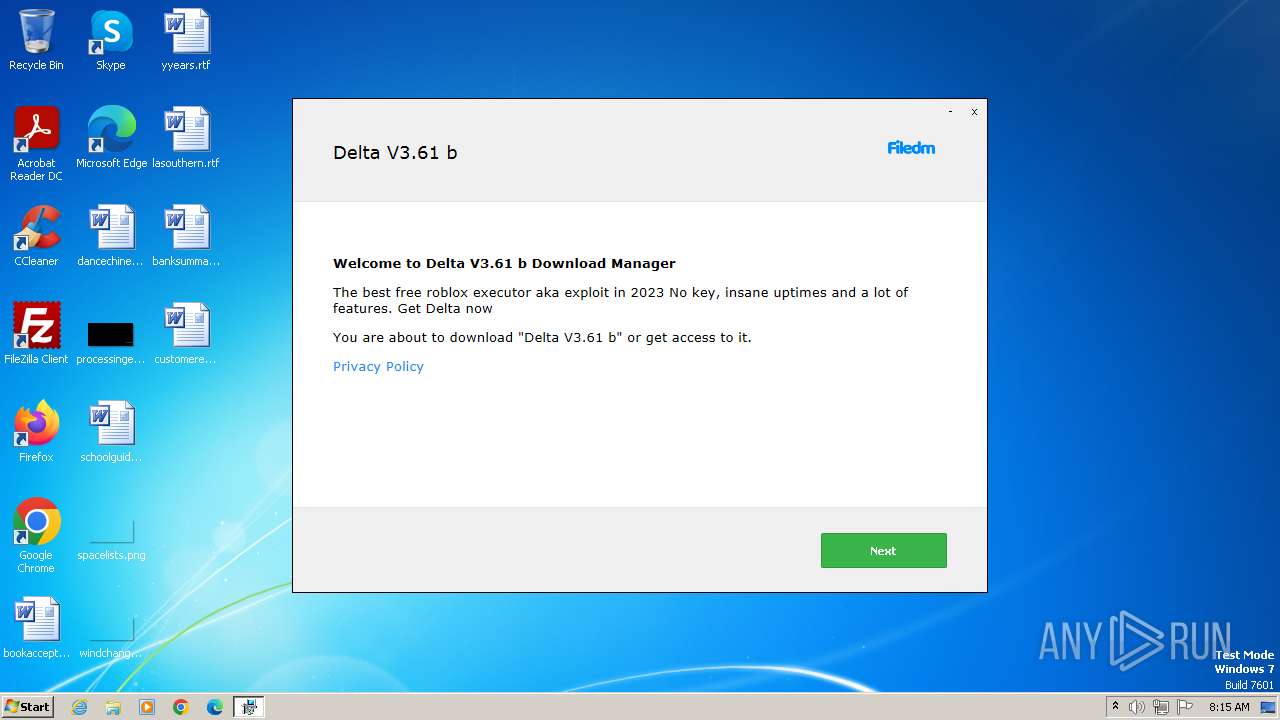
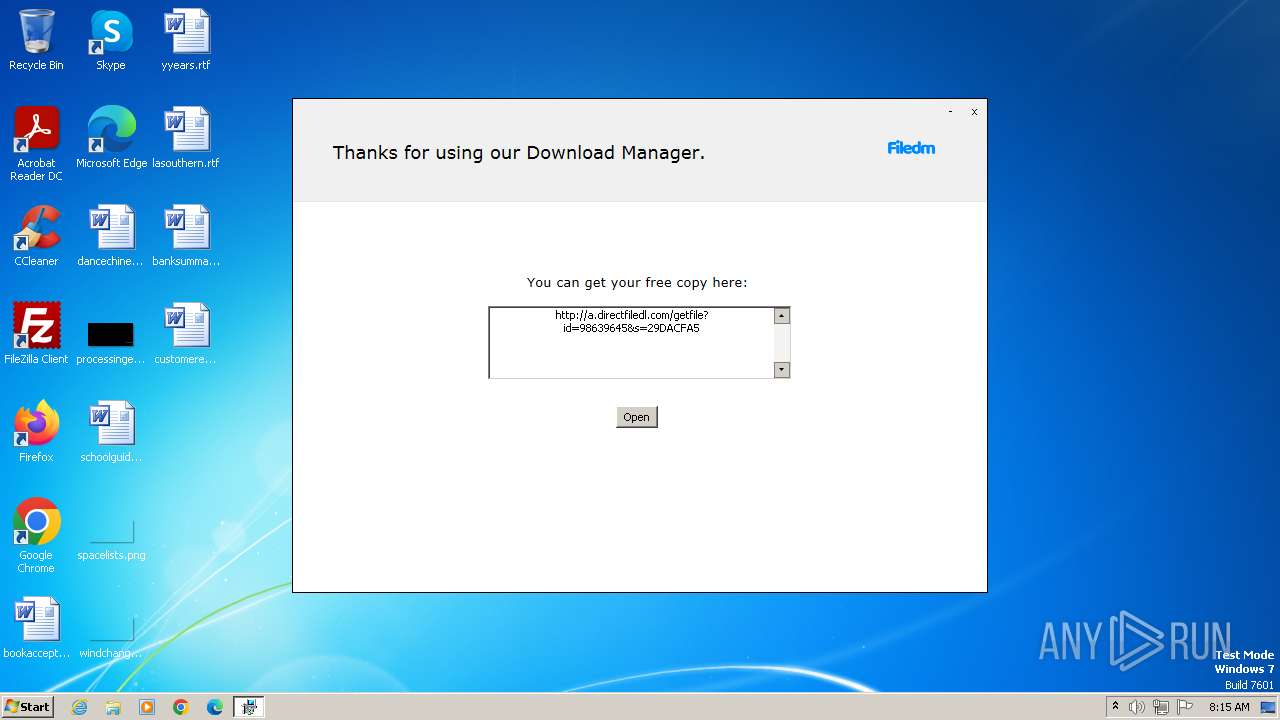
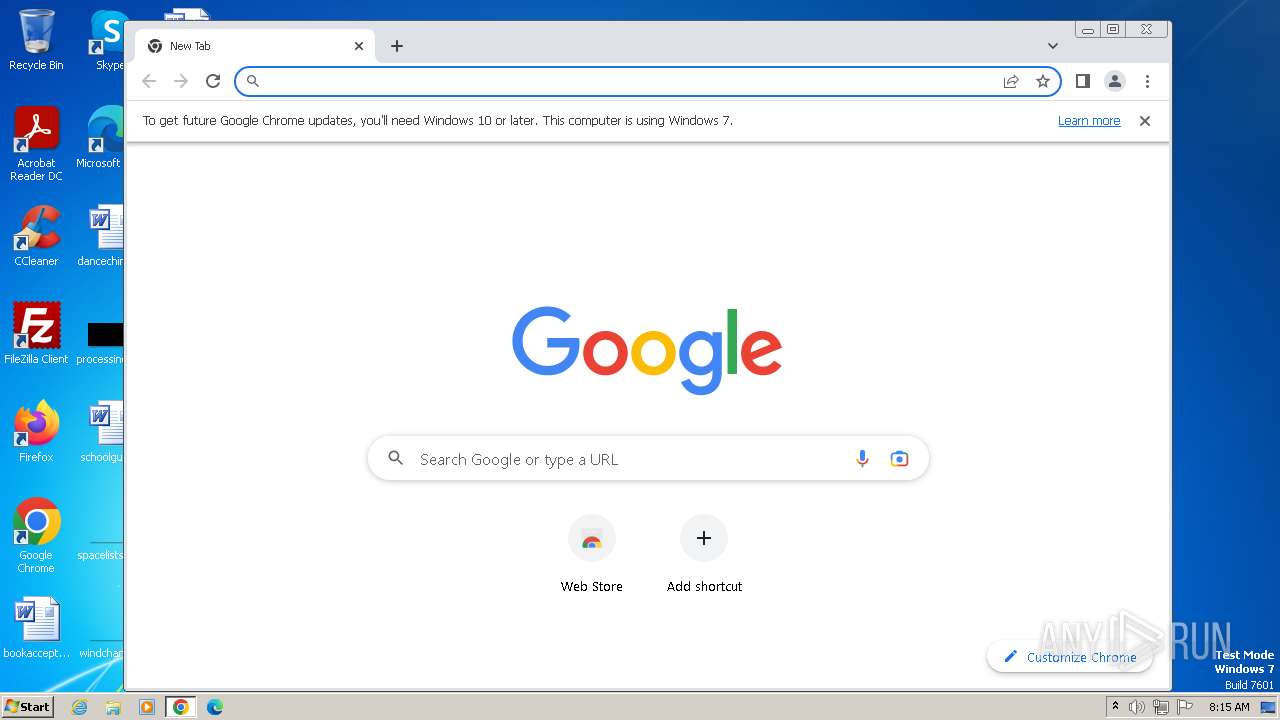
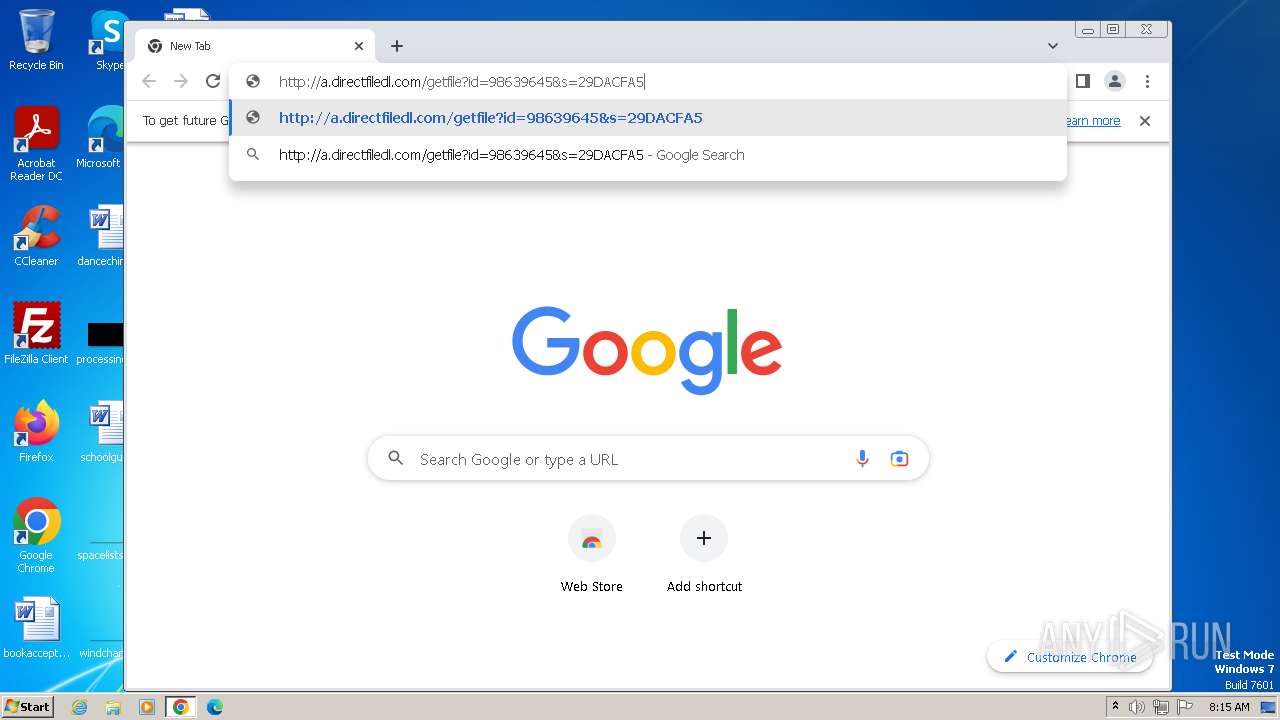
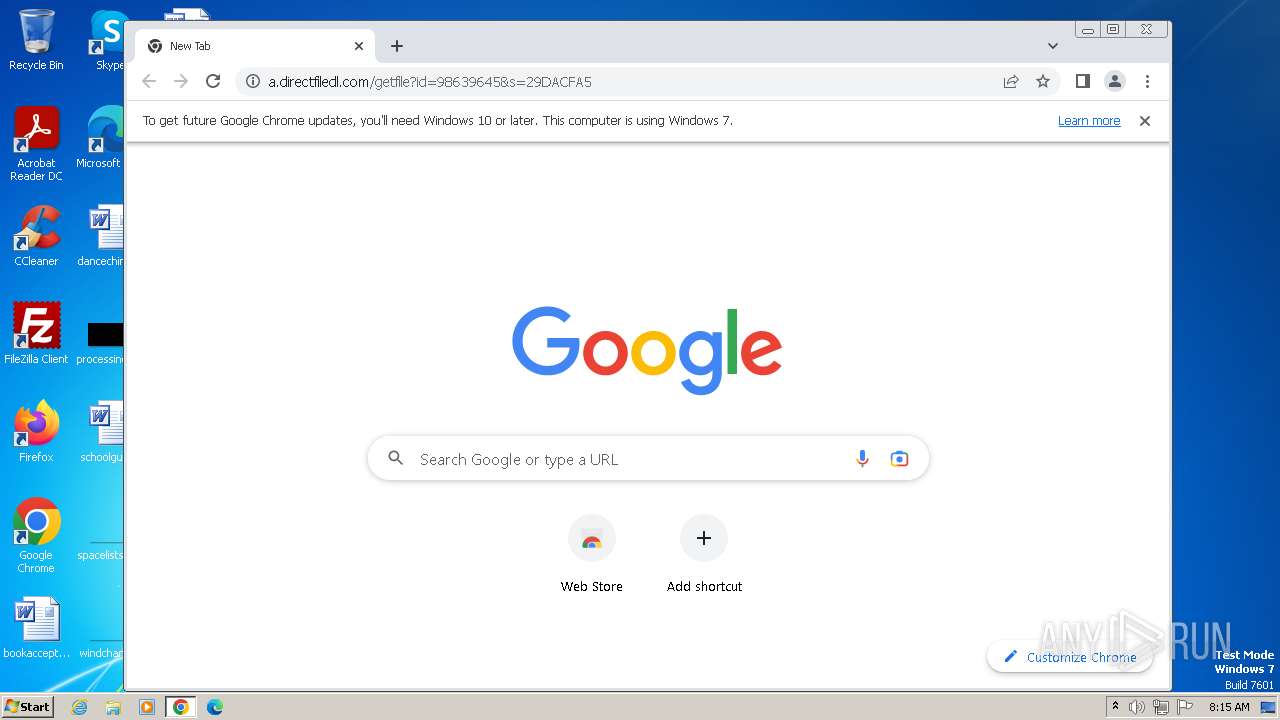
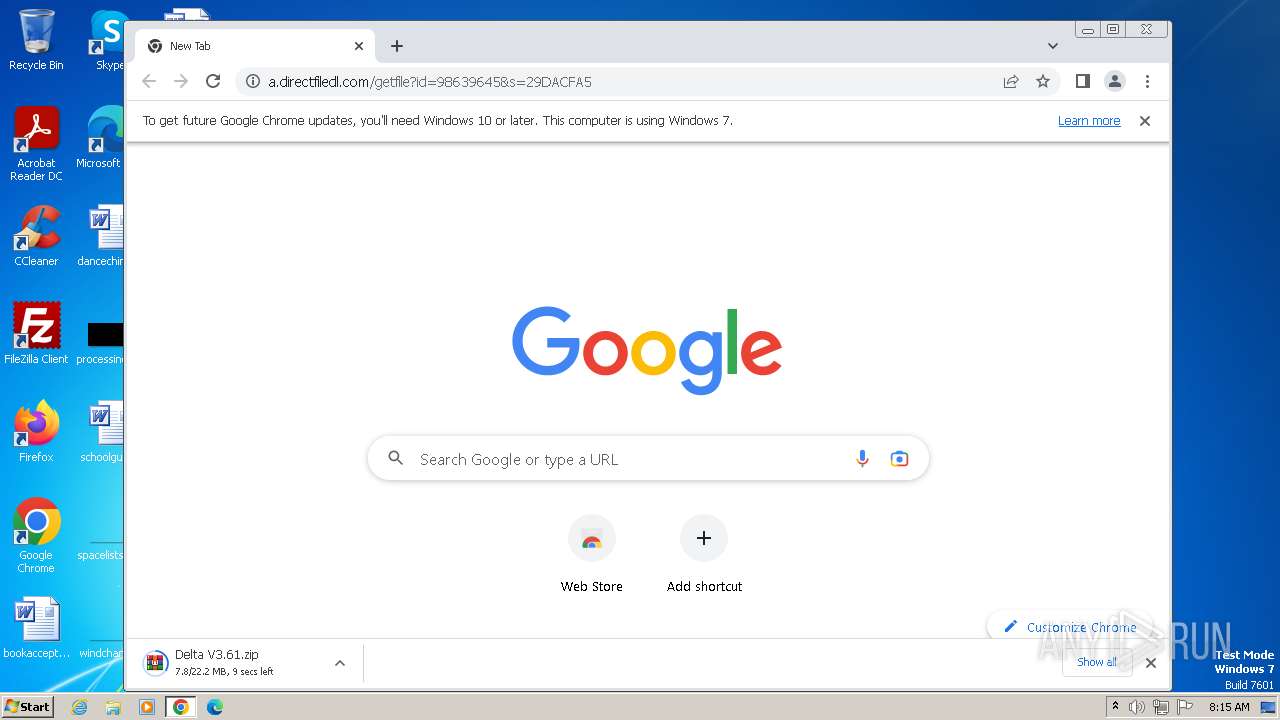
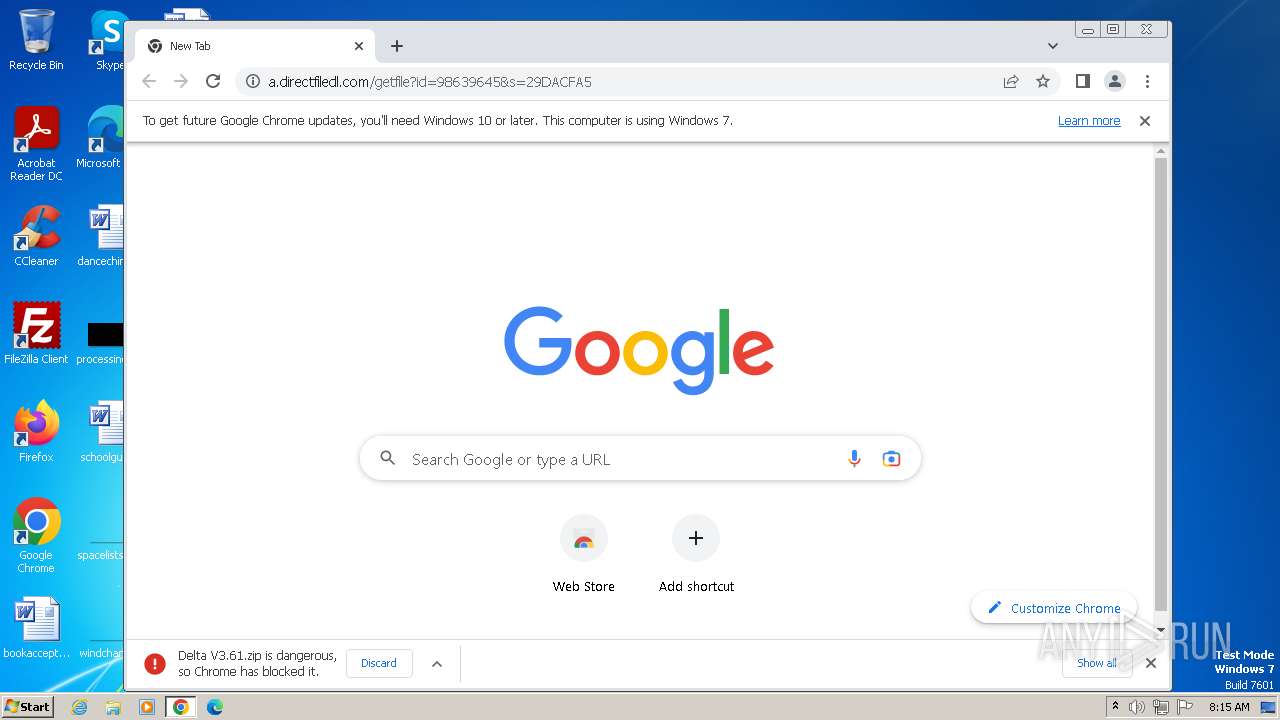
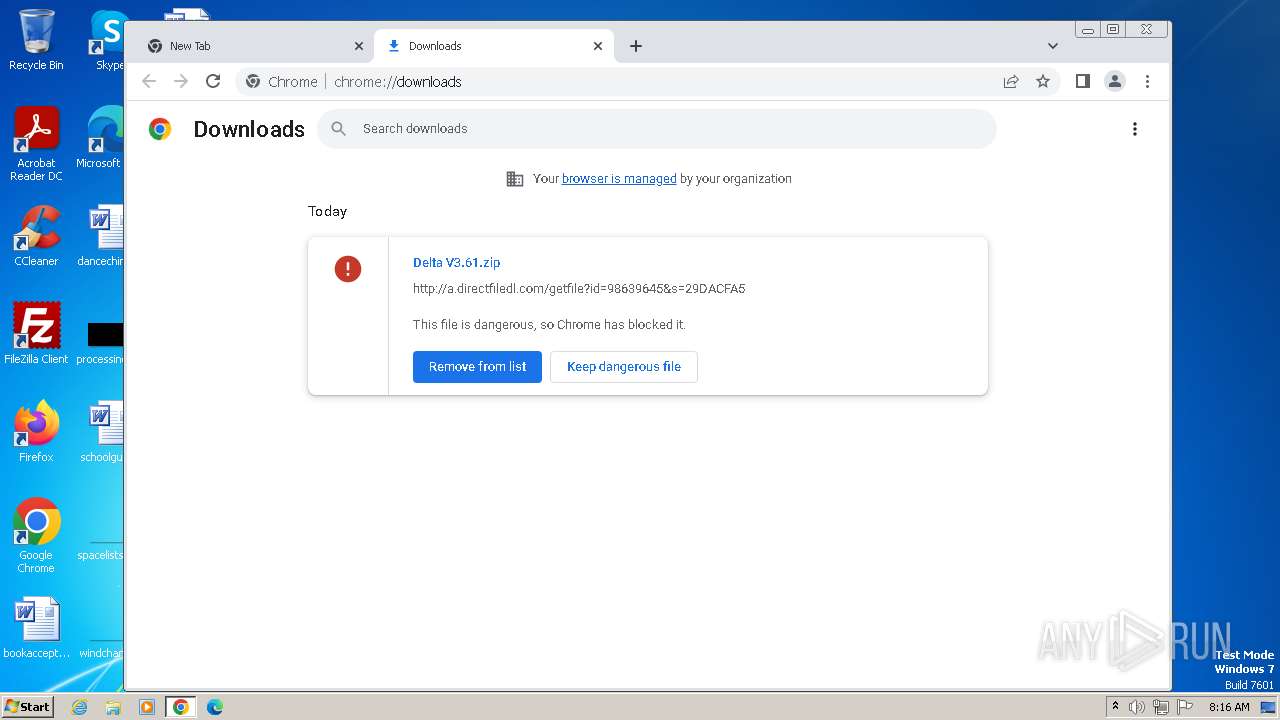
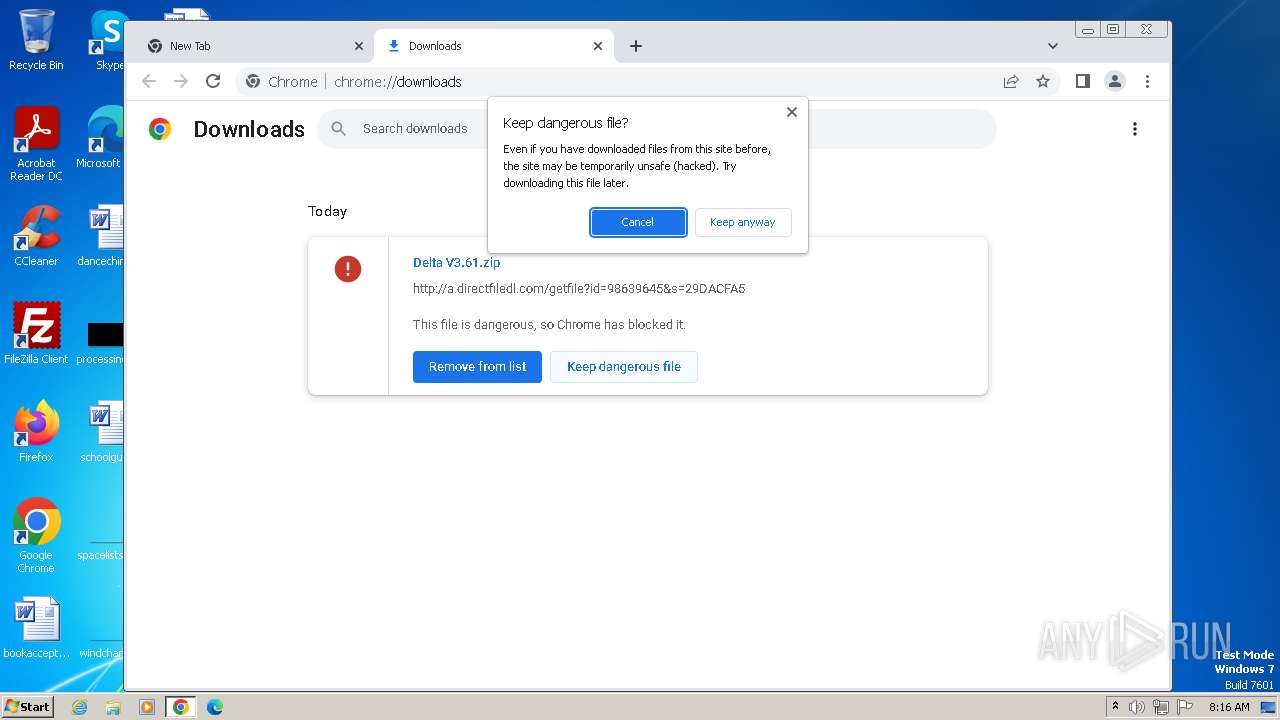
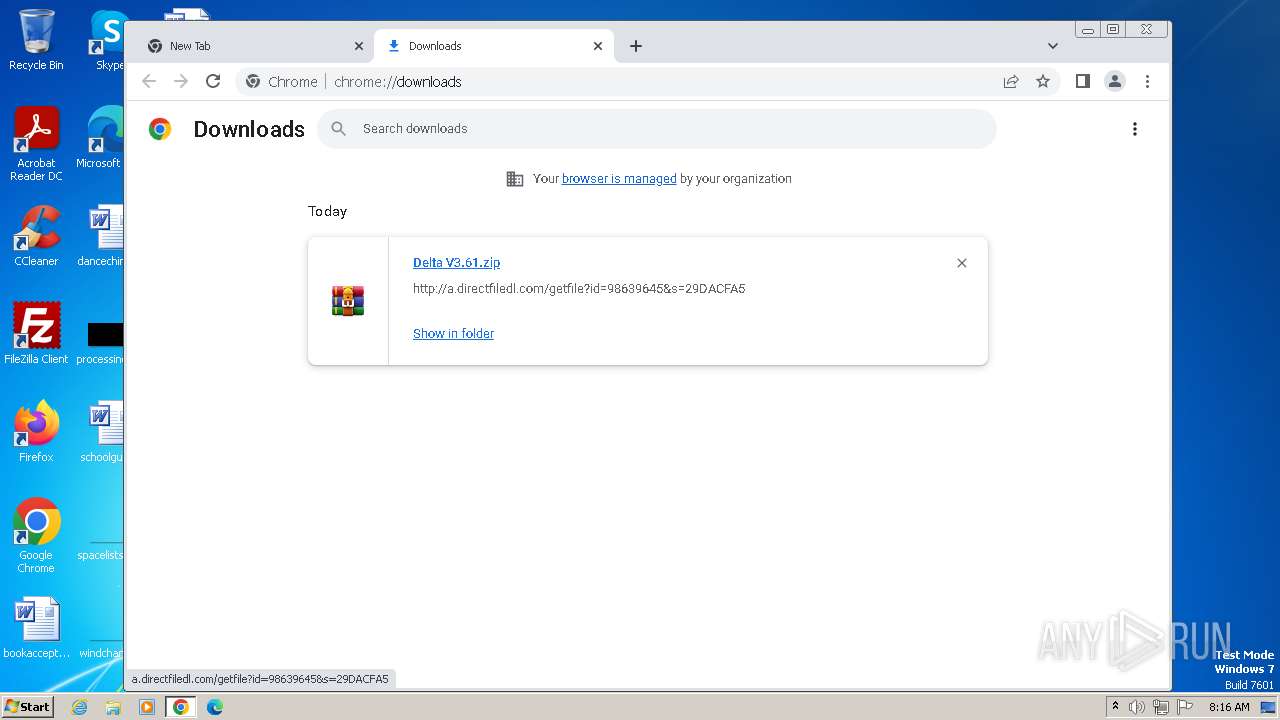
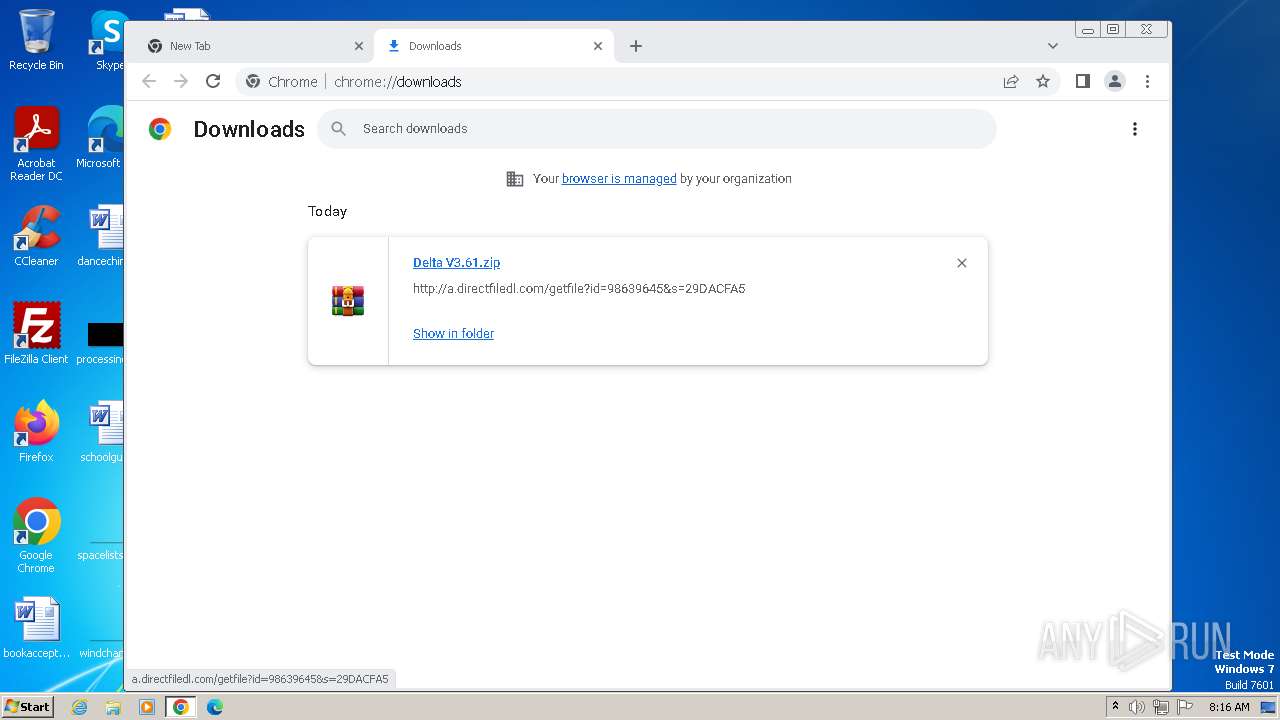
| URL: | https://getfilenow.com/lp?id=Delta%20V3.61%20b_98639645 |
| Full analysis: | https://app.any.run/tasks/fc9b6a3b-5dd7-422f-87d2-908b553513c3 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2023, 08:14:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 6180BFE6B146E0DF9879E30E5957CC650FBCE363 |
| SHA256: | E0E8CC26D94F59048B22C8248618236F0EED5153B869DBABA084AE0B3AC4DF5D |
| SSDEEP: | 3:N8hOAtRaAMAfyZXVBWi2:201BG |
MALICIOUS
Drops the executable file immediately after the start
- Delta V3.61 b_98639645.exe (PID: 2364)
- setup98639645.exe (PID: 644)
- setup98639645.exe (PID: 3644)
Actions looks like stealing of personal data
- setup98639645.exe (PID: 644)
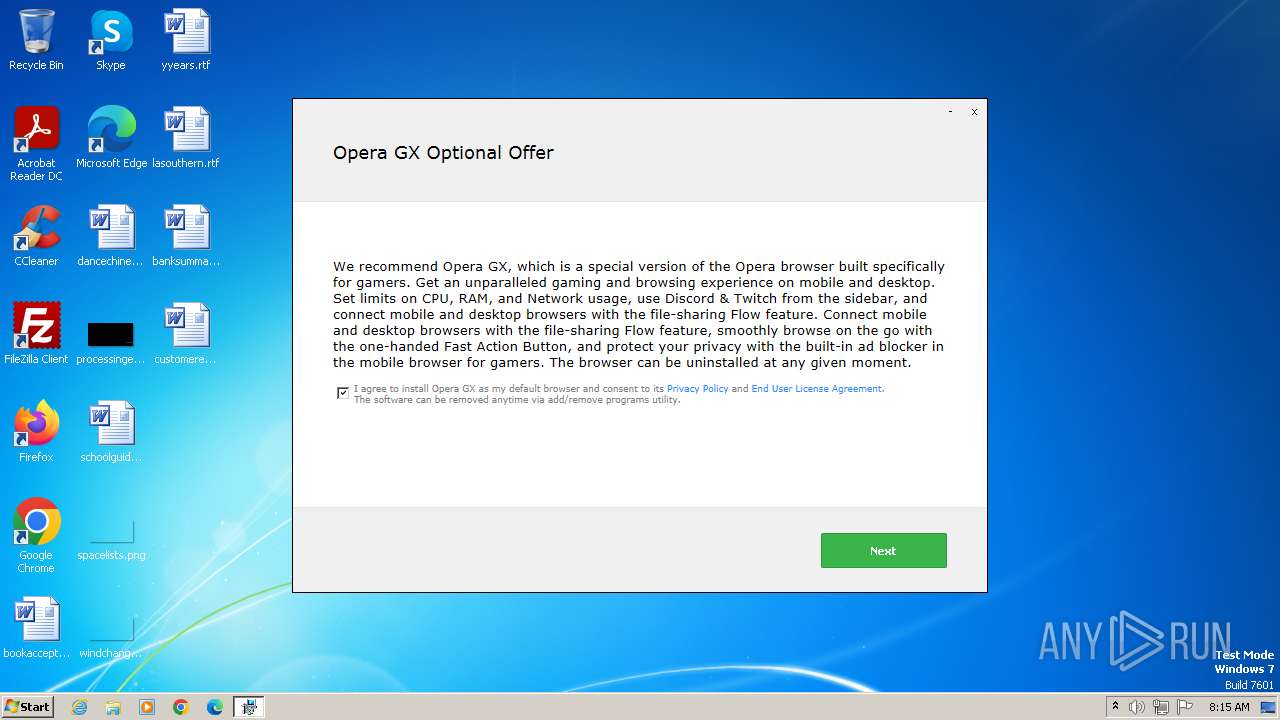
SUSPICIOUS
Reads the Internet Settings
- Delta V3.61 b_98639645.exe (PID: 2364)
- setup98639645.exe (PID: 644)
- setup98639645.exe (PID: 3644)
- Delta.exe (PID: 2092)
- Delta.exe (PID: 2052)
Checks Windows Trust Settings
- Delta V3.61 b_98639645.exe (PID: 2364)
- setup98639645.exe (PID: 644)
Reads settings of System Certificates
- Delta V3.61 b_98639645.exe (PID: 2364)
- setup98639645.exe (PID: 644)
Reads security settings of Internet Explorer
- Delta V3.61 b_98639645.exe (PID: 2364)
- setup98639645.exe (PID: 644)
Process drops legitimate windows executable
- setup98639645.exe (PID: 644)
- setup98639645.exe (PID: 3644)
The process drops C-runtime libraries
- setup98639645.exe (PID: 644)
- setup98639645.exe (PID: 3644)
Reads the Windows owner or organization settings
- setup98639645.exe (PID: 644)
Adds/modifies Windows certificates
- Delta V3.61 b_98639645.exe (PID: 2364)
- iexplore.exe (PID: 948)
Starts CMD.EXE for commands execution
- setup98639645.exe (PID: 644)
Searches for installed software
- setup98639645.exe (PID: 644)
Executing commands from a ".bat" file
- setup98639645.exe (PID: 644)
The process creates files with name similar to system file names
- setup98639645.exe (PID: 3644)
- setup98639645.exe (PID: 644)
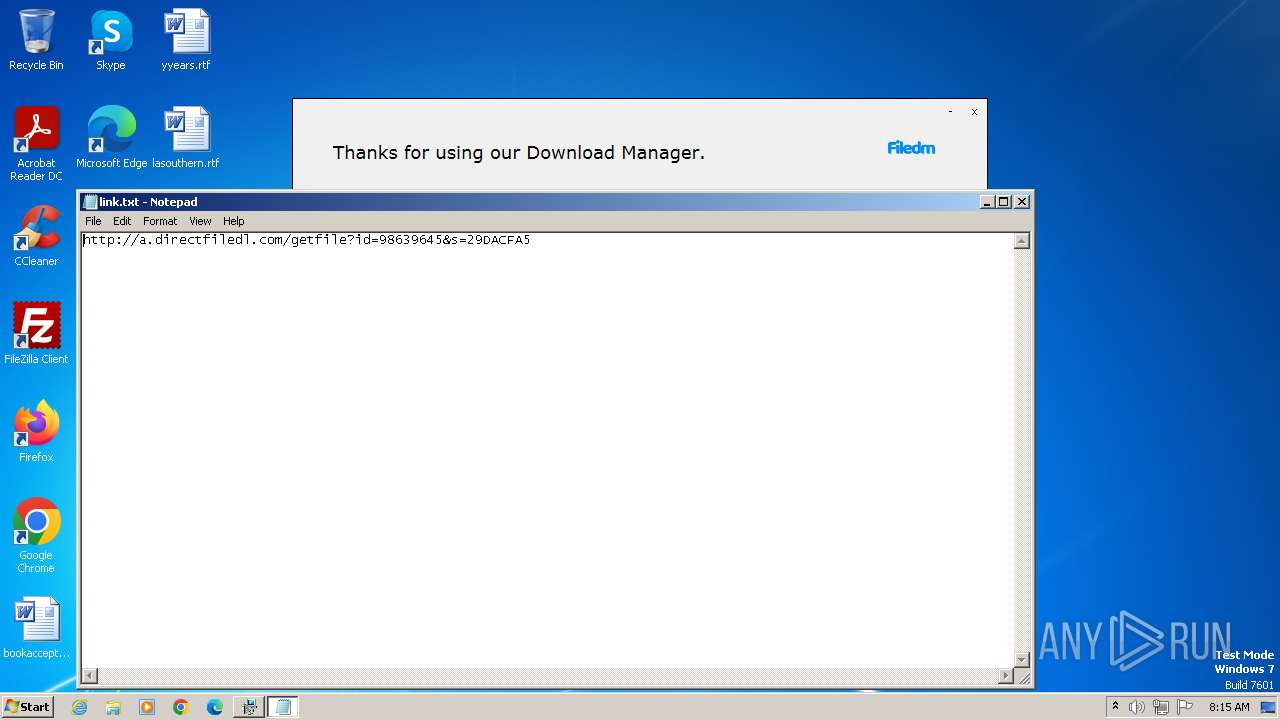
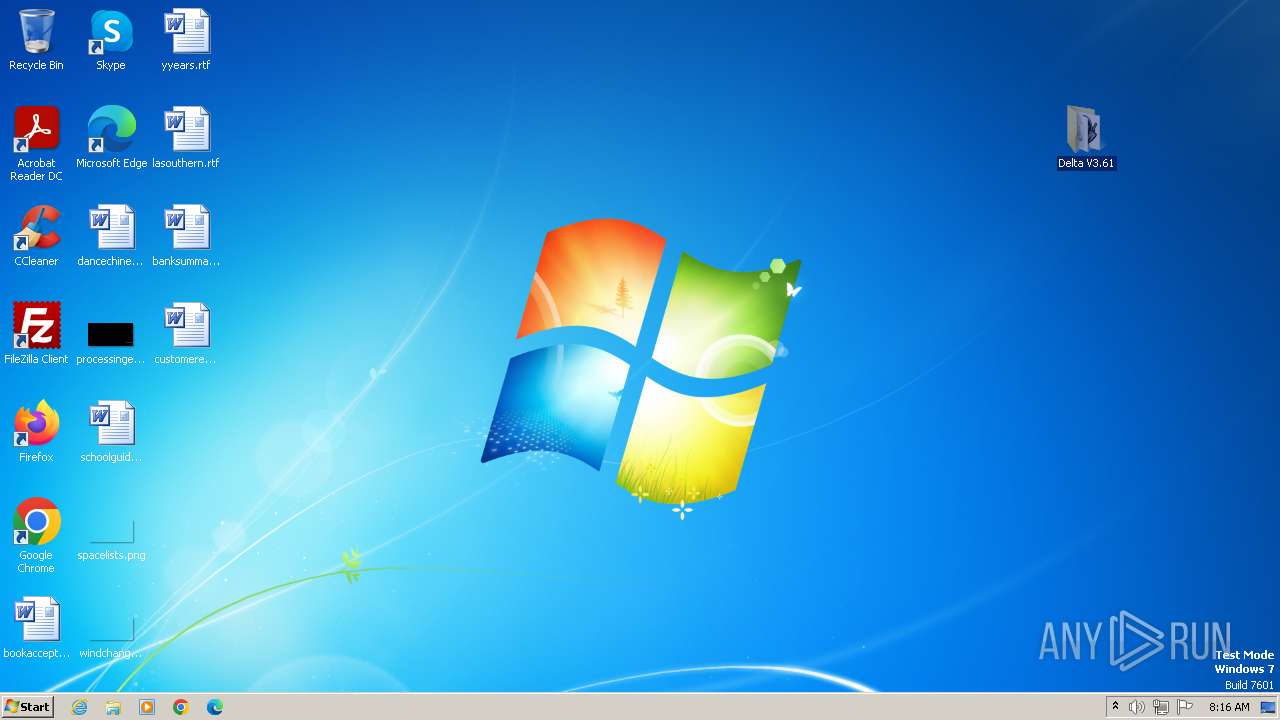
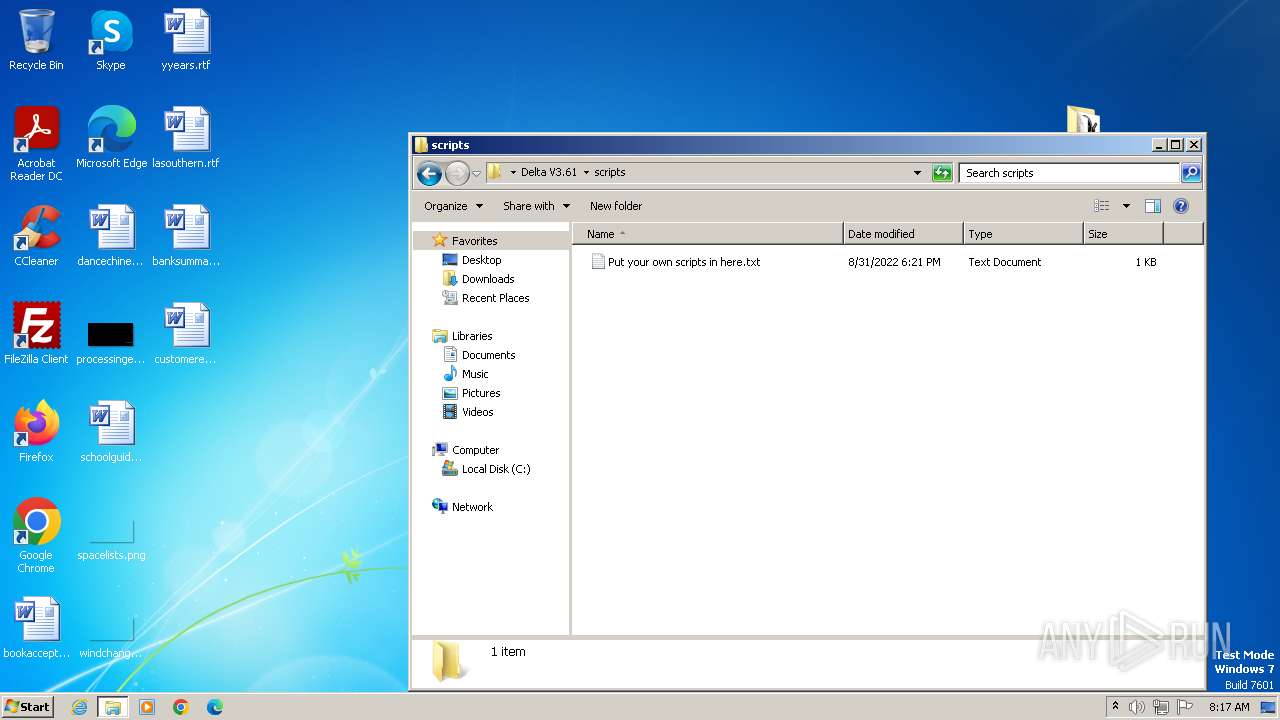
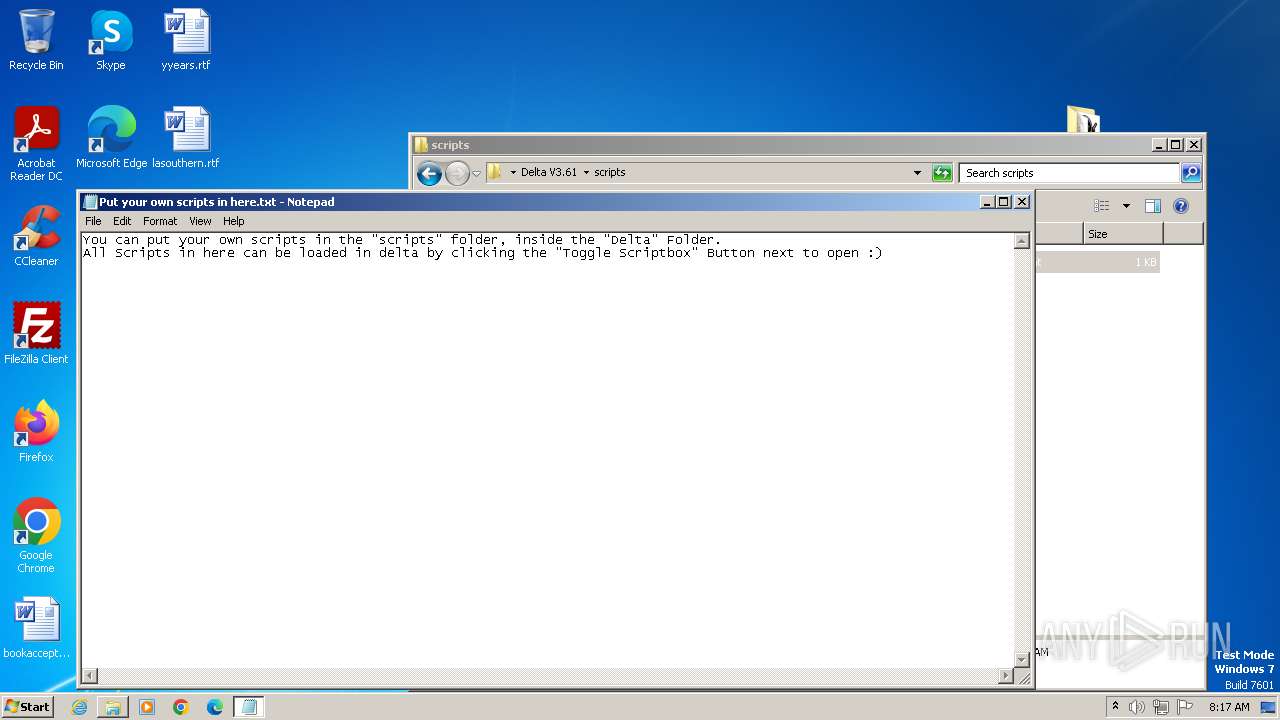
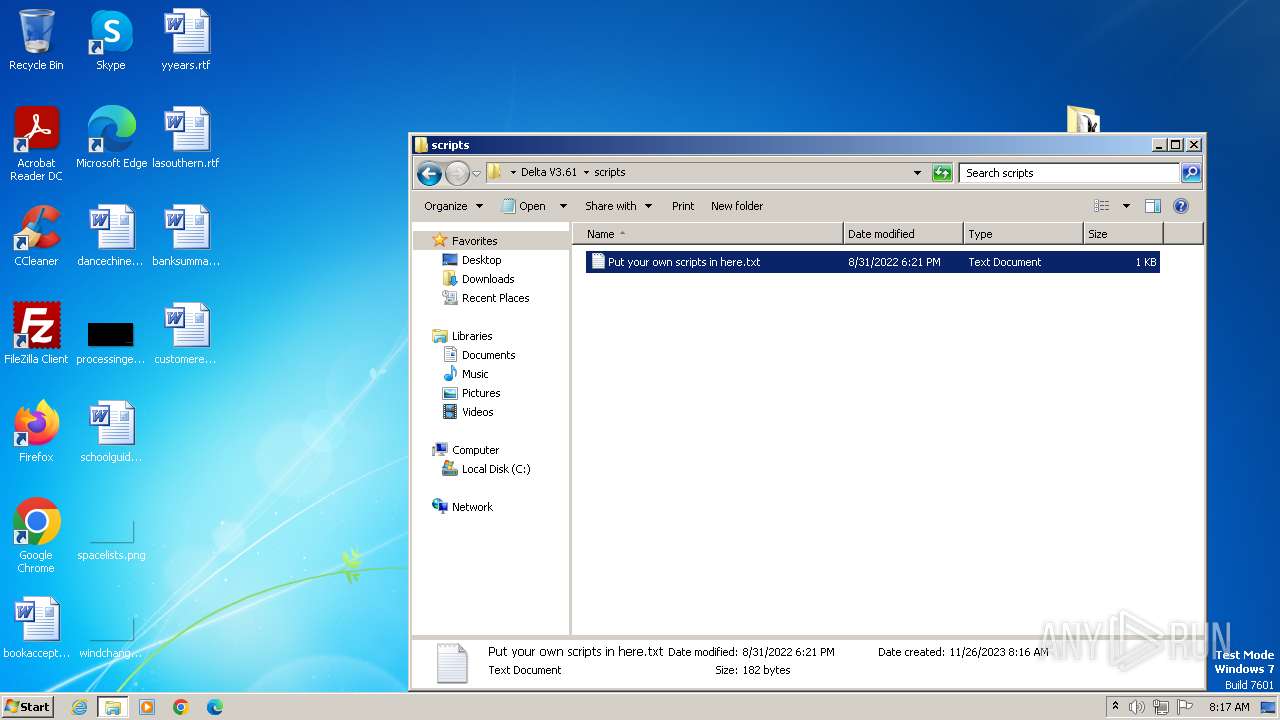
Start notepad (likely ransomware note)
- Delta V3.61 b_98639645.exe (PID: 2364)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3384)
Get information on the list of running processes
- cmd.exe (PID: 3384)
INFO
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2760)
- Delta V3.61 b_98639645.exe (PID: 2364)
- setup98639645.exe (PID: 644)
- setup98639645.exe (PID: 3644)
- Delta.exe (PID: 2092)
- Delta.exe (PID: 2052)
Application launched itself
- iexplore.exe (PID: 948)
- chrome.exe (PID: 3604)
Checks supported languages
- wmpnscfg.exe (PID: 2760)
- Delta V3.61 b_98639645.exe (PID: 2364)
- setup98639645.exe (PID: 644)
- setup98639645.exe (PID: 3644)
- Delta.exe (PID: 2092)
- Delta.exe (PID: 2052)
Reads the computer name
- wmpnscfg.exe (PID: 2760)
- Delta V3.61 b_98639645.exe (PID: 2364)
- setup98639645.exe (PID: 644)
- Delta.exe (PID: 2092)
- Delta.exe (PID: 2052)
- setup98639645.exe (PID: 3644)
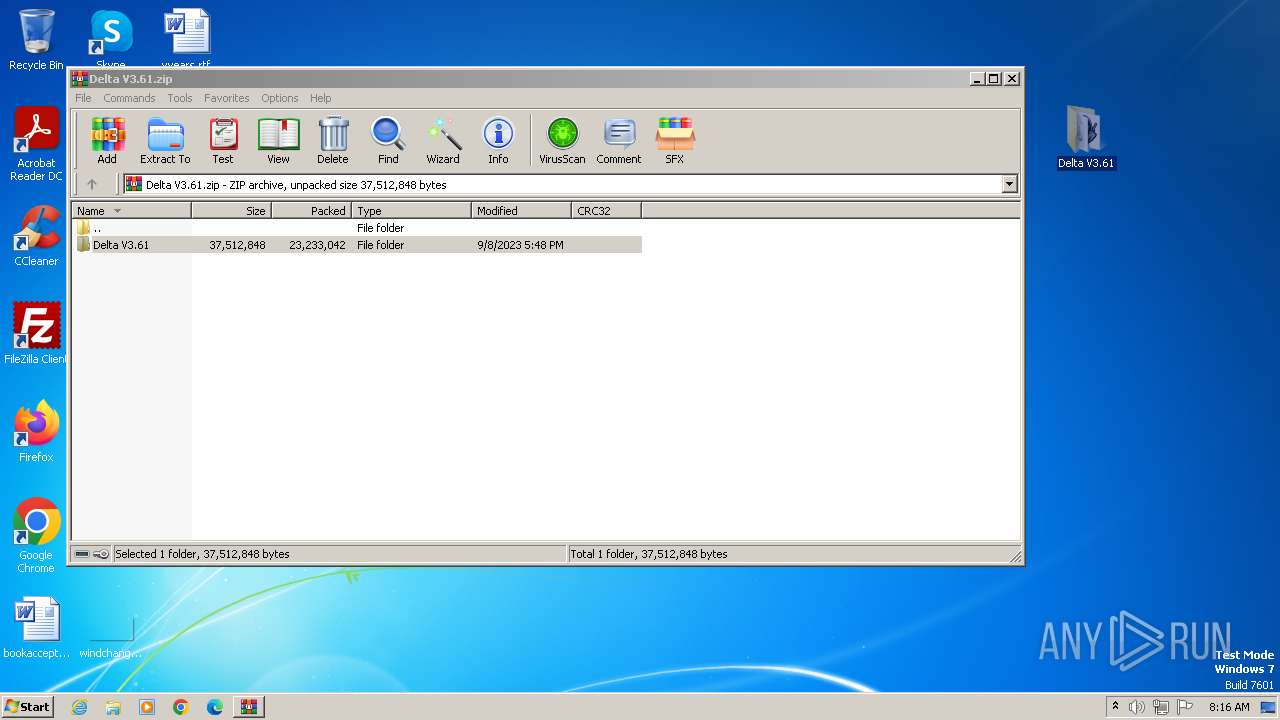
Drops the executable file immediately after the start
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 948)
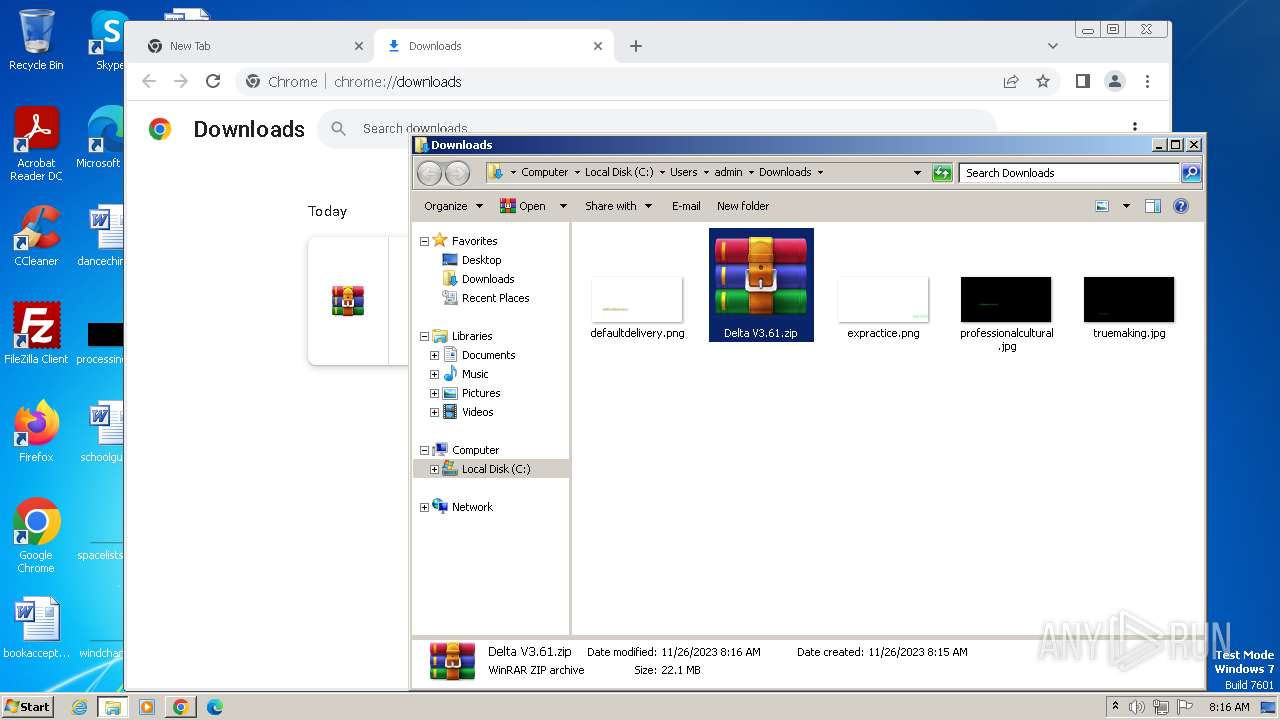
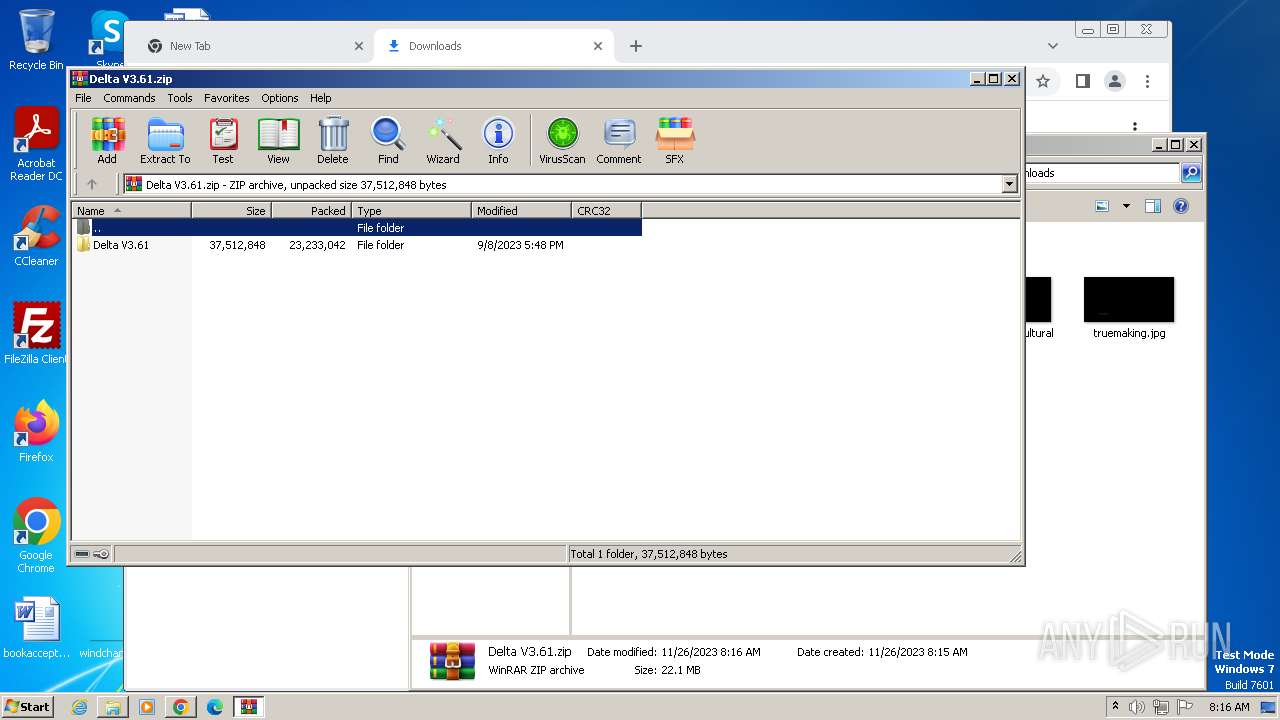
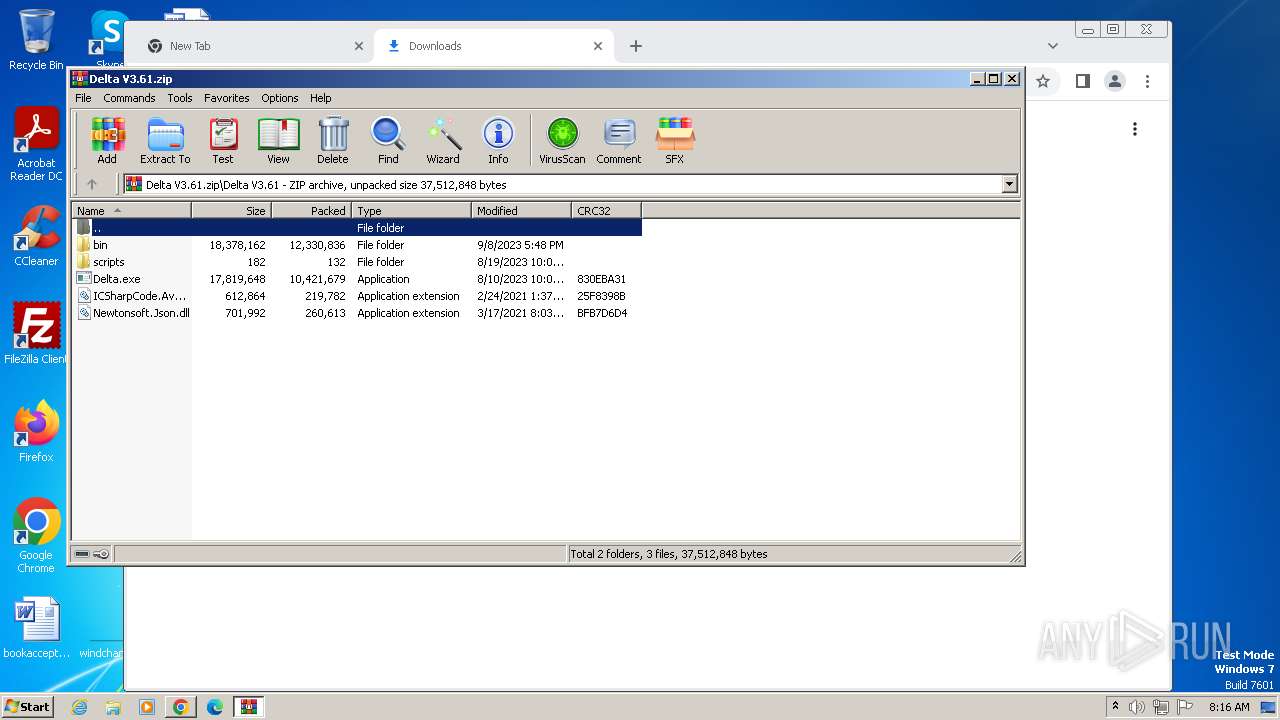
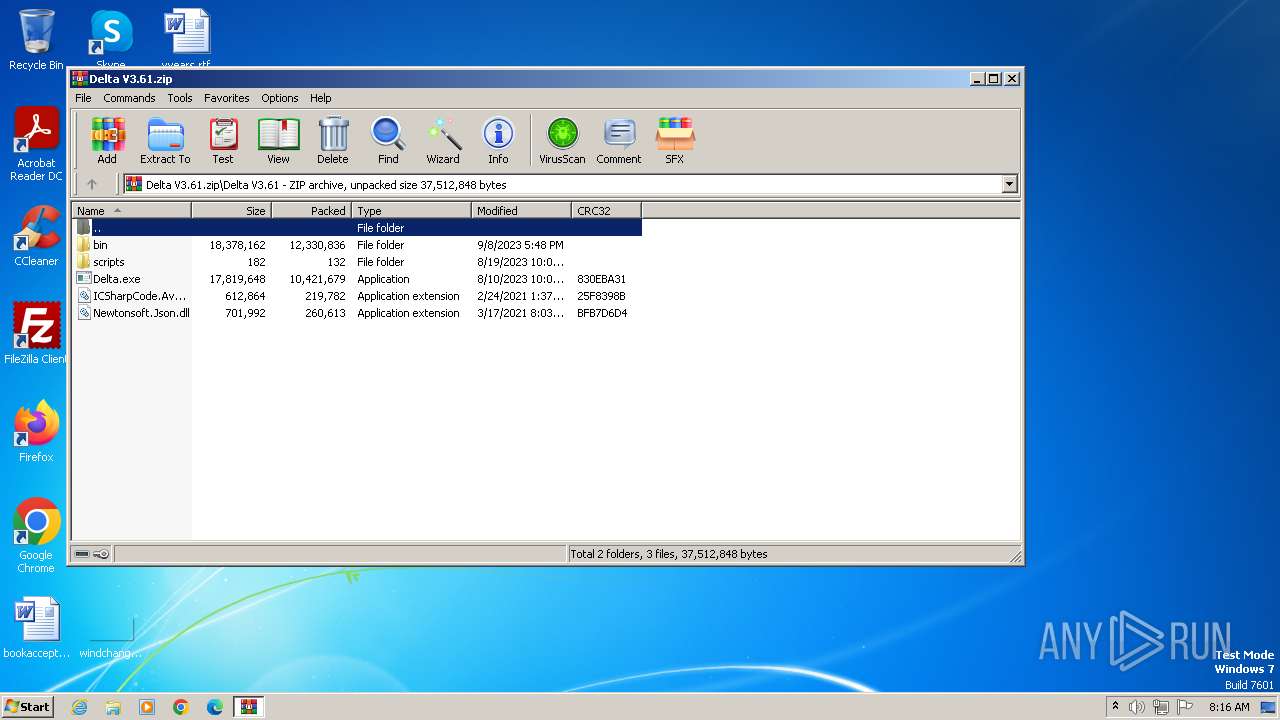
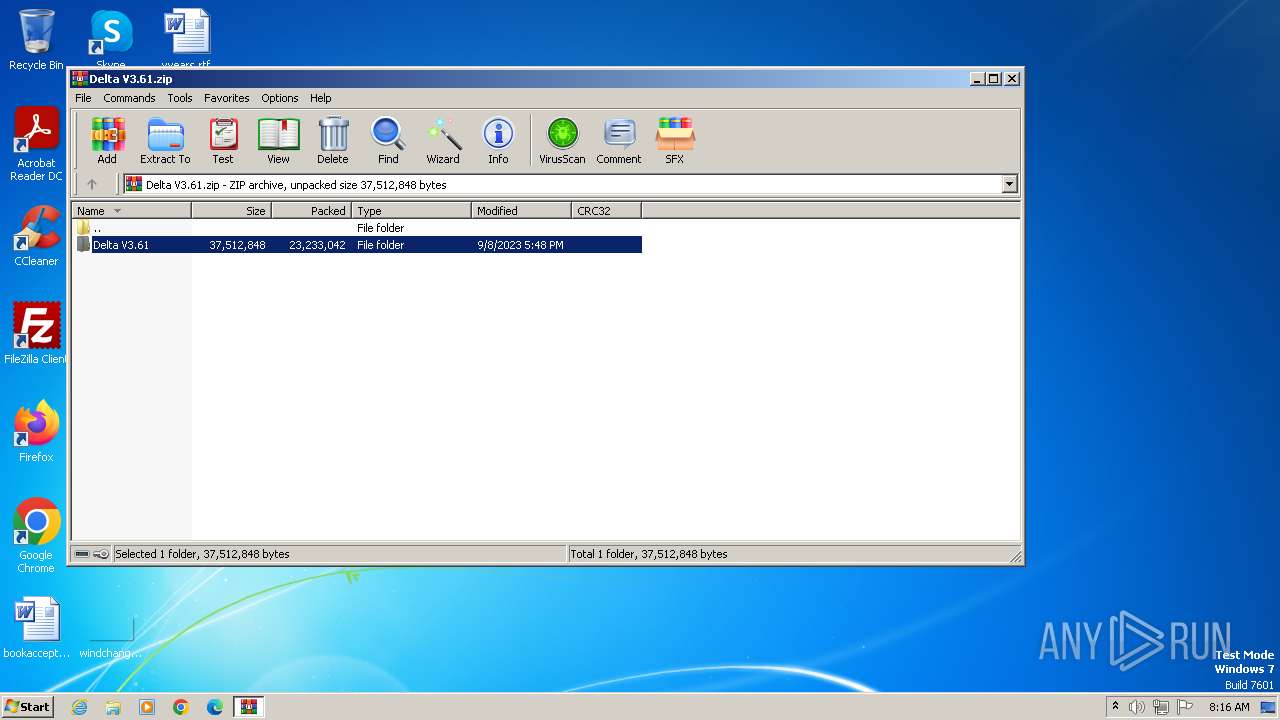
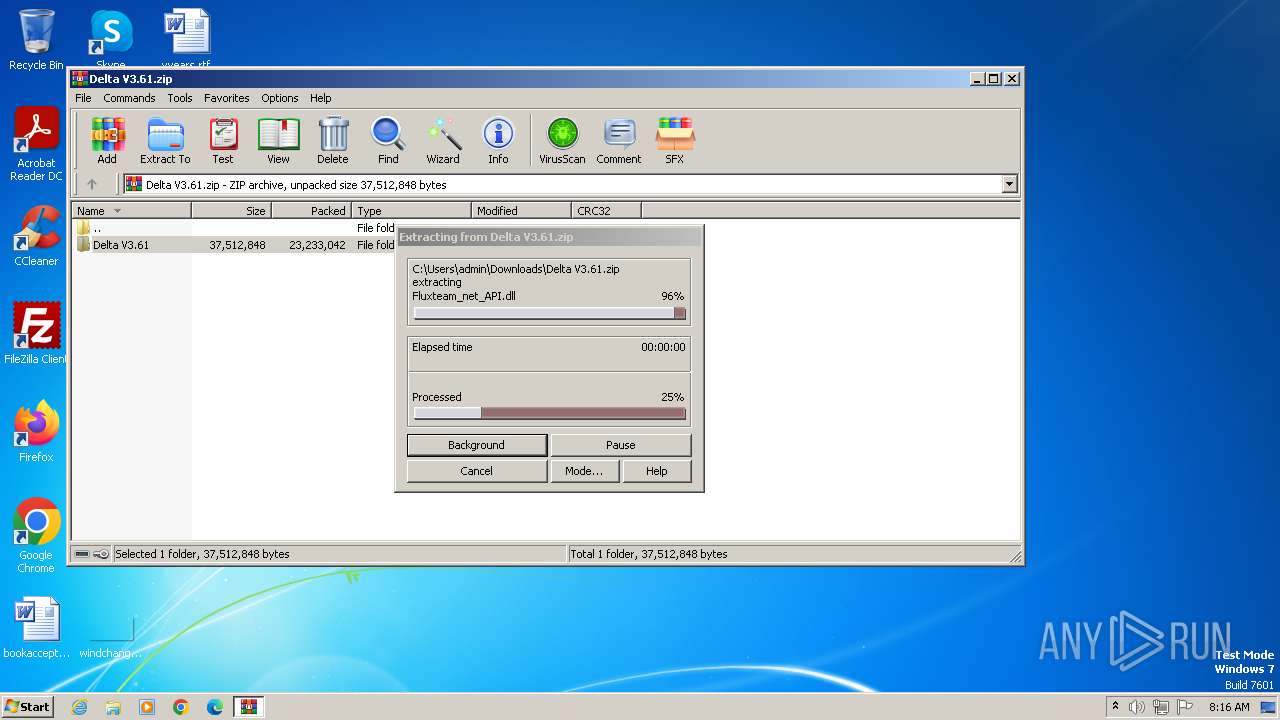
- WinRAR.exe (PID: 2912)
The process uses the downloaded file
- iexplore.exe (PID: 948)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 2100)
- WinRAR.exe (PID: 2912)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3352)
Checks proxy server information
- Delta V3.61 b_98639645.exe (PID: 2364)
Create files in a temporary directory
- setup98639645.exe (PID: 644)
- setup98639645.exe (PID: 3644)
Reads Environment values
- setup98639645.exe (PID: 644)
Reads product name
- setup98639645.exe (PID: 644)
Creates files or folders in the user directory
- setup98639645.exe (PID: 644)
- Delta V3.61 b_98639645.exe (PID: 2364)
Manual execution by a user
- chrome.exe (PID: 3604)
- wmpnscfg.exe (PID: 2760)
- WinRAR.exe (PID: 2912)
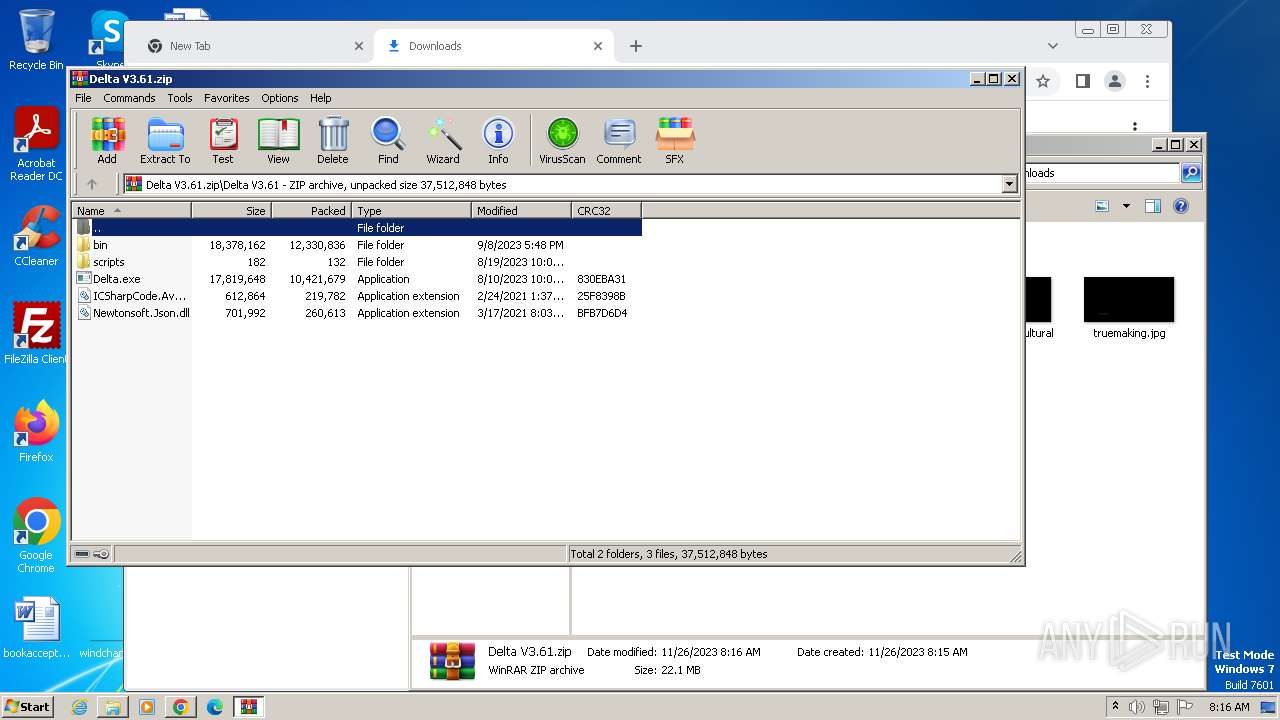
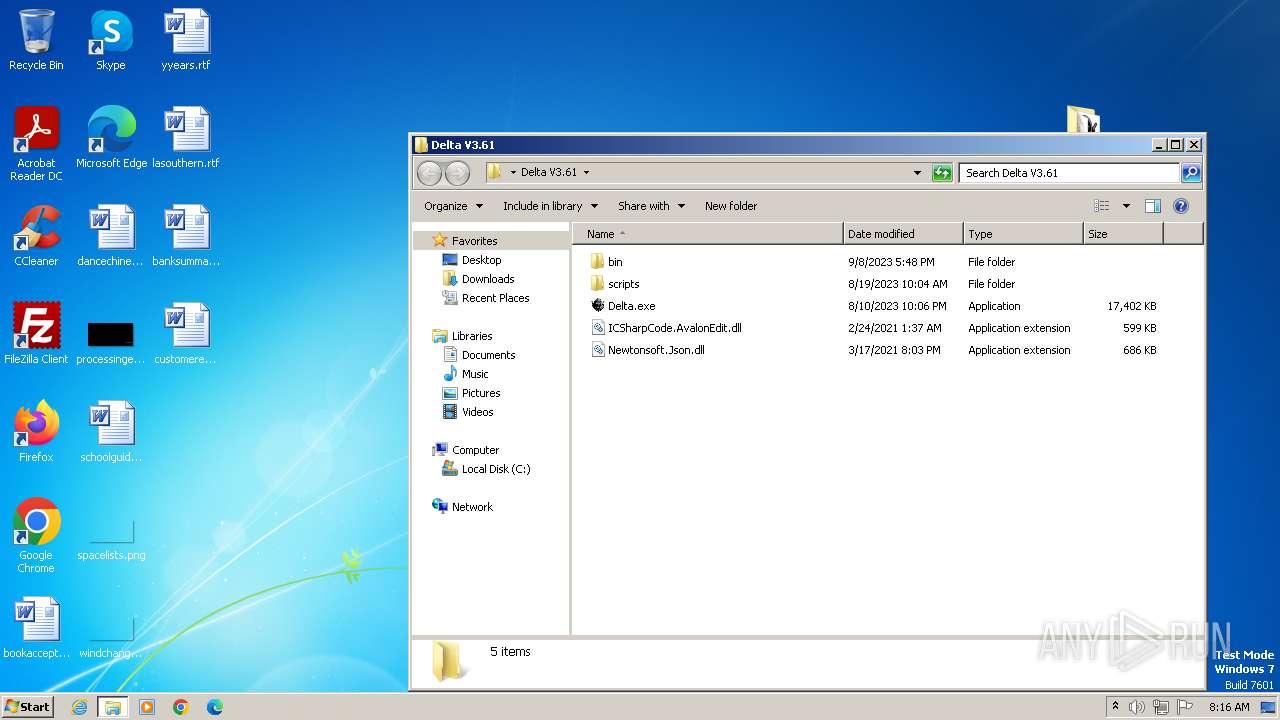
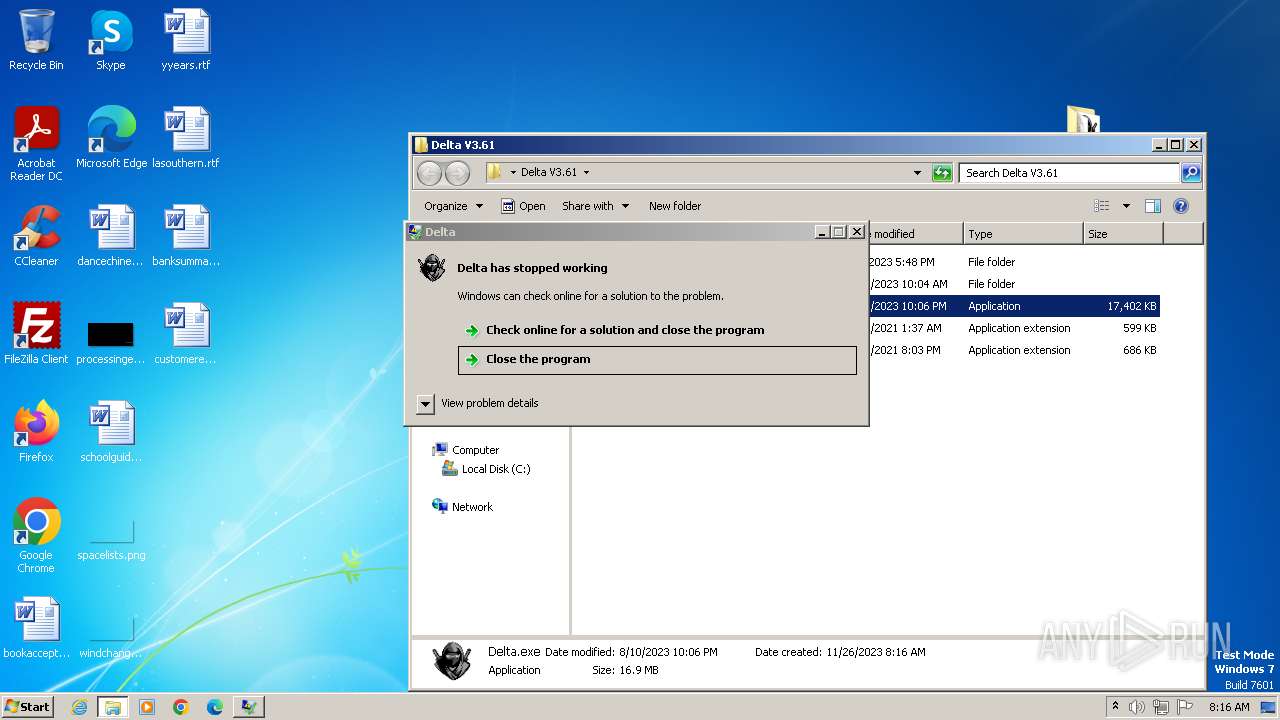
- Delta.exe (PID: 2092)
- Delta.exe (PID: 2052)
- notepad.exe (PID: 1660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
38
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | C:\Users\admin\AppData\Local\setup98639645.exe hhwnd=655848 hreturntoinstaller hextras=id:4bb3f51feab6c7b-DE-KA1rz | C:\Users\admin\AppData\Local\setup98639645.exe | Delta V3.61 b_98639645.exe | ||||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://getfilenow.com/lp?id=Delta%20V3.61%20b_98639645" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
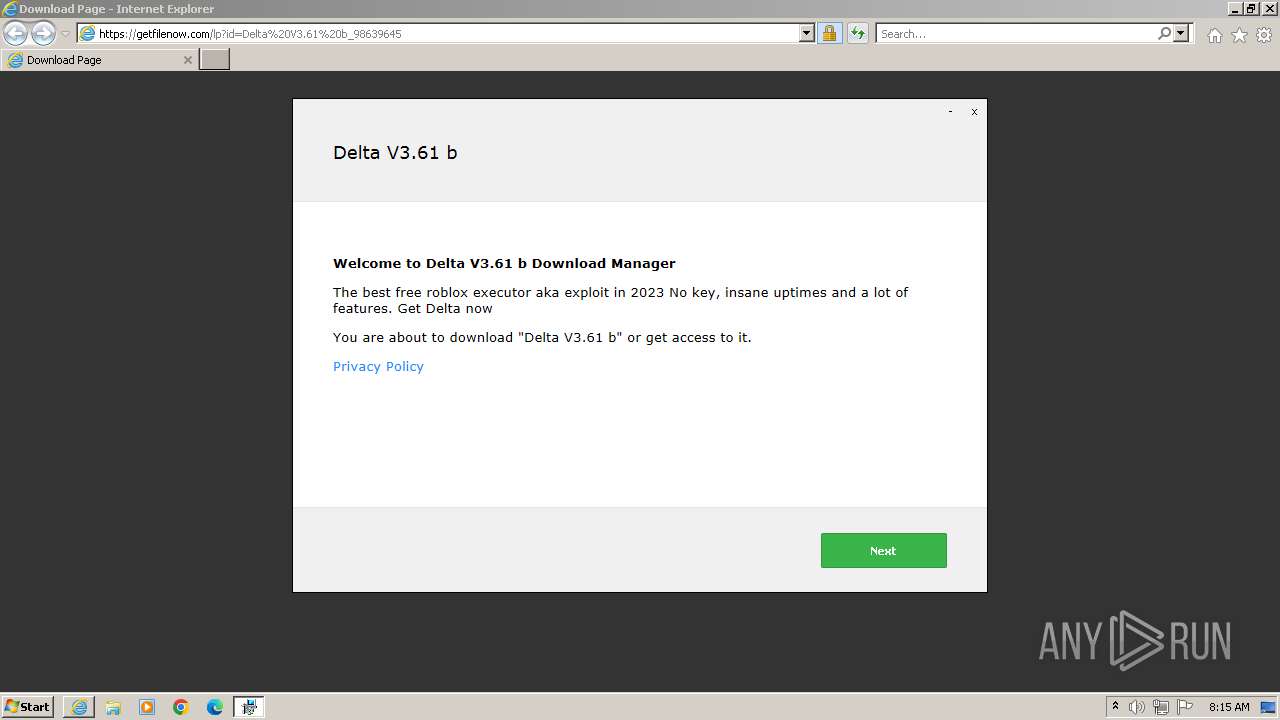
| 1360 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Delta V3.61 b_98639645.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Delta V3.61 b_98639645.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Download Manager Exit code: 3221226540 Version: 1 Modules
| |||||||||||||||
| 1660 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Delta V3.61\scripts\Put your own scripts in here.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=708 --field-trial-handle=1144,i,7384370547479706789,13180164711167822243,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
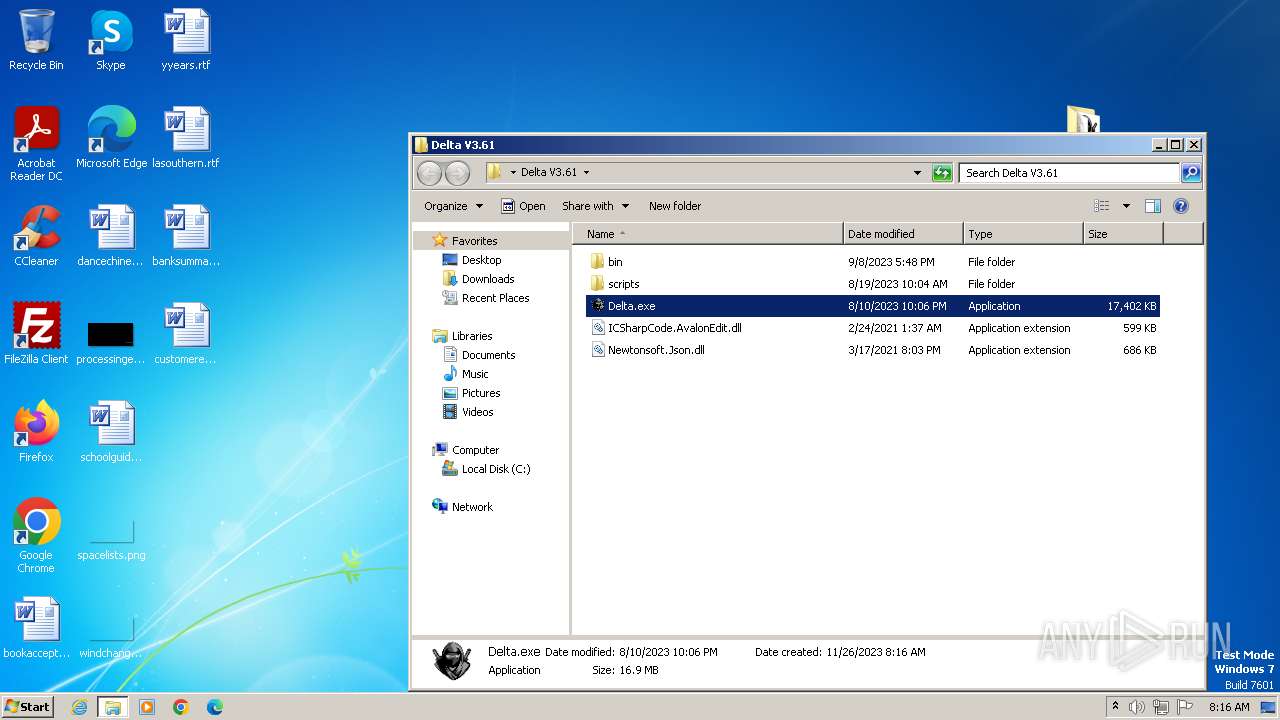
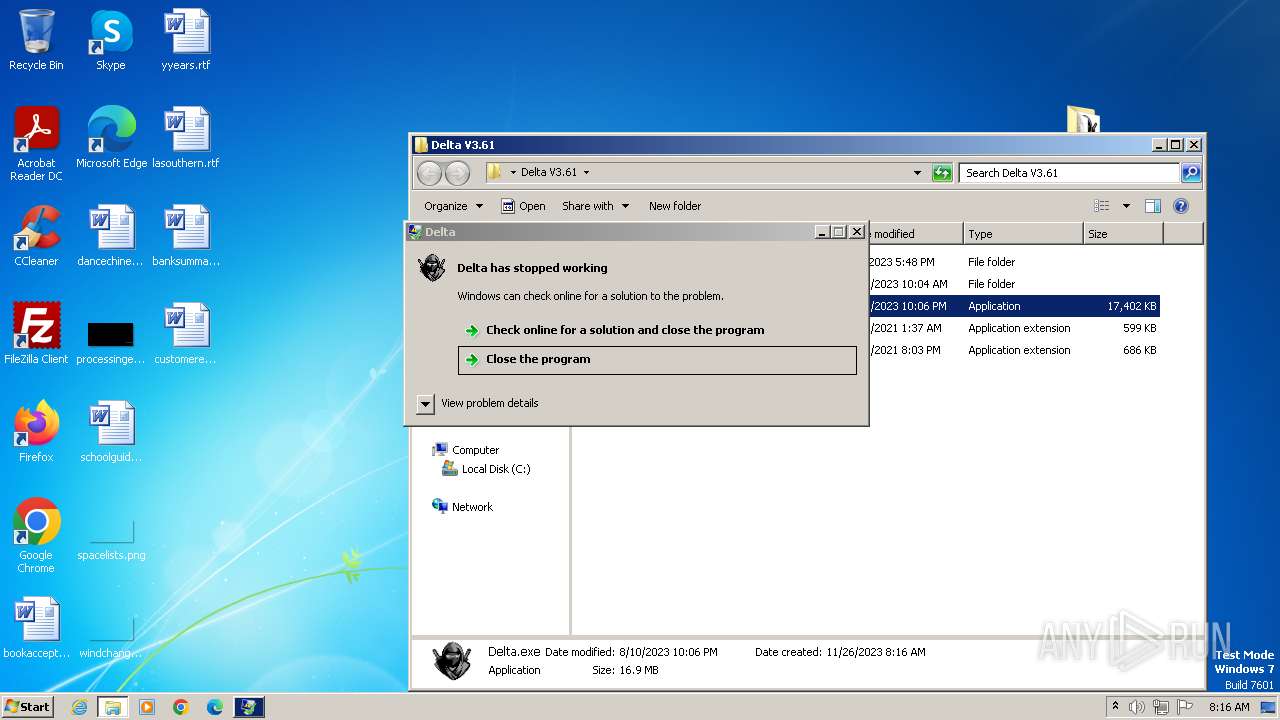
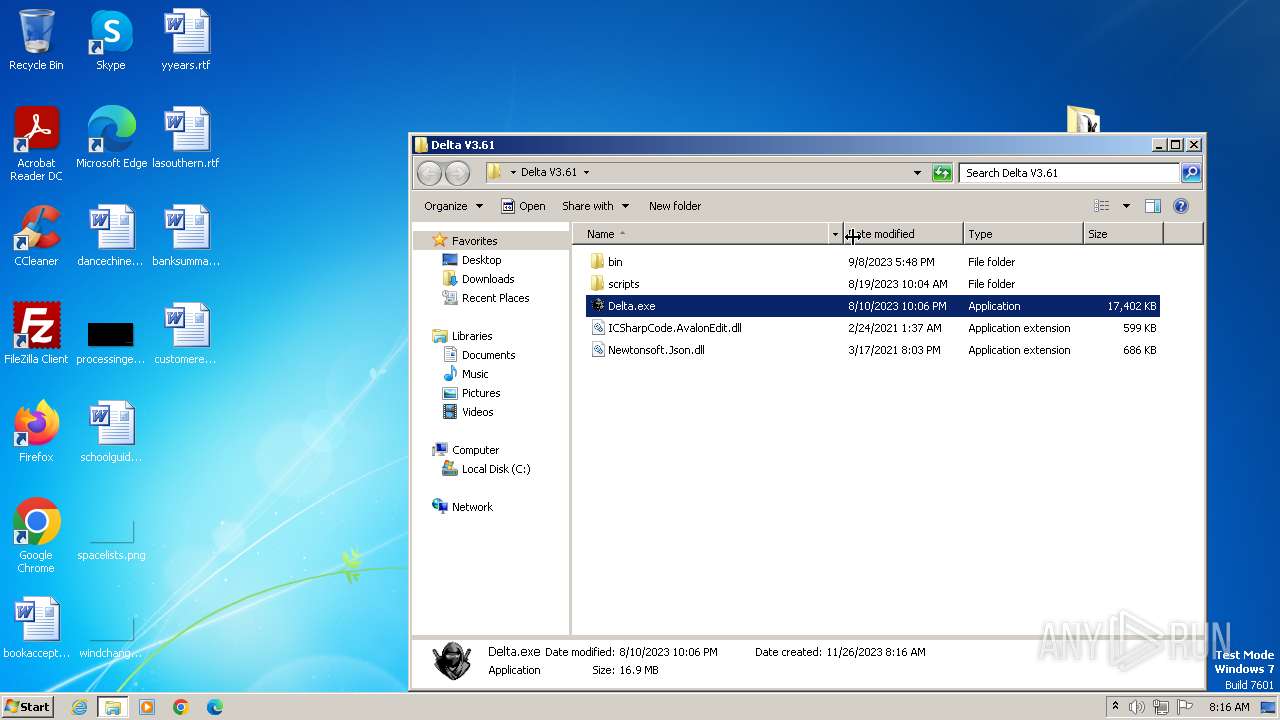
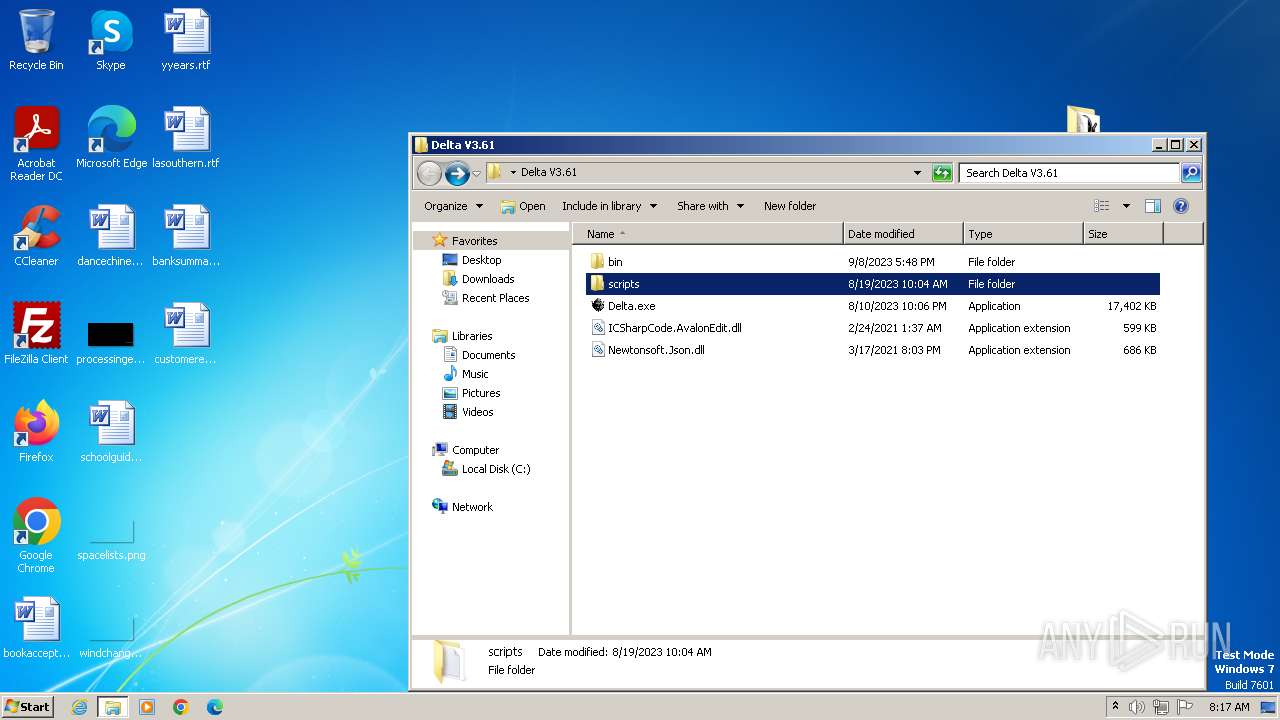
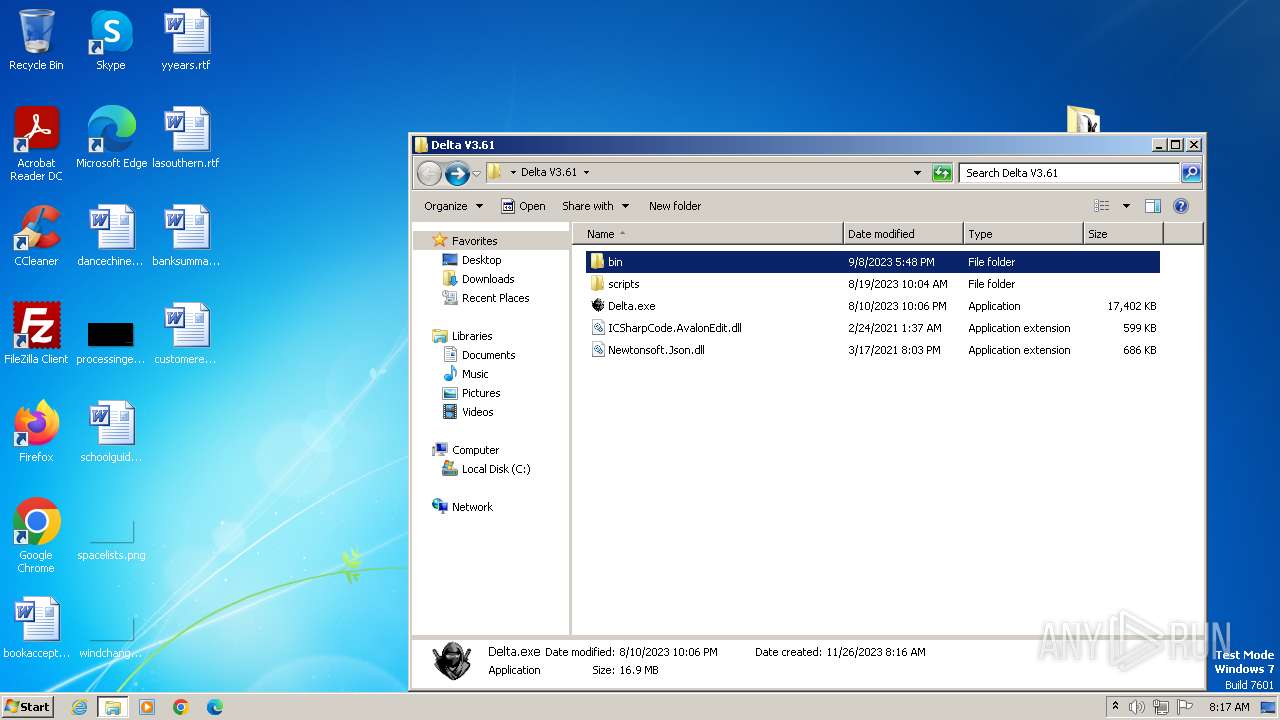
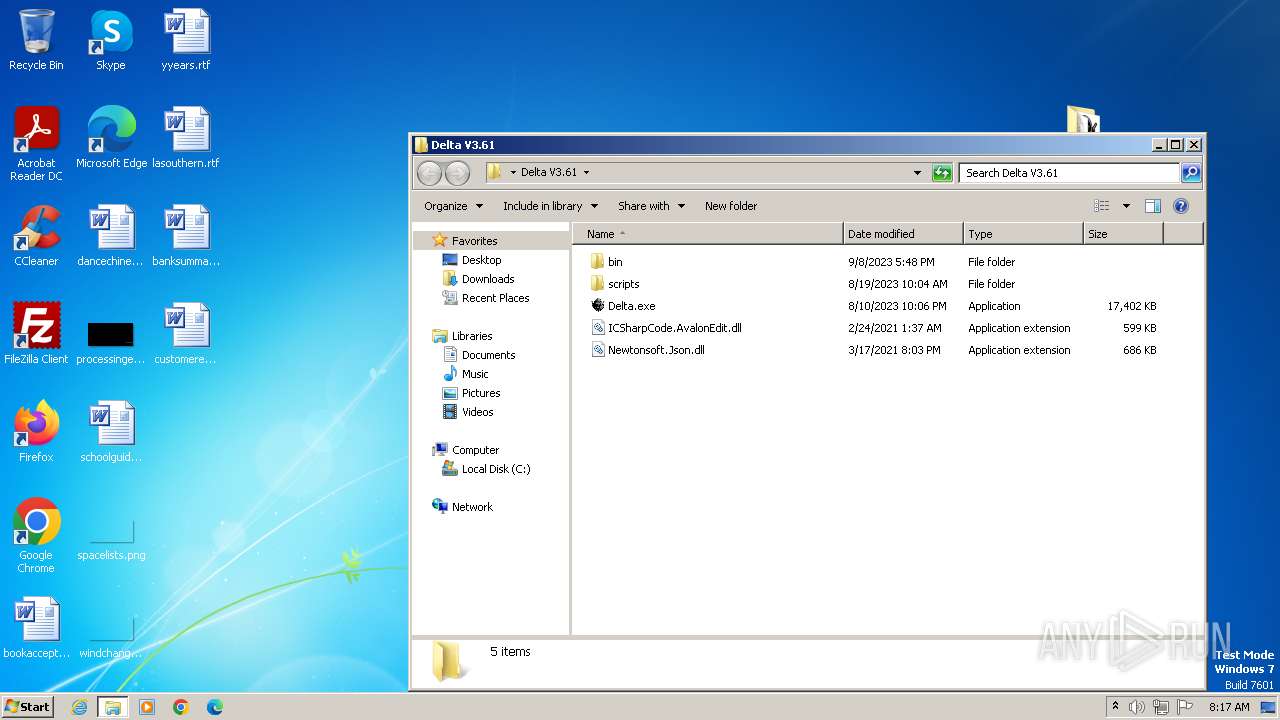
| 2052 | "C:\Users\admin\Desktop\Delta V3.61\Delta.exe" | C:\Users\admin\Desktop\Delta V3.61\Delta.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Delta Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\Desktop\Delta V3.61\Delta.exe" | C:\Users\admin\Desktop\Delta V3.61\Delta.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Delta Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1976 --field-trial-handle=1144,i,7384370547479706789,13180164711167822243,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Delta V3.61 b_98639645.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Delta V3.61 b_98639645.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Download Manager Exit code: 0 Version: 1 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3904 --field-trial-handle=1144,i,7384370547479706789,13180164711167822243,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
35 242
Read events
34 909
Write events
325
Delete events
8
Modification events
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
43
Suspicious files
139
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:2F8E7D2F8DA7D95ED47A7987E74FCBDC | SHA256:7E85E744DADA9690FB122F81B16905FBB6DFC2FF7902C6E4ACF987B4BBC3F746 | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:0A8BB3908AEFC674DB5DD70E924400D5 | SHA256:61EBEA88B28985EB97C73F7B59531916476E7A5D1187333A04F610E9D989AFF4 | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarDBC7.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:D3EB8F495DD8FDF6DF7802D4AF854564 | SHA256:57291C1186355D7BB16BFCDE93880AA14484E1DDB5FEBFBB7CCDA06F5249733A | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[3].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:62EFA20A2633BF752134F0617E0D259F | SHA256:DDB0ADA3617F7971CB3596050A4EA0F76A4E1CC262A8A767C6417B04D115BDA9 | |||
| 948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:7300AFD4563D0BDF43DEBB3DF2BAB9F6 | SHA256:46677FA770A9C2D340757B4CC3A1102F172119888FACD2AC757D8EAE4832CF75 | |||
| 948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:DEC6BBE308EB44937F77160A25EE32DB | SHA256:68A71DE28F488586C2B169F4652347E0A1FD632D48A6D6725393607BFA18BC7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
40
DNS requests
36
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2516 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0e152650b56312b4 | unknown | compressed | 4.66 Kb | unknown |
2516 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?be0537bbbaca182f | unknown | compressed | 4.66 Kb | unknown |
2516 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?96b0e3886bc1c9da | unknown | compressed | 61.6 Kb | unknown |
2516 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2516 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8e9952842b8b9b0b | unknown | compressed | 61.6 Kb | unknown |
2516 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
2364 | Delta V3.61 b_98639645.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/s/gts1d4/BLyg_-h63RA/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEACRI2vGqzWlEof0zfA2Du0%3D | unknown | binary | 471 b | unknown |
2364 | Delta V3.61 b_98639645.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/s/gts1d4/fBhj9wRXMMA/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEGMmYrCWCX4LCfKe4VeZo4Q%3D | unknown | binary | 471 b | unknown |
948 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3792 | chrome.exe | GET | 200 | 167.235.218.62:80 | http://a.directfiledl.com/getfile?id=98639645&s=29DACFA5 | unknown | compressed | 22.1 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | iexplore.exe | 188.114.97.3:443 | getfilenow.com | CLOUDFLARENET | NL | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2516 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2516 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
948 | iexplore.exe | 188.114.97.3:443 | getfilenow.com | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getfilenow.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.dlsft.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report